| File name: | BandiView.exe |
| Full analysis: | https://app.any.run/tasks/f36e5cc2-5fa8-4e5a-8da0-aaac396db062 |
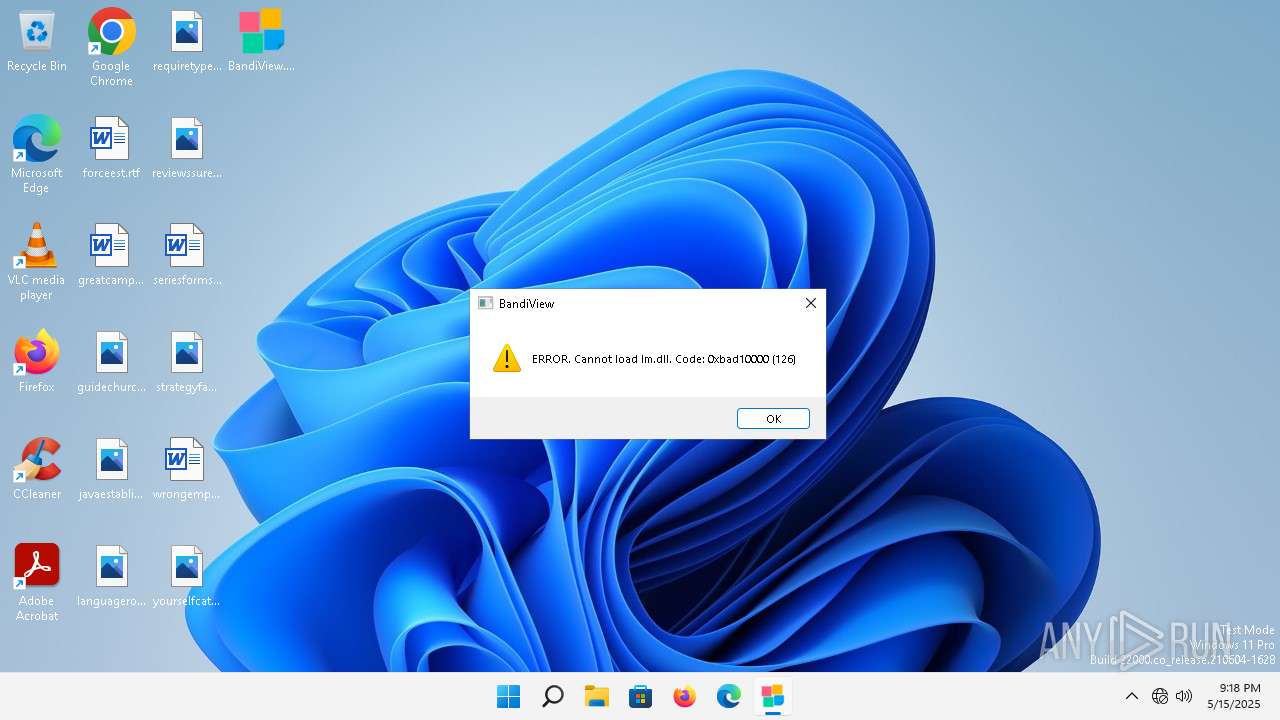
| Verdict: | Malicious activity |
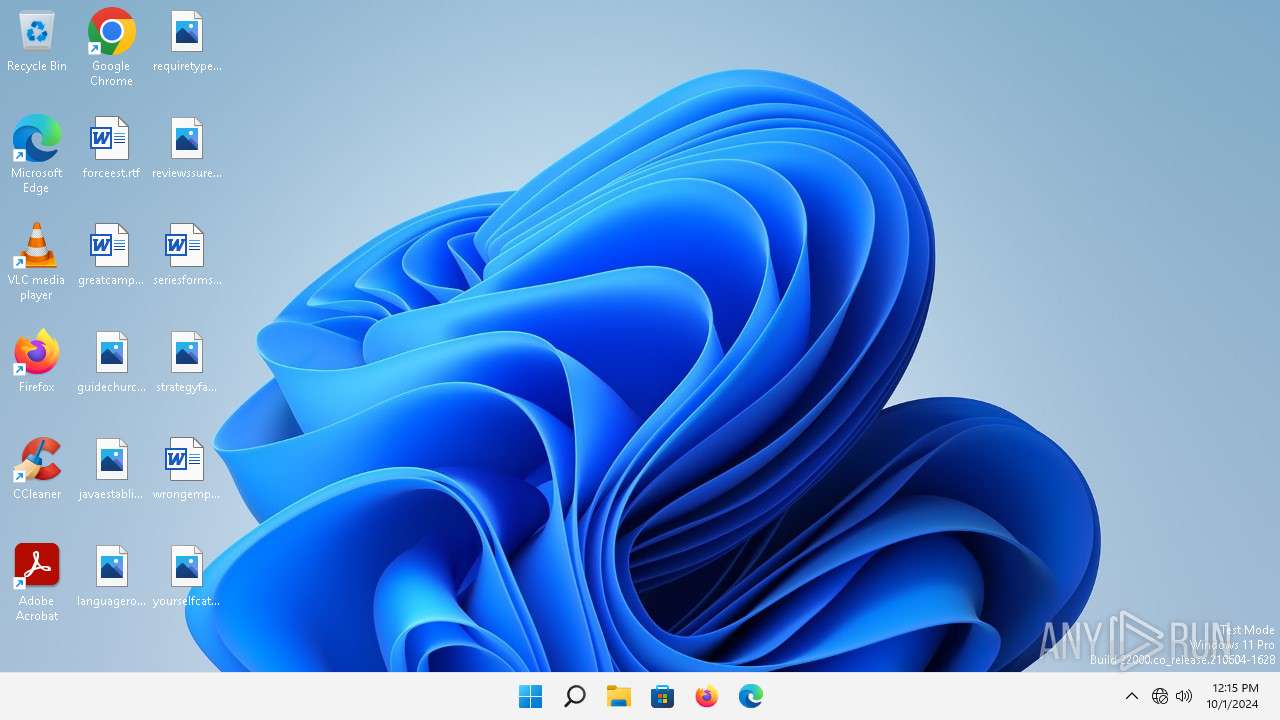
| Analysis date: | May 15, 2025, 21:18:45 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 10 sections |
| MD5: | 3DA4851E8B808B346158A3B5301D876C |
| SHA1: | 4431A857D466F3F272F248DF44EC0CB44EFA5ABA |
| SHA256: | 2F6C4433BF6B43C696F940225990CAD8DD0CEE574C3082F316B8AABD8912806E |
| SSDEEP: | 98304:Q43EWdl35DyJvyHrn2MnIe4XEv6eeE23t00uRlrz5KlFs6D3MBF+4XqZAsDt+sYx:MSL558xTomy |
MALICIOUS
Executing a file with an untrusted certificate
- BandiView.exe (PID: 1784)
SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- BandiView.exe (PID: 1784)
The sample compiled with korean language support
- BandiView.exe (PID: 1784)
Reads the computer name
- BandiView.exe (PID: 1784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:04 08:37:01+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.43 |
| CodeSize: | 5355520 |
| InitializedDataSize: | 1920512 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x426990 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.16.0.1 |
| ProductVersionNumber: | 7.16.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Korean |
| CharacterSet: | Unicode |
| CompanyName: | Bandisoft International Inc. |
| FileDescription: | BandiView Image viewer |
| FileVersion: | 7.16.0.1 |
| InternalName: | BandiView.exe |
| LegalCopyright: | Copyright(C) 2023-2025 Bandisoft International Inc. All rights reserved. |
| OriginalFileName: | BandiView.exe |
| ProductName: | BandiView |
| ProductVersion: | 7.16.0.1 |
Total processes
100
Monitored processes
1
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1784 | "C:\Users\admin\Desktop\BandiView.exe" | C:\Users\admin\Desktop\BandiView.exe | — | explorer.exe | |||||||||||
User: admin Company: Bandisoft International Inc. Integrity Level: MEDIUM Description: BandiView Image viewer Version: 7.16.0.1 Modules
| |||||||||||||||
Total events
18
Read events
18
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
12
DNS requests
9
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1748 | smartscreen.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5a549681eae53e7f | unknown | — | — | whitelisted |
1352 | svchost.exe | GET | 200 | 184.24.77.20:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?cd93d97035913c62 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?9a78fd978e6e7371 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?3e0b4dd42efe063e | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?966e481a9fe01acd | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1352 | svchost.exe | 184.24.77.20:80 | — | Akamai International B.V. | DE | unknown |
1748 | smartscreen.exe | 48.209.164.47:443 | checkappexec.microsoft.com | — | US | whitelisted |
1748 | smartscreen.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
5336 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4788 | svchost.exe | 23.197.142.186:443 | fs.microsoft.com | Akamai International B.V. | US | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2988 | OfficeClickToRun.exe | 20.189.173.9:443 | self.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2768 | svchost.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
3640 | svchost.exe | 40.126.31.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
checkappexec.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
dns.msftncsi.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
1352 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |