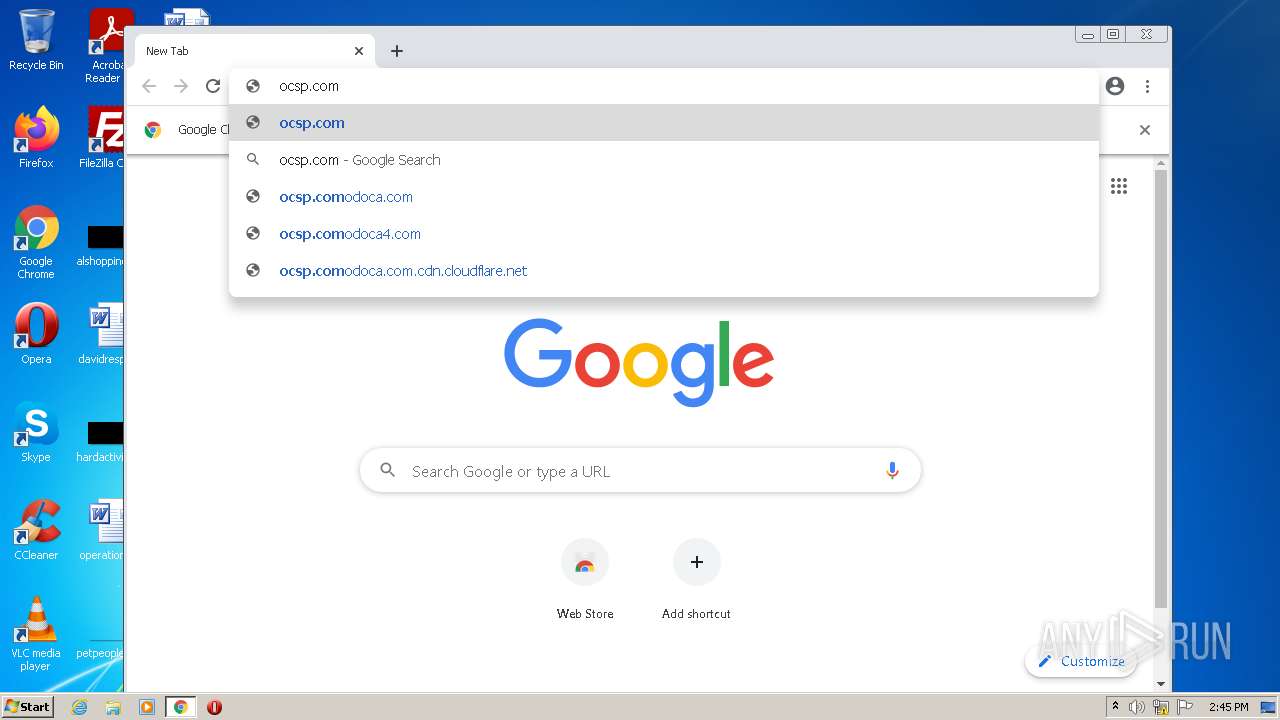
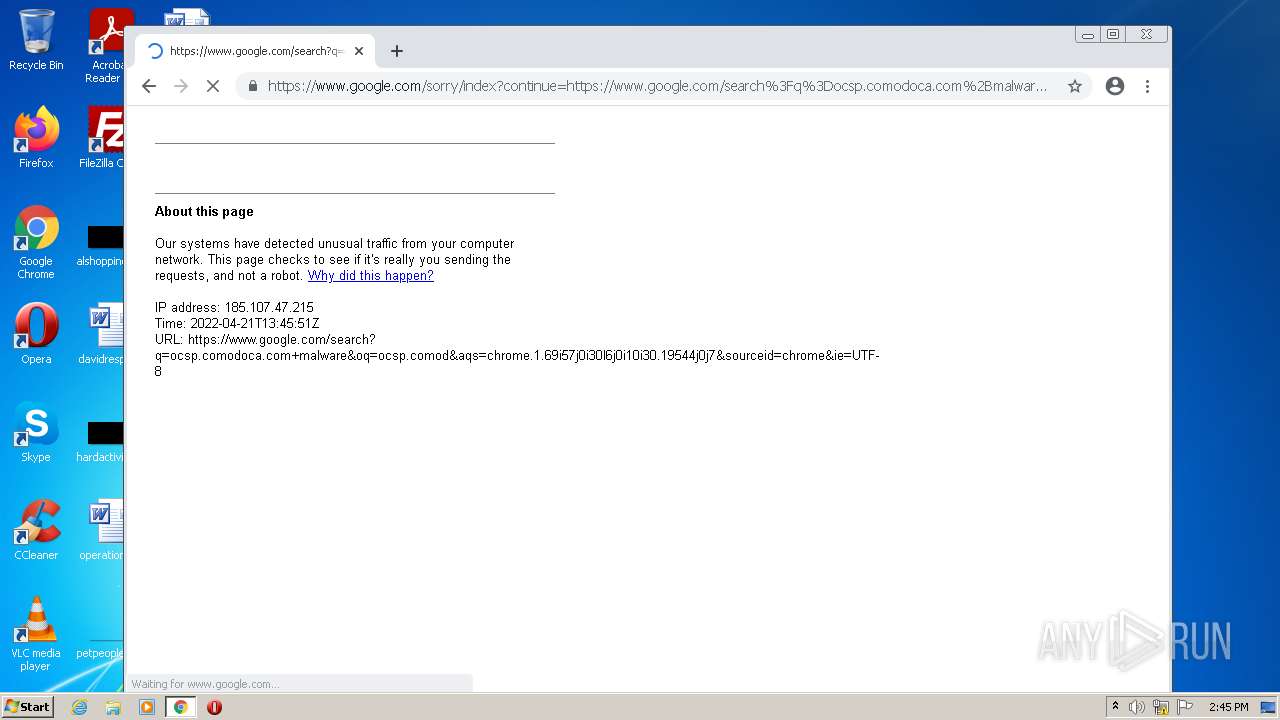
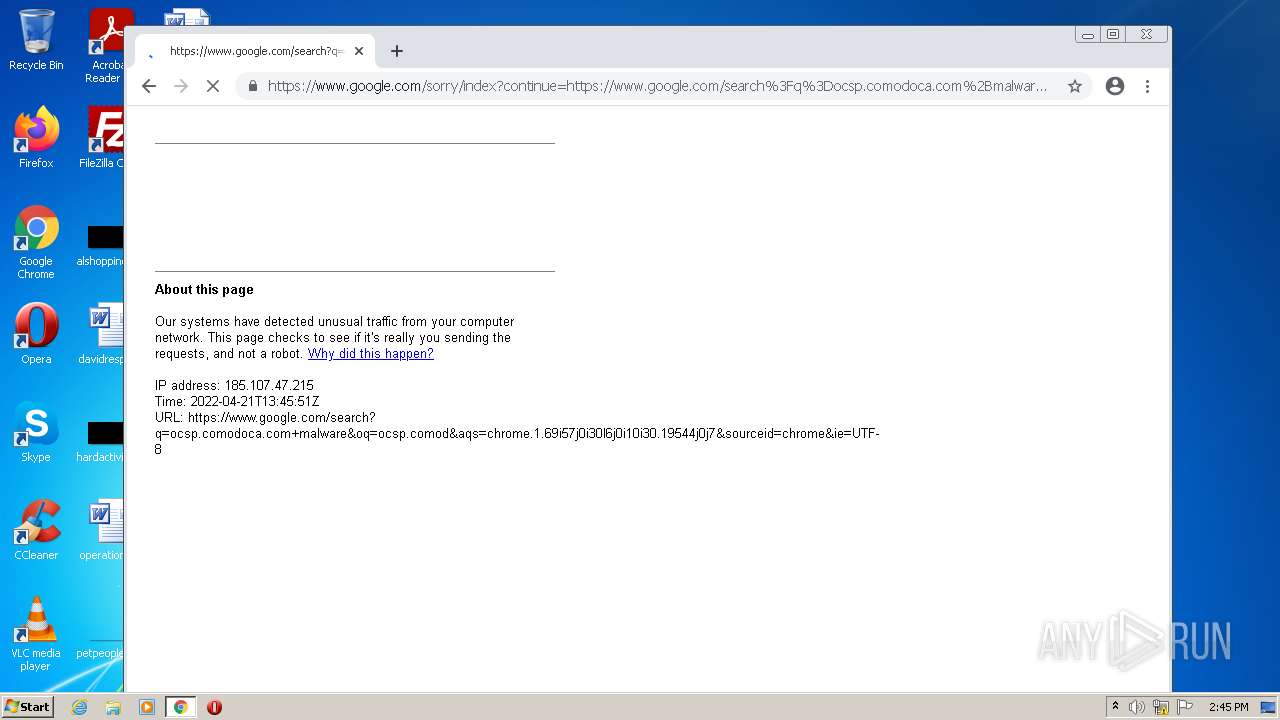
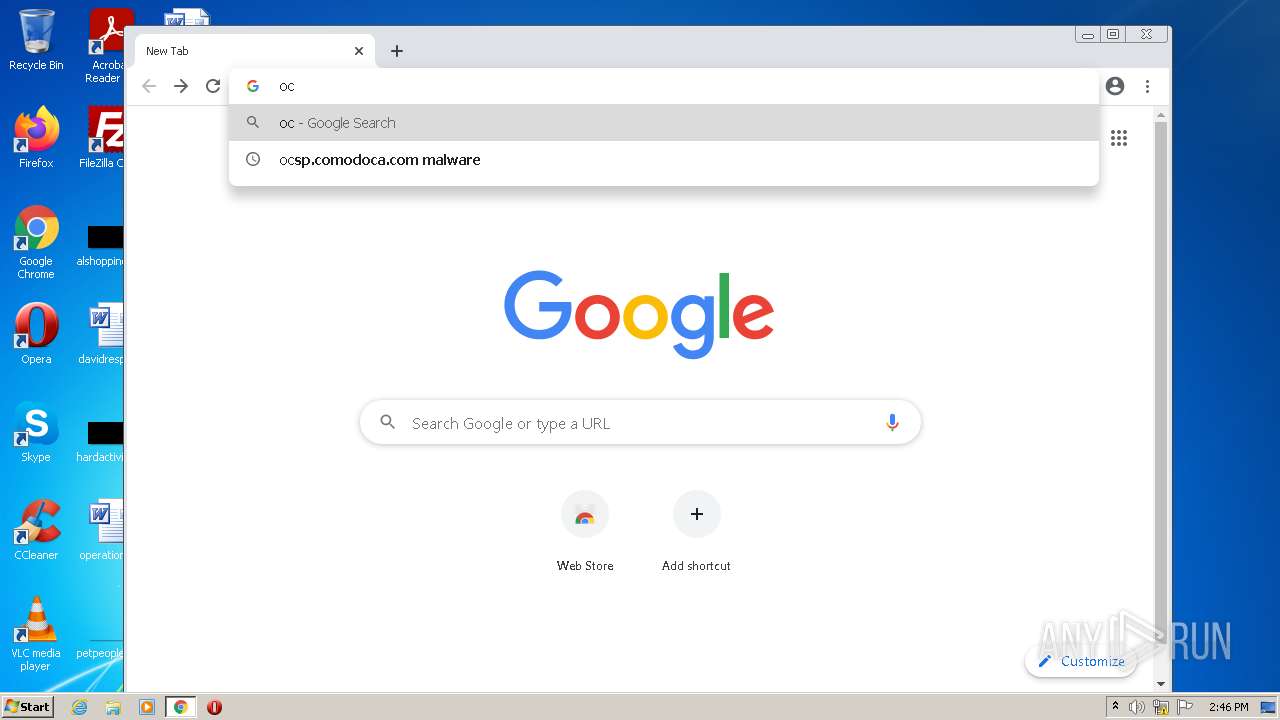
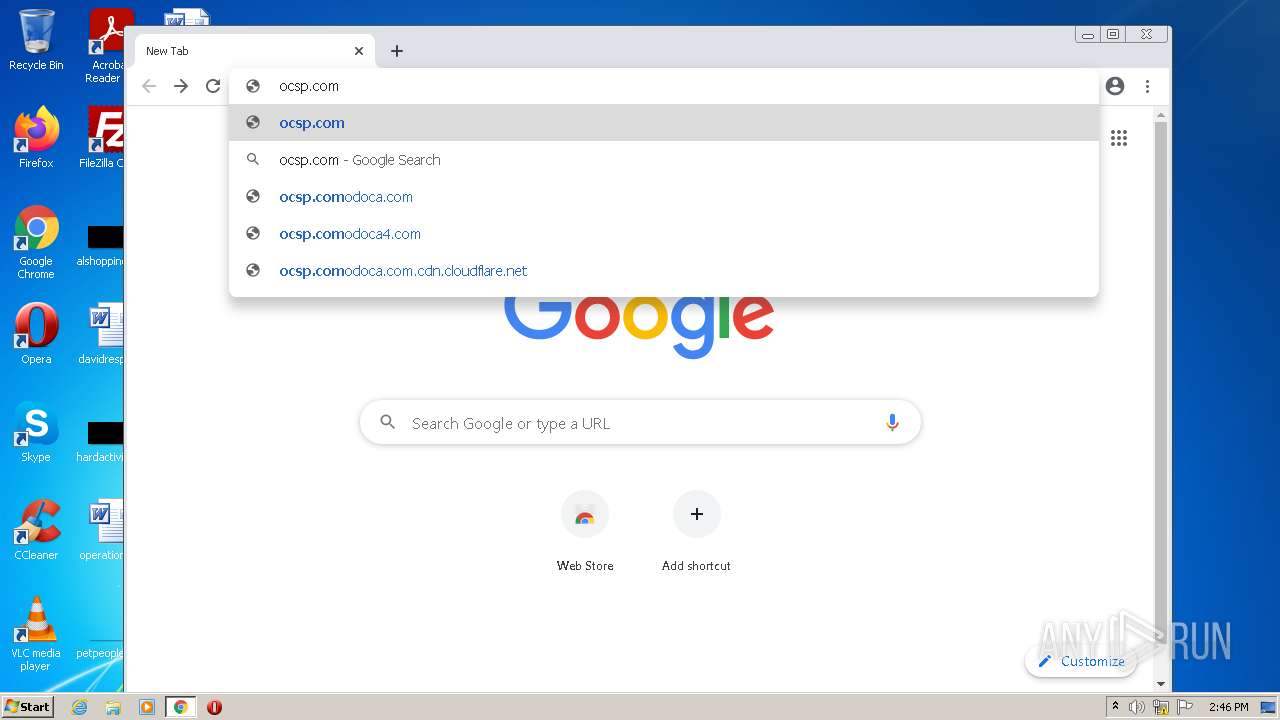
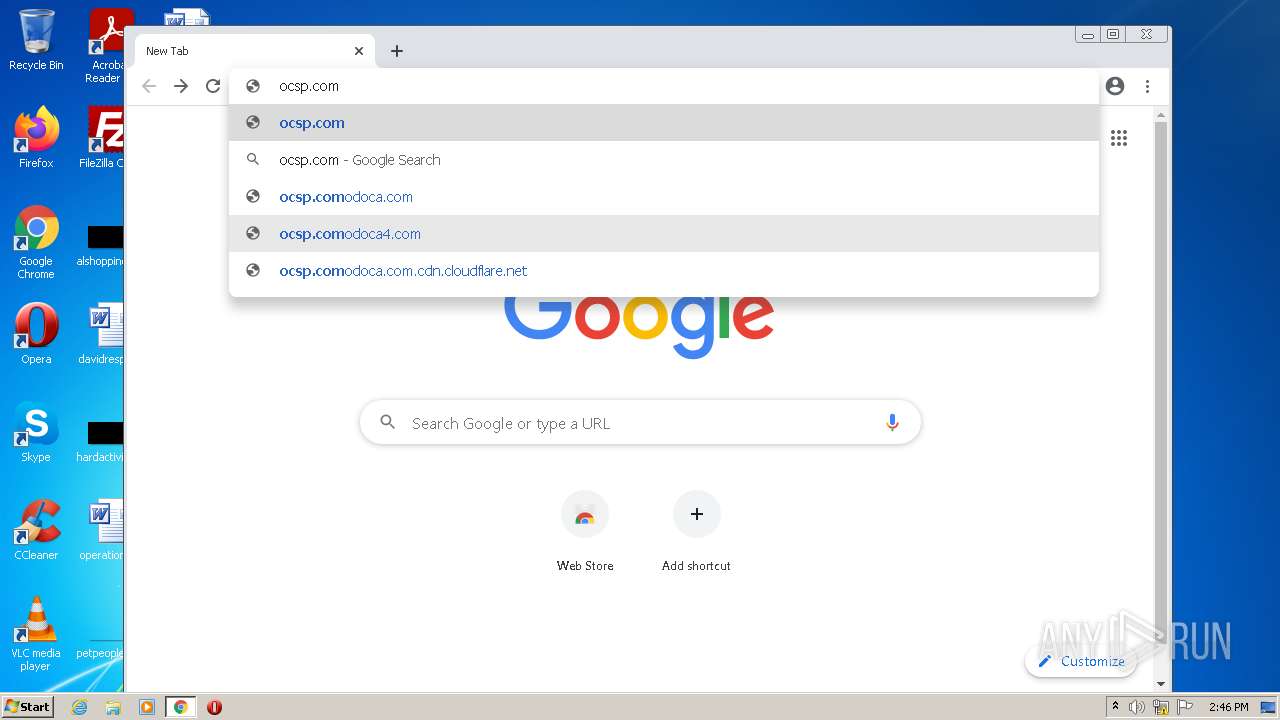
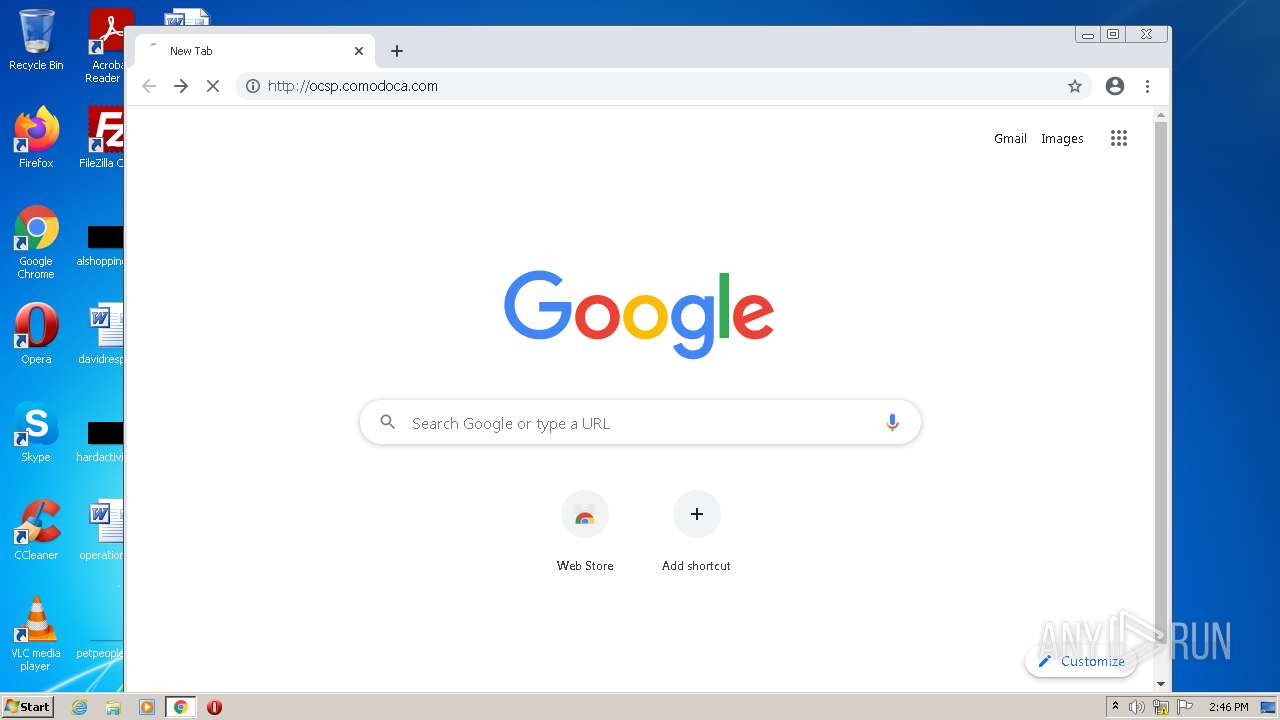
| URL: | http://ocsp.comodoca.com |
| Full analysis: | https://app.any.run/tasks/72881c44-3775-4d95-8d2f-519dcc3c7533 |
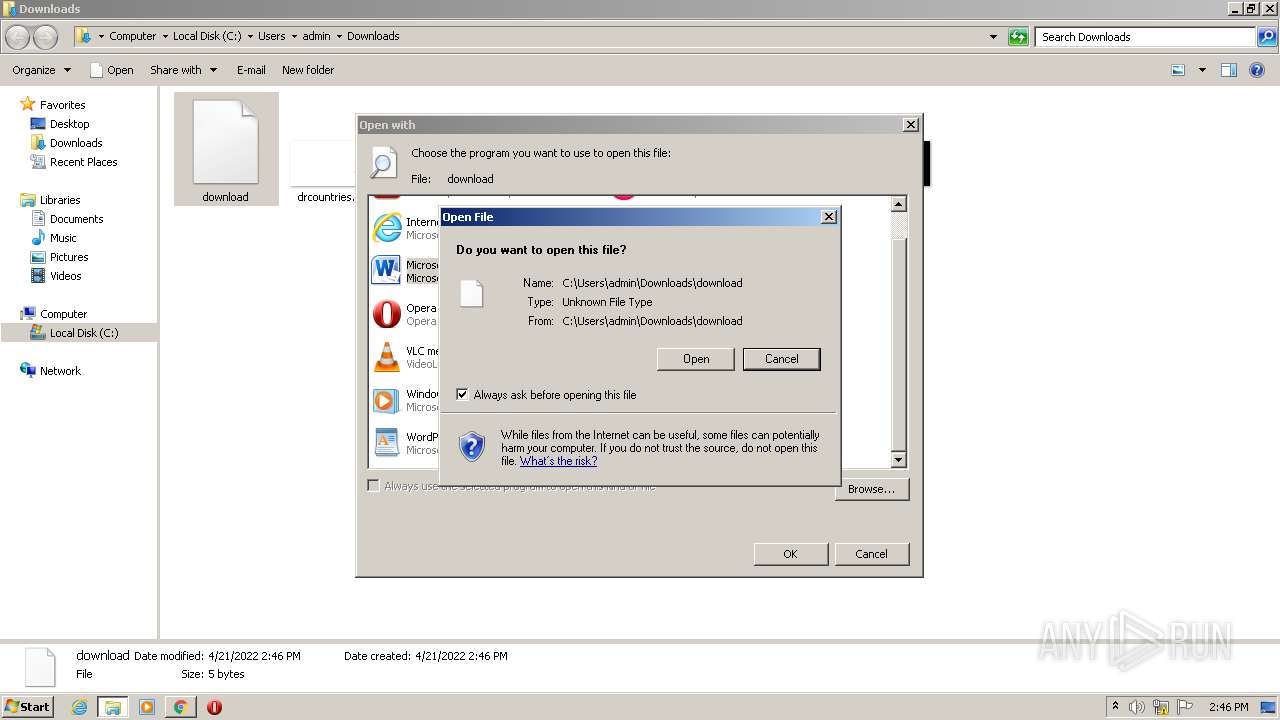
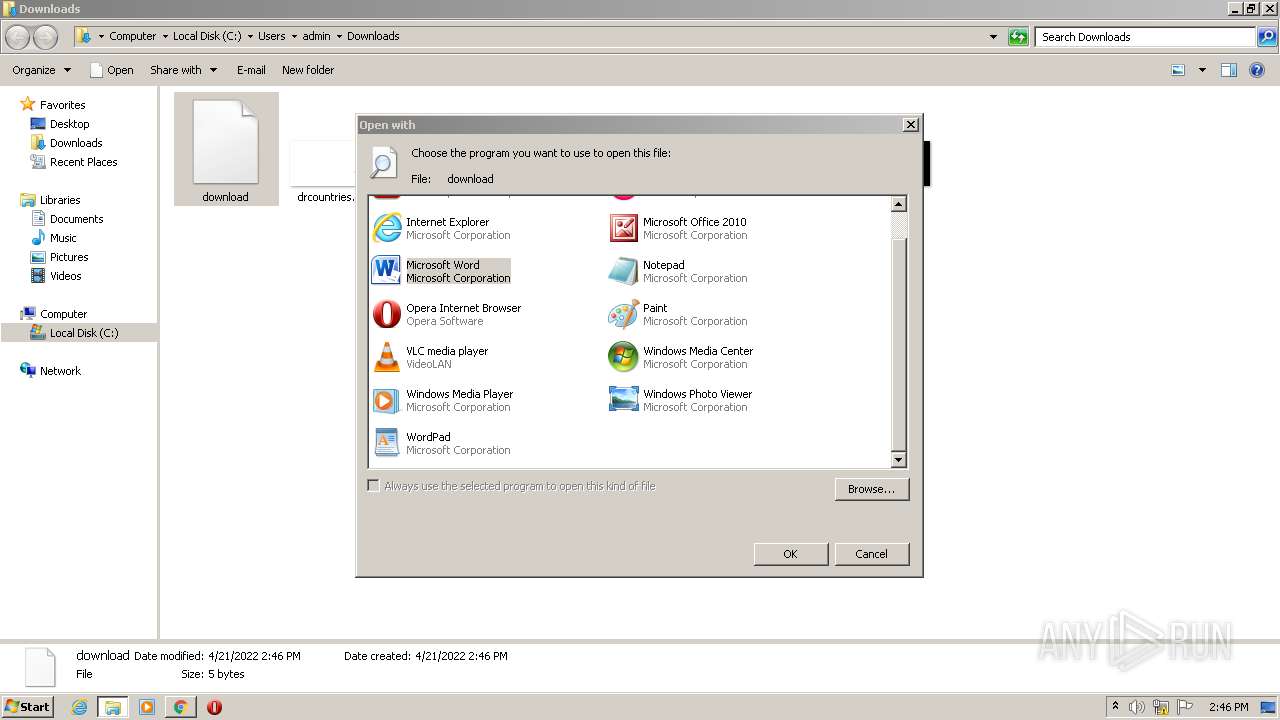
| Verdict: | Malicious activity |
| Analysis date: | April 21, 2022, 13:43:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F939A3AE6DC84CCBC2CBD9031EC81D3D |
| SHA1: | 817074E6E05CF2C082F06487C679992D0CF85697 |
| SHA256: | 2FB77010AFA6DF7F1FB28C6CB05E97E69567E176A98D6A165A6B2E60D249B961 |
| SSDEEP: | 3:N1KRGWVCLGKIn:CgWVCLKn |
MALICIOUS
No malicious indicators.SUSPICIOUS
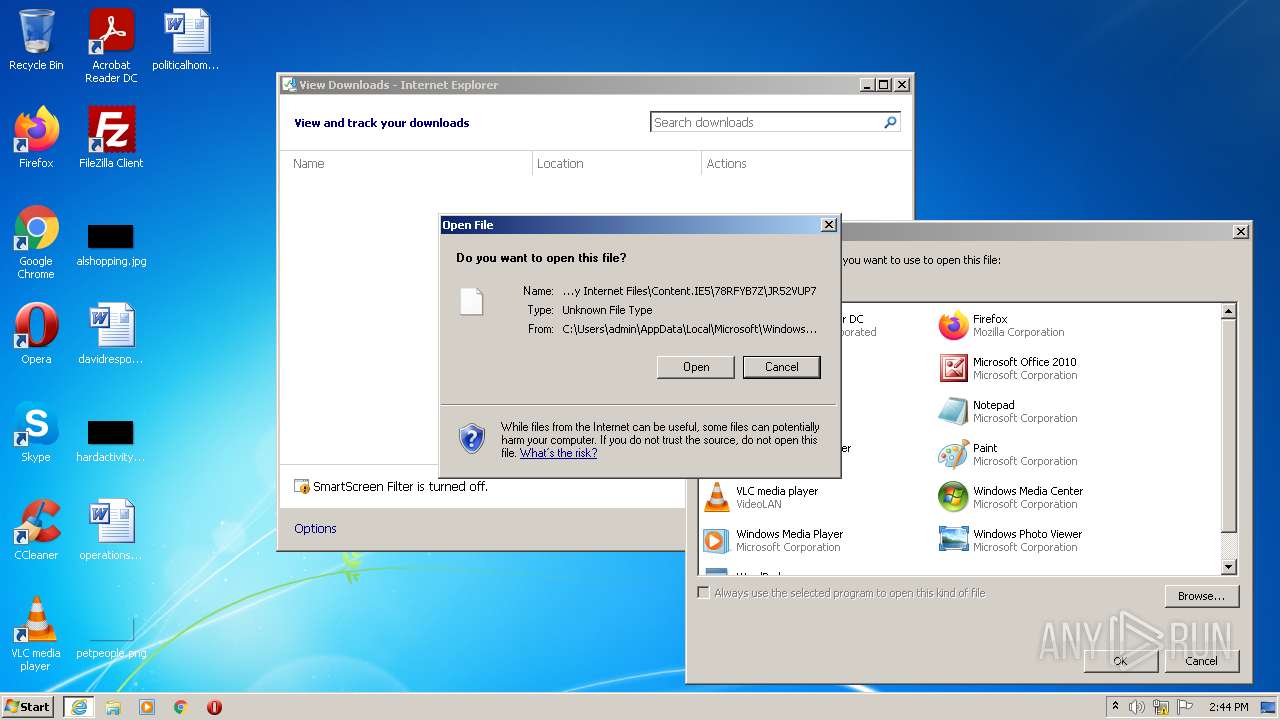
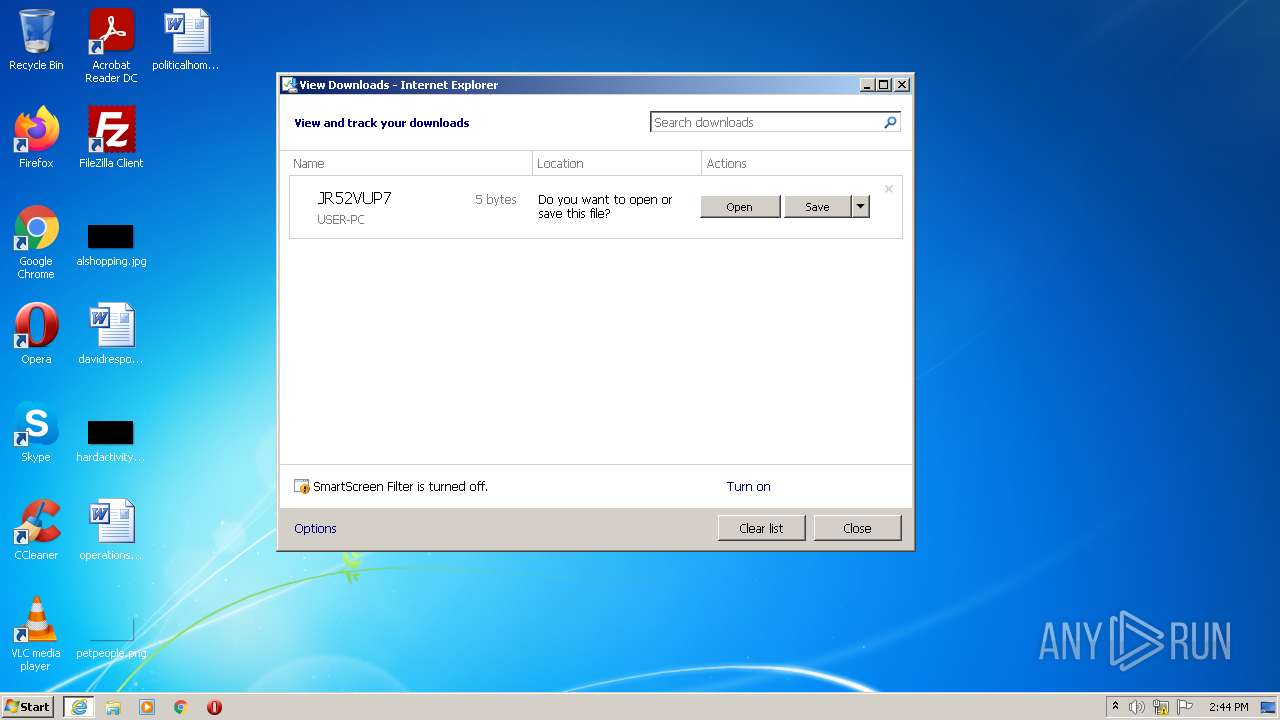
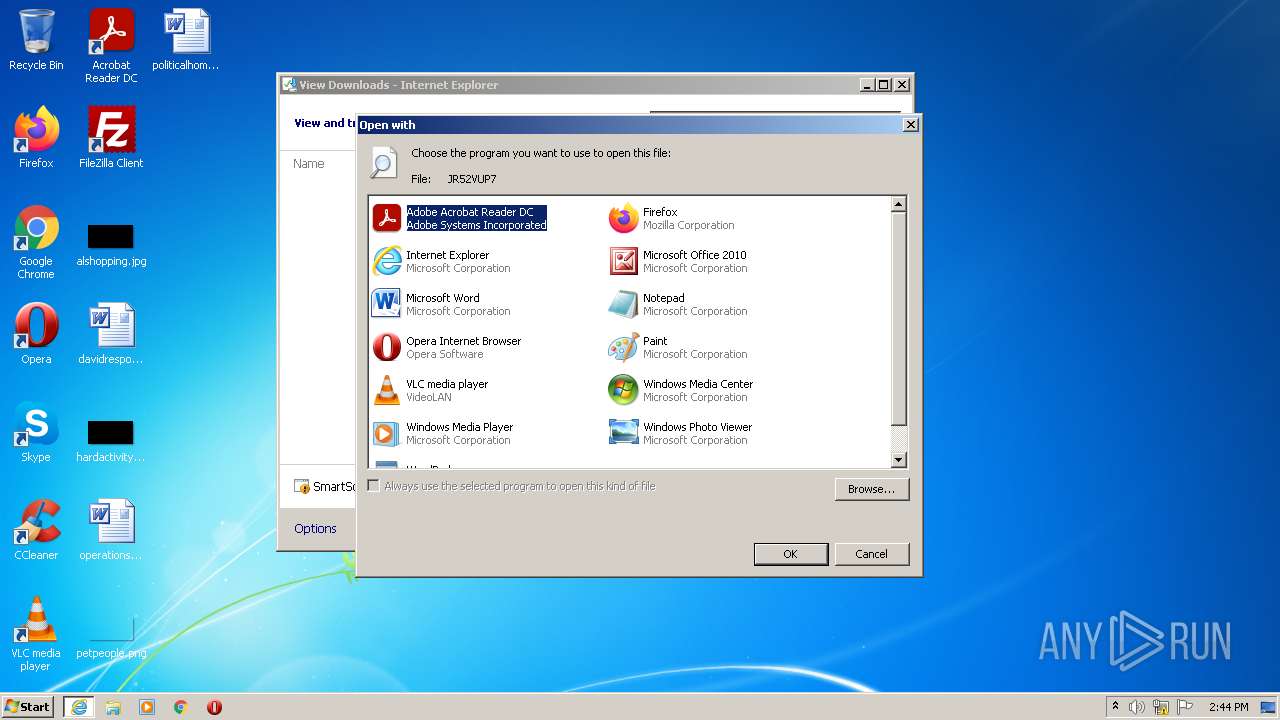
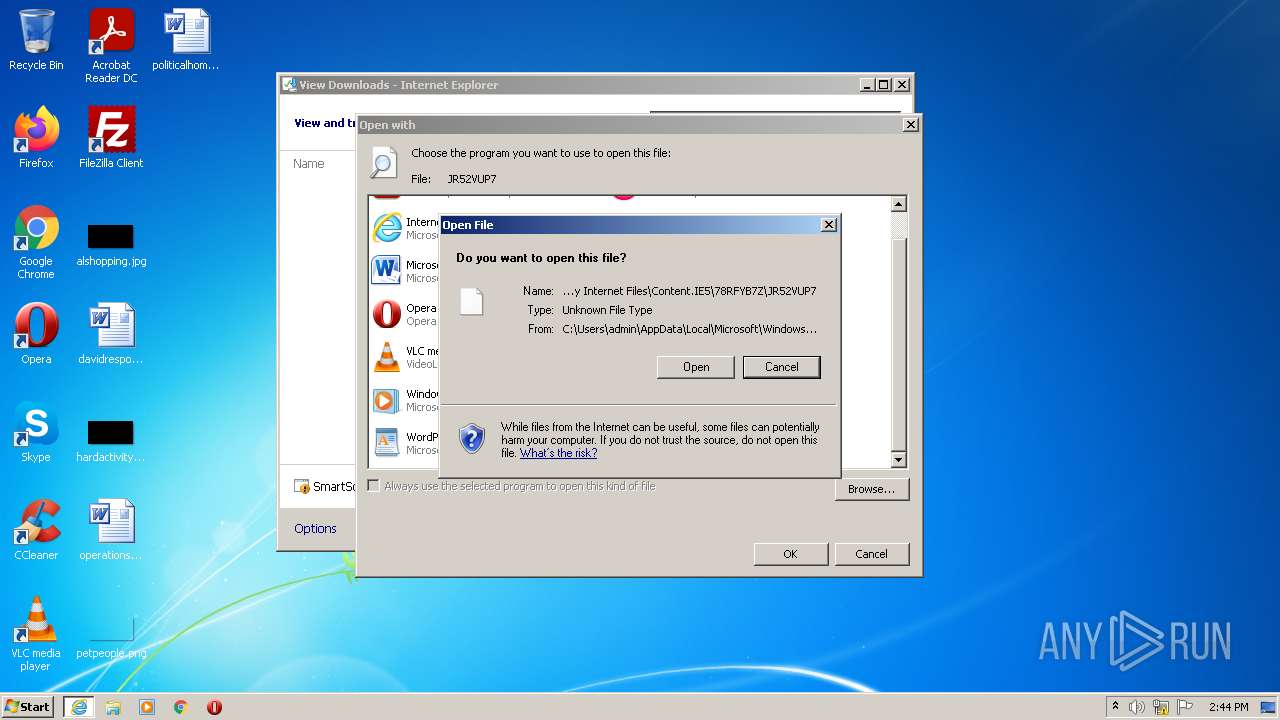
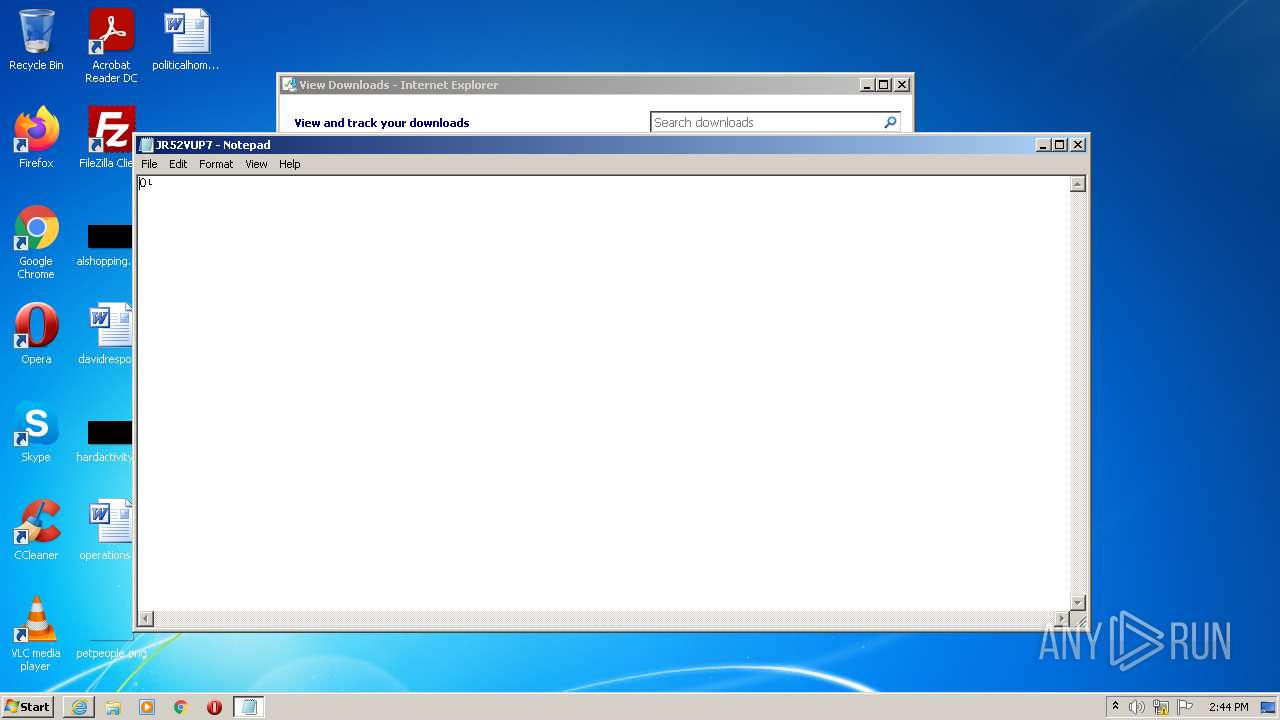
Uses RUNDLL32.EXE to load library
- iexplore.exe (PID: 3116)
Starts Internet Explorer
- rundll32.exe (PID: 1228)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1180)
Reads the date of Windows installation
- rundll32.exe (PID: 1228)
- rundll32.exe (PID: 4028)
- rundll32.exe (PID: 3080)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3888)
Starts Microsoft Office Application
- rundll32.exe (PID: 3080)
Executed via COM
- DllHost.exe (PID: 4044)
INFO
Application launched itself
- iexplore.exe (PID: 3116)
- chrome.exe (PID: 3888)
Checks supported languages
- iexplore.exe (PID: 1180)
- iexplore.exe (PID: 3116)
- rundll32.exe (PID: 4028)
- rundll32.exe (PID: 1228)
- iexplore.exe (PID: 3316)
- NOTEPAD.EXE (PID: 3832)
- chrome.exe (PID: 3888)
- chrome.exe (PID: 2100)
- chrome.exe (PID: 2168)
- chrome.exe (PID: 2952)
- chrome.exe (PID: 400)
- chrome.exe (PID: 2488)
- chrome.exe (PID: 3024)
- chrome.exe (PID: 2072)
- chrome.exe (PID: 3040)
- chrome.exe (PID: 916)
- chrome.exe (PID: 2416)
- chrome.exe (PID: 116)
- chrome.exe (PID: 2812)
- chrome.exe (PID: 968)
- chrome.exe (PID: 1712)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 2032)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 3204)
- chrome.exe (PID: 1744)
- chrome.exe (PID: 3480)
- chrome.exe (PID: 3292)
- chrome.exe (PID: 4088)
- chrome.exe (PID: 3484)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 3100)
- rundll32.exe (PID: 3080)
- WINWORD.EXE (PID: 4036)
- DllHost.exe (PID: 4044)
Reads the computer name
- iexplore.exe (PID: 1180)
- iexplore.exe (PID: 3116)
- rundll32.exe (PID: 1228)
- iexplore.exe (PID: 3316)
- chrome.exe (PID: 3888)
- rundll32.exe (PID: 4028)
- chrome.exe (PID: 400)
- chrome.exe (PID: 2488)
- chrome.exe (PID: 2168)
- chrome.exe (PID: 968)
- chrome.exe (PID: 3204)
- chrome.exe (PID: 2416)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 4088)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 3484)
- rundll32.exe (PID: 3080)
- WINWORD.EXE (PID: 4036)
- DllHost.exe (PID: 4044)
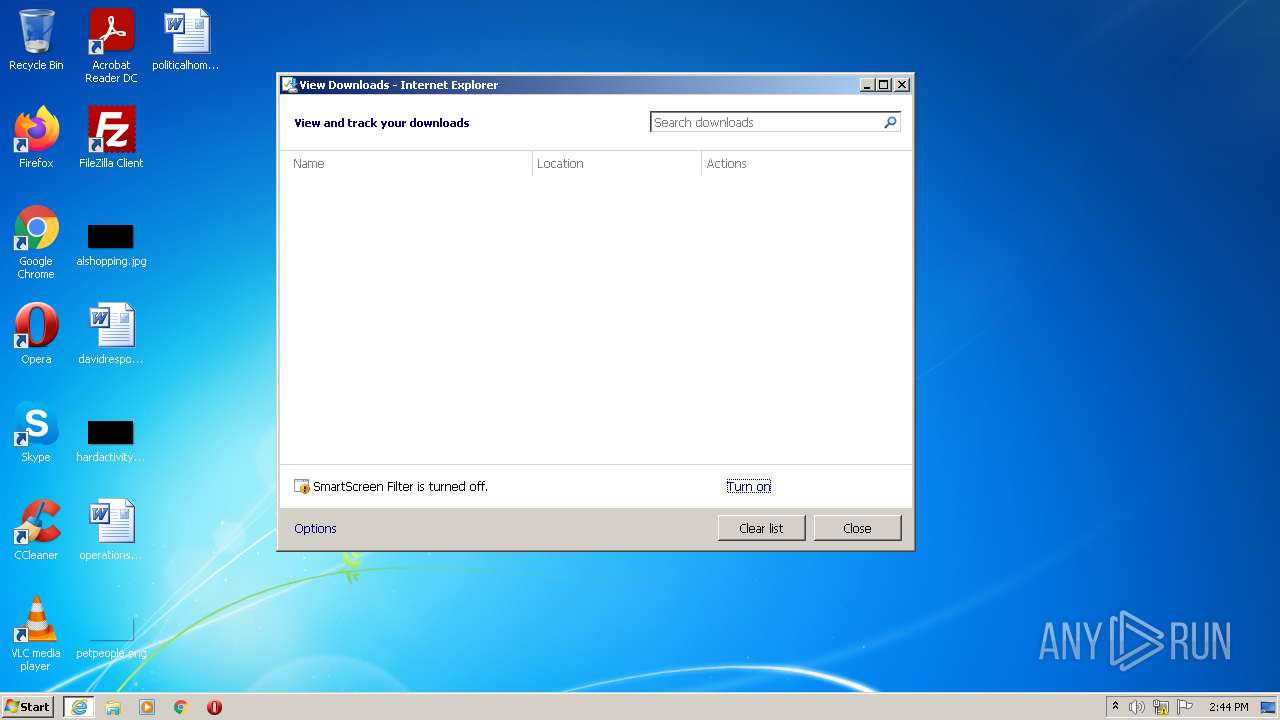
Modifies the phishing filter of IE
- iexplore.exe (PID: 3116)
Changes internet zones settings
- iexplore.exe (PID: 3116)
Checks Windows Trust Settings
- iexplore.exe (PID: 3116)
- rundll32.exe (PID: 1228)
- rundll32.exe (PID: 4028)
- chrome.exe (PID: 3888)
- rundll32.exe (PID: 3080)
Reads the date of Windows installation
- iexplore.exe (PID: 3116)
- chrome.exe (PID: 968)
Reads settings of System Certificates
- iexplore.exe (PID: 3116)
- chrome.exe (PID: 2488)
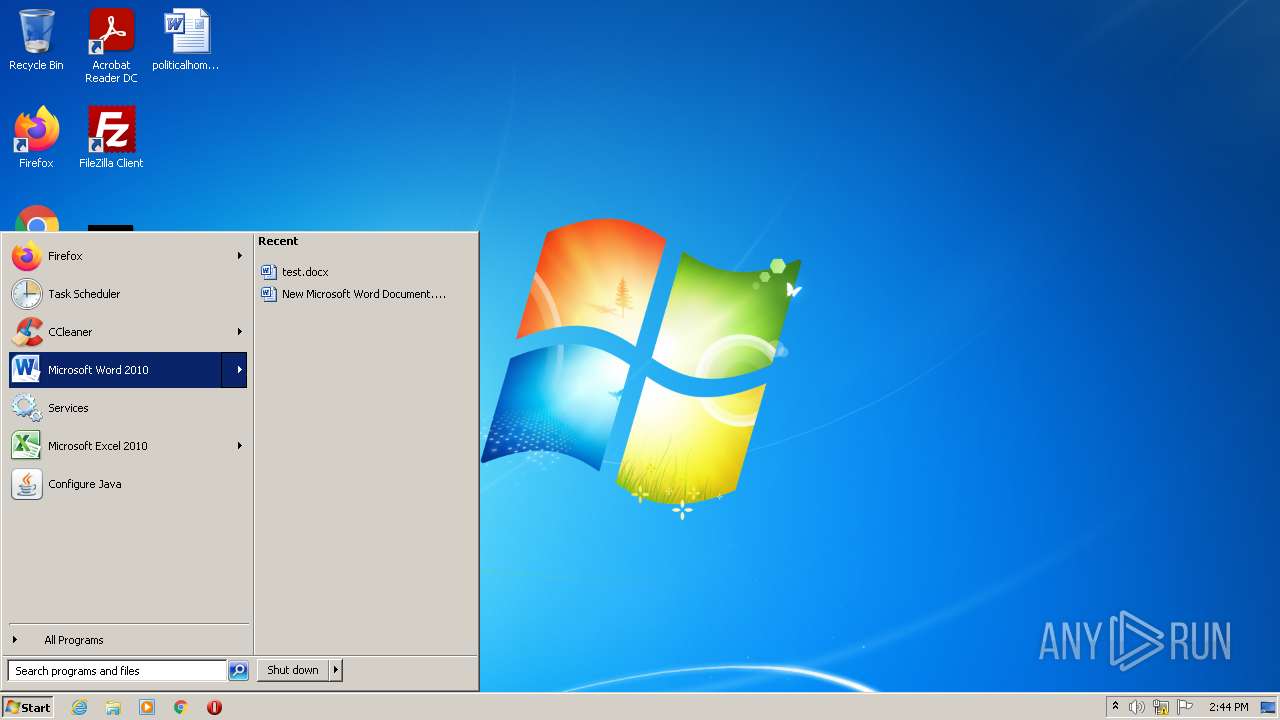
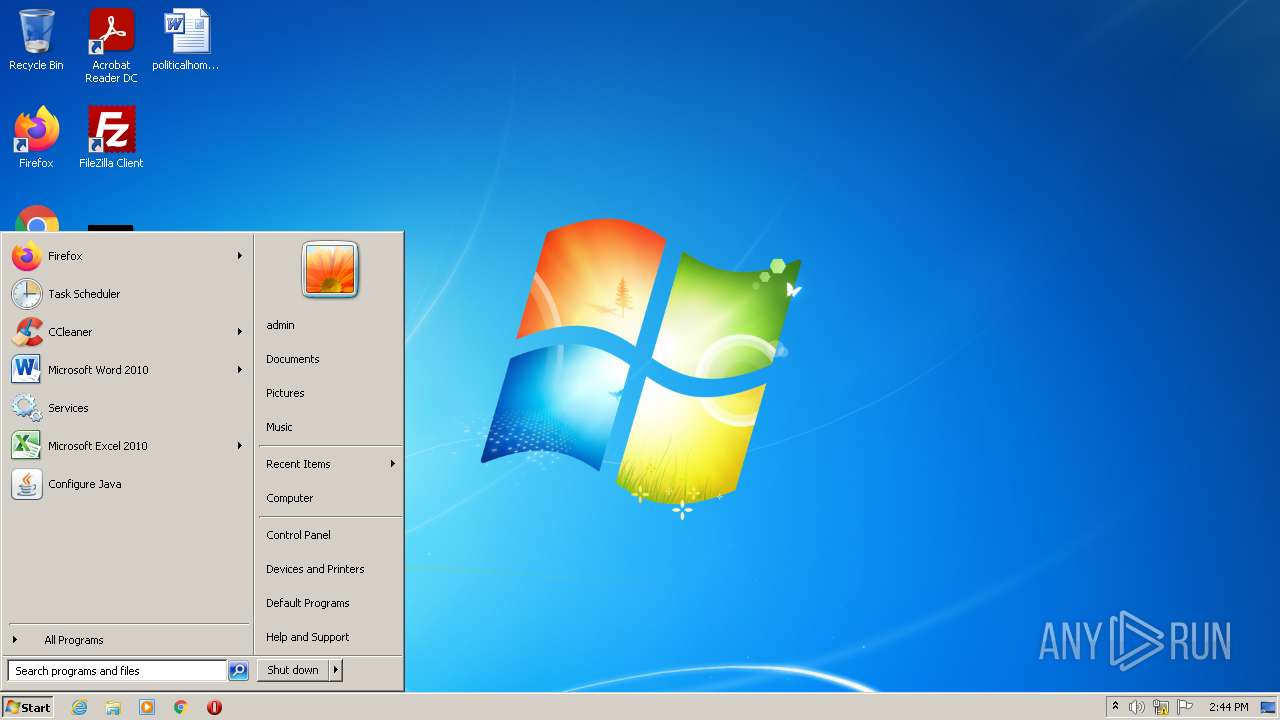
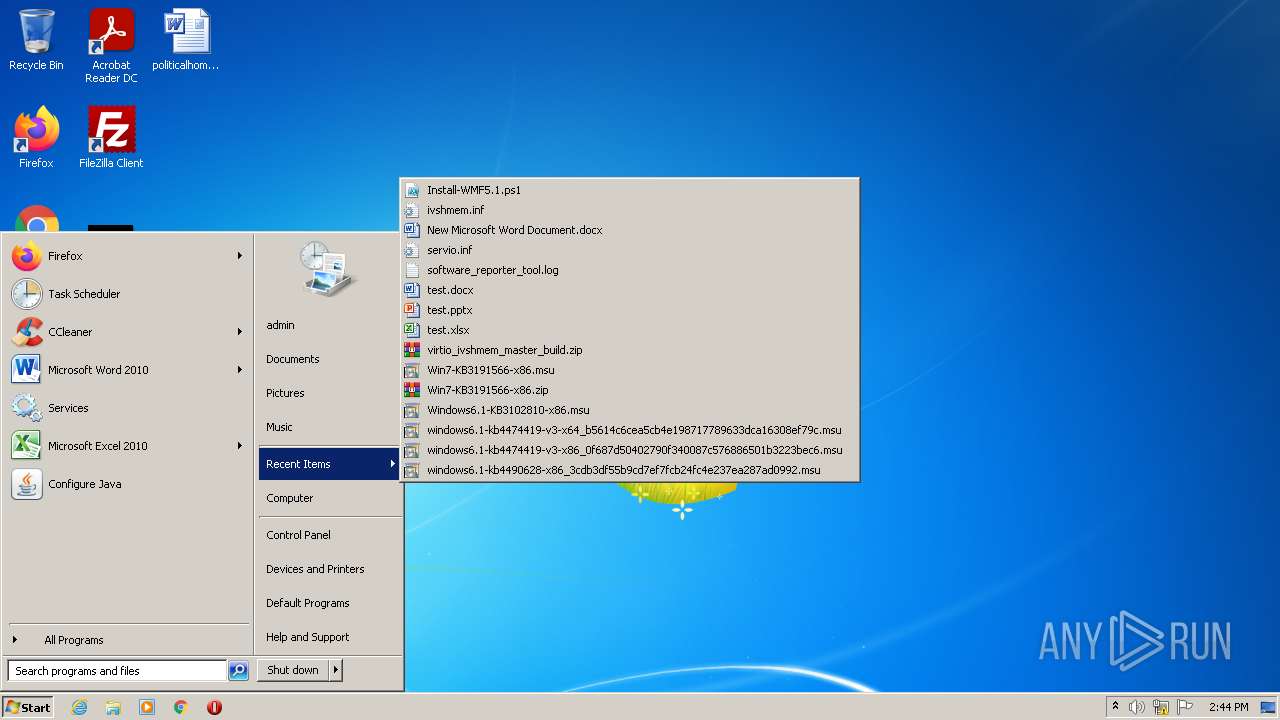
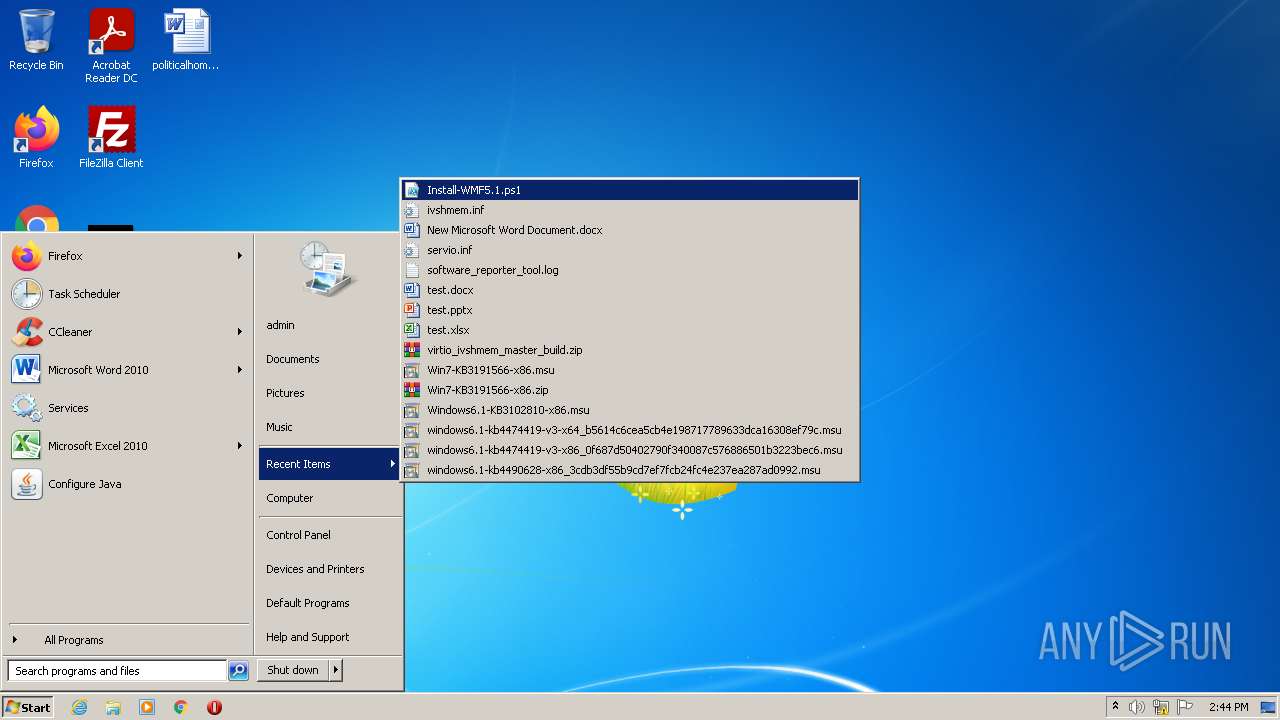
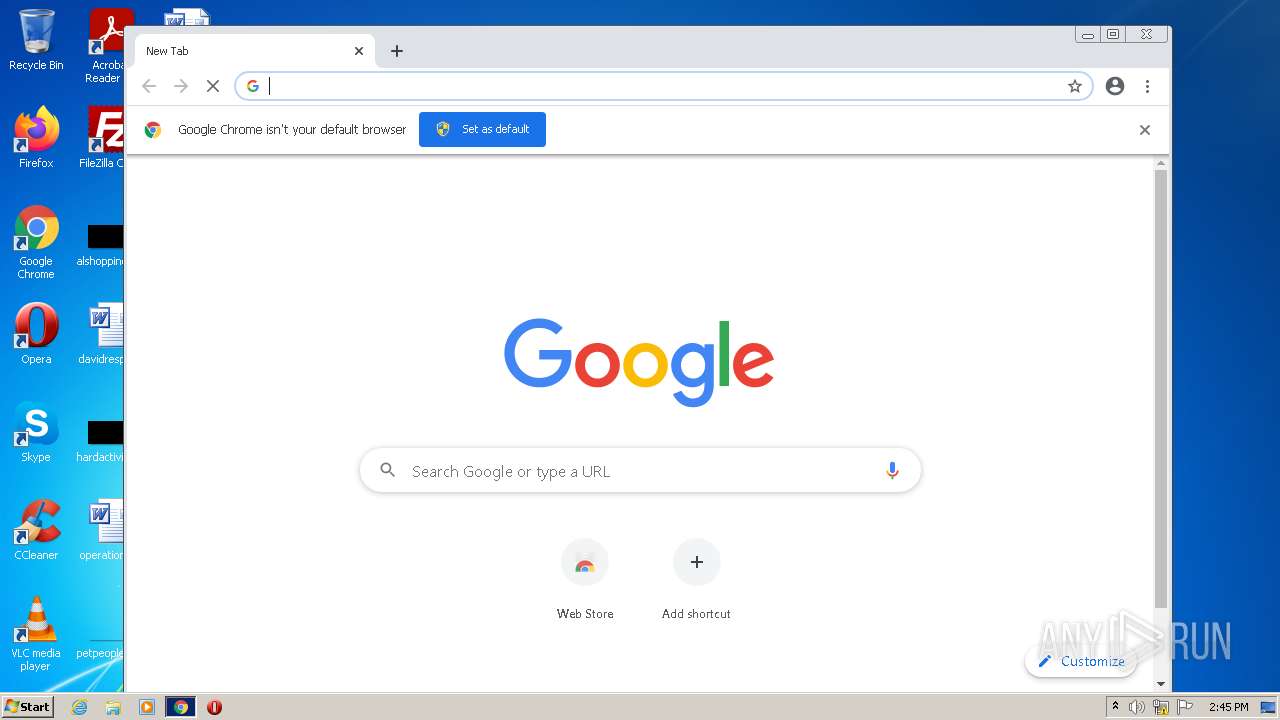
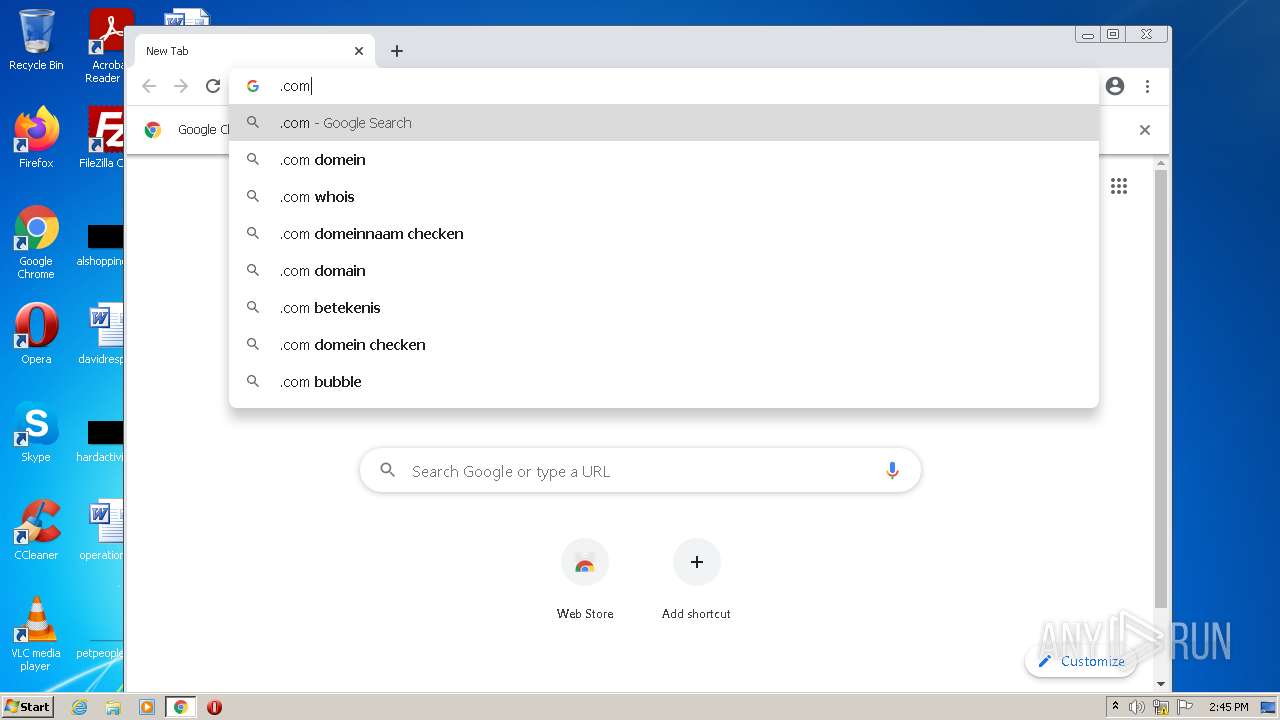
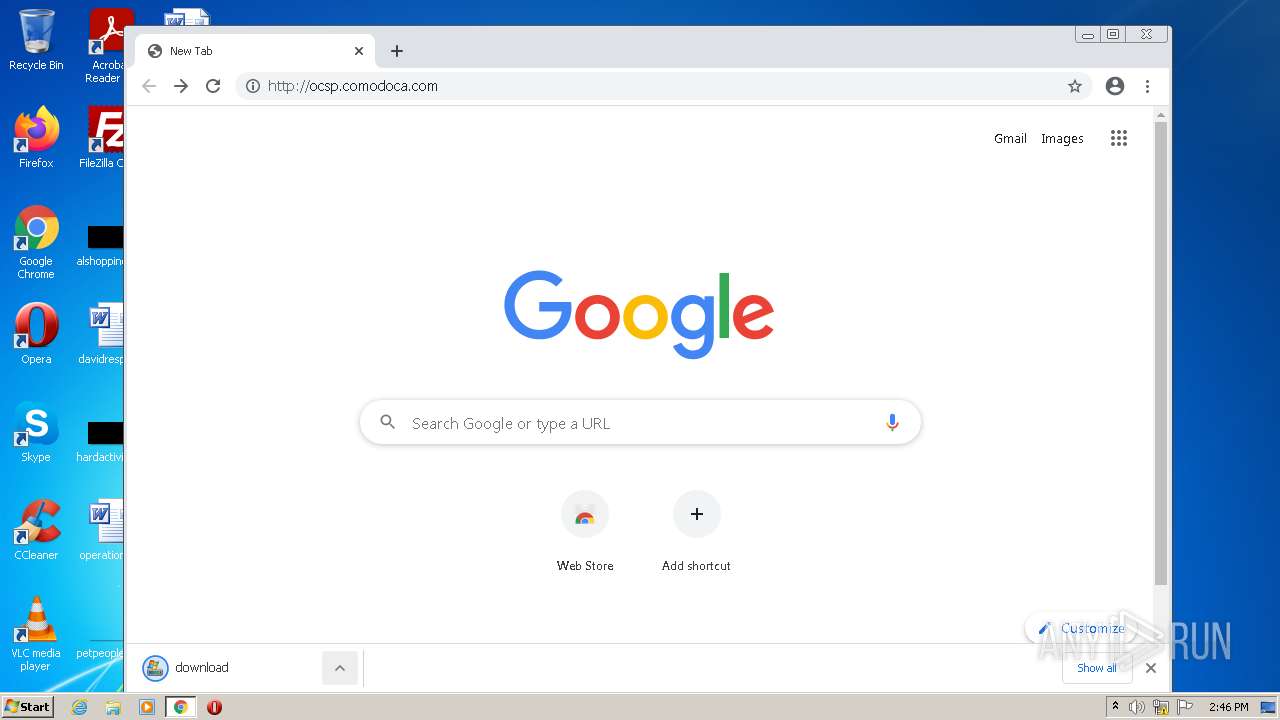
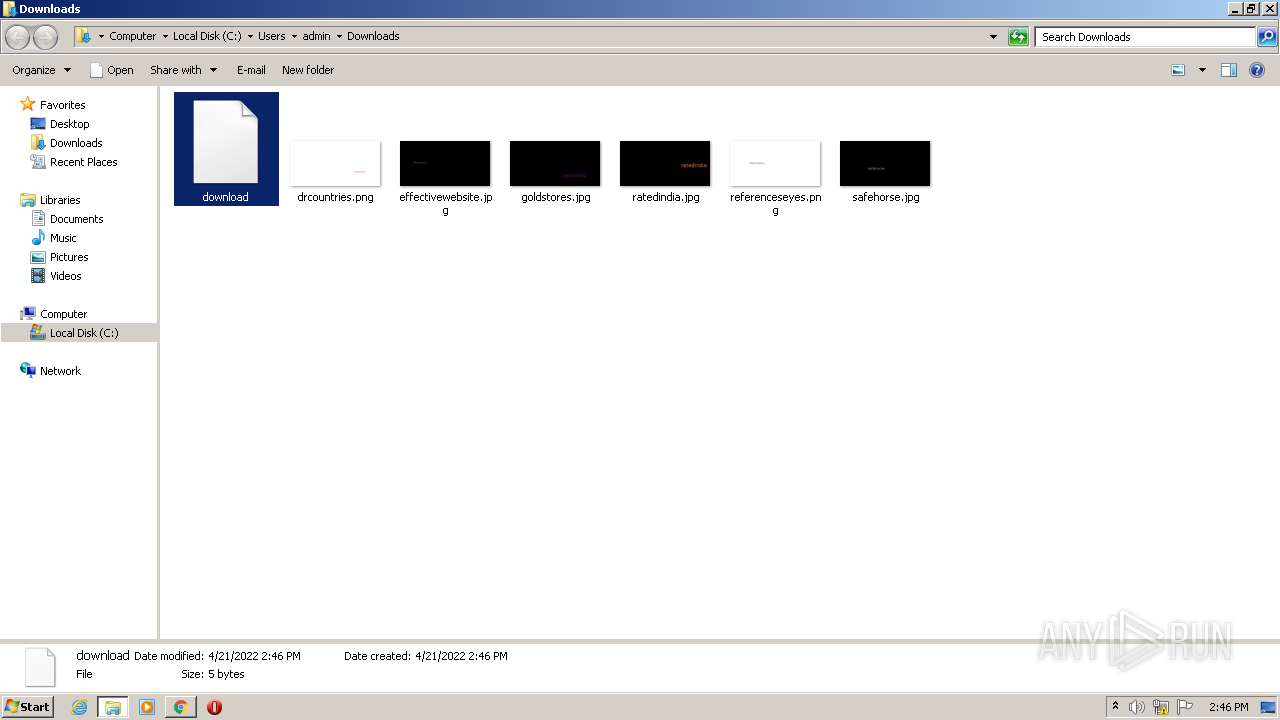
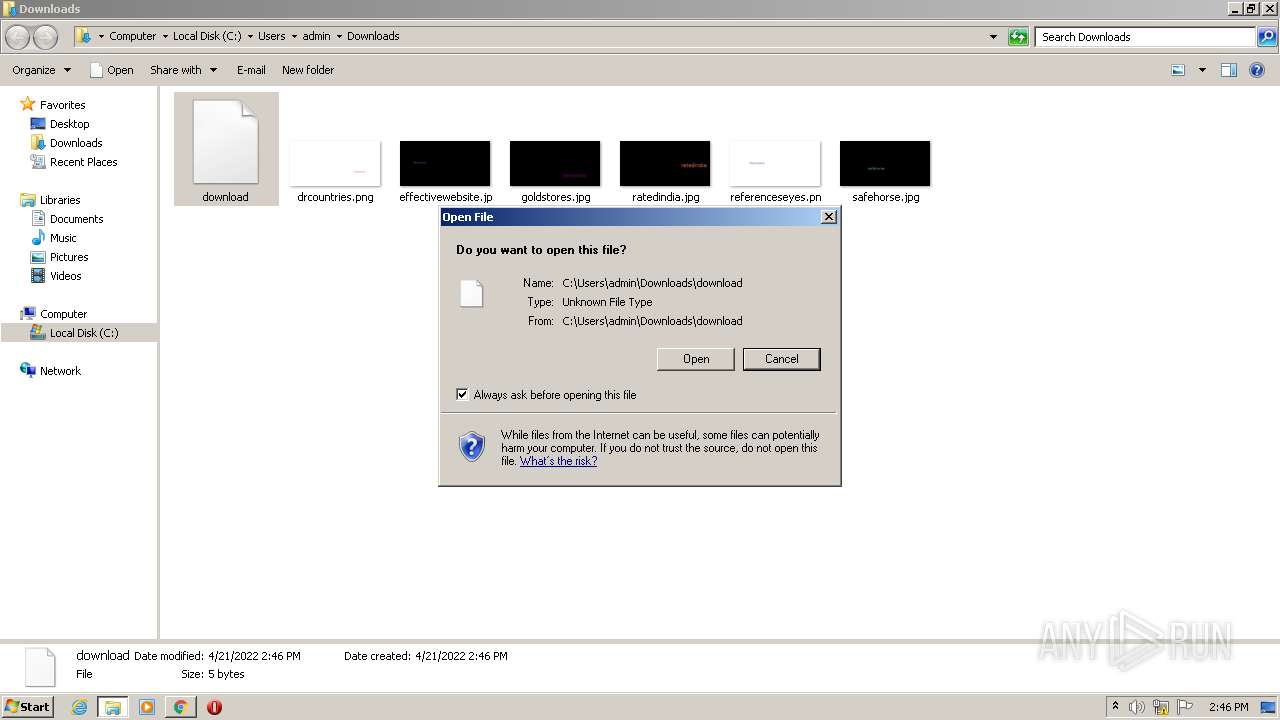
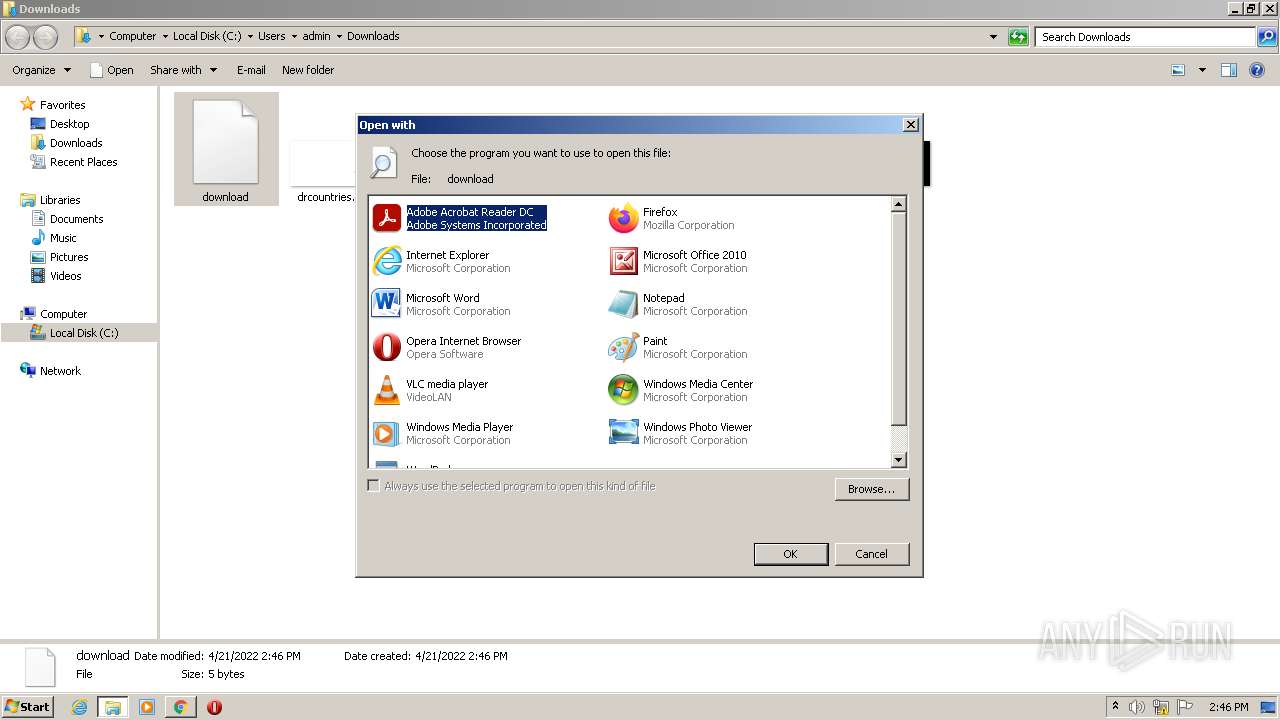
Manual execution by user
- chrome.exe (PID: 3888)
- rundll32.exe (PID: 3080)
Reads the hosts file
- chrome.exe (PID: 3888)
- chrome.exe (PID: 2488)
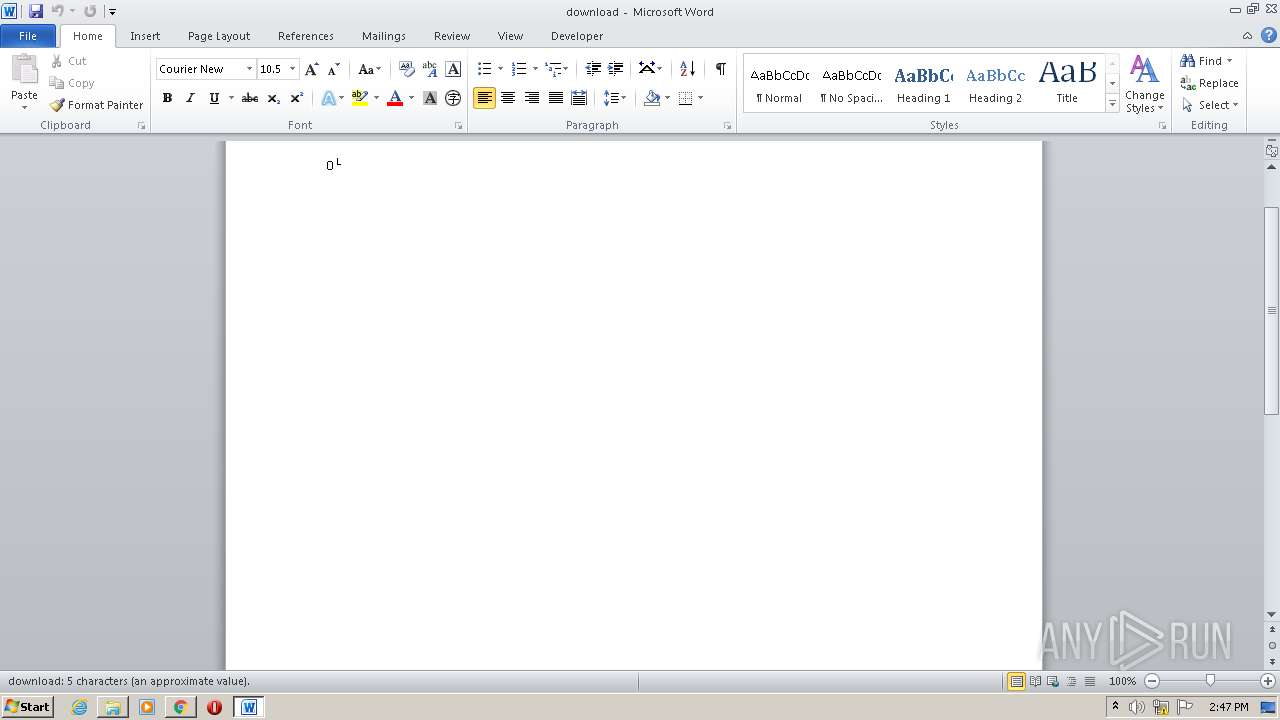
Creates files in the user directory
- WINWORD.EXE (PID: 4036)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 4036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
79
Monitored processes
38
Malicious processes
0
Suspicious processes
1
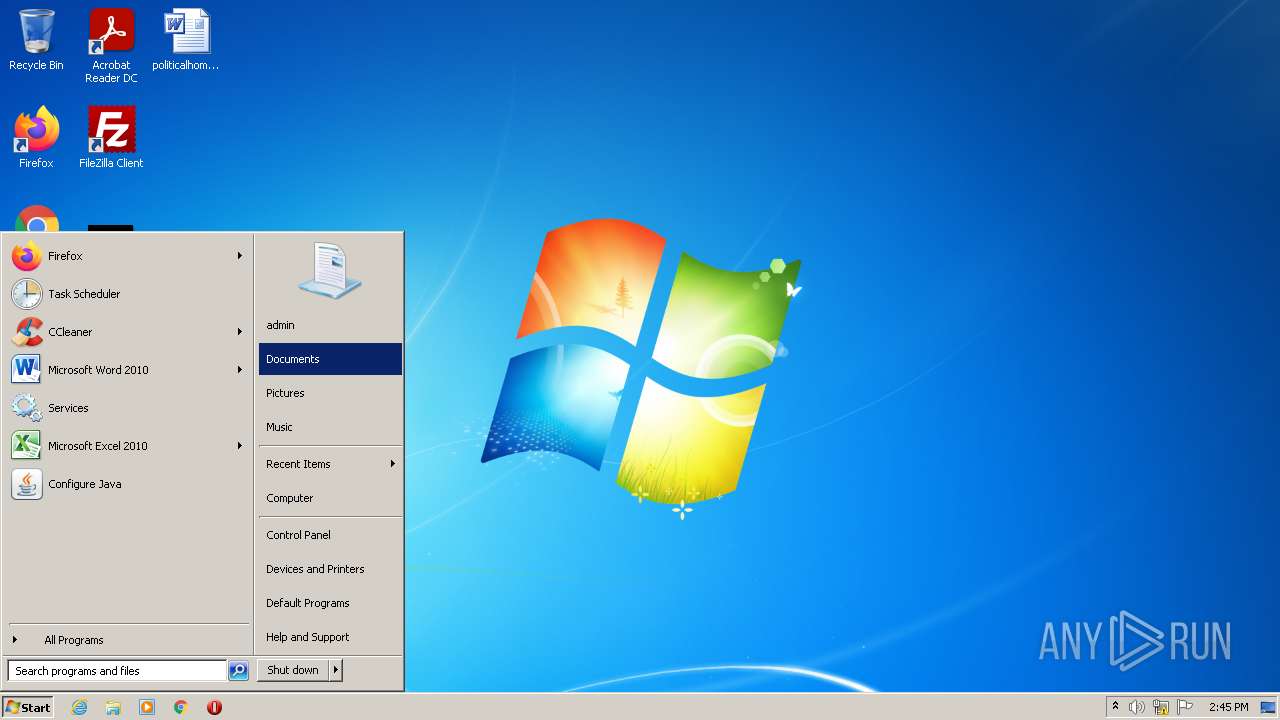
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,15881651153094514501,2186532075183015471,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2424 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1048,15881651153094514501,2186532075183015471,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1052 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1048,15881651153094514501,2186532075183015471,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2916 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,15881651153094514501,2186532075183015471,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2352 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3116 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
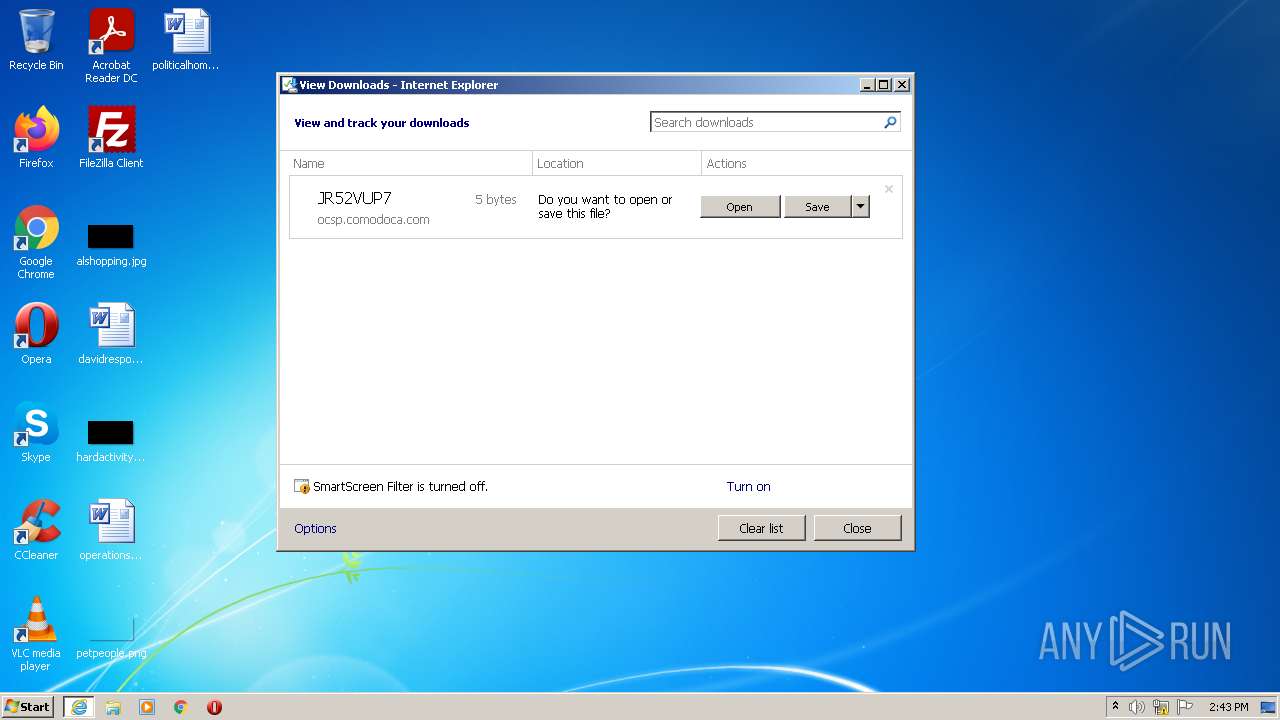
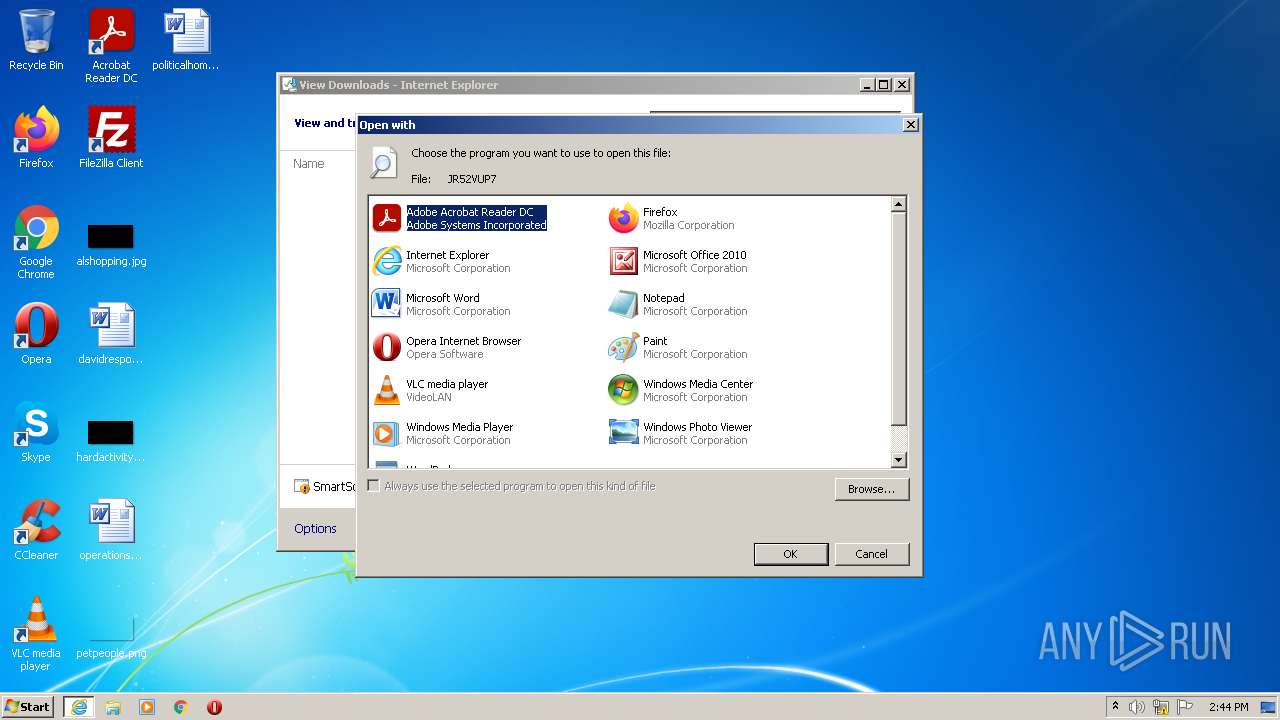
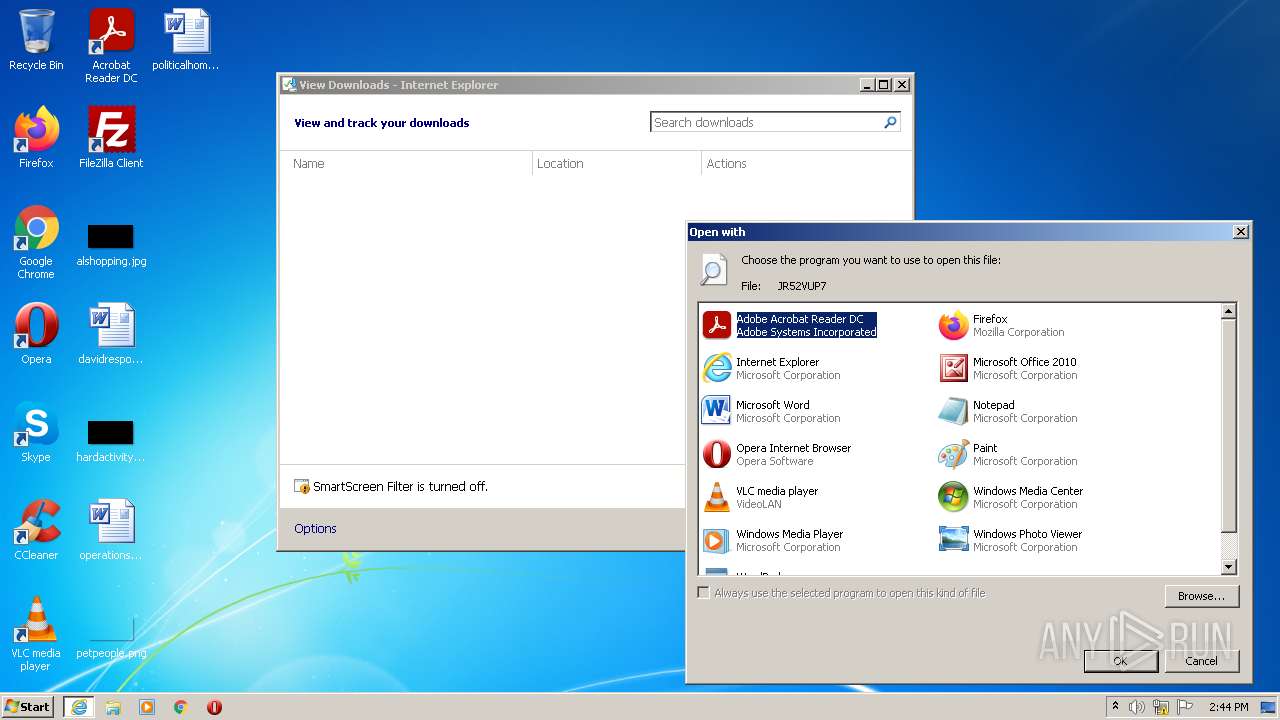
| 1228 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\JR52VUP7 | C:\Windows\system32\rundll32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,15881651153094514501,2186532075183015471,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2088 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1048,15881651153094514501,2186532075183015471,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2104 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1048,15881651153094514501,2186532075183015471,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2032 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,15881651153094514501,2186532075183015471,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2312 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
28 704
Read events
27 914
Write events
637
Delete events
153
Modification events
| (PID) Process: | (3116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30954885 | |||
| (PID) Process: | (3116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30954885 | |||
| (PID) Process: | (3116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
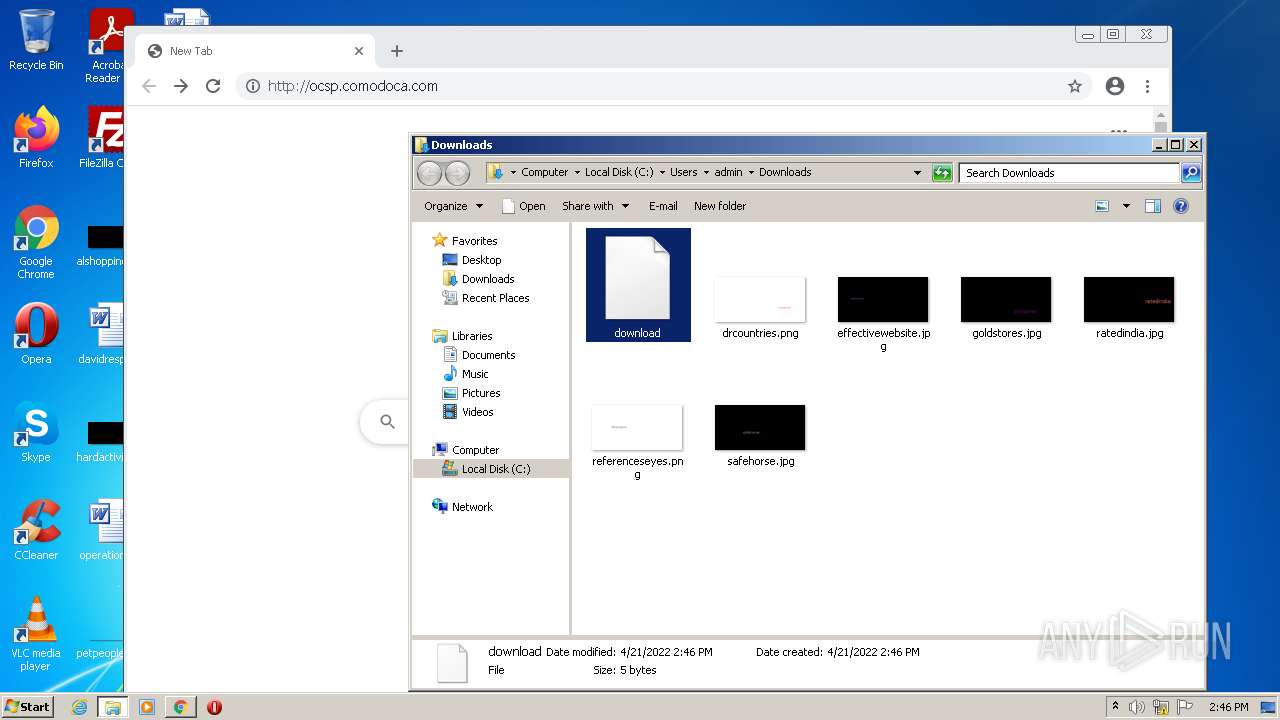
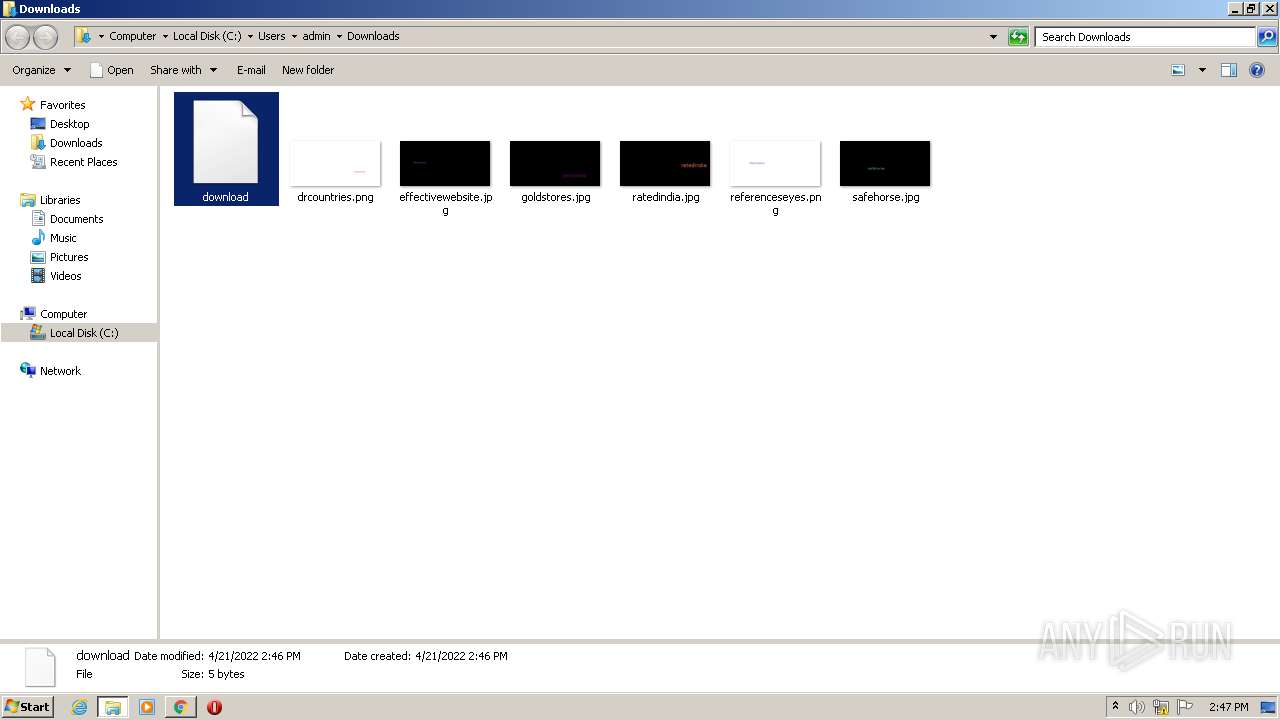
Executable files
0
Suspicious files
154
Text files
151
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:335E3C60A42D85DAD533FB991D2F7286 | SHA256:05D11FEE569A5AA36496A33FB4C8C4FB7AD3E7B1A1E985C53074B1387FC10DD7 | |||
| 3116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:EE7ABE0E8BF4BB699F487FC0E71D135E | SHA256:3F52D71A7955154A0FA5F8444BC05F73412E1BDBFB09CCA1A5645D958DFAE2F8 | |||
| 3116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:DEB68FFC0F68E1790946302A0E165892 | SHA256:B7DBD6C513201B675E981C591AC81B60B11AF5266DA89E8B9B5B442B4C060D3A | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62615FE7-F30.pma | — | |
MD5:— | SHA256:— | |||
| 3116 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{0DEF85CF-C179-11EC-B9F6-12A9866C77DE}.dat | binary | |
MD5:B1D2E775DBF002907C61B3589D2897CA | SHA256:FA255244F1ED729105BD37BD6DB6A2296D39DEA837C45F1F1B8F34FB50B2360A | |||
| 3116 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF905458B7D383E642.TMP | gmc | |
MD5:6F23D5C0A726100E05017E9B74FCDA1F | SHA256:DB51DE8E5B0E79A7FB3ACE579AA1C3691E80C1AE225ECC27AA007A9580C7D14F | |||
| 3116 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{21B5262B-C179-11EC-B9F6-12A9866C77DE}.dat | binary | |
MD5:EF8C45F64EEE68D925E79872F4215093 | SHA256:BBD97AFF62A044737712902E4C9ED07B412AFEA2615995F3BD8A76E920A27BD6 | |||
| 3116 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF5C171323394D2E1E.TMP | gmc | |
MD5:16D5B7C775019B5CFD291DA2244D1A92 | SHA256:433904EDFC1299AE1C4D98E20053F3D3F741D13CD946A53E7408821015F90CDC | |||
| 3116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6DB145CFEEC544B1582FED1ADA3370DD | binary | |
MD5:88D7C18BFEF9CAAE06CEA55CC4A0D62A | SHA256:521741371AC62AC2FAC4AE48D40BD9999351D87AB7ADEE4FA90CA7CAC5328AE4 | |||
| 3116 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFDC7A8DAE4A0EF320.TMP | gmc | |
MD5:5523E0168EE6BD3ACBE5DABFBD117420 | SHA256:31AEF940E3D0888D8ECD309C5B3C3E34AF6056D87FBCEB2F3CBD692BB0120CFD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
38
DNS requests
103
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3116 | iexplore.exe | GET | 200 | 104.110.191.133:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?07aa7a3b80a5b1b3 | US | compressed | 4.70 Kb | whitelisted |
3116 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3116 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertGlobalRootCA.crl | US | der | 631 b | whitelisted |
1180 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.comodoca.com/ | US | binary | 5 b | whitelisted |
3116 | iexplore.exe | GET | — | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | — | — | whitelisted |
2488 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 5.64 Kb | whitelisted |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | — | — | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 7.82 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 10.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3116 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3116 | iexplore.exe | 104.110.191.133:80 | ctldl.windowsupdate.com | Akamai Technologies, Inc. | US | unknown |
1180 | iexplore.exe | 104.18.32.68:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
3116 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3116 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2488 | chrome.exe | 216.58.208.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
2488 | chrome.exe | 216.58.208.100:443 | www.google.com | Google Inc. | US | whitelisted |
2488 | chrome.exe | 142.250.179.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2488 | chrome.exe | 142.251.39.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2488 | chrome.exe | 142.251.36.45:443 | accounts.google.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ocsp.comodoca.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
dns.msftncsi.com |
| shared |
ocsp.digicert.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |