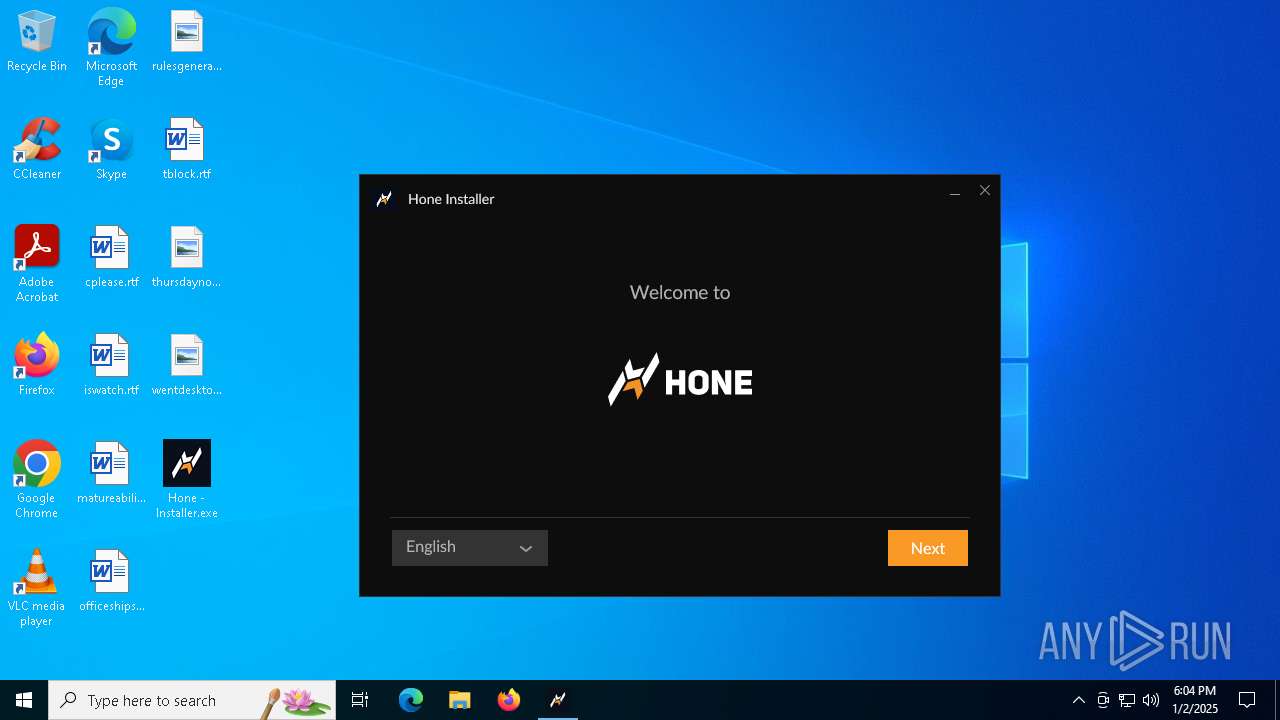
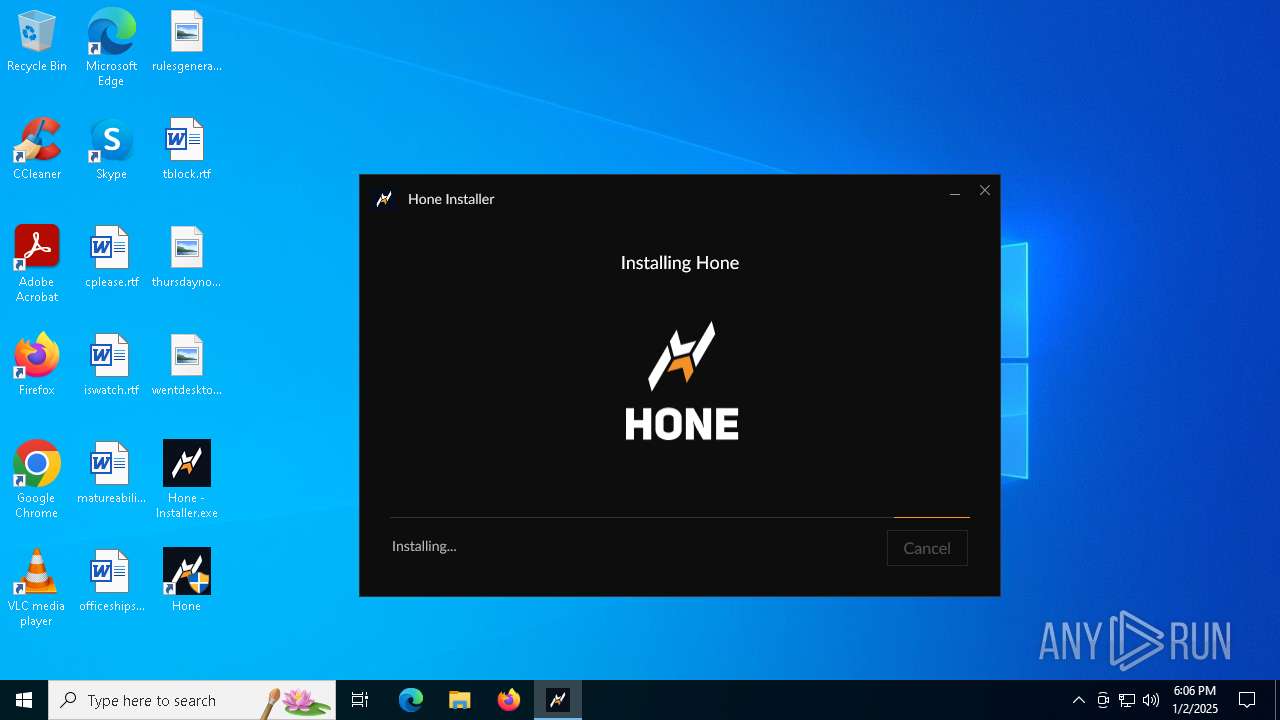
| File name: | Hone - Installer.exe |
| Full analysis: | https://app.any.run/tasks/7b9a41e8-c207-4b4f-acbe-945724e9b5e8 |
| Verdict: | Malicious activity |
| Analysis date: | January 02, 2025, 18:04:20 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 5BB17FB2C53D4DC7427D0E526CF1AD8A |
| SHA1: | C96C9DF5F626FDE444B29AF1929A94DE881E66F6 |
| SHA256: | 2FE2FE9E4B01502C23F64C2707D69F0C42B1501115519EC612C833905EC9E397 |
| SSDEEP: | 98304:d/d5kO4fJ/A9nGcRa1xXcVsy3RxeLLCIJgap176MVhAuMdehHtW3FRgpXNhW2Gep:BZc |
MALICIOUS
Executing a file with an untrusted certificate
- ow-electron-setup.exe (PID: 3812)
- Hone.exe (PID: 4444)
- Hone.exe (PID: 5988)
- Hone.exe (PID: 6604)
- Hone.exe (PID: 1416)
- Hone.exe (PID: 4144)
- Hone.exe (PID: 244)
- Hone.exe (PID: 2380)
- gamefinder472.exe (PID: 6204)
- HoneStartup.exe (PID: 6576)
- gamefinder472.exe (PID: 936)
Changes powershell execution policy (Unrestricted)
- Hone.exe (PID: 4444)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- Hone - Installer.exe (PID: 5920)
- Hone - Installer.exe (PID: 6700)
- Hone - Installer.exe (PID: 6796)
- ow-electron-setup.exe (PID: 3812)
- Hone - Installer.exe (PID: 6176)
Drops 7-zip archiver for unpacking
- Hone - Installer.exe (PID: 5920)
- Hone - Installer.exe (PID: 6700)
- Hone - Installer.exe (PID: 6796)
- Hone - Installer.exe (PID: 6176)
Reads security settings of Internet Explorer
- Hone - Installer.exe (PID: 5920)
- Hone - Installer.exe (PID: 6176)
- OWInstaller.exe (PID: 6560)
- Hone - Installer.exe (PID: 6700)
- Hone - Installer.exe (PID: 6796)
- OWInstaller.exe (PID: 6876)
Executable content was dropped or overwritten
- Hone - Installer.exe (PID: 5920)
- Hone - Installer.exe (PID: 6700)
- Hone - Installer.exe (PID: 6796)
- ow-electron-setup.exe (PID: 3812)
- Hone - Installer.exe (PID: 6176)
Application launched itself
- Hone - Installer.exe (PID: 5920)
- Hone - Installer.exe (PID: 6700)
- Hone.exe (PID: 4444)
The process creates files with name similar to system file names
- Hone - Installer.exe (PID: 5920)
- Hone - Installer.exe (PID: 6176)
- Hone - Installer.exe (PID: 6700)
- Hone - Installer.exe (PID: 6796)
- ow-electron-setup.exe (PID: 3812)
Reads Internet Explorer settings
- OWInstaller.exe (PID: 6560)
- OWInstaller.exe (PID: 6876)
Reads Microsoft Outlook installation path
- OWInstaller.exe (PID: 6560)
- OWInstaller.exe (PID: 6876)
Checks Windows Trust Settings
- OWInstaller.exe (PID: 6560)
- OWInstaller.exe (PID: 6876)
Reads the date of Windows installation
- OWInstaller.exe (PID: 6560)
Process drops legitimate windows executable
- ow-electron-setup.exe (PID: 3812)
The process drops C-runtime libraries
- ow-electron-setup.exe (PID: 3812)
Drops a system driver (possible attempt to evade defenses)
- ow-electron-setup.exe (PID: 3812)
Creates a software uninstall entry
- ow-electron-setup.exe (PID: 3812)
Starts CMD.EXE for commands execution
- Hone.exe (PID: 4444)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4052)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 6520)
The process bypasses the loading of PowerShell profile settings
- Hone.exe (PID: 4444)
Starts POWERSHELL.EXE for commands execution
- Hone.exe (PID: 4444)
- cmd.exe (PID: 2280)
The process hides Powershell's copyright startup banner
- Hone.exe (PID: 4444)
The process executes Powershell scripts
- cmd.exe (PID: 2280)
INFO
Create files in a temporary directory
- Hone - Installer.exe (PID: 5920)
- Hone - Installer.exe (PID: 6176)
- OWInstaller.exe (PID: 6560)
- Hone - Installer.exe (PID: 6700)
- Hone - Installer.exe (PID: 6796)
- OWInstaller.exe (PID: 6876)
- ow-electron-setup.exe (PID: 3812)
- Hone.exe (PID: 4444)
Checks supported languages
- Hone - Installer.exe (PID: 5920)
- Hone - Installer.exe (PID: 6176)
- OWInstaller.exe (PID: 6560)
- Hone - Installer.exe (PID: 6700)
- Hone - Installer.exe (PID: 6796)
- OWInstaller.exe (PID: 6876)
- ow-electron-setup.exe (PID: 3812)
- Hone.exe (PID: 5988)
- Hone.exe (PID: 6604)
- Hone.exe (PID: 1416)
- Hone.exe (PID: 4444)
- Hone.exe (PID: 4144)
- Hone.exe (PID: 244)
- Hone.exe (PID: 2380)
- HoneStartup.exe (PID: 1460)
The sample compiled with english language support
- Hone - Installer.exe (PID: 5920)
- Hone - Installer.exe (PID: 6176)
- Hone - Installer.exe (PID: 6700)
- Hone - Installer.exe (PID: 6796)
- ow-electron-setup.exe (PID: 3812)
Checks proxy server information
- Hone - Installer.exe (PID: 6176)
- OWInstaller.exe (PID: 6560)
- Hone - Installer.exe (PID: 6796)
- OWInstaller.exe (PID: 6876)
- Hone.exe (PID: 4444)
Reads the computer name
- Hone - Installer.exe (PID: 5920)
- OWInstaller.exe (PID: 6560)
- Hone - Installer.exe (PID: 6700)
- Hone - Installer.exe (PID: 6796)
- ow-electron-setup.exe (PID: 3812)
- Hone.exe (PID: 4444)
- Hone - Installer.exe (PID: 6176)
- Hone.exe (PID: 1416)
- Hone.exe (PID: 6604)
- OWInstaller.exe (PID: 6876)
Process checks computer location settings
- Hone - Installer.exe (PID: 5920)
- Hone - Installer.exe (PID: 6700)
- OWInstaller.exe (PID: 6560)
- Hone.exe (PID: 4444)
- Hone.exe (PID: 5988)
- Hone.exe (PID: 4144)
- Hone.exe (PID: 244)
- Hone.exe (PID: 2380)
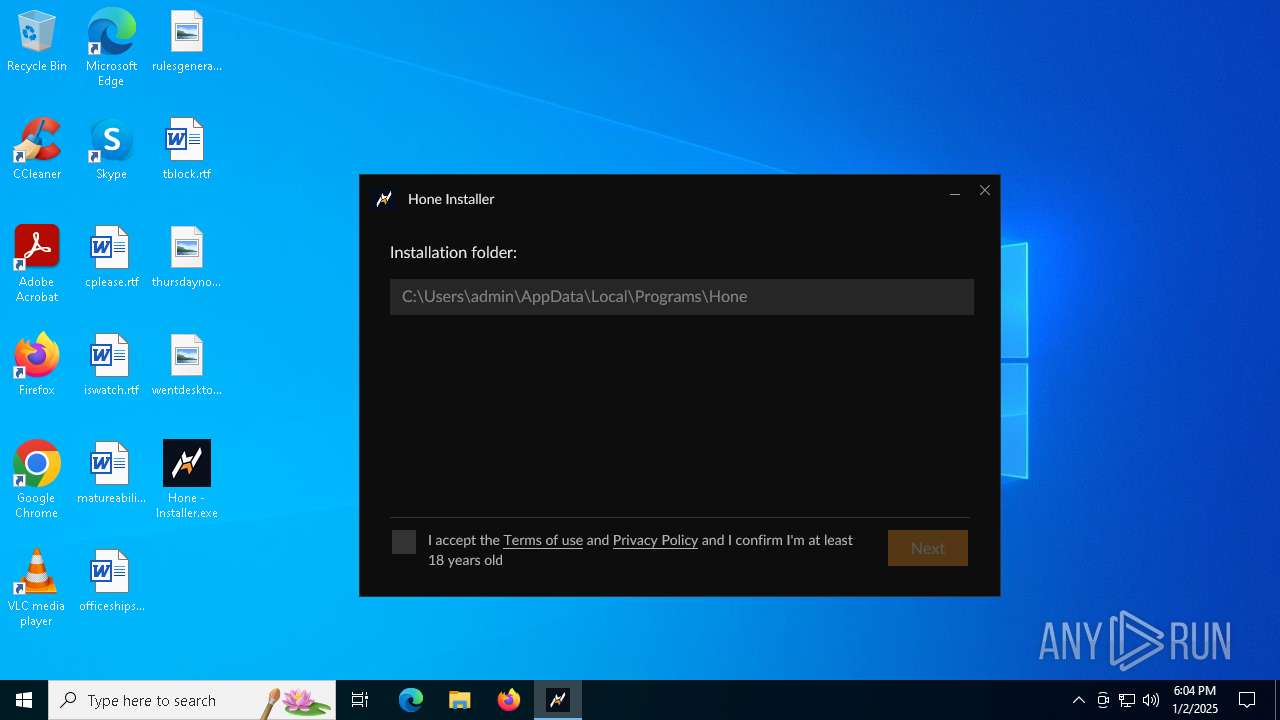
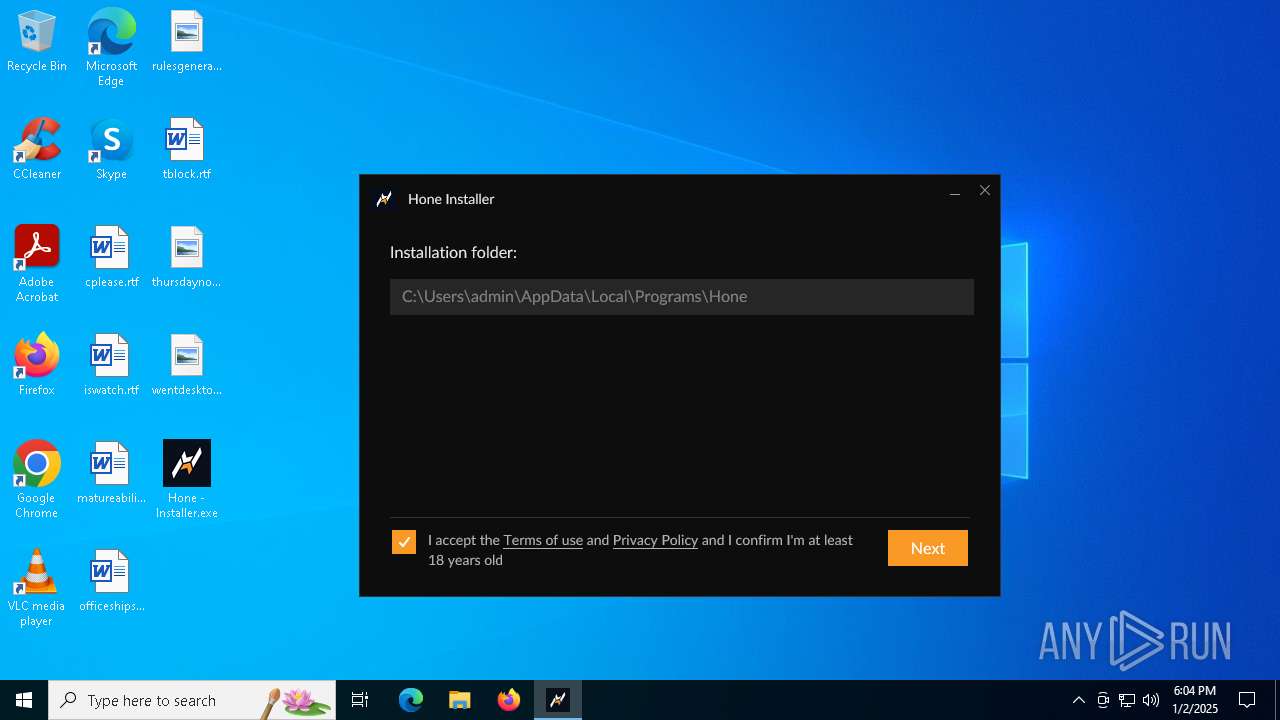
Creates files or folders in the user directory
- Hone - Installer.exe (PID: 6176)
- OWInstaller.exe (PID: 6560)
- Hone - Installer.exe (PID: 6796)
- OWInstaller.exe (PID: 6876)
- ow-electron-setup.exe (PID: 3812)
- Hone.exe (PID: 4444)
- Hone.exe (PID: 1416)
Reads Environment values
- OWInstaller.exe (PID: 6560)
- OWInstaller.exe (PID: 6876)
- Hone.exe (PID: 4444)
The process uses the downloaded file
- OWInstaller.exe (PID: 6560)
- OWInstaller.exe (PID: 6876)
Disables trace logs
- OWInstaller.exe (PID: 6560)
- OWInstaller.exe (PID: 6876)
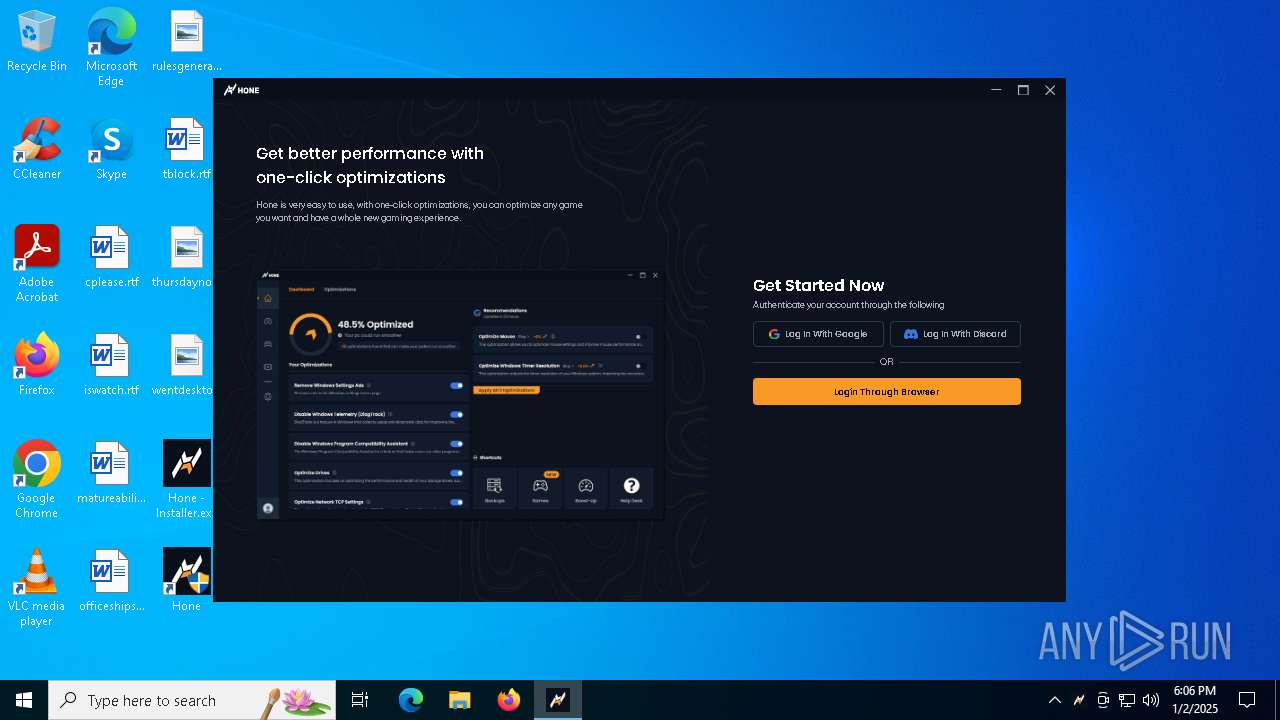
Manual execution by a user
- Hone - Installer.exe (PID: 6700)
Reads the software policy settings
- OWInstaller.exe (PID: 6560)
- OWInstaller.exe (PID: 6876)
- Hone.exe (PID: 6604)
Reads the machine GUID from the registry
- OWInstaller.exe (PID: 6876)
- OWInstaller.exe (PID: 6560)
- Hone.exe (PID: 4444)
Creates files in the program directory
- ow-electron-setup.exe (PID: 3812)
- Hone.exe (PID: 4444)
Reads product name
- Hone.exe (PID: 4444)
Reads CPU info
- Hone.exe (PID: 4444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 21:57:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 27136 |
| InitializedDataSize: | 186880 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x352d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.265.0.3 |
| ProductVersionNumber: | 2.265.0.3 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Overwolf Ltd. |
| FileDescription: | Hone |
| FileVersion: | 2.265.0.3 |
| LegalCopyright: | Copyright (C) 2021 Overwolf Ltd. All Rights Reserved. |
| LegalTrademarks: | - |
| ProductName: | Hone |
| ProductVersion: | 2.265.0.3 |
Total processes
166
Monitored processes
44
Malicious processes
8
Suspicious processes
9
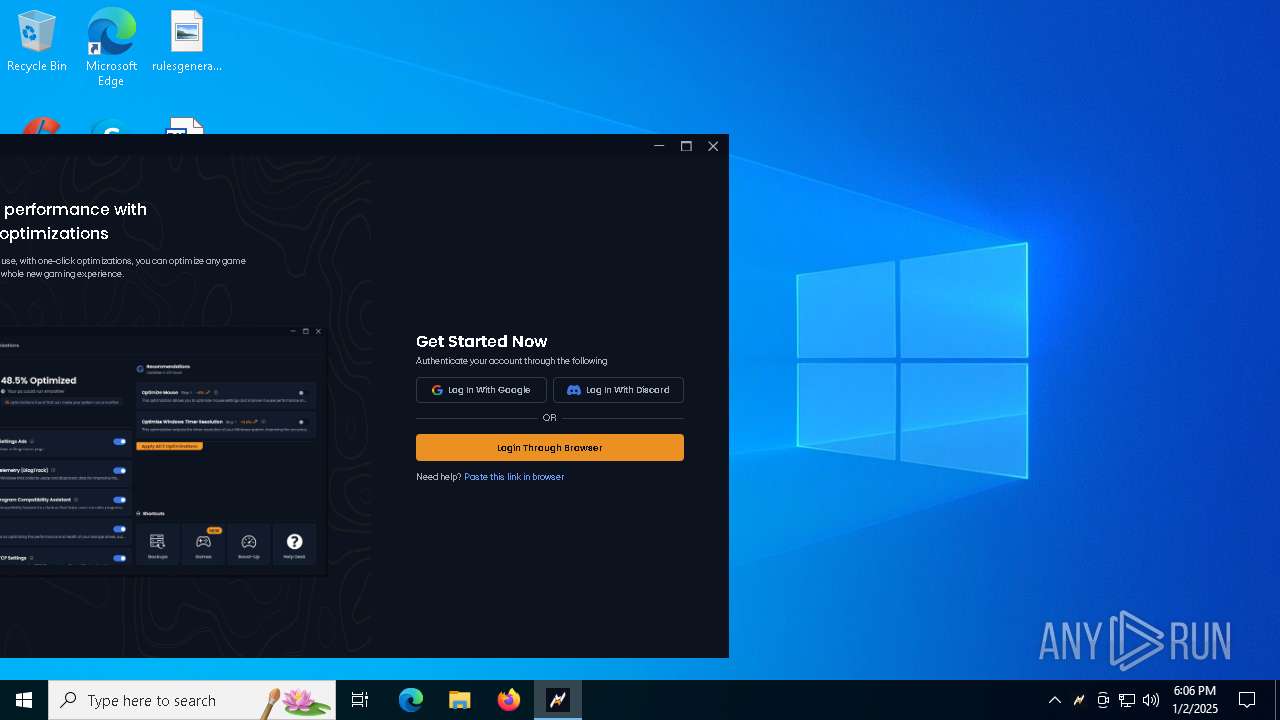
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 244 | "C:\Users\admin\AppData\Local\Programs\Hone\Hone.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\Hone" --standard-schemes=owepm --secure-schemes=owepm --bypasscsp-schemes=owepm --fetch-schemes=owepm --streaming-schemes=owepm --app-user-model-id=Hone --app-path="C:\Users\admin\AppData\Local\Programs\Hone\resources\app.asar" --enable-sandbox --no-sandbox --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --field-trial-handle=3812,i,9893929753588565144,1367316892662291030,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=3808 /prefetch:1 | C:\Users\admin\AppData\Local\Programs\Hone\Hone.exe | — | Hone.exe | |||||||||||
User: admin Company: AuraSide Inc Integrity Level: HIGH Description: Hone Version: 1.1.41 Modules
| |||||||||||||||
| 936 | C:\Users\admin\AppData\Local\Programs\Hone\resources\assets\hone-resources\gamefinder472.exe --installed-only | C:\Users\admin\AppData\Local\Programs\Hone\resources\assets\hone-resources\gamefinder472.exe | — | Hone.exe | |||||||||||
User: admin Company: AuraSide, Inc Integrity Level: HIGH Description: gamedetector Version: 1.0.2.4 | |||||||||||||||
| 1416 | "C:\Users\admin\AppData\Local\Programs\Hone\Hone.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-sandbox --user-data-dir="C:\Users\admin\AppData\Roaming\Hone" --standard-schemes=owepm --secure-schemes=owepm --bypasscsp-schemes=owepm --fetch-schemes=owepm --streaming-schemes=owepm --field-trial-handle=2036,i,9893929753588565144,1367316892662291030,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=2028 /prefetch:3 | C:\Users\admin\AppData\Local\Programs\Hone\Hone.exe | Hone.exe | ||||||||||||
User: admin Company: AuraSide Inc Integrity Level: HIGH Description: Hone Version: 1.1.41 Modules
| |||||||||||||||
| 1460 | C:\Users\admin\AppData\Local\Programs\Hone\resources\assets\hone-resources\HoneStartup.exe | C:\Users\admin\AppData\Local\Programs\Hone\resources\assets\hone-resources\HoneStartup.exe | — | Hone.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1480 | "C:\WINDOWS\System32\WindowsPowershell\v1.0\powershell.exe" -Command "Unblock-File -Path 'c:\ProgramData\Microsoft\bbba12b9-7672-4b4a-bd7c-20c6dac5c9fa.ps1'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2008 | reg add "hklm\Software\Classes\hone" /ve /t REG_SZ /d "URL:hone" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2280 | C:\WINDOWS\system32\cmd.exe /d /s /c ""C:\WINDOWS\System32\WindowsPowershell\v1.0\powershell.exe" -Command "Unblock-File -Path 'c:\ProgramData\Microsoft\bbba12b9-7672-4b4a-bd7c-20c6dac5c9fa.ps1'"" | C:\Windows\System32\cmd.exe | — | Hone.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2380 | "C:\Users\admin\AppData\Local\Programs\Hone\Hone.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\Hone" --standard-schemes=owepm --secure-schemes=owepm --bypasscsp-schemes=owepm --fetch-schemes=owepm --streaming-schemes=owepm --app-user-model-id=Hone --app-path="C:\Users\admin\AppData\Local\Programs\Hone\resources\app.asar" --no-sandbox --no-zygote --node-integration-in-worker --no-sandbox --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=3856,i,9893929753588565144,1367316892662291030,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=3852 --uid=mgkabooemhaamambocobpeoeelpadcjhjgbcfhlc --package-folder="C:\Users\admin\AppData\Roaming\ow-electron" --app-root="C:\Users\admin\AppData\Local\Programs\Hone\resources\app.asar" --muid=bb926e54-e3ca-40fd-ae90-2764341e7792 --phase=43 --owepm-config="{\"phasing\":100}" --js-flags=--expose-gc /prefetch:1 | C:\Users\admin\AppData\Local\Programs\Hone\Hone.exe | — | Hone.exe | |||||||||||
User: admin Company: AuraSide Inc Integrity Level: HIGH Description: Hone Version: 1.1.41 Modules
| |||||||||||||||
| 3288 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | gamefinder472.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 3812 | "C:\Users\admin\AppData\Local\Temp\ow-electron-setup-mgkabooemhaamambocobpeoeelpadcjhjgbcfhlc\ow-electron-setup.exe" /S --force-run /d="C:\Users\admin\AppData\Local\Programs\Hone" | C:\Users\admin\AppData\Local\Temp\ow-electron-setup-mgkabooemhaamambocobpeoeelpadcjhjgbcfhlc\ow-electron-setup.exe | OWInstaller.exe | ||||||||||||
User: admin Company: AuraSide Inc Integrity Level: HIGH Description: Hone installer for Windows Exit code: 0 Version: 1.1.41.0 Modules
| |||||||||||||||
Total events
19 592
Read events
19 510
Write events
62
Delete events
20
Modification events
| (PID) Process: | (6176) Hone - Installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6560) OWInstaller.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\OverwolfPersist |
| Operation: | write | Name: | MUIDV2 |
Value: c55b4507-9f0a-40c5-b1e2-734956efb083 | |||
| (PID) Process: | (6560) OWInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\OverwolfPersist |
| Operation: | write | Name: | MUIDV2 |
Value: c55b4507-9f0a-40c5-b1e2-734956efb083 | |||
| (PID) Process: | (6560) OWInstaller.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6560) OWInstaller.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6560) OWInstaller.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6176) Hone - Installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6176) Hone - Installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6560) OWInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Overwolf |
| Operation: | write | Name: | MUID |
Value: bb926e54-e3ca-40fd-ae90-2764341e7792 | |||
| (PID) Process: | (6560) OWInstaller.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\OverwolfElectron |
| Operation: | write | Name: | MUID |
Value: bb926e54-e3ca-40fd-ae90-2764341e7792 | |||
Executable files
99
Suspicious files
210
Text files
248
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5920 | Hone - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsh5D66.tmp\OWInstaller.exe | executable | |
MD5:1B49AA2792BAE165B1A8EDB20CB5D675 | SHA256:522A50B813B24EACA425DBF17CF4ABFAD8ACF75AC3071D4D0569EFDC8F5F4F92 | |||
| 5920 | Hone - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsh5D66.tmp\SharpRaven.dll | executable | |
MD5:F2F1CD4E9B1F772B7B7955C3310A126A | SHA256:A8CD61FC4478DA0464967F5C74B6ECC6A880E879F49BA552F7C3056D3D0D562A | |||
| 5920 | Hone - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsh5D66.tmp\CommandLine.dll | executable | |
MD5:6D11C677CAE02CAA249A4F7F35FFF112 | SHA256:DDE08C1DB1FF43B08C7DE59AE14045CB6FEC13BEC7AC65E142142453B8AB1AD4 | |||
| 5920 | Hone - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsh5D66.tmp\nsProcess.dll | executable | |
MD5:10E47E822B85D2A12FA4727001612182 | SHA256:D530589A90918334B8E08D7355630892DD62F41333D948A860735D5BECFCB391 | |||
| 5920 | Hone - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsh5D66.tmp\System.dll | executable | |
MD5:51BD16A2EA23AE1E7A92CEDC6785C82E | SHA256:4DBC79D2B1C7987CC64BB5D014DB81BB5108BDD6D8BF3A5F820FAC1DED62BE33 | |||
| 5920 | Hone - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsh5D66.tmp\uac.dll | executable | |
MD5:861F7E800BB28F68927E65719869409C | SHA256:10A0E8CF46038AB3B2C3CF5DCE407B9A043A631CBDE9A5C8BCF0A54B2566C010 | |||
| 5920 | Hone - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsh5D66.tmp\UserInfo.dll | executable | |
MD5:1DD4CA0F4A94155F8D46EC95A20ADA4A | SHA256:A27DC3069793535CB64123C27DCA8748983D133C8FA5AADDEE8CDBC83F16986D | |||
| 5920 | Hone - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsh5D66.tmp\log4net.dll | executable | |
MD5:F15C8A9E2876568B3910189B2D493706 | SHA256:AE9C8073C3357C490F5D1C64101362918357C568F6B9380A60B09A4A4C1FF309 | |||
| 5920 | Hone - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsh5D66.tmp\Newtonsoft.Json.dll | executable | |
MD5:98CBB64F074DC600B23A2EE1A0F46448 | SHA256:7B44639CBFBC8DDAC8C7A3DE8FFA97A7460BEBB0D54E9FF2E1CCDC3A742C2B13 | |||
| 5920 | Hone - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsh5D66.tmp\DotNetZip.dll | executable | |
MD5:190E712F2E3B065BA3D5F63CB9B7725E | SHA256:6C512D9943A225D686B26FC832589E4C8BEF7C4DD0A8BDFD557D5D27FE5BBA0F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
58
TCP/UDP connections
167
DNS requests
219
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
2736 | svchost.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
— | — | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
2736 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
6560 | OWInstaller.exe | GET | 200 | 18.65.32.231:80 | http://ocsp.rootca3.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRkNawYMzz%2BjKSfYbTyFR0AXuhs6QQUq7bb1waeN6wwhgeRcMecxBmxeMACEwdzEm3iwvr9LEetiLFWbgGCBG0%3D | US | binary | 853 b | unknown |
6560 | OWInstaller.exe | GET | 200 | 173.194.69.94:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | binary | 1.41 Kb | whitelisted |
6560 | OWInstaller.exe | GET | 200 | 173.194.69.94:80 | http://c.pki.goog/r/r1.crl | US | binary | 854 b | whitelisted |
6876 | OWInstaller.exe | GET | 200 | 173.194.69.94:80 | http://c.pki.goog/r/r1.crl | US | binary | 854 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.55.110.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2736 | svchost.exe | 23.55.110.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.55.110.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2736 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6176 | Hone - Installer.exe | 13.227.219.31:80 | analyticsnew.overwolf.com | AMAZON-02 | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
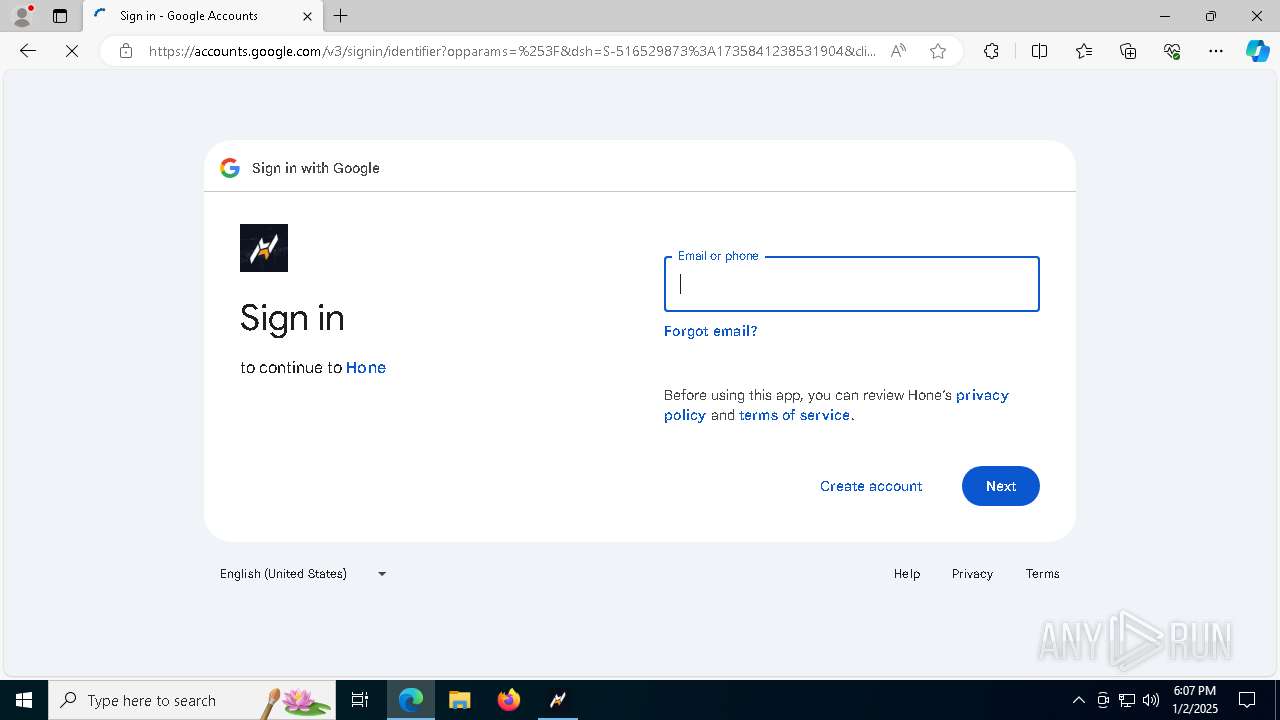
google.com |
| whitelisted |
crl.microsoft.com |
| unknown |
www.microsoft.com |
| whitelisted |
analyticsnew.overwolf.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
content.overwolf.com |
| whitelisted |
ocsp.rootca3.amazontrust.com |
| unknown |
storeapi.overwolf.com |
| shared |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6176 | Hone - Installer.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
6796 | Hone - Installer.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
10 ETPRO signatures available at the full report