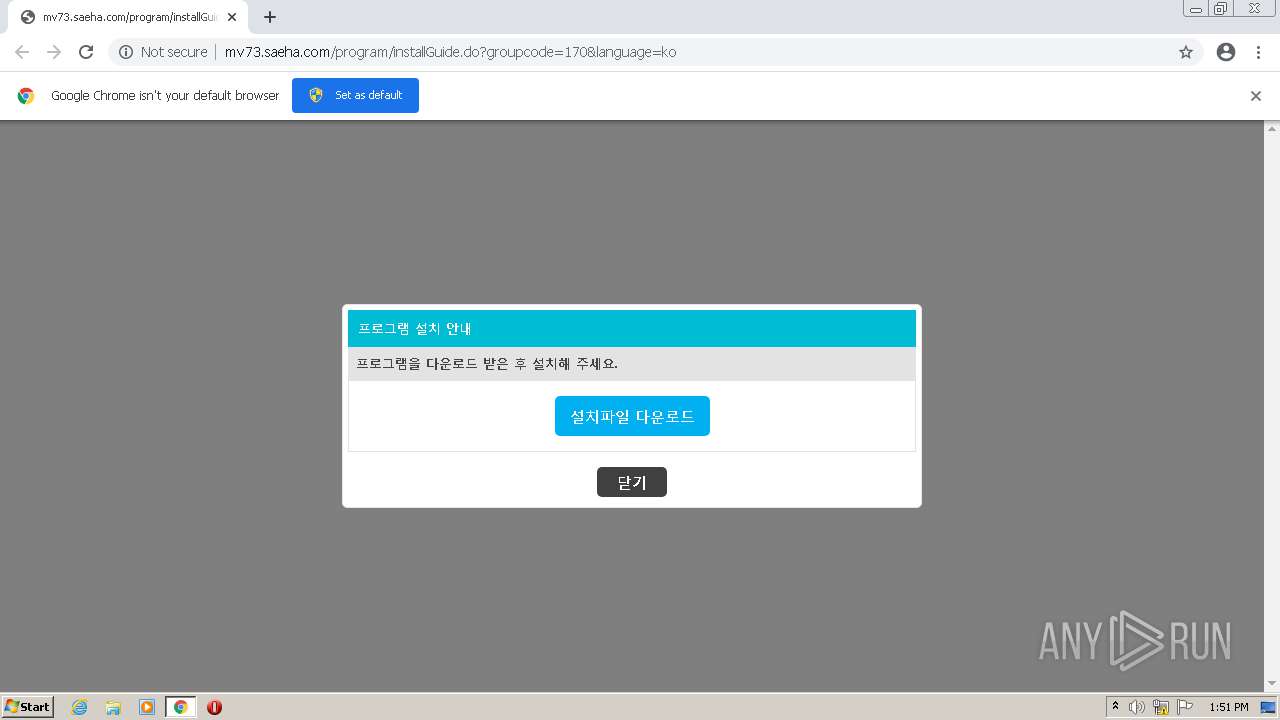
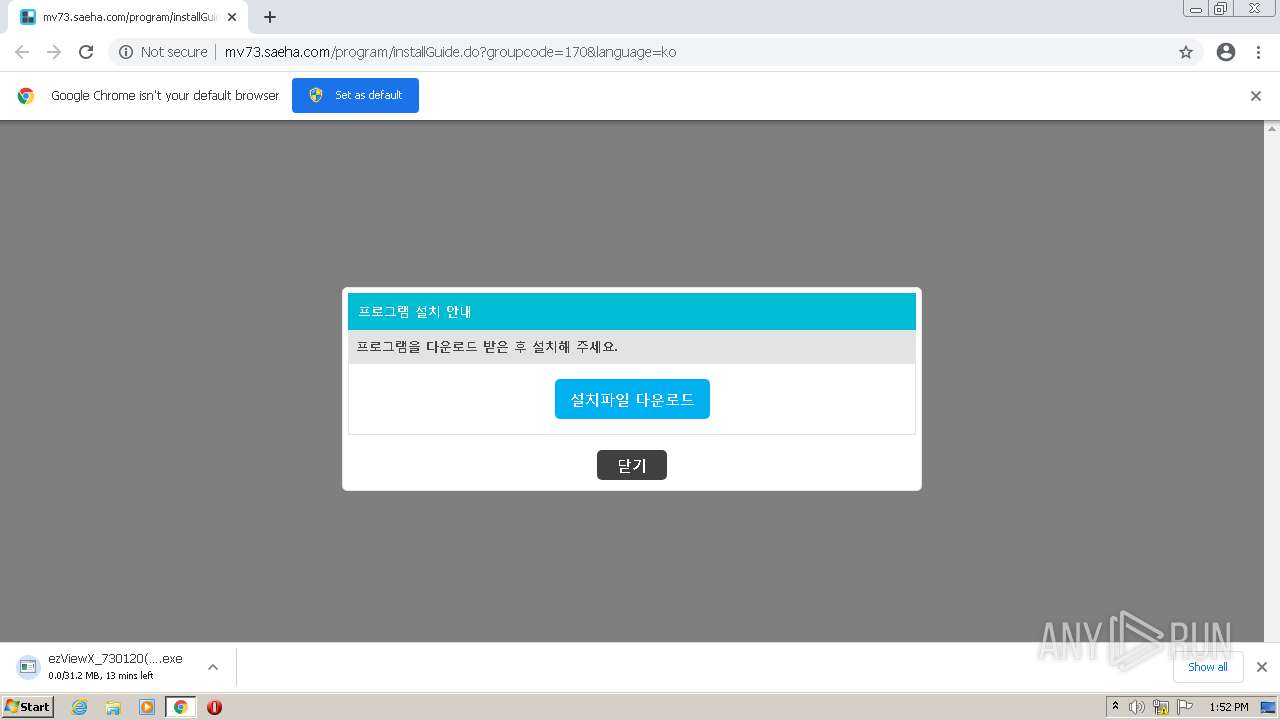
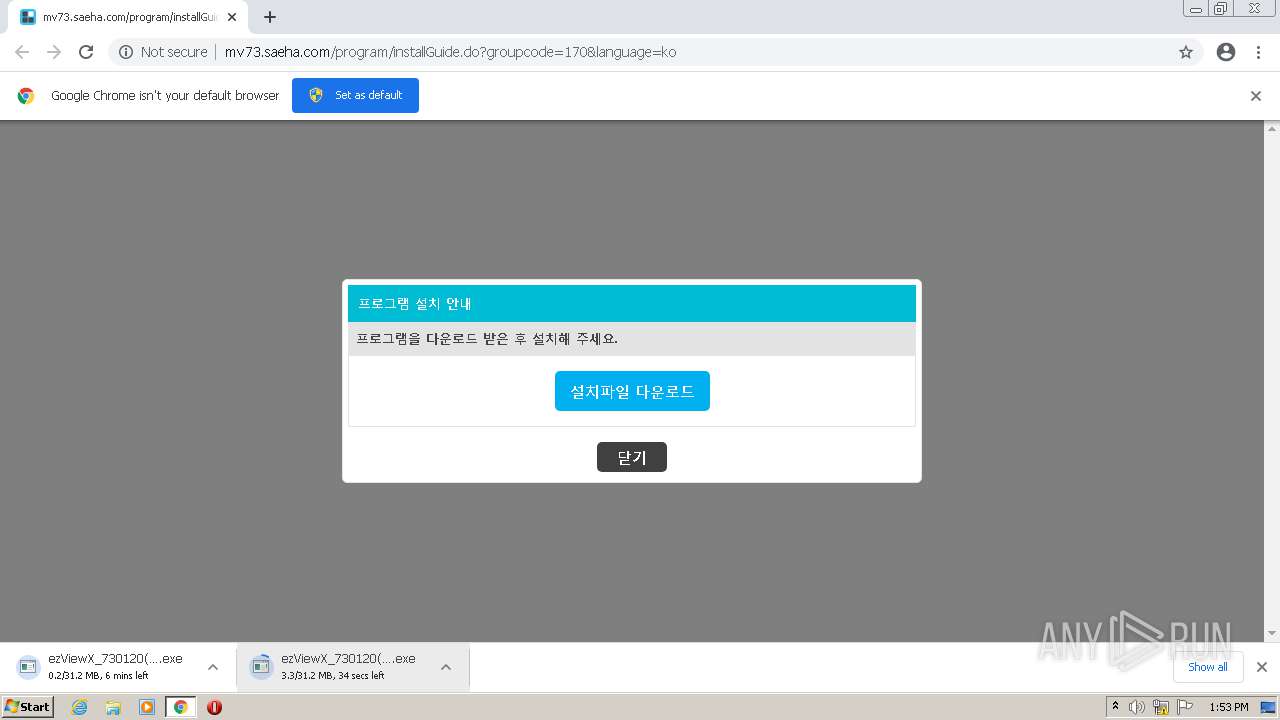
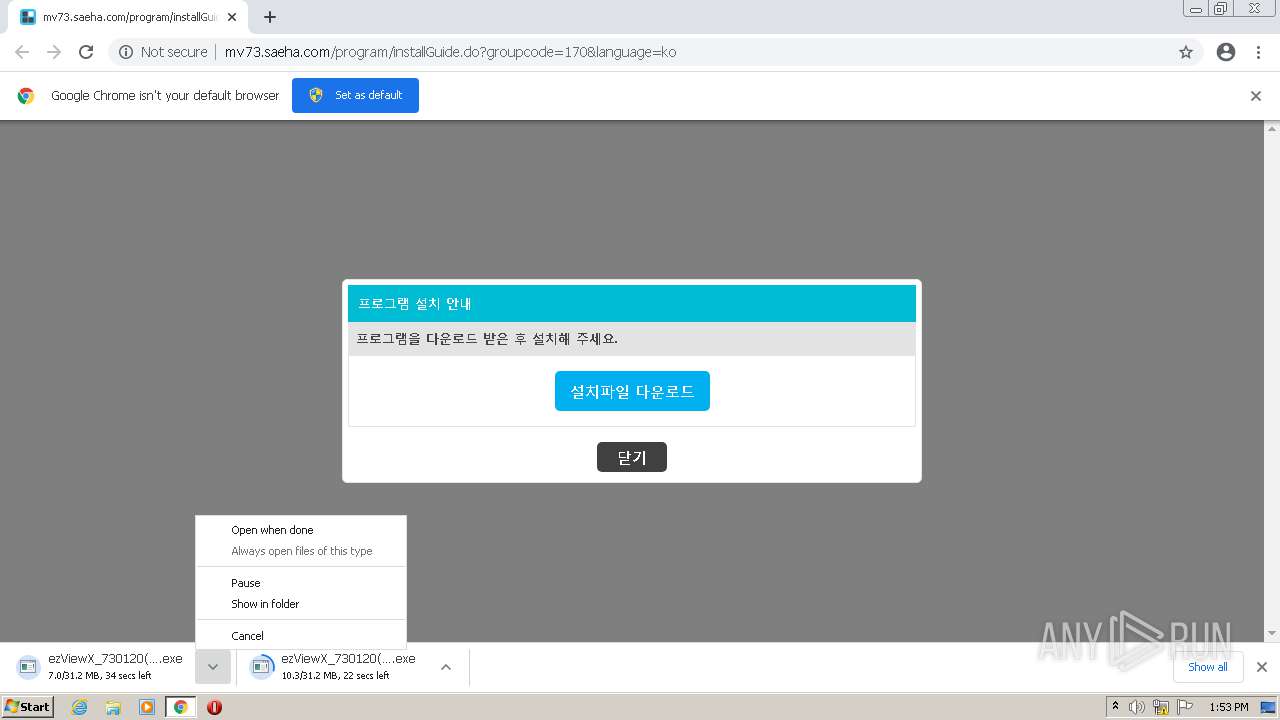
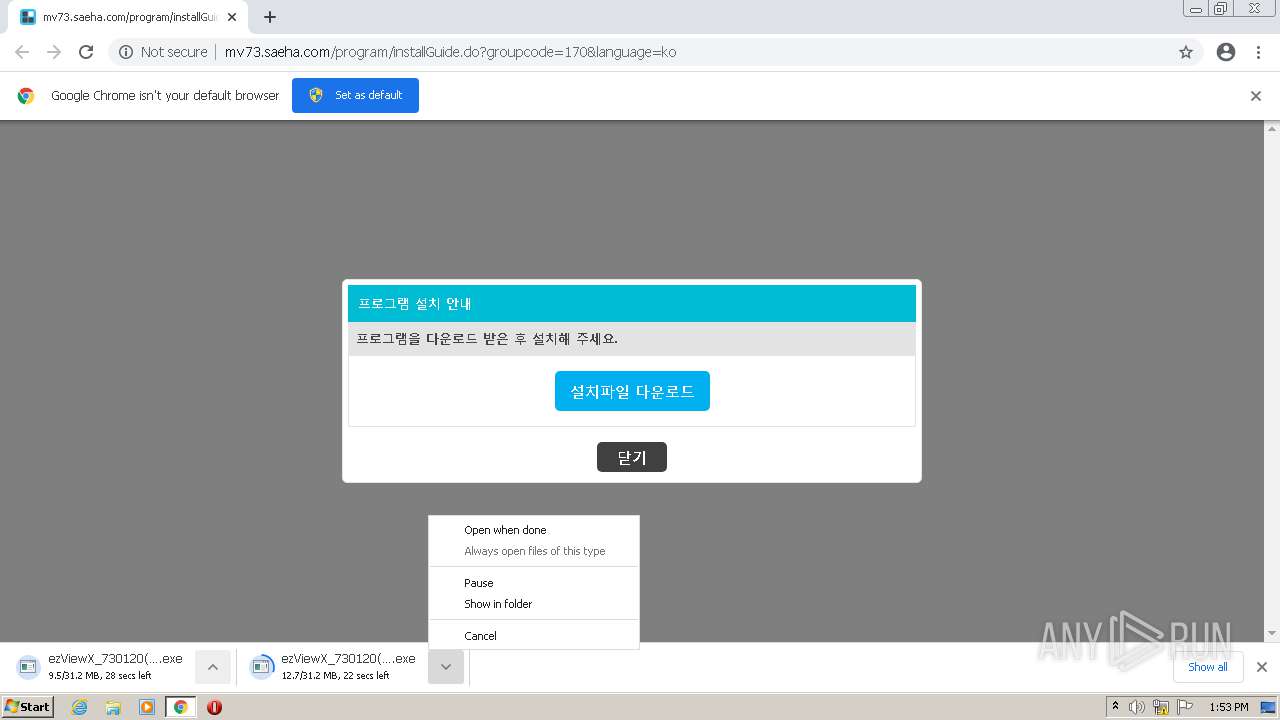
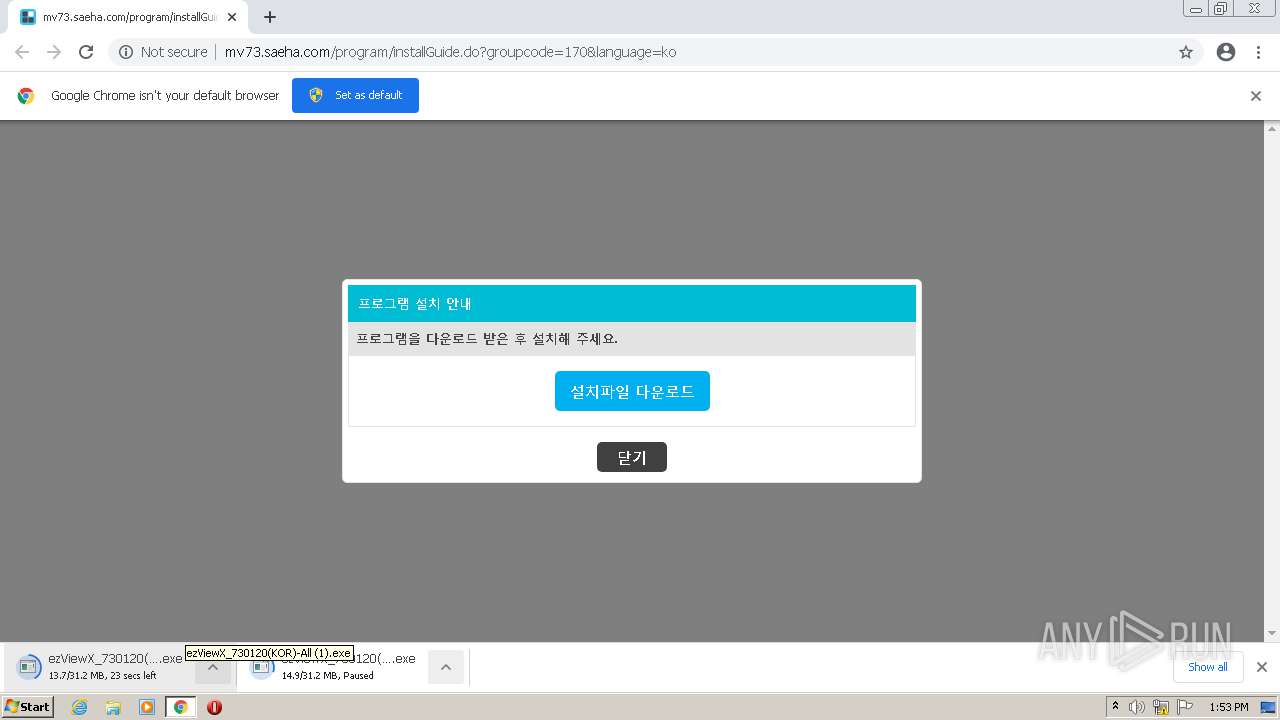
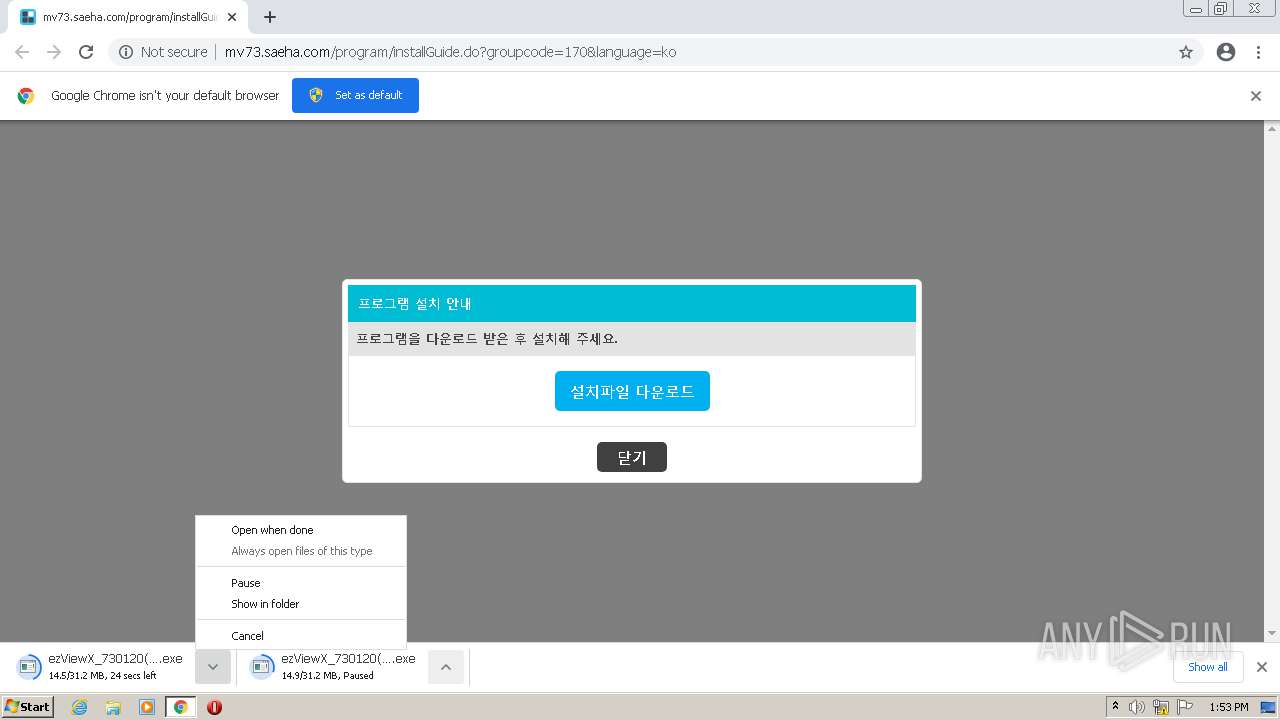
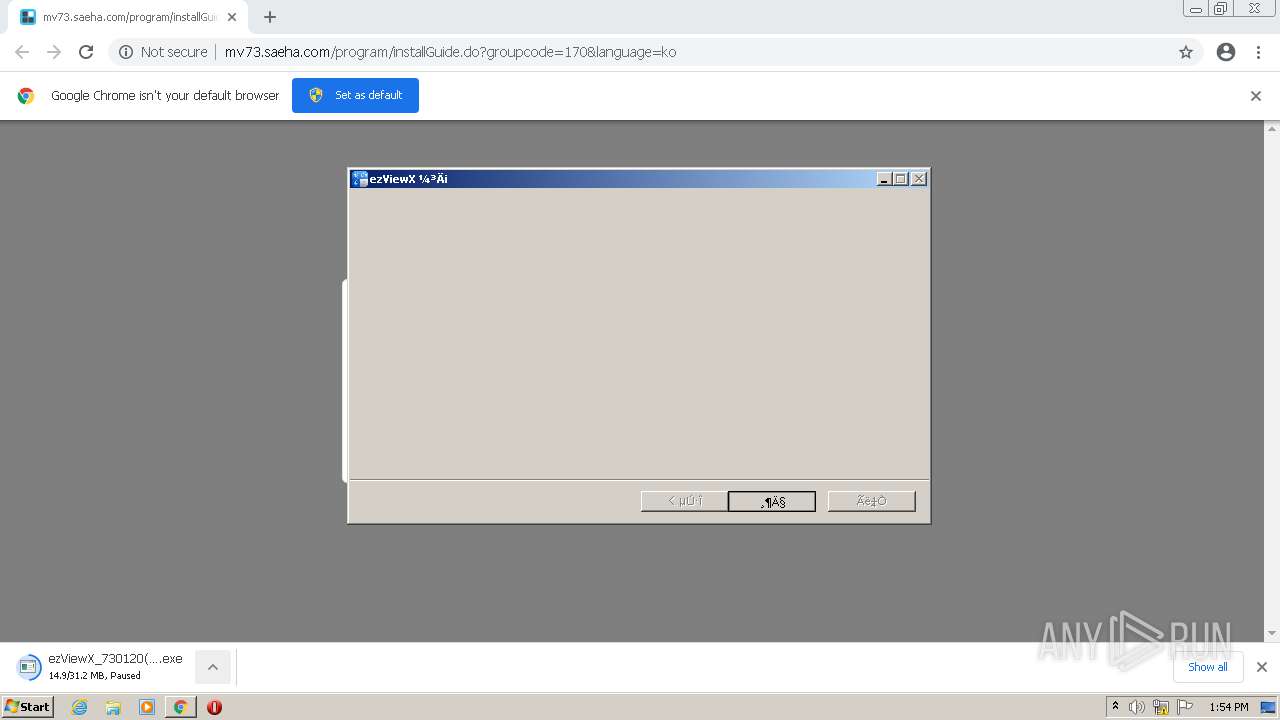
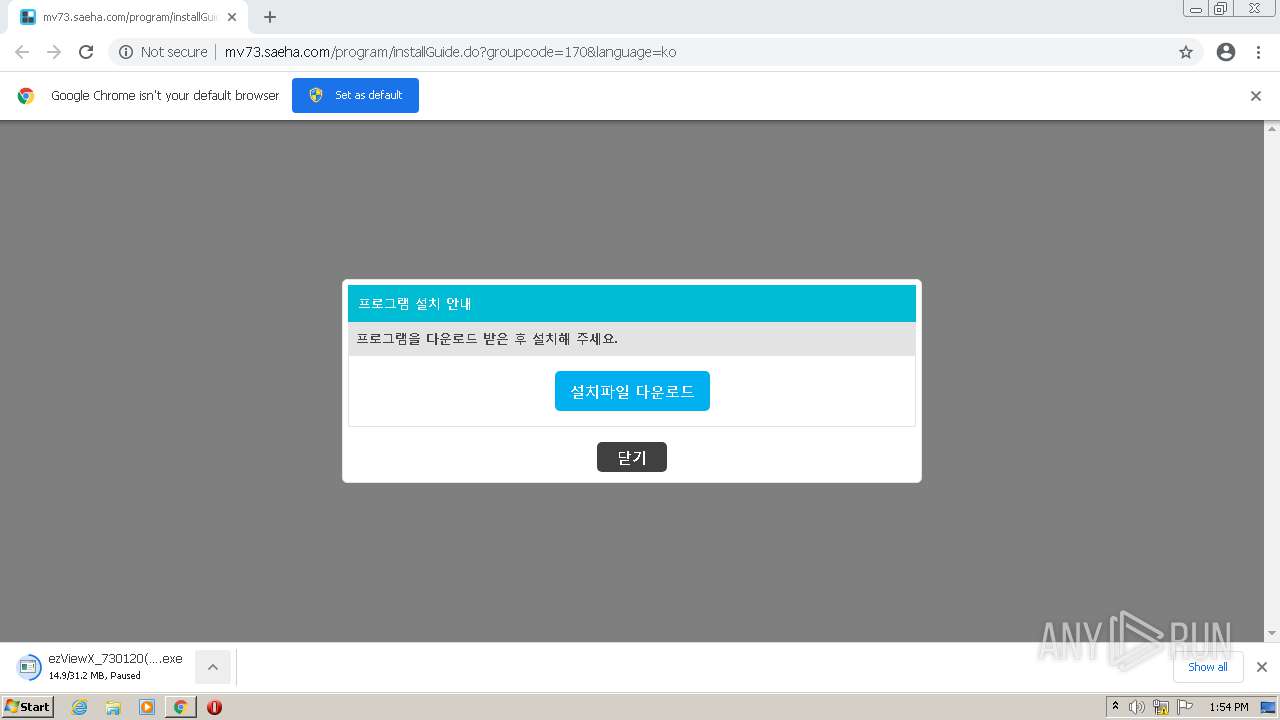
| URL: | http://mv73.saeha.com/program/installGuide.do?groupcode=170&language=ko |
| Full analysis: | https://app.any.run/tasks/392d3d3f-3f2f-41ba-a132-6f66e0e2051c |
| Verdict: | Malicious activity |
| Analysis date: | July 05, 2021, 12:51:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5D6773260746668DD8A8362BDF38E108 |
| SHA1: | 57DA04F2BC04F991D6179A31A86C26B0D4A5C218 |
| SHA256: | 2F505422C9B6DD6F47D3784AD8B3482A862F360B129B0ED0B41BD07BAF66CD62 |
| SSDEEP: | 3:N1KTJLDANQ39ZXhKks4Caj1mVTC9ln:CJANkRKksPA1R |
MALICIOUS
Application was dropped or rewritten from another process
- ezViewX_730120(KOR)-All (1).exe (PID: 3104)
- ezViewX_730120(KOR)-All (1).exe (PID: 4016)
- printerinstaller.exe (PID: 3652)
- MVWebAgent_6343(Kor).exe (PID: 3512)
- MVWebAgent.exe (PID: 452)
Drops executable file immediately after starts
- ezViewX_730120(KOR)-All (1).exe (PID: 3104)
- printerinstaller.exe (PID: 3652)
- spoolsv.exe (PID: 1236)
- MVWebAgent_6343(Kor).exe (PID: 3512)
Loads dropped or rewritten executable
- ezViewX_730120(KOR)-All (1).exe (PID: 3104)
- chrome.exe (PID: 2052)
- SearchProtocolHost.exe (PID: 2220)
- chrome.exe (PID: 3892)
- DllHost.exe (PID: 2460)
- consent.exe (PID: 1596)
- chrome.exe (PID: 1904)
- printerinstaller.exe (PID: 3652)
- spoolsv.exe (PID: 1236)
- MVWebAgent_6343(Kor).exe (PID: 3512)
- nsA7FF.tmp (PID: 1372)
- nsA8EA.tmp (PID: 1252)
- nsA9C6.tmp (PID: 1800)
- MVWebAgent.exe (PID: 452)
Changes the autorun value in the registry
- MVWebAgent_6343(Kor).exe (PID: 3512)
Changes settings of System certificates
- MVWebAgent.exe (PID: 452)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 1904)
- spoolsv.exe (PID: 1236)
- printerinstaller.exe (PID: 3652)
- ezViewX_730120(KOR)-All (1).exe (PID: 3104)
- MVWebAgent_6343(Kor).exe (PID: 3512)
Drops a file with too old compile date
- chrome.exe (PID: 1904)
- ezViewX_730120(KOR)-All (1).exe (PID: 3104)
- MVWebAgent_6343(Kor).exe (PID: 3512)
Reads the computer name
- ezViewX_730120(KOR)-All (1).exe (PID: 3104)
- printerinstaller.exe (PID: 3652)
- MVWebAgent_6343(Kor).exe (PID: 3512)
- MVWebAgent.exe (PID: 452)
Checks supported languages
- ezViewX_730120(KOR)-All (1).exe (PID: 3104)
- printerinstaller.exe (PID: 3652)
- MVWebAgent_6343(Kor).exe (PID: 3512)
- nsA7FF.tmp (PID: 1372)
- nsA8EA.tmp (PID: 1252)
- nsA9C6.tmp (PID: 1800)
- MVWebAgent.exe (PID: 452)
Drops a file that was compiled in debug mode
- ezViewX_730120(KOR)-All (1).exe (PID: 3104)
- MVWebAgent_6343(Kor).exe (PID: 3512)
Creates files in the Windows directory
- printerinstaller.exe (PID: 3652)
- spoolsv.exe (PID: 1236)
- ezViewX_730120(KOR)-All (1).exe (PID: 3104)
Removes files from Windows directory
- spoolsv.exe (PID: 1236)
Executed via COM
- rundll32.exe (PID: 3584)
Reads Environment values
- ezViewX_730120(KOR)-All (1).exe (PID: 3104)
Uses TASKKILL.EXE to kill process
- nsA7FF.tmp (PID: 1372)
- nsA8EA.tmp (PID: 1252)
Starts application with an unusual extension
- MVWebAgent_6343(Kor).exe (PID: 3512)
Executed as Windows Service
- spoolsv.exe (PID: 3436)
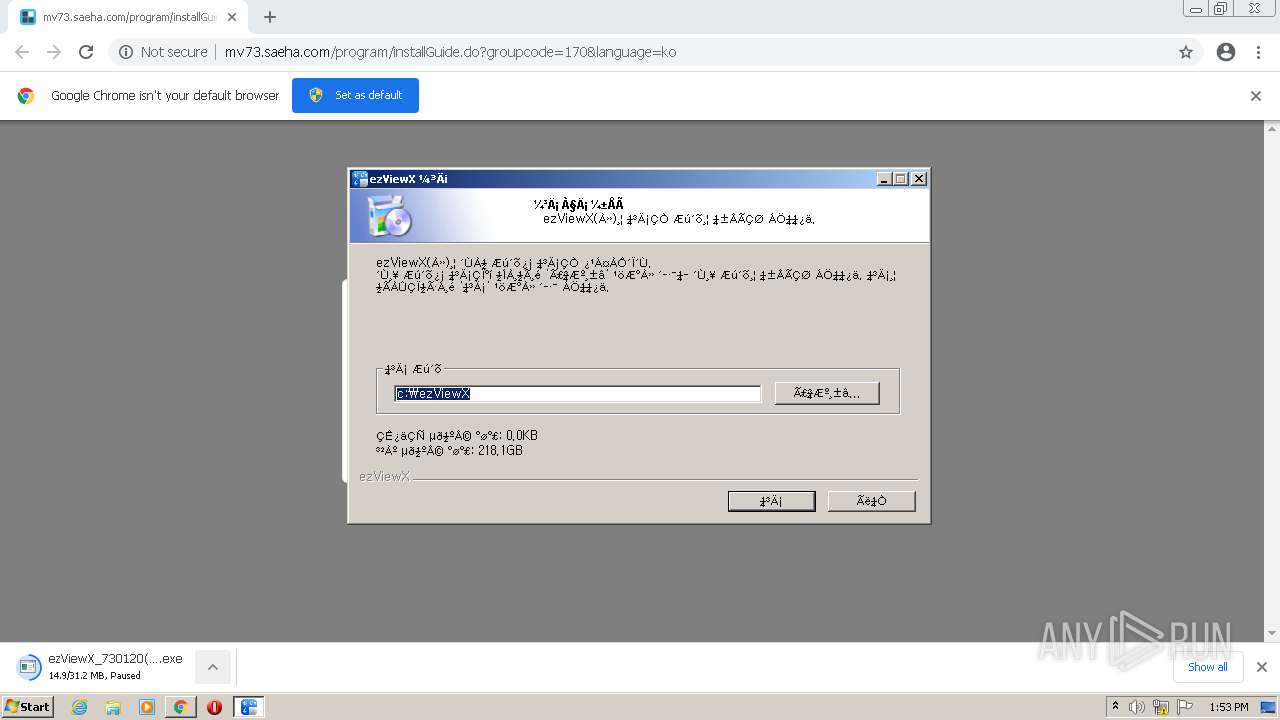
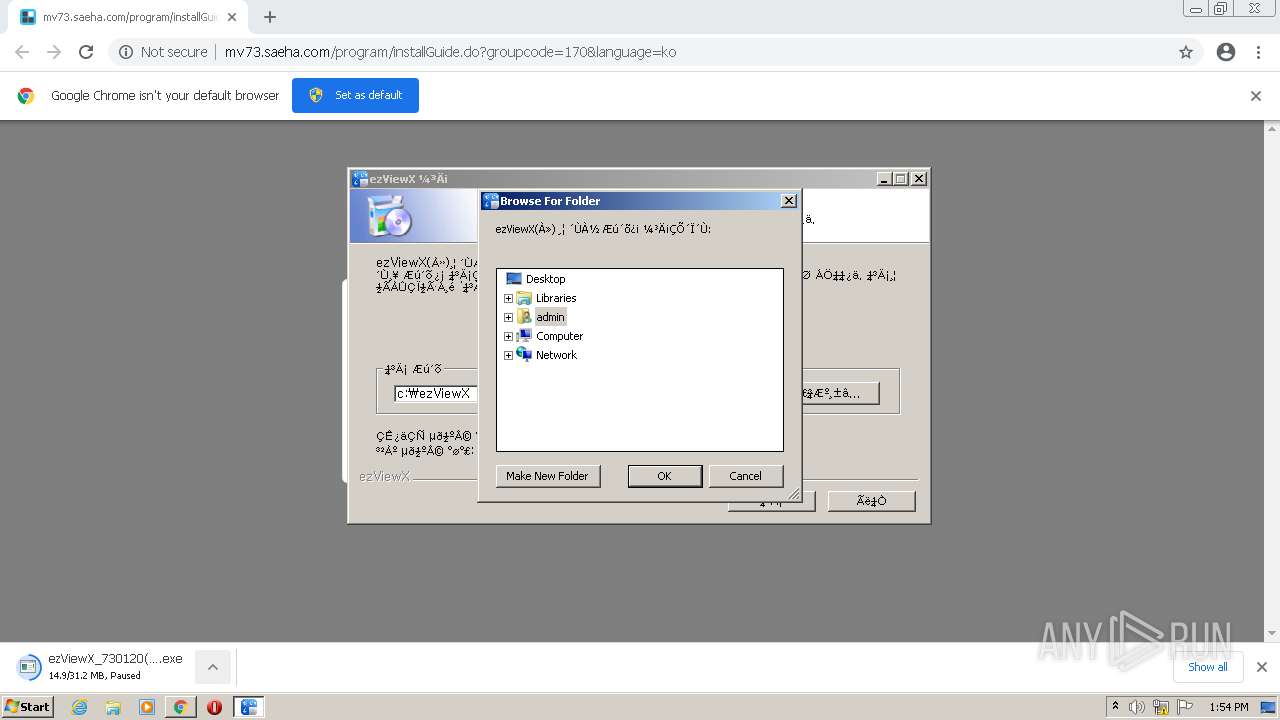
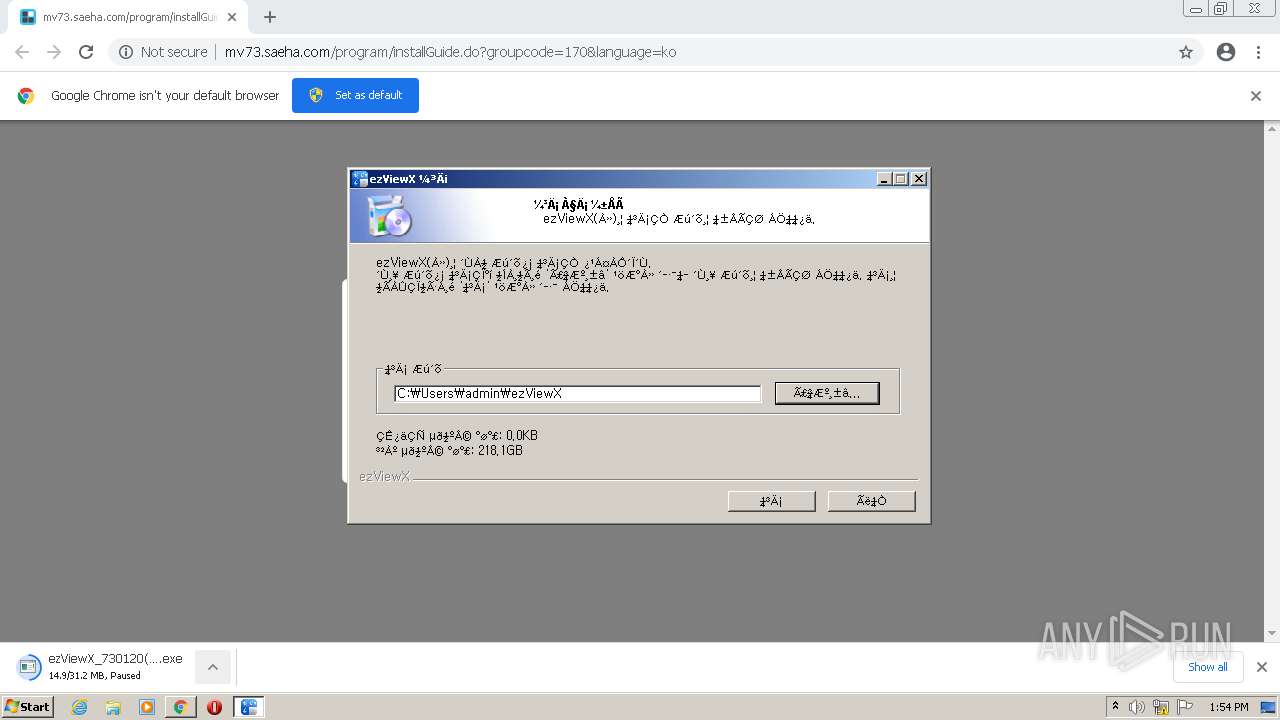
Creates a software uninstall entry
- MVWebAgent_6343(Kor).exe (PID: 3512)
- ezViewX_730120(KOR)-All (1).exe (PID: 3104)
Changes default file association
- ezViewX_730120(KOR)-All (1).exe (PID: 3104)
Creates files in the program directory
- ezViewX_730120(KOR)-All (1).exe (PID: 3104)
Creates files in the user directory
- MVWebAgent.exe (PID: 452)
INFO
Checks supported languages
- chrome.exe (PID: 1904)
- chrome.exe (PID: 1124)
- chrome.exe (PID: 4064)
- chrome.exe (PID: 1676)
- chrome.exe (PID: 2244)
- chrome.exe (PID: 2176)
- chrome.exe (PID: 3260)
- chrome.exe (PID: 2708)
- chrome.exe (PID: 3236)
- chrome.exe (PID: 3144)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 1820)
- chrome.exe (PID: 3904)
- chrome.exe (PID: 2872)
- SearchProtocolHost.exe (PID: 2220)
- chrome.exe (PID: 2400)
- chrome.exe (PID: 2292)
- chrome.exe (PID: 2572)
- chrome.exe (PID: 2840)
- chrome.exe (PID: 2524)
- chrome.exe (PID: 120)
- chrome.exe (PID: 3552)
- chrome.exe (PID: 2052)
- chrome.exe (PID: 3892)
- chrome.exe (PID: 3436)
- chrome.exe (PID: 3208)
- DllHost.exe (PID: 2460)
- consent.exe (PID: 1596)
- chrome.exe (PID: 2968)
- chrome.exe (PID: 1204)
- spoolsv.exe (PID: 1236)
- rundll32.exe (PID: 3584)
- spoolsv.exe (PID: 3436)
- TaskKill.exe (PID: 3960)
- TaskKill.exe (PID: 3644)
Application launched itself
- chrome.exe (PID: 1904)
Reads the computer name
- chrome.exe (PID: 1904)
- chrome.exe (PID: 2176)
- chrome.exe (PID: 3144)
- chrome.exe (PID: 1676)
- chrome.exe (PID: 3260)
- chrome.exe (PID: 3236)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 3904)
- SearchProtocolHost.exe (PID: 2220)
- chrome.exe (PID: 2052)
- chrome.exe (PID: 3892)
- DllHost.exe (PID: 2460)
- consent.exe (PID: 1596)
- spoolsv.exe (PID: 3436)
- TaskKill.exe (PID: 3960)
- TaskKill.exe (PID: 3644)
Reads the hosts file
- chrome.exe (PID: 2176)
- chrome.exe (PID: 1904)
Reads settings of System Certificates
- chrome.exe (PID: 2176)
- chrome.exe (PID: 1904)
- consent.exe (PID: 1596)
- MVWebAgent.exe (PID: 452)
Reads the date of Windows installation
- chrome.exe (PID: 2420)
Checks Windows Trust Settings
- chrome.exe (PID: 1904)
- consent.exe (PID: 1596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
83
Monitored processes
43
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1016,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1600 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 452 | c:\MVWebAgent\MVWebAgent.exe | c:\MVWebAgent\MVWebAgent.exe | — | MVWebAgent_6343(Kor).exe | |||||||||||
User: admin Company: (?)???? Integrity Level: HIGH Description: MVWebAgent Exit code: 0 Version: 6.3.4.3 Modules
| |||||||||||||||
| 1124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1816 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1016,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3676 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1236 | C:\Windows\System32\spoolsv.exe | C:\Windows\System32\spoolsv.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Spooler SubSystem App Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1252 | "C:\Users\admin\AppData\Local\Temp\nstA7FE.tmp\nsA8EA.tmp" TaskKill /F /IM MVWebAgent.exe | C:\Users\admin\AppData\Local\Temp\nstA7FE.tmp\nsA8EA.tmp | — | MVWebAgent_6343(Kor).exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 128 Modules
| |||||||||||||||
| 1372 | "C:\Users\admin\AppData\Local\Temp\nstA7FE.tmp\nsA7FF.tmp" TaskKill /F /IM MVLauncher.exe | C:\Users\admin\AppData\Local\Temp\nstA7FE.tmp\nsA7FF.tmp | — | MVWebAgent_6343(Kor).exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 128 Modules
| |||||||||||||||
| 1596 | consent.exe 872 414 0030BF50 | C:\Windows\system32\consent.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Consent UI for administrative applications Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1044 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1800 | "C:\Users\admin\AppData\Local\Temp\nstA7FE.tmp\nsA9C6.tmp" c:\MVWebAgent\MVLauncher.exe -u | C:\Users\admin\AppData\Local\Temp\nstA7FE.tmp\nsA9C6.tmp | — | MVWebAgent_6343(Kor).exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225501 Modules
| |||||||||||||||
Total events
22 251
Read events
21 809
Write events
436
Delete events
6
Modification events
| (PID) Process: | (1904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1904) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (1904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
198
Suspicious files
32
Text files
144
Unknown types
142
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60E30067-770.pma | — | |
MD5:— | SHA256:— | |||
| 1904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\28085f79-a929-46fa-aa6d-5cf74e9e8c3b.tmp | text | |
MD5:— | SHA256:— | |||
| 1904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 1904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4f76d879-022d-4de2-b35c-ffc5067cdb06.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 1904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 1904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 1904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 1904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
15
DNS requests
10
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2176 | chrome.exe | GET | — | 121.170.164.120:80 | http://mv73.saeha.com/download/client/totalPackage.do?groupcode=170&callurl= | KR | — | — | suspicious |
— | — | HEAD | — | 173.194.182.106:80 | http://r5---sn-4g5ednld.gvt1.com/edgedl/release2/chrome_component/AM0QFpqOodq9cFQ3ZjT-PNU_6711/ANuDTnGviHzlMEVyXl5HKy8?cms_redirect=yes&mh=qa&mip=45.135.187.25&mm=28&mn=sn-4g5ednld&ms=nvh&mt=1625489296&mv=m&mvi=5&pl=24&rmhost=r1---sn-4g5ednld.gvt1.com&shardbypass=yes&smhost=r1---sn-4g5ednse.gvt1.com | US | — | — | whitelisted |
2176 | chrome.exe | GET | — | 121.170.164.120:80 | http://mv73.saeha.com/download/client/totalPackage.do?groupcode=170&callurl= | KR | — | — | suspicious |
— | — | HEAD | — | 74.125.11.23:80 | http://r1---sn-4g5ednee.gvt1.com/edgedl/release2/chrome_component/OF5zAAN0ldzNcghwIbX-qA_2021.6.21.1141/M1eZenhp7SDXqDz1O16sdA?cms_redirect=yes&mh=Rv&mip=45.135.187.25&mm=28&mn=sn-4g5ednee&ms=nvh&mt=1625489296&mv=m&mvi=1&pl=24&rmhost=r6---sn-4g5ednee.gvt1.com&shardbypass=yes&smhost=r5---sn-4g5ednsz.gvt1.com | US | — | — | whitelisted |
2176 | chrome.exe | GET | 200 | 121.170.164.120:80 | http://mv73.saeha.com/resources/common/images/favicon.ico | KR | image | 115 Kb | suspicious |
2176 | chrome.exe | GET | 200 | 121.170.164.120:80 | http://mv73.saeha.com/generateMessage.do | KR | text | 7.49 Kb | suspicious |
2176 | chrome.exe | GET | 200 | 121.170.164.120:80 | http://mv73.saeha.com/resources/common/images/favicon.ico | KR | image | 115 Kb | suspicious |
2176 | chrome.exe | GET | 200 | 121.170.164.120:80 | http://mv73.saeha.com/resources/common/images/btn/bu_check.png | KR | image | 2.51 Kb | suspicious |
— | — | HEAD | — | 142.250.186.174:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/OF5zAAN0ldzNcghwIbX-qA_2021.6.21.1141/M1eZenhp7SDXqDz1O16sdA | US | — | — | whitelisted |
2176 | chrome.exe | GET | 200 | 121.170.164.120:80 | http://mv73.saeha.com/resources/service/css/layout.css?v=2021-01-07T12:46:31Z | KR | text | 10.0 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2176 | chrome.exe | 142.250.186.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
2176 | chrome.exe | 142.250.184.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
2176 | chrome.exe | 121.170.164.120:80 | mv73.saeha.com | Korea Telecom | KR | suspicious |
2176 | chrome.exe | 142.250.186.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
— | — | 142.250.185.67:443 | update.googleapis.com | Google Inc. | US | whitelisted |
2176 | chrome.exe | 142.250.185.67:443 | update.googleapis.com | Google Inc. | US | whitelisted |
— | — | 74.125.11.23:80 | — | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mv73.saeha.com |
| suspicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r3---sn-4g5ednle.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2176 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2176 | chrome.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2176 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2176 | chrome.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
Process | Message |
|---|---|
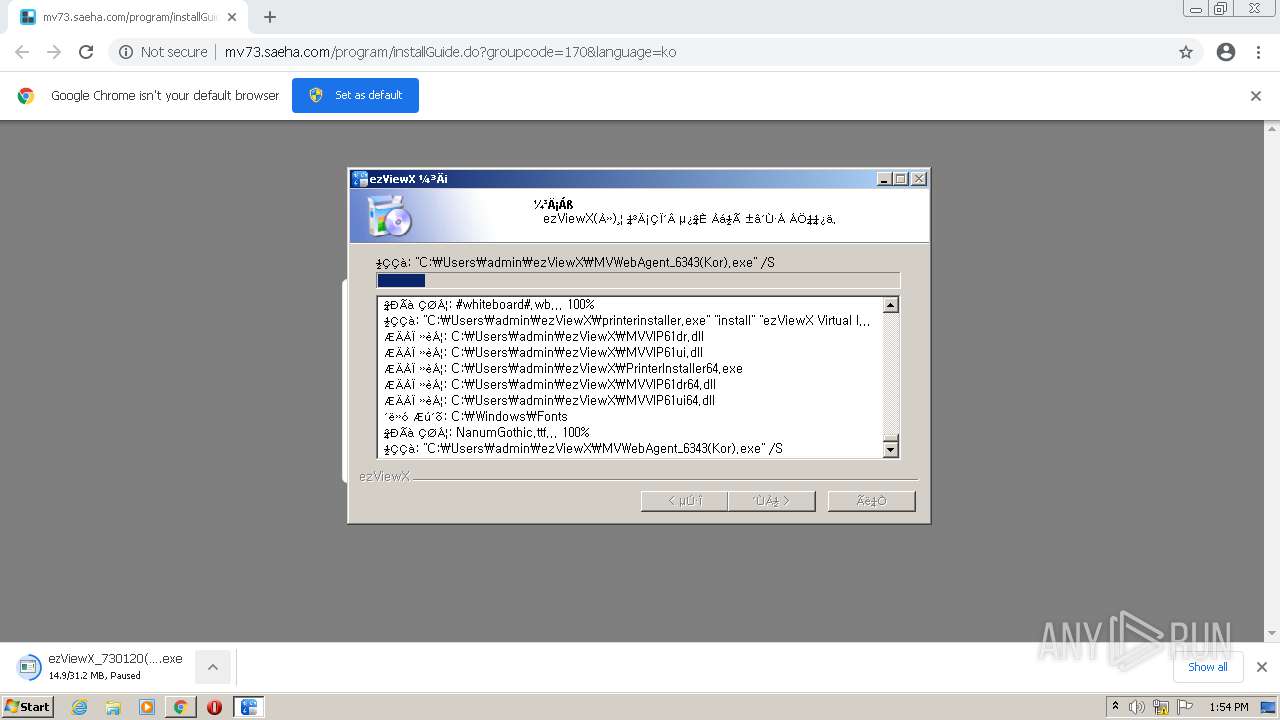
printerinstaller.exe | [PDI] install Start
|
printerinstaller.exe | [PDI] szPrinterName:ezViewX Virtual Image Printer, szSourceDir:C:\Users\admin\ezViewX, szProductName:ezViewX
|
printerinstaller.exe | [PDI] [DoInstallDriver] AddPrinterDriver pSourceDirs:C:\Users\admin\ezViewX, szDriverName:ezViewX Virtual Image Driver, szPrinterName:ezViewX Virtual Image Printer
|
printerinstaller.exe | [PDI] ChangeSpoolerDirectory, start szPrinterName:ezViewX Virtual Image Printer
|
printerinstaller.exe | [PDI] ChangeSpoolerDirectory, Success szPrinterName:ezViewX Virtual Image Printer, Path:C:\temp\PRINTERS
|
printerinstaller.exe | [PDI] [CheckPortInstalled] Check Port installed: 0
|
printerinstaller.exe | [PDI] DoInstallPort, AddPort szPortName:ezViewX Virtual Image Port
|
printerinstaller.exe | [PDI] g_szProductName:ezViewX, g_szDriverName:ezViewX Virtual Image Driver, g_szPortName:ezViewX Virtual Image Port
|
printerinstaller.exe | [PDI] DoInstallPrinter, AddPrinter lptstrPrinterName:ezViewX Virtual Image Printer, szDriverName:ezViewX Virtual Image Driver, lptstrPortName:ezViewX Virtual Image Port
|
printerinstaller.exe | [PDI] [DoInstallPrinter] AddPrinter Success!!!
|