| download: | /pankoza2-pl/malwaredatabase-old/raw/refs/heads/main/DeathInstaller.zip |
| Full analysis: | https://app.any.run/tasks/71ceee34-1f57-45f9-8513-b5609876cee2 |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 02:40:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
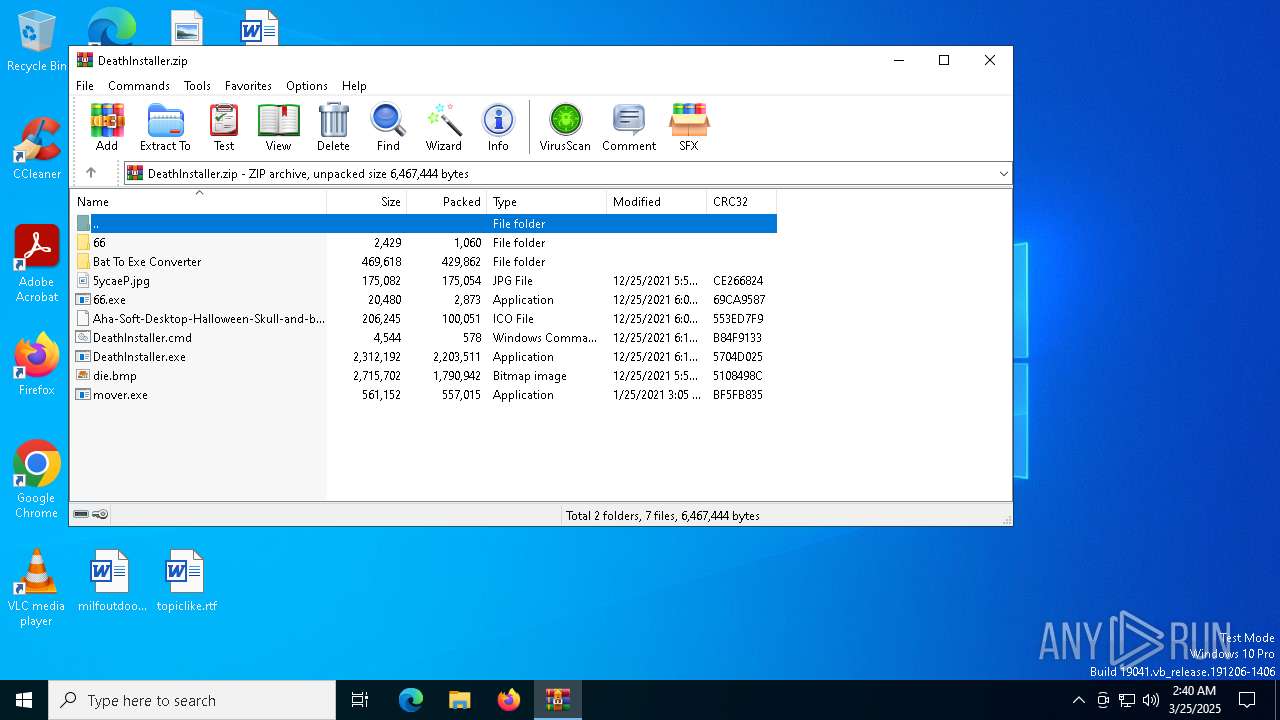
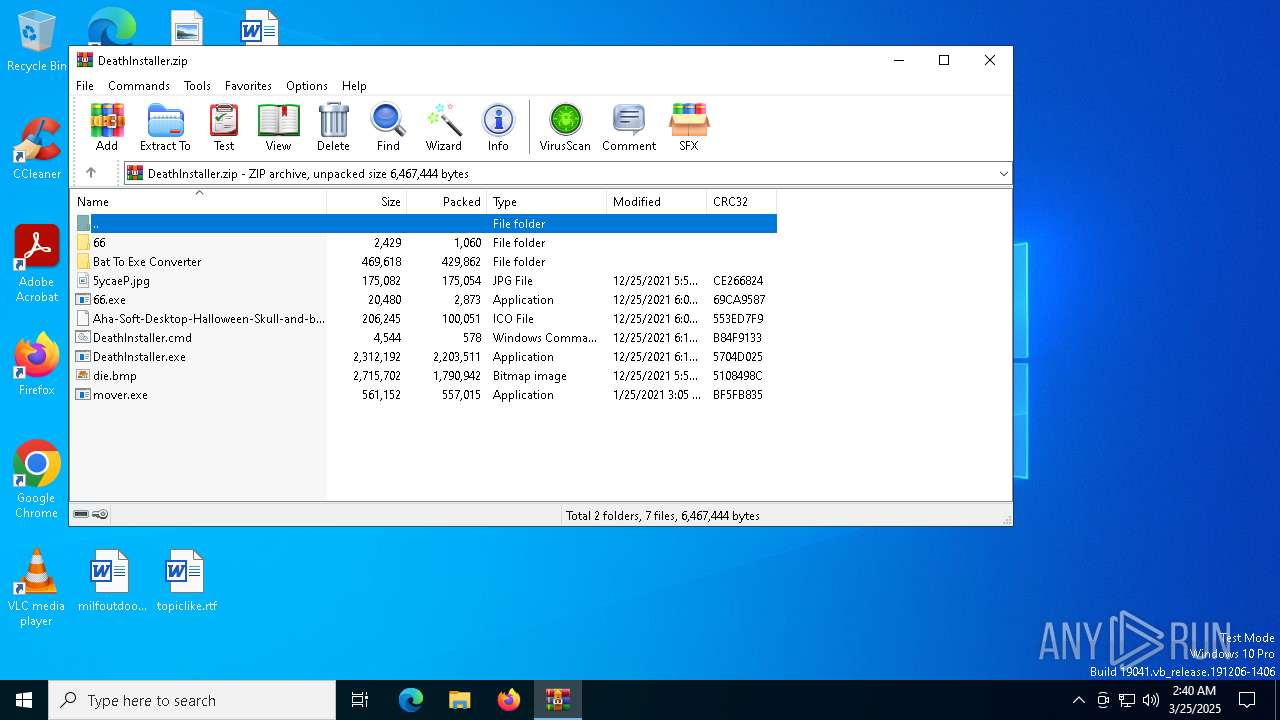
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 0D77C116F8BF43DC9D5EAFE2F755F9EC |
| SHA1: | 72E873E06ECE37B23D04F77C4317F978A391BC89 |
| SHA256: | 2F8D95F63F3E53E15F6BADC567B13BBB664C135BF749C56CECE346B66E254E52 |
| SSDEEP: | 98304:eJ4Qm5JSqebYaDR/ei+yhevAO+FFYiaTyEiqxGly4N+Z+81QS9mfjw1gHu/WhExE:eJbDh6P3kccXvRQAh |
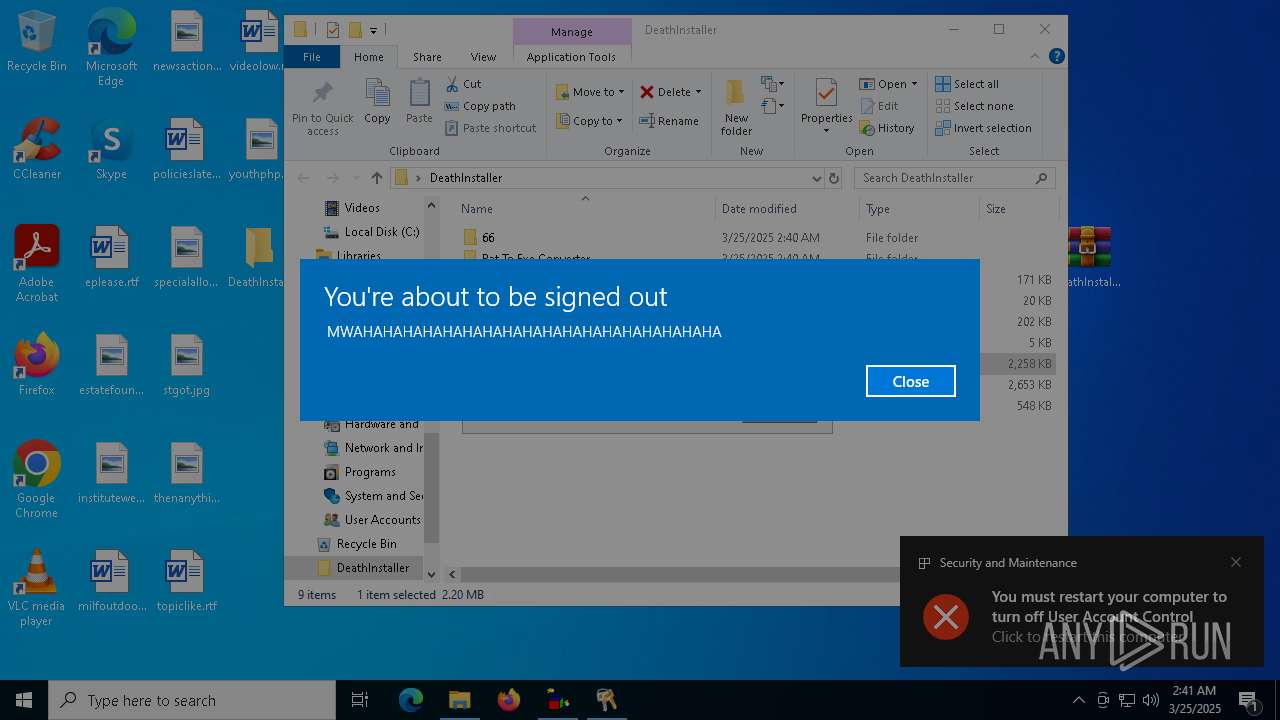
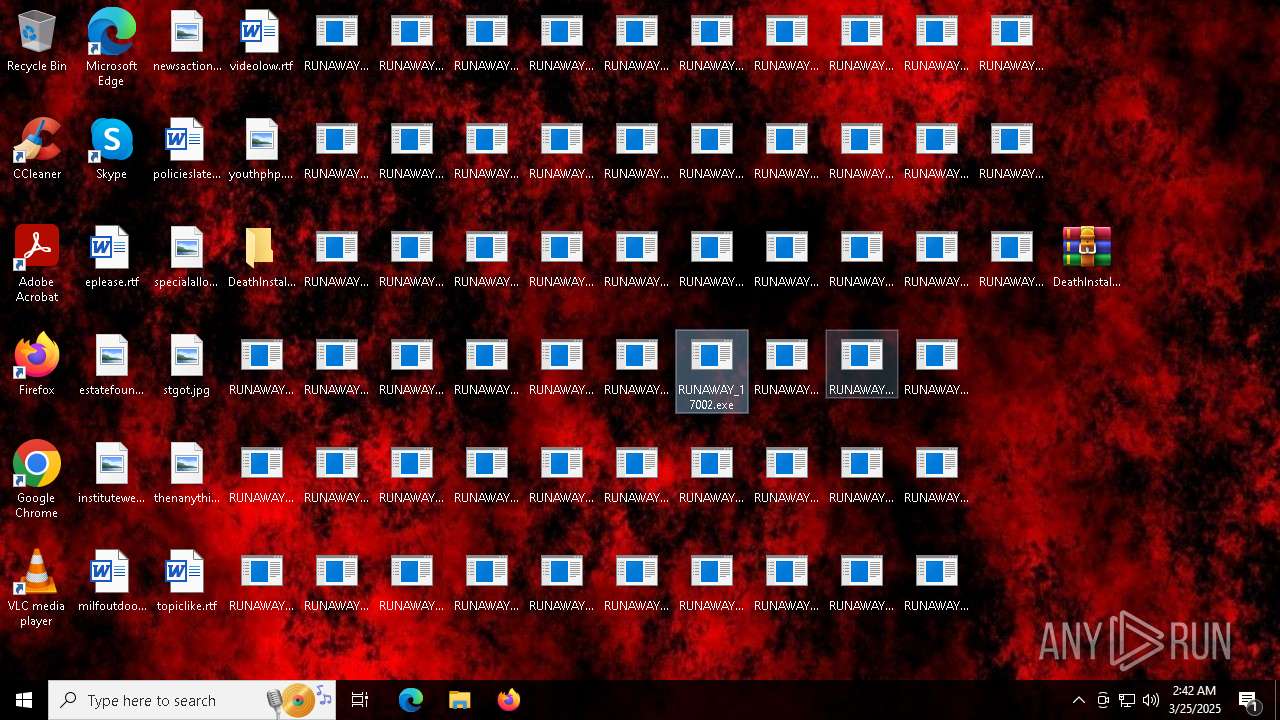
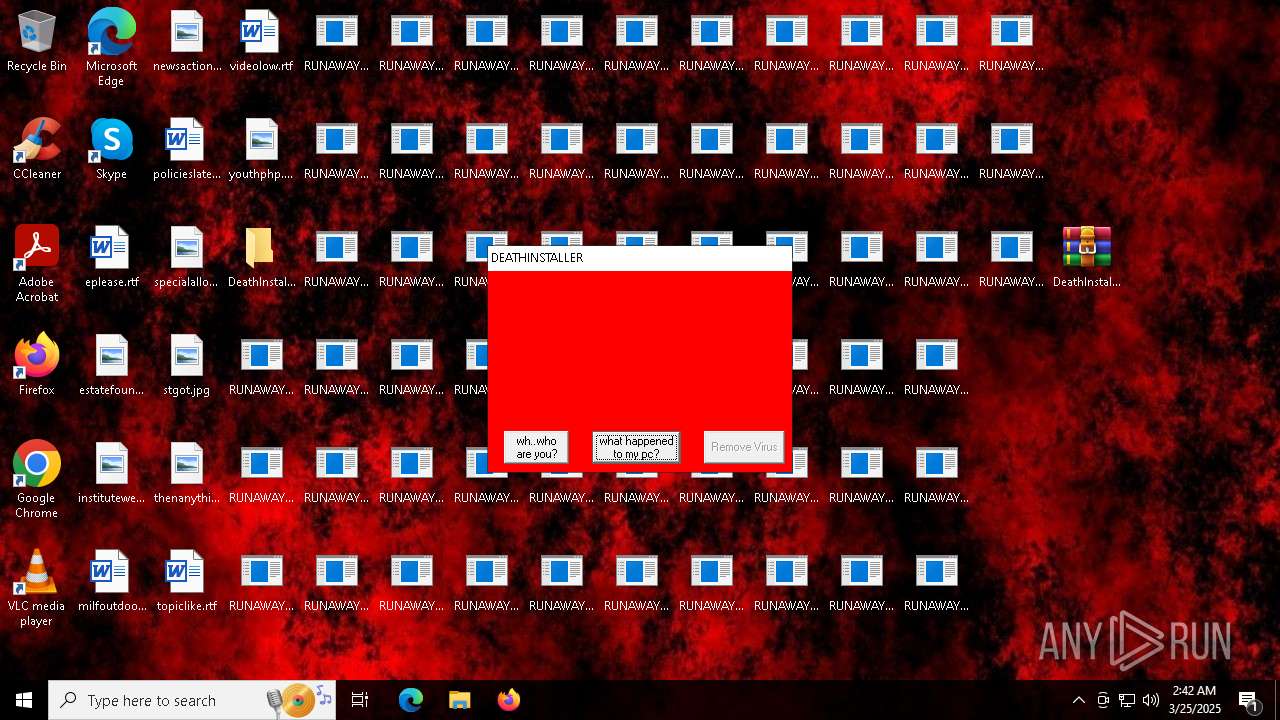
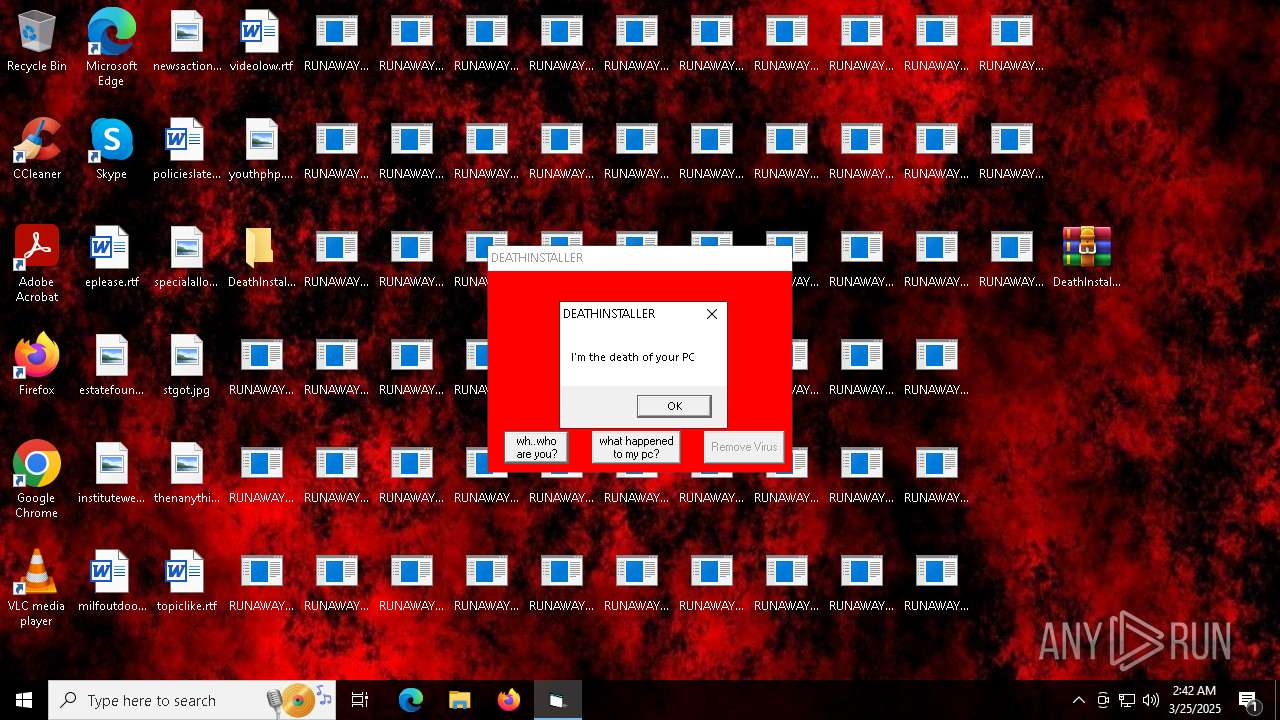
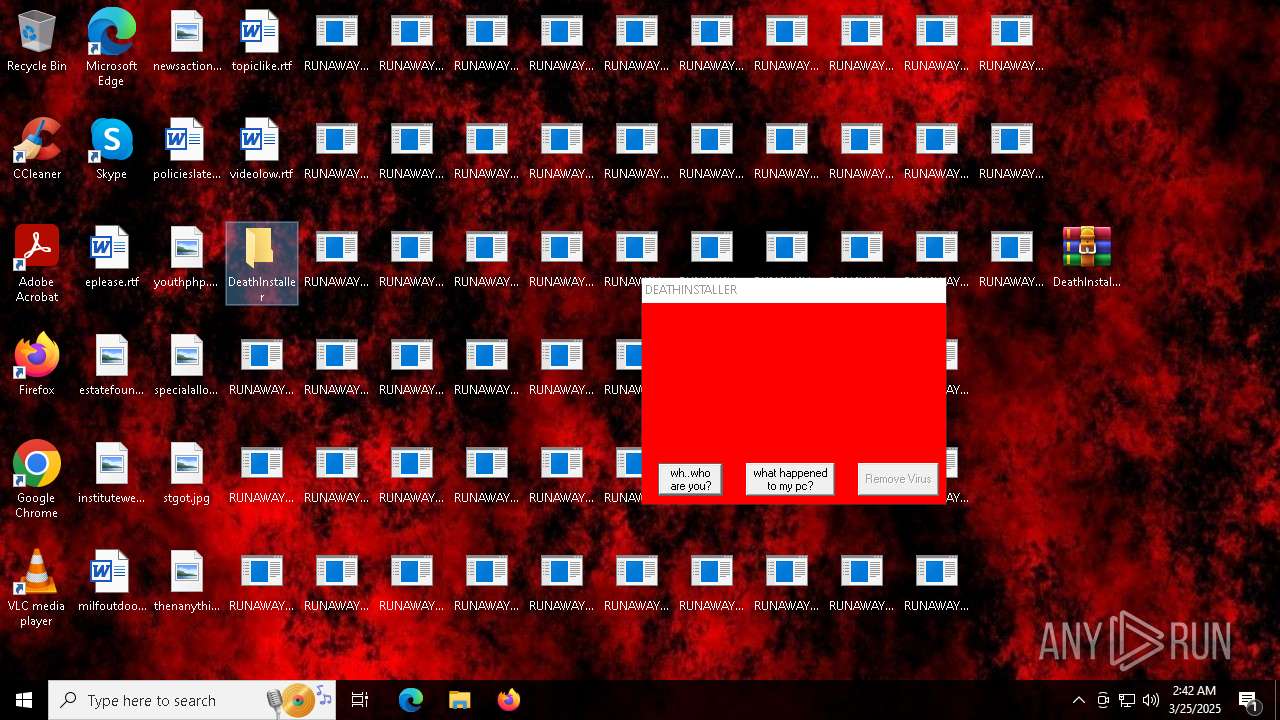
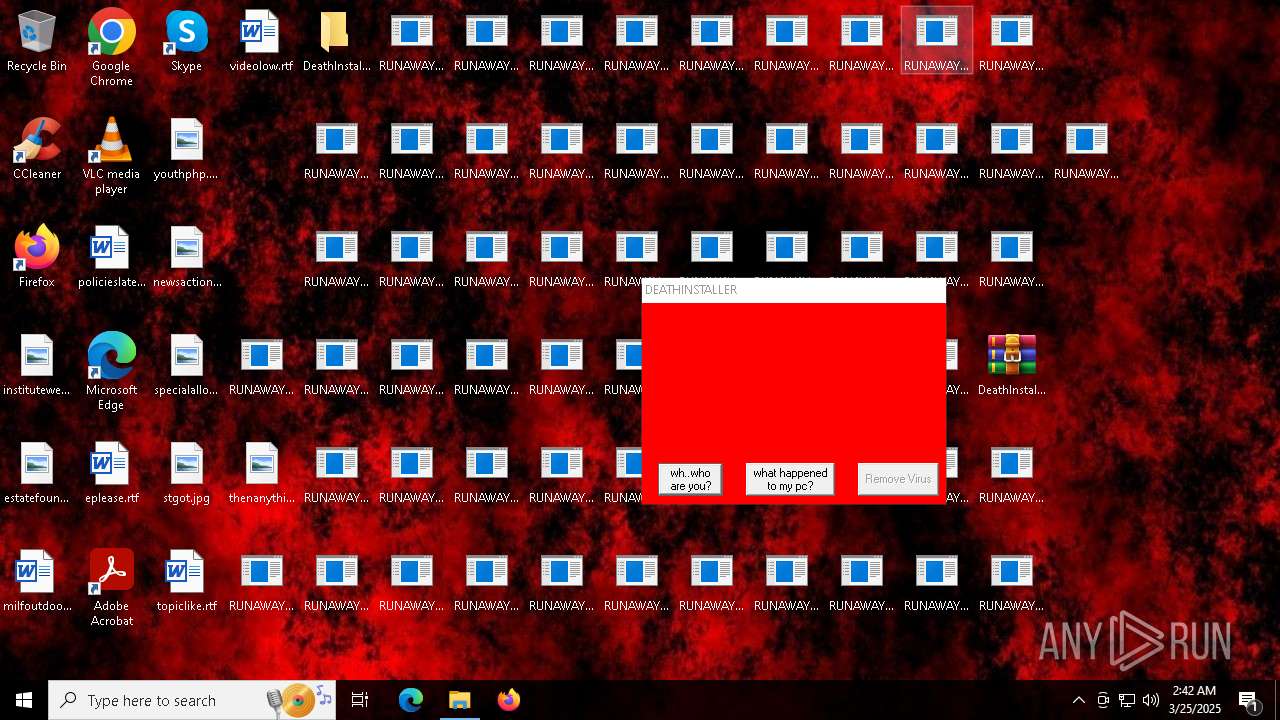
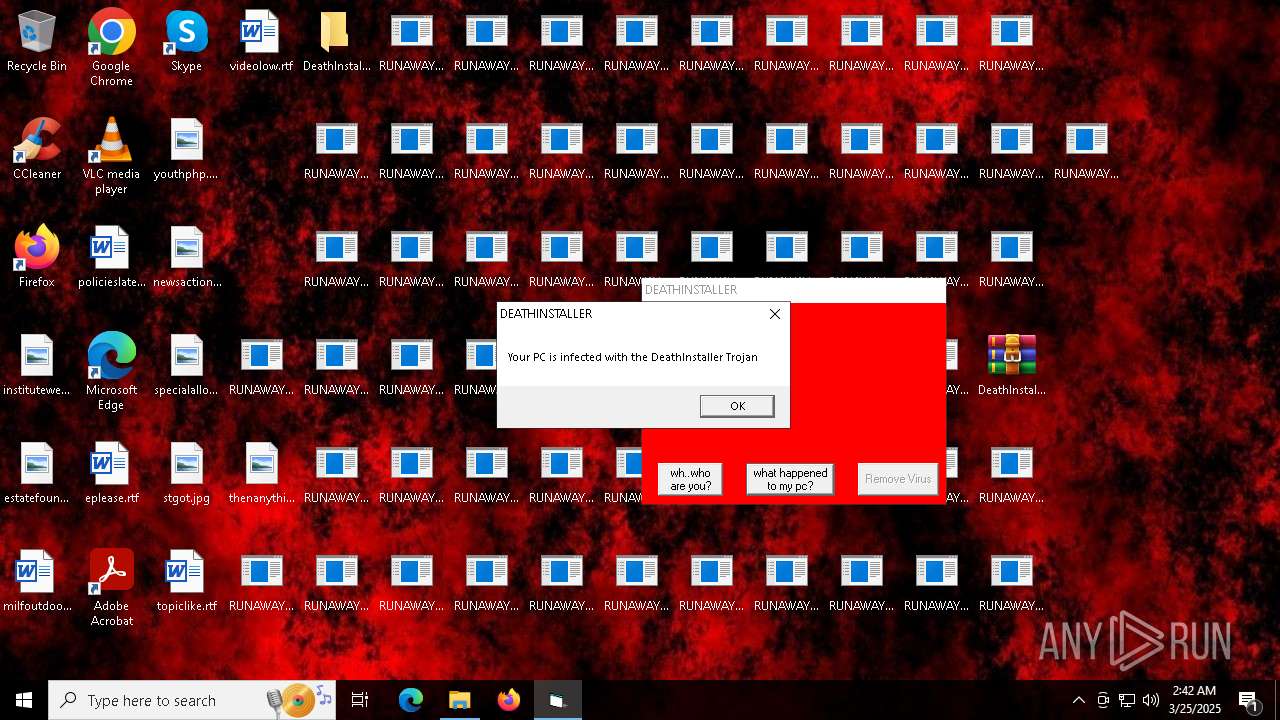
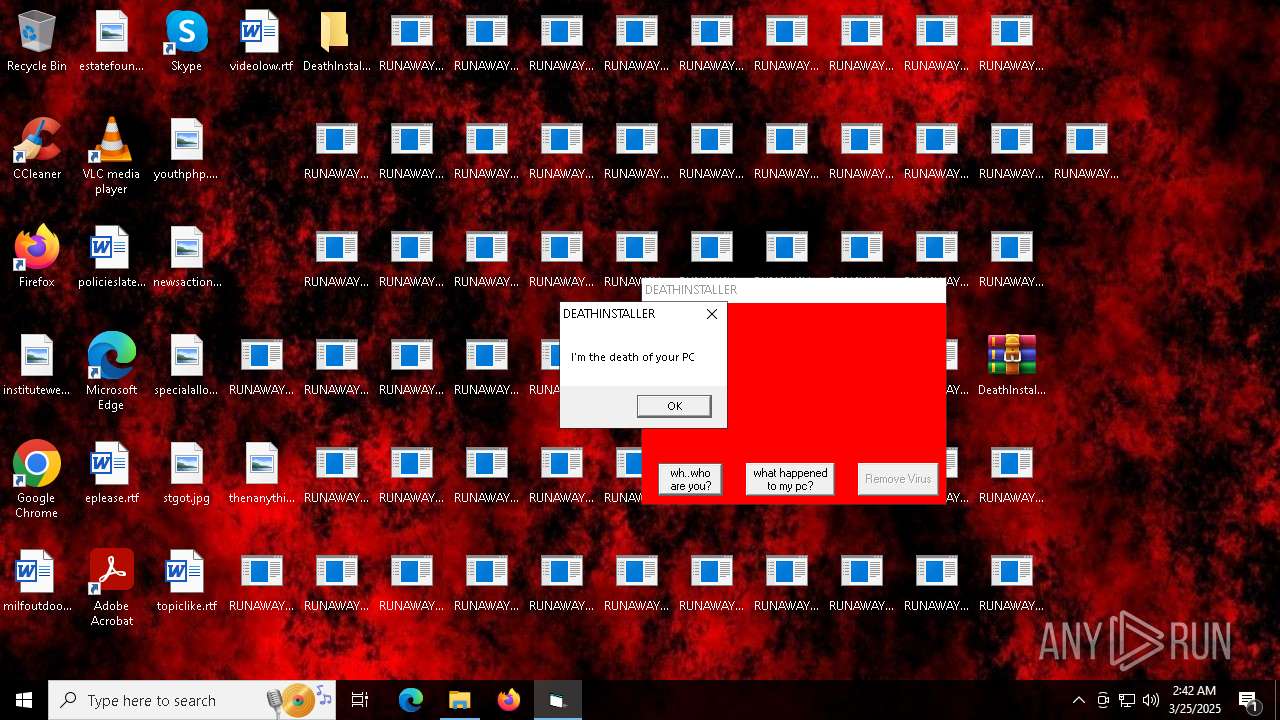
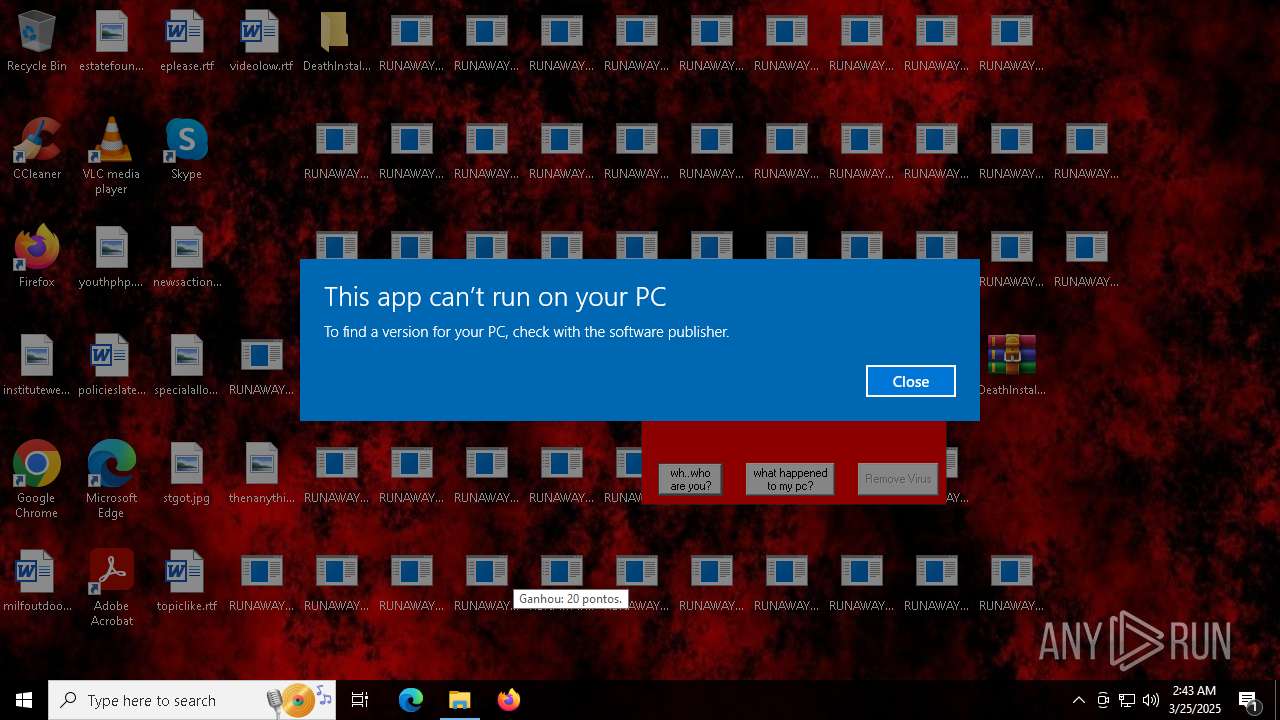
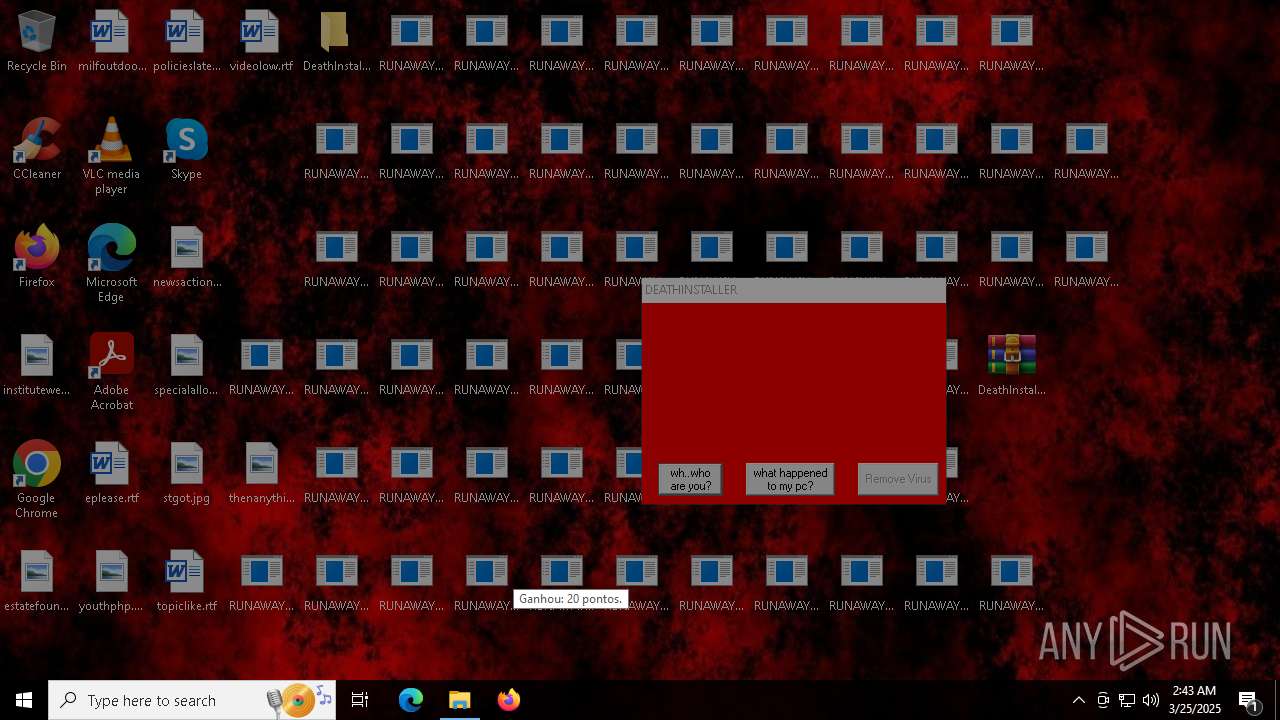
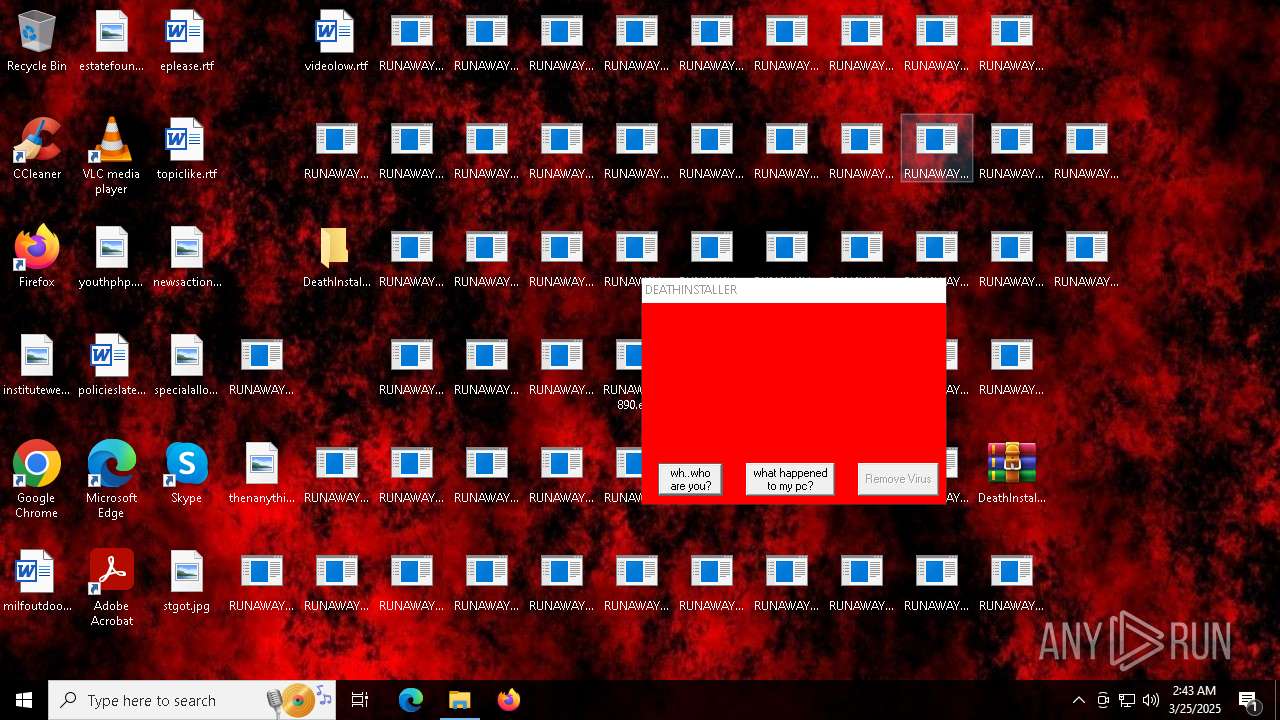
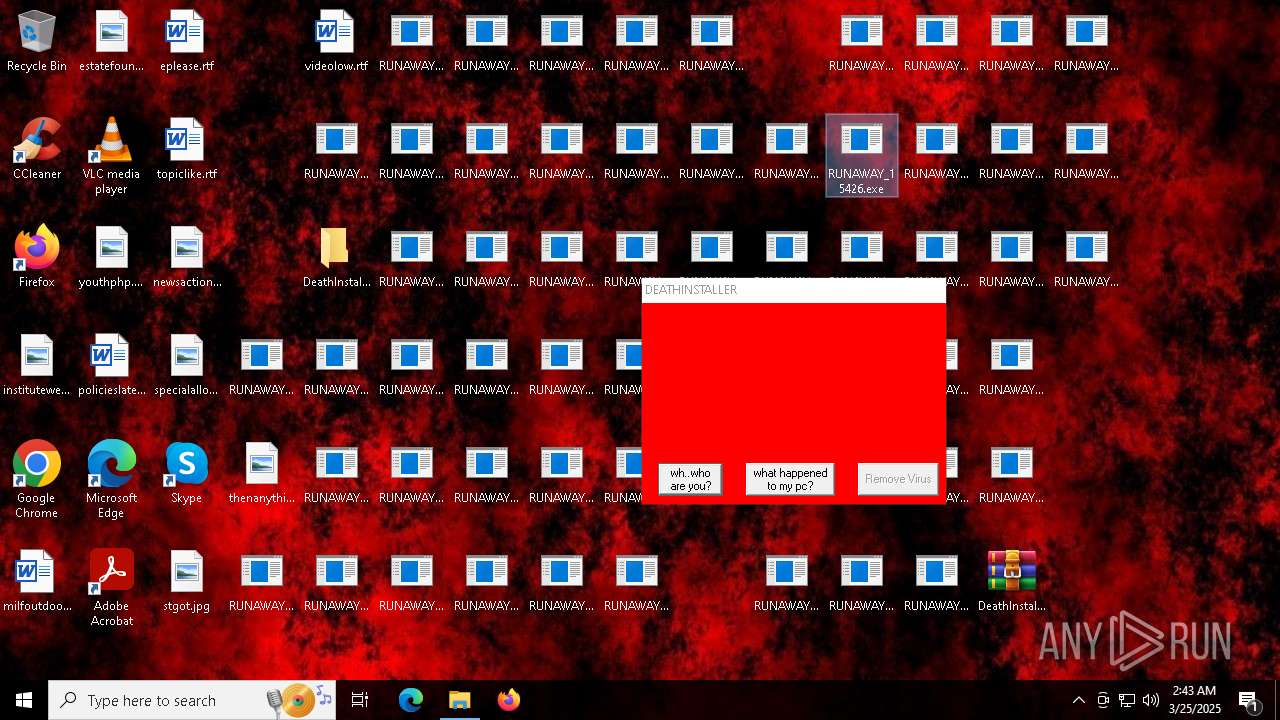
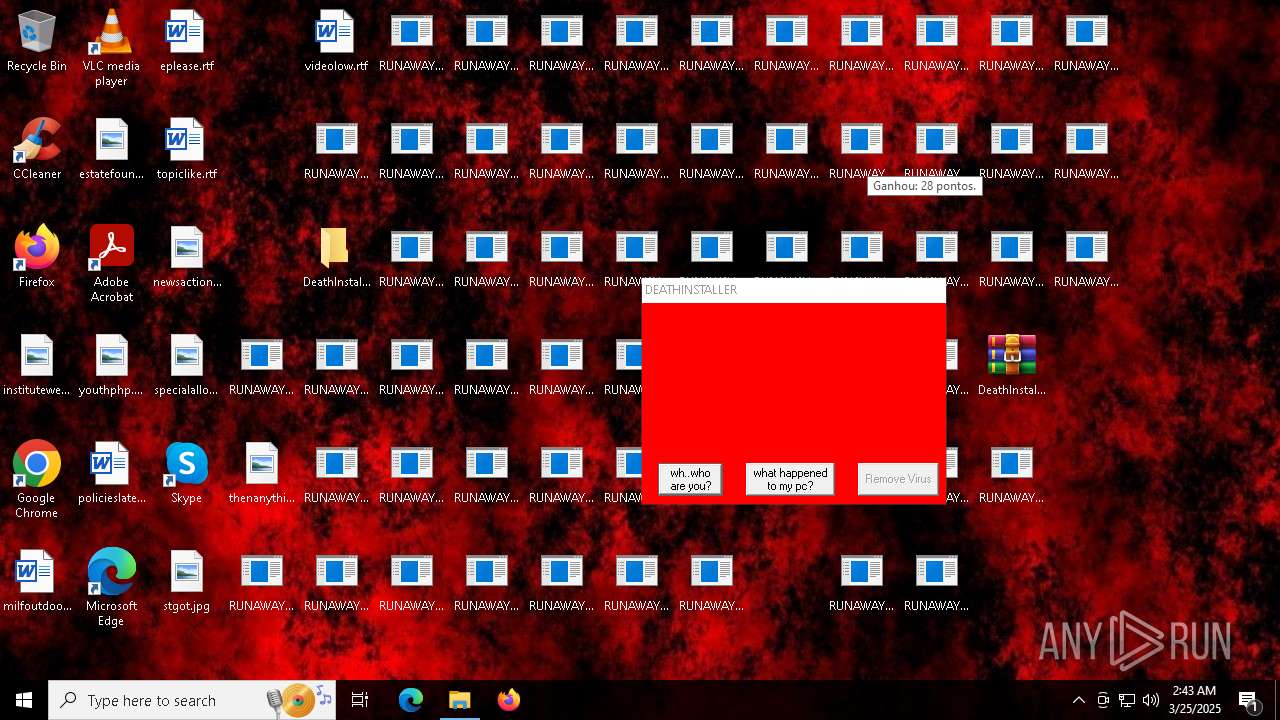
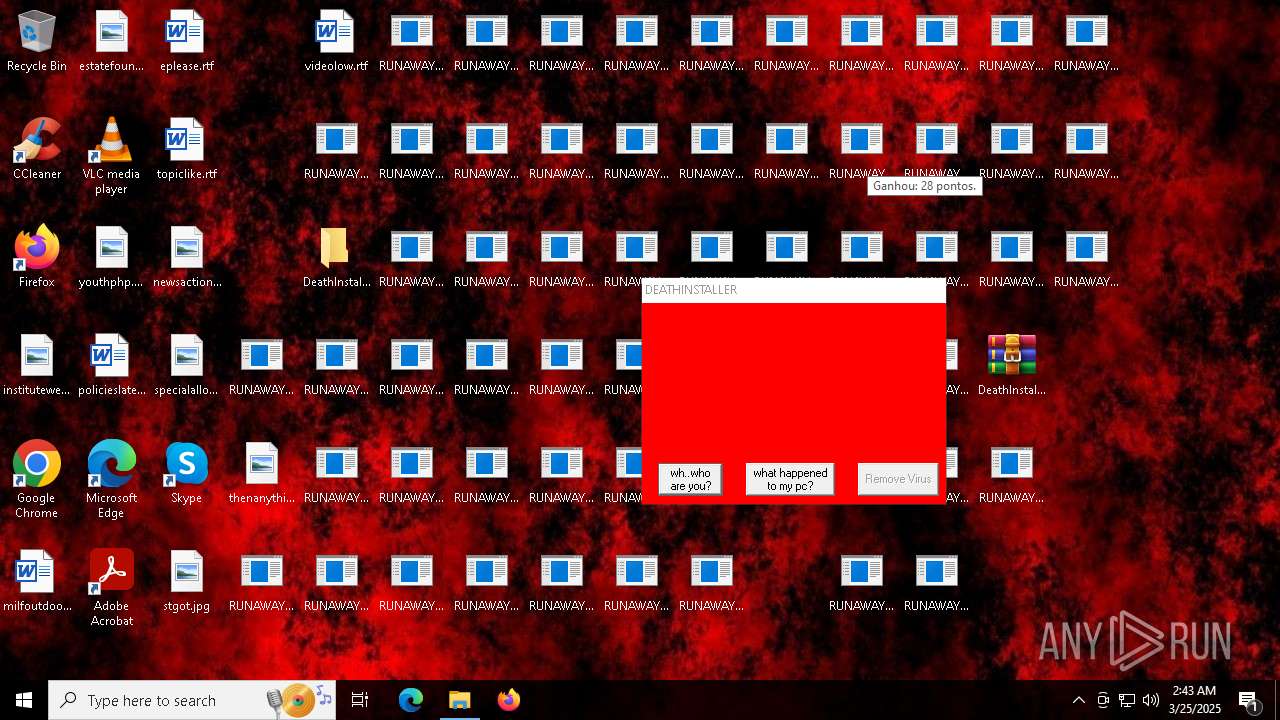
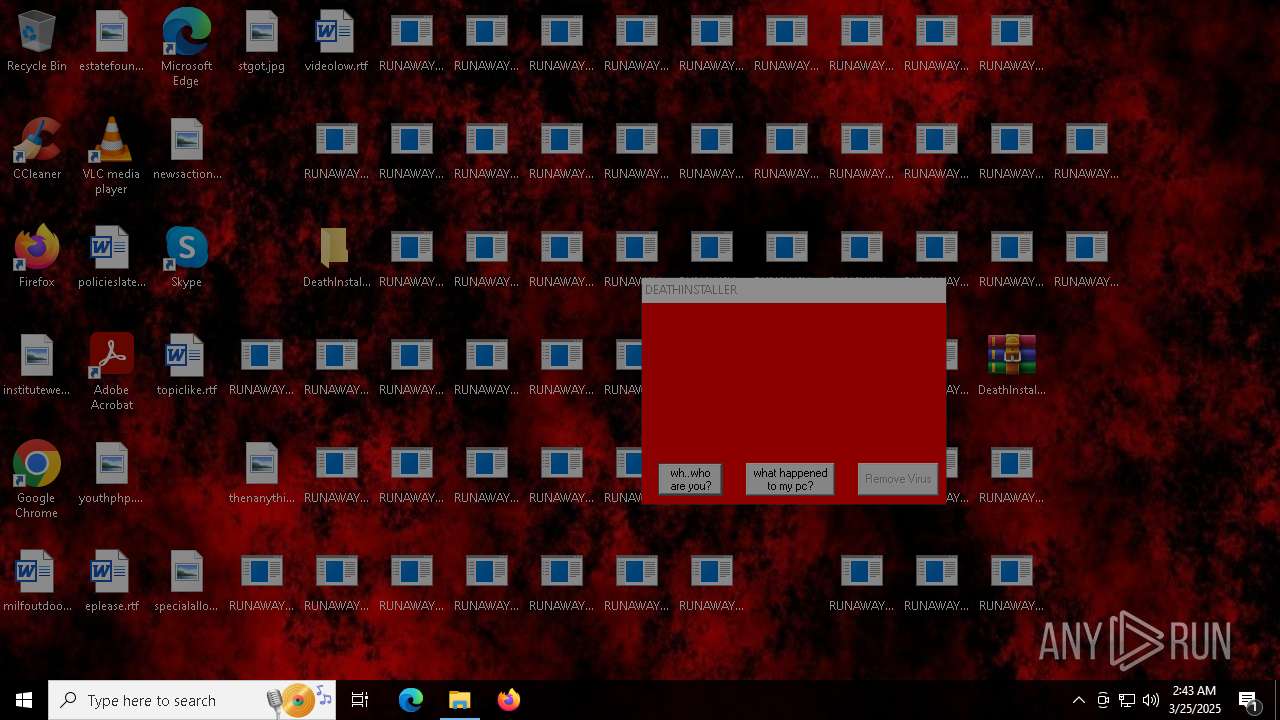
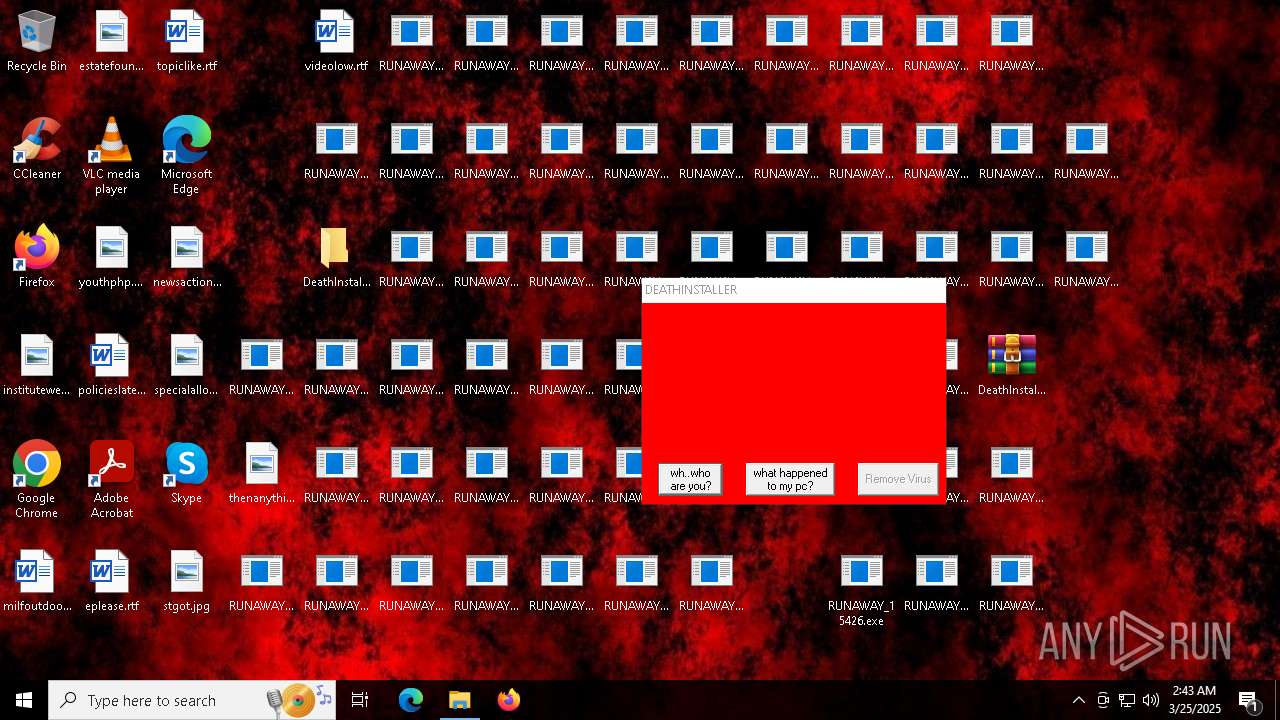
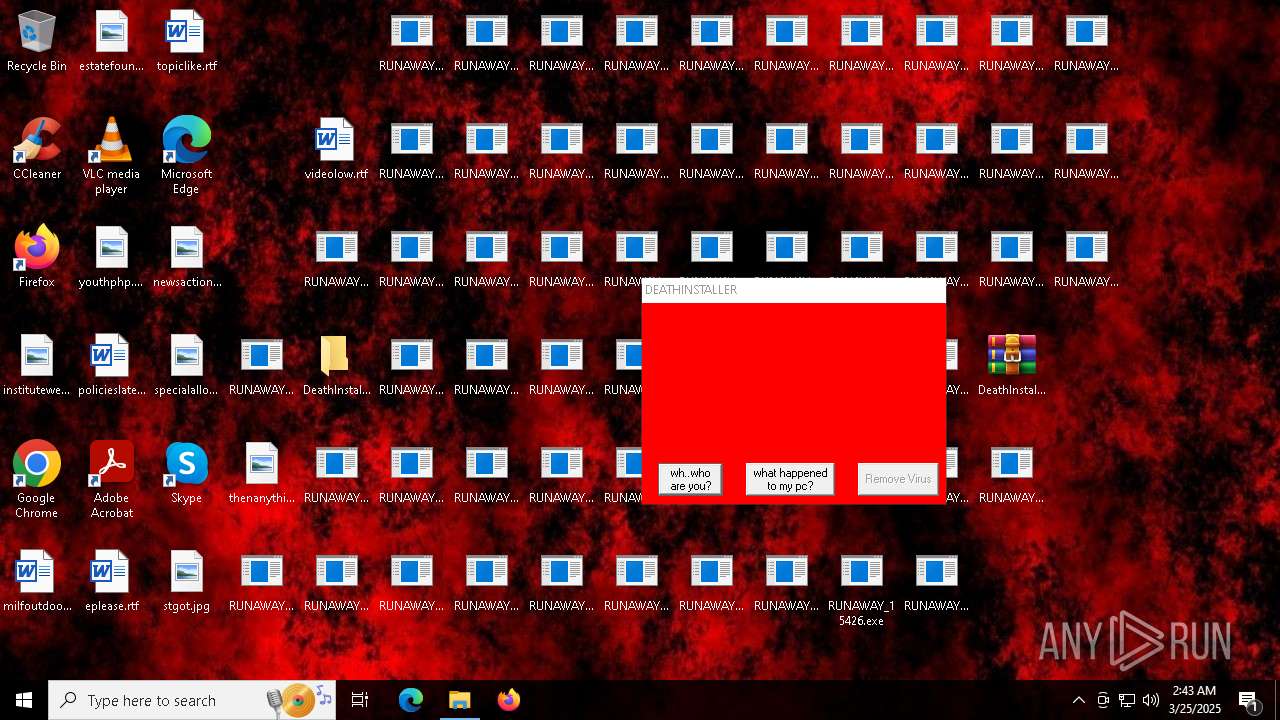
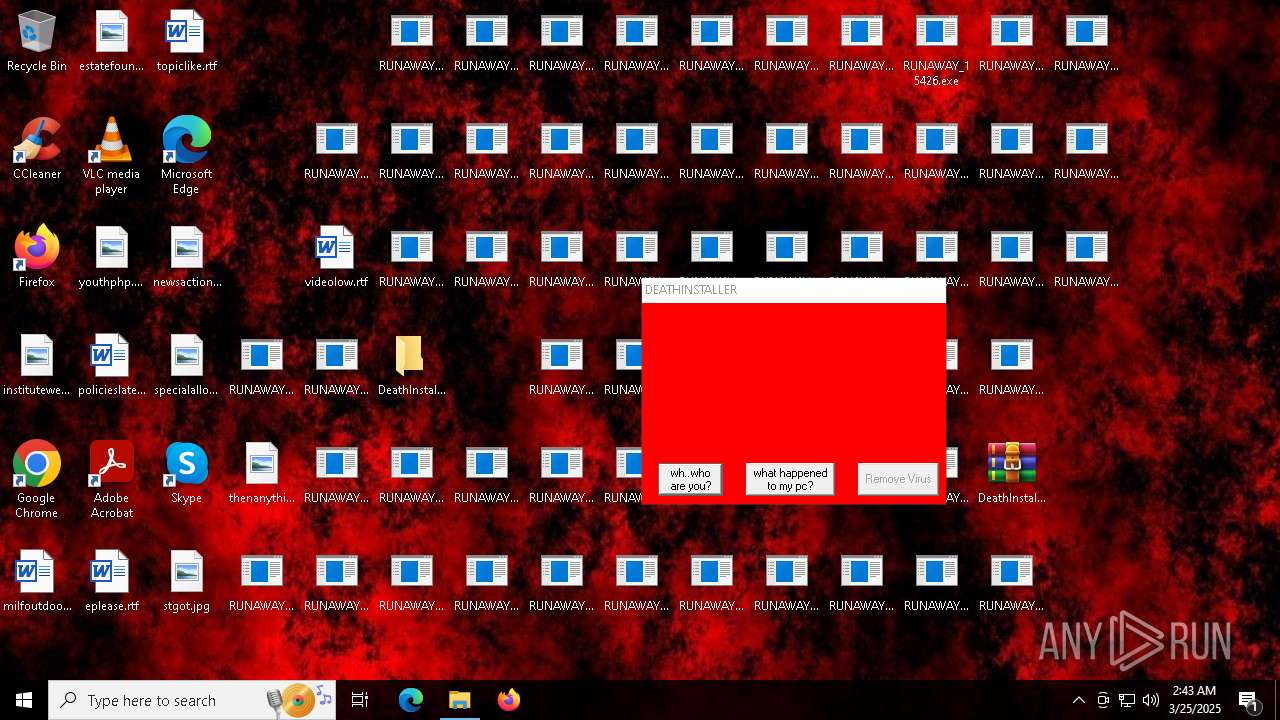
MALICIOUS
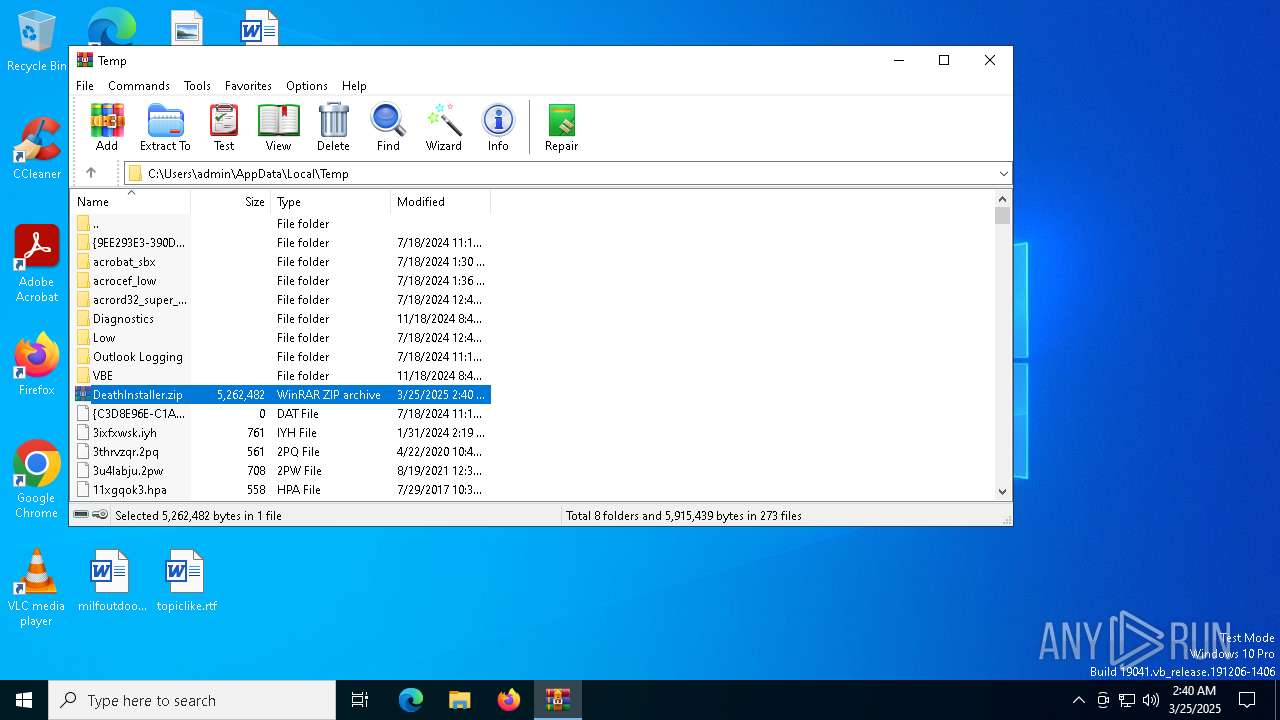
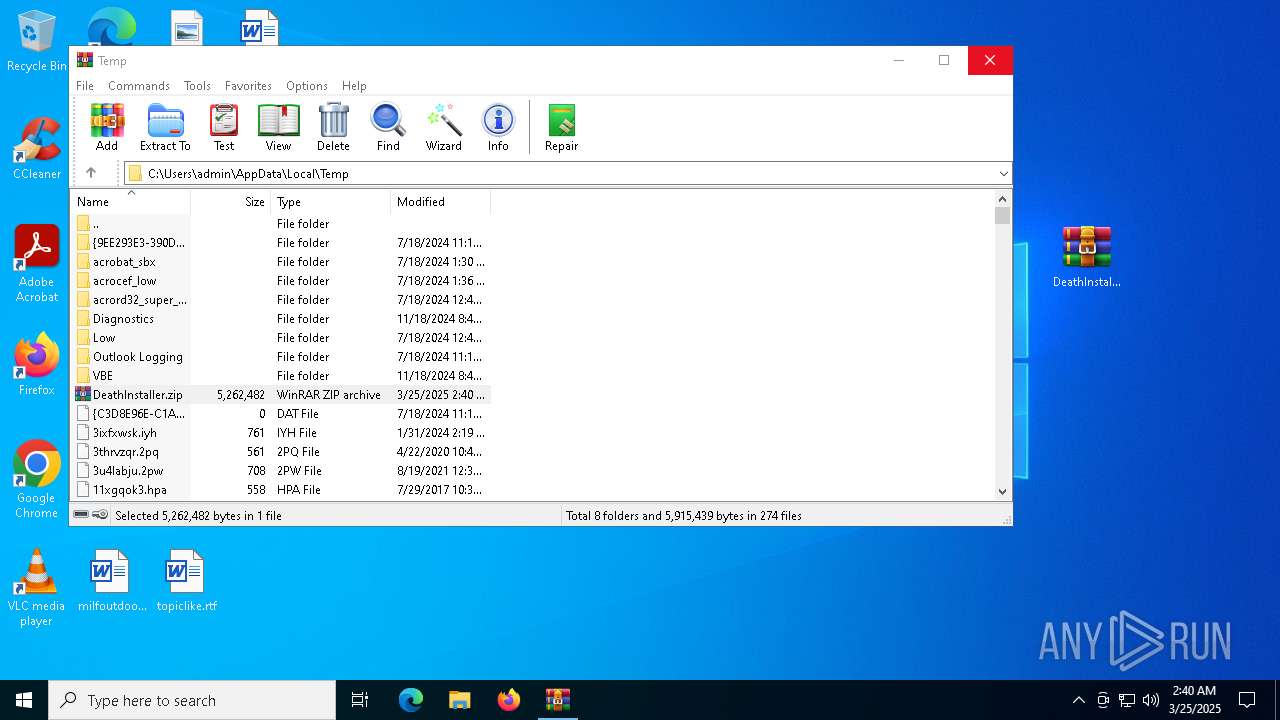
Generic archive extractor
- WinRAR.exe (PID: 4996)
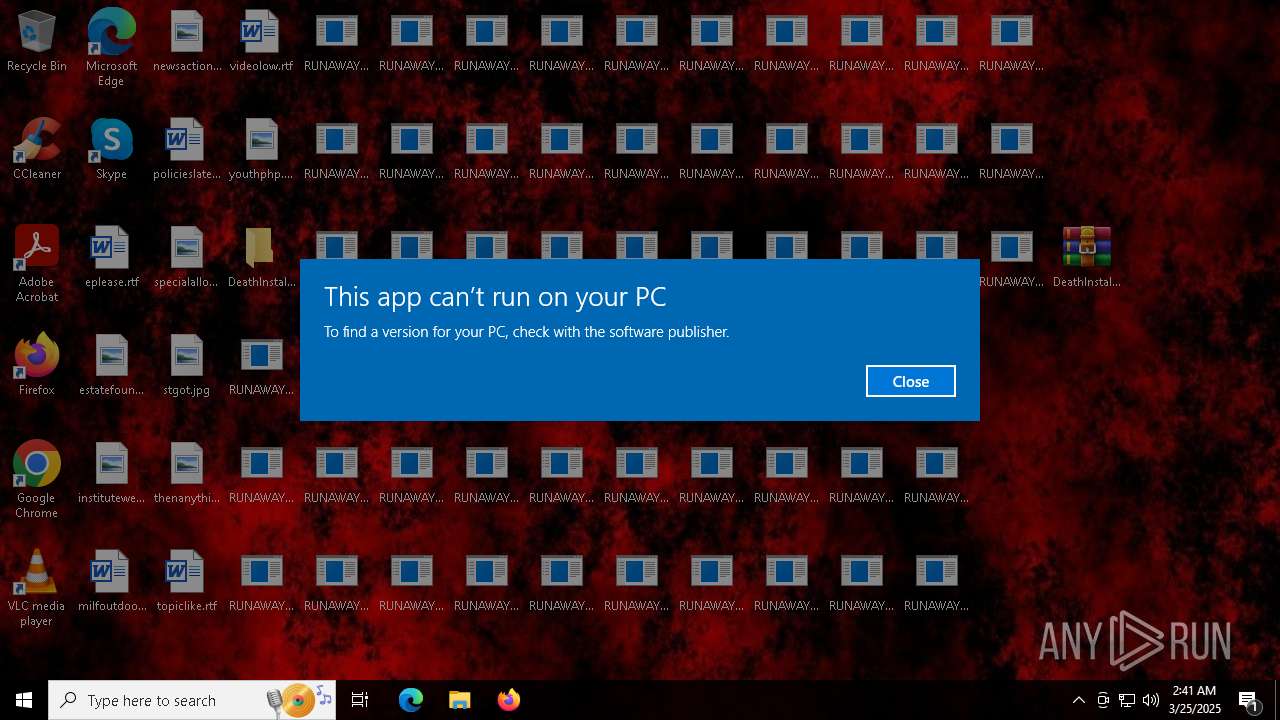
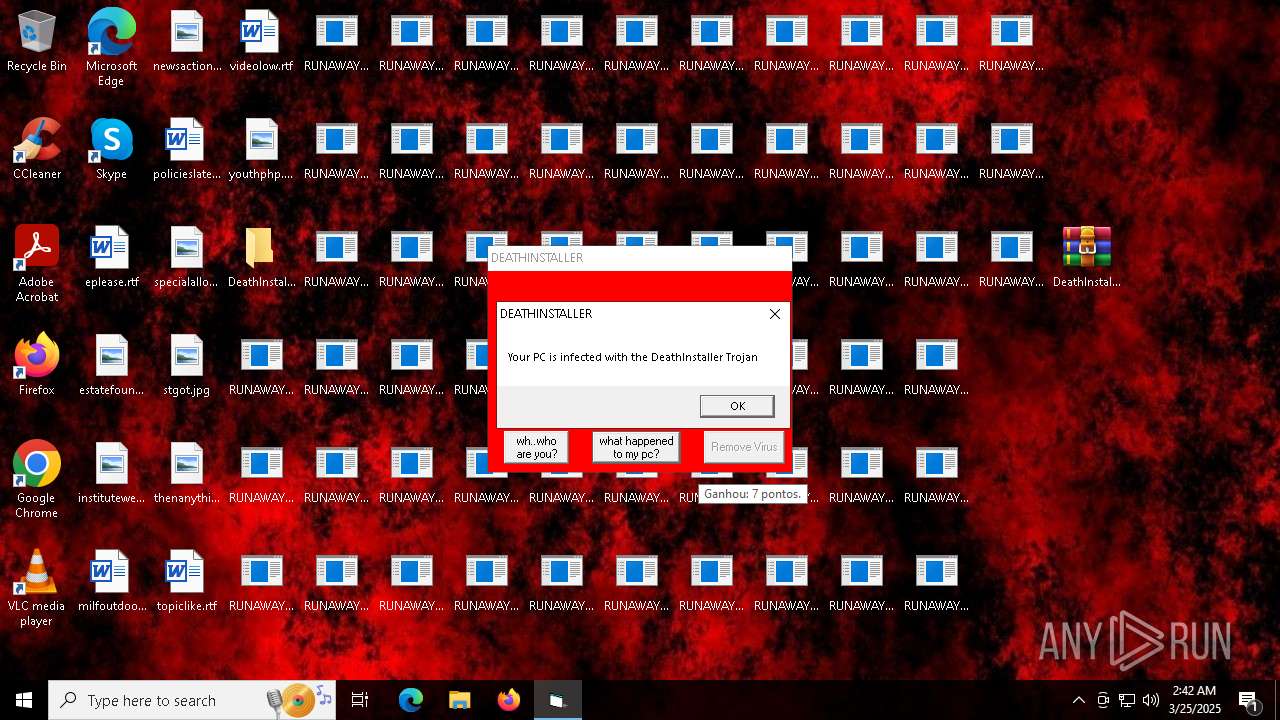
Disables task manager
- reg.exe (PID: 7408)
UAC/LUA settings modification
- reg.exe (PID: 7316)
Disables Windows Defender
- reg.exe (PID: 7532)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 7304)
- net.exe (PID: 7288)
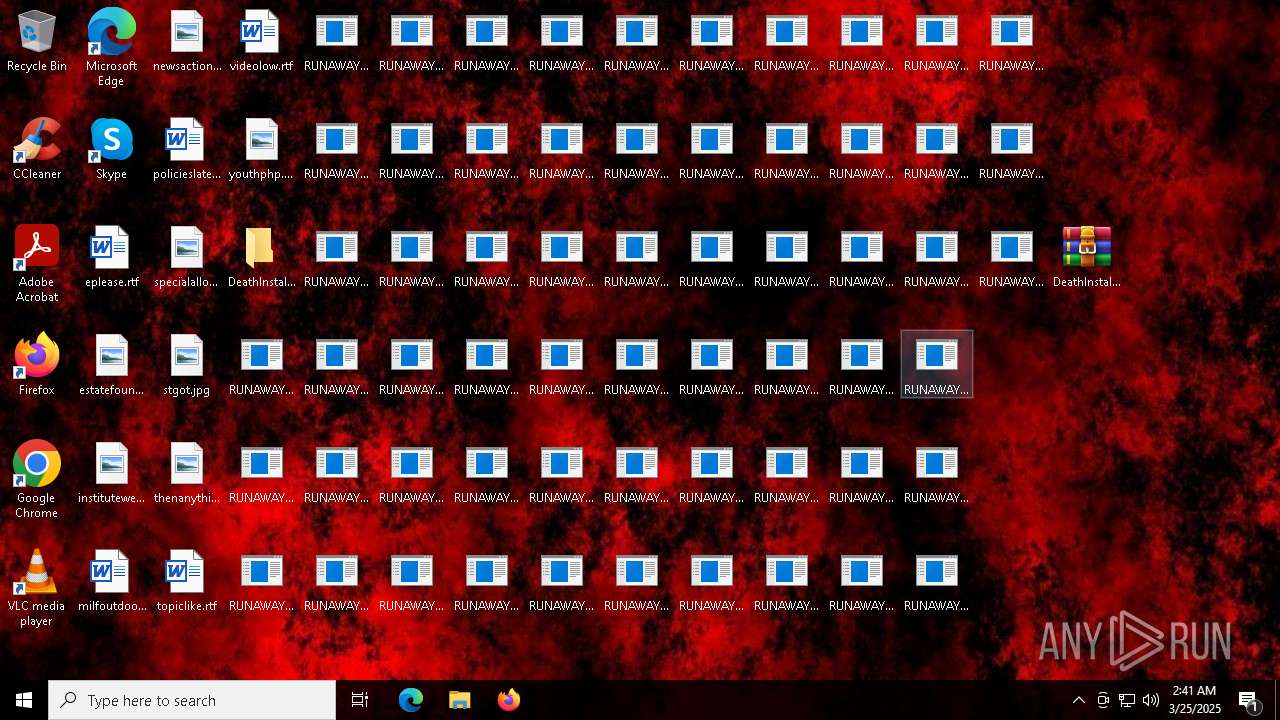
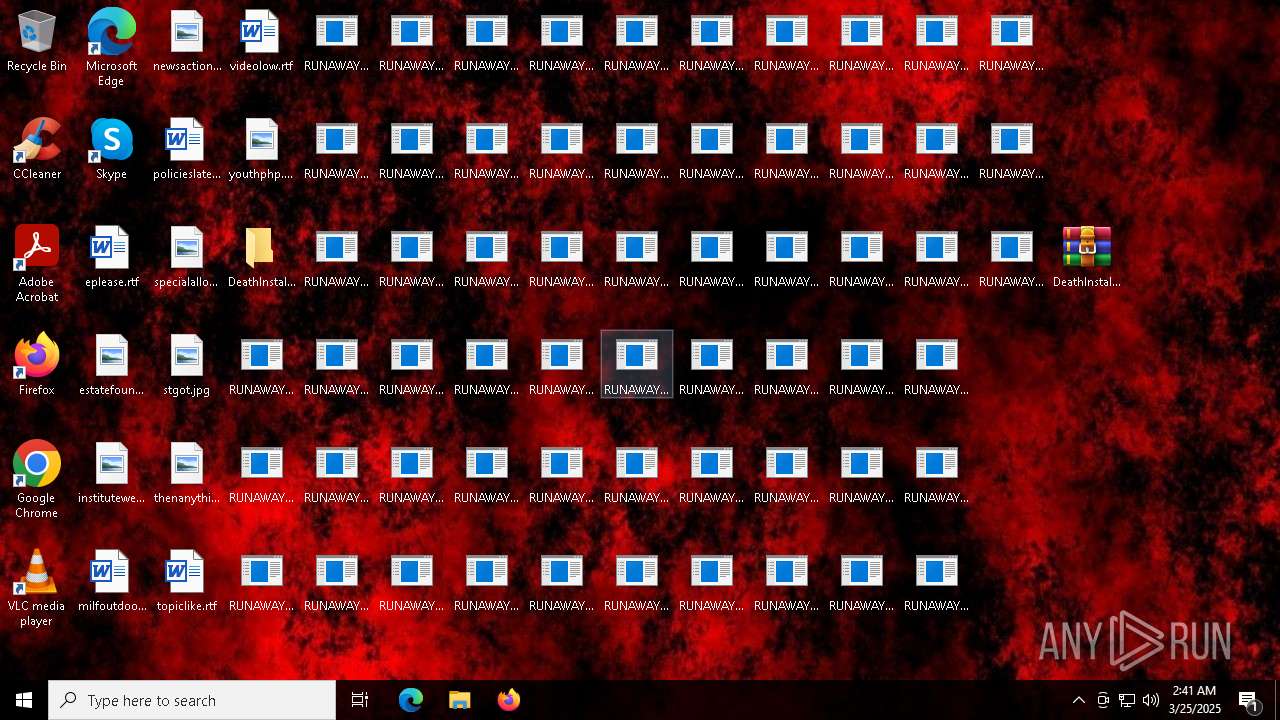
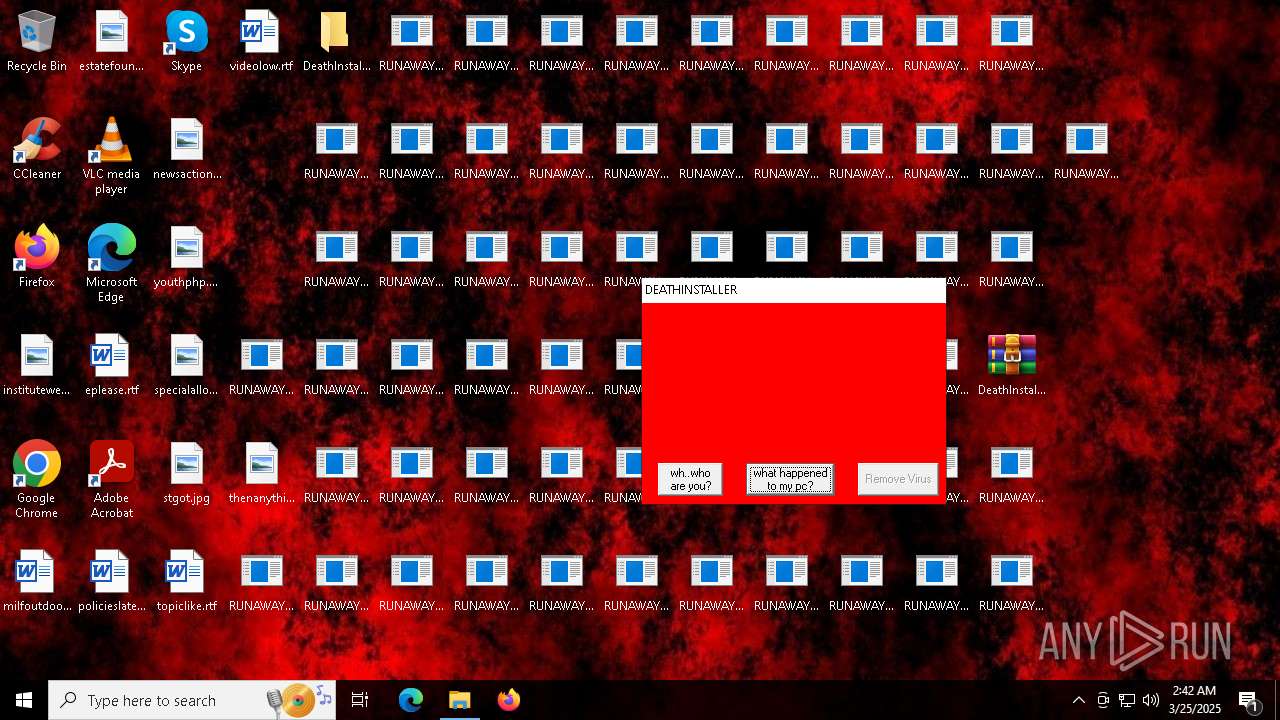
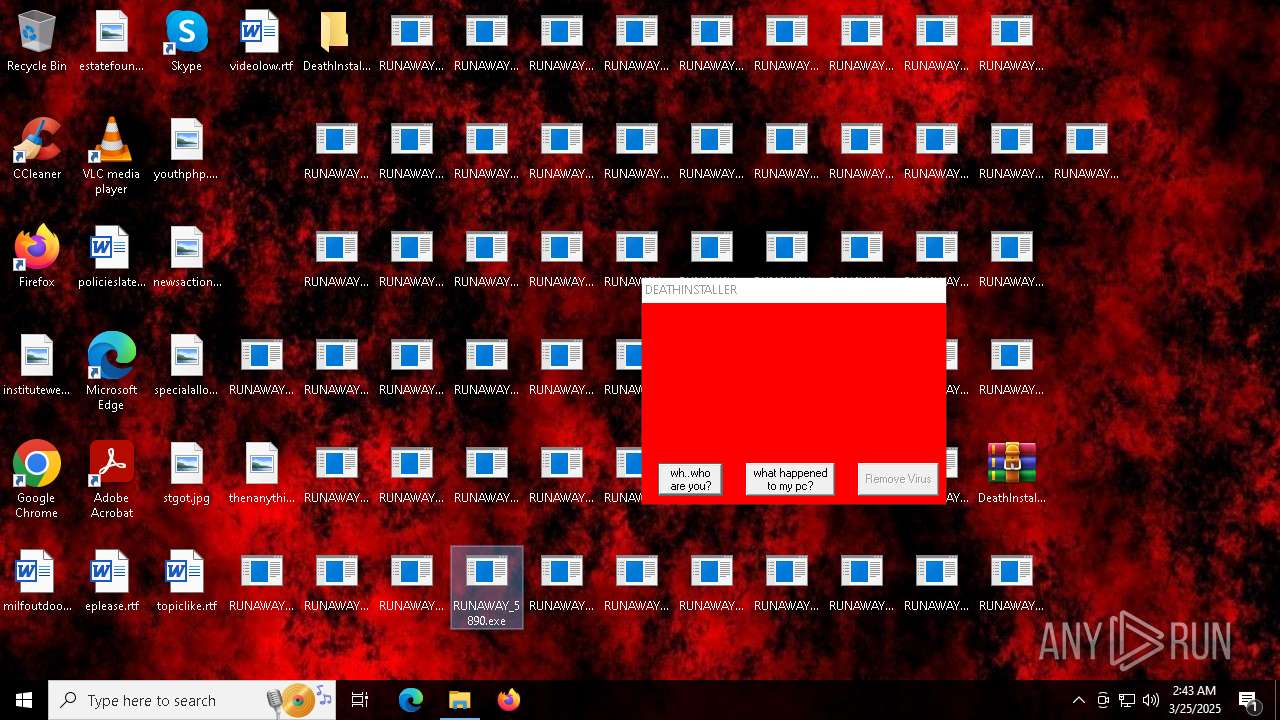
Create files in the Startup directory
- cmd.exe (PID: 7304)
SUSPICIOUS
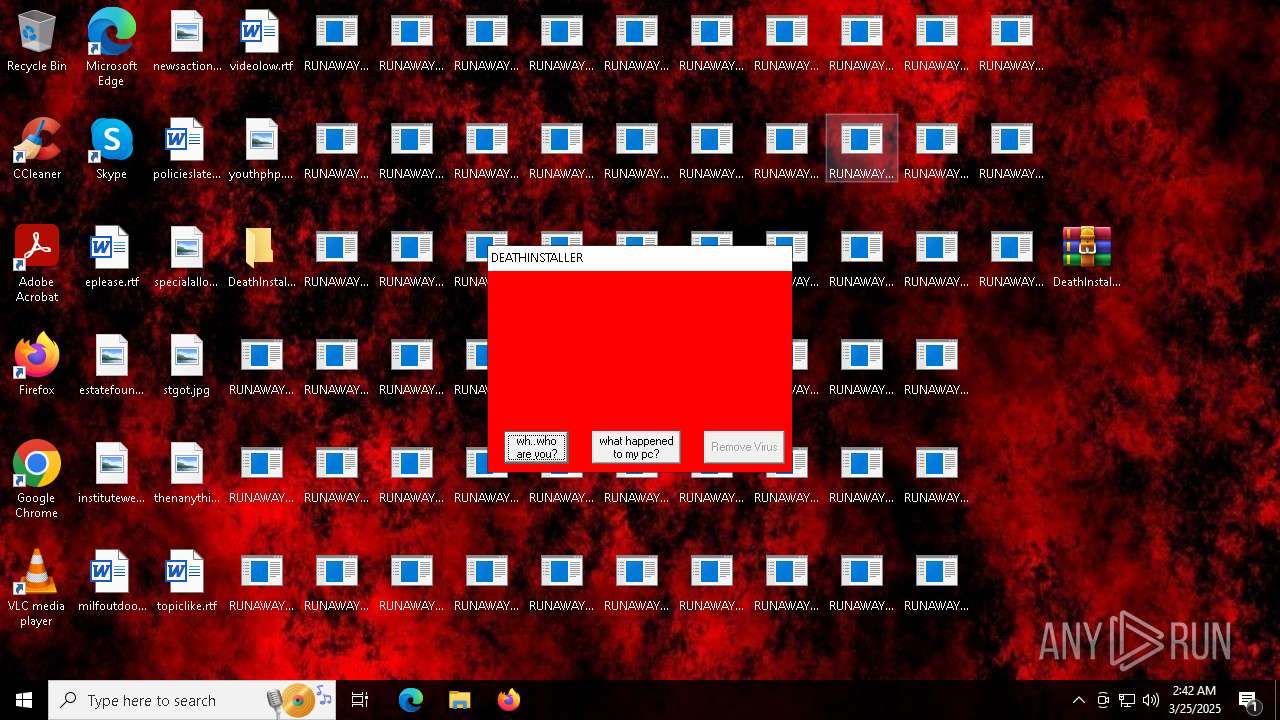
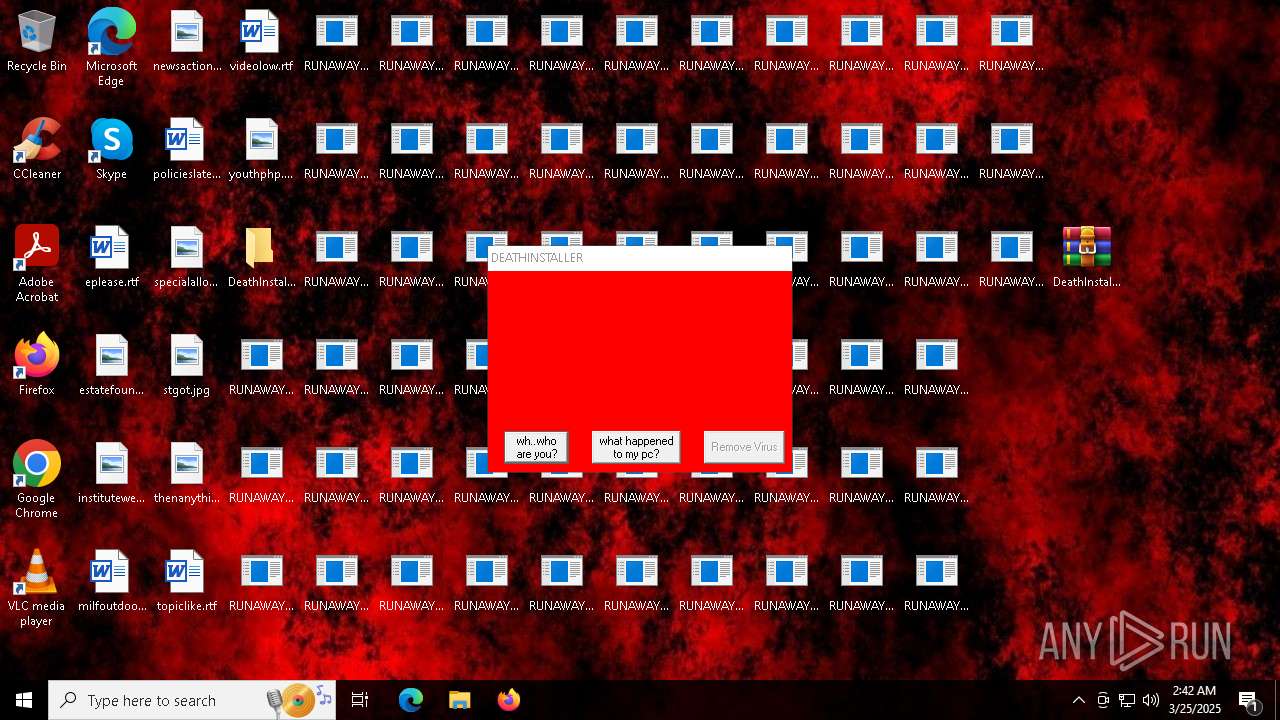
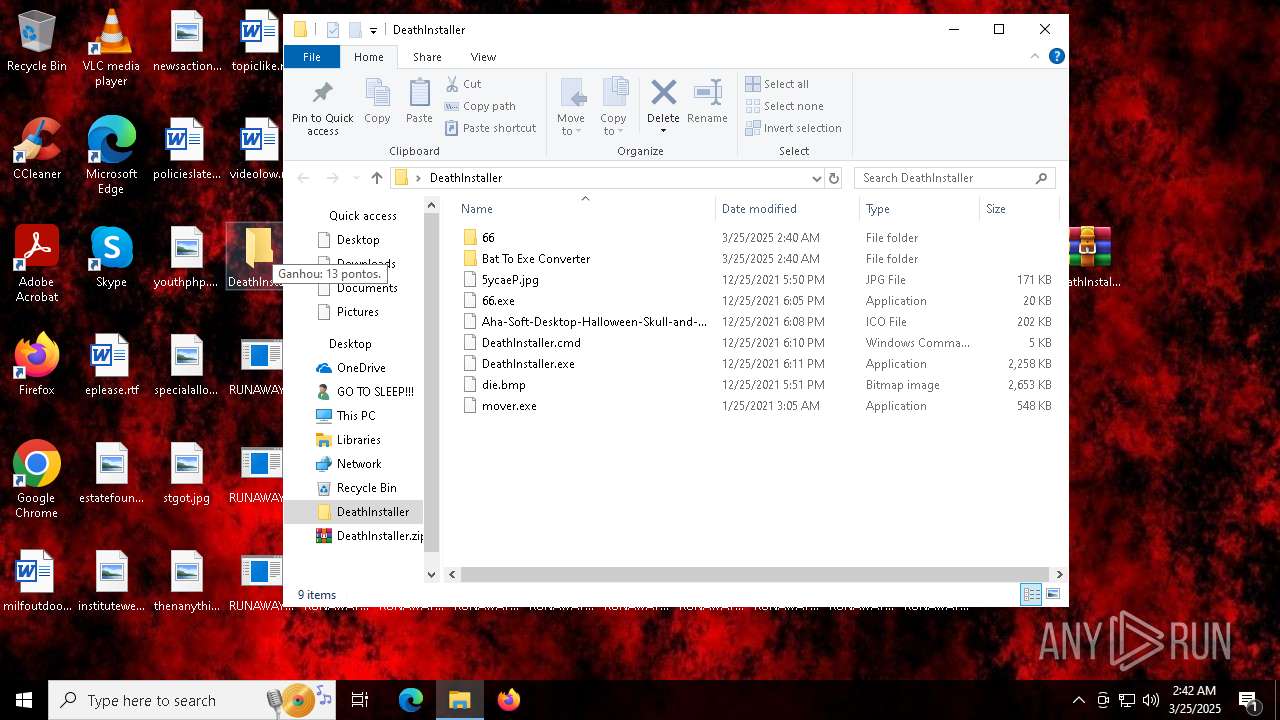
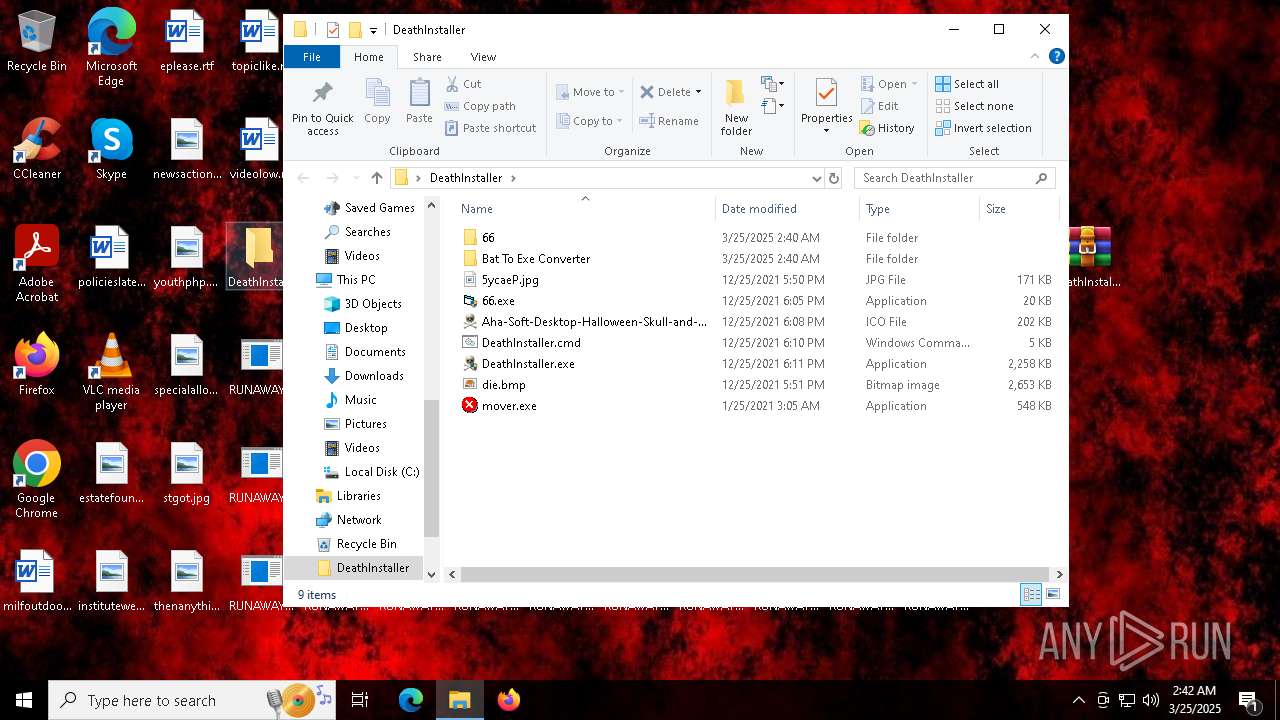
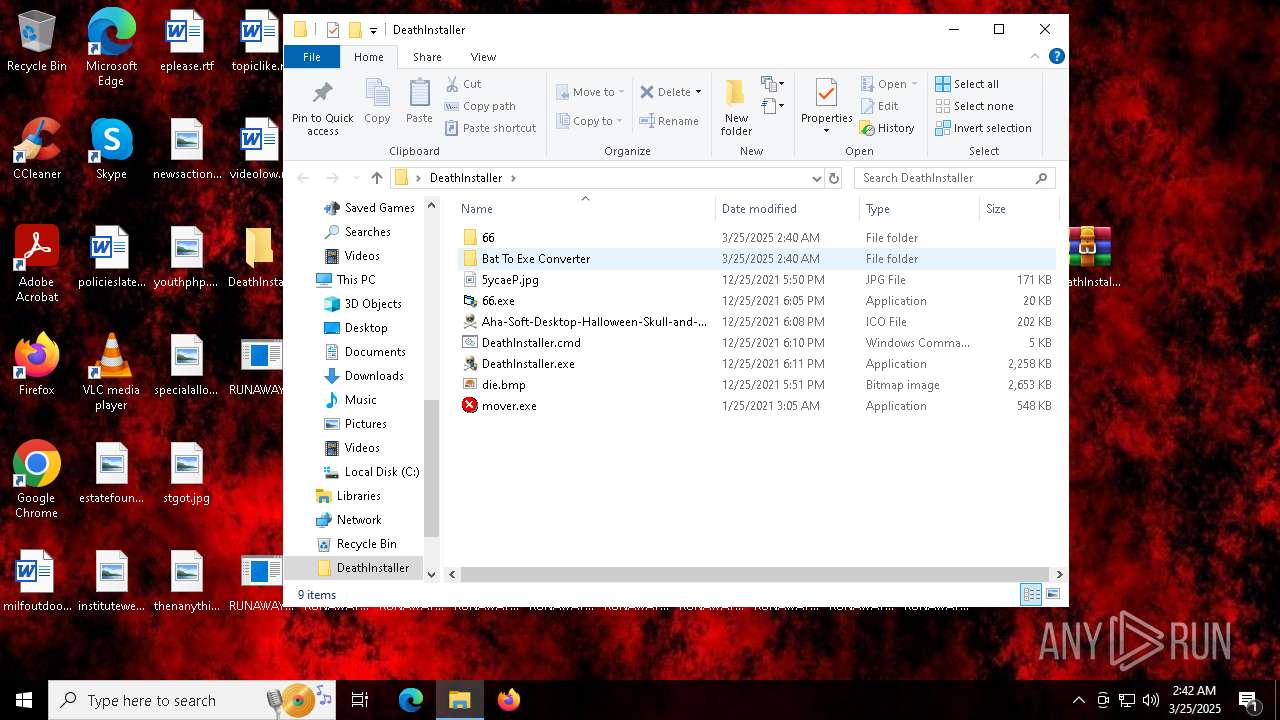
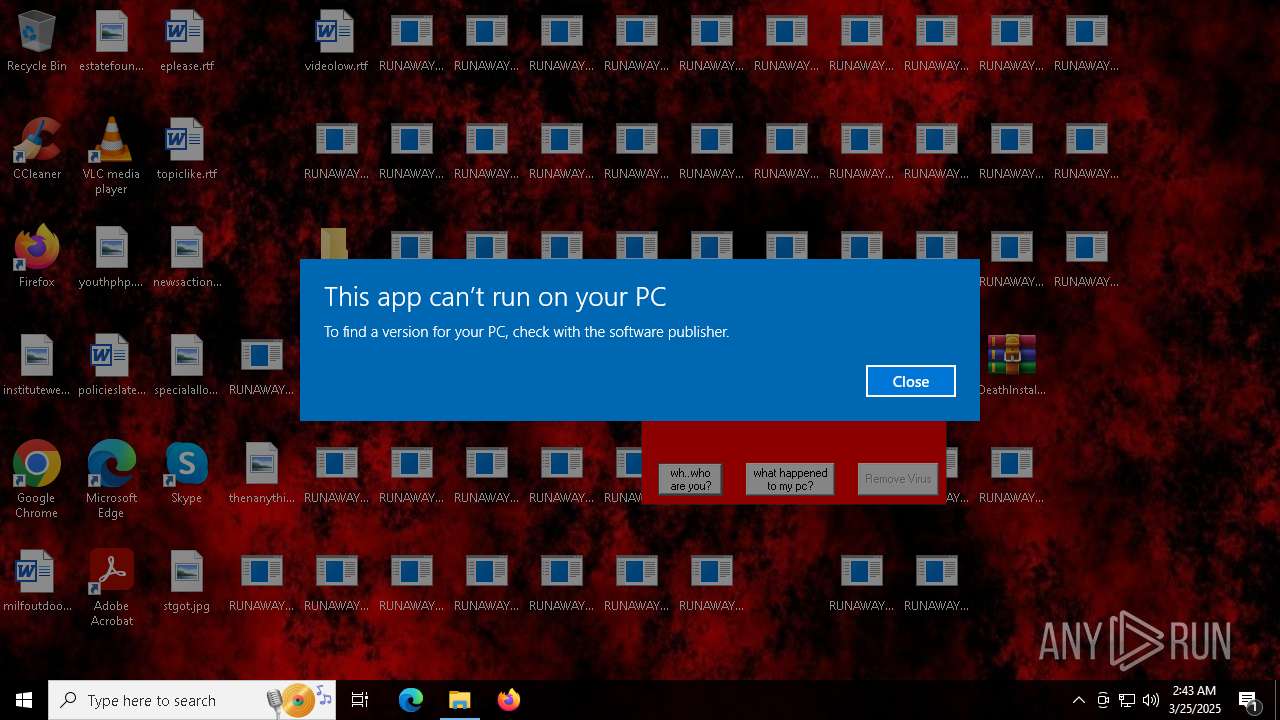
Executable content was dropped or overwritten
- DeathInstaller.exe (PID: 5204)
- cmd.exe (PID: 7304)
Reads security settings of Internet Explorer
- DeathInstaller.exe (PID: 5204)
- ShellExperienceHost.exe (PID: 5968)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7304)
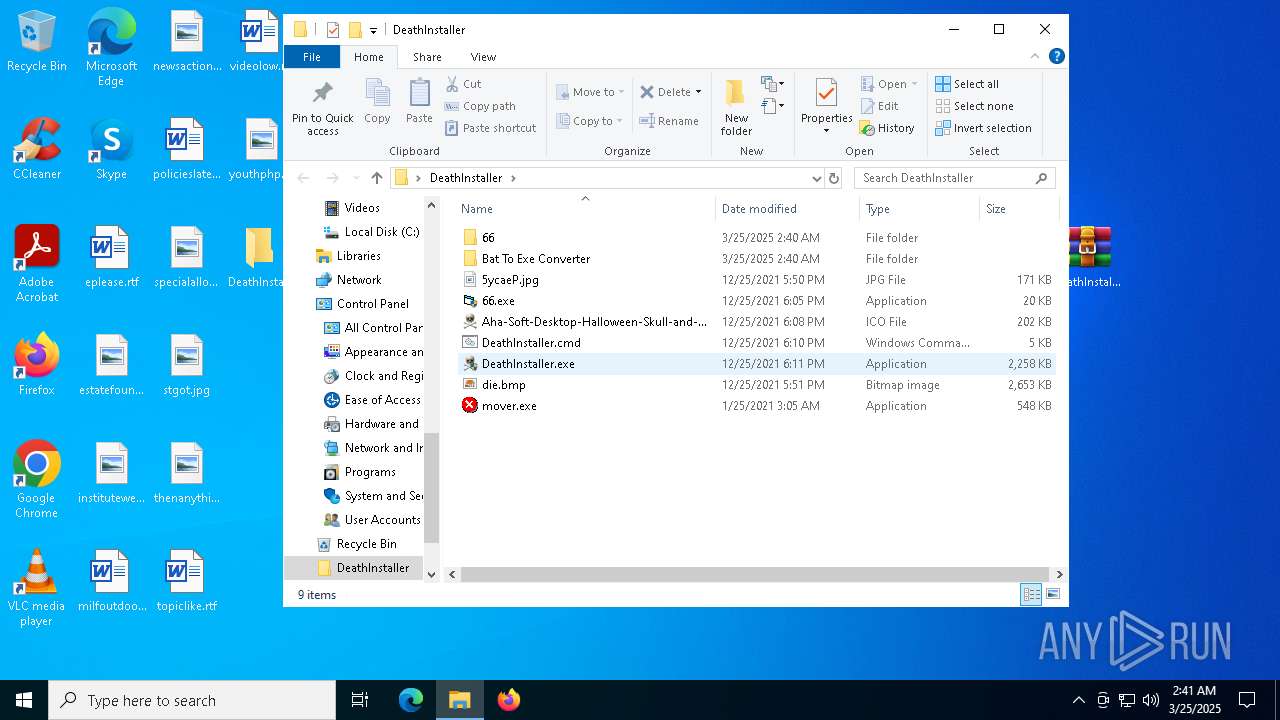
Executing commands from ".cmd" file
- DeathInstaller.exe (PID: 5204)
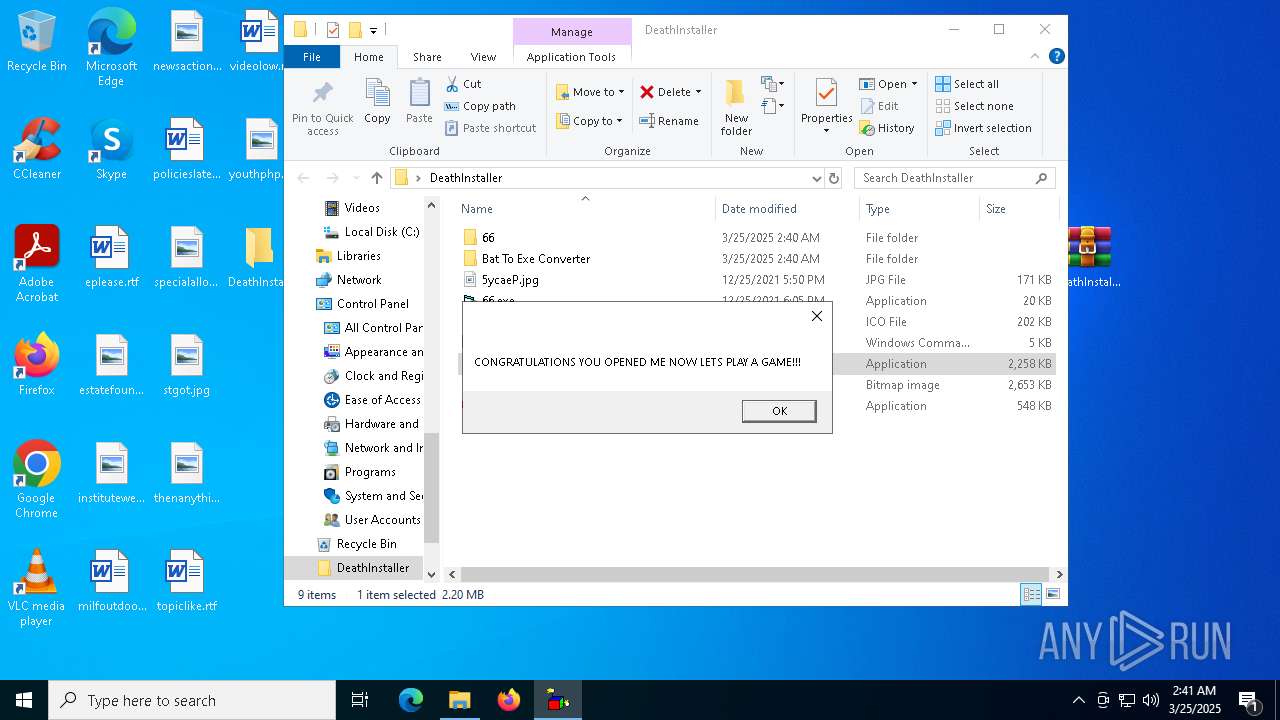
Starts CMD.EXE for commands execution
- DeathInstaller.exe (PID: 5204)
The process executes VB scripts
- cmd.exe (PID: 7304)
Creates file in the systems drive root
- cmd.exe (PID: 7304)
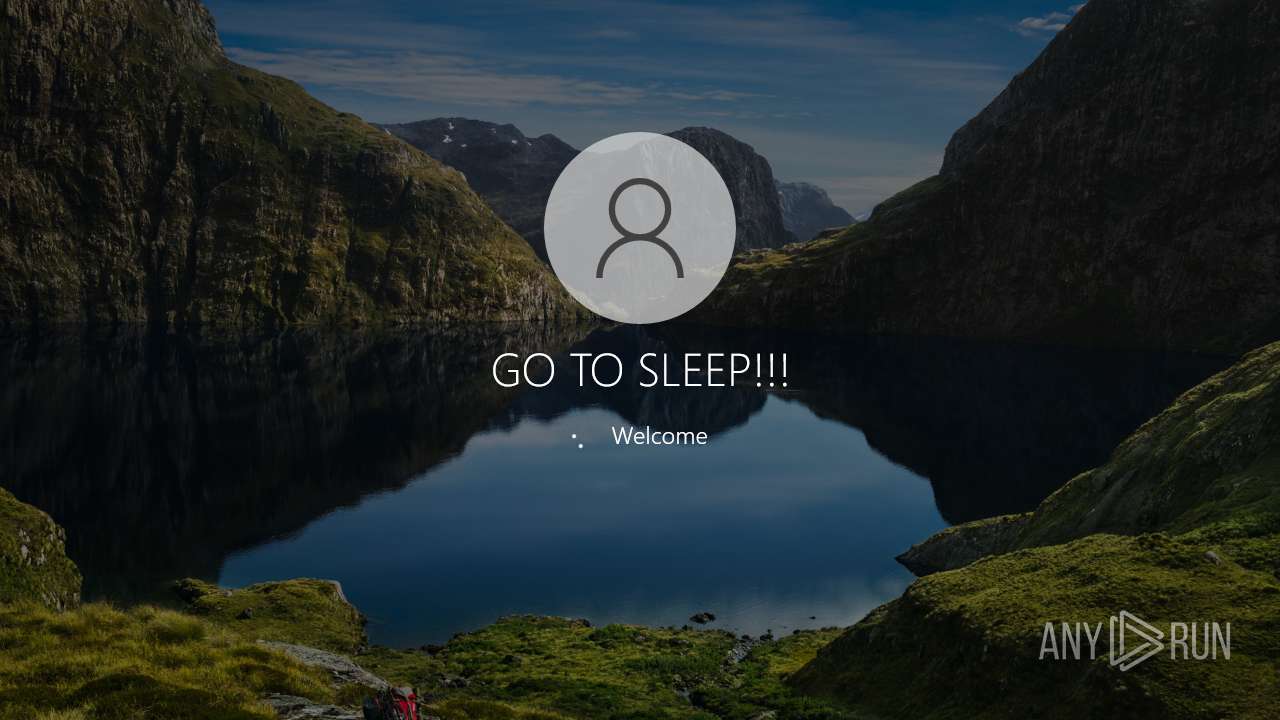
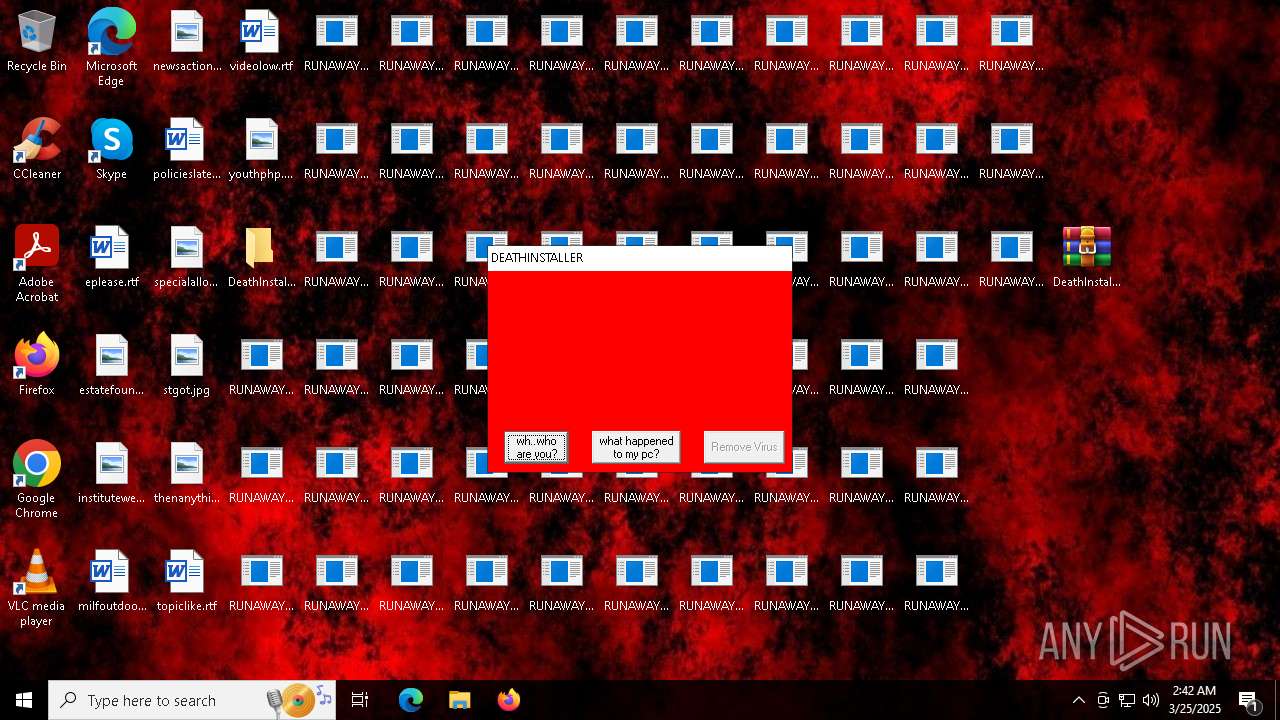
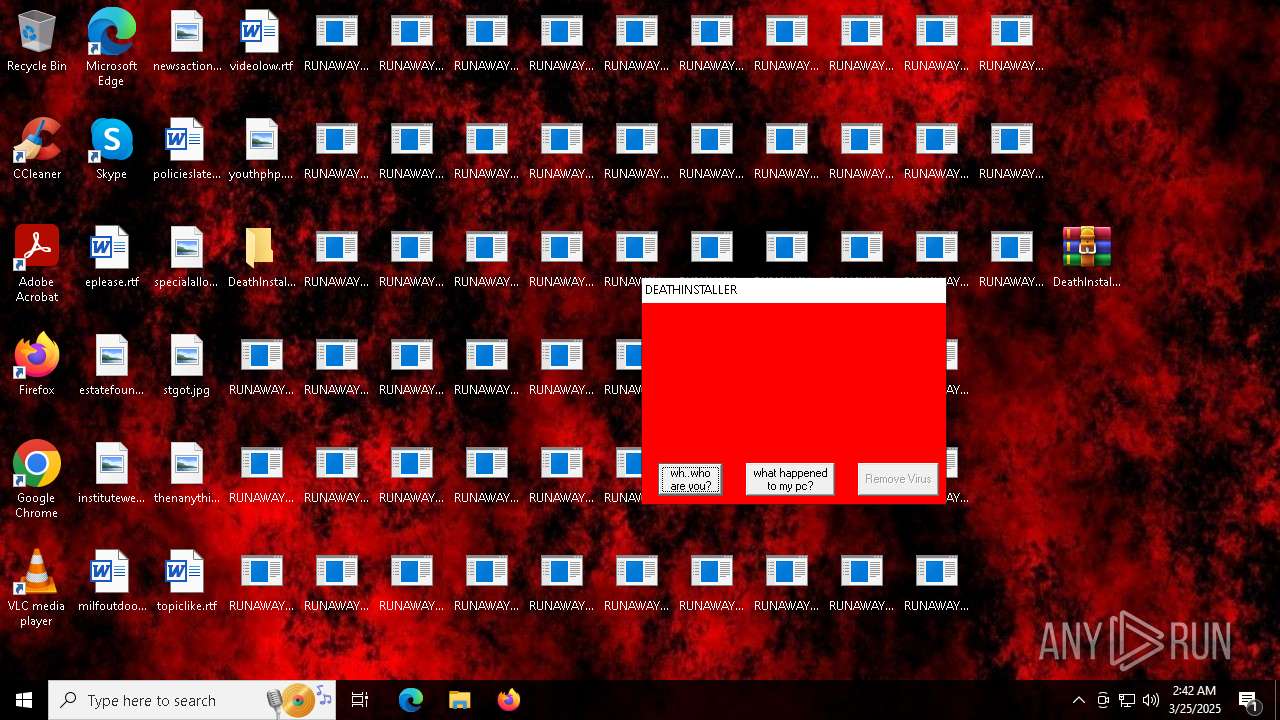
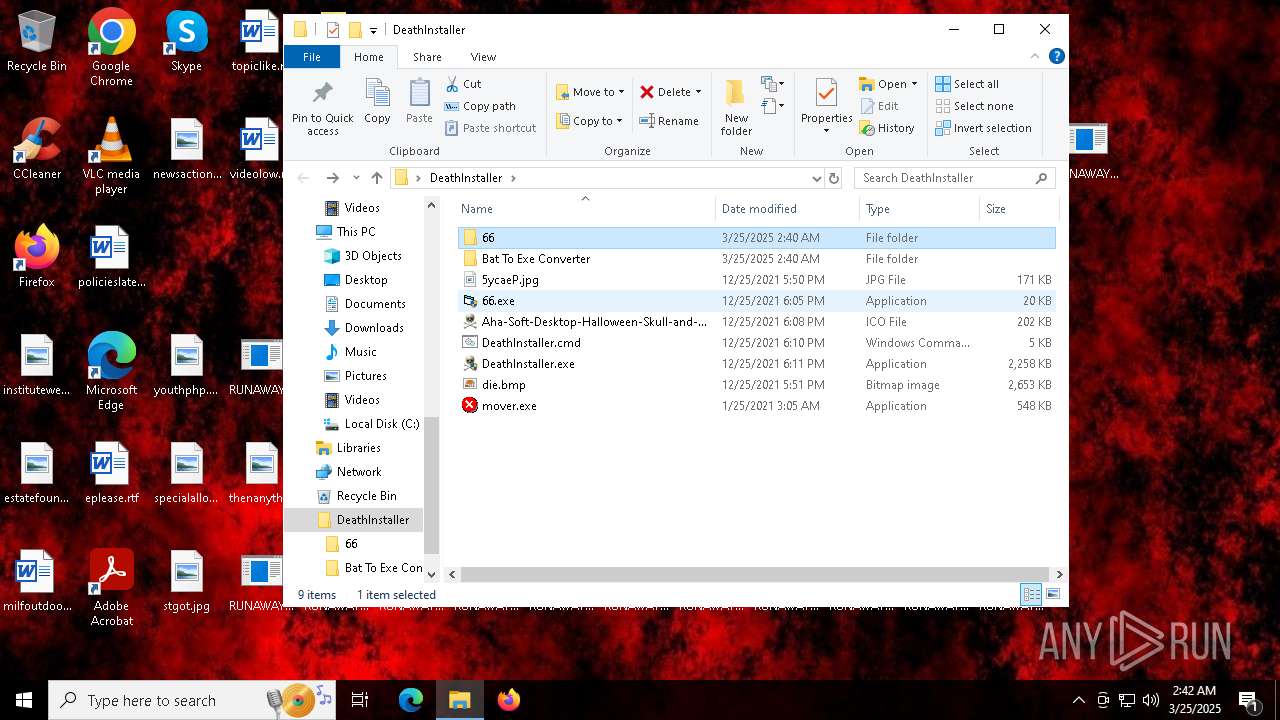
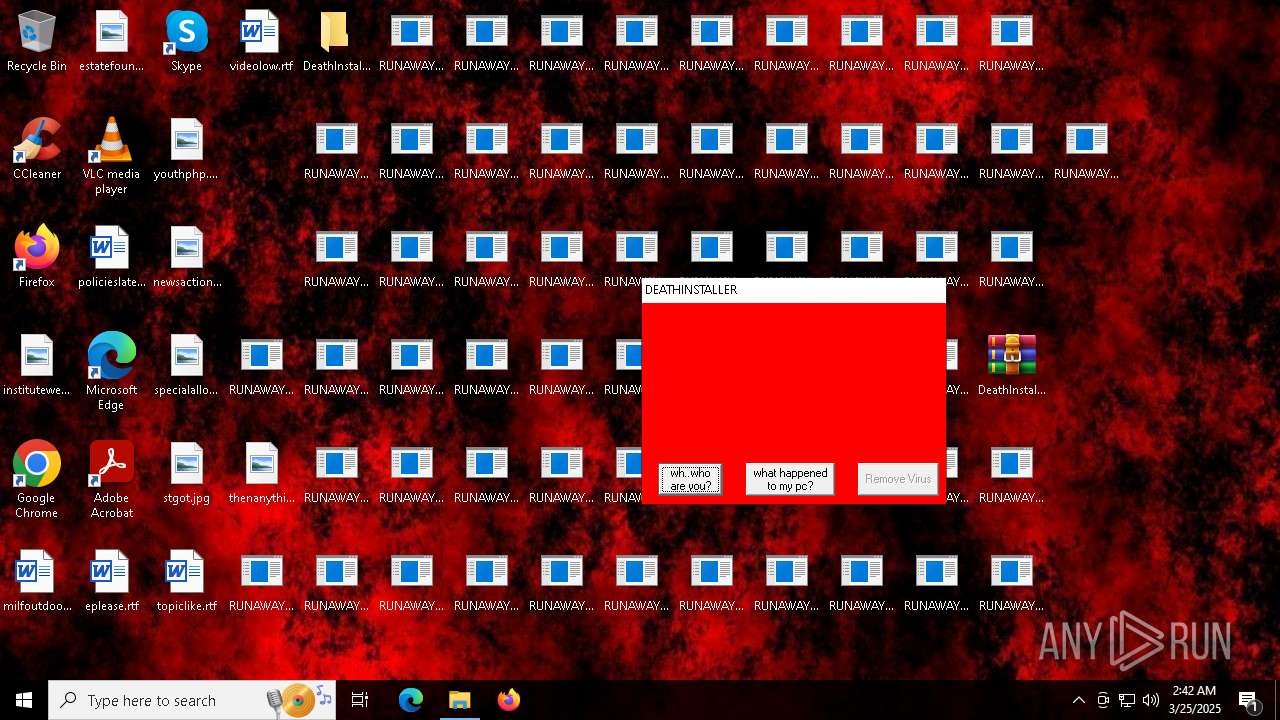
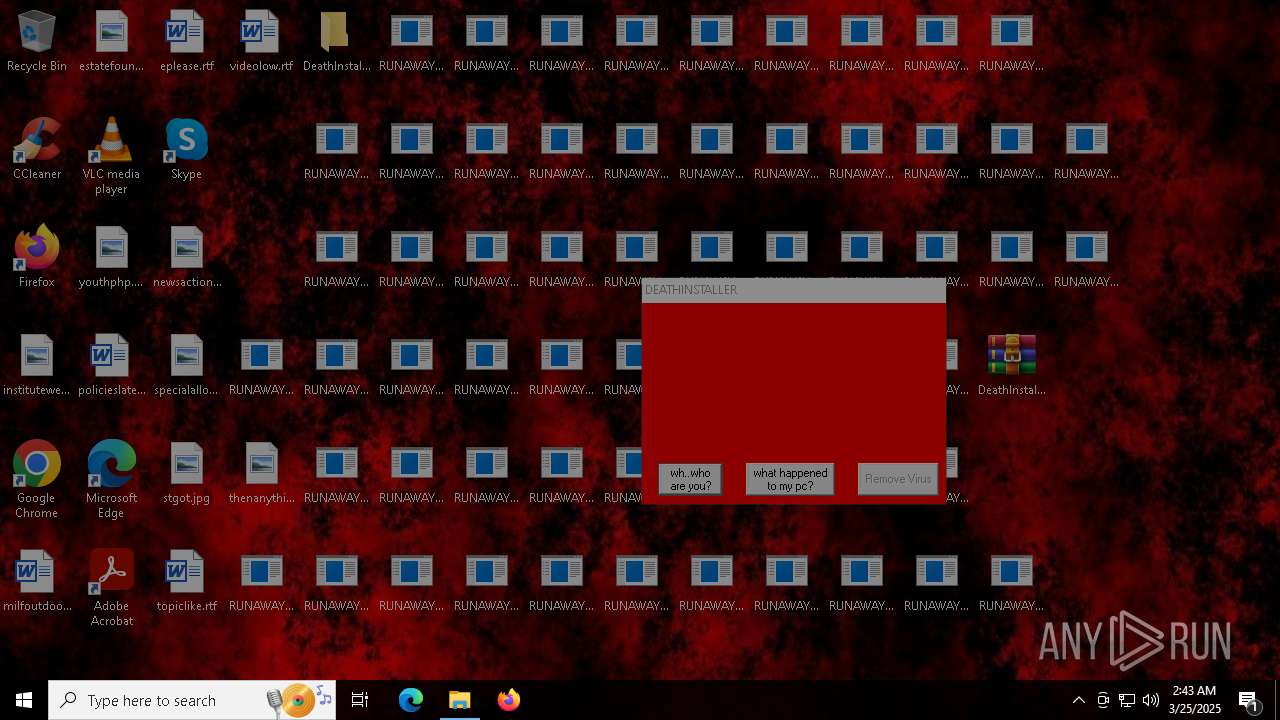
Changes the desktop background image
- reg.exe (PID: 7512)
- reg.exe (PID: 7516)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4128)
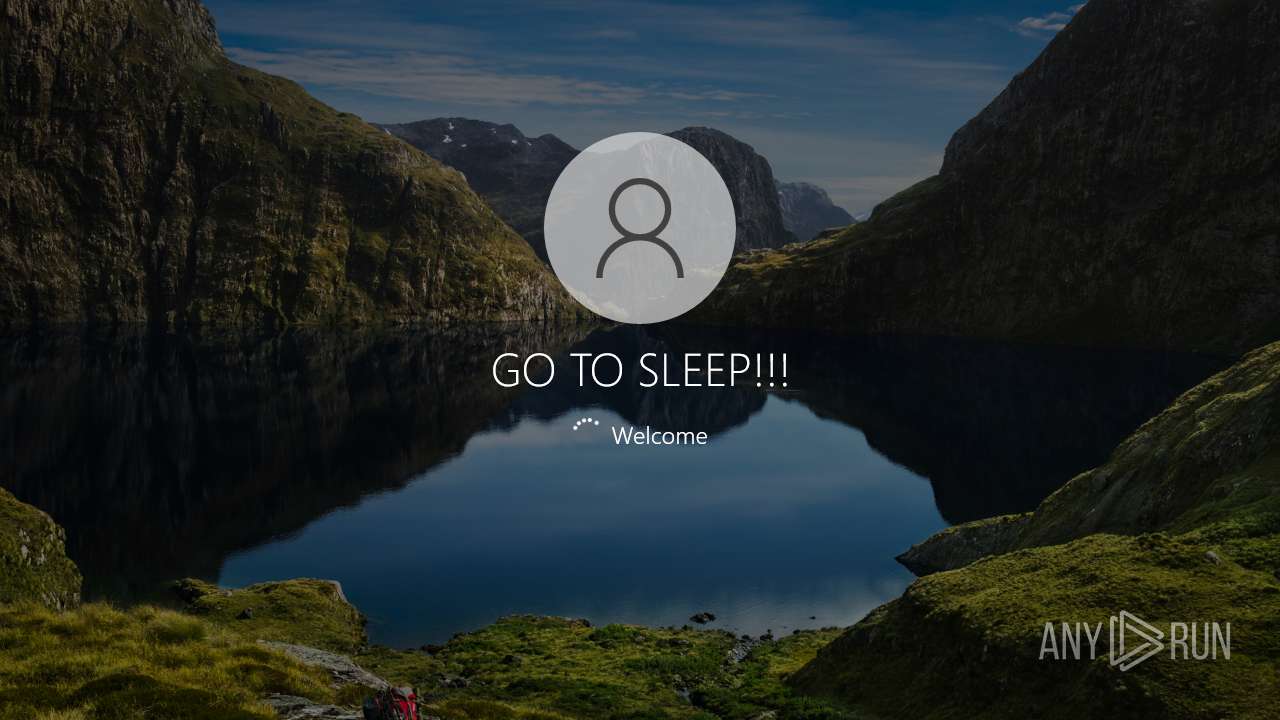
The system shut down or reboot
- cmd.exe (PID: 7304)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 6944)
- DeathInstaller.exe (PID: 5204)
- cmd.exe (PID: 7304)
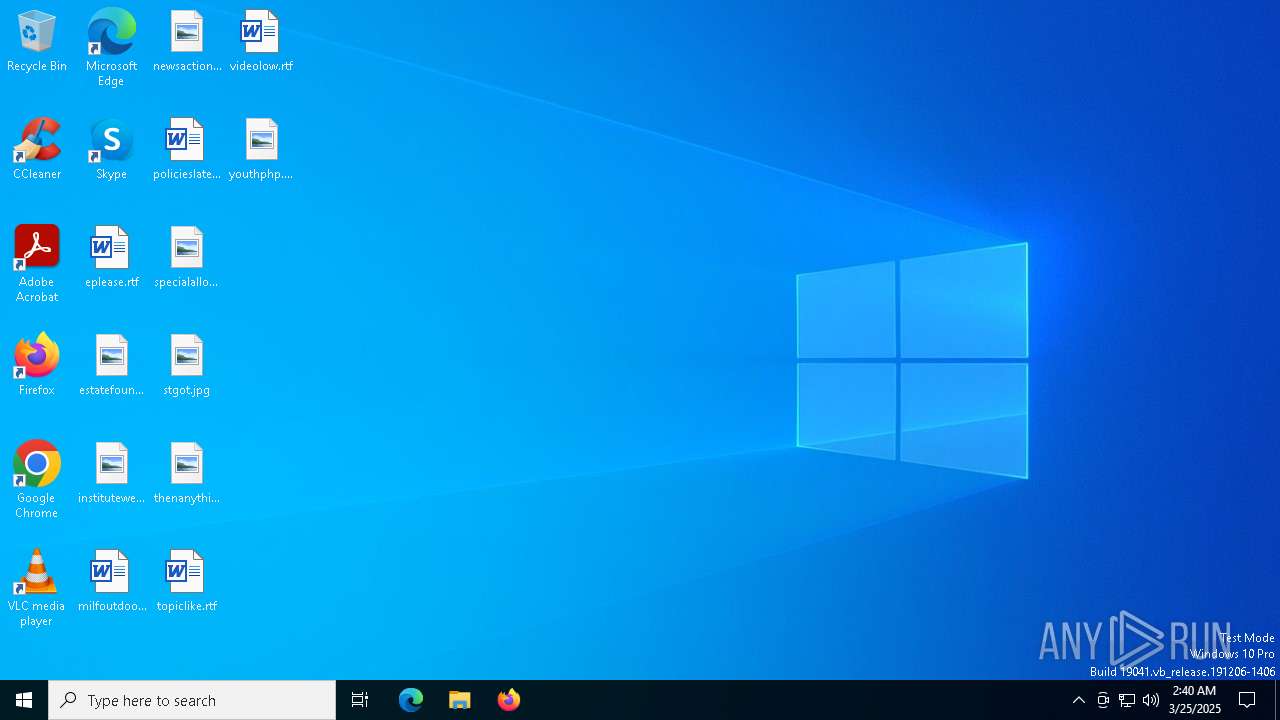
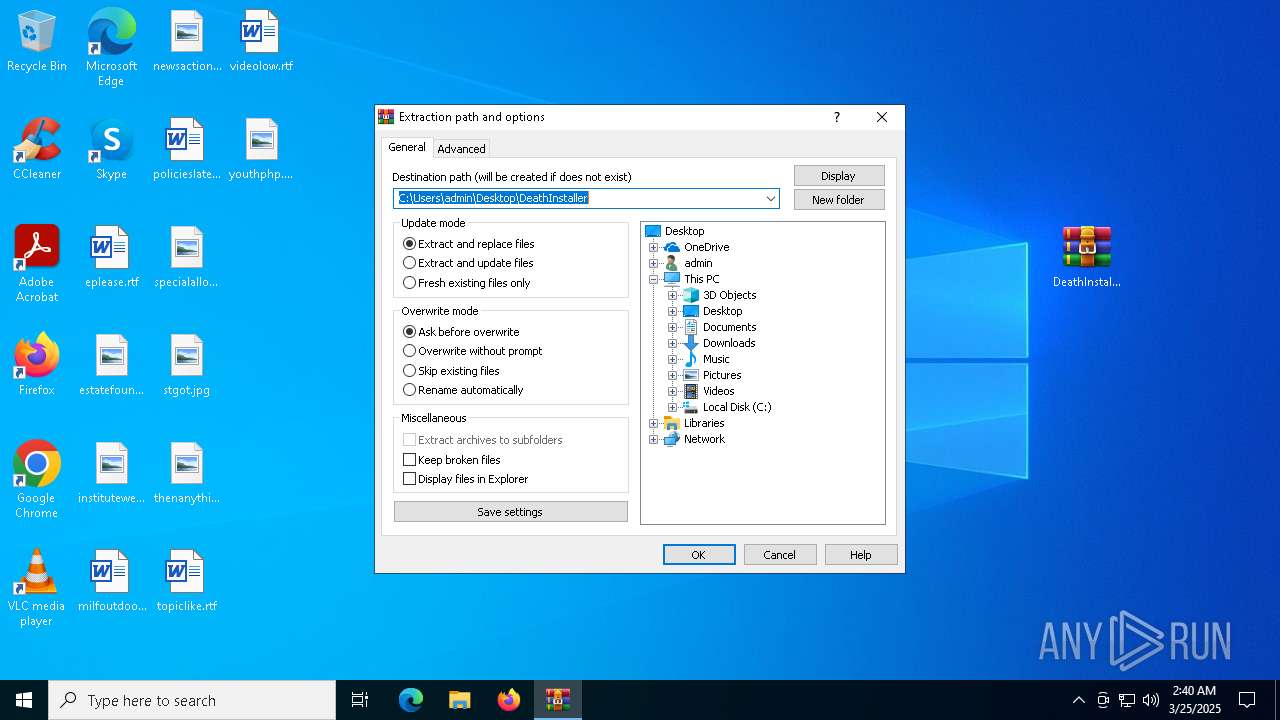
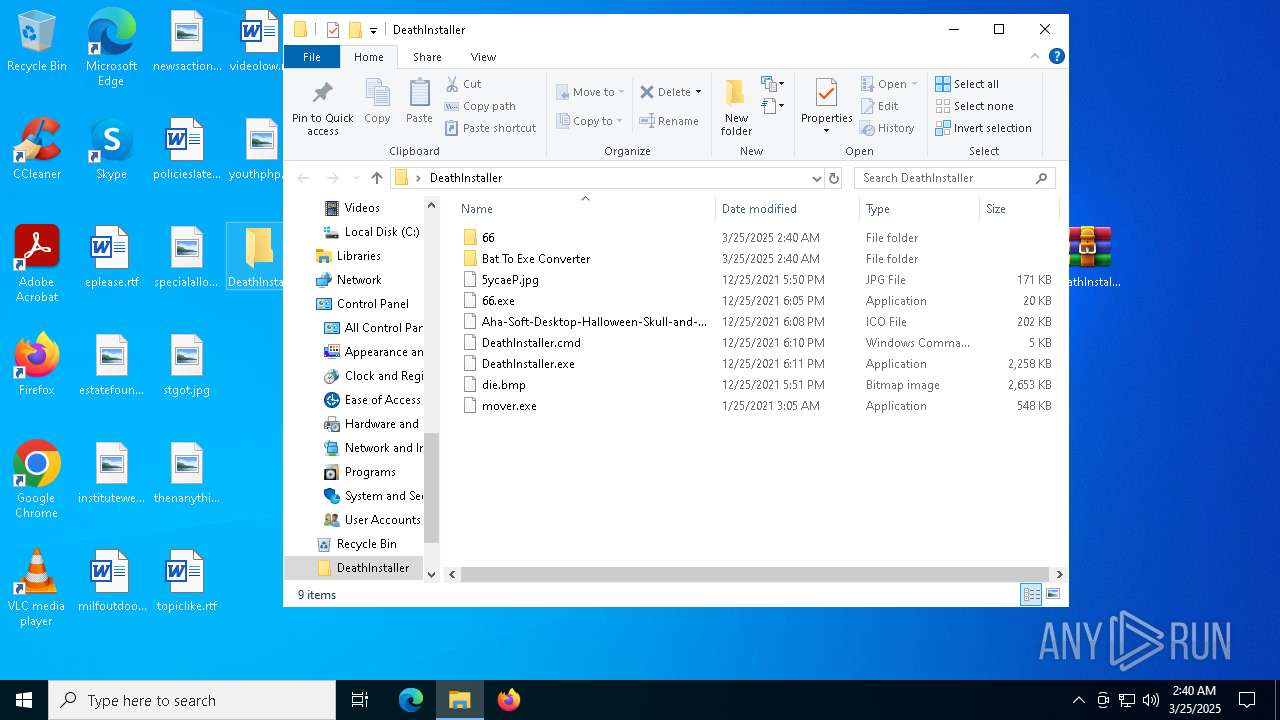
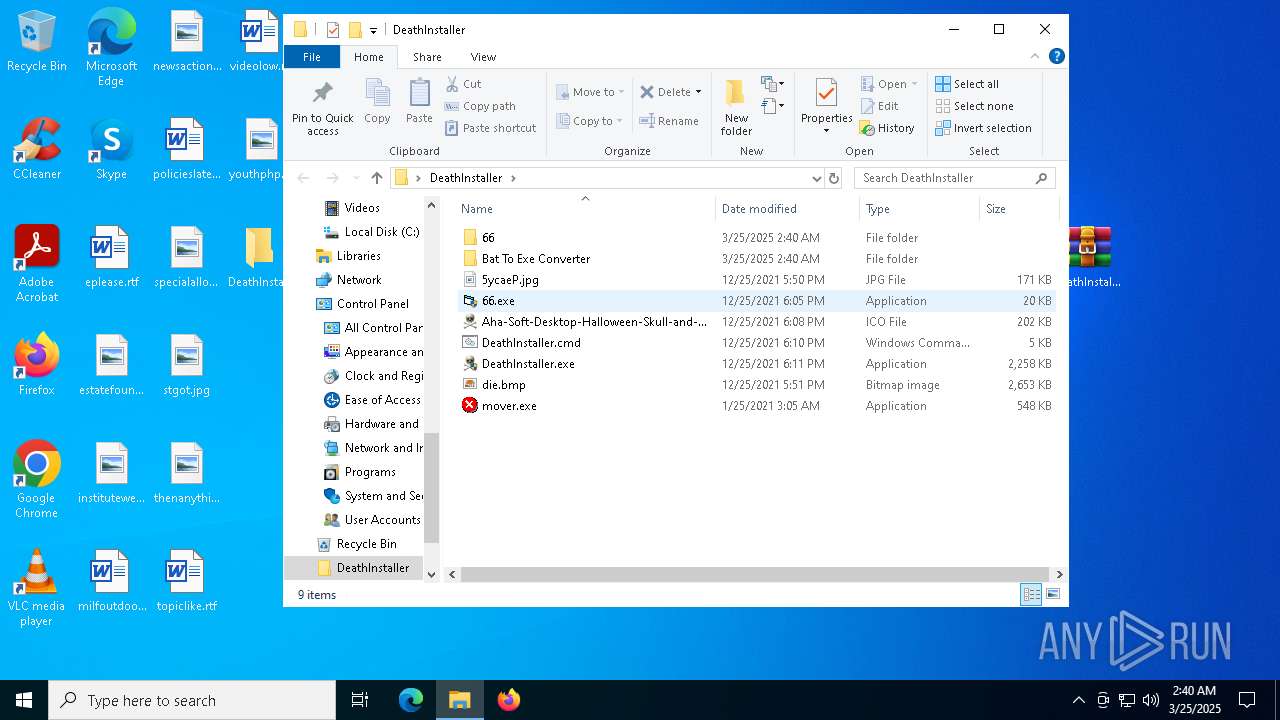
Manual execution by a user
- WinRAR.exe (PID: 6944)
- DeathInstaller.exe (PID: 6184)
- DeathInstaller.exe (PID: 5204)
- 66.exe (PID: 6388)
- mover.exe (PID: 6428)
The sample compiled with german language support
- WinRAR.exe (PID: 6944)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6944)
Create files in a temporary directory
- DeathInstaller.exe (PID: 5204)
Reads the computer name
- DeathInstaller.exe (PID: 5204)
- ShellExperienceHost.exe (PID: 5968)
- 66.exe (PID: 6388)
- PLUGScheduler.exe (PID: 4128)
Checks supported languages
- DeathInstaller.exe (PID: 5204)
- PLUGScheduler.exe (PID: 4128)
- 66.exe (PID: 6388)
- mover.exe (PID: 6428)
- ShellExperienceHost.exe (PID: 5968)
Process checks computer location settings
- DeathInstaller.exe (PID: 5204)
Reads the time zone
- net1.exe (PID: 7464)
Creates files in the program directory
- cmd.exe (PID: 7304)
- PLUGScheduler.exe (PID: 4128)
Autorun file from Startup directory
- cmd.exe (PID: 7304)
Reads mouse settings
- mover.exe (PID: 6428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2021:12:25 17:50:28 |
| ZipCRC: | 0xce266824 |
| ZipCompressedSize: | 175054 |
| ZipUncompressedSize: | 175082 |
| ZipFileName: | 5ycaeP.jpg |
Total processes
279
Monitored processes
24
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3192 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4112 | shutdown /r /t 6 /c "MWAHAHAHAHAHAHAHAHAHAHAHAHAHAHAHAHAHAHA" | C:\Windows\SysWOW64\shutdown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4128 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4996 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\DeathInstaller.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5204 | "C:\Users\admin\Desktop\DeathInstaller\DeathInstaller.exe" | C:\Users\admin\Desktop\DeathInstaller\DeathInstaller.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 5380 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\6C05.tmp\6.vbs" | C:\Windows\SysWOW64\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 1073807364 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 5968 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6184 | "C:\Users\admin\Desktop\DeathInstaller\DeathInstaller.exe" | C:\Users\admin\Desktop\DeathInstaller\DeathInstaller.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 6388 | "C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartUp\66.exe" | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartUp\66.exe | — | explorer.exe | |||||||||||
User: admin Company: BKHN Integrity Level: HIGH Version: 6.06.0006 Modules
| |||||||||||||||
Total events
8 996
Read events
8 945
Write events
38
Delete events
13
Modification events
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\DeathInstaller.zip | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
9
Suspicious files
45
Text files
11
Unknown types
0
Dropped files
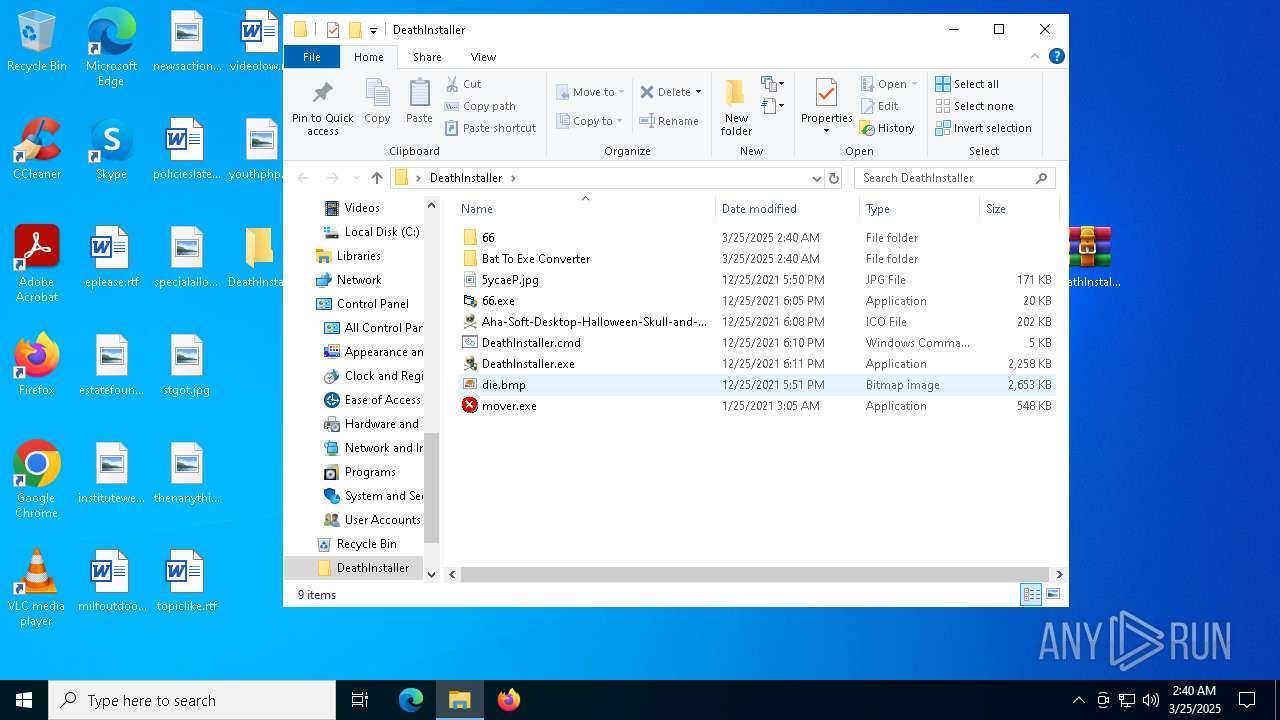
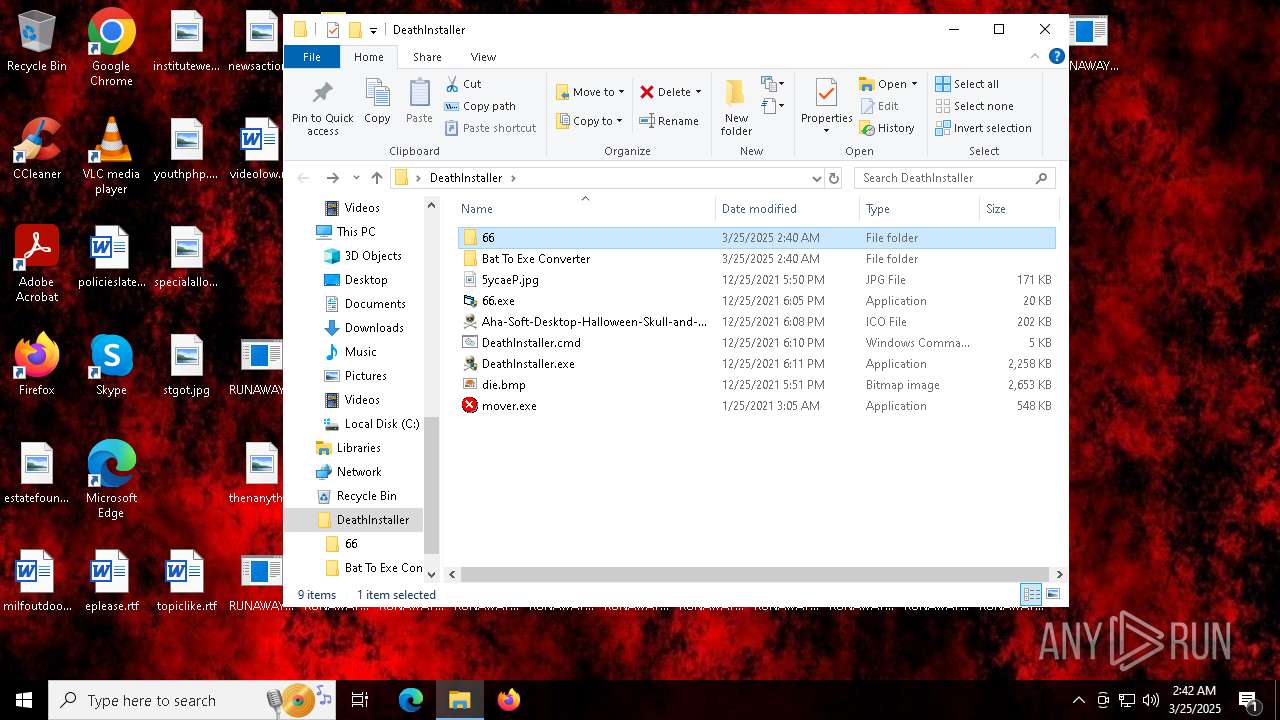
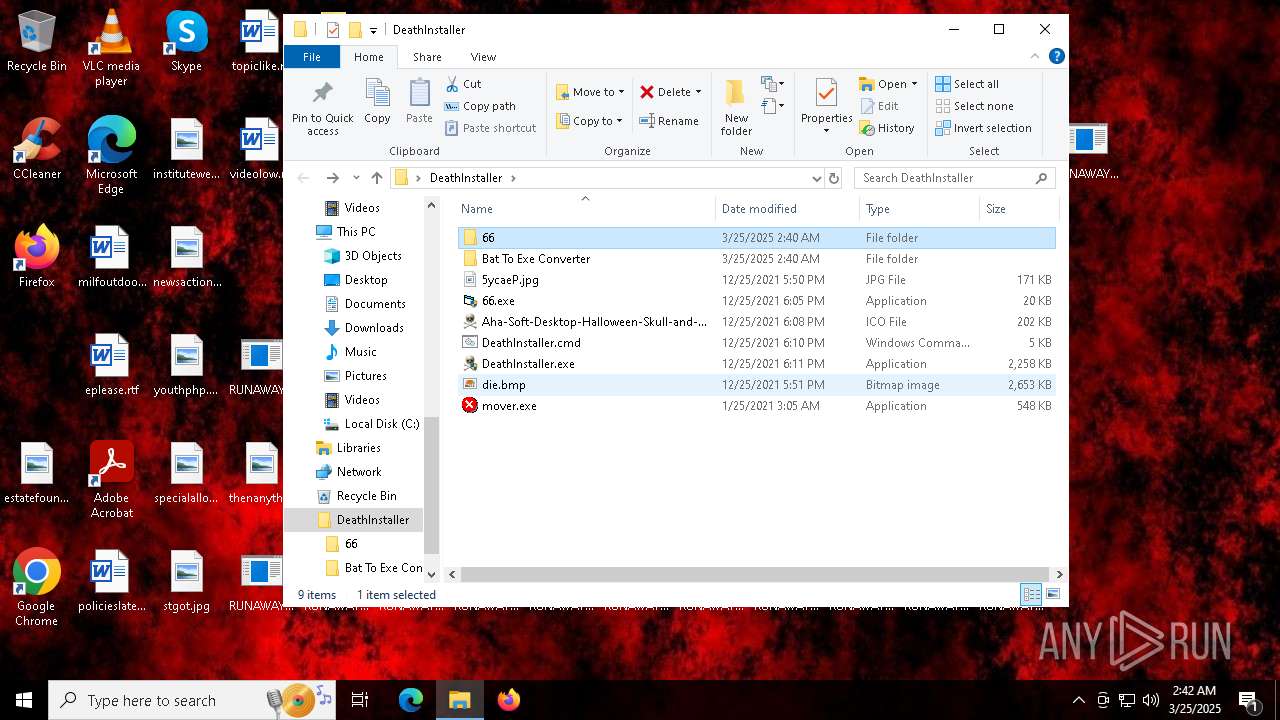
PID | Process | Filename | Type | |
|---|---|---|---|---|
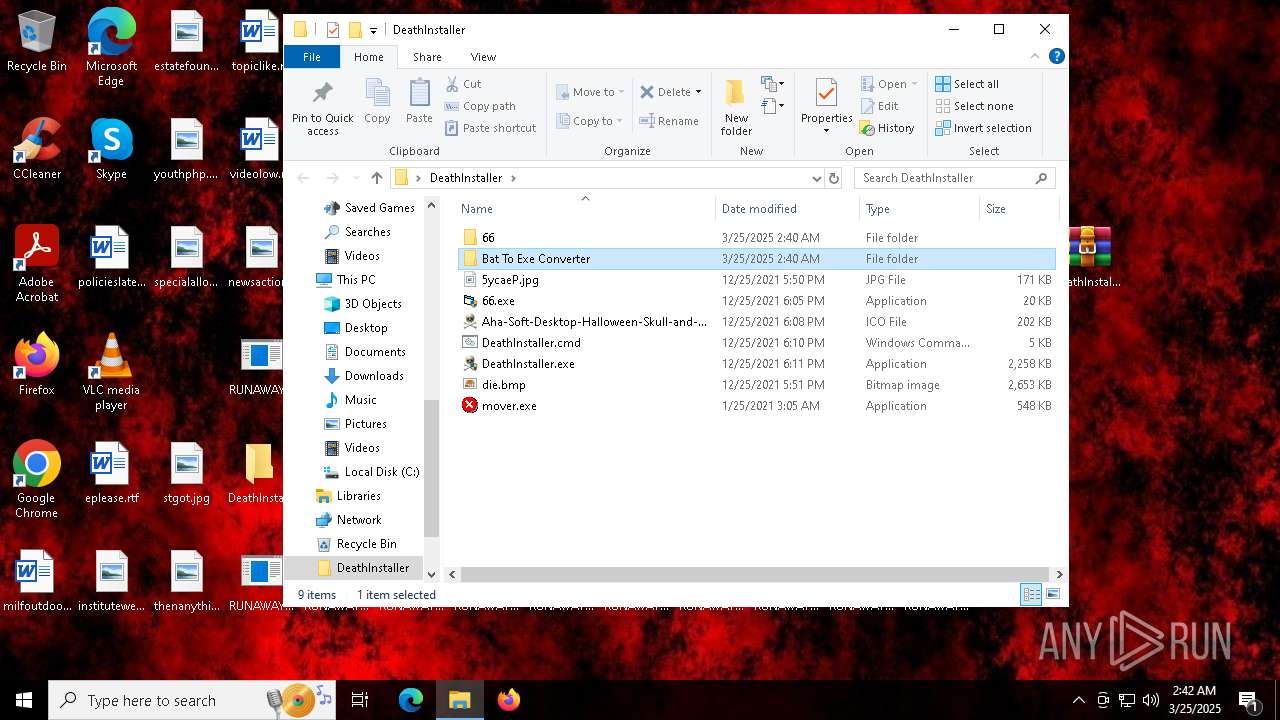
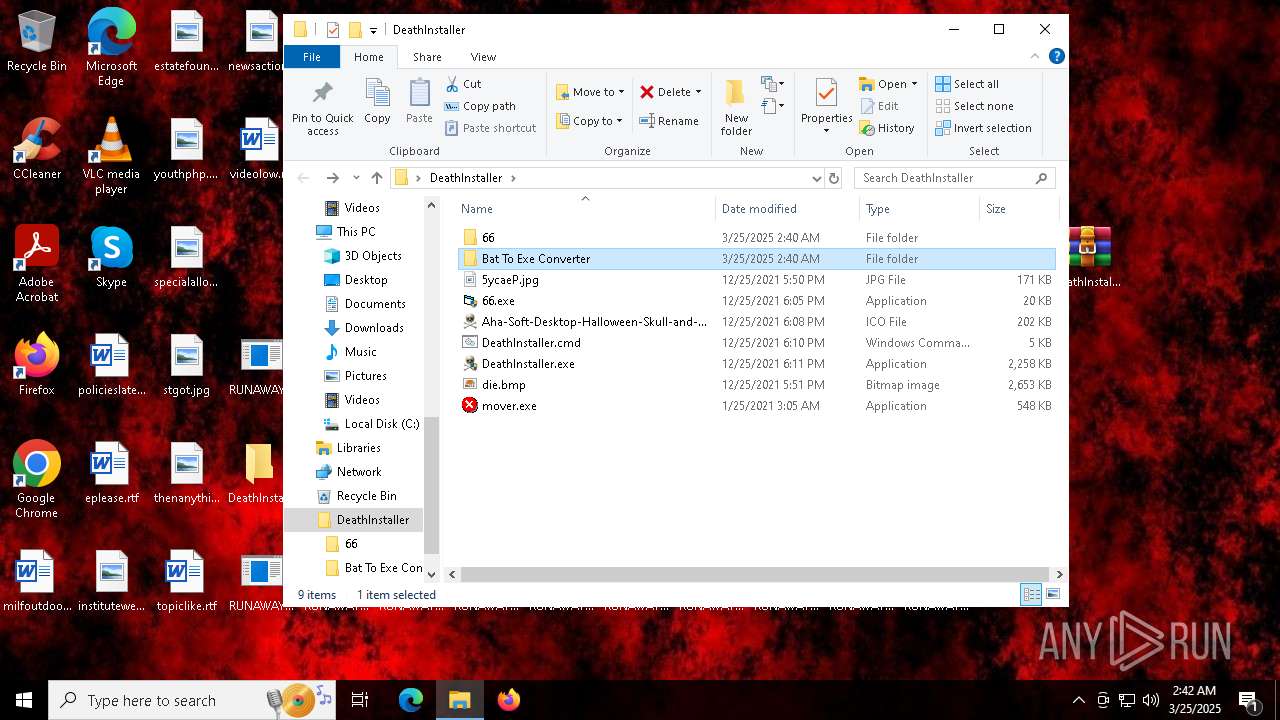
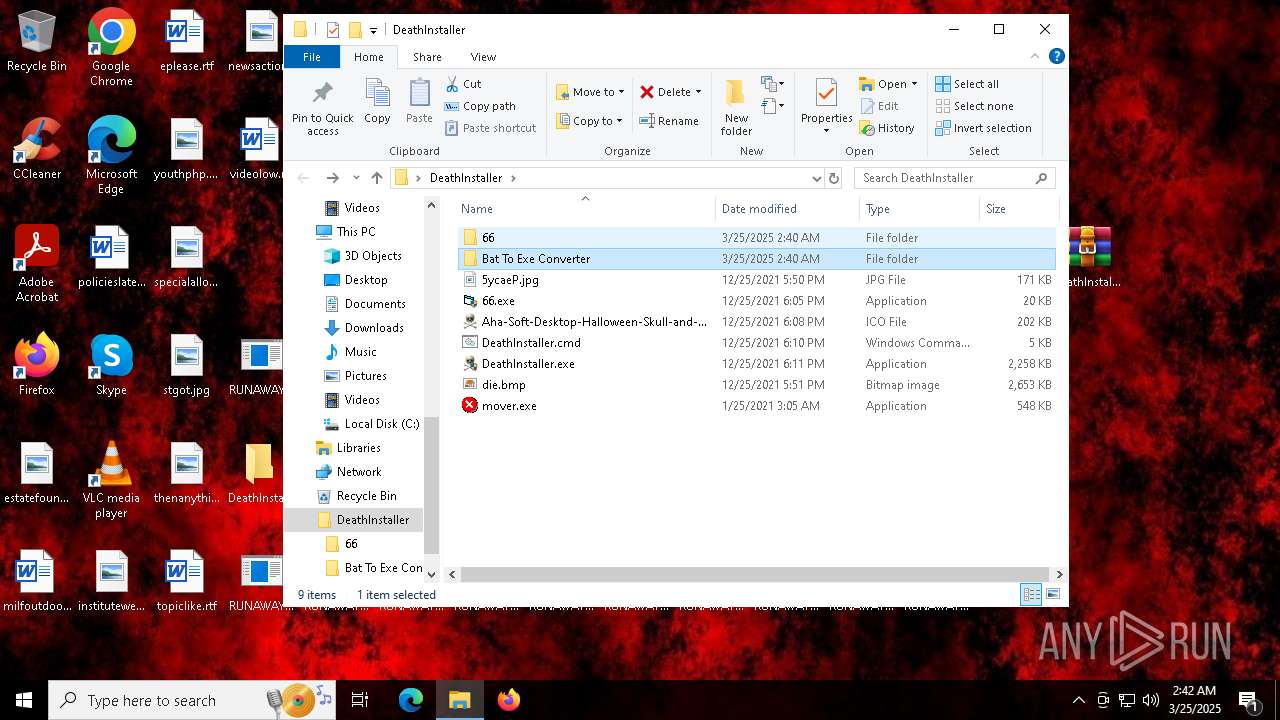
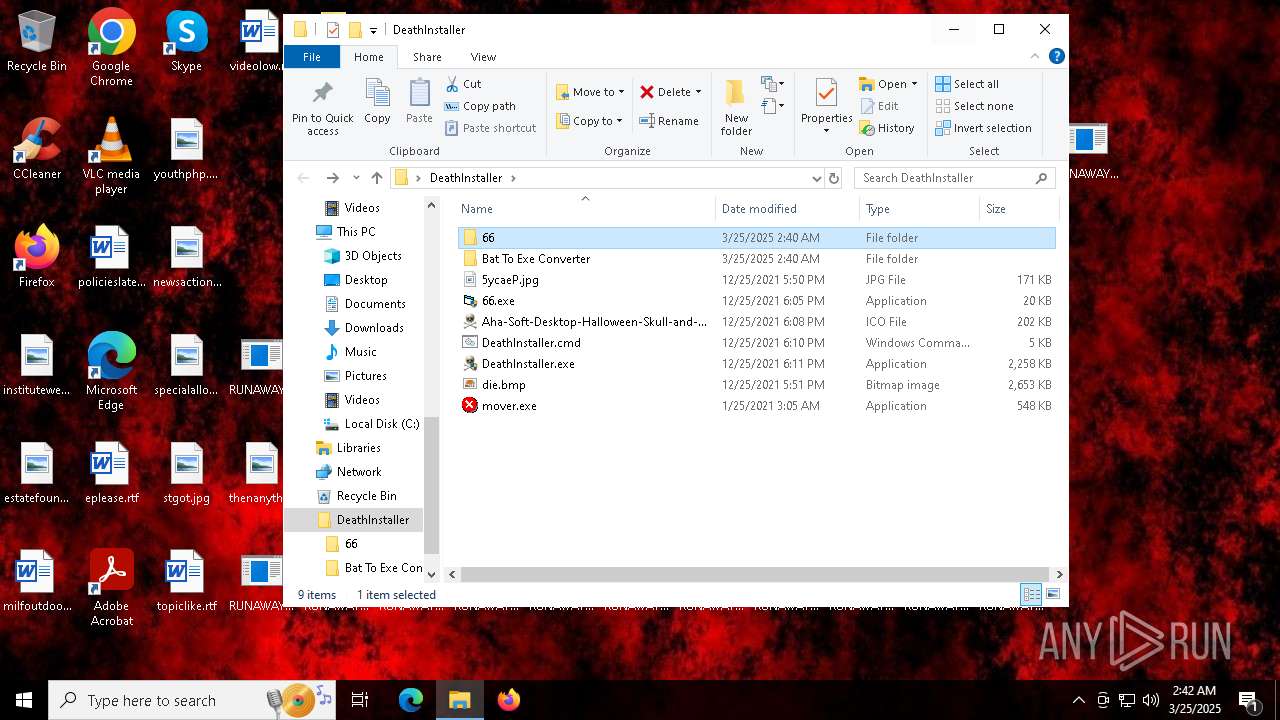
| 6944 | WinRAR.exe | C:\Users\admin\Desktop\DeathInstaller\5ycaeP.jpg | image | |
MD5:9C6C93AC5A80178A218908348F5CE10D | SHA256:E0E995764213C08C9FB1F94A3C3C1AC8DF4147978E87D4E9FE5250EB99143BF5 | |||
| 6944 | WinRAR.exe | C:\Users\admin\Desktop\DeathInstaller\mover.exe | executable | |
MD5:C1978E4080D1EC7E2EDF49D6C9710045 | SHA256:C9E2A7905501745C304FFC5A70B290DB40088D9DC10C47A98A953267468284A8 | |||
| 6944 | WinRAR.exe | C:\Users\admin\Desktop\DeathInstaller\66.exe | executable | |
MD5:06C23607C9981D94284BA00A4F513A7E | SHA256:BAE999E3131BF7BF9680760830CB0D462133F57BA6F8595BDD313C005934F87B | |||
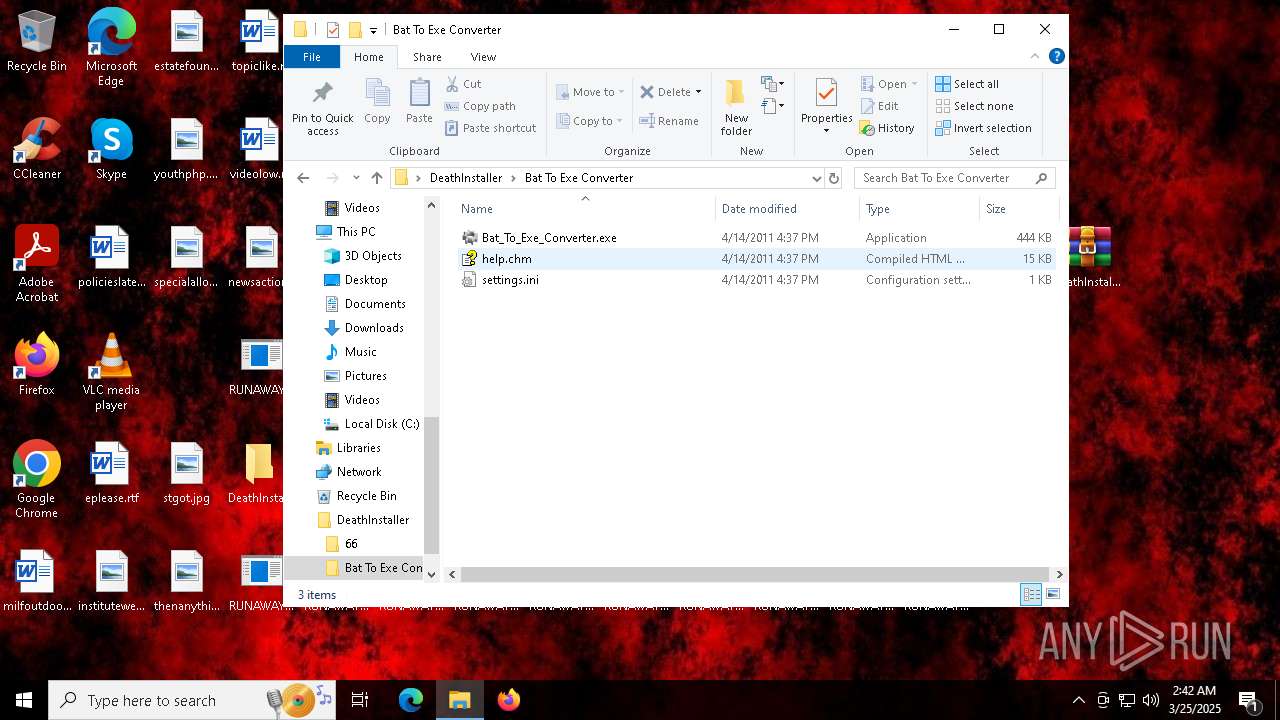
| 6944 | WinRAR.exe | C:\Users\admin\Desktop\DeathInstaller\Bat To Exe Converter\help.chm | binary | |
MD5:FFA8C49B21B077B0DC4B51A1F6F9A753 | SHA256:00037BFC41AFACF262AFDA160E17D3CCA33606276324E99BBD93AD1207E9A7C0 | |||
| 6944 | WinRAR.exe | C:\Users\admin\Desktop\DeathInstaller\Bat To Exe Converter\Bat_To_Exe_Converter.exe | executable | |
MD5:76D5900A4ADF4C1F2AB8DBFD0A450C4A | SHA256:7ADC1F7FF040628A600F99465BD70E71AD83FECFE60B0F1DADC84B5D262FF350 | |||
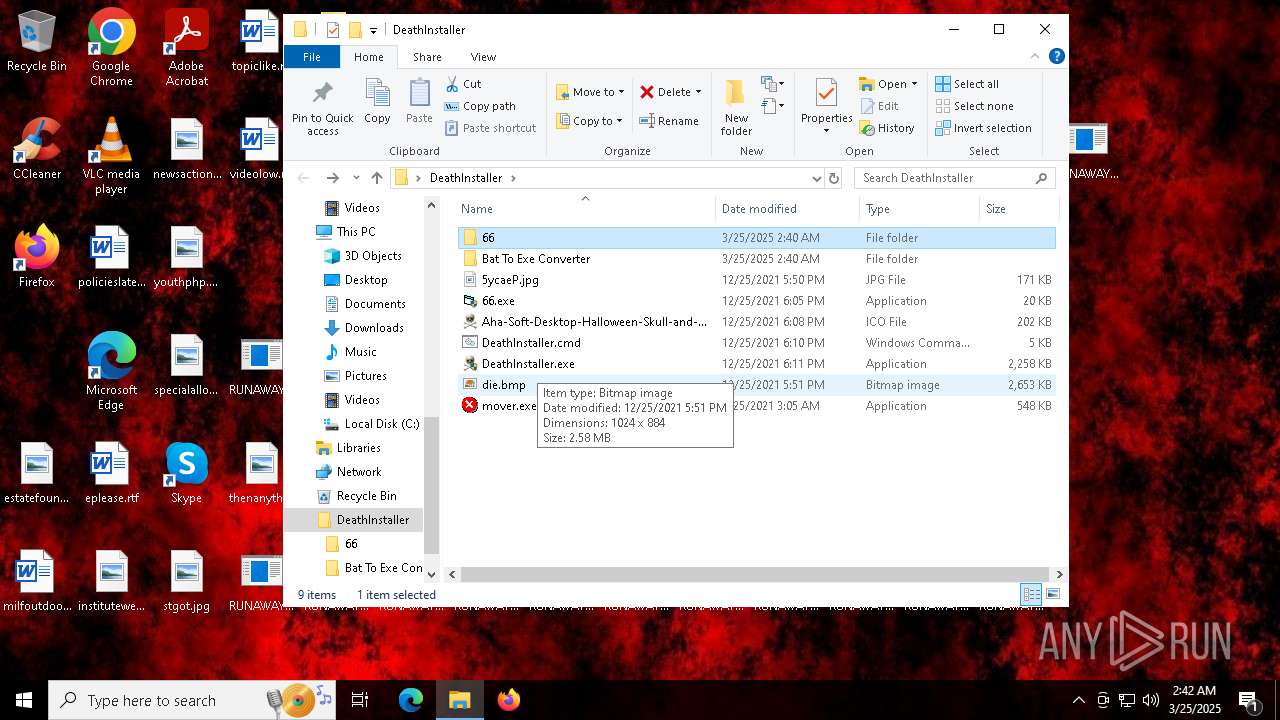
| 5204 | DeathInstaller.exe | C:\Users\admin\AppData\Local\Temp\6C05.tmp\die.bmp | image | |
MD5:F8AD78EFAB2A29DBED7BC585B042ADC0 | SHA256:7C35142AD07231CAE2E14E5E151A48D5824EF8415AF0D84B76C33FB8AC1F6754 | |||
| 5204 | DeathInstaller.exe | C:\Users\admin\AppData\Local\Temp\6C05.tmp\66.exe | executable | |
MD5:06C23607C9981D94284BA00A4F513A7E | SHA256:BAE999E3131BF7BF9680760830CB0D462133F57BA6F8595BDD313C005934F87B | |||
| 6944 | WinRAR.exe | C:\Users\admin\Desktop\DeathInstaller\DeathInstaller.cmd | text | |
MD5:F62A19E44FCCB256E3B7DCA67FEC6237 | SHA256:433A2B16126BBCB92BA07E12C5C07E1EBB4FB56C84A0B28D550BF49C7ED82B92 | |||
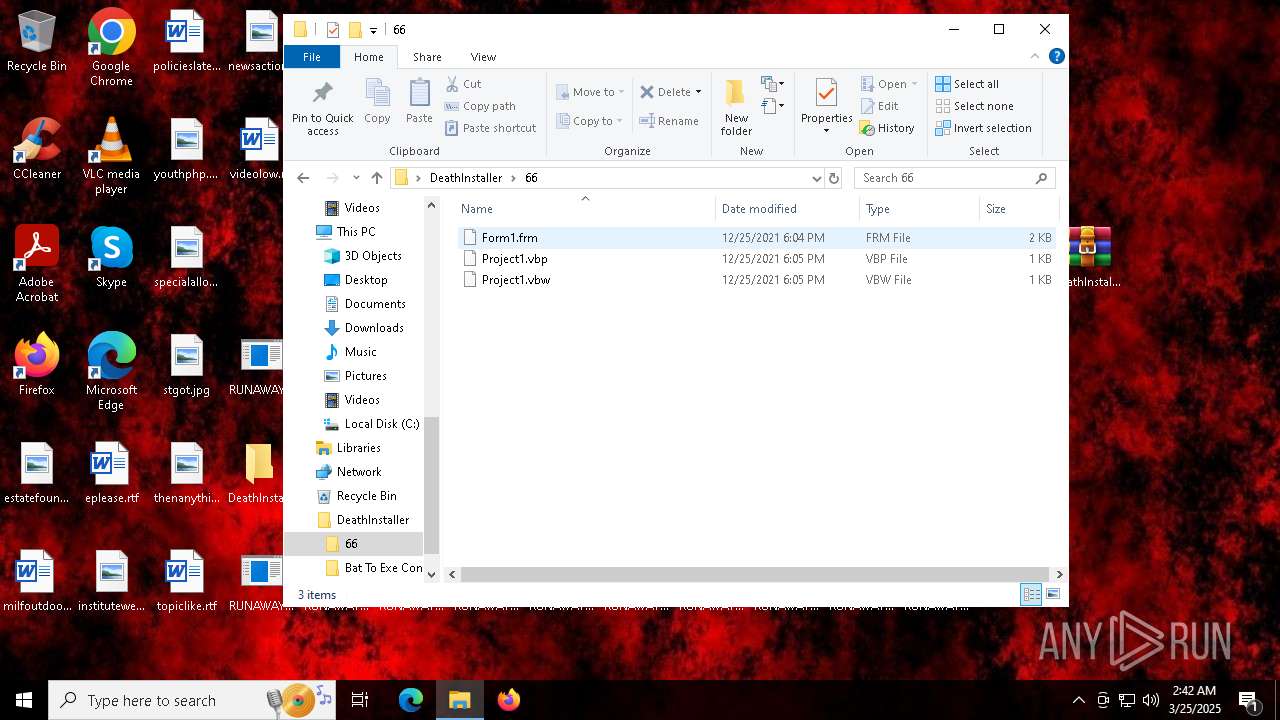
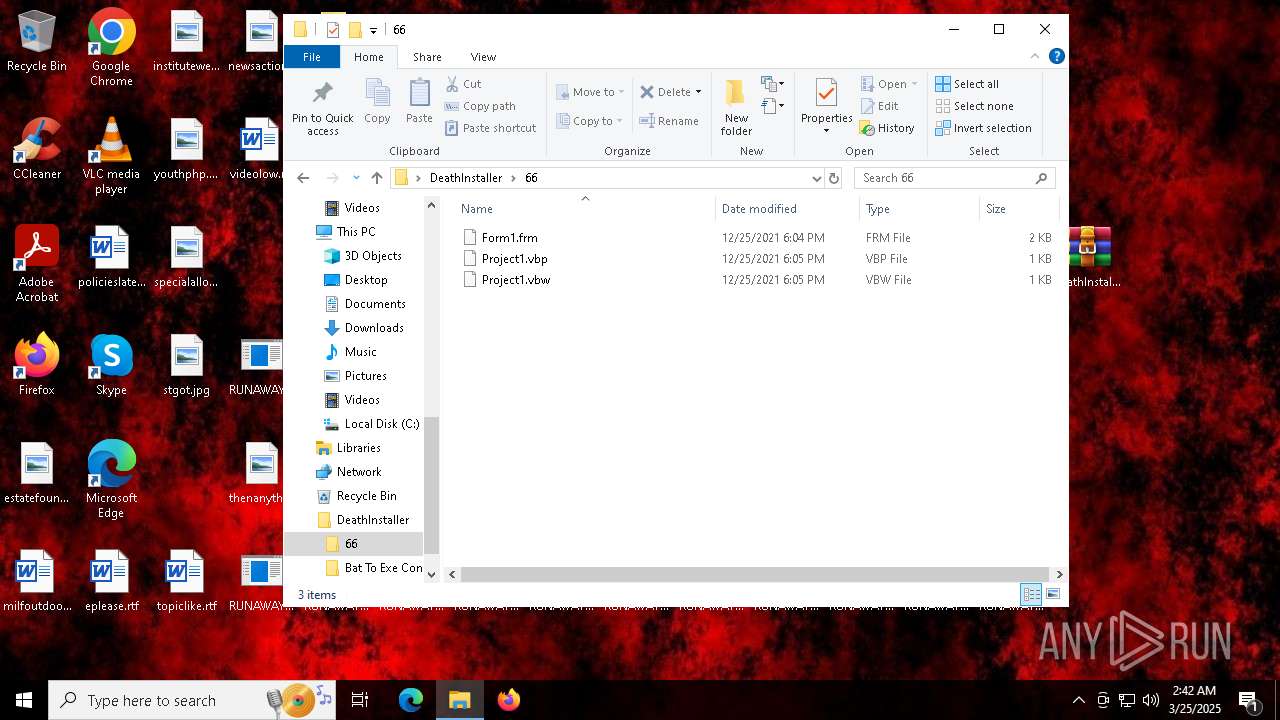
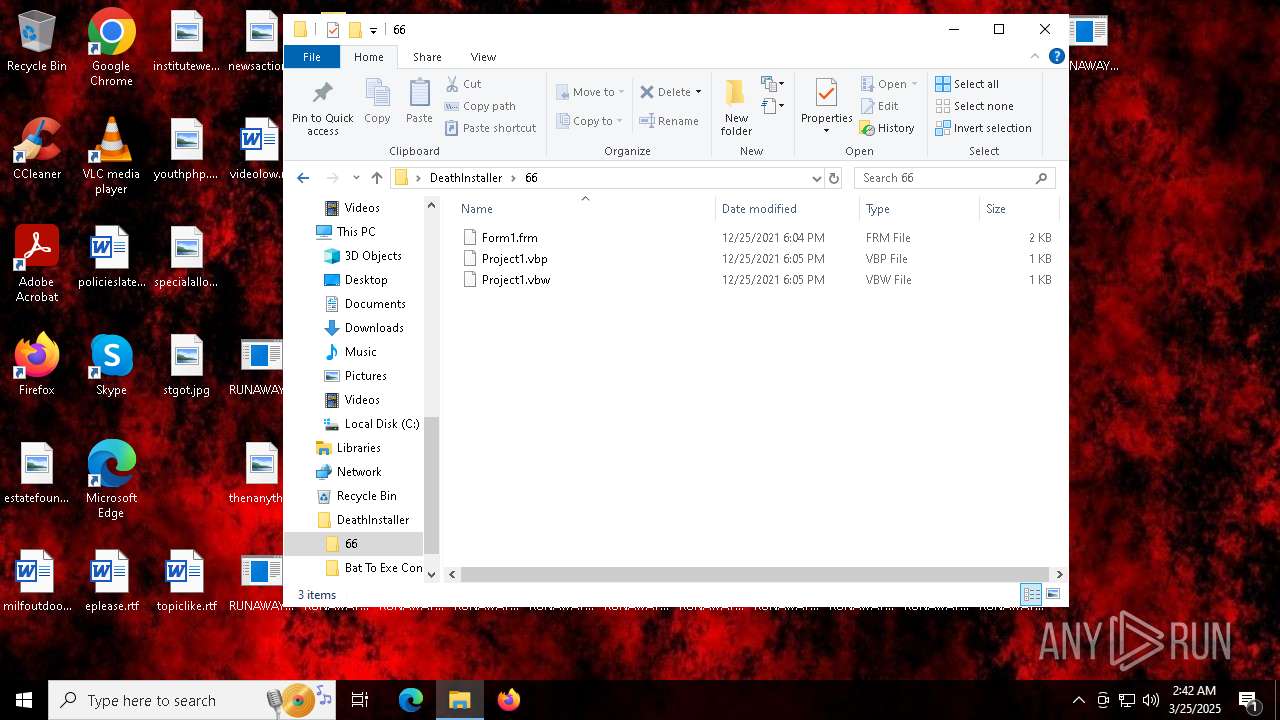
| 6944 | WinRAR.exe | C:\Users\admin\Desktop\DeathInstaller\66\Project1.vbw | text | |
MD5:CCE9A95961E640314F609859E8E13C13 | SHA256:EE6448888E70136944EC7B513B81CE5174F9B9EAD9E41F93E2A6D06164E52DB5 | |||
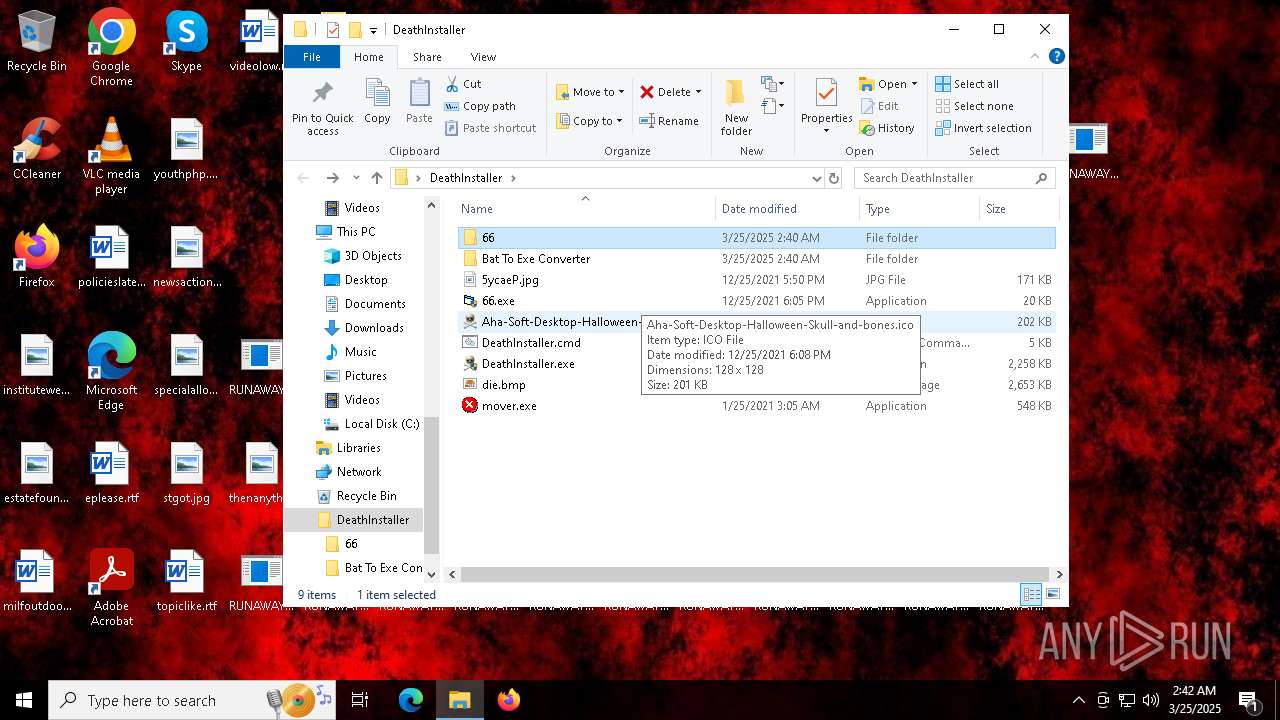
| 6944 | WinRAR.exe | C:\Users\admin\Desktop\DeathInstaller\Aha-Soft-Desktop-Halloween-Skull-and-bones.ico | image | |
MD5:F5870F60AB13F8EB4D633D87E21F360A | SHA256:E5FFD59A5D6BF1F1E62B60AD449D2DA9BF34990FA8CD00CD19B6A9C722626B33 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
42
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7556 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8016 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5224 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8016 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.160.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7556 | backgroundTaskHost.exe | 20.223.36.55:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7556 | backgroundTaskHost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |