| File name: | DecEmp23 (2).jnlp |
| Full analysis: | https://app.any.run/tasks/55239c6a-c16b-4434-b5df-10d6834014ca |
| Verdict: | Malicious activity |
| Analysis date: | September 02, 2024, 09:44:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, Unicode text, UTF-8 text |
| MD5: | BC9C85D9D117DF42DB5A87B761168FF2 |
| SHA1: | 3F7F210F2D2B81D1C91EEC90CDC0A0823C4E66DB |
| SHA256: | 2FD527B185699572667483D00AE52419BE55505790A28B26DAFBE52C6FE8D6F4 |
| SSDEEP: | 12:ZFMHdumpIGOD8zbxyhePe2t6FLQBKpIGOJlOlunrI4Oh7:udv08jr+EBKc0lD |
MALICIOUS
No malicious indicators.SUSPICIOUS
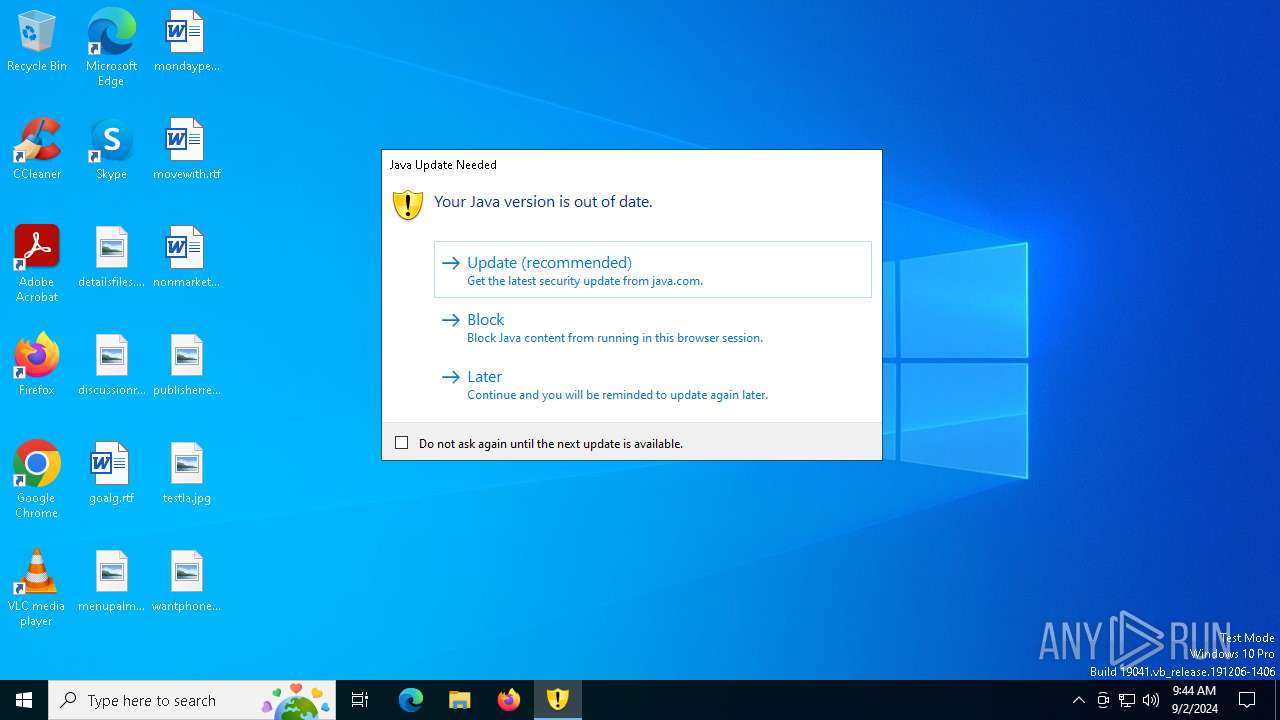
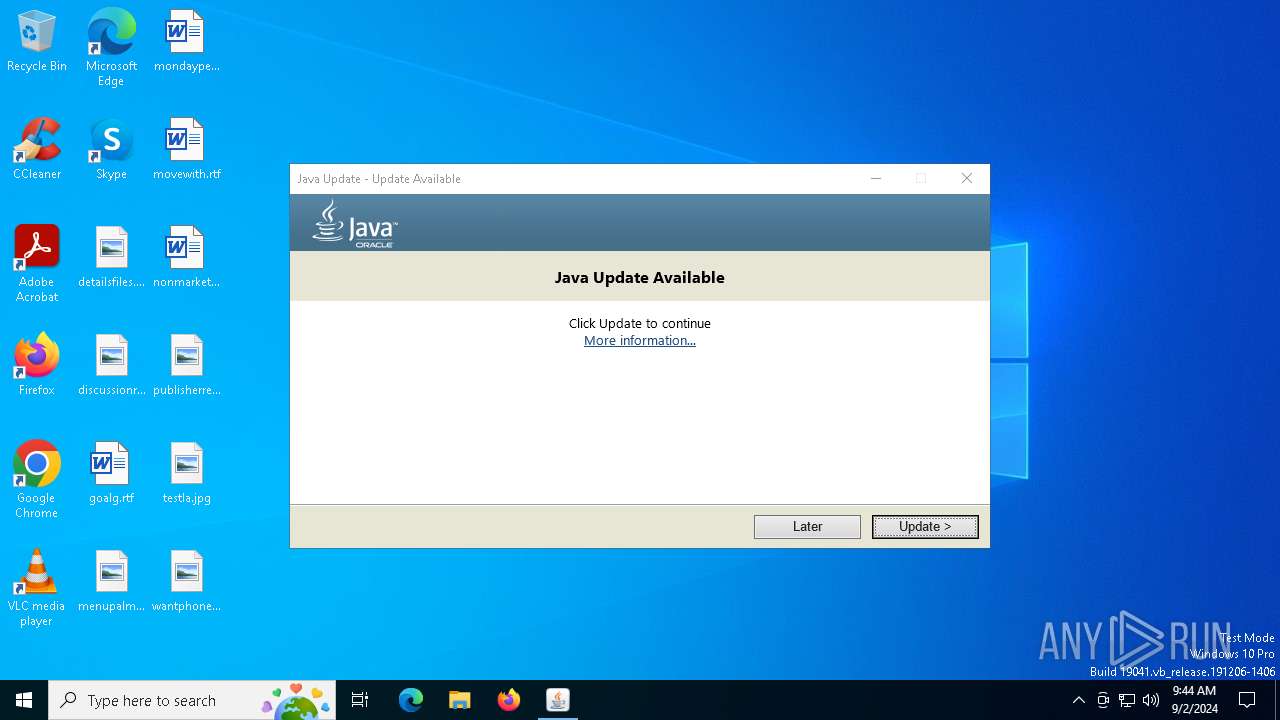
Checks for Java to be installed
- javaws.exe (PID: 3728)
- javaw.exe (PID: 2268)
- javaw.exe (PID: 4444)
- javaw.exe (PID: 4008)
- jucheck.exe (PID: 208)
- jp2launcher.exe (PID: 6244)
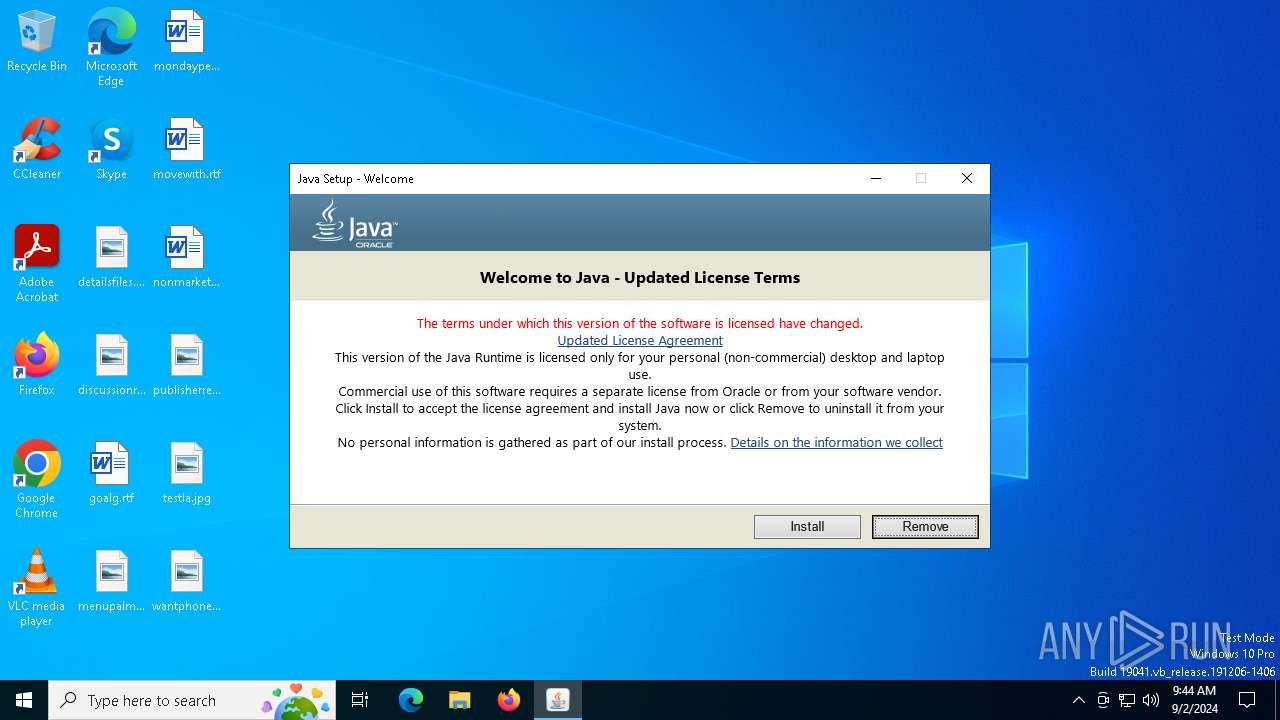
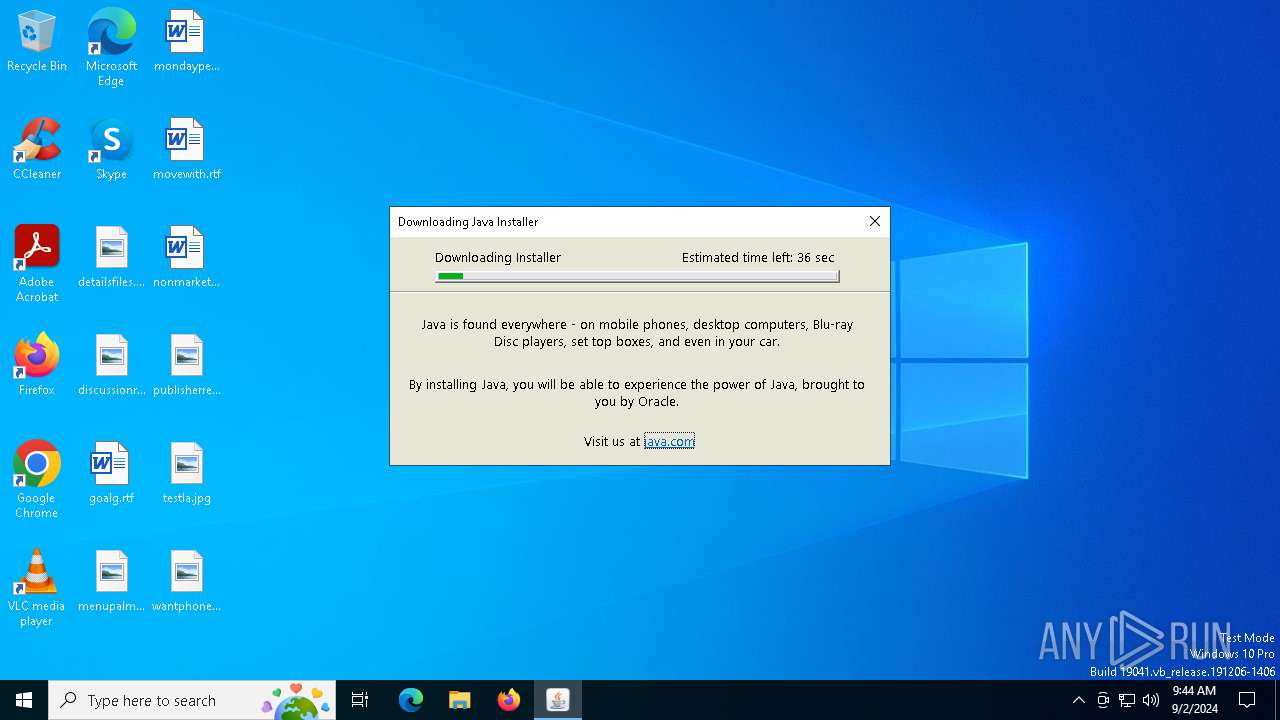
- jre-8u421-windows-au.exe (PID: 3268)
- msiexec.exe (PID: 6380)
- msiexec.exe (PID: 5148)
- installer.exe (PID: 6328)
- ssvagent.exe (PID: 5772)
- jp2launcher.exe (PID: 6356)
- jp2launcher.exe (PID: 1964)
- msiexec.exe (PID: 6576)
- msiexec.exe (PID: 6368)
Checks Windows Trust Settings
- jucheck.exe (PID: 208)
- jre-8u421-windows-au.exe (PID: 3268)
- msiexec.exe (PID: 5148)
Reads Microsoft Outlook installation path
- jucheck.exe (PID: 208)
- jre-8u421-windows-au.exe (PID: 3268)
Reads security settings of Internet Explorer
- jucheck.exe (PID: 208)
- jp2launcher.exe (PID: 6244)
- jre-8u421-windows-au.exe (PID: 3268)
- jp2launcher.exe (PID: 6356)
- jp2launcher.exe (PID: 1964)
- installer.exe (PID: 6328)
Reads Internet Explorer settings
- jucheck.exe (PID: 208)
- jre-8u421-windows-au.exe (PID: 3268)
Executable content was dropped or overwritten
- jucheck.exe (PID: 208)
- jre-8u421-windows-au.exe (PID: 4392)
- jre-8u421-windows-au.exe (PID: 3268)
- LZMA_EXE (PID: 4732)
- installer.exe (PID: 6328)
Drops the executable file immediately after the start
- jucheck.exe (PID: 208)
- jre-8u421-windows-au.exe (PID: 4392)
- jre-8u421-windows-au.exe (PID: 3268)
- LZMA_EXE (PID: 4732)
- msiexec.exe (PID: 5148)
- installer.exe (PID: 6328)
Reads the date of Windows installation
- jucheck.exe (PID: 208)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5148)
Process drops legitimate windows executable
- msiexec.exe (PID: 5148)
The process drops C-runtime libraries
- msiexec.exe (PID: 5148)
Reads Mozilla Firefox installation path
- MSI9701.tmp (PID: 6940)
- installer.exe (PID: 6328)
Starts application with an unusual extension
- jre-8u421-windows-au.exe (PID: 3268)
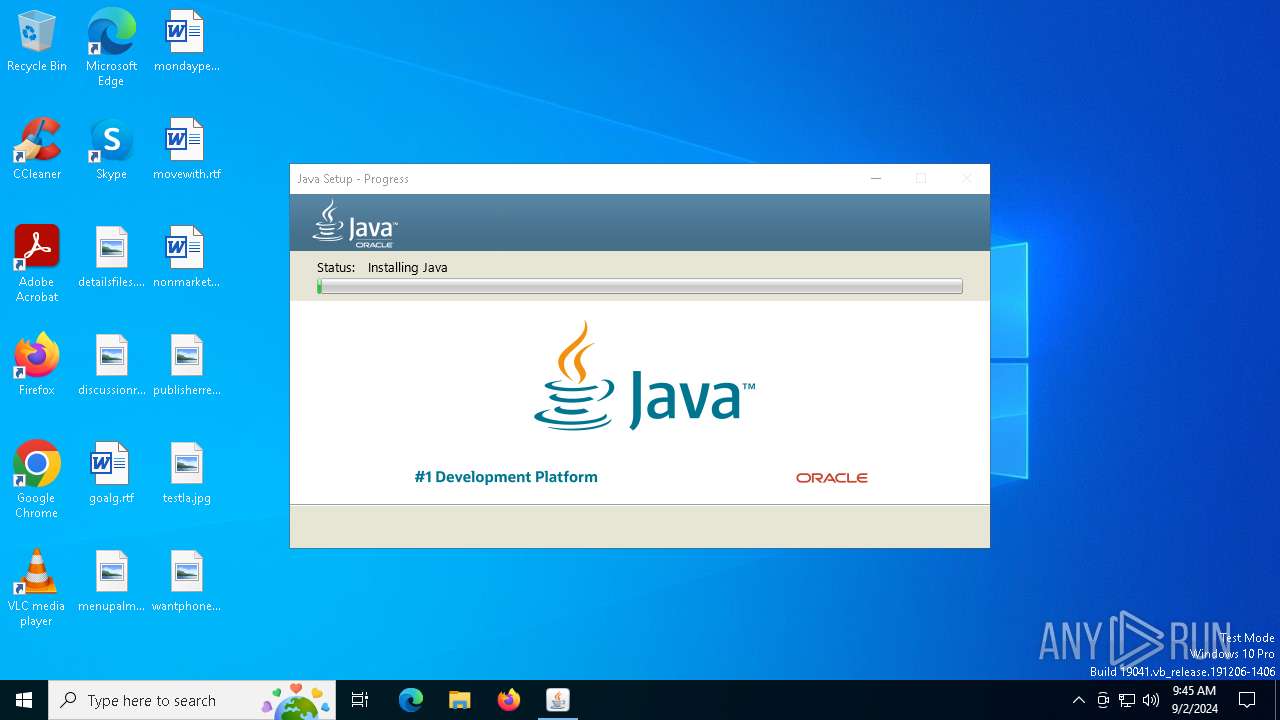
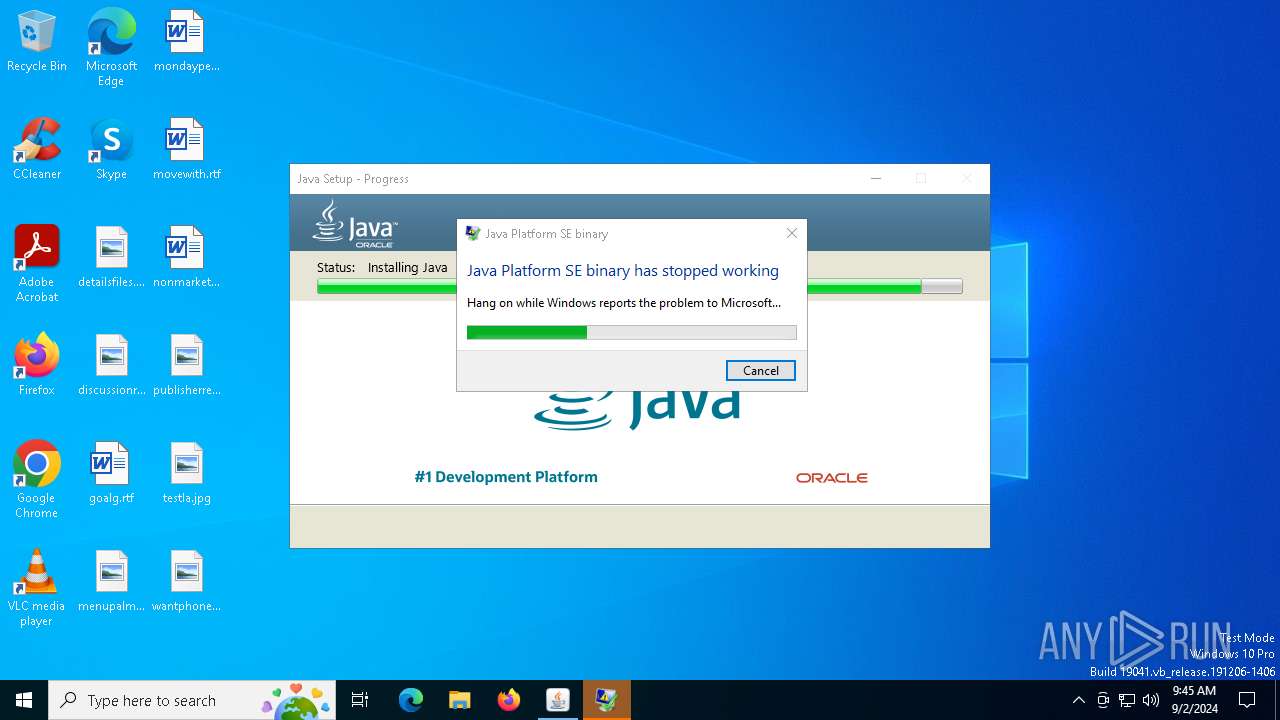
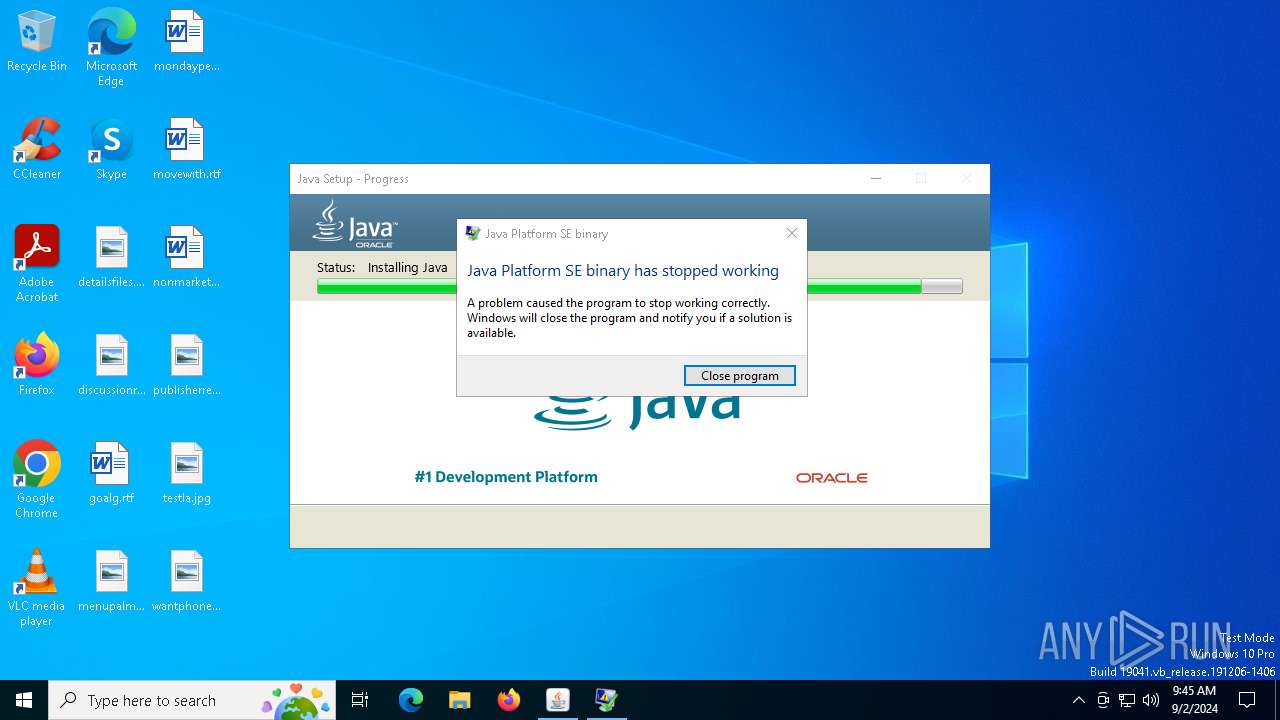
Executes application which crashes
- jre-8u421-windows-au.exe (PID: 3268)
Creates/Modifies COM task schedule object
- ssvagent.exe (PID: 5772)
- installer.exe (PID: 6328)
INFO
Create files in a temporary directory
- javaw.exe (PID: 4444)
- javaw.exe (PID: 4008)
- jucheck.exe (PID: 208)
- javaw.exe (PID: 2268)
- jp2launcher.exe (PID: 6244)
- jre-8u421-windows-au.exe (PID: 4392)
- MSI9701.tmp (PID: 6940)
- javaw.exe (PID: 2268)
- jp2launcher.exe (PID: 6356)
- jp2launcher.exe (PID: 1964)
Reads the computer name
- javaw.exe (PID: 4444)
- javaws.exe (PID: 3728)
- javaw.exe (PID: 2268)
- jucheck.exe (PID: 208)
- jp2launcher.exe (PID: 6244)
- jre-8u421-windows-au.exe (PID: 4392)
- javaws.exe (PID: 6404)
- jre-8u421-windows-au.exe (PID: 3268)
- javaw.exe (PID: 4008)
- msiexec.exe (PID: 5148)
- msiexec.exe (PID: 6380)
- MSI9701.tmp (PID: 6940)
- installer.exe (PID: 6328)
- javaws.exe (PID: 7020)
- javaws.exe (PID: 5984)
- jp2launcher.exe (PID: 1964)
- msiexec.exe (PID: 6576)
- jp2launcher.exe (PID: 6356)
- msiexec.exe (PID: 4732)
- msiexec.exe (PID: 7076)
- msiexec.exe (PID: 6368)
- msiexec.exe (PID: 6708)
Checks supported languages
- javaw.exe (PID: 2268)
- jp2launcher.exe (PID: 5140)
- javaws.exe (PID: 3728)
- javaw.exe (PID: 4444)
- jucheck.exe (PID: 208)
- javaws.exe (PID: 6404)
- javaw.exe (PID: 4008)
- jre-8u421-windows-au.exe (PID: 4392)
- jre-8u421-windows-au.exe (PID: 3268)
- jp2launcher.exe (PID: 6244)
- LZMA_EXE (PID: 4732)
- LZMA_EXE (PID: 4820)
- msiexec.exe (PID: 5148)
- msiexec.exe (PID: 6380)
- MSI9701.tmp (PID: 6940)
- installer.exe (PID: 6328)
- jaureg.exe (PID: 5816)
- javaw.exe (PID: 2268)
- ssvagent.exe (PID: 5772)
- javaws.exe (PID: 7020)
- jp2launcher.exe (PID: 6356)
- javaws.exe (PID: 5984)
- jp2launcher.exe (PID: 1964)
- msiexec.exe (PID: 4732)
- msiexec.exe (PID: 7076)
- msiexec.exe (PID: 6368)
- msiexec.exe (PID: 6576)
- msiexec.exe (PID: 6708)
Creates files in the program directory
- javaw.exe (PID: 4444)
- installer.exe (PID: 6328)
- javaw.exe (PID: 2268)
Checks proxy server information
- jucheck.exe (PID: 208)
- jp2launcher.exe (PID: 6244)
- jre-8u421-windows-au.exe (PID: 3268)
- jp2launcher.exe (PID: 6356)
- jp2launcher.exe (PID: 1964)
- WerFault.exe (PID: 6496)
Reads the machine GUID from the registry
- jucheck.exe (PID: 208)
- jp2launcher.exe (PID: 6244)
- msiexec.exe (PID: 5148)
- jre-8u421-windows-au.exe (PID: 3268)
Creates files or folders in the user directory
- jucheck.exe (PID: 208)
- jp2launcher.exe (PID: 6244)
- jre-8u421-windows-au.exe (PID: 3268)
- LZMA_EXE (PID: 4732)
- LZMA_EXE (PID: 4820)
- WerFault.exe (PID: 6496)
Reads the software policy settings
- jucheck.exe (PID: 208)
- jre-8u421-windows-au.exe (PID: 3268)
- msiexec.exe (PID: 5148)
- WerFault.exe (PID: 6496)
- slui.exe (PID: 6640)
The process uses the downloaded file
- jucheck.exe (PID: 208)
- jre-8u421-windows-au.exe (PID: 3268)
Process checks Internet Explorer phishing filters
- jucheck.exe (PID: 208)
- jre-8u421-windows-au.exe (PID: 3268)
Process checks computer location settings
- jucheck.exe (PID: 208)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5148)
Application launched itself
- msiexec.exe (PID: 5148)
Starts application with an unusual extension
- msiexec.exe (PID: 5148)
Reads CPU info
- msiexec.exe (PID: 5148)
Creates a software uninstall entry
- msiexec.exe (PID: 5148)
Reads Environment values
- jre-8u421-windows-au.exe (PID: 3268)
Reads Microsoft Office registry keys
- installer.exe (PID: 6328)
Reads security settings of Internet Explorer
- WerFault.exe (PID: 6496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
173
Monitored processes
38
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Program Files (x86)\Common Files\Java\Java Update\jucheck.exe" | C:\Program Files (x86)\Common Files\Java\Java Update\jucheck.exe | javaws.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java Update Checker Exit code: 0 Version: 2.8.271.9 Modules
| |||||||||||||||
| 1044 | "C:\Windows\SysWOW64\msiexec.exe" /x {4A03706F-666A-4037-7777-5F2748764D10} /qn | C:\Windows\SysWOW64\msiexec.exe | — | jaureg.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 1605 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | LZMA_EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1712 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1964 | "C:\Program Files\Java\jre1.8.0_421\bin\jp2launcher.exe" -secure -javaws -jre "C:\Program Files\Java\jre1.8.0_421" -vma LWNsYXNzcGF0aABDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDIxXGxpYlxkZXBsb3kuamFyAC1EamF2YS5zZWN1cml0eS5wb2xpY3k9ZmlsZTpDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDIxXGxpYlxzZWN1cml0eVxqYXZhd3MucG9saWN5AC1EdHJ1c3RQcm94eT10cnVlAC1YdmVyaWZ5OnJlbW90ZQAtRGpubHB4LmhvbWU9QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzQyMVxiaW4ALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIALURzdW4uYXd0Lndhcm11cD10cnVlAC1YYm9vdGNsYXNzcGF0aC9hOkM6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUxLjguMF80MjFcbGliXGphdmF3cy5qYXI7QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzQyMVxsaWJcZGVwbG95LmphcjtDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDIxXGxpYlxwbHVnaW4uamFyAC1EamF2YS5hd3QuaGVhZGxlc3M9dHJ1ZQAtRGpubHB4Lmp2bT1DOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDIxXGJpblxqYXZhdy5leGU= -ma LXdhaXQALWZpeAAtc2hvcnRjdXQALXNpbGVudAAtbm90V2ViSmF2YQ== | C:\Program Files\Java\jre1.8.0_421\bin\jp2launcher.exe | — | javaws.exe | |||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.421.2.09 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_2\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.timestamp.11.271.2" "1725270256" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | javaws.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Java\jre1.8.0_421\bin\javaw.exe" -Xshare:dump -Djdk.disableLastUsageTracking | C:\Program Files\Java\jre1.8.0_421\bin\javaw.exe | installer.exe | ||||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.4210.9 Modules
| |||||||||||||||
| 3268 | "C:\Users\admin\AppData\Local\Temp\jds1233828.tmp\jre-8u421-windows-au.exe" "/installmethod=jau-m" "FAMILYUPGRADE=1" | C:\Users\admin\AppData\Local\Temp\jds1233828.tmp\jre-8u421-windows-au.exe | jre-8u421-windows-au.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java Platform SE binary Exit code: 3221225477 Version: 8.0.4210.9 Modules
| |||||||||||||||
| 3728 | "C:\Program Files\Java\jre1.8.0_271\bin\javaws.exe" "C:\Users\admin\AppData\Local\Temp\DecEmp23 (2).jnlp" | C:\Program Files\Java\jre1.8.0_271\bin\javaws.exe | — | jp2launcher.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Start Launcher Exit code: 1 Version: 11.271.2.09 Modules
| |||||||||||||||
| 3880 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
66 498
Read events
39 089
Write events
12 848
Delete events
14 561
Modification events
| (PID) Process: | (4444) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.modified.timestamp |
Value: 1675955855080 | |||
| (PID) Process: | (4444) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.roaming.profile |
Value: false | |||
| (PID) Process: | (4444) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.version |
Value: 8 | |||
| (PID) Process: | (4444) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.expired.version |
Value: 11.271.2 | |||
| (PID) Process: | (4444) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.browser.path |
Value: C:\Program Files\Internet Explorer\IEXPLORE.EXE | |||
| (PID) Process: | (4444) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4444) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.expiration.decision.11.271.2 |
Value: update | |||
| (PID) Process: | (2268) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2268) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.expiration.decision.11.271.2 |
Value: update | |||
| (PID) Process: | (2268) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.modified.timestamp |
Value: 1725270256603 | |||
Executable files
362
Suspicious files
110
Text files
219
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6244 | jp2launcher.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1693682860-607145093-2874071422-1001\83aa4cc77f591dfc2374580bbd95f6ba_bb926e54-e3ca-40fd-ae90-2764341e7792 | dbf | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
| 6244 | jp2launcher.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\security\baseline.versions | text | |
MD5:74798BE1F4CA6115228214925061CF9E | SHA256:FF22C45E4DE806EC2C8CF165CA956D5AD343DD209F9193DD48BFFC4340C5A5B0 | |||
| 208 | jucheck.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:AFF366C2631FB848419D301840981502 | SHA256:930DEDE0A447BD8E7580472AC5C78F0D8DCD3B009C10EA437F588D805BE25329 | |||
| 6244 | jp2launcher.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\security\blacklisted.certs | text | |
MD5:8273F70416F494F7FA5B6C70A101E00E | SHA256:583500B76965EB54B03493372989AB4D3426F85462D1DB232C5AE6706A4D6C58 | |||
| 6244 | jp2launcher.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\security\update.securitypack.timestamp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 6244 | jp2launcher.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\security\securitypack.jar | java | |
MD5:00E5F72258E6C602E6841BBF4C30B136 | SHA256:905A454FCB15E9F2A469A9A7E6E42B8C6425D20B33A59BE5B84818DAAE964807 | |||
| 3268 | jre-8u421-windows-au.exe | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_421_x64\jds1235656.tmp | — | |
MD5:— | SHA256:— | |||
| 3268 | jre-8u421-windows-au.exe | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_421_x64\jre1.8.0_42164.msi | — | |
MD5:— | SHA256:— | |||
| 208 | jucheck.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:A0E0207226481D8D870E03C191C71CC4 | SHA256:04A8091FBBBA9AF6C2831BCF4836B9A9AC5A7AB76A1838E3A64F07086A189C00 | |||
| 4820 | LZMA_EXE | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_421_x64\msi.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
48
DNS requests
21
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
208 | jucheck.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | — | — | whitelisted |
6244 | jp2launcher.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | unknown |
6244 | jp2launcher.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | unknown |
208 | jucheck.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
208 | jucheck.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAYOL4%2BeG4vlGNX%2BK2nPzLE%3D | unknown | — | — | whitelisted |
6244 | jp2launcher.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | unknown |
208 | jucheck.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
1440 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3984 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3984 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6428 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6012 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6012 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
208 | jucheck.exe | 23.199.222.107:443 | javadl-esd-secure.oracle.com | AKAMAI-AS | US | whitelisted |
208 | jucheck.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6244 | jp2launcher.exe | 23.199.222.107:443 | javadl-esd-secure.oracle.com | AKAMAI-AS | US | whitelisted |
6244 | jp2launcher.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
208 | jucheck.exe | 23.210.126.114:443 | javadl.oracle.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
javadl-esd-secure.oracle.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
javadl.oracle.com |
| whitelisted |
sdlc-esd.oracle.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6244 | jp2launcher.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
6244 | jp2launcher.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |