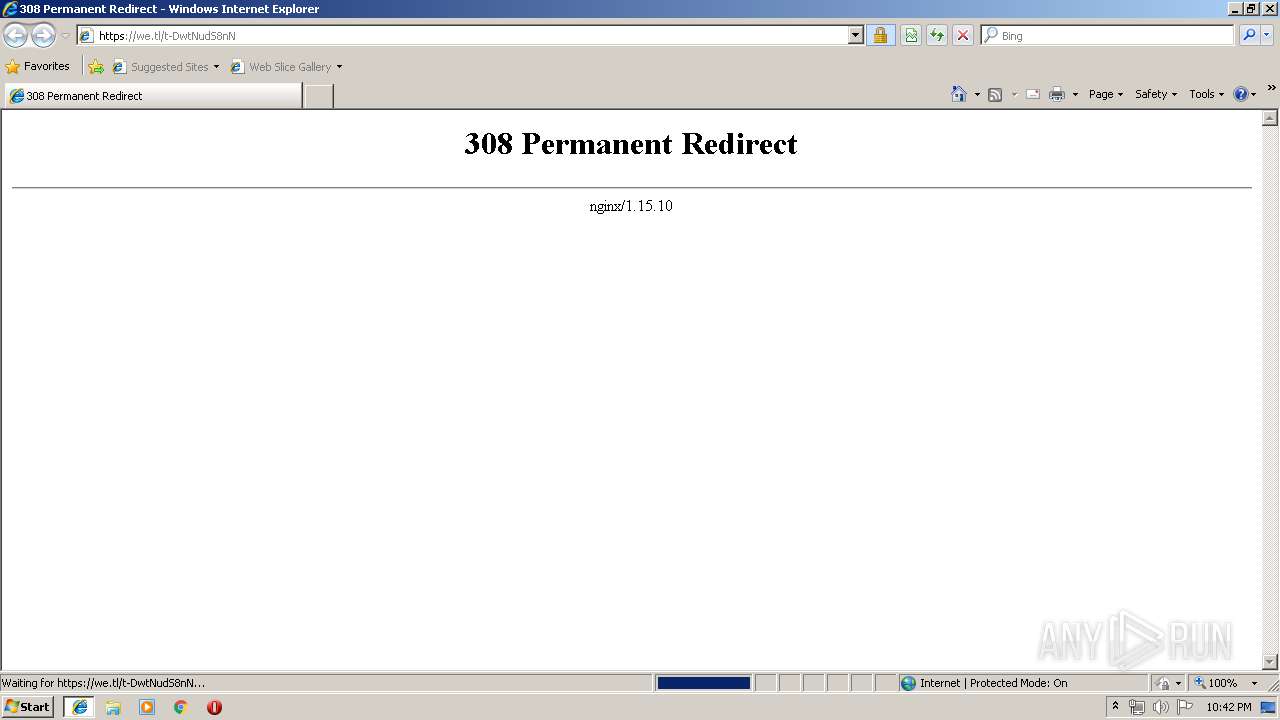
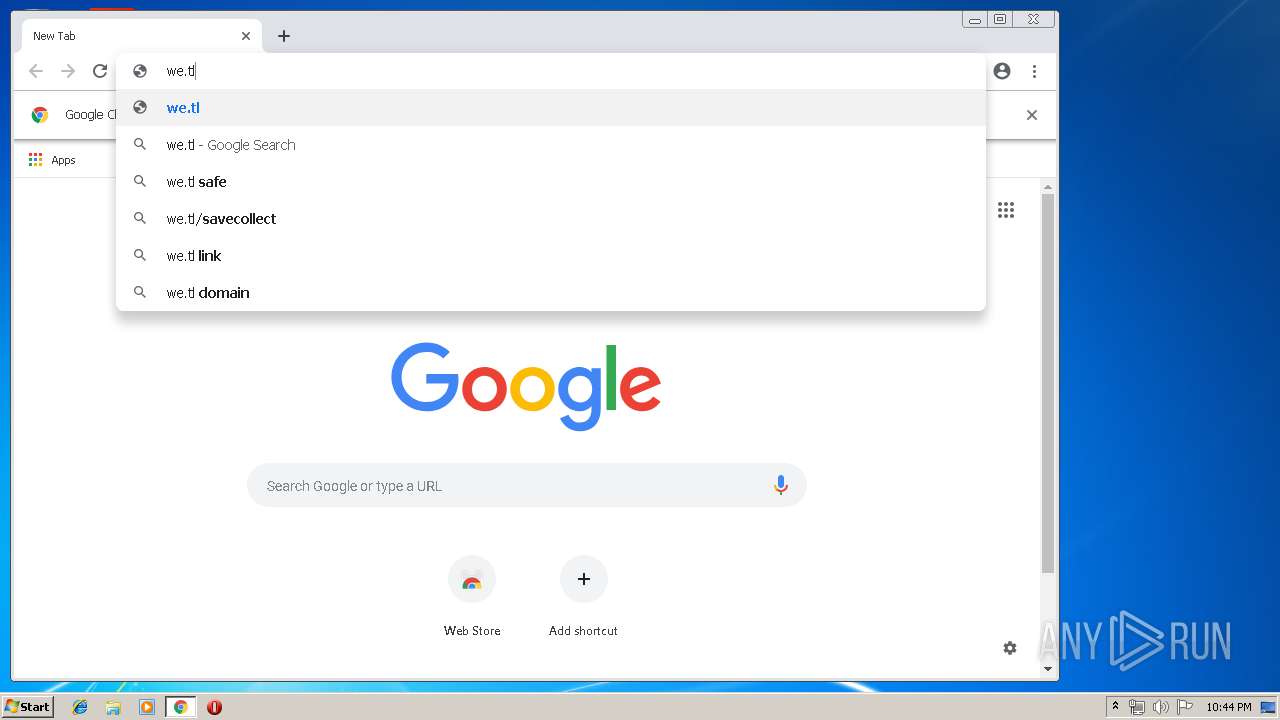
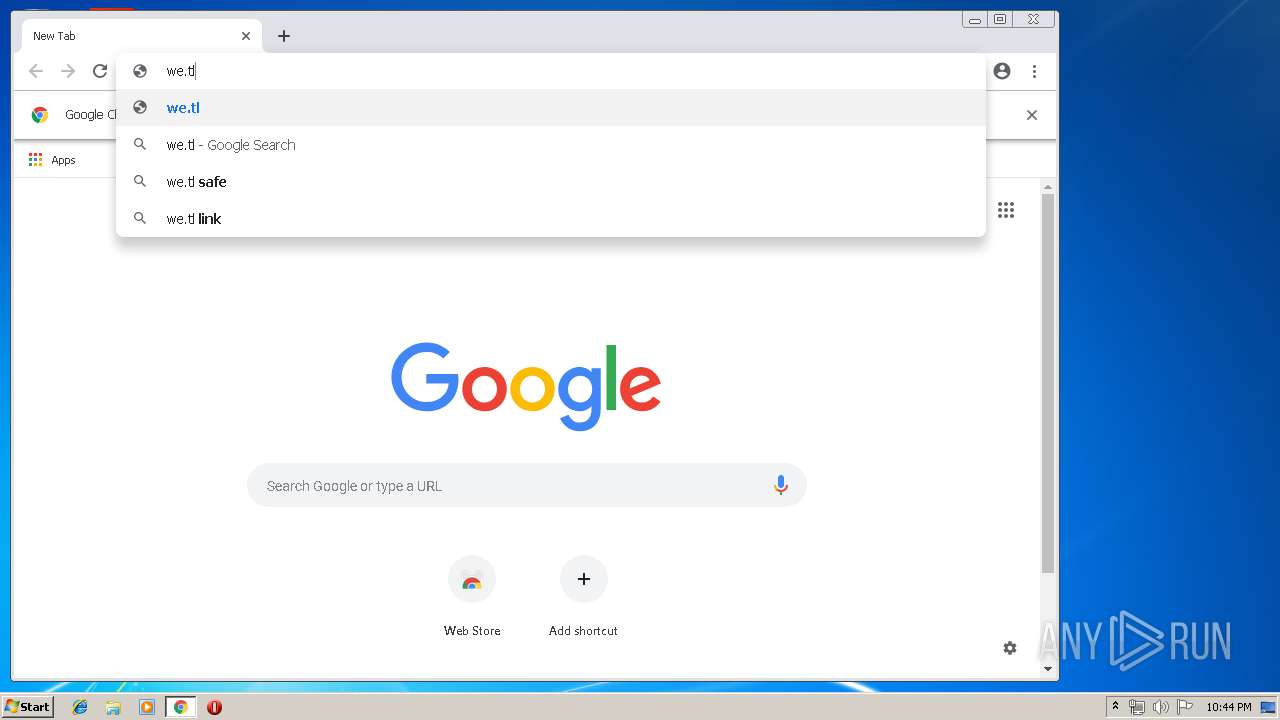
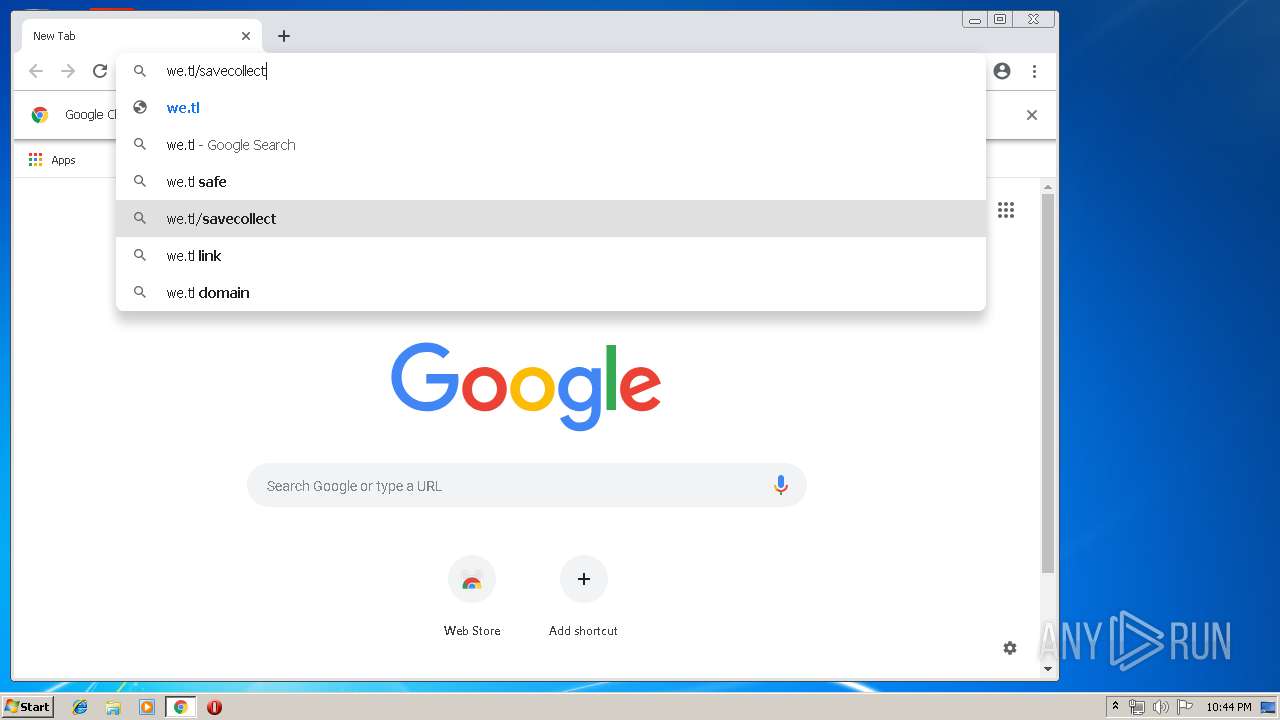
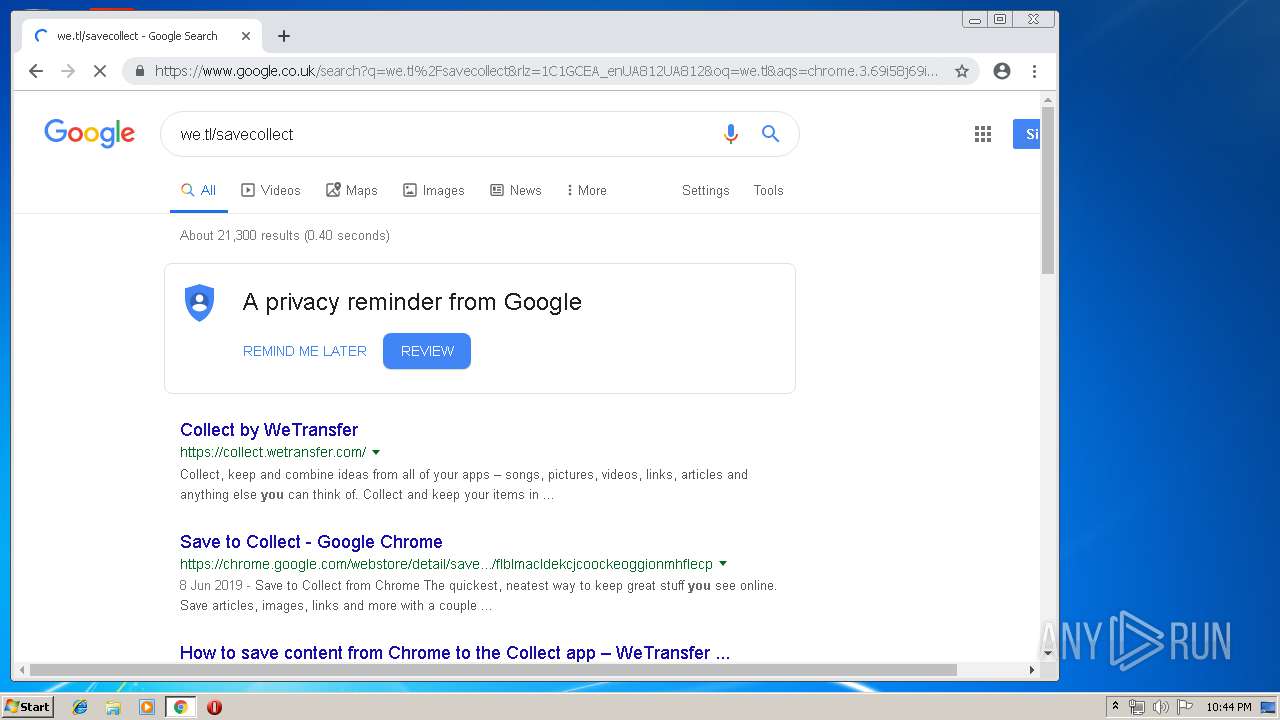
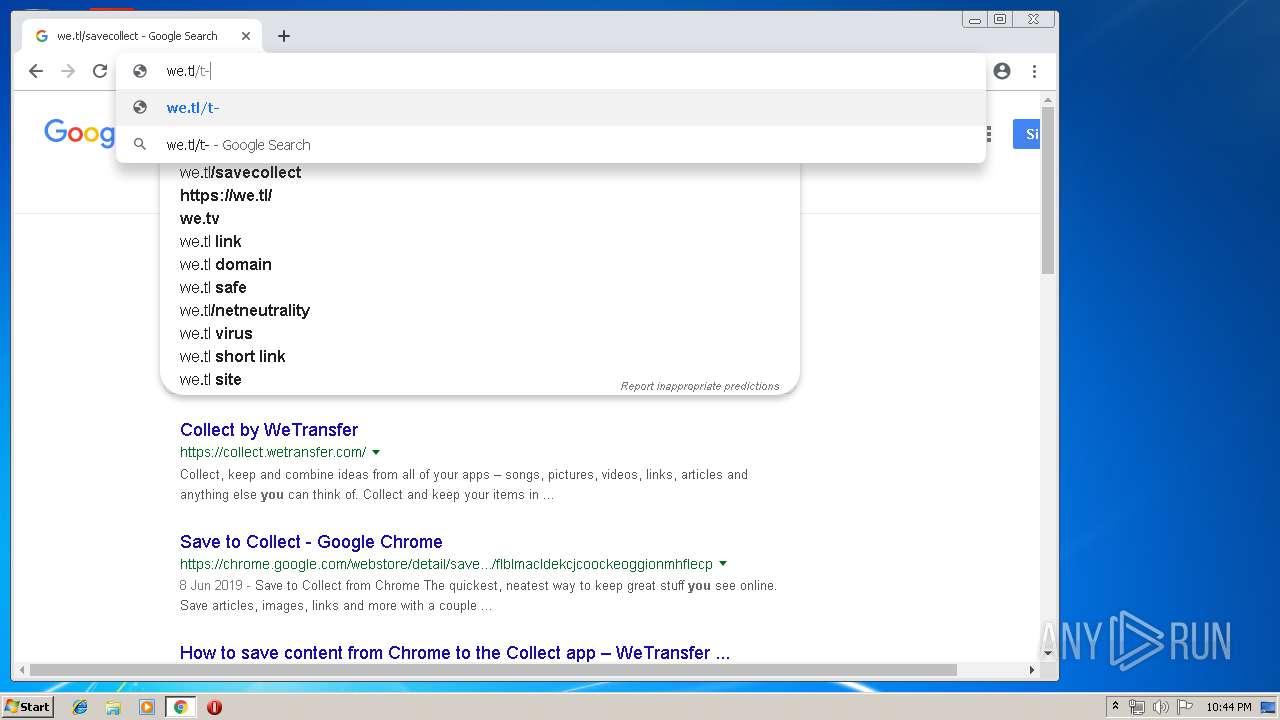
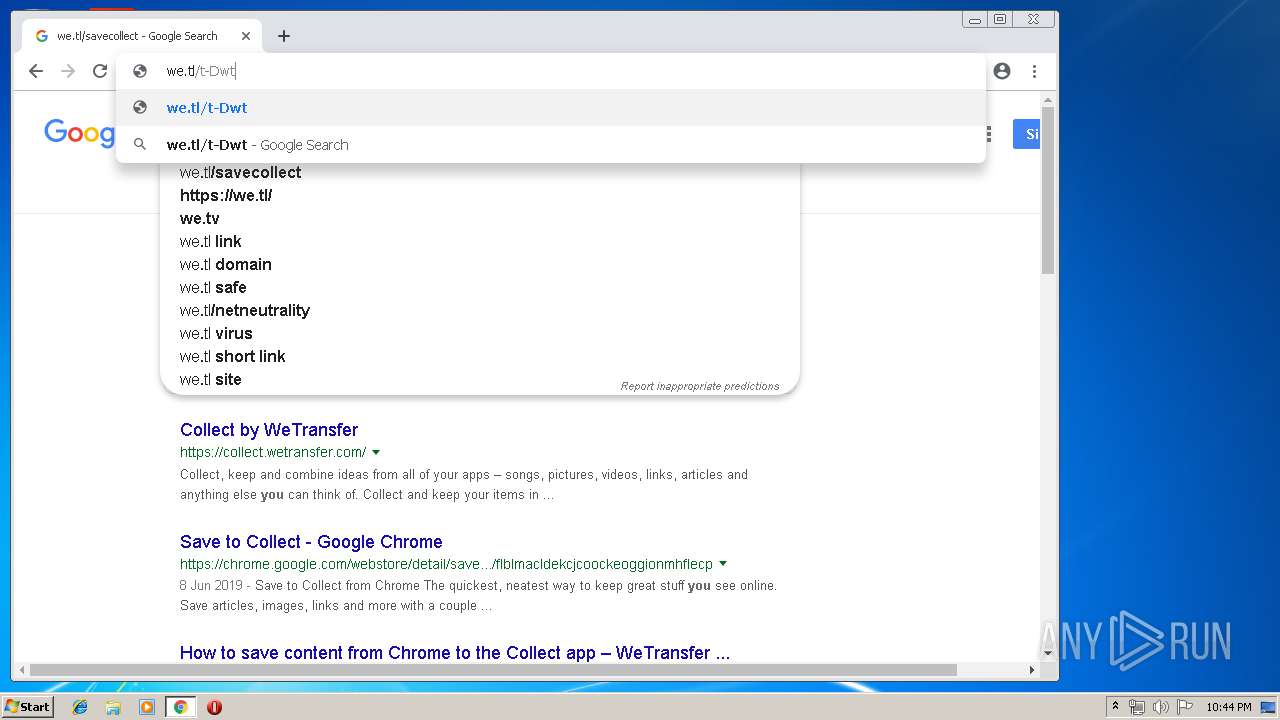
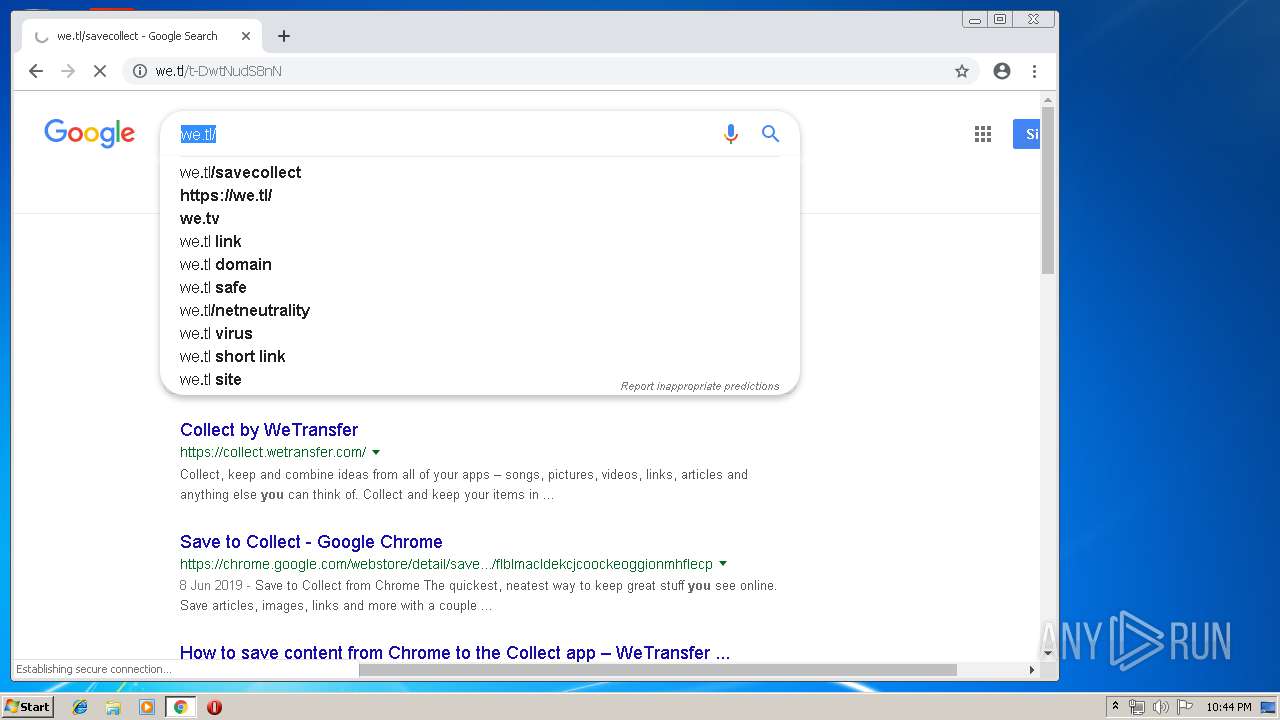
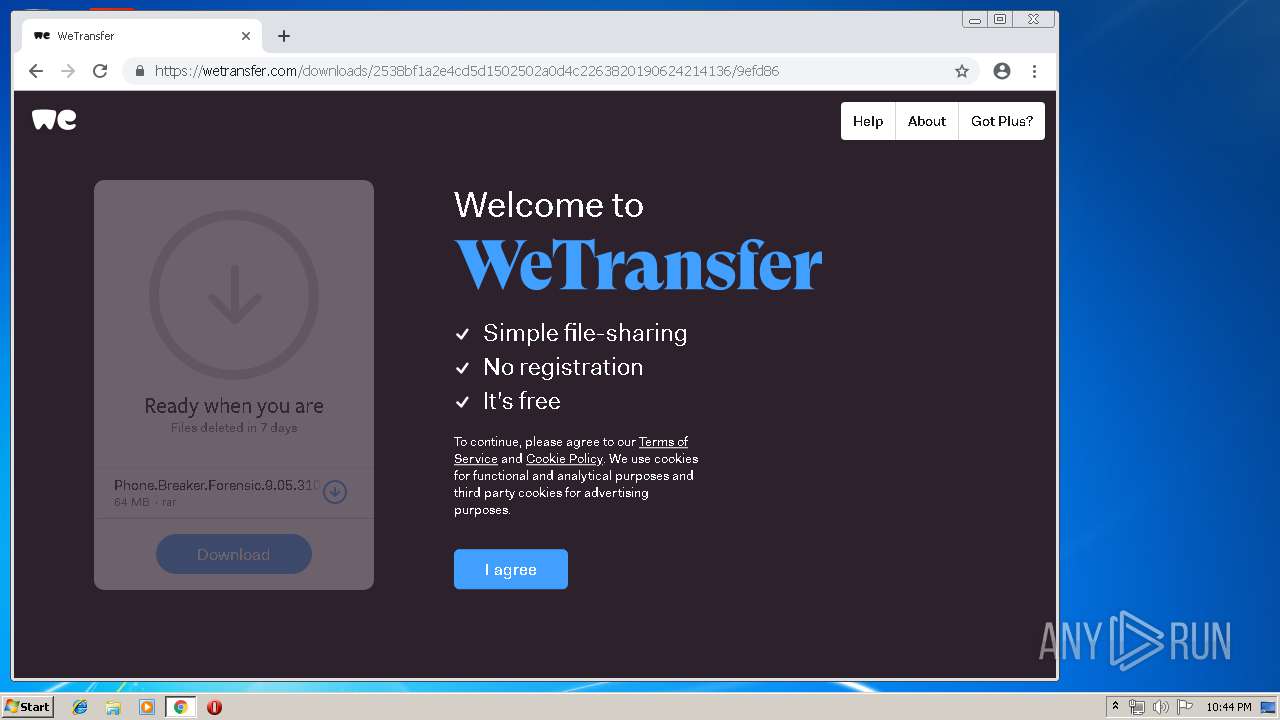
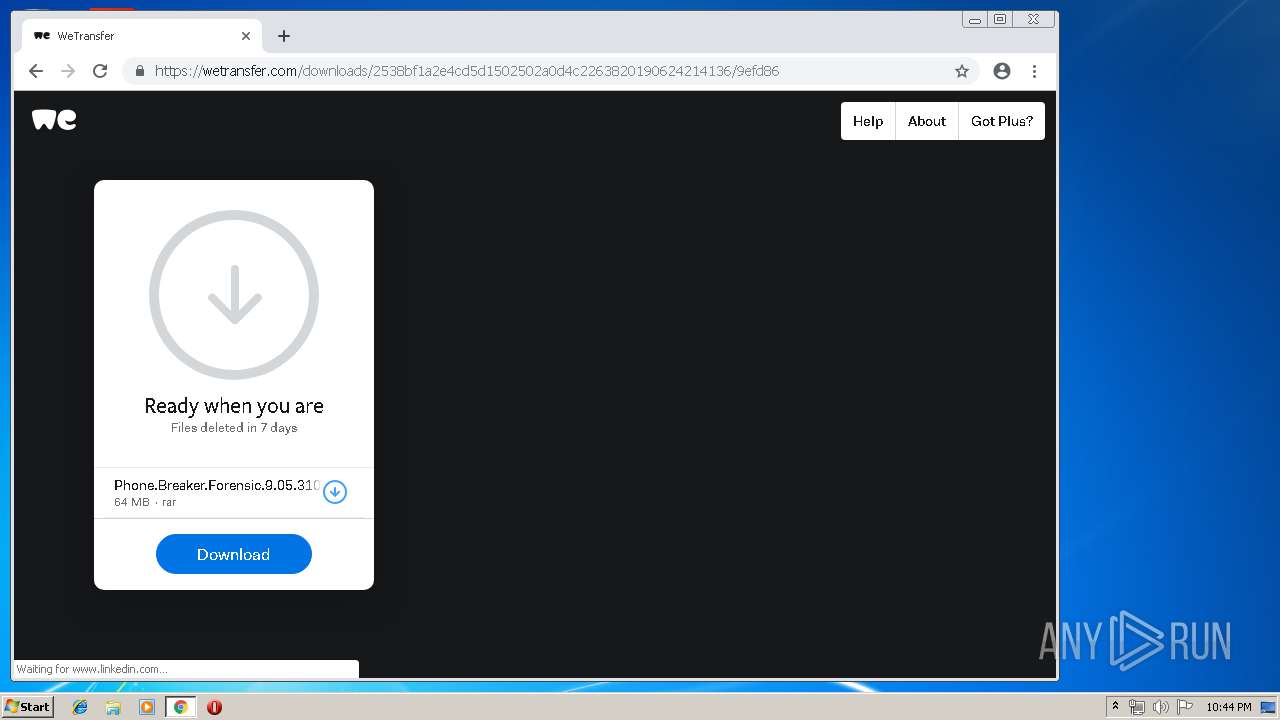
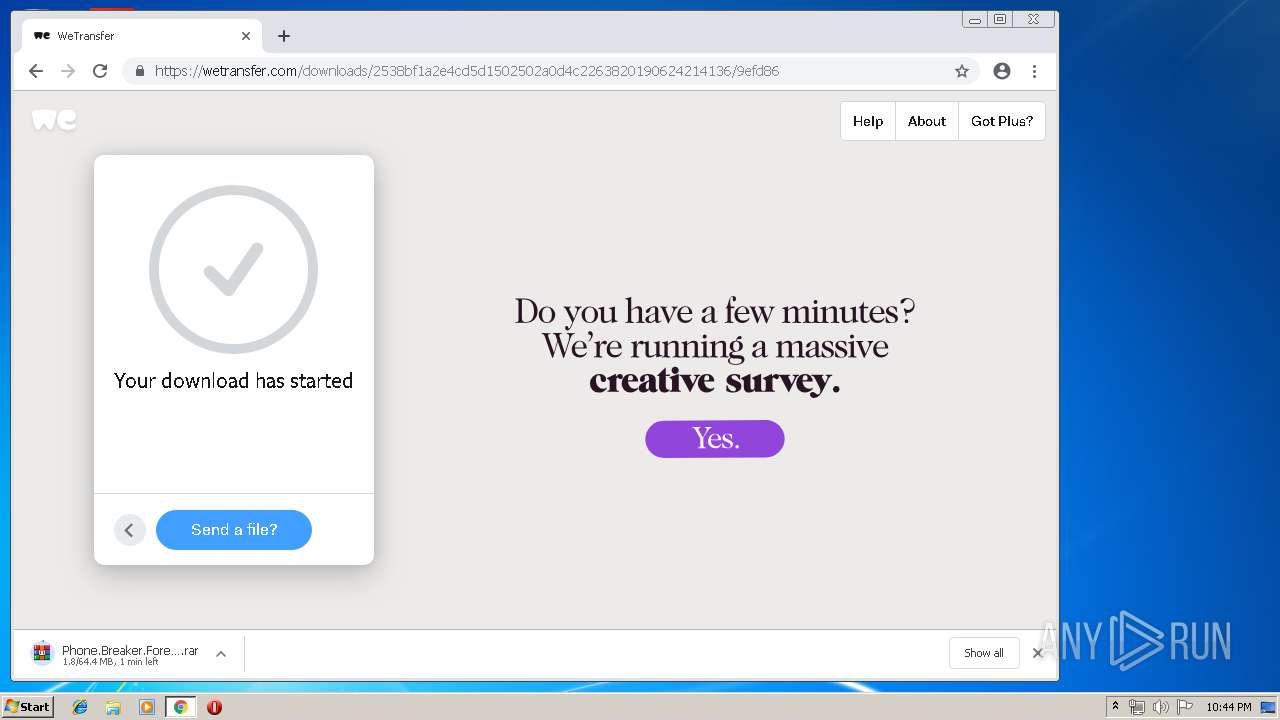
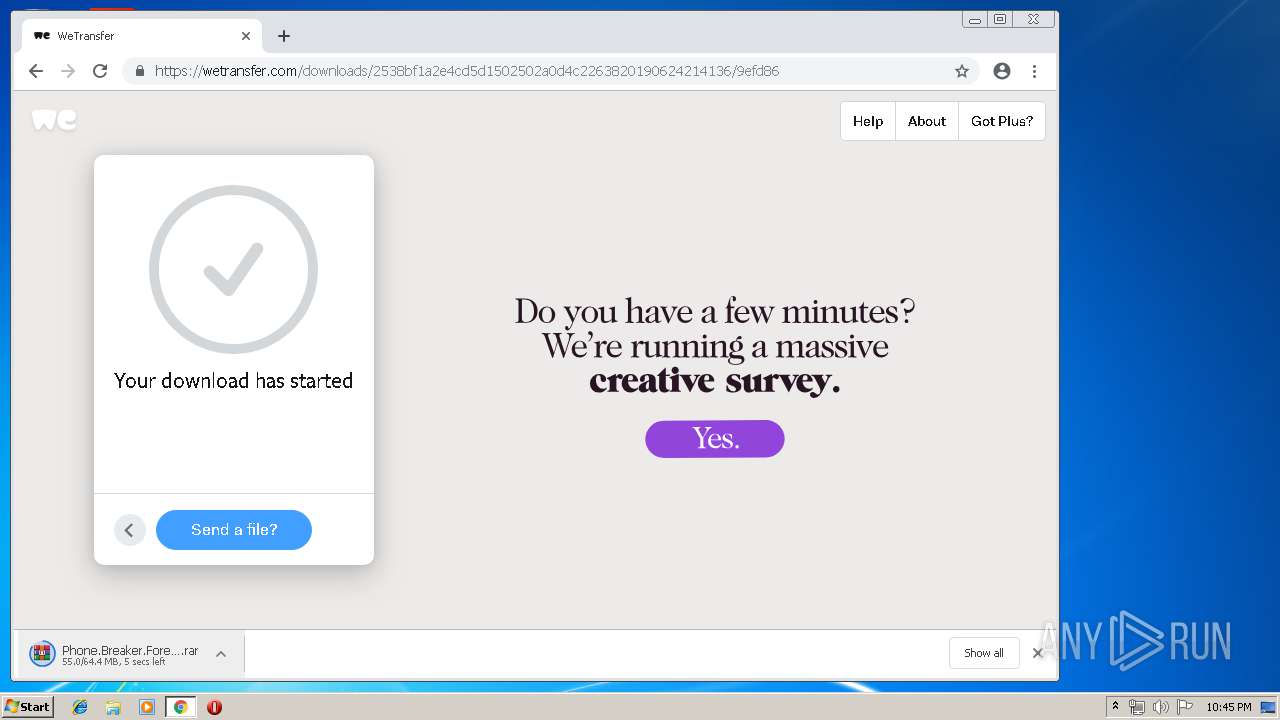
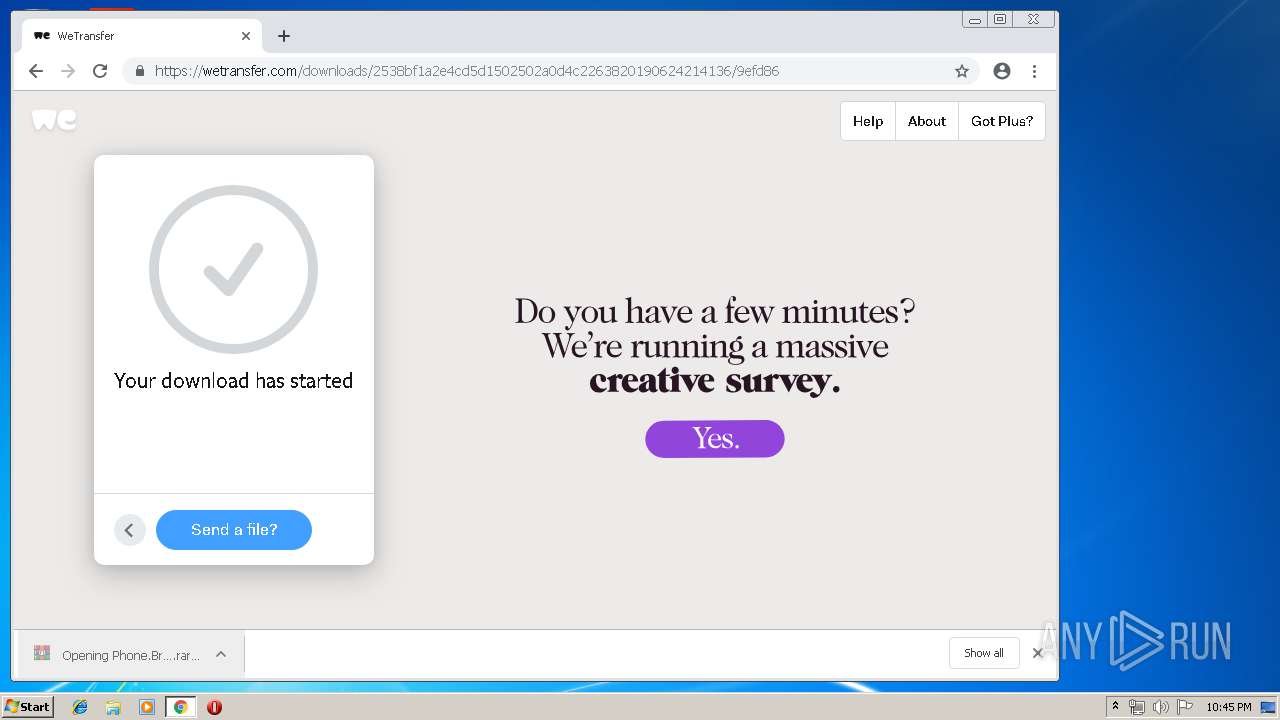
| URL: | https://we.tl/t-DwtNudS8nN |
| Full analysis: | https://app.any.run/tasks/231124b2-6aec-420b-99fa-fb4c660a9041 |
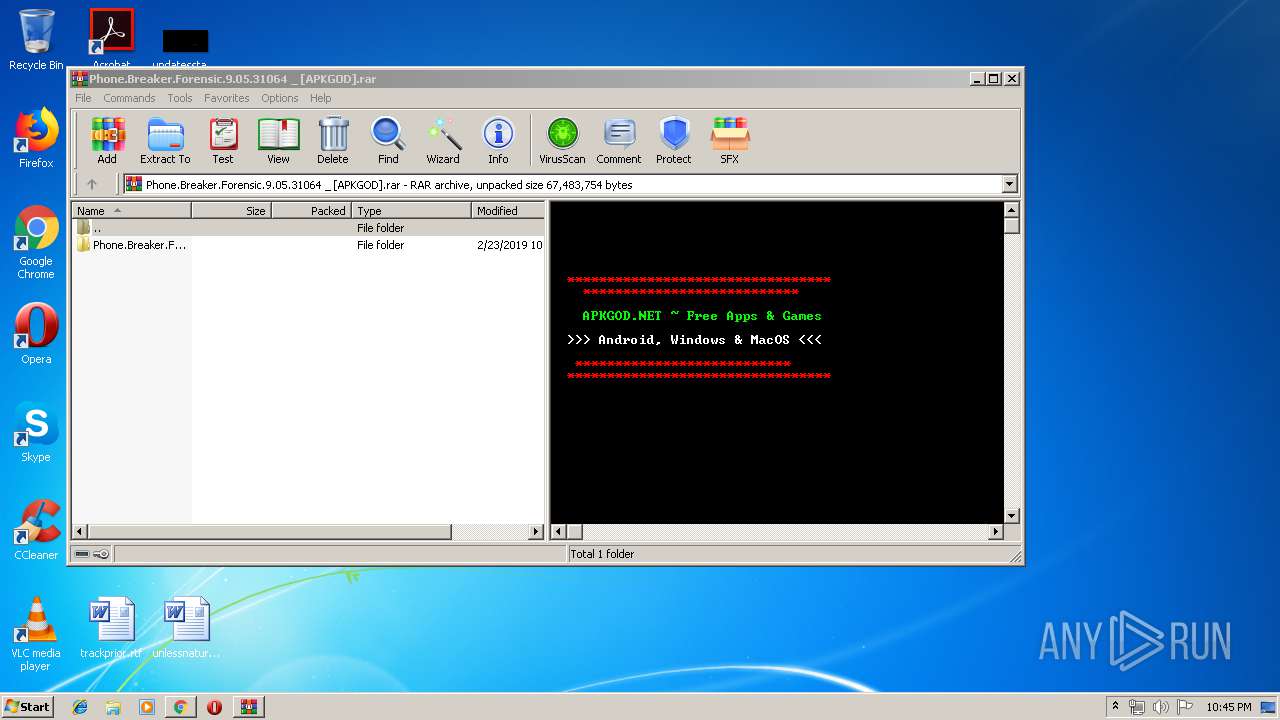
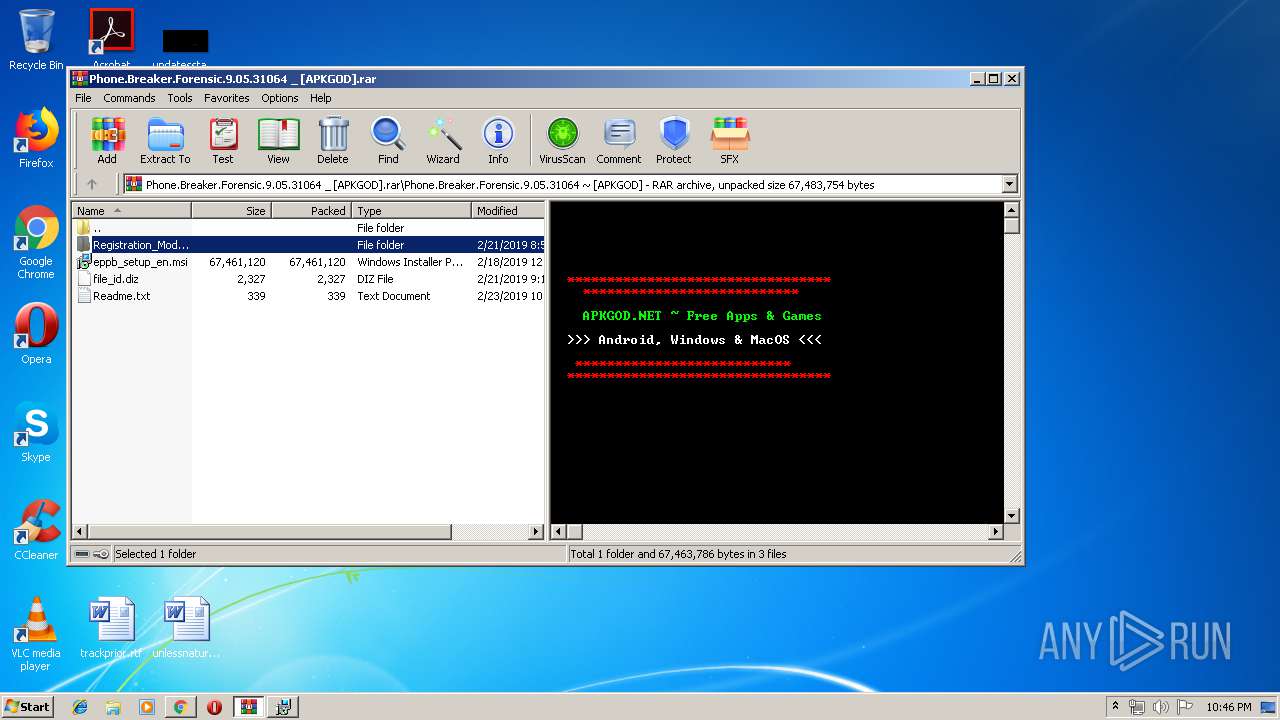
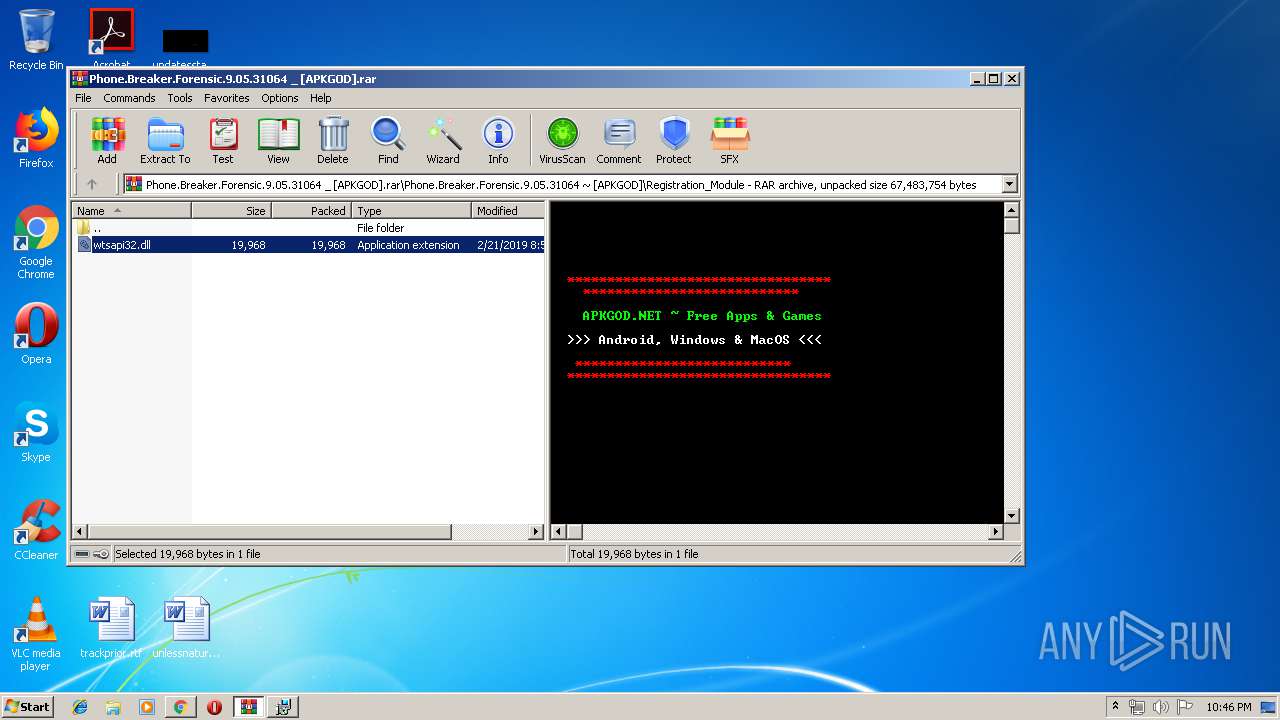
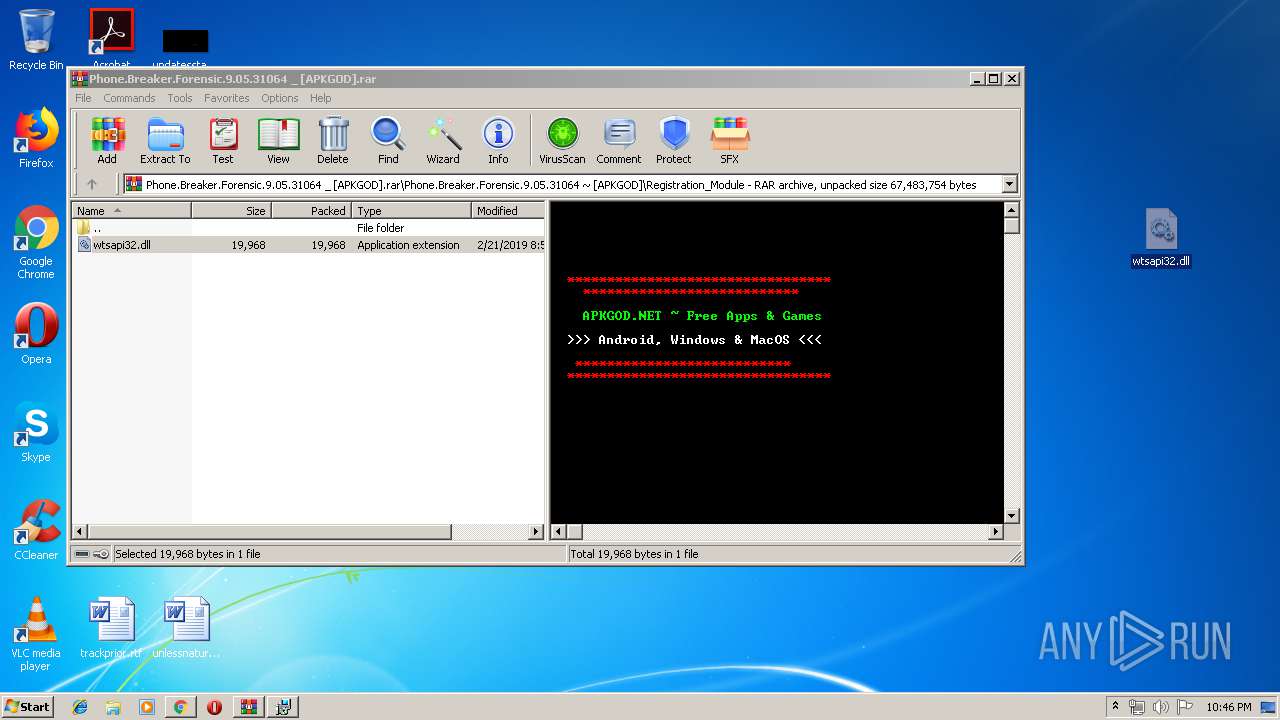
| Verdict: | Malicious activity |
| Analysis date: | June 24, 2019, 21:42:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8DAD367890D8D75850A77C087BF9E475 |
| SHA1: | 4D877BDC05C0537C77C6EB23D810C60766281055 |
| SHA256: | 2FC1E489DEC5FDA2A73BBF01BEBF765984AF529DA2043995C05175BE77C4C5C8 |
| SSDEEP: | 3:N8RlJKual:2q |
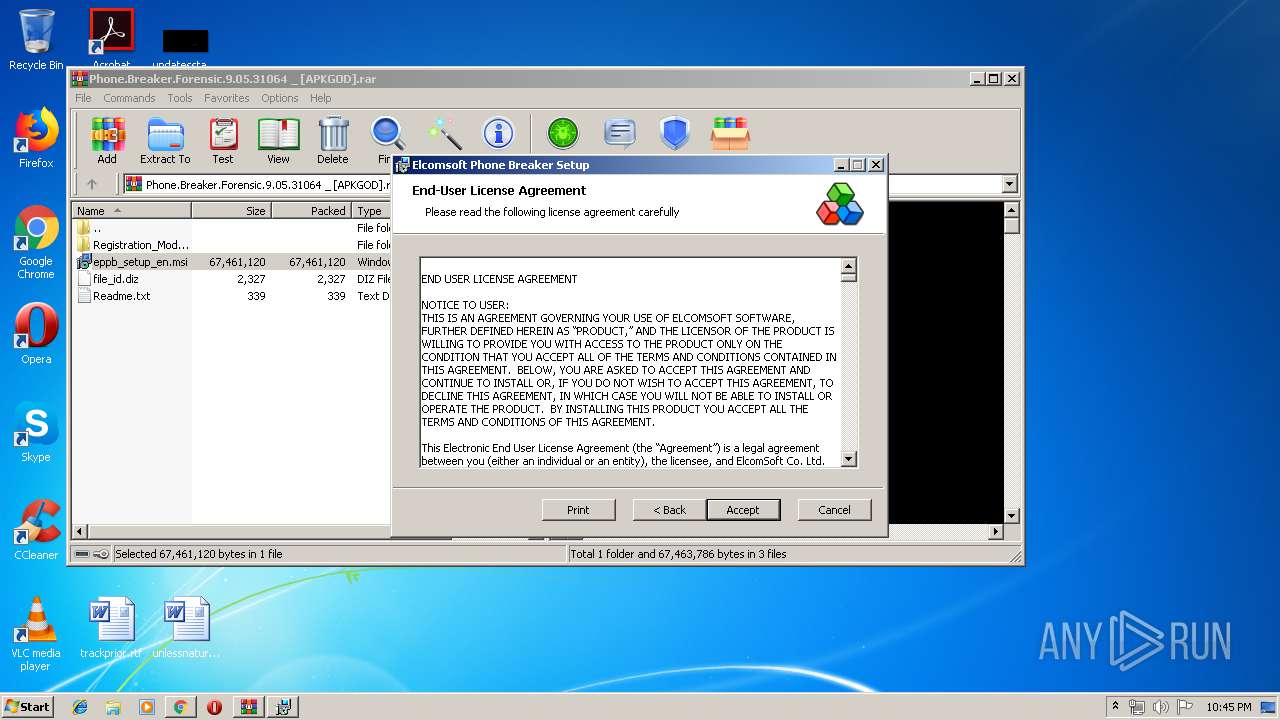
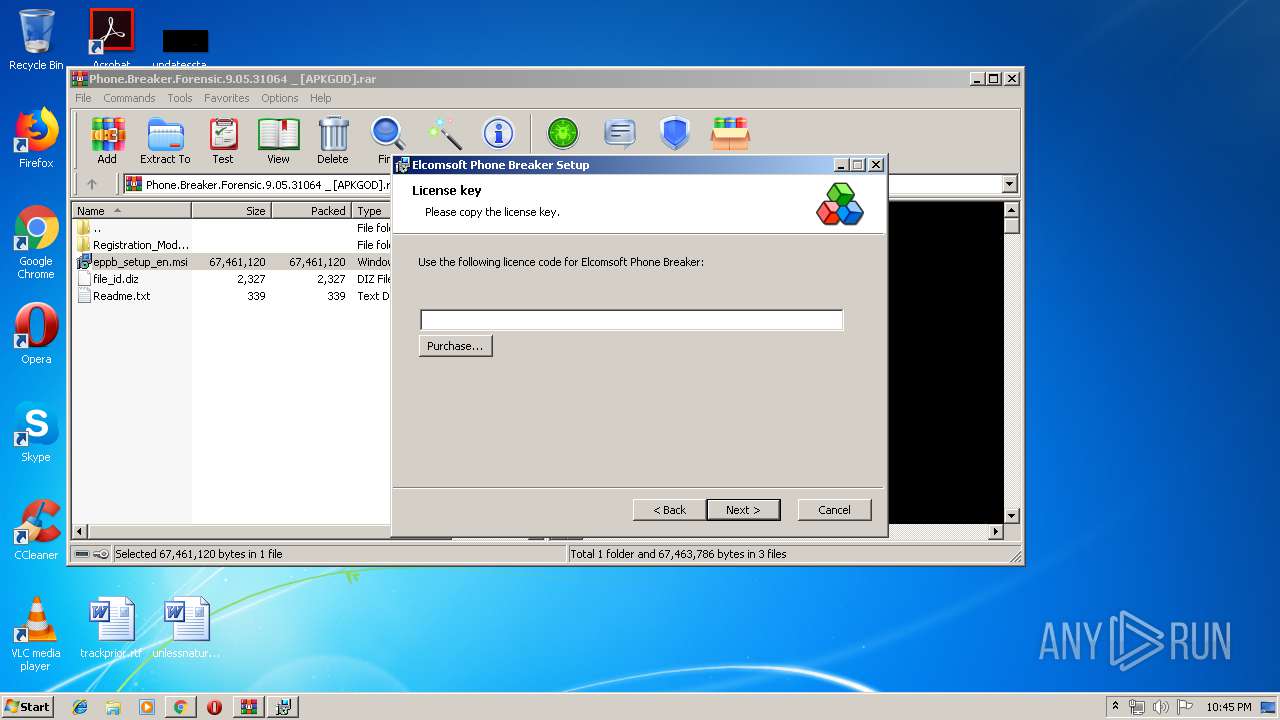
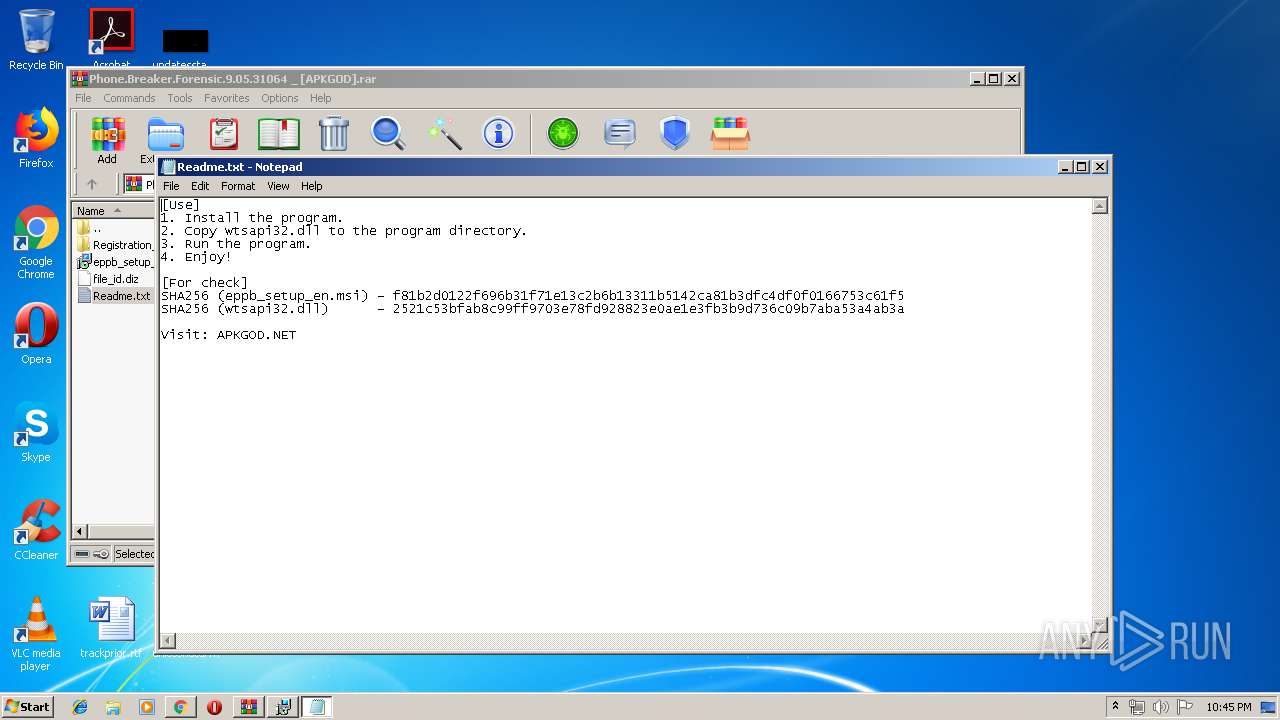
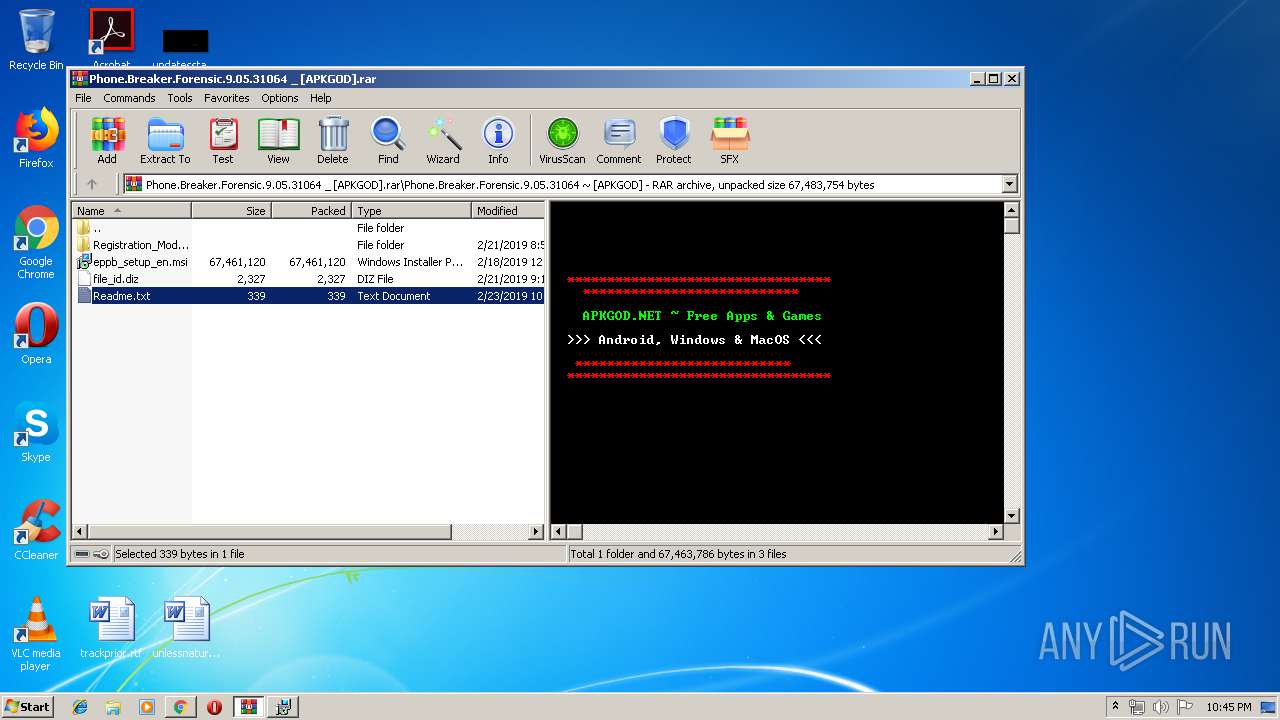
MALICIOUS
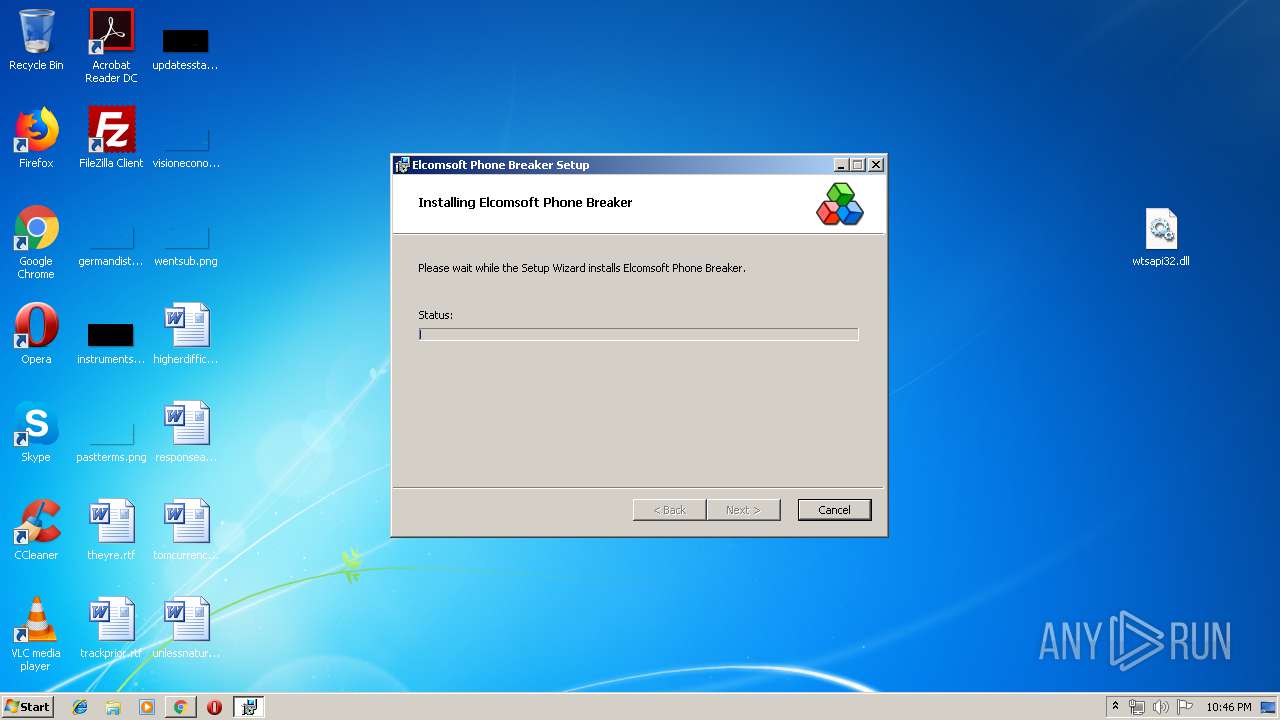
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2148)
- updater-launcher.exe (PID: 1824)
- updater.exe (PID: 2504)
- explorer.exe (PID: 2036)
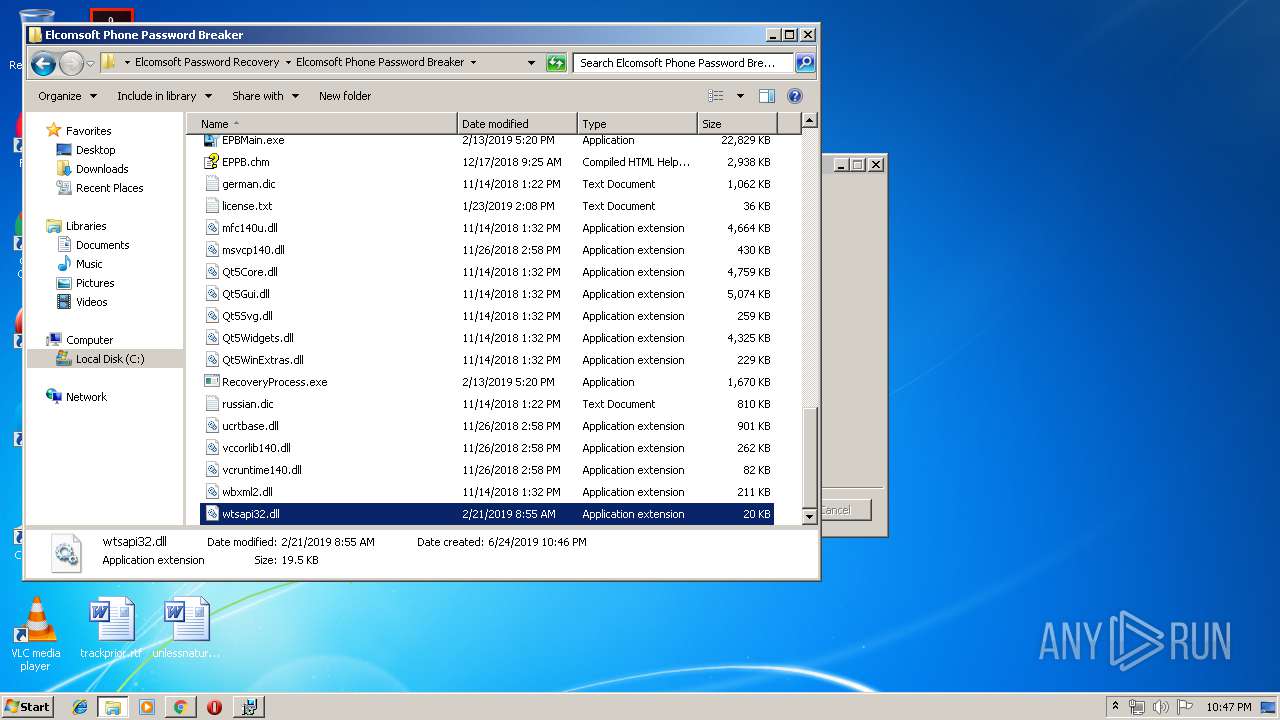
- EPB.exe (PID: 2648)
- EPBMain.exe (PID: 1568)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1416)
- schtasks.exe (PID: 1548)
- schtasks.exe (PID: 3912)
- schtasks.exe (PID: 3016)
Uses Task Scheduler to run other applications
- MSI4AF2.tmp (PID: 1040)
- MSI49F7.tmp (PID: 2300)
- MSI4BFD.tmp (PID: 3916)
Uses Task Scheduler to autorun other applications
- MSI48DD.tmp (PID: 2940)
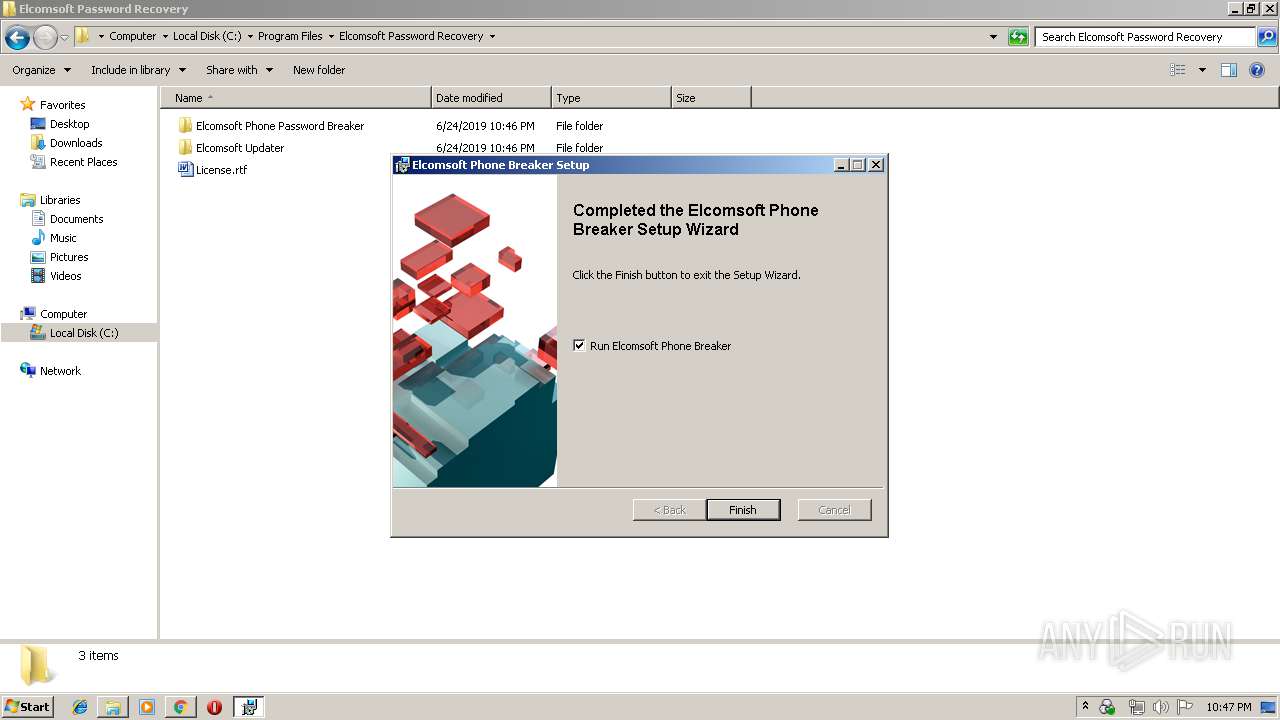
Application was dropped or rewritten from another process
- updater-launcher.exe (PID: 1824)
- updater.exe (PID: 2504)
- EPB.exe (PID: 2648)
- EPBMain.exe (PID: 1568)
SUSPICIOUS
Starts Internet Explorer
- explorer.exe (PID: 2036)
Reads Internet Cache Settings
- explorer.exe (PID: 2036)
Creates files in the user directory
- explorer.exe (PID: 2036)
- updater.exe (PID: 2504)
- EPBMain.exe (PID: 1568)
Modifies files in Chrome extension folder
- chrome.exe (PID: 628)
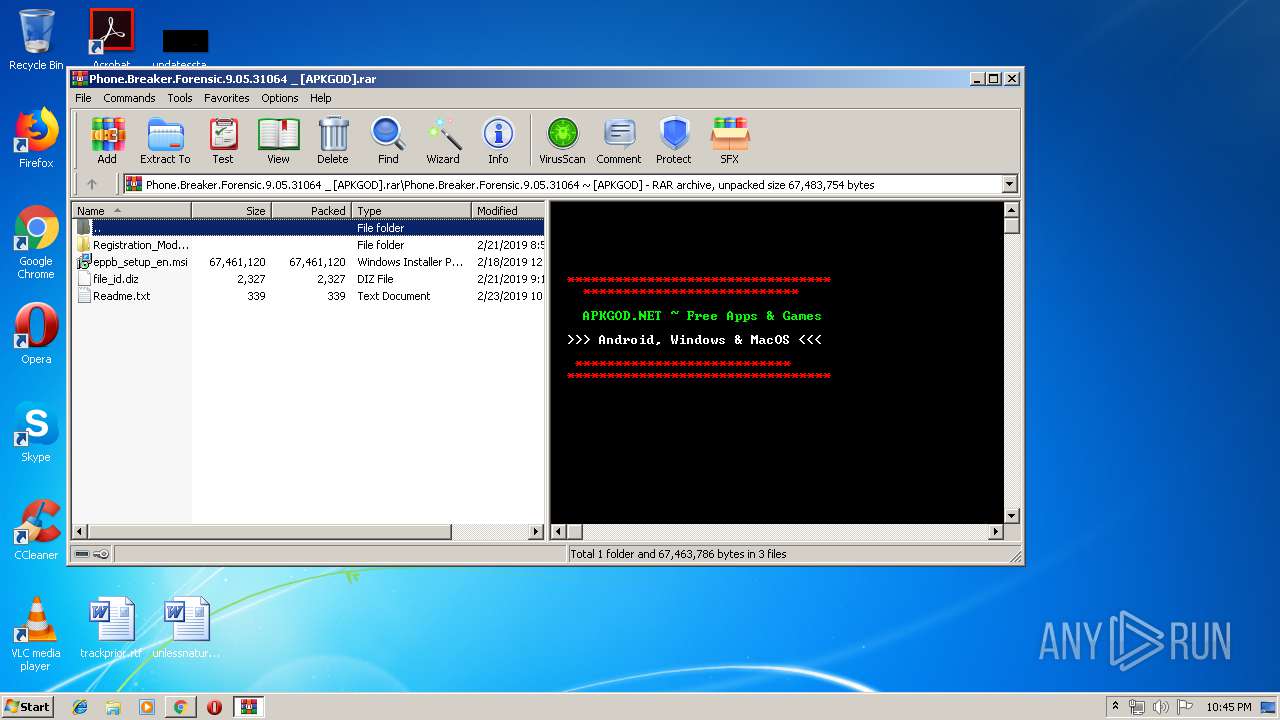
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3088)
- msiexec.exe (PID: 3964)
- msiexec.exe (PID: 3580)
- DllHost.exe (PID: 3792)
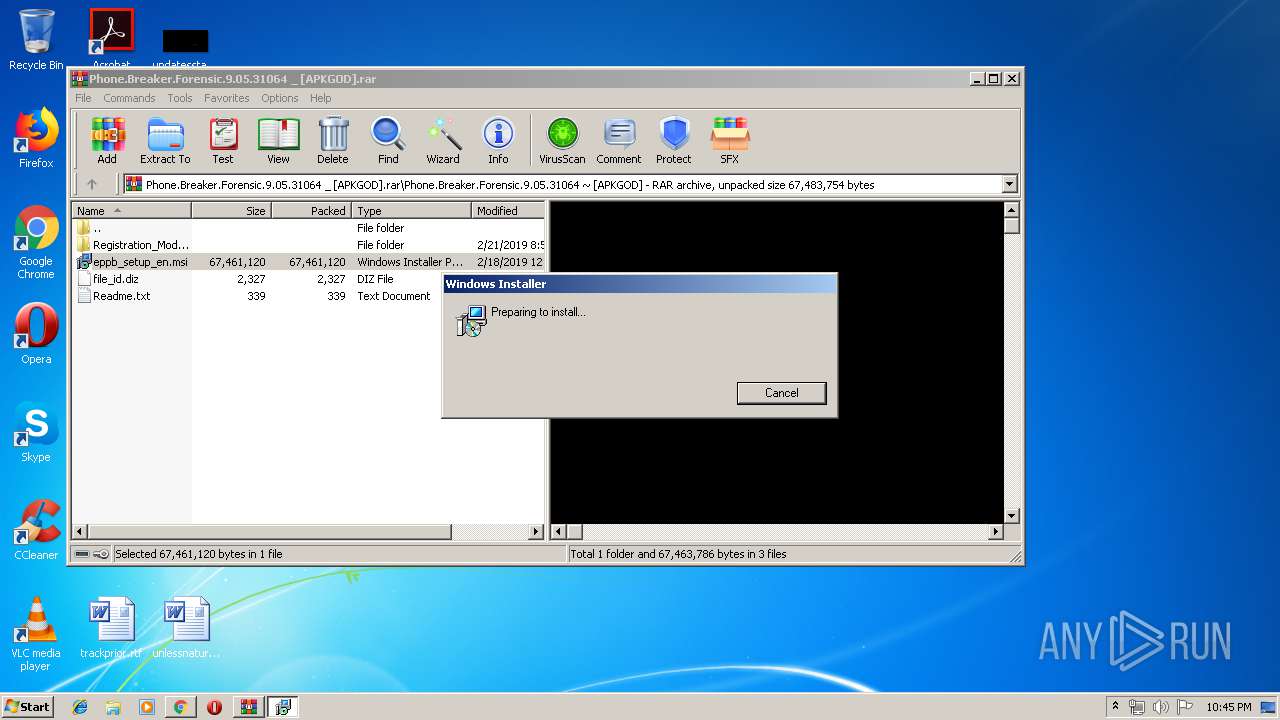
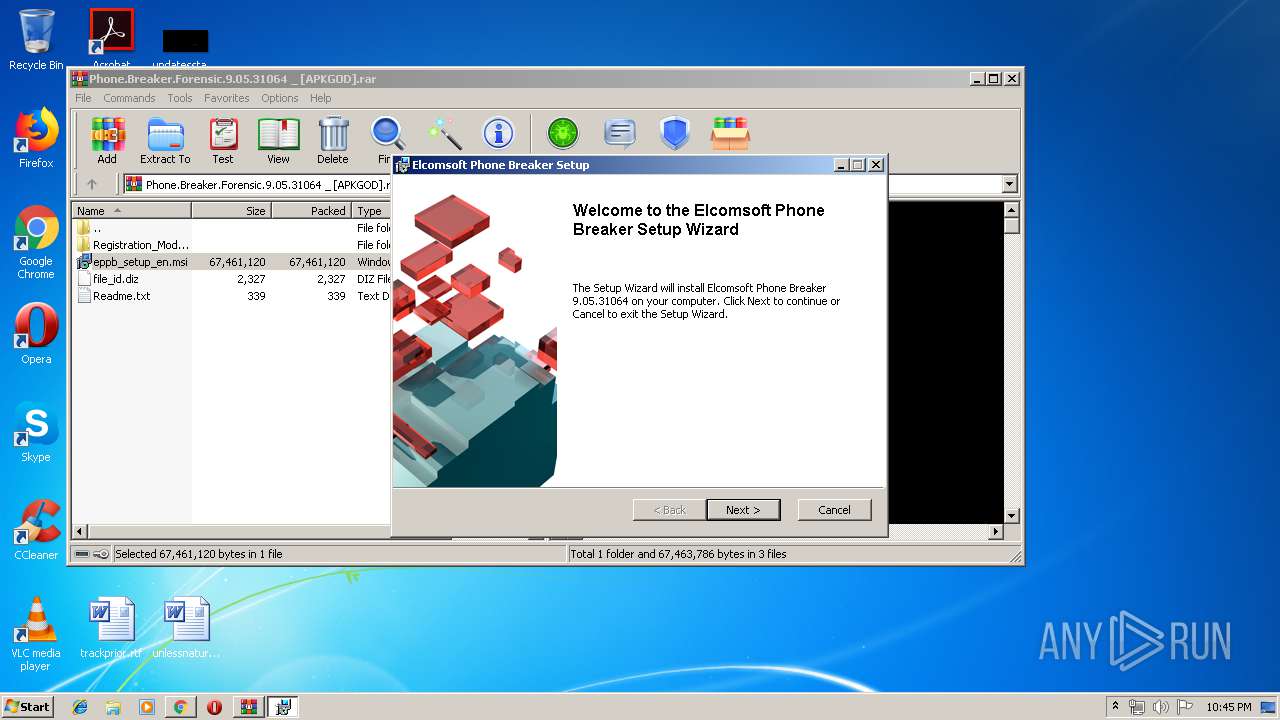
Starts Microsoft Installer
- WinRAR.exe (PID: 3088)
Executed as Windows Service
- vssvc.exe (PID: 3324)
Executed via COM
- DrvInst.exe (PID: 1880)
- DllHost.exe (PID: 3792)
Executed via Task Scheduler
- updater-launcher.exe (PID: 1824)
Creates files in the program directory
- updater.exe (PID: 2504)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3084)
Creates files in the user directory
- iexplore.exe (PID: 3084)
- iexplore.exe (PID: 928)
Reads Internet Cache Settings
- iexplore.exe (PID: 928)
- chrome.exe (PID: 628)
Application launched itself
- chrome.exe (PID: 628)
- iexplore.exe (PID: 3084)
- msiexec.exe (PID: 3580)
Reads settings of System Certificates
- iexplore.exe (PID: 3084)
- chrome.exe (PID: 628)
Reads internet explorer settings
- iexplore.exe (PID: 928)
Changes settings of System certificates
- iexplore.exe (PID: 3084)
- DrvInst.exe (PID: 1880)
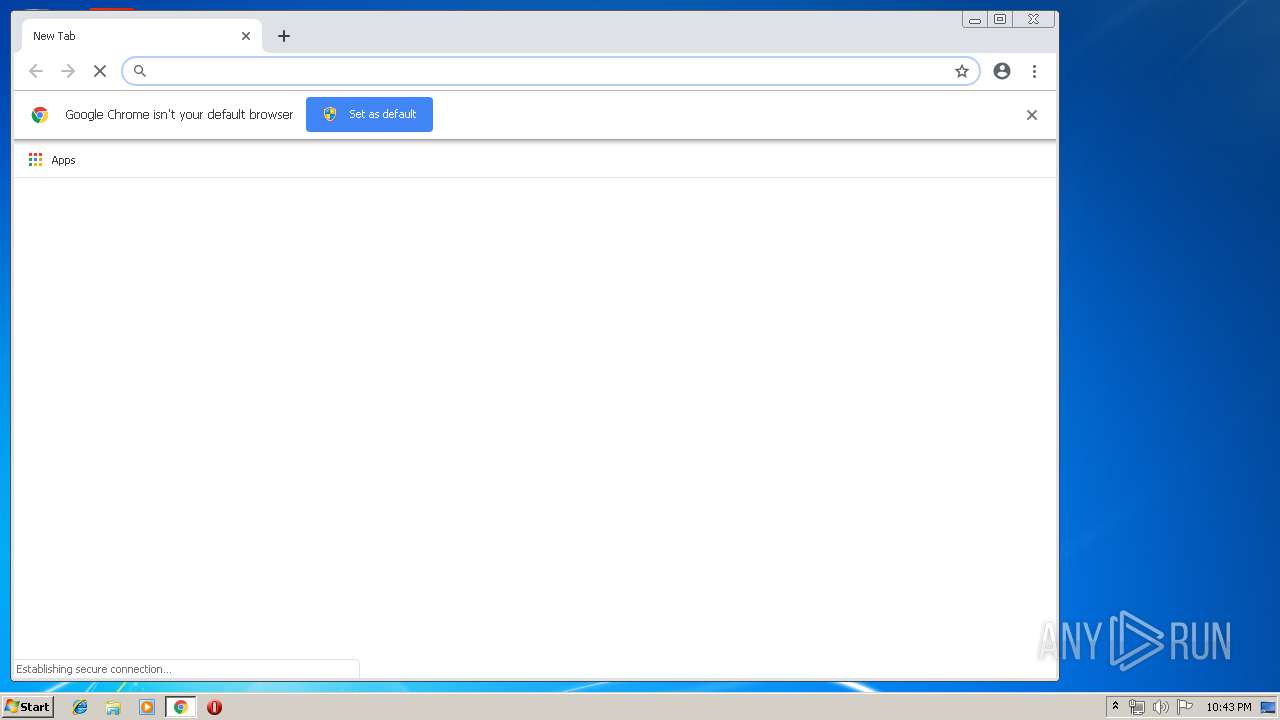
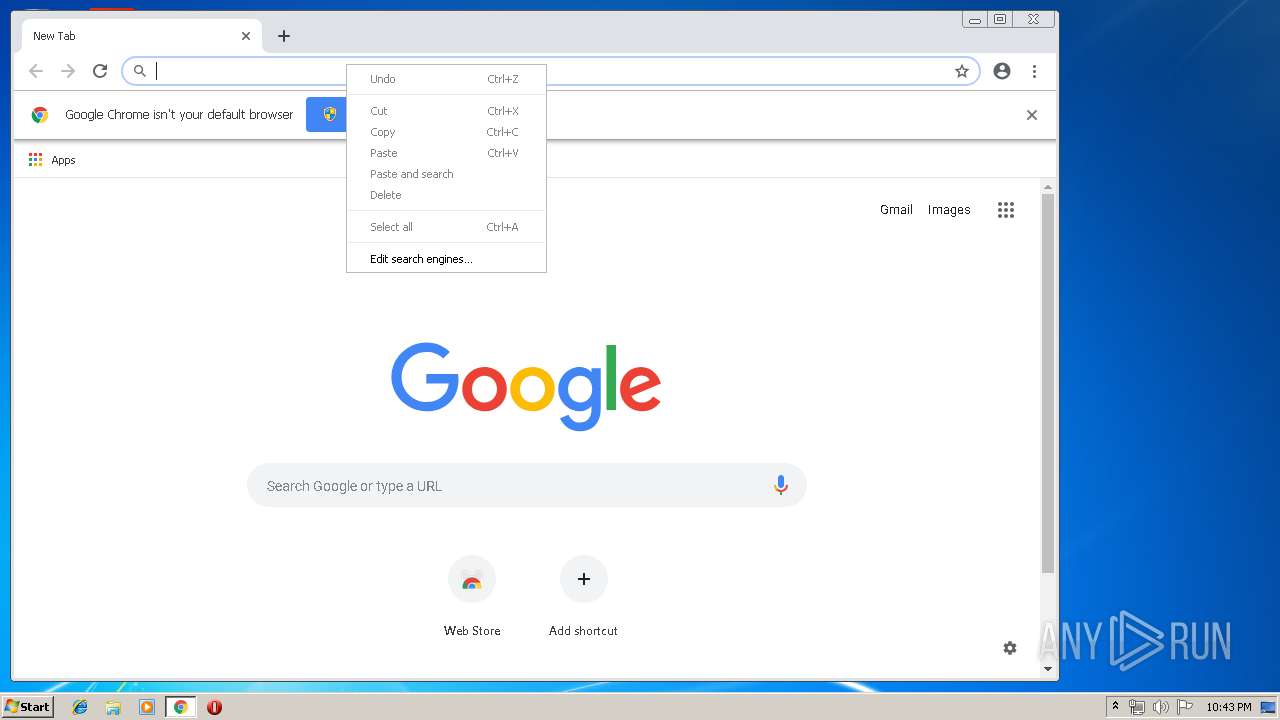
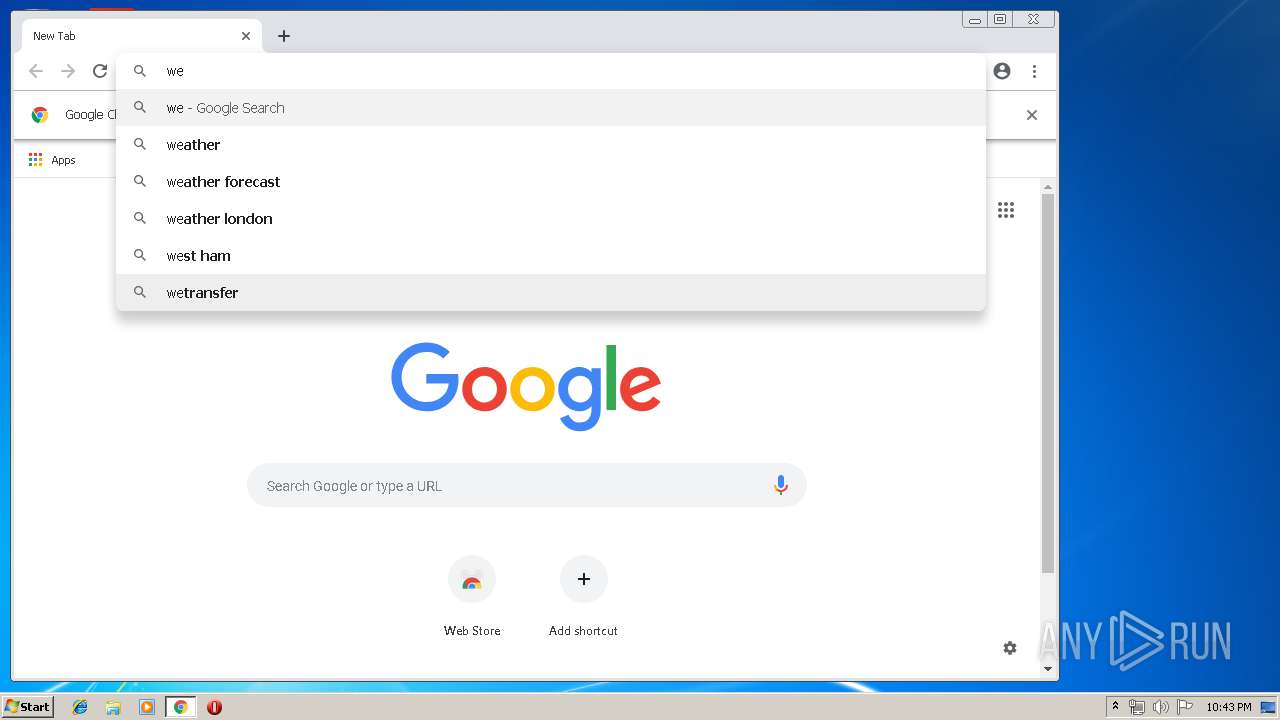
Manual execution by user
- chrome.exe (PID: 628)
- explorer.exe (PID: 2940)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3084)
- DrvInst.exe (PID: 1880)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 1532)
- MsiExec.exe (PID: 3908)
Searches for installed software
- msiexec.exe (PID: 3580)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3324)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 3580)
Starts application with an unusual extension
- msiexec.exe (PID: 3580)
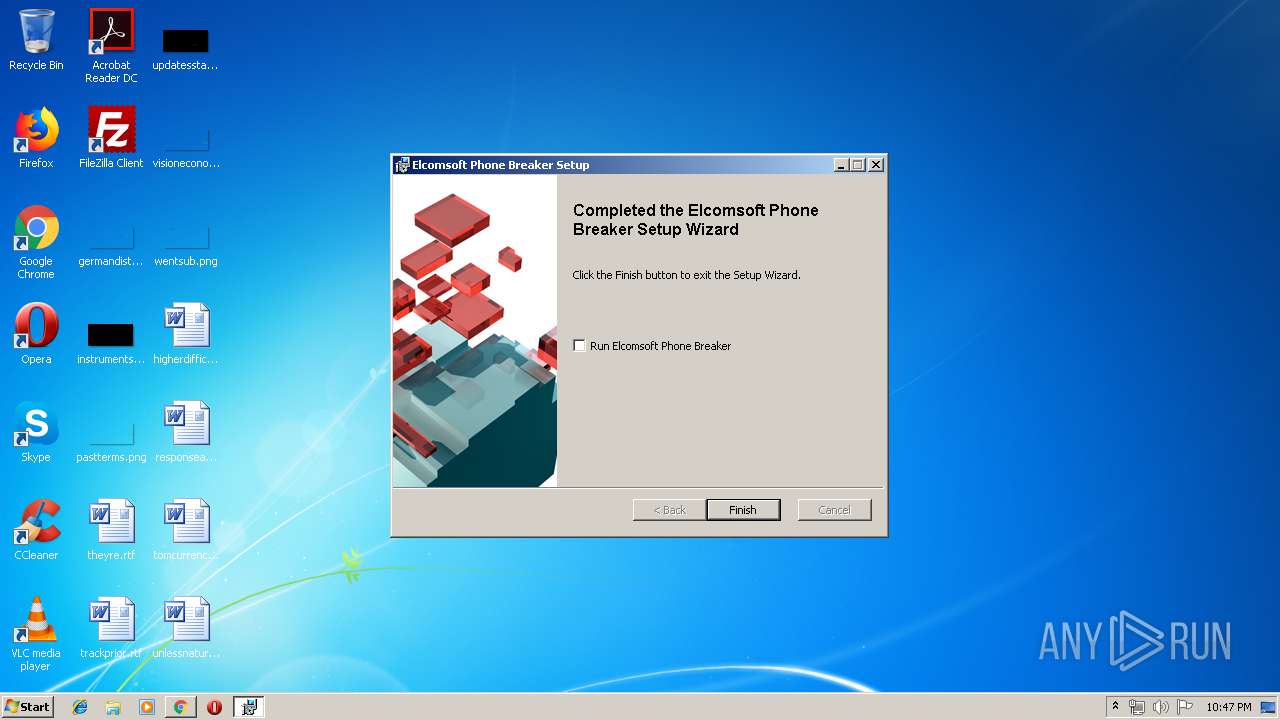
Creates a software uninstall entry
- msiexec.exe (PID: 3580)
Application was dropped or rewritten from another process
- MSI518D.tmp (PID: 3308)
- MSI49F7.tmp (PID: 2300)
- MSI4BFD.tmp (PID: 3916)
- MSI4AF2.tmp (PID: 1040)
- MSI48DD.tmp (PID: 2940)
Creates files in the program directory
- msiexec.exe (PID: 3580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
102
Monitored processes
56
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,15698078044999784559,12773419463091921275,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=186162084600666879 --mojo-platform-channel-handle=3892 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6cd70f18,0x6cd70f28,0x6cd70f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3084 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1040 | "C:\Windows\Installer\MSI4AF2.tmp" "C:\Windows\system32\schtasks.exe" /Create /SC ONCE /SD 10/10/2017 /ST 00:01 /TN "Elcomsoft\Elcomsoft Updater Show" /TR "\"C:\Program Files\Elcomsoft Password Recovery\Elcomsoft Updater\updater-launcher.exe\"" /RU "admin" /F /RL HIGHEST | C:\Windows\Installer\MSI4AF2.tmp | — | msiexec.exe | |||||||||||
User: admin Company: ElcomSoft Co. Ltd. Integrity Level: MEDIUM Description: ElcomSoft Distributed Password Recovery Installator Component Exit code: 0 Version: 3.30.1080 Modules
| |||||||||||||||
| 1100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,15698078044999784559,12773419463091921275,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8627857650737690614 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8627857650737690614 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4456 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,15698078044999784559,12773419463091921275,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16758720938266930380 --mojo-platform-channel-handle=3916 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1416 | "C:\Windows\system32\schtasks.exe" /Create /SC ONCE /SD 10/10/2017 /ST 00:01 /TN "Elcomsoft\Elcomsoft Updater Terminate" /TR "\"C:\Program Files\Elcomsoft Password Recovery\Elcomsoft Updater\updater-launcher.exe\" --kill" /RU "admin" /F /RL HIGHEST | C:\Windows\system32\schtasks.exe | MSI49F7.tmp | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,15698078044999784559,12773419463091921275,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14542391276331115240 --mojo-platform-channel-handle=4060 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1532 | C:\Windows\system32\MsiExec.exe -Embedding A0F4A127CFB29A4685A83420057091EE C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
7 067
Read events
5 924
Write events
1 116
Delete events
27
Modification events
| (PID) Process: | (3084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {05B867FB-96C9-11E9-B63D-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E30706000100180015002A003700B702 | |||
Executable files
99
Suspicious files
140
Text files
362
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3084 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3084 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 928 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab1610.tmp | — | |
MD5:— | SHA256:— | |||
| 928 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar1611.tmp | — | |
MD5:— | SHA256:— | |||
| 928 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab1651.tmp | — | |
MD5:— | SHA256:— | |||
| 928 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar1652.tmp | — | |
MD5:— | SHA256:— | |||
| 928 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab16EF.tmp | — | |
MD5:— | SHA256:— | |||
| 928 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar16F0.tmp | — | |
MD5:— | SHA256:— | |||
| 3084 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF3666DEB19AA66D5A.TMP | — | |
MD5:— | SHA256:— | |||
| 3084 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFFE2B4C5F4C8043D8.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
74
DNS requests
54
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
628 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
928 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.2 Kb | whitelisted |
928 | iexplore.exe | GET | 200 | 13.32.222.53:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
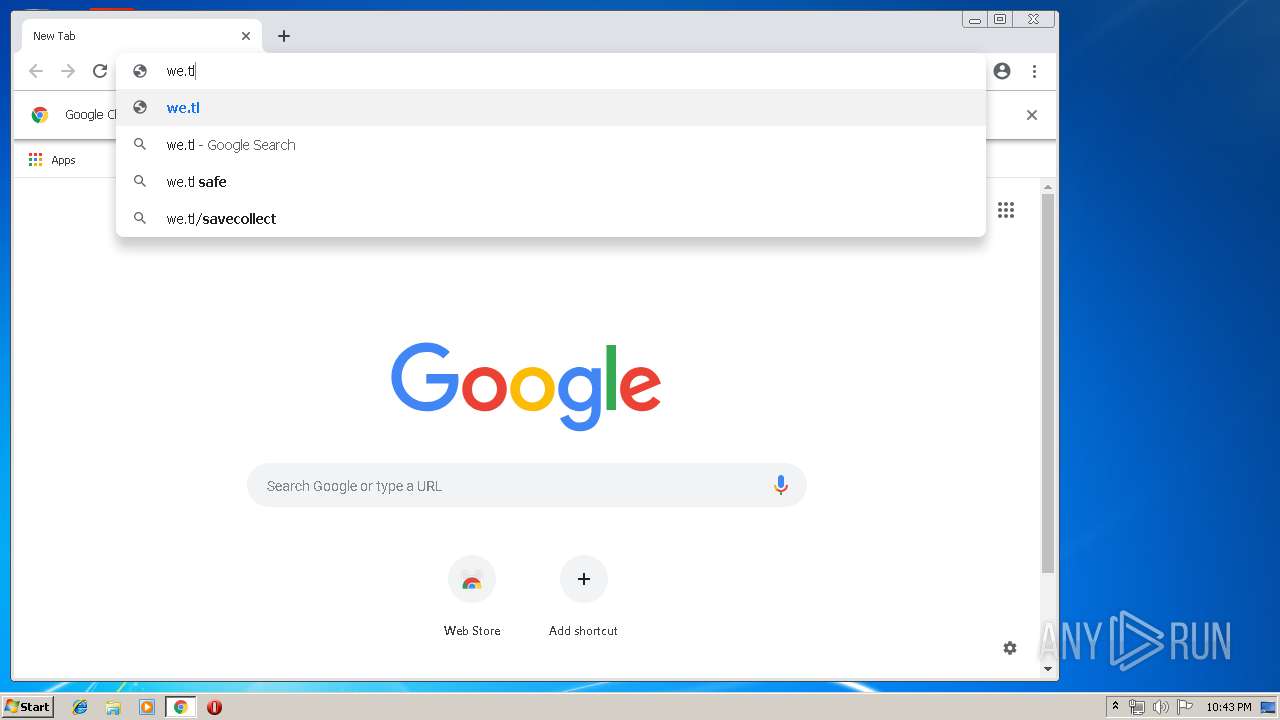
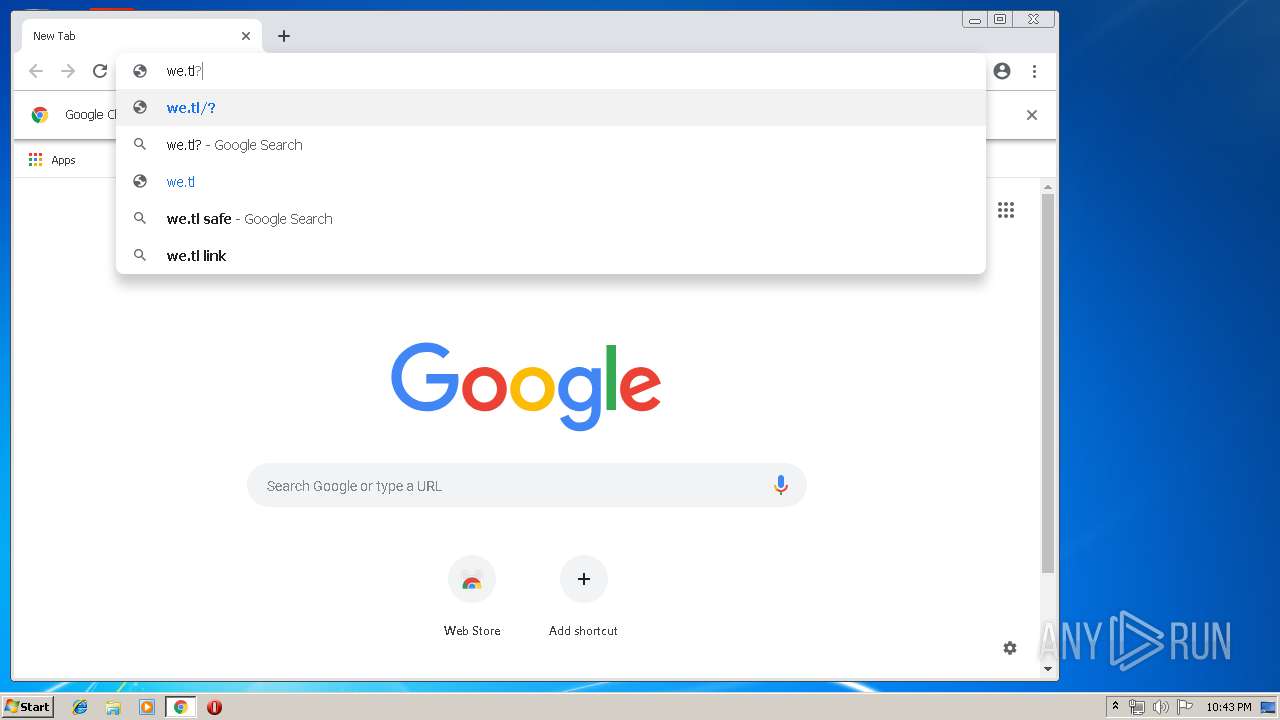
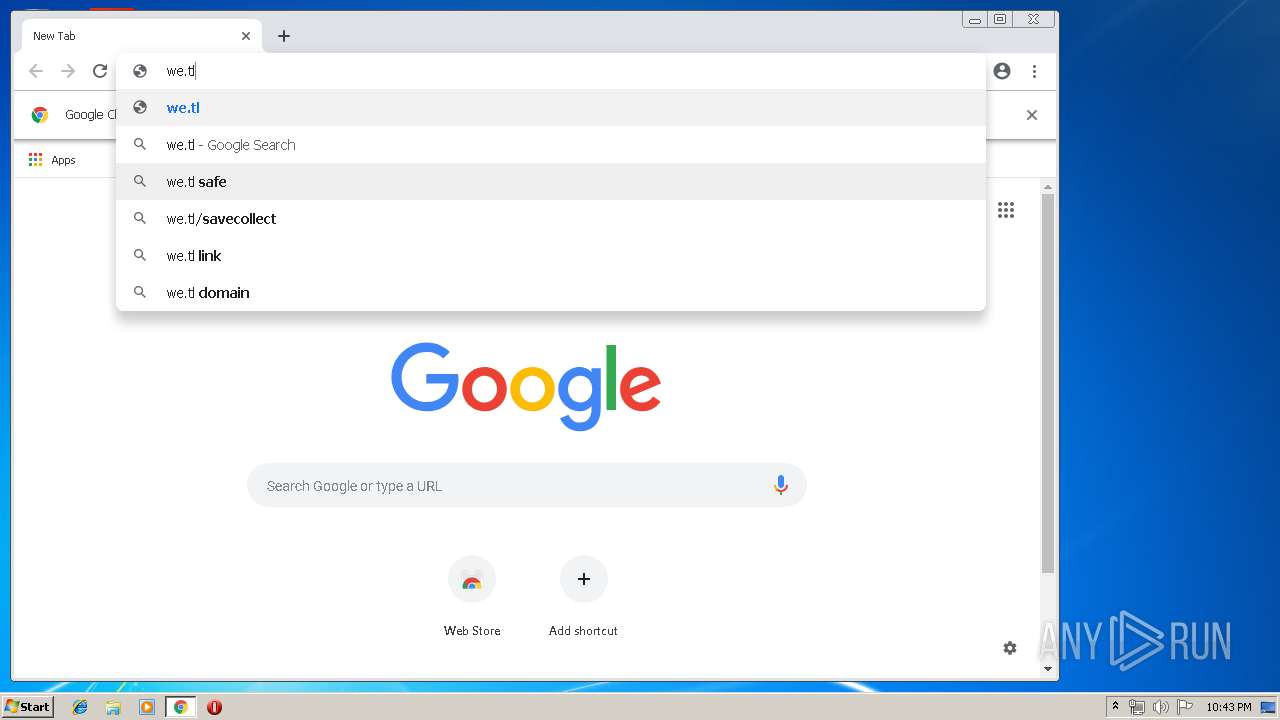
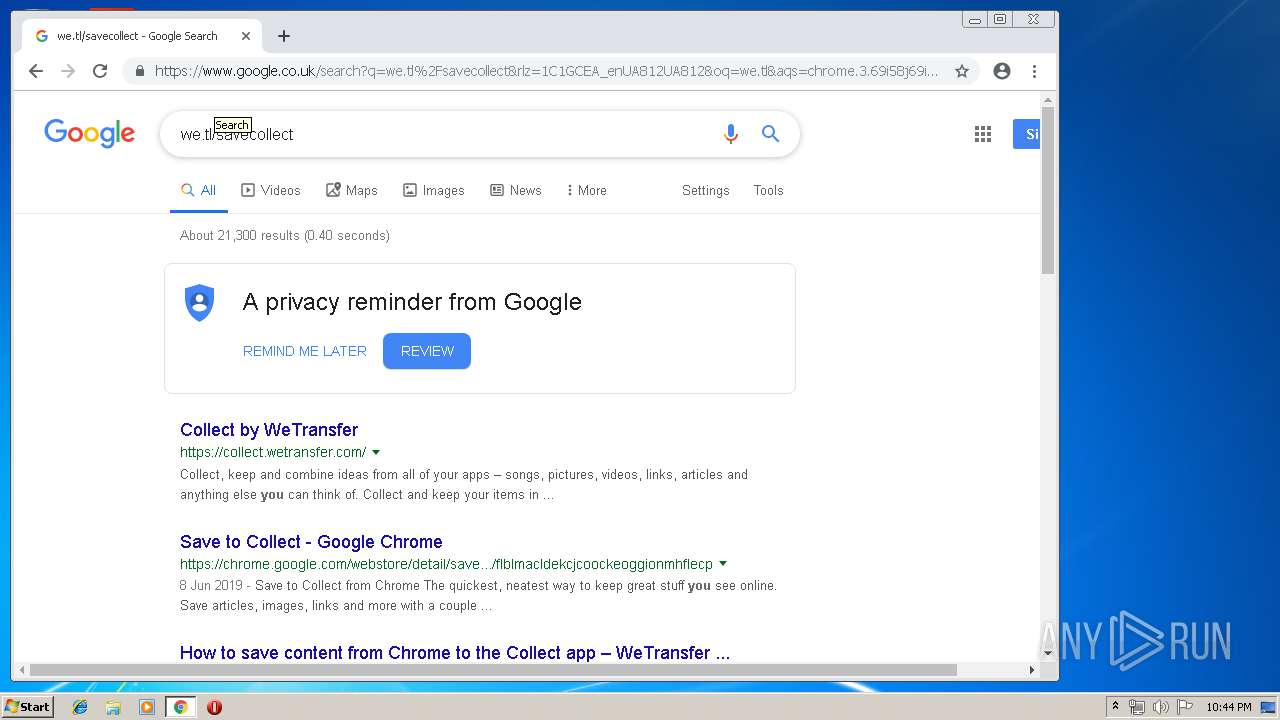
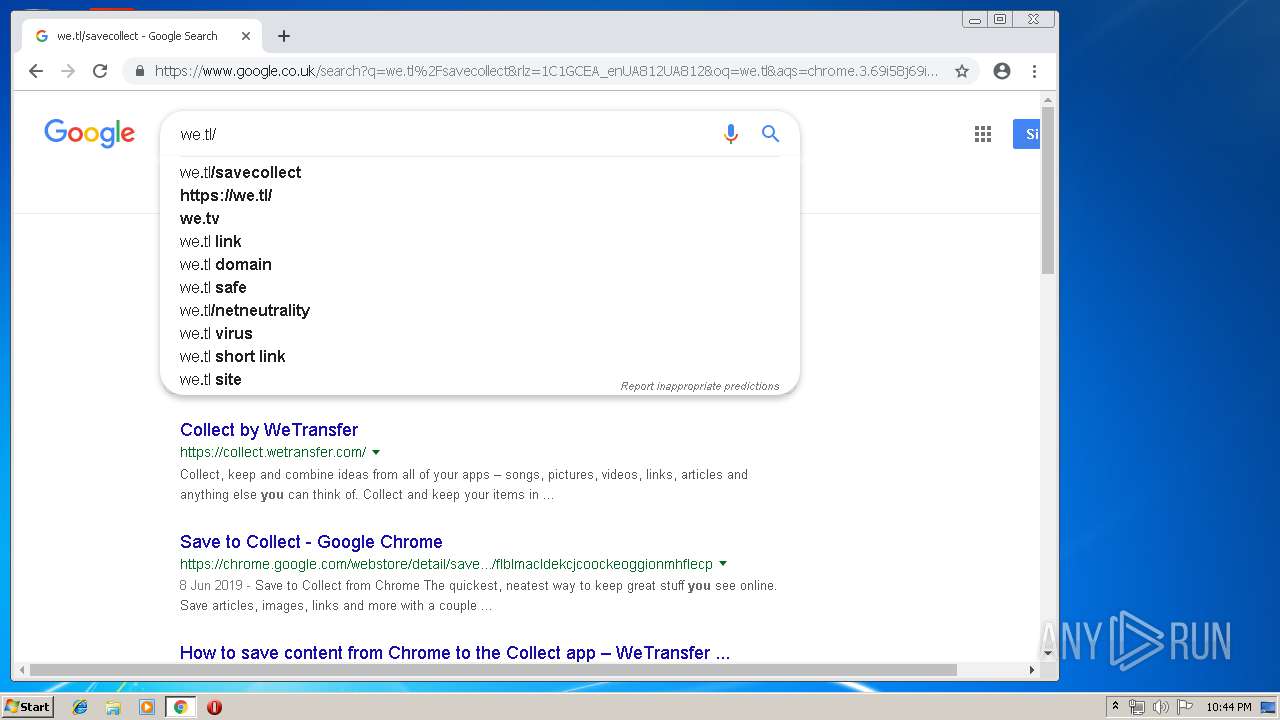
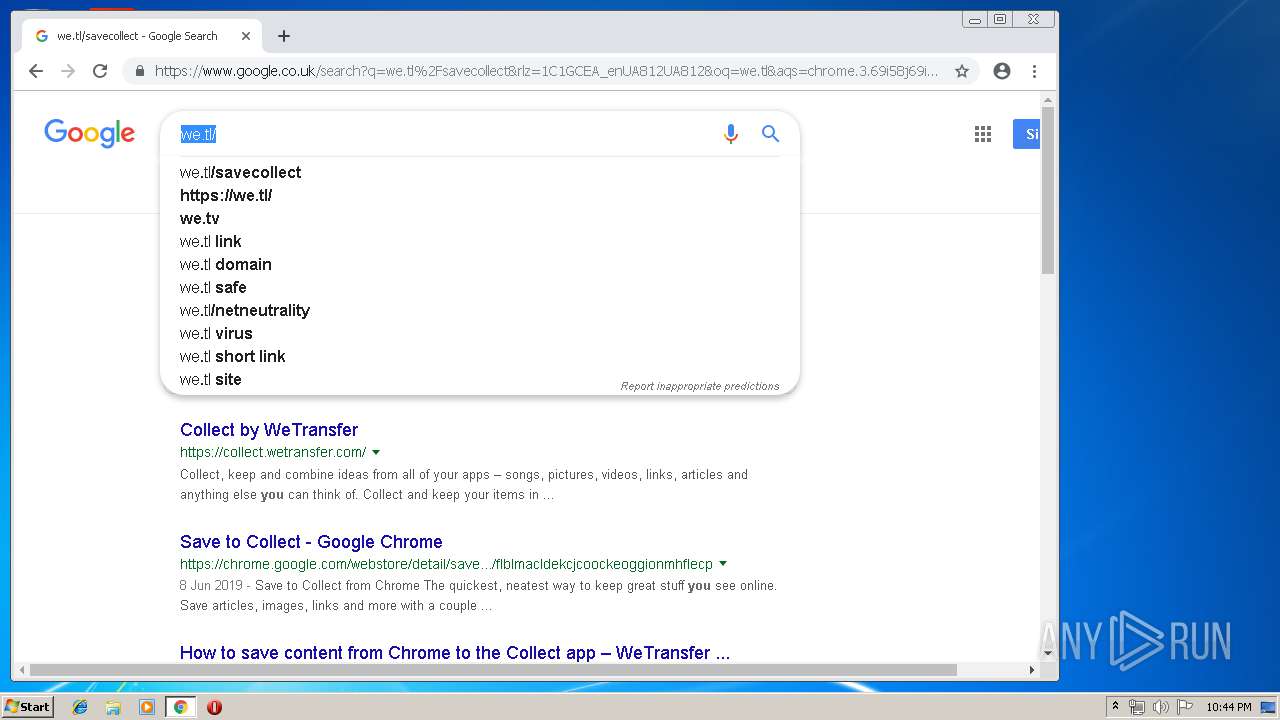
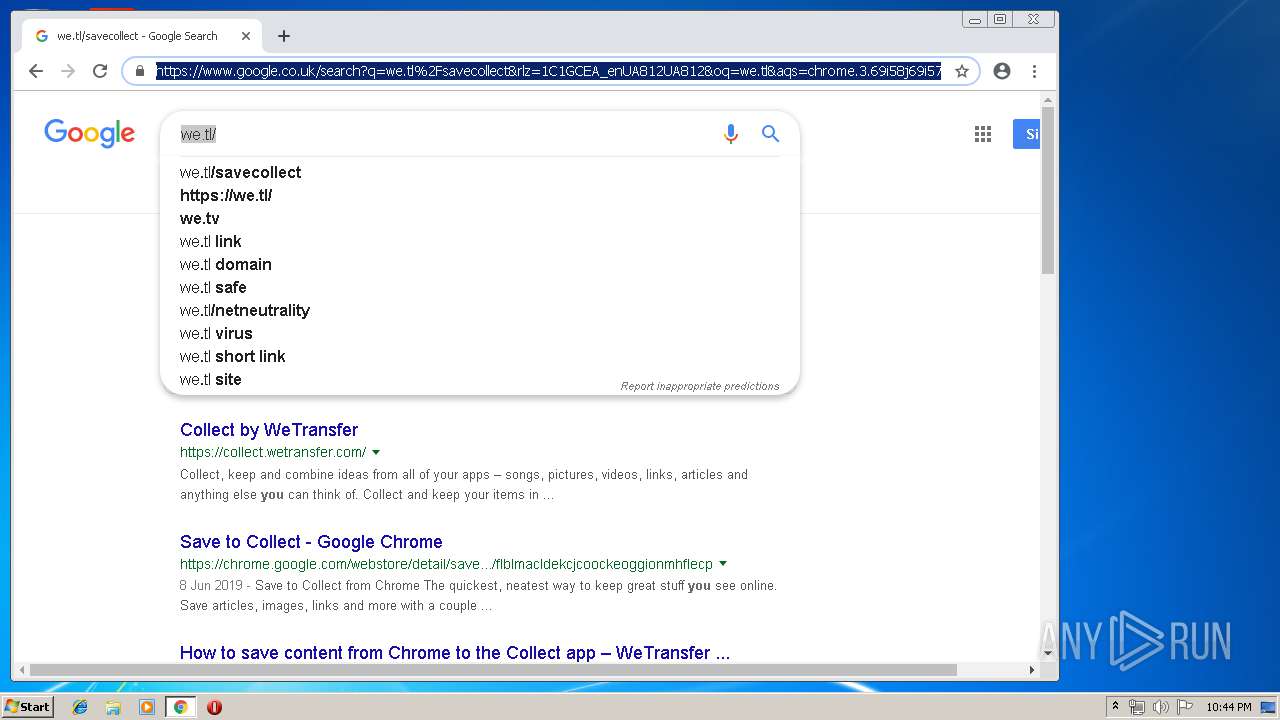
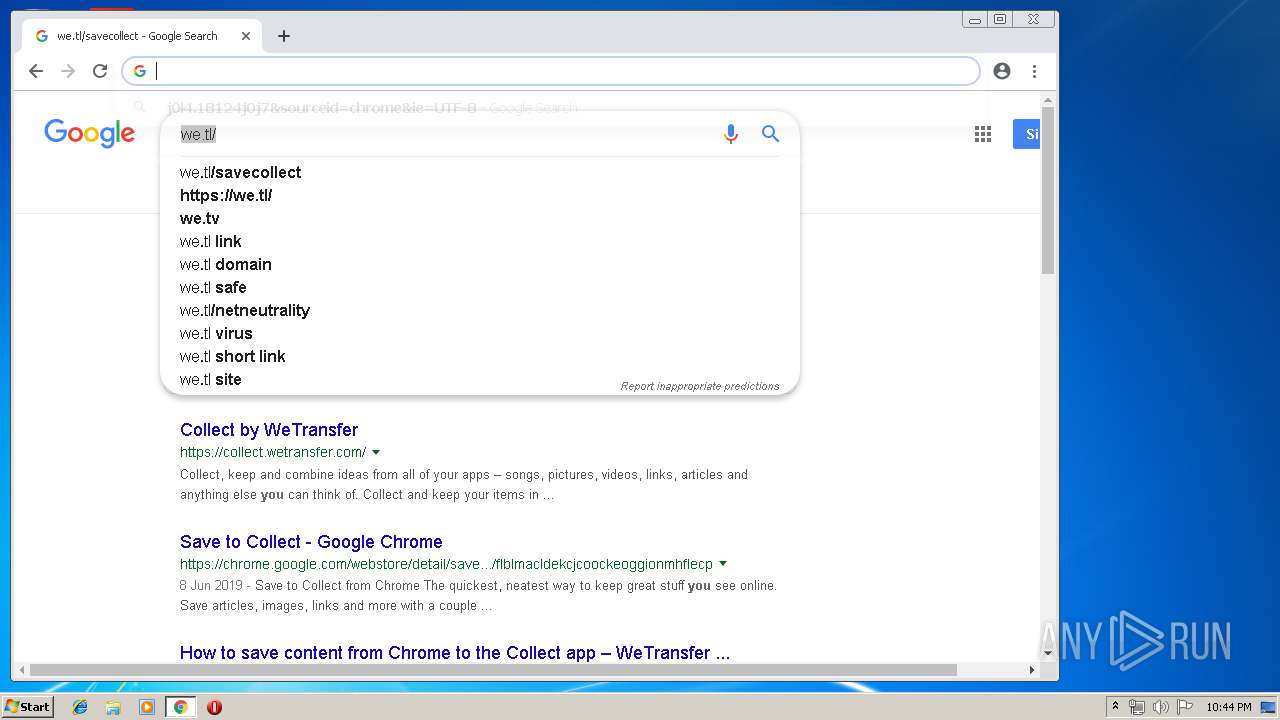
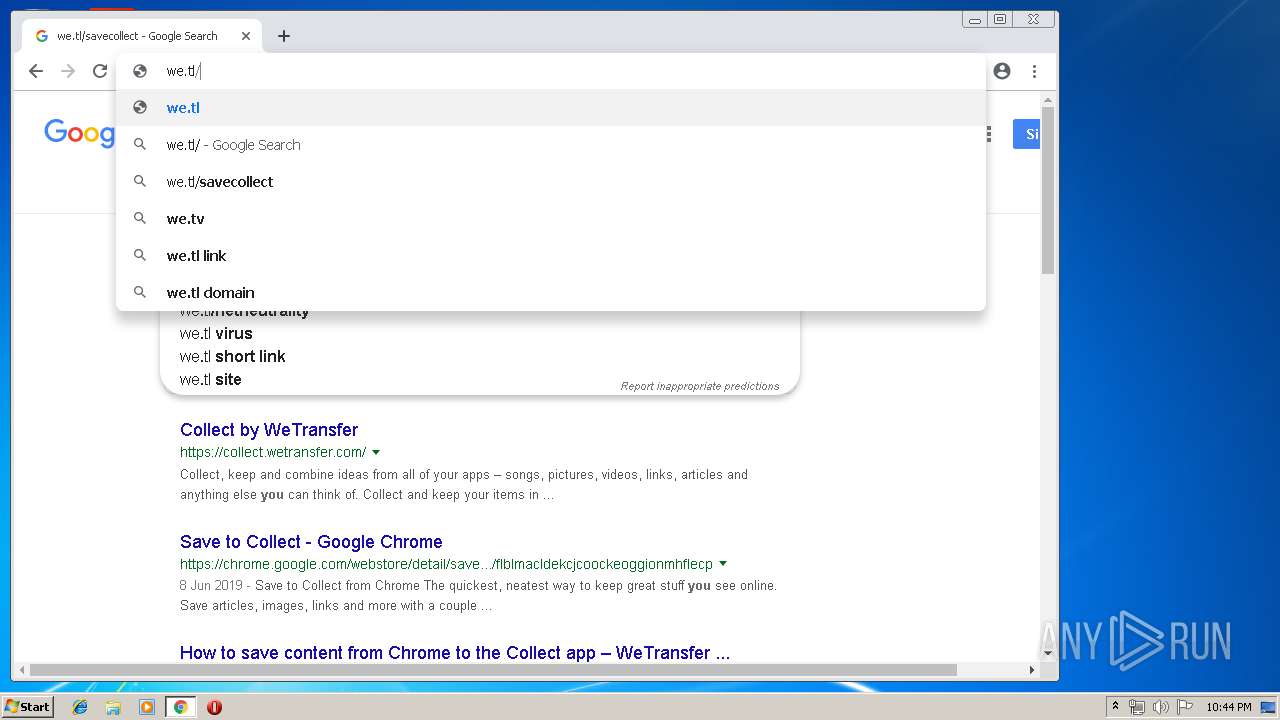
628 | chrome.exe | GET | 301 | 13.32.158.150:80 | http://we.tl/t-DwtNudS8nN | US | html | 183 b | shared |
628 | chrome.exe | GET | 200 | 173.194.5.41:80 | http://r4---sn-aigzrn7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=217.147.89.18&mm=28&mn=sn-aigzrn7e&ms=nvh&mt=1561411642&mv=u&pl=22&shardbypass=yes | US | crx | 842 Kb | whitelisted |
3084 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
928 | iexplore.exe | 13.32.158.251:443 | we.tl | Amazon.com, Inc. | US | suspicious |
3084 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
928 | iexplore.exe | 13.32.222.53:80 | x.ss2.us | Amazon.com, Inc. | US | malicious |
3084 | iexplore.exe | 13.32.158.251:443 | we.tl | Amazon.com, Inc. | US | suspicious |
628 | chrome.exe | 172.217.21.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
628 | chrome.exe | 172.217.18.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
628 | chrome.exe | 172.217.23.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
628 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
628 | chrome.exe | 172.217.22.78:443 | ogs.google.com | Google Inc. | US | whitelisted |
628 | chrome.exe | 172.217.18.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
we.tl |
| shared |
www.bing.com |
| whitelisted |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
EPBMain.exe | QMetaObject::connectSlotsByName: No matching signal for on_chkMaskPasswords_stateChanged(int)
|