| File name: | 4363463463464363463463463.exe |
| Full analysis: | https://app.any.run/tasks/af21ddcc-cb4f-414e-8924-a65b27d2a13b |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | August 22, 2024, 05:36:34 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 2A94F3960C58C6E70826495F76D00B85 |
| SHA1: | E2A1A5641295F5EBF01A37AC1C170AC0814BB71A |
| SHA256: | 2FCAD226B17131DA4274E1B9F8F31359BDD325C9568665F08FD1F6C5D06A23CE |
| SSDEEP: | 192:2we8sGKE6MqyG7c20L7BIW12n/ePSmzkTInu8stYcFwVc03KY:9e8sGKfMqyGg20PKn/cRaInuptYcFwVY |
MALICIOUS
Changes the autorun value in the registry
- s.exe (PID: 6848)
- 1.exe (PID: 7060)
- 794428842.exe (PID: 6248)
- pi.exe (PID: 7176)
- v.exe (PID: 7728)
- nano.exe (PID: 7732)
- DiskUtility.exe (PID: 3236)
- 440322220.exe (PID: 1168)
Changes the Windows auto-update feature
- sysmablsvr.exe (PID: 6908)
- sysarddrvs.exe (PID: 7132)
- sysmysldrv.exe (PID: 6300)
- syslyqdvr.exe (PID: 7640)
Creates or modifies Windows services
- sysmablsvr.exe (PID: 6908)
- sysarddrvs.exe (PID: 7132)
- sysmysldrv.exe (PID: 6300)
Changes appearance of the Explorer extensions
- sysmablsvr.exe (PID: 6908)
- sysarddrvs.exe (PID: 7132)
- sysmysldrv.exe (PID: 6300)
- syslyqdvr.exe (PID: 7640)
Changes Security Center notification settings
- sysmablsvr.exe (PID: 6908)
- sysarddrvs.exe (PID: 7132)
- sysmysldrv.exe (PID: 6300)
- sylsplvc.exe (PID: 2128)
- syslyqdvr.exe (PID: 7640)
PHORPIEX has been detected (SURICATA)
- svchost.exe (PID: 2256)
- sysmablsvr.exe (PID: 6908)
- sysarddrvs.exe (PID: 7132)
- sysmysldrv.exe (PID: 6300)
- 4363463463464363463463463.exe (PID: 6724)
- sylsplvc.exe (PID: 2128)
- syslyqdvr.exe (PID: 7640)
Connects to the CnC server
- svchost.exe (PID: 2256)
- sysmablsvr.exe (PID: 6908)
- sysarddrvs.exe (PID: 7132)
- sysmysldrv.exe (PID: 6300)
- sylsplvc.exe (PID: 2128)
- jsc.exe (PID: 6680)
- jsc.exe (PID: 608)
- notepad.exe (PID: 7968)
- RegAsm.exe (PID: 7888)
- dialer.exe (PID: 7364)
- dialer.exe (PID: 6188)
- jsc.exe (PID: 7888)
- syslyqdvr.exe (PID: 7640)
Adds path to the Windows Defender exclusion list
- sysarddrvs.exe (PID: 7132)
- cmd.exe (PID: 3236)
- sysmysldrv.exe (PID: 6300)
- cmd.exe (PID: 2384)
- explorer.exe (PID: 4552)
- wahost.exe (PID: 8176)
- syslyqdvr.exe (PID: 7640)
- cmd.exe (PID: 6224)
HAUSBOMBER has been detected (YARA)
- 4363463463464363463463463.exe (PID: 6724)
DCRAT has been detected (YARA)
- 4363463463464363463463463.exe (PID: 6724)
Antivirus name has been found in the command line (generic signature)
- findstr.exe (PID: 7220)
- findstr.exe (PID: 7344)
Uses Task Scheduler to autorun other applications
- Community.pif (PID: 7464)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7528)
- wahost.exe (PID: 8176)
Create files in the Startup directory
- cmd.exe (PID: 6624)
PHORPIEX has been detected (YARA)
- sysarddrvs.exe (PID: 7132)
- sysmablsvr.exe (PID: 6908)
- sysmysldrv.exe (PID: 6300)
Actions looks like stealing of personal data
- jsc.exe (PID: 6680)
- jsc.exe (PID: 608)
- aspnet_regiis.exe (PID: 3208)
- RegAsm.exe (PID: 7888)
- peinf.exe (PID: 6604)
- RegAsm.exe (PID: 8008)
- RegAsm.exe (PID: 4784)
- RegAsm.exe (PID: 6216)
- RegAsm.exe (PID: 6776)
- jsc.exe (PID: 7888)
Steals credentials from Web Browsers
- jsc.exe (PID: 6680)
- jsc.exe (PID: 608)
- RegAsm.exe (PID: 7888)
- jsc.exe (PID: 7888)
METASTEALER has been detected (SURICATA)
- jsc.exe (PID: 6680)
- jsc.exe (PID: 608)
- jsc.exe (PID: 7888)
REDLINE has been detected (SURICATA)
- jsc.exe (PID: 6680)
- jsc.exe (PID: 608)
- jsc.exe (PID: 7888)
Stealers network behavior
- jsc.exe (PID: 6680)
- jsc.exe (PID: 608)
- aspnet_regiis.exe (PID: 3208)
- RegAsm.exe (PID: 7888)
- jsc.exe (PID: 7888)
Attempt to connect to SMB server
- System (PID: 4)
Application was injected by another process
- winlogon.exe (PID: 684)
- lsass.exe (PID: 768)
- svchost.exe (PID: 1036)
- dwm.exe (PID: 852)
- svchost.exe (PID: 1472)
- svchost.exe (PID: 1364)
- svchost.exe (PID: 1316)
- svchost.exe (PID: 1508)
- svchost.exe (PID: 1408)
- svchost.exe (PID: 1588)
- svchost.exe (PID: 1620)
- svchost.exe (PID: 1864)
- svchost.exe (PID: 1816)
- svchost.exe (PID: 1628)
- svchost.exe (PID: 1600)
- svchost.exe (PID: 1200)
- svchost.exe (PID: 1208)
- svchost.exe (PID: 1272)
- svchost.exe (PID: 476)
- svchost.exe (PID: 2256)
- svchost.exe (PID: 2184)
- svchost.exe (PID: 2496)
- svchost.exe (PID: 1872)
- svchost.exe (PID: 2412)
- svchost.exe (PID: 2344)
- spoolsv.exe (PID: 2592)
- svchost.exe (PID: 2312)
- svchost.exe (PID: 2788)
- svchost.exe (PID: 2692)
- svchost.exe (PID: 2996)
- svchost.exe (PID: 3012)
- svchost.exe (PID: 1796)
- svchost.exe (PID: 2072)
- svchost.exe (PID: 2160)
- svchost.exe (PID: 2000)
- svchost.exe (PID: 2304)
- svchost.exe (PID: 3056)
- svchost.exe (PID: 3220)
- svchost.exe (PID: 3200)
- svchost.exe (PID: 3084)
- svchost.exe (PID: 3260)
- svchost.exe (PID: 3340)
- svchost.exe (PID: 3496)
- svchost.exe (PID: 3408)
- svchost.exe (PID: 3888)
- sihost.exe (PID: 4112)
- svchost.exe (PID: 4140)
- svchost.exe (PID: 4332)
- svchost.exe (PID: 4184)
- ctfmon.exe (PID: 4356)
- svchost.exe (PID: 4300)
- svchost.exe (PID: 4532)
- svchost.exe (PID: 4808)
- OfficeClickToRun.exe (PID: 2656)
- svchost.exe (PID: 3020)
- svchost.exe (PID: 2968)
- explorer.exe (PID: 4552)
- RuntimeBroker.exe (PID: 5560)
- dllhost.exe (PID: 3312)
- RuntimeBroker.exe (PID: 4244)
- RuntimeBroker.exe (PID: 776)
- dllhost.exe (PID: 5568)
- uhssvc.exe (PID: 536)
- svchost.exe (PID: 5236)
- svchost.exe (PID: 4000)
- svchost.exe (PID: 5256)
- svchost.exe (PID: 1824)
- ApplicationFrameHost.exe (PID: 4052)
- UserOOBEBroker.exe (PID: 2744)
- svchost.exe (PID: 5036)
- svchost.exe (PID: 6048)
- dllhost.exe (PID: 4424)
- svchost.exe (PID: 3384)
- svchost.exe (PID: 5416)
- svchost.exe (PID: 232)
- svchost.exe (PID: 6940)
- svchost.exe (PID: 2400)
- RuntimeBroker.exe (PID: 5600)
- svchost.exe (PID: 7812)
- taskhostw.exe (PID: 304)
- svchost.exe (PID: 6632)
- svchost.exe (PID: 6392)
Runs injected code in another process
- dialer.exe (PID: 7972)
- dialer.exe (PID: 7844)
REDLINE has been detected (YARA)
- jsc.exe (PID: 608)
LUMMA has been detected (SURICATA)
- aspnet_regiis.exe (PID: 3208)
- svchost.exe (PID: 2256)
MINER has been detected (SURICATA)
- notepad.exe (PID: 7968)
- dialer.exe (PID: 7364)
- dialer.exe (PID: 6188)
- svchost.exe (PID: 2256)
STEALC has been detected (SURICATA)
- RegAsm.exe (PID: 7888)
SNAKEKEYLOGGER has been detected (SURICATA)
- wahost.exe (PID: 6704)
XORed URL has been found (YARA)
- notepad.exe (PID: 7968)
- dialer.exe (PID: 7364)
- dialer.exe (PID: 6188)
METASTEALER has been detected (YARA)
- InstallUtil.exe (PID: 4544)
SILENTCRYPTOMINER has been detected (SURICATA)
- dialer.exe (PID: 7364)
- dialer.exe (PID: 6188)
NANOCORE has been detected (YARA)
- nano.exe (PID: 7732)
LUMMA has been detected (YARA)
- ClientCaller.exe (PID: 1060)
- POS_C032.exe (PID: 4344)
- qt51crk.exe (PID: 2572)
- DiskUtility.exe (PID: 3236)
XWORM has been detected (YARA)
- DiskUtility.exe (PID: 3236)
SUSPICIOUS
Drops the executable file immediately after the start
- 4363463463464363463463463.exe (PID: 6724)
- s.exe (PID: 6848)
- tpeinf.exe (PID: 7024)
- 1.exe (PID: 7060)
- 794428842.exe (PID: 6248)
- Dropper.exe (PID: 6988)
- cmd.exe (PID: 7048)
- Community.pif (PID: 7464)
- pi.exe (PID: 7176)
- pei.exe (PID: 6376)
- Update.exe (PID: 2868)
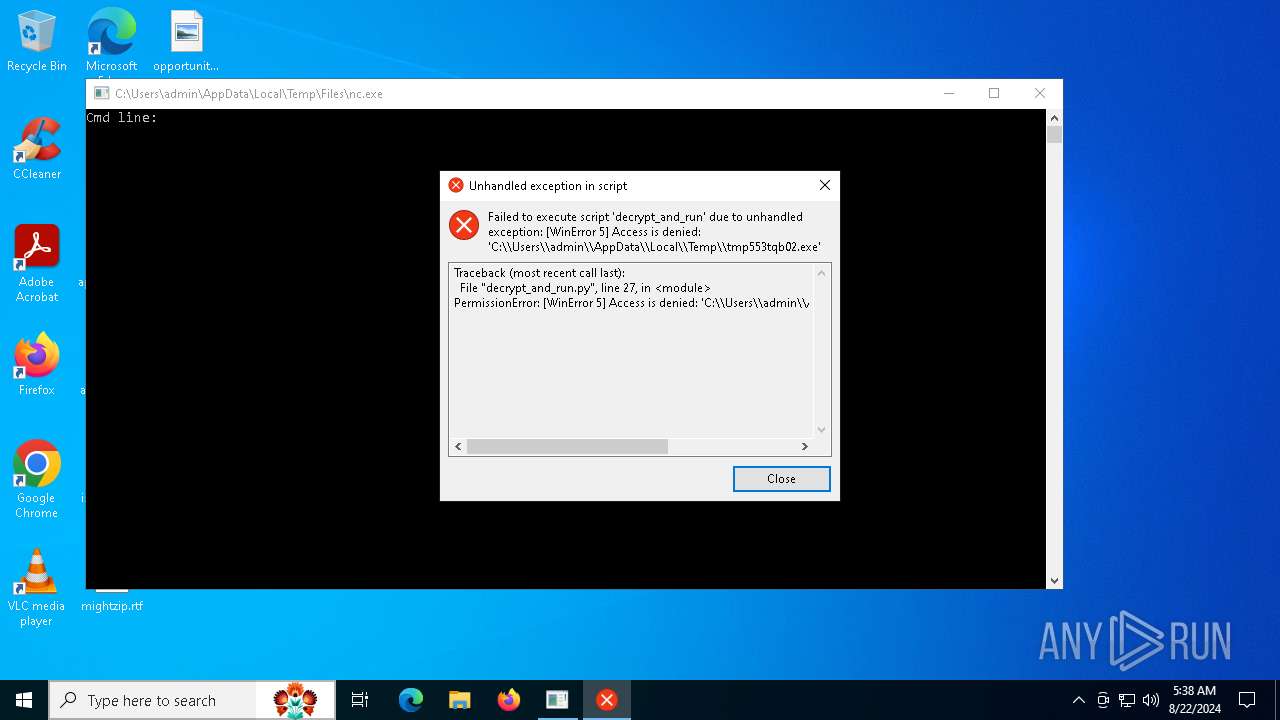
- tmp553tqb02.exe (PID: 4092)
- nxmr.exe (PID: 4828)
- Rage.exe (PID: 7244)
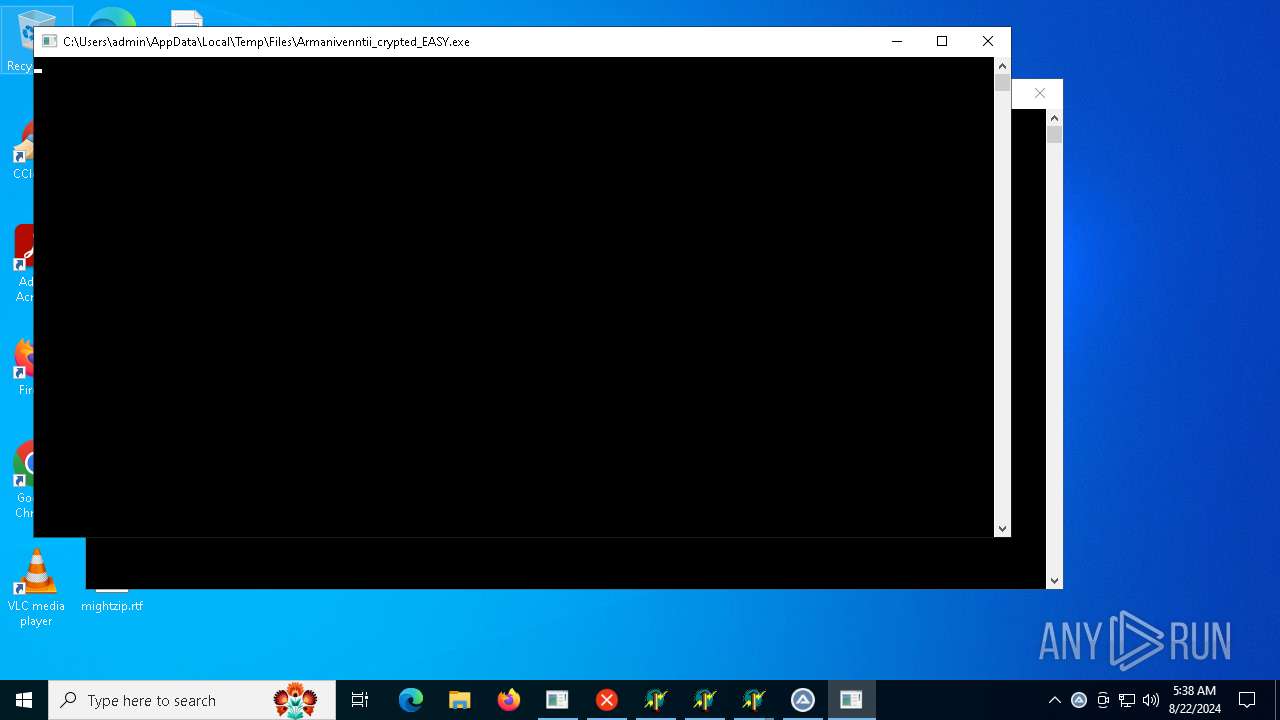
- Armanivenntii_crypted_EASY.exe (PID: 6784)
- npp.exe (PID: 6496)
- v.exe (PID: 7728)
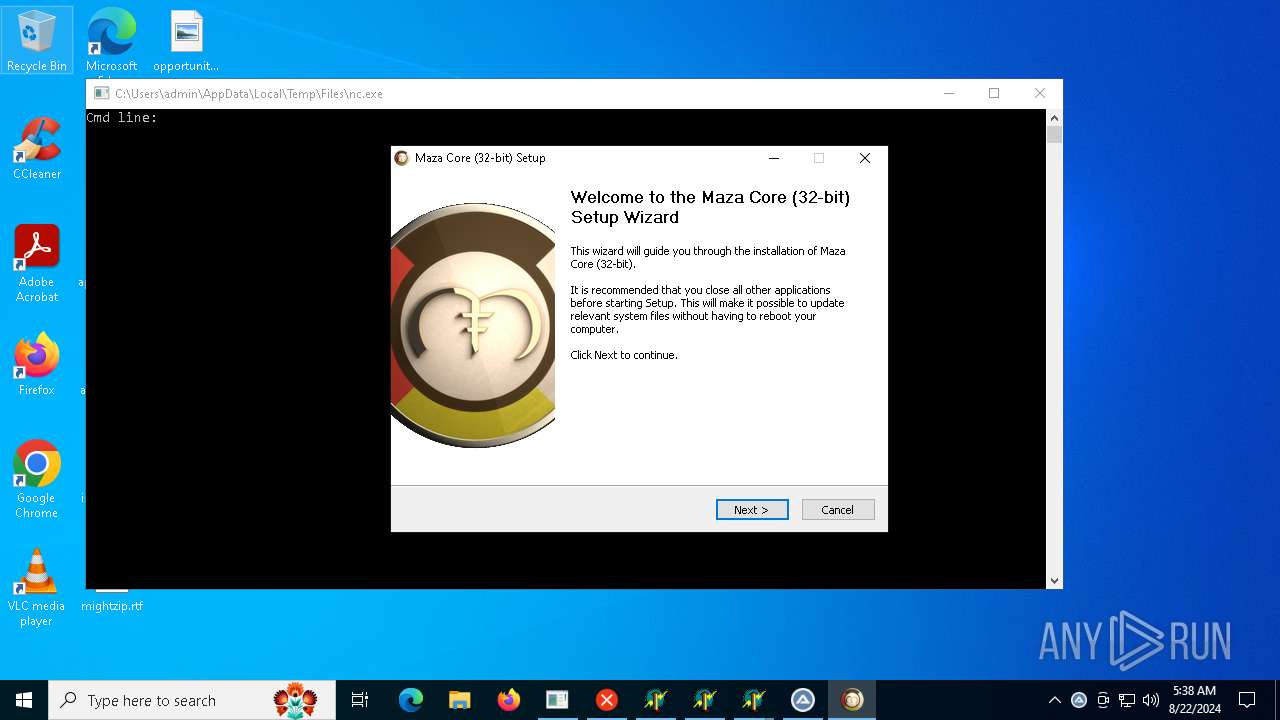
- maza-0.16.3-win32-setup-unsigned.exe (PID: 7460)
- wupgrdsv.exe (PID: 7408)
- wahost.exe (PID: 8176)
- RegAsm.exe (PID: 7888)
- updater.exe (PID: 4004)
- nano.exe (PID: 7732)
- peinf.exe (PID: 6604)
- 66c2d861a5b4d_google.exe (PID: 6276)
- erzljnhmzkuz.exe (PID: 6668)
- 66af31c75d213_123p.exe (PID: 7784)
- eqtpkqwqodik.exe (PID: 400)
- 440322220.exe (PID: 1168)
- bot.exe (PID: 8112)
Reads security settings of Internet Explorer
- 4363463463464363463463463.exe (PID: 6724)
- tpeinf.exe (PID: 7024)
- sysmablsvr.exe (PID: 6908)
- sysarddrvs.exe (PID: 7132)
- VBoxSVC.exe (PID: 6492)
- sysmysldrv.exe (PID: 6300)
- 66bf359bf0474_BattleGermany.exe (PID: 6472)
- DownSysSoft.exe (PID: 6324)
- pei.exe (PID: 6376)
- sylsplvc.exe (PID: 2128)
- Update.exe (PID: 3316)
- Downaqzh.exe (PID: 6872)
- Rage.exe (PID: 7244)
- npp.exe (PID: 6496)
- v.exe (PID: 7728)
- winsvc.exe (PID: 6180)
- RegAsm.exe (PID: 7888)
- wahost.exe (PID: 8176)
- wahost.exe (PID: 6704)
- DiskUtility.exe (PID: 3236)
- syslyqdvr.exe (PID: 7640)
Reads the date of Windows installation
- 4363463463464363463463463.exe (PID: 6724)
- sysarddrvs.exe (PID: 7132)
- sysmysldrv.exe (PID: 6300)
- 66bf359bf0474_BattleGermany.exe (PID: 6472)
- Update.exe (PID: 3316)
- Rage.exe (PID: 7244)
- wahost.exe (PID: 8176)
- wahost.exe (PID: 6704)
- RegAsm.exe (PID: 7888)
- 23c2343.exe (PID: 4828)
- syslyqdvr.exe (PID: 7640)
Executable content was dropped or overwritten
- 4363463463464363463463463.exe (PID: 6724)
- s.exe (PID: 6848)
- tpeinf.exe (PID: 7024)
- 1.exe (PID: 7060)
- 794428842.exe (PID: 6248)
- Dropper.exe (PID: 6988)
- cmd.exe (PID: 7048)
- Community.pif (PID: 7464)
- pi.exe (PID: 7176)
- pei.exe (PID: 6376)
- Update.exe (PID: 2868)
- tmp553tqb02.exe (PID: 4092)
- nxmr.exe (PID: 4828)
- Rage.exe (PID: 7244)
- Armanivenntii_crypted_EASY.exe (PID: 6784)
- npp.exe (PID: 6496)
- v.exe (PID: 7728)
- maza-0.16.3-win32-setup-unsigned.exe (PID: 7460)
- wupgrdsv.exe (PID: 7408)
- wahost.exe (PID: 8176)
- nano.exe (PID: 7732)
- RegAsm.exe (PID: 7888)
- updater.exe (PID: 4004)
- peinf.exe (PID: 6604)
- 66c2d861a5b4d_google.exe (PID: 6276)
- erzljnhmzkuz.exe (PID: 6668)
- eqtpkqwqodik.exe (PID: 400)
- 66af31c75d213_123p.exe (PID: 7784)
- 440322220.exe (PID: 1168)
- bot.exe (PID: 8112)
Adds/modifies Windows certificates
- lsass.exe (PID: 768)
- jsc.exe (PID: 6680)
Starts itself from another location
- s.exe (PID: 6848)
- 1.exe (PID: 7060)
- 794428842.exe (PID: 6248)
- pi.exe (PID: 7176)
- v.exe (PID: 7728)
- 440322220.exe (PID: 1168)
Found AnyDesk certificate that may have been compromised
- Dropper.exe (PID: 6988)
Creates or modifies Windows services
- sysmablsvr.exe (PID: 6908)
- sysmysldrv.exe (PID: 6300)
- sysarddrvs.exe (PID: 7132)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2256)
- aspnet_regiis.exe (PID: 3208)
- RegAsm.exe (PID: 7888)
Potential Corporate Privacy Violation
- 4363463463464363463463463.exe (PID: 6724)
- tpeinf.exe (PID: 7024)
- DownSysSoft.exe (PID: 6324)
- System (PID: 4)
- Downaqzh.exe (PID: 6872)
- notepad.exe (PID: 7968)
- RegAsm.exe (PID: 7888)
- dialer.exe (PID: 6188)
Starts CMD.EXE for commands execution
- sysarddrvs.exe (PID: 7132)
- VBoxSVC.exe (PID: 6492)
- sysmysldrv.exe (PID: 6300)
- 66bf359bf0474_BattleGermany.exe (PID: 6472)
- cmd.exe (PID: 7048)
- Community.pif (PID: 7464)
- explorer.exe (PID: 4552)
- wahost.exe (PID: 6704)
- RegAsm.exe (PID: 7888)
- syslyqdvr.exe (PID: 7640)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3236)
- cmd.exe (PID: 2384)
- explorer.exe (PID: 4552)
- wahost.exe (PID: 8176)
- cmd.exe (PID: 6224)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 3236)
- cmd.exe (PID: 2384)
- explorer.exe (PID: 4552)
- wahost.exe (PID: 8176)
- cmd.exe (PID: 6224)
The process drops C-runtime libraries
- Dropper.exe (PID: 6988)
- Update.exe (PID: 2868)
- RegAsm.exe (PID: 7888)
Process drops legitimate windows executable
- Dropper.exe (PID: 6988)
- Update.exe (PID: 2868)
- RegAsm.exe (PID: 7888)
- bot.exe (PID: 8112)
Reads Microsoft Outlook installation path
- VBoxSVC.exe (PID: 6492)
Executing commands from ".cmd" file
- 66bf359bf0474_BattleGermany.exe (PID: 6472)
Get information on the list of running processes
- cmd.exe (PID: 7048)
Process requests binary or script from the Internet
- 4363463463464363463463463.exe (PID: 6724)
- RegAsm.exe (PID: 7888)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7048)
Connects to the server without a host name
- 4363463463464363463463463.exe (PID: 6724)
- sysarddrvs.exe (PID: 7132)
- sysmablsvr.exe (PID: 6908)
- RegAsm.exe (PID: 7888)
- sylsplvc.exe (PID: 2128)
- dialer.exe (PID: 6188)
- dialer.exe (PID: 7364)
- syslyqdvr.exe (PID: 7640)
Application launched itself
- cmd.exe (PID: 7048)
- Update.exe (PID: 2868)
- wahost.exe (PID: 8176)
Drops a file with a rarely used extension (PIF)
- cmd.exe (PID: 7048)
- Community.pif (PID: 7464)
The executable file from the user directory is run by the CMD process
- Community.pif (PID: 7464)
Starts application with an unusual extension
- cmd.exe (PID: 7048)
Connects to unusual port
- 4363463463464363463463463.exe (PID: 6724)
- DownSysSoft.exe (PID: 6324)
- sylsplvc.exe (PID: 2128)
- sysmablsvr.exe (PID: 6908)
- jsc.exe (PID: 6680)
- aaa.exe (PID: 7684)
- sysmysldrv.exe (PID: 6300)
- sysarddrvs.exe (PID: 7132)
- Downaqzh.exe (PID: 6872)
- jsc.exe (PID: 608)
- notepad.exe (PID: 7968)
- InstallUtil.exe (PID: 4544)
- nano.exe (PID: 7732)
- RegAsm.exe (PID: 6776)
- dialer.exe (PID: 7364)
- dialer.exe (PID: 6188)
- DiskUtility.exe (PID: 3236)
- jsc.exe (PID: 7888)
Searches for installed software
- jsc.exe (PID: 6680)
- jsc.exe (PID: 608)
- aspnet_regiis.exe (PID: 3208)
- RegAsm.exe (PID: 7888)
- jsc.exe (PID: 7888)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- explorer.exe (PID: 6244)
Process drops python dynamic module
- Update.exe (PID: 2868)
Loads Python modules
- Update.exe (PID: 3316)
There is functionality for taking screenshot (YARA)
- POS_C067.exe (PID: 6856)
- TMS_C029.exe (PID: 6996)
- POS_C012.exe (PID: 7028)
- POS_C032.exe (PID: 4344)
- ClientCaller.exe (PID: 1060)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 4160)
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 4100)
- cmd.exe (PID: 7108)
- 66c2d861a5b4d_google.exe (PID: 6276)
- erzljnhmzkuz.exe (PID: 6668)
- 66af31c75d213_123p.exe (PID: 7784)
- eqtpkqwqodik.exe (PID: 400)
Starts SC.EXE for service management
- cmd.exe (PID: 8188)
- cmd.exe (PID: 7096)
- 66c2d861a5b4d_google.exe (PID: 6276)
- 66af31c75d213_123p.exe (PID: 7784)
The process executes via Task Scheduler
- wupgrdsv.exe (PID: 7408)
- updater.exe (PID: 4004)
- wscript.exe (PID: 208)
Windows Defender mutex has been found
- RegAsm.exe (PID: 2572)
- RegAsm.exe (PID: 7888)
The process creates files with name similar to system file names
- 4363463463464363463463463.exe (PID: 6724)
- maza-0.16.3-win32-setup-unsigned.exe (PID: 7460)
- nano.exe (PID: 7732)
Reads the Windows owner or organization settings
- POS_C012.exe (PID: 7028)
- bot.exe (PID: 8112)
Drops a system driver (possible attempt to evade defenses)
- wupgrdsv.exe (PID: 7408)
- updater.exe (PID: 4004)
- erzljnhmzkuz.exe (PID: 6668)
- eqtpkqwqodik.exe (PID: 400)
Malware-specific behavior (creating "System.dll" in Temp)
- maza-0.16.3-win32-setup-unsigned.exe (PID: 7460)
There is functionality for communication over UDP network (YARA)
- POS_C012.exe (PID: 7028)
The process drops Mozilla's DLL files
- RegAsm.exe (PID: 7888)
Checks for external IP
- svchost.exe (PID: 2256)
- wahost.exe (PID: 6704)
Checks Windows Trust Settings
- RegAsm.exe (PID: 7888)
Executes application which crashes
- peinf.exe (PID: 6604)
Crypto Currency Mining Activity Detected
- dialer.exe (PID: 6188)
- dialer.exe (PID: 7364)
- svchost.exe (PID: 2256)
- notepad.exe (PID: 7968)
Executes as Windows Service
- erzljnhmzkuz.exe (PID: 6668)
- eqtpkqwqodik.exe (PID: 400)
- VSSVC.exe (PID: 2132)
The process checks if it is being run in the virtual environment
- 4363463463464363463463463.exe (PID: 6724)
The process executes JS scripts
- svchost.exe (PID: 1316)
INFO
Reads security settings of Internet Explorer
- explorer.exe (PID: 4552)
- RuntimeBroker.exe (PID: 5560)
- explorer.exe (PID: 6244)
Disables trace logs
- 4363463463464363463463463.exe (PID: 6724)
- wahost.exe (PID: 6704)
- DiskUtility.exe (PID: 3236)
Reads the computer name
- 4363463463464363463463463.exe (PID: 6724)
- Dropper.exe (PID: 6988)
- tpeinf.exe (PID: 7024)
- sysmablsvr.exe (PID: 6908)
- sysarddrvs.exe (PID: 7132)
- VBoxSVC.exe (PID: 6492)
- sysmysldrv.exe (PID: 6300)
- 66bf359bf0474_BattleGermany.exe (PID: 6472)
- Community.pif (PID: 7464)
- DownSysSoft.exe (PID: 6324)
- pei.exe (PID: 6376)
- jsc.exe (PID: 6680)
- sylsplvc.exe (PID: 2128)
- aaa.exe (PID: 7684)
- Update.exe (PID: 3316)
- Update.exe (PID: 2868)
- POS_C067.exe (PID: 6856)
- Downaqzh.exe (PID: 6872)
- jsc.exe (PID: 608)
- TMS_C029.exe (PID: 6996)
- POS_C012.exe (PID: 7028)
- AutoIt3.exe (PID: 4680)
- Rage.exe (PID: 7244)
- RegAsm.exe (PID: 2572)
- wahost.exe (PID: 8176)
- v.exe (PID: 7728)
- Armanivenntii_crypted_EASY.exe (PID: 6784)
- npp.exe (PID: 6496)
- aspnet_regiis.exe (PID: 3208)
- winsvc.exe (PID: 6180)
- maza-0.16.3-win32-setup-unsigned.exe (PID: 7460)
- RegAsm.exe (PID: 7888)
- 66c3373394621_srealc_cry.exe (PID: 6580)
- wahost.exe (PID: 6704)
- InstallUtil.exe (PID: 4544)
- POS_C032.exe (PID: 4344)
- nano.exe (PID: 7732)
- qt51crk.exe (PID: 2572)
- ClientCaller.exe (PID: 1060)
- DiskUtility.exe (PID: 3236)
- RegAsm.exe (PID: 6776)
- TMS_C061.exe (PID: 7940)
- bp.exe (PID: 3308)
- POS_C164.exe (PID: 1640)
- jsc.exe (PID: 7888)
- 23c2343.exe (PID: 4828)
- bot.exe (PID: 8112)
- Identification.exe (PID: 8088)
- msiexec.exe (PID: 4072)
- syslyqdvr.exe (PID: 7640)
- msiexec.exe (PID: 6332)
- POS_C093.exe (PID: 3164)
- RegAsm.exe (PID: 8008)
Checks supported languages
- 4363463463464363463463463.exe (PID: 6724)
- s.exe (PID: 6848)
- r.exe (PID: 6868)
- Dropper.exe (PID: 6988)
- sysmablsvr.exe (PID: 6908)
- m.exe (PID: 7080)
- tpeinf.exe (PID: 7024)
- 1.exe (PID: 7060)
- 794428842.exe (PID: 6248)
- sysarddrvs.exe (PID: 7132)
- twztl.exe (PID: 6888)
- VBoxSVC.exe (PID: 6492)
- sysmysldrv.exe (PID: 6300)
- 66bf359bf0474_BattleGermany.exe (PID: 6472)
- Community.pif (PID: 7464)
- pi.exe (PID: 7176)
- DownSysSoft.exe (PID: 6324)
- a.exe (PID: 6304)
- sylsplvc.exe (PID: 2128)
- pei.exe (PID: 6376)
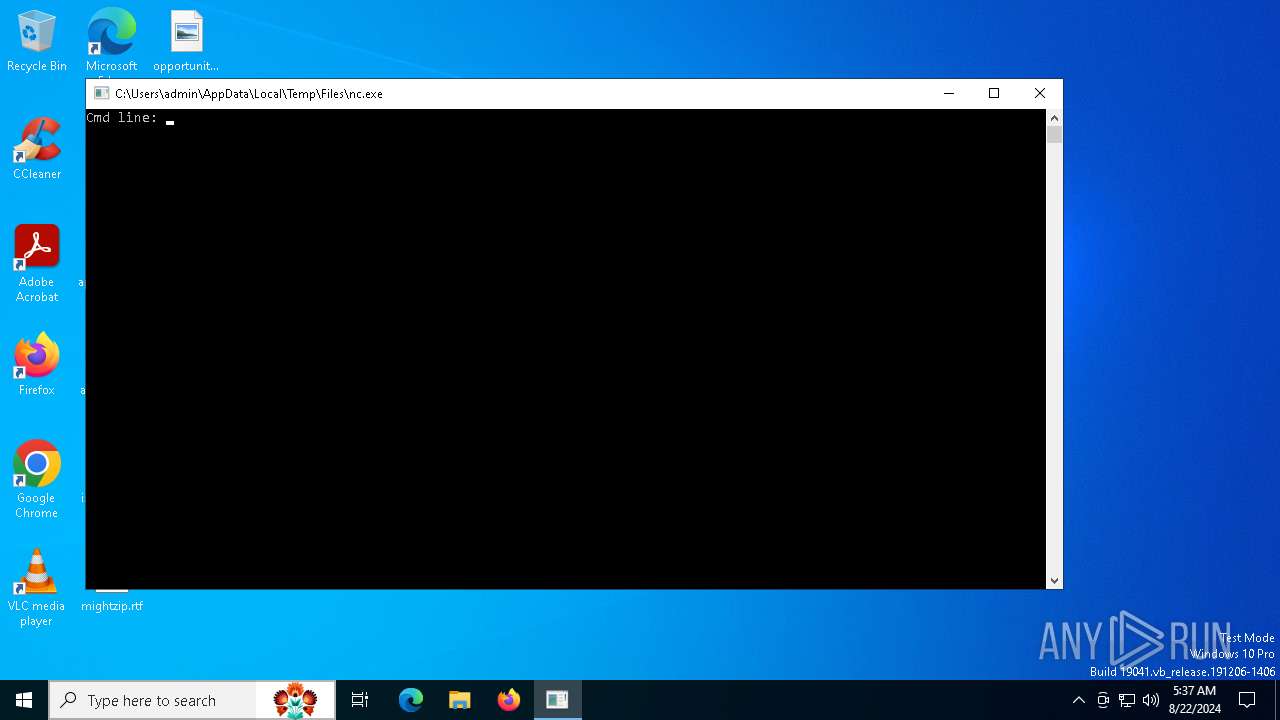
- nc.exe (PID: 7560)
- pp.exe (PID: 7208)
- jsc.exe (PID: 6680)
- 11.exe (PID: 7692)
- t1.exe (PID: 2636)
- Downdd.exe (PID: 6428)
- aaa.exe (PID: 7684)
- 296042778.exe (PID: 6012)
- Update.exe (PID: 2868)
- Update.exe (PID: 3316)
- Downaqzh.exe (PID: 6872)
- nxmr.exe (PID: 4828)
- jsc.exe (PID: 608)
- tmp553tqb02.exe (PID: 4092)
- POS_C067.exe (PID: 6856)
- TMS_C029.exe (PID: 6996)
- t.exe (PID: 7684)
- POS_C012.exe (PID: 7028)
- 5447jsX.exe (PID: 6732)
- v.exe (PID: 7728)
- Rage.exe (PID: 7244)
- wupgrdsv.exe (PID: 7408)
- AutoIt3.exe (PID: 4680)
- o.exe (PID: 8016)
- RegAsm.exe (PID: 2572)
- updater.exe (PID: 4004)
- npp.exe (PID: 6496)
- wahost.exe (PID: 8176)
- aspnet_regiis.exe (PID: 3208)
- Armanivenntii_crypted_EASY.exe (PID: 6784)
- winsvc.exe (PID: 6180)
- 3221520410.exe (PID: 4080)
- newtpp.exe (PID: 6848)
- maza-0.16.3-win32-setup-unsigned.exe (PID: 7460)
- tdrpload.exe (PID: 5164)
- RegAsm.exe (PID: 7888)
- 66c3373394621_srealc_cry.exe (PID: 6580)
- cock.exe (PID: 3308)
- wahost.exe (PID: 6704)
- InstallUtil.exe (PID: 4544)
- nano.exe (PID: 7732)
- tt.exe (PID: 1128)
- POS_C032.exe (PID: 4344)
- ClientCaller.exe (PID: 1060)
- peinf.exe (PID: 6604)
- qt51crk.exe (PID: 2572)
- 66c2d861a5b4d_google.exe (PID: 6276)
- t2.exe (PID: 7488)
- crypted.exe (PID: 8064)
- DiskUtility.exe (PID: 3236)
- 23c2343.exe (PID: 4828)
- bp.exe (PID: 3308)
- TMS_C061.exe (PID: 7940)
- crypted_c360a5b7.exe (PID: 6532)
- RegAsm.exe (PID: 6776)
- 66af31c75d213_123p.exe (PID: 7784)
- RegAsm.exe (PID: 8008)
- POS_C164.exe (PID: 1640)
- L.exe (PID: 2080)
- jsc.exe (PID: 7888)
- erzljnhmzkuz.exe (PID: 6668)
- eqtpkqwqodik.exe (PID: 400)
- 440322220.exe (PID: 1168)
- bot.exe (PID: 8112)
- syslyqdvr.exe (PID: 7640)
- msiexec.exe (PID: 4072)
- Identification.exe (PID: 8088)
- msiexec.exe (PID: 6332)
- POS_C093.exe (PID: 3164)
- channel.exe (PID: 3116)
Reads Environment values
- 4363463463464363463463463.exe (PID: 6724)
- jsc.exe (PID: 6680)
- jsc.exe (PID: 608)
- RegAsm.exe (PID: 7888)
- wahost.exe (PID: 6704)
- nano.exe (PID: 7732)
- DiskUtility.exe (PID: 3236)
- jsc.exe (PID: 7888)
- bot.exe (PID: 8112)
- msiexec.exe (PID: 6332)
Reads the machine GUID from the registry
- 4363463463464363463463463.exe (PID: 6724)
- jsc.exe (PID: 6680)
- sylsplvc.exe (PID: 2128)
- sysmablsvr.exe (PID: 6908)
- sysarddrvs.exe (PID: 7132)
- sysmysldrv.exe (PID: 6300)
- jsc.exe (PID: 608)
- AutoIt3.exe (PID: 4680)
- wahost.exe (PID: 8176)
- nano.exe (PID: 7732)
- wahost.exe (PID: 6704)
- InstallUtil.exe (PID: 4544)
- RegAsm.exe (PID: 7888)
- DiskUtility.exe (PID: 3236)
- RegAsm.exe (PID: 6776)
- jsc.exe (PID: 7888)
- 23c2343.exe (PID: 4828)
Checks proxy server information
- 4363463463464363463463463.exe (PID: 6724)
- tpeinf.exe (PID: 7024)
- sysmablsvr.exe (PID: 6908)
- sysarddrvs.exe (PID: 7132)
- sysmysldrv.exe (PID: 6300)
- DownSysSoft.exe (PID: 6324)
- pei.exe (PID: 6376)
- sylsplvc.exe (PID: 2128)
- explorer.exe (PID: 6244)
- Downaqzh.exe (PID: 6872)
- npp.exe (PID: 6496)
- v.exe (PID: 7728)
- winsvc.exe (PID: 6180)
- RegAsm.exe (PID: 7888)
- wahost.exe (PID: 6704)
- WerFault.exe (PID: 8088)
- DiskUtility.exe (PID: 3236)
- 23c2343.exe (PID: 4828)
- syslyqdvr.exe (PID: 7640)
Process checks computer location settings
- 4363463463464363463463463.exe (PID: 6724)
- sysarddrvs.exe (PID: 7132)
- sysmysldrv.exe (PID: 6300)
- 66bf359bf0474_BattleGermany.exe (PID: 6472)
- Update.exe (PID: 3316)
- Rage.exe (PID: 7244)
- wahost.exe (PID: 8176)
- wahost.exe (PID: 6704)
- RegAsm.exe (PID: 7888)
- syslyqdvr.exe (PID: 7640)
Reads the software policy settings
- 4363463463464363463463463.exe (PID: 6724)
- lsass.exe (PID: 768)
- Dropper.exe (PID: 6988)
- explorer.exe (PID: 6244)
- aspnet_regiis.exe (PID: 3208)
- wahost.exe (PID: 6704)
- RegAsm.exe (PID: 7888)
- WerFault.exe (PID: 8088)
- DiskUtility.exe (PID: 3236)
Create files in a temporary directory
- 4363463463464363463463463.exe (PID: 6724)
- tpeinf.exe (PID: 7024)
- 66bf359bf0474_BattleGermany.exe (PID: 6472)
- VBoxSVC.exe (PID: 6492)
- DownSysSoft.exe (PID: 6324)
- pei.exe (PID: 6376)
- Update.exe (PID: 2868)
- Update.exe (PID: 3316)
- Downaqzh.exe (PID: 6872)
- tmp553tqb02.exe (PID: 4092)
- npp.exe (PID: 6496)
- v.exe (PID: 7728)
- wupgrdsv.exe (PID: 7408)
- maza-0.16.3-win32-setup-unsigned.exe (PID: 7460)
- wahost.exe (PID: 8176)
- sylsplvc.exe (PID: 2128)
- bot.exe (PID: 8112)
Creates files or folders in the user directory
- tpeinf.exe (PID: 7024)
- Dropper.exe (PID: 6988)
- Community.pif (PID: 7464)
- explorer.exe (PID: 4552)
- DownSysSoft.exe (PID: 6324)
- dllhost.exe (PID: 5568)
- jsc.exe (PID: 6680)
- explorer.exe (PID: 6244)
- Downaqzh.exe (PID: 6872)
- jsc.exe (PID: 608)
- POS_C012.exe (PID: 7028)
- Armanivenntii_crypted_EASY.exe (PID: 6784)
- v.exe (PID: 7728)
- wupgrdsv.exe (PID: 7408)
- RegAsm.exe (PID: 7888)
- wahost.exe (PID: 8176)
- nano.exe (PID: 7732)
- WerFault.exe (PID: 8088)
- jsc.exe (PID: 7888)
- sylsplvc.exe (PID: 2128)
- bot.exe (PID: 8112)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6744)
- powershell.exe (PID: 6988)
- powershell.exe (PID: 4160)
- powershell.exe (PID: 7328)
- powershell.exe (PID: 4544)
- powershell.exe (PID: 6844)
- powershell.exe (PID: 7320)
- powershell.exe (PID: 964)
- powershell.exe (PID: 5612)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6744)
- powershell.exe (PID: 6988)
- powershell.exe (PID: 4160)
- powershell.exe (PID: 7320)
- powershell.exe (PID: 964)
Reads mouse settings
- Community.pif (PID: 7464)
- DownSysSoft.exe (PID: 6324)
- Downdd.exe (PID: 6428)
- Downaqzh.exe (PID: 6872)
- AutoIt3.exe (PID: 4680)
Reads the time zone
- svchost.exe (PID: 7812)
- MoUsoCoreWorker.exe (PID: 7888)
- svchost.exe (PID: 2692)
Creates files in the program directory
- svchost.exe (PID: 7812)
- MoUsoCoreWorker.exe (PID: 7888)
- AutoIt3.exe (PID: 4680)
- tmp553tqb02.exe (PID: 4092)
- Rage.exe (PID: 7244)
- RegAsm.exe (PID: 7888)
- nano.exe (PID: 7732)
- updater.exe (PID: 4004)
- svchost.exe (PID: 6632)
- 66c2d861a5b4d_google.exe (PID: 6276)
- 66af31c75d213_123p.exe (PID: 7784)
Reads Microsoft Office registry keys
- OfficeClickToRun.exe (PID: 2656)
- RuntimeBroker.exe (PID: 5560)
Attempting to use instant messaging service
- explorer.exe (PID: 6244)
PyInstaller has been detected (YARA)
- Update.exe (PID: 2868)
- Update.exe (PID: 3316)
Manual execution by a user
- powershell.exe (PID: 4160)
- powershell.exe (PID: 7328)
- cmd.exe (PID: 4100)
- powershell.exe (PID: 4544)
- cmd.exe (PID: 8188)
- dialer.exe (PID: 7972)
- schtasks.exe (PID: 3308)
- schtasks.exe (PID: 3304)
- cmd.exe (PID: 8000)
- powershell.exe (PID: 6844)
- notepad.exe (PID: 7968)
- powershell.exe (PID: 964)
- cmd.exe (PID: 7096)
- cmd.exe (PID: 7108)
- powershell.exe (PID: 5612)
- dialer.exe (PID: 7844)
- dialer.exe (PID: 4688)
- dialer.exe (PID: 7364)
- dialer.exe (PID: 6188)
Reads CPU info
- POS_C012.exe (PID: 7028)
- RegAsm.exe (PID: 7888)
Reads product name
- RegAsm.exe (PID: 7888)
Process checks whether UAC notifications are on
- nano.exe (PID: 7732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(608) jsc.exe
C2 (1)88.99.151.68:7200
Botnet816FA
Options
ErrorMessage
Keys
XorCotillons
MetaStealer
(PID) Process(4544) InstallUtil.exe
C2 (1)5.42.65.101:48790
Botnet740675865-26990097-packlab
Options
ErrorMessage
Keys
XorPyrometry
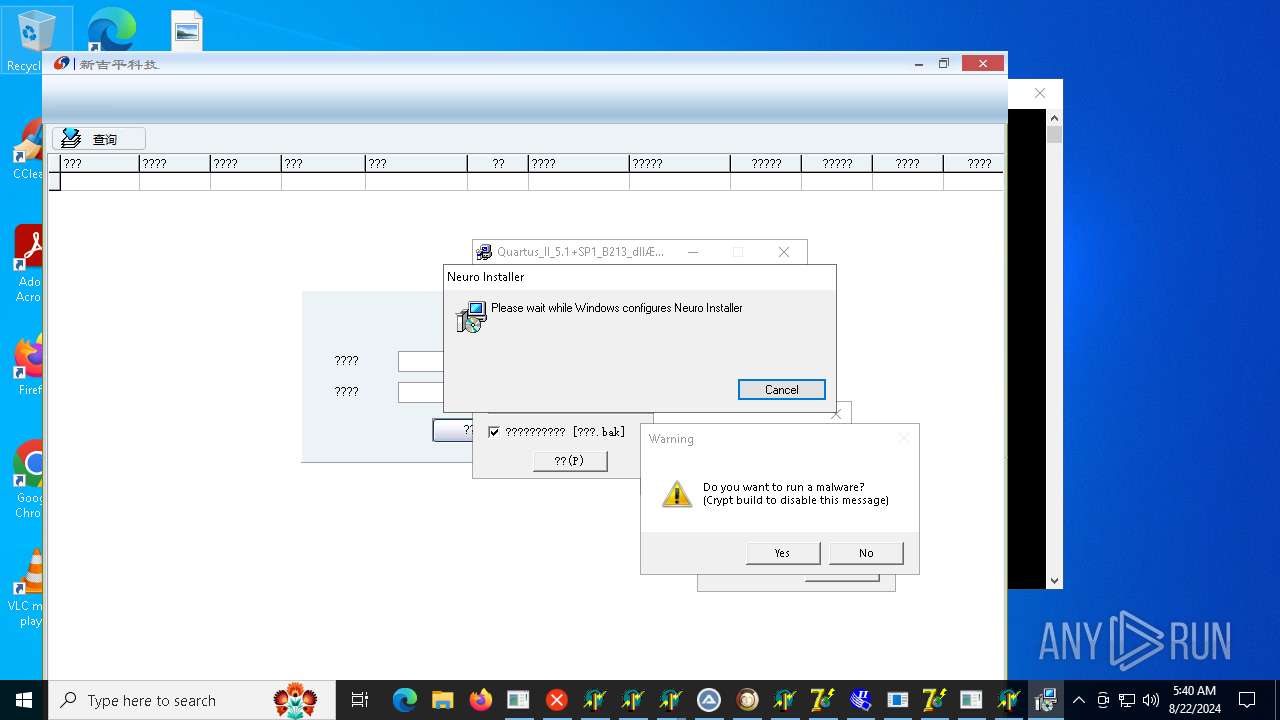
Nanocore
(PID) Process(7732) nano.exe
KeyboardLoggingTrue
BuildTime2024-08-11 19:06:37.834528
Version1.2.2.0
Mutex7029ef73-6025-47e5-b0d0-fb5b27c261b8
DefaultGroupDefault
PrimaryConnectionHost91.92.240.41
BackupConnectionHost91.92.240.41
ConnectionPort7575
RunOnStartupTrue
RequestElevationFalse
BypassUserAccountControlFalse
ClearZoneIdentifierTrue
ClearAccessControlTrue
SetCriticalProcessFalse
PreventSystemSleepTrue
ActivateAwayModeTrue
EnableDebugModeFalse
RunDelay5000
ConnectDelay4000
RestartDelay5000
TimeoutInterval5000
KeepAliveTimeout30000
MutexTimeout5000
LanTimeout2500
WanTimeout8000
BufferSize65535
MaxPacketSize10485760
GCThreshold10485760
UseCustomDnsServerTrue
PrimaryDnsServer8.8.8.8
BackupDnsServer8.8.4.4
XWorm
(PID) Process(3236) DiskUtility.exe
C2ktamapro.duckdns.org:58159
Keys
AES<123456789>
Options
Splitter<Xwormmm>
Sleep time5
USB drop nameXWorm V5.0
MutexY5NgJSHGNPmhibML
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:22 08:29:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 5632 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3552 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | 4363463463464363463463463.exe |
| LegalCopyright: | |
| OriginalFileName: | 4363463463464363463463463.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
410
Monitored processes
354
Malicious processes
130
Suspicious processes
19
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4 | System | [System Process] | |||||||||||||
User: SYSTEM Integrity Level: SYSTEM | |||||||||||||||
| 208 | "C:\WINDOWS\system32\wscript.EXE" //B "C:\Users\admin\AppData\Local\SkyNav Technologies\SkyPilot.js" | C:\Windows\System32\wscript.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 232 | C:\WINDOWS\System32\svchost.exe -k netsvcs -p -s Browser | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 252 | C:\WINDOWS\system32\powercfg.exe /x -hibernate-timeout-ac 0 | C:\Windows\System32\powercfg.exe | — | eqtpkqwqodik.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 304 | taskhostw.exe None | C:\Windows\System32\taskhostw.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Tasks Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 368 | "C:\Windows\System32\cmd.exe" /c sc stop UsoSvc & sc stop WaaSMedicSvc & sc stop wuauserv & sc stop DoSvc & sc stop BITS | C:\Windows\SysWOW64\cmd.exe | — | sysmysldrv.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1062 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 368 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 400 | C:\ProgramData\lmguvcpihozg\eqtpkqwqodik.exe | C:\ProgramData\lmguvcpihozg\eqtpkqwqodik.exe | services.exe | ||||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: SYSTEM Description: Google Chrome Exit code: 0 Version: 80,0,3538,110 Modules
| |||||||||||||||
| 460 | sc stop wuauserv | C:\Windows\SysWOW64\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1062 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 476 | C:\WINDOWS\system32\svchost.exe -k DcomLaunch -p -s LSM | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
266 230
Read events
264 655
Write events
1 100
Delete events
475
Modification events
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Security and Maintenance\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F00620000000000000000000000010000004400000044000000 | |||
| (PID) Process: | (5236) svchost.exe | Key: | \REGISTRY\A\{97df79f6-4c74-aec1-ceea-757b34fa82e1}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (5236) svchost.exe | Key: | \REGISTRY\A\{97df79f6-4c74-aec1-ceea-757b34fa82e1}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5236) svchost.exe | Key: | \REGISTRY\A\{97df79f6-4c74-aec1-ceea-757b34fa82e1}\Root\InventoryApplicationFile\4363463463464363|e3ecc927de8bfde6 |
| Operation: | write | Name: | ProgramId |
Value: 0006f1b97f12d8b502d0034f62cef27d481400000000 | |||
| (PID) Process: | (5236) svchost.exe | Key: | \REGISTRY\A\{97df79f6-4c74-aec1-ceea-757b34fa82e1}\Root\InventoryApplicationFile\4363463463464363|e3ecc927de8bfde6 |
| Operation: | write | Name: | FileId |
Value: 0000e2a1a5641295f5ebf01a37ac1c170ac0814bb71a | |||
| (PID) Process: | (5236) svchost.exe | Key: | \REGISTRY\A\{97df79f6-4c74-aec1-ceea-757b34fa82e1}\Root\InventoryApplicationFile\4363463463464363|e3ecc927de8bfde6 |
| Operation: | write | Name: | LowerCaseLongPath |
Value: c:\users\admin\appdata\local\temp\4363463463464363463463463.exe | |||
| (PID) Process: | (5236) svchost.exe | Key: | \REGISTRY\A\{97df79f6-4c74-aec1-ceea-757b34fa82e1}\Root\InventoryApplicationFile\4363463463464363|e3ecc927de8bfde6 |
| Operation: | write | Name: | LongPathHash |
Value: 4363463463464363|e3ecc927de8bfde6 | |||
| (PID) Process: | (5236) svchost.exe | Key: | \REGISTRY\A\{97df79f6-4c74-aec1-ceea-757b34fa82e1}\Root\InventoryApplicationFile\4363463463464363|e3ecc927de8bfde6 |
| Operation: | write | Name: | Name |
Value: 4363463463464363463463463.exe | |||
| (PID) Process: | (5236) svchost.exe | Key: | \REGISTRY\A\{97df79f6-4c74-aec1-ceea-757b34fa82e1}\Root\InventoryApplicationFile\4363463463464363|e3ecc927de8bfde6 |
| Operation: | write | Name: | OriginalFileName |
Value: 4363463463464363463463463.exe | |||
| (PID) Process: | (5236) svchost.exe | Key: | \REGISTRY\A\{97df79f6-4c74-aec1-ceea-757b34fa82e1}\Root\InventoryApplicationFile\4363463463464363|e3ecc927de8bfde6 |
| Operation: | write | Name: | Publisher |
Value: | |||
Executable files
164
Suspicious files
221
Text files
69
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6724 | 4363463463464363463463463.exe | C:\Users\admin\AppData\Local\Temp\Files\s.exe | executable | |
MD5:ABABCA6D12D96E8DD2F1D7114B406FAE | SHA256:A992920E64A64763F3DD8C2A431A0F5E56E5B3782A1496DE92BC80EE71CCA5BA | |||
| 6848 | s.exe | C:\Windows\sysmablsvr.exe | executable | |
MD5:ABABCA6D12D96E8DD2F1D7114B406FAE | SHA256:A992920E64A64763F3DD8C2A431A0F5E56E5B3782A1496DE92BC80EE71CCA5BA | |||
| 1620 | svchost.exe | C:\Windows\Prefetch\S.EXE-CAFAF8B8.pf | binary | |
MD5:B53BB966BFF309F3B826EC7CE2FD4B30 | SHA256:846610B2B4E34BF49E683A7830A7226BAF667C65CB13A2DC8AE20F6CDB03459A | |||
| 1620 | svchost.exe | C:\Windows\Prefetch\TWZTL.EXE-7DE75BCA.pf | binary | |
MD5:804CCDB6AD6AFAE1FD0AC6D13952460C | SHA256:42D1ED9723E212DFE8B67BB0E630A807FA58394680E766DD8F8960FB391CCB8D | |||
| 1620 | svchost.exe | C:\Windows\Prefetch\SVCHOST.EXE-61541290.pf | binary | |
MD5:8738690A1F8C38C25DEBF95CDBCABED7 | SHA256:29C043BC1012406AA5C0B1F1B5DA94ADEDD8695AF51945CB8B11FCBF7596CD7D | |||
| 6724 | 4363463463464363463463463.exe | C:\Users\admin\AppData\Local\Temp\Files\tpeinf.exe | executable | |
MD5:CFB7FBF1D4B077A0E74ED6E9AAB650A8 | SHA256:D93ADD71A451EC7C04C99185AE669E59FB866EB38F463E9425044981ED1BCAE0 | |||
| 1620 | svchost.exe | C:\Windows\Prefetch\SVCHOST.EXE-2E4E3AC7.pf | binary | |
MD5:FBB225F846470601908E6A8F8F94E51E | SHA256:113E20F47F3248E2E35F52BD83C83AD25C99464B75A2B106FB9B230D45AAEAB9 | |||
| 6724 | 4363463463464363463463463.exe | C:\Users\admin\AppData\Local\Temp\Files\m.exe | executable | |
MD5:ABABCA6D12D96E8DD2F1D7114B406FAE | SHA256:A992920E64A64763F3DD8C2A431A0F5E56E5B3782A1496DE92BC80EE71CCA5BA | |||
| 7024 | tpeinf.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\newtpp[1].exe | executable | |
MD5:BE9388B42333B3D4E163B0ACE699897B | SHA256:D281E0A0F1E1073F2D290A7EB1F77BED4C210DBF83A0F4F4E22073F50FAA843F | |||
| 6988 | Dropper.exe | C:\Users\admin\AppData\Roaming\SNDLWRAONZEYUNNQSBX\YWHQZJMLZVNAOJEKEQJVODI | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
131
TCP/UDP connections
455
DNS requests
63
Threats
461
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6724 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.66:80 | http://privacy.aefiabeuodbauobfafoebbf.net/r.exe | unknown | — | — | malicious |
6724 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.66:80 | http://e9ee228b-57e8-4349-a41e-71a7b6d67aa2.random.aefiabeuodbauobfafoebbf.net/s.exe | unknown | — | — | malicious |
6724 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.66:80 | http://aefiabeuodbauobfafoebbf.net/twztl.exe | unknown | — | — | malicious |
6724 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.66:80 | http://aefieiaehfiaehr.top/tpeinf.exe | unknown | — | — | malicious |
6724 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.84:80 | http://225c2cd6-cbd3-4ac2-8464-cc7686273c9c.random.tsrv1.ws/1.exe | unknown | — | — | malicious |
6724 | 4363463463464363463463463.exe | GET | 200 | 45.141.84.14:80 | http://45.141.84.14/Dropper.exe | unknown | — | — | suspicious |
6724 | 4363463463464363463463463.exe | GET | 200 | 147.45.44.104:80 | http://147.45.44.104/yuop/66bf359bf0474_BattleGermany.exe | unknown | — | — | suspicious |
6724 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.84:80 | http://a012a656-f566-48a1-afad-3dcc46018380.random.tsrv1.ws/m.exe | unknown | — | — | malicious |
6908 | sysmablsvr.exe | GET | 404 | 185.215.113.66:80 | http://185.215.113.66/1 | unknown | — | — | unknown |
6908 | sysmablsvr.exe | GET | 404 | 185.215.113.66:80 | http://185.215.113.66/2 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2088 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3304 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6724 | 4363463463464363463463463.exe | 151.101.130.49:443 | urlhaus.abuse.ch | FASTLY | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6724 | 4363463463464363463463463.exe | 185.215.113.66:80 | e9ee228b-57e8-4349-a41e-71a7b6d67aa2.random.aefiabeuodbauobfafoebbf.net | 1337team Limited | SC | unknown |
6724 | 4363463463464363463463463.exe | 45.141.84.14:80 | — | Media Land LLC | RU | unknown |
6988 | Dropper.exe | 104.20.6.134:443 | creativecommons.org | CLOUDFLARENET | — | unknown |
6988 | Dropper.exe | 162.19.58.161:443 | i.ibb.co | OVH SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
e9ee228b-57e8-4349-a41e-71a7b6d67aa2.random.aefiabeuodbauobfafoebbf.net |
| unknown |
privacy.aefiabeuodbauobfafoebbf.net |
| unknown |
aefiabeuodbauobfafoebbf.net |
| unknown |
aefieiaehfiaehr.top |
| unknown |
creativecommons.org |
| whitelisted |
225c2cd6-cbd3-4ac2-8464-cc7686273c9c.random.tsrv1.ws |
| malicious |
i.ibb.co |
| shared |
a012a656-f566-48a1-afad-3dcc46018380.random.tsrv1.ws |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6724 | 4363463463464363463463463.exe | A Network Trojan was detected | ET MALWARE Single char EXE direct download likely trojan (multiple families) |
6724 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile |
6724 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6724 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6724 | 4363463463464363463463463.exe | A Network Trojan was detected | ET MALWARE Single char EXE direct download likely trojan (multiple families) |
6724 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile |
6724 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6724 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6724 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6724 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
37 ETPRO signatures available at the full report
Process | Message |
|---|---|
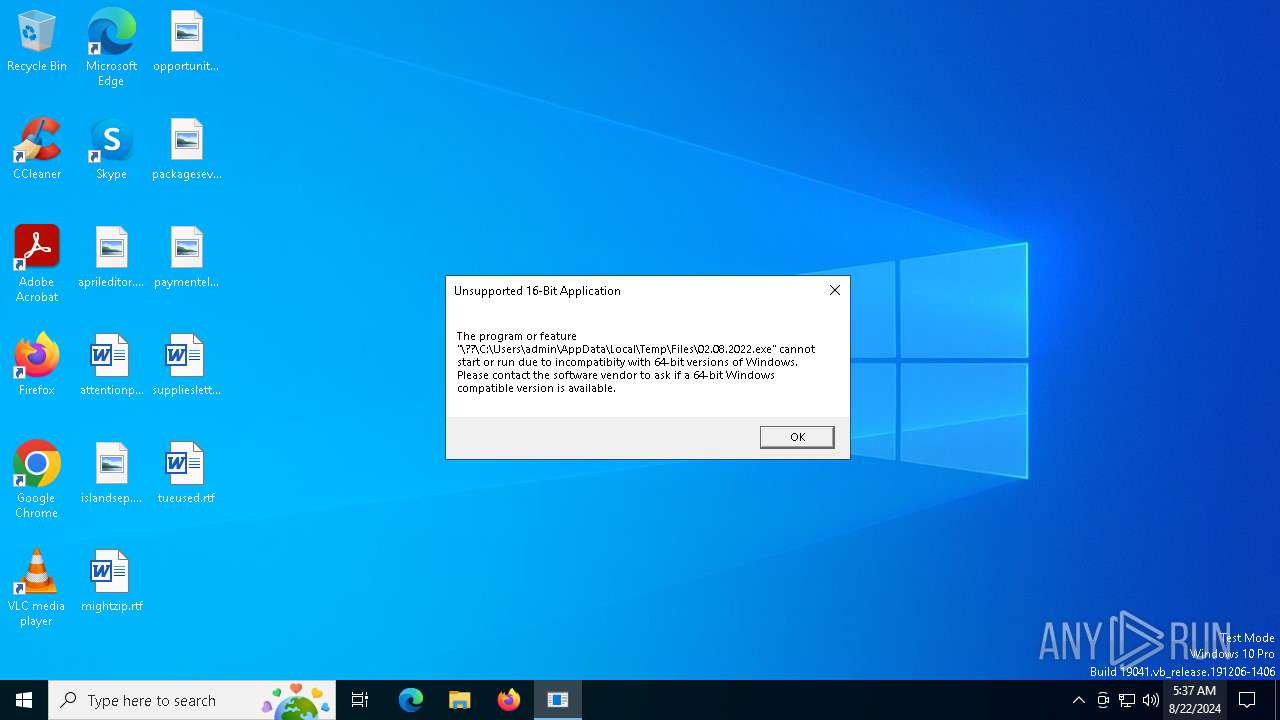
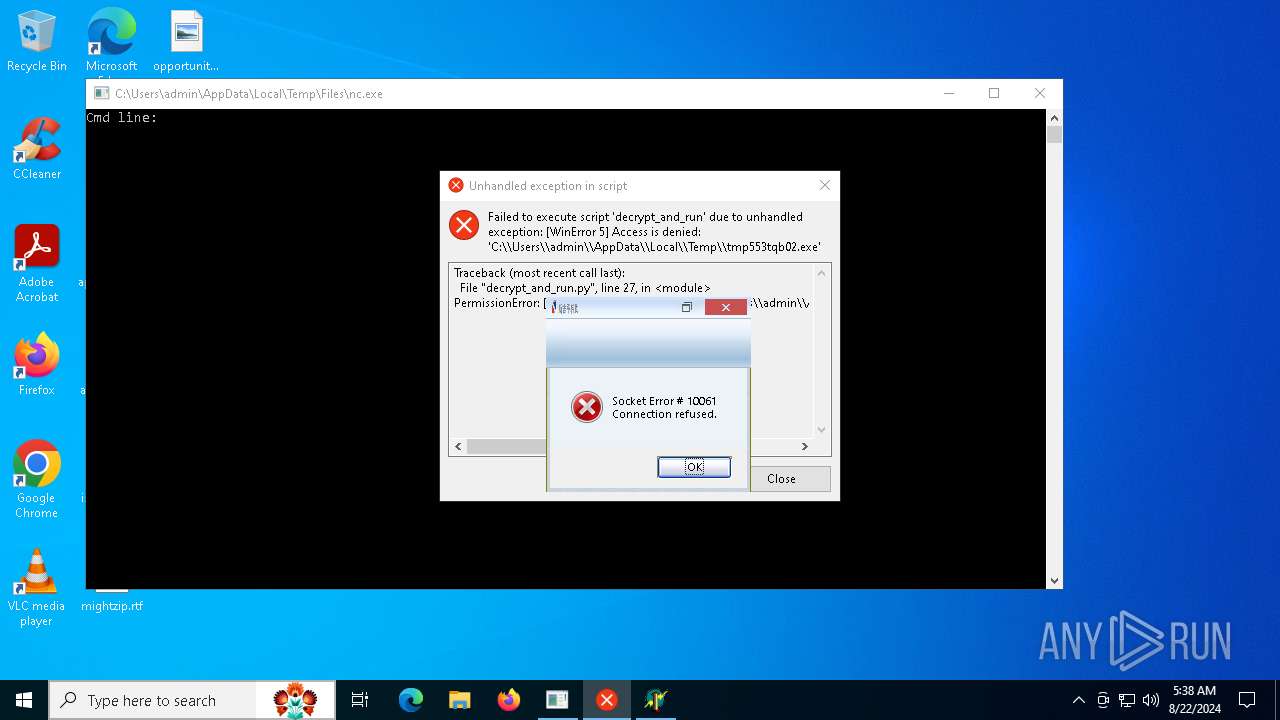
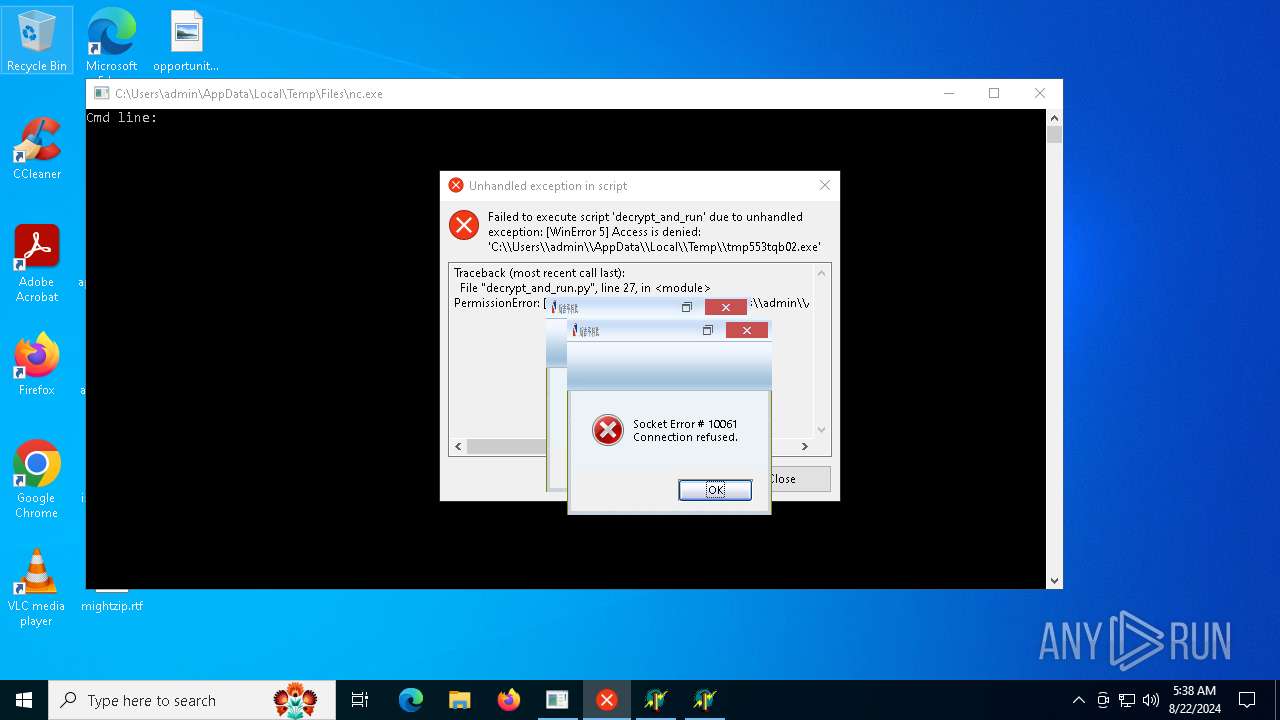
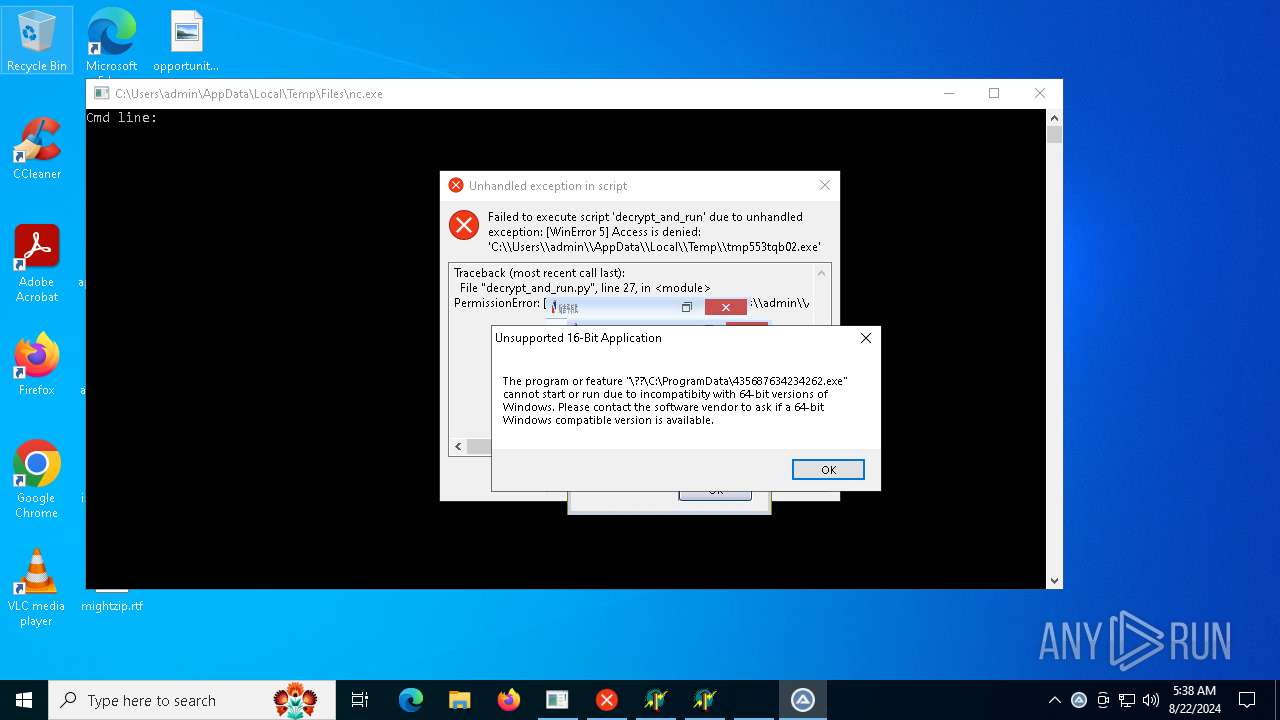
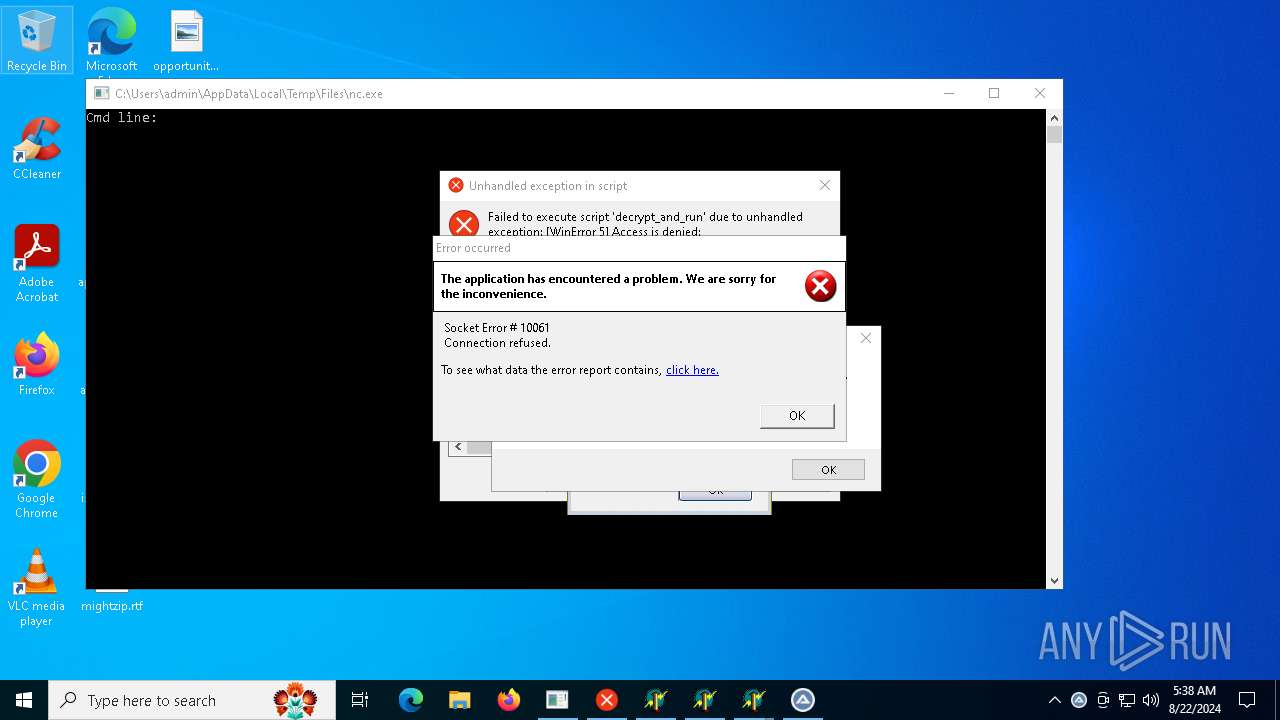
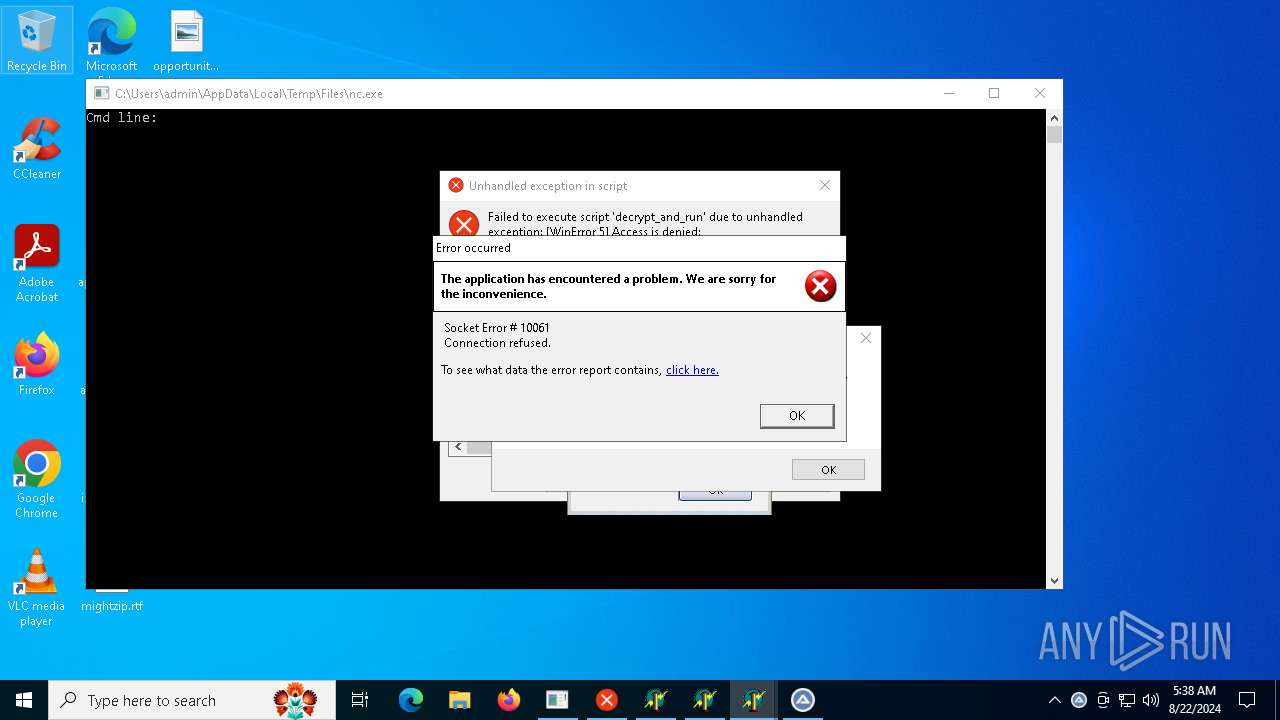
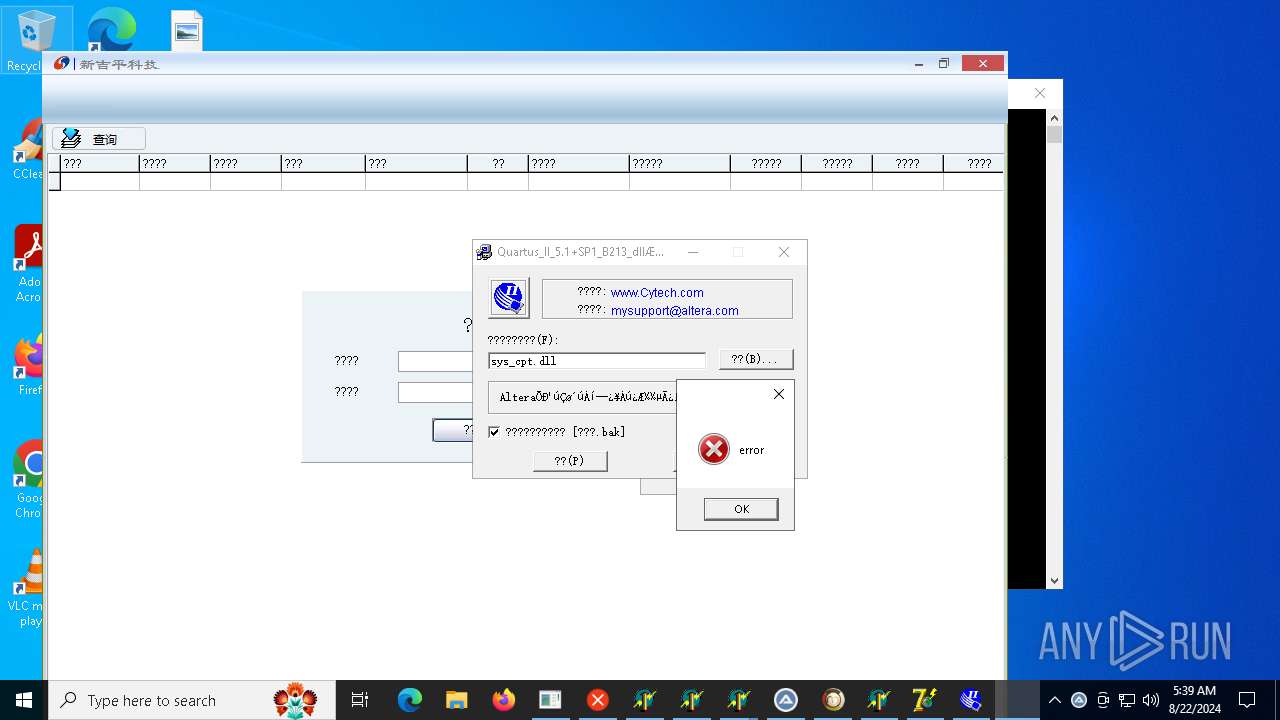
4363463463464363463463463.exe | The specified executable is not a valid application for this OS platform.
|
4363463463464363463463463.exe | The remote server returned an error: (403) Forbidden.
|