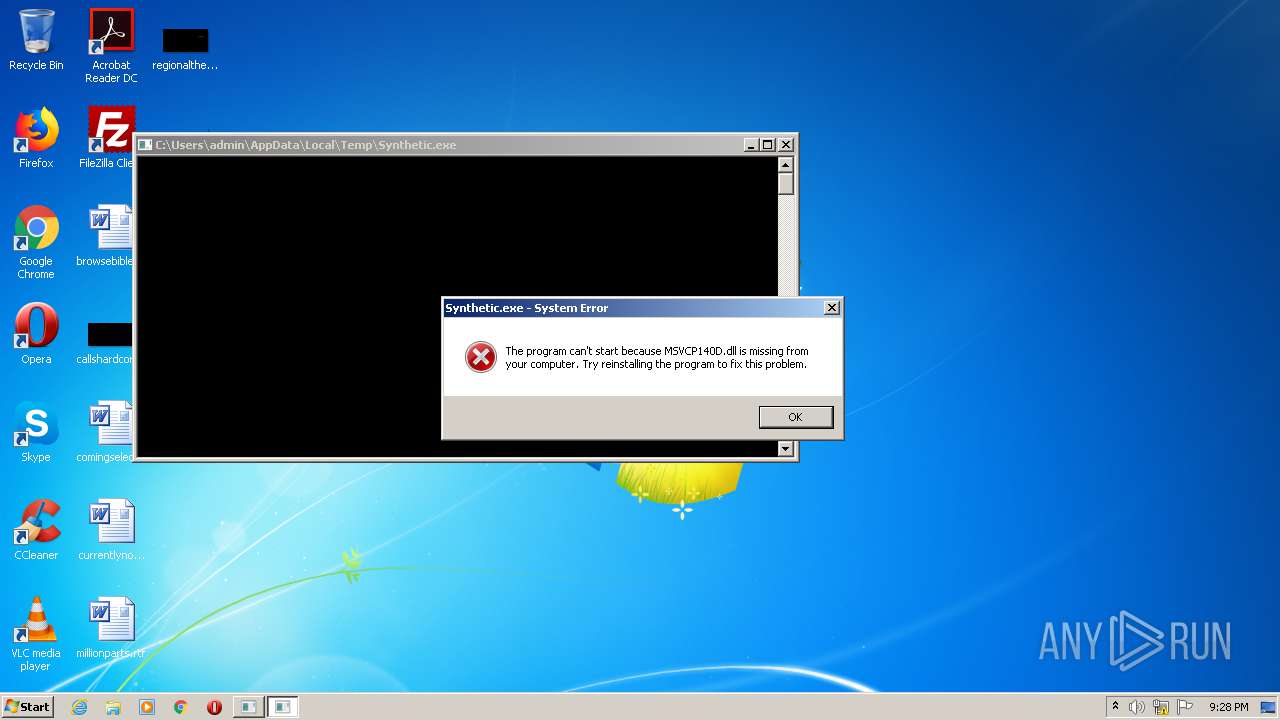
| File name: | Synthetic.exe |
| Full analysis: | https://app.any.run/tasks/6447fbbc-9233-4d73-81c2-fa7af765967e |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 21:28:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 615298007E652607A627E907E5B66245 |
| SHA1: | FD41CC164B0C427E69DED11D4EE2F4C494A9CCD0 |
| SHA256: | 2FEA21A20955FE6B66935AC9581B901BB1D19AC467482A0242CE9C3F8EF22830 |
| SSDEEP: | 384:0DBsgXmq86sV1uDSGul4PfErO/++Y/D0QpwPhdm52GMBbD2l7Bg:qWgXw+SOPfErO/biWhqEBbDag |
MALICIOUS
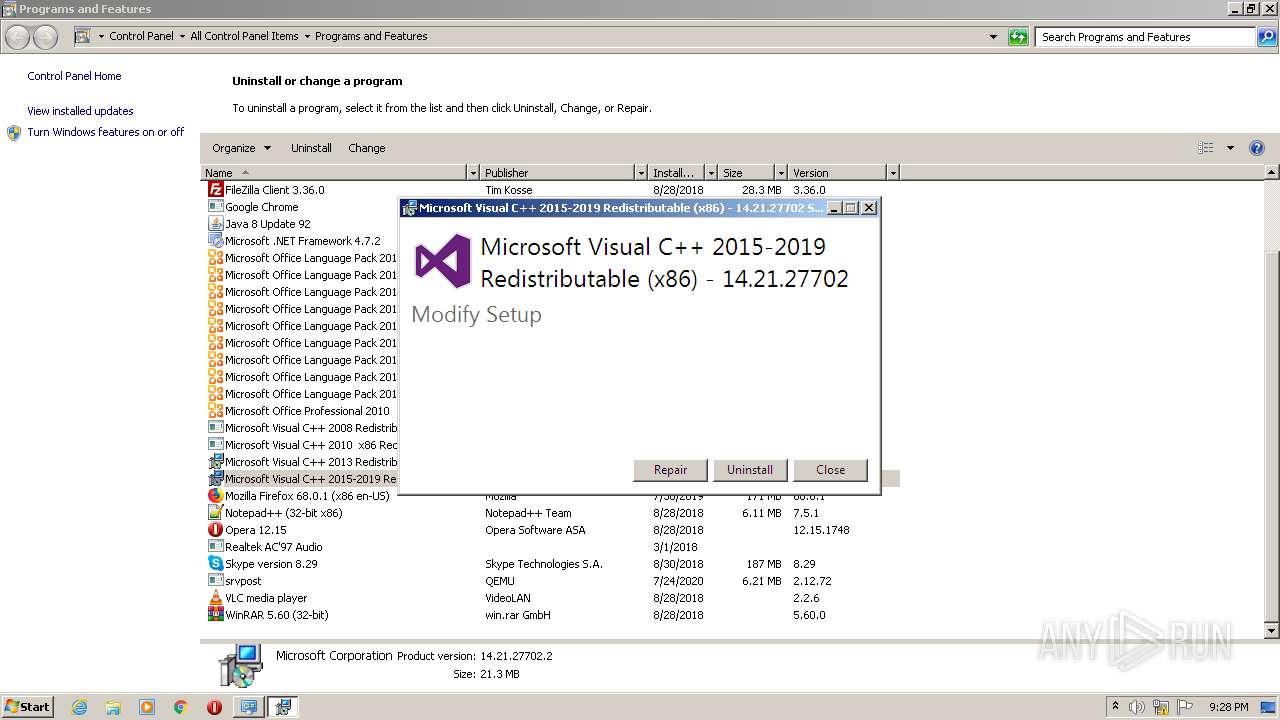
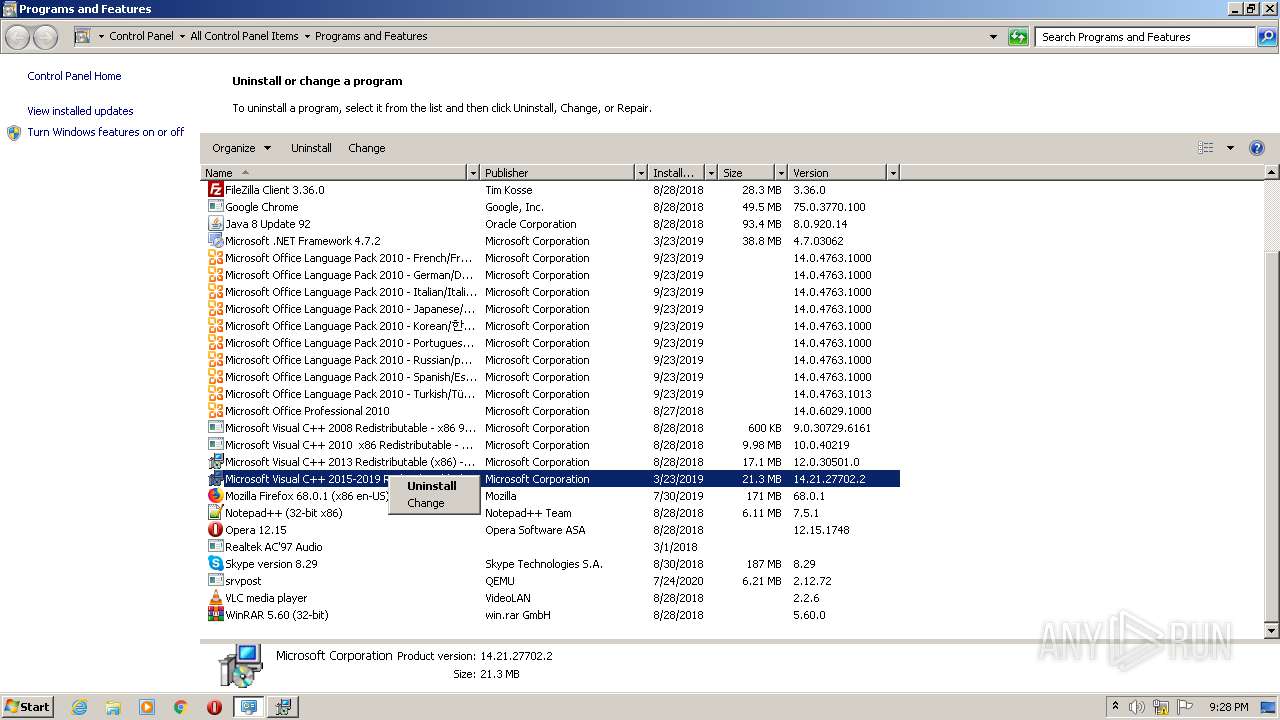
Loads dropped or rewritten executable
- VC_redist.x86.exe (PID: 3964)
Drops executable file immediately after starts
- VC_redist.x86.exe (PID: 3964)
SUSPICIOUS
Application launched itself
- VC_redist.x86.exe (PID: 2992)
Creates files in the Windows directory
- VC_redist.x86.exe (PID: 3964)
Executed via COM
- DllHost.exe (PID: 2516)
Drops a file that was compiled in debug mode
- VC_redist.x86.exe (PID: 3964)
Executable content was dropped or overwritten
- VC_redist.x86.exe (PID: 3964)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:11:29 22:07:34+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.28 |
| CodeSize: | 29696 |
| InitializedDataSize: | 19456 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x11023 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 29-Nov-2020 21:07:34 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 29-Nov-2020 21:07:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.textbss | 0x00001000 | 0x00010000 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.text | 0x00011000 | 0x00007330 | 0x00007400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.11985 |
.rdata | 0x00019000 | 0x00002392 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.87165 |
.data | 0x0001C000 | 0x000005A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.344302 |
.idata | 0x0001D000 | 0x00000F43 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.56771 |
.msvcjmc<\x01 | 0x0001E000 | 0x0000013C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.461522 |
.00cfg | 0x0001F000 | 0x00000109 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.110557 |
.rsrc | 0x00020000 | 0x0000043C | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.14043 |
.reloc | 0x00021000 | 0x0000061C | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.19937 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
KERNEL32.dll |
MSVCP140D.dll |
VCRUNTIME140D.dll |
ucrtbased.dll |
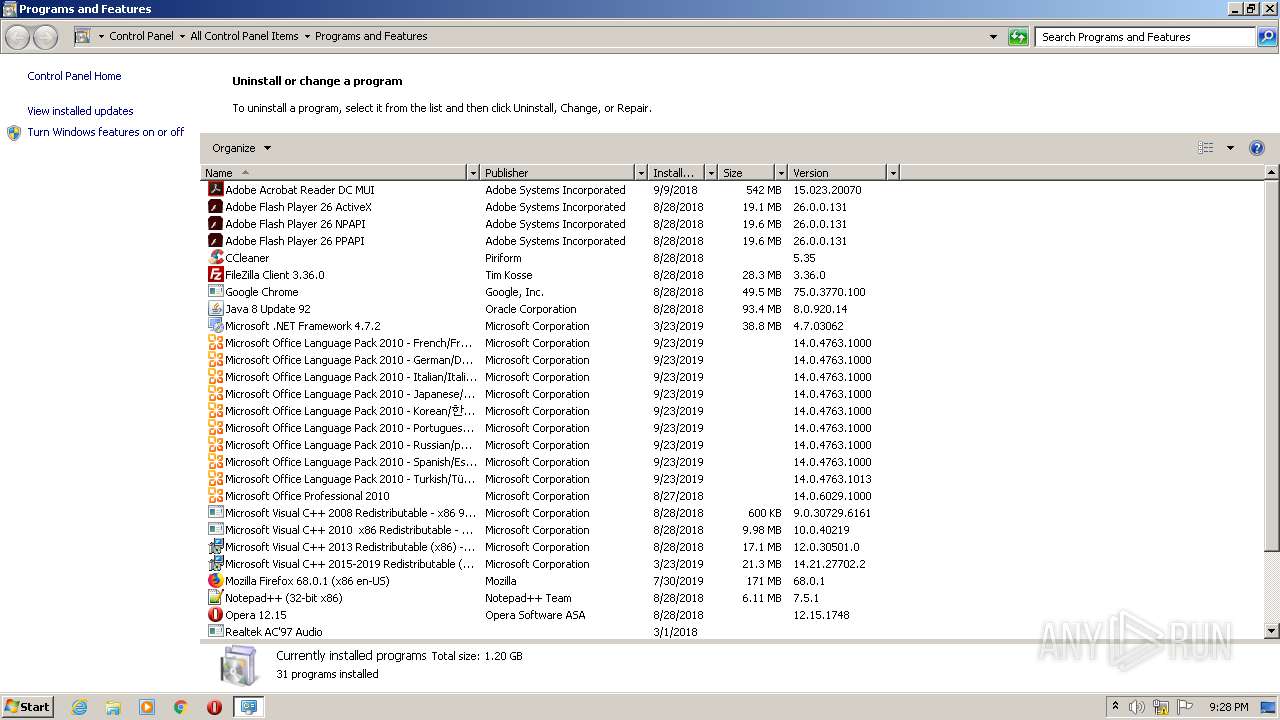
Total processes
41
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2516 | C:\Windows\system32\DllHost.exe /Processid:{FCC74B77-EC3E-4DD8-A80B-008A702075A9} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2684 | "C:\Users\admin\AppData\Local\Temp\Synthetic.exe" | C:\Users\admin\AppData\Local\Temp\Synthetic.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225781 Modules
| |||||||||||||||
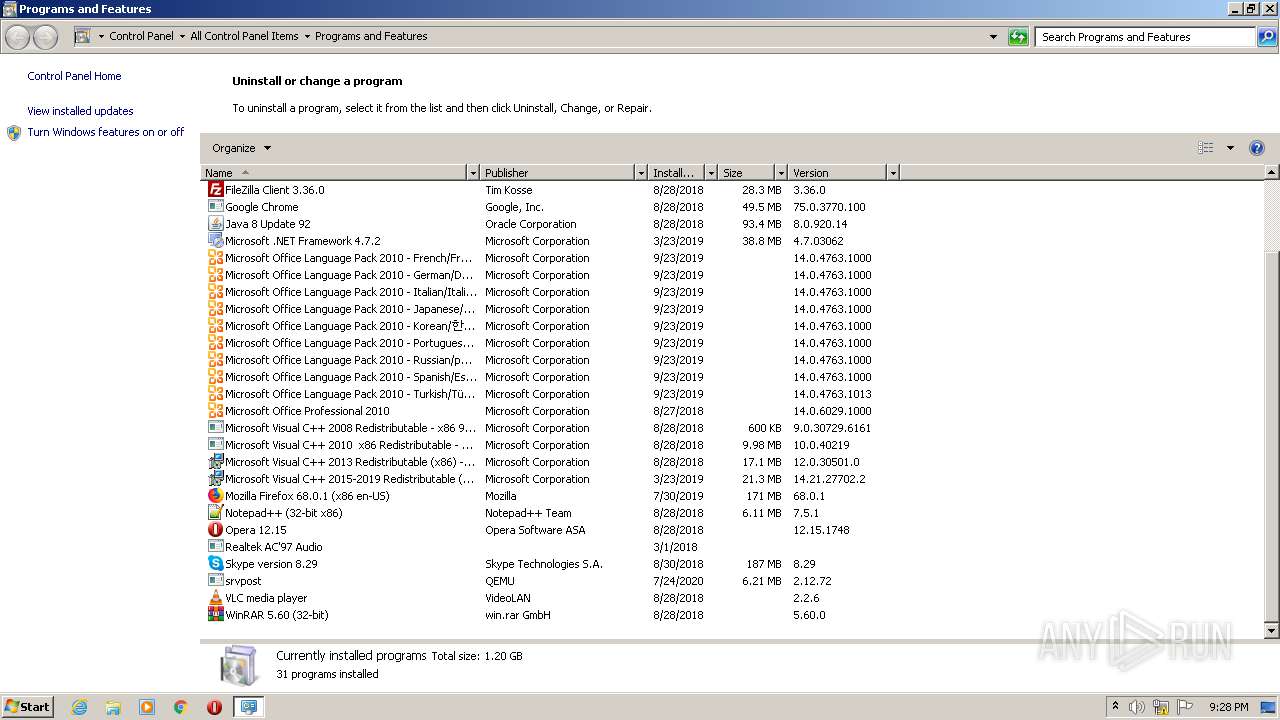
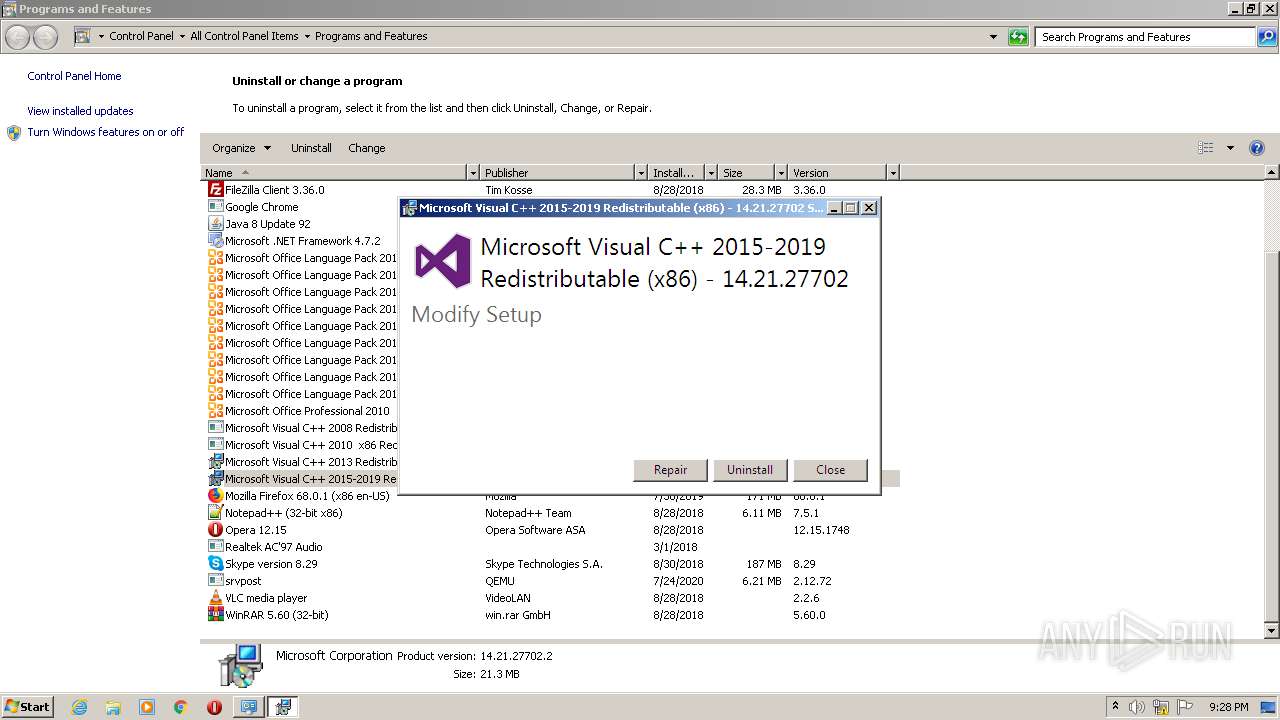
| 2992 | "C:\ProgramData\Package Cache\{49697869-be8e-427d-81a0-c334d1d14950}\VC_redist.x86.exe" /uninstall | C:\ProgramData\Package Cache\{49697869-be8e-427d-81a0-c334d1d14950}\VC_redist.x86.exe | — | DllHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2019 Redistributable (x86) - 14.21.27702 Exit code: 0 Version: 14.21.27702.2 Modules
| |||||||||||||||
| 3964 | "C:\ProgramData\Package Cache\{49697869-be8e-427d-81a0-c334d1d14950}\VC_redist.x86.exe" -burn.clean.room="C:\ProgramData\Package Cache\{49697869-be8e-427d-81a0-c334d1d14950}\VC_redist.x86.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 /uninstall | C:\ProgramData\Package Cache\{49697869-be8e-427d-81a0-c334d1d14950}\VC_redist.x86.exe | VC_redist.x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2019 Redistributable (x86) - 14.21.27702 Exit code: 0 Version: 14.21.27702.2 Modules
| |||||||||||||||
Total events
43
Read events
43
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
0
Text files
31
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | VC_redist.x86.exe | C:\Windows\Temp\{D2907B5F-5AFB-41EF-9885-6937C7D0D8D6}\.ba\wixstdba.dll | executable | |
MD5:EAB9CAF4277829ABDF6223EC1EFA0EDD | SHA256:A4EFBDB2CE55788FFE92A244CB775EFD475526EF5B61AD78DE2BCDFADDAC7041 | |||
| 3964 | VC_redist.x86.exe | C:\Windows\Temp\{D2907B5F-5AFB-41EF-9885-6937C7D0D8D6}\.ba\license.rtf | text | |
MD5:2EABBB391ACB89942396DF5C1CA2BAD8 | SHA256:E3156D170014CED8D17A02B3C4FF63237615E5C2A8983B100A78CB1F881D6F38 | |||
| 3964 | VC_redist.x86.exe | C:\Windows\Temp\{D2907B5F-5AFB-41EF-9885-6937C7D0D8D6}\.ba\1036\thm.wxl | xml | |
MD5:7B46AE8698459830A0F9116BC27DE7DF | SHA256:704DDF2E60C1F292BE95C7C79EE48FE8BA8534CEB7CCF9A9EA68B1AD788AE9D4 | |||
| 3964 | VC_redist.x86.exe | C:\Windows\Temp\{D2907B5F-5AFB-41EF-9885-6937C7D0D8D6}\.ba\thm.xml | xml | |
MD5:F62729C6D2540015E072514226C121C7 | SHA256:F13BAE0EC08C91B4A315BB2D86EE48FADE597E7A5440DCE6F751F98A3A4D6916 | |||
| 3964 | VC_redist.x86.exe | C:\Windows\Temp\{D2907B5F-5AFB-41EF-9885-6937C7D0D8D6}\.ba\1029\thm.wxl | xml | |
MD5:16343005D29EC431891B02F048C7F581 | SHA256:07FB3EC174F25DFBE532D9D739234D9DFDA8E9D34F01FE660C5B4D56989FA779 | |||
| 3964 | VC_redist.x86.exe | C:\Windows\Temp\{D2907B5F-5AFB-41EF-9885-6937C7D0D8D6}\.ba\1029\license.rtf | text | |
MD5:B408556A89FCE3B47CD61302ECA64AC9 | SHA256:21DDCBB0B0860E15FF9294CBB3C4E25B1FE48619210B8A1FDEC90BDCDC8C04BC | |||
| 3964 | VC_redist.x86.exe | C:\Windows\Temp\{D2907B5F-5AFB-41EF-9885-6937C7D0D8D6}\.ba\1031\thm.wxl | xml | |
MD5:561F3F32DB2453647D1992D4D932E872 | SHA256:8E0DCA6E085744BFCBFF46F7DCBCFA6FBD722DFA52013EE8CEEAF682D7509581 | |||
| 3964 | VC_redist.x86.exe | C:\Windows\Temp\{D2907B5F-5AFB-41EF-9885-6937C7D0D8D6}\.ba\1040\thm.wxl | xml | |
MD5:D90BC60FA15299925986A52861B8E5D5 | SHA256:0C57F40CC2091554307AA8A7C35DD38E4596E9513E9EFAE00AC30498EF4E9BC2 | |||
| 3964 | VC_redist.x86.exe | C:\Windows\Temp\{D2907B5F-5AFB-41EF-9885-6937C7D0D8D6}\.ba\1040\license.rtf | text | |
MD5:9D98044BAC59684489C4CF66C3B34C85 | SHA256:A3F745C01DEA84CE746BA630814E68C7C592B965B048DDC4B1BBE1D6E533BE22 | |||
| 3964 | VC_redist.x86.exe | C:\Windows\Temp\{D2907B5F-5AFB-41EF-9885-6937C7D0D8D6}\.ba\1041\license.rtf | text | |
MD5:8C49936EC4CF0F64CA2398191C462698 | SHA256:7355367B7C48F1BBACC66DFFE1D4BF016C16156D020D4156F288C2B2207ED1C2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report