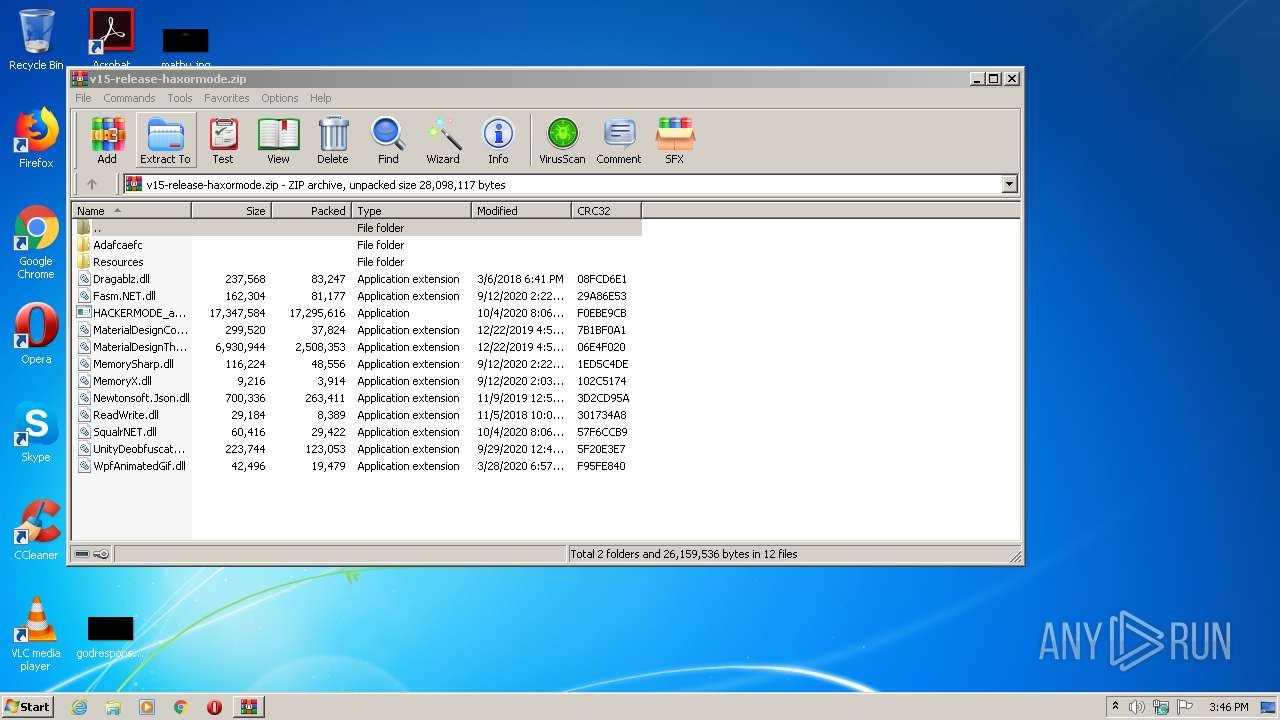
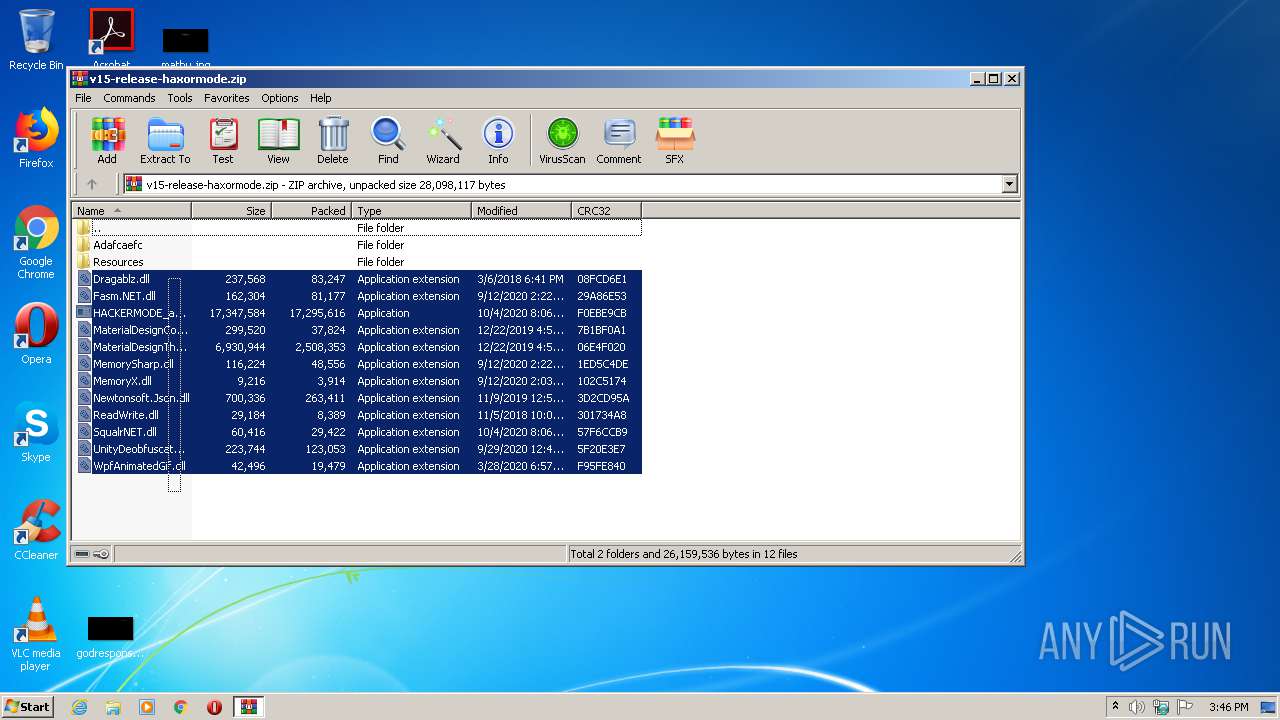
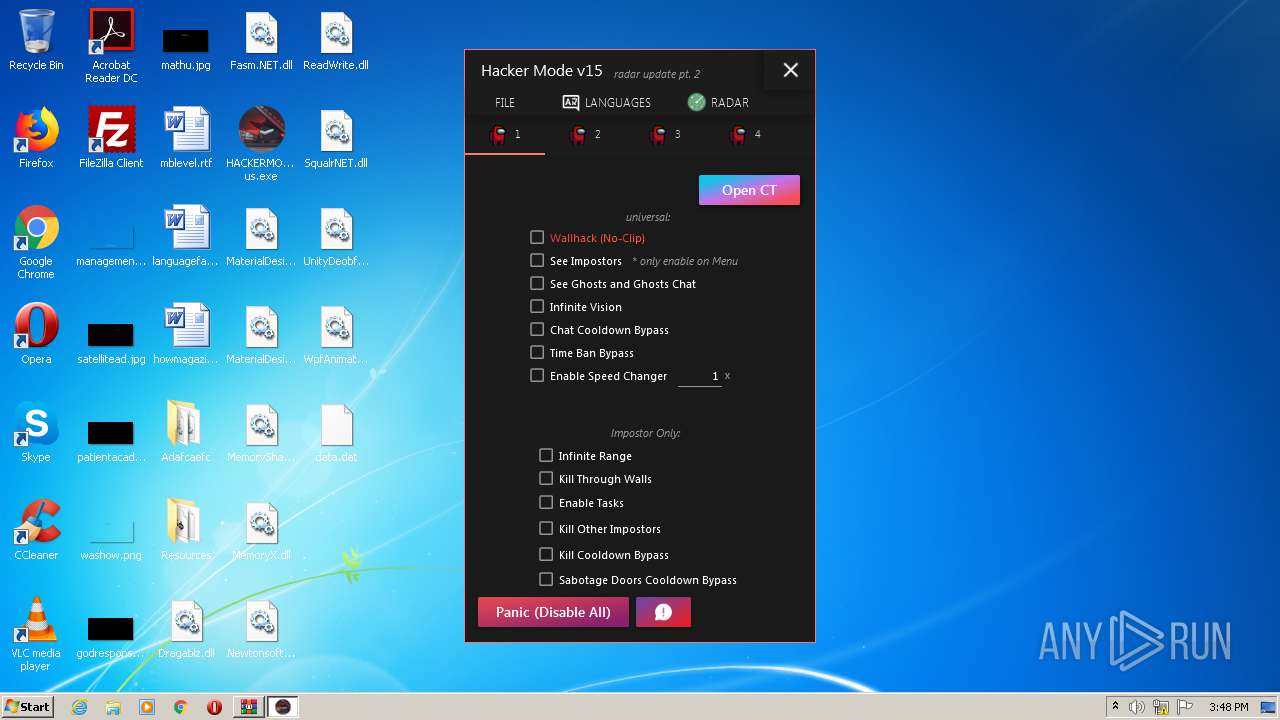
| download: | v15-release-haxormode.zip |
| Full analysis: | https://app.any.run/tasks/be83282d-98bc-4abb-a1e8-fbff78eb4a3a |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2020, 14:45:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | F53446694B806AD36A01EEFCB9FC9308 |
| SHA1: | E521B377BBBBE334CAB9E5FAB807DF14B4219F43 |
| SHA256: | 2FD3F619D2DC6F978ADF6DDD387E69B7B614A056932D0F8DA221FD767A1B0C55 |
| SSDEEP: | 393216:tPXMzwRgfp8MFXhGmOJjke9zLA2+Vghtfs72PmZP+O:tPcNTVoNdAhVgPfsqeZPt |
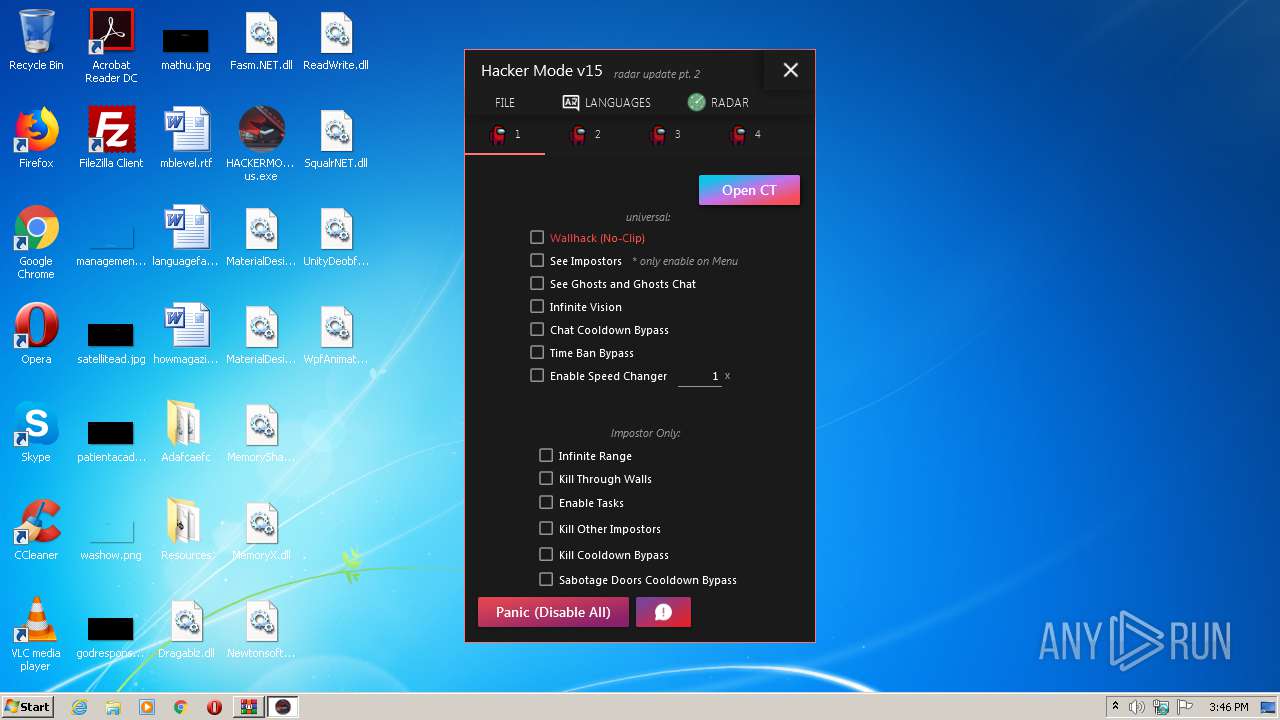
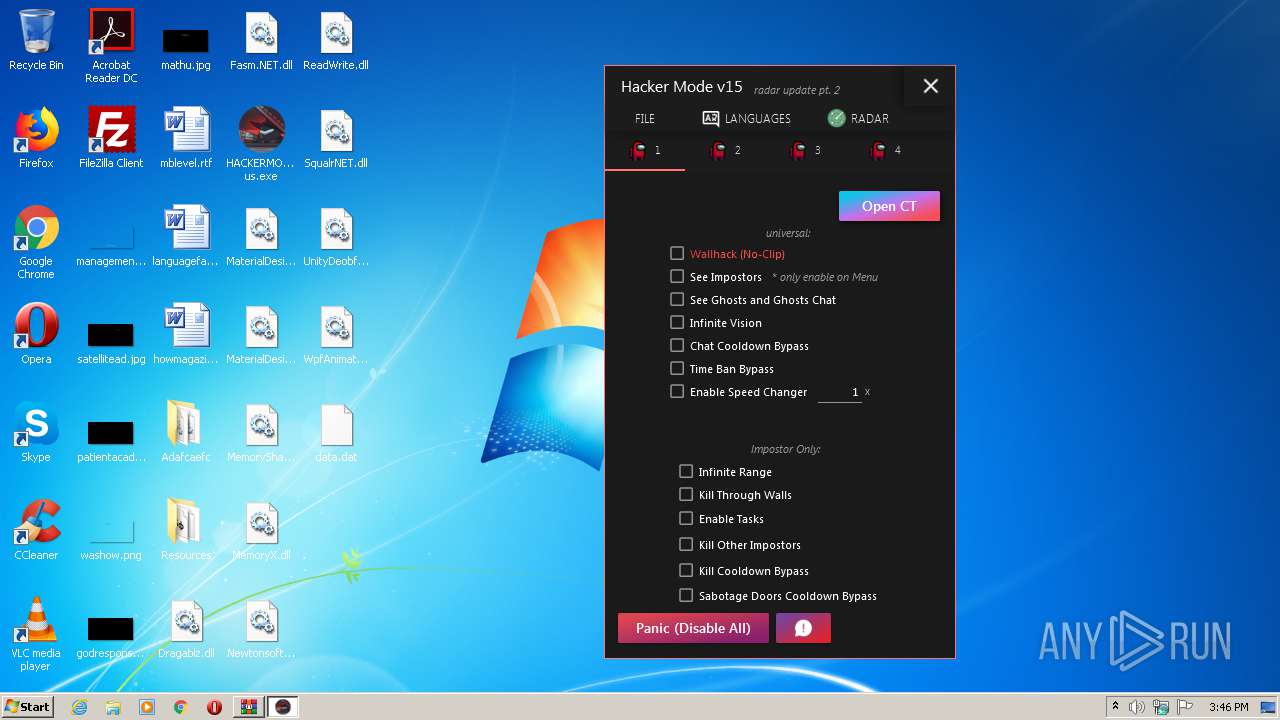
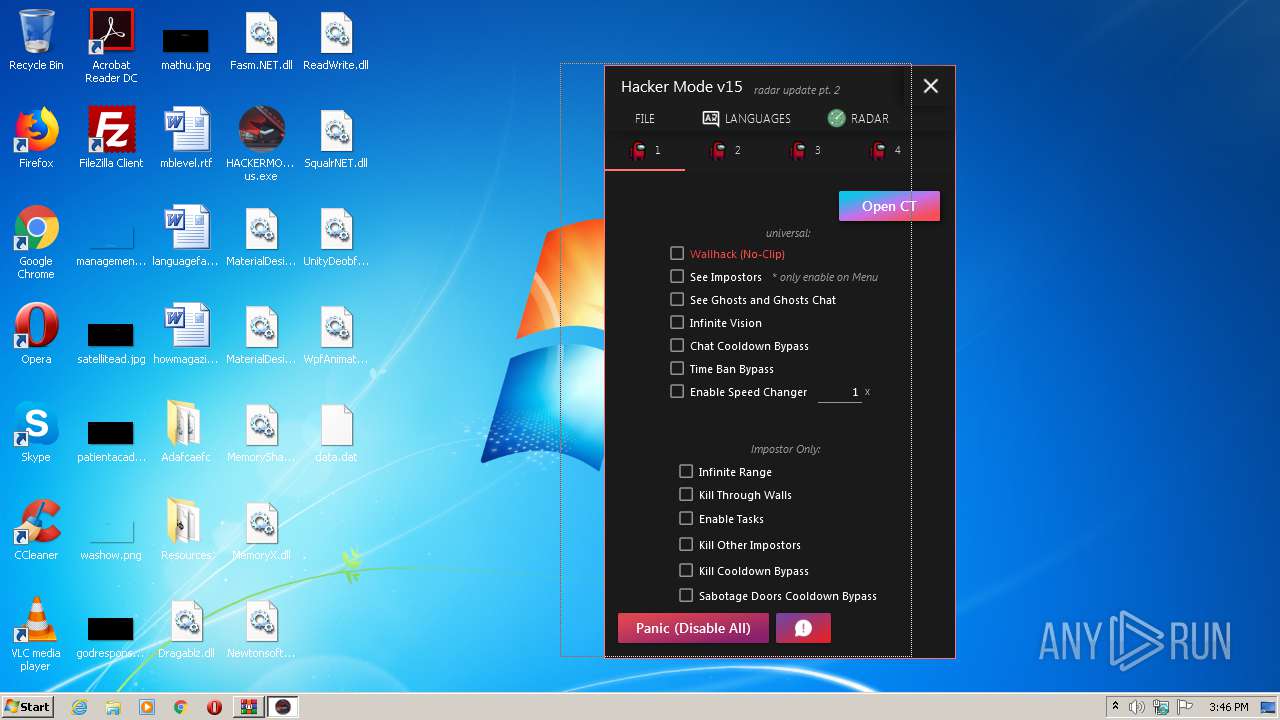
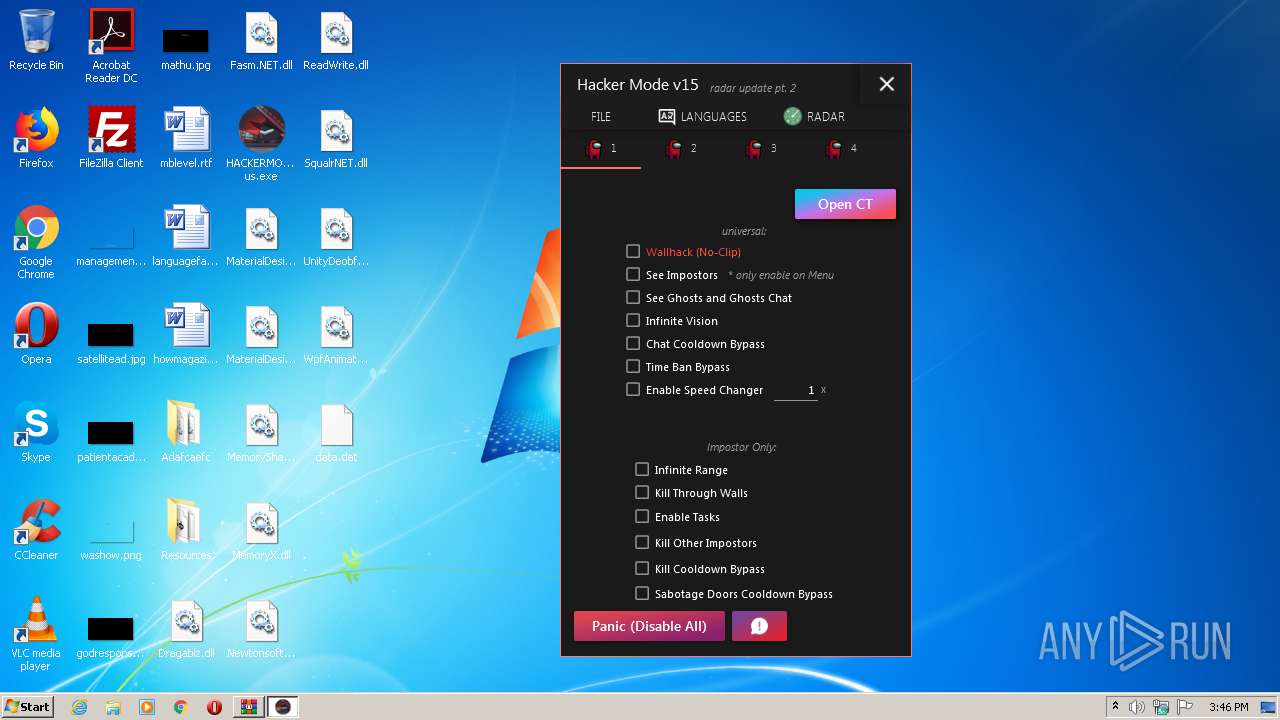
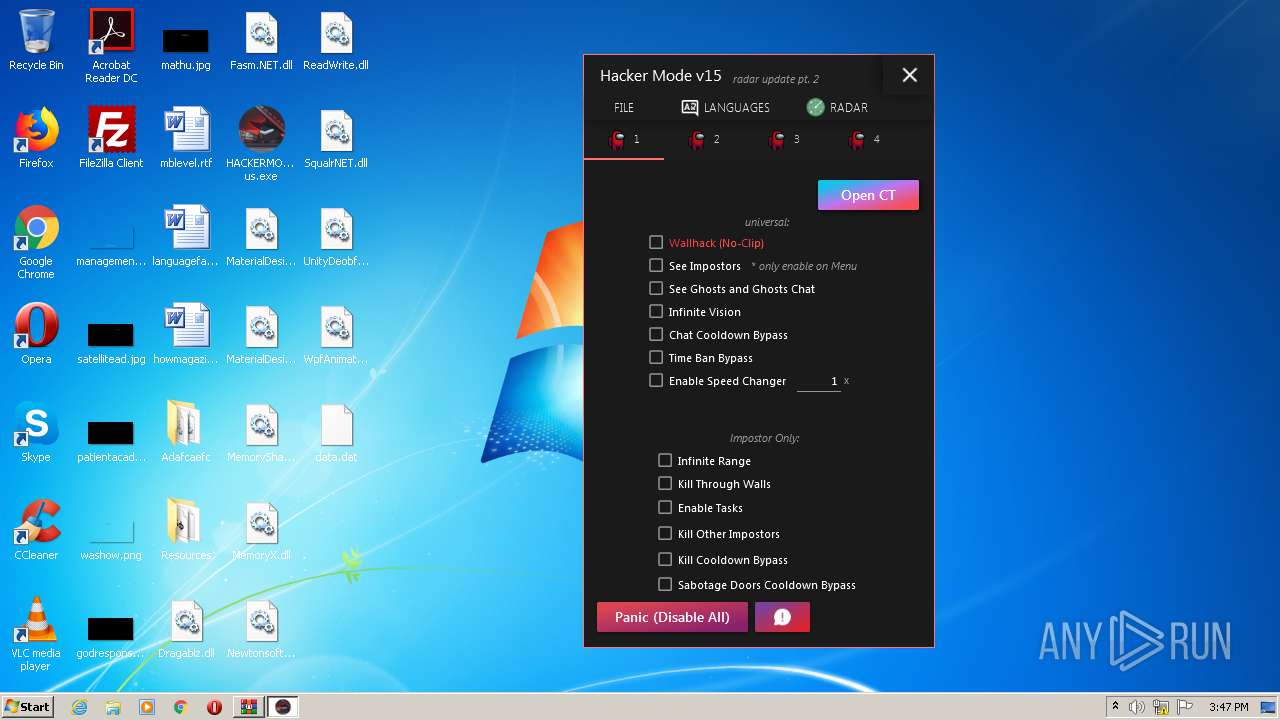
MALICIOUS
Application was dropped or rewritten from another process
- HACKERMODE_among us.exe (PID: 1292)
- HACKERMODE_among us.exe (PID: 2488)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3100)
- HACKERMODE_among us.exe (PID: 1292)
- HACKERMODE_among us.exe (PID: 2488)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2868)
Executed via COM
- MsSpellCheckingFacility.exe (PID: 1132)
- MsSpellCheckingFacility.exe (PID: 2012)
Reads Environment values
- HACKERMODE_among us.exe (PID: 1292)
- HACKERMODE_among us.exe (PID: 2488)
INFO
Reads settings of System Certificates
- HACKERMODE_among us.exe (PID: 1292)
- HACKERMODE_among us.exe (PID: 2488)
Manual execution by user
- HACKERMODE_among us.exe (PID: 1292)
- HACKERMODE_among us.exe (PID: 2488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:09:09 12:32:11 |
| ZipCRC: | 0x862e9b63 |
| ZipCompressedSize: | 101932 |
| ZipUncompressedSize: | 188928 |
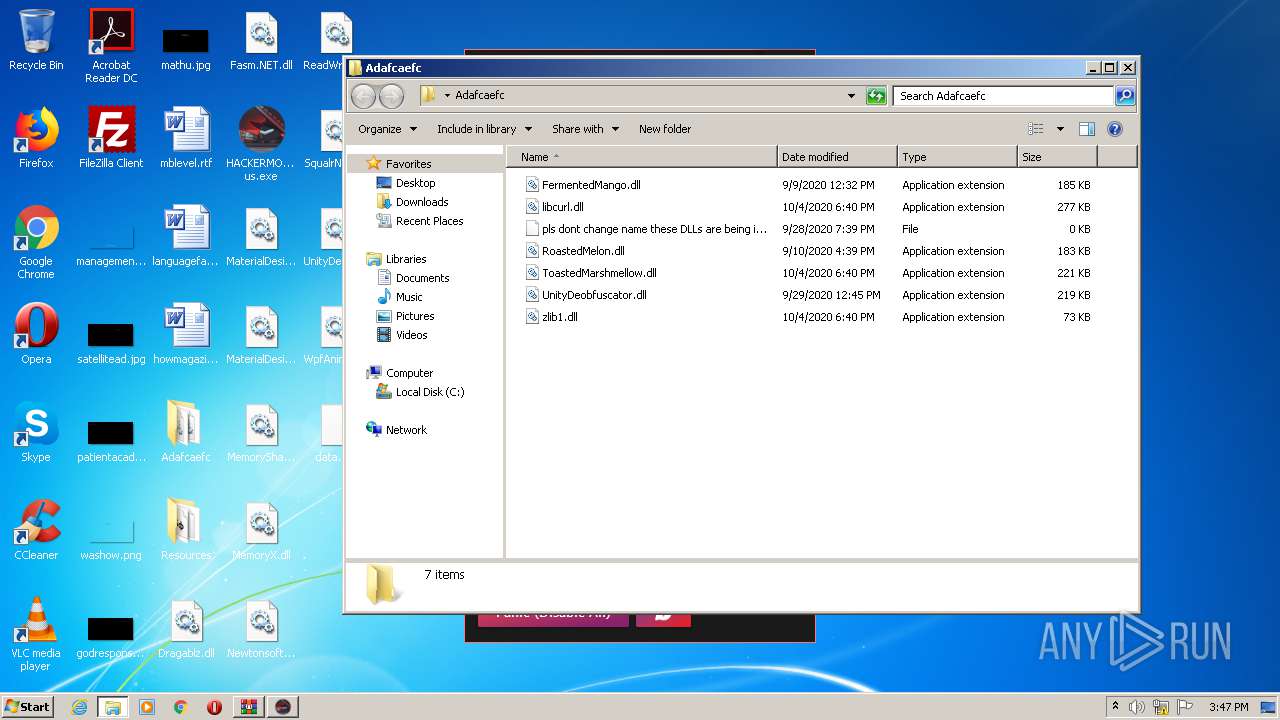
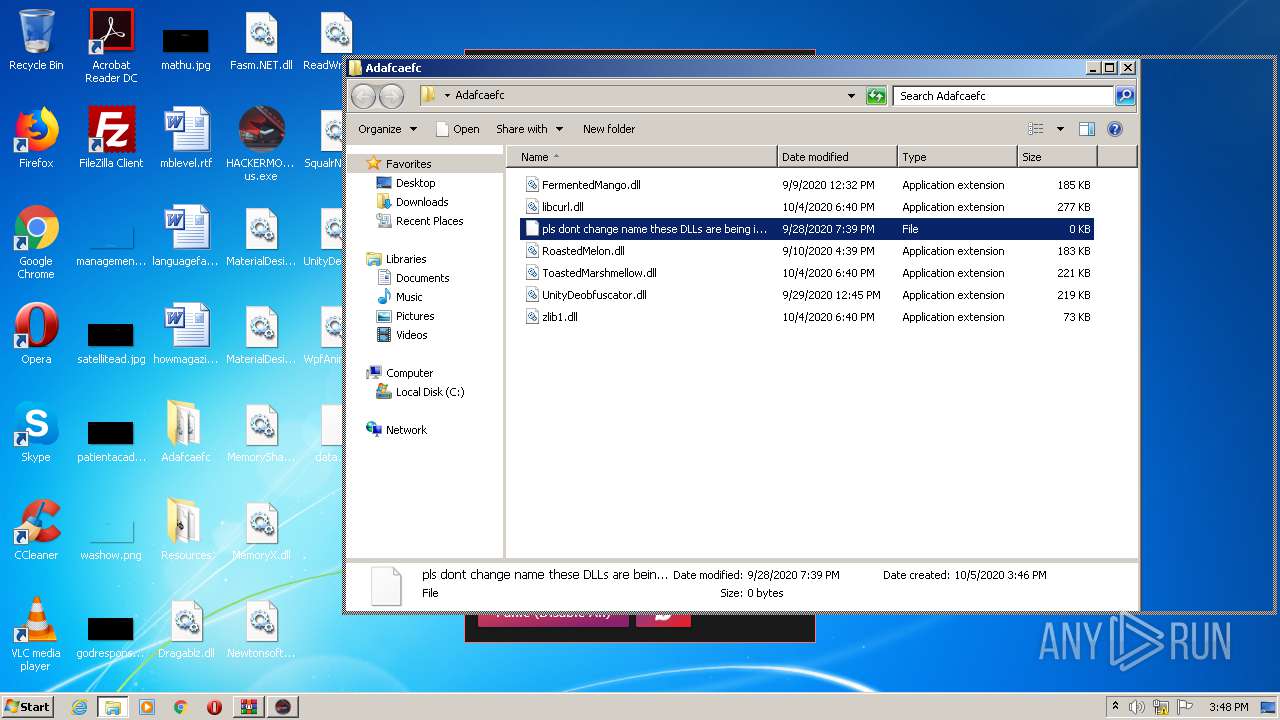
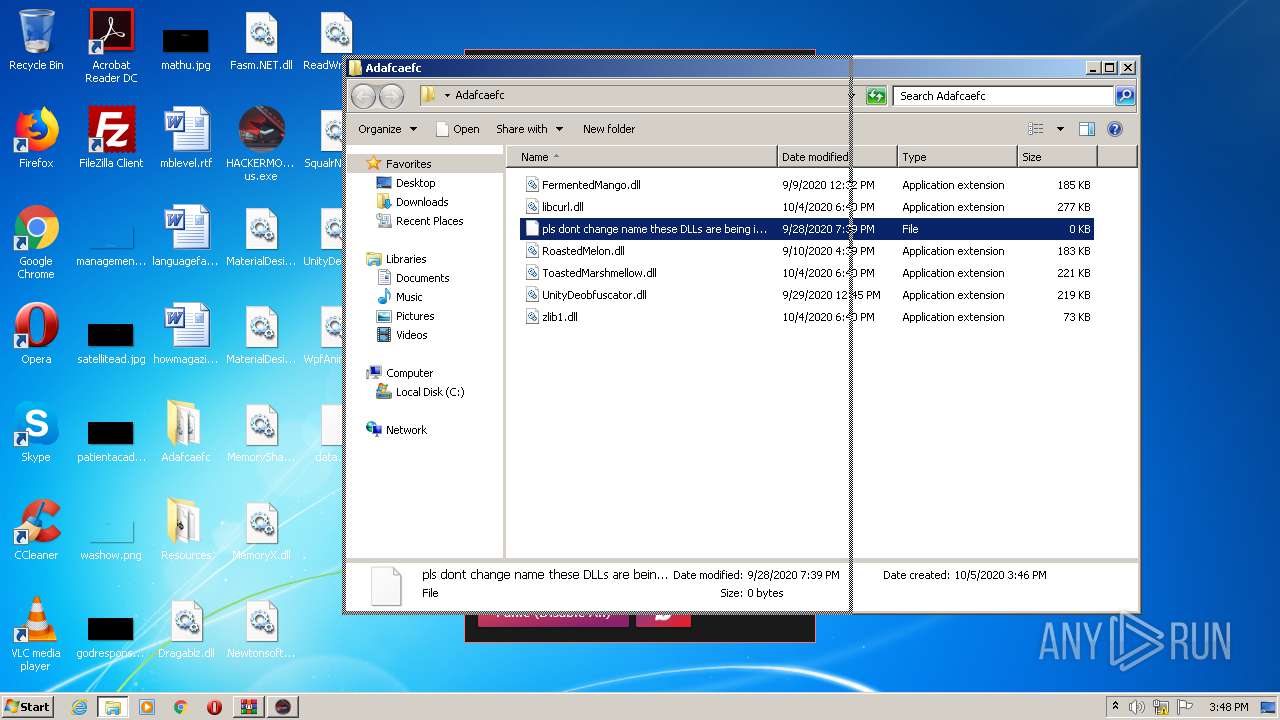
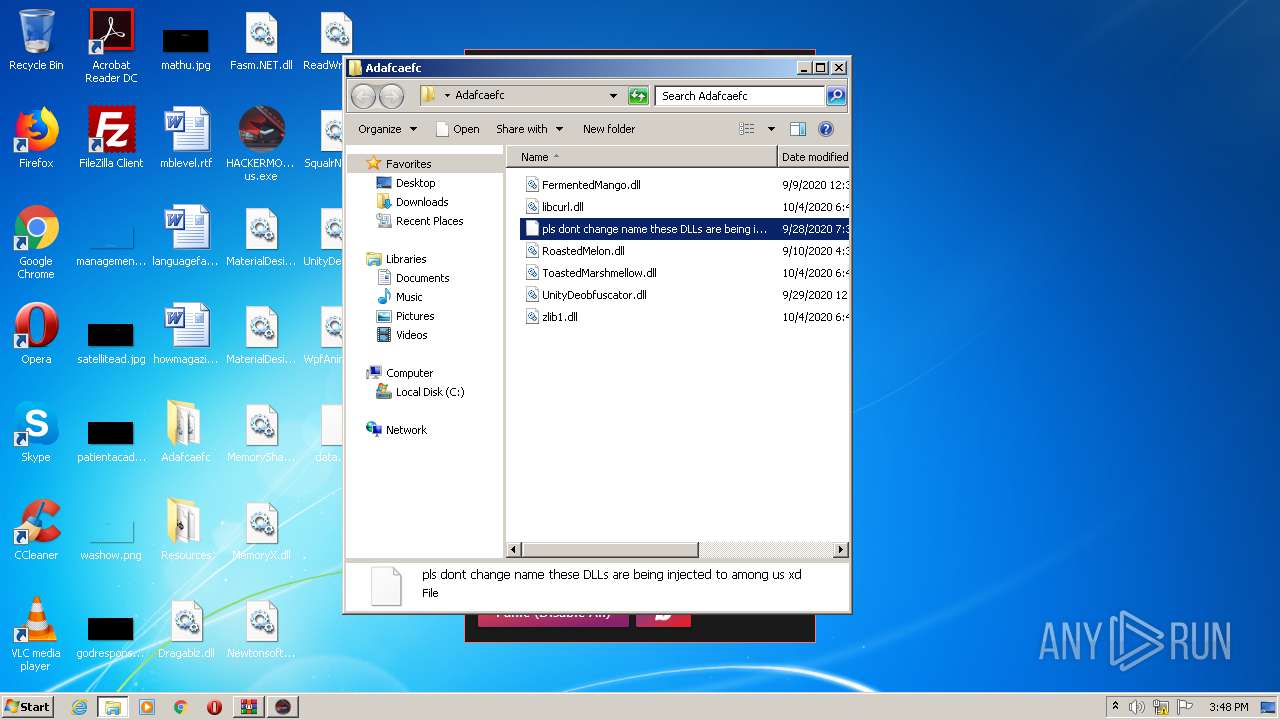
| ZipFileName: | Adafcaefc/FermentedMango.dll |
Total processes
43
Monitored processes
6
Malicious processes
3
Suspicious processes
0
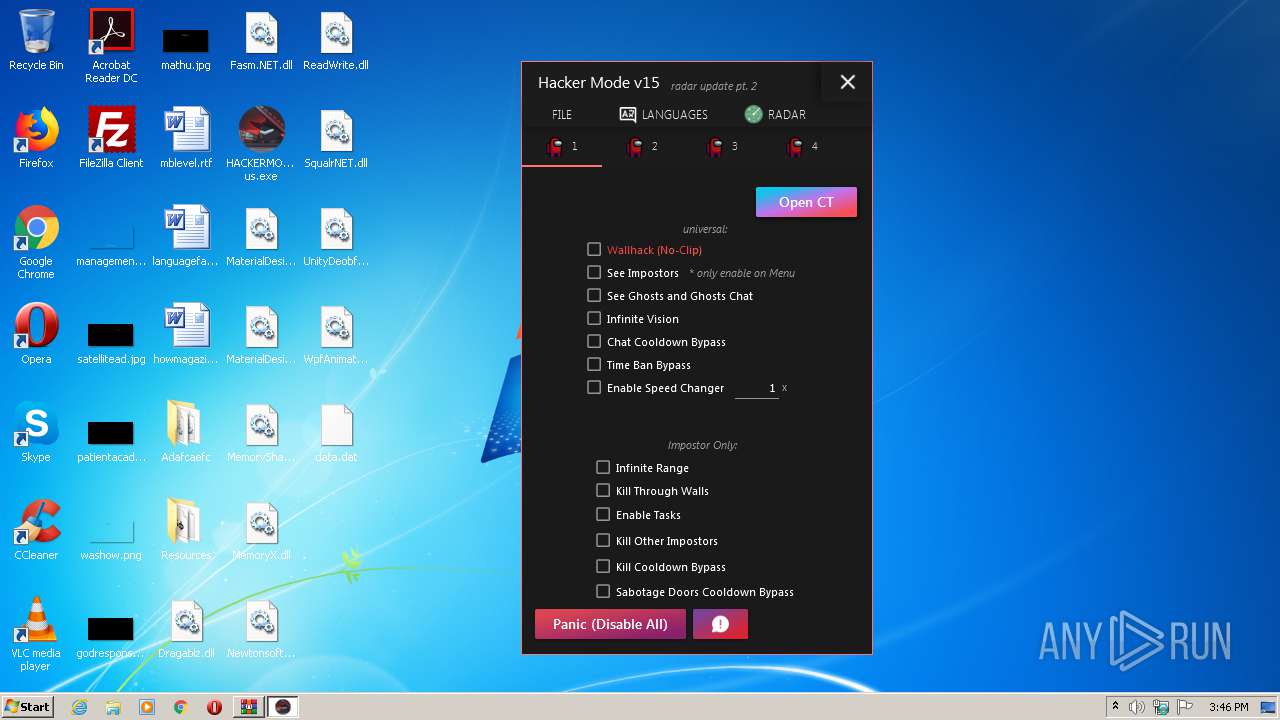
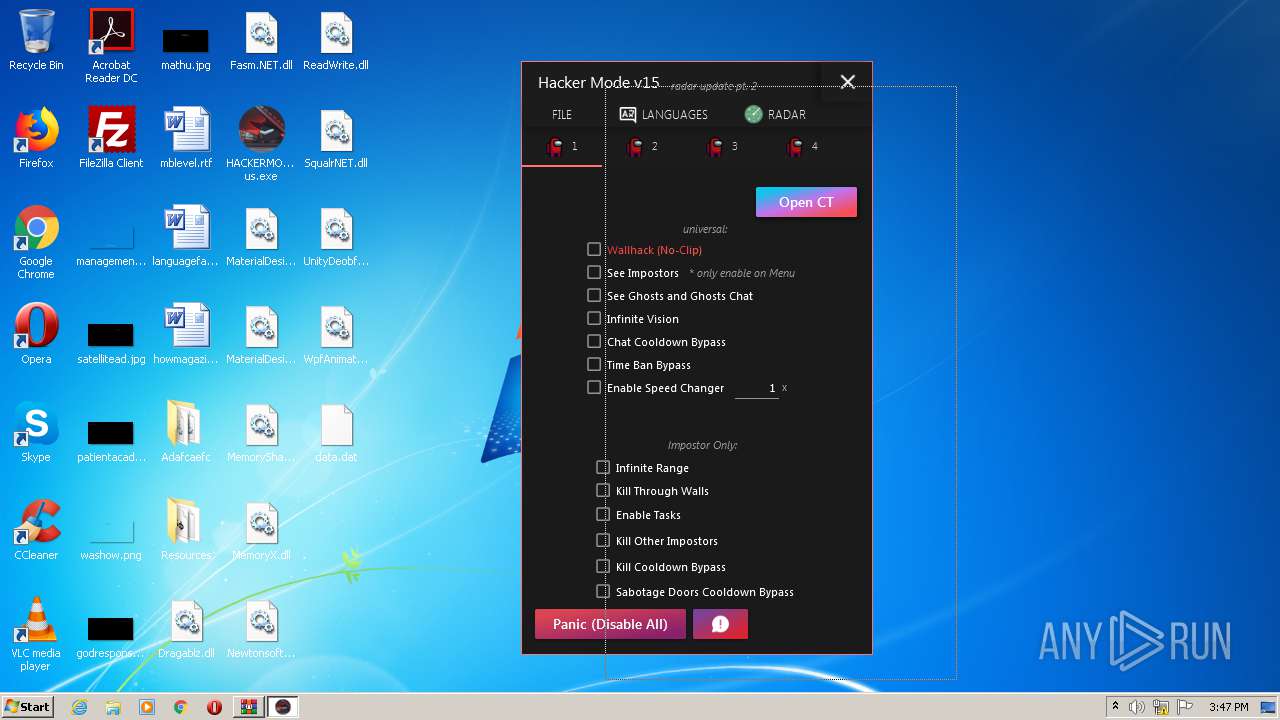
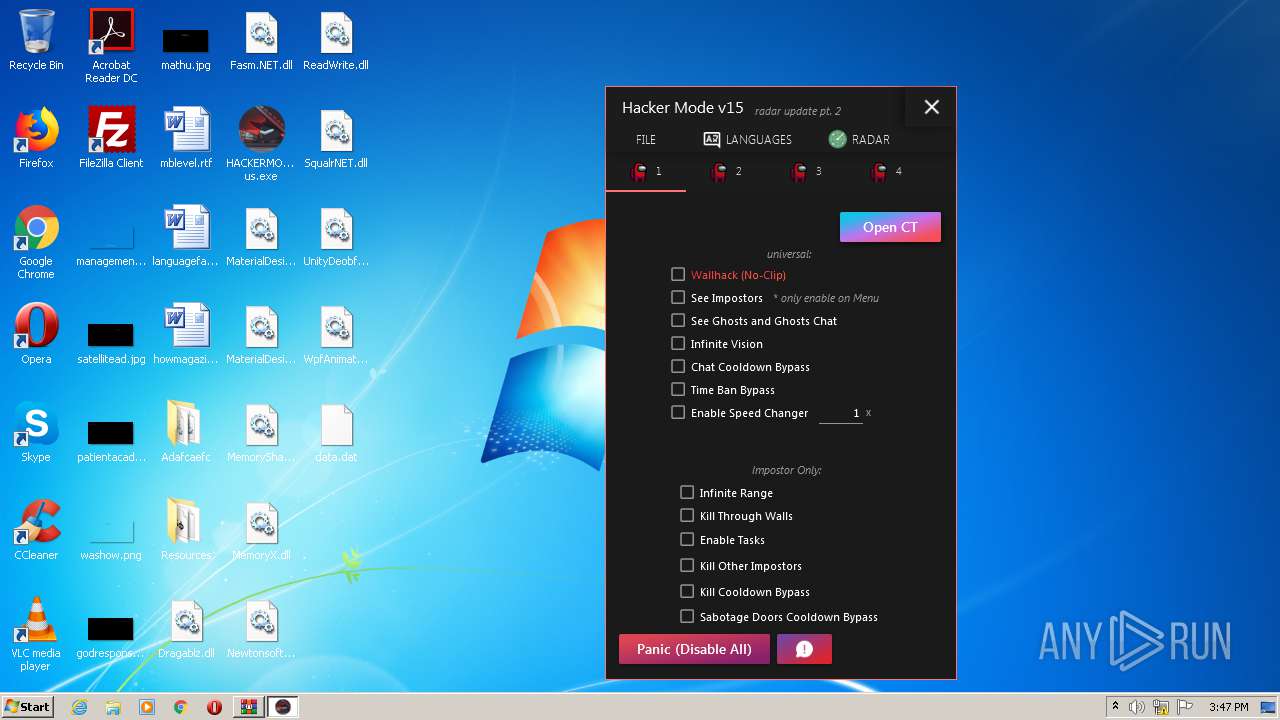
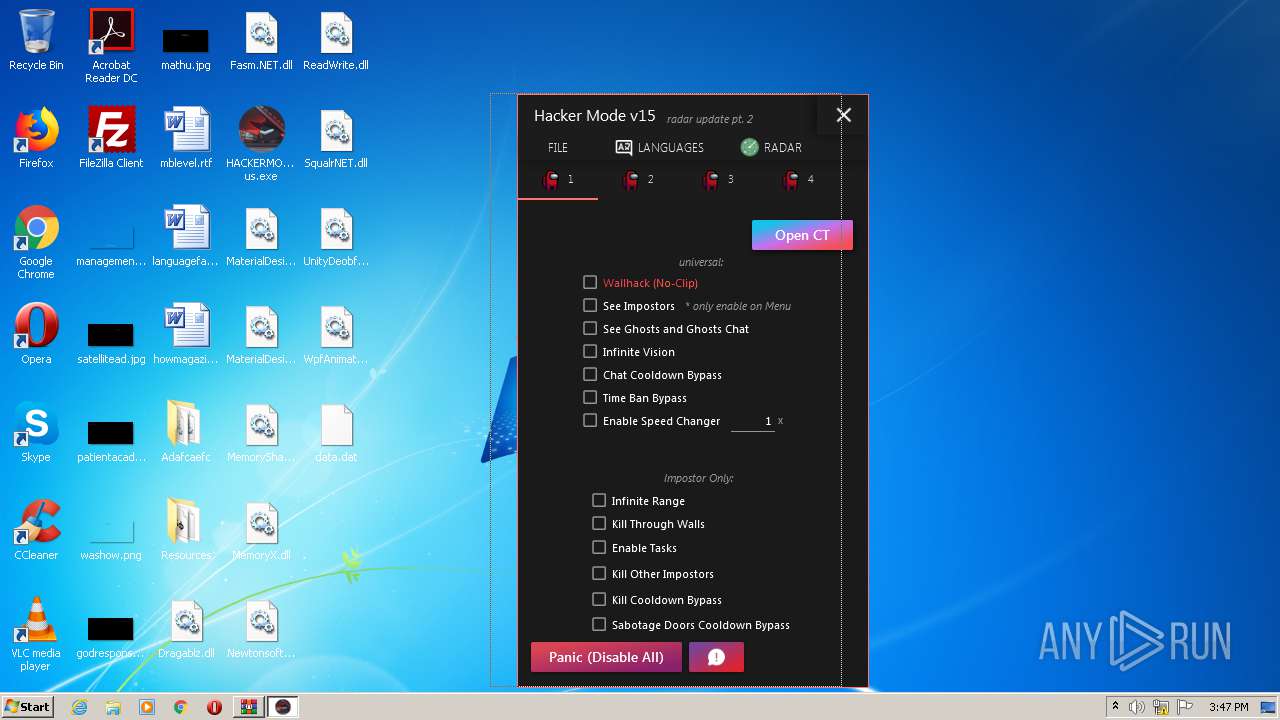
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1132 | "C:\Windows\System32\MsSpellCheckingFacility.exe" -Embedding | C:\Windows\System32\MsSpellCheckingFacility.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Spell Checking Facility Exit code: 0 Version: 6.3.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
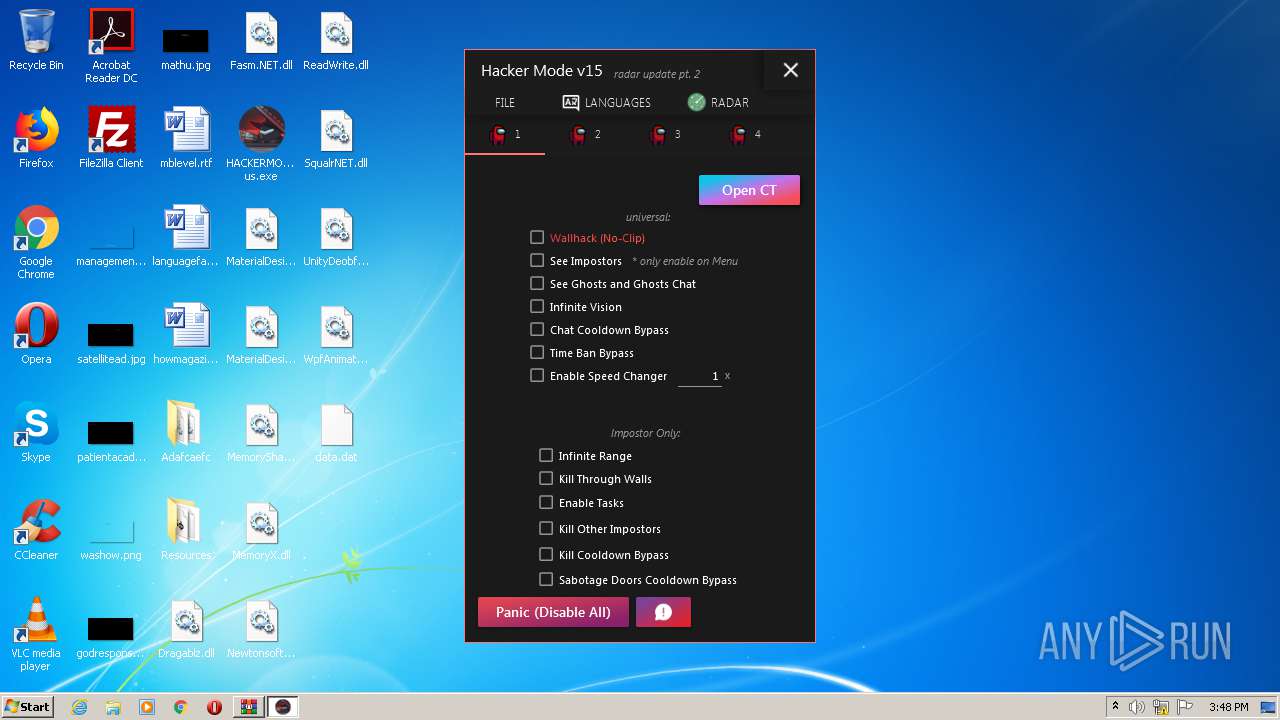
| 1292 | "C:\Users\admin\Desktop\HACKERMODE_among us.exe" | C:\Users\admin\Desktop\HACKERMODE_among us.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Hacker Mode (Among Us) Exit code: 4294967295 Version: 1.0.9.0 Modules
| |||||||||||||||
| 2012 | "C:\Windows\System32\MsSpellCheckingFacility.exe" -Embedding | C:\Windows\System32\MsSpellCheckingFacility.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Spell Checking Facility Exit code: 0 Version: 6.3.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2488 | "C:\Users\admin\Desktop\HACKERMODE_among us.exe" | C:\Users\admin\Desktop\HACKERMODE_among us.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Hacker Mode (Among Us) Exit code: 4294967295 Version: 1.0.9.0 Modules
| |||||||||||||||
| 2868 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\v15-release-haxormode.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3100 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
904
Read events
862
Write events
42
Delete events
0
Modification events
| (PID) Process: | (2868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2868) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\v15-release-haxormode.zip | |||
| (PID) Process: | (2868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1292) HACKERMODE_among us.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: HACKERMODE_among us.exe | |||
| (PID) Process: | (1292) HACKERMODE_among us.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\HACKERMODE_among us_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
8
Suspicious files
0
Text files
4
Unknown types
0
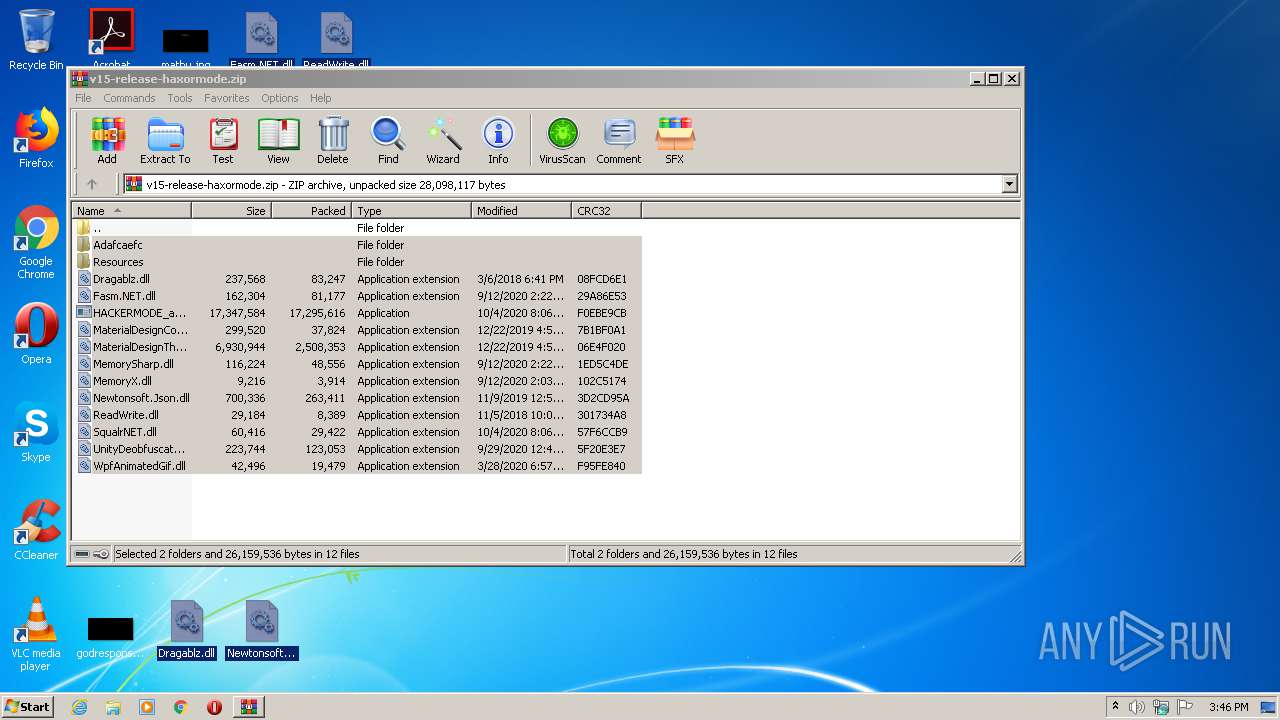
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2868 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2868.668\HACKERMODE_among us.exe | — | |
MD5:— | SHA256:— | |||
| 2868 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2868.668\MaterialDesignColors.dll | — | |
MD5:— | SHA256:— | |||
| 2868 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2868.668\MaterialDesignThemes.Wpf.dll | — | |
MD5:— | SHA256:— | |||
| 2868 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2868.668\MemorySharp.dll | — | |
MD5:— | SHA256:— | |||
| 2868 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2868.668\MemoryX.dll | — | |
MD5:— | SHA256:— | |||
| 2868 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2868.668\Newtonsoft.Json.dll | — | |
MD5:— | SHA256:— | |||
| 2868 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2868.668\ReadWrite.dll | — | |
MD5:— | SHA256:— | |||
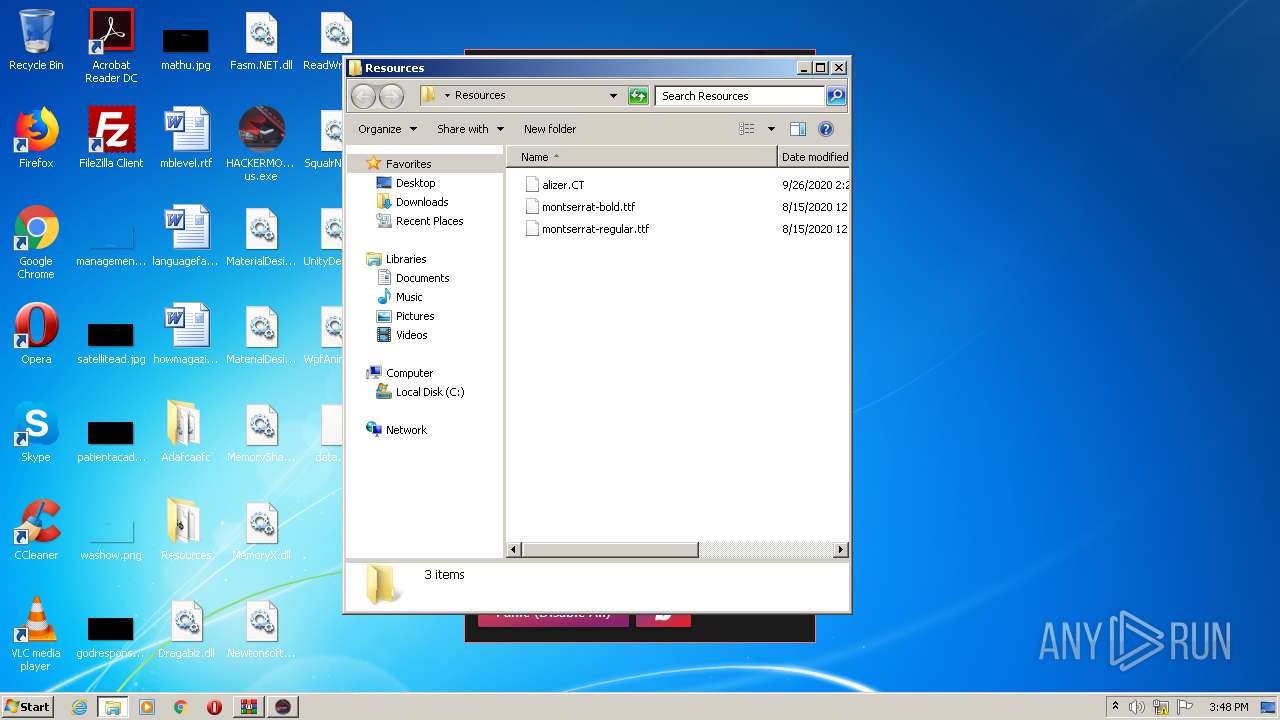
| 2868 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2868.668\Resources\alizer.CT | — | |
MD5:— | SHA256:— | |||
| 2868 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2868.668\Resources\montserrat-bold.ttf | — | |
MD5:— | SHA256:— | |||
| 2868 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2868.668\Resources\montserrat-regular.ttf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1292 | HACKERMODE_among us.exe | 104.23.98.190:443 | pastebin.com | Cloudflare Inc | US | malicious |
2488 | HACKERMODE_among us.exe | 104.23.99.190:443 | pastebin.com | Cloudflare Inc | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |