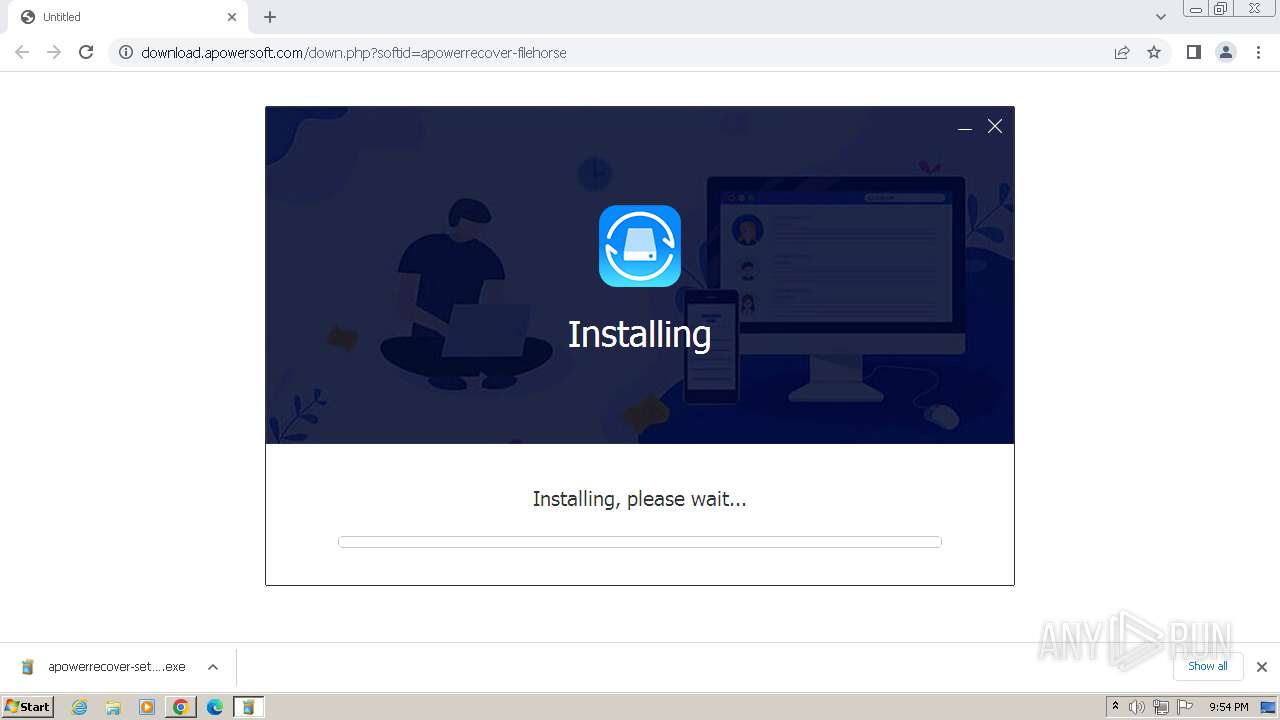
| URL: | https://download.apowersoft.com/down.php?softid=apowerrecover-filehorse |
| Full analysis: | https://app.any.run/tasks/0d44528e-ce3d-4721-a363-970bffb5682b |
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2024, 20:54:17 |
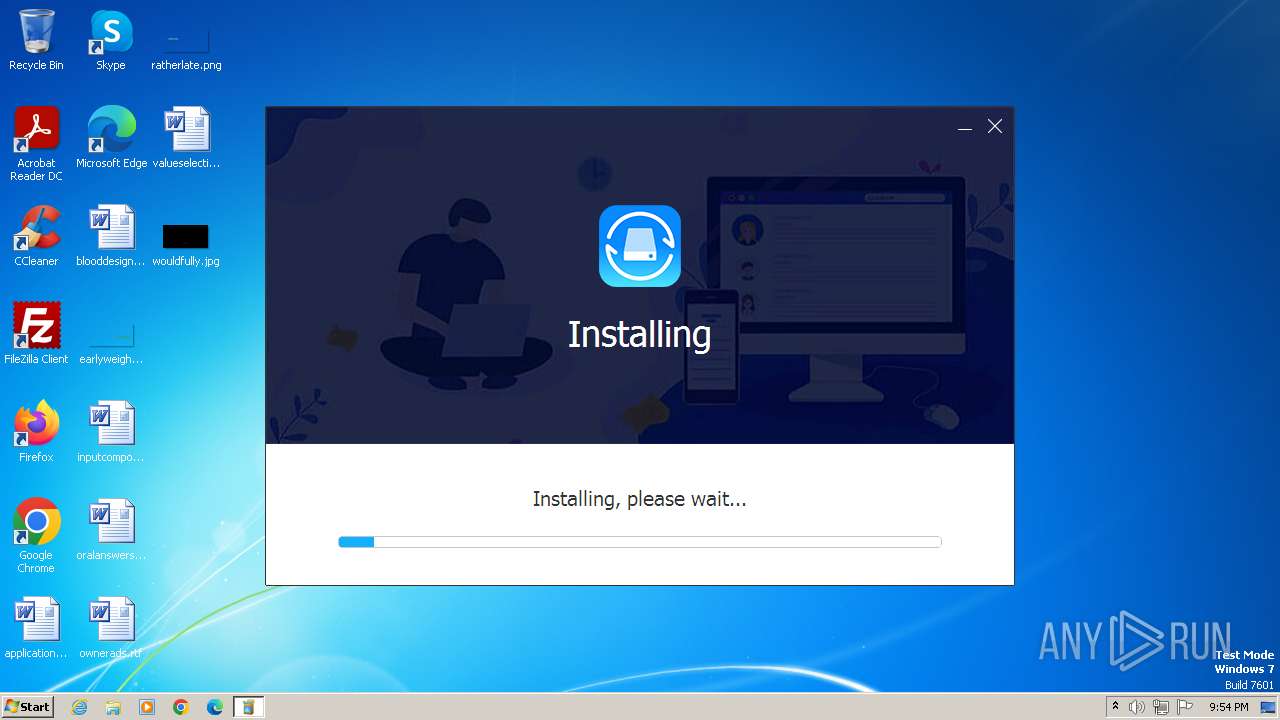
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5AE47F94C9EBBBBFC94C6A40C7596227 |
| SHA1: | 3EC9BAF709B1D270BDBE44013C3C1E3BEA51798C |
| SHA256: | 2FA9E14DC0AD0AB5C3E306E248BE38AD7E3B6A44C64929B0390208420FF4502F |
| SSDEEP: | 3:N8SEl22RLR8CNVd8iJyT9Y0:2SK2sR8CNVuiJyTn |
MALICIOUS
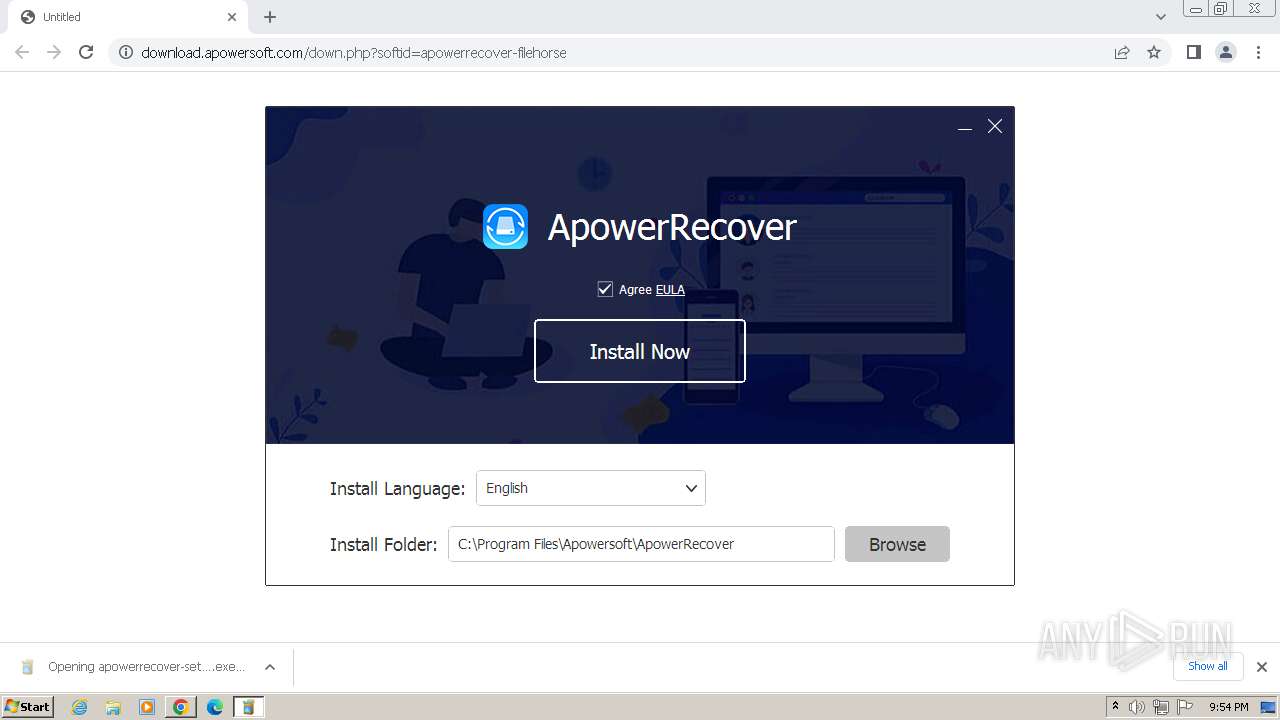
Drops the executable file immediately after the start
- installer.exe (PID: 1644)
- installer.tmp (PID: 2780)
SUSPICIOUS
Reads the Internet Settings
- apowerrecover-setup-filehorse.exe (PID: 2764)
- AliyunWrapExe.Exe (PID: 2696)
- installer.tmp (PID: 2780)
Reads security settings of Internet Explorer
- apowerrecover-setup-filehorse.exe (PID: 2764)
- AliyunWrapExe.Exe (PID: 2696)
- installer.tmp (PID: 2780)
Executable content was dropped or overwritten
- installer.exe (PID: 1644)
- installer.tmp (PID: 2780)
Reads the Windows owner or organization settings
- installer.tmp (PID: 2780)
Changes Internet Explorer settings (feature browser emulation)
- EUinApp.exe (PID: 3440)
Process drops legitimate windows executable
- installer.tmp (PID: 2780)
The process drops C-runtime libraries
- installer.tmp (PID: 2780)
INFO
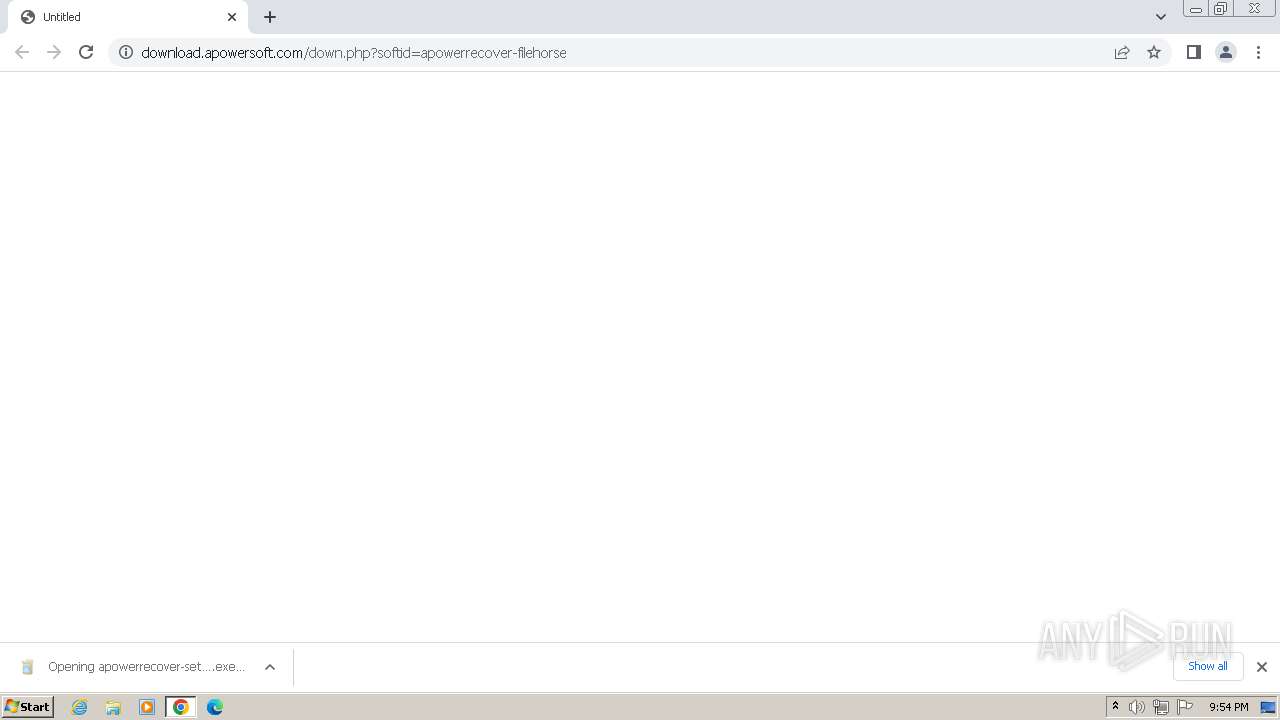
The process uses the downloaded file
- chrome.exe (PID: 188)
- chrome.exe (PID: 3960)
Application launched itself
- chrome.exe (PID: 3960)
- msedge.exe (PID: 3540)
- msedge.exe (PID: 2052)
Reads the computer name
- wmpnscfg.exe (PID: 2168)
- apowerrecover-setup-filehorse.exe (PID: 2764)
- installer.tmp (PID: 2780)
- AliyunWrapExe.Exe (PID: 2696)
- InfoForSetup.exe (PID: 916)
Checks supported languages
- wmpnscfg.exe (PID: 2168)
- apowerrecover-setup-filehorse.exe (PID: 2764)
- installer.exe (PID: 1644)
- installer.tmp (PID: 2780)
- InfoForSetup.exe (PID: 916)
- AliyunWrapExe.Exe (PID: 2696)
- InfoForSetup.exe (PID: 2836)
- InfoForSetup.exe (PID: 2912)
- InfoForSetup.exe (PID: 2672)
- EUinApp.exe (PID: 3440)
- InfoForSetup.exe (PID: 3496)
- SetupUE.exe (PID: 3684)
- InfoForSetup.exe (PID: 3576)
- InfoForSetup.exe (PID: 3700)
Manual execution by a user
- wmpnscfg.exe (PID: 2168)
- msedge.exe (PID: 2052)
Executable content was dropped or overwritten
- chrome.exe (PID: 3960)
Drops the executable file immediately after the start
- chrome.exe (PID: 3960)
Create files in a temporary directory
- apowerrecover-setup-filehorse.exe (PID: 2764)
- installer.exe (PID: 1644)
- installer.tmp (PID: 2780)
- AliyunWrapExe.Exe (PID: 2696)
Reads the machine GUID from the registry
- apowerrecover-setup-filehorse.exe (PID: 2764)
- AliyunWrapExe.Exe (PID: 2696)
Creates files in the program directory
- apowerrecover-setup-filehorse.exe (PID: 2764)
- installer.tmp (PID: 2780)
Checks proxy server information
- AliyunWrapExe.Exe (PID: 2696)
Creates a software uninstall entry
- installer.tmp (PID: 2780)
Creates files or folders in the user directory
- apowerrecover-setup-filehorse.exe (PID: 2764)
- AliyunWrapExe.Exe (PID: 2696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
85
Monitored processes
44
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3772 --field-trial-handle=1148,i,13539599199737919351,5092840889132813259,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3912 --field-trial-handle=1148,i,13539599199737919351,5092840889132813259,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3532 --field-trial-handle=1148,i,13539599199737919351,5092840889132813259,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1636 --field-trial-handle=1304,i,16230497714127023551,3651055894363054267,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 916 | "C:\Users\admin\AppData\Local\Temp\is-Q5FKA.tmp\InfoForSetup.exe" /SendInfo "Window" "Langsel" "Activity" "Click_Confirm" "Attribute" "{\"Language\":\"en\"}" | C:\Users\admin\AppData\Local\Temp\is-Q5FKA.tmp\InfoForSetup.exe | — | installer.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=2220 --field-trial-handle=1304,i,16230497714127023551,3651055894363054267,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 972 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=1100 --field-trial-handle=1304,i,16230497714127023551,3651055894363054267,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1104 --field-trial-handle=1148,i,13539599199737919351,5092840889132813259,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1508 --field-trial-handle=1148,i,13539599199737919351,5092840889132813259,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1260 --field-trial-handle=1304,i,16230497714127023551,3651055894363054267,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
19 989
Read events
19 760
Write events
203
Delete events
26
Modification events
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
152
Suspicious files
167
Text files
3 015
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF103c7e.TMP | — | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF103c7e.TMP | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:456D3EF989973A7C218E338A6CFFAD25 | SHA256:75631D994431F254B94255C50038A3657BFC45D76FCE9D794D514E57CA678872 | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF103e34.TMP | text | |
MD5:4755704EAEB72509F8E78594142D80D6 | SHA256:52D45B3A4947B8B5B8C48F83F83BA6758CFB7C4434FC574124378F5B01E15999 | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF104a0b.TMP | — | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:825B582C78EC88D54C215EFDF1EAD639 | SHA256:367995D01A8F13E5C30C79499F86B034775BFD009D83DC97635DE438D47DFA37 | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:98CC34E7F20FD8F55568DB9B3D3B507E | SHA256:8D3D74EC41FF0CCE1F26B23F66E5981B7F59C40AB0DBB468B3A3E5E63C80F3C7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
57
DNS requests
50
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2764 | apowerrecover-setup-filehorse.exe | GET | 200 | 47.89.5.161:80 | http://wx-user-behavior.cn-hongkong.log.aliyuncs.com/logstores/webtrack/track?APIVersion=0.6.0&__topic__=win-launcher&unique_id=8287a29015fb0005117c3061d4580267&session_id=1716670478&app=ApowerRecover&appid=406&apptype=filehorse&installer_version=1.1.1.6&is_old_user=-1&last_step_duration=0&os_available_memory=2470000000&os_culture=0409&os_dpi=100&os_fullname=Microsoft%20Windows%207%20Professional%20&os_lang=en-US&os_resolution=1280x720&os_total_memory=3145208000&os_version=6.1.7601&step=1 | unknown | — | — | unknown |
2764 | apowerrecover-setup-filehorse.exe | GET | 200 | 47.89.5.161:80 | http://wx-user-behavior.cn-hongkong.log.aliyuncs.com/logstores/webtrack/track?APIVersion=0.6.0&__topic__=win-launcher&unique_id=8287a29015fb0005117c3061d4580267&session_id=1716670478&app=ApowerRecover&appid=406&ga_request=https%3A%2F%2Fdownload.aoscdn.com%2Fapi%2Fclient%2Finfo%3Fot%3D1%26mt%3D1716670470%26ct%3D1716670468%26cc%3D4%26tz%3DGMT%252B0100%26ov%3D6.1%26g%3DStandard%2520VGA%2520Graphics%2520Adapter%26h%3D55483a7efe14d8cfd748c9891fe4b9ff&step=1 | unknown | — | — | unknown |
2764 | apowerrecover-setup-filehorse.exe | GET | 200 | 47.89.5.161:80 | http://wx-user-behavior.cn-hongkong.log.aliyuncs.com/logstores/webtrack/track?APIVersion=0.6.0&__topic__=win-launcher&unique_id=8287a29015fb0005117c3061d4580267&session_id=1716670478&app=ApowerRecover&app_install_path=C%3A%5CProgram%20Files%5CApowersoft%5CApowerRecover&app_lang=English&appid=406&apptype=filehorse&last_step_duration=3&step=2 | unknown | — | — | unknown |
2764 | apowerrecover-setup-filehorse.exe | GET | 200 | 47.89.5.161:80 | http://wx-user-behavior.cn-hongkong.log.aliyuncs.com/logstores/webtrack/track?APIVersion=0.6.0&__topic__=win-launcher&unique_id=8287a29015fb0005117c3061d4580267&session_id=1716670478&app=ApowerRecover&appid=406&ga_error=&ga_ok=0&ga_response=%7B%22status%22%3A404%2C%22message%22%3A%22Not%20found%22%7D&gaid=&step=1 | unknown | — | — | unknown |
2764 | apowerrecover-setup-filehorse.exe | GET | 404 | 163.181.92.226:80 | http://cdn.aoscdn.com/img/contact-group/installer-406-qq.png?19868 | unknown | — | — | unknown |
2696 | AliyunWrapExe.Exe | GET | 200 | 163.171.156.15:80 | http://track.easeus.com/product/index.php?c=main&a=getstatus&pid=2 | unknown | — | — | unknown |
2764 | apowerrecover-setup-filehorse.exe | GET | 302 | 47.243.121.132:80 | http://download.aoscdn.com/down.php?softid=apowerrecoverinstall-filehorse | unknown | — | — | unknown |
2696 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.212:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_windrw_ip/shards/lb | unknown | — | — | unknown |
2696 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.212:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_windrw_ip/shards/lb | unknown | — | — | unknown |
2696 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.212:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_windrw_ip/shards/lb | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1120 | chrome.exe | 64.233.184.84:443 | accounts.google.com | GOOGLE | US | unknown |
3960 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
1120 | chrome.exe | 47.243.121.132:443 | download.apowersoft.com | Alibaba US Technology Co., Ltd. | HK | unknown |
1120 | chrome.exe | 172.67.75.55:443 | download.apowersoft.info | CLOUDFLARENET | US | unknown |
3960 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
1120 | chrome.exe | 142.250.185.196:443 | www.google.com | GOOGLE | US | whitelisted |
1120 | chrome.exe | 142.250.184.206:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
download.apowersoft.com |
| unknown |
download.apowersoft.info |
| unknown |
www.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
wx-user-behavior.cn-hongkong.log.aliyuncs.com |
| unknown |
download.aoscdn.com |
| unknown |
cdn.aoscdn.com |
| whitelisted |
track.easeus.com |
| unknown |
easeusinfo.us-east-1.log.aliyuncs.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1088 | svchost.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
1088 | svchost.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |