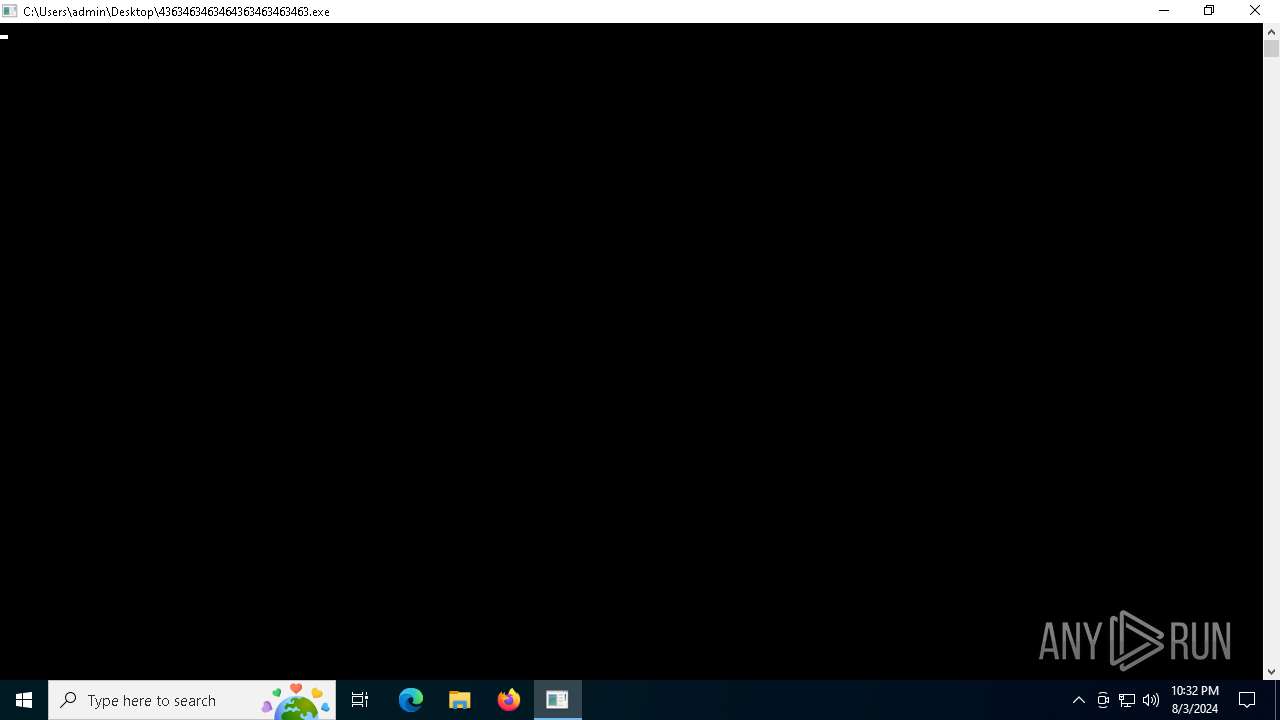
| File name: | 4363463463464363463463463.exe |
| Full analysis: | https://app.any.run/tasks/cf60b9c5-2ec6-4a13-93a7-bee8c8fd9ece |
| Verdict: | Malicious activity |
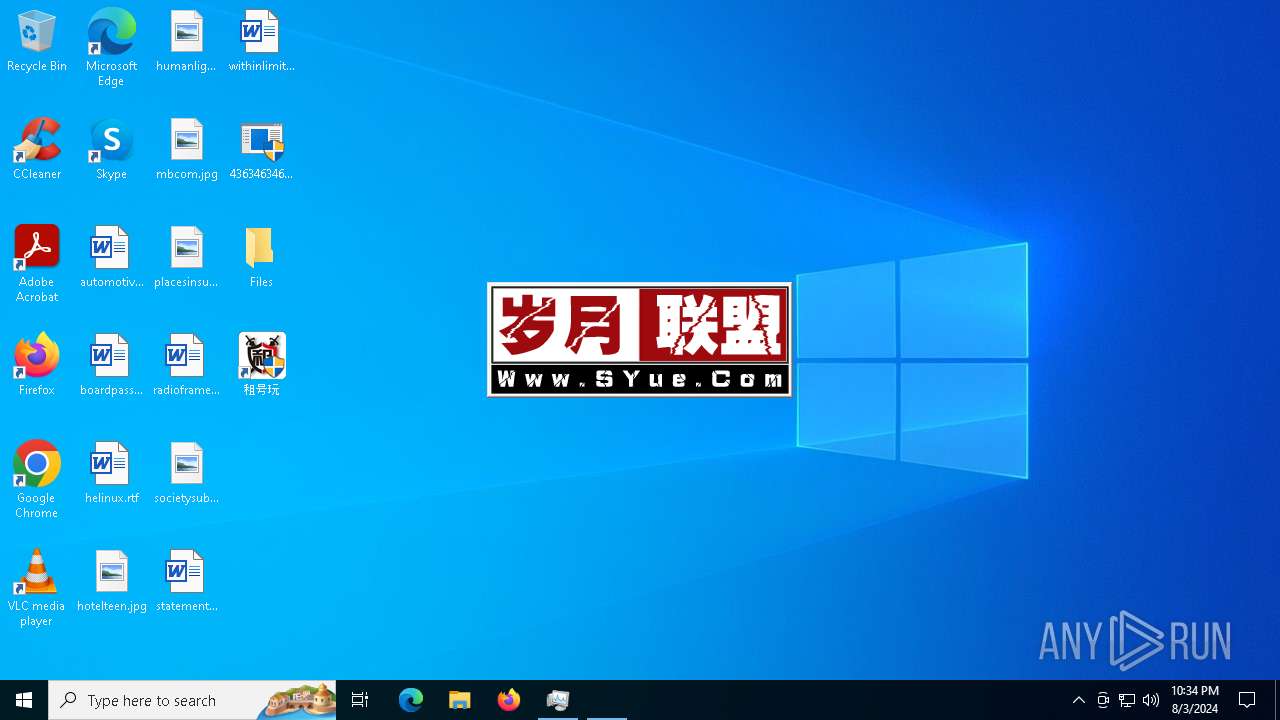
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | August 03, 2024, 22:32:19 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 2A94F3960C58C6E70826495F76D00B85 |
| SHA1: | E2A1A5641295F5EBF01A37AC1C170AC0814BB71A |
| SHA256: | 2FCAD226B17131DA4274E1B9F8F31359BDD325C9568665F08FD1F6C5D06A23CE |
| SSDEEP: | 192:2we8sGKE6MqyG7c20L7BIW12n/ePSmzkTInu8stYcFwVc03KY:9e8sGKfMqyGg20PKn/cRaInuptYcFwVY |
MALICIOUS
HAUSBOMBER has been detected (YARA)
- 4363463463464363463463463.exe (PID: 6512)
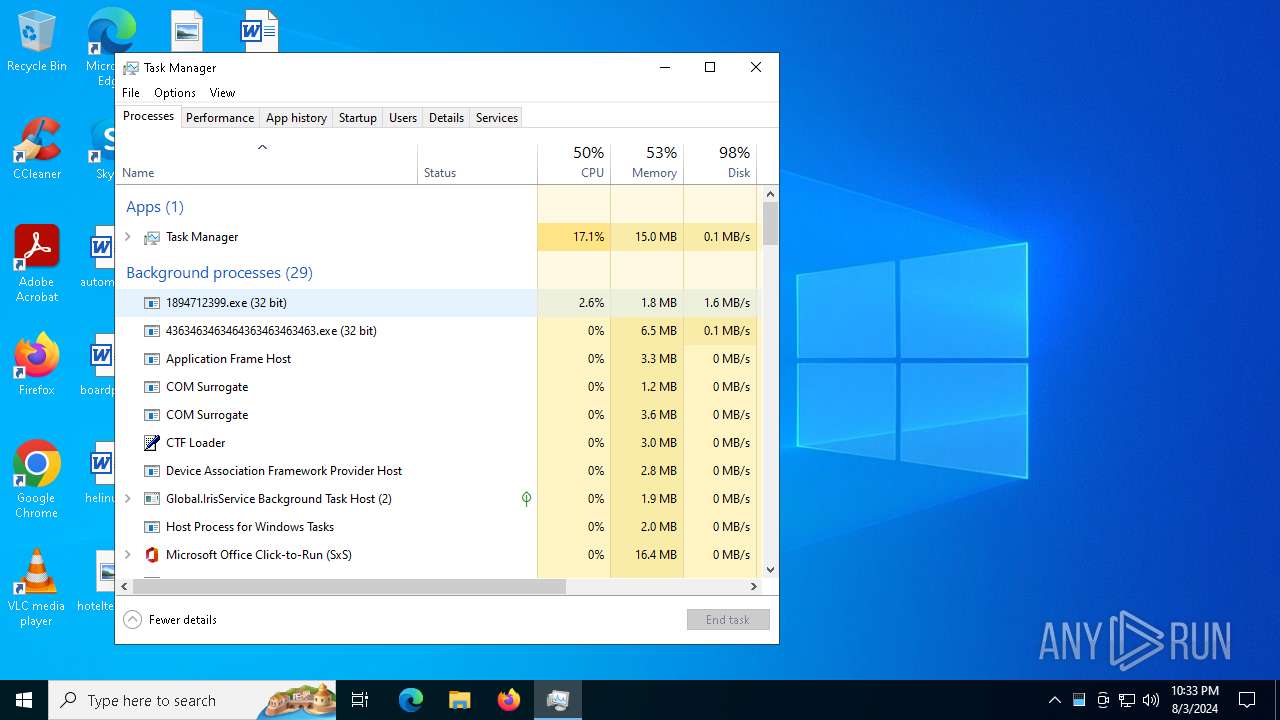
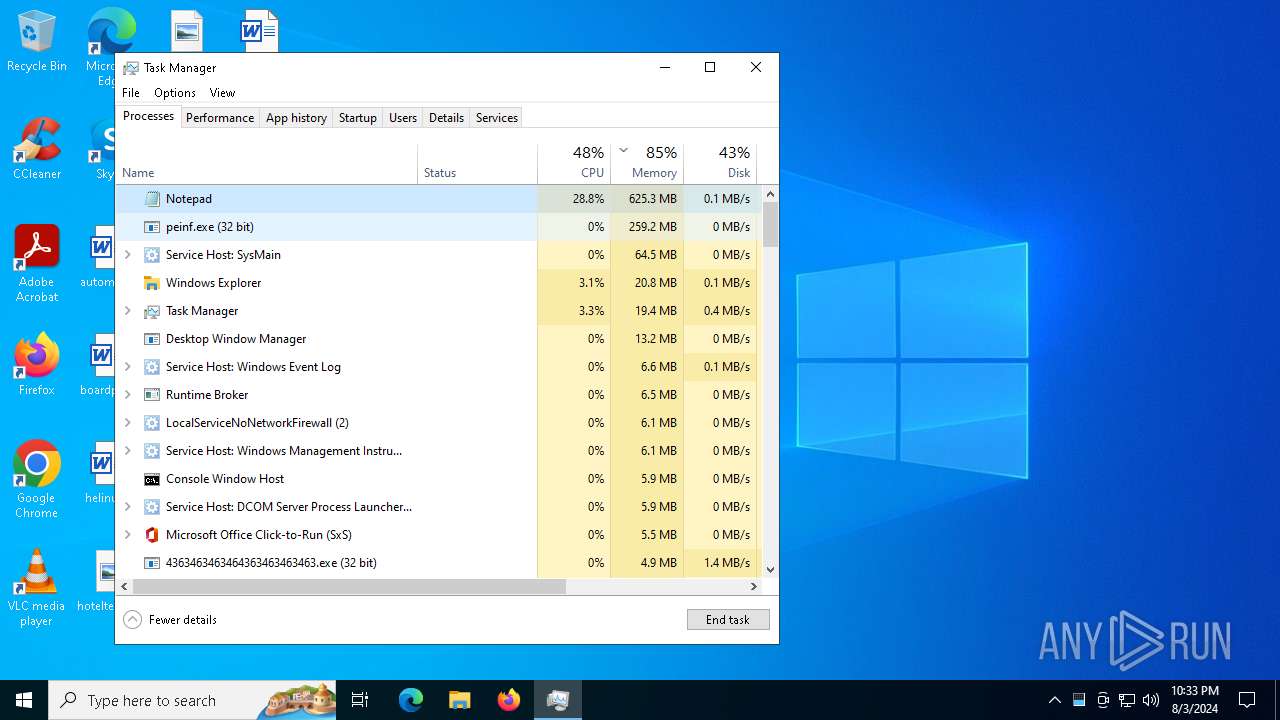
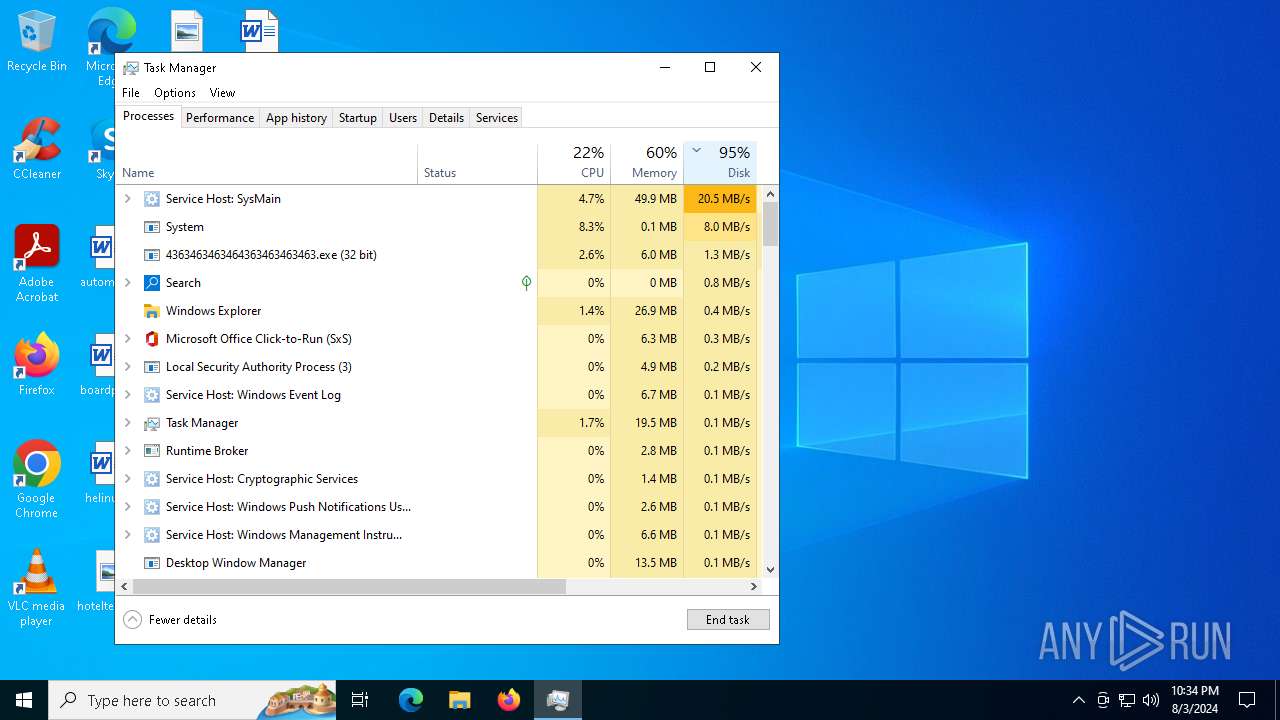
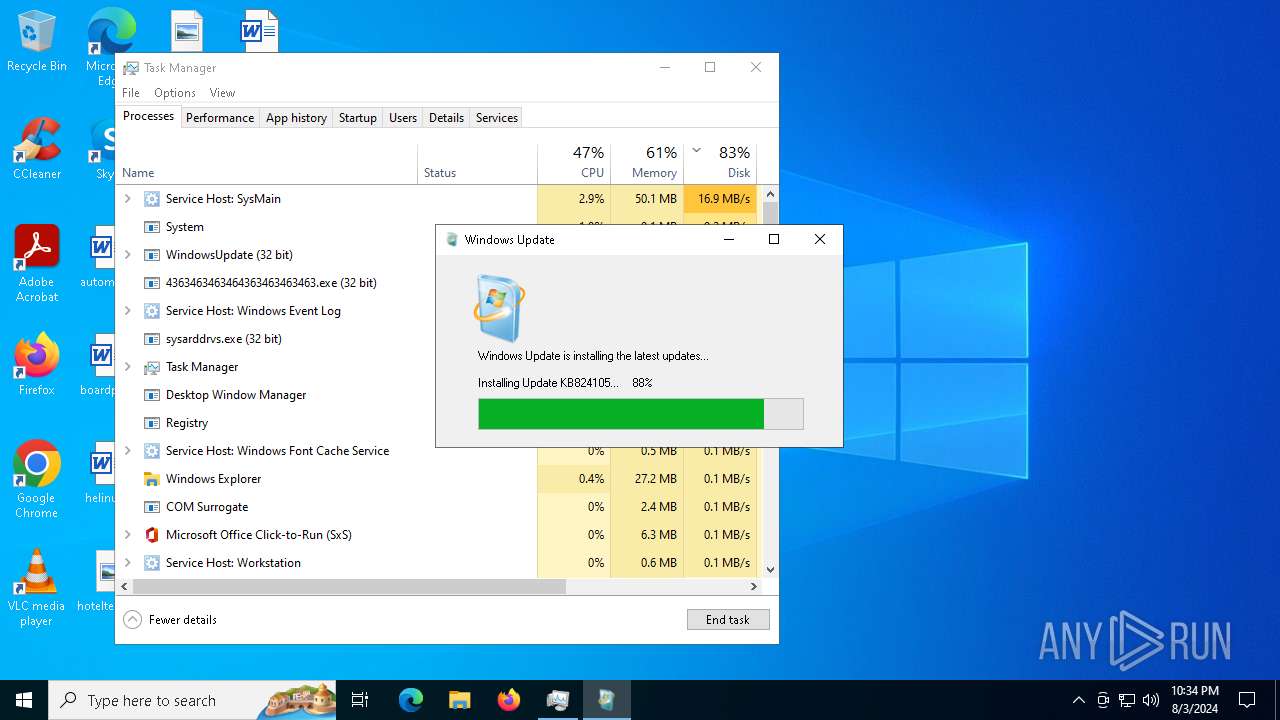
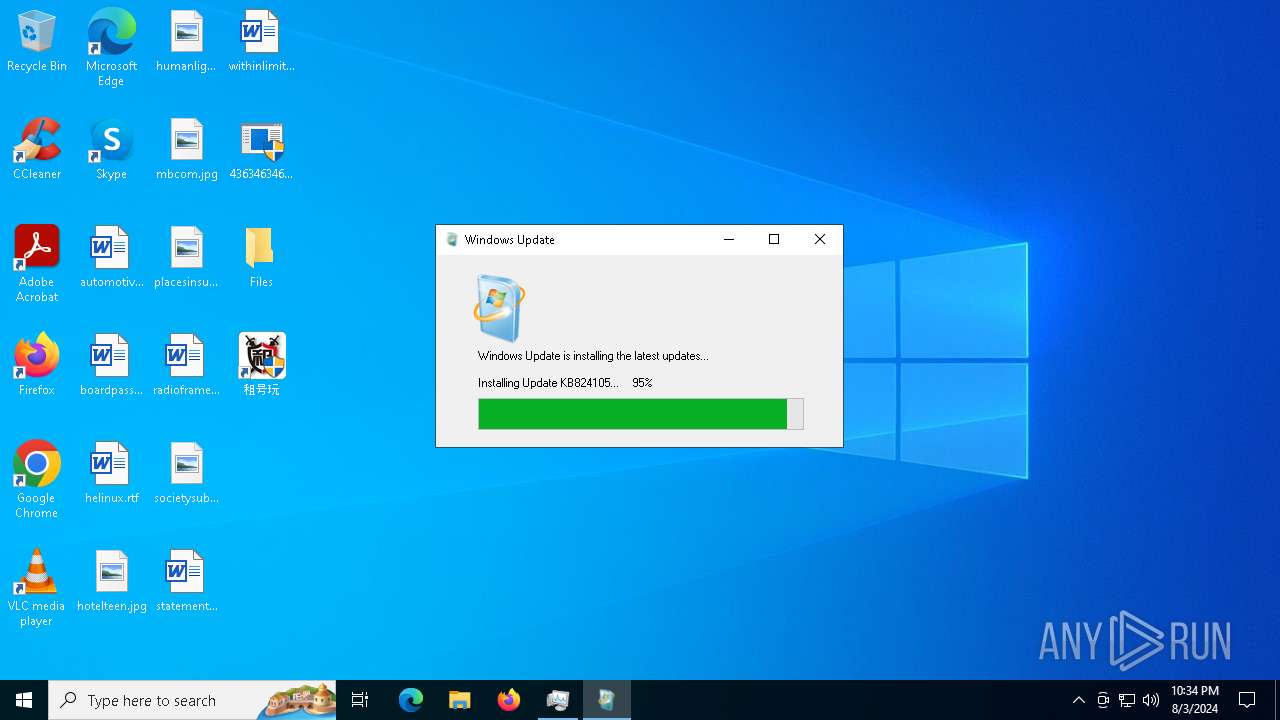
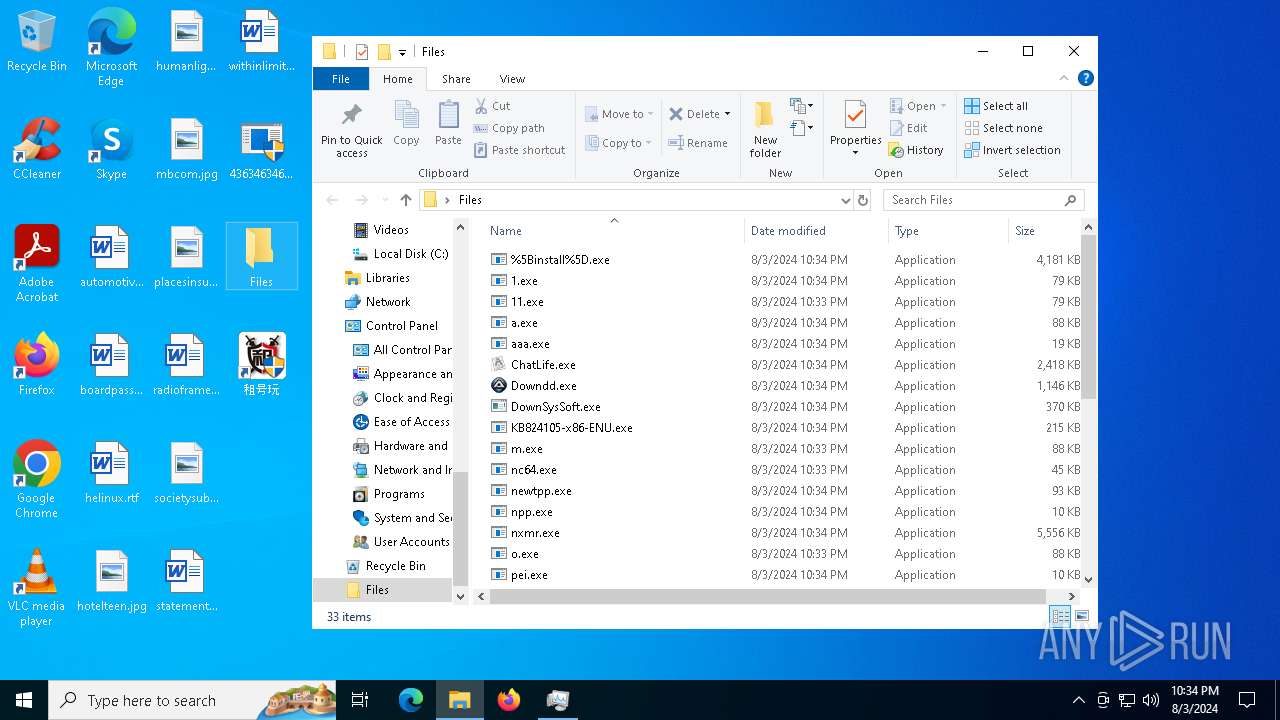
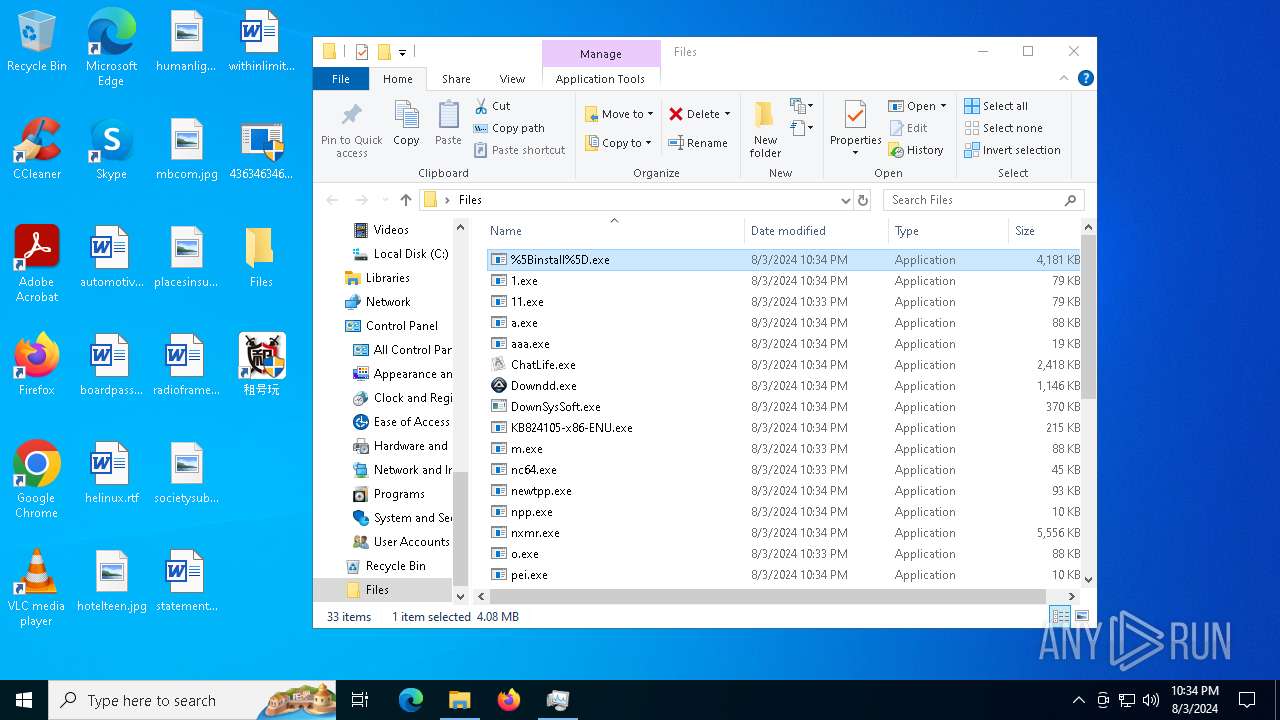
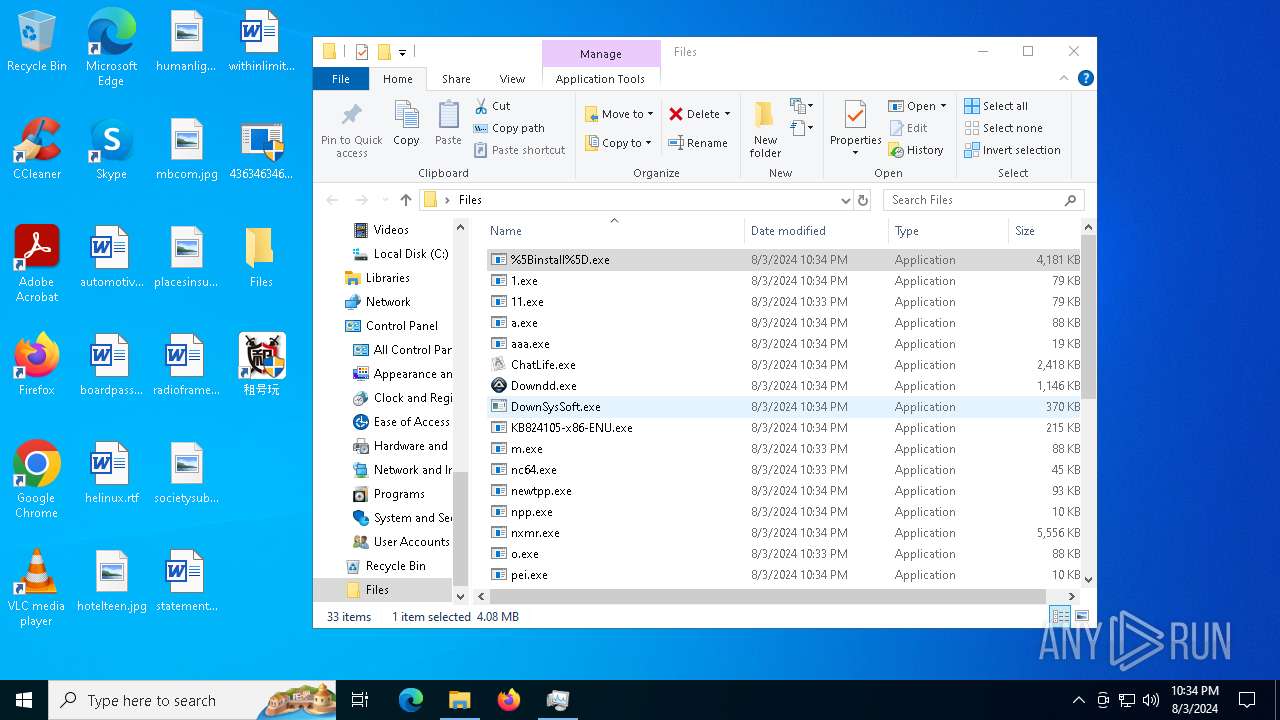
Drops the executable file immediately after the start
- t1.exe (PID: 6684)
- 4363463463464363463463463.exe (PID: 6512)
- pi.exe (PID: 6664)
- peinf.exe (PID: 6644)
- 239823184.exe (PID: 5196)
- 2789214706.exe (PID: 6156)
- sysmablsvr.exe (PID: 6728)
- sylsplvc.exe (PID: 6820)
- 1894712399.exe (PID: 2180)
- 1954338341.exe (PID: 6360)
- wupgrdsv.exe (PID: 5304)
- sysmysldrv.exe (PID: 5116)
- tpeinf.exe (PID: 6936)
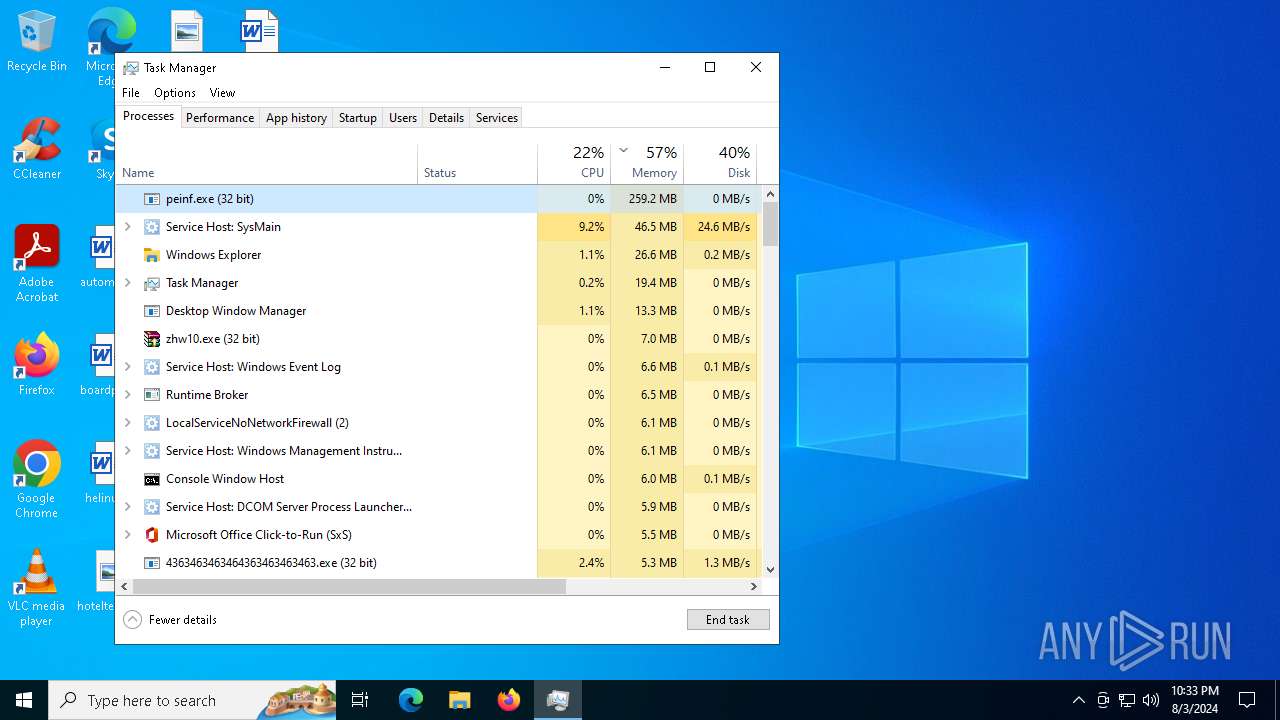
- zhw10.exe (PID: 6832)
- 11.exe (PID: 1492)
- npp.exe (PID: 6540)
- cmd.exe (PID: 2900)
- Paraguay.pif (PID: 2992)
- pei.exe (PID: 6720)
- nxmr.exe (PID: 3684)
- wupgrdsv.exe (PID: 6228)
- sysarddrvs.exe (PID: 6188)
- radbxnzdxbd.exe (PID: 6952)
Changes the autorun value in the registry
- t1.exe (PID: 6684)
- pi.exe (PID: 6664)
- 239823184.exe (PID: 5196)
- 11.exe (PID: 1492)
DCRAT has been detected (YARA)
- 4363463463464363463463463.exe (PID: 6512)
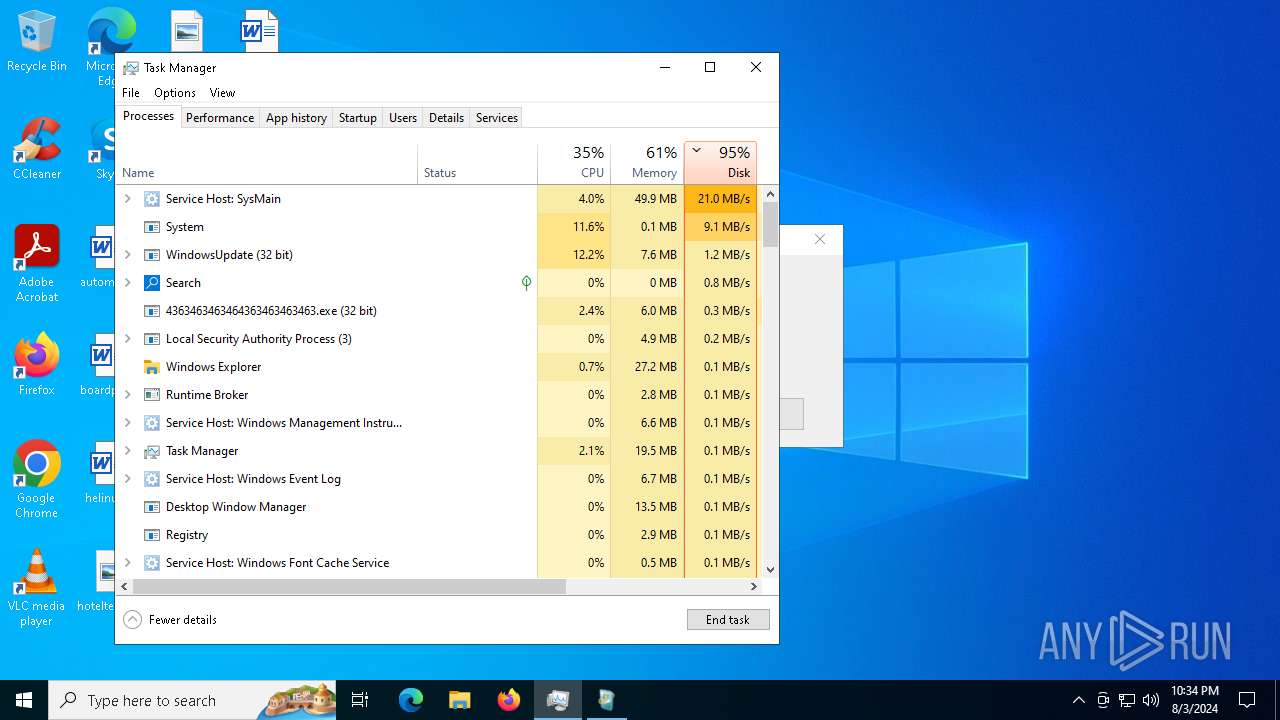
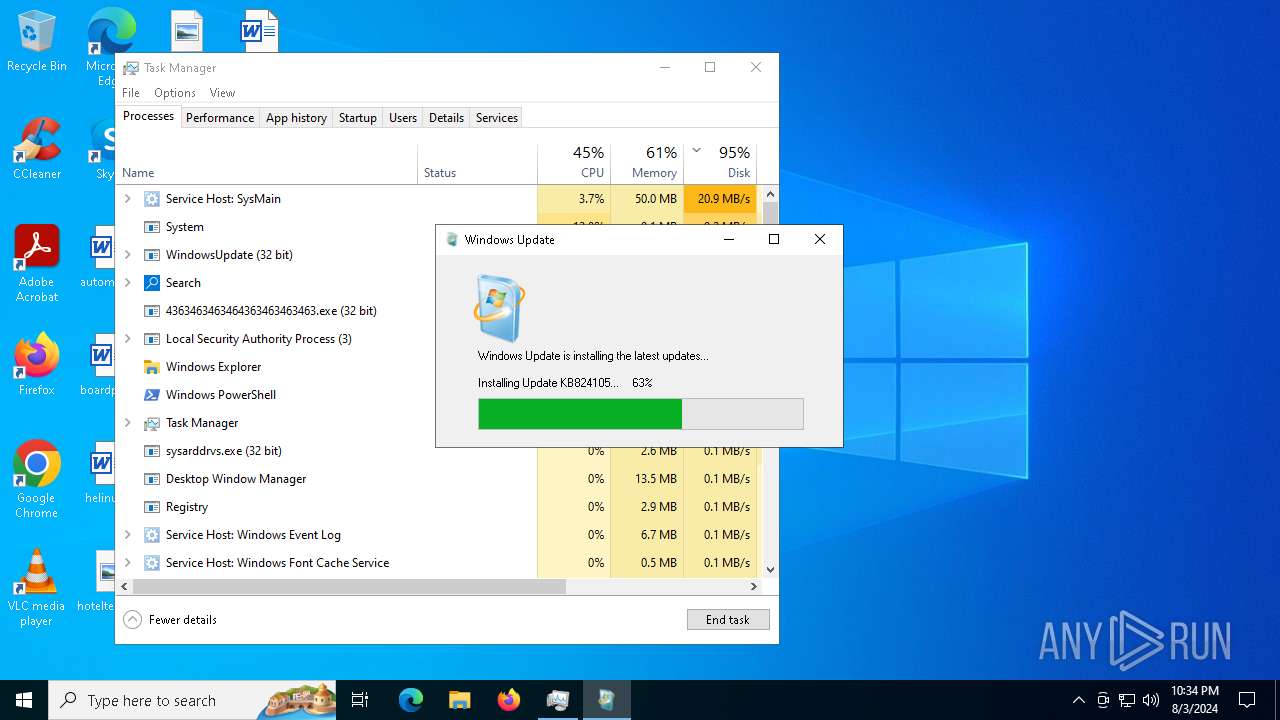
Changes the Windows auto-update feature
- sysmablsvr.exe (PID: 6728)
- sysmysldrv.exe (PID: 5116)
- sysarddrvs.exe (PID: 6188)
Changes appearance of the Explorer extensions
- sysmablsvr.exe (PID: 6728)
- sysmysldrv.exe (PID: 5116)
- sysarddrvs.exe (PID: 6188)
Changes Security Center notification settings
- sysmablsvr.exe (PID: 6728)
- sylsplvc.exe (PID: 6820)
- sysmysldrv.exe (PID: 5116)
- sysarddrvs.exe (PID: 6188)
Creates or modifies Windows services
- sysmablsvr.exe (PID: 6728)
- sysmysldrv.exe (PID: 5116)
- sysarddrvs.exe (PID: 6188)
Connects to the CnC server
- sysmablsvr.exe (PID: 6728)
- sylsplvc.exe (PID: 6820)
- sysmysldrv.exe (PID: 5116)
- notepad.exe (PID: 320)
- sysarddrvs.exe (PID: 6188)
- notepad.exe (PID: 2476)
- server.exe (PID: 3684)
PHORPIEX has been detected (SURICATA)
- sysmablsvr.exe (PID: 6728)
- svchost.exe (PID: 2256)
- sylsplvc.exe (PID: 6820)
- sysmysldrv.exe (PID: 5116)
- sysarddrvs.exe (PID: 6188)
- 4363463463464363463463463.exe (PID: 6512)
Adds path to the Windows Defender exclusion list
- sysmysldrv.exe (PID: 5116)
- cmd.exe (PID: 6748)
- sysarddrvs.exe (PID: 6188)
- cmd.exe (PID: 6656)
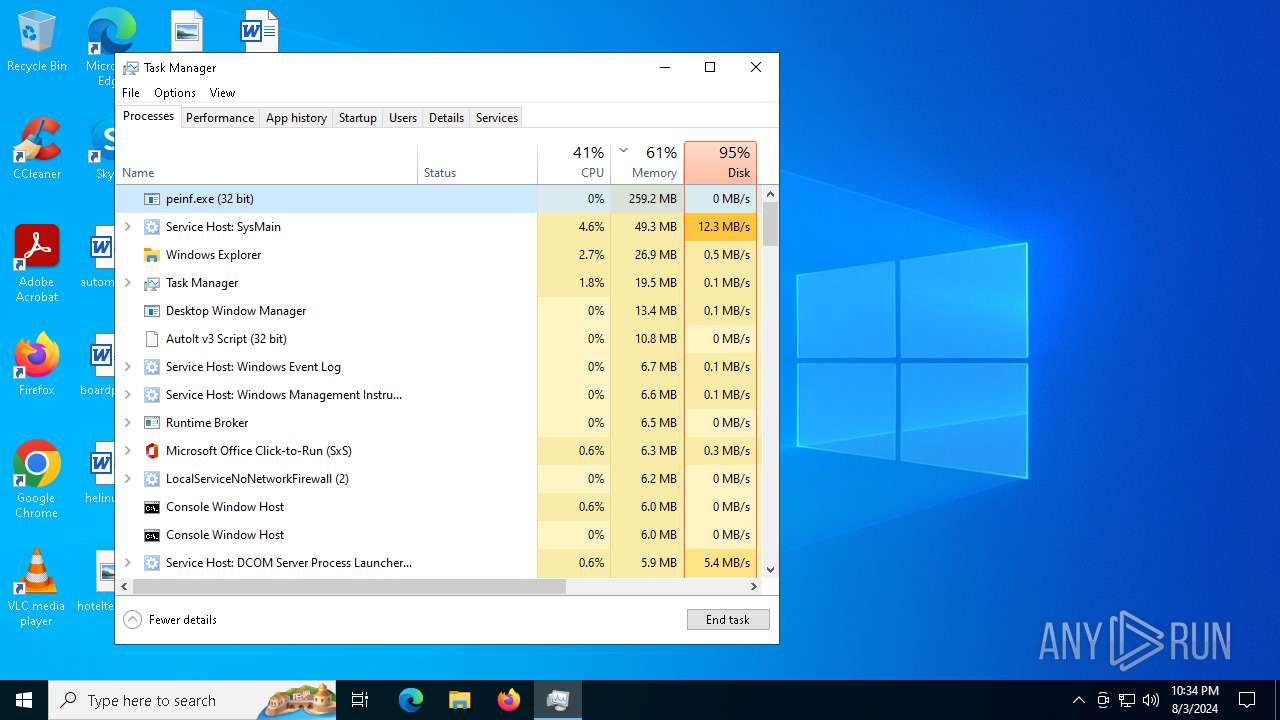
Actions looks like stealing of personal data
- peinf.exe (PID: 6644)
PHORPIEX has been detected (YARA)
- sysmablsvr.exe (PID: 6728)
- sysmysldrv.exe (PID: 5116)
- sysarddrvs.exe (PID: 6188)
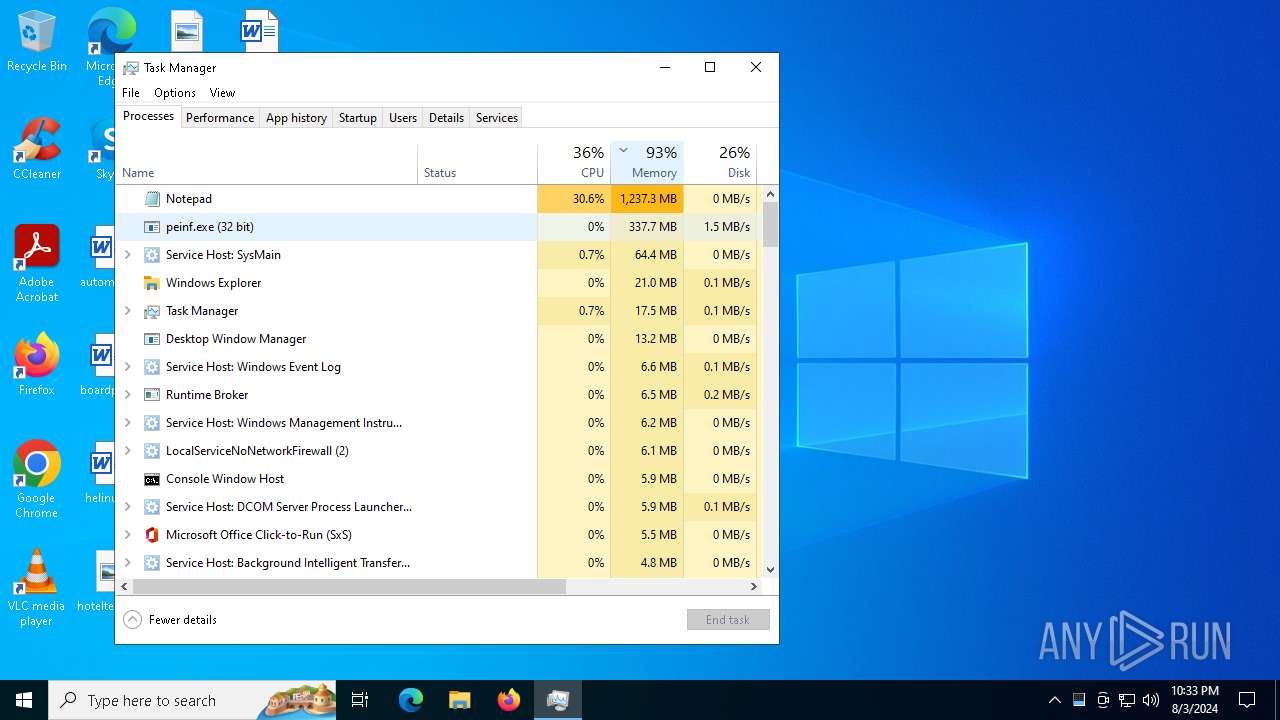
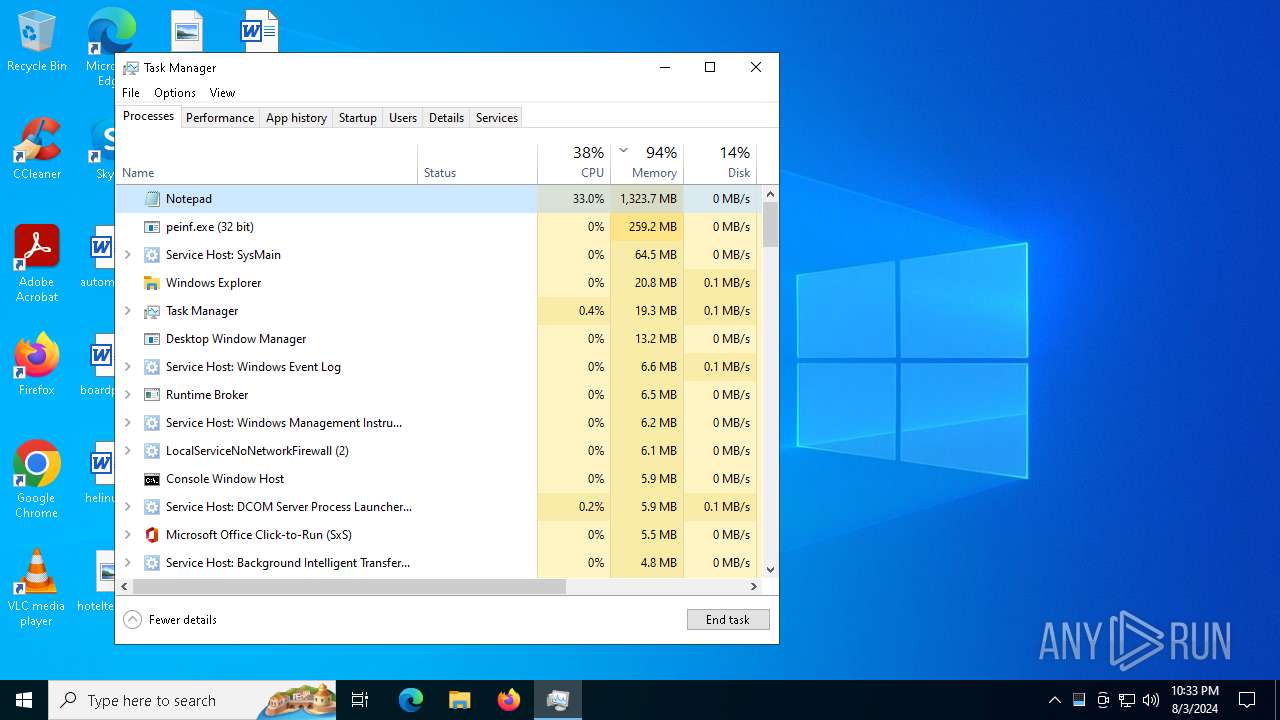
MINER has been detected (SURICATA)
- notepad.exe (PID: 320)
- notepad.exe (PID: 2476)
Antivirus name has been found in the command line (generic signature)
- findstr.exe (PID: 2928)
- findstr.exe (PID: 3292)
Create files in the Startup directory
- cmd.exe (PID: 4324)
Attempt to connect to SMB server
- System (PID: 4)
RISEPRO has been detected (YARA)
- Paraguay.pif (PID: 6692)
XFILES has been detected (SURICATA)
- server.exe (PID: 3684)
Stealers network behavior
- server.exe (PID: 3684)
SUSPICIOUS
Reads the date of Windows installation
- 4363463463464363463463463.exe (PID: 6512)
- sysmysldrv.exe (PID: 5116)
- sysarddrvs.exe (PID: 6188)
- ChatLife.exe (PID: 6956)
- server.exe (PID: 3684)
Reads security settings of Internet Explorer
- 4363463463464363463463463.exe (PID: 6512)
- sysmablsvr.exe (PID: 6728)
- sylsplvc.exe (PID: 6820)
- 2861732127.exe (PID: 640)
- sysmysldrv.exe (PID: 5116)
- 2789214706.exe (PID: 6156)
- 1894712399.exe (PID: 2180)
- tpeinf.exe (PID: 6936)
- sysarddrvs.exe (PID: 6188)
- npp.exe (PID: 6540)
- ChatLife.exe (PID: 6956)
- pei.exe (PID: 6720)
- DownSysSoft.exe (PID: 5232)
- radbxnzdxbd.exe (PID: 6952)
Executable content was dropped or overwritten
- t1.exe (PID: 6684)
- 4363463463464363463463463.exe (PID: 6512)
- pi.exe (PID: 6664)
- peinf.exe (PID: 6644)
- 239823184.exe (PID: 5196)
- 2789214706.exe (PID: 6156)
- 1894712399.exe (PID: 2180)
- 1954338341.exe (PID: 6360)
- wupgrdsv.exe (PID: 5304)
- zhw10.exe (PID: 6832)
- 11.exe (PID: 1492)
- tpeinf.exe (PID: 6936)
- npp.exe (PID: 6540)
- cmd.exe (PID: 2900)
- Paraguay.pif (PID: 2992)
- pei.exe (PID: 6720)
- nxmr.exe (PID: 3684)
- wupgrdsv.exe (PID: 6228)
- radbxnzdxbd.exe (PID: 6952)
Starts itself from another location
- t1.exe (PID: 6684)
- pi.exe (PID: 6664)
- 239823184.exe (PID: 5196)
- sysmysldrv.exe (PID: 5116)
- 11.exe (PID: 1492)
Potential Corporate Privacy Violation
- 4363463463464363463463463.exe (PID: 6512)
- 1894712399.exe (PID: 2180)
- notepad.exe (PID: 320)
- tpeinf.exe (PID: 6936)
- System (PID: 4)
- 2789214706.exe (PID: 6156)
- DownSysSoft.exe (PID: 5232)
- notepad.exe (PID: 2476)
Connects to unusual port
- 4363463463464363463463463.exe (PID: 6512)
- sylsplvc.exe (PID: 6820)
- notepad.exe (PID: 320)
- sysmablsvr.exe (PID: 6728)
- sysmysldrv.exe (PID: 5116)
- aaa.exe (PID: 6908)
- DownSysSoft.exe (PID: 5232)
- notepad.exe (PID: 2476)
- %5Binstall%5D.exe (PID: 6704)
- Paraguay.pif (PID: 6692)
- sysarddrvs.exe (PID: 6188)
- QQ.exe (PID: 2400)
- %5Binstall%5D.exe (PID: 6656)
Creates or modifies Windows services
- sysmablsvr.exe (PID: 6728)
- sysmysldrv.exe (PID: 5116)
- sysarddrvs.exe (PID: 6188)
Connects to the server without a host name
- sysmablsvr.exe (PID: 6728)
- sysmysldrv.exe (PID: 5116)
- 2789214706.exe (PID: 6156)
- sylsplvc.exe (PID: 6820)
- 1894712399.exe (PID: 2180)
- sysarddrvs.exe (PID: 6188)
- 4363463463464363463463463.exe (PID: 6512)
Process drops legitimate windows executable
- peinf.exe (PID: 6644)
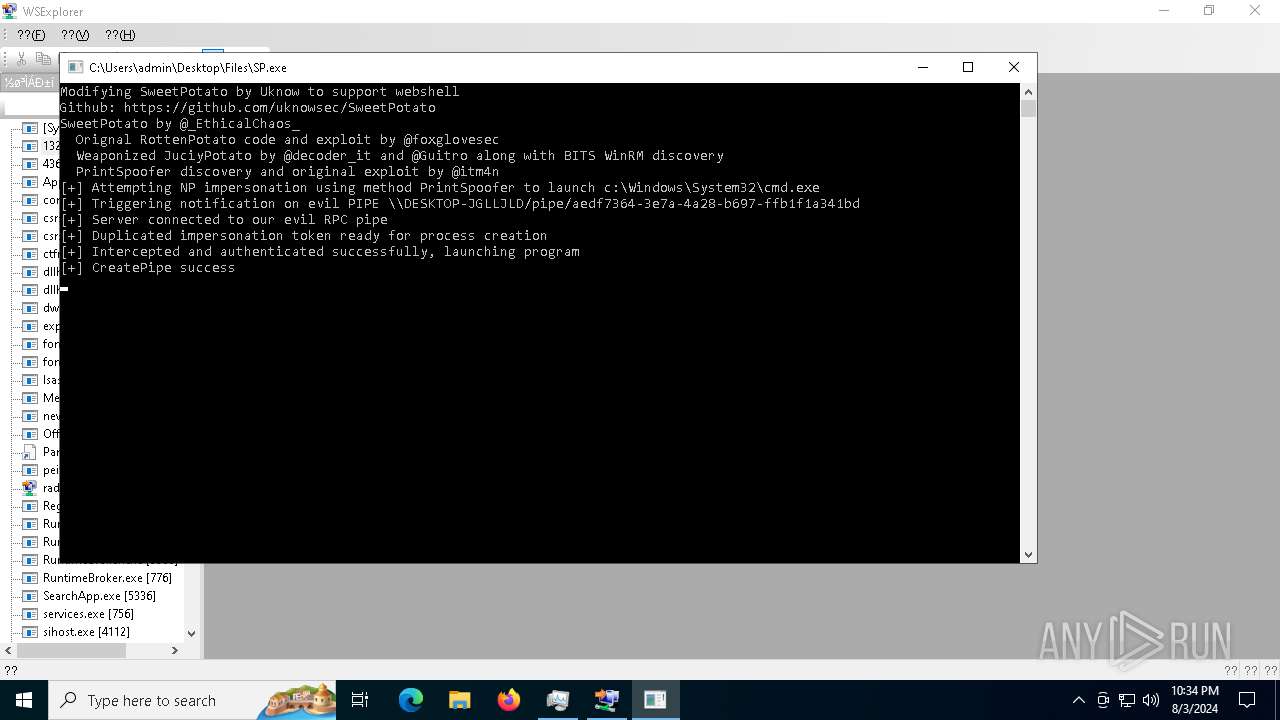
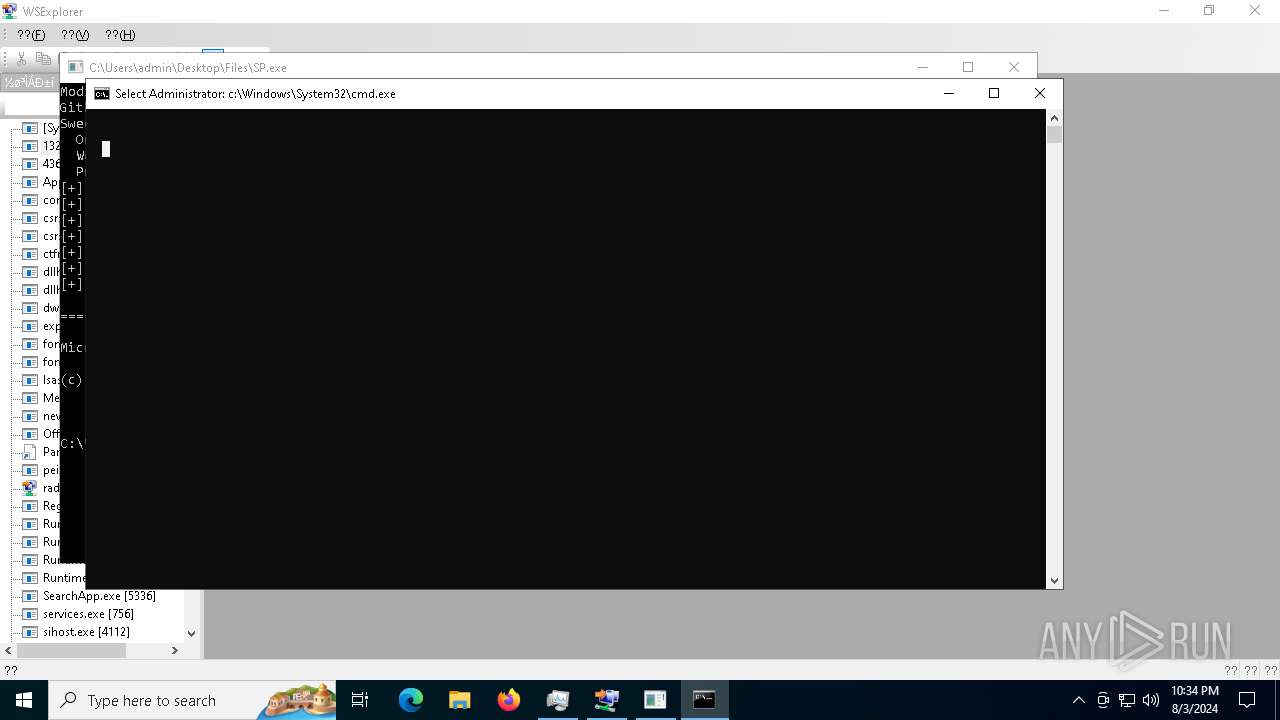
Starts CMD.EXE for commands execution
- sysmysldrv.exe (PID: 5116)
- sysarddrvs.exe (PID: 6188)
- ChatLife.exe (PID: 6956)
- cmd.exe (PID: 2900)
- Paraguay.pif (PID: 2992)
- KB824105-x86-ENU.exe (PID: 6984)
- SP.exe (PID: 3984)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6748)
- cmd.exe (PID: 6656)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 6748)
- cmd.exe (PID: 6656)
Process requests binary or script from the Internet
- 2789214706.exe (PID: 6156)
- 1894712399.exe (PID: 2180)
- 4363463463464363463463463.exe (PID: 6512)
- tpeinf.exe (PID: 6936)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 4664)
- powershell.exe (PID: 4780)
Drops a system driver (possible attempt to evade defenses)
- wupgrdsv.exe (PID: 5304)
- zhw10.exe (PID: 6832)
- wupgrdsv.exe (PID: 6228)
The process executes via Task Scheduler
- wupgrdsv.exe (PID: 5304)
- wupgrdsv.exe (PID: 6228)
Crypto Currency Mining Activity Detected
- notepad.exe (PID: 320)
Executing commands from ".cmd" file
- ChatLife.exe (PID: 6956)
Get information on the list of running processes
- cmd.exe (PID: 2900)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2900)
Application launched itself
- cmd.exe (PID: 2900)
- Paraguay.pif (PID: 2992)
- %5Binstall%5D.exe (PID: 964)
Suspicious file concatenation
- cmd.exe (PID: 5904)
The executable file from the user directory is run by the CMD process
- Paraguay.pif (PID: 2992)
Drops a file with a rarely used extension (PIF)
- Paraguay.pif (PID: 2992)
- cmd.exe (PID: 2900)
Starts application with an unusual extension
- cmd.exe (PID: 2900)
- Paraguay.pif (PID: 2992)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2900)
Starts NET.EXE to map network drives
- cmd.exe (PID: 1500)
Contacting a server suspected of hosting an CnC
- server.exe (PID: 3684)
INFO
Checks supported languages
- 4363463463464363463463463.exe (PID: 6512)
- sysmablsvr.exe (PID: 6728)
- peinf.exe (PID: 6644)
- pi.exe (PID: 6664)
- t1.exe (PID: 6684)
- pp.exe (PID: 6704)
- sylsplvc.exe (PID: 6820)
- 2861732127.exe (PID: 640)
- 239823184.exe (PID: 5196)
- 72094654.exe (PID: 5540)
- sysmysldrv.exe (PID: 5116)
- 363014155.exe (PID: 872)
- 2789214706.exe (PID: 6156)
- 2990227768.exe (PID: 208)
- 3457411655.exe (PID: 1344)
- 830128787.exe (PID: 6200)
- 1894712399.exe (PID: 2180)
- 2921726330.exe (PID: 5220)
- 1954338341.exe (PID: 6360)
- 2961713205.exe (PID: 6304)
- 2821219799.exe (PID: 2636)
- 417311002.exe (PID: 1536)
- wupgrdsv.exe (PID: 5304)
- o.exe (PID: 2336)
- zhw10.exe (PID: 6832)
- 11.exe (PID: 1492)
- tt.exe (PID: 7092)
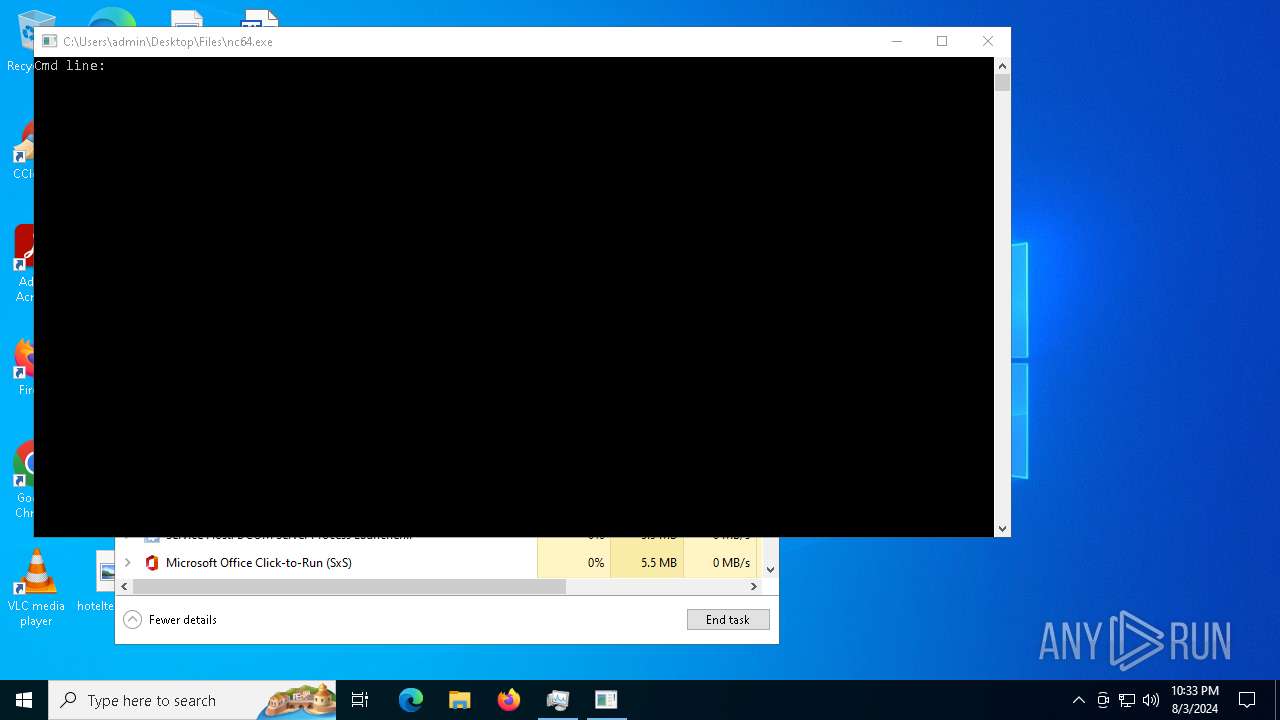
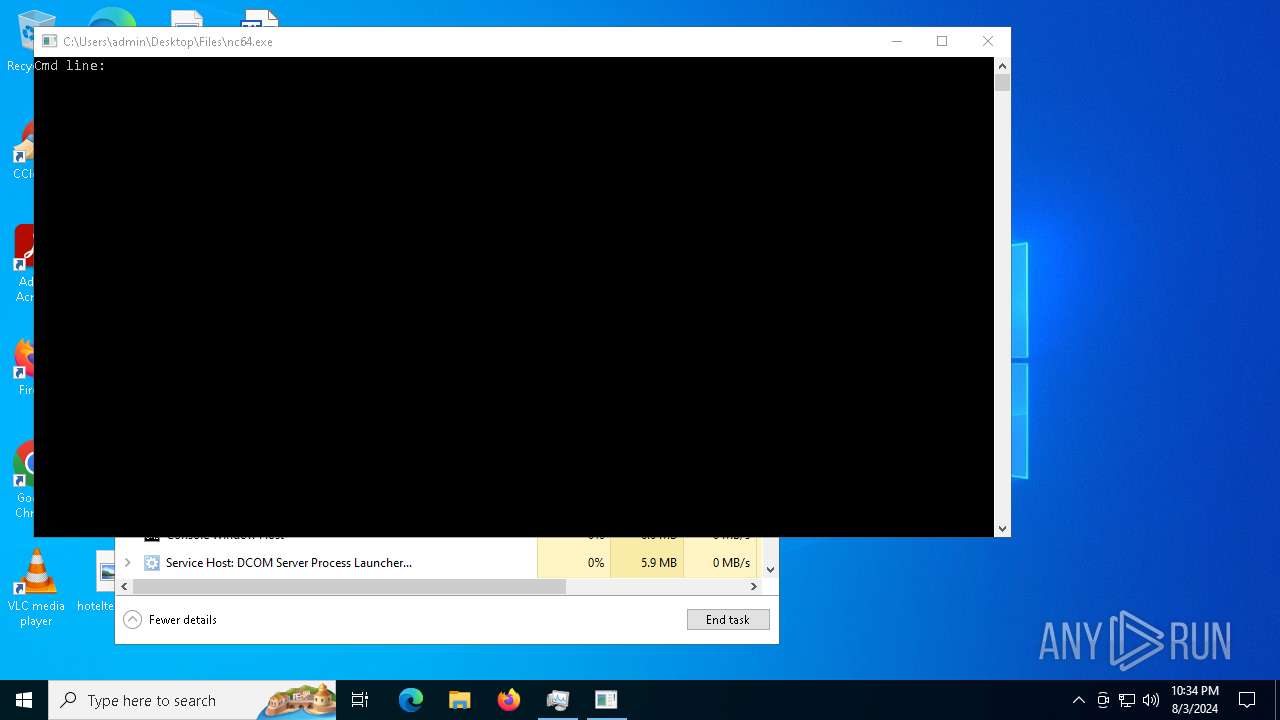
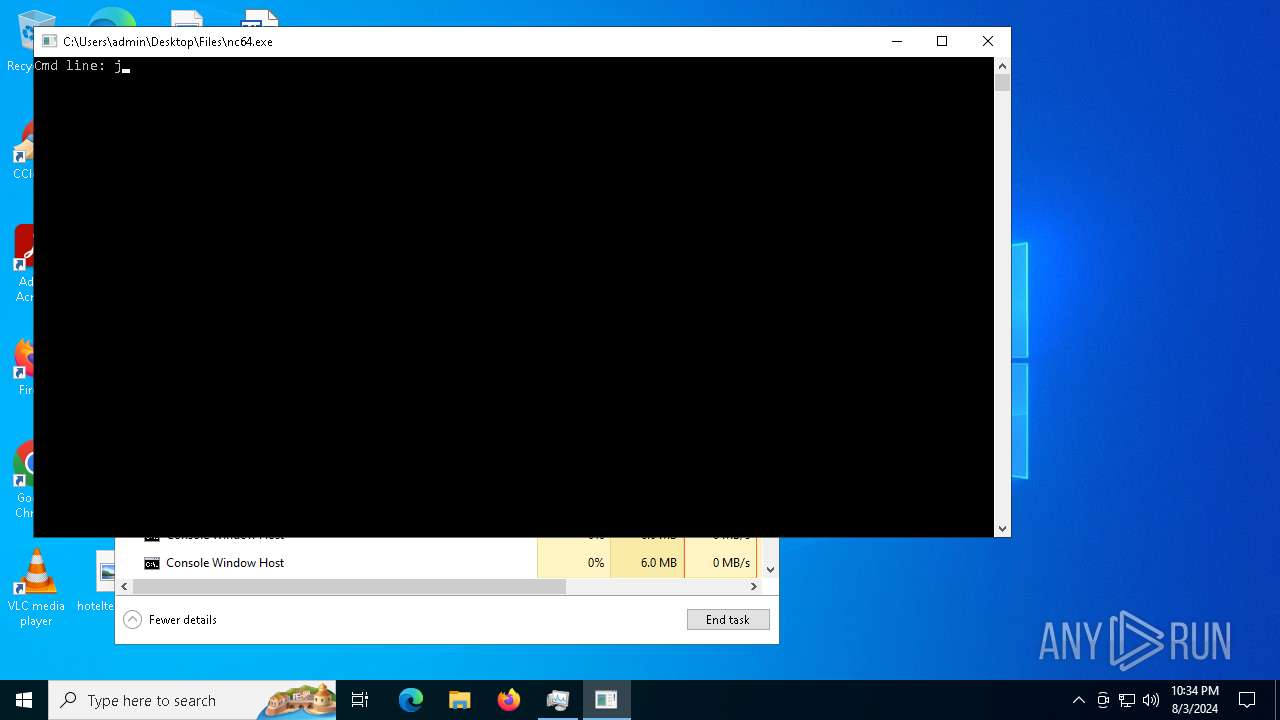
- nc64.exe (PID: 6440)
- m.exe (PID: 7064)
- tpeinf.exe (PID: 6936)
- r.exe (PID: 6932)
- sysarddrvs.exe (PID: 6188)
- aaa.exe (PID: 6908)
- npp.exe (PID: 6540)
- a.exe (PID: 5980)
- ChatLife.exe (PID: 6956)
- 91691011.exe (PID: 2384)
- 102998359.exe (PID: 6332)
- Paraguay.pif (PID: 2992)
- nxmr.exe (PID: 3684)
- pei.exe (PID: 6720)
- DownSysSoft.exe (PID: 5232)
- 411220961.exe (PID: 304)
- 2703228514.exe (PID: 5168)
- KB824105-x86-ENU.exe (PID: 6984)
- t2.exe (PID: 4592)
- twztl.exe (PID: 1688)
- tdrpload.exe (PID: 3292)
- radbxnzdxbd.exe (PID: 6952)
- wupgrdsv.exe (PID: 6228)
- 1327411970.exe (PID: 6900)
- newtpp.exe (PID: 1168)
- t.exe (PID: 2456)
- 332493390.exe (PID: 5168)
- SP.exe (PID: 3984)
- server.exe (PID: 3684)
- s.exe (PID: 6688)
- Downdd.exe (PID: 2248)
- %5Binstall%5D.exe (PID: 6704)
- 1.exe (PID: 2424)
- %5Binstall%5D.exe (PID: 964)
- %5Binstall%5D.exe (PID: 6656)
- Paraguay.pif (PID: 6692)
- 243031083.exe (PID: 1692)
- ber.exe (PID: 6364)
- QQ.exe (PID: 2400)
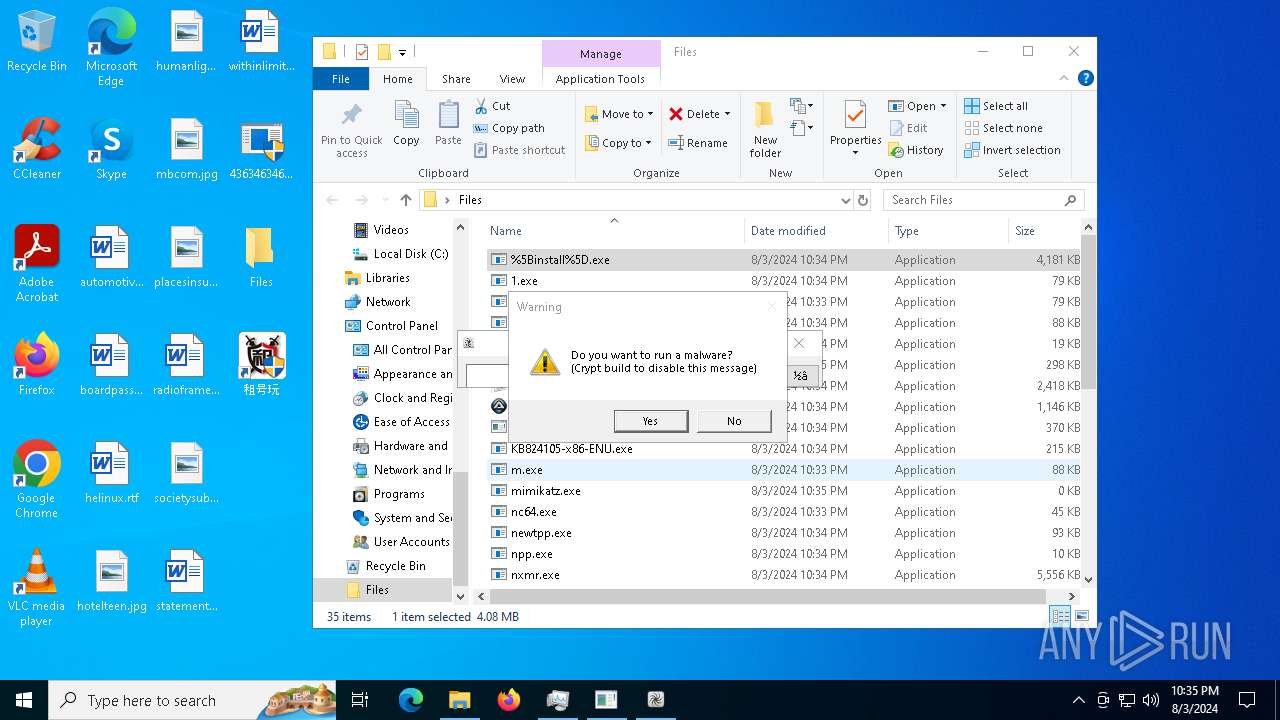
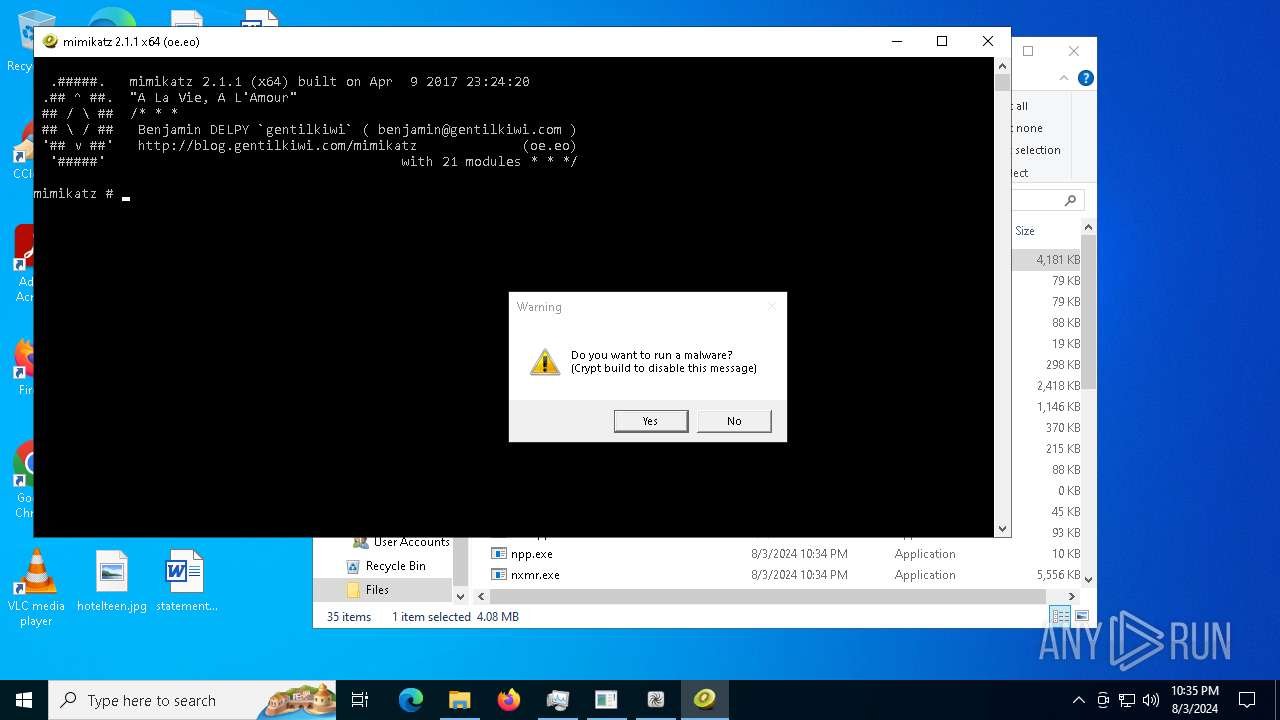
- mimikatz.exe (PID: 6700)
- build_2024-07-25_20-56.exe (PID: 6920)
- Population.exe (PID: 7108)
- 2.exe (PID: 6440)
Reads the computer name
- 4363463463464363463463463.exe (PID: 6512)
- sysmablsvr.exe (PID: 6728)
- sylsplvc.exe (PID: 6820)
- 2861732127.exe (PID: 640)
- sysmysldrv.exe (PID: 5116)
- 2789214706.exe (PID: 6156)
- 1894712399.exe (PID: 2180)
- zhw10.exe (PID: 6832)
- tpeinf.exe (PID: 6936)
- sysarddrvs.exe (PID: 6188)
- aaa.exe (PID: 6908)
- npp.exe (PID: 6540)
- ChatLife.exe (PID: 6956)
- nc64.exe (PID: 6440)
- Paraguay.pif (PID: 2992)
- pei.exe (PID: 6720)
- DownSysSoft.exe (PID: 5232)
- KB824105-x86-ENU.exe (PID: 6984)
- radbxnzdxbd.exe (PID: 6952)
- SP.exe (PID: 3984)
- Paraguay.pif (PID: 6692)
- %5Binstall%5D.exe (PID: 6704)
- server.exe (PID: 3684)
- QQ.exe (PID: 2400)
- %5Binstall%5D.exe (PID: 6656)
- mimikatz.exe (PID: 6700)
- Population.exe (PID: 7108)
Disables trace logs
- 4363463463464363463463463.exe (PID: 6512)
- KB824105-x86-ENU.exe (PID: 6984)
Reads Environment values
- 4363463463464363463463463.exe (PID: 6512)
- KB824105-x86-ENU.exe (PID: 6984)
Reads the machine GUID from the registry
- 4363463463464363463463463.exe (PID: 6512)
- sylsplvc.exe (PID: 6820)
- sysmablsvr.exe (PID: 6728)
- sysmysldrv.exe (PID: 5116)
- KB824105-x86-ENU.exe (PID: 6984)
- SP.exe (PID: 3984)
- sysarddrvs.exe (PID: 6188)
- server.exe (PID: 3684)
Checks proxy server information
- 4363463463464363463463463.exe (PID: 6512)
- sysmablsvr.exe (PID: 6728)
- sylsplvc.exe (PID: 6820)
- 2861732127.exe (PID: 640)
- sysmysldrv.exe (PID: 5116)
- 2789214706.exe (PID: 6156)
- 1894712399.exe (PID: 2180)
- tpeinf.exe (PID: 6936)
- npp.exe (PID: 6540)
- sysarddrvs.exe (PID: 6188)
- pei.exe (PID: 6720)
- DownSysSoft.exe (PID: 5232)
- KB824105-x86-ENU.exe (PID: 6984)
- server.exe (PID: 3684)
Process checks computer location settings
- 4363463463464363463463463.exe (PID: 6512)
- sysmysldrv.exe (PID: 5116)
- sysarddrvs.exe (PID: 6188)
- ChatLife.exe (PID: 6956)
Reads the software policy settings
- 4363463463464363463463463.exe (PID: 6512)
- server.exe (PID: 3684)
Creates files or folders in the user directory
- sysmablsvr.exe (PID: 6728)
- sysmysldrv.exe (PID: 5116)
- 2789214706.exe (PID: 6156)
- 1894712399.exe (PID: 2180)
- wupgrdsv.exe (PID: 5304)
- tpeinf.exe (PID: 6936)
- Paraguay.pif (PID: 2992)
- sysarddrvs.exe (PID: 6188)
- DownSysSoft.exe (PID: 5232)
Create files in a temporary directory
- sysmablsvr.exe (PID: 6728)
- sylsplvc.exe (PID: 6820)
- 2861732127.exe (PID: 640)
- sysmysldrv.exe (PID: 5116)
- 2789214706.exe (PID: 6156)
- 1894712399.exe (PID: 2180)
- wupgrdsv.exe (PID: 5304)
- tpeinf.exe (PID: 6936)
- npp.exe (PID: 6540)
- ChatLife.exe (PID: 6956)
- sysarddrvs.exe (PID: 6188)
- pei.exe (PID: 6720)
- DownSysSoft.exe (PID: 5232)
- wupgrdsv.exe (PID: 6228)
- radbxnzdxbd.exe (PID: 6952)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6688)
- powershell.exe (PID: 4664)
- powershell.exe (PID: 6536)
- powershell.exe (PID: 3276)
- powershell.exe (PID: 6316)
- powershell.exe (PID: 4780)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6688)
- powershell.exe (PID: 3276)
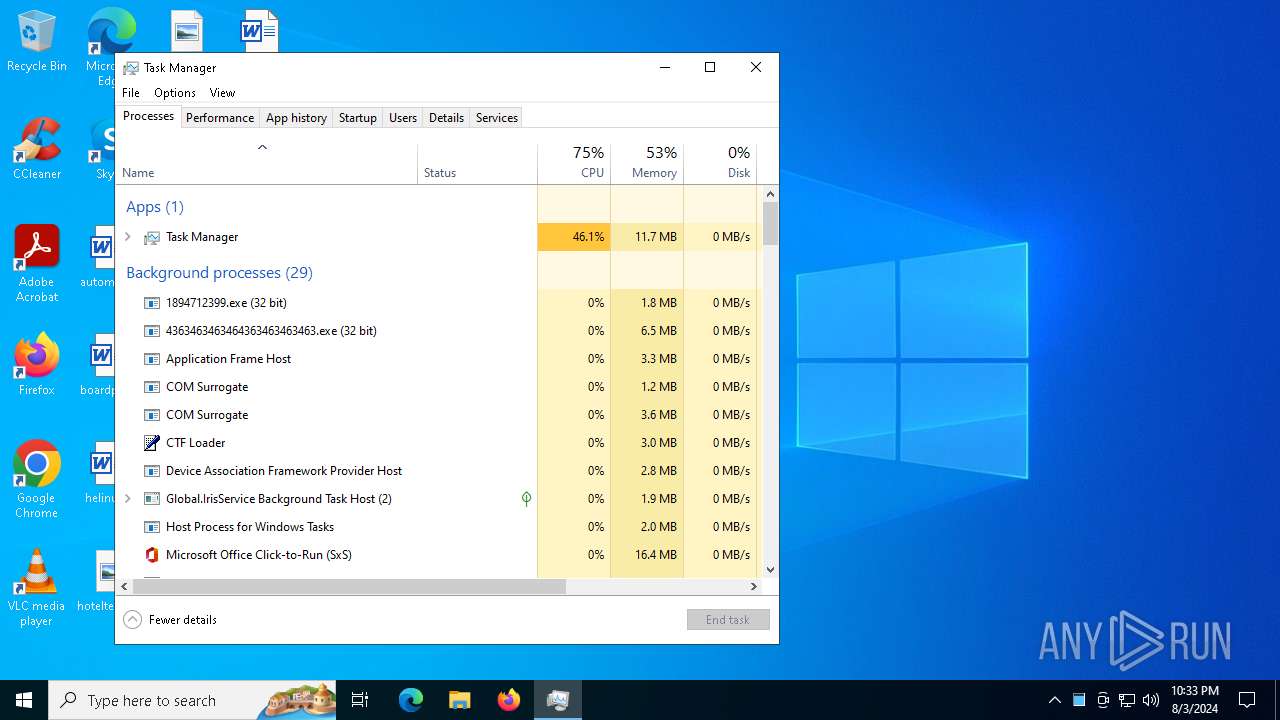
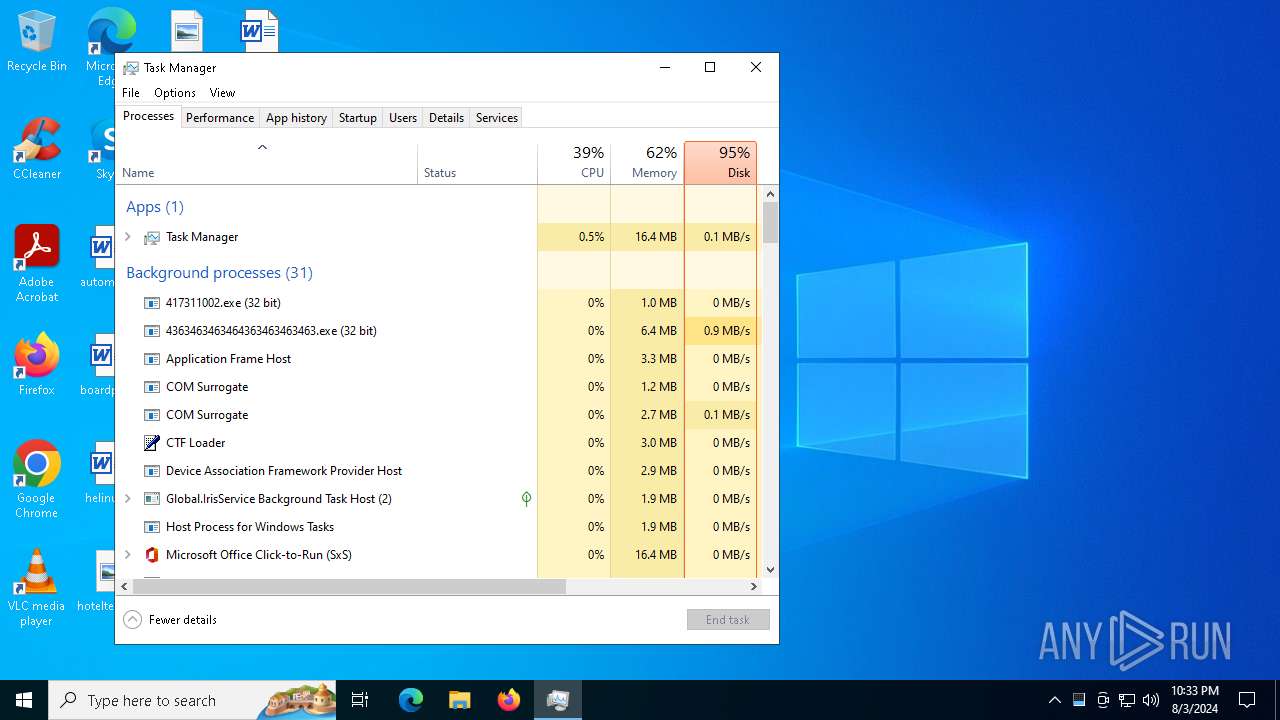
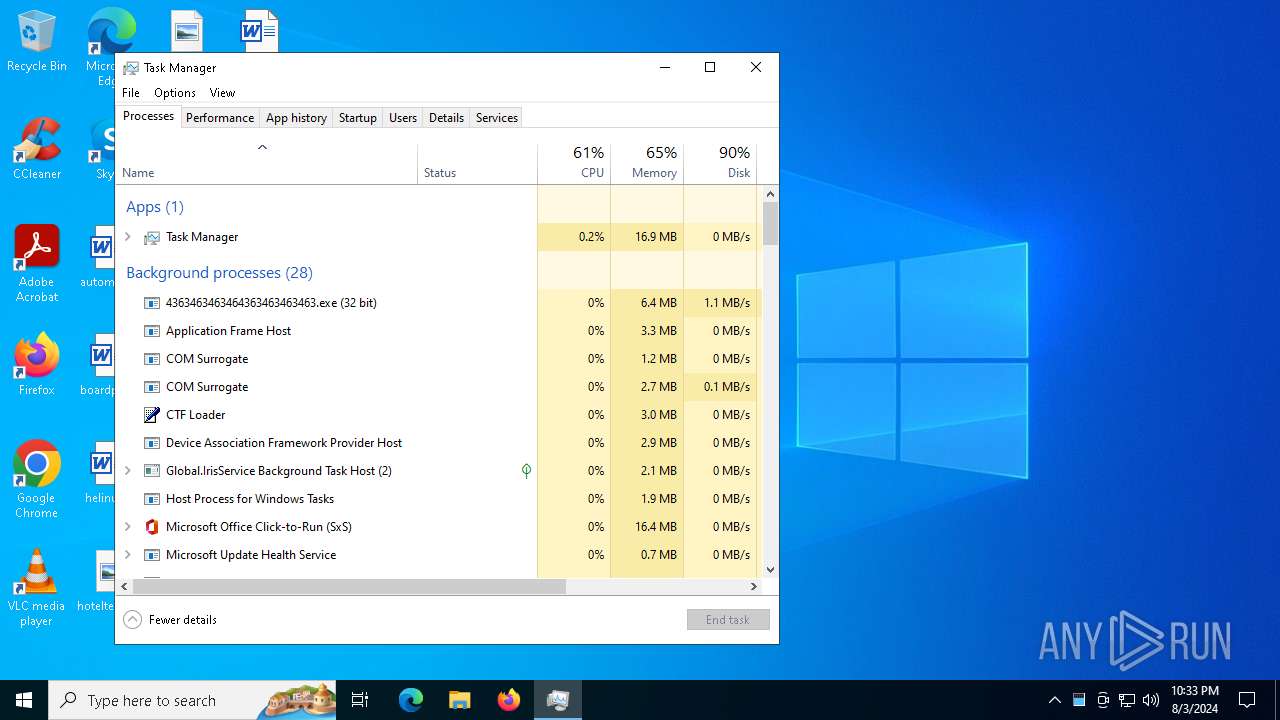
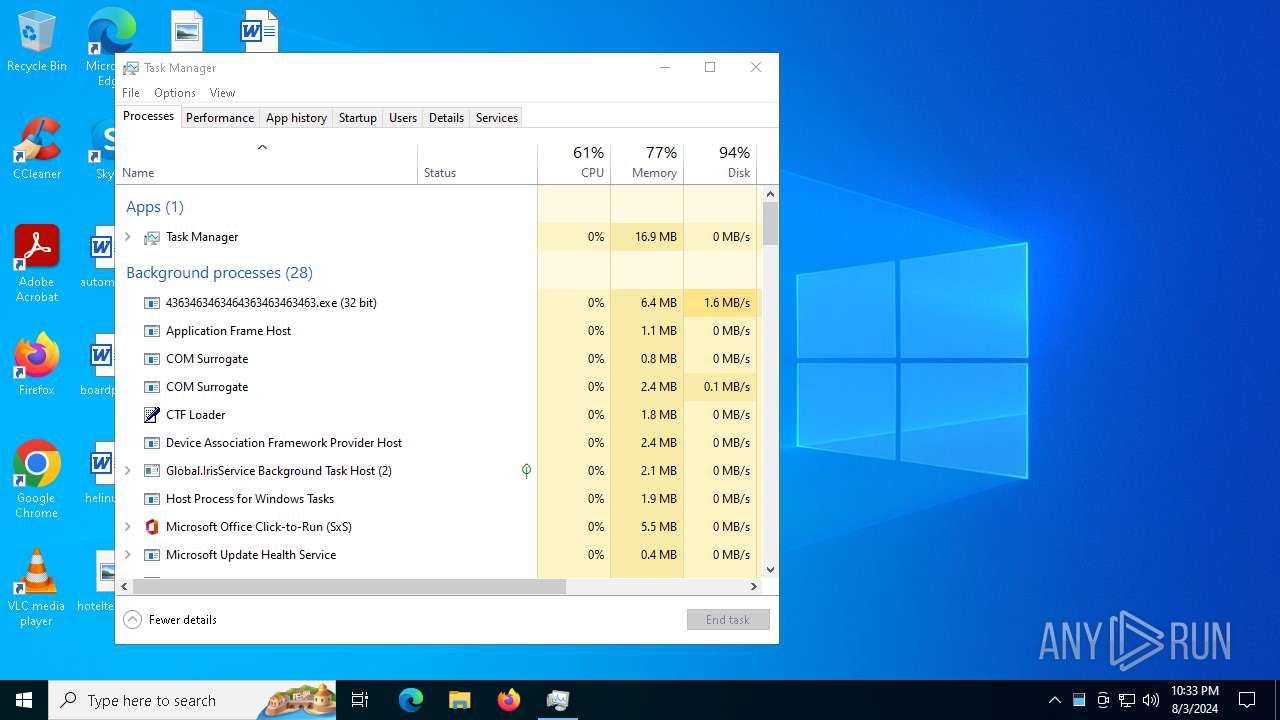
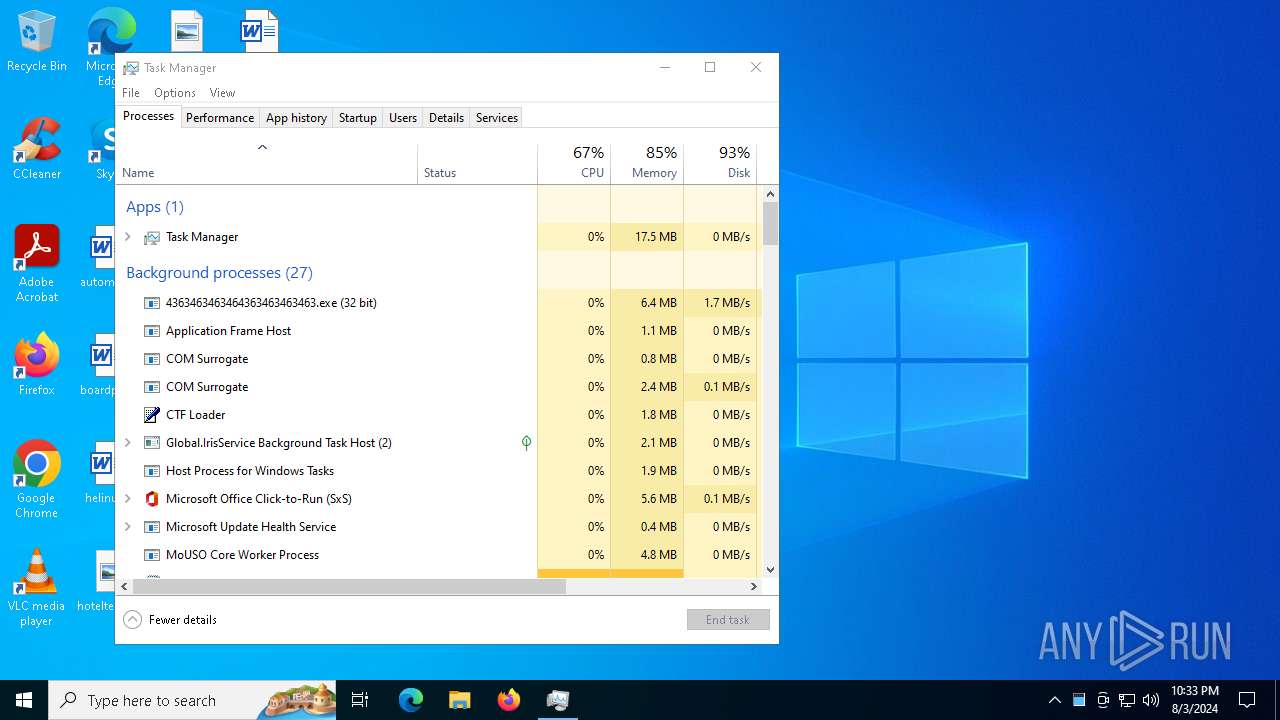
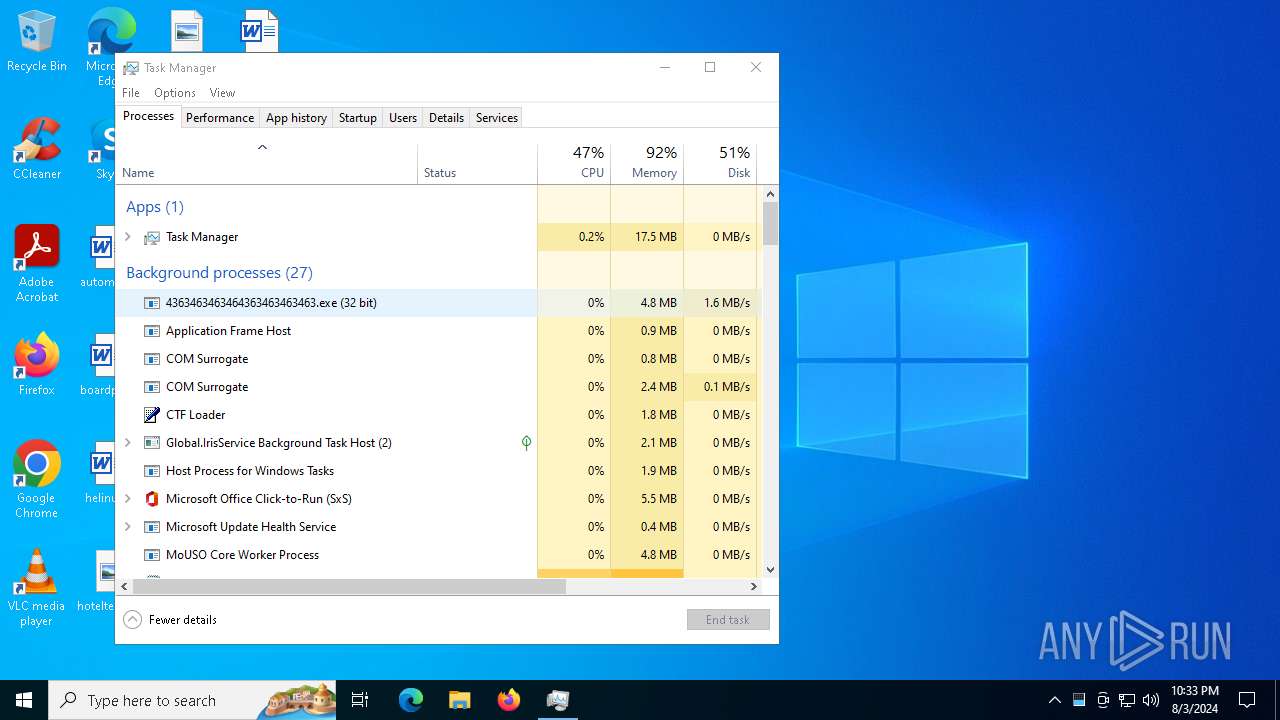
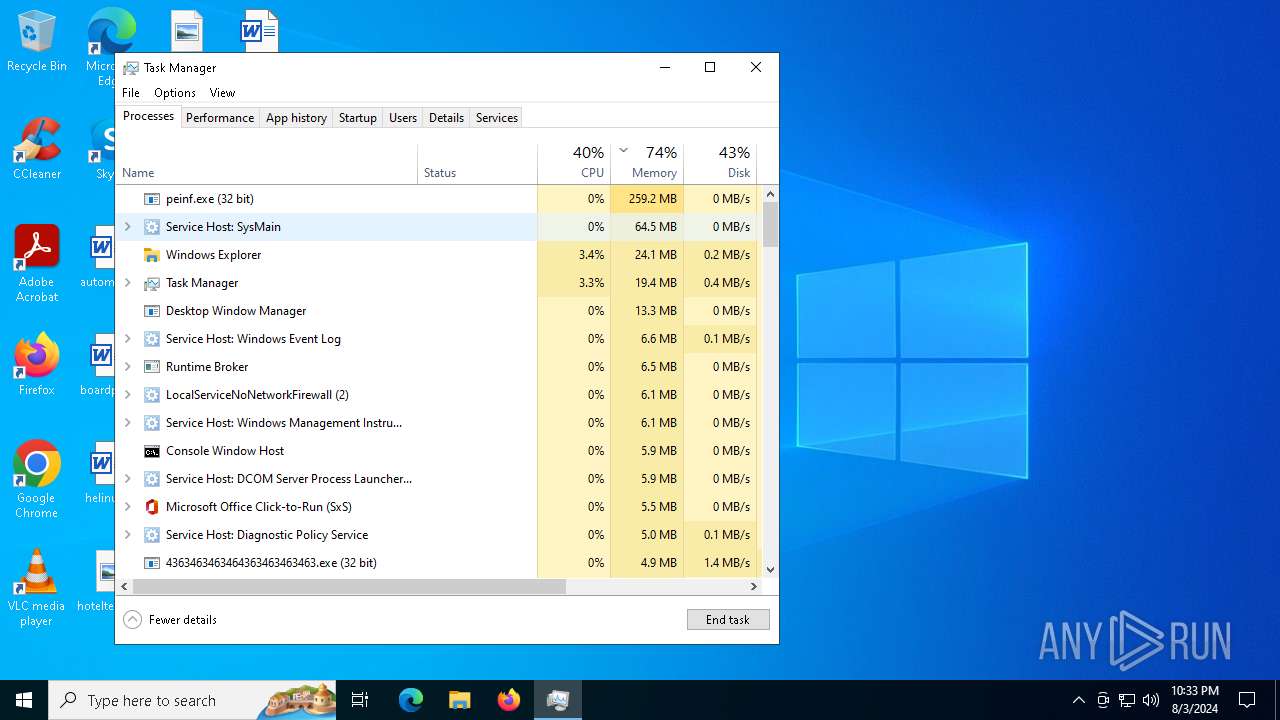
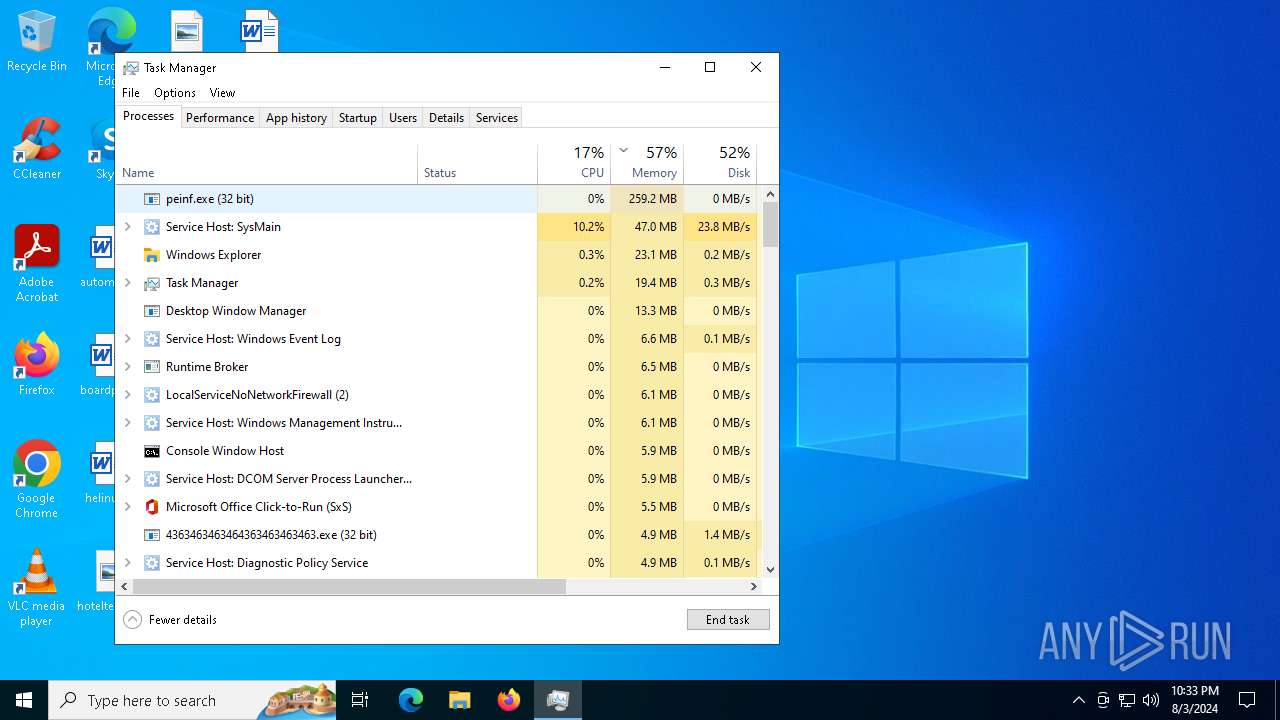
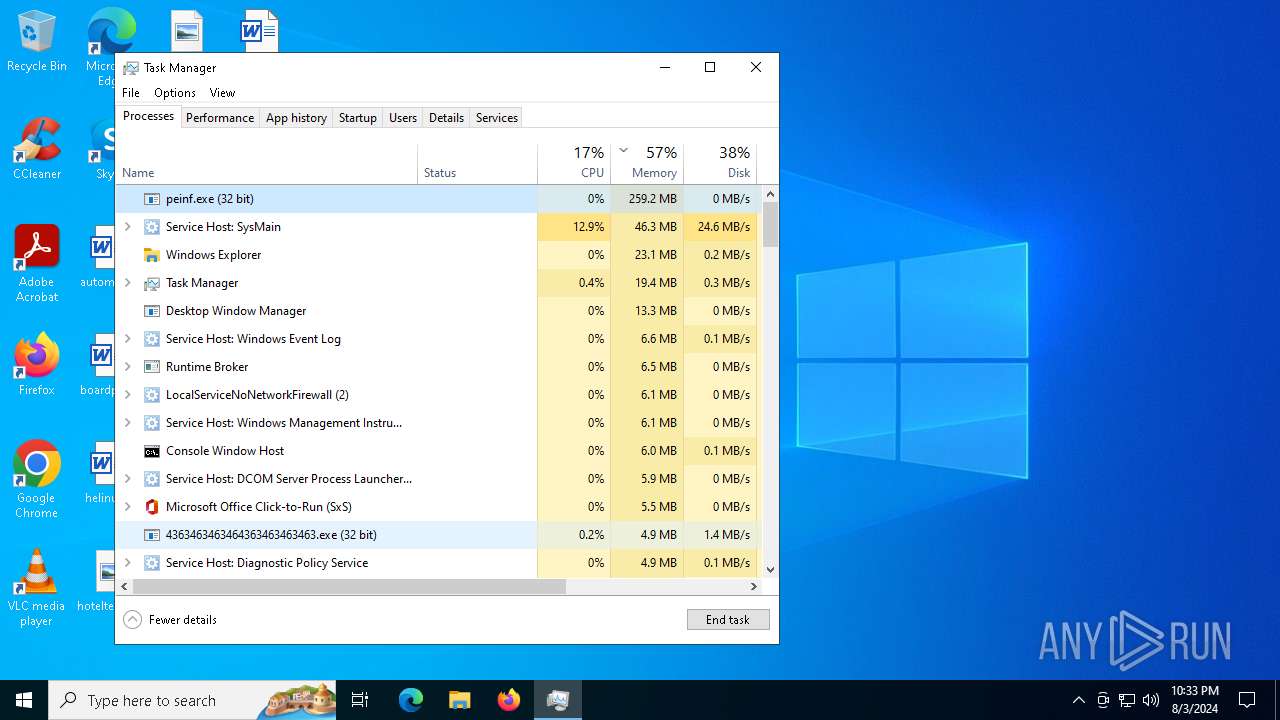
Manual execution by a user
- Taskmgr.exe (PID: 2628)
- Taskmgr.exe (PID: 6680)
- powershell.exe (PID: 4664)
- powershell.exe (PID: 6536)
- notepad.exe (PID: 320)
- schtasks.exe (PID: 2152)
- powershell.exe (PID: 4780)
- schtasks.exe (PID: 2648)
- powershell.exe (PID: 6316)
- notepad.exe (PID: 2476)
- %5Binstall%5D.exe (PID: 964)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 6680)
Creates files in the program directory
- MoUsoCoreWorker.exe (PID: 6392)
Reads the time zone
- MoUsoCoreWorker.exe (PID: 6392)
Reads mouse settings
- Paraguay.pif (PID: 2992)
- DownSysSoft.exe (PID: 5232)
- Downdd.exe (PID: 2248)
UPX packer has been detected
- %5Binstall%5D.exe (PID: 6656)
- %5Binstall%5D.exe (PID: 6704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RisePro
(PID) Process(6692) Paraguay.pif
C2 (1)3.36.173.8:50500
Strings (55)\Signal
\OpenVPN Connect\profiles
\tlauncher_profiles.json
\Local Storage
\Microsoft\Skype for Desktop\Local Storage
\GHISLER\wcx_ftp.ini
\config.json
\.purple
\ey_tokens.txt
\Growtopia
\Element\Local Storage
\save.dat
frug?0
\launcher_msa_credentials.bin
\TLauncher
\OpenVPN Connect
\databases
\Games
\accounts.txt
\TotalCommander
UaEt,
VaultCloseVault
\.minecraft\launcher_msa_credentials.bin
\Element
\.lunarclient\settings\games\accounts.txt
\Growtopia\save.dat
\Skype
\FeatherClient
\launcher_accounts.json
C:\program files\steam
\wcx_ftp.ini
logins
C:\program files (x86)\steam
\Steam
\launcher_profiles.json
S,{w_6
\.minecraft\launcher_accounts.json
\Battle.net
\config
\accounts.xml
WSASend
\Messengers
\Session Storage
J~|Hw
\.feather\accounts.json
\LunarClient
APPDATA
\.minecraft\launcher_profiles.json
\accounts.json
VaultOpenVault
VaultGetItem
\Minecraft
\FileZilla
\Pidgin
\ICQ\0001
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:22 08:29:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 5632 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3552 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | 4363463463464363463463463.exe |
| LegalCopyright: | |
| OriginalFileName: | 4363463463464363463463463.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
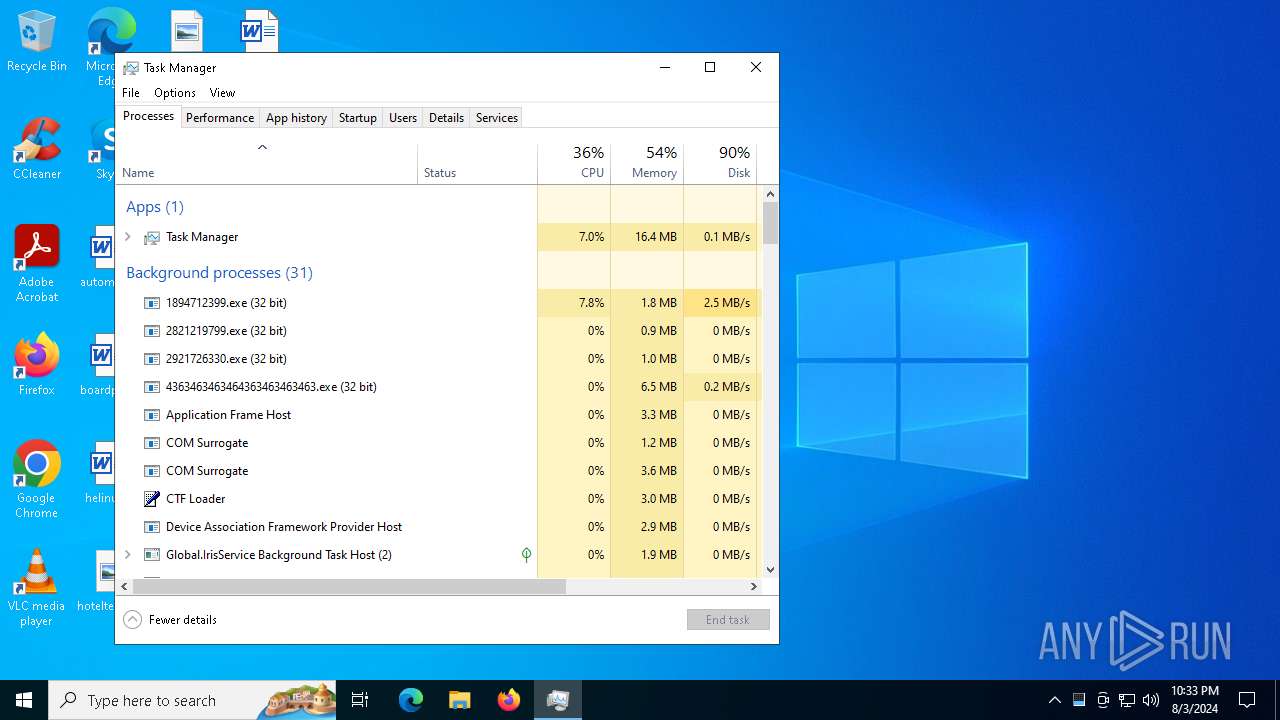
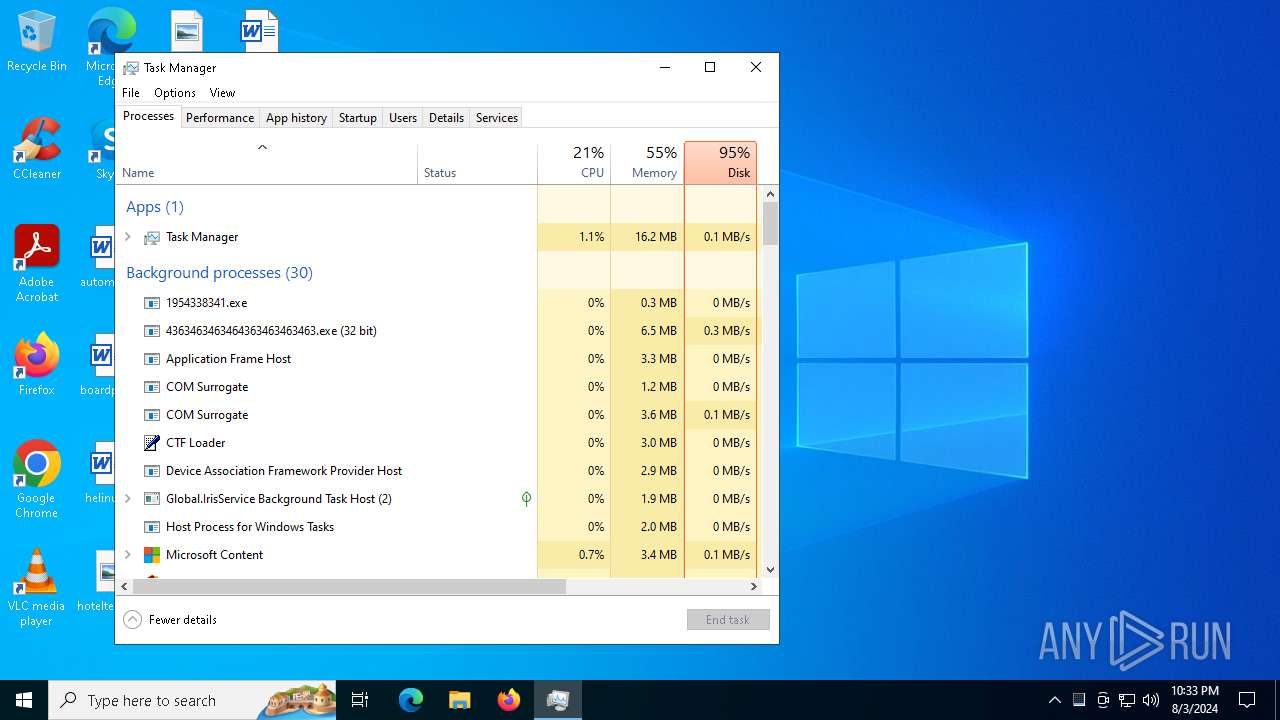
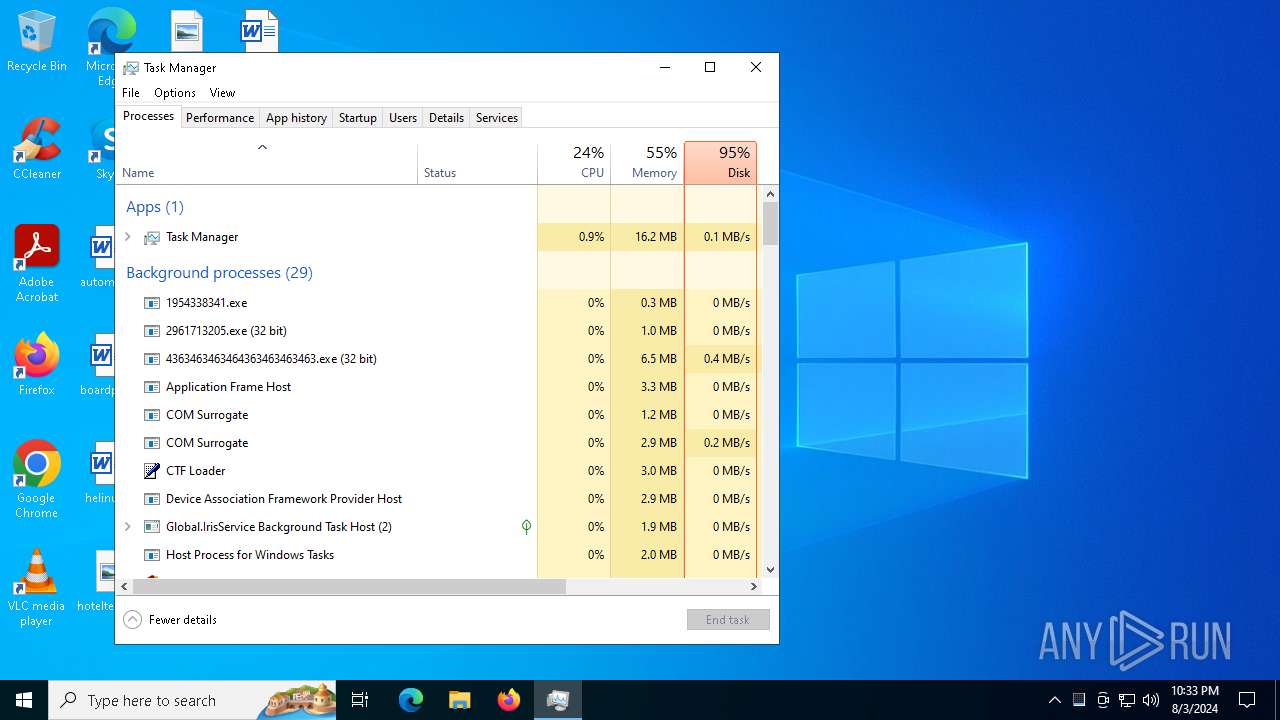
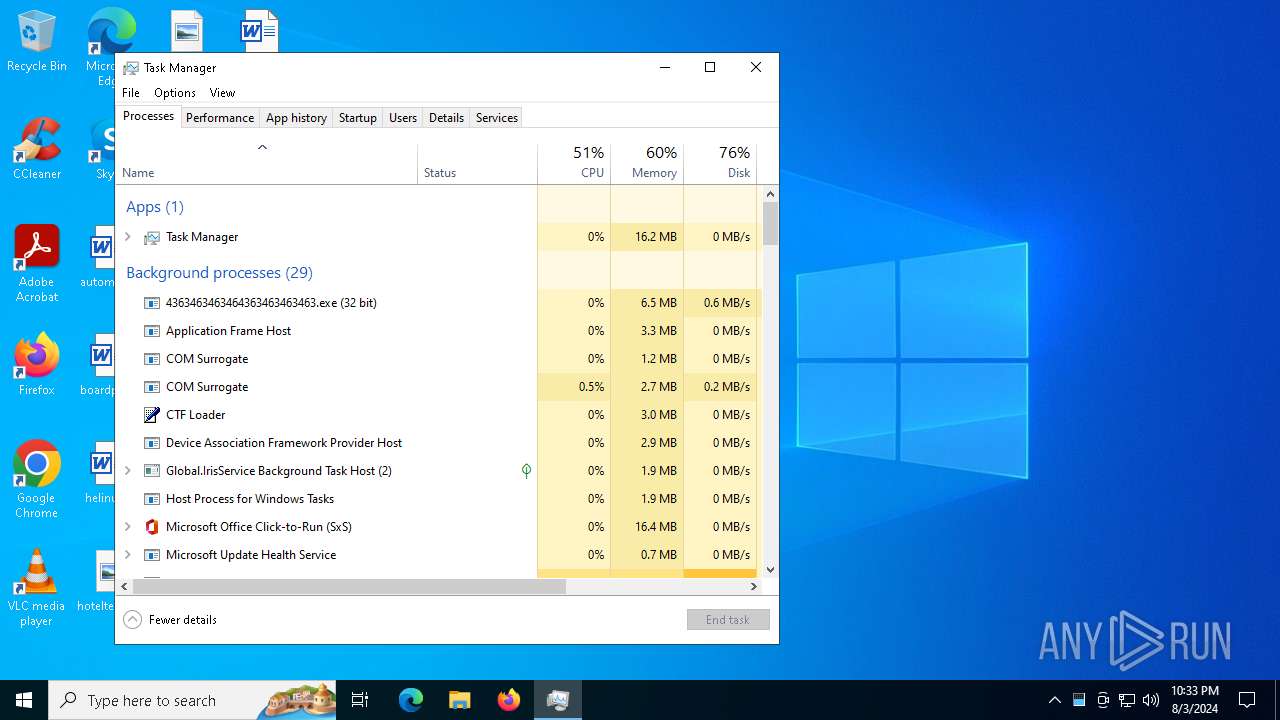
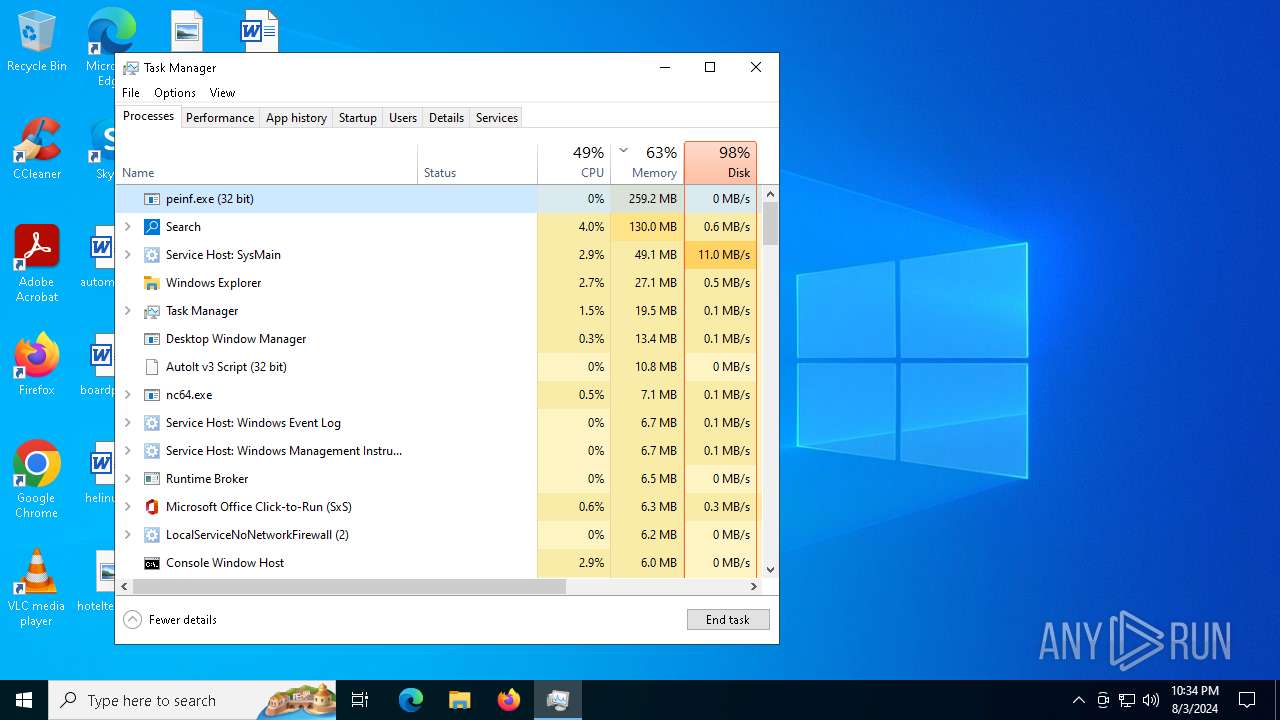
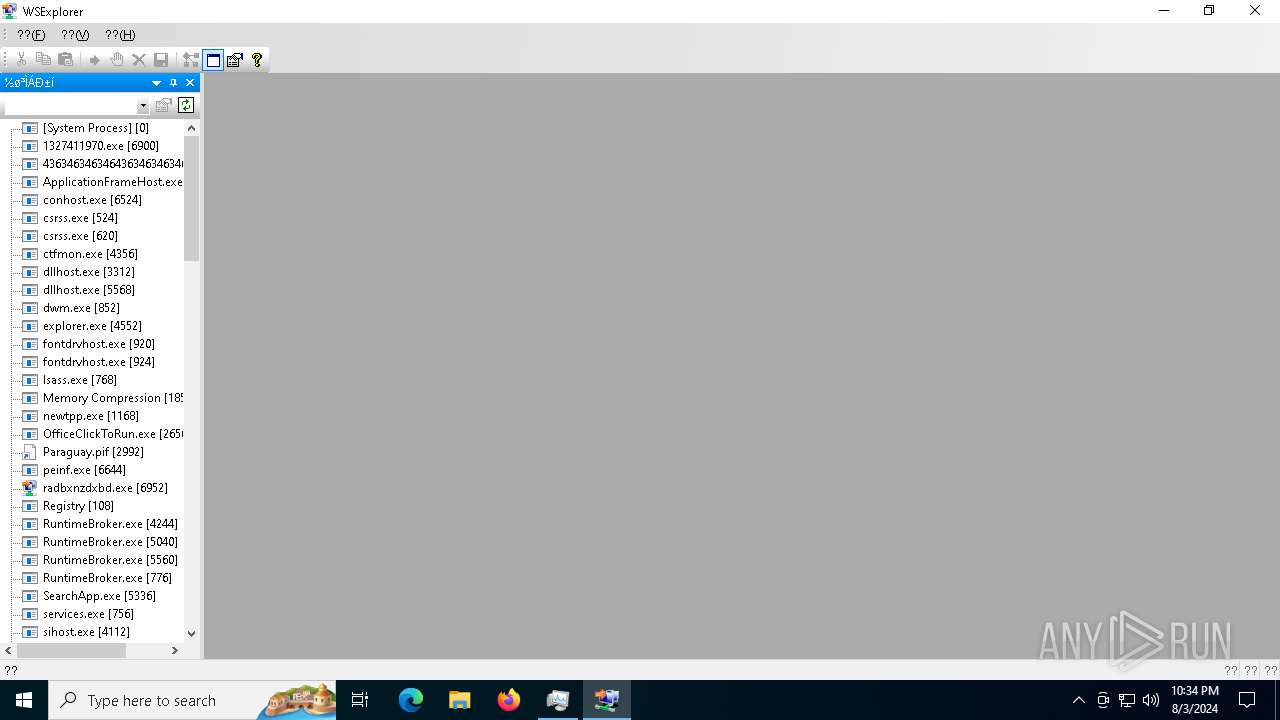
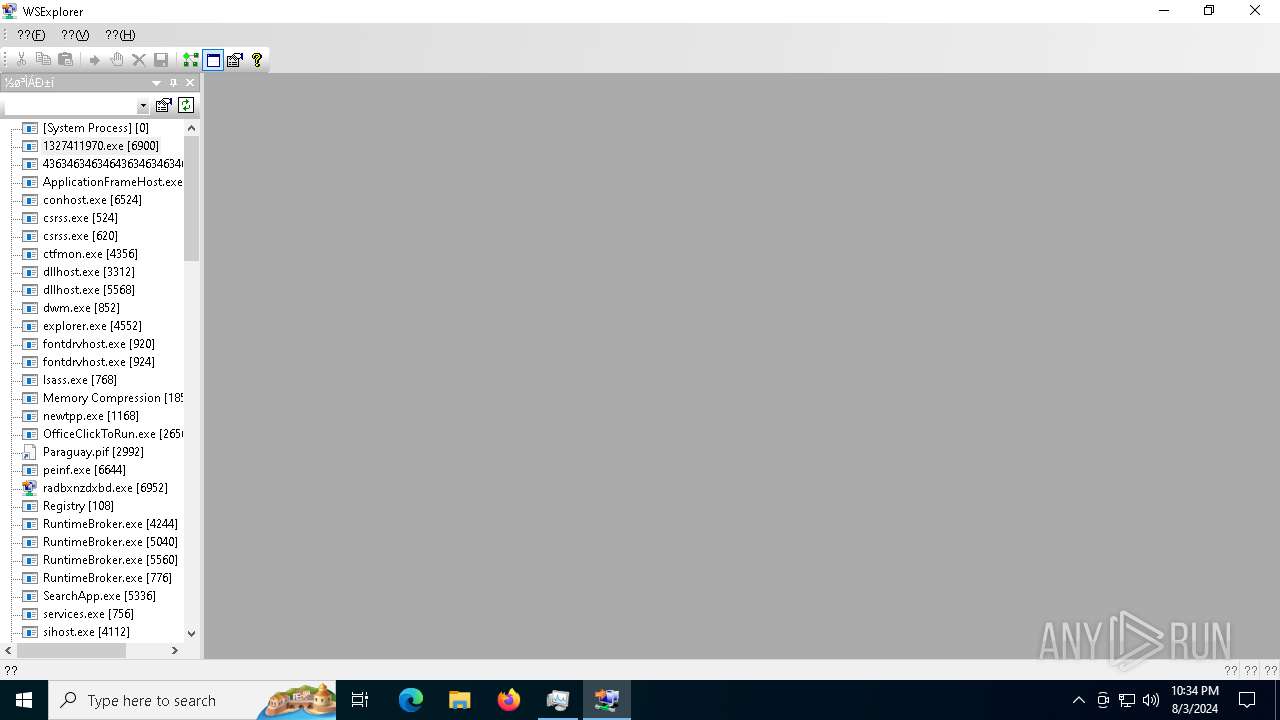
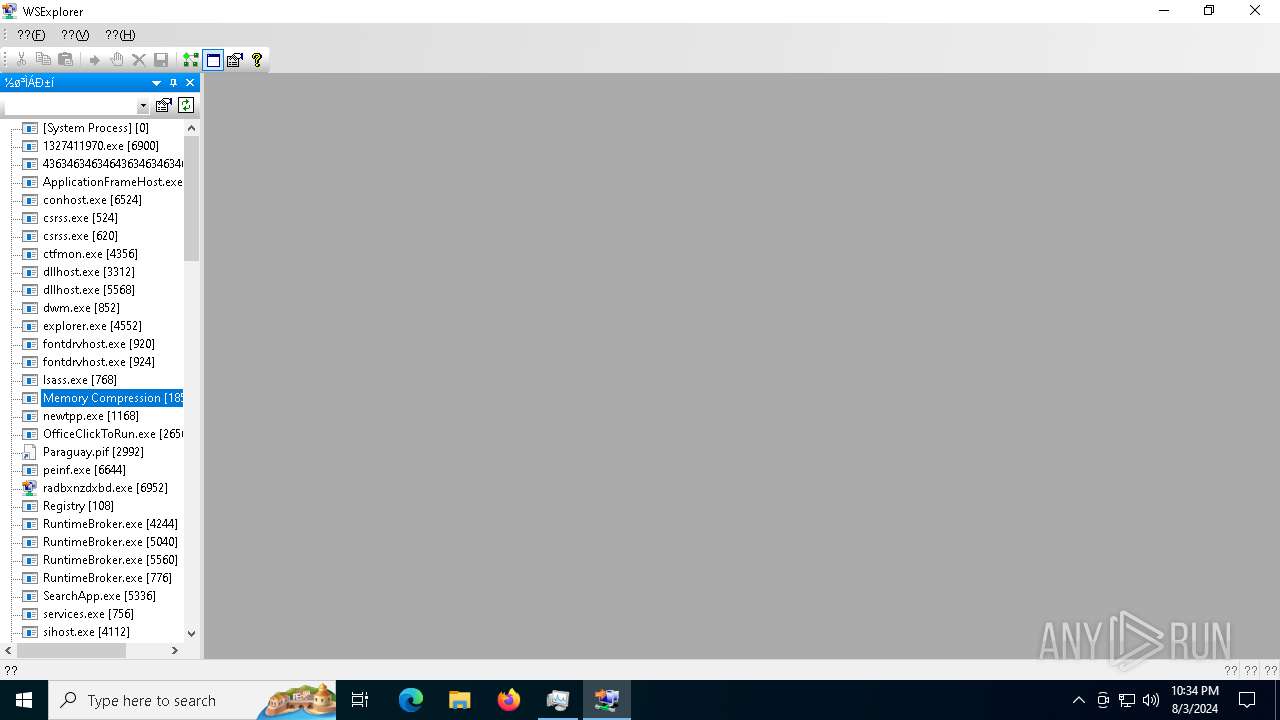
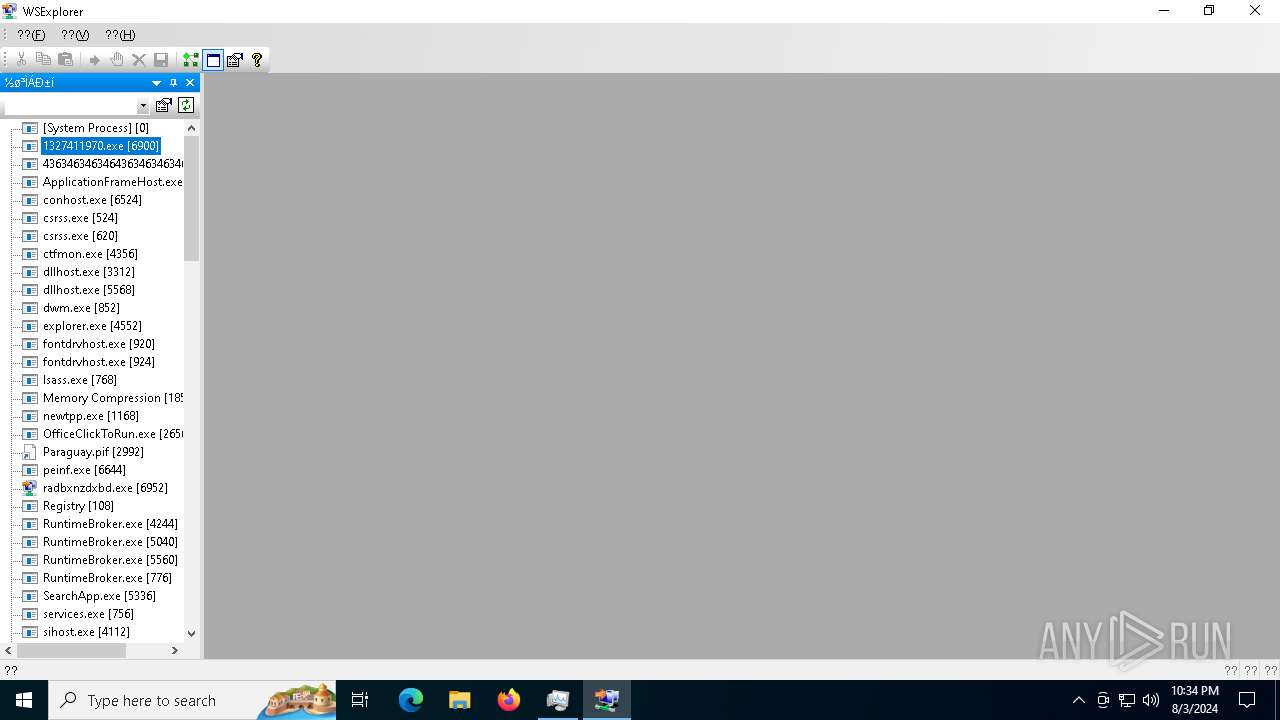
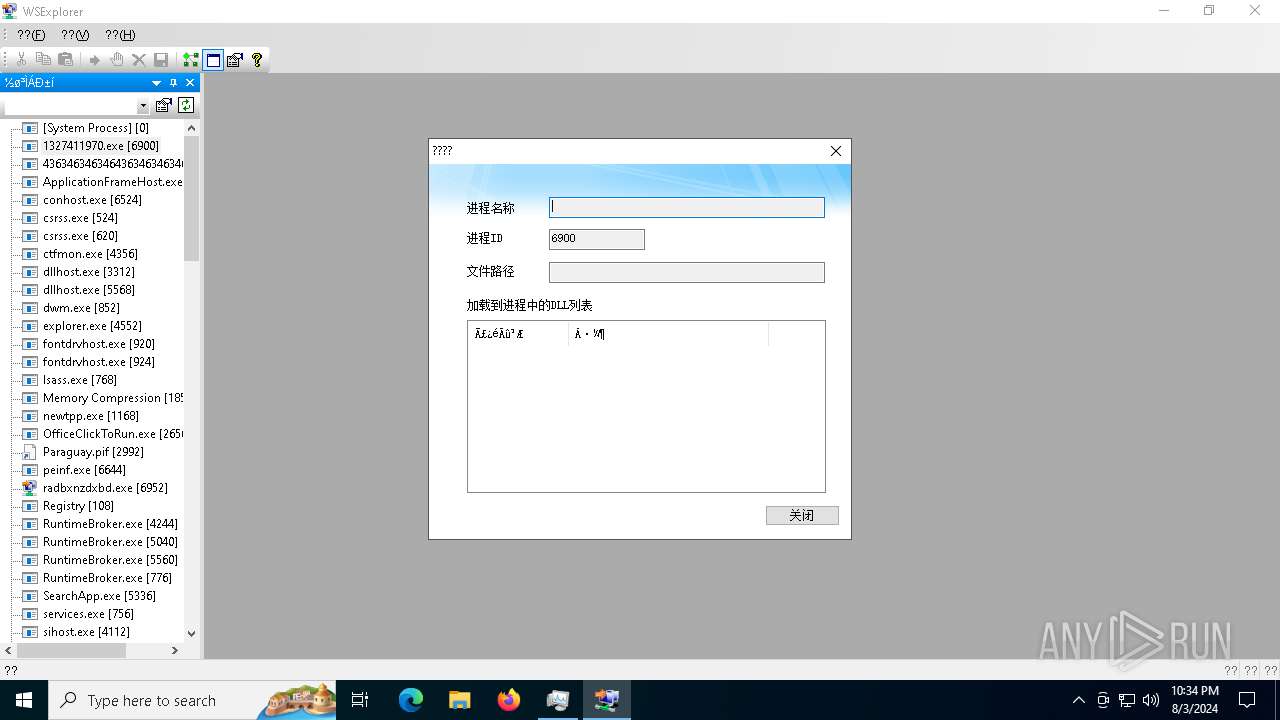
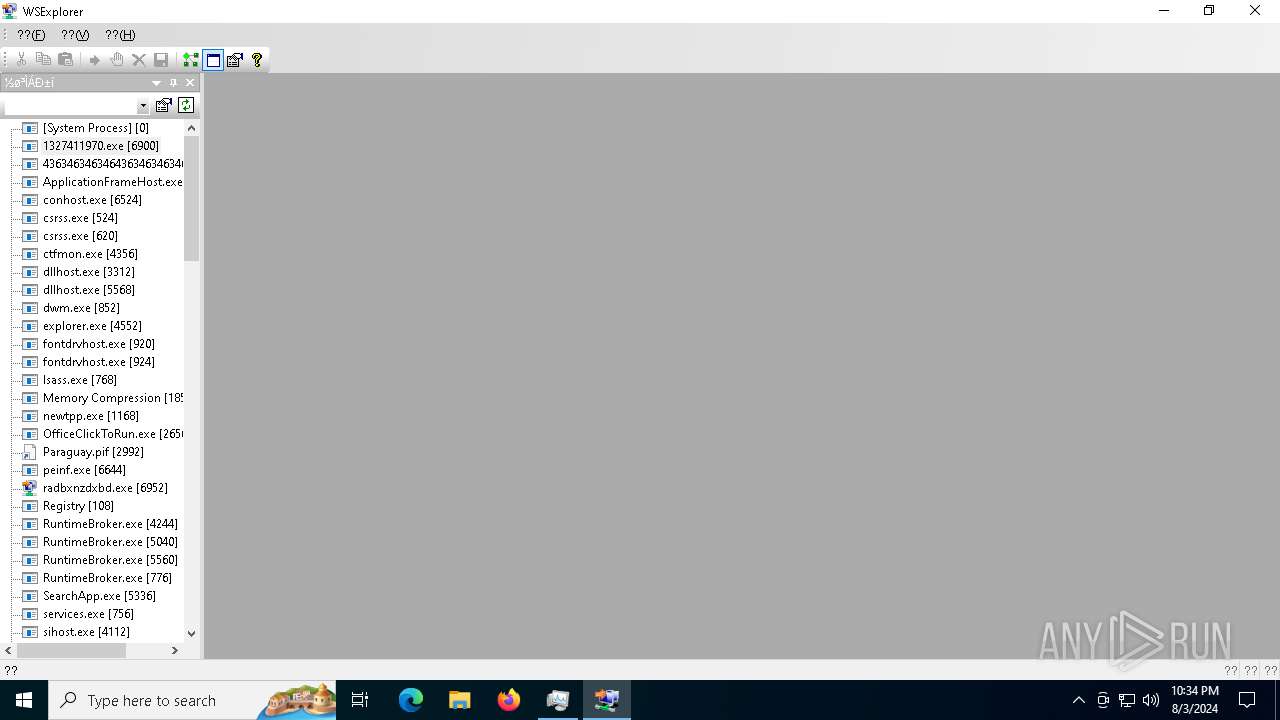
Total processes
272
Monitored processes
135
Malicious processes
27
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4 | System | [System Process] | |||||||||||||
User: SYSTEM Integrity Level: SYSTEM | |||||||||||||||
| 208 | C:\Users\admin\AppData\Local\Temp\2990227768.exe | C:\Users\admin\AppData\Local\Temp\2990227768.exe | — | sylsplvc.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 304 | C:\Users\admin\AppData\Local\Temp\411220961.exe | C:\Users\admin\AppData\Local\Temp\411220961.exe | — | sysarddrvs.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 320 | C:\WINDOWS\System32\notepad.exe | C:\Windows\System32\notepad.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | C:\Users\admin\AppData\Local\Temp\2861732127.exe | C:\Users\admin\AppData\Local\Temp\2861732127.exe | sysmablsvr.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 872 | C:\Users\admin\AppData\Local\Temp\363014155.exe | C:\Users\admin\AppData\Local\Temp\363014155.exe | — | sylsplvc.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 876 | "C:\Windows\System32\cmd.exe" /c sc stop UsoSvc & sc stop WaaSMedicSvc & sc stop wuauserv & sc stop DoSvc & sc stop BITS | C:\Windows\SysWOW64\cmd.exe | — | sysarddrvs.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 964 | "C:\Users\admin\Desktop\Files\%5Binstall%5D.exe" | C:\Users\admin\Desktop\Files\%5Binstall%5D.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1168 | cmd /c md 768318 | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1168 | "C:\Users\admin\Desktop\Files\newtpp.exe" | C:\Users\admin\Desktop\Files\newtpp.exe | — | 4363463463464363463463463.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
88 163
Read events
87 596
Write events
563
Delete events
4
Modification events
| (PID) Process: | (6512) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6512) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6512) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6512) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6512) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6512) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6512) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6512) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6512) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6512) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
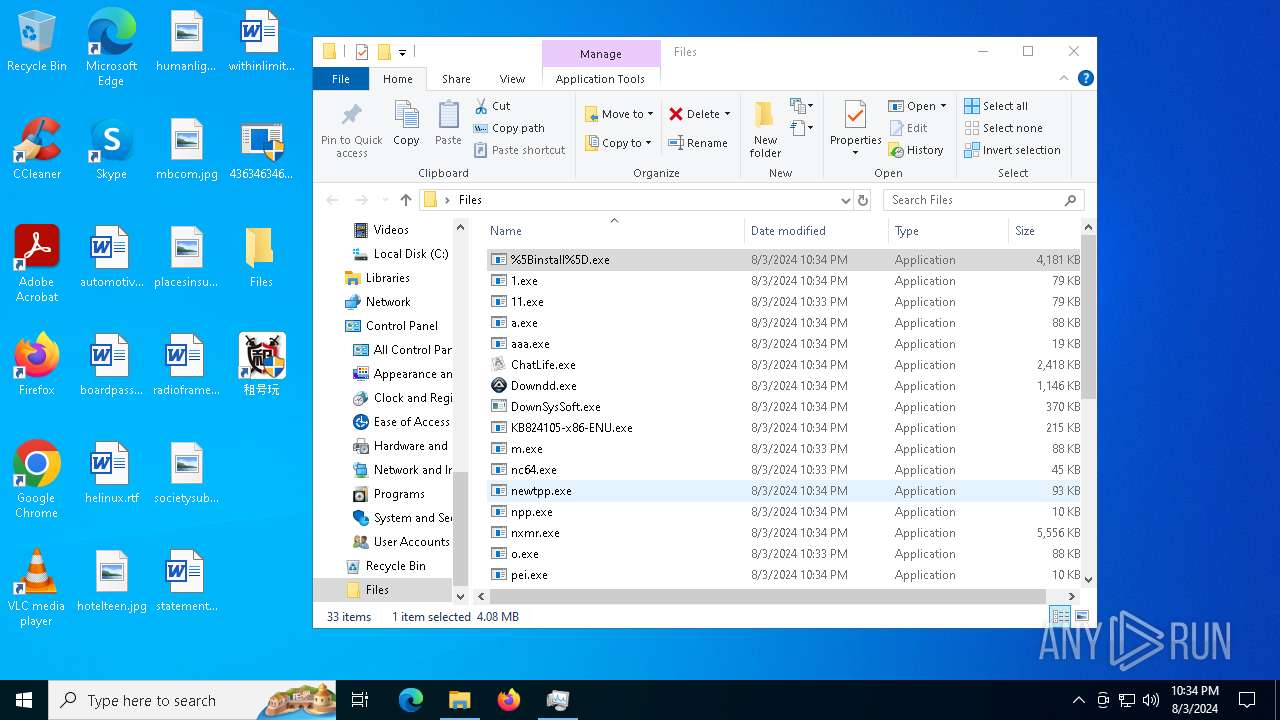
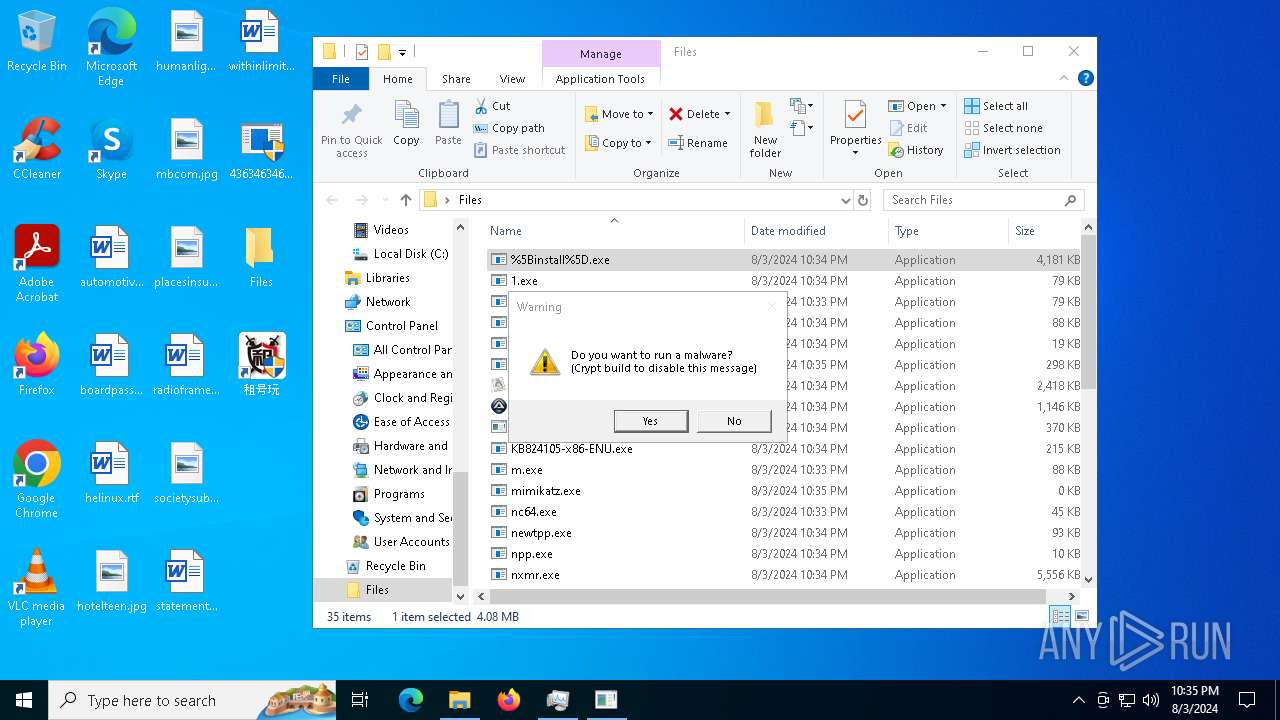
Executable files
109
Suspicious files
117
Text files
25
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6512 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\t1.exe | executable | |
MD5:ABABCA6D12D96E8DD2F1D7114B406FAE | SHA256:A992920E64A64763F3DD8C2A431A0F5E56E5B3782A1496DE92BC80EE71CCA5BA | |||
| 6512 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\pi.exe | executable | |
MD5:1E8A2ED2E3F35620FB6B8C2A782A57F3 | SHA256:3F16F4550826076B2C8CD7B392EE649AEB06740328658A2D30C3D2002C6B7879 | |||
| 6664 | pi.exe | C:\Windows\sylsplvc.exe | executable | |
MD5:1E8A2ED2E3F35620FB6B8C2A782A57F3 | SHA256:3F16F4550826076B2C8CD7B392EE649AEB06740328658A2D30C3D2002C6B7879 | |||
| 6728 | sysmablsvr.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\1[1] | binary | |
MD5:ACC5E9F20EF10165FF0F014F9600E868 | SHA256:17711519F3938EE9C93E1B15ADE22A17CFA70FFFCE02C2B1B2C77959626AB6DE | |||
| 6684 | t1.exe | C:\Windows\sysmablsvr.exe | executable | |
MD5:ABABCA6D12D96E8DD2F1D7114B406FAE | SHA256:A992920E64A64763F3DD8C2A431A0F5E56E5B3782A1496DE92BC80EE71CCA5BA | |||
| 6512 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\pp.exe | executable | |
MD5:ABABCA6D12D96E8DD2F1D7114B406FAE | SHA256:A992920E64A64763F3DD8C2A431A0F5E56E5B3782A1496DE92BC80EE71CCA5BA | |||
| 6820 | sylsplvc.exe | C:\Users\admin\tbnds.dat | binary | |
MD5:4715F74EC3AE4A45E3674706C300AC3E | SHA256:867A7FEC18E47338686973B4357B6AECCD1A977B5F0C8209782C8D88CC24925D | |||
| 6820 | sylsplvc.exe | C:\Users\admin\AppData\Local\Temp\72094654.exe | binary | |
MD5:E57F9E2FC24A1ACE0267A7962C9E465E | SHA256:AA66DF748EF74DF48C7D1C2954C49702B15E95787B1D3B562DBA50894ABC0910 | |||
| 6728 | sysmablsvr.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\3[1] | binary | |
MD5:713BA739BEFD6B3A3B3472457334EA3C | SHA256:2B3EF263C2723822ADFBE11CC2B8DB3184B34552FCAD496B2877981022273ABE | |||
| 6644 | peinf.exe | C:\ProgramData\Package Cache\{050d4fc8-5d48-4b8f-8972-47c82c46020f}\vcredist_x64.exe | executable | |
MD5:71A1059EDCBB01D76C9FBCCCFB16294C | SHA256:B0B12DDC7666B41D13F1909283E2465EB59E492A417D2E9A3A7F0E4337591FB0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
74
TCP/UDP connections
269
DNS requests
42
Threats
229
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6512 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.84:80 | http://a012a656-f566-48a1-afad-3dcc46018380.random.tsrv1.ws/peinf.exe | unknown | — | — | malicious |
6928 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6728 | sysmablsvr.exe | GET | 200 | 185.215.113.66:80 | http://185.215.113.66/3 | unknown | — | — | unknown |
6728 | sysmablsvr.exe | GET | — | 185.215.113.66:80 | http://185.215.113.66/3 | unknown | — | — | unknown |
6156 | 2789214706.exe | GET | 200 | 185.215.113.66:80 | http://185.215.113.66/peinf.exe | unknown | — | — | unknown |
6964 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5116 | sysmysldrv.exe | GET | — | 185.215.113.66:80 | http://185.215.113.66/1 | unknown | — | — | unknown |
5116 | sysmysldrv.exe | GET | 200 | 185.215.113.66:80 | http://185.215.113.66/1 | unknown | — | — | unknown |
6728 | sysmablsvr.exe | GET | 404 | 185.215.113.66:80 | http://185.215.113.66/4 | unknown | — | — | unknown |
6512 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.84:80 | http://fd8a7ef9-faae-4c3c-814a-376eb024783e.random.tsrv1.ws/pi.exe | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3140 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2464 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6512 | 4363463463464363463463463.exe | 151.101.2.49:443 | urlhaus.abuse.ch | FASTLY | US | unknown |
6512 | 4363463463464363463463463.exe | 185.215.113.84:80 | a012a656-f566-48a1-afad-3dcc46018380.random.tsrv1.ws | 1337team Limited | SC | unknown |
6512 | 4363463463464363463463463.exe | 185.215.113.66:80 | skyjsihnqew.fihsifuiiusuiuduf.com | 1337team Limited | SC | unknown |
6512 | 4363463463464363463463463.exe | 121.61.248.112:808 | — | Chinanet | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
a012a656-f566-48a1-afad-3dcc46018380.random.tsrv1.ws |
| malicious |
fd8a7ef9-faae-4c3c-814a-376eb024783e.random.tsrv1.ws |
| malicious |
skyjsihnqew.fihsifuiiusuiuduf.com |
| unknown |
d166ab3b-91ab-410f-a50d-c702fa55858d.random.tsrv1.ws |
| malicious |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6512 | 4363463463464363463463463.exe | Misc activity | ET INFO Packed Executable Download |
6512 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile |
6512 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6512 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6512 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile |
6512 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6512 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6512 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile |
6512 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6512 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
36 ETPRO signatures available at the full report