| File name: | ar32e301(3).exe |
| Full analysis: | https://app.any.run/tasks/35afb1b1-d1fe-4e09-86c8-e5b206697104 |
| Verdict: | Suspicious activity |
| Analysis date: | April 02, 2019, 17:40:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CA24E2EE63FAAB14C985C4C6DC43F063 |
| SHA1: | 252E617E48A646FBFCA465328CFF3455977FDACA |
| SHA256: | 2F68E82DE117A3D0D81BAAB111FC56213A61C230416A2C5D33143F1EEA4C5EA3 |
| SSDEEP: | 98304:NTBEtVeVRFogQJcRqTdrp5vfJmTvUbdnaniNqEtlOV+c+Z:NTKrOHBVq3RfoqaiNqE3OV+c+Z |
MALICIOUS
Application was dropped or rewritten from another process
- _INS0432._MP (PID: 480)
SUSPICIOUS
Executable content was dropped or overwritten
- ar32e301(3).exe (PID: 2116)
- ntvdm.exe (PID: 2372)
Starts application with an unusual extension
- ntvdm.exe (PID: 2372)
Creates files in the Windows directory
- ntvdm.exe (PID: 2372)
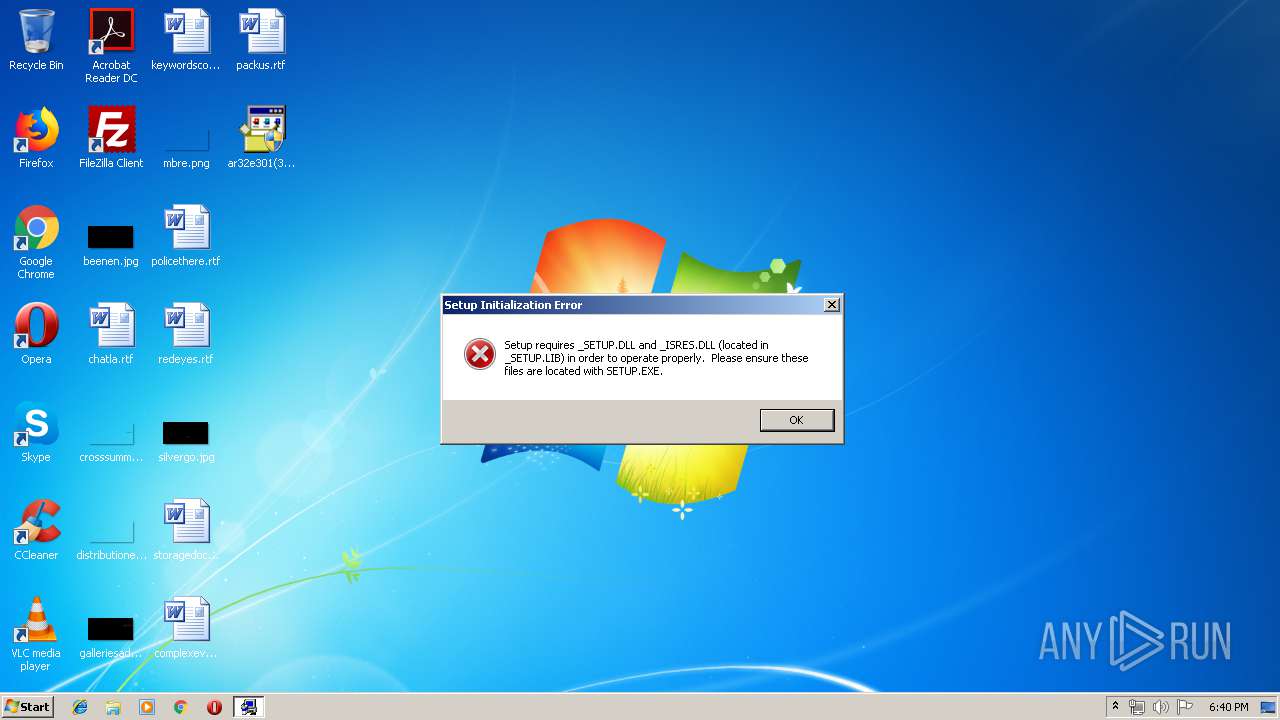
Executes application which crashes
- ar32e301(3).exe (PID: 2116)
Removes files from Windows directory
- _INS0432._MP (PID: 480)
- ntvdm.exe (PID: 2372)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
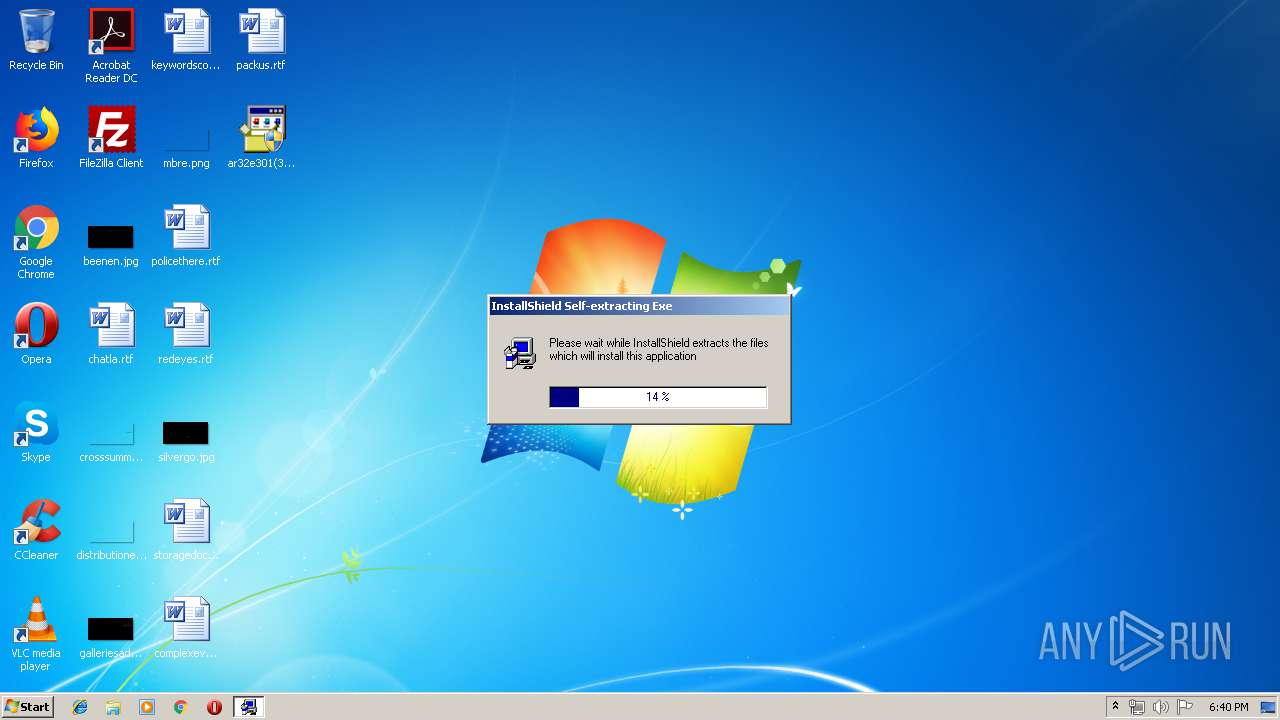
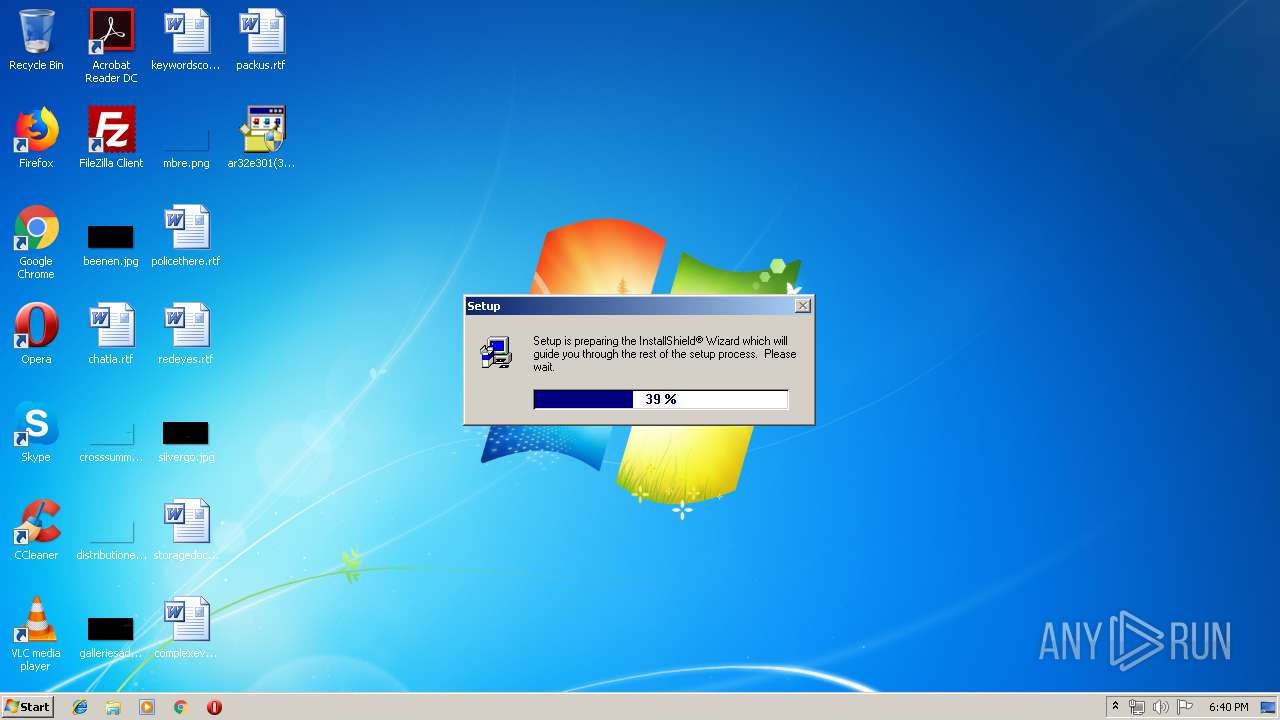
| .exe | | | InstallShield setup (33) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (23.9) |
| .exe | | | Win64 Executable (generic) (21.2) |
| .scr | | | Windows screen saver (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1997:04:25 20:27:31+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 3 |
| CodeSize: | 70656 |
| InitializedDataSize: | 33280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xcc10 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Apr-1997 18:27:31 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 25-Apr-1997 18:27:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000112AA | 0x00011400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45548 |
.rdata | 0x00013000 | 0x0000022D | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.85702 |
.data | 0x00014000 | 0x00004AD0 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.57957 |
.idata | 0x00019000 | 0x00000C30 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.96331 |
.rsrc | 0x0001A000 | 0x0000125C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.12 |
.reloc | 0x0001C000 | 0x00000EC2 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.69844 |
_cabinet | 0x0001D000 | 0x003BE000 | 0x003BD200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 7.99905 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.2638 | 1086 | UNKNOWN | English - United States | RT_STRING |
2 | 3.60545 | 296 | UNKNOWN | English - United States | RT_ICON |
3 | 3.4797 | 744 | UNKNOWN | English - United States | RT_ICON |
99 | 2.37086 | 34 | UNKNOWN | English - United States | RT_GROUP_ICON |
101 | 3.29104 | 392 | UNKNOWN | English - United States | RT_DIALOG |
102 | 3.36783 | 362 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.32322 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
MYRESOURCE | 3.47712 | 422 | UNKNOWN | English - United States | UNKNOWN |
Imports
GDI32.dll |
KERNEL32.dll |
USER32.dll |
Total processes
38
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 480 | C:\Users\admin\AppData\Local\Temp\_INS0432._MP -sms -fC:\USERS\ADMIN\APPDATA\LOCAL\TEMP\~EXB0000\SETUP.INS -z1 -cx -xC:\Users\admin\AppData\Local\Temp\ | C:\Users\admin\AppData\Local\Temp\_INS0432._MP | — | ntvdm.exe | |||||||||||
User: admin Company: InstallShield Corporation, Inc. Integrity Level: HIGH Description: InstallShield Engine EXE Exit code: 0 Version: 3.00.107.0 Modules
| |||||||||||||||
| 1920 | "C:\Users\admin\Desktop\ar32e301(3).exe" | C:\Users\admin\Desktop\ar32e301(3).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 | |||||||||||||||
| 2116 | "C:\Users\admin\Desktop\ar32e301(3).exe" | C:\Users\admin\Desktop\ar32e301(3).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2372 | "C:\Windows\system32\ntvdm.exe" -i1 -ws | C:\Windows\system32\ntvdm.exe | ar32e301(3).exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
8
Read events
8
Write events
0
Delete events
0
Modification events
Executable files
6
Suspicious files
4
Text files
10
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2116 | ar32e301(3).exe | C:\USERS\ADMIN\APPDATA\LOCAL\TEMP\~EXB0000\~IS_CMPX.~~~ | — | |
MD5:— | SHA256:— | |||
| 2372 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs488F.tmp | — | |
MD5:— | SHA256:— | |||
| 2372 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs4890.tmp | — | |
MD5:— | SHA256:— | |||
| 2116 | ar32e301(3).exe | C:\Users\admin\AppData\Local\Temp\~EXB0000\abcpydoc.ini | text | |
MD5:— | SHA256:— | |||
| 2116 | ar32e301(3).exe | C:\Users\admin\AppData\Local\Temp\~EXB0000\setup.ins | ins | |
MD5:— | SHA256:— | |||
| 2116 | ar32e301(3).exe | C:\Users\admin\AppData\Local\Temp\~EXB0000\archive.z | compressed | |
MD5:— | SHA256:— | |||
| 2116 | ar32e301(3).exe | C:\Users\admin\AppData\Local\Temp\~EXB0000\_setup.lib | compressed | |
MD5:— | SHA256:— | |||
| 2372 | ntvdm.exe | C:\Windows\_delis43.ini | text | |
MD5:— | SHA256:— | |||
| 2116 | ar32e301(3).exe | C:\Users\admin\AppData\Local\Temp\~EXB0000\setup.pkg | binary | |
MD5:— | SHA256:— | |||
| 2116 | ar32e301(3).exe | C:\Users\admin\AppData\Local\Temp\~EXB0000\README.wri | wri | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report