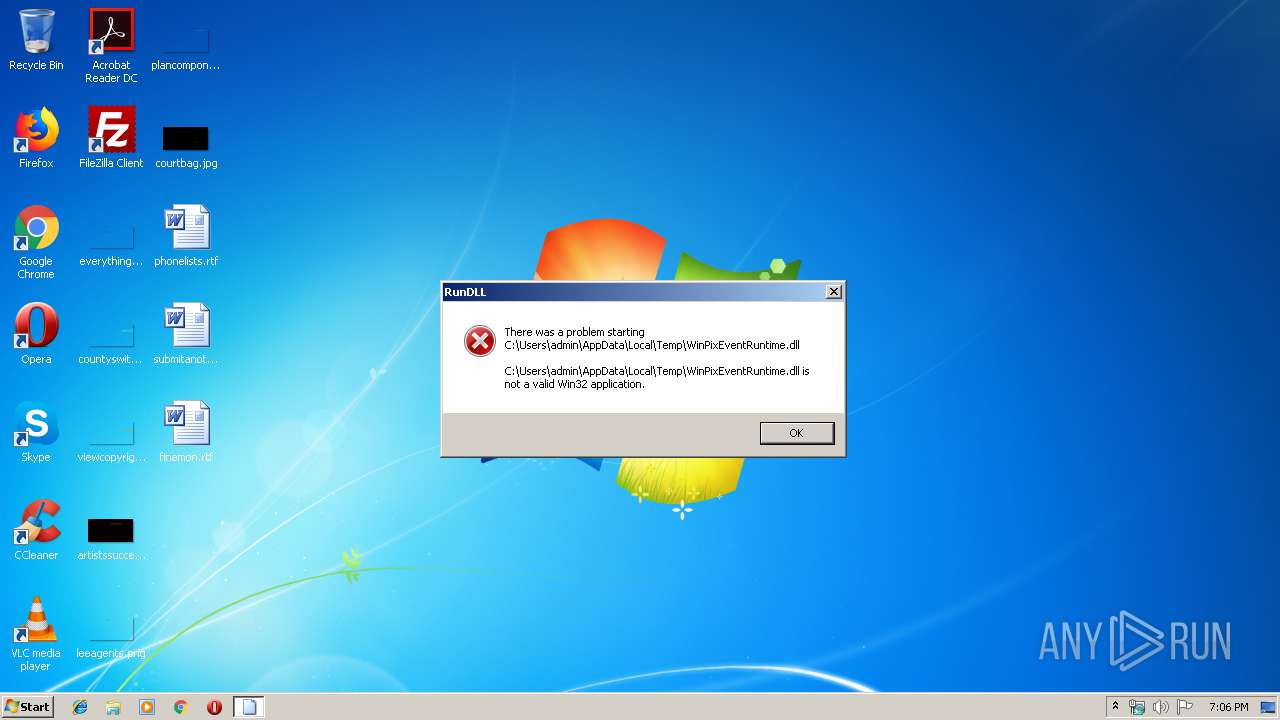
| File name: | WinPixEventRuntime.dll |
| Full analysis: | https://app.any.run/tasks/072fd4a9-4bcc-43c7-9987-f1eadb3b5c9a |
| Verdict: | No threats detected |
| Analysis date: | November 29, 2019, 19:06:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (DLL) (GUI) x86-64, for MS Windows |
| MD5: | AE4D6C34422B85BFA2E99A456FC4C733 |
| SHA1: | BBFB4B08C694FF7DF134939A19F05EAC0C84A816 |
| SHA256: | 2F84A7583F08064F55AC9EA3426F898E1BEF6F408FECEE22C1F5567601E70123 |
| SSDEEP: | 384:6/30skuKCMqwvuULtj+K9tX2jBcZaXB5wGlq47zvQHVsrHJWZvkA80aq0GftpBj3:iECMEULtj+RaI0GlqYSusQiC6bcy1oY |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2017:01:26 18:20:43+01:00 |
| PEType: | PE32+ |
| LinkerVersion: | 14 |
| CodeSize: | 14336 |
| InitializedDataSize: | 16792064 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x37b0 |
| OSVersion: | 10 |
| ImageVersion: | 1701.26001 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.1701.26001 |
| ProductVersionNumber: | 1.0.1701.26001 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | WinPixEventRuntime.dll |
| FileVersion: | 1.0.1701.26001 |
| InternalName: | WinPixEventRuntime |
| LegalCopyright: | ©Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WinPixEventRuntime.dll |
| ProductVersion: | 1.0.170126001 |
| ProductName: | PIX |
| Comments: | PIX_master_1701.26001 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_AMD64 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Jan-2017 17:20:43 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | WinPixEventRuntime.dll |
| FileVersion: | 1.0.1701.26001 |
| InternalName: | WinPixEventRuntime |
| LegalCopyright: | ©Microsoft Corporation. All rights reserved. |
| OriginalFilename: | WinPixEventRuntime.dll |
| ProductVersion: | 1.0.170126001 |
| ProductName: | PIX |
| Comments: | PIX_master_1701.26001 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_AMD64 |
| Number of sections: | 7 |
| Time date stamp: | 26-Jan-2017 17:20:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00F0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000036A5 | 0x00003800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.17143 |
.rdata | 0x00005000 | 0x00001B98 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.47748 |
.data | 0x00007000 | 0x01000EF0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29022 |
.pdata | 0x01008000 | 0x000003FC | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.1352 |
.tls | 0x01009000 | 0x00000029 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0100A000 | 0x000005B0 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.0051 |
.reloc | 0x0100B000 | 0x00000068 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 1.40194 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.45748 | 908 | UNKNOWN | English - United States | RT_VERSION |
2 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
KERNEL32.dll |
MSVCP140.dll |
VCRUNTIME140.dll |
api-ms-win-crt-heap-l1-1-0.dll |
api-ms-win-crt-runtime-l1-1-0.dll |
api-ms-win-crt-stdio-l1-1-0.dll |
api-ms-win-crt-string-l1-1-0.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
PEvtGetTimeRange | 1 | 0x00001930 |
PEvtGetTimeRangeEvent | 2 | 0x00001960 |
PEvtResetService | 3 | 0x000017C0 |
PEvtSetState | 4 | 0x00001EE0 |
PEvtStartService | 5 | 0x00001650 |
PEvtStartServiceEx | 6 | 0x00001660 |
PEvtStopService | 7 | 0x00001720 |
PEvtSweepBlks | 8 | 0x00001D80 |
PEvtSweepBlksRange | 9 | 0x00001DA0 |
PIXStartEventTrace | 10 | 0x00001150 |
Total processes
33
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\WinPixEventRuntime.dll", PEvtGetTimeRange | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report