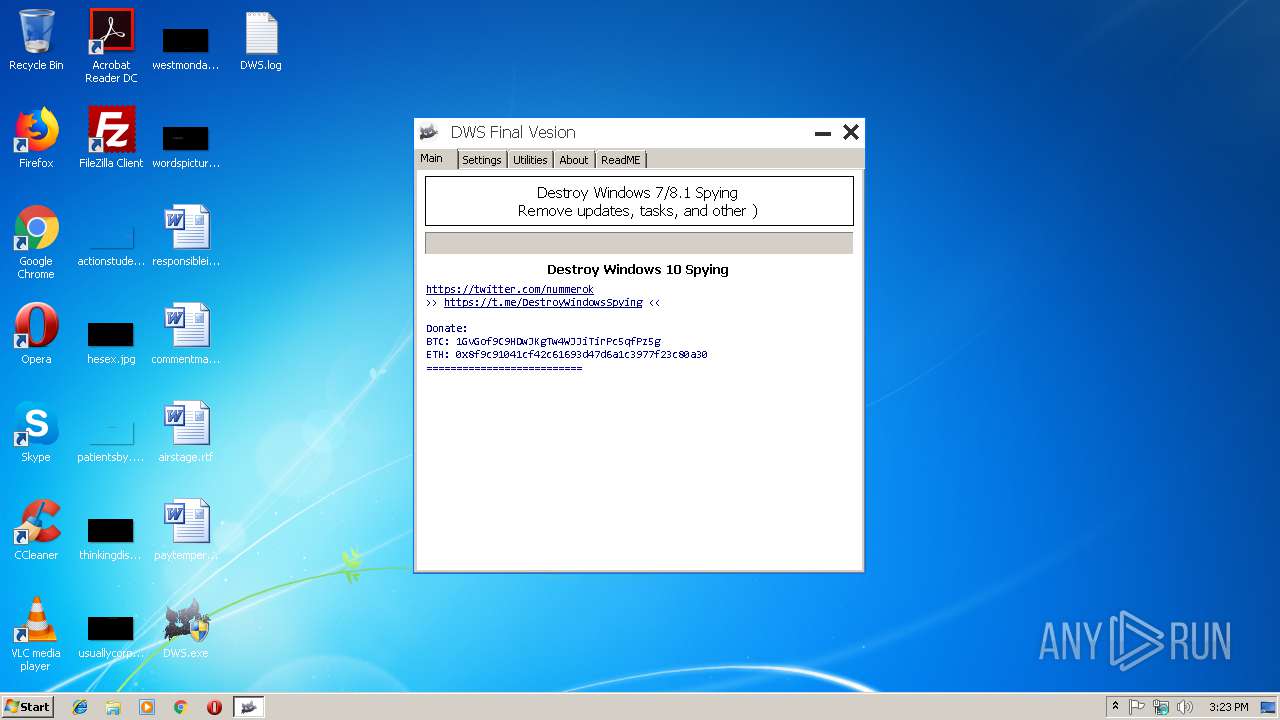
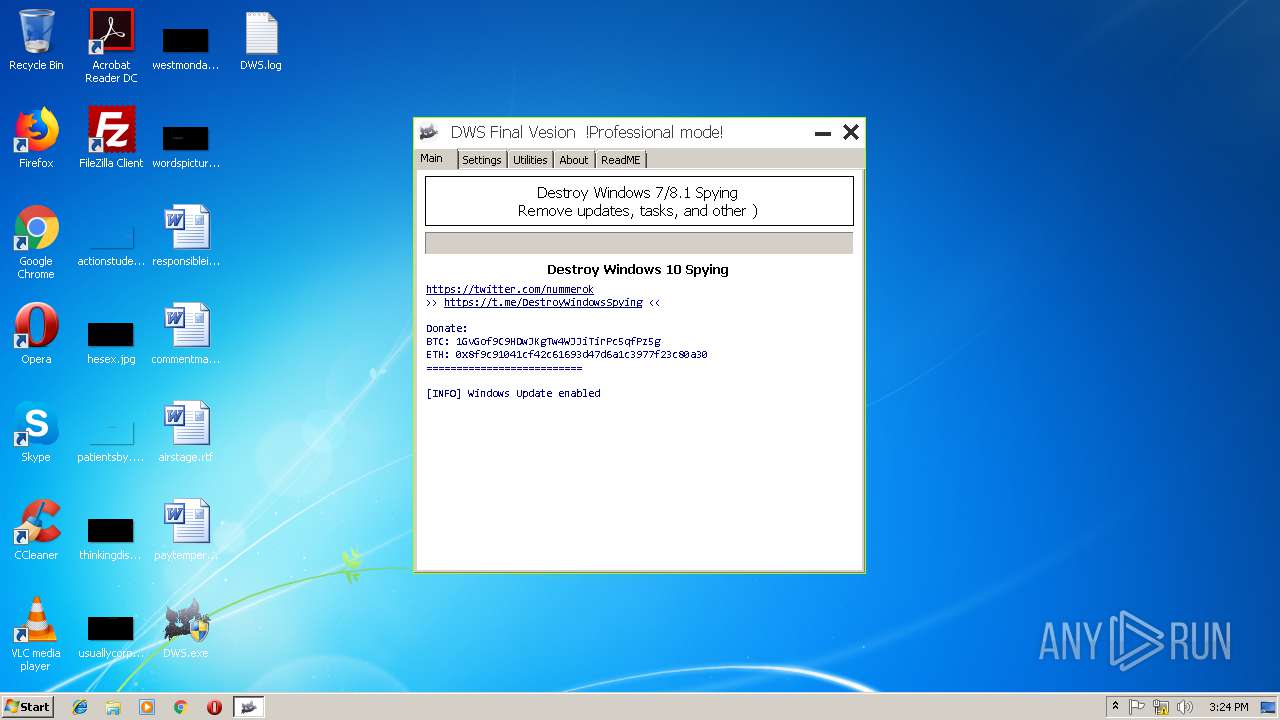
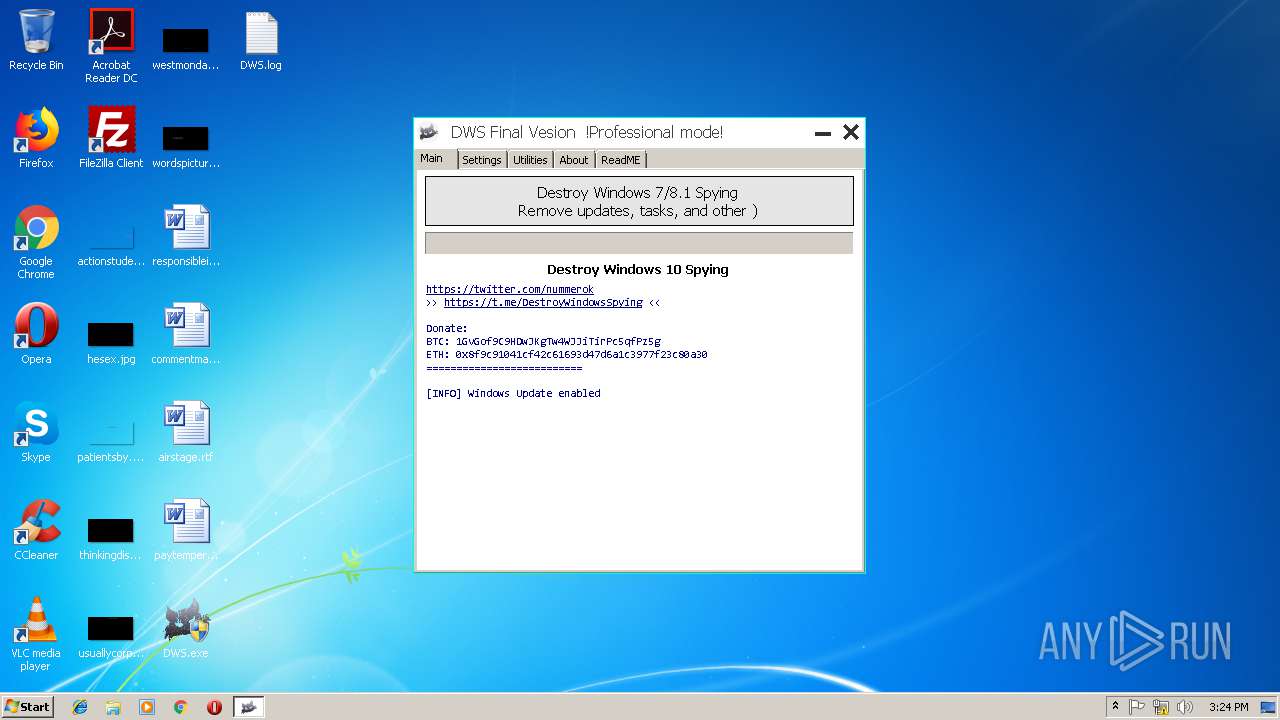
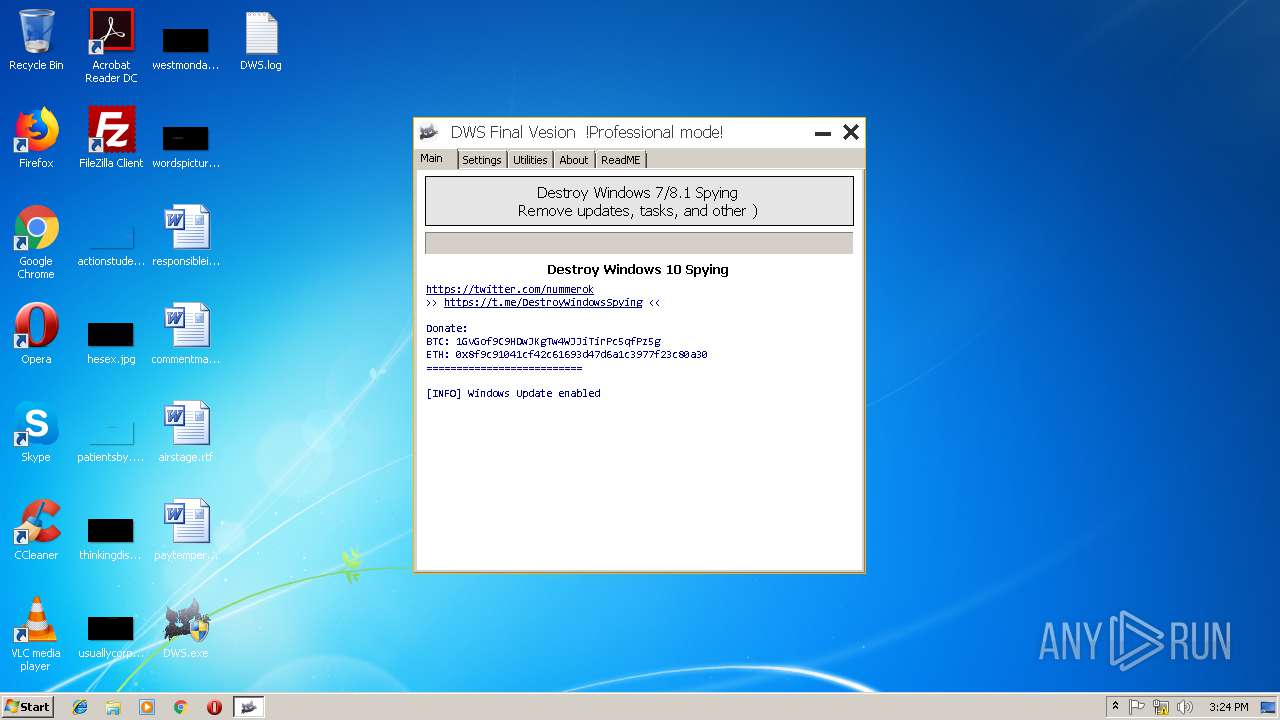
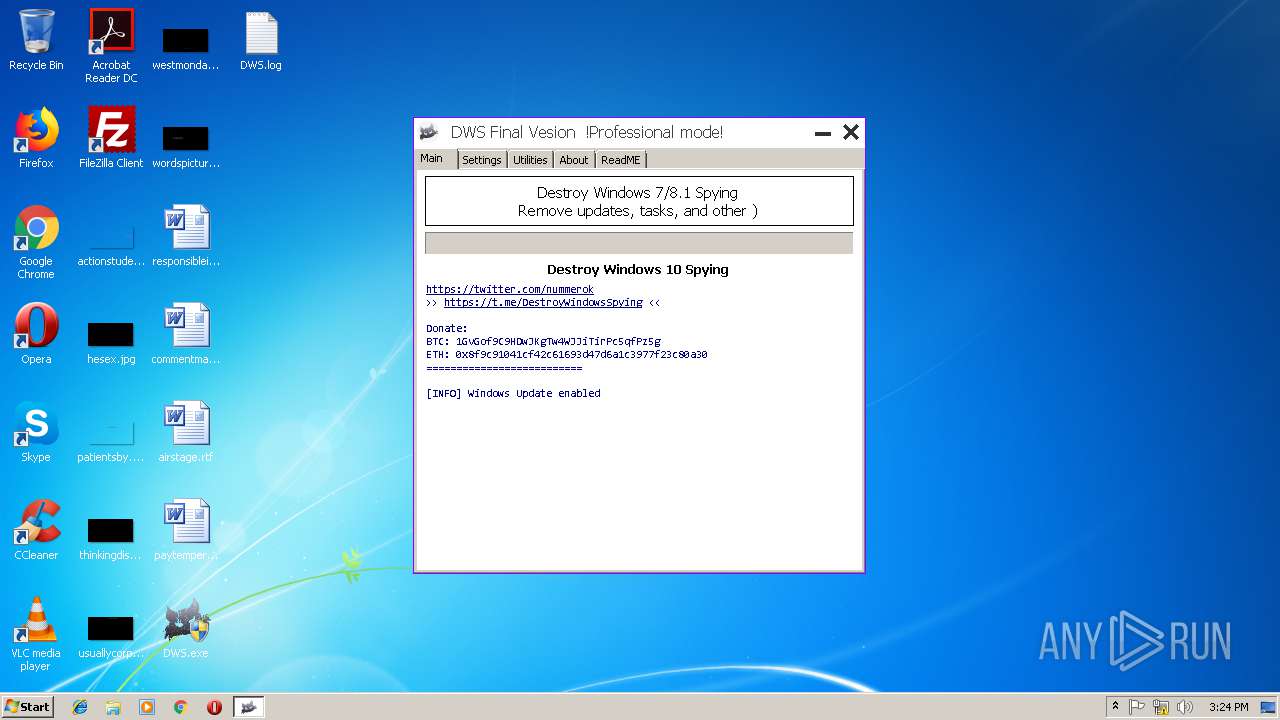
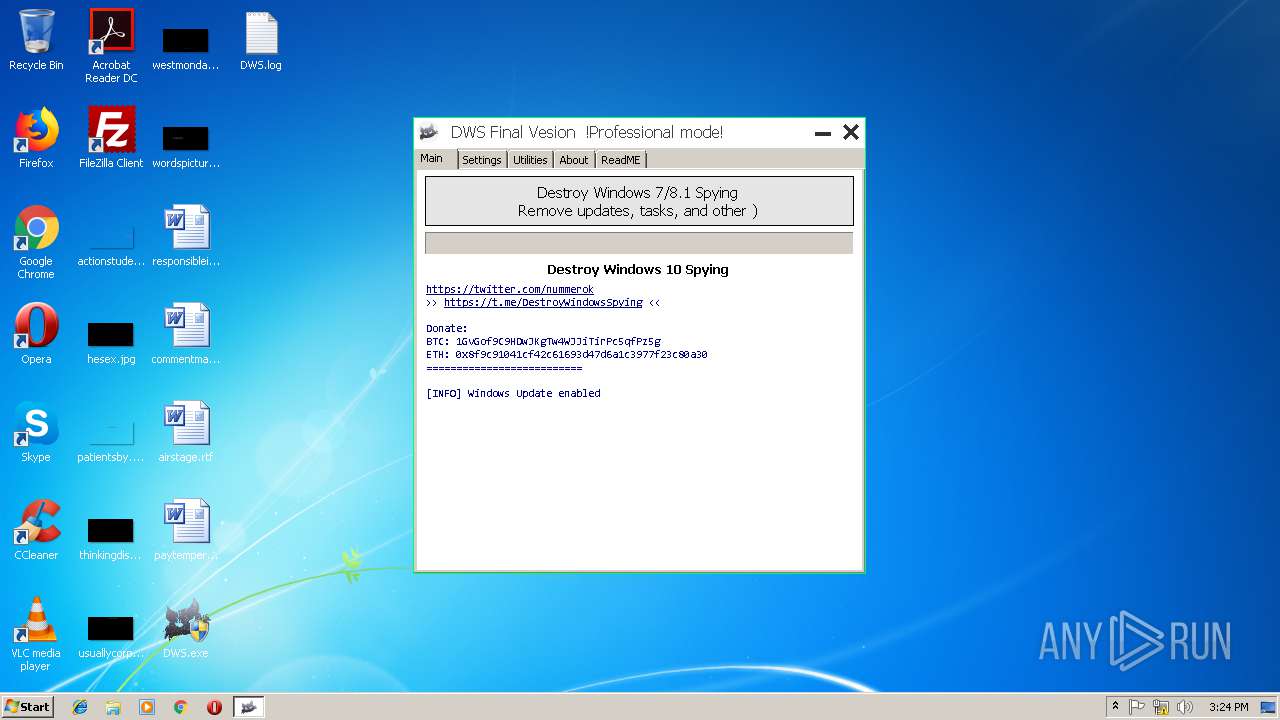
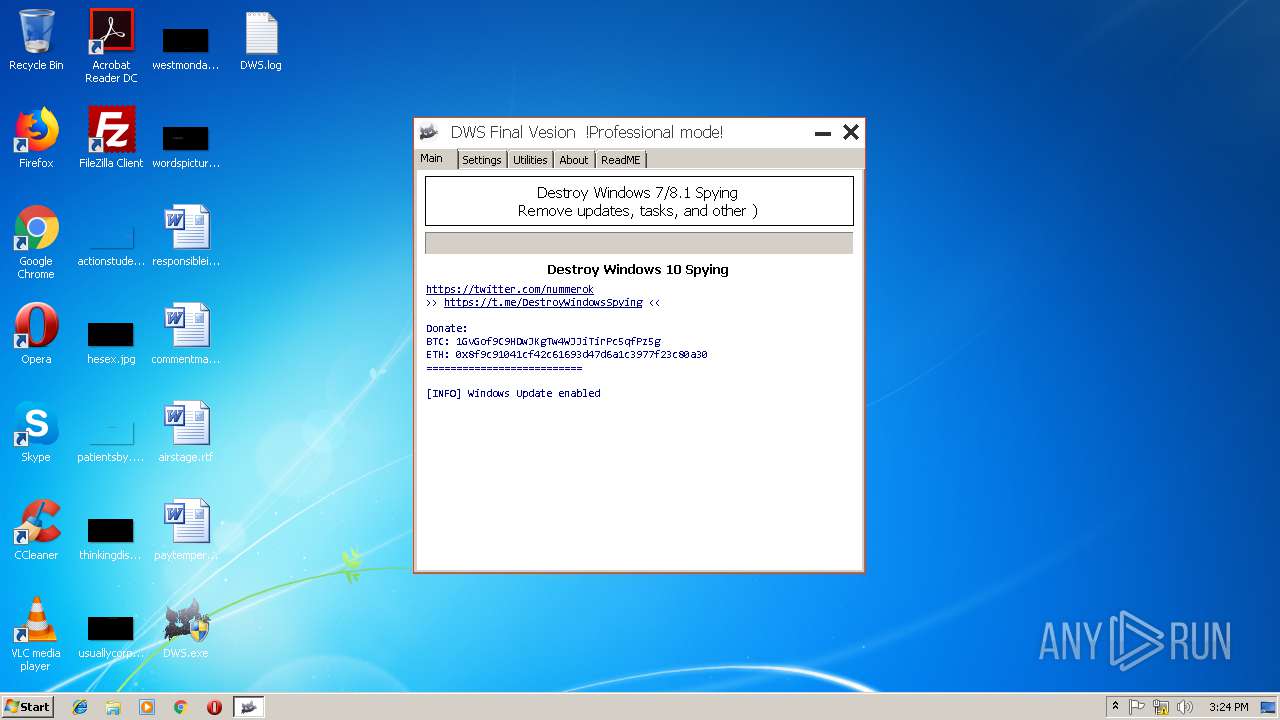
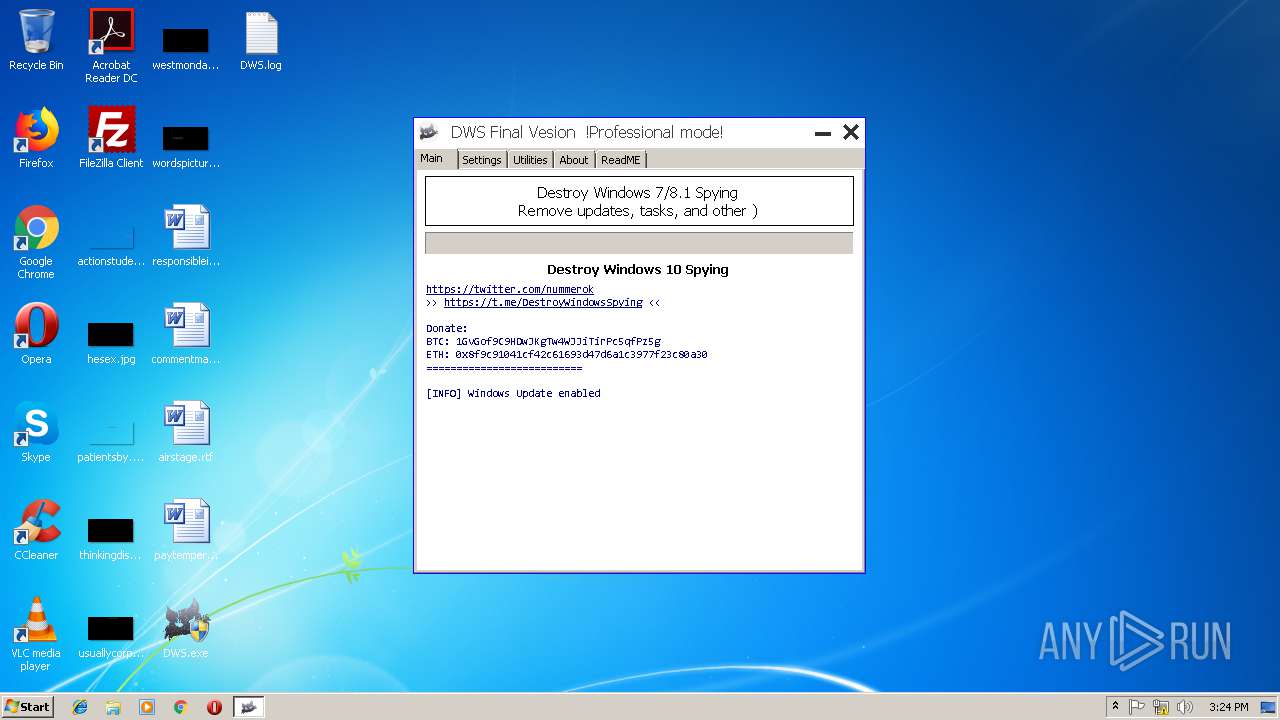
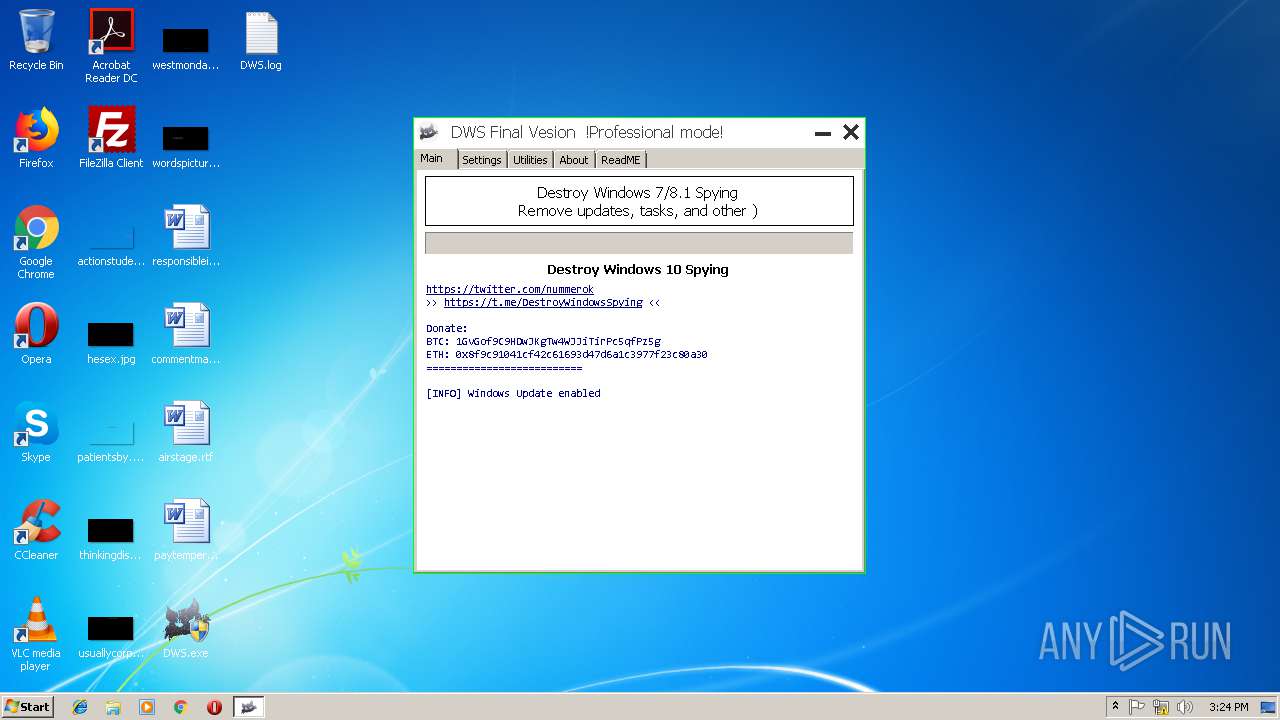
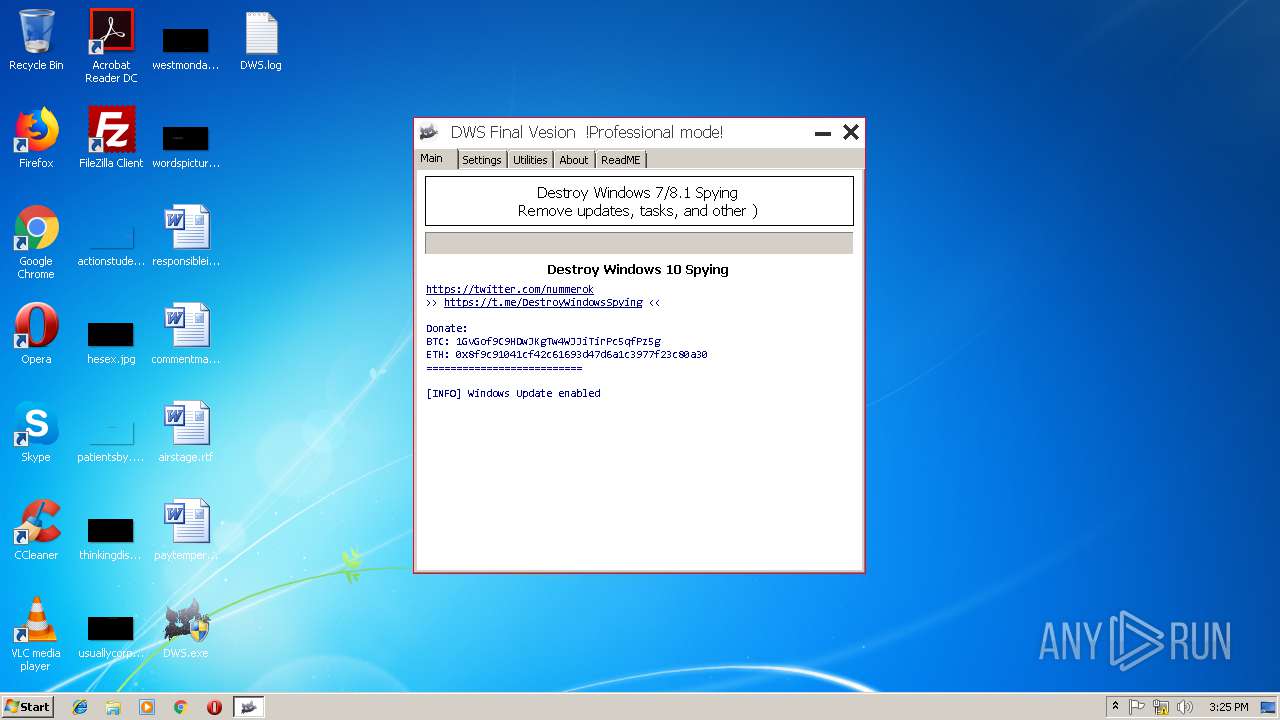
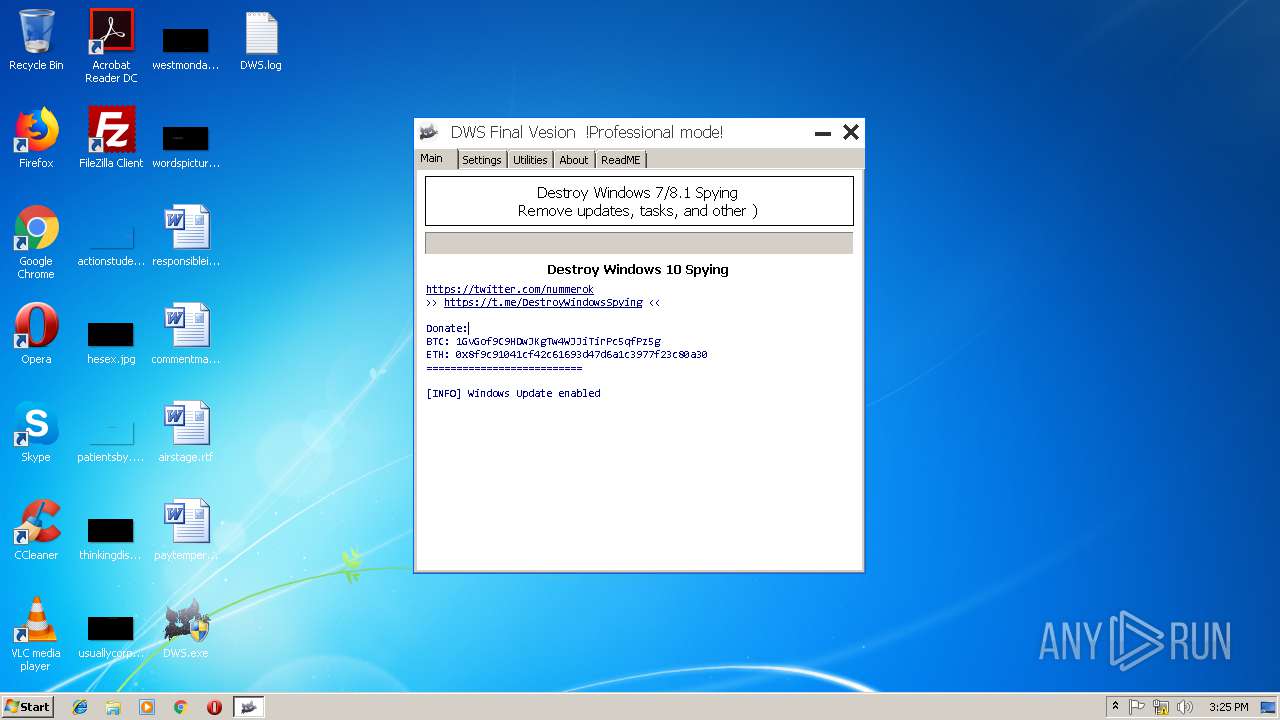
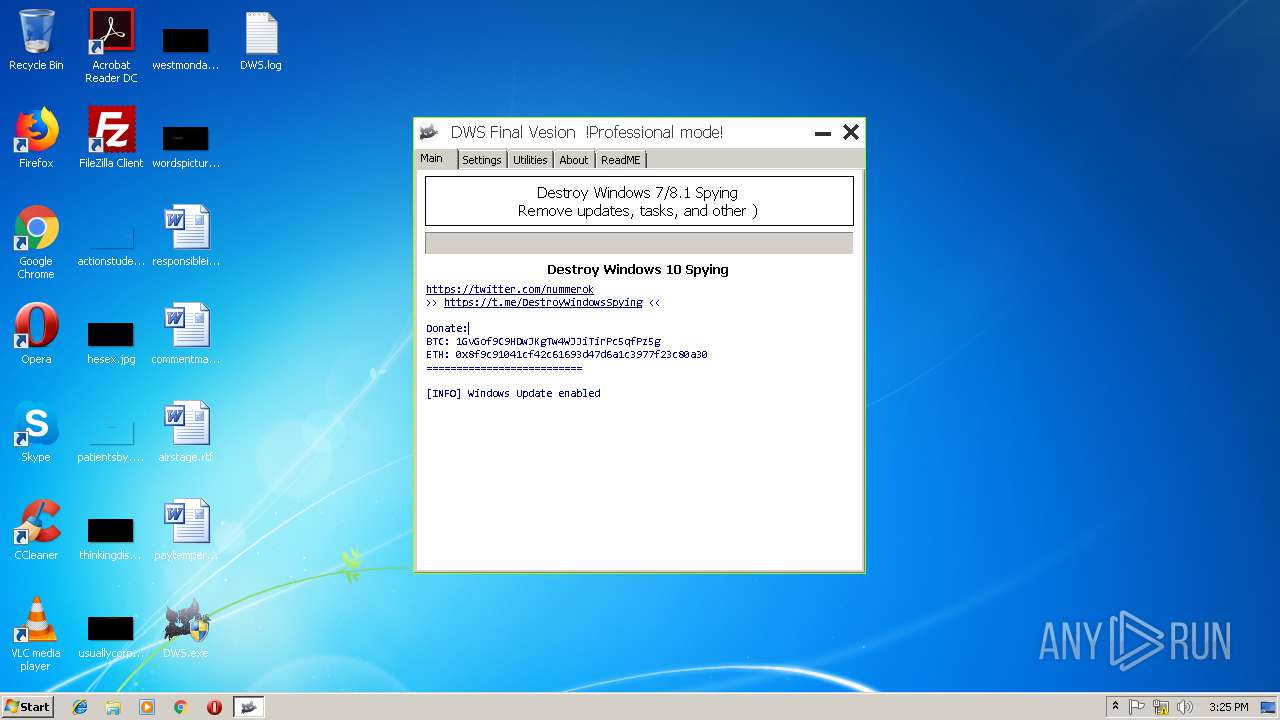
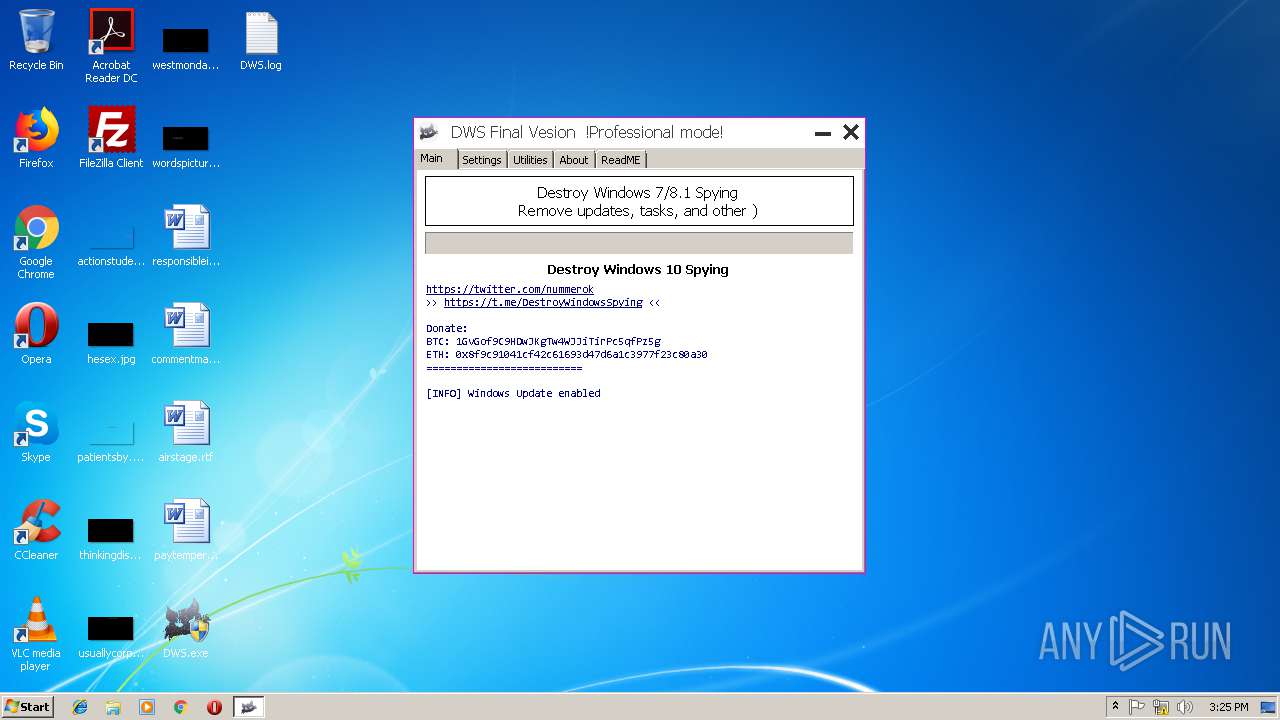
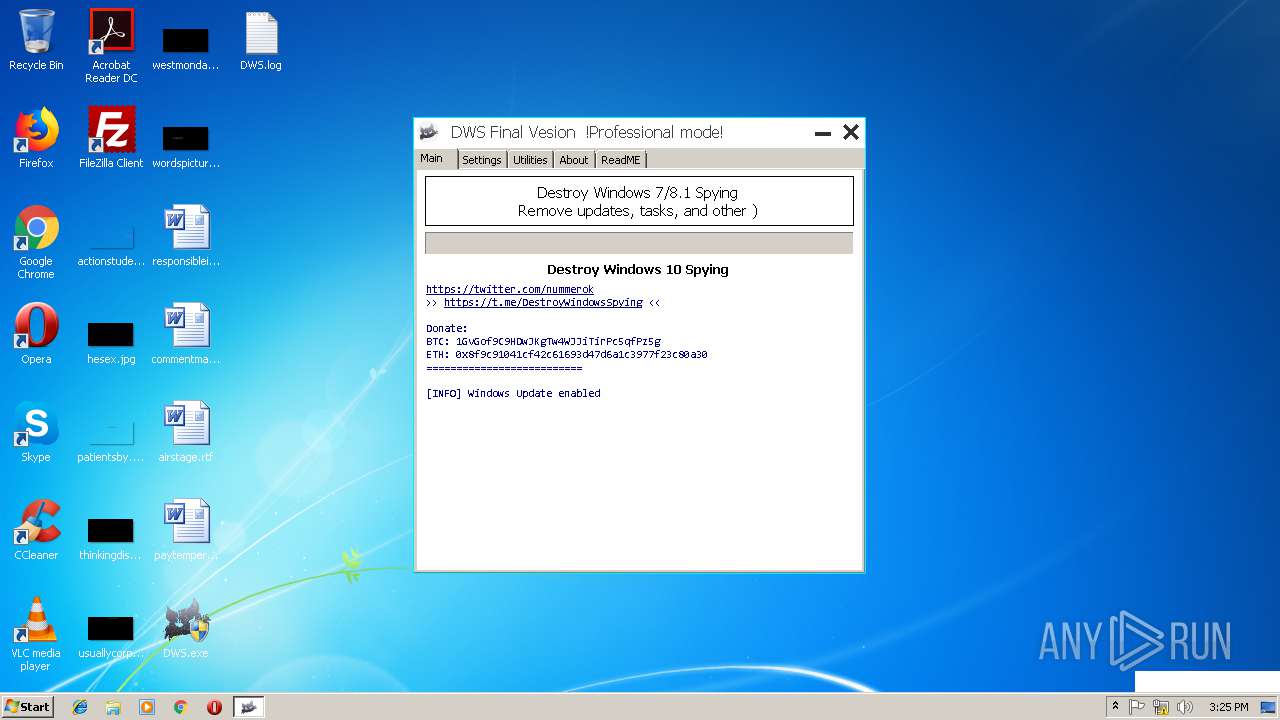
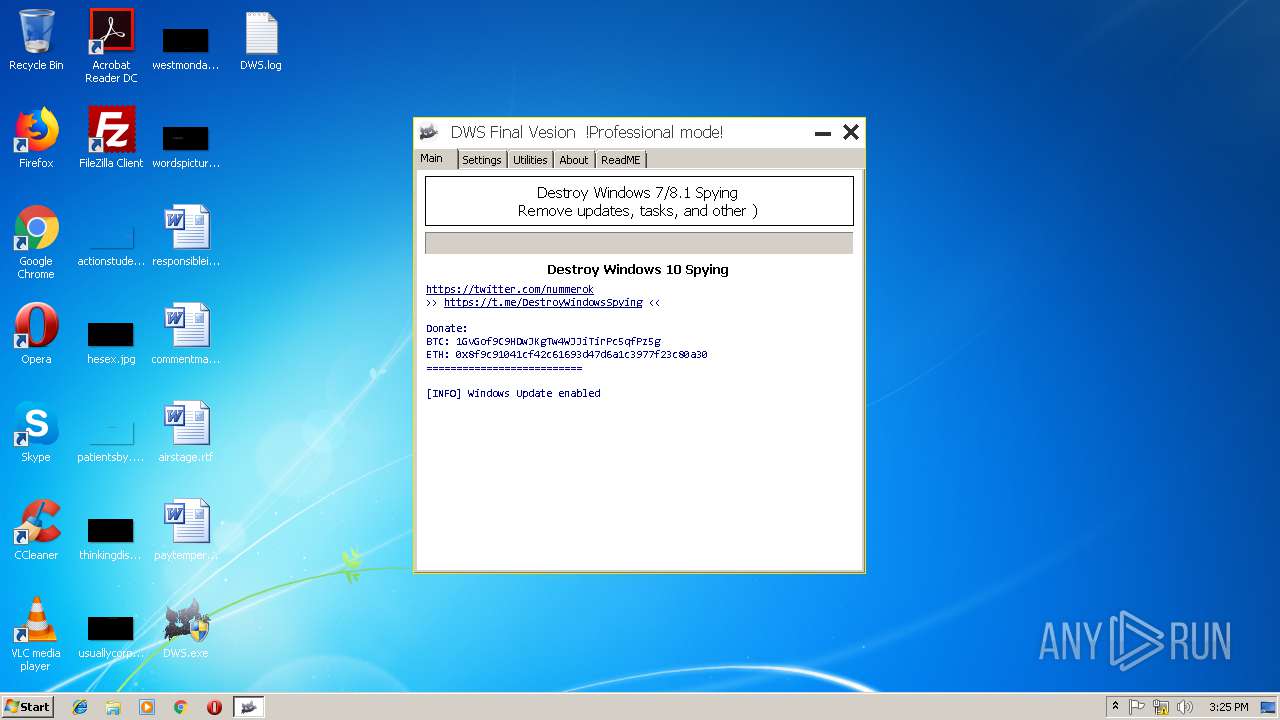
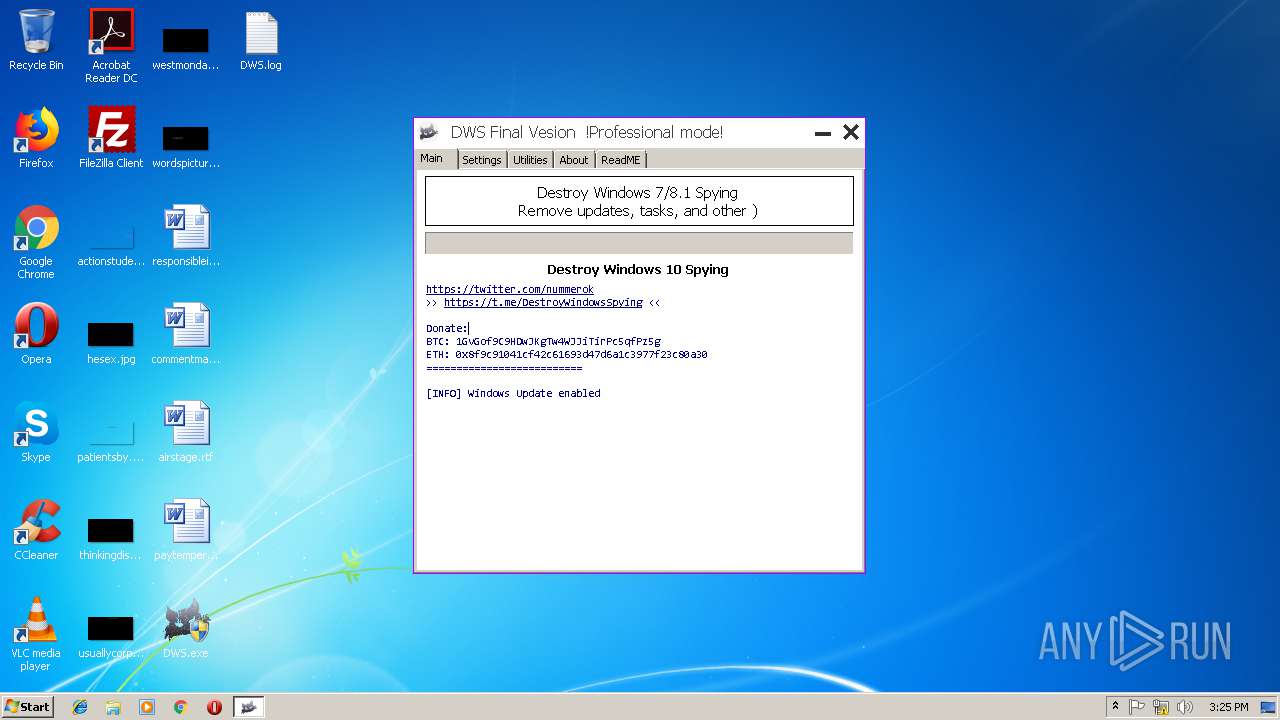
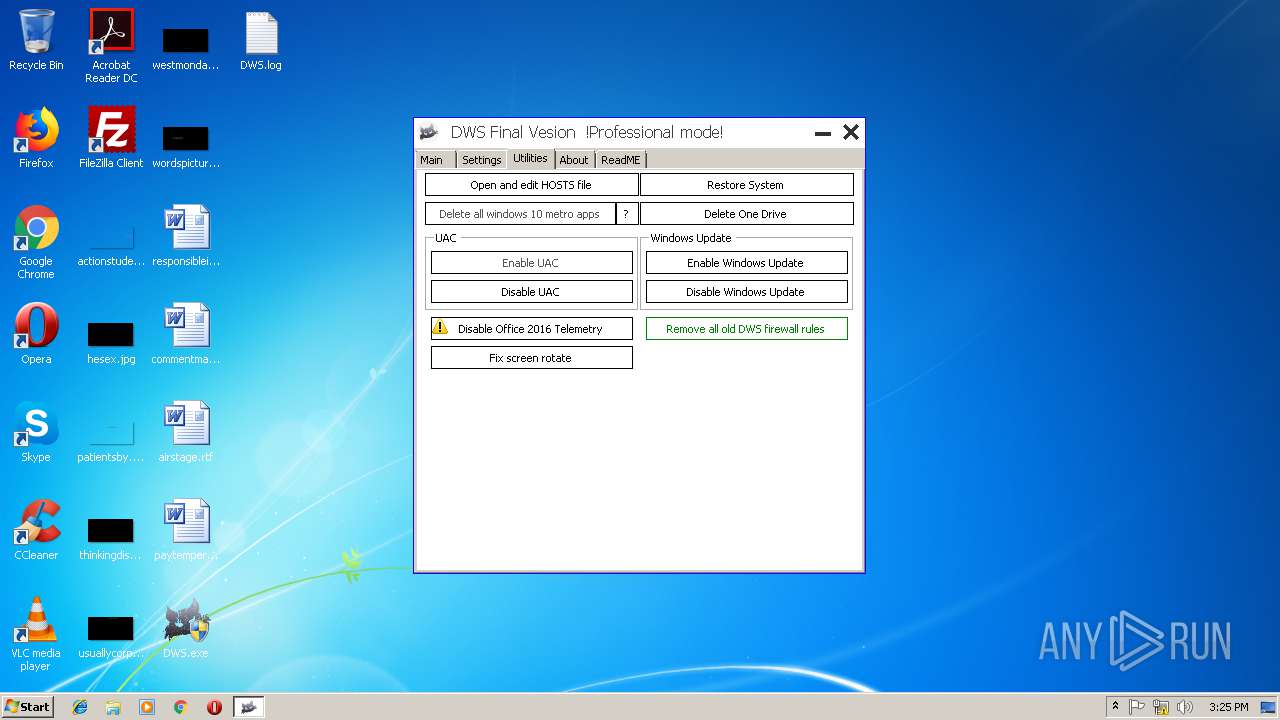
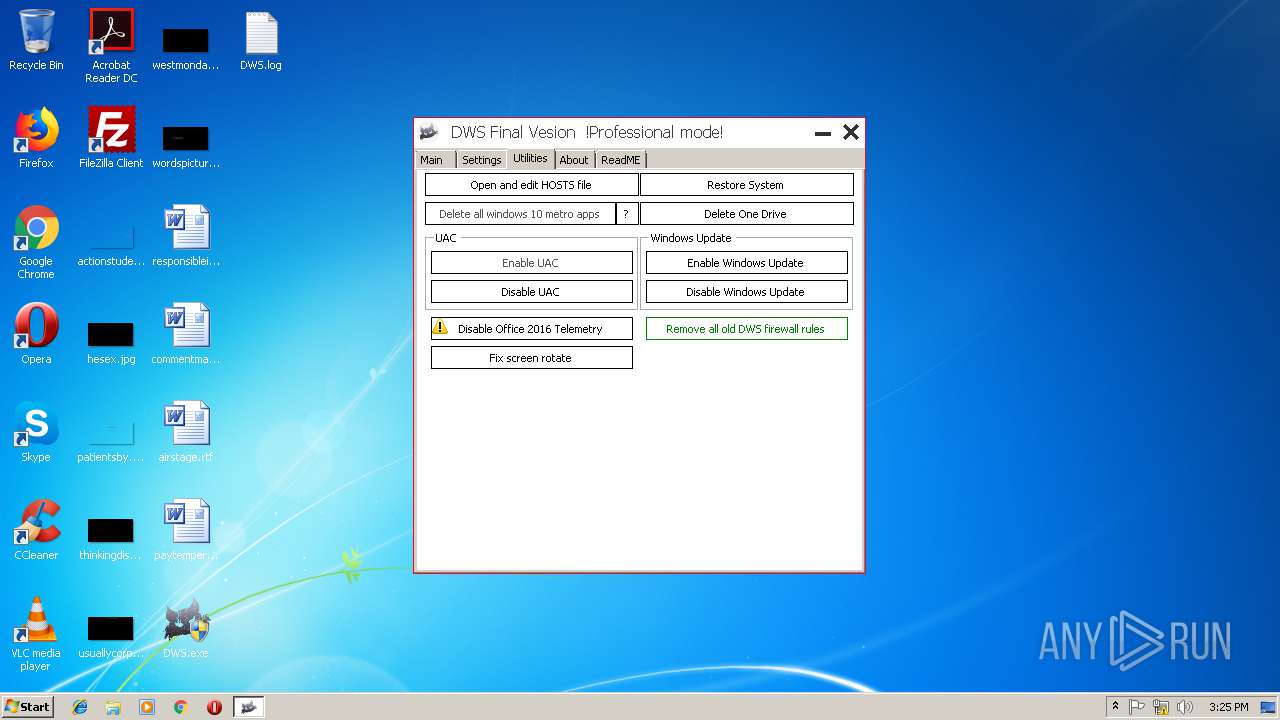
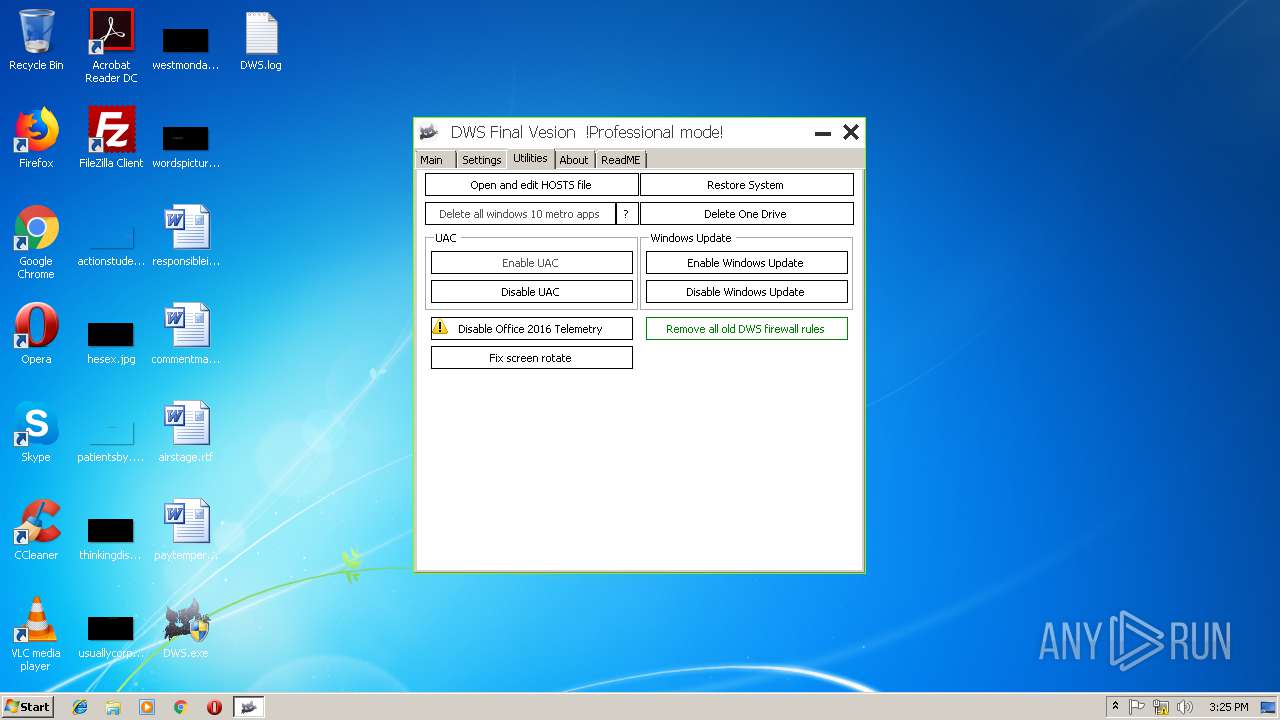
| File name: | DWS.exe |
| Full analysis: | https://app.any.run/tasks/4146ee21-f489-4ebf-b06e-13f1ae902157 |
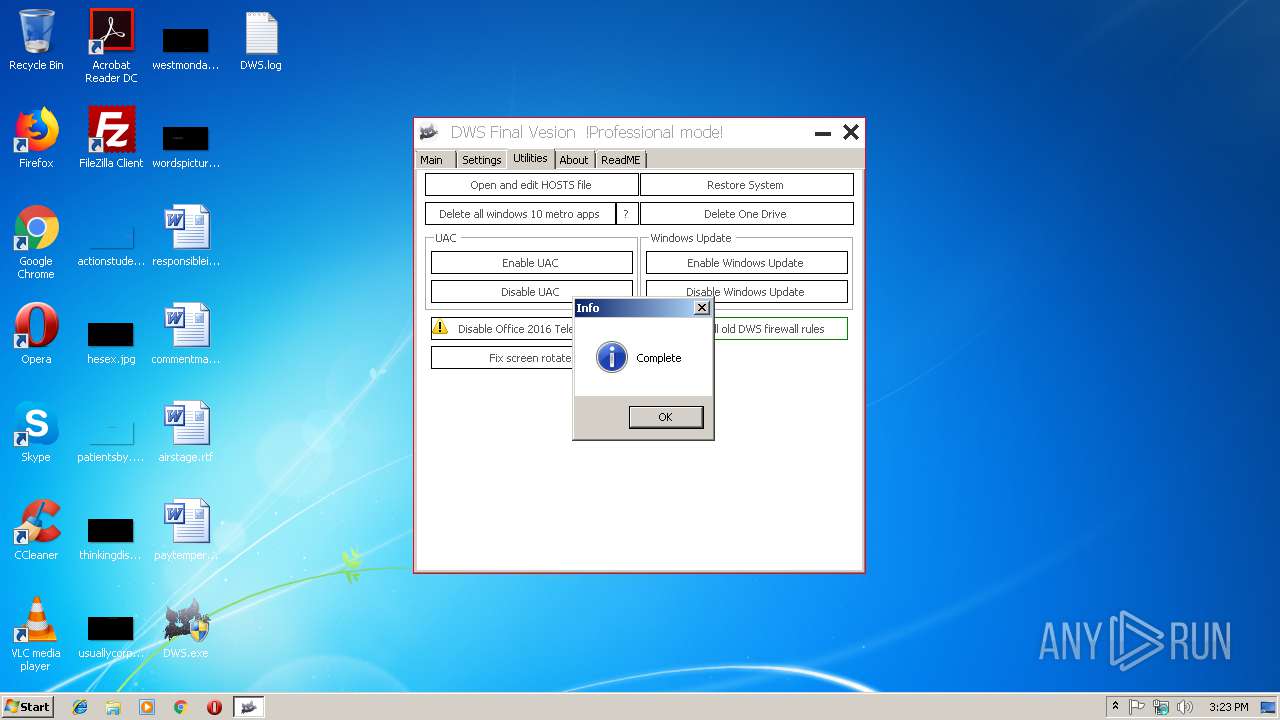
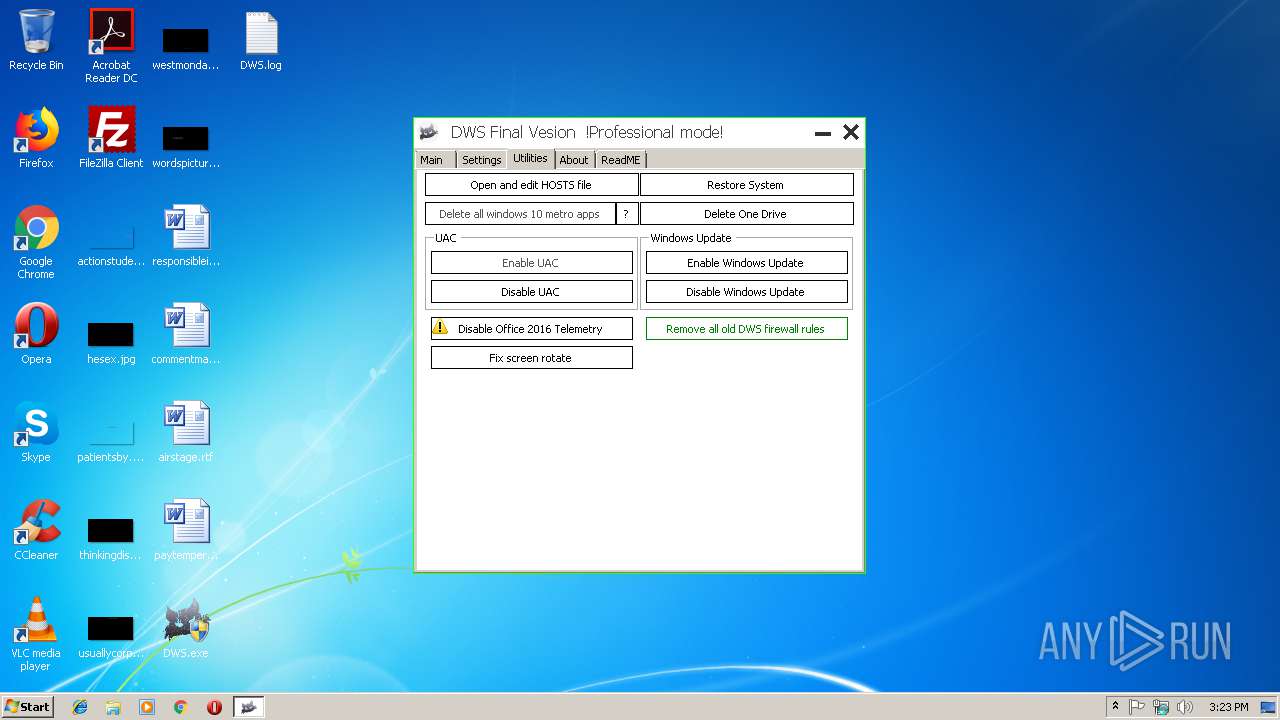
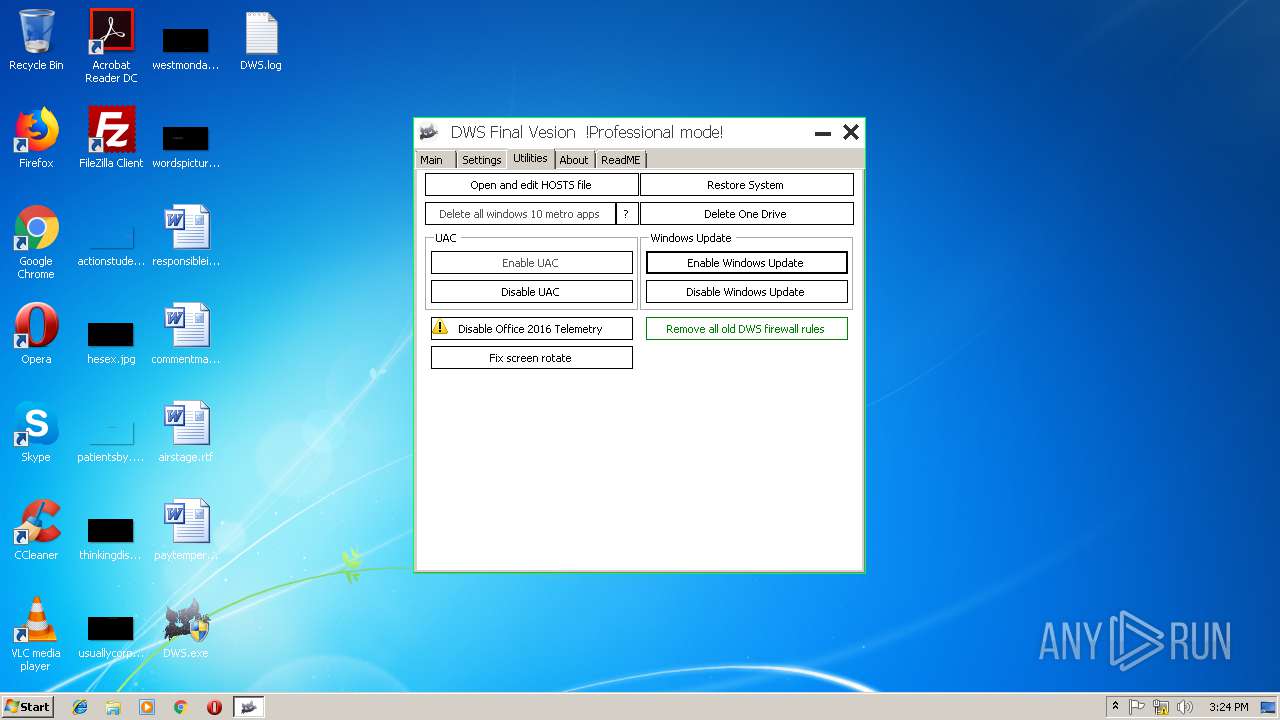
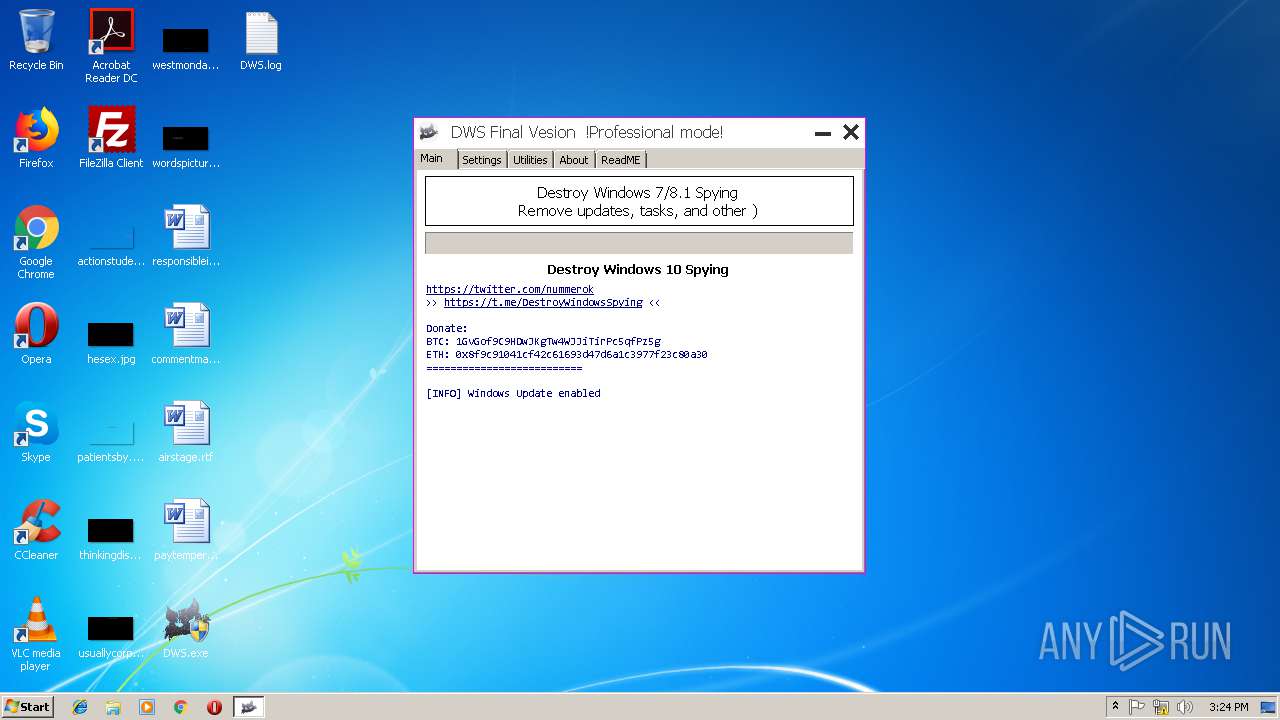
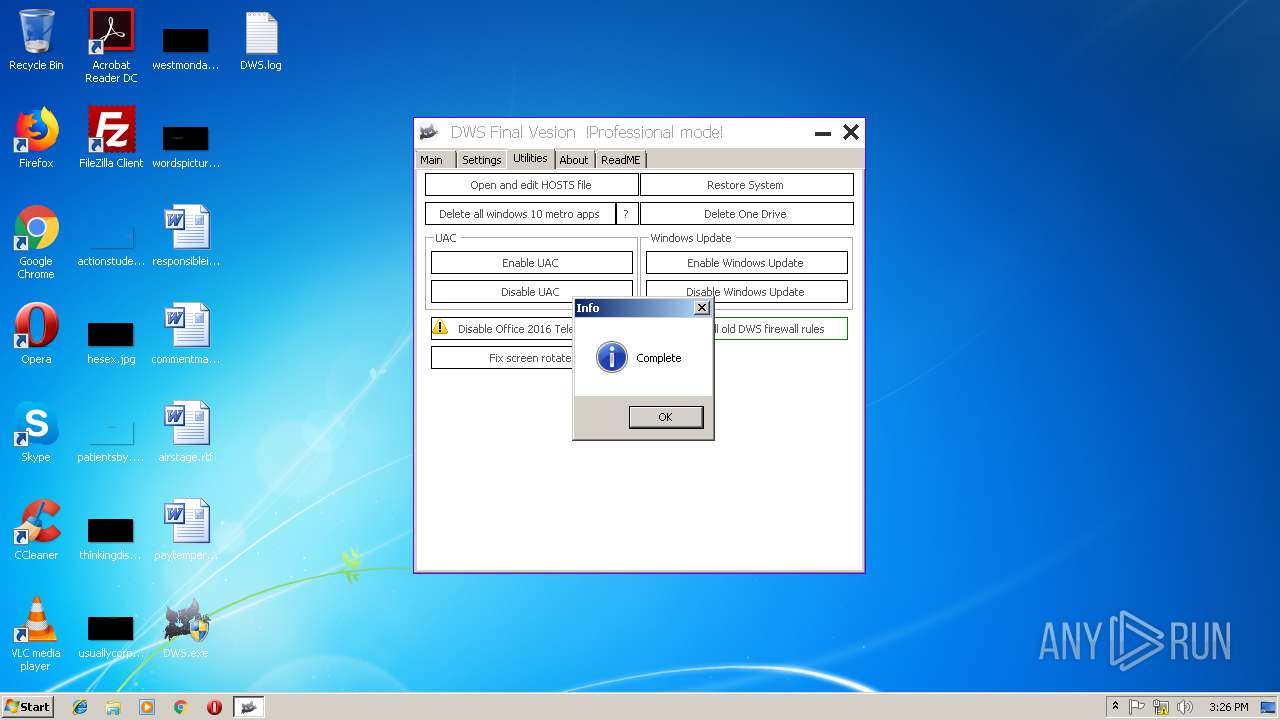
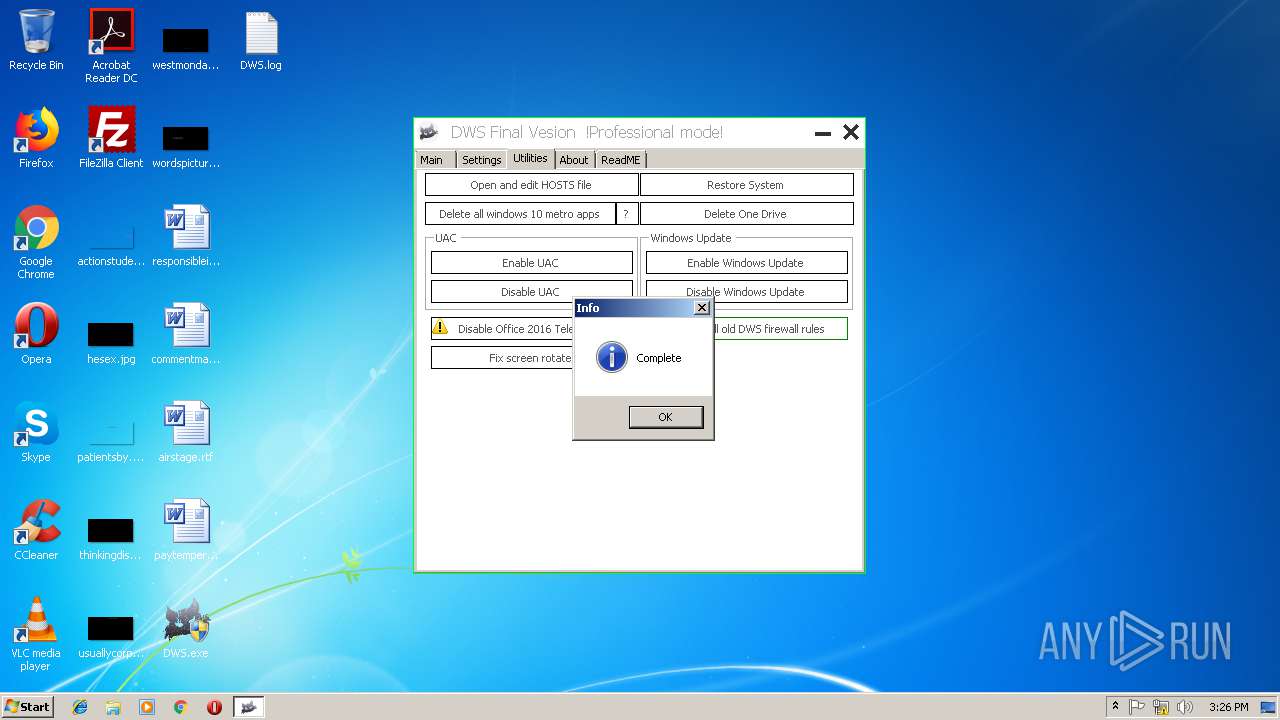
| Verdict: | Malicious activity |
| Analysis date: | February 10, 2019, 15:22:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 40CF9B8371664331A2D0C09DDBE23A41 |
| SHA1: | AB503EDA30AAC6105E3C76186BD0A43301F588F7 |
| SHA256: | 2F50EA4DD2B4A90622D1BA9D9B68DD40F1941F3A913B5D449100055A21552BF4 |
| SSDEEP: | 6144:2a8IIWIYfOfeDhzQL/24yrKvjGHWp95zQ8bbm+BF+:2yxIYTG0KvjGCbzvbb7B4 |
MALICIOUS
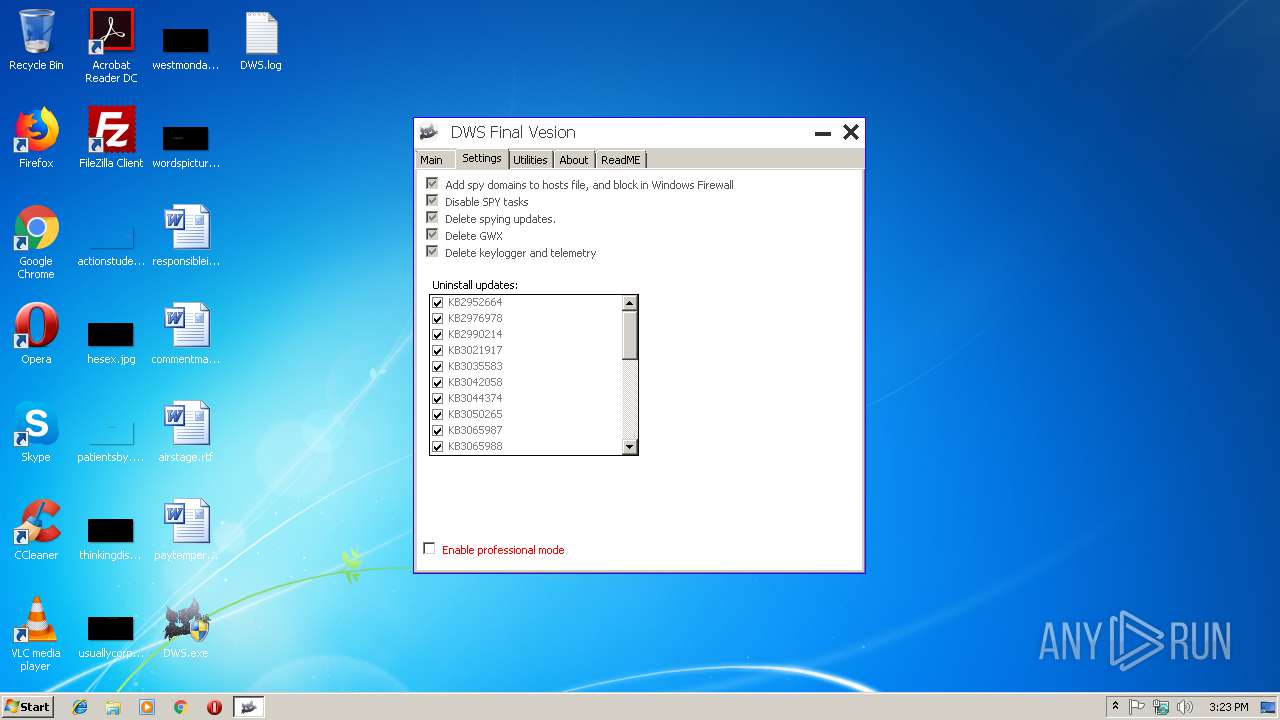
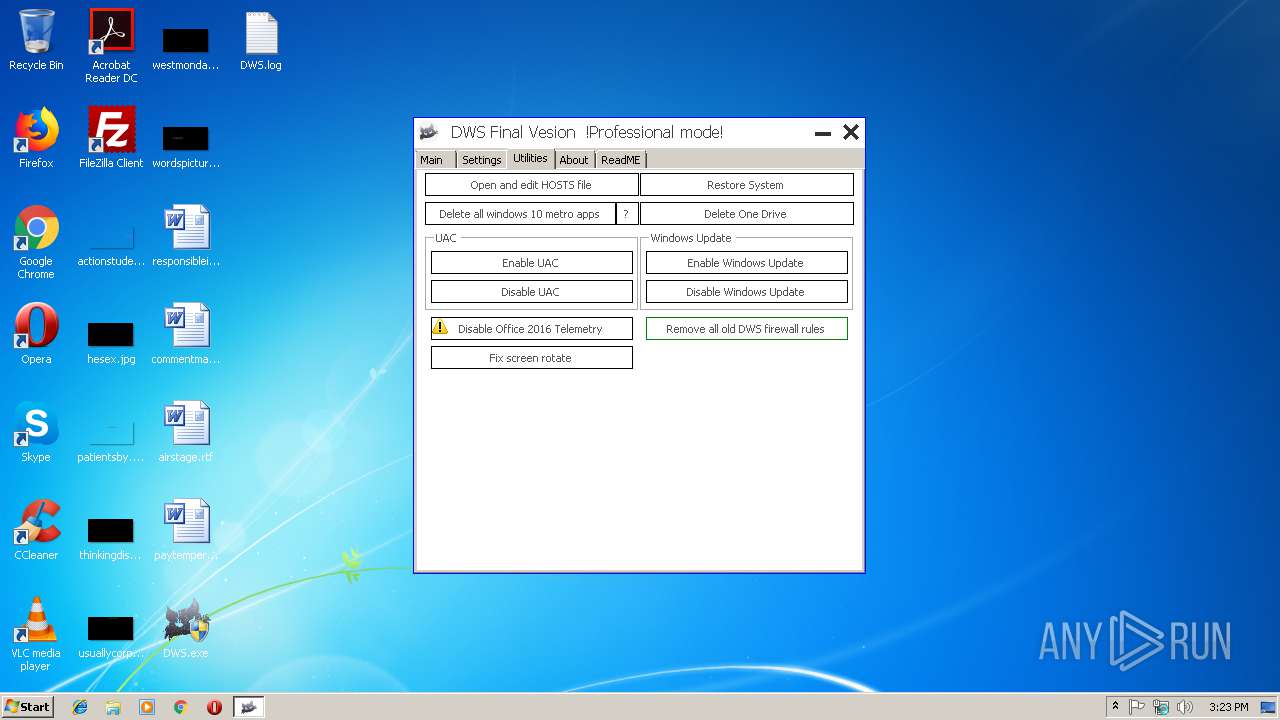
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3224)
- cmd.exe (PID: 3960)
- cmd.exe (PID: 3008)
- cmd.exe (PID: 3816)
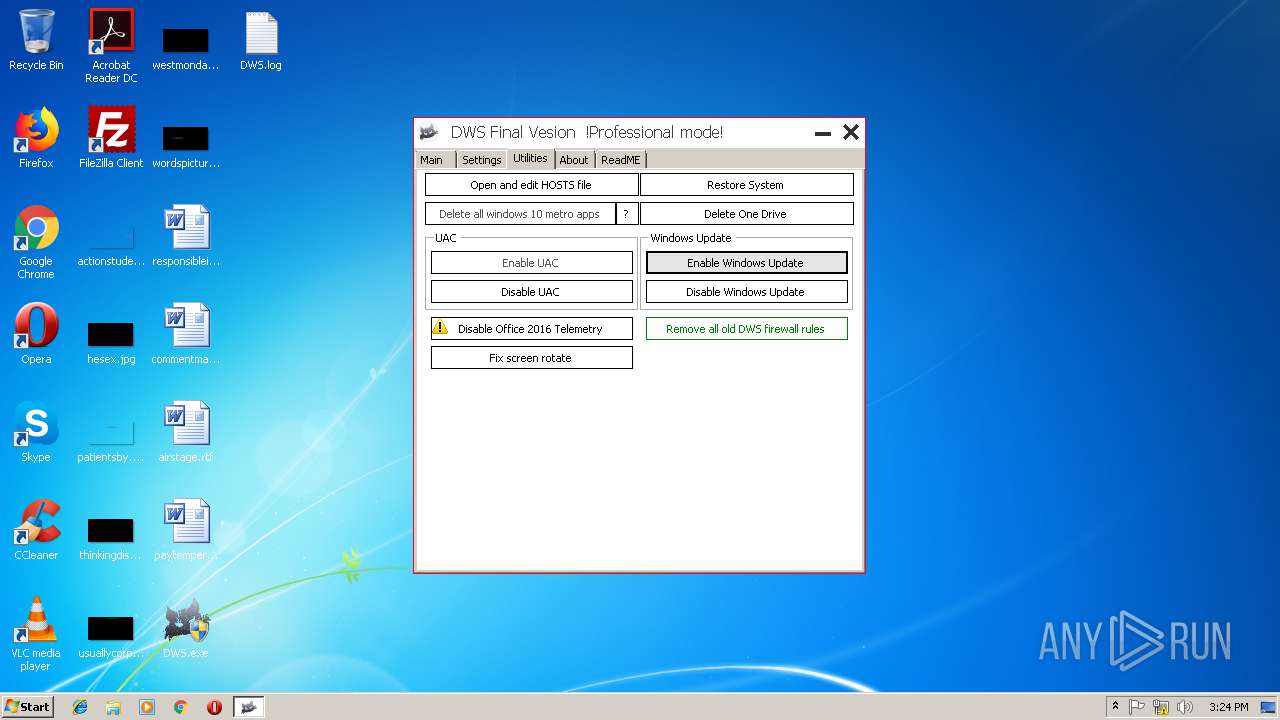
Starts NET.EXE for service management
- cmd.exe (PID: 2320)
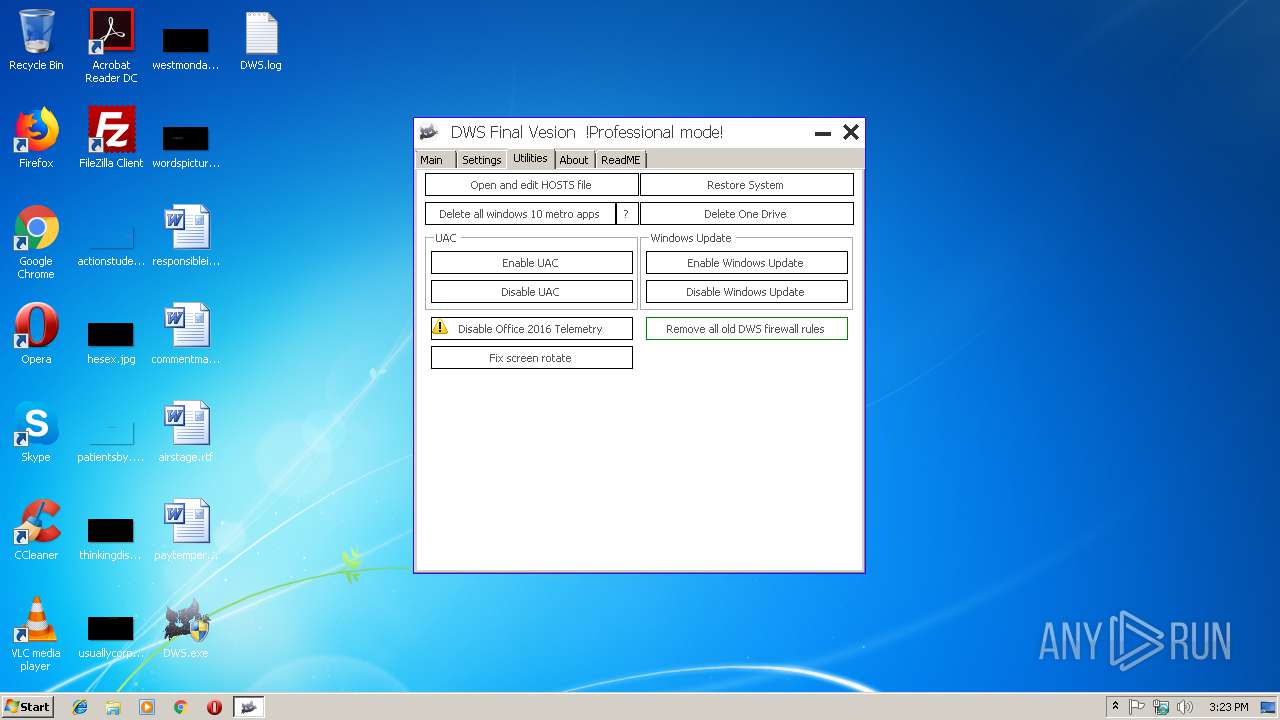
SUSPICIOUS
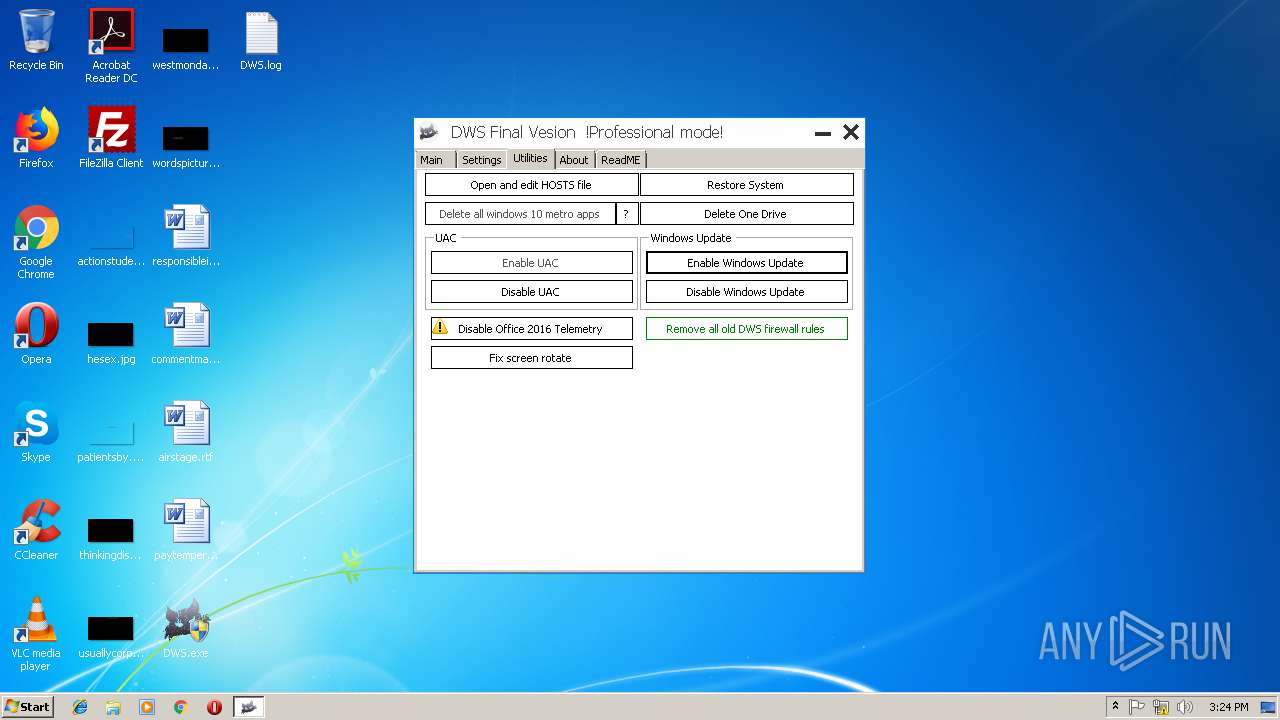
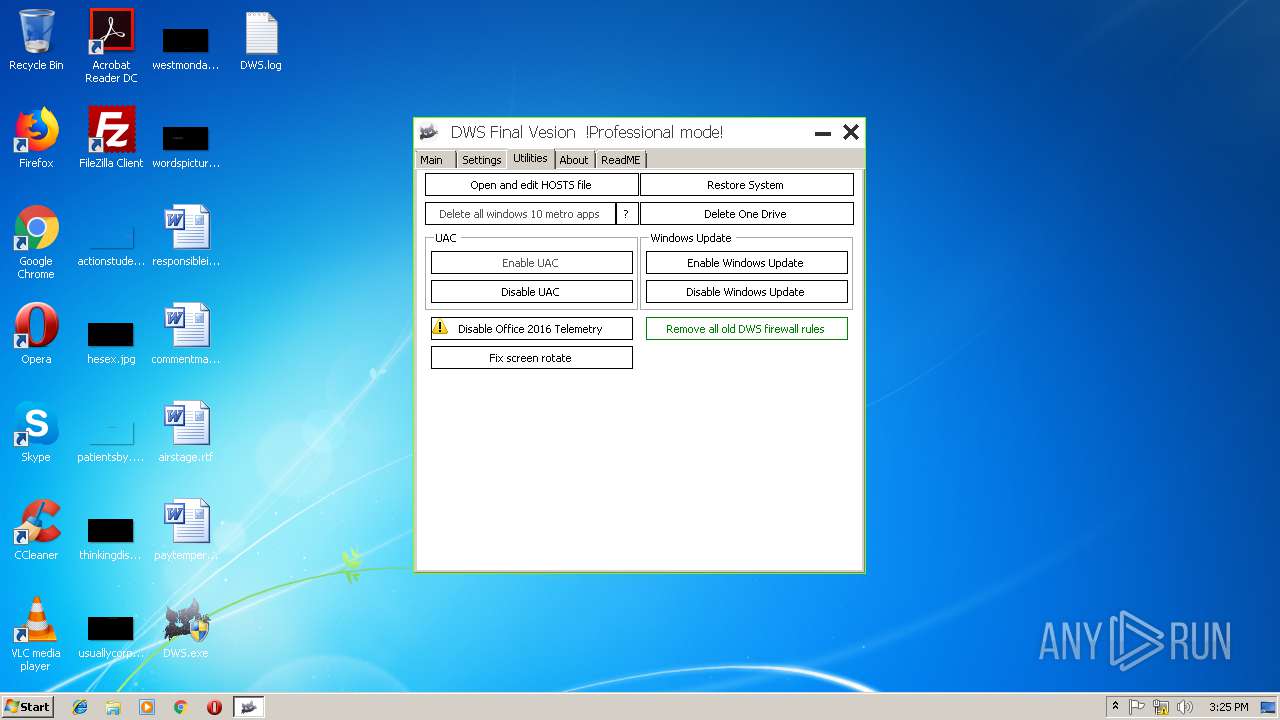
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2716)
- cmd.exe (PID: 2892)
Starts CMD.EXE for commands execution
- DWS.exe (PID: 2116)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2416)
- cmd.exe (PID: 3416)
- cmd.exe (PID: 3576)
- cmd.exe (PID: 1836)
Executes PowerShell scripts
- DWS.exe (PID: 2116)
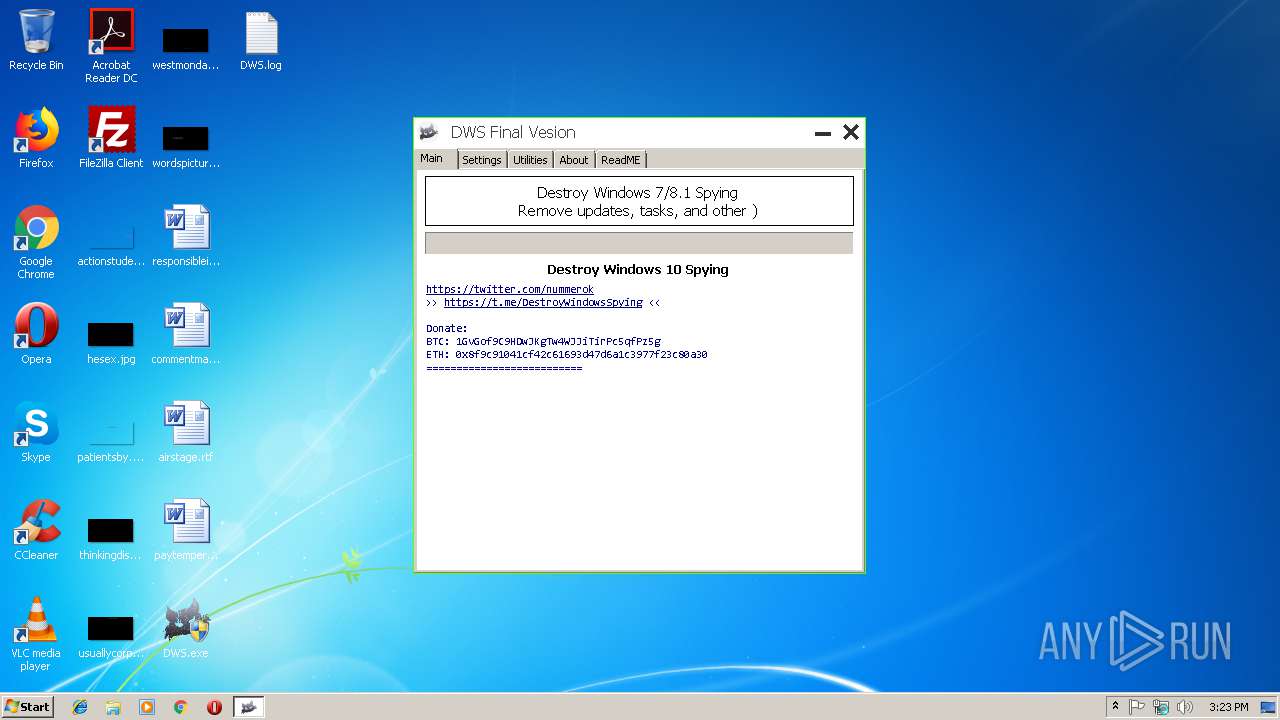
Creates files in the user directory
- powershell.exe (PID: 2760)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 3948)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:03:04 18:52:25+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 254464 |
| InitializedDataSize: | 72192 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x400be |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.2.2 |
| ProductVersionNumber: | 2.2.2.2 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | WZT |
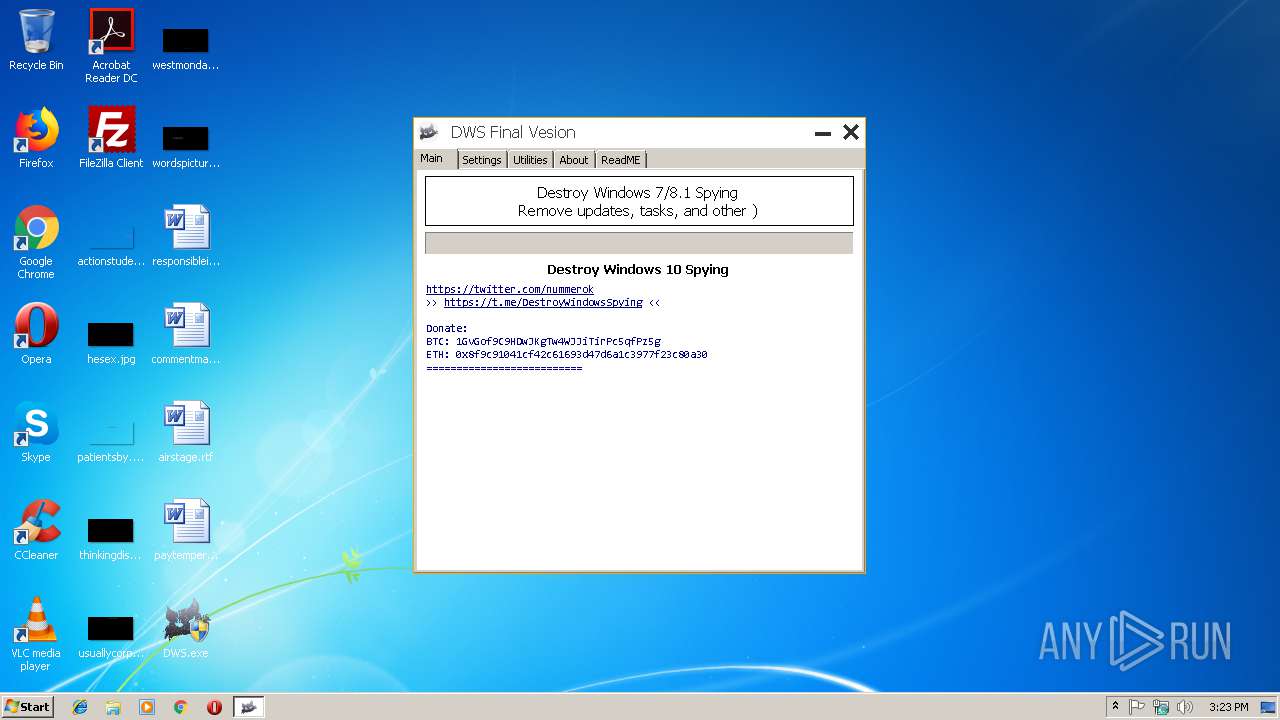
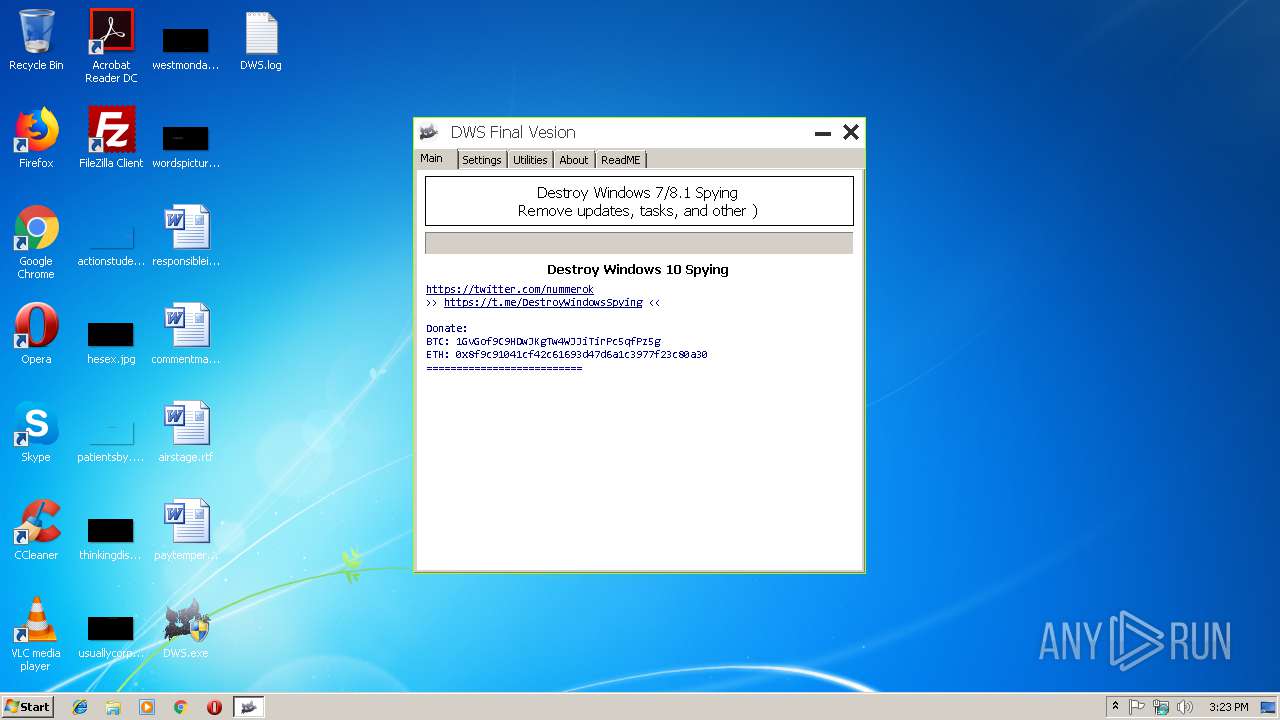
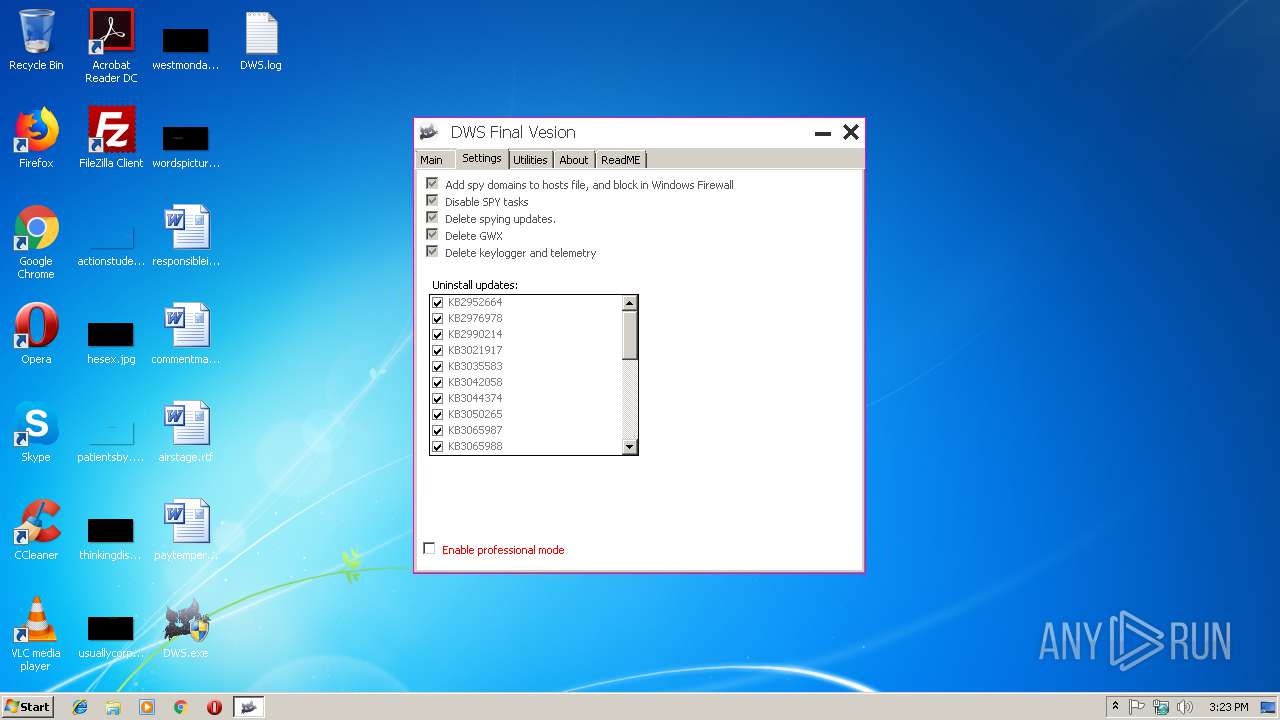
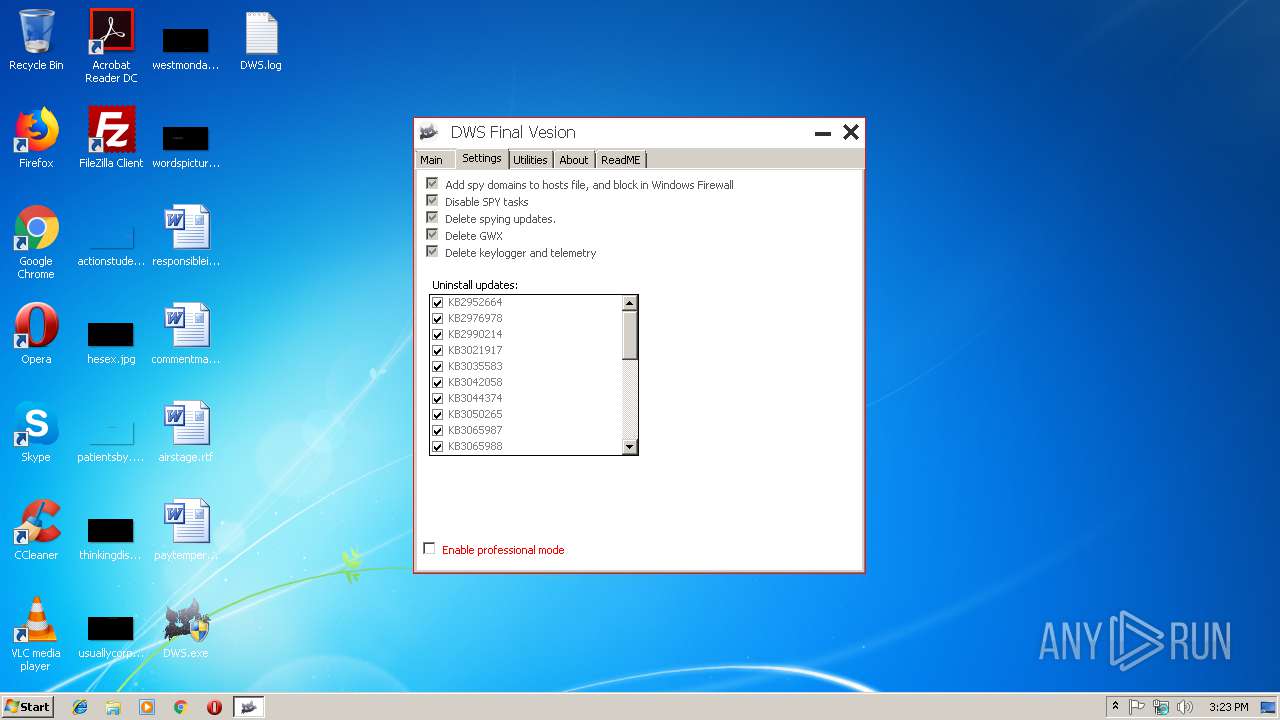
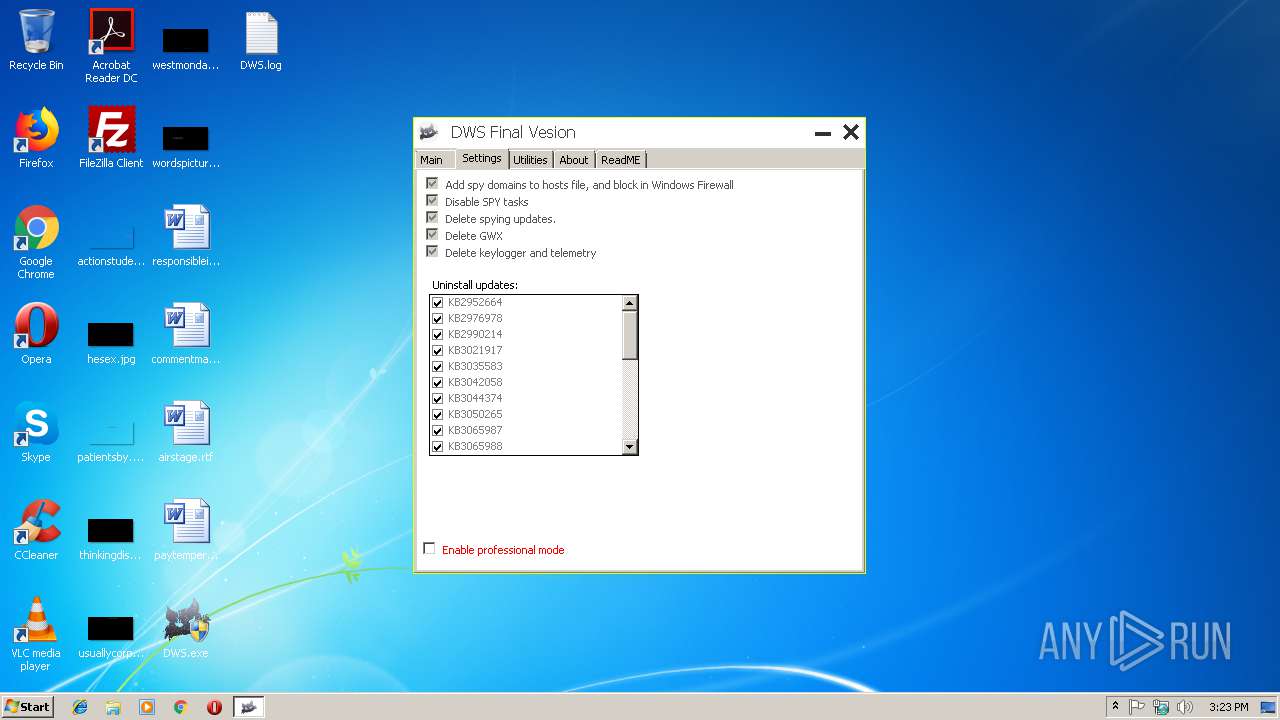
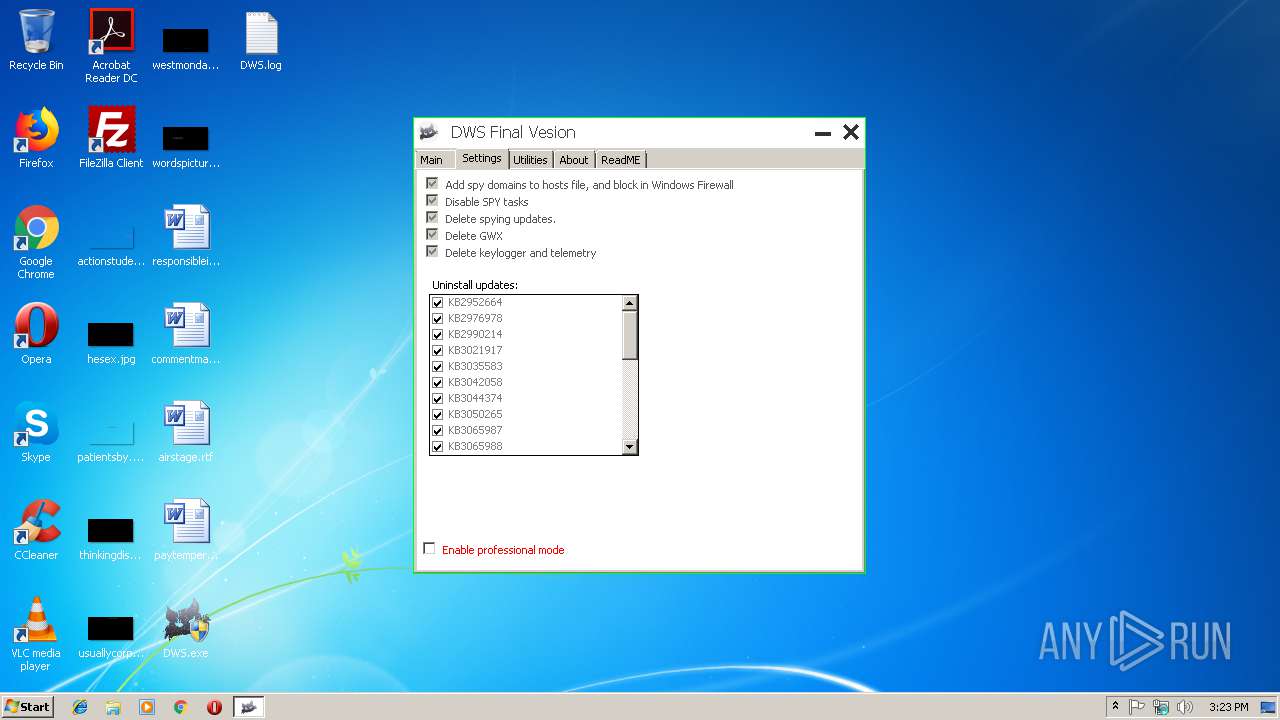
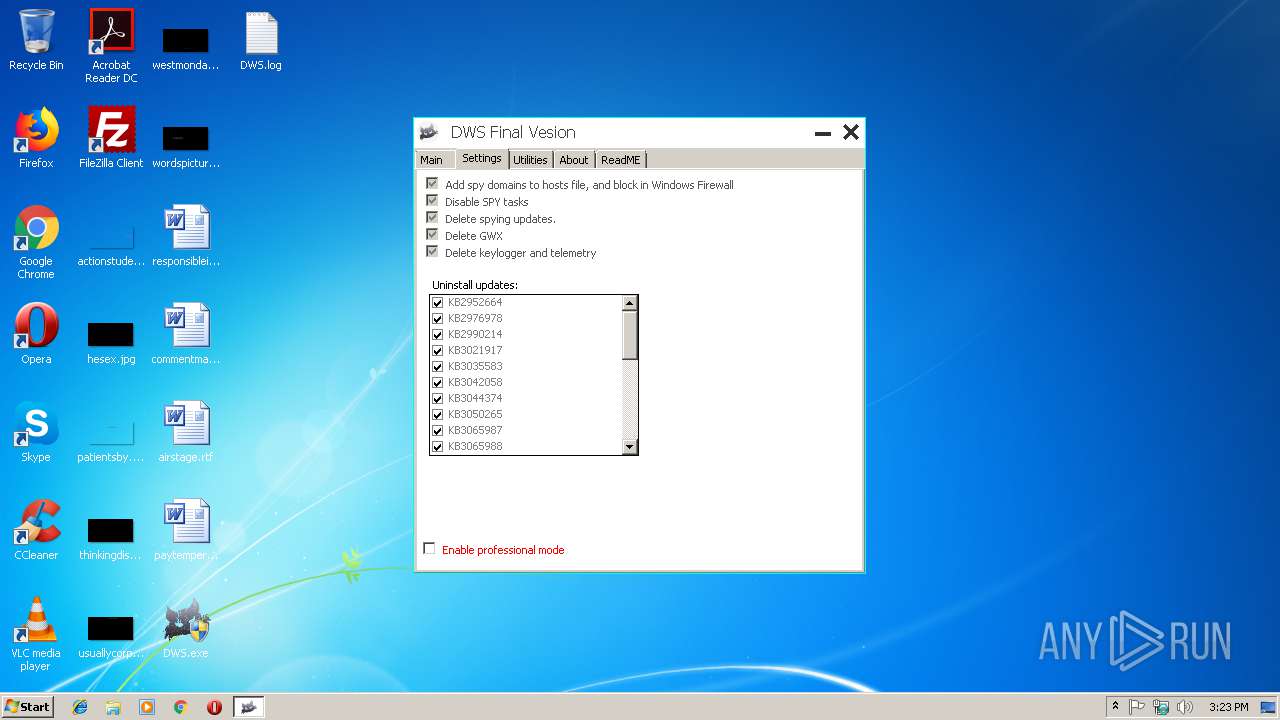
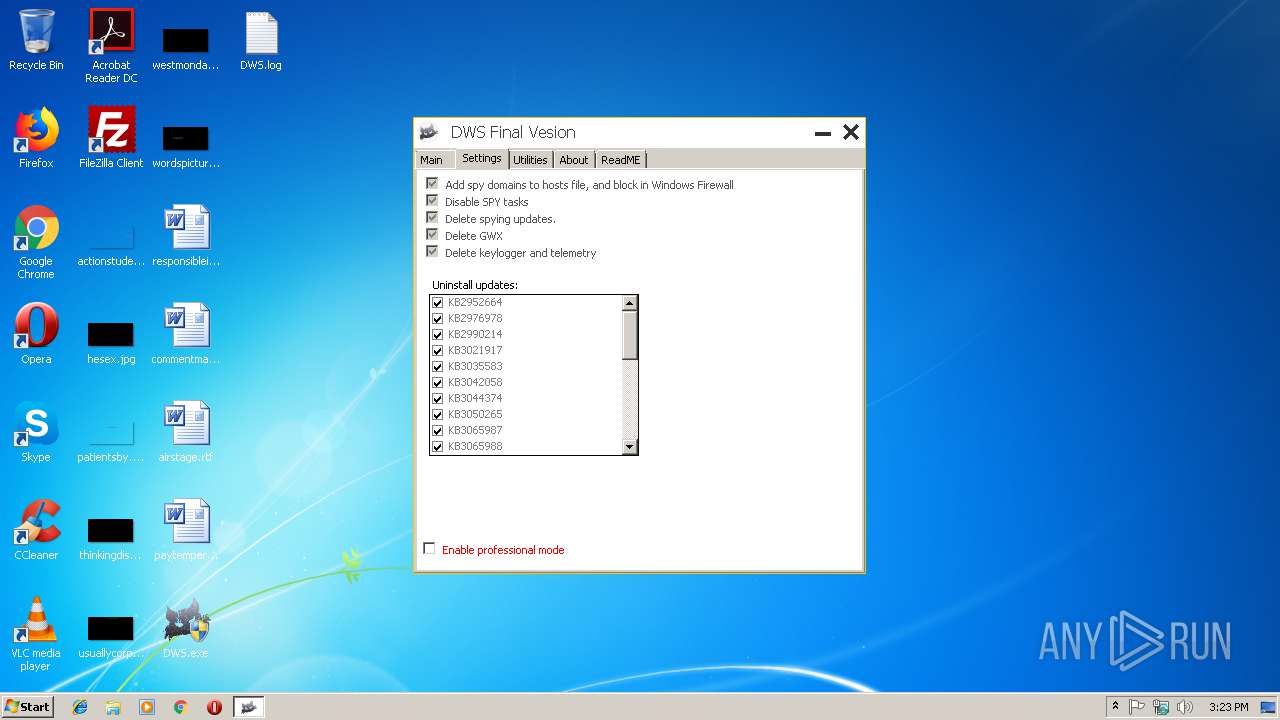
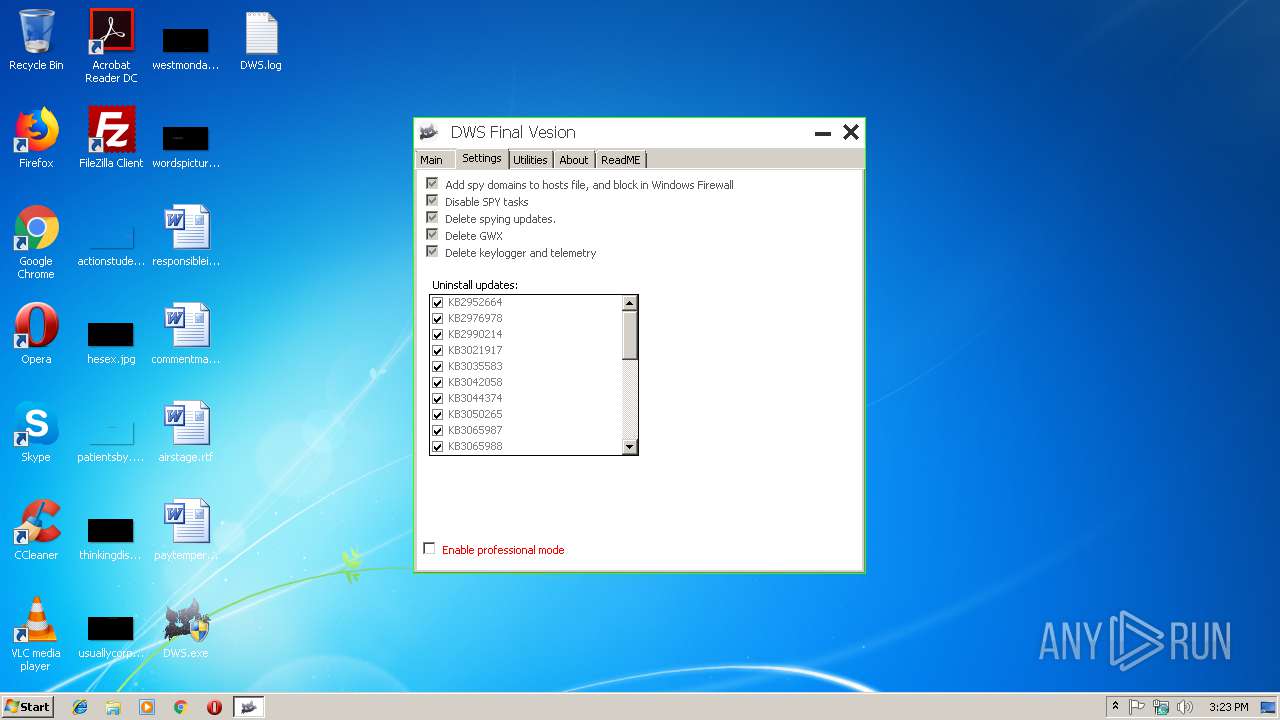
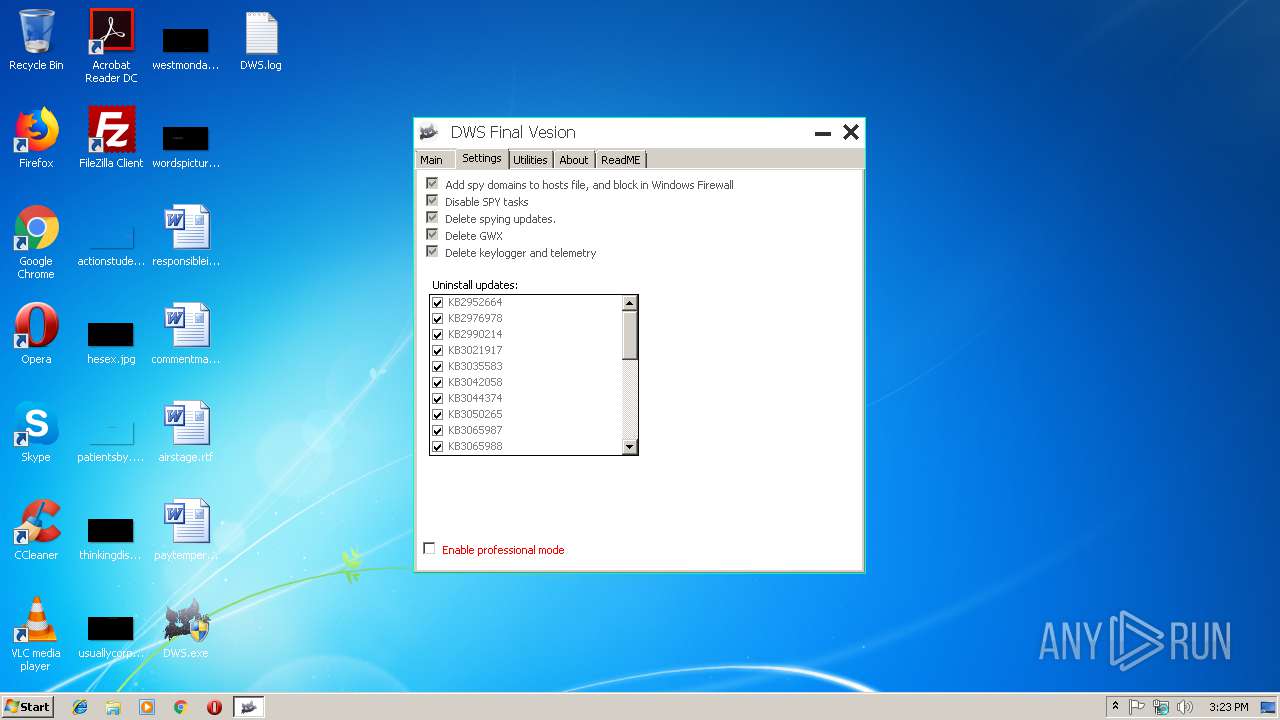
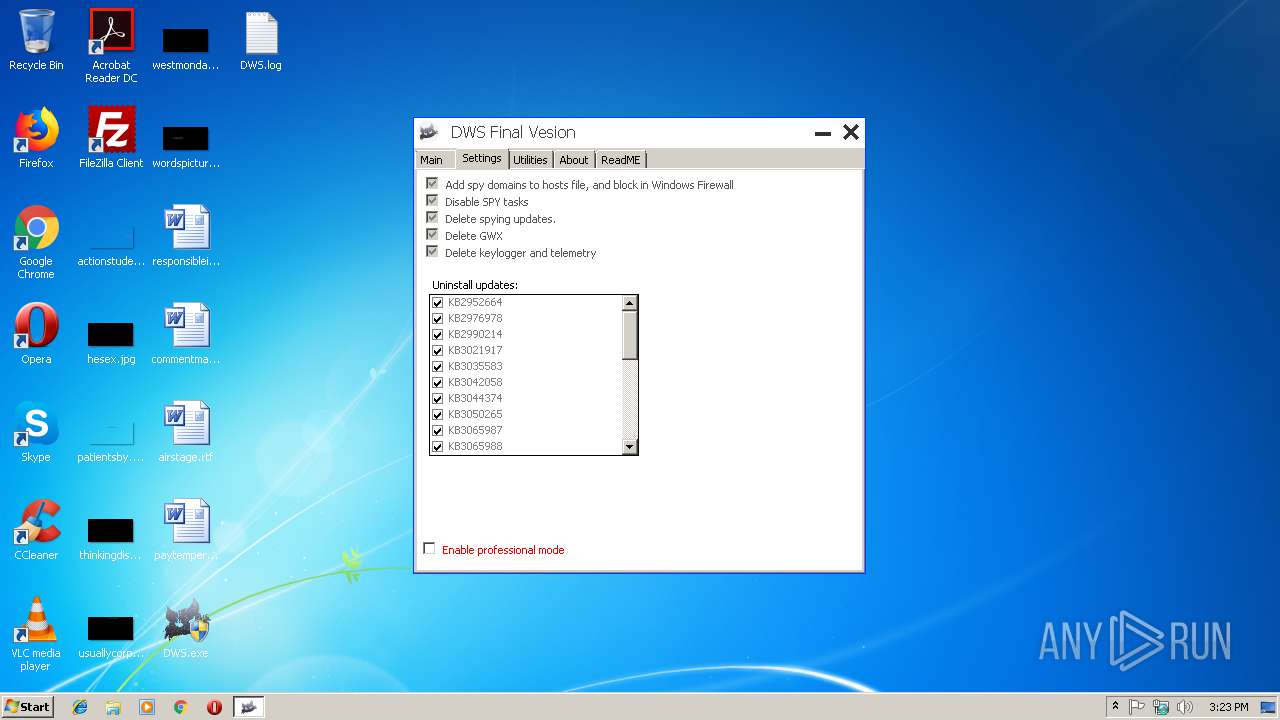
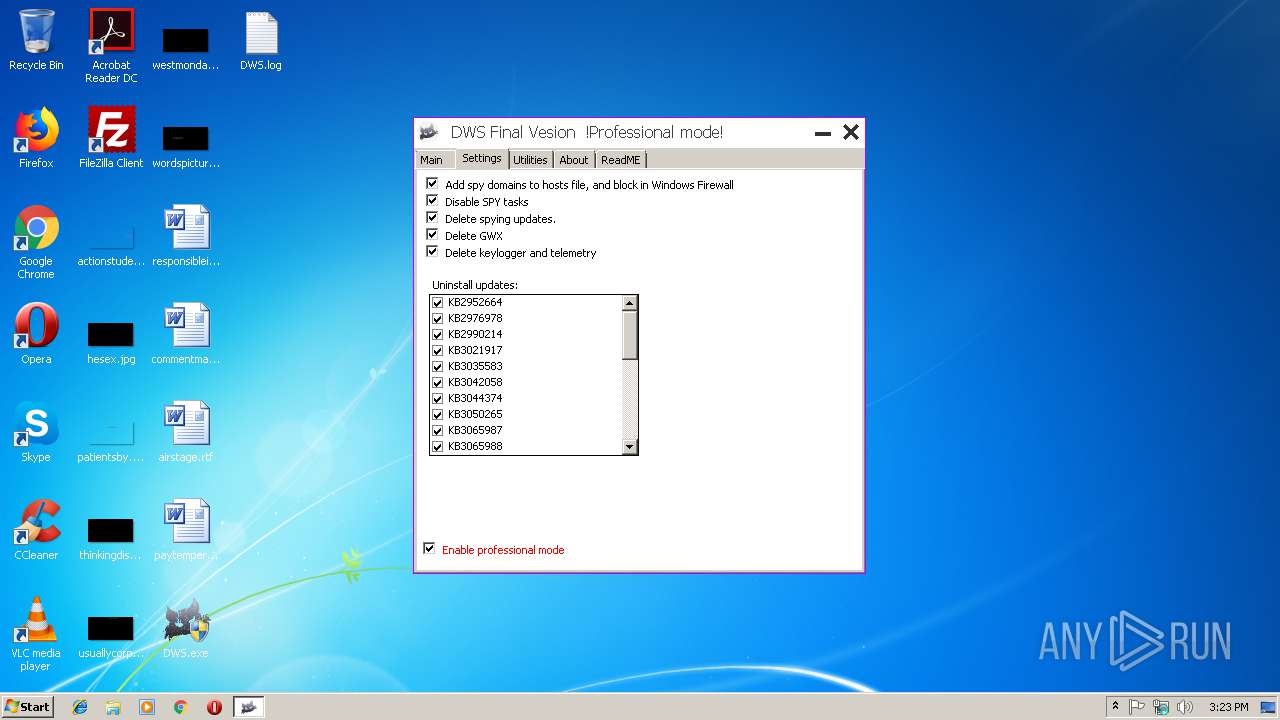
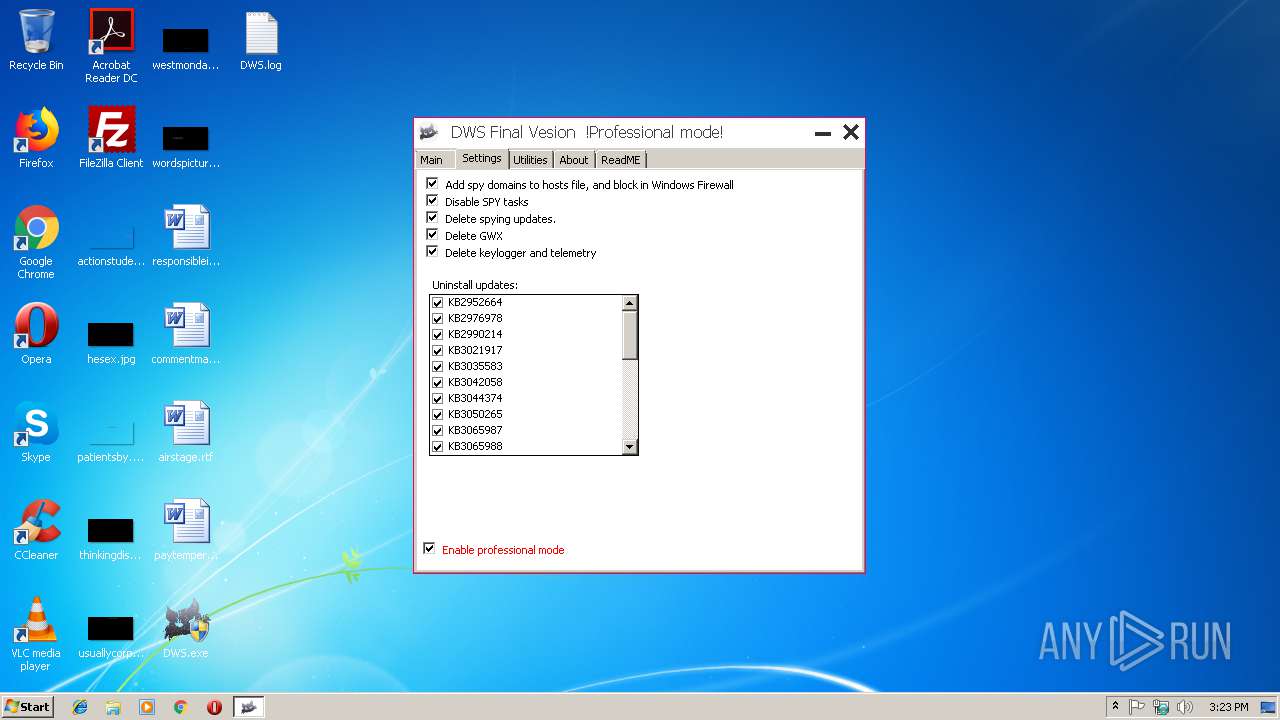
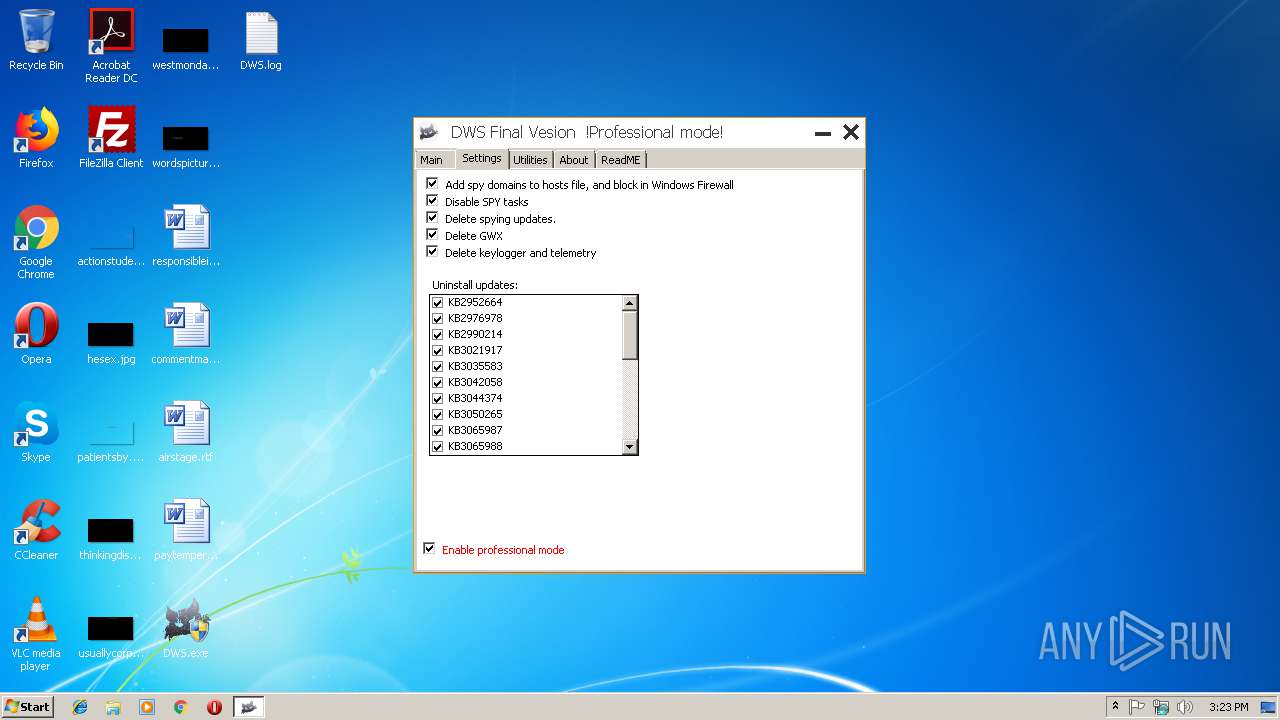
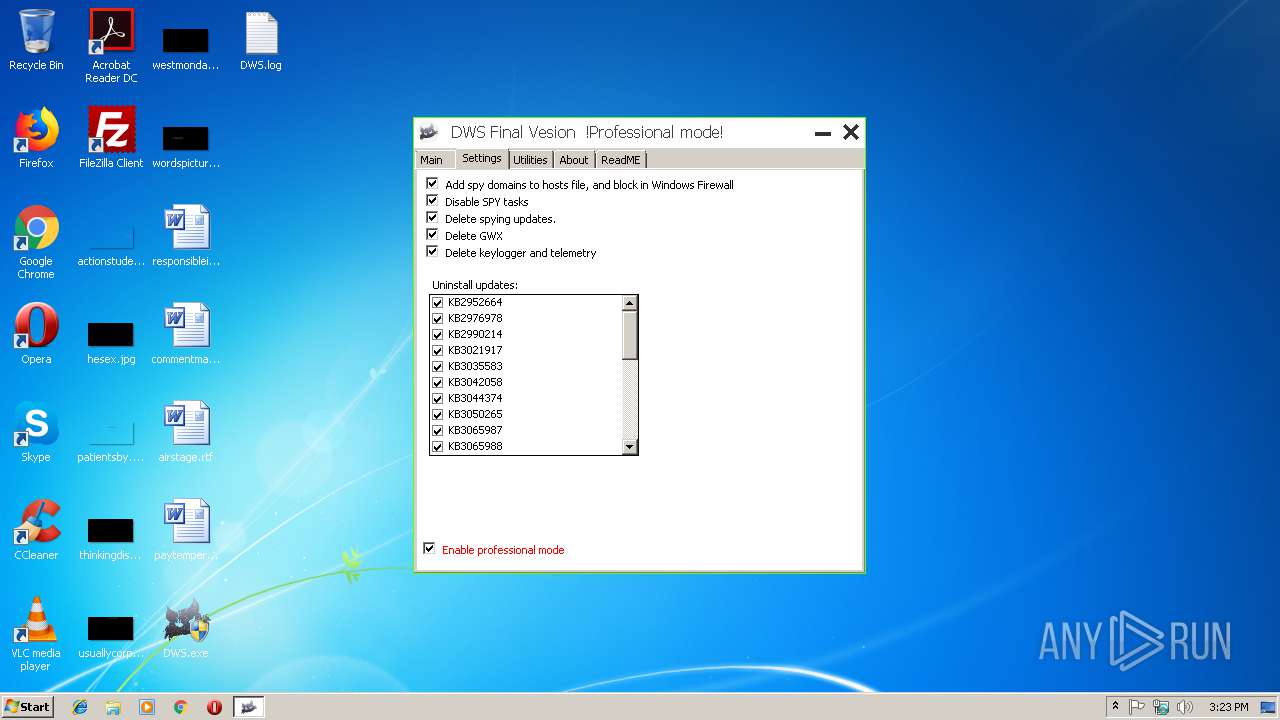
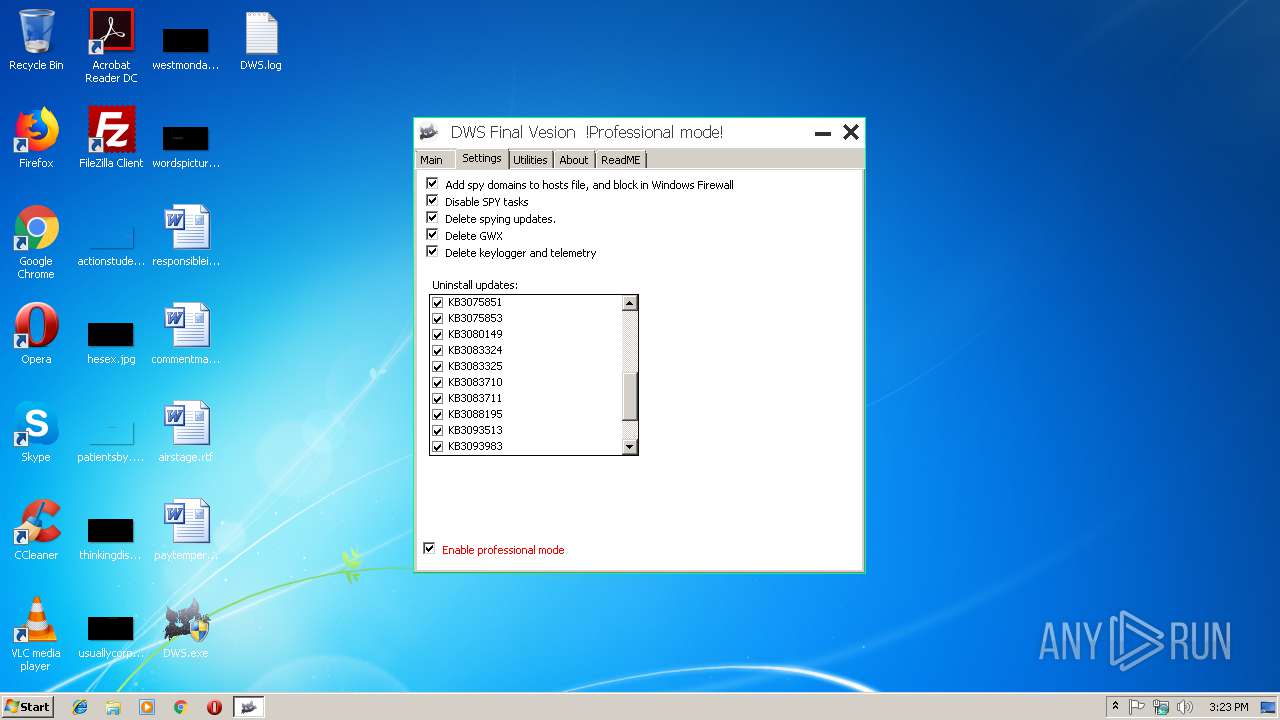
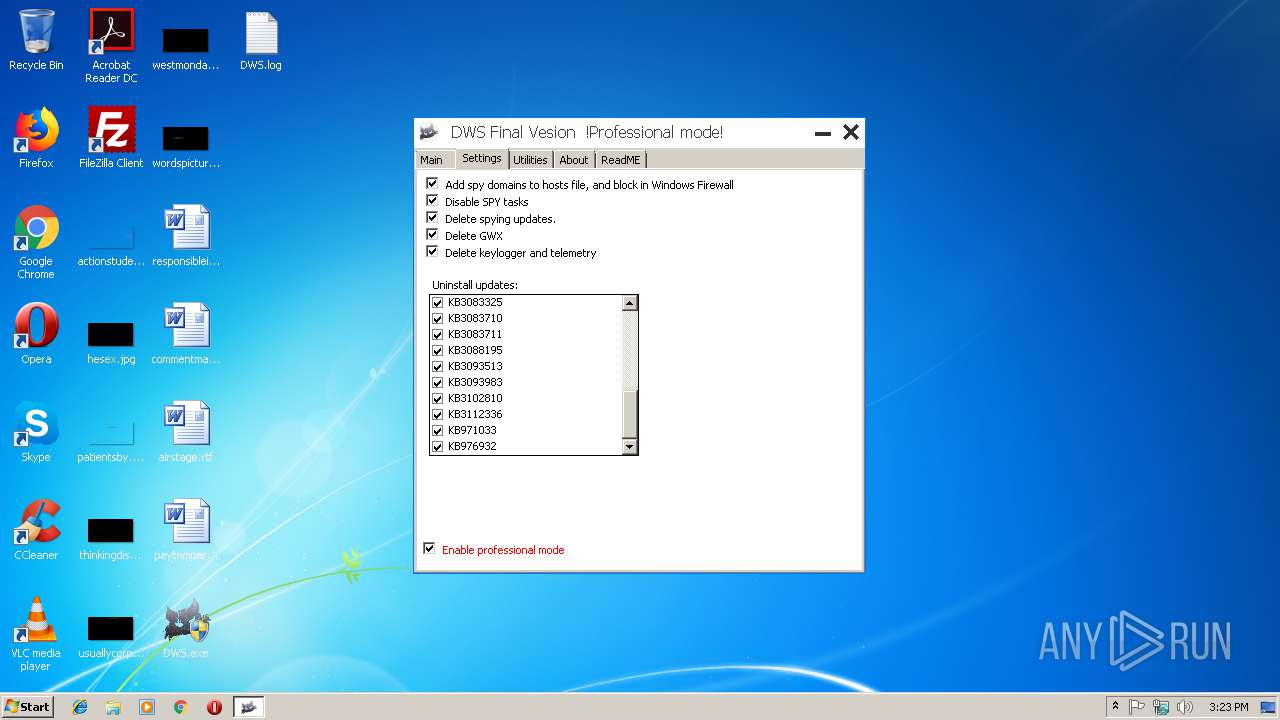
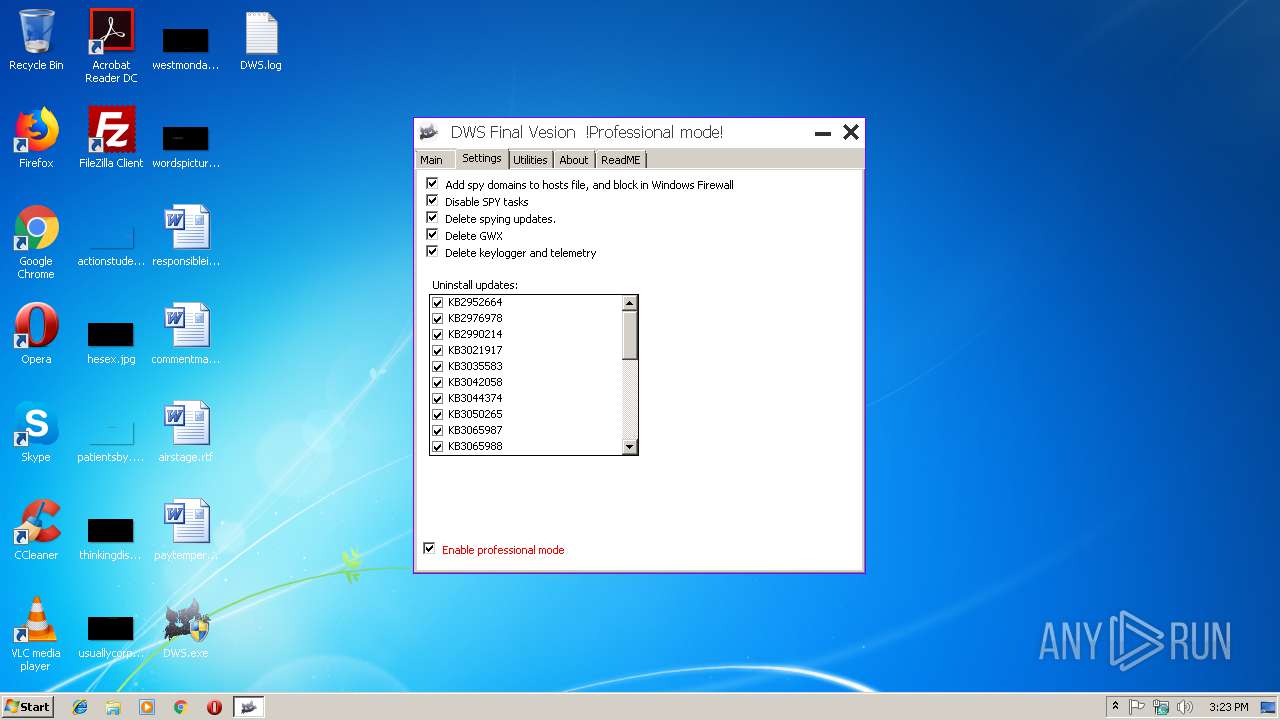
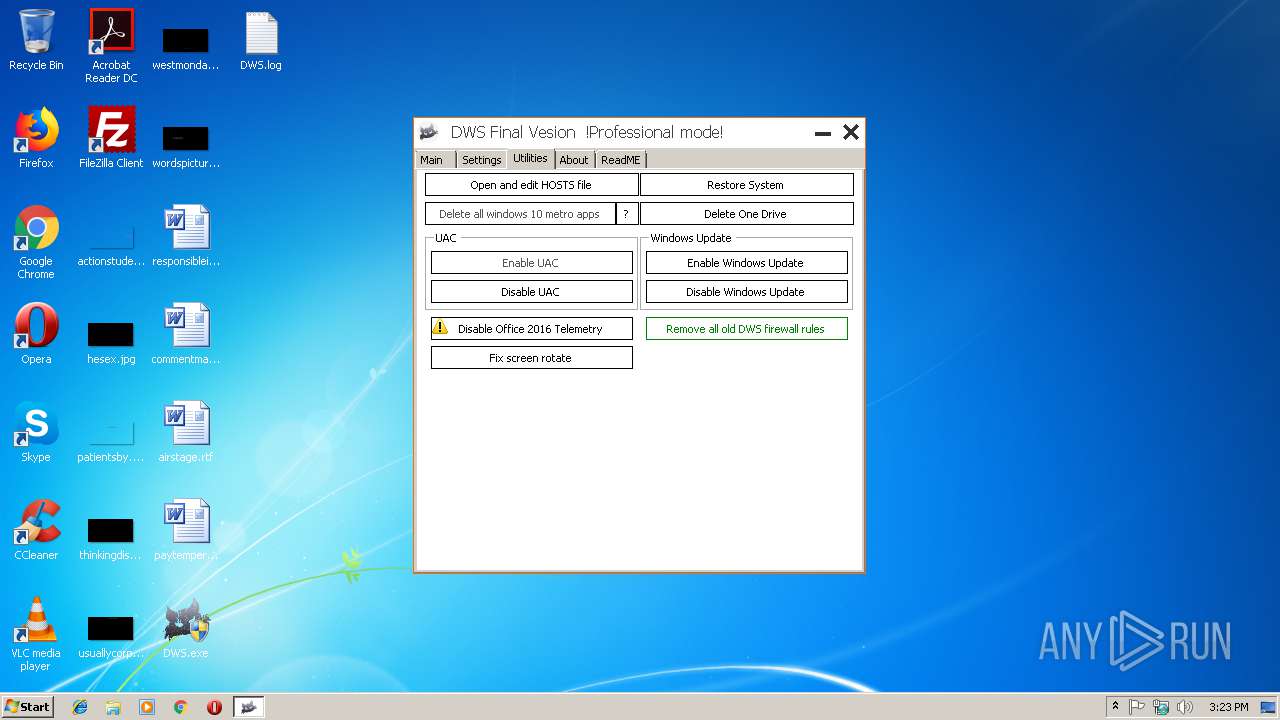
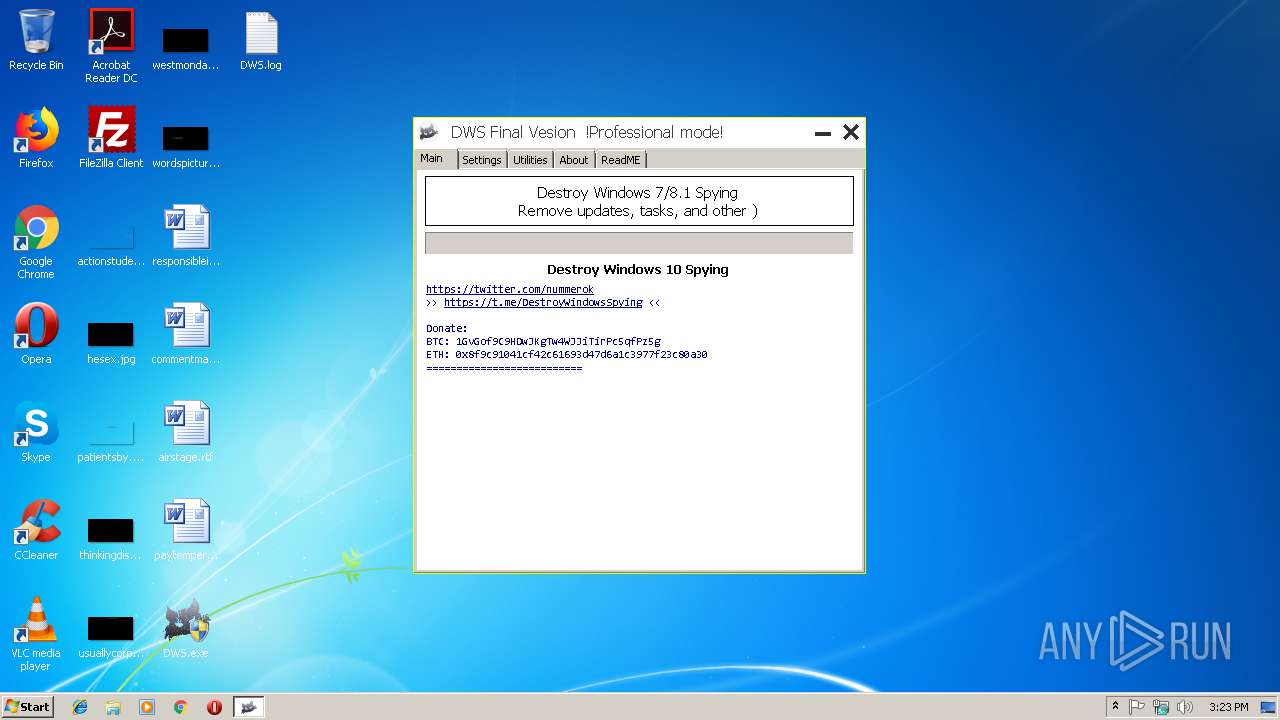
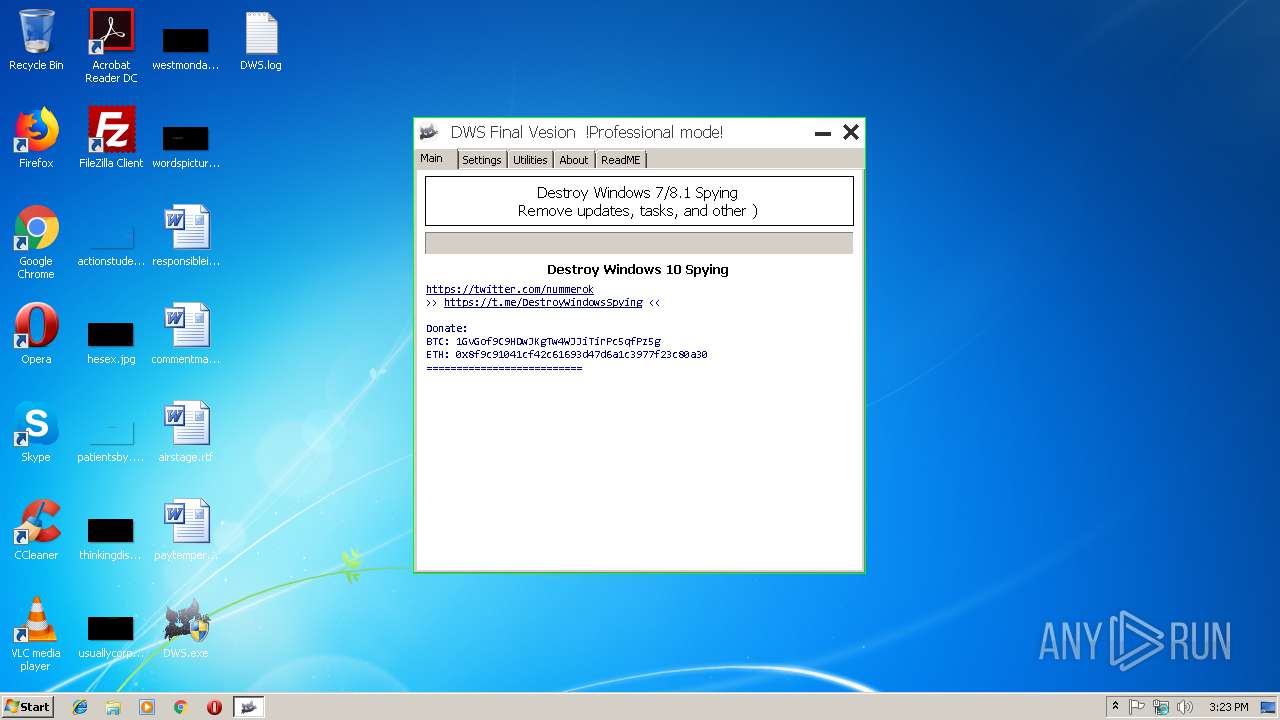
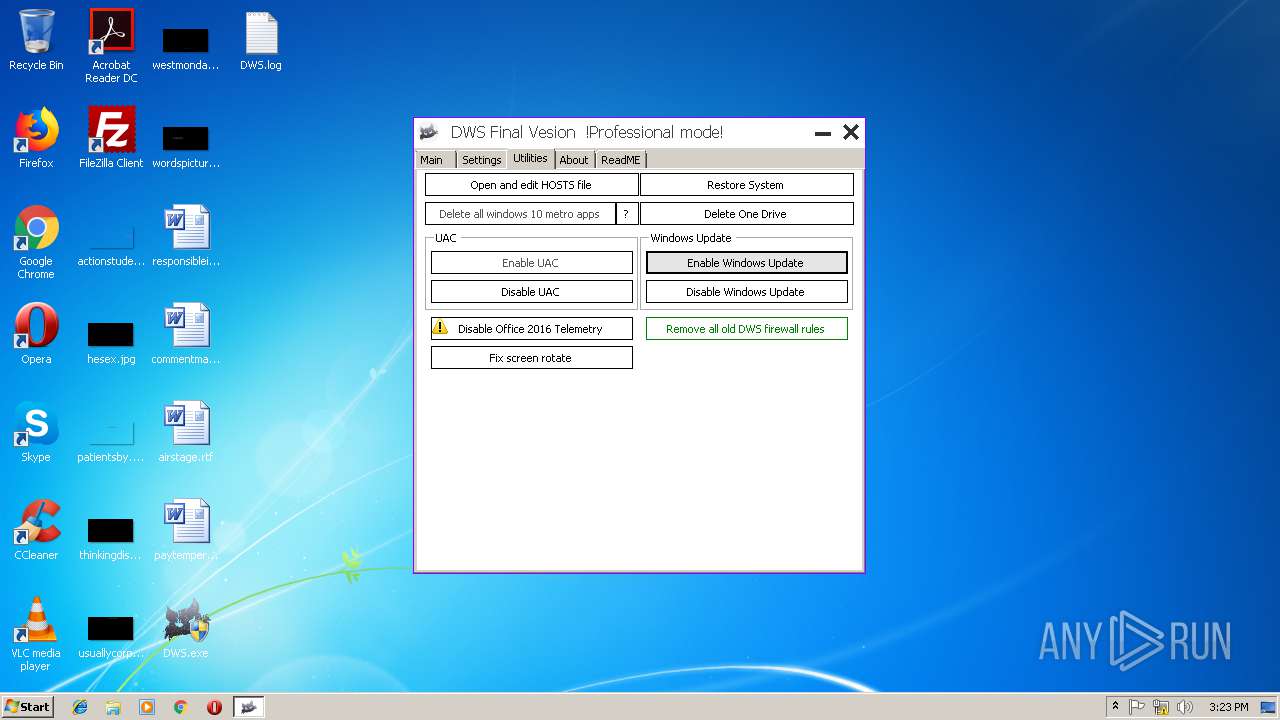
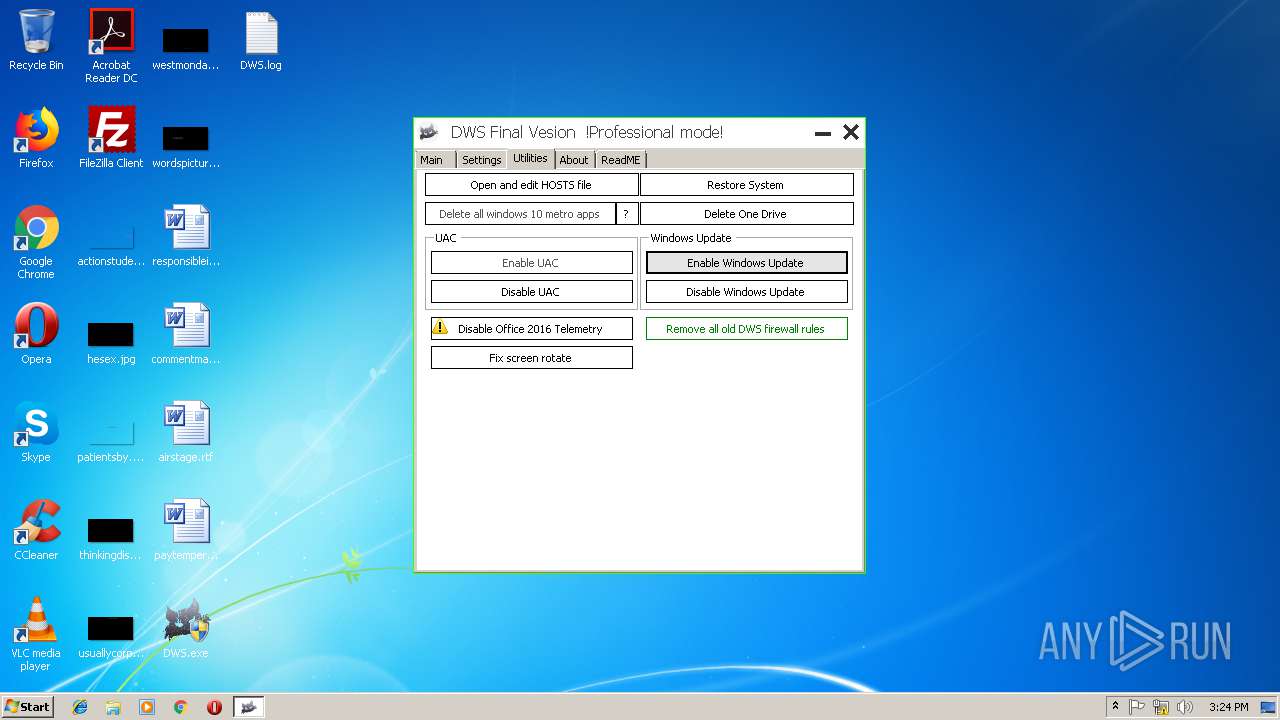
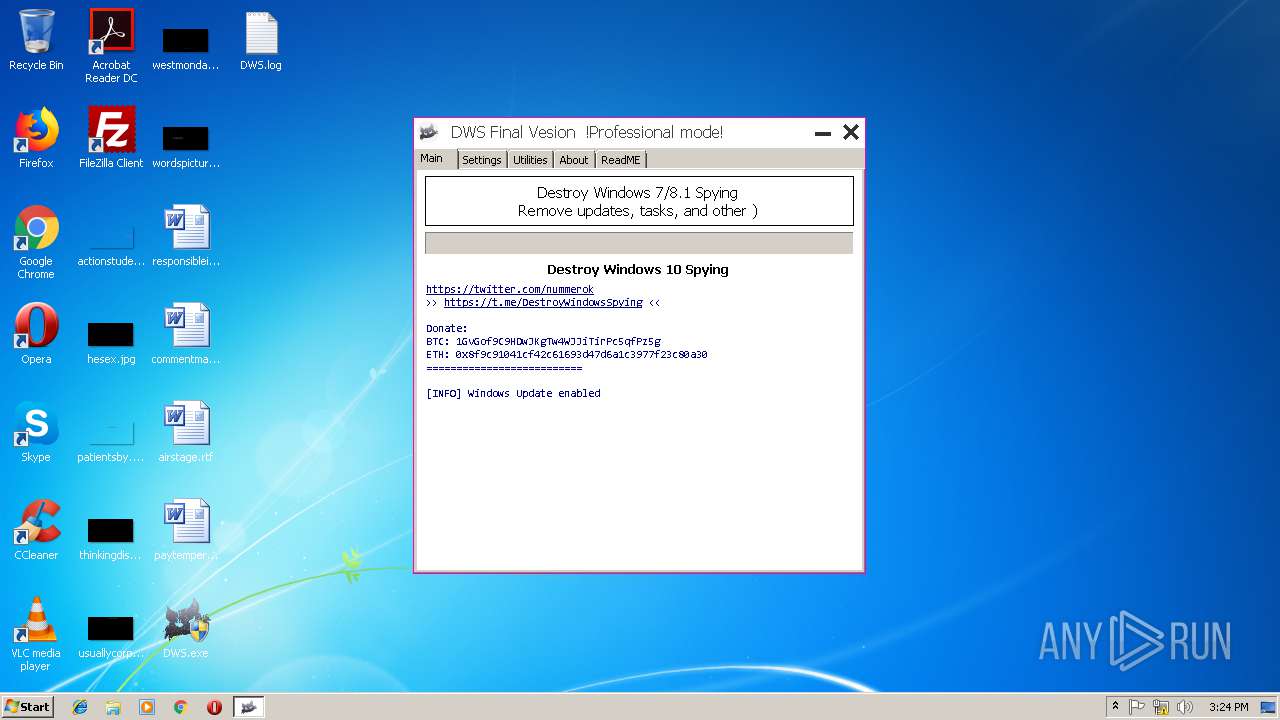
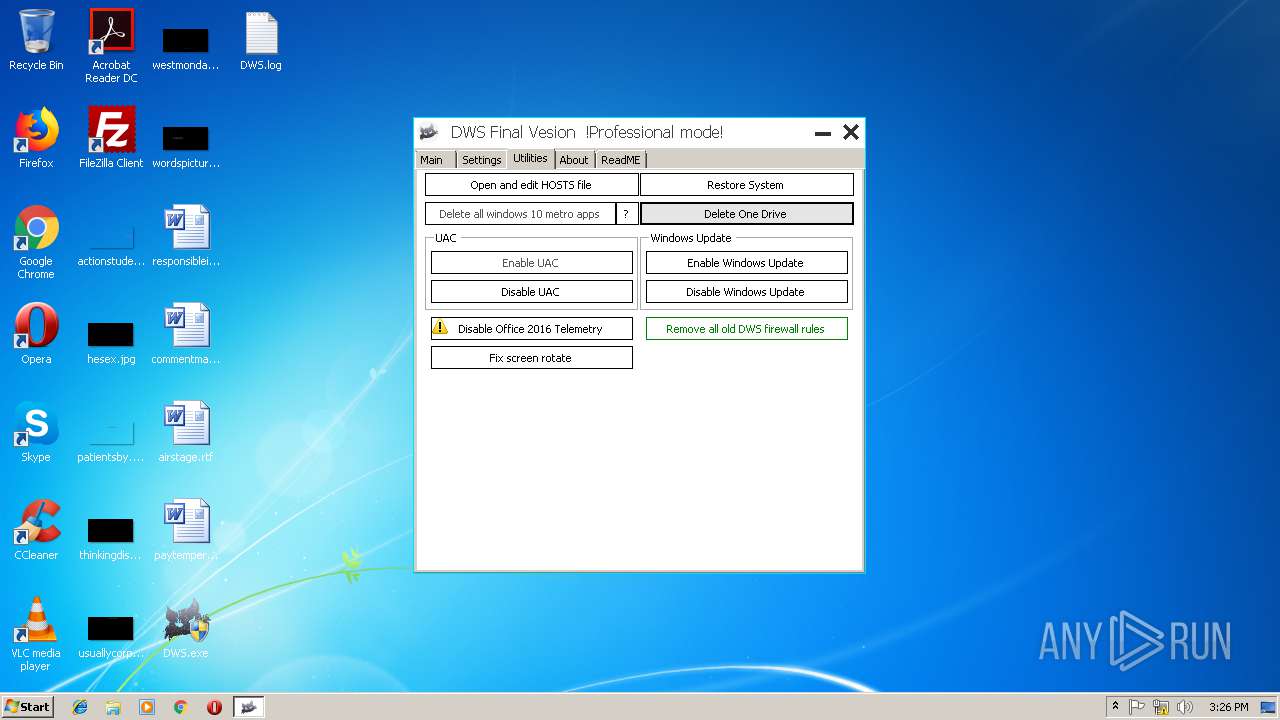
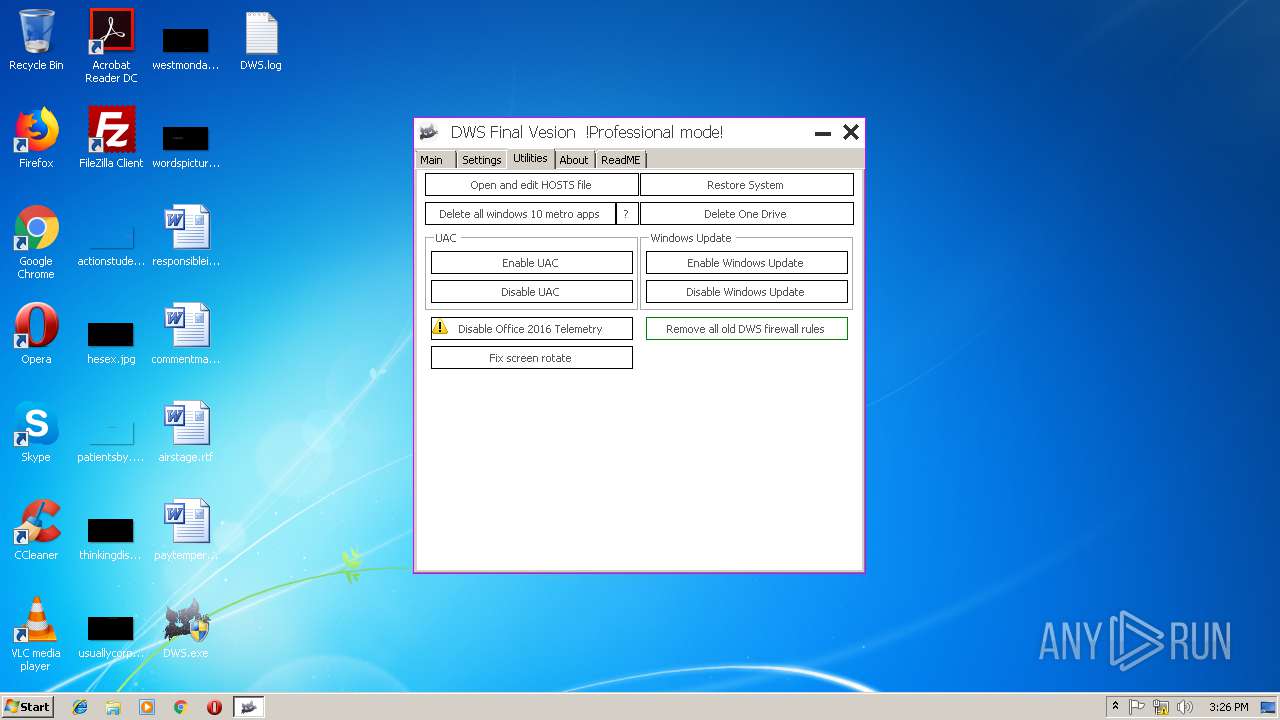
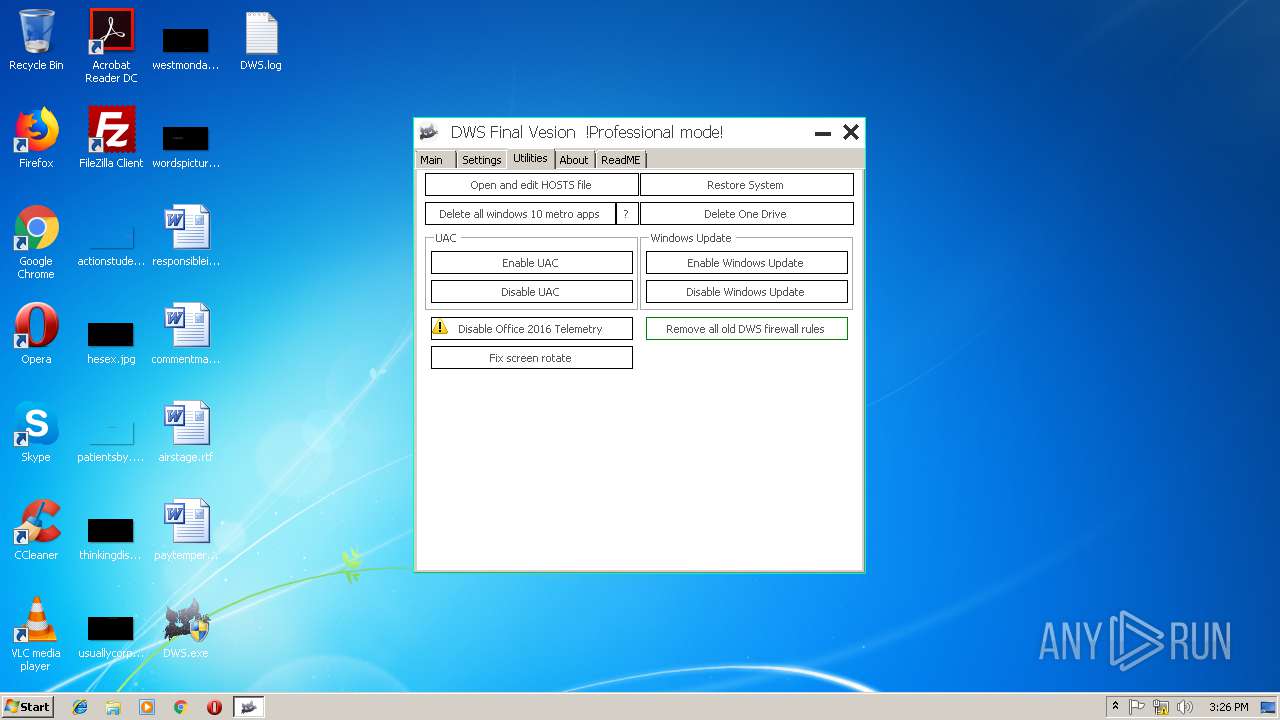
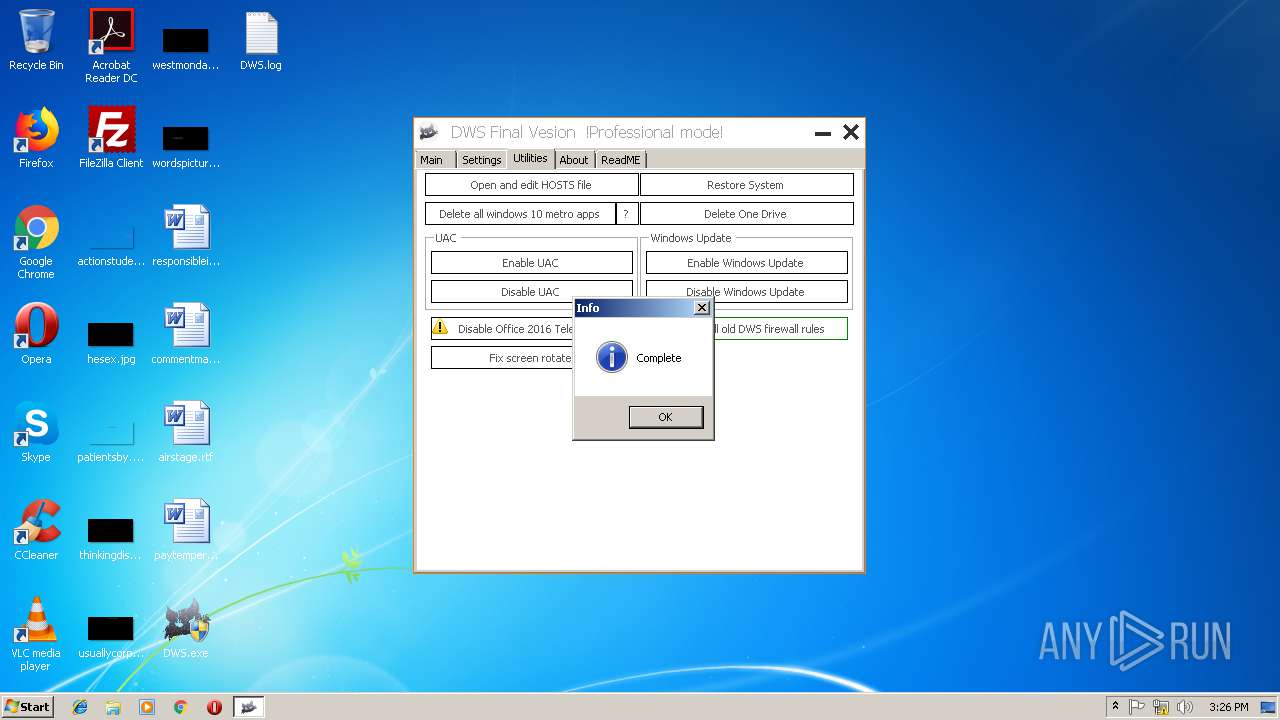
| FileDescription: | Destroy Windows 10 Spying |
| FileVersion: | 2.2.2.2 |
| InternalName: | DWS.exe |
| LegalCopyright: | Copyright © 2018 |
| LegalTrademarks: | - |
| OriginalFileName: | DWS.exe |
| ProductName: | Destroy Windows 10 Spying |
| ProductVersion: | 2.2.2.2 |
| AssemblyVersion: | 2.2.2.2 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Mar-2018 17:52:25 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | WZT |
| FileDescription: | Destroy Windows 10 Spying |
| FileVersion: | 2.2.2.2 |
| InternalName: | DWS.exe |
| LegalCopyright: | Copyright © 2018 |
| LegalTrademarks: | - |
| OriginalFilename: | DWS.exe |
| ProductName: | Destroy Windows 10 Spying |
| ProductVersion: | 2.2.2.2 |
| Assembly Version: | 2.2.2.2 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 04-Mar-2018 17:52:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0003E0C4 | 0x0003E200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.66754 |
.rsrc | 0x00042000 | 0x000117E8 | 0x00011800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.28486 |
.reloc | 0x00054000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.04075 | 2861 | UNKNOWN | UNKNOWN | RT_MANIFEST |
32512 | 1.98048 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
93
Monitored processes
36
Malicious processes
1
Suspicious processes
0
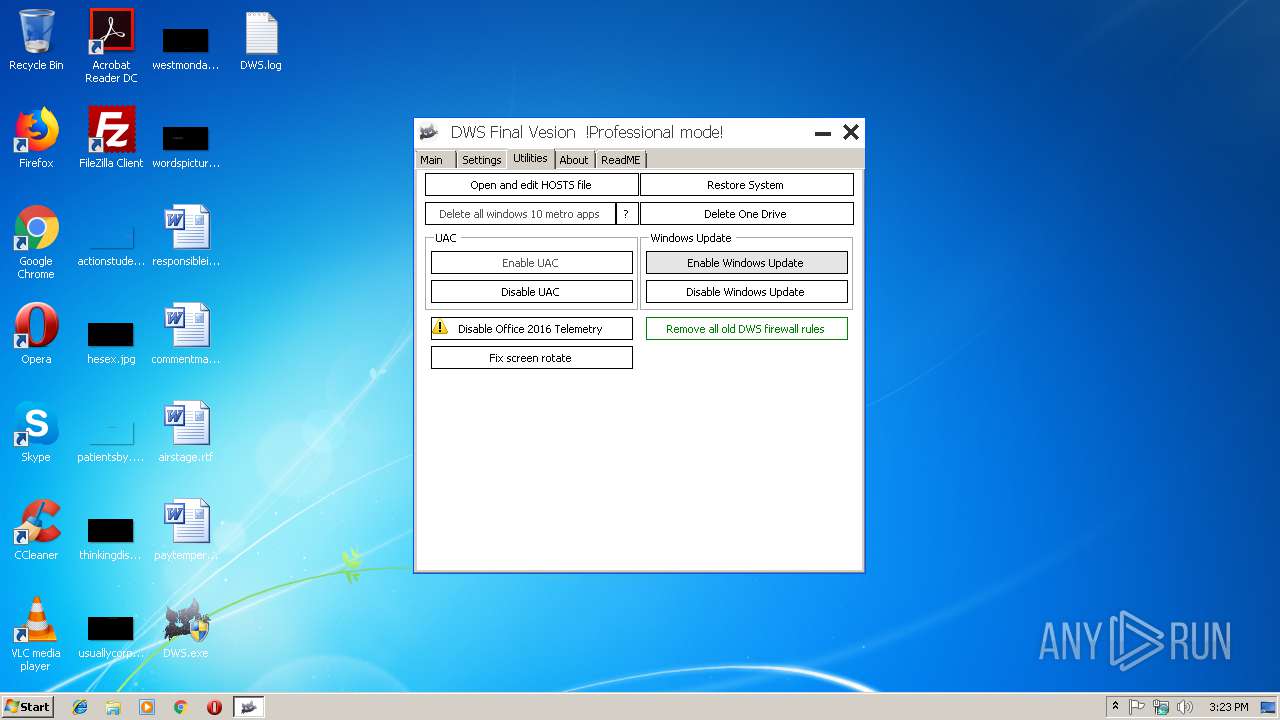
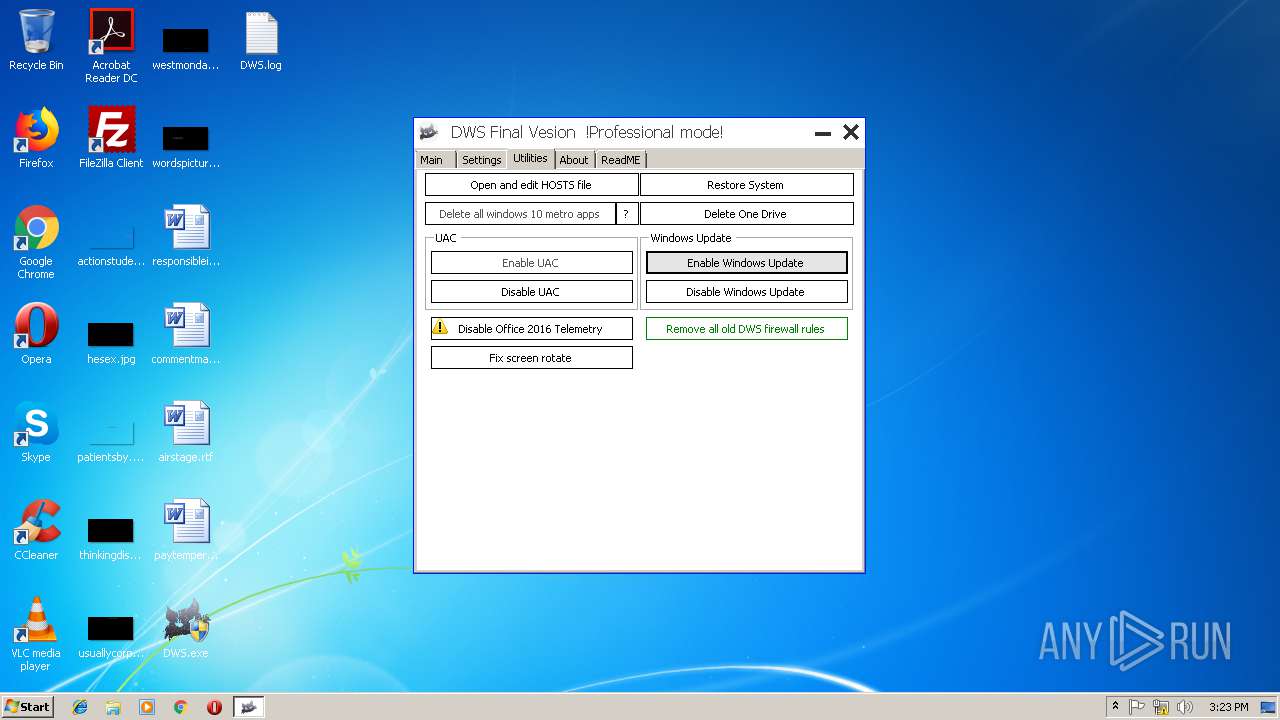
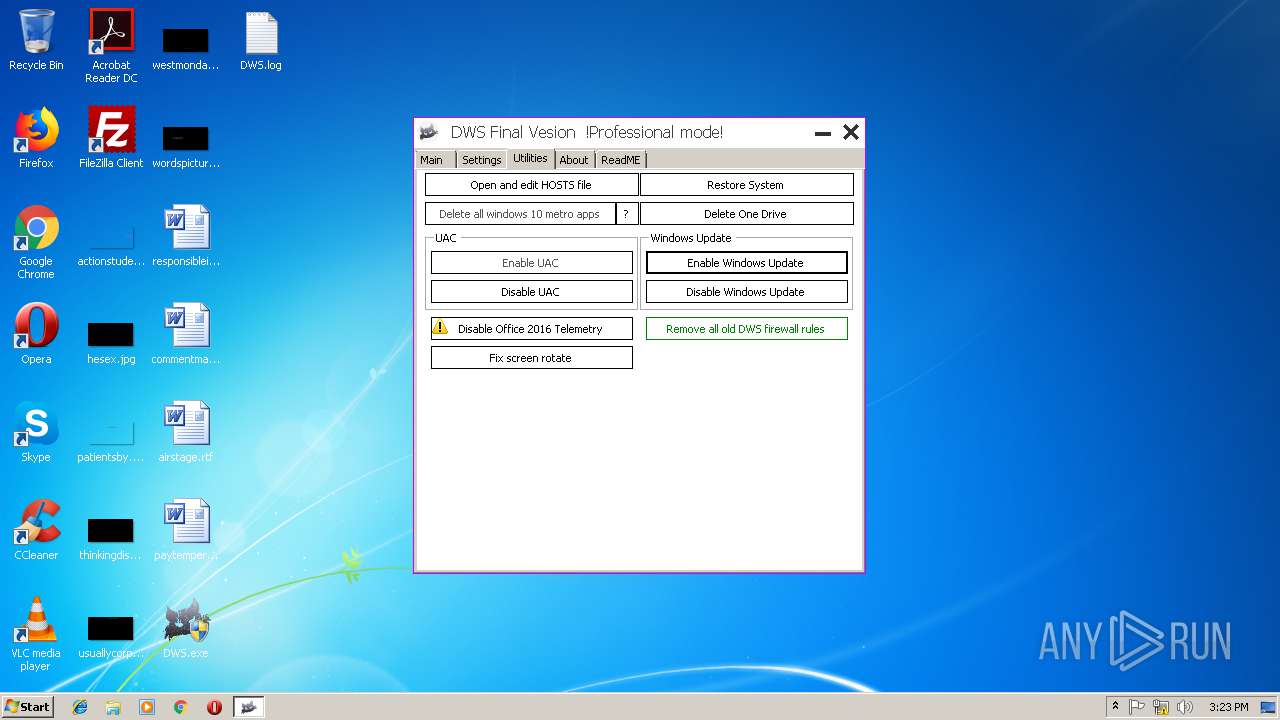
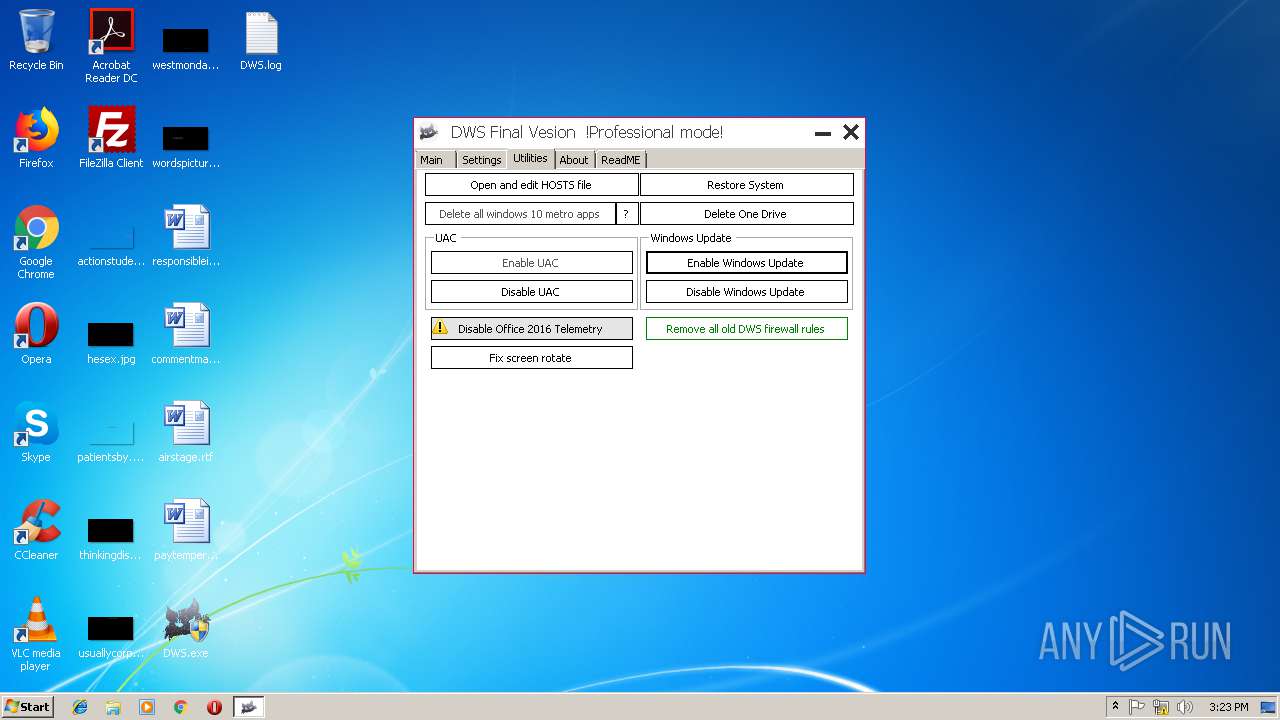
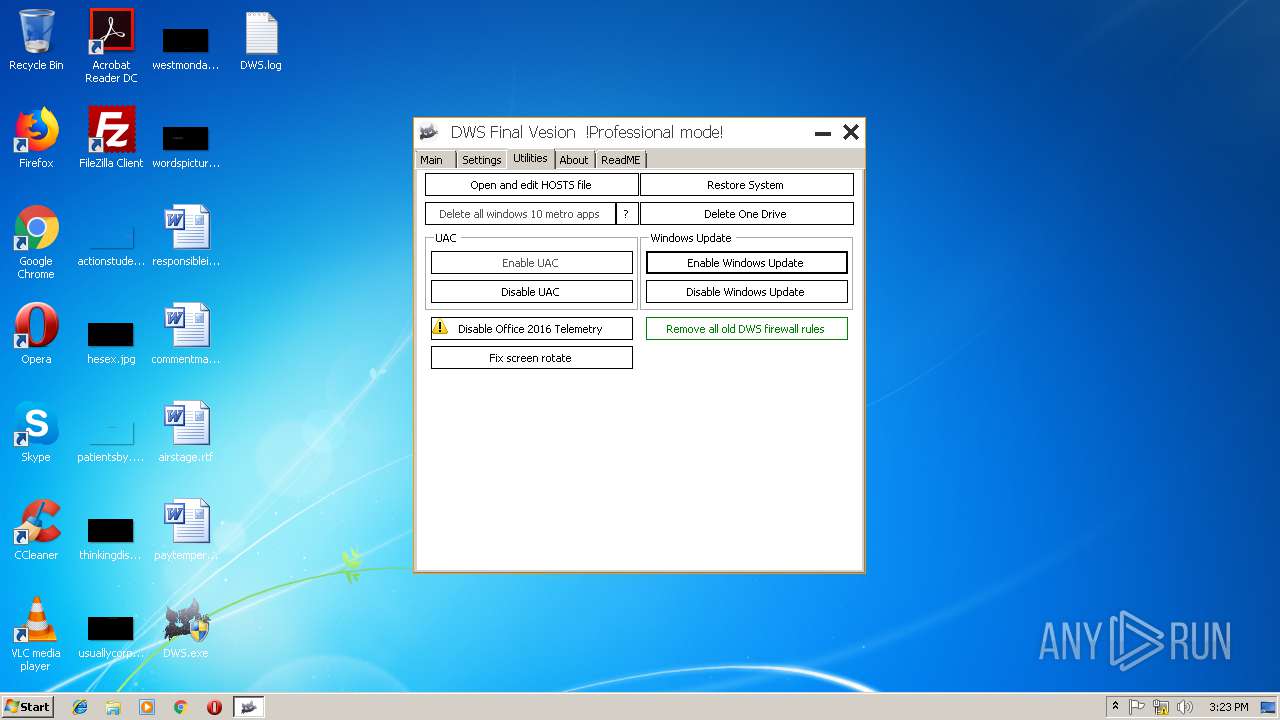
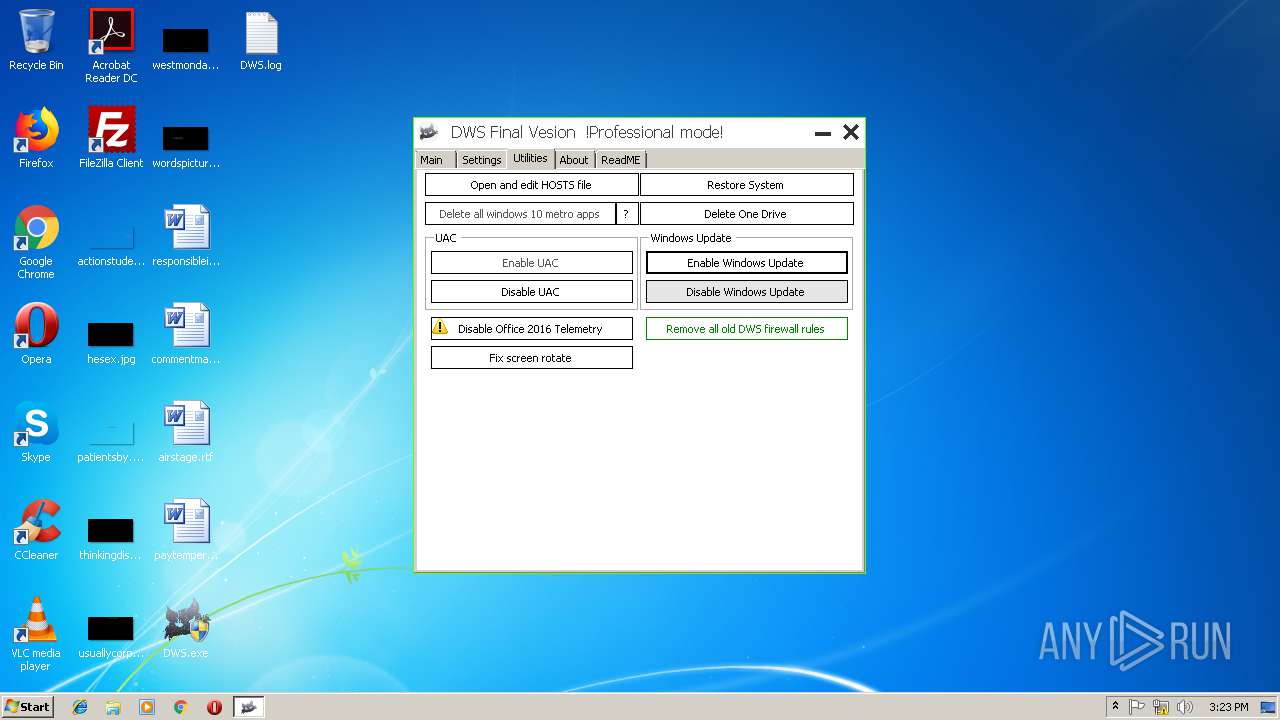
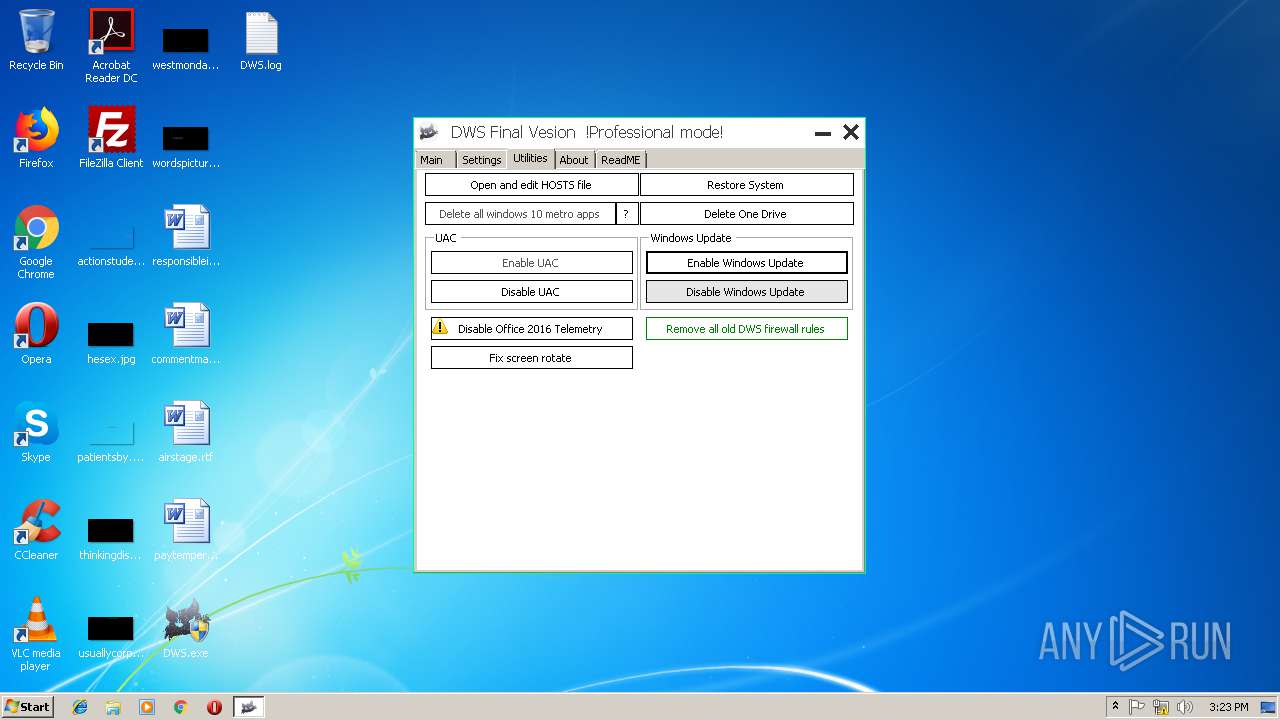
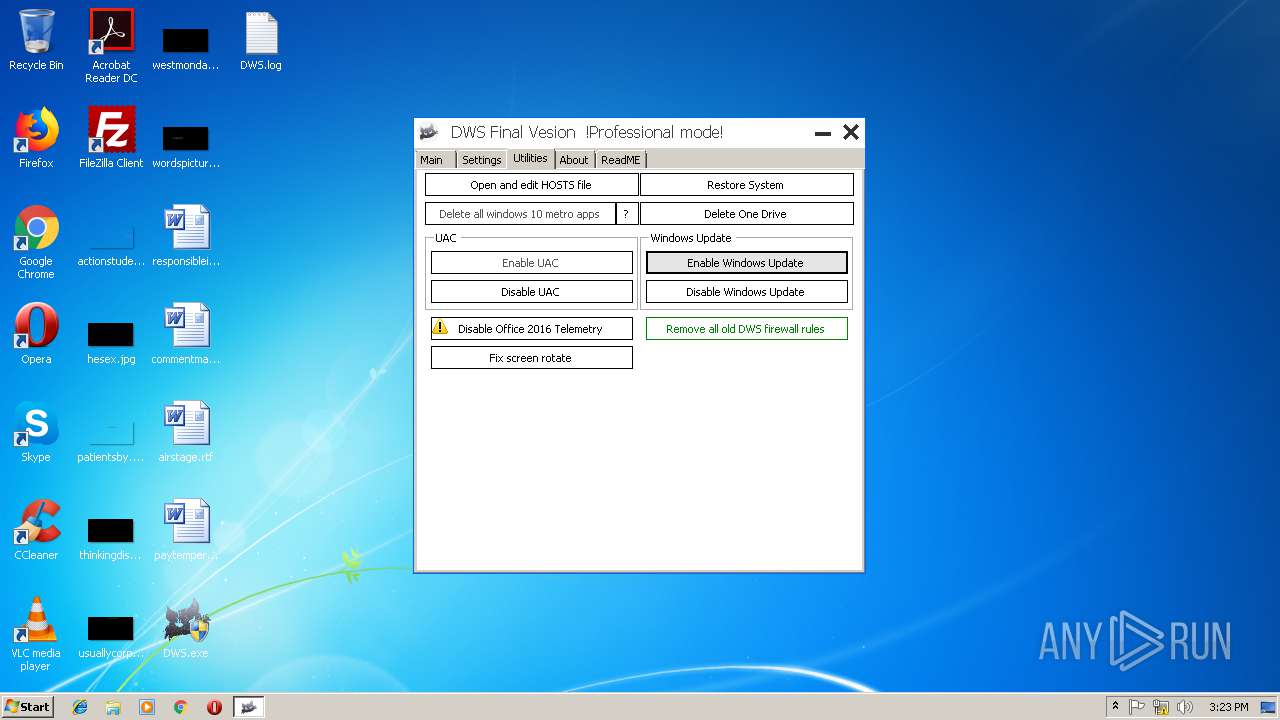
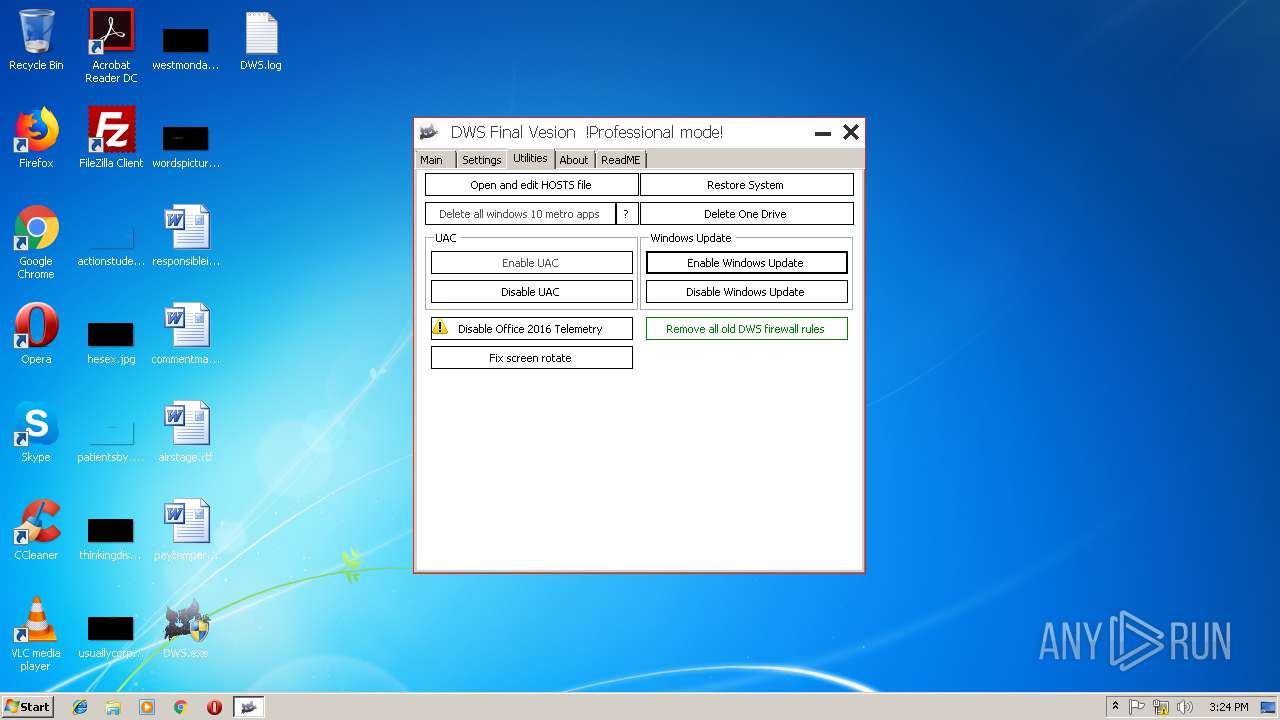
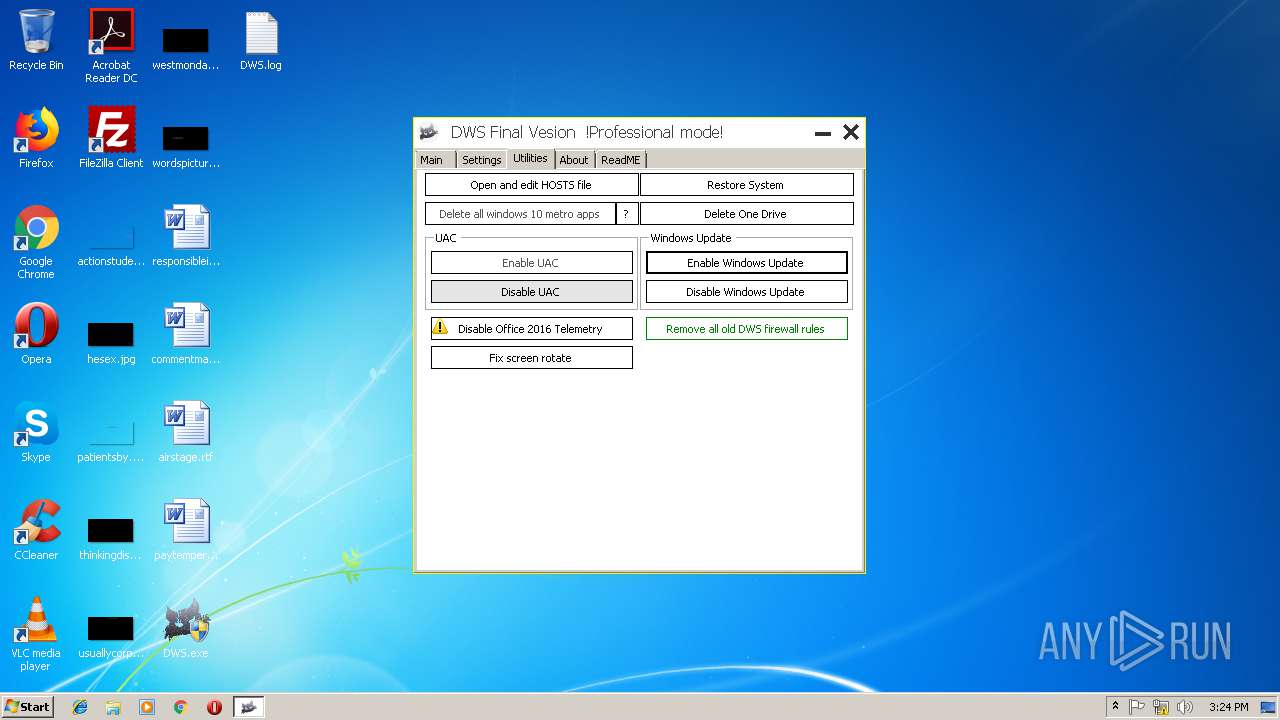
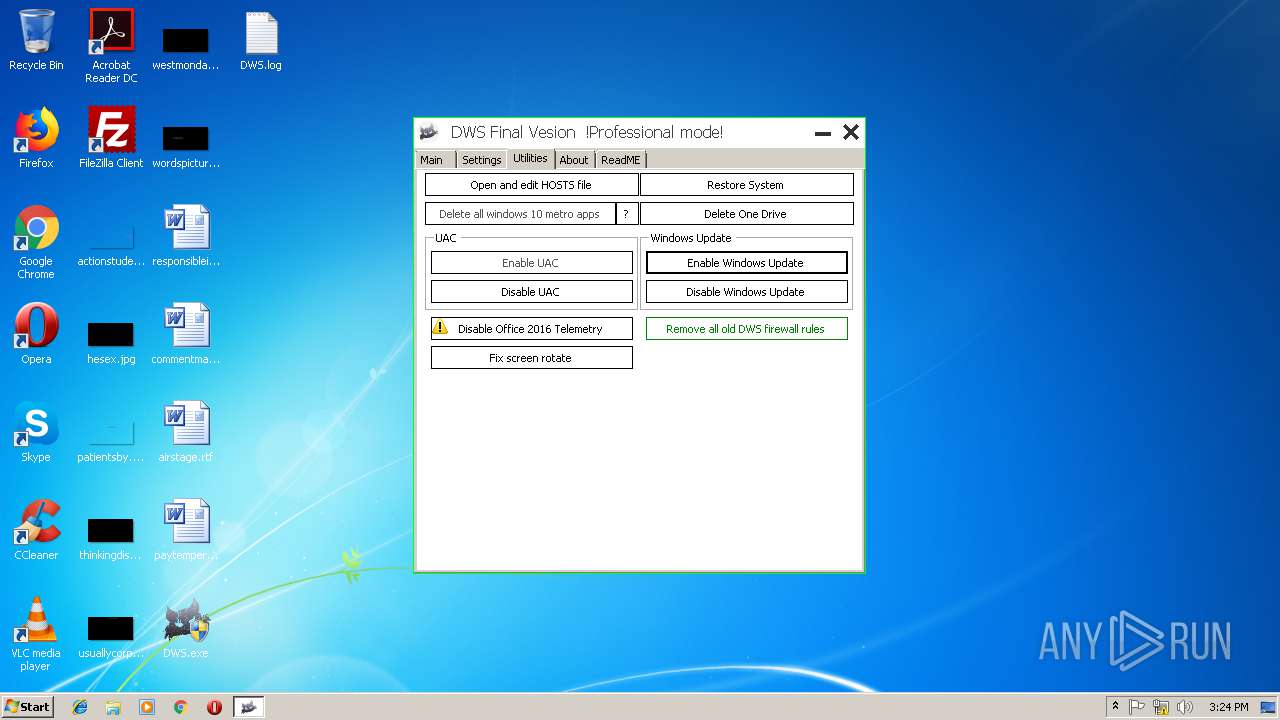
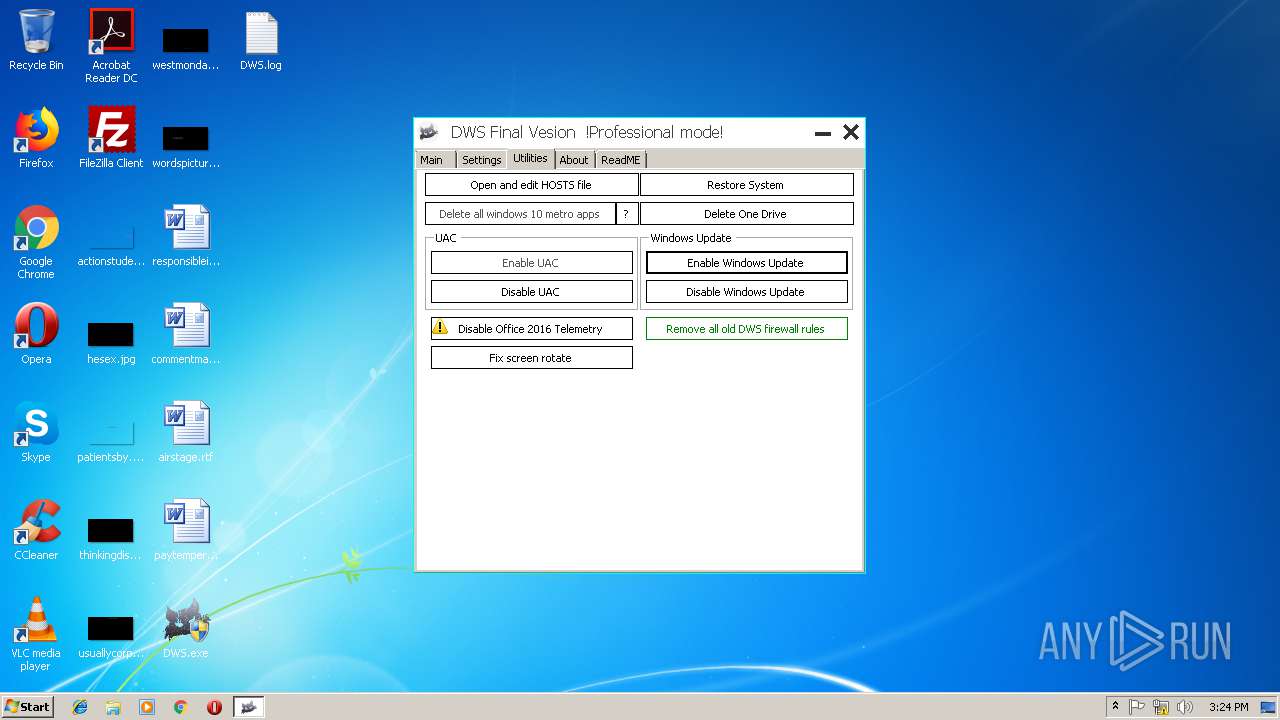
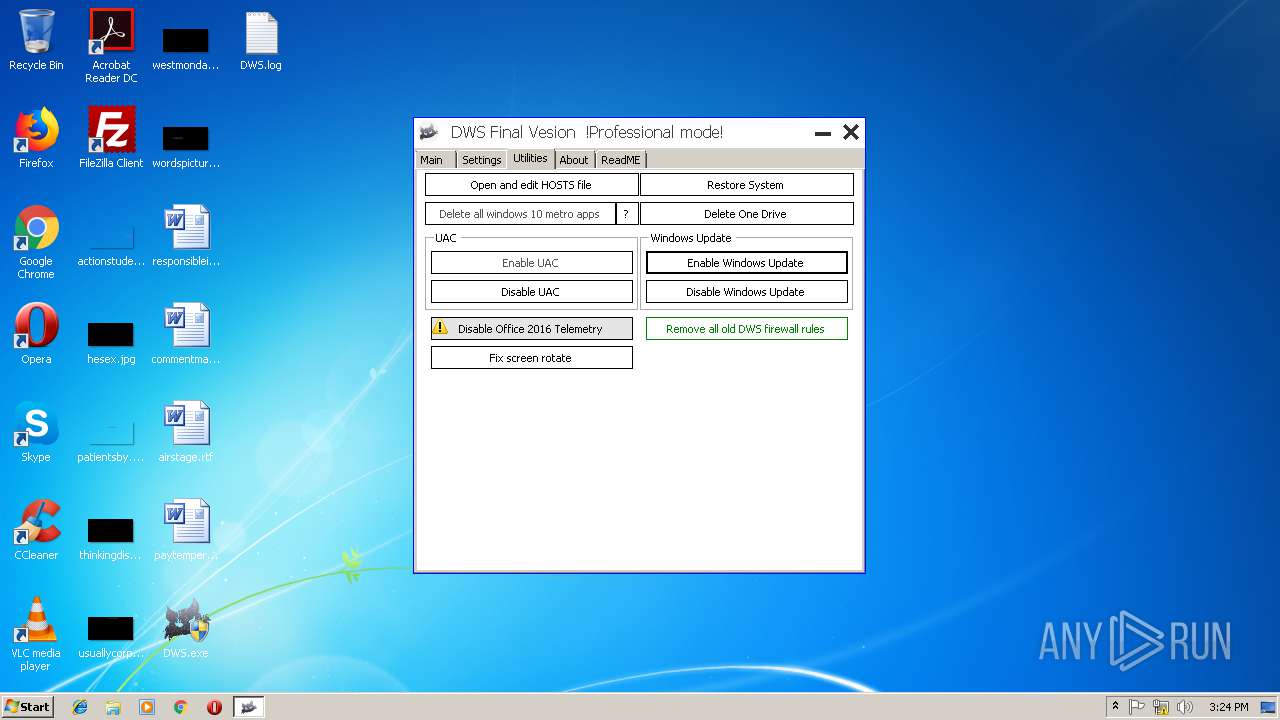
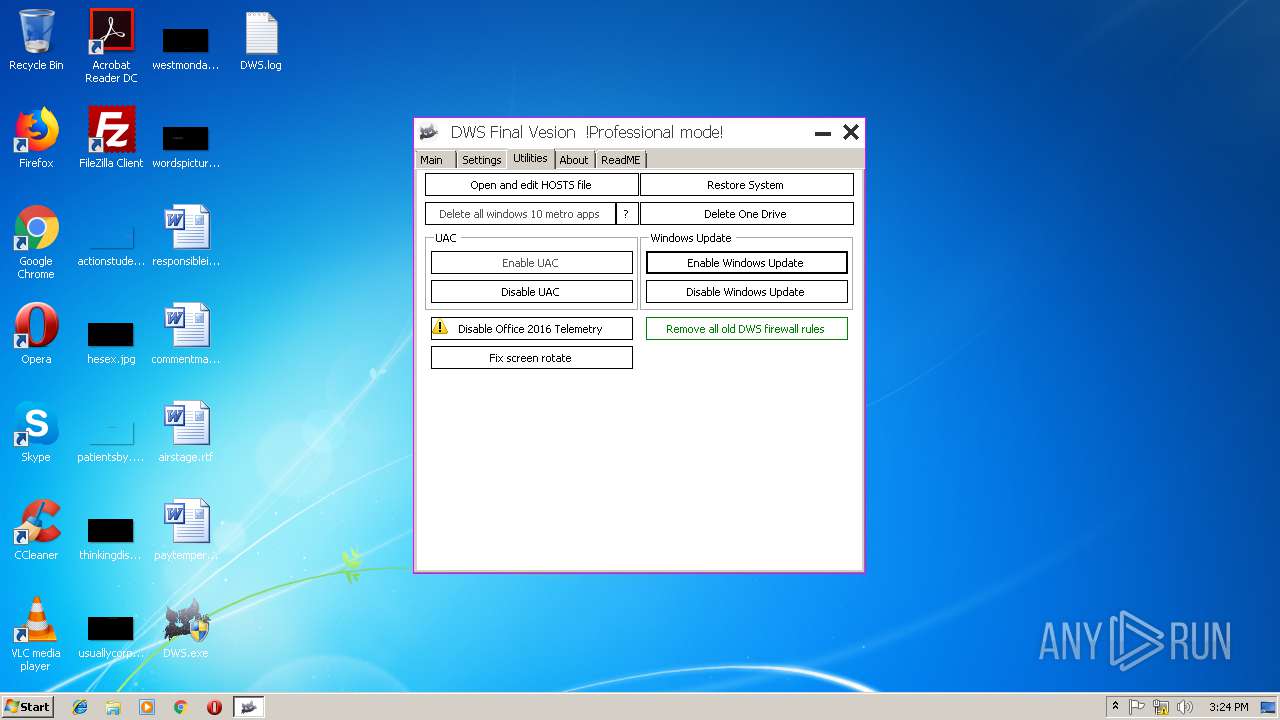
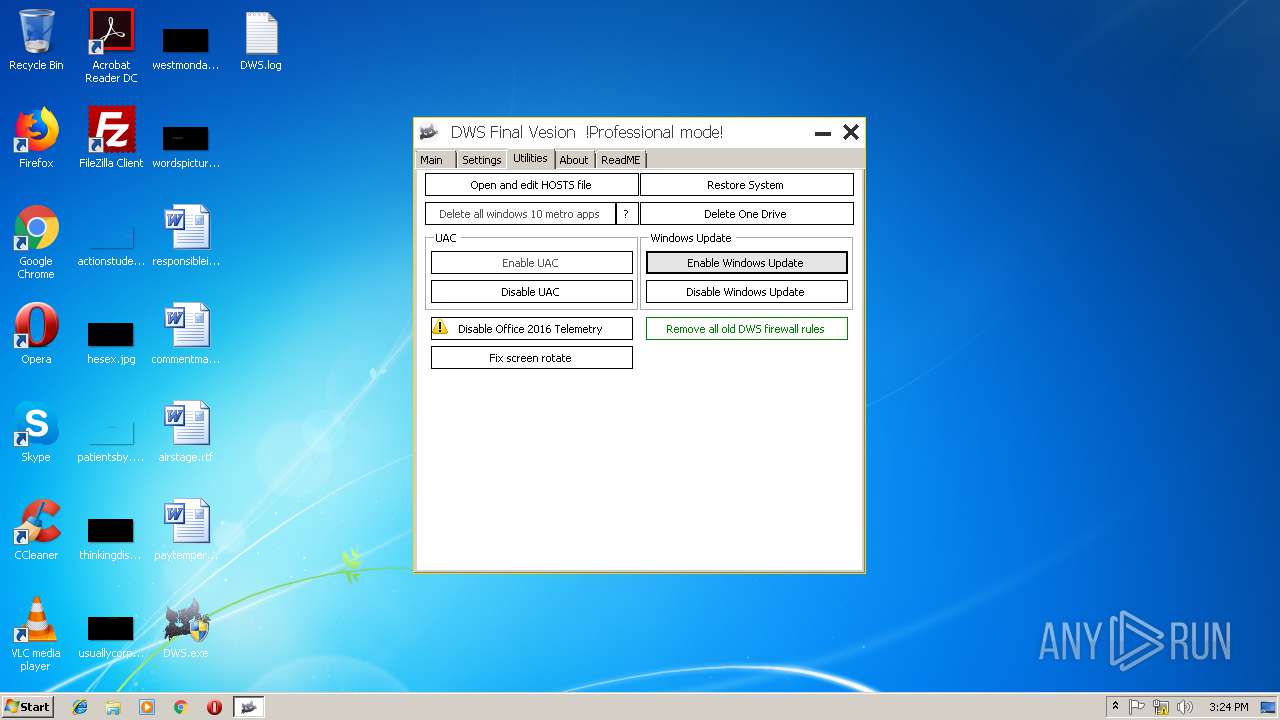
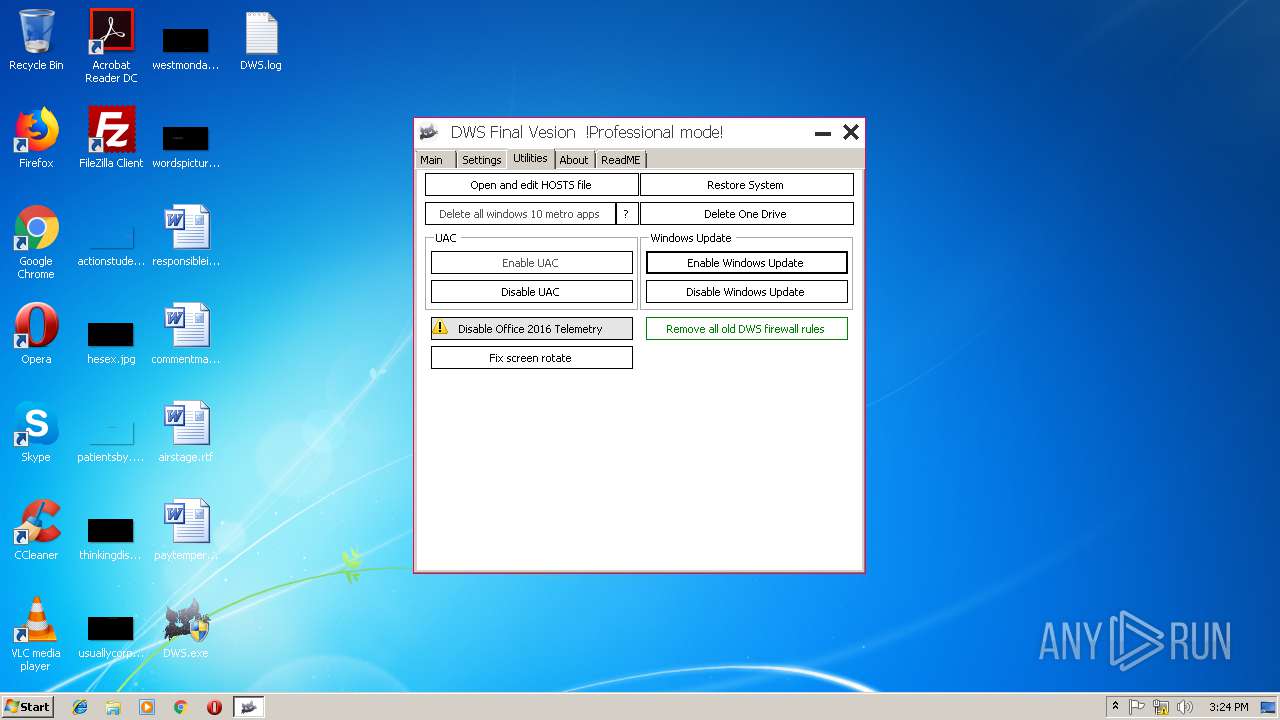
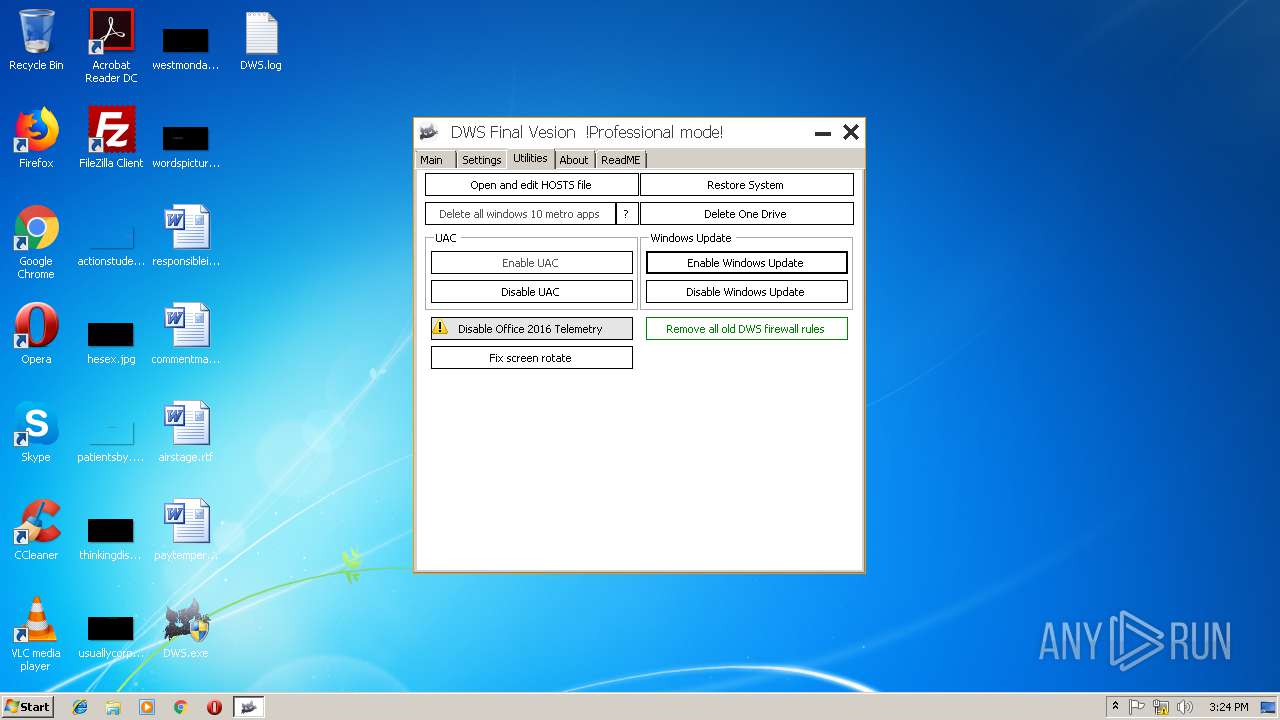
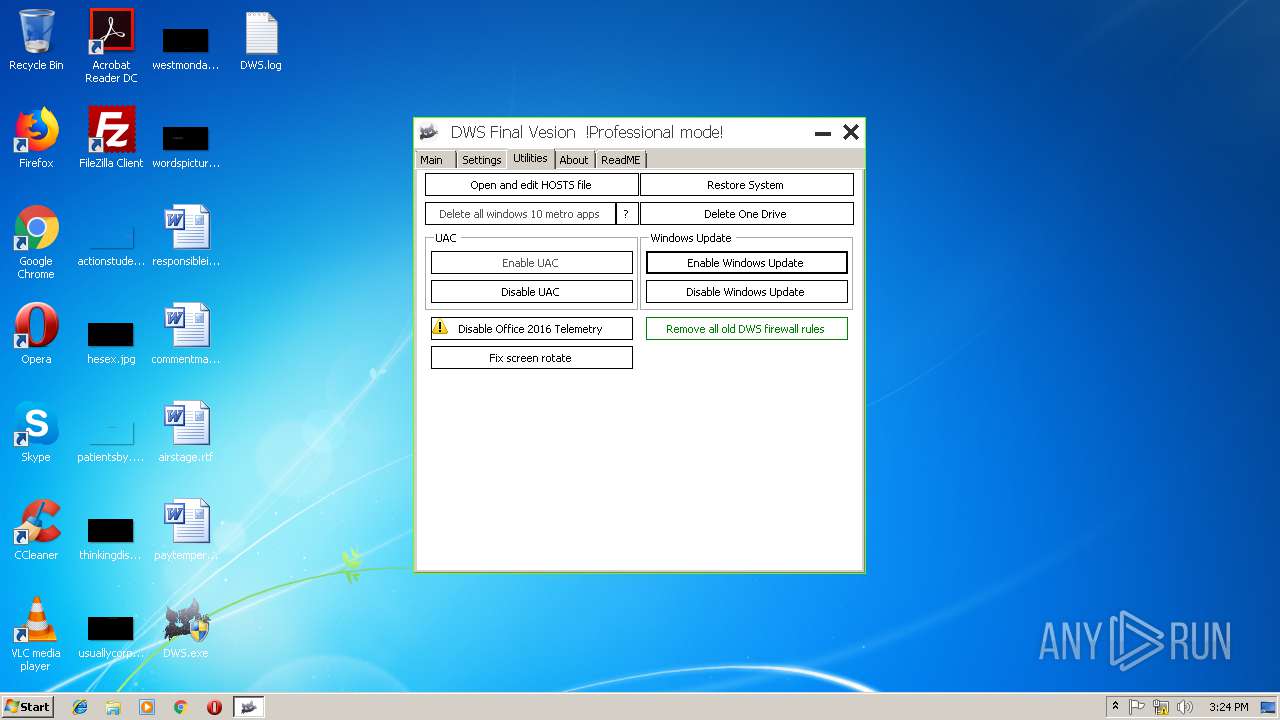
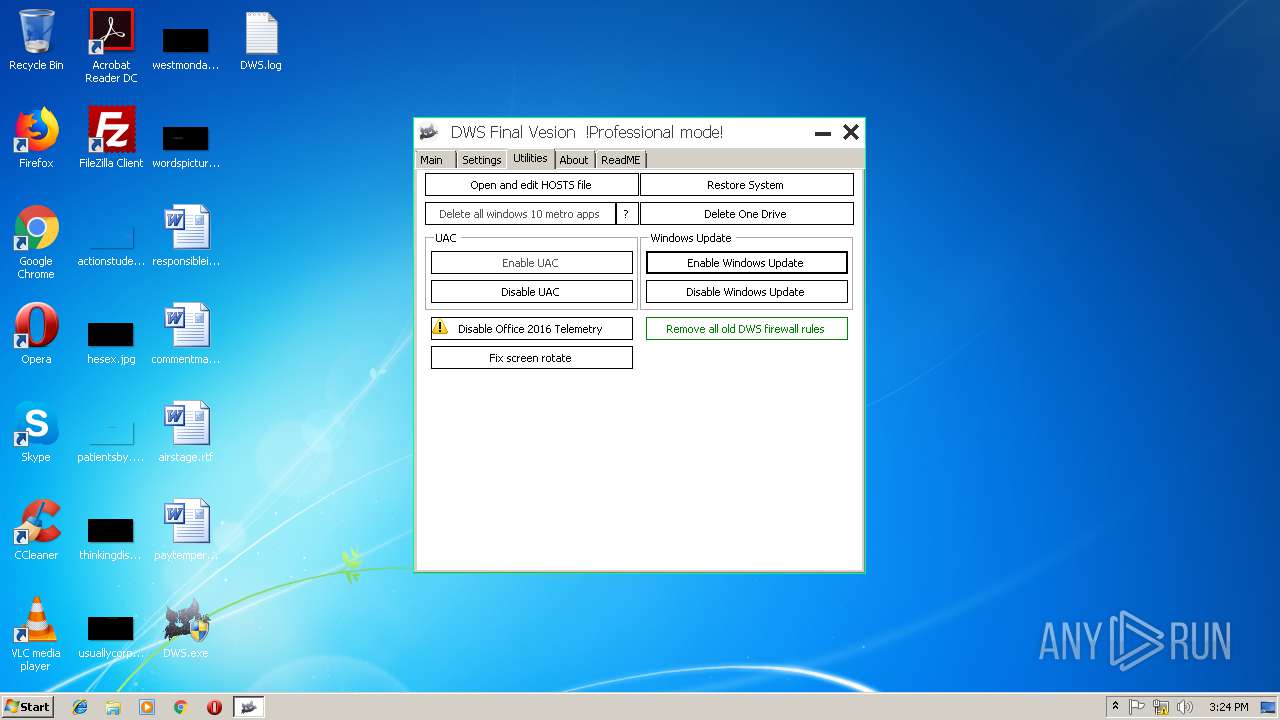
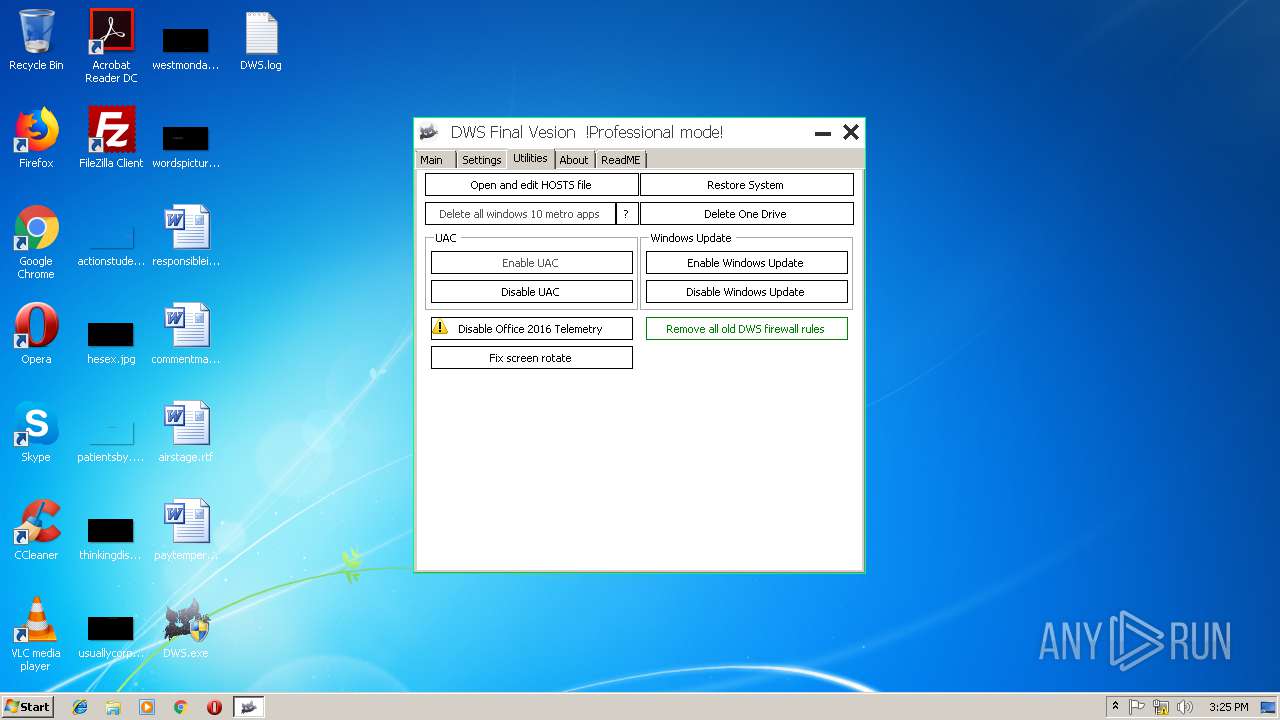
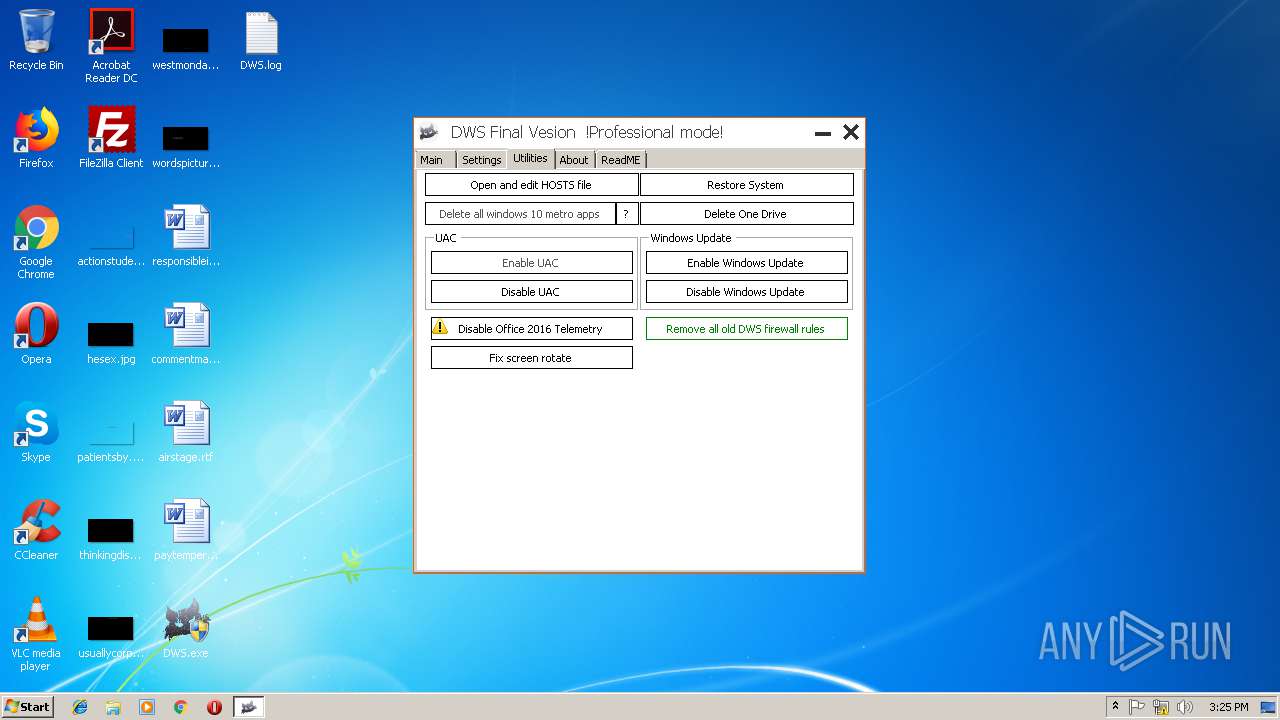
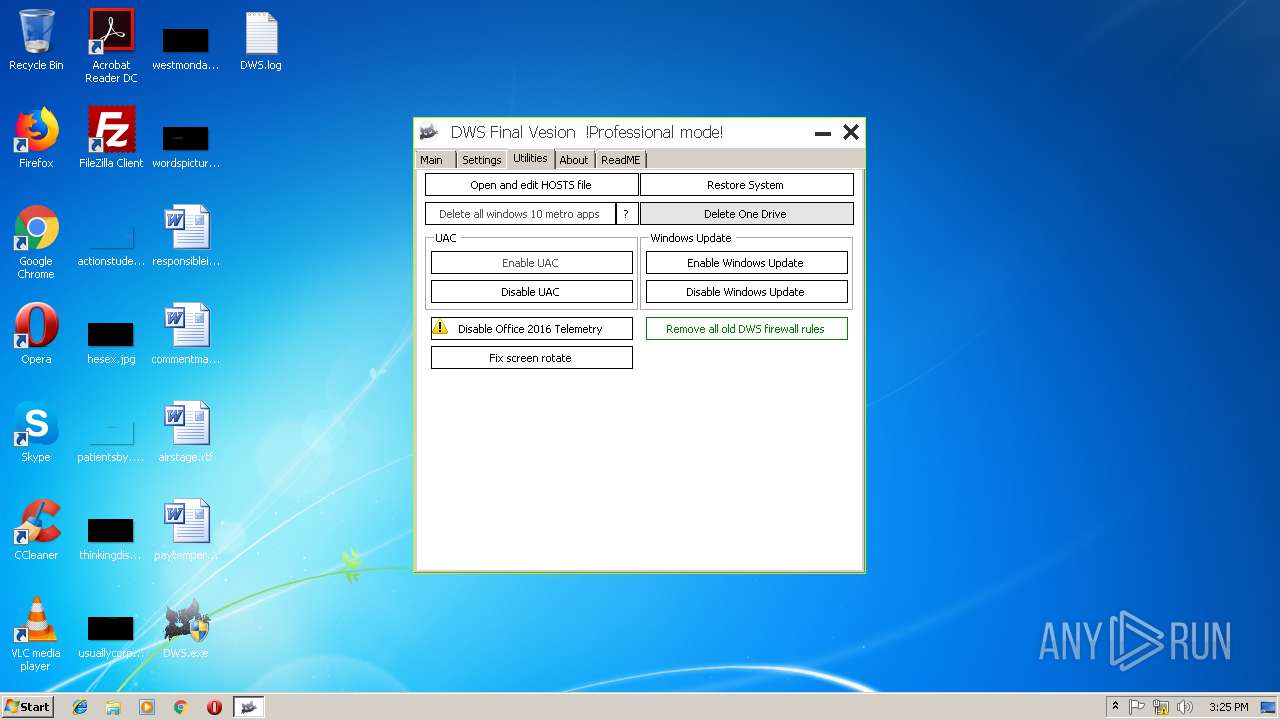
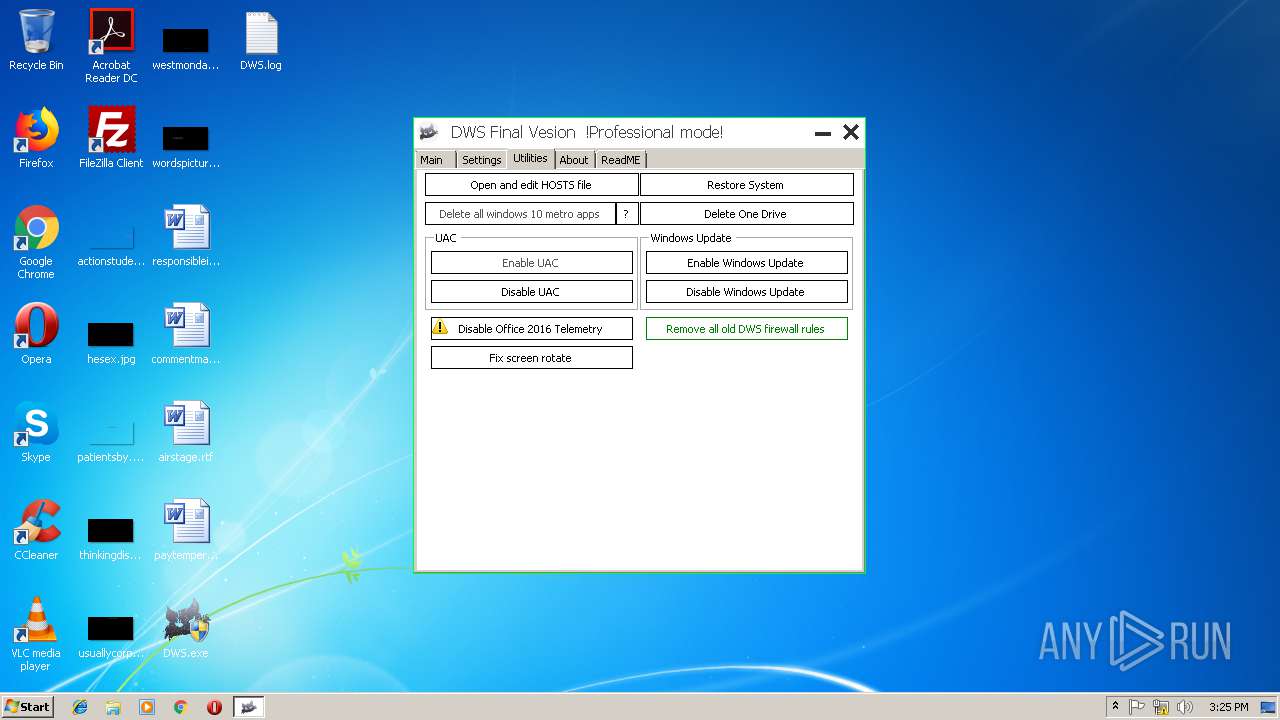
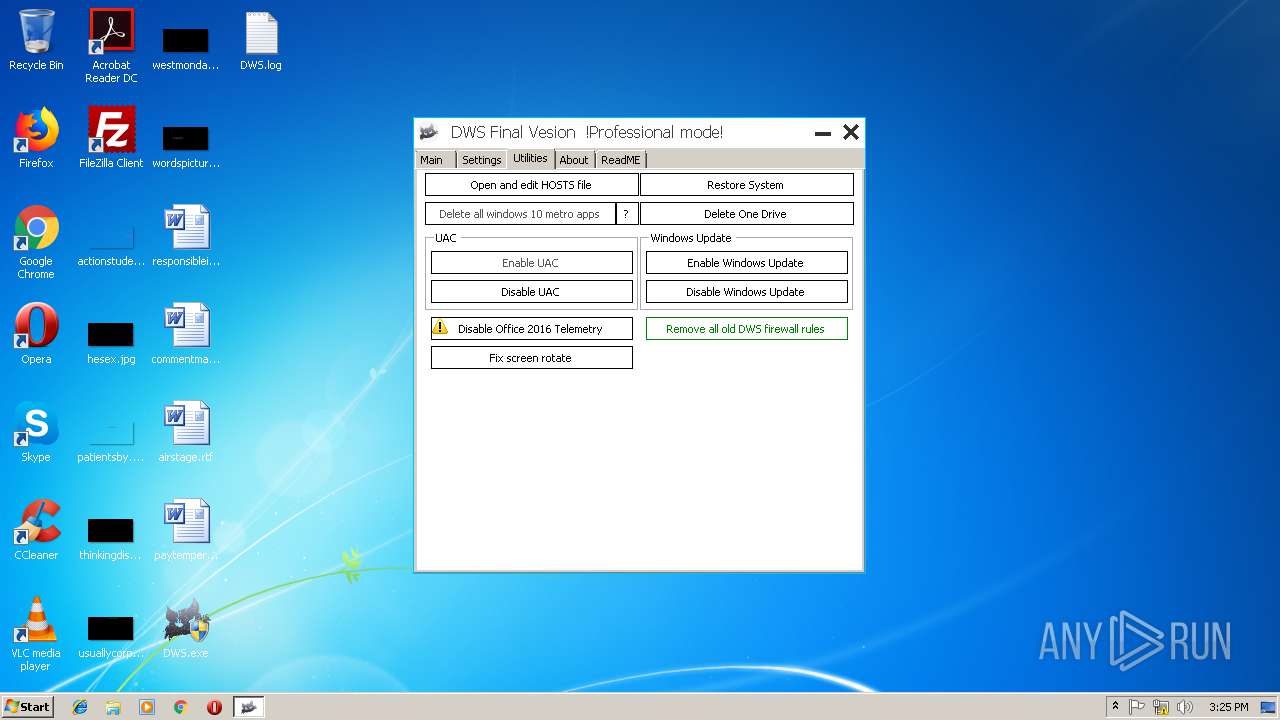
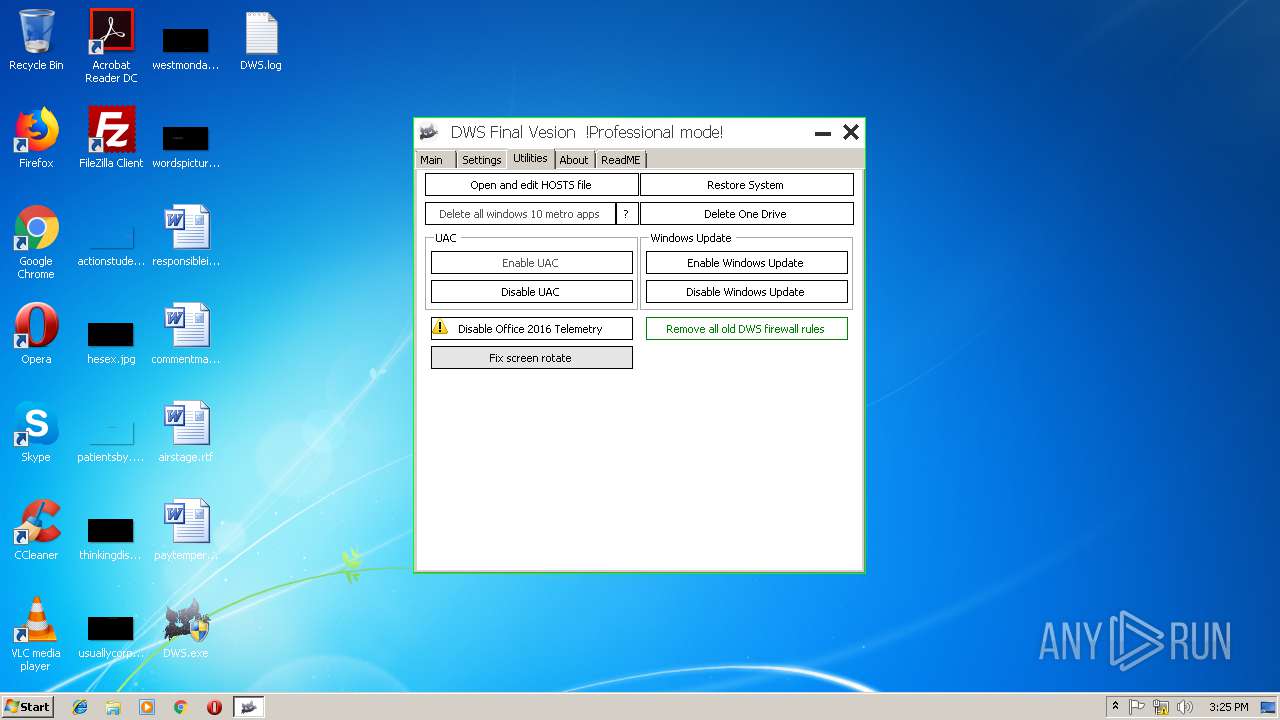
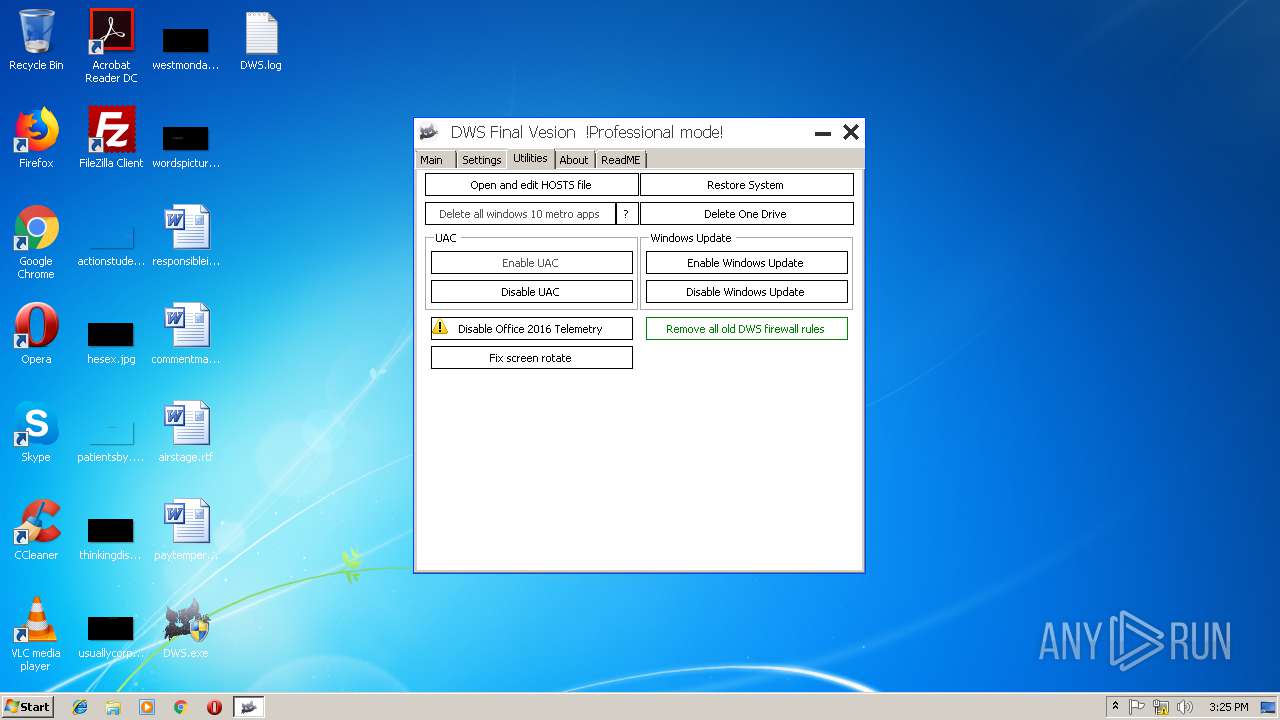
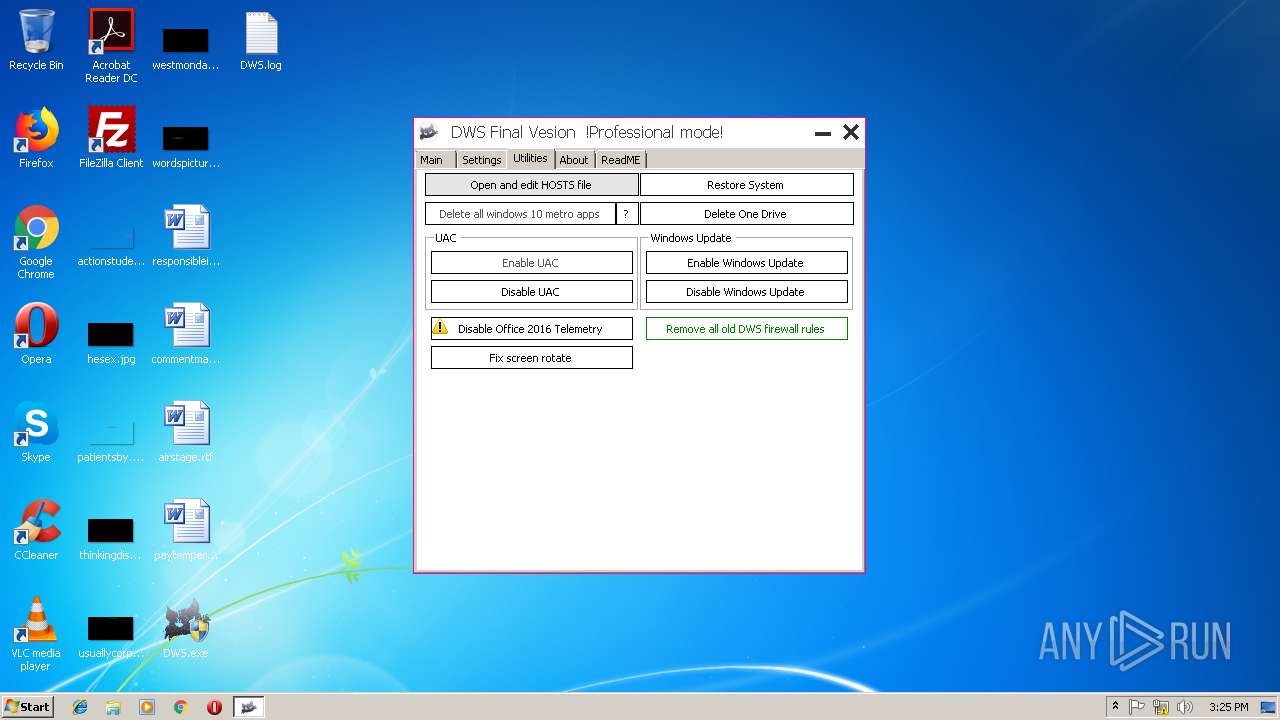
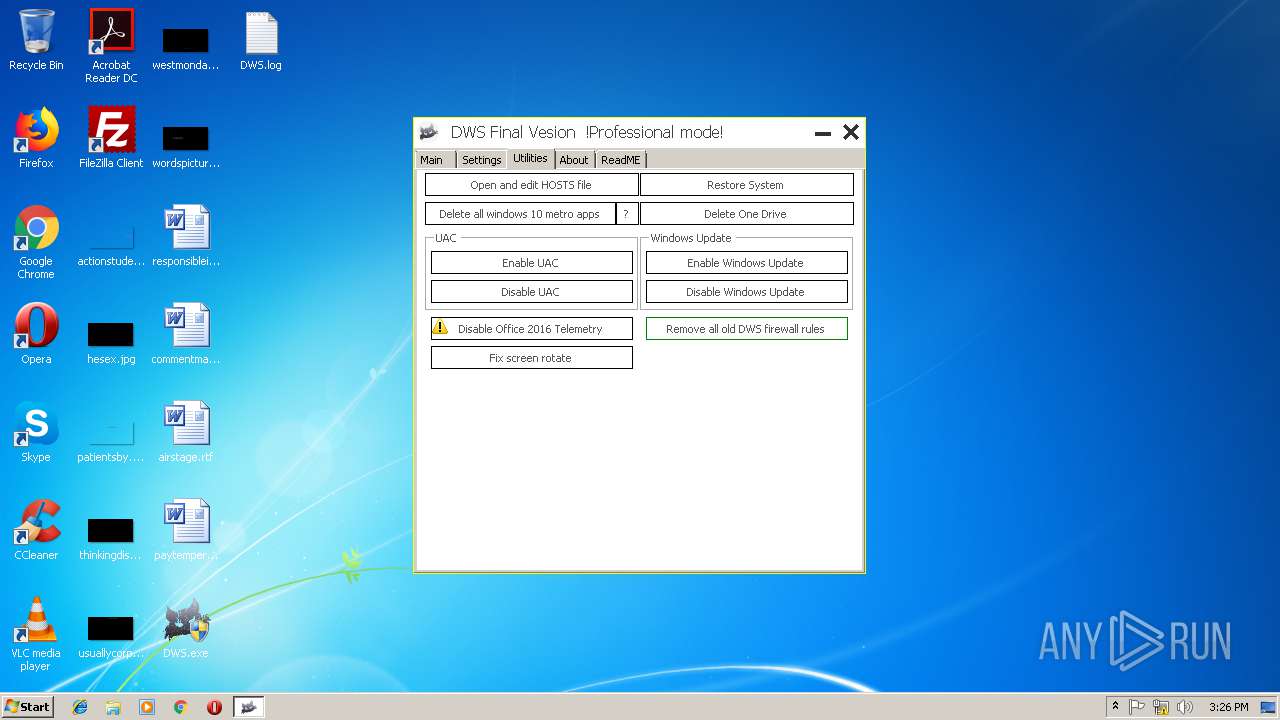
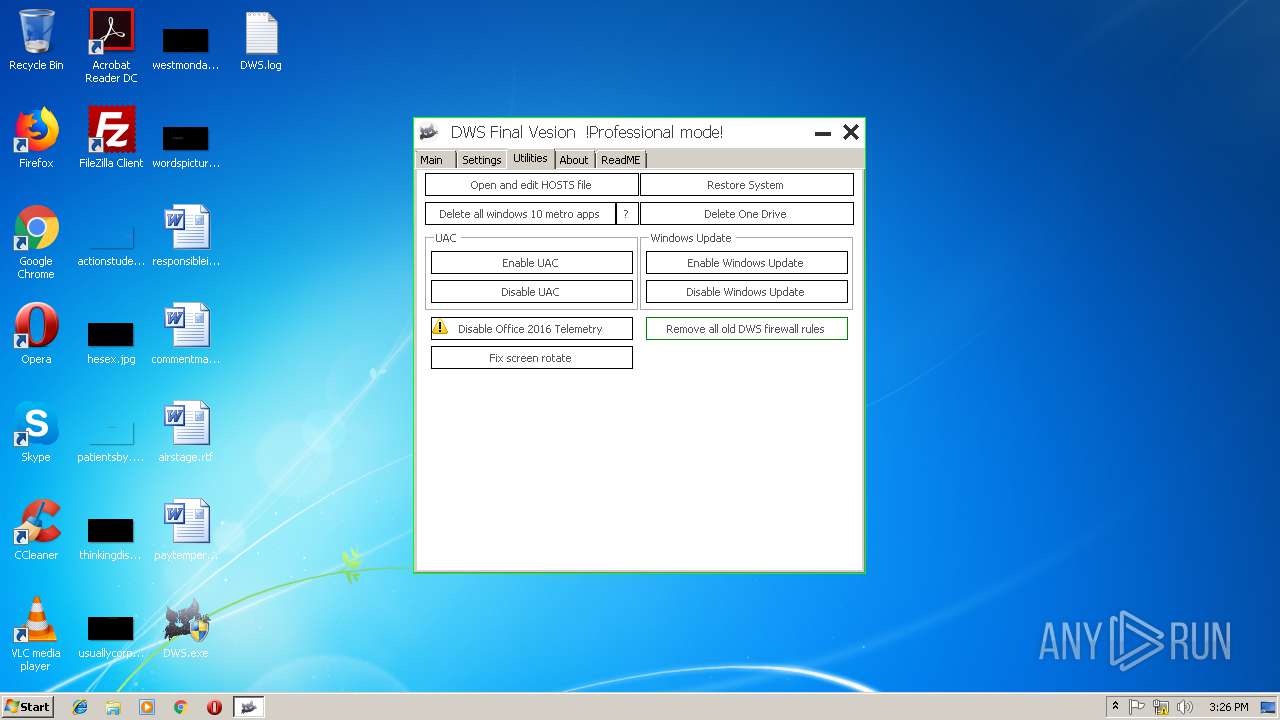
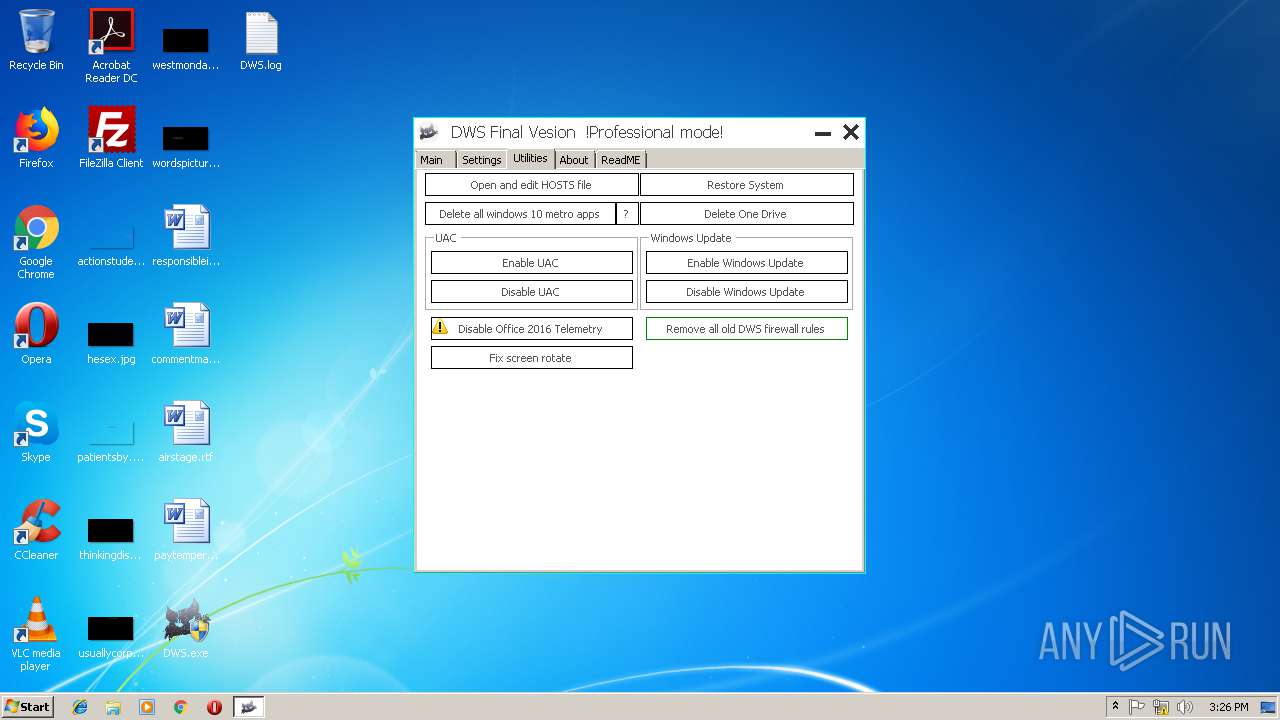
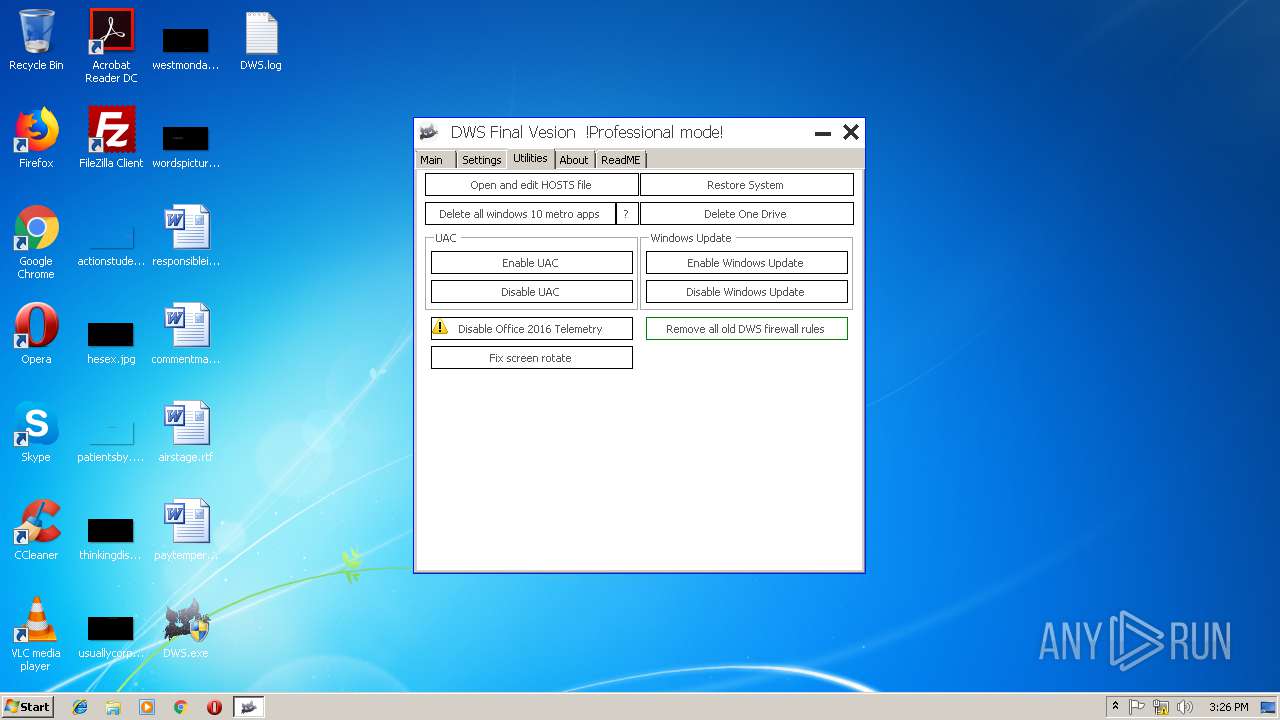
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1316 | "C:\Windows\System32\cmd.exe" /c rd "%LOCALAPPDATA%\Microsoft\OneDrive" /Q /S > NUL 2>&1 | C:\Windows\System32\cmd.exe | — | DWS.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1836 | "C:\Windows\System32\cmd.exe" /c REG DELETE "HKEY_CLASSES_ROOT\Wow6432Node\CLSID\{018D5C66-4533-4307-9B53-224DE2ED1FE6}" /f > NUL 2>&1 | C:\Windows\System32\cmd.exe | — | DWS.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2116 | "C:\Users\admin\Desktop\DWS.exe" | C:\Users\admin\Desktop\DWS.exe | explorer.exe | ||||||||||||
User: admin Company: WZT Integrity Level: HIGH Description: Destroy Windows 10 Spying Exit code: 0 Version: 2.2.2.2 Modules
| |||||||||||||||
| 2320 | "C:\Windows\System32\cmd.exe" /c net start wuauserv | C:\Windows\System32\cmd.exe | — | DWS.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2416 | "C:\Windows\System32\cmd.exe" /c REG DELETE "HKEY_CLASSES_ROOT\CLSID\{018D5C66-4533-4307-9B53-224DE2ED1FE6}" /f > NUL 2>&1 | C:\Windows\System32\cmd.exe | — | DWS.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2472 | "C:\Windows\System32\cmd.exe" /c rd "C:\OneDriveTemp" /Q /S > NUL 2>&1 | C:\Windows\System32\cmd.exe | — | DWS.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2528 | "C:\Windows\System32\cmd.exe" /c rd "C:\OneDriveTemp" /Q /S > NUL 2>&1 | C:\Windows\System32\cmd.exe | — | DWS.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2644 | ping 127.0.0.1 -n 5 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2664 | net start wuauserv | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2692 | REG DELETE "HKEY_CLASSES_ROOT\CLSID\{018D5C66-4533-4307-9B53-224DE2ED1FE6}" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
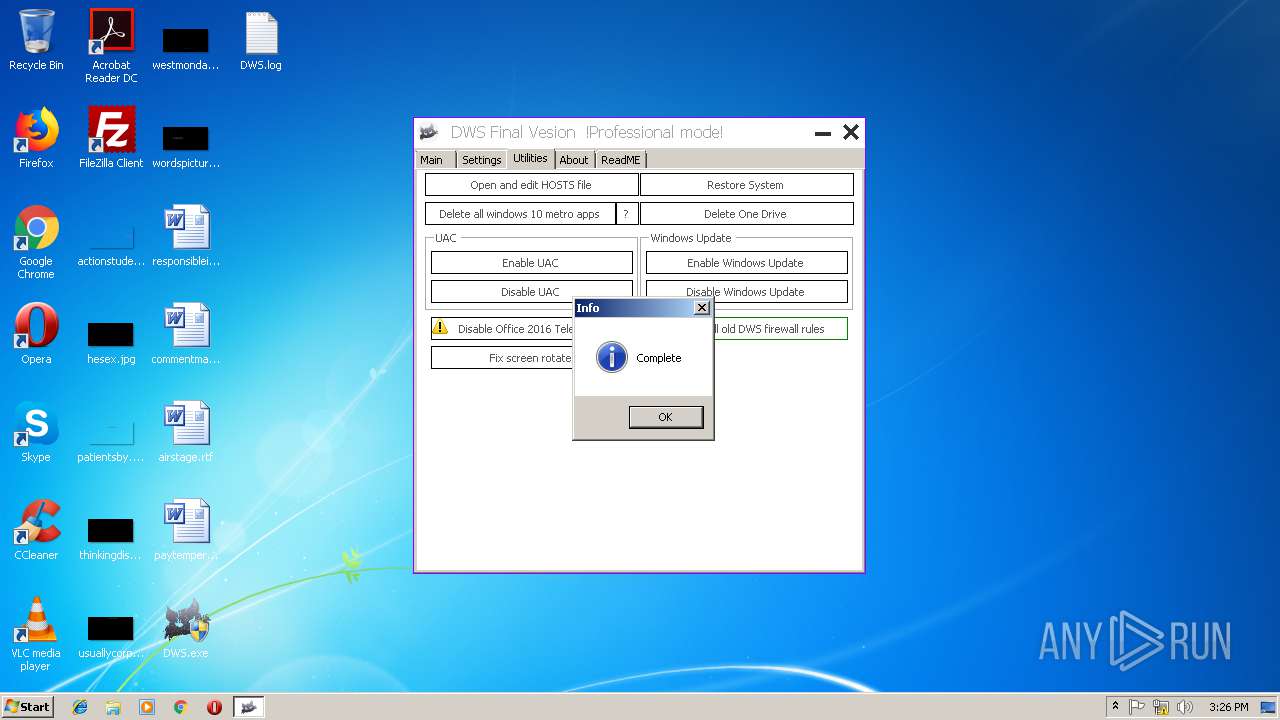
Total events
425
Read events
310
Write events
115
Delete events
0
Modification events
| (PID) Process: | (2116) DWS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\OneDrive |
| Operation: | write | Name: | DisableFileSyncNGSC |
Value: 1 | |||
| (PID) Process: | (2760) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3212) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3212) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (3212) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (3212) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (3212) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (3212) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (3212) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
| (PID) Process: | (3212) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-4 |
Value: 1.0 | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2760 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8Y03MC5QY6UCLIS1ALCJ.temp | — | |
MD5:— | SHA256:— | |||
| 2760 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1a598b.TMP | binary | |
MD5:— | SHA256:— | |||
| 2760 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2116 | DWS.exe | C:\Users\admin\Desktop\DWS.log | text | |
MD5:C59896B69385C7409882D598F723901F | SHA256:8BEC90F0CFAEBD5489DE823B6A53BB911412F5F43FFD72AB8F9E1B4BE1E07B55 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report