| download: | /TeraTermProject/teraterm/releases/download/v5.2/teraterm-5.2.exe |
| Full analysis: | https://app.any.run/tasks/7447cf49-aaa8-4542-bc92-01216d54a584 |
| Verdict: | Malicious activity |
| Analysis date: | February 28, 2024, 19:12:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4AC117A0319B40C745F2E0A8DBC7CBC1 |
| SHA1: | 41D35A040E55C282E7AAA8EE363EC0B6BF226352 |
| SHA256: | 2FFA22571B93F5F2BA03A41FCE6C9F8CB9B5D1D429AE48242128481AC4A81718 |
| SSDEEP: | 98304:m+cD4dncTBPR/F8ZGl2ICAgdbrGFUkNv25XOIqjFZb+nDAZA+4LmjsuQoZSwEPes:bnyESRVY0SaMPyrRaWYh |
MALICIOUS
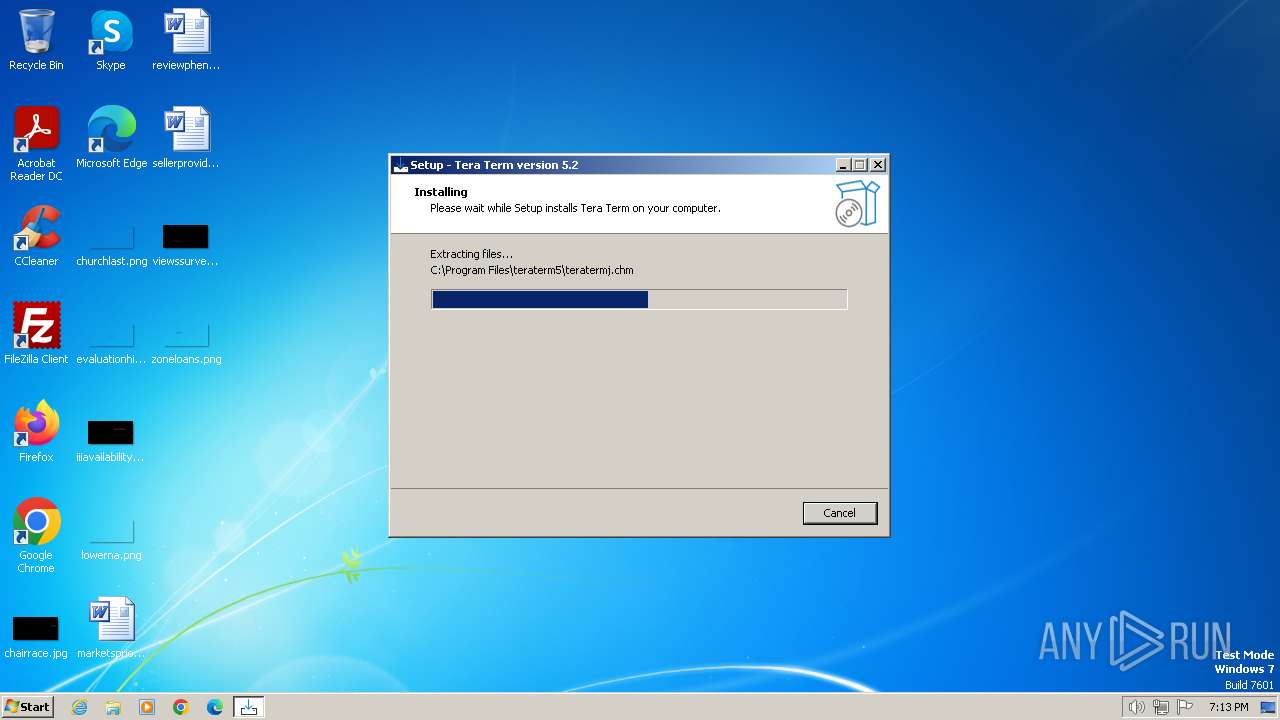
Drops the executable file immediately after the start
- teraterm-5.2.exe (PID: 3672)
- teraterm-5.2.exe (PID: 2964)
- teraterm-5.2.tmp (PID: 2752)
SUSPICIOUS
Executable content was dropped or overwritten
- teraterm-5.2.exe (PID: 3672)
- teraterm-5.2.exe (PID: 2964)
- teraterm-5.2.tmp (PID: 2752)
Reads the Windows owner or organization settings
- teraterm-5.2.tmp (PID: 2752)
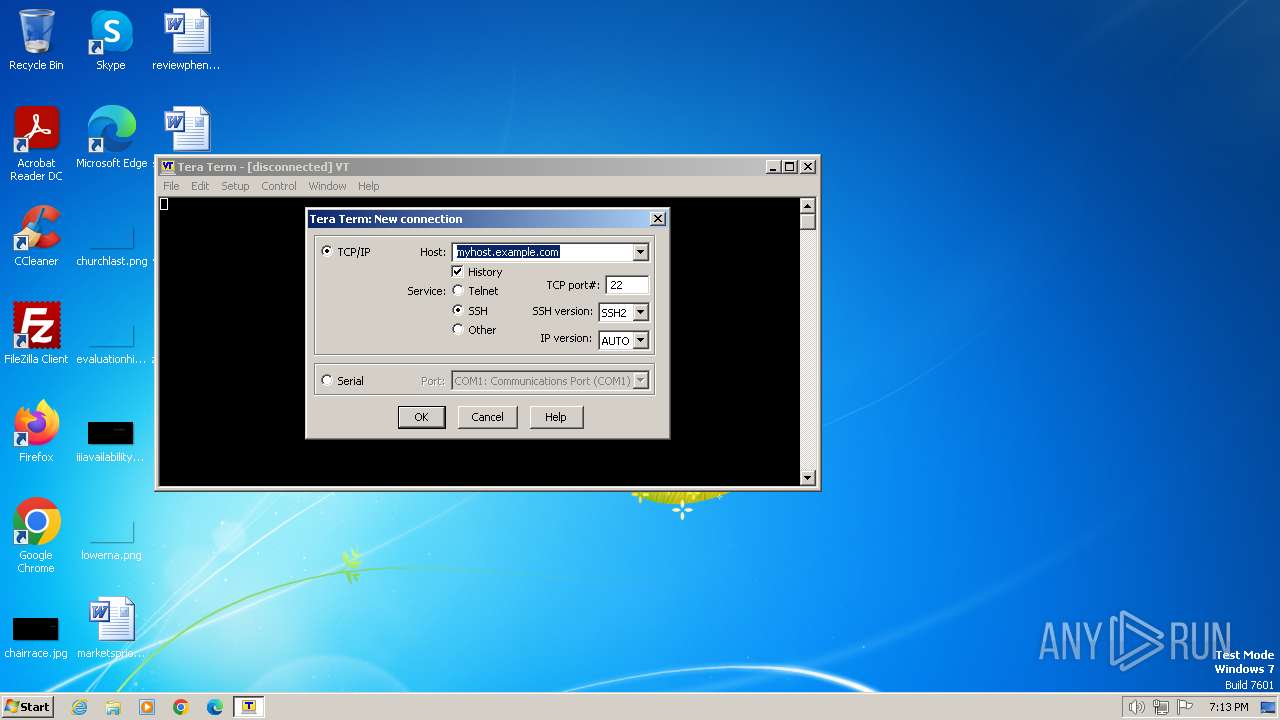
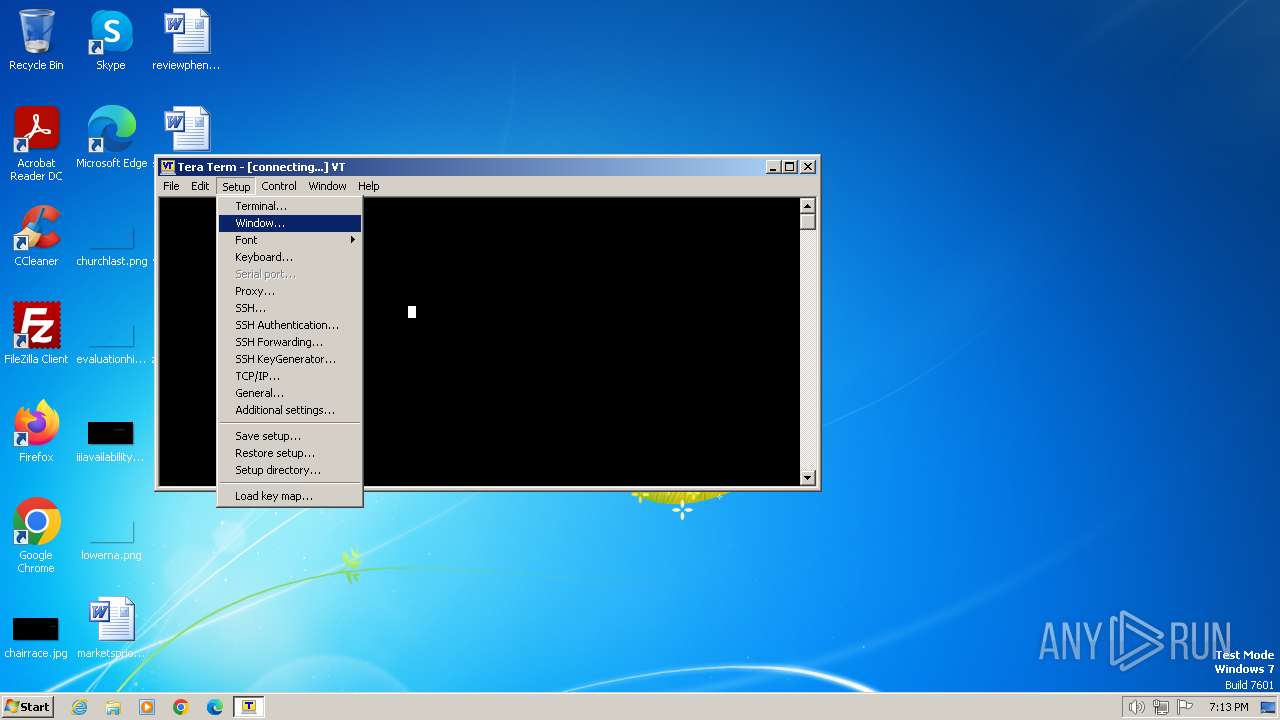
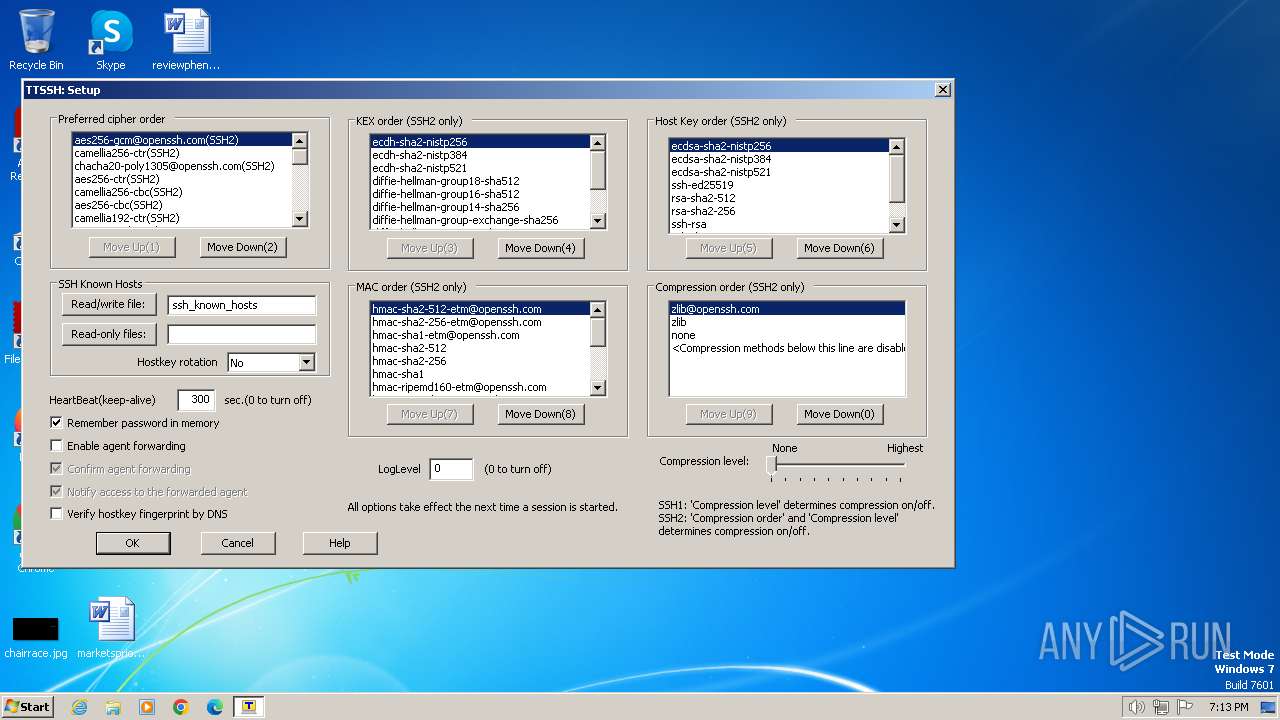
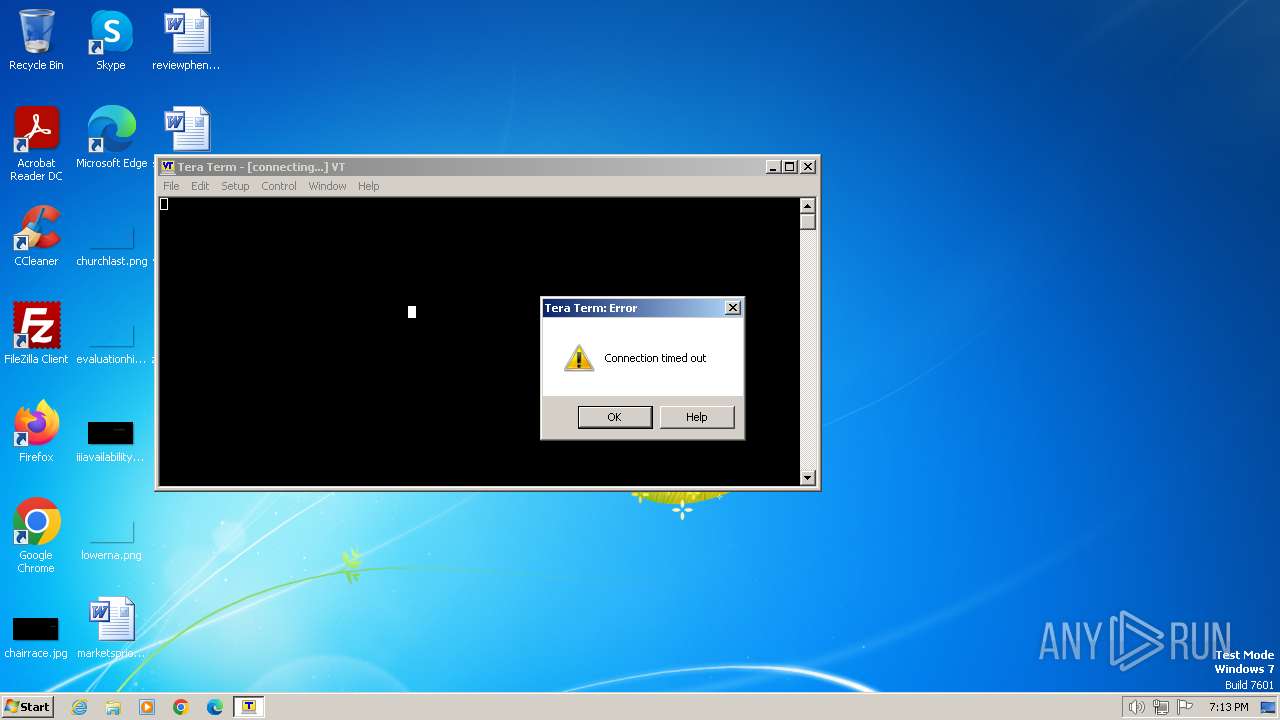
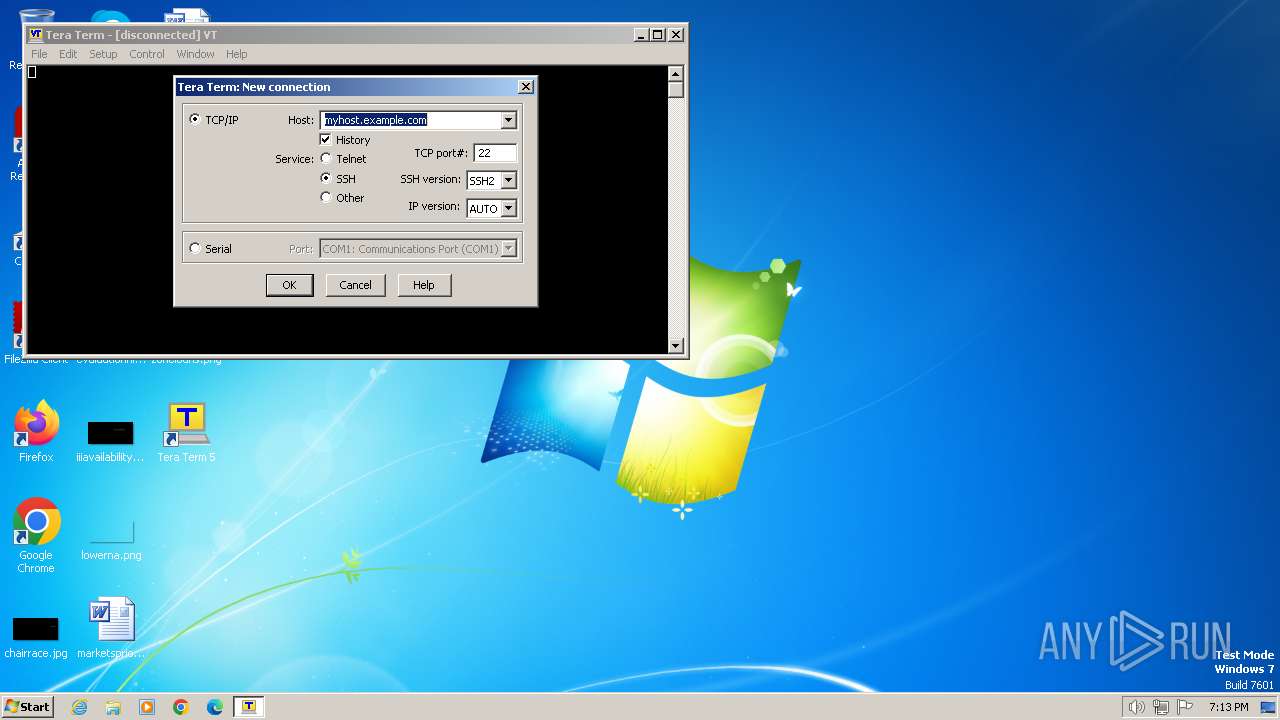
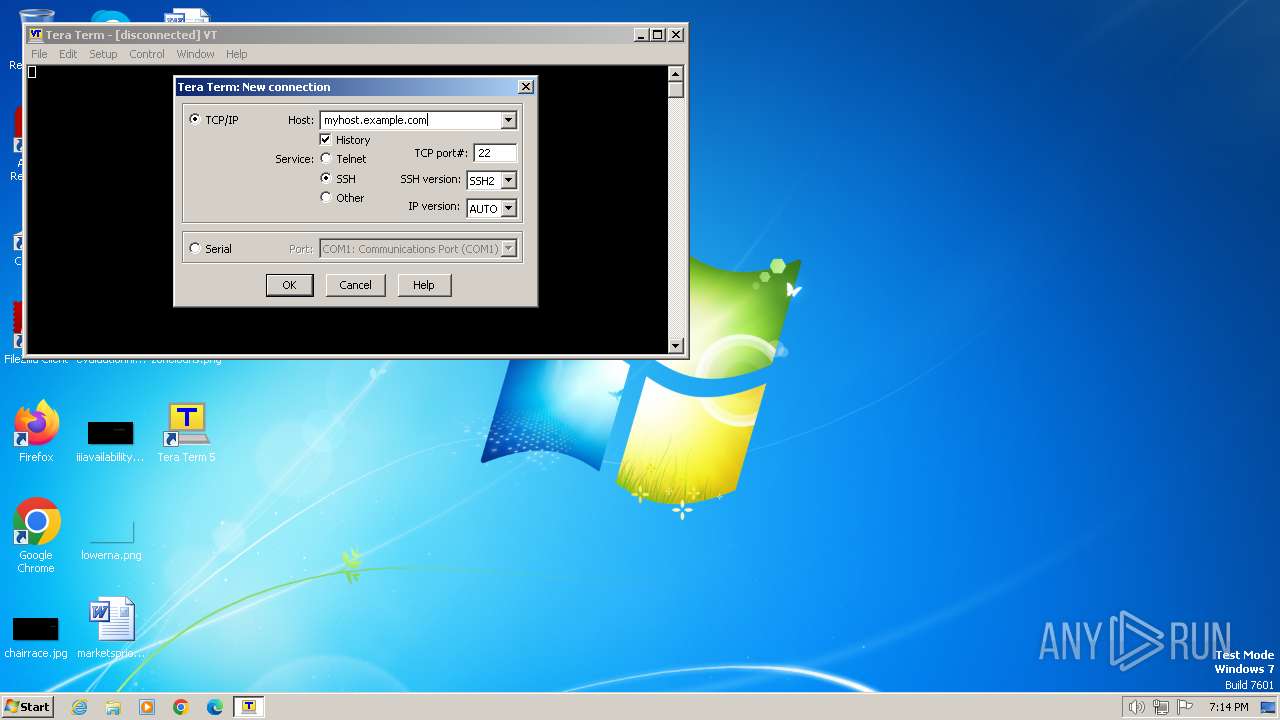
Connects to SSH
- ttermpro.exe (PID: 2340)
Reads the date of Windows installation
- ttermpro.exe (PID: 2340)
INFO
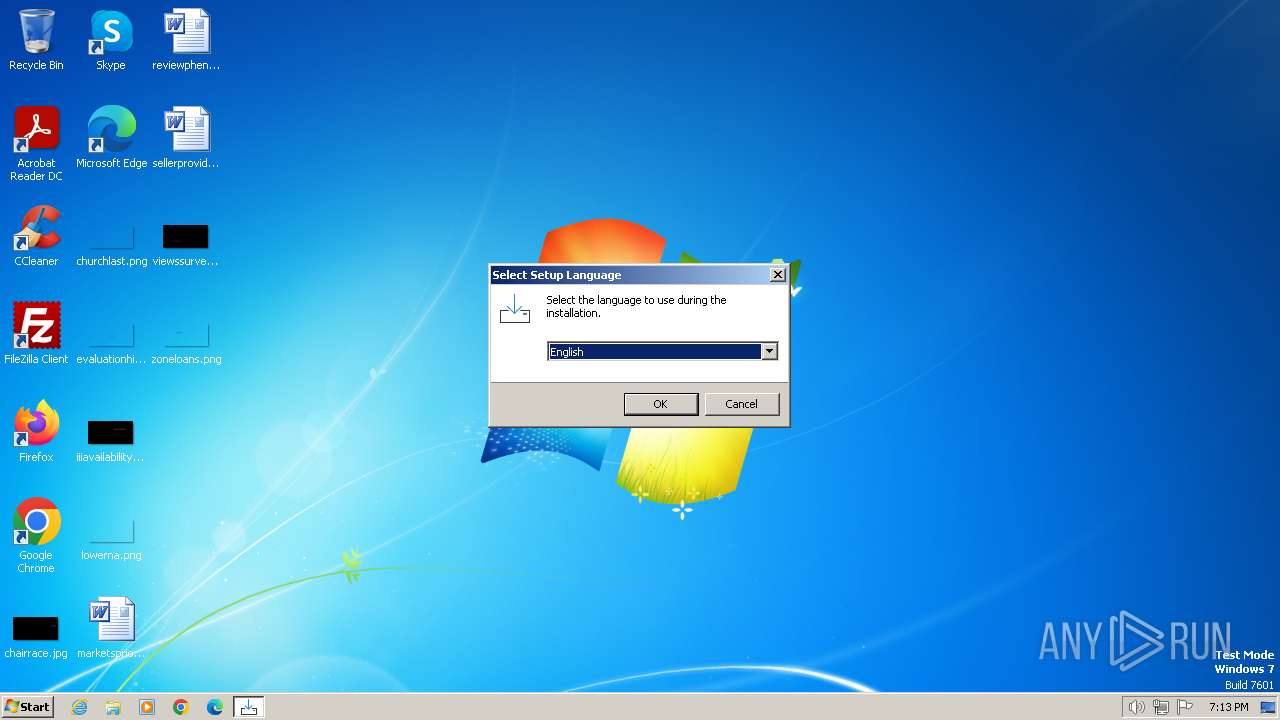
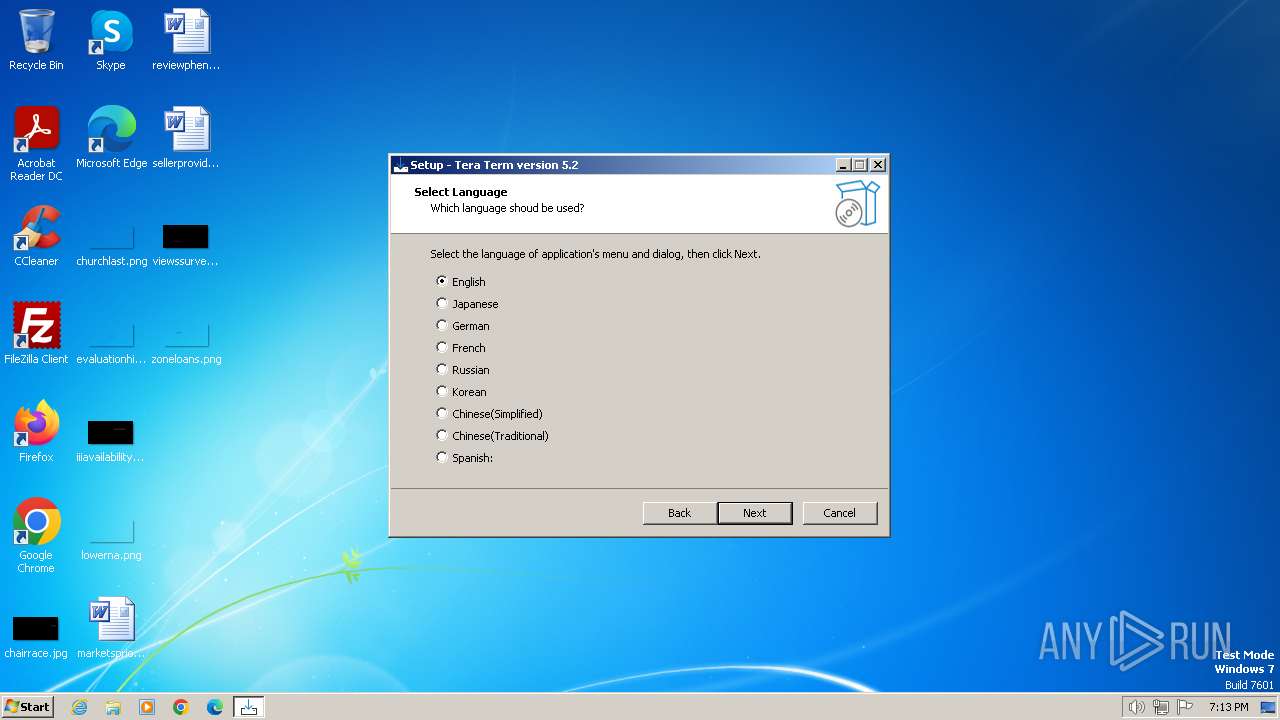
Checks supported languages
- teraterm-5.2.exe (PID: 3672)
- teraterm-5.2.tmp (PID: 4052)
- teraterm-5.2.exe (PID: 2964)
- teraterm-5.2.tmp (PID: 2752)
- ttermpro.exe (PID: 2692)
- ttermpro.exe (PID: 2340)
Reads the computer name
- teraterm-5.2.tmp (PID: 4052)
- teraterm-5.2.tmp (PID: 2752)
- ttermpro.exe (PID: 2692)
- ttermpro.exe (PID: 2340)
Create files in a temporary directory
- teraterm-5.2.exe (PID: 3672)
- teraterm-5.2.exe (PID: 2964)
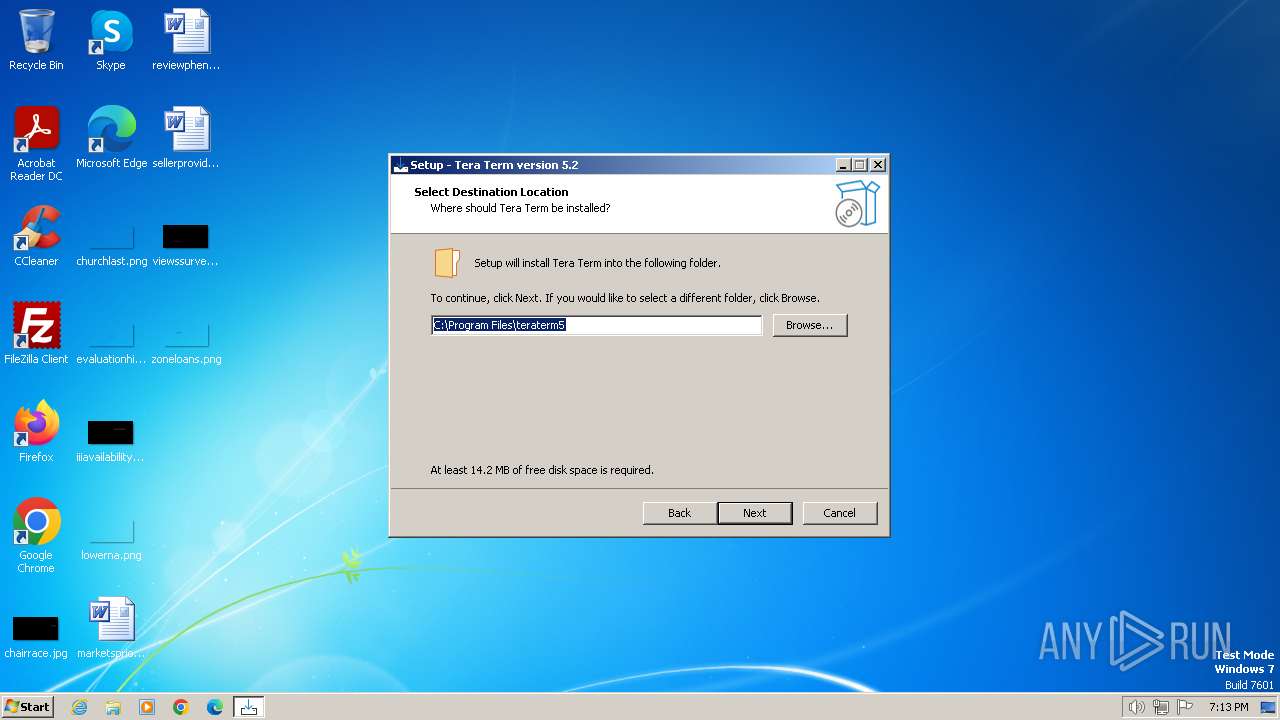
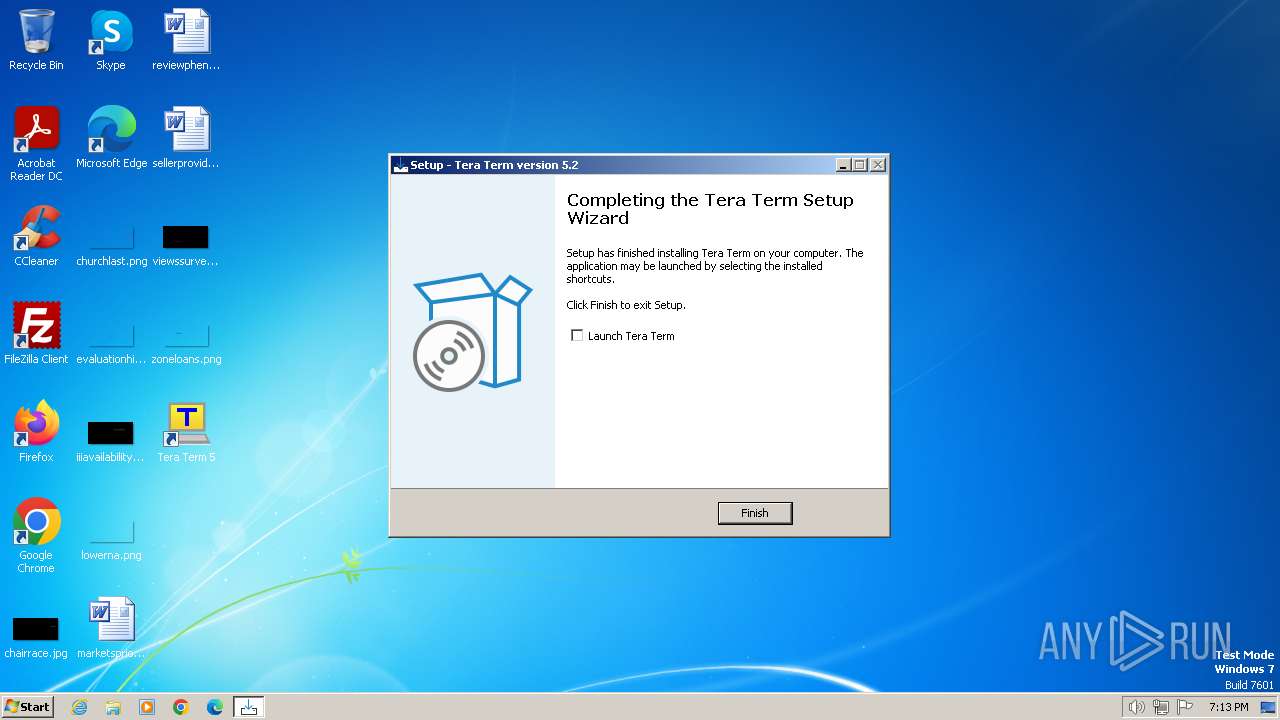
Creates files in the program directory
- teraterm-5.2.tmp (PID: 2752)
Creates a software uninstall entry
- teraterm-5.2.tmp (PID: 2752)
Reads the machine GUID from the registry
- ttermpro.exe (PID: 2340)
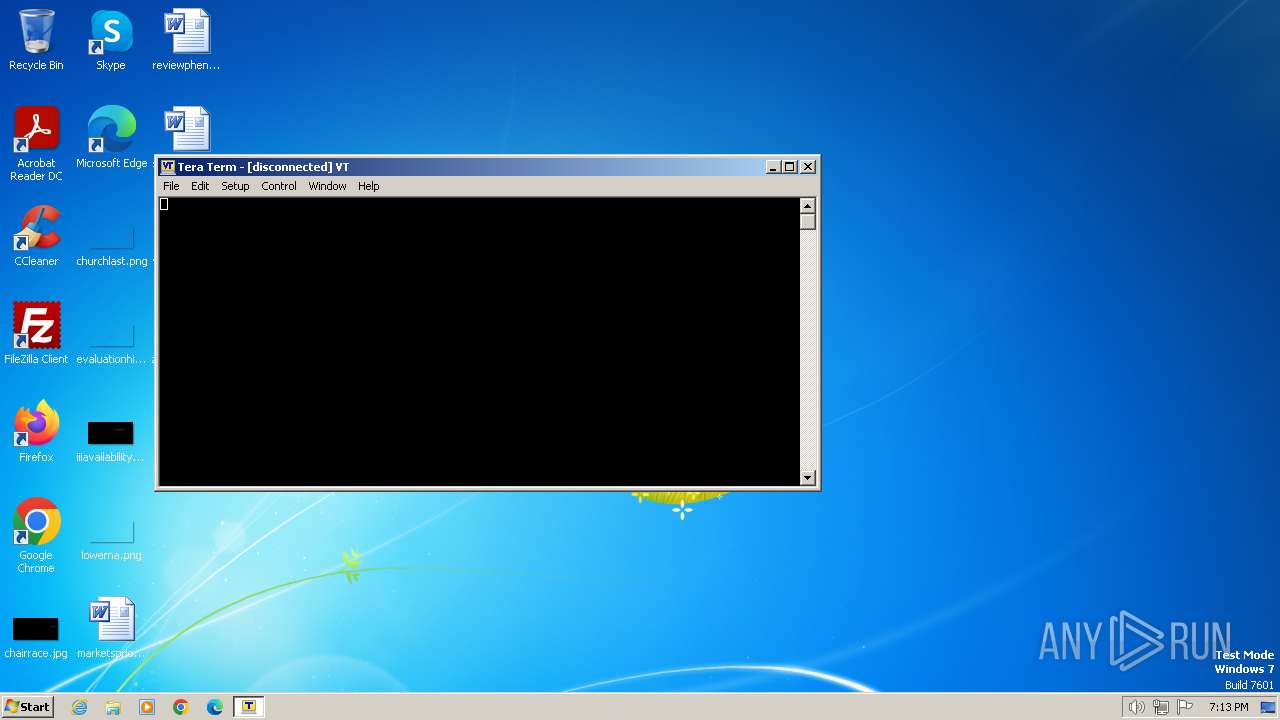
Manual execution by a user
- ttermpro.exe (PID: 2692)
Creates files or folders in the user directory
- ttermpro.exe (PID: 2340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (53.5) |
|---|---|---|
| .exe | | | InstallShield setup (21) |
| .exe | | | Win32 EXE PECompact compressed (generic) (20.2) |
| .exe | | | Win32 Executable (generic) (2.1) |
| .exe | | | Win16/32 Executable Delphi generic (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:02:15 14:54:16+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741888 |
| InitializedDataSize: | 89600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
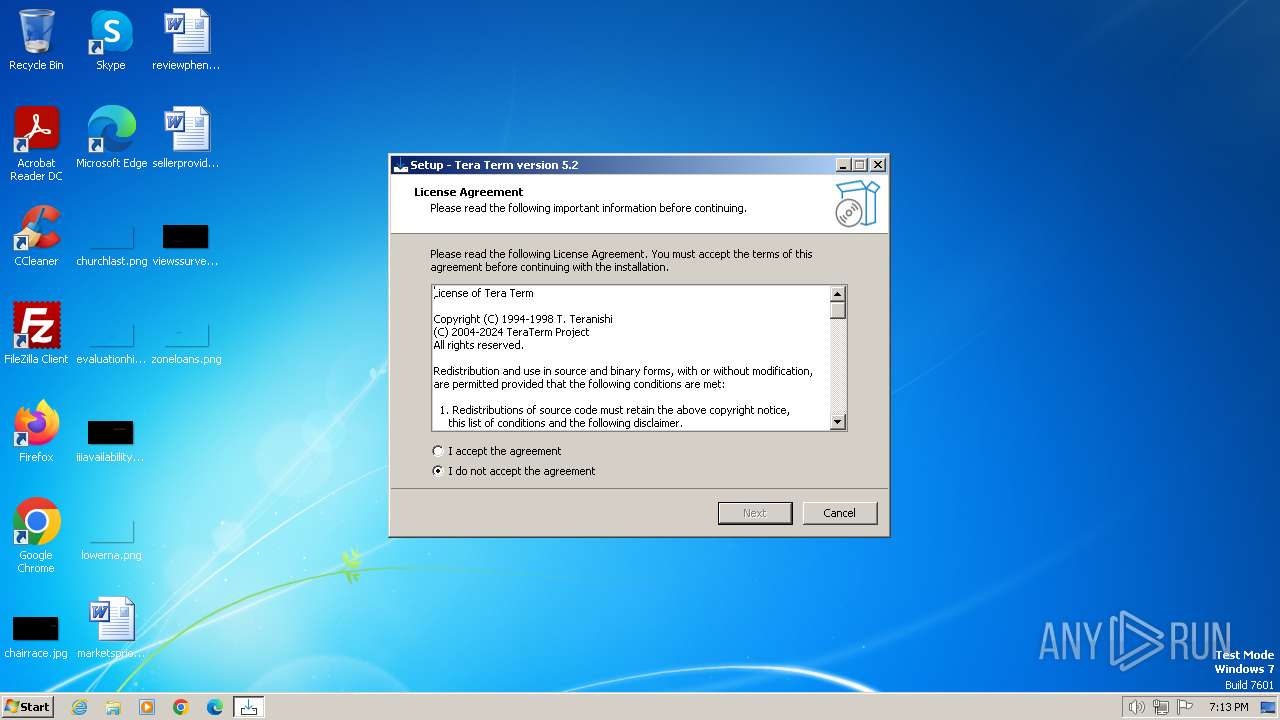
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | TeraTerm Project |
| FileDescription: | Tera Term Setup |
| FileVersion: | |
| LegalCopyright: | © 2004-2024 TeraTerm Project |
| OriginalFileName: | |
| ProductName: | Tera Term |
| ProductVersion: | 5.2 |
Total processes
45
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2340 | "C:\Program Files\teraterm5\ttermpro.exe" | C:\Program Files\teraterm5\ttermpro.exe | teraterm-5.2.tmp | ||||||||||||
User: admin Company: T. Teranishi, TeraTerm Project Integrity Level: MEDIUM Description: Tera Term Exit code: 0 Version: 5, 2, 0, 0 Modules
| |||||||||||||||
| 2692 | "C:\Program Files\teraterm5\ttermpro.exe" | C:\Program Files\teraterm5\ttermpro.exe | — | explorer.exe | |||||||||||
User: admin Company: T. Teranishi, TeraTerm Project Integrity Level: MEDIUM Description: Tera Term Exit code: 0 Version: 5, 2, 0, 0 Modules
| |||||||||||||||
| 2752 | "C:\Users\admin\AppData\Local\Temp\is-IQIAR.tmp\teraterm-5.2.tmp" /SL5="$100130,8459522,832512,C:\Users\admin\AppData\Local\Temp\teraterm-5.2.exe" /SPAWNWND=$16013E /NOTIFYWND=$E0170 | C:\Users\admin\AppData\Local\Temp\is-IQIAR.tmp\teraterm-5.2.tmp | teraterm-5.2.exe | ||||||||||||
User: admin Company: TeraTerm Project Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2964 | "C:\Users\admin\AppData\Local\Temp\teraterm-5.2.exe" /SPAWNWND=$16013E /NOTIFYWND=$E0170 | C:\Users\admin\AppData\Local\Temp\teraterm-5.2.exe | teraterm-5.2.tmp | ||||||||||||
User: admin Company: TeraTerm Project Integrity Level: HIGH Description: Tera Term Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3672 | "C:\Users\admin\AppData\Local\Temp\teraterm-5.2.exe" | C:\Users\admin\AppData\Local\Temp\teraterm-5.2.exe | explorer.exe | ||||||||||||
User: admin Company: TeraTerm Project Integrity Level: MEDIUM Description: Tera Term Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 4052 | "C:\Users\admin\AppData\Local\Temp\is-8OARF.tmp\teraterm-5.2.tmp" /SL5="$E0170,8459522,832512,C:\Users\admin\AppData\Local\Temp\teraterm-5.2.exe" | C:\Users\admin\AppData\Local\Temp\is-8OARF.tmp\teraterm-5.2.tmp | — | teraterm-5.2.exe | |||||||||||
User: admin Company: TeraTerm Project Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
5 523
Read events
5 429
Write events
88
Delete events
6
Modification events
| (PID) Process: | (2752) teraterm-5.2.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: C00A0000464399267A6ADA01 | |||
| (PID) Process: | (2752) teraterm-5.2.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 999B4578BDF2F4F21F96A89E3E990D9EAA9AD6D2F2CD8BF35F400CD27604BDF2 | |||
| (PID) Process: | (2752) teraterm-5.2.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2752) teraterm-5.2.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\teraterm5\ttermpro.exe | |||
| (PID) Process: | (2752) teraterm-5.2.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 605242C62DE16594AE12CEB6758520212AE693EFD6E37A663E3FCA64A5A980E1 | |||
| (PID) Process: | (2752) teraterm-5.2.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Fonts |
| Operation: | write | Name: | Tera Special (TrueType) |
Value: TSPECIAL1.TTF | |||
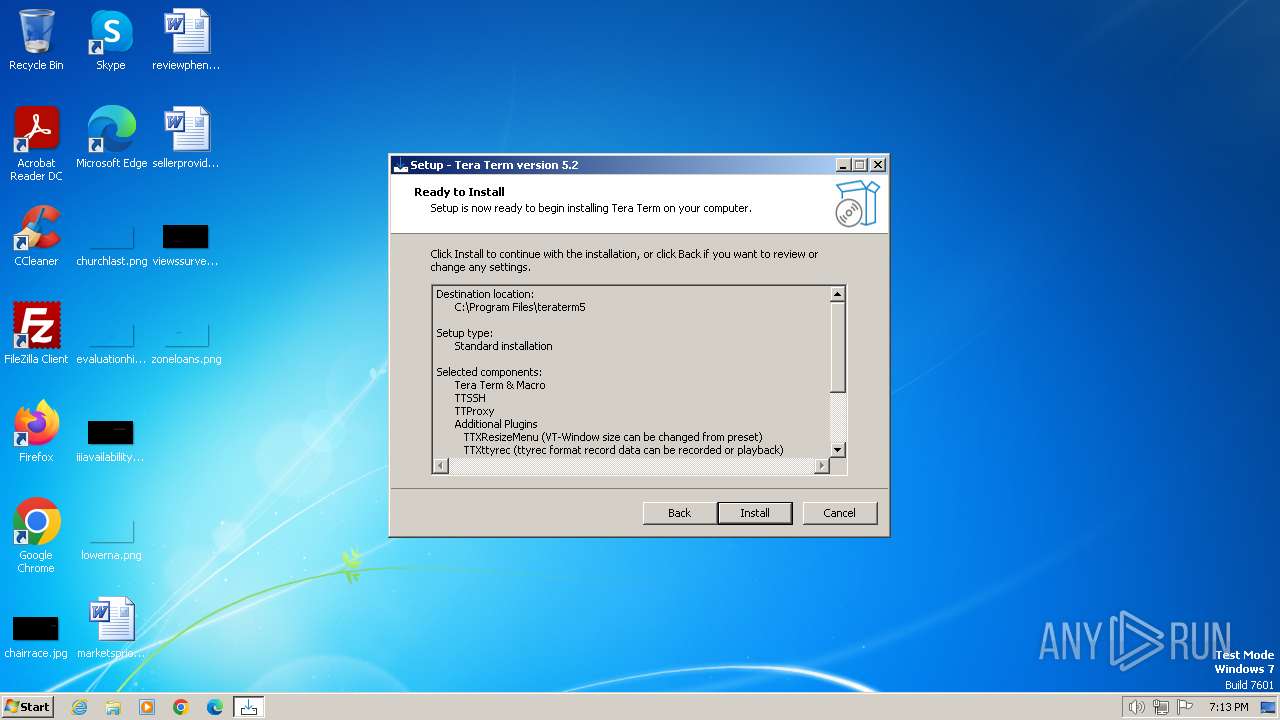
| (PID) Process: | (2752) teraterm-5.2.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{07A7E17A-F6D6-44A7-82E6-6BEE528CCA2A}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.2.2 | |||
| (PID) Process: | (2752) teraterm-5.2.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{07A7E17A-F6D6-44A7-82E6-6BEE528CCA2A}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\teraterm5 | |||
| (PID) Process: | (2752) teraterm-5.2.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{07A7E17A-F6D6-44A7-82E6-6BEE528CCA2A}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\teraterm5\ | |||
| (PID) Process: | (2752) teraterm-5.2.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{07A7E17A-F6D6-44A7-82E6-6BEE528CCA2A}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Tera Term 5 | |||
Executable files
26
Suspicious files
17
Text files
82
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3672 | teraterm-5.2.exe | C:\Users\admin\AppData\Local\Temp\is-8OARF.tmp\teraterm-5.2.tmp | executable | |
MD5:3C0CB4D279FA23CEF85C3C431C5474A2 | SHA256:A08C3CA76ED992861F9DB0E475DD2A295269212C2FC0566001320006F314420A | |||
| 2752 | teraterm-5.2.tmp | C:\Windows\Fonts\is-M6KH5.tmp | binary | |
MD5:2E743CD2B882CA1C1B25922792A2B122 | SHA256:F60767CEAE6383A9CB5A3EB50329440BCA99A27B3BE29D39AB959E8E41B926E8 | |||
| 2752 | teraterm-5.2.tmp | C:\Program Files\teraterm5\is-QSDHT.tmp | executable | |
MD5:E6D35FD61B87D6546E03596650F91510 | SHA256:641440C1B990700788E9199AB1A77A7EBA957E1B77B5637F7D195703913C0596 | |||
| 2964 | teraterm-5.2.exe | C:\Users\admin\AppData\Local\Temp\is-IQIAR.tmp\teraterm-5.2.tmp | executable | |
MD5:3C0CB4D279FA23CEF85C3C431C5474A2 | SHA256:A08C3CA76ED992861F9DB0E475DD2A295269212C2FC0566001320006F314420A | |||
| 2752 | teraterm-5.2.tmp | C:\Program Files\teraterm5\ttermpro.exe | executable | |
MD5:D0E939303F176458F9B2B0BEF8E97AEA | SHA256:6FFD252D378474CBC3CBE1608D35DC0FAF4BFA998FB36E090E921FE1BE3BFF87 | |||
| 2752 | teraterm-5.2.tmp | C:\Program Files\teraterm5\unins000.exe | executable | |
MD5:E6D35FD61B87D6546E03596650F91510 | SHA256:641440C1B990700788E9199AB1A77A7EBA957E1B77B5637F7D195703913C0596 | |||
| 2752 | teraterm-5.2.tmp | C:\Program Files\teraterm5\is-QIF4R.tmp | executable | |
MD5:28C5478F1EB54D73591FEFCC3CC46196 | SHA256:2F4F54CDA8D47693AA902C3CF807F6FCC29AEEA1A058E783E17BC5B0C3195D97 | |||
| 2752 | teraterm-5.2.tmp | C:\Windows\Fonts\TSPECIAL1.TTF | binary | |
MD5:2E743CD2B882CA1C1B25922792A2B122 | SHA256:F60767CEAE6383A9CB5A3EB50329440BCA99A27B3BE29D39AB959E8E41B926E8 | |||
| 2752 | teraterm-5.2.tmp | C:\Program Files\teraterm5\ttpcmn.dll | executable | |
MD5:28C5478F1EB54D73591FEFCC3CC46196 | SHA256:2F4F54CDA8D47693AA902C3CF807F6FCC29AEEA1A058E783E17BC5B0C3195D97 | |||
| 2752 | teraterm-5.2.tmp | C:\Program Files\teraterm5\TERATERM.INI | text | |
MD5:F8B0D8271F344097312529DF8A12C6CD | SHA256:98891B4D710082F48F4A78375AD37AA11485EED54C748F4DC78CA6068DDF9502 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2340 | ttermpro.exe | 49.13.77.253:22 | myhost.example.com | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
myhost.example.com |
| unknown |
dns.msftncsi.com |
| shared |