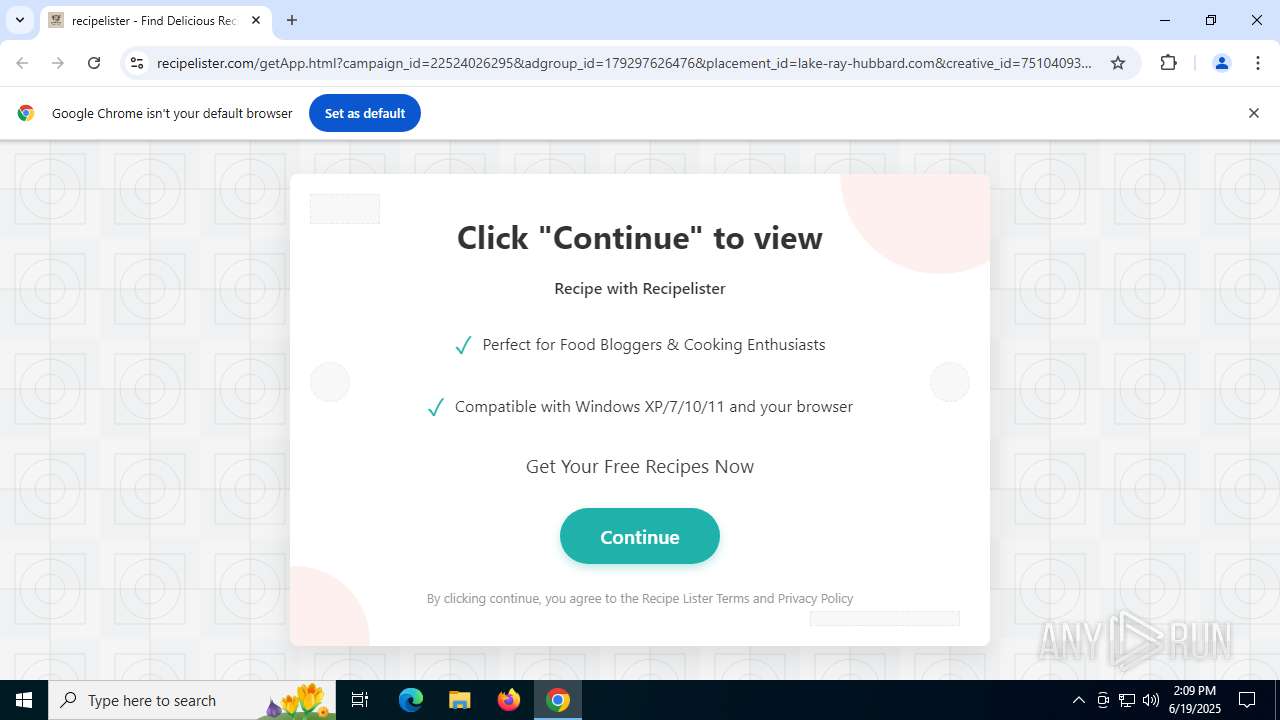
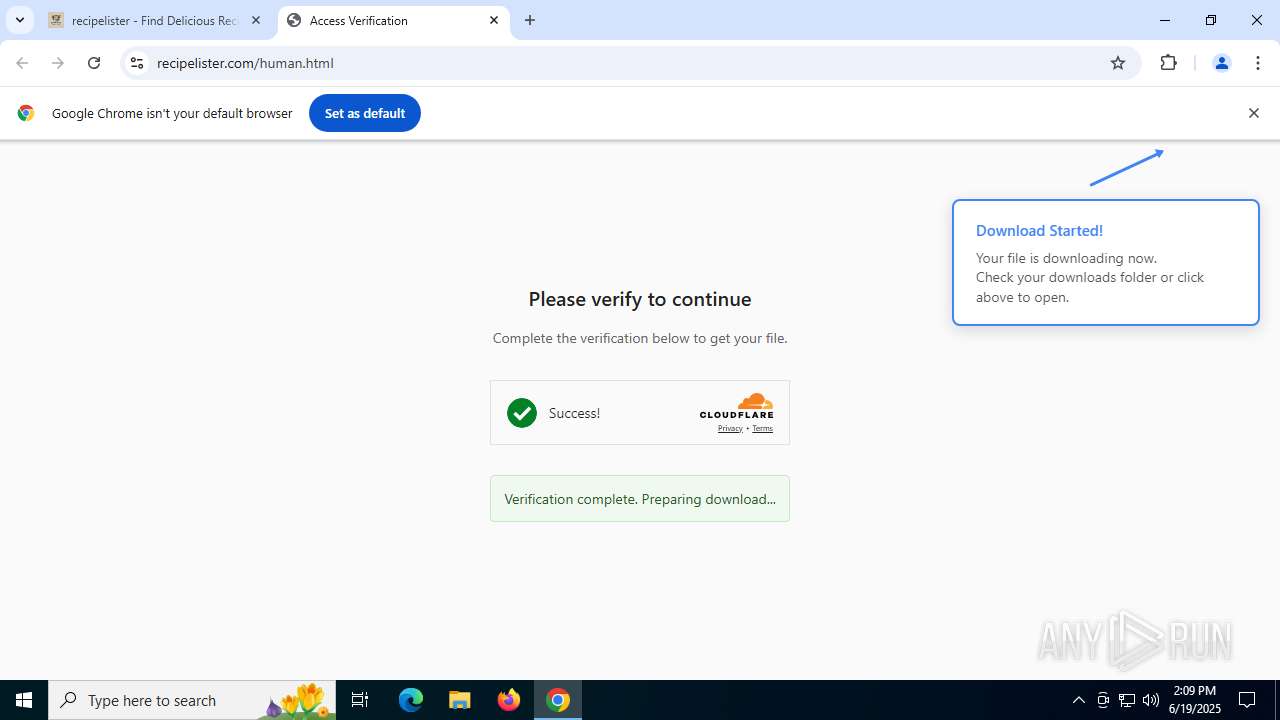
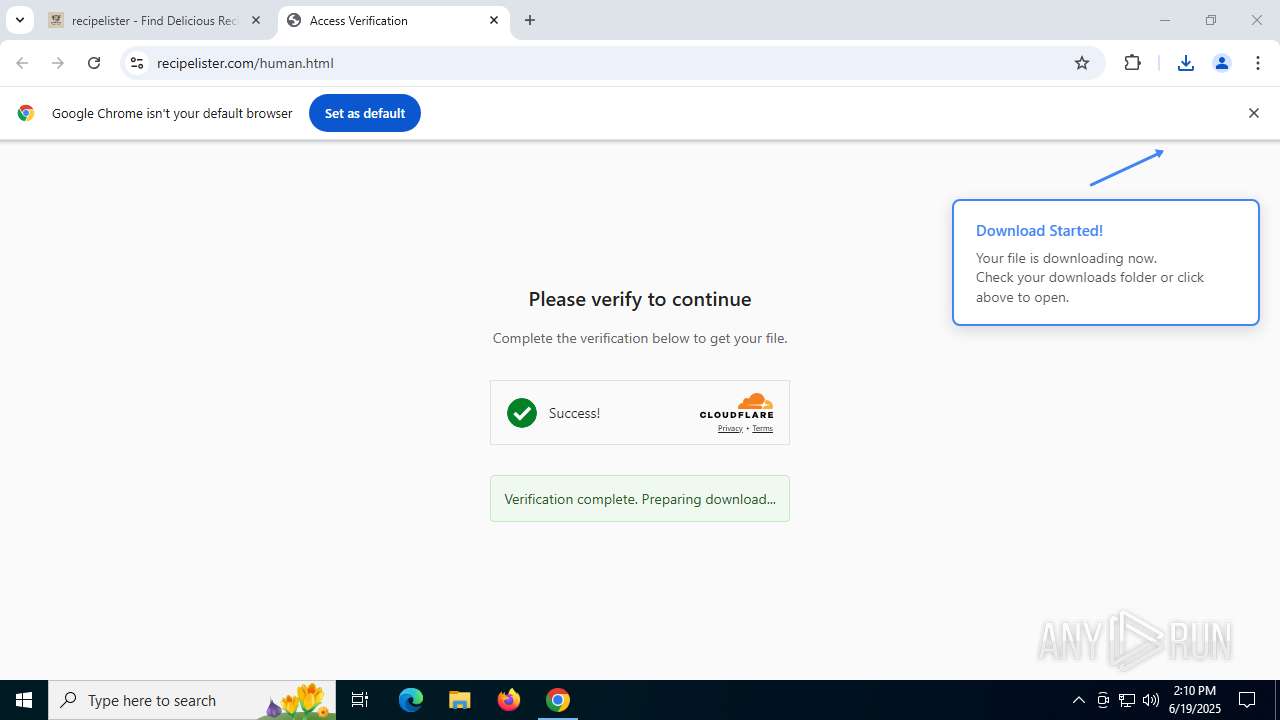
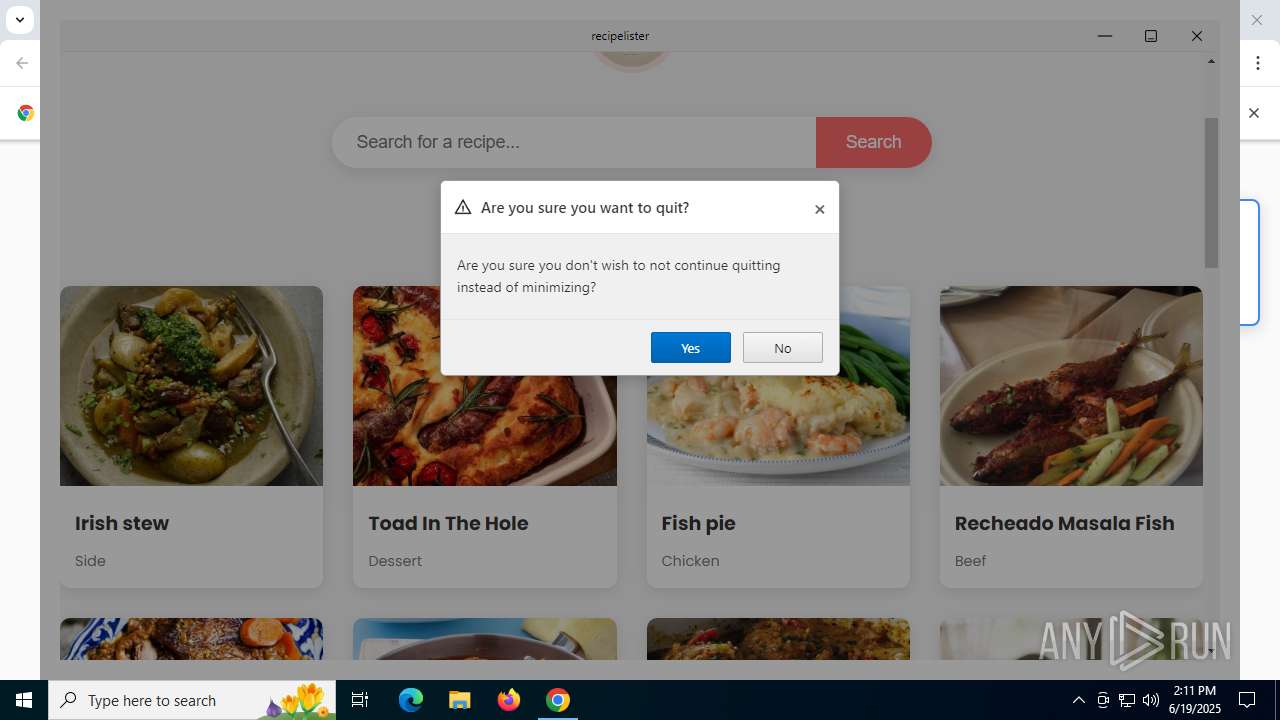
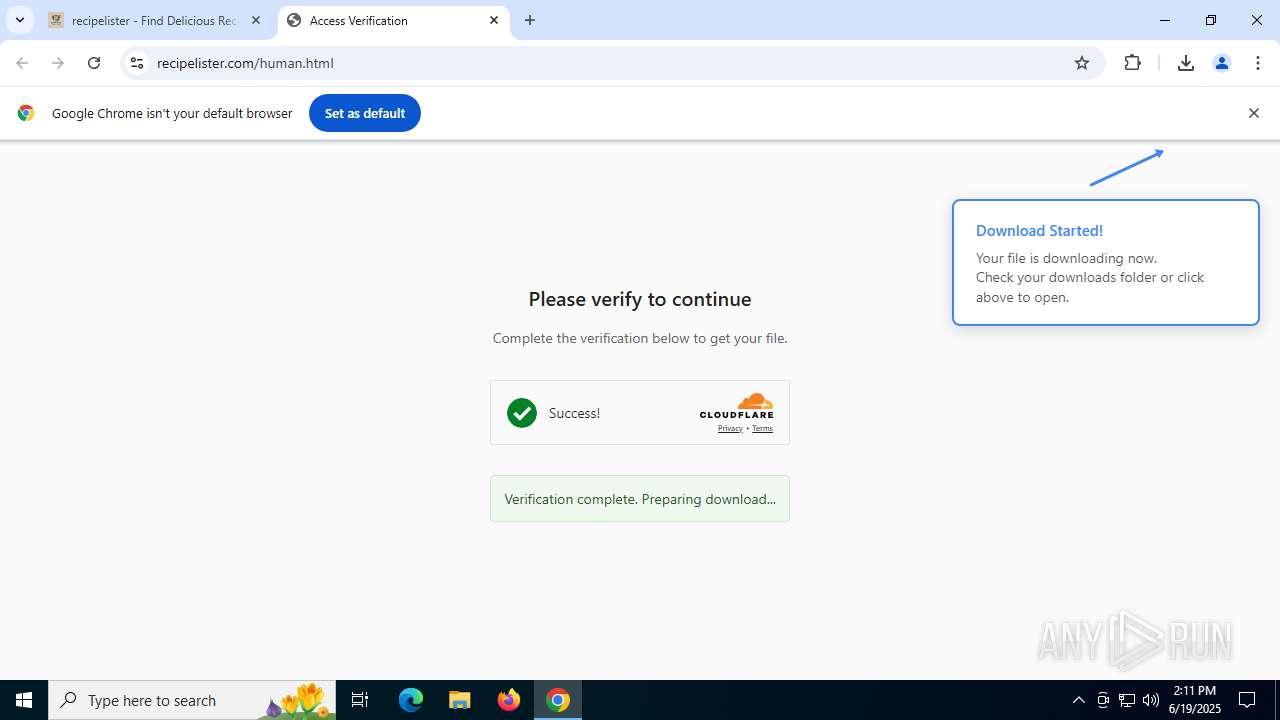
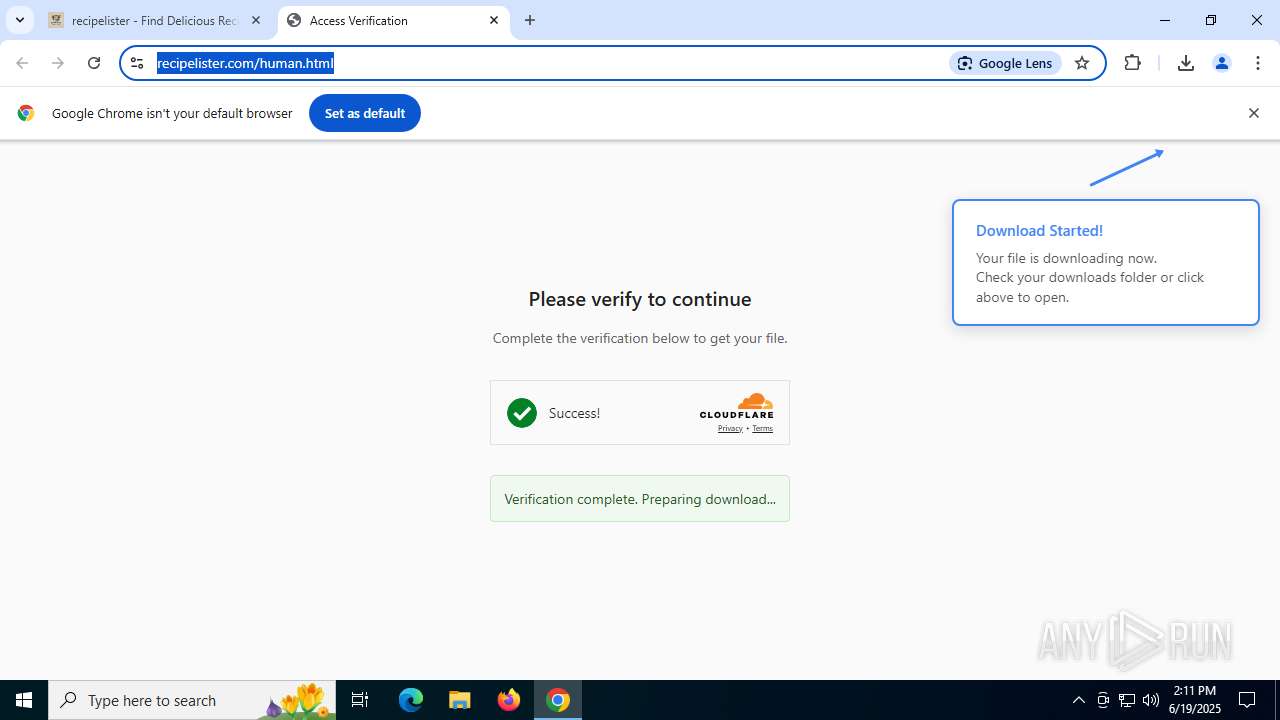
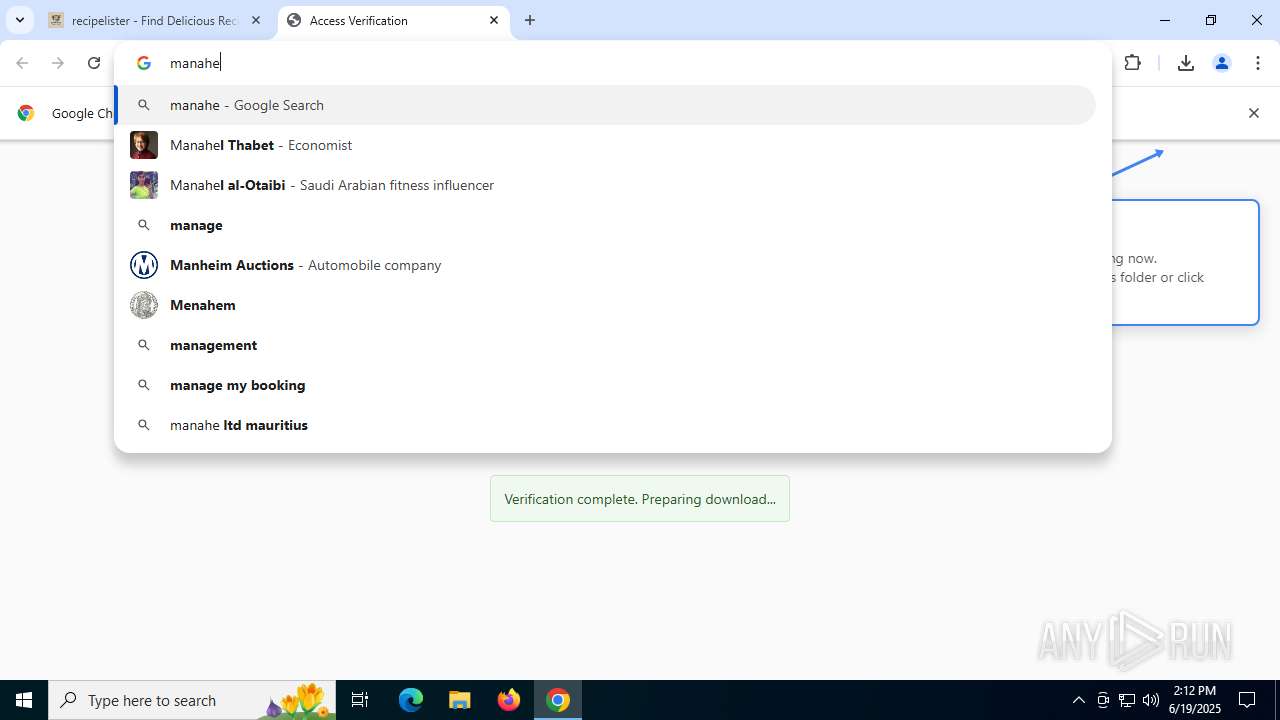
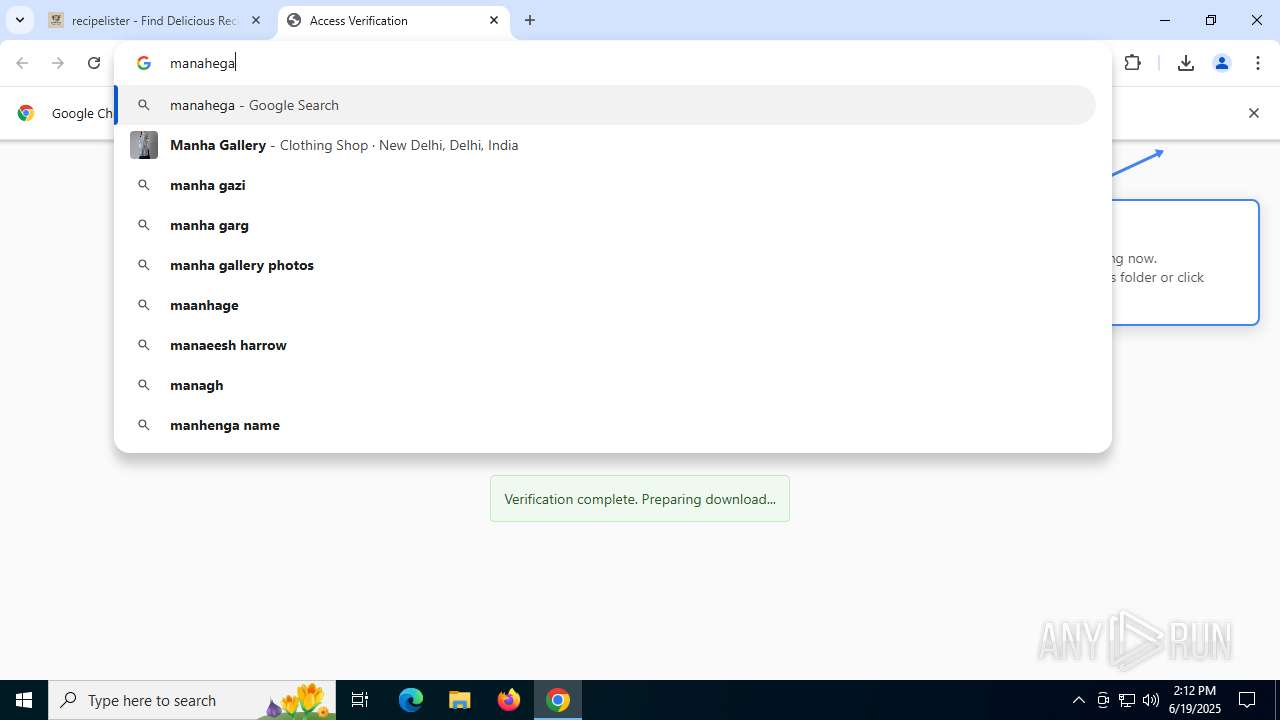
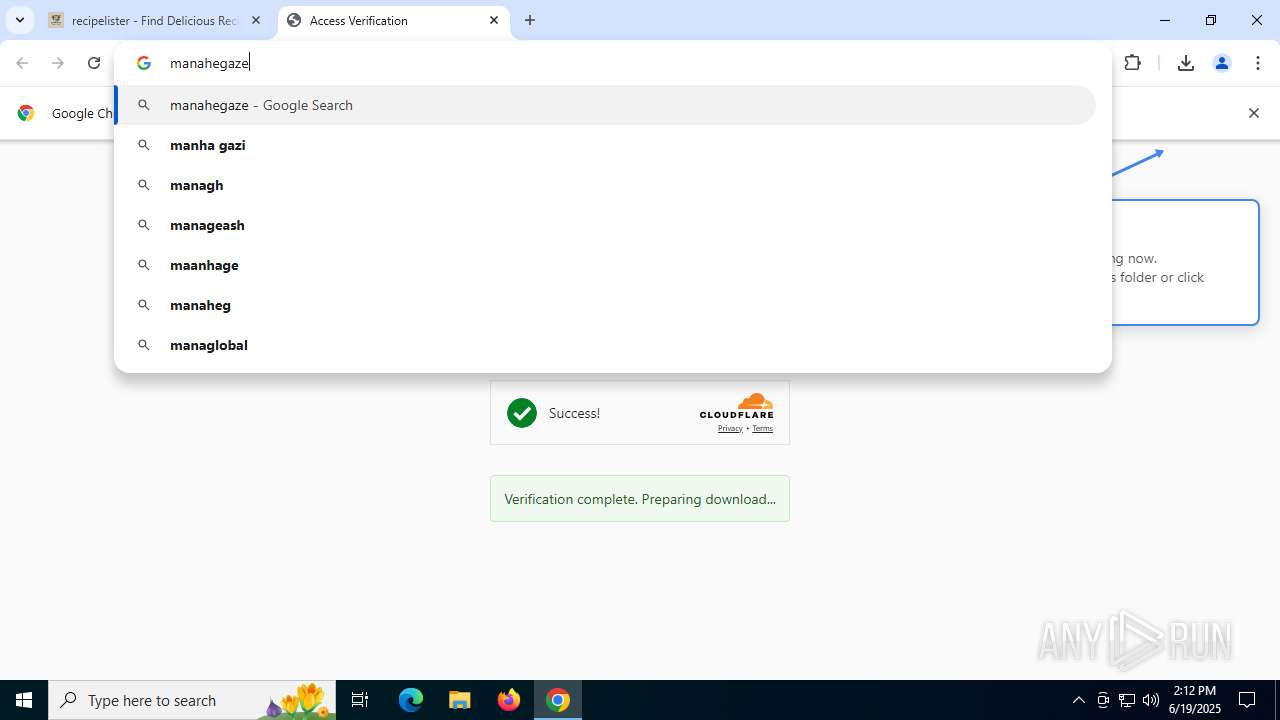
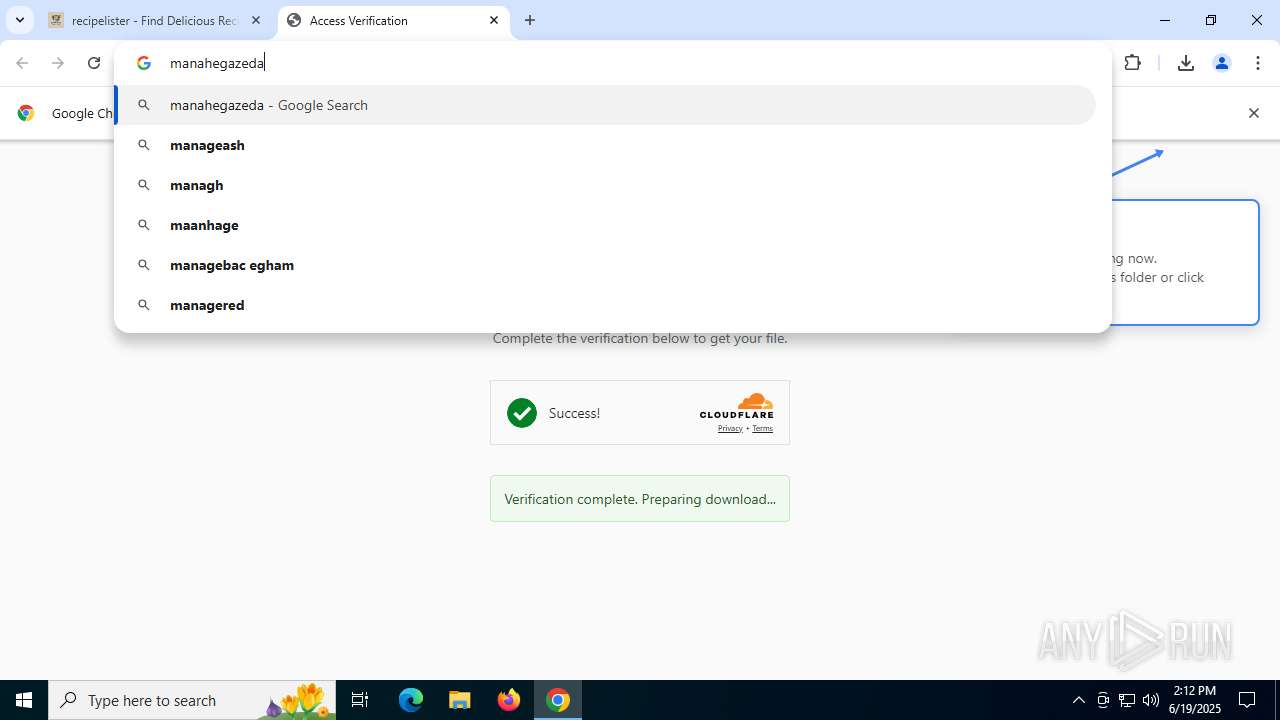
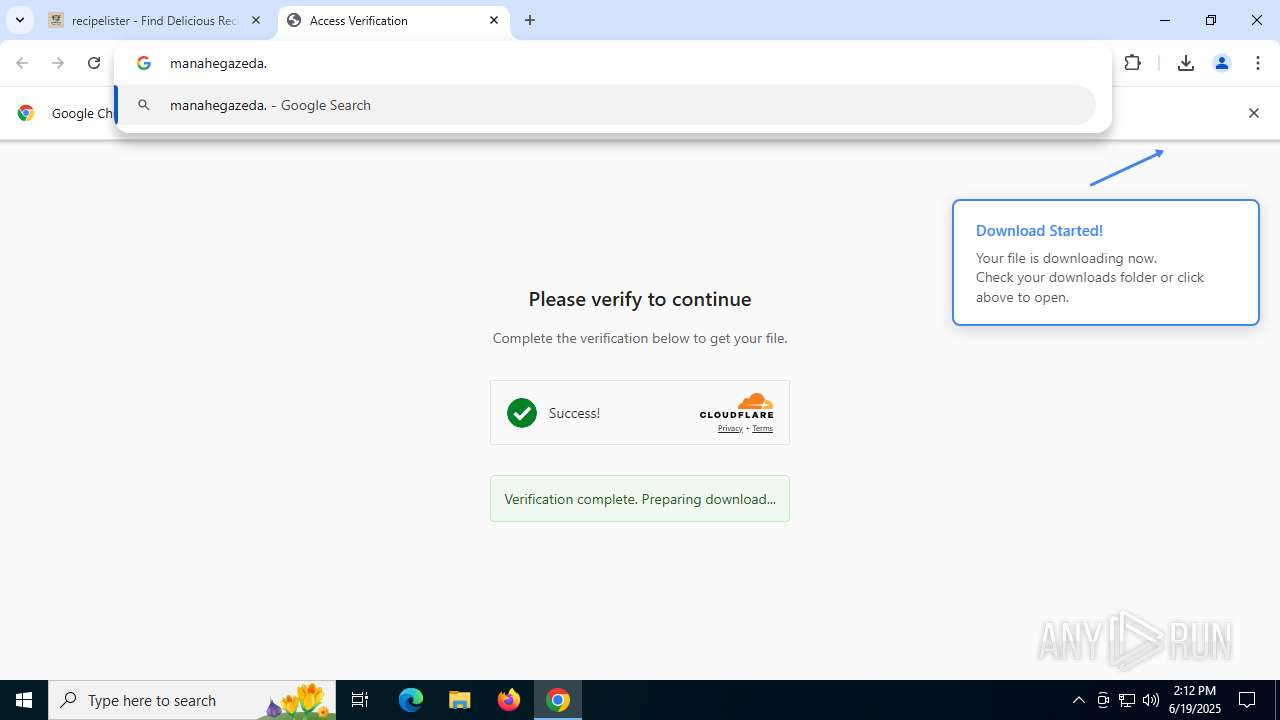
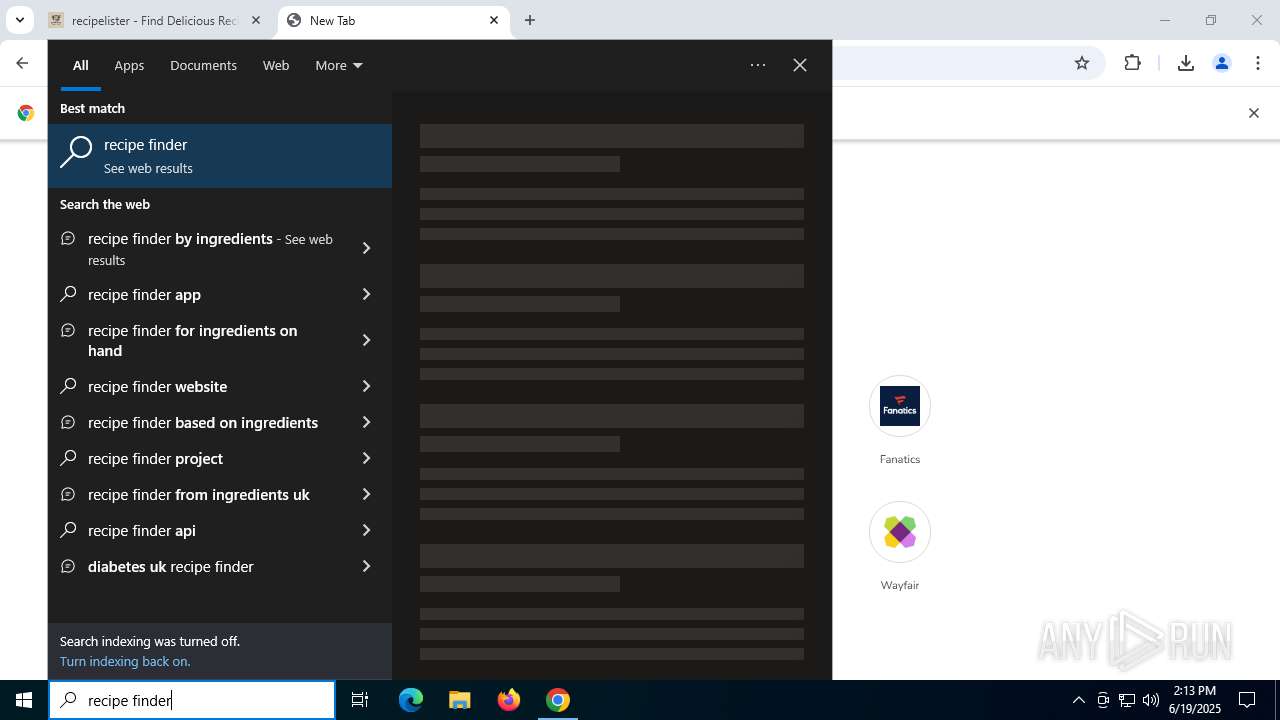
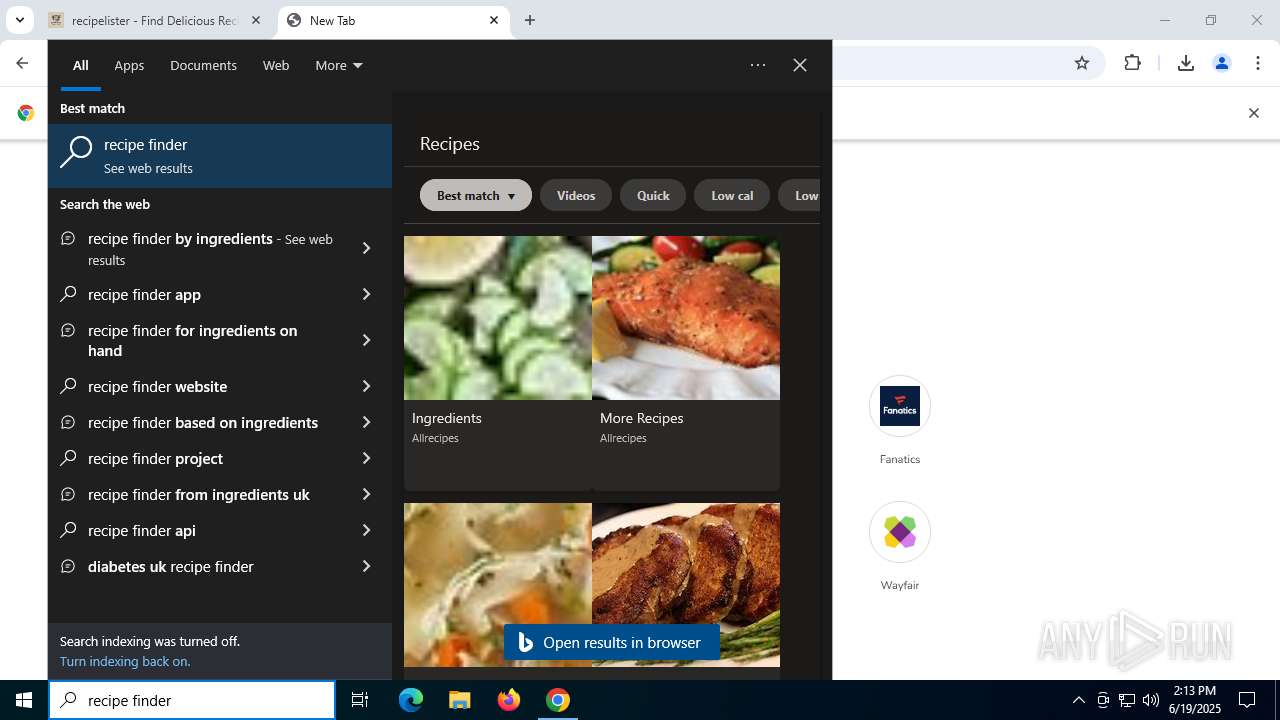
| URL: | recipelister.com/getApp.html?campaign_id=22524026295&adgroup_id=179297626476&placement_id=lake-ray-hubbard.com&creative_id=751040937583&rec=EAIaIQobChMI546LsOzmjQMVfaKOCB3-ByQSEAEYASAAEgItSvD_BwE&gad_source=5&gad_campaignid=22524026295&gclid=EAIaIQobChMI546LsOzmjQMVfaKOCB3-ByQSEAEYASAAEgItSvD_BwE |
| Full analysis: | https://app.any.run/tasks/ac3a7cec-910d-4bc2-927c-e37f8f3d7509 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2025, 14:09:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
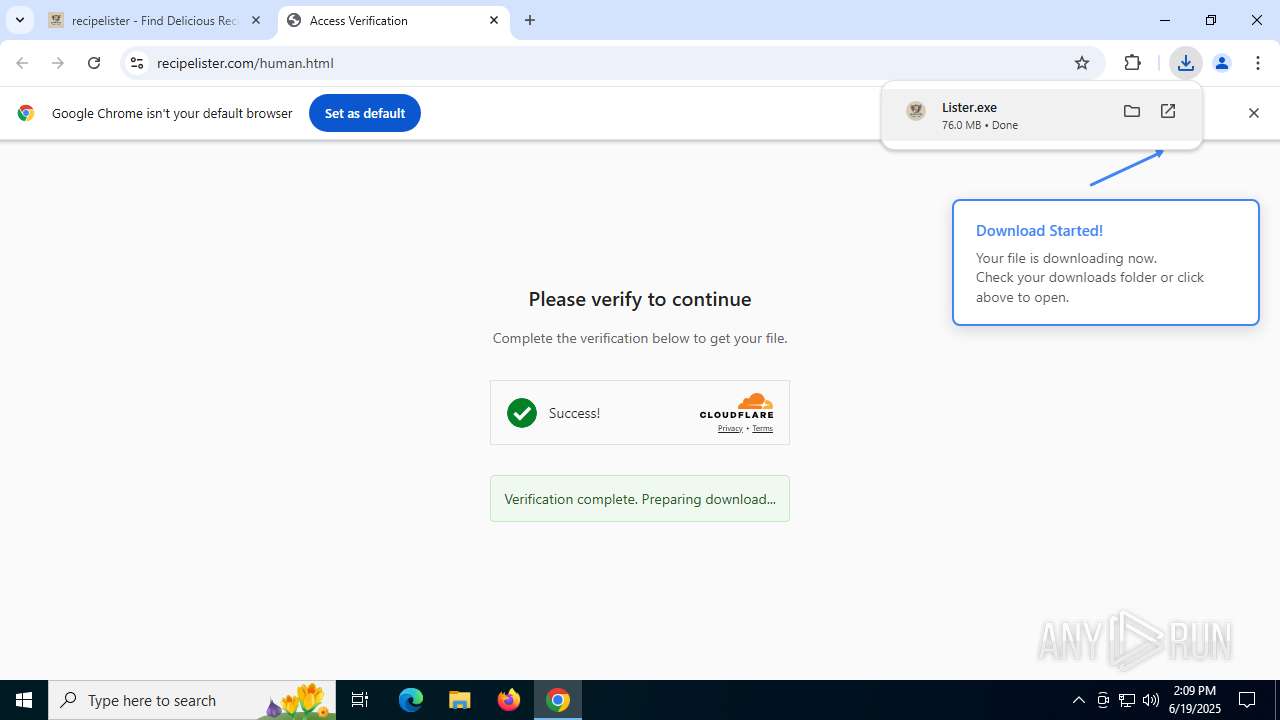
| MD5: | 4A6E10F4E65438ABE52D3EE19120440B |
| SHA1: | 151135CB49C2F3A3B6580EE9858CE9737BB2F674 |
| SHA256: | 2FCEF705FE204B48348E08CC726A3A0240A943E0EB1C361E6D0E222107B80B25 |
| SSDEEP: | 6:Sr3JNYXzgAQMrTSkwAJzkLz9fInTDseYXABHNkLz9fInTn:Sr5Mzg6vJgLZgncSHOLZgnT |
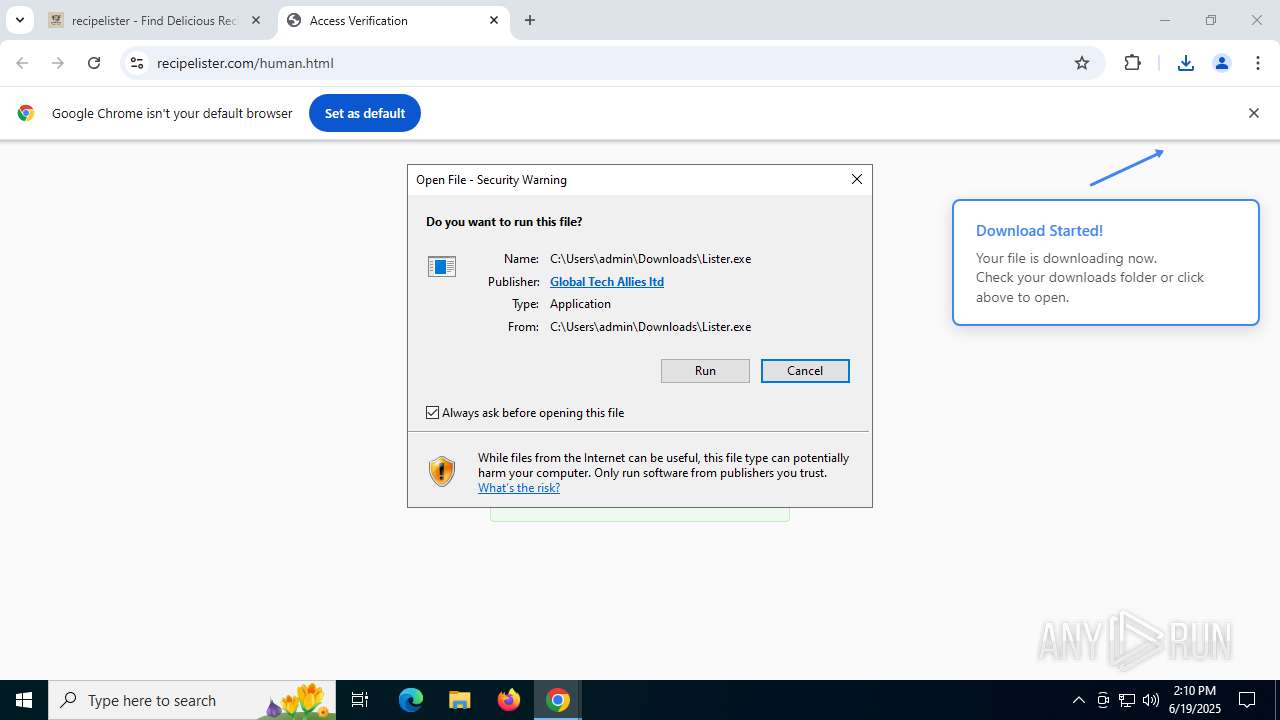
MALICIOUS
Executing a file with an untrusted certificate
- Lister.exe (PID: 2696)
SUSPICIOUS
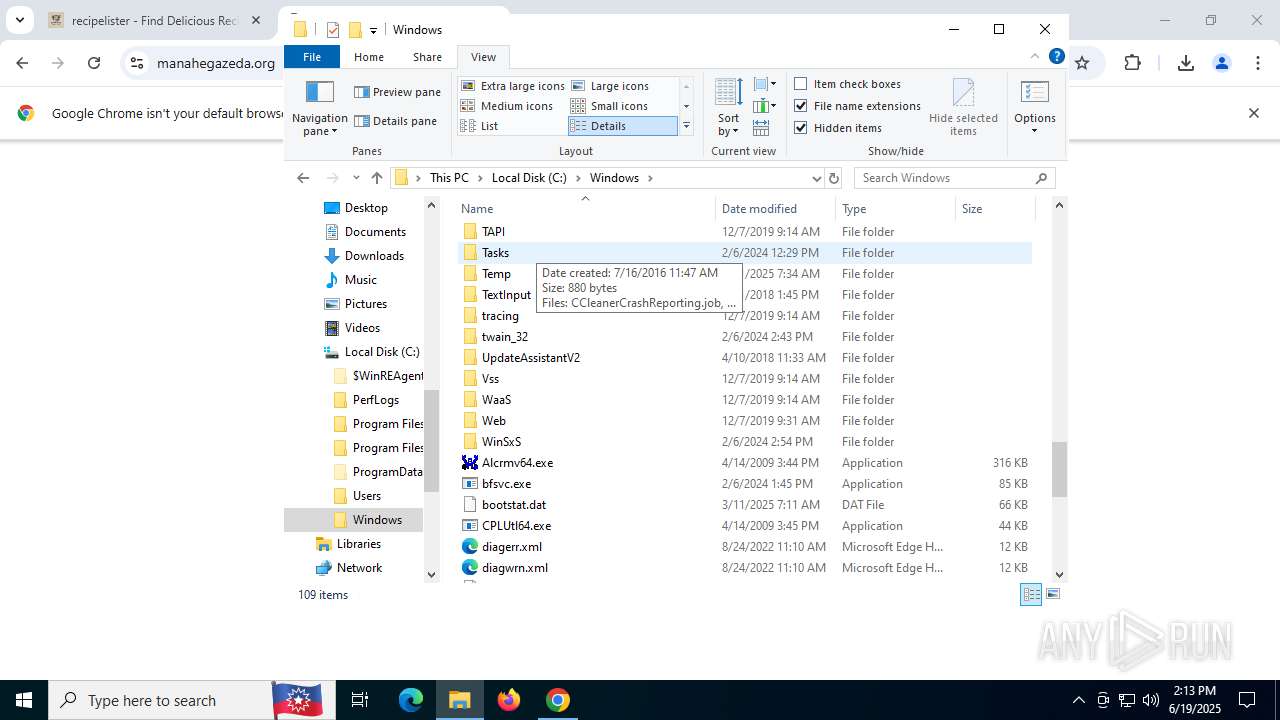
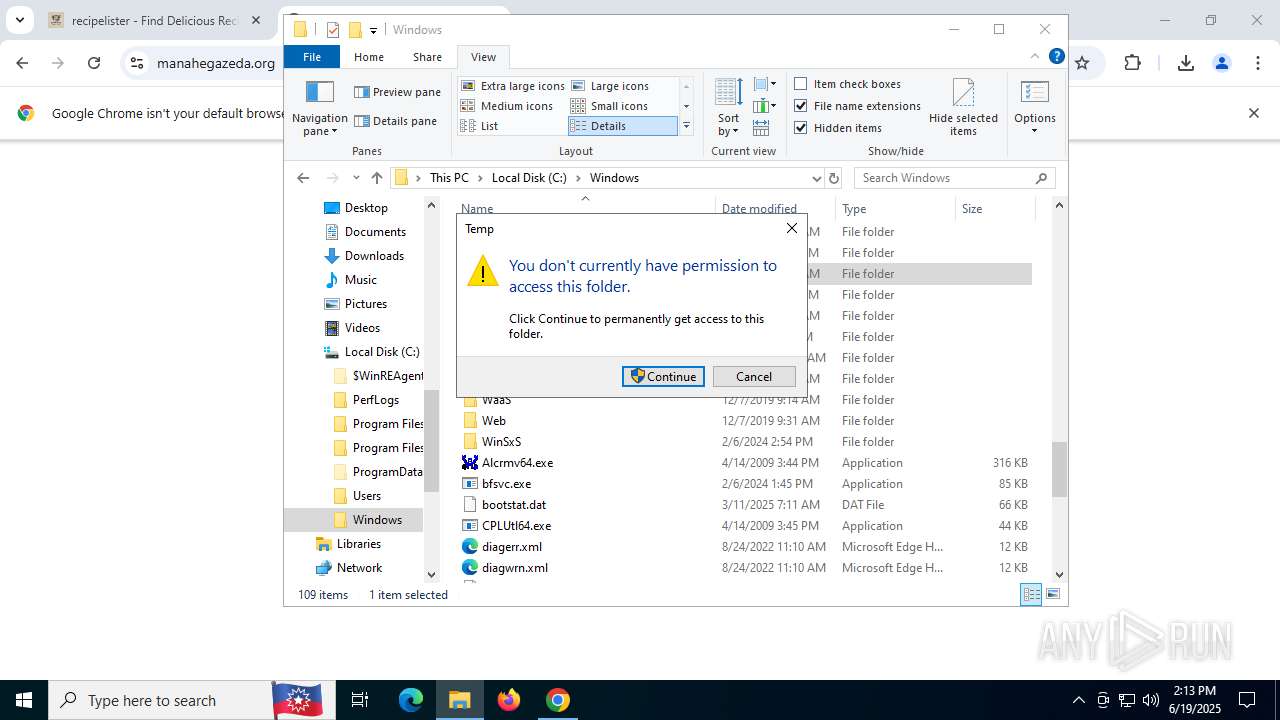
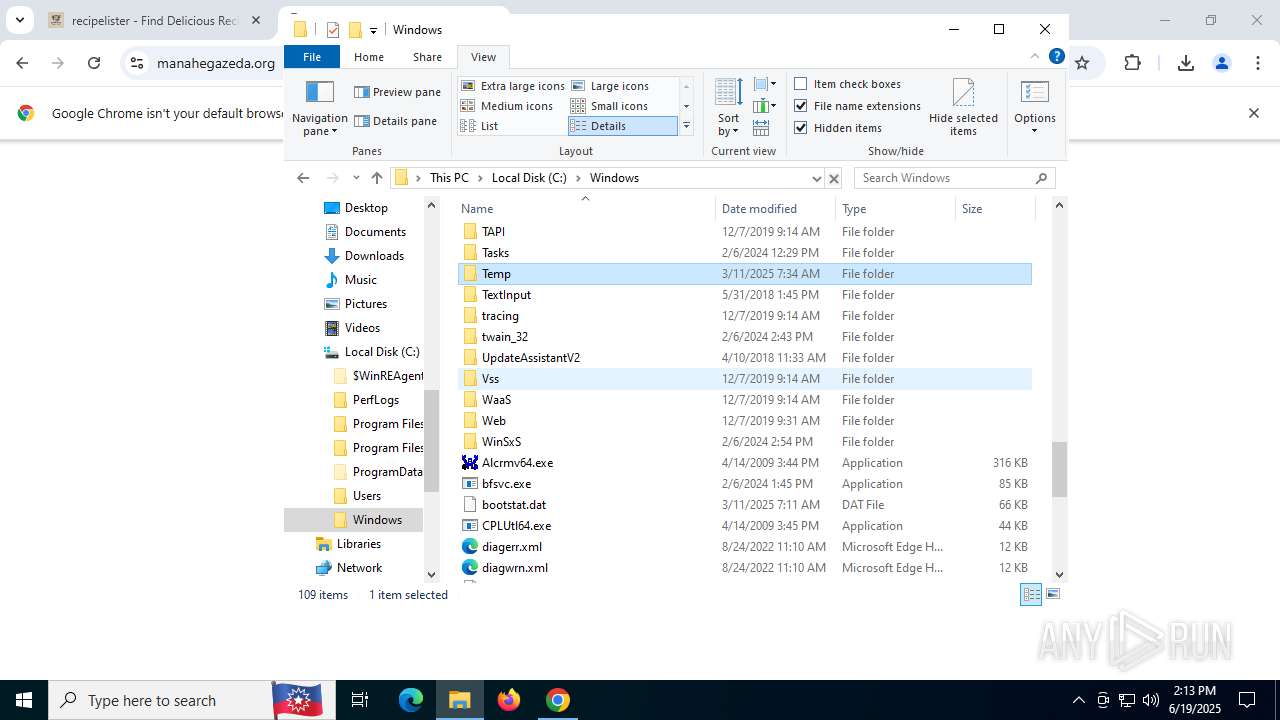
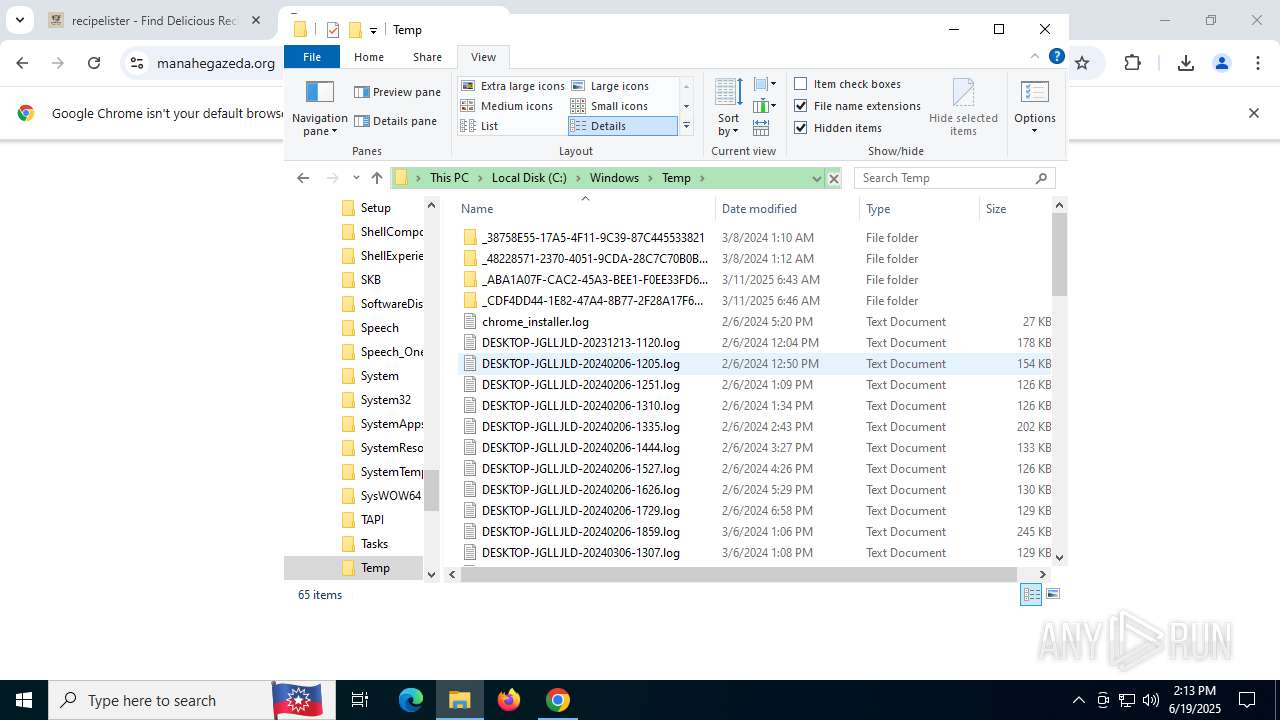
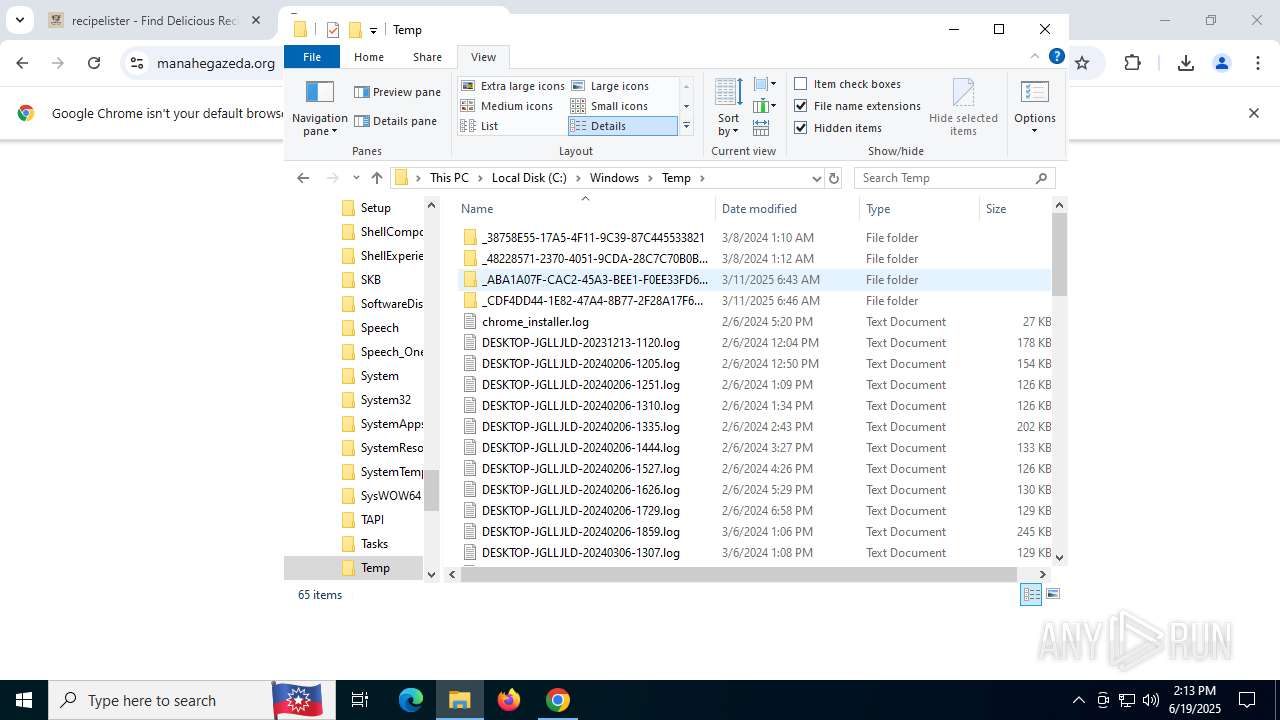
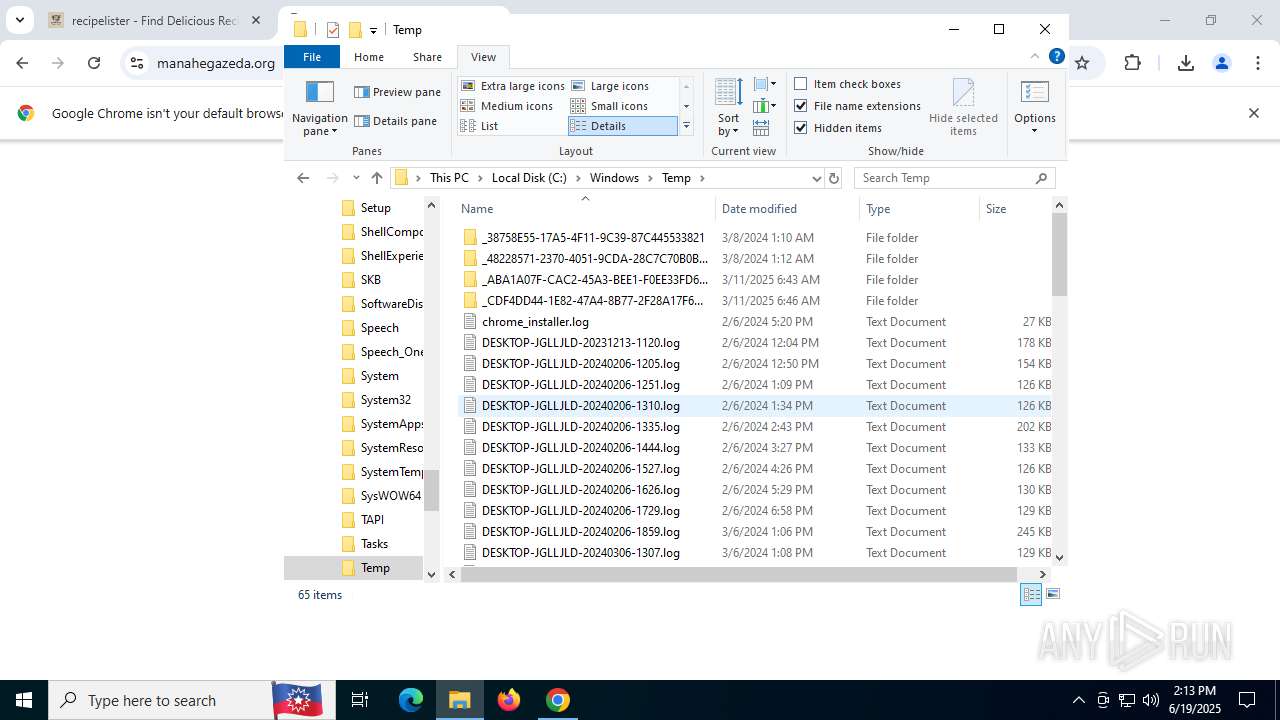
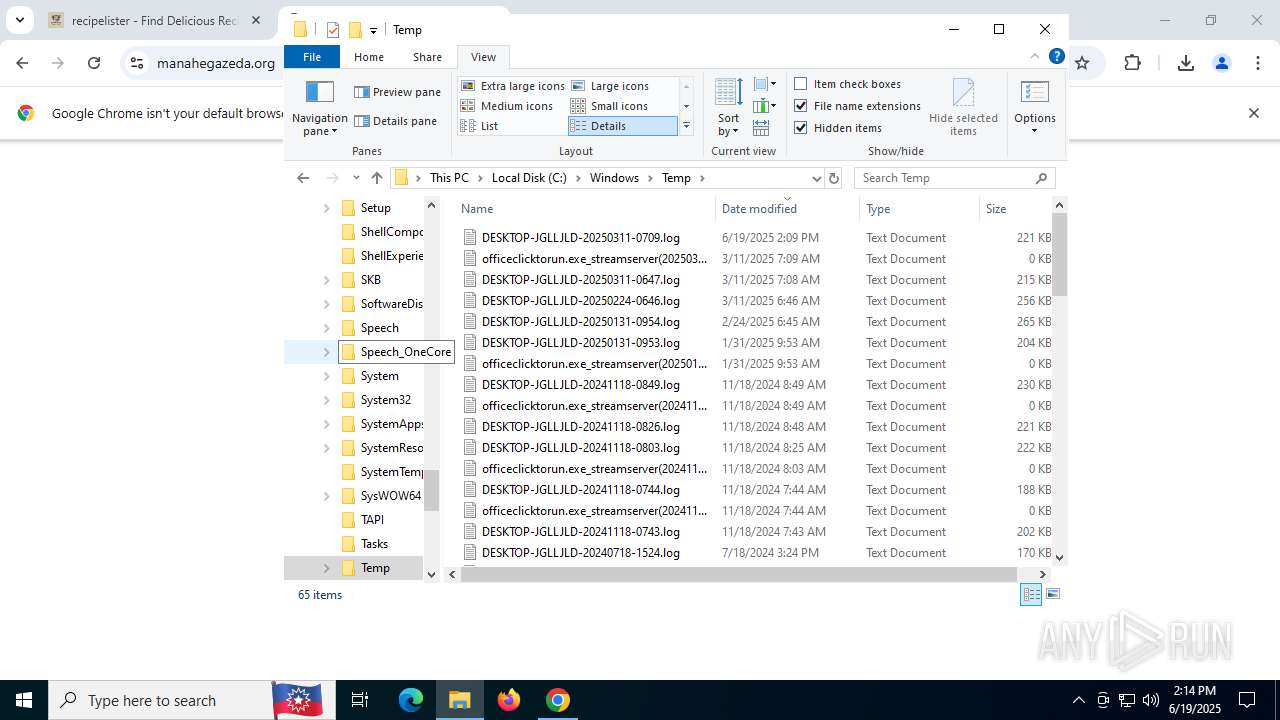
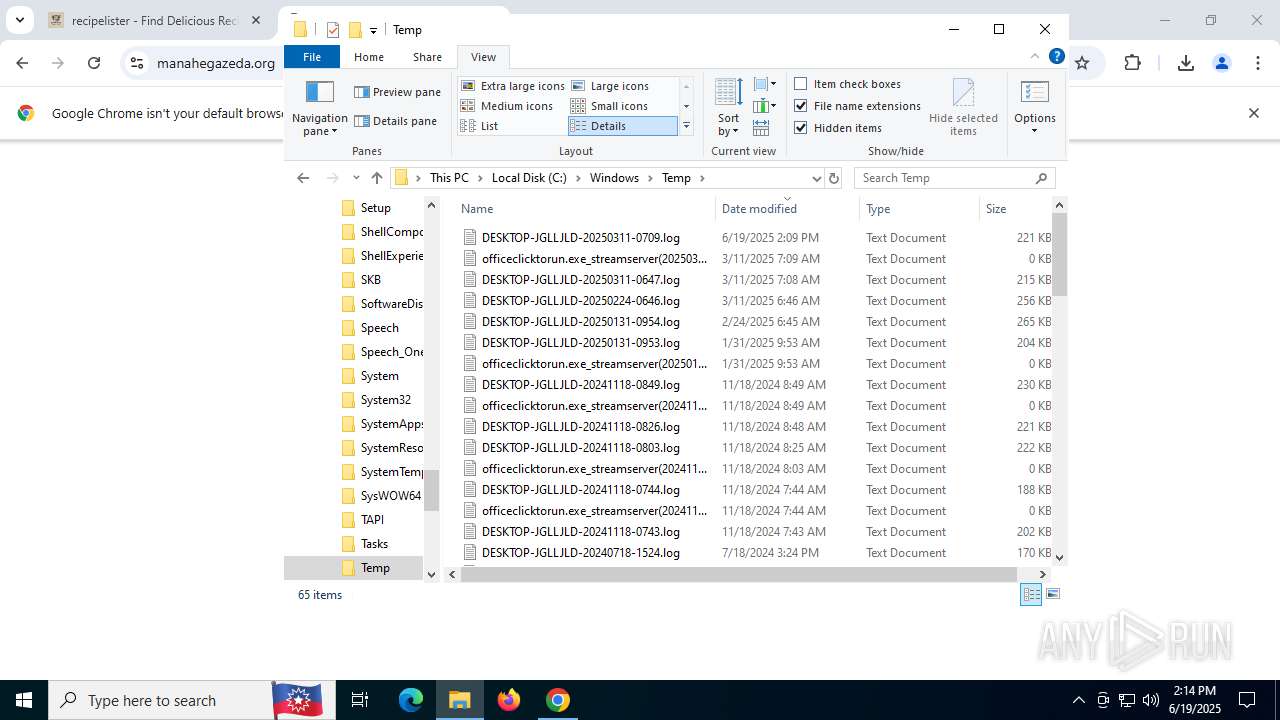
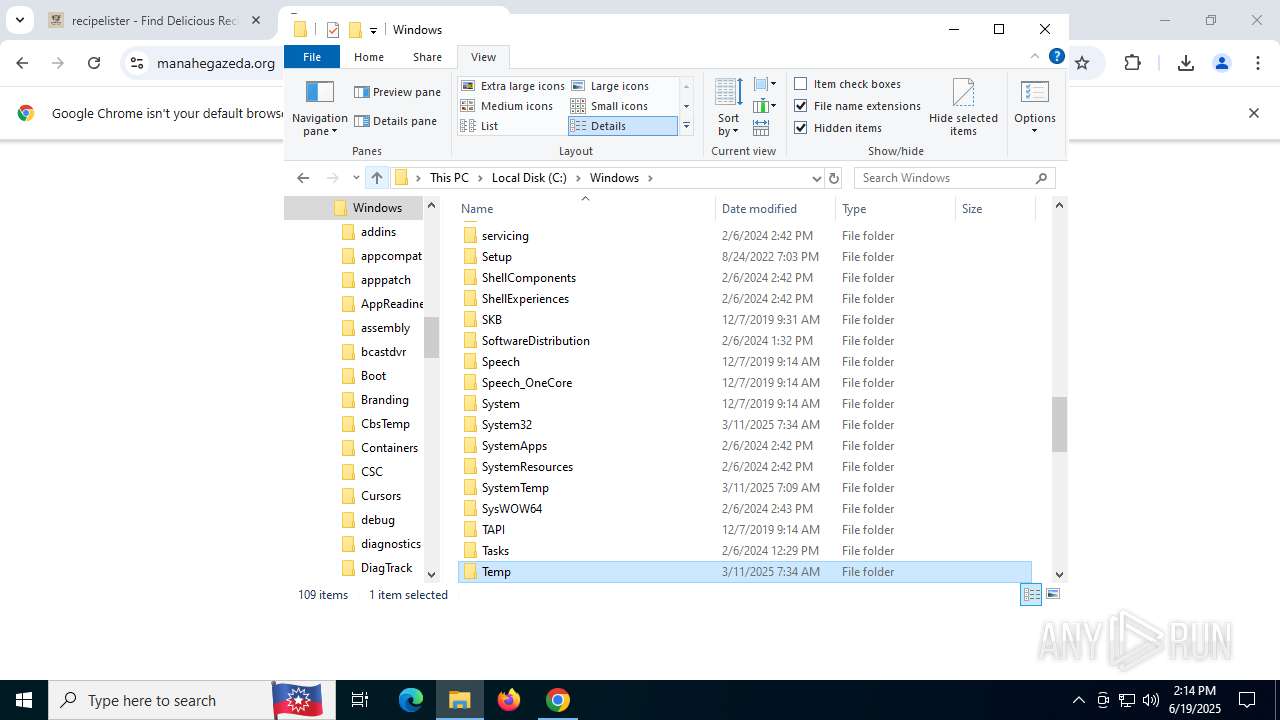
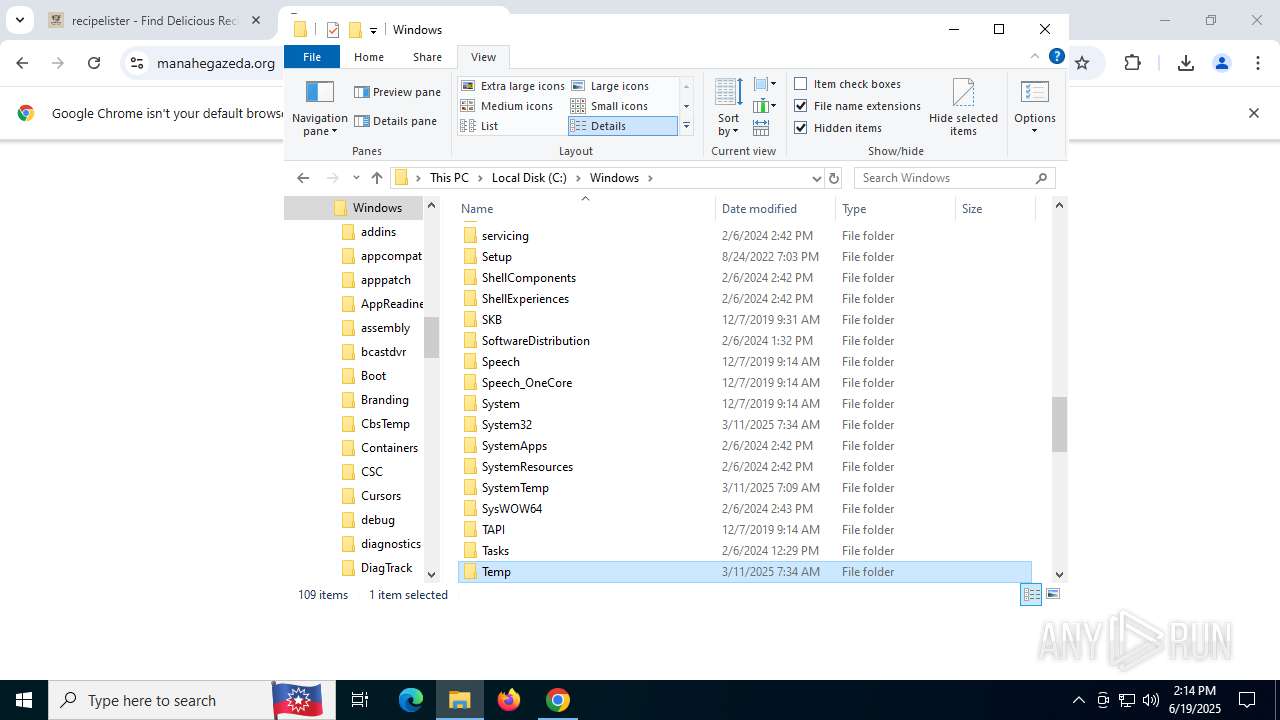
Malware-specific behavior (creating "System.dll" in Temp)
- Lister.exe (PID: 2696)
Drops 7-zip archiver for unpacking
- Lister.exe (PID: 2696)
The process creates files with name similar to system file names
- Lister.exe (PID: 2696)
Executable content was dropped or overwritten
- Lister.exe (PID: 2696)
Process drops legitimate windows executable
- Lister.exe (PID: 2696)
Reads security settings of Internet Explorer
- Lister.exe (PID: 2696)
- Recipe Finder - Recipe Lister.exe (PID: 3936)
- Recipe Finder - Recipe Lister.exe (PID: 4892)
There is functionality for taking screenshot (YARA)
- Recipe Finder - Recipe Lister.exe (PID: 1880)
- Lister.exe (PID: 2696)
Application launched itself
- Recipe Finder - Recipe Lister.exe (PID: 3936)
INFO
Checks supported languages
- Lister.exe (PID: 2696)
- Recipe Finder - Recipe Lister.exe (PID: 2148)
- Recipe Finder - Recipe Lister.exe (PID: 3936)
- Recipe Finder - Recipe Lister.exe (PID: 1880)
- Recipe Finder - Recipe Lister.exe (PID: 7448)
- Recipe Finder - Recipe Lister.exe (PID: 4892)
- Recipe Finder - Recipe Lister.exe (PID: 6620)
The sample compiled with english language support
- Lister.exe (PID: 2696)
- chrome.exe (PID: 7740)
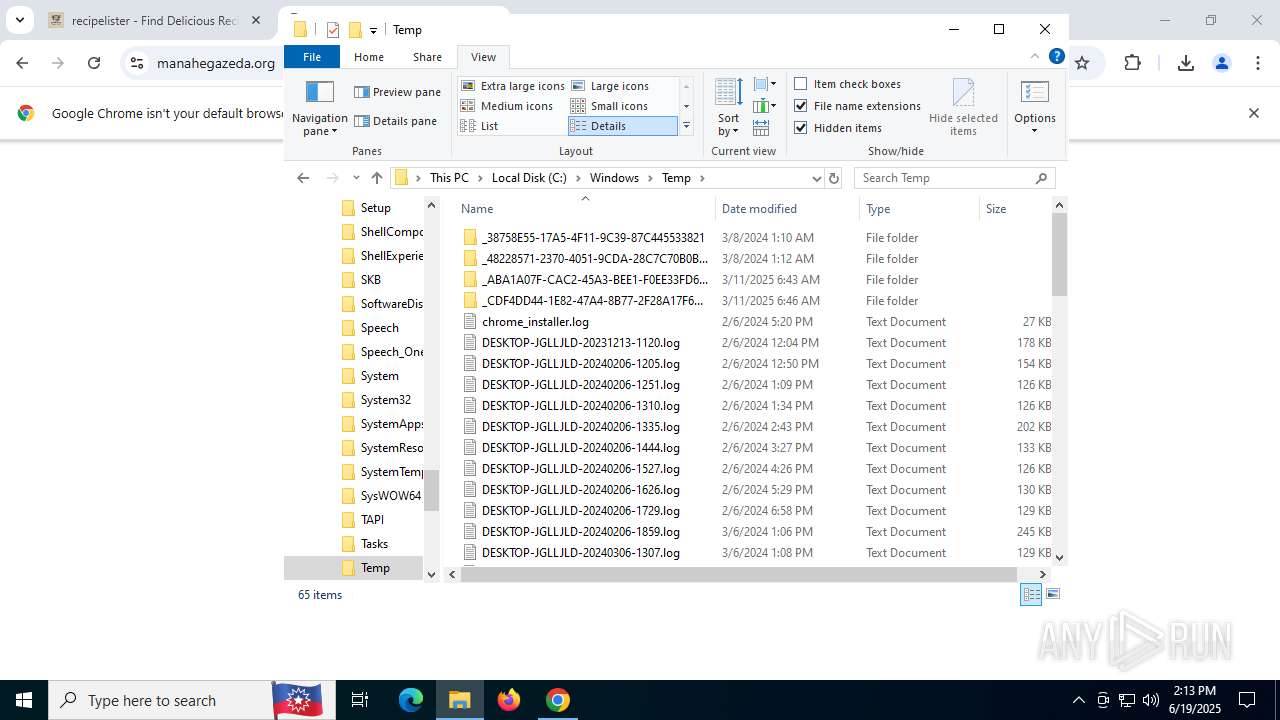
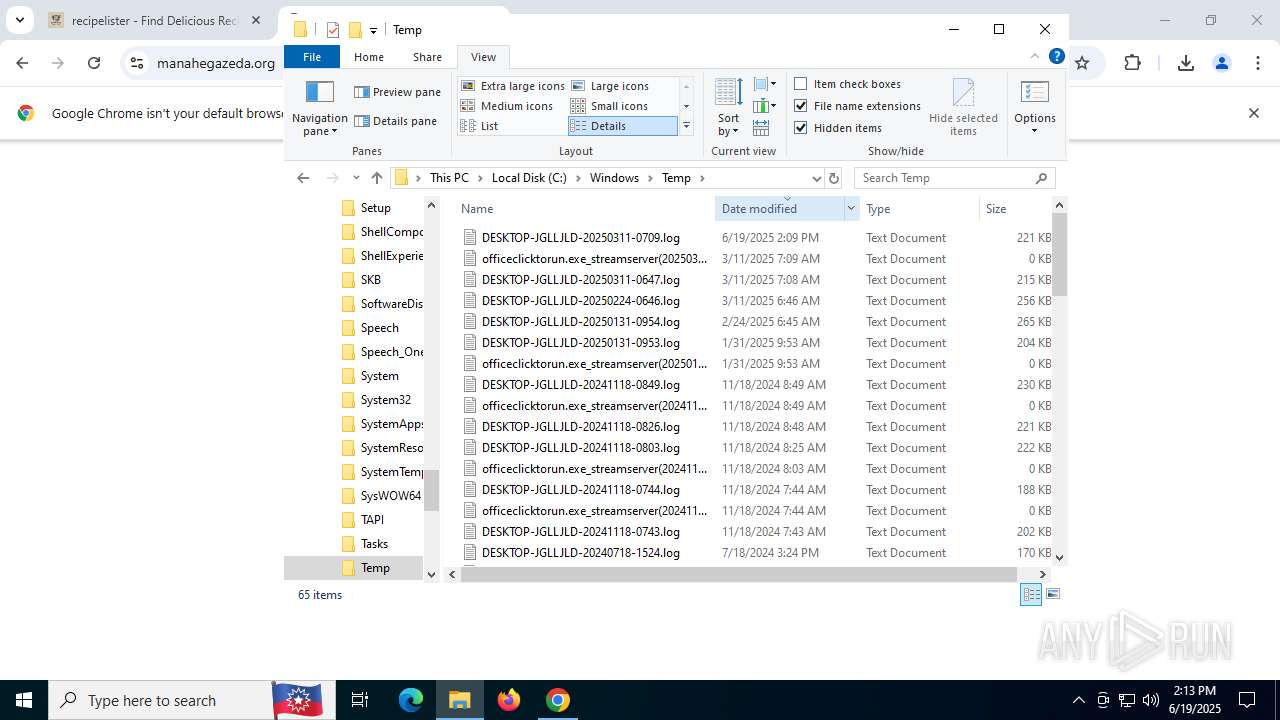
Create files in a temporary directory
- Lister.exe (PID: 2696)
- Recipe Finder - Recipe Lister.exe (PID: 3936)
Executable content was dropped or overwritten
- chrome.exe (PID: 1604)
- chrome.exe (PID: 7740)
Creates files or folders in the user directory
- Recipe Finder - Recipe Lister.exe (PID: 3936)
- Recipe Finder - Recipe Lister.exe (PID: 2148)
- Recipe Finder - Recipe Lister.exe (PID: 4892)
Process checks computer location settings
- Recipe Finder - Recipe Lister.exe (PID: 3936)
- Recipe Finder - Recipe Lister.exe (PID: 6620)
- Recipe Finder - Recipe Lister.exe (PID: 7448)
Reads the computer name
- Recipe Finder - Recipe Lister.exe (PID: 2148)
- Recipe Finder - Recipe Lister.exe (PID: 3936)
- Recipe Finder - Recipe Lister.exe (PID: 1880)
- Lister.exe (PID: 2696)
- Recipe Finder - Recipe Lister.exe (PID: 4892)
Application launched itself
- chrome.exe (PID: 1604)
Reads Environment values
- Recipe Finder - Recipe Lister.exe (PID: 3936)
- Recipe Finder - Recipe Lister.exe (PID: 4892)
Reads product name
- Recipe Finder - Recipe Lister.exe (PID: 3936)
Node.js compiler has been detected
- Recipe Finder - Recipe Lister.exe (PID: 3936)
- Recipe Finder - Recipe Lister.exe (PID: 1880)
- Recipe Finder - Recipe Lister.exe (PID: 2148)
- Recipe Finder - Recipe Lister.exe (PID: 6620)
Reads the software policy settings
- slui.exe (PID: 7232)
- Recipe Finder - Recipe Lister.exe (PID: 4892)
Checks proxy server information
- slui.exe (PID: 7232)
- Recipe Finder - Recipe Lister.exe (PID: 3936)
Reads the machine GUID from the registry
- Recipe Finder - Recipe Lister.exe (PID: 3936)
- Recipe Finder - Recipe Lister.exe (PID: 4892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
196
Monitored processes
42
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x220,0x224,0x228,0x1c0,0x1fc,0x7ffc437bfff8,0x7ffc437c0004,0x7ffc437c0010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=4496,i,16975013446637296884,10121996911036106408,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4544 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "recipelister.com/getApp.html?campaign_id=22524026295&adgroup_id=179297626476&placement_id=lake-ray-hubbard.com&creative_id=751040937583&rec=EAIaIQobChMI546LsOzmjQMVfaKOCB3-ByQSEAEYASAAEgItSvD_BwE&gad_source=5&gad_campaignid=22524026295&gclid=EAIaIQobChMI546LsOzmjQMVfaKOCB3-ByQSEAEYASAAEgItSvD_BwE" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1632 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --field-trial-handle=5116,i,16975013446637296884,10121996911036106408,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1880 | "C:\Users\admin\AppData\Local\Temp\2w1rXpxZnwDUwuTeNvdD6FUkeI0\Recipe Finder - Recipe Lister.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\recipe-finder" --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1684 --field-trial-handle=1688,i,14972602053257040536,5962038760801190758,262144 --enable-features=kWebSQLAccess --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version /prefetch:2 | C:\Users\admin\AppData\Local\Temp\2w1rXpxZnwDUwuTeNvdD6FUkeI0\Recipe Finder - Recipe Lister.exe | — | Recipe Finder - Recipe Lister.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: LOW Description: Recipe Finder - Recipe Lister Version: 1.0.0 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=2272,i,16975013446637296884,10121996911036106408,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2300 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2148 | "C:\Users\admin\AppData\Local\Temp\2w1rXpxZnwDUwuTeNvdD6FUkeI0\Recipe Finder - Recipe Lister.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\recipe-finder" --mojo-platform-channel-handle=2072 --field-trial-handle=1688,i,14972602053257040536,5962038760801190758,262144 --enable-features=kWebSQLAccess --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version /prefetch:8 | C:\Users\admin\AppData\Local\Temp\2w1rXpxZnwDUwuTeNvdD6FUkeI0\Recipe Finder - Recipe Lister.exe | Recipe Finder - Recipe Lister.exe | ||||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: Recipe Finder - Recipe Lister Version: 1.0.0 Modules
| |||||||||||||||
| 2288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=4520,i,16975013446637296884,10121996911036106408,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=6388 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5440,i,16975013446637296884,10121996911036106408,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5448 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
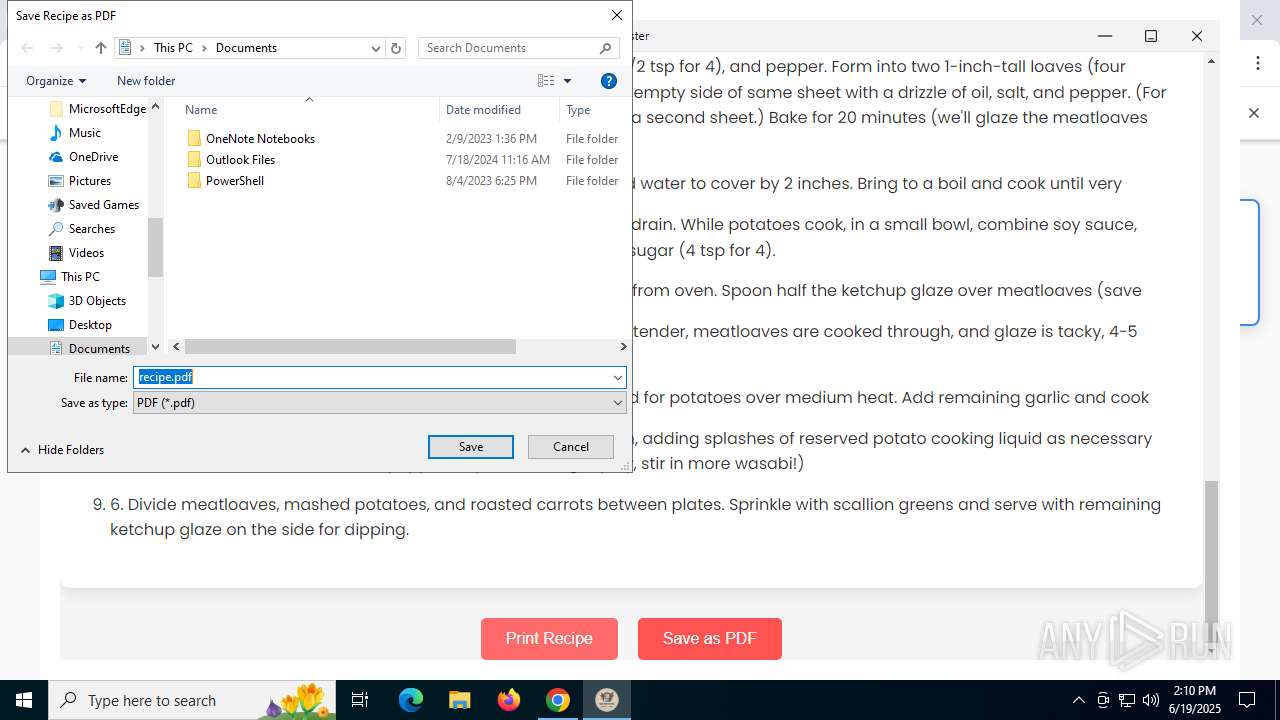
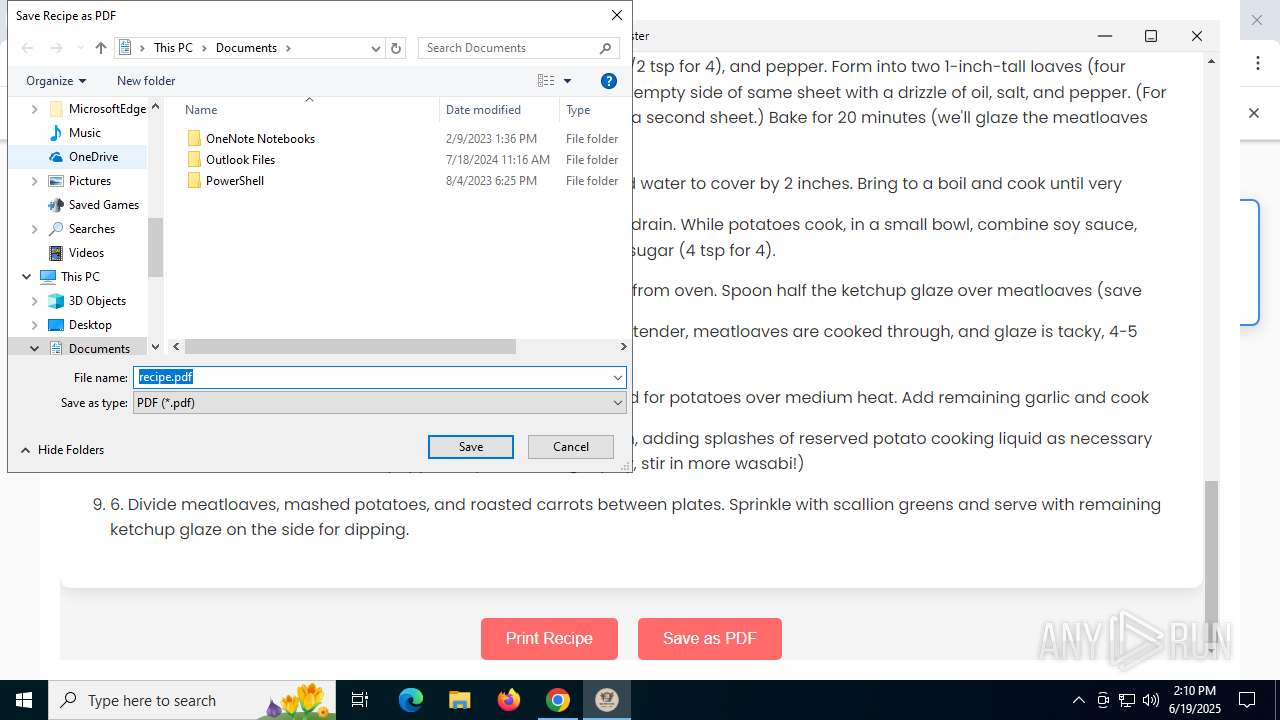
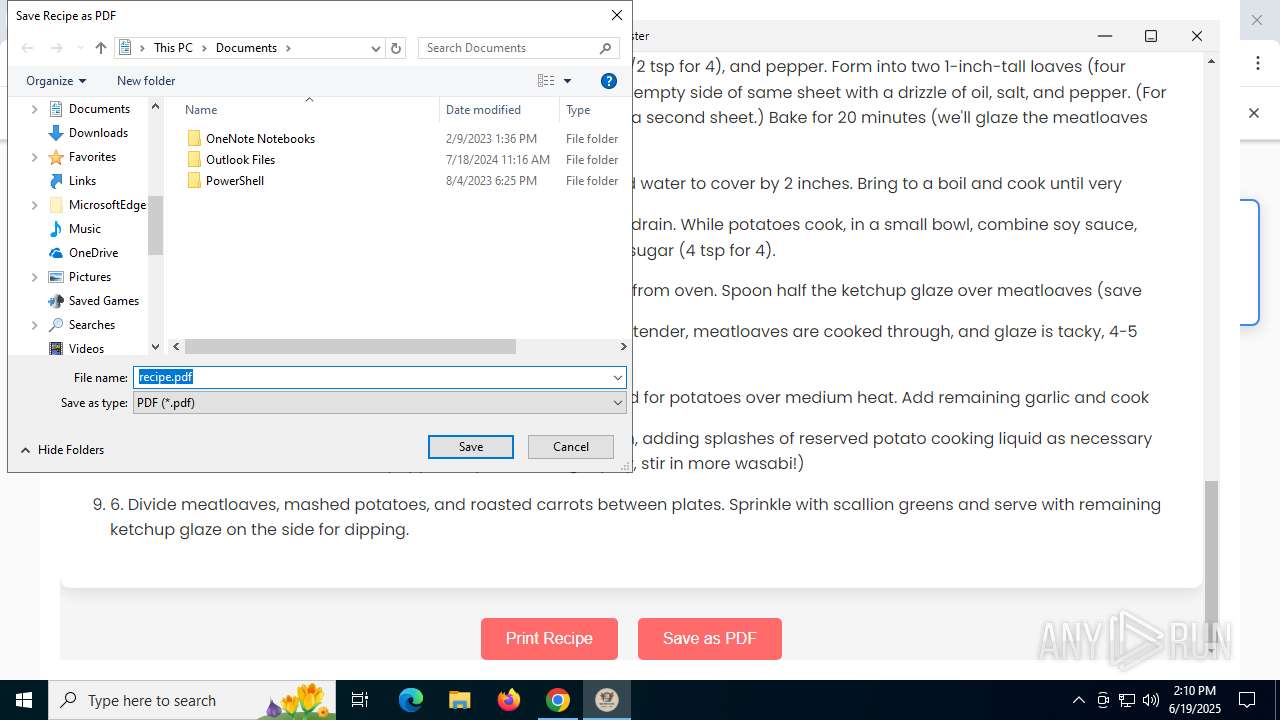
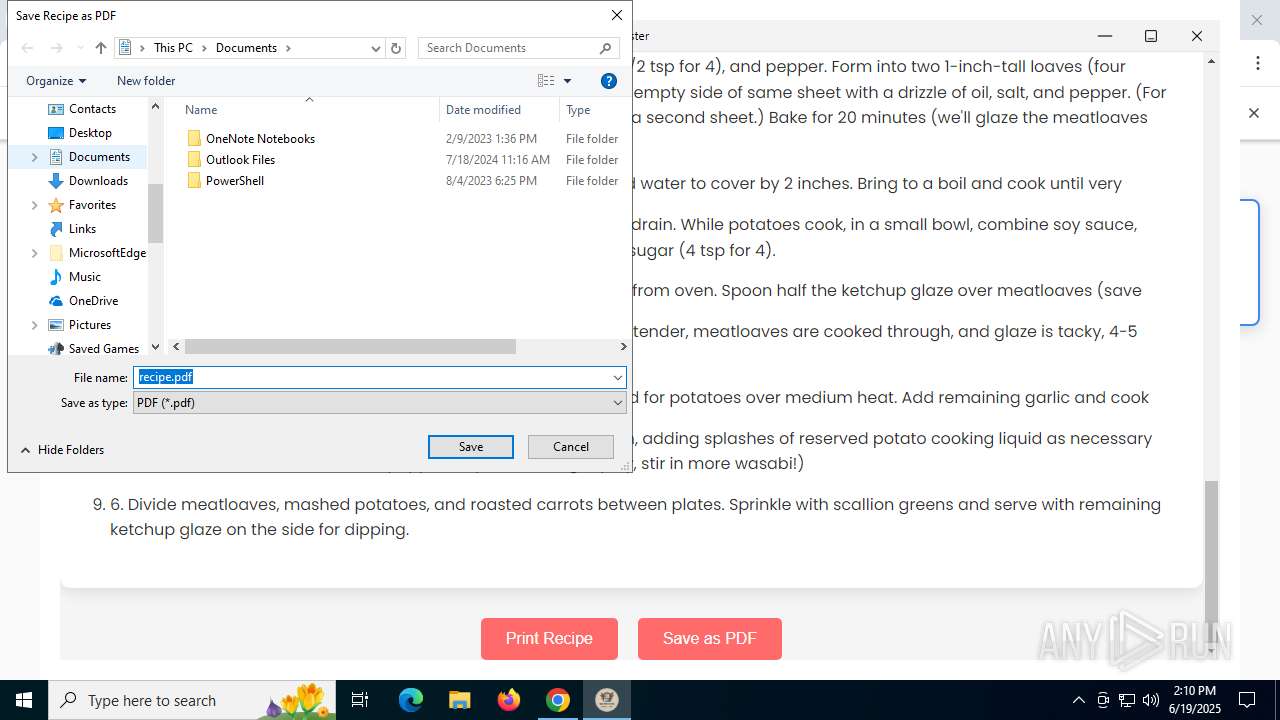
Total events
19 074
Read events
18 953
Write events
93
Delete events
28
Modification events
| (PID) Process: | (1604) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1604) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1604) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1604) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1604) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1604) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1604) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3936) Recipe Finder - Recipe Lister.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en-US |
Value: | |||
| (PID) Process: | (3936) Recipe Finder - Recipe Lister.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en |
Value: | |||
| (PID) Process: | (3936) Recipe Finder - Recipe Lister.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | _Global_ |
Value: | |||
Executable files
20
Suspicious files
227
Text files
214
Unknown types
362
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF176273.TMP | — | |
MD5:— | SHA256:— | |||
| 1604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF176282.TMP | — | |
MD5:— | SHA256:— | |||
| 1604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF176282.TMP | — | |
MD5:— | SHA256:— | |||
| 1604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF176292.TMP | — | |
MD5:— | SHA256:— | |||
| 1604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF176292.TMP | — | |
MD5:— | SHA256:— | |||
| 1604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF176292.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
104
DNS requests
97
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4800 | chrome.exe | GET | 200 | 142.250.181.238:80 | http://clients2.google.com/time/1/current?cup2key=8:aBswxRel6DYrHpU_sNVR22Tdb1CaGayfffRAEPdAby8&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 106 b | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1604 | chrome.exe | GET | 200 | 18.173.205.113:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT4XPMAgX8rbNb10iD9IkFVxGbTWwQUW8pe5d7SgarNqC1kUbbZcpuX5k8CEG7dTyXnMX05gVcxNM%2FB3KA%3D | US | binary | 314 b | whitelisted |
1604 | chrome.exe | GET | 200 | 18.173.205.113:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBROpre88MpUocDyy2wCPdWKwtQZDwQUAYmUuf60M13w8fqF%2BSRGhKNXaV4CED%2FPMYE3OZi7YghPjS3TGKM%3D | US | binary | 338 b | whitelisted |
3196 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 420 b | whitelisted |
3196 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
7288 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acpeapixpwuzscfa5h5j5m7c4xaa_2025.6.16.0/niikhdgajlphfehepabhhblakbdgeefj_2025.06.16.00_all_acgsomx5qtwgffxcrxwhoksfom7q.crx3 | US | — | — | whitelisted |
5012 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
7288 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acpeapixpwuzscfa5h5j5m7c4xaa_2025.6.16.0/niikhdgajlphfehepabhhblakbdgeefj_2025.06.16.00_all_acgsomx5qtwgffxcrxwhoksfom7q.crx3 | US | binary | 1.09 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5720 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4800 | chrome.exe | 172.217.18.106:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
4800 | chrome.exe | 142.250.181.238:80 | clients2.google.com | GOOGLE | US | whitelisted |
4800 | chrome.exe | 172.67.150.5:443 | recipelister.com | CLOUDFLARENET | US | unknown |
4800 | chrome.exe | 142.251.168.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
1604 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
recipelister.com |
| unknown |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
challenges.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4800 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
4800 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
4800 | chrome.exe | Misc activity | ET INFO Clearbit Logo Query in DNS Lookup |
4800 | chrome.exe | Misc activity | ET INFO Clearbit Logo Query in DNS Lookup |
4800 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Logo Request (logo.clearbit.com) |
4800 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Logo Request (logo.clearbit.com) |
4800 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Logo Request (logo.clearbit.com) |
4800 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Logo Request (logo.clearbit.com) |
4800 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Logo Request (logo.clearbit.com) |
4800 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Logo Request (logo.clearbit.com) |