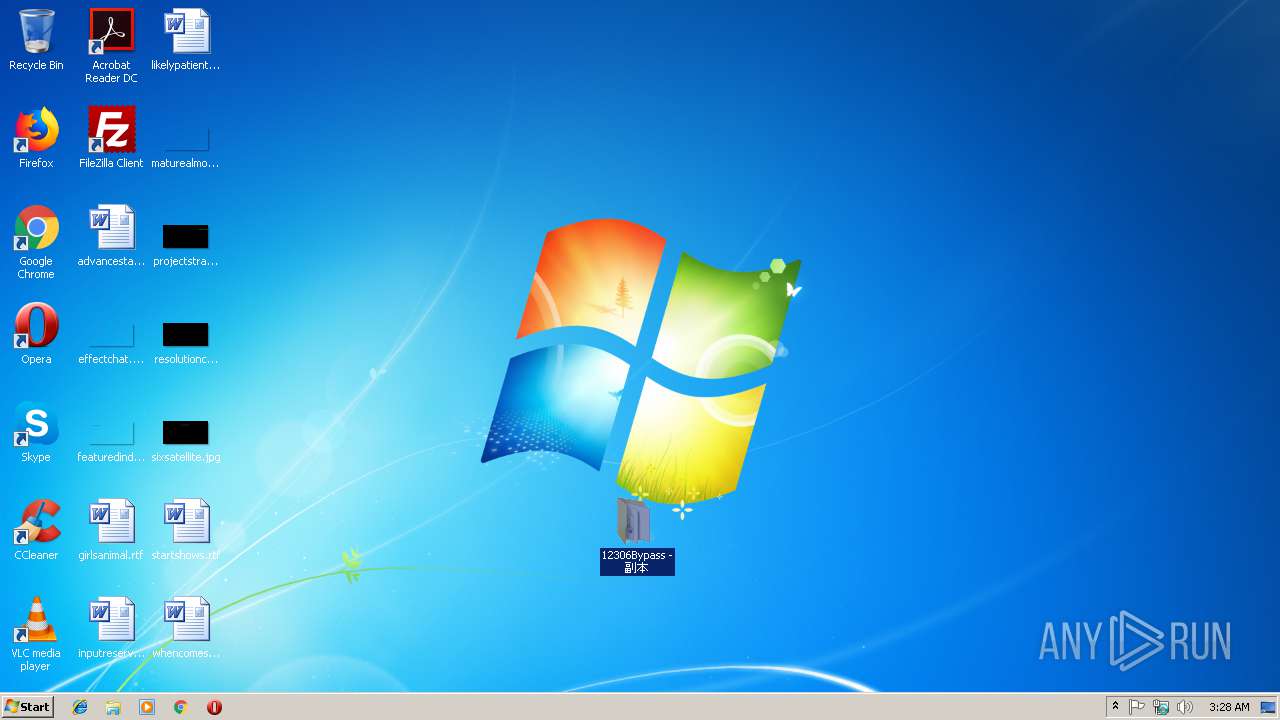
| File name: | 12306Bypass - 副本.rar |
| Full analysis: | https://app.any.run/tasks/8fb56be6-bb95-487a-901d-c1f333569f2e |
| Verdict: | Malicious activity |
| Analysis date: | January 29, 2019, 03:28:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 62A5332E3EA9503A6A1884B3548F21CC |
| SHA1: | E74D2AC986E82E5C86950FC85E2845BE6F140FD1 |
| SHA256: | 2F8EF63E3472C13F62ACF30BCB58B1916EE738447C56766B474F472FE6D10718 |
| SSDEEP: | 98304:NGz8nA7OJVw6o1Xyxu/ukidQ4s5uPzt7vVGEJdjKQvy2rl0WILiONIXK7ByE1UfN:MzoZJhk/u1KxGzt84ZK9WIWONIXKk2IV |
MALICIOUS
Application was dropped or rewritten from another process
- 12306Bypass.exe (PID: 2784)
- 12306Bypass.exe (PID: 1104)
Runs app for hidden code execution
- 12306Bypass.exe (PID: 2784)
SUSPICIOUS
Starts CMD.EXE for commands execution
- 12306Bypass.exe (PID: 2784)
Reads Environment values
- 12306Bypass.exe (PID: 2784)
Reads internet explorer settings
- 12306Bypass.exe (PID: 2784)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3220)
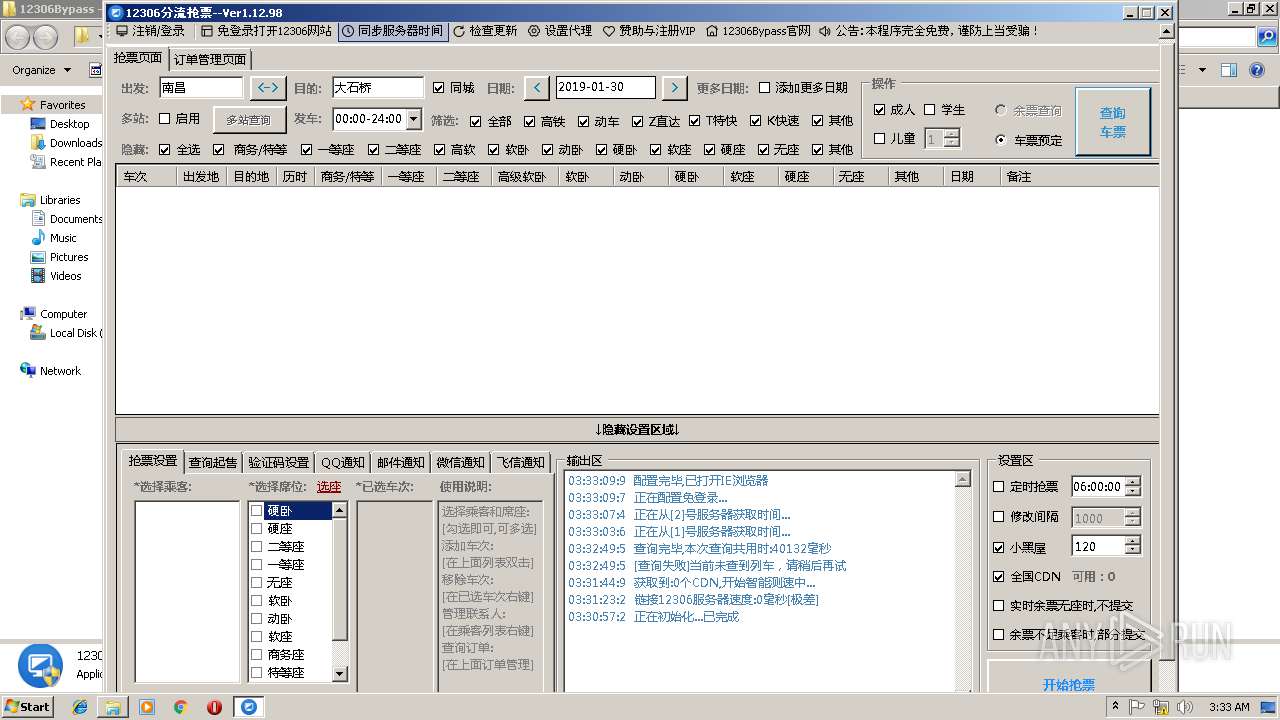
Starts Internet Explorer
- 12306Bypass.exe (PID: 2784)
Changes IE settings (feature browser emulation)
- 12306Bypass.exe (PID: 2784)
Reads Internet Cache Settings
- 12306Bypass.exe (PID: 2784)
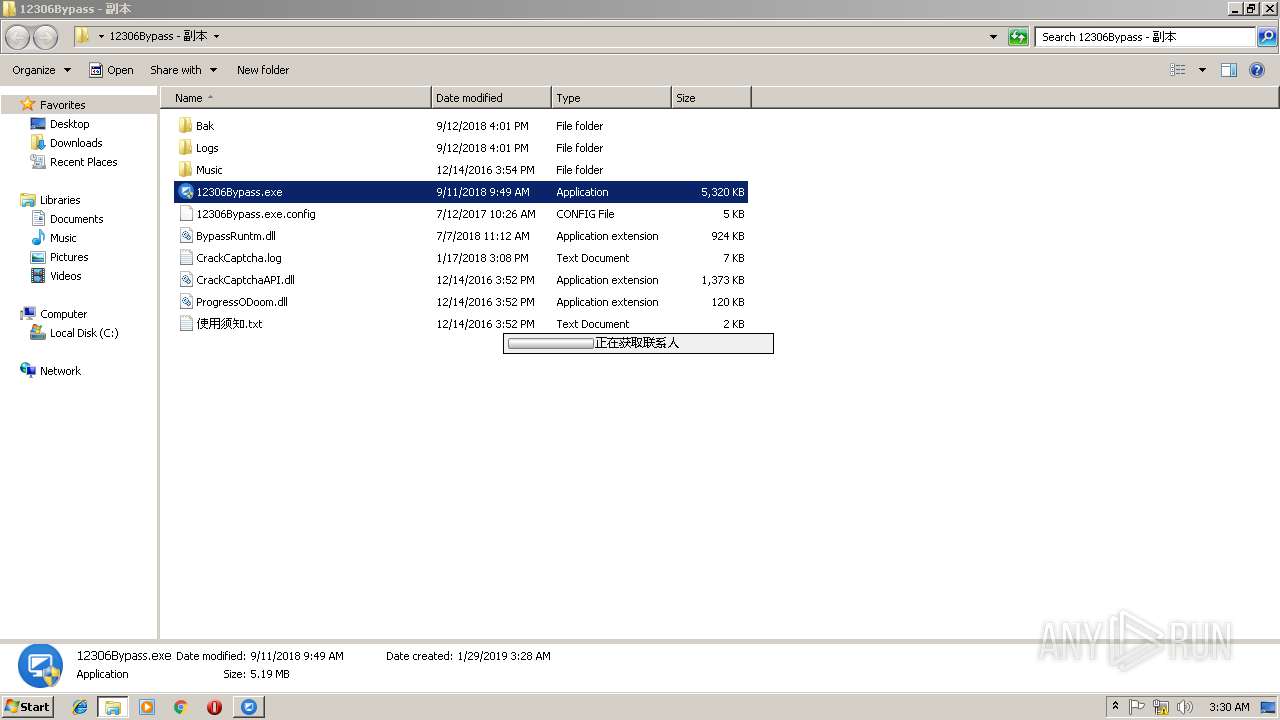
Uses IPCONFIG.EXE to discover IP address
- cmd.exe (PID: 3548)
Creates files in the user directory
- 12306Bypass.exe (PID: 2784)
INFO
Creates files in the user directory
- iexplore.exe (PID: 896)
Changes internet zones settings
- iexplore.exe (PID: 780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
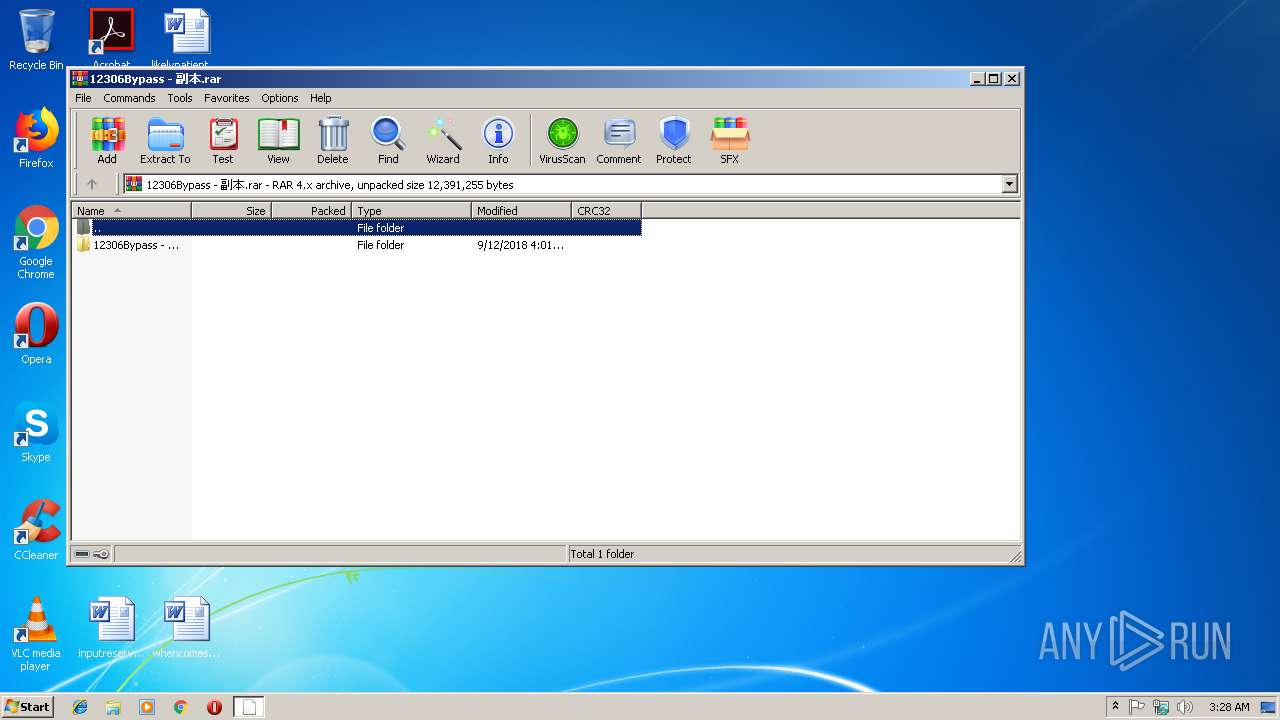
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 2954887 |
|---|---|
| UncompressedSize: | 5447168 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2018:09:11 09:49:06 |
| PackingMethod: | Normal |
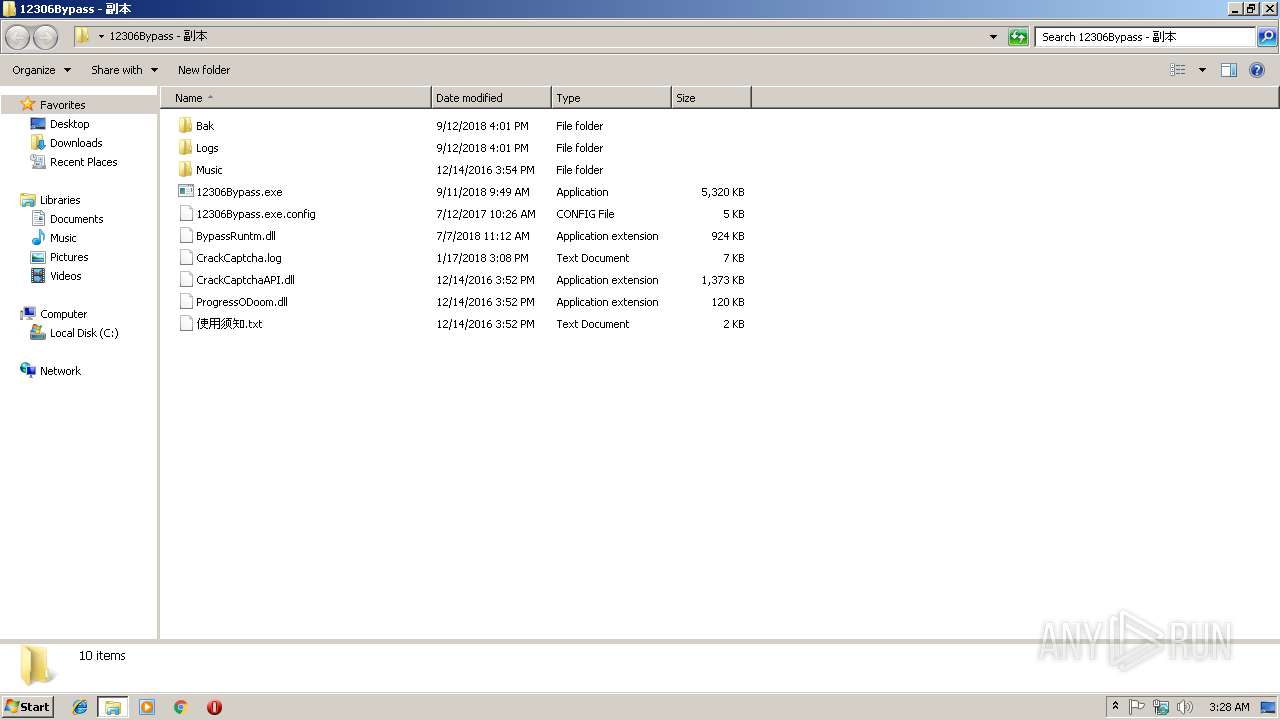
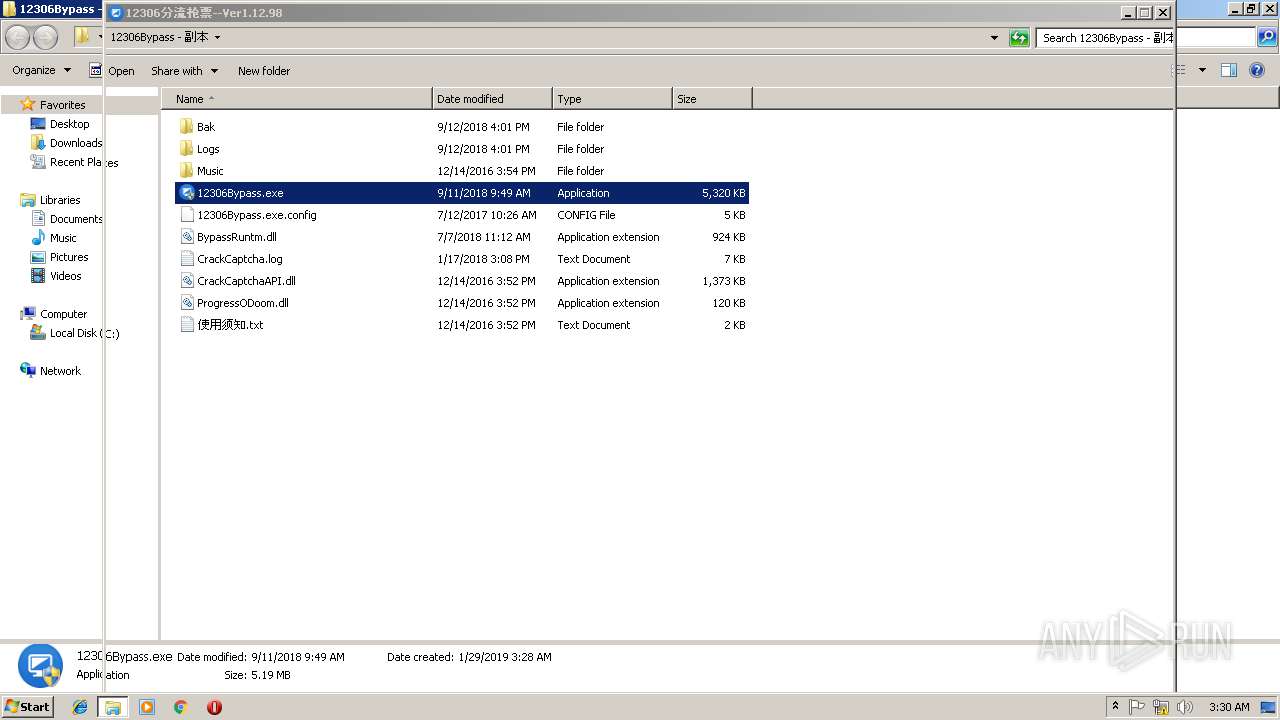
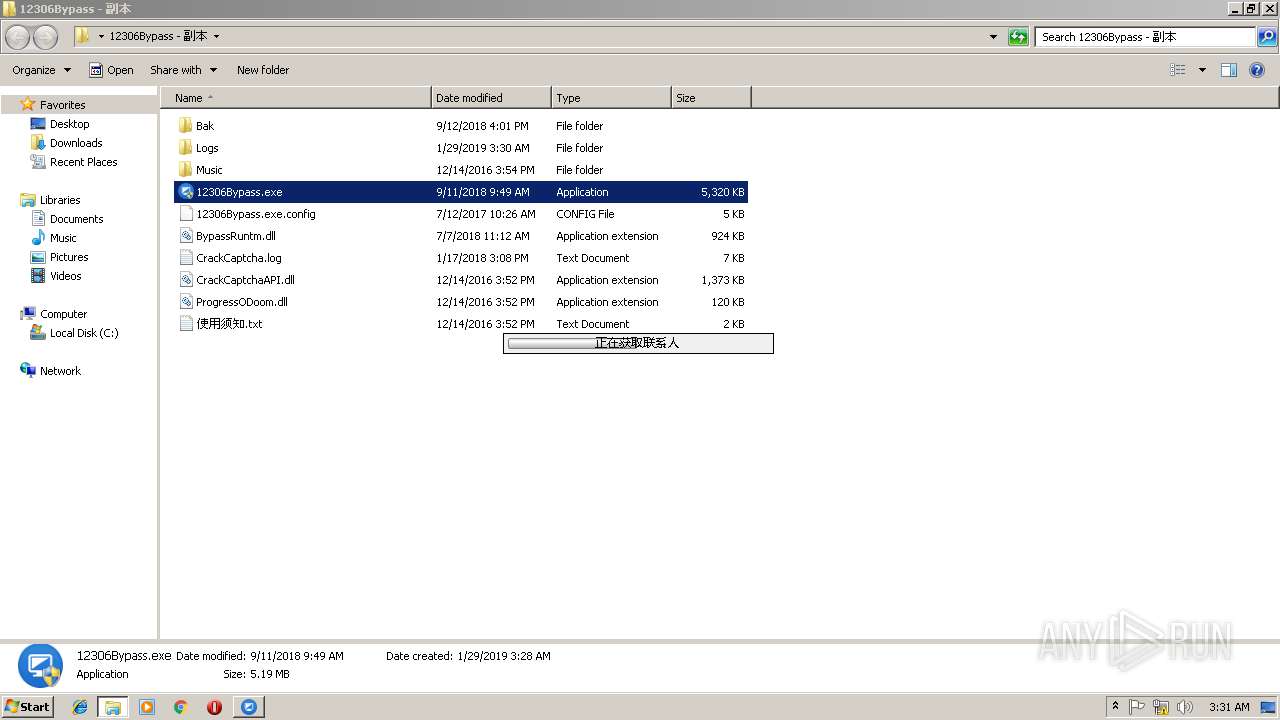
| ArchivedFileName: | 12306Bypass - ????\12306Bypass.exe |
Total processes
47
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
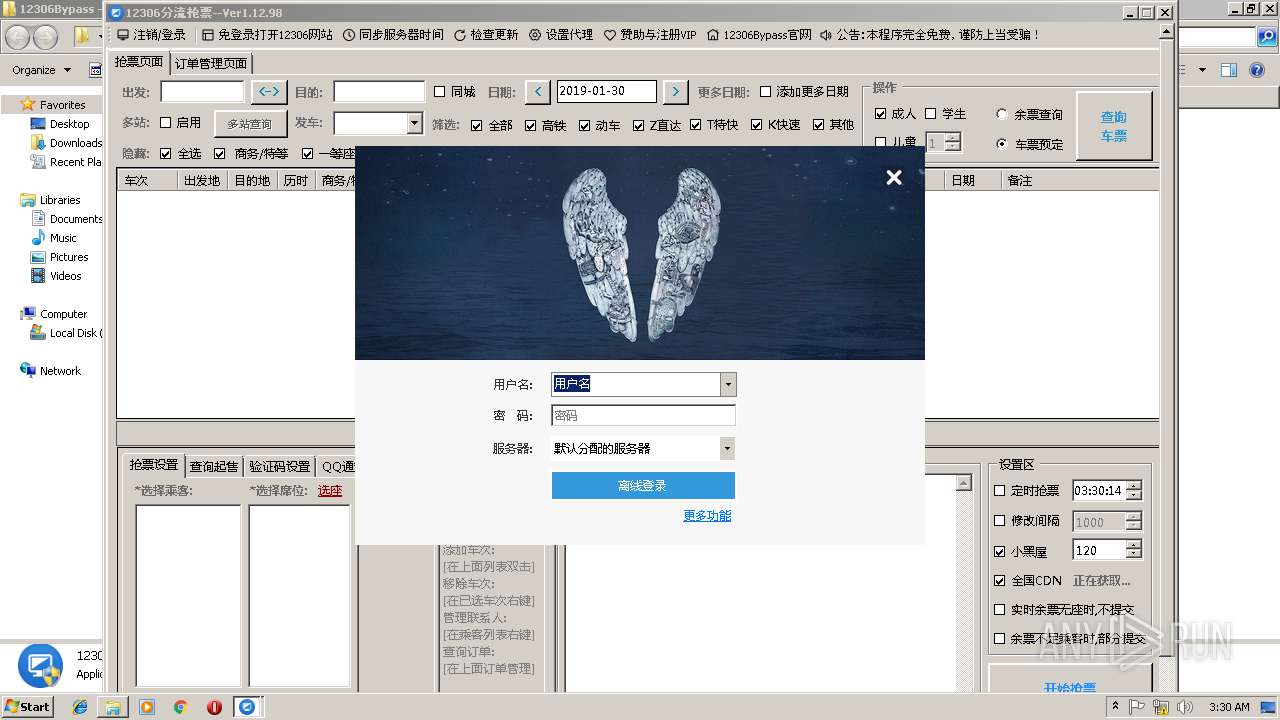
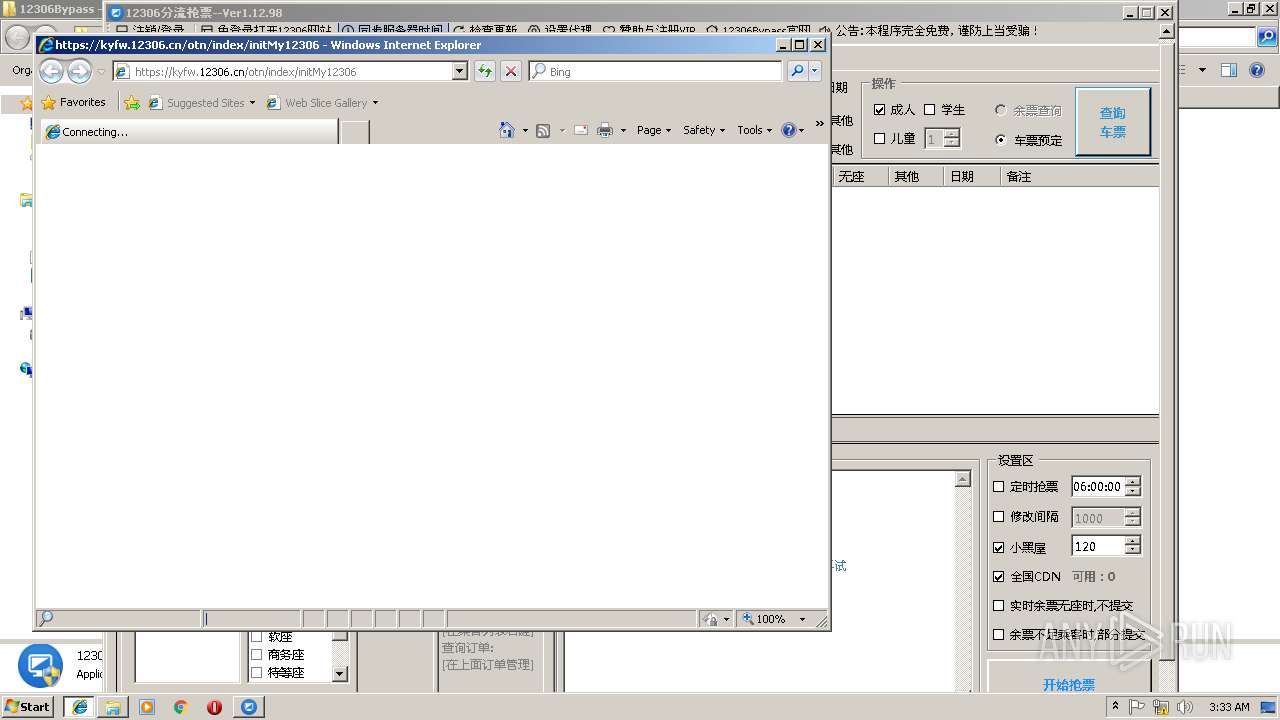
| 780 | "C:\Program Files\Internet Explorer\iexplore.exe" https://kyfw.12306.cn/otn/index/initMy12306 | C:\Program Files\Internet Explorer\iexplore.exe | 12306Bypass.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 896 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:780 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
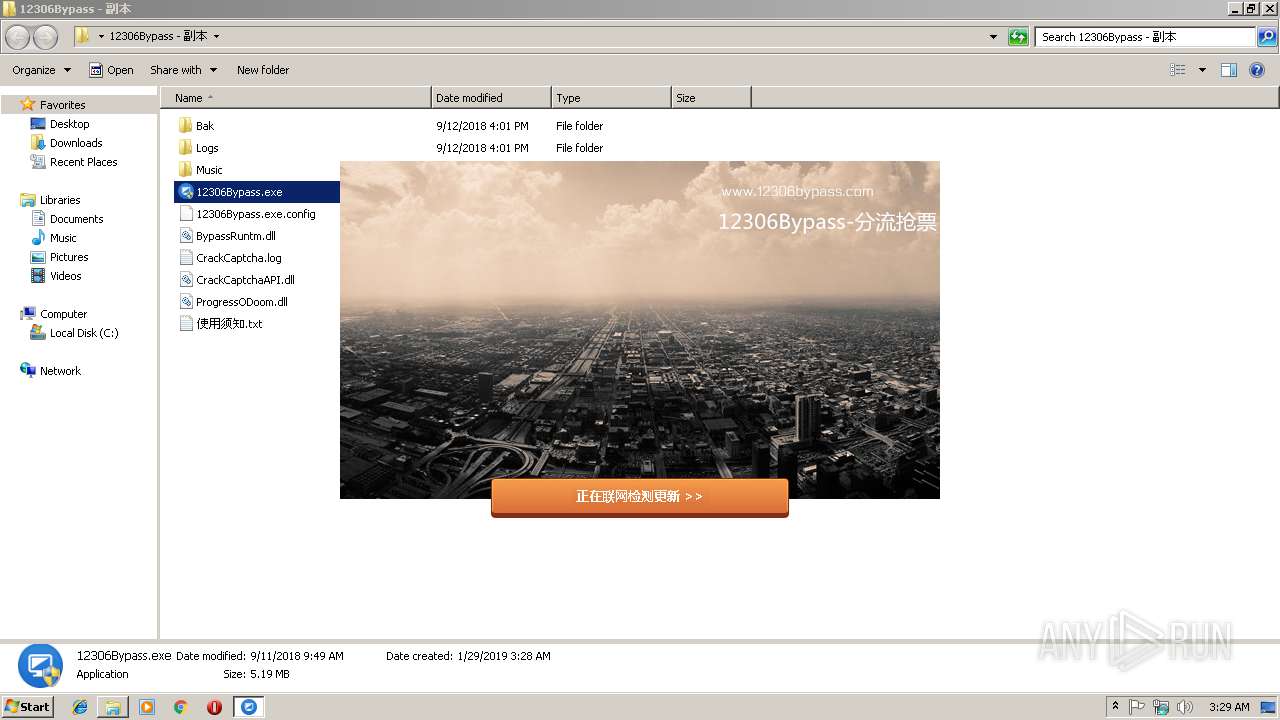
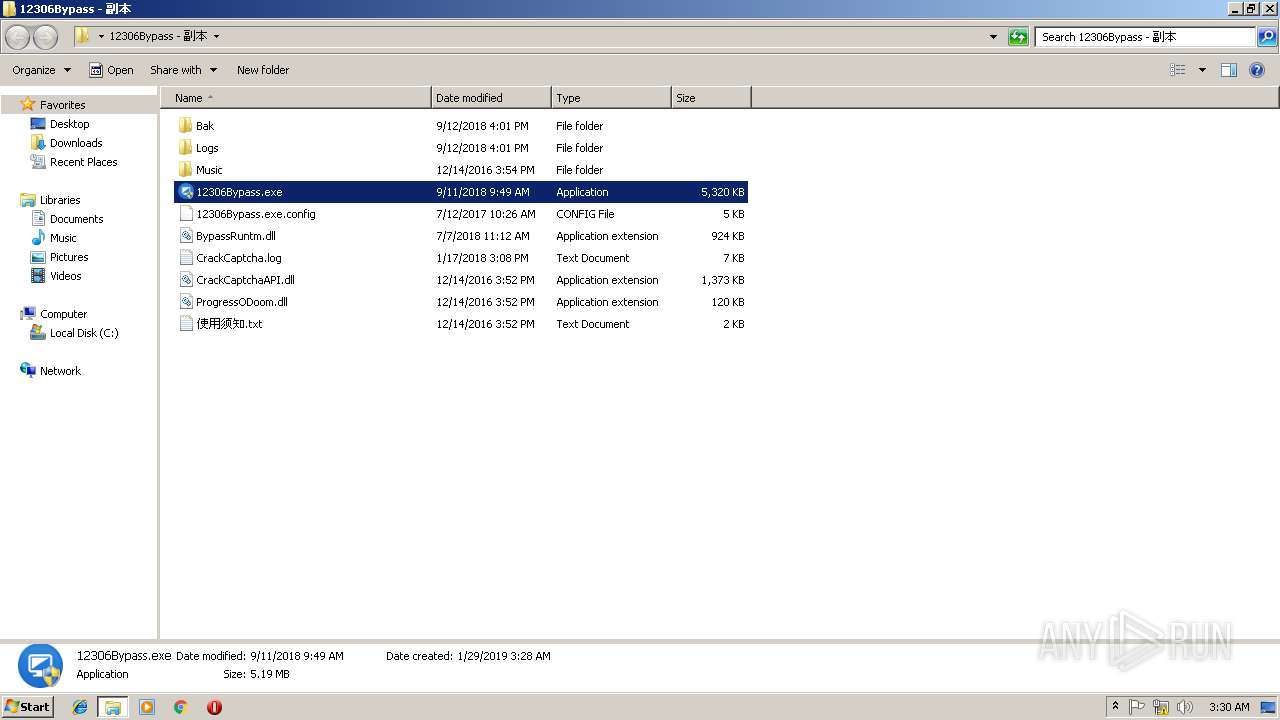
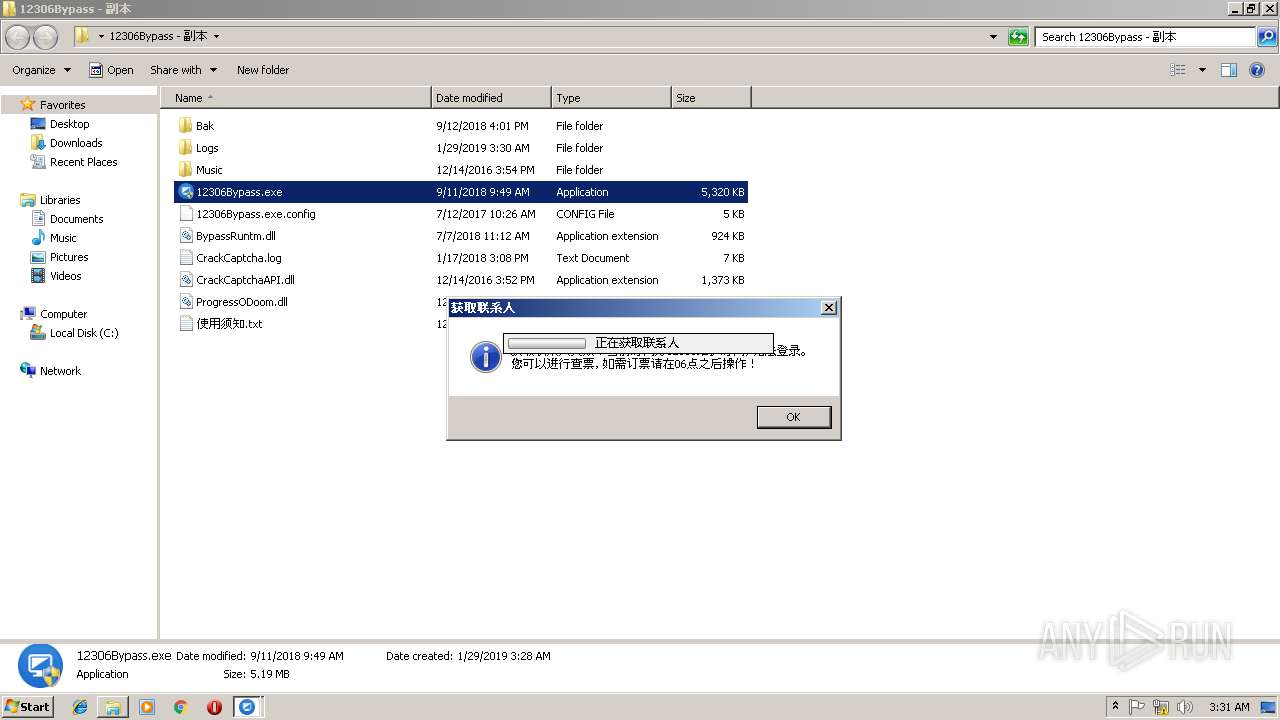
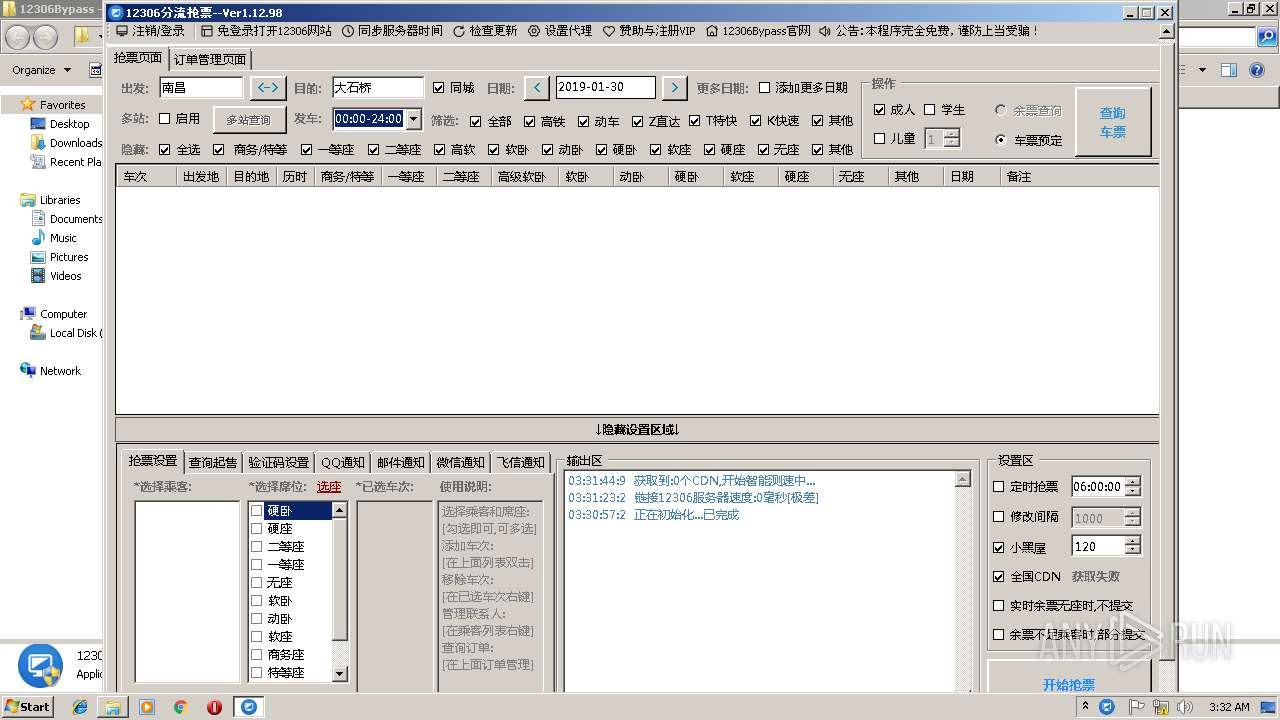
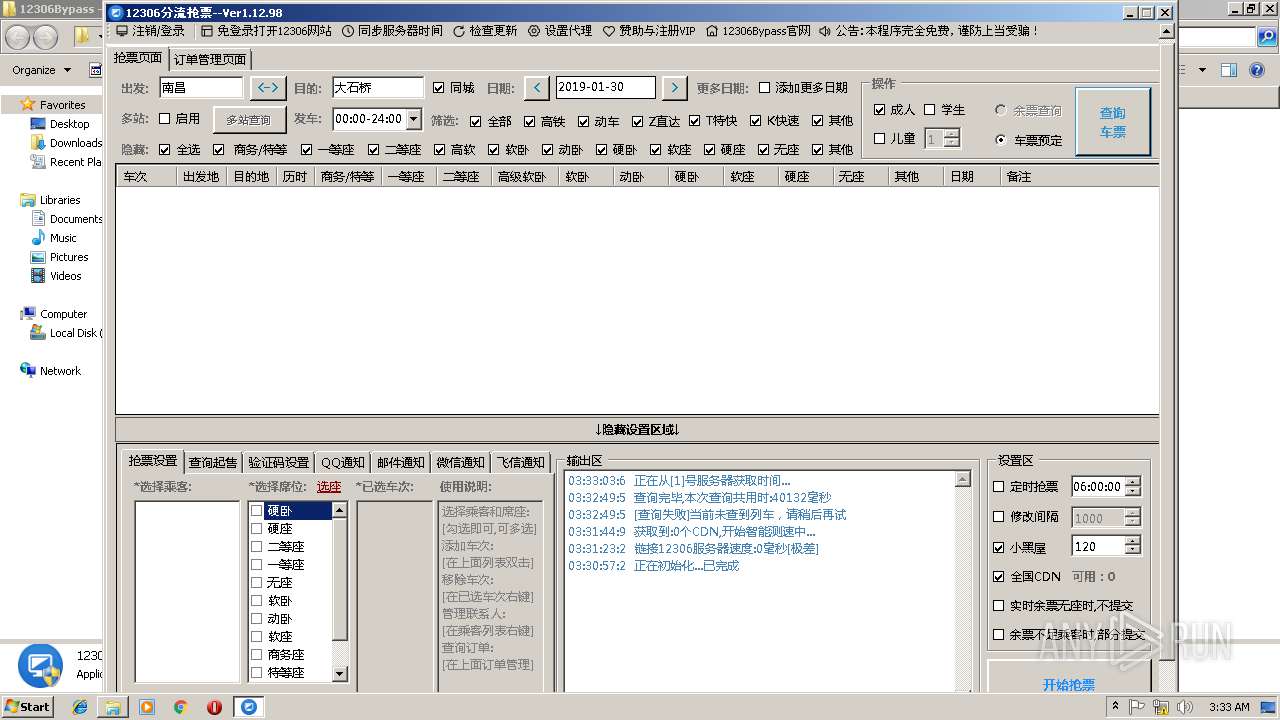
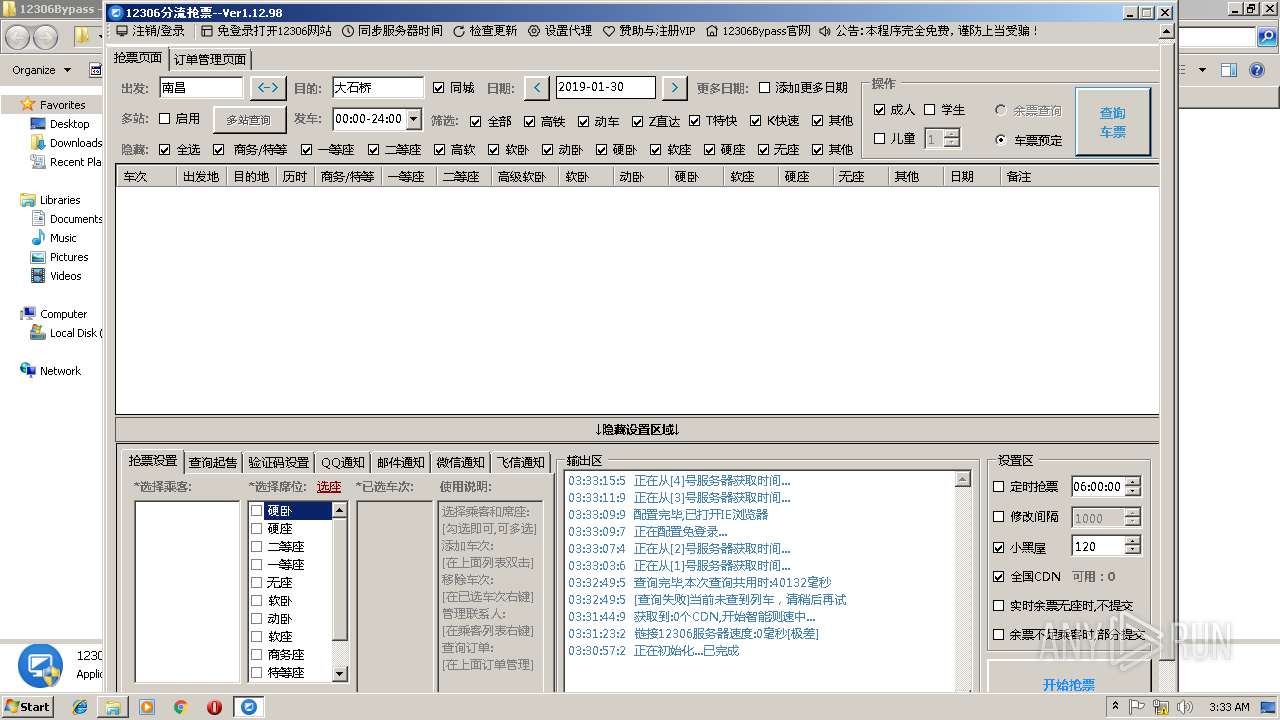
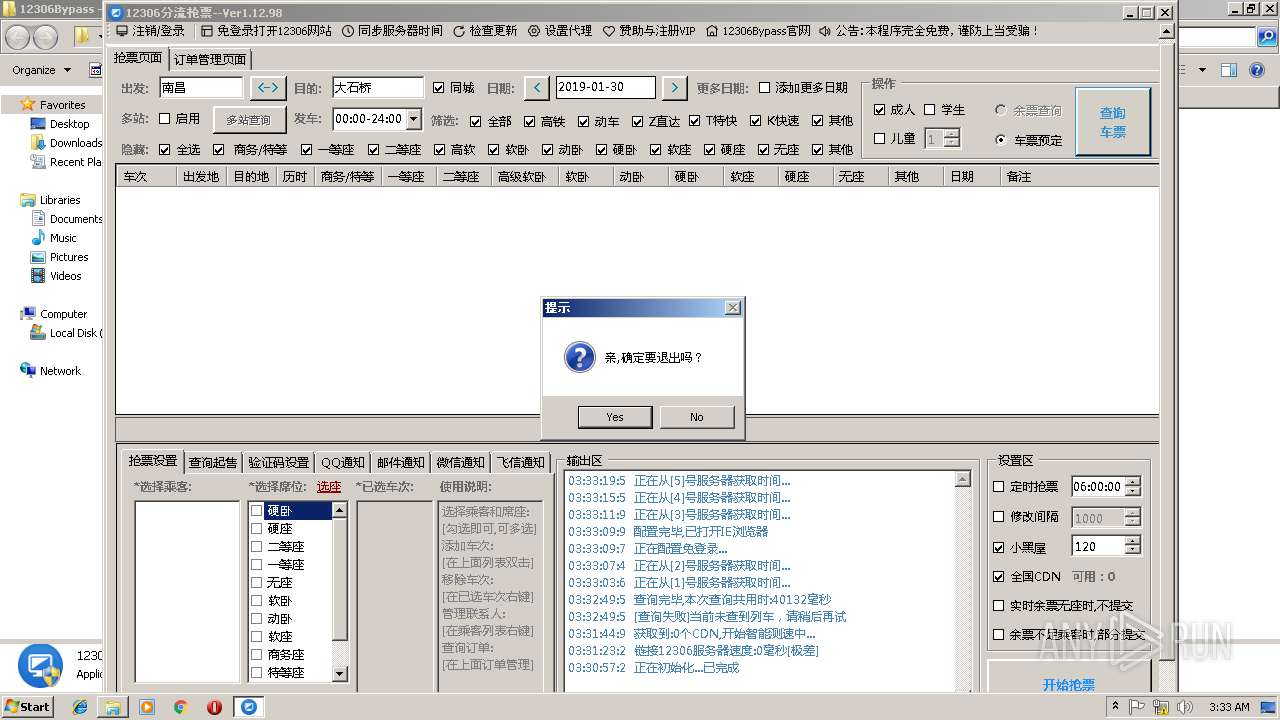
| 1104 | "C:\Users\admin\Desktop\12306Bypass - 副本\12306Bypass.exe" | C:\Users\admin\Desktop\12306Bypass - 副本\12306Bypass.exe | — | explorer.exe | |||||||||||
User: admin Company: Cheney.小风 Integrity Level: MEDIUM Description: 分流抢票 Exit code: 3221226540 Version: 1.1.9.9 Modules
| |||||||||||||||
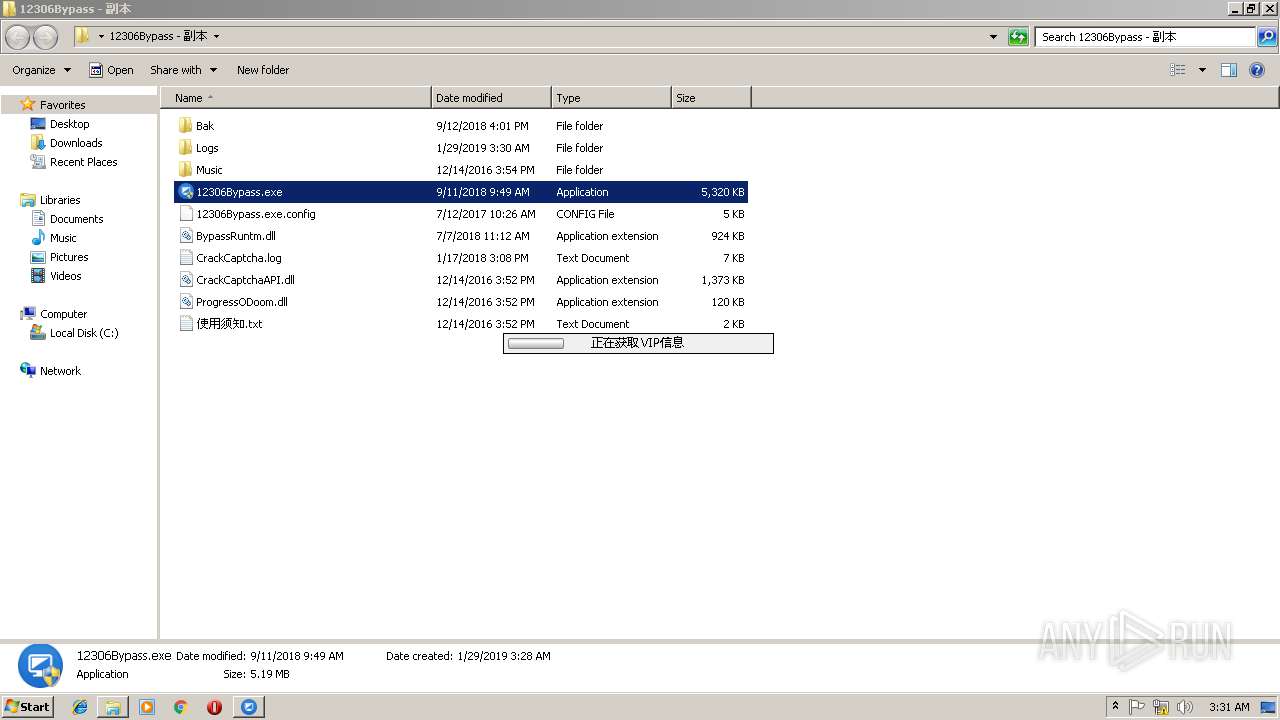
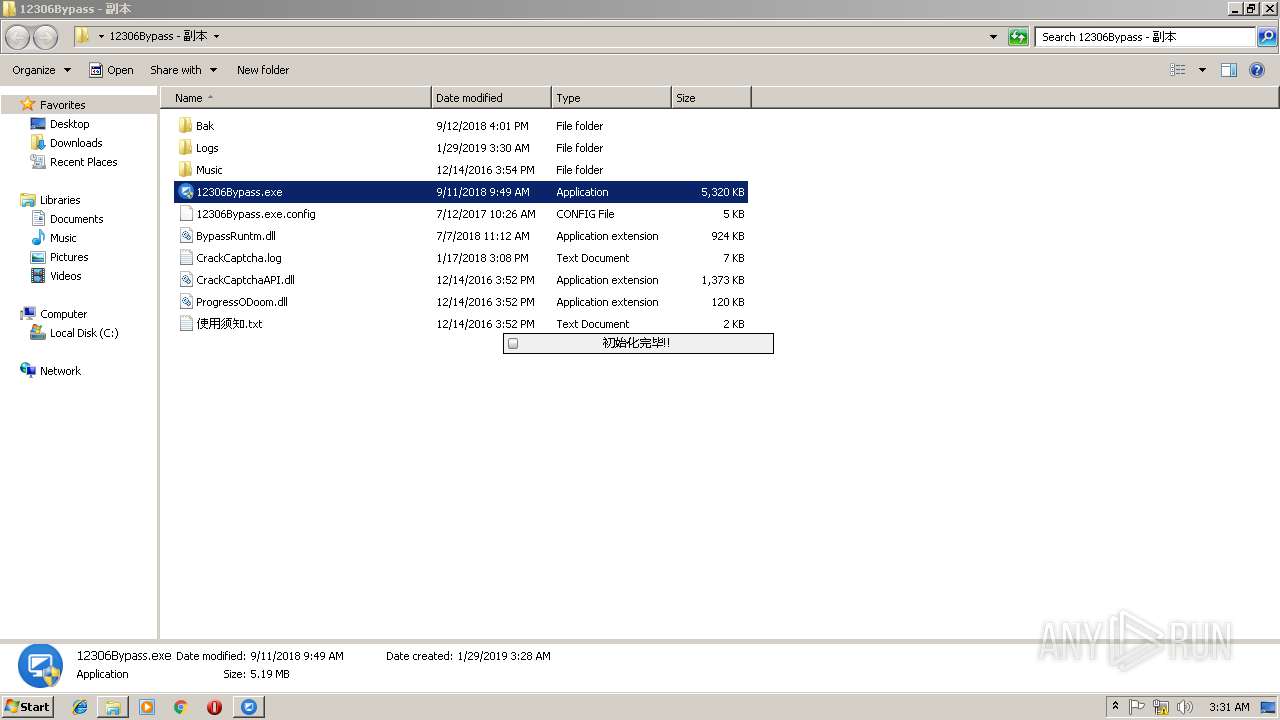
| 2784 | "C:\Users\admin\Desktop\12306Bypass - 副本\12306Bypass.exe" | C:\Users\admin\Desktop\12306Bypass - 副本\12306Bypass.exe | explorer.exe | ||||||||||||
User: admin Company: Cheney.小风 Integrity Level: HIGH Description: 分流抢票 Exit code: 0 Version: 1.1.9.9 Modules
| |||||||||||||||
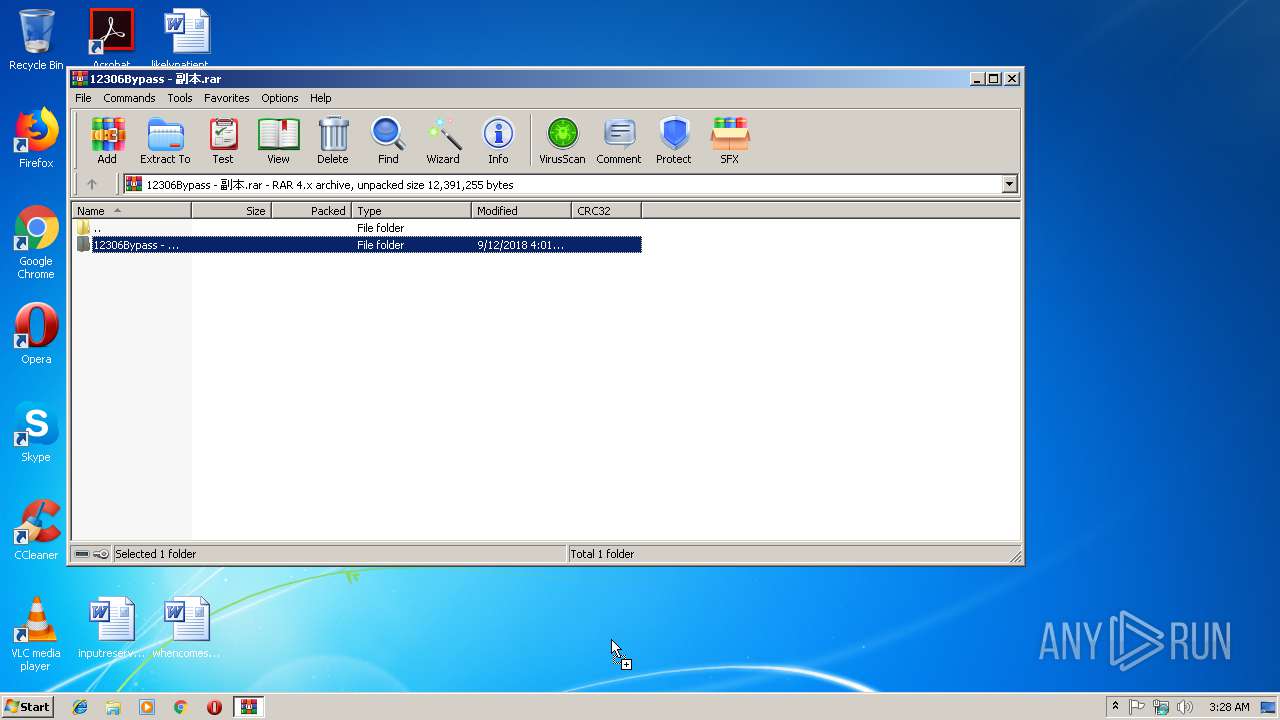
| 3220 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\12306Bypass - 副本.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3548 | "cmd.exe" | C:\Windows\system32\cmd.exe | — | 12306Bypass.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4060 | ipconfig /flushdns | C:\Windows\system32\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
902
Read events
819
Write events
82
Delete events
1
Modification events
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\12306Bypass - 副本.rar | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
2
Suspicious files
2
Text files
22
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
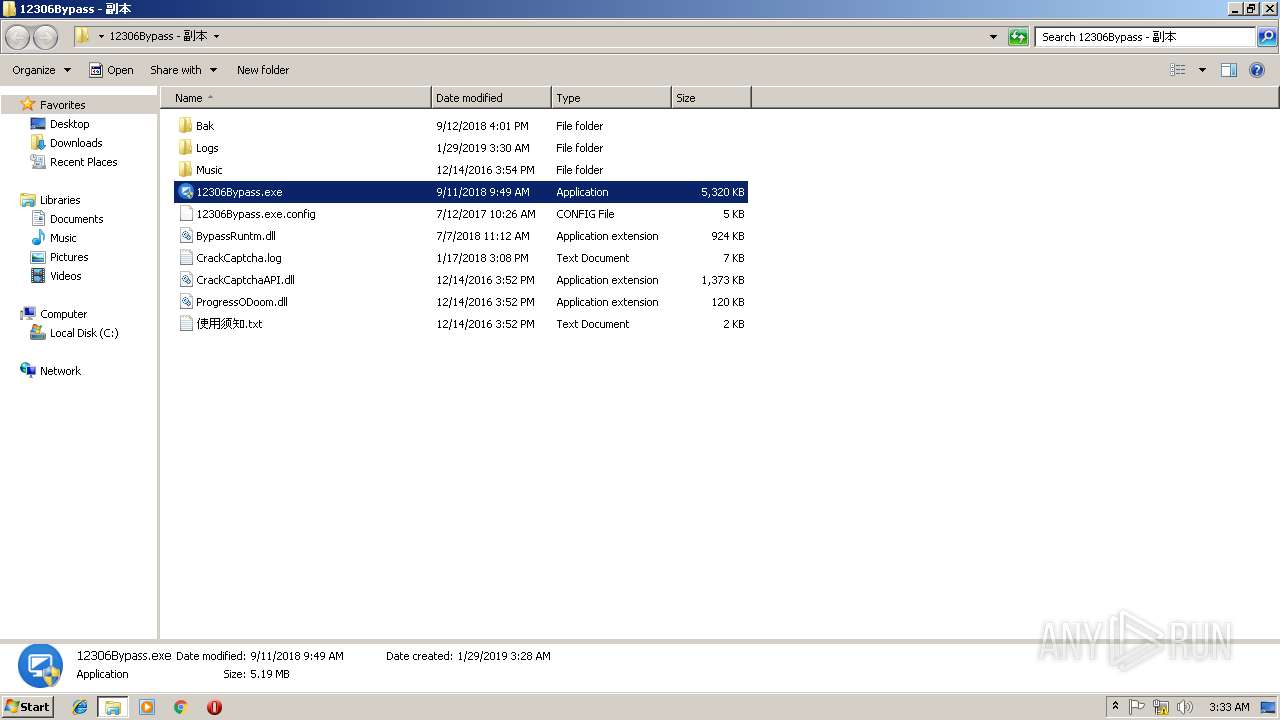
| 3220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3220.2221\12306Bypass - 副本\BypassRuntm.dll | — | |
MD5:— | SHA256:— | |||
| 3220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3220.2221\12306Bypass - 副本\CrackCaptcha.log | — | |
MD5:— | SHA256:— | |||
| 3220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3220.2221\12306Bypass - 副本\CrackCaptchaAPI.dll | — | |
MD5:— | SHA256:— | |||
| 3220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3220.2221\12306Bypass - 副本\Logs\2016-12-26.txt | — | |
MD5:— | SHA256:— | |||
| 3220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3220.2221\12306Bypass - 副本\Logs\2016-12-27.txt | — | |
MD5:— | SHA256:— | |||
| 3220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3220.2221\12306Bypass - 副本\Logs\2016-12-29.txt | — | |
MD5:— | SHA256:— | |||
| 3220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3220.2221\12306Bypass - 副本\Logs\2016-12-30.txt | — | |
MD5:— | SHA256:— | |||
| 3220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3220.2221\12306Bypass - 副本\Logs\2017-01-04.txt | — | |
MD5:— | SHA256:— | |||
| 3220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3220.2221\12306Bypass - 副本\Logs\2017-01-09.txt | — | |
MD5:— | SHA256:— | |||
| 3220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3220.2221\12306Bypass - 副本\Logs\2017-01-11.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
30
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2784 | 12306Bypass.exe | GET | — | 106.15.25.58:80 | http://www.12306bypass.com/js/station_name.js | CN | — | — | unknown |
2784 | 12306Bypass.exe | GET | — | 106.15.25.58:80 | http://www.12306bypass.com/js/tcStation.js | CN | — | — | unknown |
2784 | 12306Bypass.exe | POST | — | 106.15.25.58:80 | http://www.12306bypass.com/GetList.ashx | CN | — | — | unknown |
2784 | 12306Bypass.exe | POST | — | 106.15.25.58:80 | http://www.12306bypass.com/General.ashx | CN | — | — | unknown |
2784 | 12306Bypass.exe | POST | — | 106.15.25.58:80 | http://www.12306bypass.com/GetList.ashx | CN | — | — | unknown |
2784 | 12306Bypass.exe | POST | — | 106.15.25.58:80 | http://www.12306bypass.com/General.ashx | CN | — | — | unknown |
2784 | 12306Bypass.exe | POST | — | 106.15.25.58:80 | http://www.12306bypass.com/GetList.ashx | CN | — | — | unknown |
2784 | 12306Bypass.exe | POST | — | 106.15.25.58:80 | http://www.12306bypass.com/GetList.ashx | CN | — | — | unknown |
2784 | 12306Bypass.exe | POST | — | 106.15.25.58:80 | http://www.12306bypass.com/Cdn.ashx | CN | — | — | unknown |
780 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2784 | 12306Bypass.exe | 106.15.25.58:80 | www.12306bypass.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
896 | iexplore.exe | 58.216.109.187:443 | kyfw.12306.cn | AS Number for CHINANET jiangsu province backbone | CN | unknown |
2784 | 12306Bypass.exe | 203.107.6.88:123 | ntp2.aliyun.com | — | CN | unknown |
780 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2784 | 12306Bypass.exe | 72.52.4.119:123 | ntp3.aliyun.co | Akamai Technologies, Inc. | US | whitelisted |
2784 | 12306Bypass.exe | 120.25.115.20:123 | ntp1.aliyun.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2784 | 12306Bypass.exe | 58.216.109.187:443 | kyfw.12306.cn | AS Number for CHINANET jiangsu province backbone | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.12306bypass.com |
| unknown |
kyfw.12306.cn |
| unknown |
ntp1.aliyun.com |
| unknown |
ntp2.aliyun.com |
| unknown |
www.bing.com |
| whitelisted |
ntp3.aliyun.co |
| malicious |
ntp4.aliyun.com |
| unknown |
ntp5.aliyun.com |
| unknown |