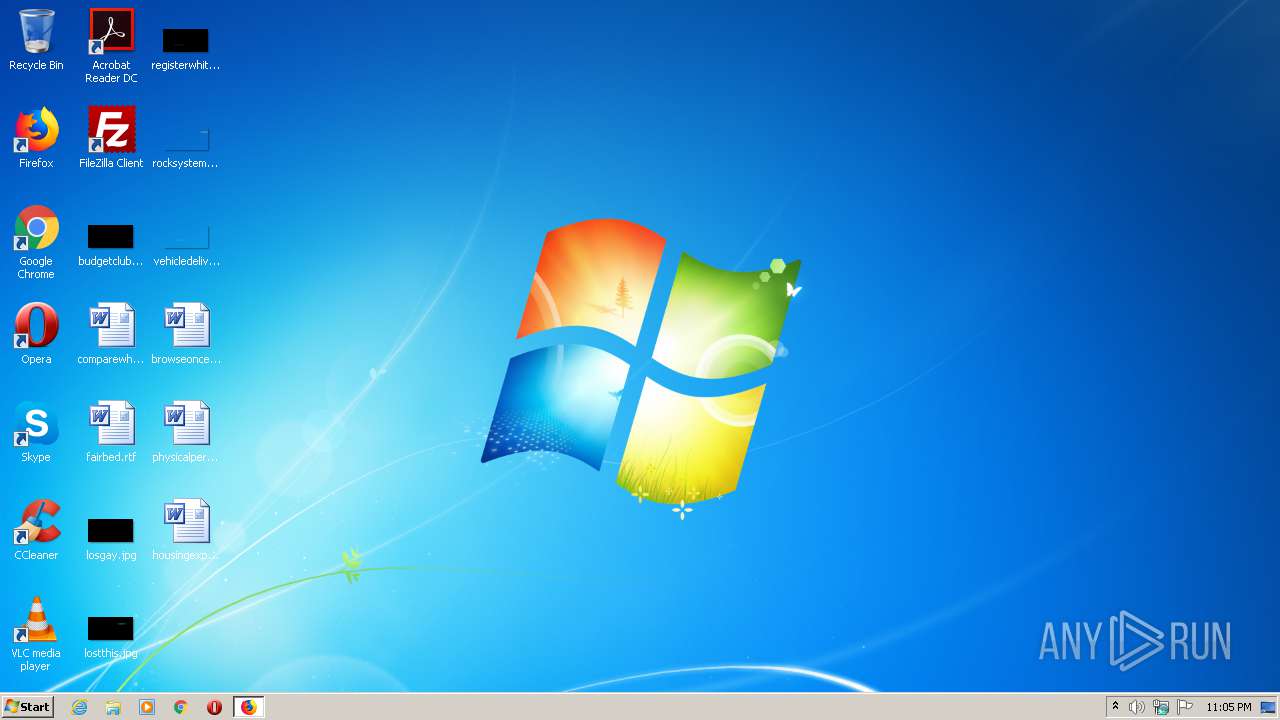
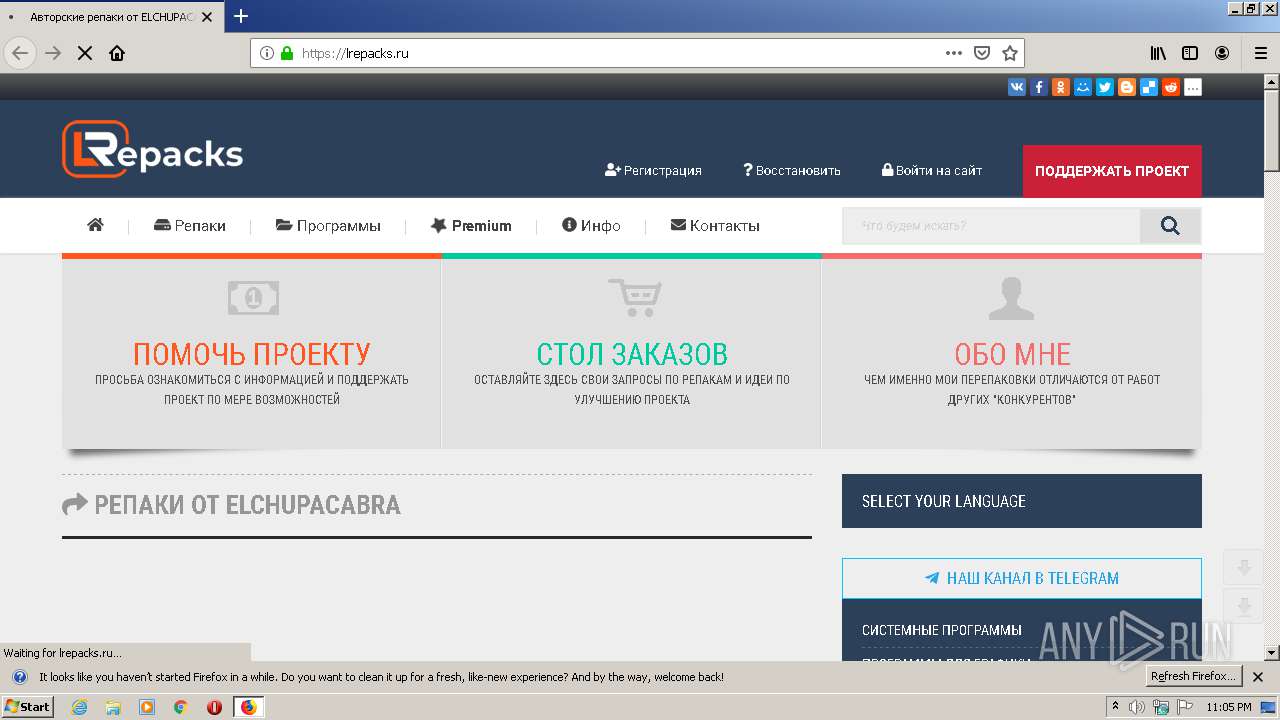
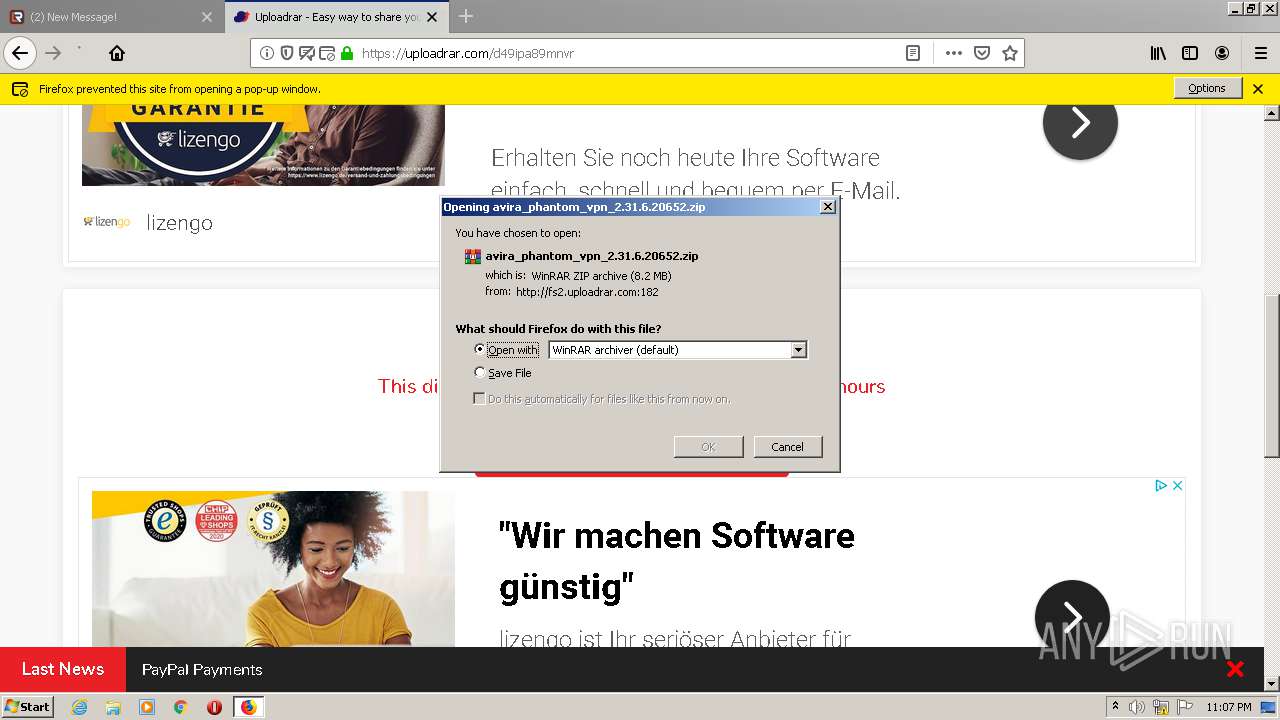
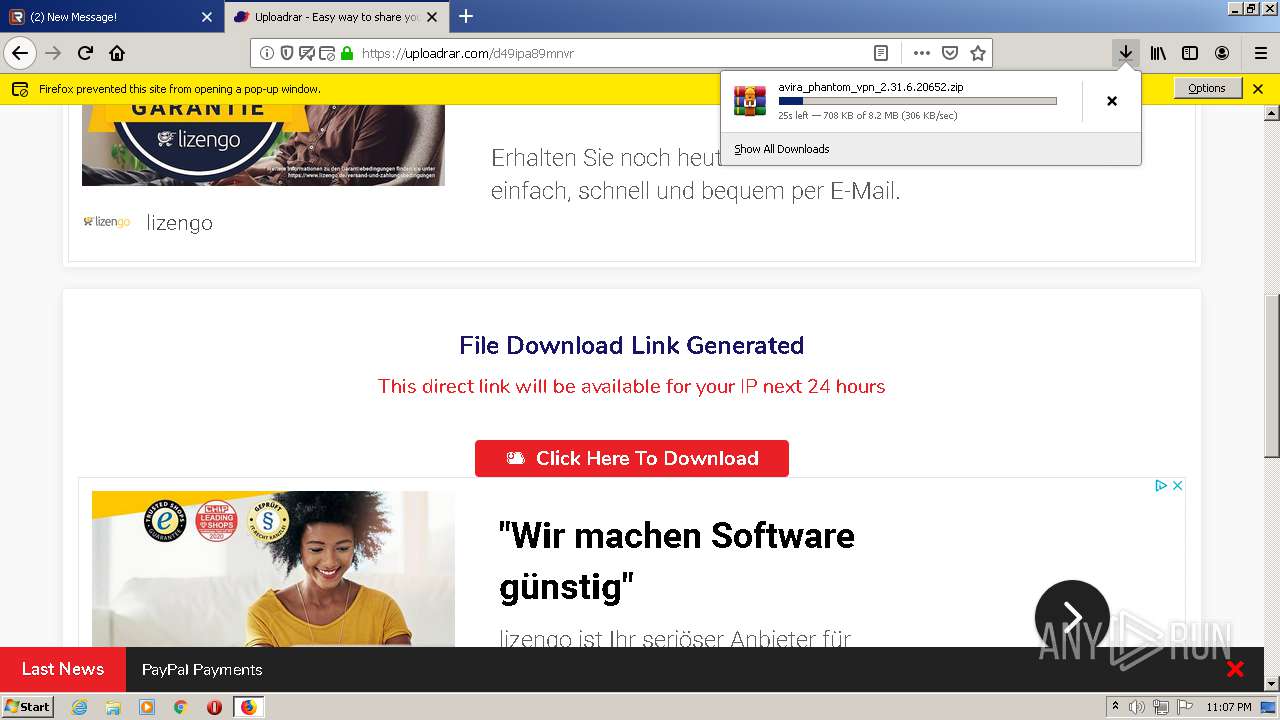
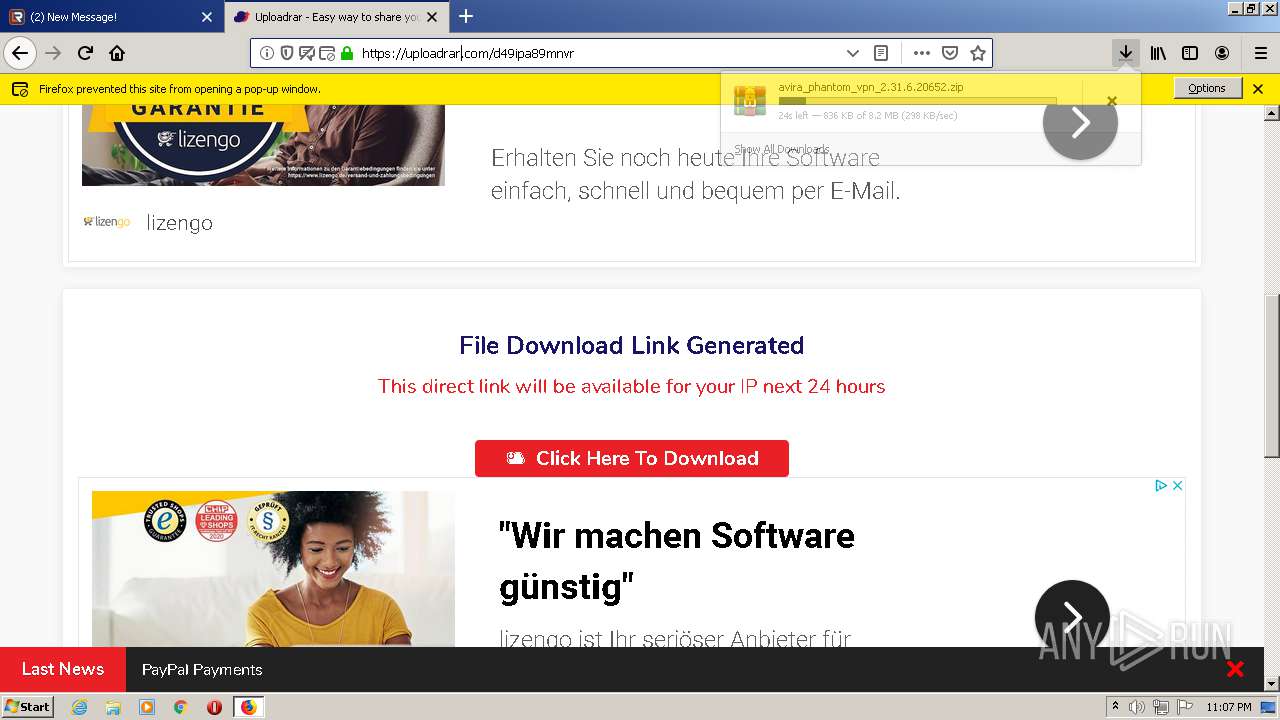
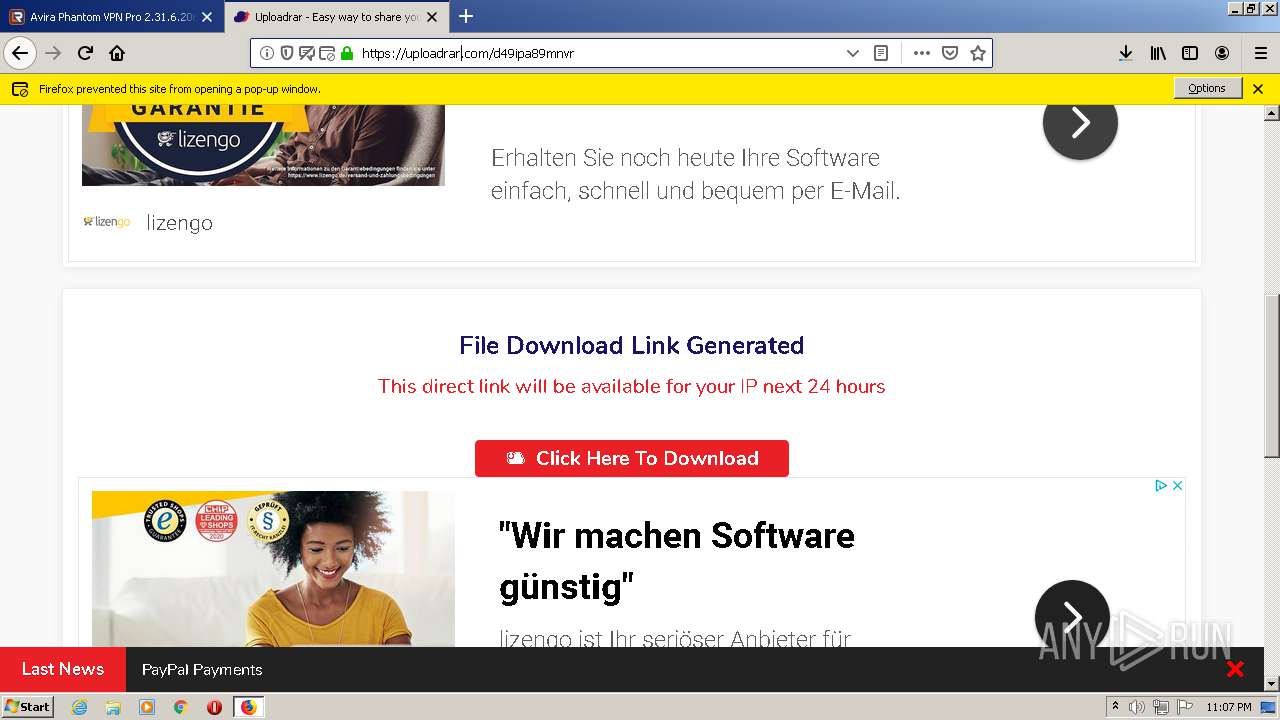
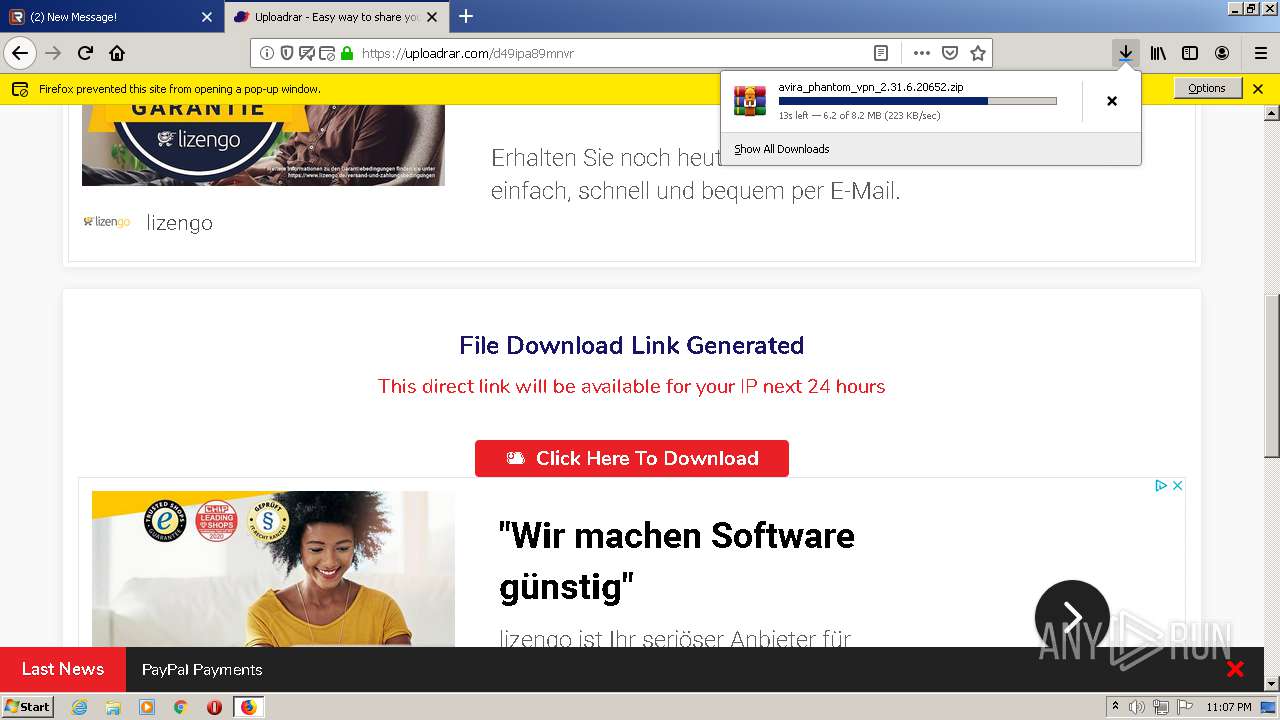
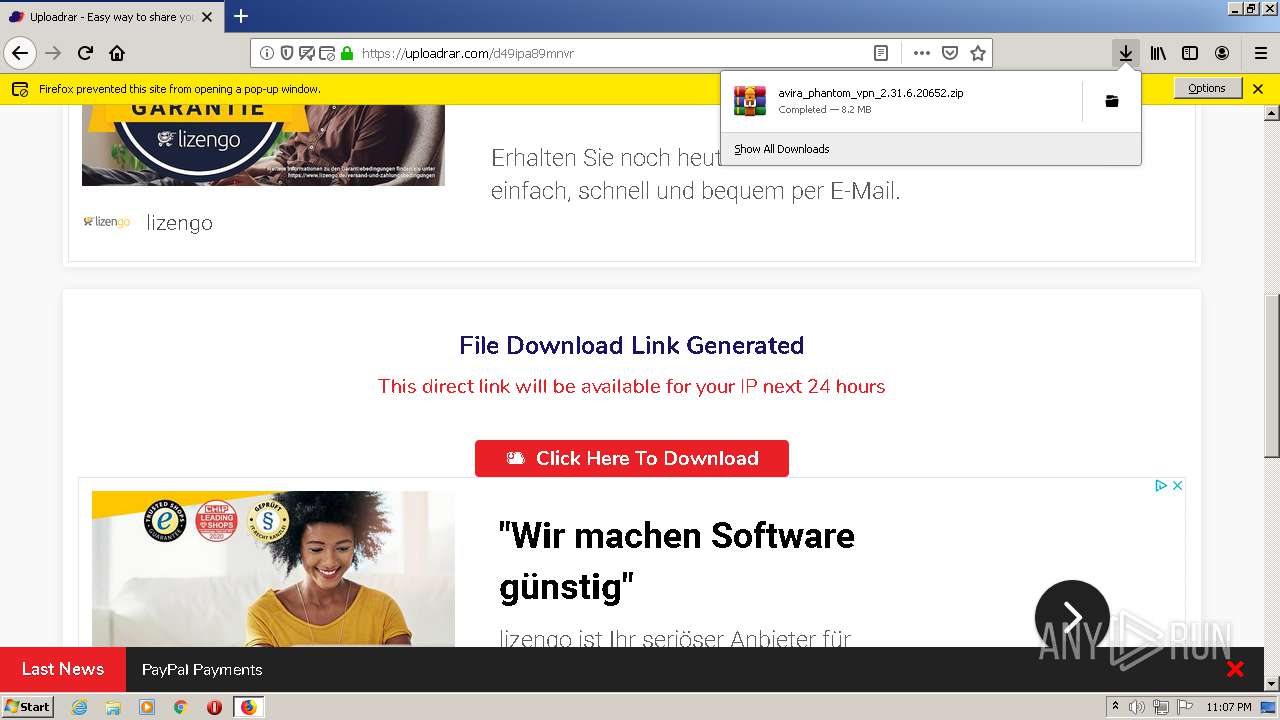
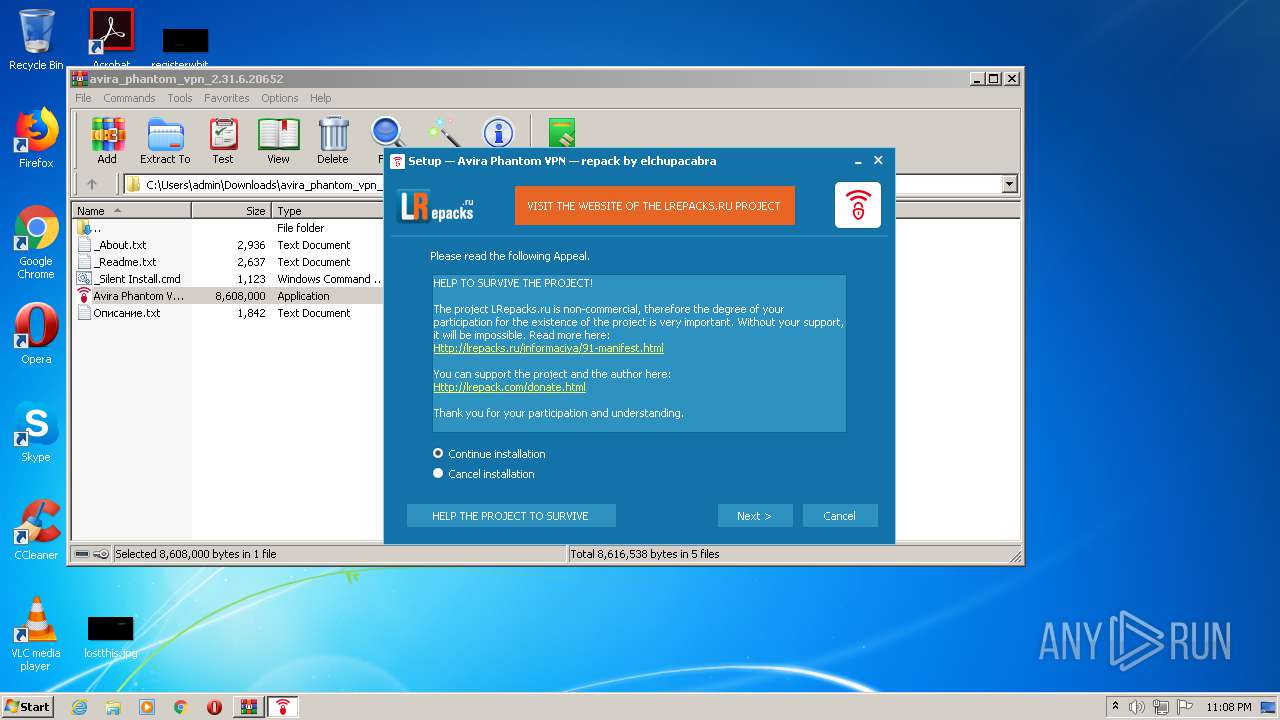
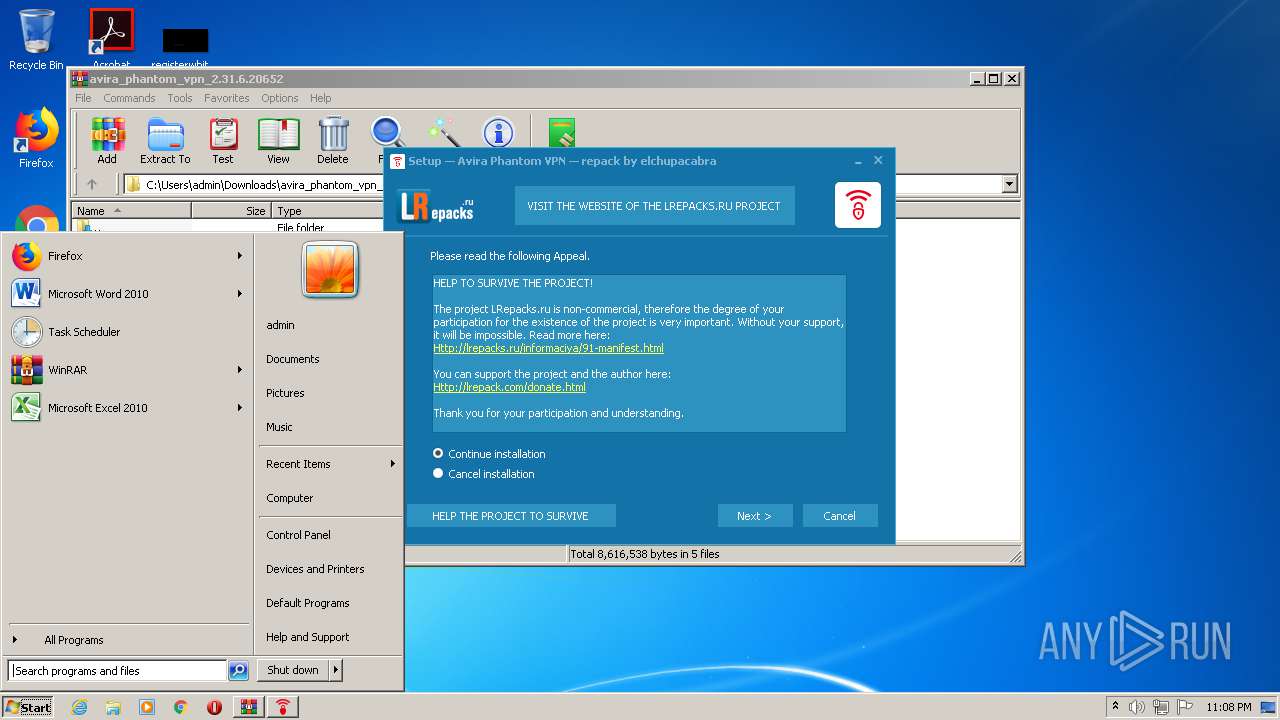
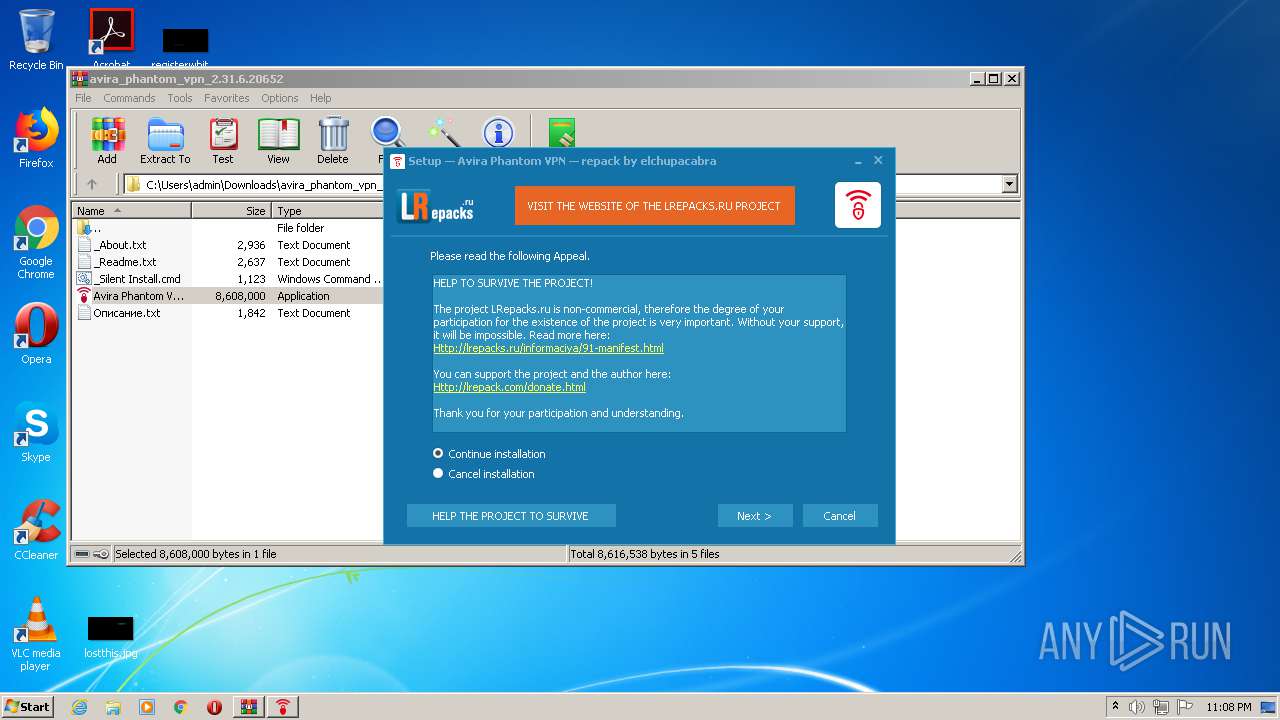
| URL: | https://www.lrepacks.ru |
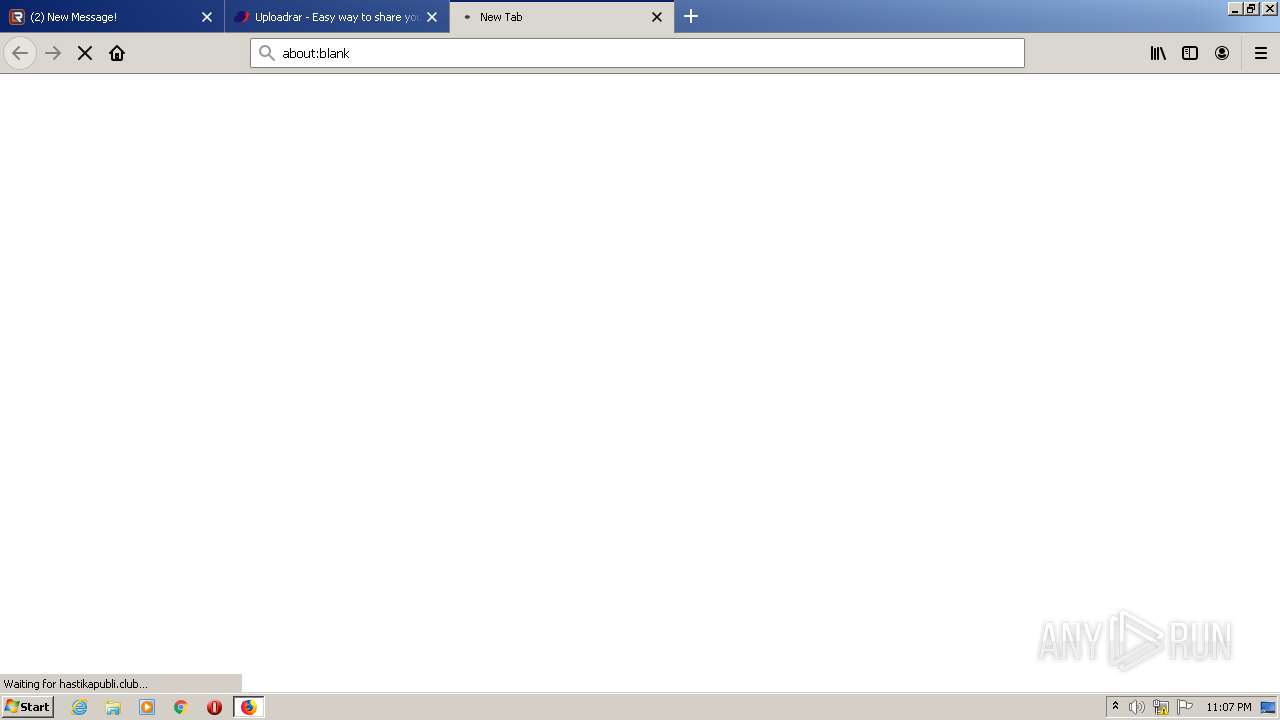
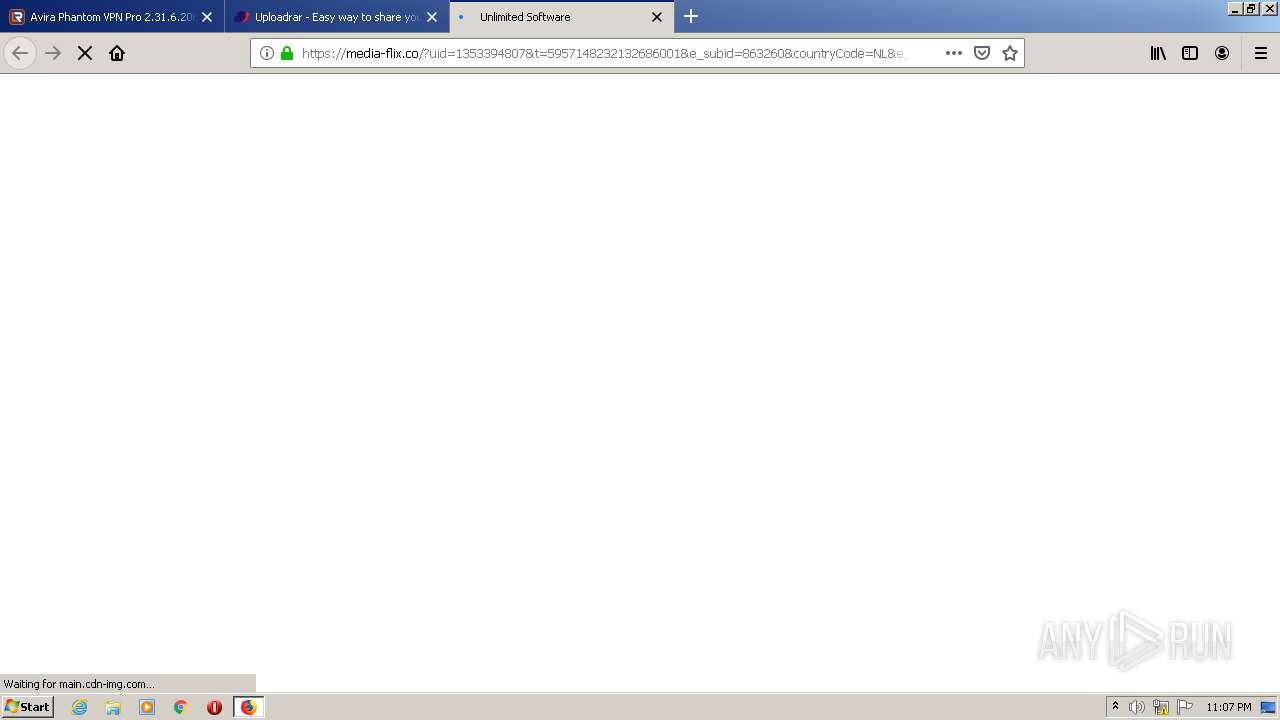
| Full analysis: | https://app.any.run/tasks/de9a2b3f-2dcc-4002-a413-5317c960b2cb |
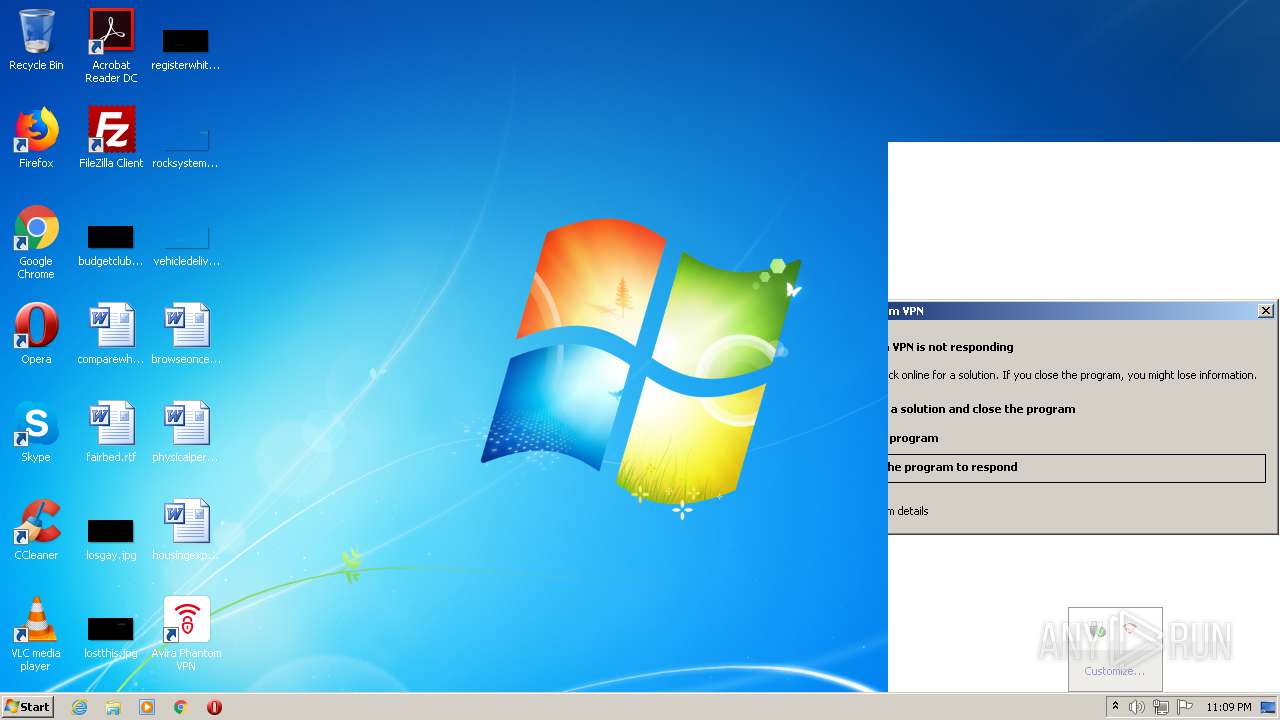
| Verdict: | Malicious activity |
| Analysis date: | July 25, 2020, 22:04:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
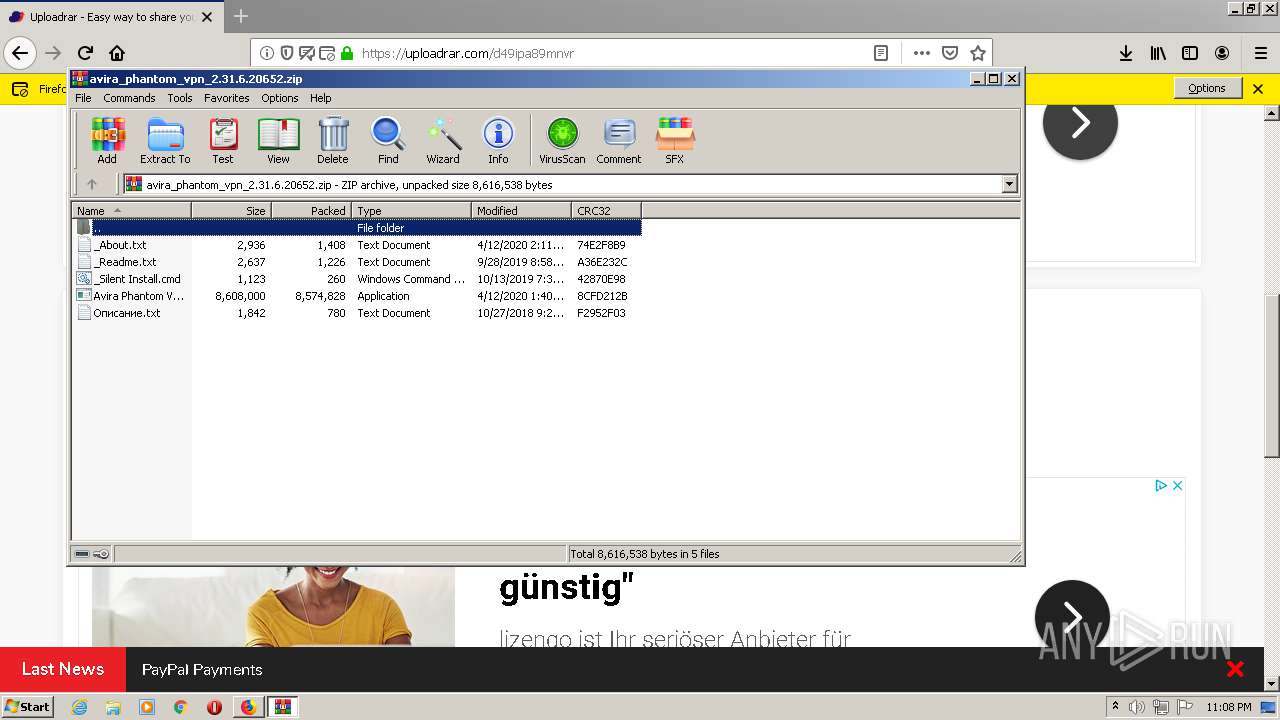
| MD5: | 025A40EC08AB022F7BE4FE739C8EC070 |
| SHA1: | E558B576FD2468EC5A99E7ACB1ED6DFFF1A5D2D6 |
| SHA256: | 2F636FECF72CEAE7D33AA82DCC17BB34399E9634BD5C93B02CA890A0C75886D4 |
| SSDEEP: | 3:N8DSLYQ:2OL9 |
MALICIOUS
Starts NET.EXE for service management
- Avira Phantom VPN 2.31.6.20652.tmp (PID: 3184)
Application was dropped or rewritten from another process
- Avira Phantom VPN 2.31.6.20652.exe (PID: 2932)
- Avira Phantom VPN 2.31.6.20652.exe (PID: 1352)
- Avira.VpnService.exe (PID: 3848)
- Avira.WebAppHost.exe (PID: 2548)
- Avira.WebAppHost.exe (PID: 3652)
- Avira.NetworkBlocker.exe (PID: 2848)
- tapinstall.exe (PID: 3388)
- tapinstall.exe (PID: 1836)
- tapinstall.exe (PID: 1796)
- tapinstall.exe (PID: 3336)
- tapinstall.exe (PID: 2088)
Loads dropped or rewritten executable
- Avira.VpnService.exe (PID: 3848)
- Avira.WebAppHost.exe (PID: 2548)
- Avira.WebAppHost.exe (PID: 3652)
Adds new firewall rule via NETSH.EXE
- Avira Phantom VPN 2.31.6.20652.tmp (PID: 3184)
Changes settings of System certificates
- Avira.VpnService.exe (PID: 3848)
- tapinstall.exe (PID: 3388)
- tapinstall.exe (PID: 2088)
Actions looks like stealing of personal data
- Avira.VpnService.exe (PID: 3848)
SUSPICIOUS
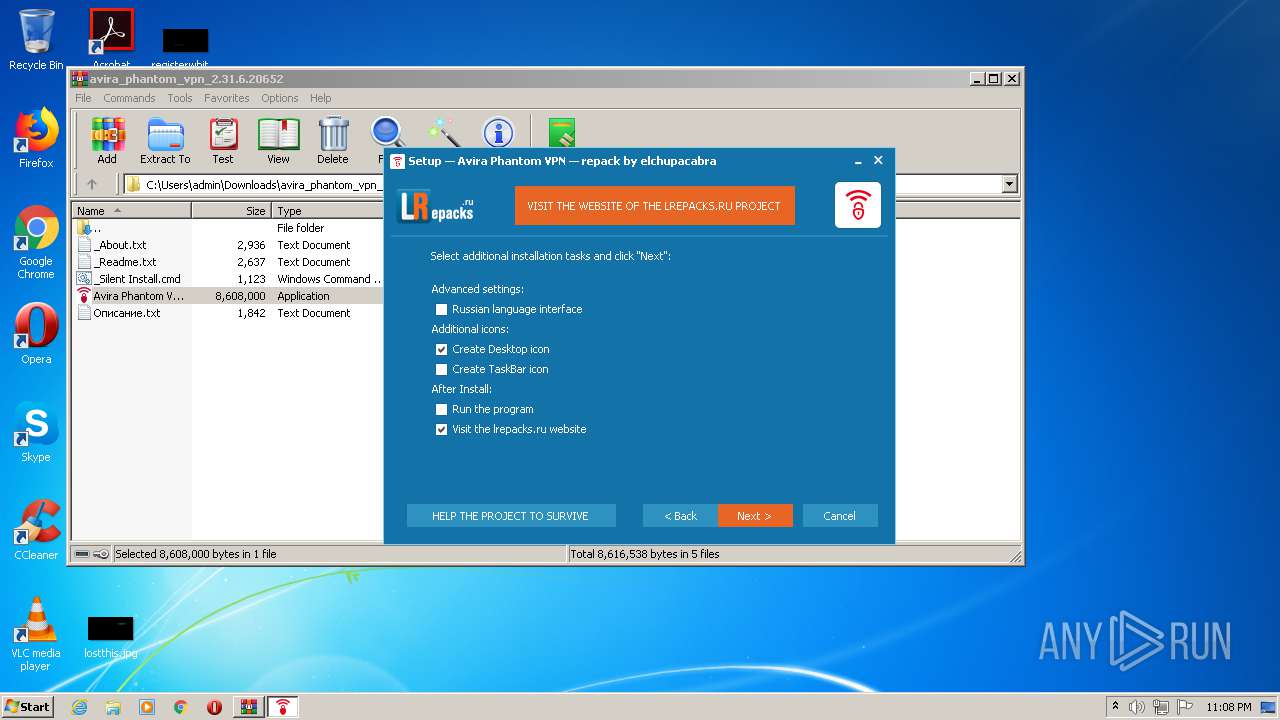
Creates files in the program directory
- firefox.exe (PID: 3236)
- Avira.VpnService.exe (PID: 3848)
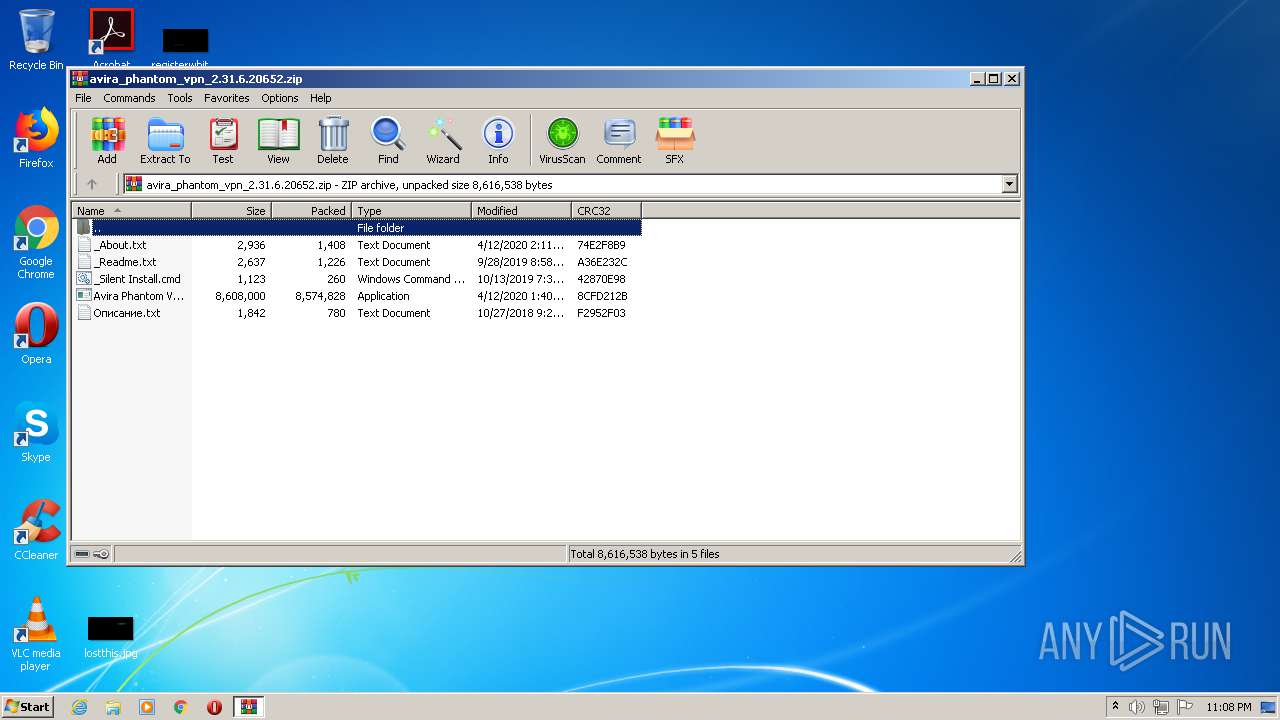
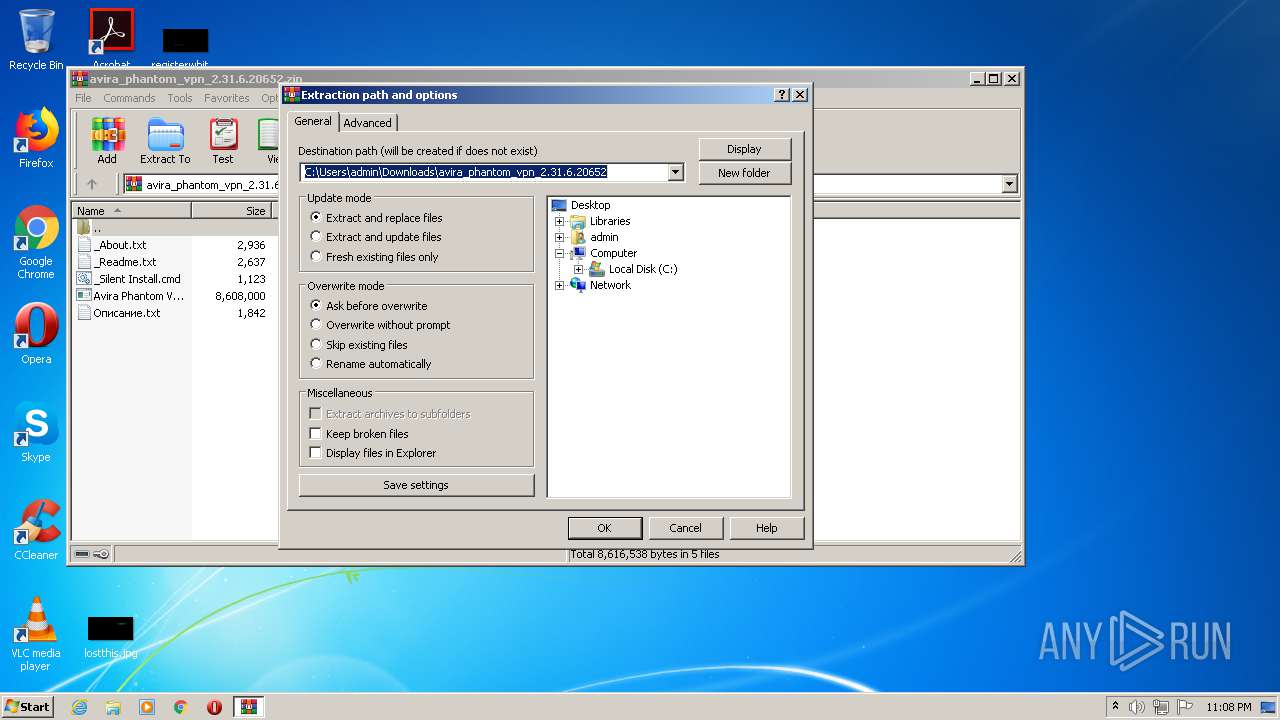
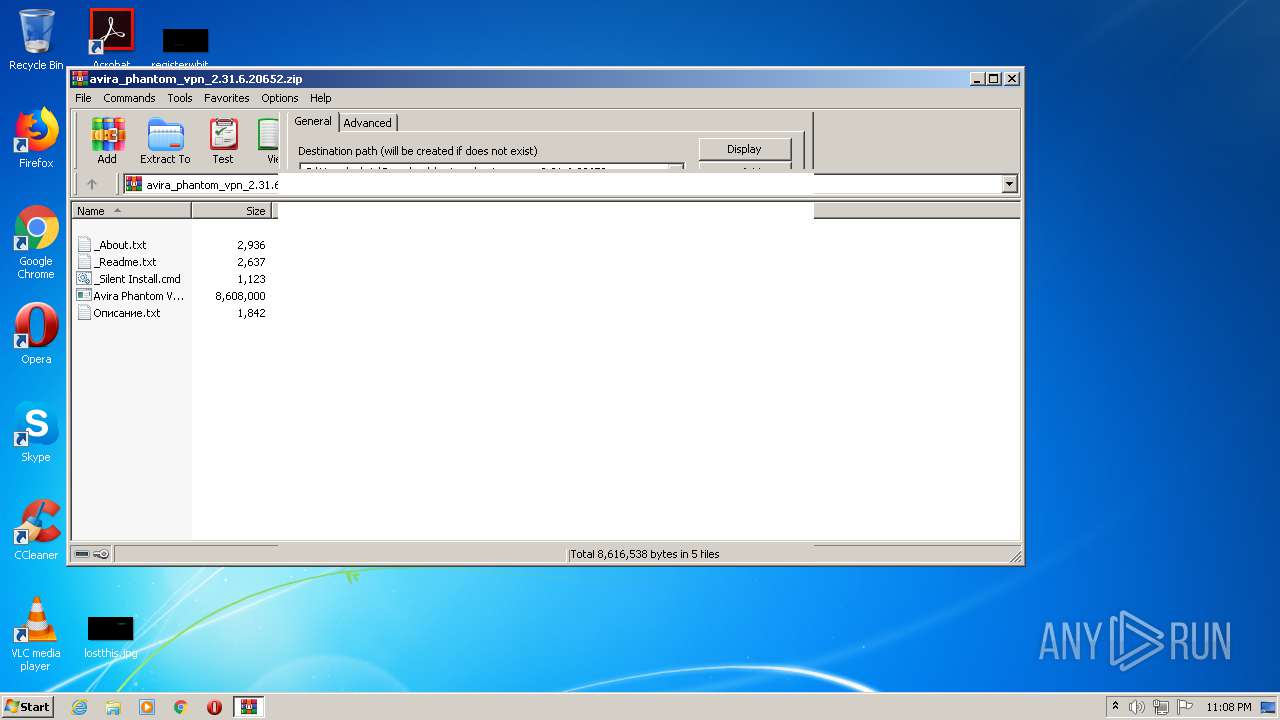
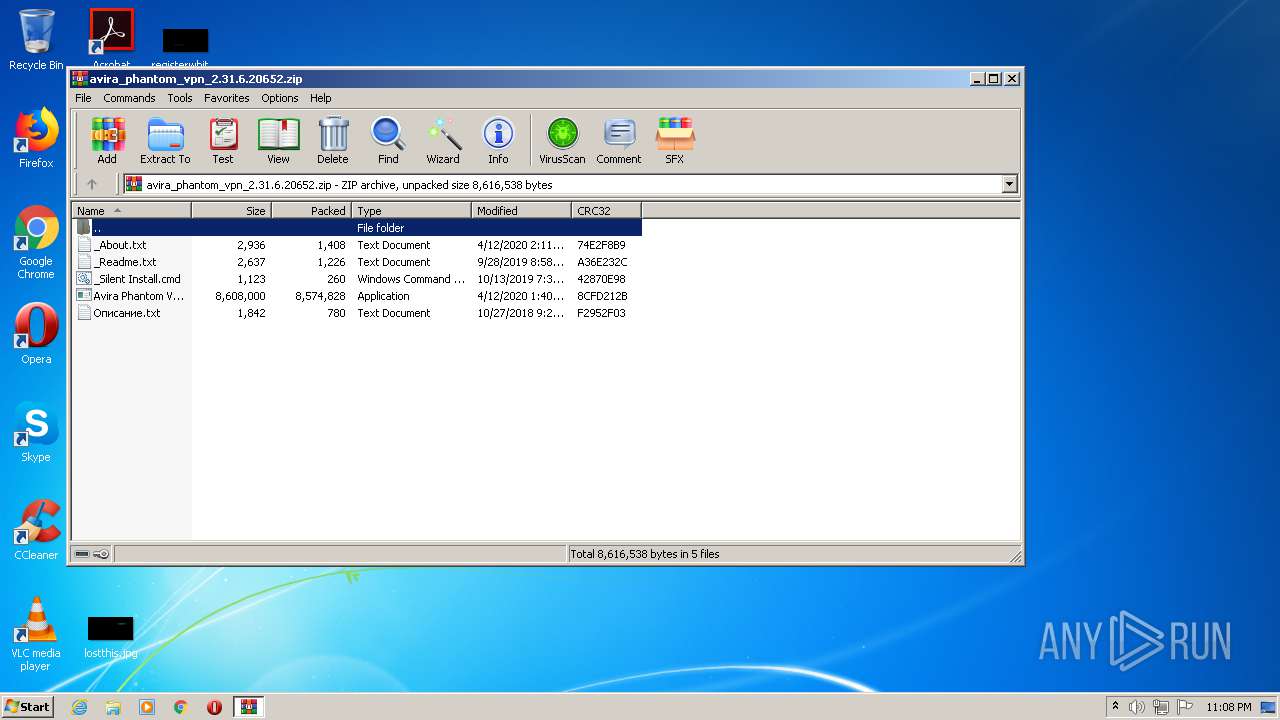
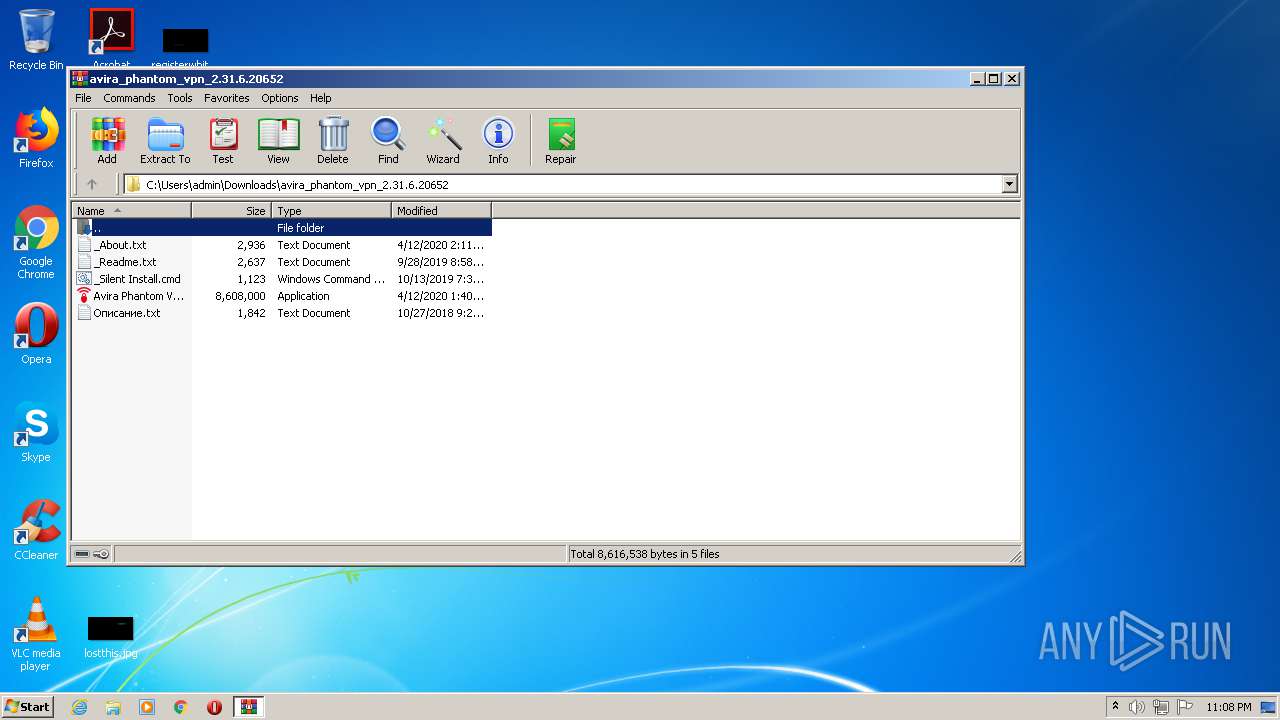
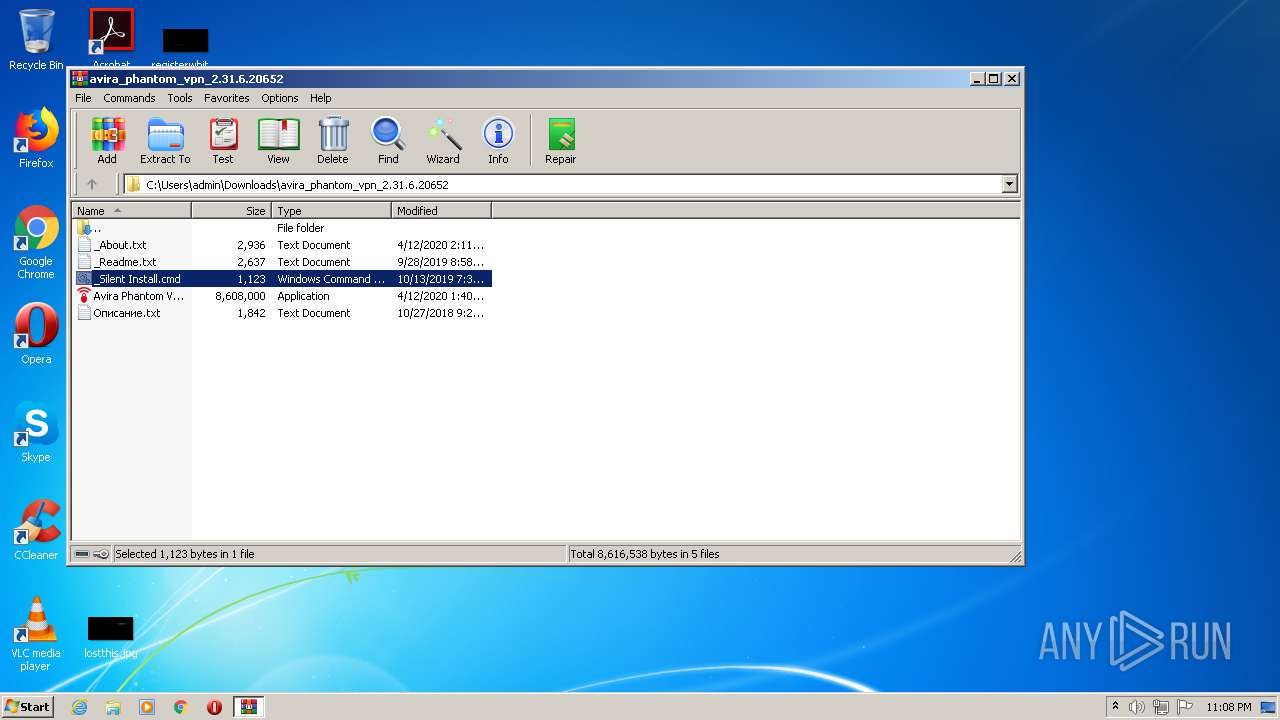
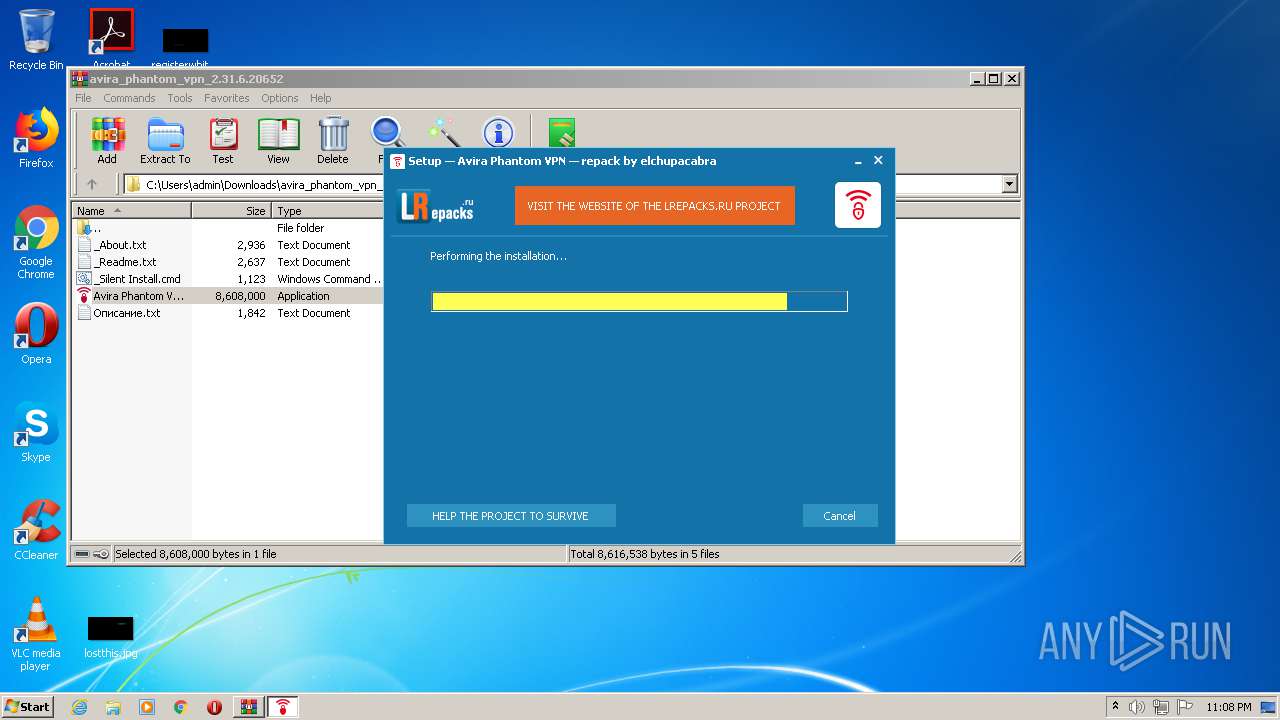
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2372)
- Avira Phantom VPN 2.31.6.20652.exe (PID: 1352)
- Avira Phantom VPN 2.31.6.20652.tmp (PID: 3184)
- DrvInst.exe (PID: 3928)
- tapinstall.exe (PID: 3388)
- DrvInst.exe (PID: 2720)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 2372)
Creates files in the Windows directory
- Avira Phantom VPN 2.31.6.20652.tmp (PID: 3184)
- Avira.VpnService.exe (PID: 3848)
- tapinstall.exe (PID: 3388)
- DrvInst.exe (PID: 3928)
- DrvInst.exe (PID: 2720)
- tapinstall.exe (PID: 2088)
- DrvInst.exe (PID: 2800)
Executed as Windows Service
- Avira.VpnService.exe (PID: 3848)
- vssvc.exe (PID: 3972)
Uses NETSH.EXE for network configuration
- Avira Phantom VPN 2.31.6.20652.tmp (PID: 3184)
Starts Internet Explorer
- Avira Phantom VPN 2.31.6.20652.tmp (PID: 3184)
Creates or modifies windows services
- Avira Phantom VPN 2.31.6.20652.tmp (PID: 3184)
Reads Environment values
- Avira.VpnService.exe (PID: 3848)
- Avira.WebAppHost.exe (PID: 3652)
Starts SC.EXE for service management
- Avira Phantom VPN 2.31.6.20652.tmp (PID: 3184)
Adds / modifies Windows certificates
- Avira.VpnService.exe (PID: 3848)
- tapinstall.exe (PID: 3388)
Removes files from Windows directory
- Avira.VpnService.exe (PID: 3848)
- DrvInst.exe (PID: 3928)
- tapinstall.exe (PID: 3388)
- DrvInst.exe (PID: 2720)
- tapinstall.exe (PID: 2088)
- DrvInst.exe (PID: 2800)
Reads internet explorer settings
- Avira.WebAppHost.exe (PID: 3652)
Executed via COM
- DrvInst.exe (PID: 3928)
- DrvInst.exe (PID: 2720)
- DrvInst.exe (PID: 2800)
- rundll32.exe (PID: 3160)
Reads Windows owner or organization settings
- Avira.VpnService.exe (PID: 3848)
Creates files in the driver directory
- DrvInst.exe (PID: 3928)
- DrvInst.exe (PID: 2720)
Reads Internet Cache Settings
- Avira.WebAppHost.exe (PID: 3652)
Searches for installed software
- Avira.VpnService.exe (PID: 3848)
Reads the Windows organization settings
- Avira.VpnService.exe (PID: 3848)
INFO
Application launched itself
- firefox.exe (PID: 1560)
- firefox.exe (PID: 3236)
- iexplore.exe (PID: 4092)
Reads Internet Cache Settings
- pingsender.exe (PID: 2752)
- firefox.exe (PID: 3236)
- firefox.exe (PID: 3860)
- iexplore.exe (PID: 4092)
- iexplore.exe (PID: 3052)
Changes settings of System certificates
- pingsender.exe (PID: 2752)
- iexplore.exe (PID: 3052)
Reads CPU info
- firefox.exe (PID: 3236)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3236)
Adds / modifies Windows certificates
- pingsender.exe (PID: 2752)
- iexplore.exe (PID: 3052)
Loads dropped or rewritten executable
- Avira Phantom VPN 2.31.6.20652.tmp (PID: 3184)
Application was dropped or rewritten from another process
- Avira Phantom VPN 2.31.6.20652.tmp (PID: 3184)
Creates files in the user directory
- firefox.exe (PID: 3236)
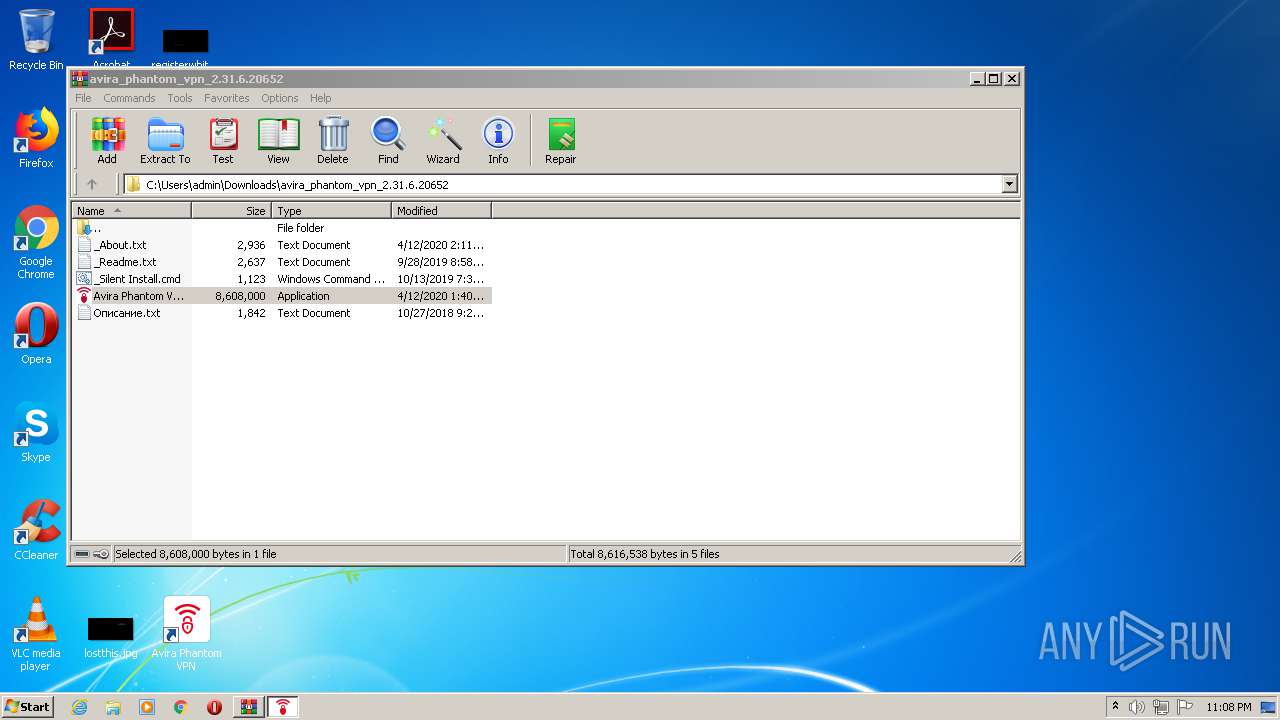
Creates a software uninstall entry
- Avira Phantom VPN 2.31.6.20652.tmp (PID: 3184)
Manual execution by user
- Avira.WebAppHost.exe (PID: 2548)
- Avira.WebAppHost.exe (PID: 3652)
Changes internet zones settings
- iexplore.exe (PID: 4092)
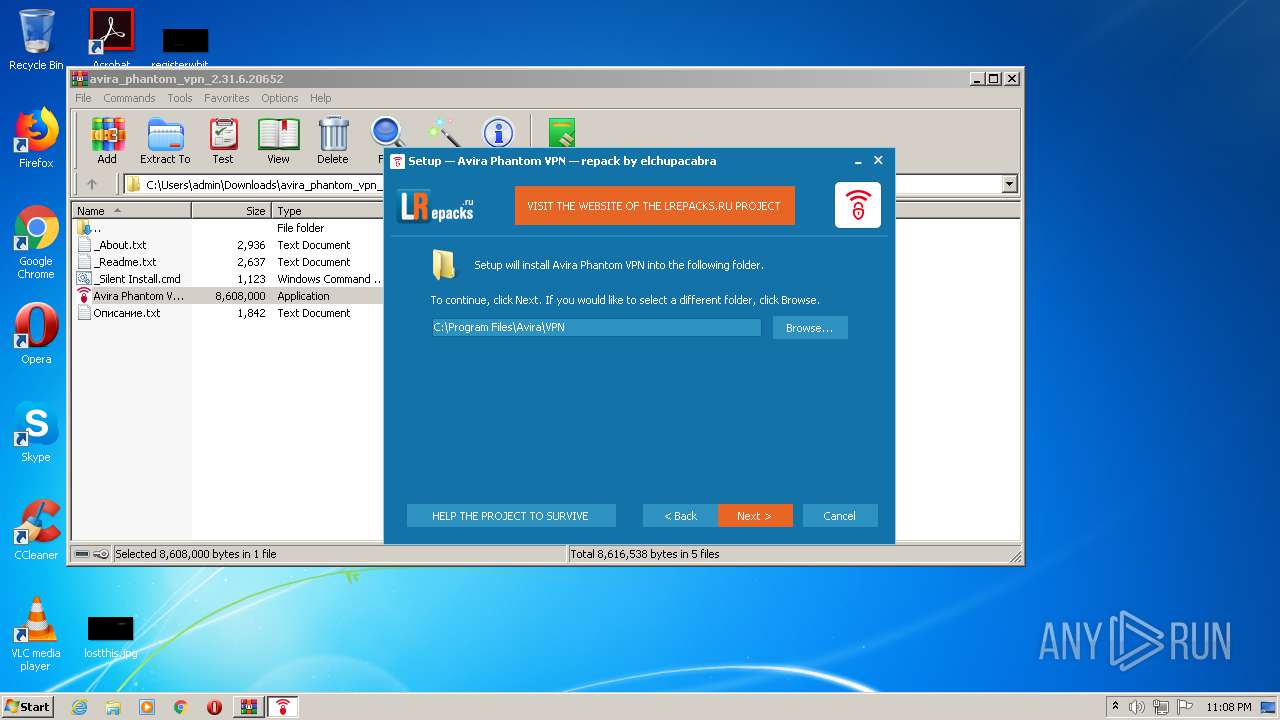
Creates files in the program directory
- Avira Phantom VPN 2.31.6.20652.tmp (PID: 3184)
Reads settings of System Certificates
- Avira.VpnService.exe (PID: 3848)
- Avira.WebAppHost.exe (PID: 3652)
- tapinstall.exe (PID: 3388)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3972)
Searches for installed software
- DrvInst.exe (PID: 3928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
100
Monitored processes
39
Malicious processes
14
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Windows\system32\sc.exe" create "AviraPhantomVPN" binPath= "C:\Program Files\Avira\VPN\Avira.VpnService.exe" start= auto error= ignore DisplayName= "Avira Phantom VPN" | C:\Windows\system32\sc.exe | — | Avira Phantom VPN 2.31.6.20652.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 996 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3236.13.2107837655\1812388261" -childID 2 -isForBrowser -prefsHandle 2720 -prefMapHandle 2880 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3236 "\\.\pipe\gecko-crash-server-pipe.3236" 2892 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1120 | "C:\Windows\system32\netsh.exe" advfirewall firewall add rule name="Avira Phantom VPN" program="C:\Program Files\Avira\VPN\OpenVpn\phantomvpn.exe" dir=in enable=yes profile=any action=allow | C:\Windows\system32\netsh.exe | — | Avira Phantom VPN 2.31.6.20652.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1352 | "C:\Users\admin\Downloads\avira_phantom_vpn_2.31.6.20652\Avira Phantom VPN 2.31.6.20652.exe" | C:\Users\admin\Downloads\avira_phantom_vpn_2.31.6.20652\Avira Phantom VPN 2.31.6.20652.exe | WinRAR.exe | ||||||||||||
User: admin Company: lrepacks.ru Integrity Level: HIGH Description: Avira Phantom VPN Setup Exit code: 0 Version: 2.31.6.20652.0 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3236.0.353112656\412397543" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3236 "\\.\pipe\gecko-crash-server-pipe.3236" 1160 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 68.0.1 Modules
| |||||||||||||||
| 1560 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://www.lrepacks.ru" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Avira\VPN\OpenVpn\TAP\win7\i386\tapinstall.exe" find phantomtap | C:\Program Files\Avira\VPN\OpenVpn\TAP\win7\i386\tapinstall.exe | — | Avira.VpnService.exe | |||||||||||
User: SYSTEM Company: Windows (R) Win 7 DDK provider Integrity Level: SYSTEM Description: Windows Setup API Exit code: 0 Version: 10.0.10011.16384 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Avira\VPN\OpenVpn\TAP\win7\i386\tapinstall.exe" status phantomtap | C:\Program Files\Avira\VPN\OpenVpn\TAP\win7\i386\tapinstall.exe | — | Avira.VpnService.exe | |||||||||||
User: SYSTEM Company: Windows (R) Win 7 DDK provider Integrity Level: SYSTEM Description: Windows Setup API Exit code: 0 Version: 10.0.10011.16384 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Avira\VPN\OpenVpn\TAP\win7\i386\tapinstall.exe" update "C:\Program Files\Avira\VPN\OpenVpn\TAP\win7\i386\OemVista.inf" phantomtap | C:\Program Files\Avira\VPN\OpenVpn\TAP\win7\i386\tapinstall.exe | — | Avira.VpnService.exe | |||||||||||
User: SYSTEM Company: Windows (R) Win 7 DDK provider Integrity Level: SYSTEM Description: Windows Setup API Exit code: 0 Version: 10.0.10011.16384 Modules
| |||||||||||||||
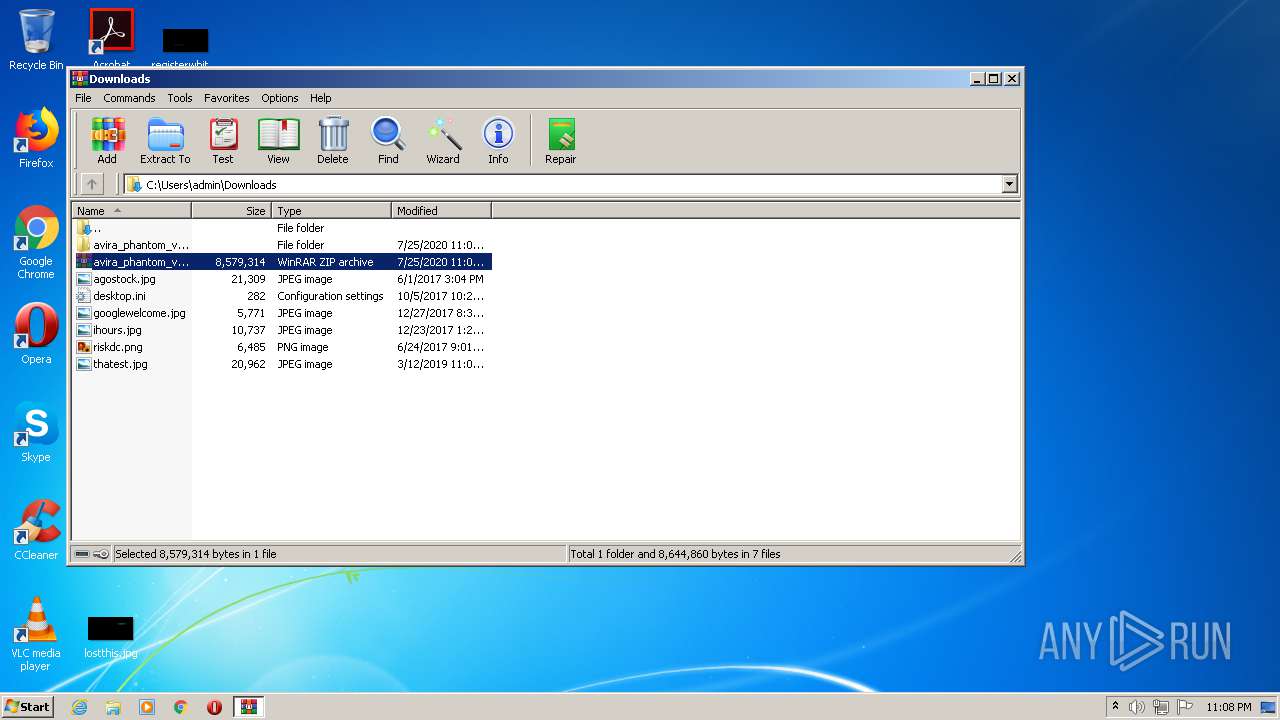
| 2372 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\avira_phantom_vpn_2.31.6.20652.zip" | C:\Program Files\WinRAR\WinRAR.exe | firefox.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
6 326
Read events
5 263
Write events
988
Delete events
75
Modification events
| (PID) Process: | (1560) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 8AC5CD0700000000 | |||
| (PID) Process: | (3236) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 8BC5CD0700000000 | |||
| (PID) Process: | (3236) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (3236) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3236) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3236) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3236) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2372) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2372) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3236) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithProgids |
| Operation: | write | Name: | WinRAR.ZIP |
Value: | |||
Executable files
75
Suspicious files
456
Text files
1 029
Unknown types
249
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3236 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3236 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3236 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3236 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3236 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3236 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3236 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 3236 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 3236 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 3236 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
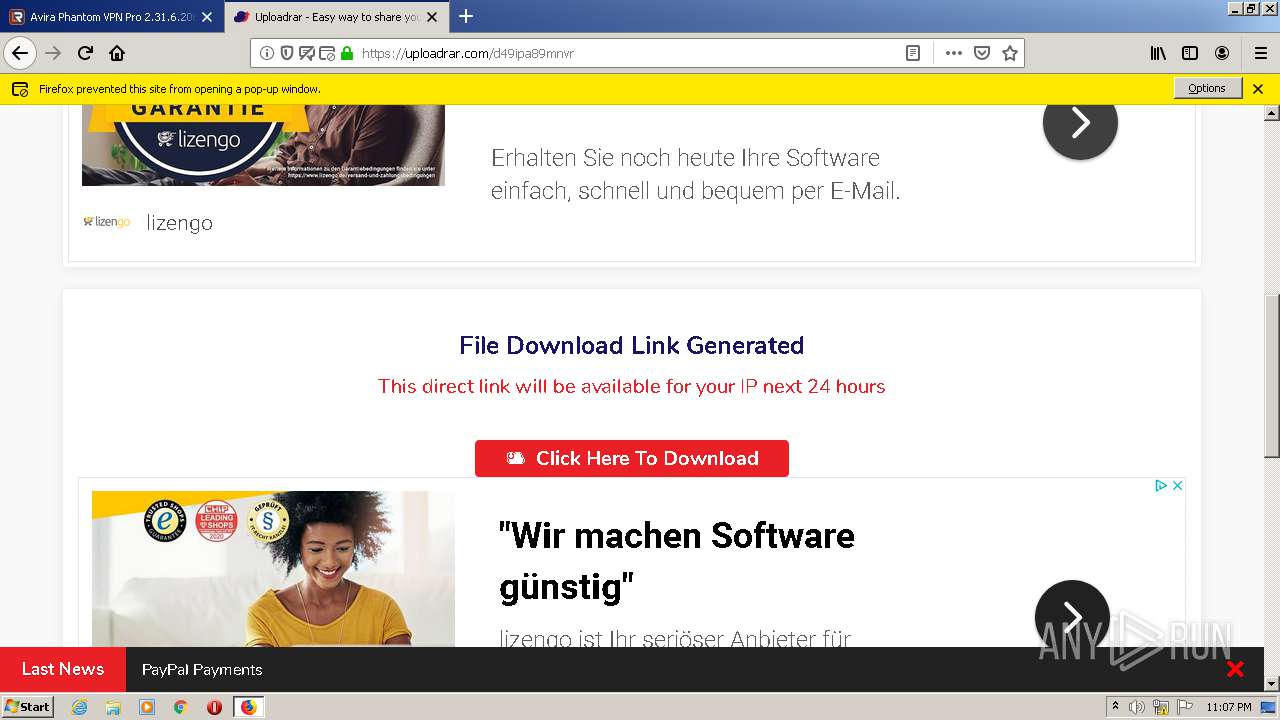
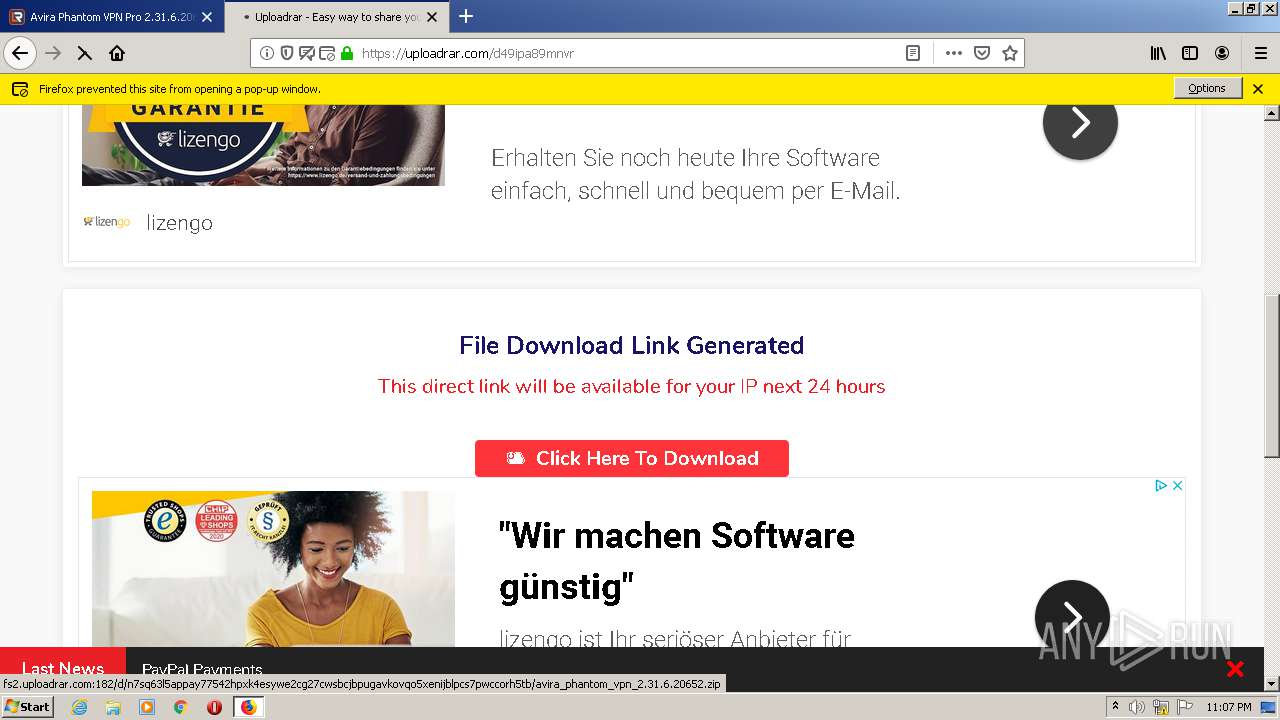
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
65
TCP/UDP connections
199
DNS requests
470
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3236 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1core | US | der | 471 b | whitelisted |
3236 | firefox.exe | POST | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/gsorganizationvalsha2g2 | US | der | 1.54 Kb | whitelisted |
3236 | firefox.exe | POST | 200 | 5.45.205.245:80 | http://yandex.ocsp-responder.com/ | RU | der | 1.48 Kb | whitelisted |
3236 | firefox.exe | POST | 200 | 2.16.107.114:80 | http://ocsp.int-x3.letsencrypt.org/ | unknown | der | 527 b | whitelisted |
3236 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3236 | firefox.exe | POST | 200 | 5.45.205.245:80 | http://yandex.ocsp-responder.com/ | RU | der | 1.48 Kb | whitelisted |
3236 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
3236 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3236 | firefox.exe | POST | 200 | 2.16.107.114:80 | http://ocsp.int-x3.letsencrypt.org/ | unknown | der | 527 b | whitelisted |
3236 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3236 | firefox.exe | 2.16.177.88:80 | detectportal.firefox.com | Akamai International B.V. | — | suspicious |
3236 | firefox.exe | 5.44.221.96:443 | www.lrepacks.ru | Camelhost Sia | LV | suspicious |
3236 | firefox.exe | 52.41.191.52:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3236 | firefox.exe | 2.16.107.114:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | — | suspicious |
3236 | firefox.exe | 52.10.136.43:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3236 | firefox.exe | 143.204.201.119:443 | snippets.cdn.mozilla.net | — | US | suspicious |
3236 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3236 | firefox.exe | 194.247.13.127:443 | crm.platformbot.xyz | Hosting Ukraine LTD | UA | suspicious |
3236 | firefox.exe | 178.154.131.215:443 | yastatic.net | YANDEX LLC | RU | whitelisted |
3236 | firefox.exe | 172.217.18.110:443 | translate.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.lrepacks.ru |
| suspicious |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
a771.dscq.akamai.net |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3236 | firefox.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1 ETPRO signatures available at the full report