| download: | gny6p8-jbd-686 |
| Full analysis: | https://app.any.run/tasks/2b3acee5-02de-4254-8a8b-f0a8802730f1 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 18, 2020, 09:31:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
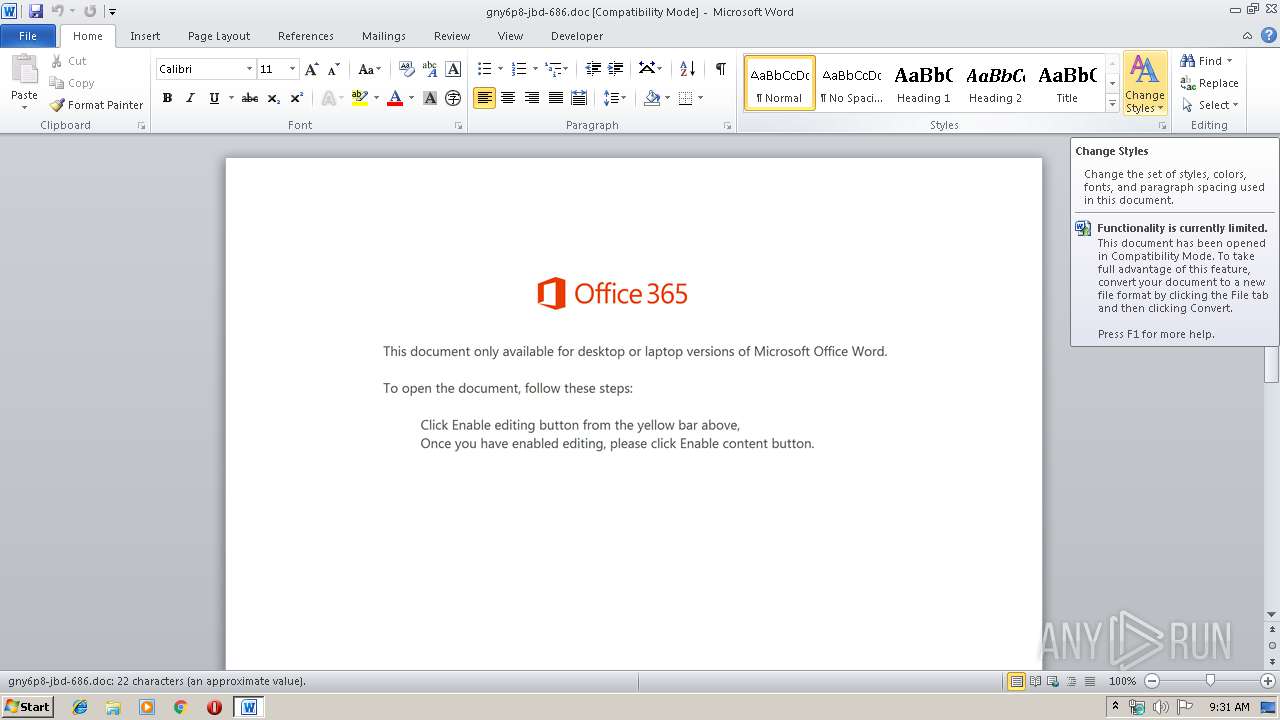
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Nulla., Author: Mohamed Deschamps, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Jan 17 19:33:00 2020, Last Saved Time/Date: Fri Jan 17 19:33:00 2020, Number of Pages: 1, Number of Words: 4, Number of Characters: 23, Security: 0 |
| MD5: | B28AC13475BFA5AF9555EE68B1A1FCD1 |
| SHA1: | A027DF13A1A3BDBF45640AD1E18A8DD4BA701559 |
| SHA256: | 2F90590DA13BE020CAB94F6054224224AF5D674BB07964796CBB051CEF5DDE3A |
| SSDEEP: | 6144:W0Rum7mdLRp1bbSBIR/EHGtCMXgTo8qoFt/etg+soR9wNjaMwVO:W0E3dxtR/iU9mvUPs0ataMwVO |
MALICIOUS
Application was dropped or rewritten from another process
- 948.exe (PID: 1784)
- serialfunc.exe (PID: 2516)
- serialfunc.exe (PID: 2120)
- 948.exe (PID: 520)
- serialfunc.exe (PID: 2772)
- serialfunc.exe (PID: 3388)
- serialfunc.exe (PID: 284)
- 9v4cRdm1u2.exe (PID: 964)
- 9v4cRdm1u2.exe (PID: 3040)
- serialfunc.exe (PID: 2204)
Connects to CnC server
- serialfunc.exe (PID: 2120)
- serialfunc.exe (PID: 284)
Emotet process was detected
- 948.exe (PID: 520)
- 9v4cRdm1u2.exe (PID: 3040)
EMOTET was detected
- serialfunc.exe (PID: 2120)
- serialfunc.exe (PID: 284)
Changes the autorun value in the registry
- serialfunc.exe (PID: 2120)
- serialfunc.exe (PID: 284)
SUSPICIOUS
Executed via WMI
- Powershell.exe (PID: 3688)
PowerShell script executed
- Powershell.exe (PID: 3688)
Starts itself from another location
- 948.exe (PID: 520)
- 9v4cRdm1u2.exe (PID: 3040)
Executable content was dropped or overwritten
- Powershell.exe (PID: 3688)
- 948.exe (PID: 520)
- serialfunc.exe (PID: 2120)
- 9v4cRdm1u2.exe (PID: 3040)
Connects to server without host name
- serialfunc.exe (PID: 2120)
- serialfunc.exe (PID: 284)
Creates files in the program directory
- serialfunc.exe (PID: 2120)
Creates files in the user directory
- Powershell.exe (PID: 3688)
Application launched itself
- serialfunc.exe (PID: 2120)
- serialfunc.exe (PID: 2204)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2764)
- serialfunc.exe (PID: 3388)
- serialfunc.exe (PID: 2772)
Creates files in the user directory
- WINWORD.EXE (PID: 2764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | Nulla. |
|---|---|
| Subject: | - |
| Author: | Mohamed Deschamps |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:01:17 19:33:00 |
| ModifyDate: | 2020:01:17 19:33:00 |
| Pages: | 1 |
| Words: | 4 |
| Characters: | 23 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 26 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
48
Monitored processes
12
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: sample MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 520 | --a900cf3b | C:\Users\admin\948.exe | 948.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Application MFC DShowEncoder Exit code: 0 Version: 1, 0, 0, 76 Modules
| |||||||||||||||
| 964 | "C:\ProgramData\9v4cRdm1u2.exe" | C:\ProgramData\9v4cRdm1u2.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: sample MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1784 | "C:\Users\admin\948.exe" | C:\Users\admin\948.exe | — | Powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Application MFC DShowEncoder Exit code: 0 Version: 1, 0, 0, 76 Modules
| |||||||||||||||
| 2120 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Application MFC DShowEncoder Exit code: 0 Version: 1, 0, 0, 76 Modules
| |||||||||||||||
| 2204 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 9v4cRdm1u2.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: sample MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2516 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 948.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Application MFC DShowEncoder Exit code: 0 Version: 1, 0, 0, 76 Modules
| |||||||||||||||
| 2764 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\gny6p8-jbd-686.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2772 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" "C:\Users\admin\AppData\Local\Temp\3946.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Application MFC DShowEncoder Exit code: 0 Version: 1, 0, 0, 76 Modules
| |||||||||||||||
| 3040 | --dde2eab6 | C:\ProgramData\9v4cRdm1u2.exe | 9v4cRdm1u2.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: sample MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
2 539
Read events
1 637
Write events
775
Delete events
127
Modification events
| (PID) Process: | (2764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 1,c |
Value: 312C6300CC0A0000010000000000000000000000 | |||
| (PID) Process: | (2764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2764) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1345454142 | |||
Executable files
4
Suspicious files
2
Text files
0
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2764 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9891.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2764 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF43750D244E9A2F67.TMP | — | |
MD5:— | SHA256:— | |||
| 3688 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\R29SUB7KB4NIFAW9APSH.temp | — | |
MD5:— | SHA256:— | |||
| 2772 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~Outlook Data File - NoMail.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 2772 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~Outlook.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 2772 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~honey@pot.com.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 2772 | serialfunc.exe | C:\Users\admin\AppData\Local\Temp\3946.tmp | — | |
MD5:— | SHA256:— | |||
| 2764 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2764 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 520 | 948.exe | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
12
DNS requests
5
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | serialfunc.exe | POST | 200 | 51.77.113.102:80 | http://51.77.113.102/3yvSfUp9s | GB | binary | 148 b | malicious |
2120 | serialfunc.exe | POST | — | 98.192.74.164:80 | http://98.192.74.164/IqNhn | US | — | — | malicious |
2120 | serialfunc.exe | POST | 200 | 59.135.126.129:443 | http://59.135.126.129:443/5JpIqWpnPoB9bQc | JP | binary | 724 Kb | malicious |
3688 | Powershell.exe | GET | 403 | 103.209.144.198:80 | http://neproperty.in/cgi-bin/hjjz1r5p-5n7mea41-7609513198/ | IN | html | 380 b | suspicious |
284 | serialfunc.exe | POST | — | 98.192.74.164:80 | http://98.192.74.164/rSDH1wPb4ZXB3wTxl | US | — | — | malicious |
284 | serialfunc.exe | POST | 200 | 59.135.126.129:443 | http://59.135.126.129:443/AFFRH2g | JP | binary | 148 b | malicious |
2120 | serialfunc.exe | POST | 200 | 59.135.126.129:443 | http://59.135.126.129:443/osUOrQOxP | JP | binary | 148 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2120 | serialfunc.exe | 98.192.74.164:80 | — | Comcast Cable Communications, LLC | US | malicious |
2120 | serialfunc.exe | 51.77.113.102:80 | — | — | GB | malicious |
3688 | Powershell.exe | 103.209.144.198:80 | neproperty.in | Micro Hosting Private Limited | IN | suspicious |
3688 | Powershell.exe | 145.14.145.157:443 | mcuong.000webhostapp.com | Hostinger International Limited | US | shared |
284 | serialfunc.exe | 98.192.74.164:80 | — | Comcast Cable Communications, LLC | US | malicious |
2120 | serialfunc.exe | 59.135.126.129:443 | — | KDDI CORPORATION | JP | malicious |
284 | serialfunc.exe | 59.135.126.129:443 | — | KDDI CORPORATION | JP | malicious |
3688 | Powershell.exe | 217.160.5.123:443 | okaseo.com | 1&1 Internet SE | DE | unknown |
3688 | Powershell.exe | 185.216.113.122:443 | koddata.com | — | TR | suspicious |
3688 | Powershell.exe | 23.235.217.105:443 | parentingtopsecrets.com | InMotion Hosting, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
okaseo.com |
| malicious |
koddata.com |
| suspicious |
parentingtopsecrets.com |
| unknown |
neproperty.in |
| unknown |
mcuong.000webhostapp.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
3688 | Powershell.exe | Not Suspicious Traffic | ET INFO Observed SSL Cert for Free Hosting Domain (*.000webhostapp .com) |
2120 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
2120 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
2120 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2120 | serialfunc.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2120 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2120 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
2120 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
2120 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |