| File name: | 2f2ff0008cd3177041066f039a345307a917704207c407d7dde255483c42764a.rtf |
| Full analysis: | https://app.any.run/tasks/ef043708-a3ce-47c6-9e63-35b956632331 |
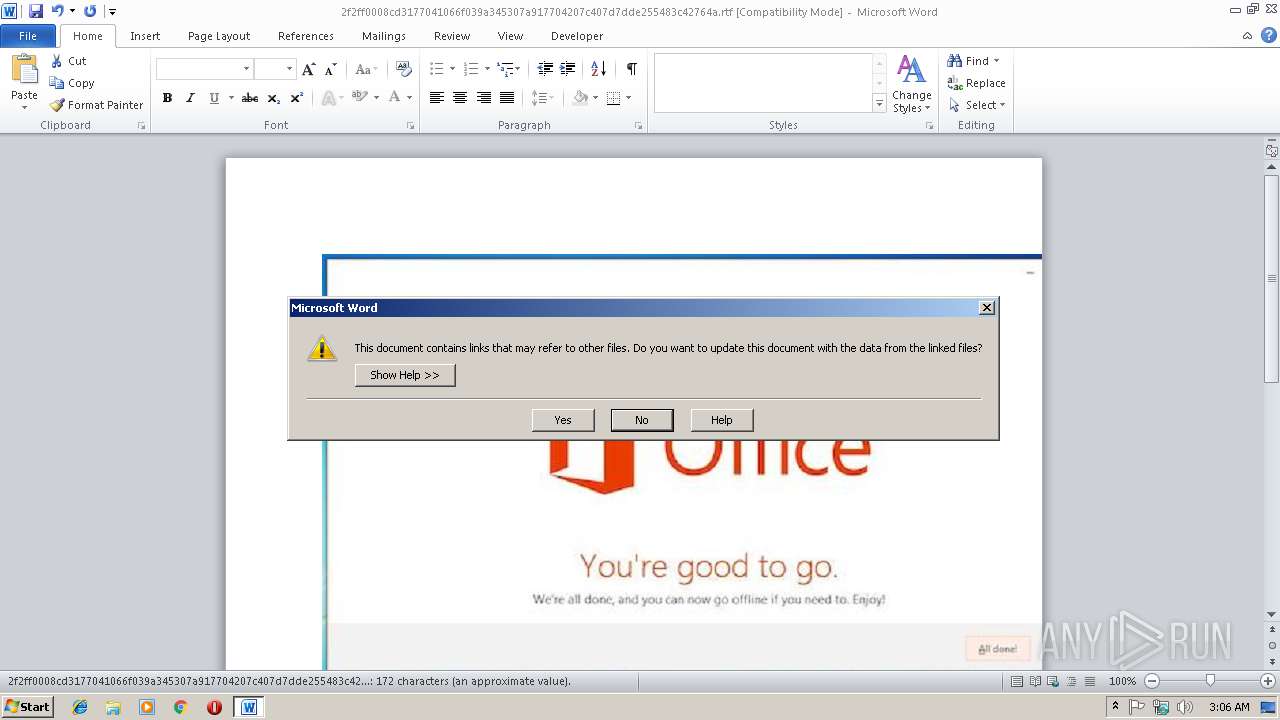
| Verdict: | Malicious activity |
| Analysis date: | March 15, 2019, 03:06:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | 473909C2647D2C200FD40CC2F44ADFBE |
| SHA1: | 515804545A7C51CCD9553198C28BAE85DF2A9C1D |
| SHA256: | 2F2FF0008CD3177041066F039A345307A917704207C407D7DDE255483C42764A |
| SSDEEP: | 24576:pd6qlMEjK5vK59lDYY88E19qd1UVueD10515VPiKPpz6mpKZglenGZxL:t |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2996)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2996)
Runs app for hidden code execution
- cmd.exe (PID: 2460)
- cmd.exe (PID: 3948)
Application was dropped or rewritten from another process
- saver.scr (PID: 2788)
- saver.scr (PID: 3332)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3948)
- cmd.exe (PID: 2380)
- cmd.exe (PID: 2460)
- cmd.exe (PID: 2652)
Executes scripts
- cmd.exe (PID: 2652)
Executable content was dropped or overwritten
- cscript.exe (PID: 3896)
Uses TASKKILL.EXE to kill Office Apps
- cmd.exe (PID: 2652)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2652)
- cmd.exe (PID: 2404)
- cmd.exe (PID: 2792)
- cmd.exe (PID: 3736)
- cmd.exe (PID: 2732)
- cmd.exe (PID: 3684)
- cmd.exe (PID: 3328)
Starts application with an unusual extension
- cmd.exe (PID: 2652)
- saver.scr (PID: 3332)
Application launched itself
- saver.scr (PID: 3332)
- cmd.exe (PID: 2652)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2996)
Creates files in the user directory
- WINWORD.EXE (PID: 2996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
69
Monitored processes
37
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | TASkKILL /F /IM winword.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 764 | TIMEOUT /T 1 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1760 | REG QUERY "HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Word\File MRU" /v "Item 1" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2064 | REG QUERY "HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\12.0\Word\File MRU" /v "Item 1" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2240 | TIMEOUT /T 1 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2312 | reg delete HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Word\Resiliency /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2320 | reg delete HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\14.0\Word\Resiliency /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2368 | reg delete HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\12.0\Word\Resiliency /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2380 | CmD | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2404 | C:\Windows\system32\cmd.exe /c REG QUERY "HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Word\File MRU" /v "Item 1" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 095
Read events
1 064
Write events
28
Delete events
3
Modification events
| (PID) Process: | (2996) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 7<, |
Value: 373C2C00B40B0000010000000000000000000000 | |||
| (PID) Process: | (2996) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2996) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2996) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1315897367 | |||
| (PID) Process: | (2996) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315897488 | |||
| (PID) Process: | (2996) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315897489 | |||
| (PID) Process: | (2996) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: B40B000082D62C10DCDAD40100000000 | |||
| (PID) Process: | (2996) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 1=, |
Value: 313D2C00B40B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2996) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 1=, |
Value: 313D2C00B40B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2996) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
4
Text files
9
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2996 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE497.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2996 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\mt6nzqofd.cmd | text | |
MD5:— | SHA256:— | |||
| 2996 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2652 | cmd.exe | C:\Users\admin\AppData\Local\Temp\_.vbs | text | |
MD5:— | SHA256:— | |||
| 2996 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\kulebiaka.ZiP | compressed | |
MD5:— | SHA256:— | |||
| 2996 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$2ff0008cd3177041066f039a345307a917704207c407d7dde255483c42764a.rtf | pgc | |
MD5:— | SHA256:— | |||
| 2996 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\uffm.cmd | text | |
MD5:C8F1BFC0B0E46EE97DE6214DAE9011A1 | SHA256:D631AF21957914C1FA711184F0553198C6C4B252CD6A43E481793E81034796A9 | |||
| 2996 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\a.ScT | xml | |
MD5:5CEF9568750C6F4273282DF6710C3F55 | SHA256:0B5AFEC364F5263893A6F4C1707D7D1E6188EB5AD0378252C9595424DD9FA35E | |||
| 3332 | saver.scr | C:\Users\admin\AppData\Local\Temp\~DFF74CB86A335FE1F5.TMP | binary | |
MD5:— | SHA256:— | |||
| 2996 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{3FF639A6-C22C-4E9B-B5CF-1823B65FCF7D}.tmp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report