| File name: | NSC.exe |
| Full analysis: | https://app.any.run/tasks/646fd521-8a86-4498-b076-0ccbf0067f9f |
| Verdict: | Malicious activity |
| Analysis date: | March 08, 2018, 09:07:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | A97C264BB3D8A9FB96A9921277E384C8 |
| SHA1: | 971B45BDBD3B2F98A302DDB17D77E446919CE96F |
| SHA256: | 2FC21732FD83DB1C3146037A89A8455ABA4DB6434A0331A7F5345C13CB6EDB0D |
| SSDEEP: | 12288:iOQwRFNYVPShL+ikOAX3xcDy/DAjj/ttXjEc0eDcVczYdoIGy1S4feBFMliEho:NQwRxLVkOq3iDwDCtXjqcMmQiR |
MALICIOUS
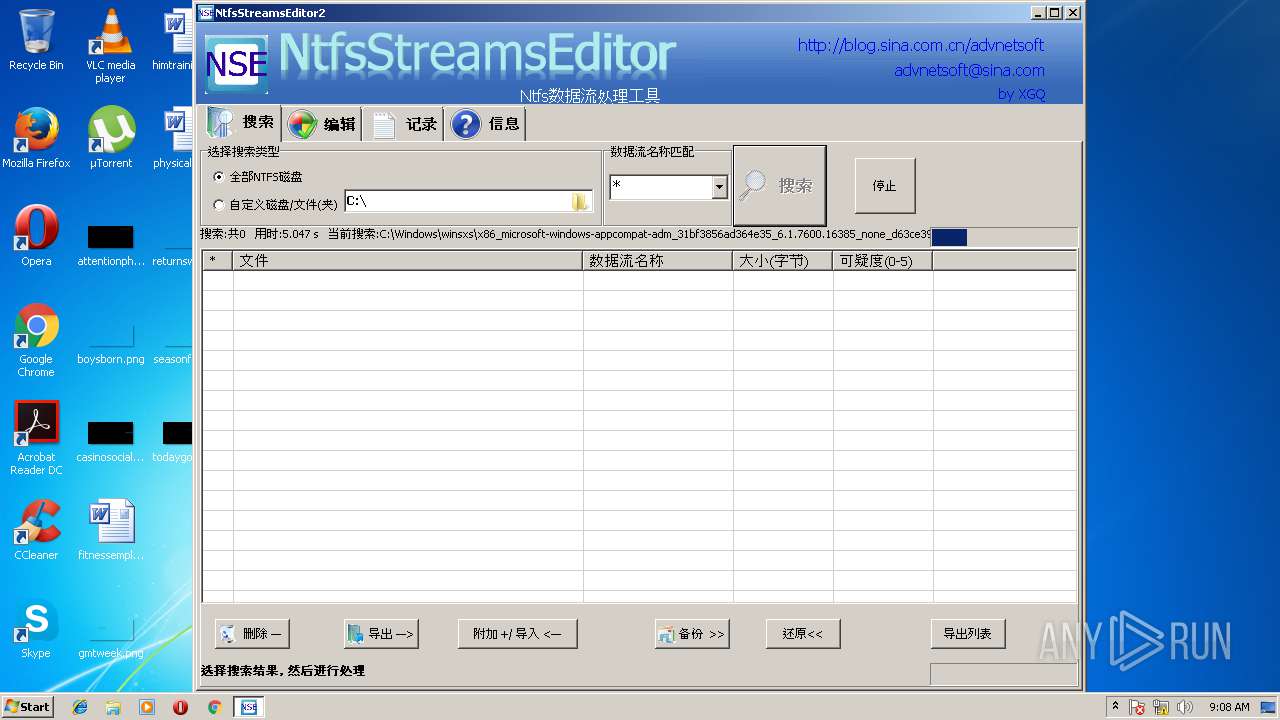
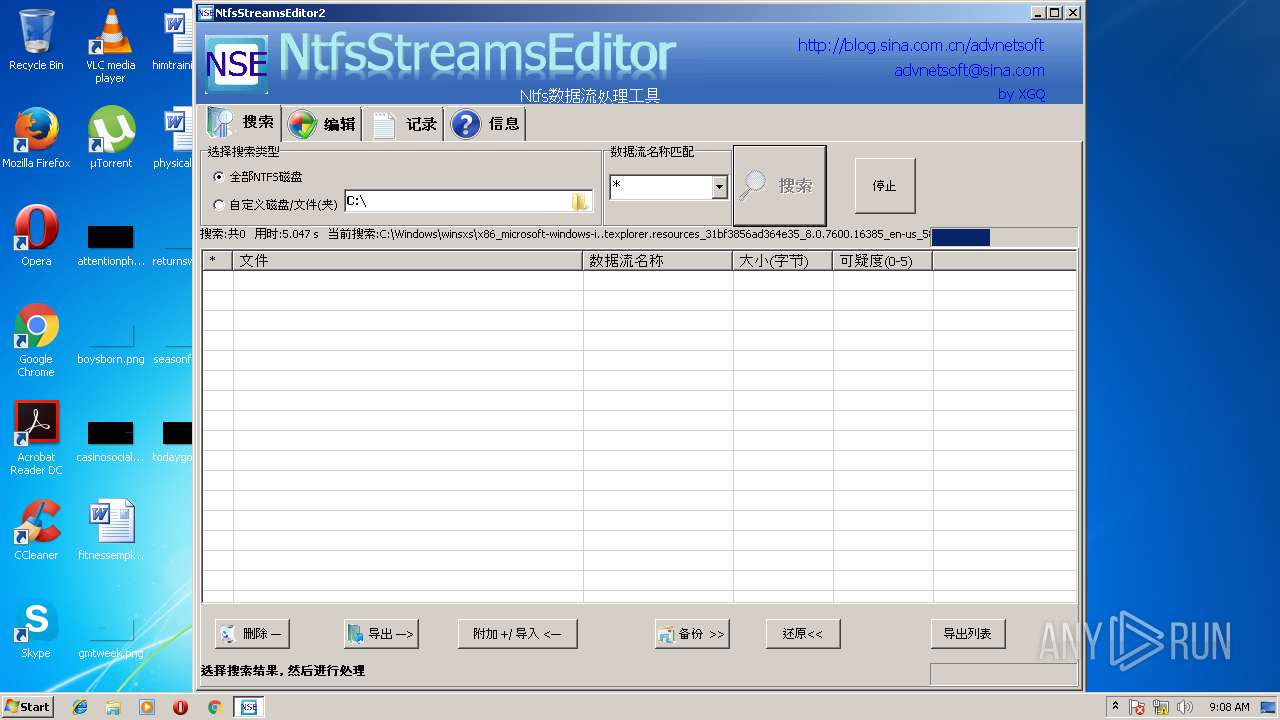
Application was dropped or rewritten from another process
- ntfsstreamseditor.exe (PID: 3144)
SUSPICIOUS
Reads internet explorer settings
- ntfsstreamseditor.exe (PID: 3144)
Creates files in the user directory
- ntfsstreamseditor.exe (PID: 3144)
Modifies the open verb of a shell class
- ntfsstreamseditor.exe (PID: 3144)
INFO
Dropped object may contain URL's
- NSC.exe (PID: 256)
- ntfsstreamseditor.exe (PID: 3144)
Loads rich edit control libraries
- NSC.exe (PID: 256)
Dropped object may contain Bitcoin addresses
- ntfsstreamseditor.exe (PID: 3144)
- NSC.exe (PID: 256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (93.4) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .scr | | | Windows screen saver (1.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:05:05 14:23:41+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3190 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2008.3.11.0 |
| ProductVersionNumber: | 2008.3.11.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 2008.3.11 |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| ProductName: | normal |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-May-2007 12:23:41 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 2008.3.11 |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| ProductName: | normal |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-May-2007 12:23:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005B6E | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47324 |
.rdata | 0x00007000 | 0x00001286 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04135 |
.data | 0x00009000 | 0x00025CB8 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.44289 |
.ndata | 0x0002F000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00038000 | 0x00002668 | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.09298 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.11126 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 1.91924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.68733 | 494 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.86626 | 228 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.9304 | 218 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
37
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | "C:\Users\admin\AppData\Local\Temp\NSC.exe" | C:\Users\admin\AppData\Local\Temp\NSC.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 2008.3.11 Modules
| |||||||||||||||
| 1440 | "C:\Users\admin\AppData\Local\Temp\NSC.exe" | C:\Users\admin\AppData\Local\Temp\NSC.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 2008.3.11 Modules
| |||||||||||||||
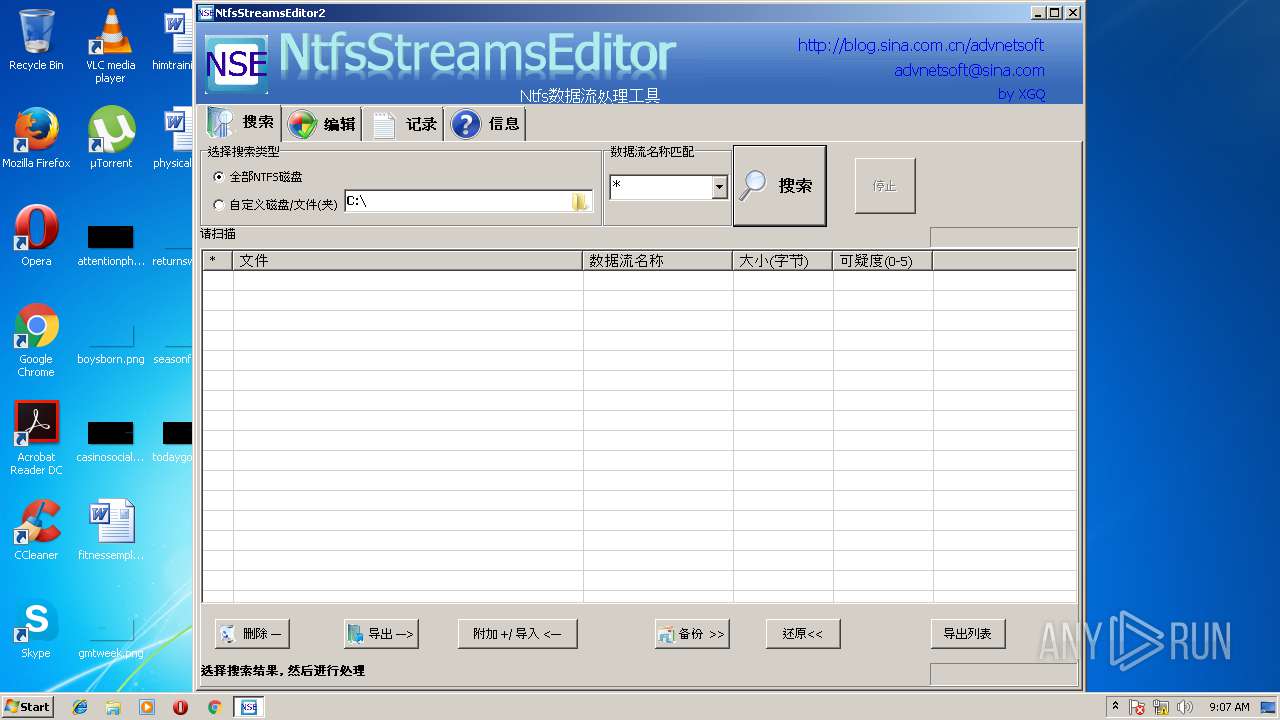
| 3144 | C:\Users\admin\AppData\Local\Temp\nsb2D6C.tmp\ntfsstreamseditor.exe | C:\Users\admin\AppData\Local\Temp\nsb2D6C.tmp\ntfsstreamseditor.exe | — | NSC.exe | |||||||||||
User: admin Company: http://blog.sina.com.cn/advnetsoft Integrity Level: HIGH Description: NtfsStreamsEditor,tool for Ntfs Streams(ADS) Process Exit code: 0 Version: 20090412 Modules
| |||||||||||||||
Total events
136
Read events
112
Write events
24
Delete events
0
Modification events
| (PID) Process: | (256) NSC.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\SearchScopes |
| Operation: | write | Name: | DefaultScope |
Value: {24588FA4-10F1-41D7-B19D-6E22361E47FA} | |||
| (PID) Process: | (256) NSC.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\SearchScopes\{24588FA4-10F1-41D7-B19D-6E22361E47FA} |
| Operation: | write | Name: | Codepage |
Value: 65001 | |||
| (PID) Process: | (256) NSC.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\SearchScopes\{24588FA4-10F1-41D7-B19D-6E22361E47FA} |
| Operation: | write | Name: | DisplayName |
Value: °Ù¶È | |||
| (PID) Process: | (256) NSC.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\SearchScopes\{24588FA4-10F1-41D7-B19D-6E22361E47FA} |
| Operation: | write | Name: | URL |
Value: http://www.baidu.com/s?wd={searchTerms}&tn=site888_1_pg&cl=3&ie=utf-8 | |||
| (PID) Process: | (3144) ntfsstreamseditor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3144) ntfsstreamseditor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3144) ntfsstreamseditor.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\nse |
| Operation: | write | Name: | |
Value: nseProtocol | |||
| (PID) Process: | (3144) ntfsstreamseditor.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\nse |
| Operation: | write | Name: | URL Protocol |
Value: C:\Users\admin\AppData\Local\Temp\nsb2D6C.tmp\ntfsstreamseditor.exe | |||
| (PID) Process: | (3144) ntfsstreamseditor.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\nse\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\Temp\nsb2D6C.tmp\ntfsstreamseditor.exe,1 | |||
| (PID) Process: | (3144) ntfsstreamseditor.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\nse\shell\open\command |
| Operation: | write | Name: | |
Value: "C:\Users\admin\AppData\Local\Temp\nsb2D6C.tmp\ntfsstreamseditor.exe" "%1" | |||
Executable files
1
Suspicious files
0
Text files
6
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 256 | NSC.exe | C:\Users\admin\AppData\Local\Temp\nsb2D6C.tmp\ntfsstreamseditor.exe | executable | |
MD5:— | SHA256:— | |||
| 3144 | ntfsstreamseditor.exe | C:\Users\admin\AppData\Local\Temp\NSE2HELP.mht | eml | |
MD5:— | SHA256:— | |||
| 3144 | ntfsstreamseditor.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\GZH9GIXH\antiTrojan.jpg | image | |
MD5:— | SHA256:— | |||
| 3144 | ntfsstreamseditor.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\GZH9GIXH\logo2.png | image | |
MD5:— | SHA256:— | |||
| 3144 | ntfsstreamseditor.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\GZH9GIXH\wbk305A.tmp | html | |
MD5:— | SHA256:— | |||
| 3144 | ntfsstreamseditor.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\GZH9GIXH\tips.gif | image | |
MD5:— | SHA256:— | |||
| 3144 | ntfsstreamseditor.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\GZH9GIXH\createnewads.png | image | |
MD5:— | SHA256:— | |||
| 3144 | ntfsstreamseditor.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012018030820180309\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3144 | ntfsstreamseditor.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\GZH9GIXH\info.gif | image | |
MD5:17CBED6170CA1137A42C78200315509B | SHA256:9E831B5C9125A94B0EFF525FF40ABC9D8BCF4F71879E54591F77CE534B32562A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report