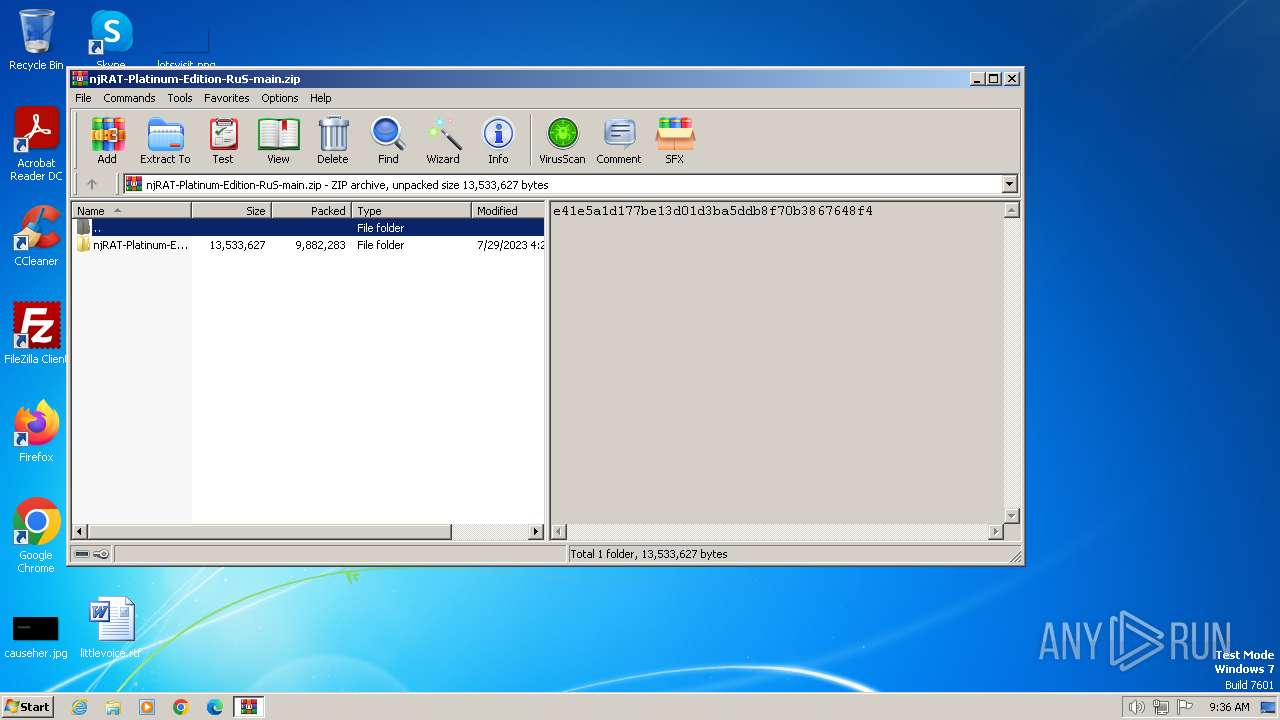
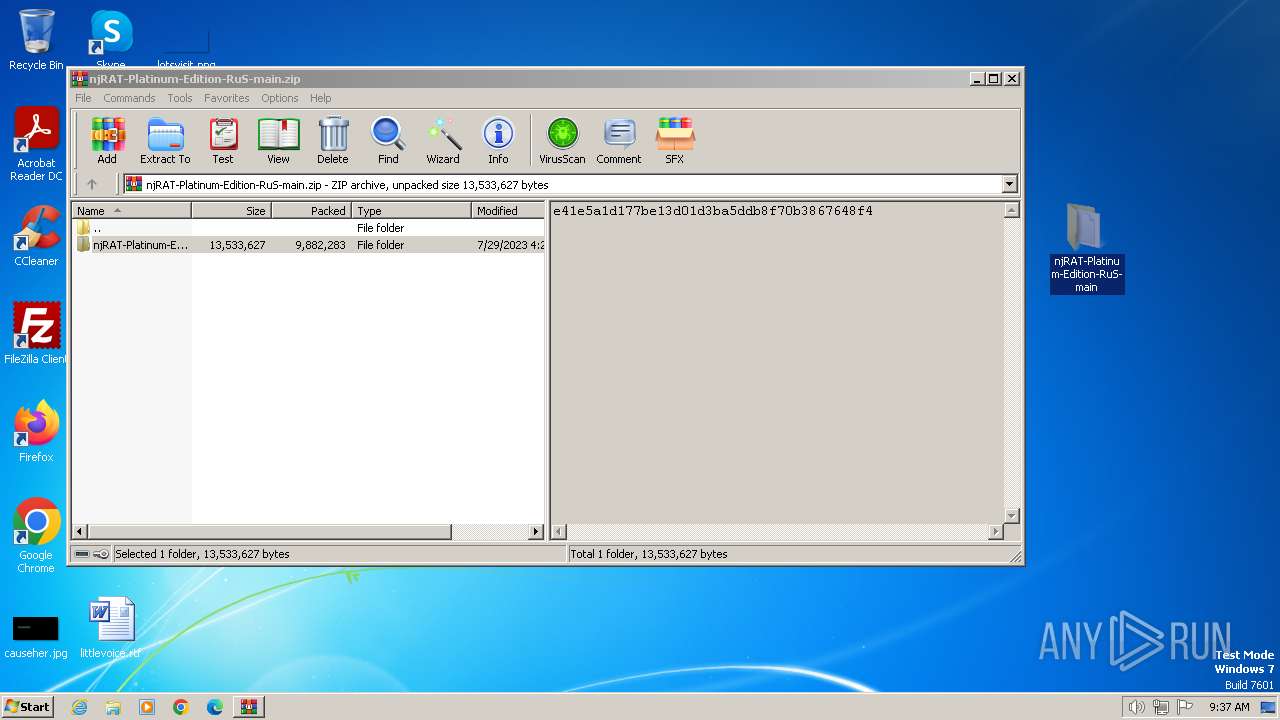
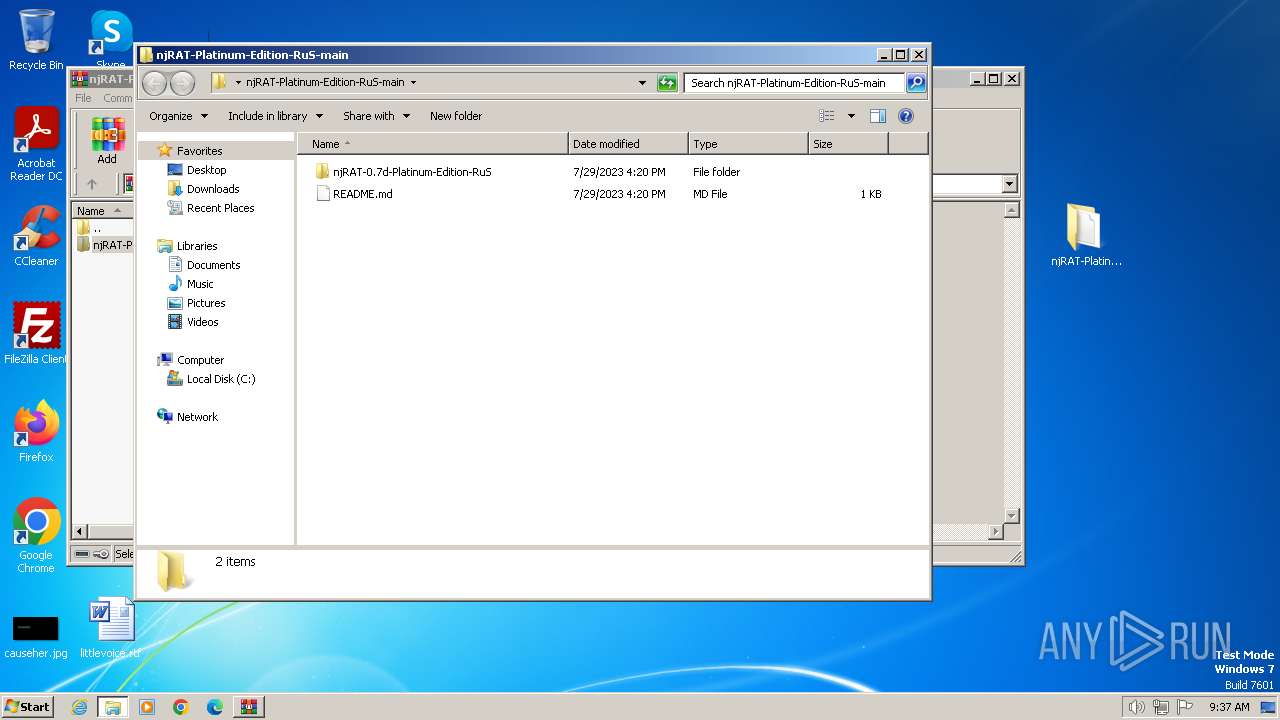
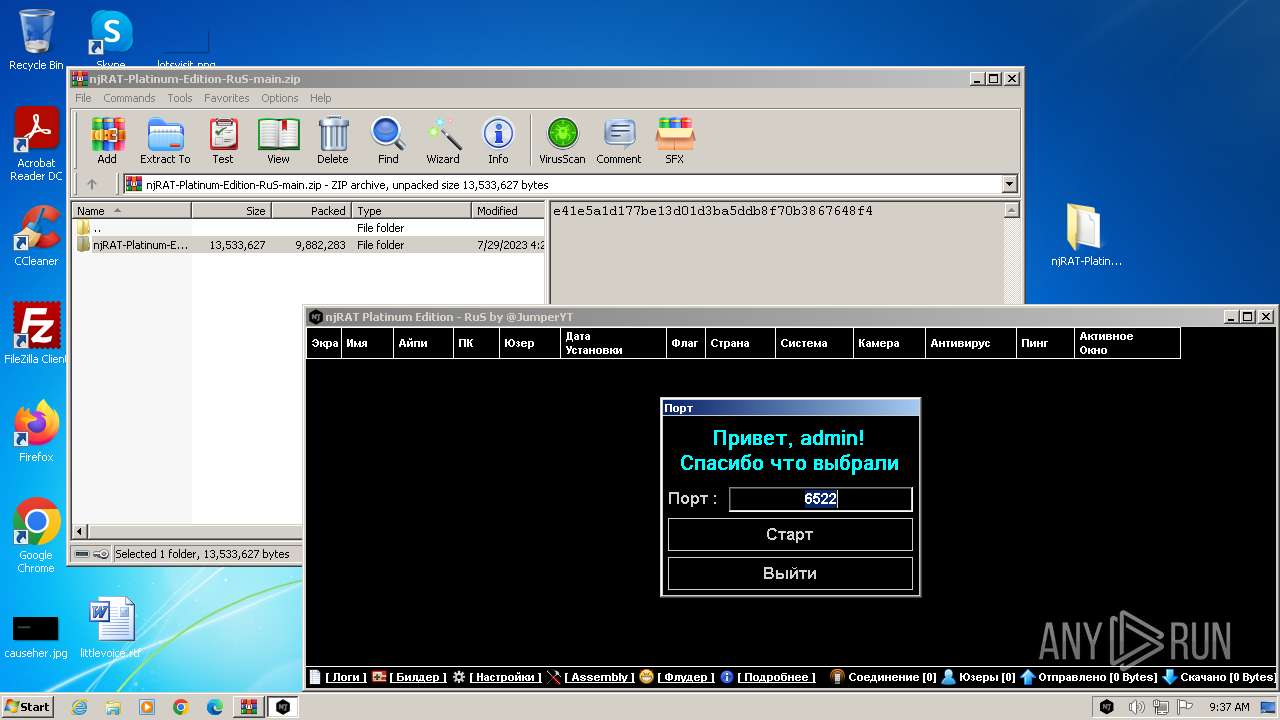
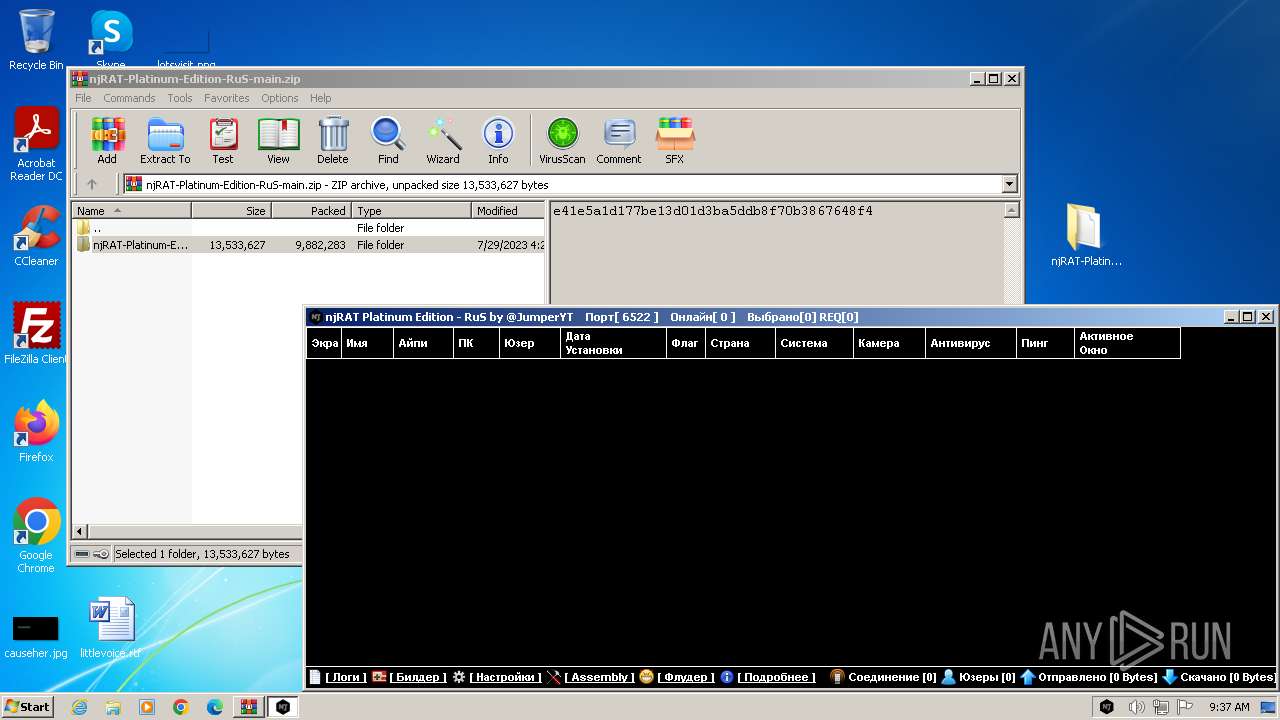
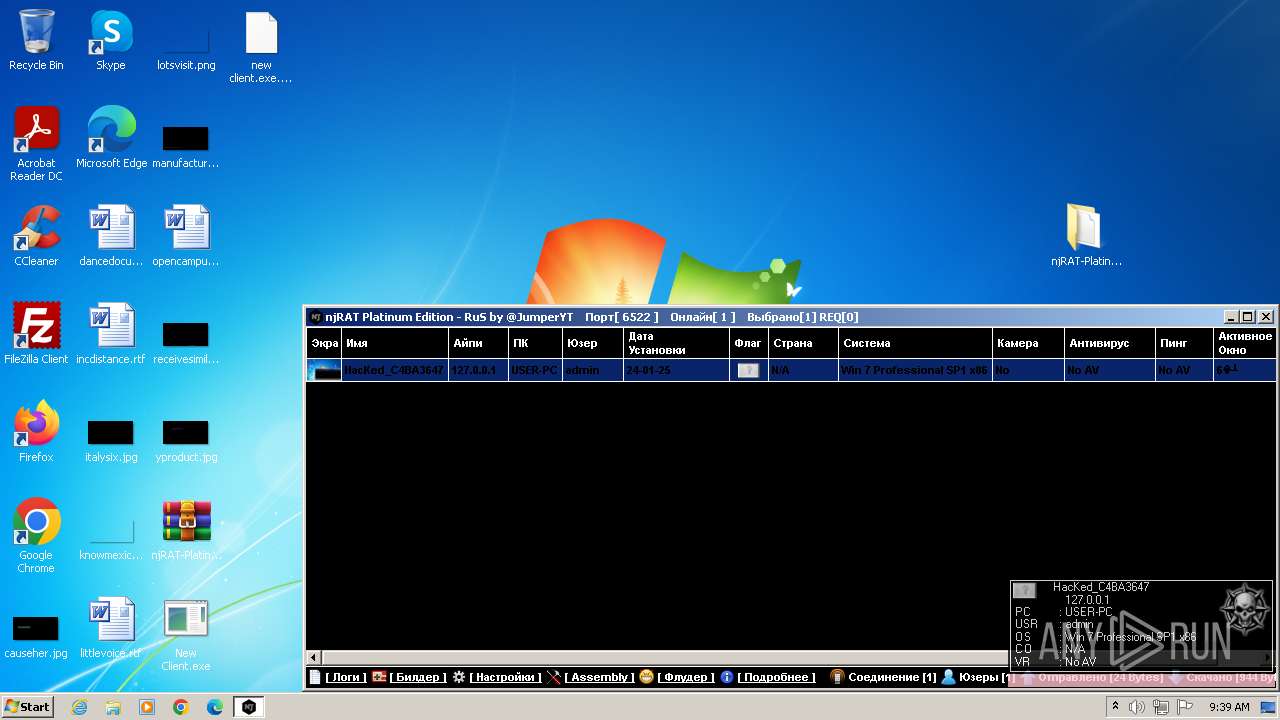
| File name: | njRAT-Platinum-Edition-RuS-main.zip |
| Full analysis: | https://app.any.run/tasks/c1c89d89-448e-4b9b-b3bd-10cb668d78df |
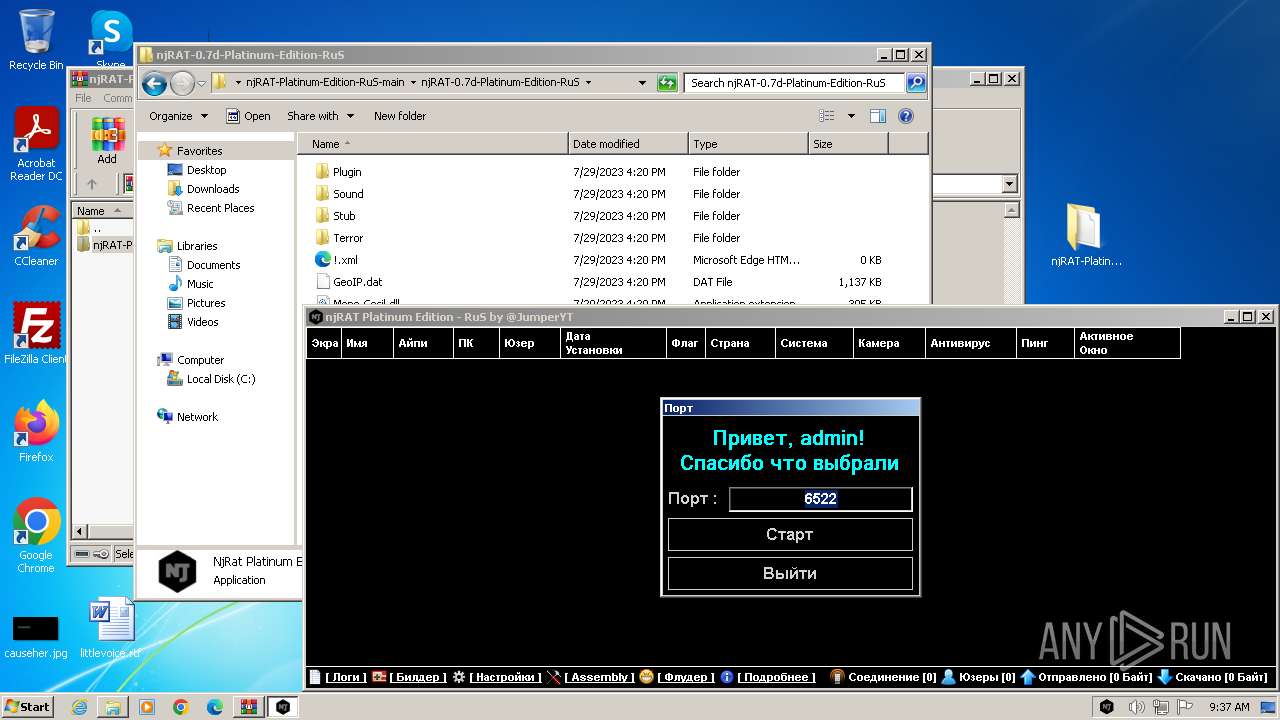
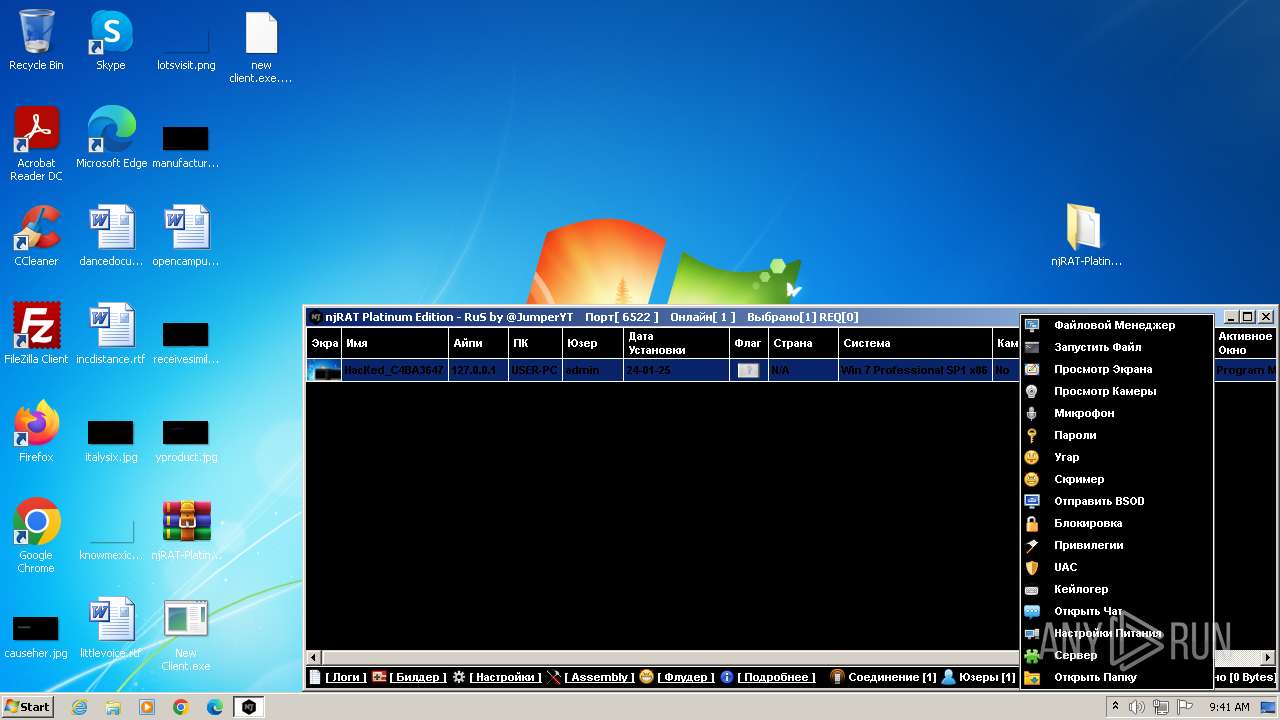
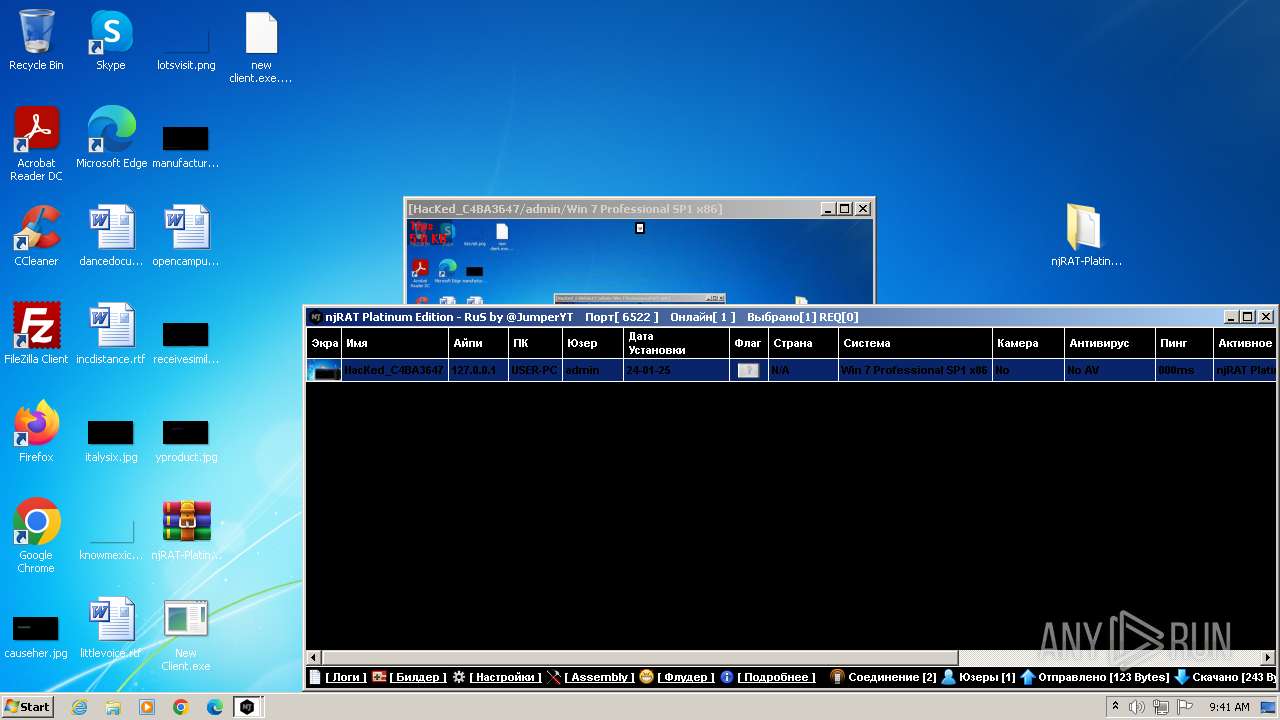
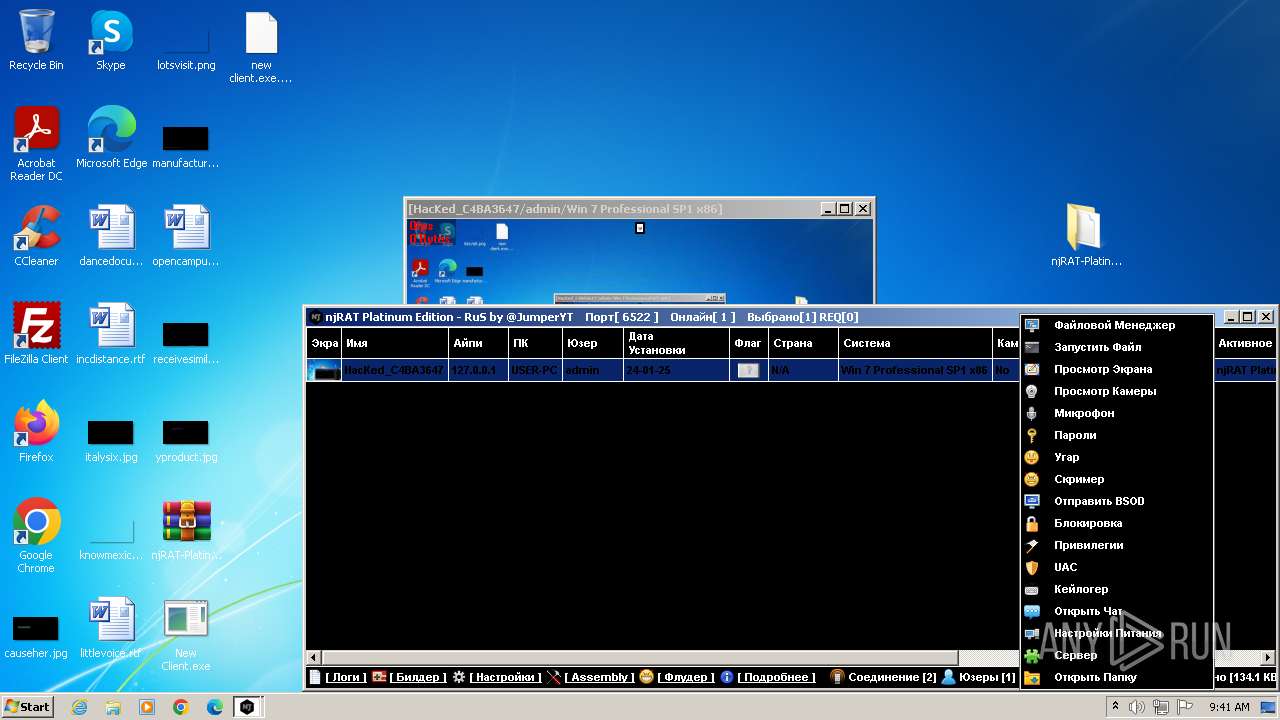
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2024, 09:36:40 |
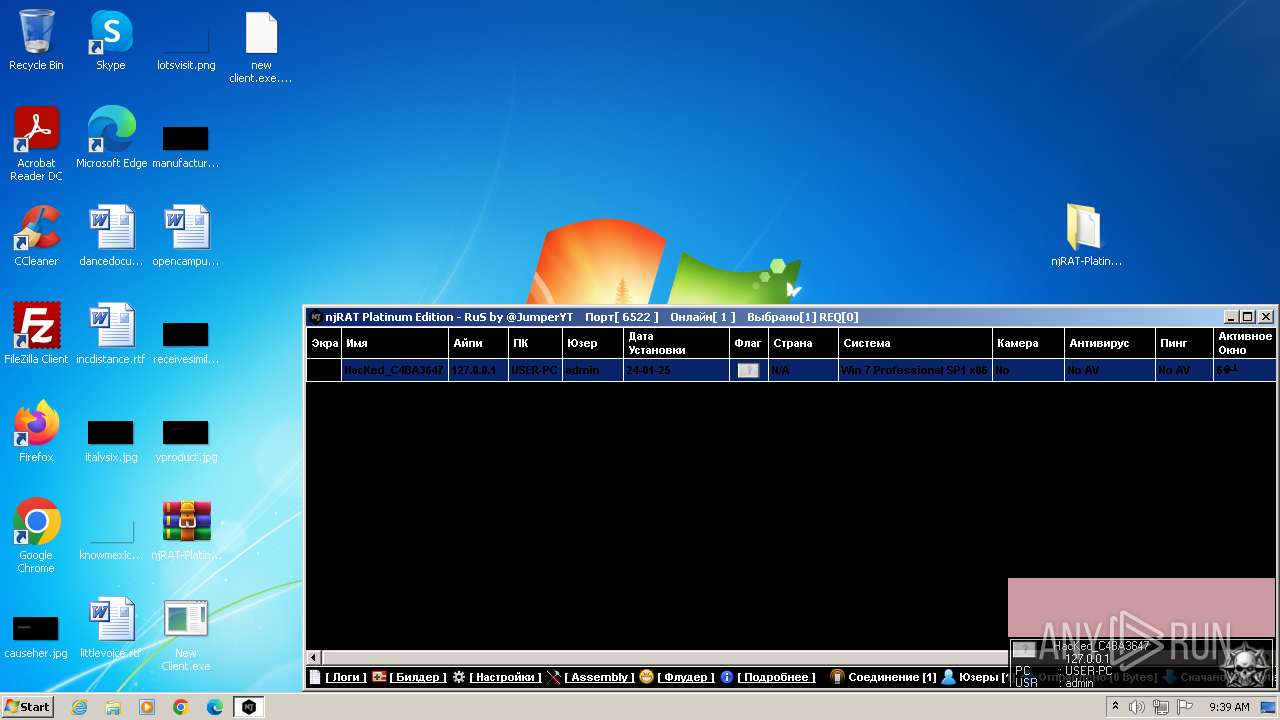
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 77B83A87828704868DF93A4C15C6FBB7 |
| SHA1: | 69955655C90B8FC5778FF165B2417933560F2772 |
| SHA256: | 2F2EED1731F3ADDBD1C192AB1C82631CABA60E6CBA3B32AAACDE4C1D75EFFB0B |
| SSDEEP: | 196608:6xdOKW7oB7TWxVg15Va4Htz+WrVHH2ZMuP06mKdJEb5ffsA6M8uF2dYK0:StWSTBM4Hp+WrVHH2ZMkPmKHE1fs5Mtf |
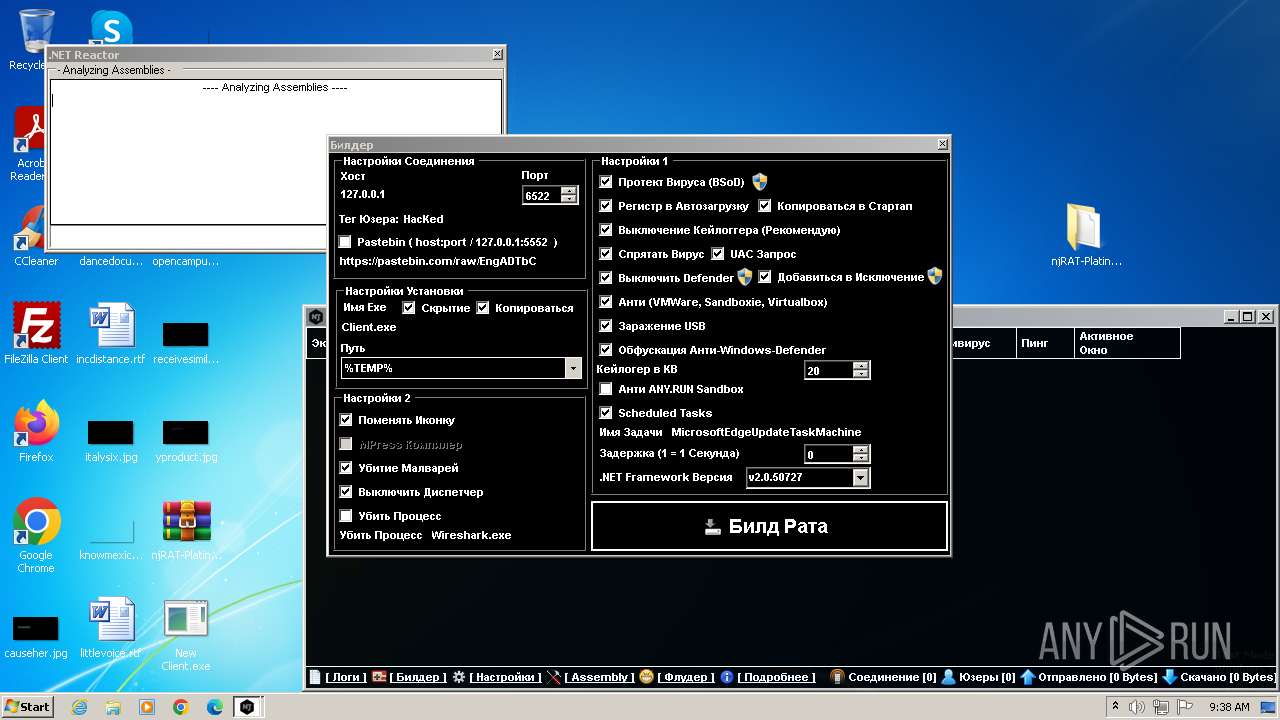
MALICIOUS
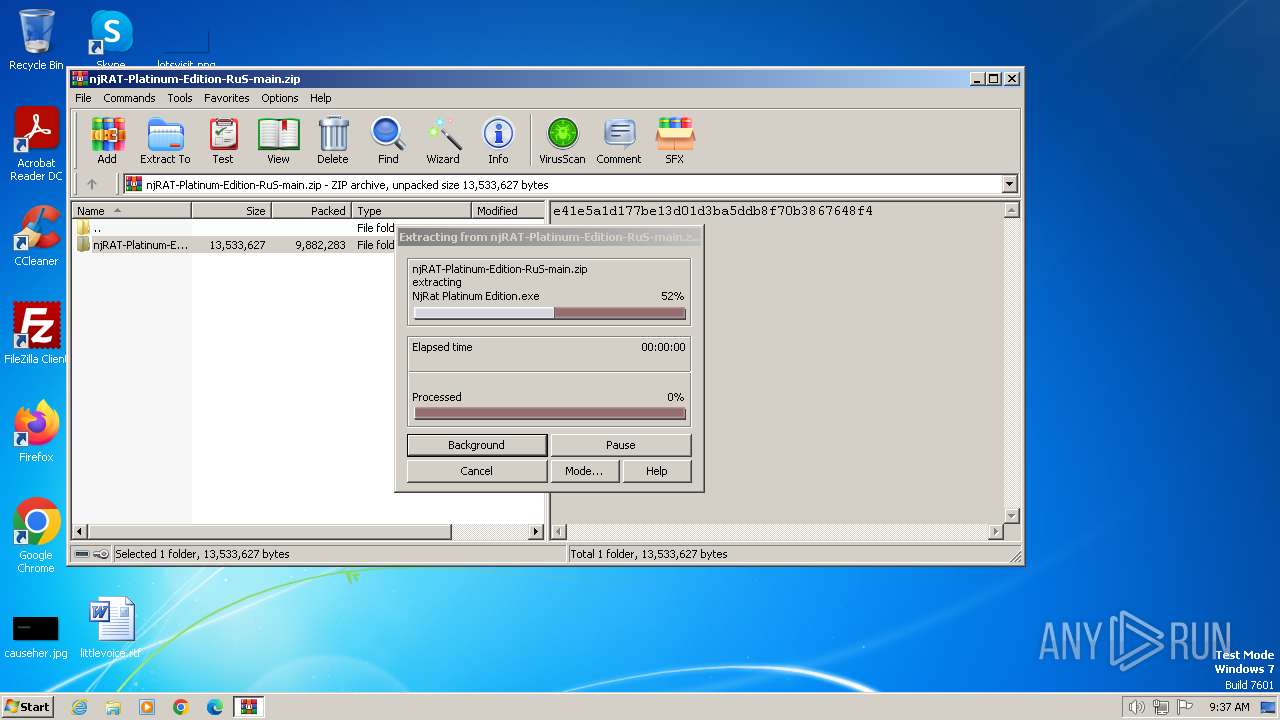
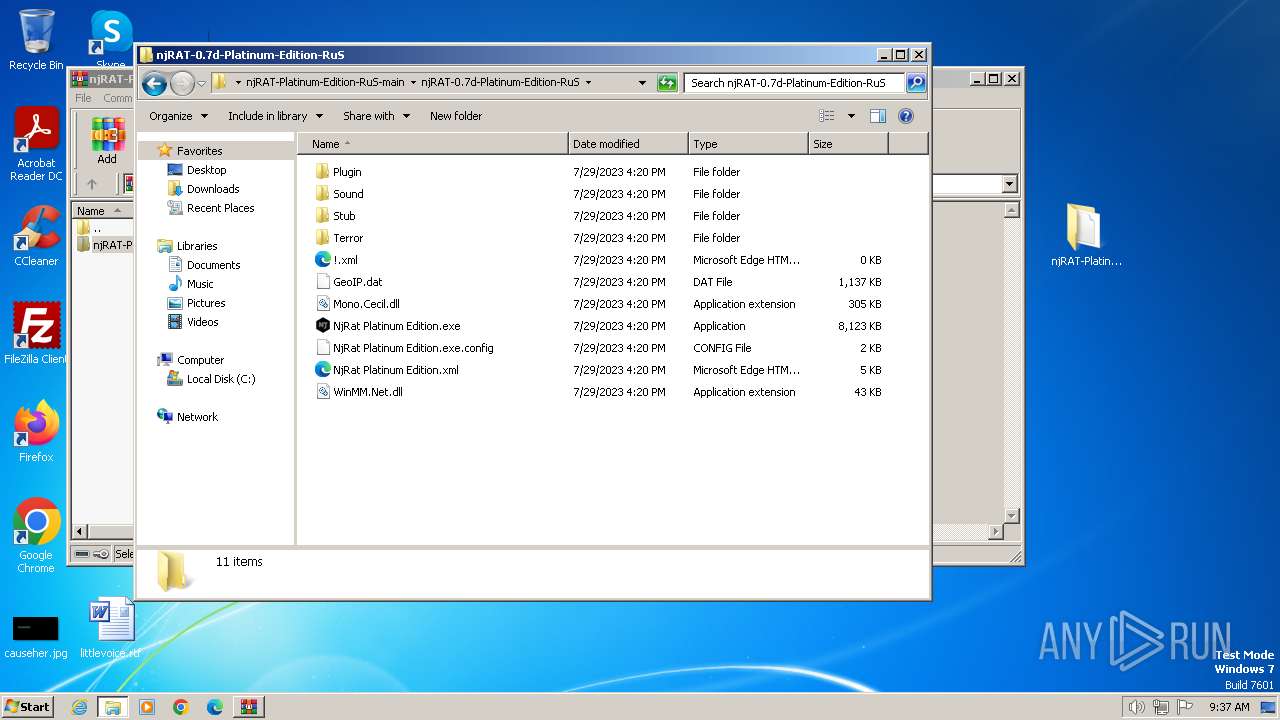
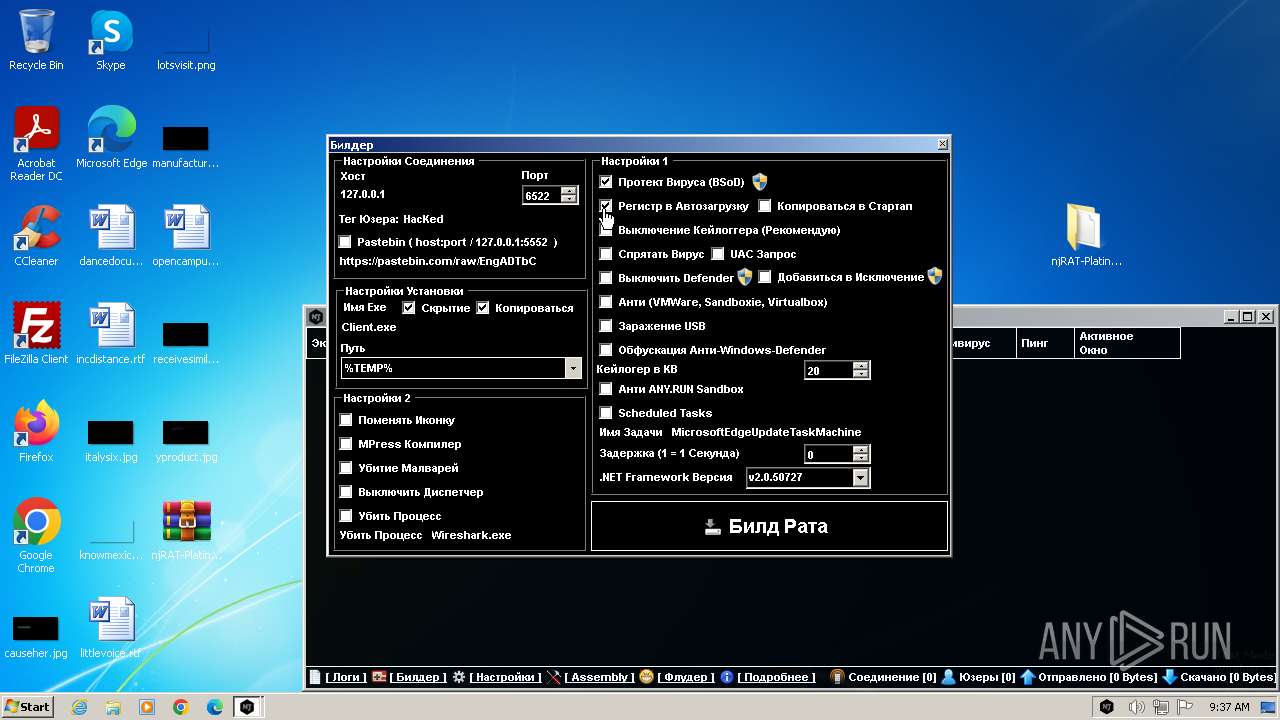
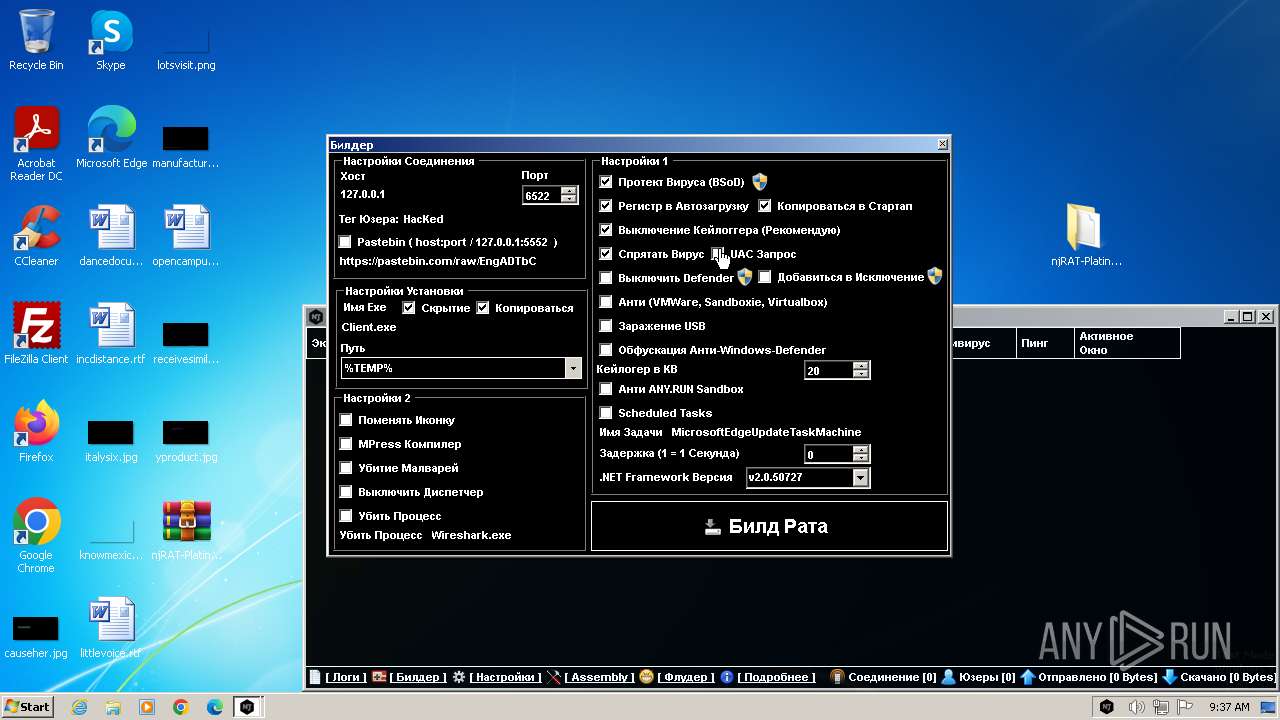
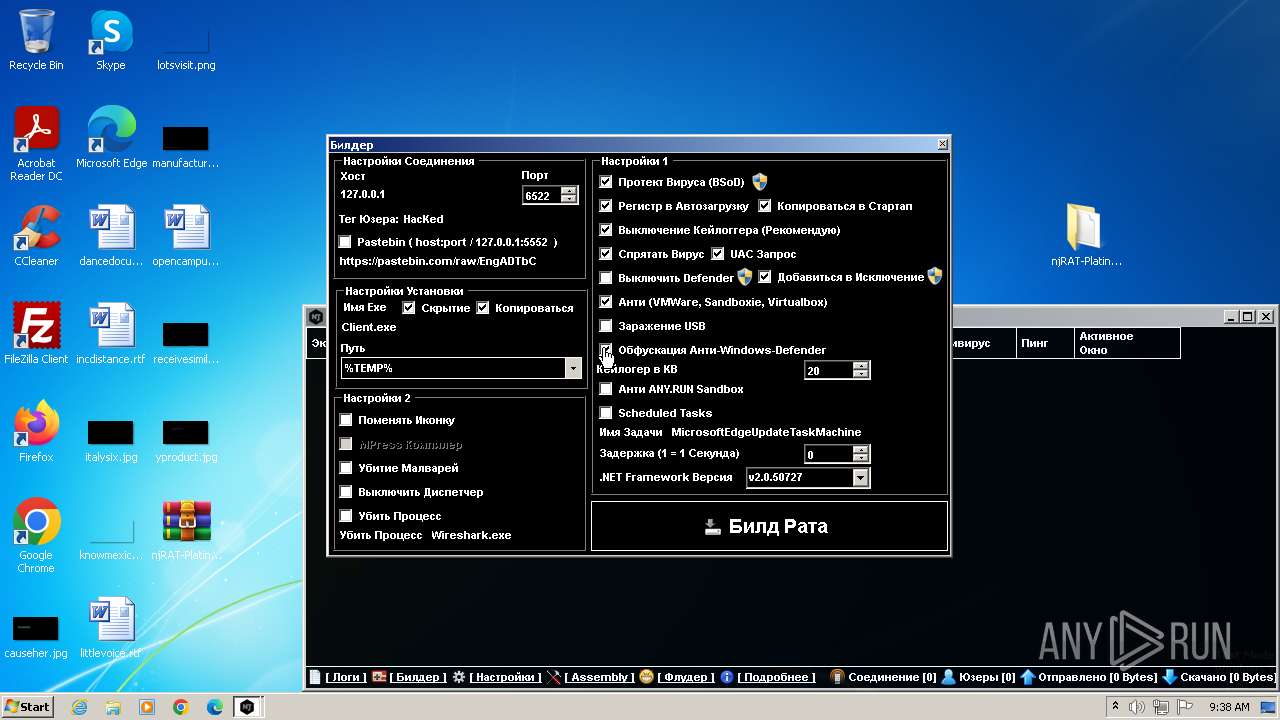
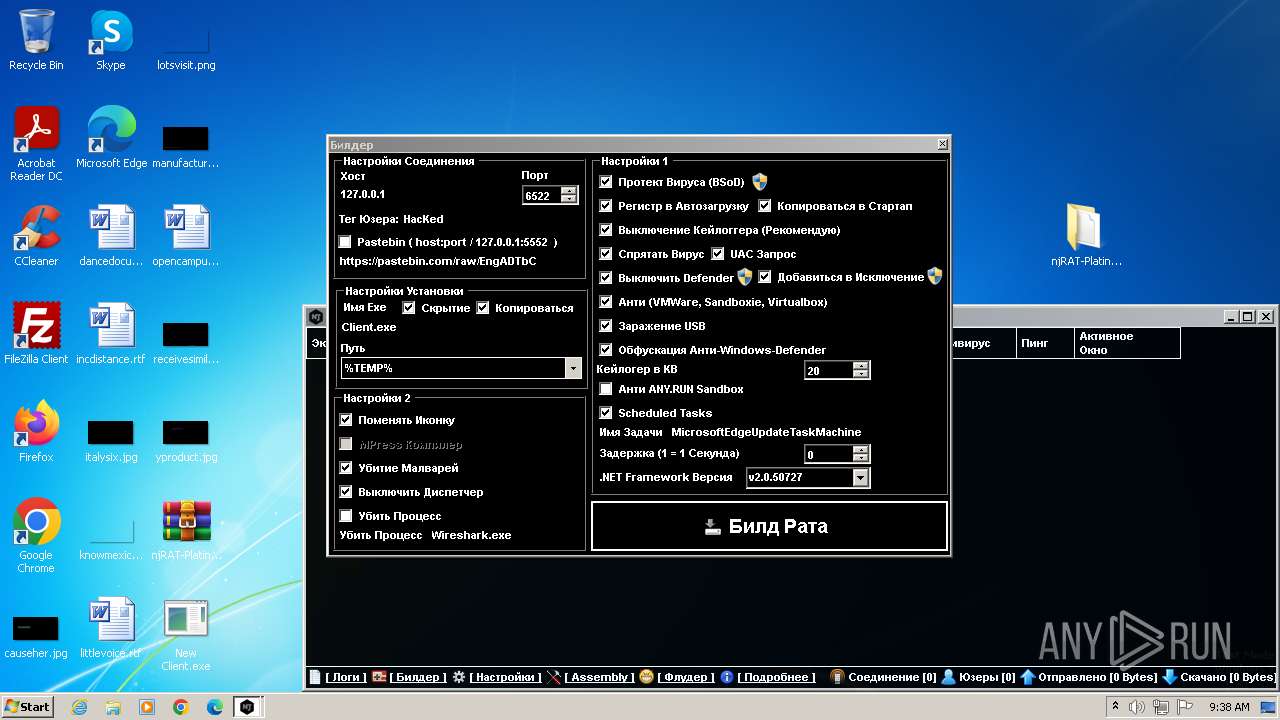
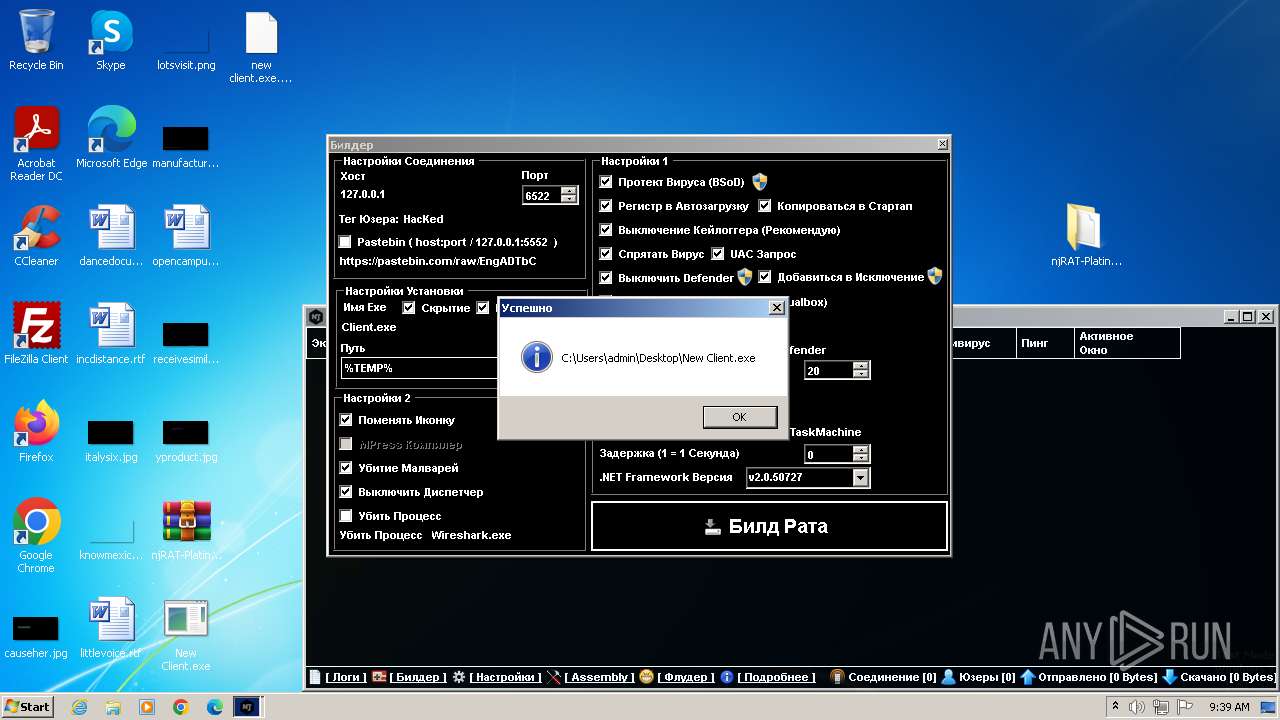
Drops the executable file immediately after the start
- ilasm.exe (PID: 2768)
- NjRat Platinum Edition.exe (PID: 696)
- csc.exe (PID: 3820)
- Client.exe (PID: 3780)
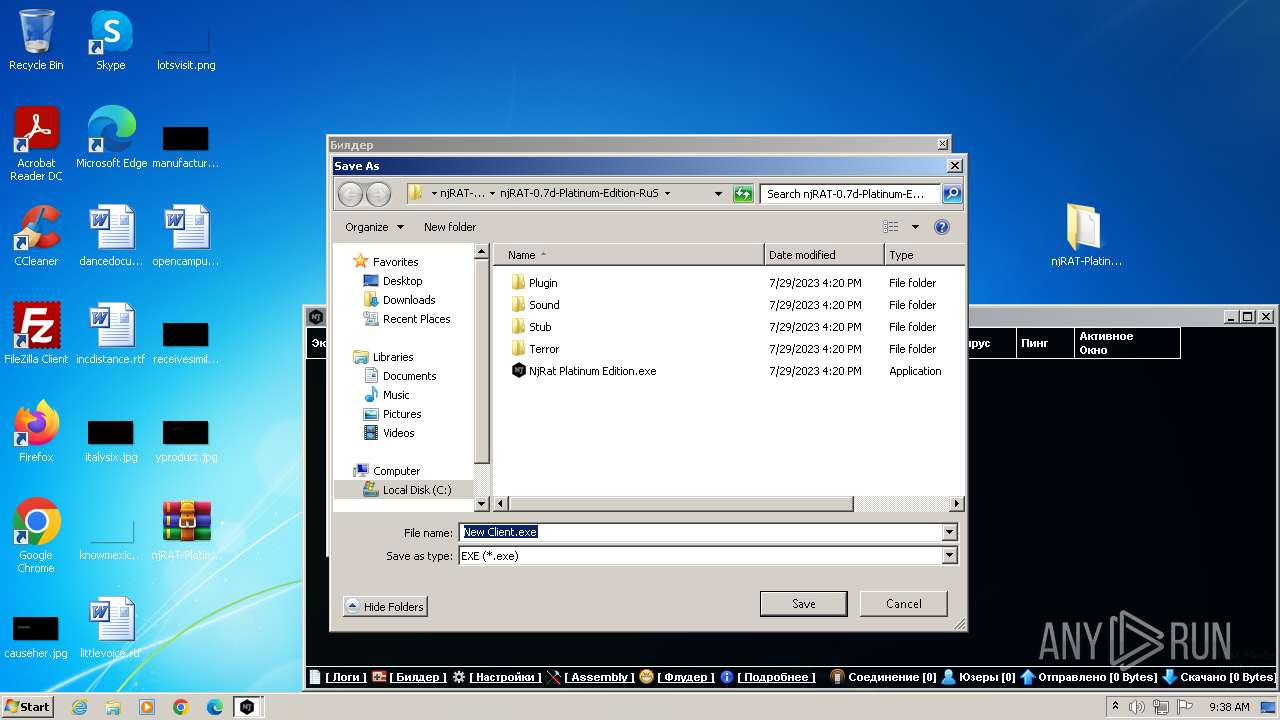
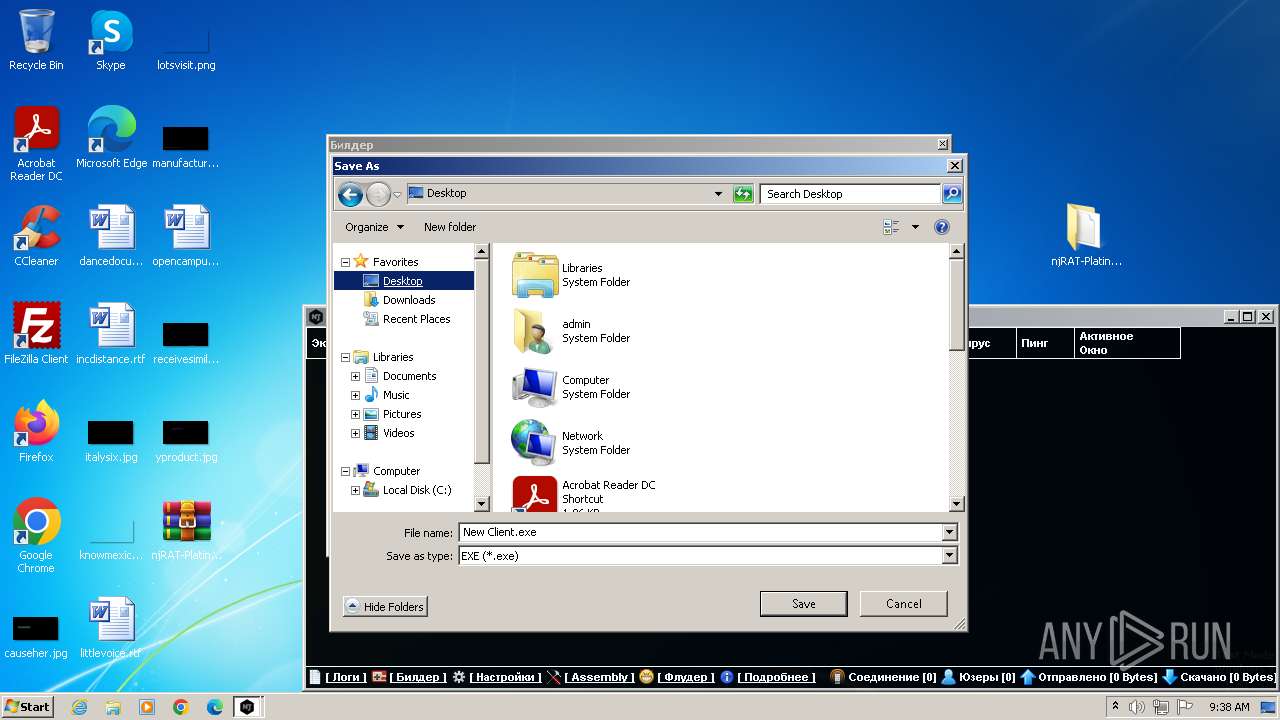
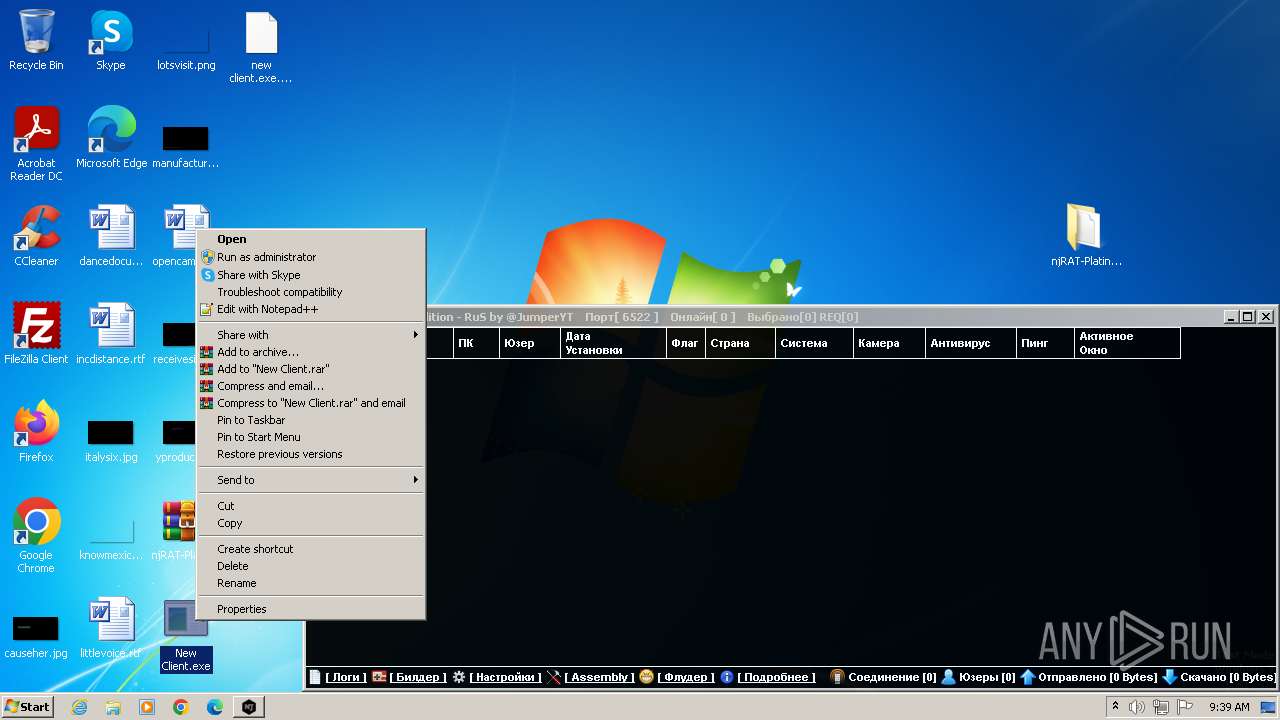
- New Client.exe (PID: 120)
Starts Visual C# compiler
- dotNET_Reactor.exe (PID: 3596)
Create files in the Startup directory
- Client.exe (PID: 3780)
Changes the autorun value in the registry
- Client.exe (PID: 3780)
SUSPICIOUS
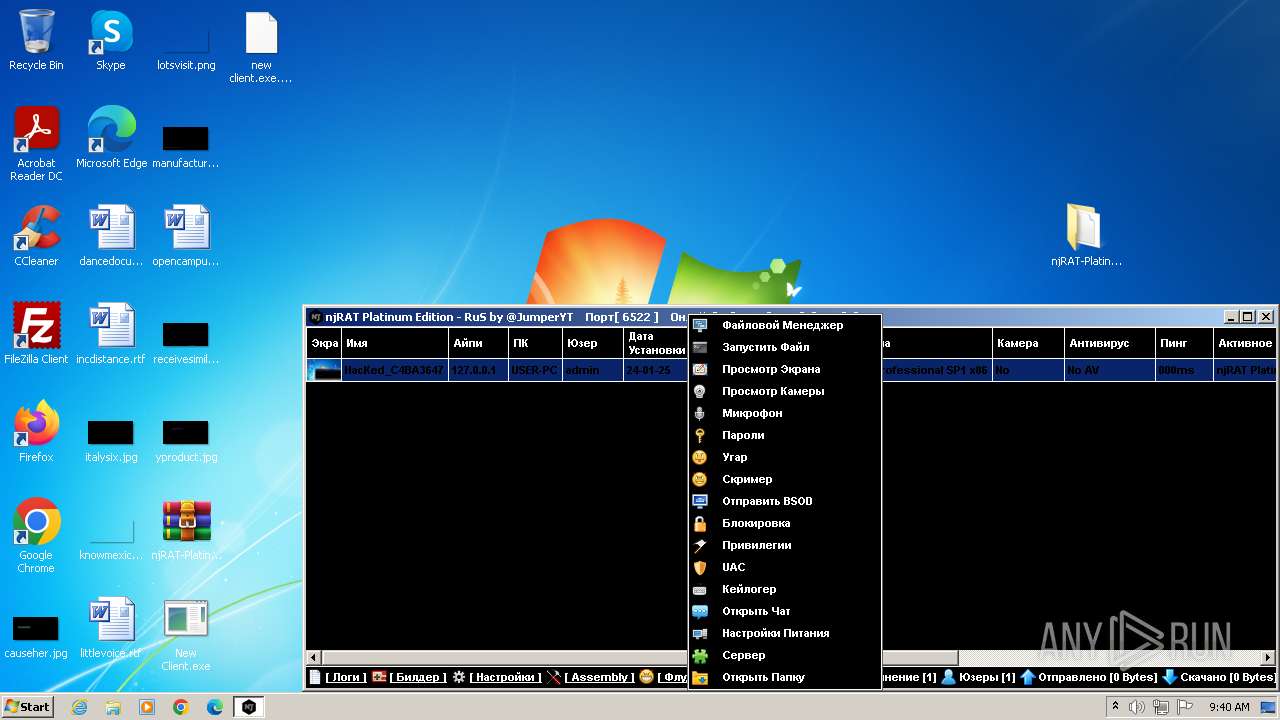
Reads the Internet Settings
- NjRat Platinum Edition.exe (PID: 696)
- dotNET_Reactor.exe (PID: 3596)
- New Client.exe (PID: 120)
Executable content was dropped or overwritten
- ilasm.exe (PID: 2768)
- NjRat Platinum Edition.exe (PID: 696)
- New Client.exe (PID: 120)
- csc.exe (PID: 3820)
- Client.exe (PID: 3780)
Starts CMD.EXE for commands execution
- NjRat Platinum Edition.exe (PID: 696)
- New Client.exe (PID: 120)
Uses .NET C# to load dll
- dotNET_Reactor.exe (PID: 3596)
Uses TASKKILL.EXE to kill process
- New Client.exe (PID: 120)
- Client.exe (PID: 3780)
- Client.exe (PID: 2268)
- Client.exe (PID: 1924)
Checks Windows Trust Settings
- New Client.exe (PID: 120)
- Client.exe (PID: 3780)
- Client.exe (PID: 1924)
Reads security settings of Internet Explorer
- New Client.exe (PID: 120)
- Client.exe (PID: 3780)
- Client.exe (PID: 1924)
Reads settings of System Certificates
- New Client.exe (PID: 120)
Starts itself from another location
- New Client.exe (PID: 120)
The process executes via Task Scheduler
- Client.exe (PID: 1924)
- Client.exe (PID: 2268)
INFO
Reads the computer name
- NjRat Platinum Edition.exe (PID: 696)
- dotNET_Reactor.exe (PID: 3596)
- New Client.exe (PID: 120)
- Client.exe (PID: 3780)
- Client.exe (PID: 2268)
- Client.exe (PID: 1924)
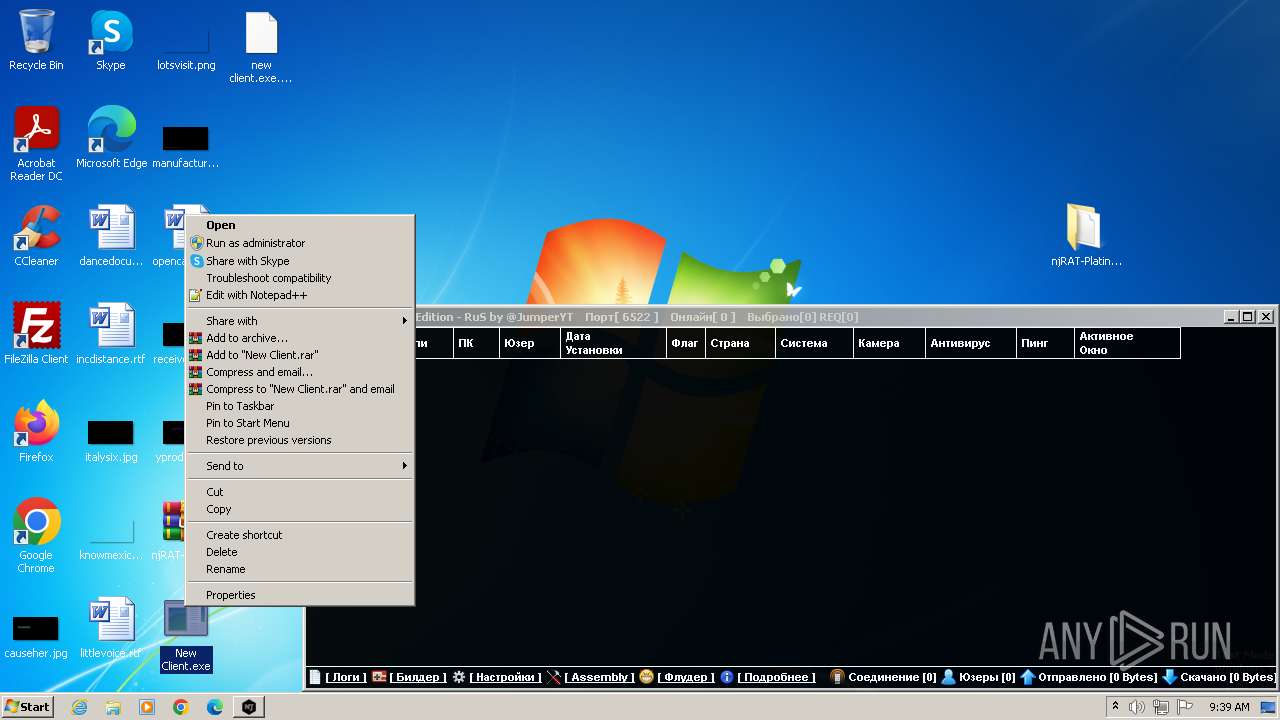
Manual execution by a user
- NjRat Platinum Edition.exe (PID: 696)
- New Client.exe (PID: 120)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2580)
Checks supported languages
- NjRat Platinum Edition.exe (PID: 696)
- ilasm.exe (PID: 2768)
- dotNET_Reactor.exe (PID: 3596)
- csc.exe (PID: 3820)
- New Client.exe (PID: 120)
- cvtres.exe (PID: 3788)
- Client.exe (PID: 3780)
- Client.exe (PID: 2268)
- Client.exe (PID: 1924)
Reads the machine GUID from the registry
- NjRat Platinum Edition.exe (PID: 696)
- dotNET_Reactor.exe (PID: 3596)
- New Client.exe (PID: 120)
- csc.exe (PID: 3820)
- cvtres.exe (PID: 3788)
- Client.exe (PID: 3780)
- Client.exe (PID: 1924)
- Client.exe (PID: 2268)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2580)
Reads Environment values
- NjRat Platinum Edition.exe (PID: 696)
- Client.exe (PID: 3780)
Create files in a temporary directory
- NjRat Platinum Edition.exe (PID: 696)
- dotNET_Reactor.exe (PID: 3596)
- csc.exe (PID: 3820)
- cvtres.exe (PID: 3788)
- New Client.exe (PID: 120)
Creates files or folders in the user directory
- Client.exe (PID: 3780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:07:29 08:20:54 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | njRAT-Platinum-Edition-RuS-main/ |
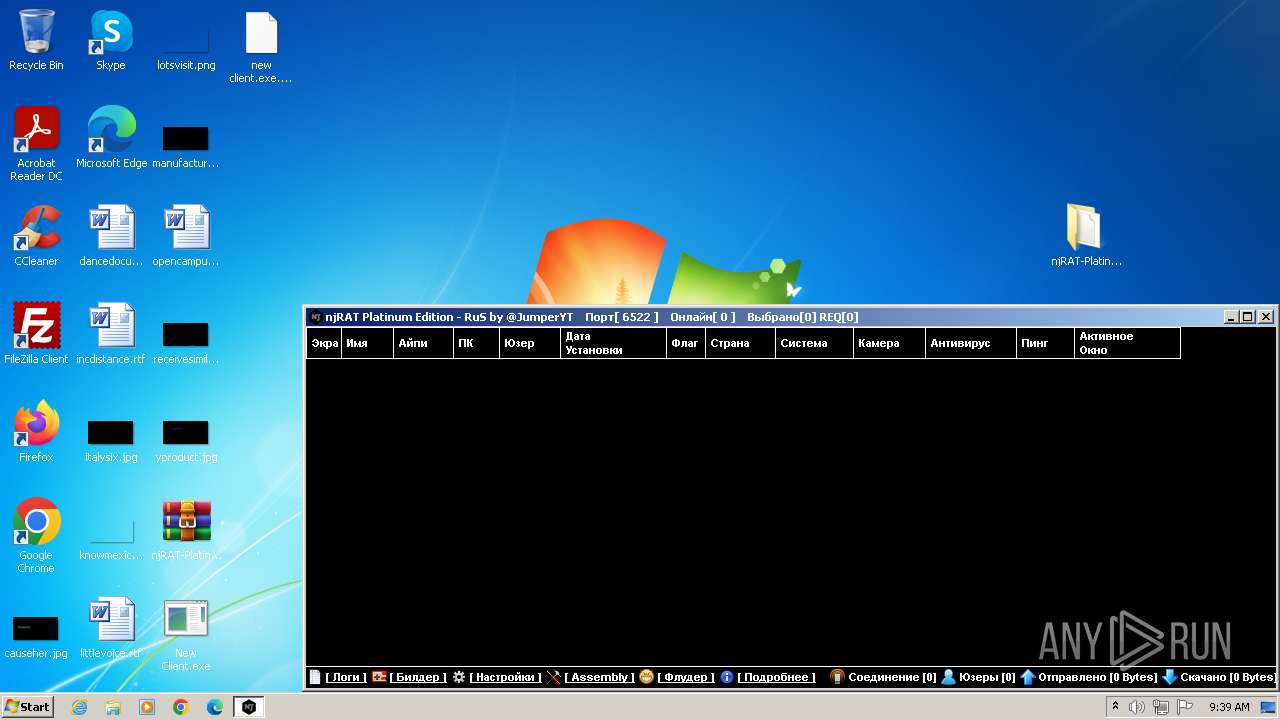
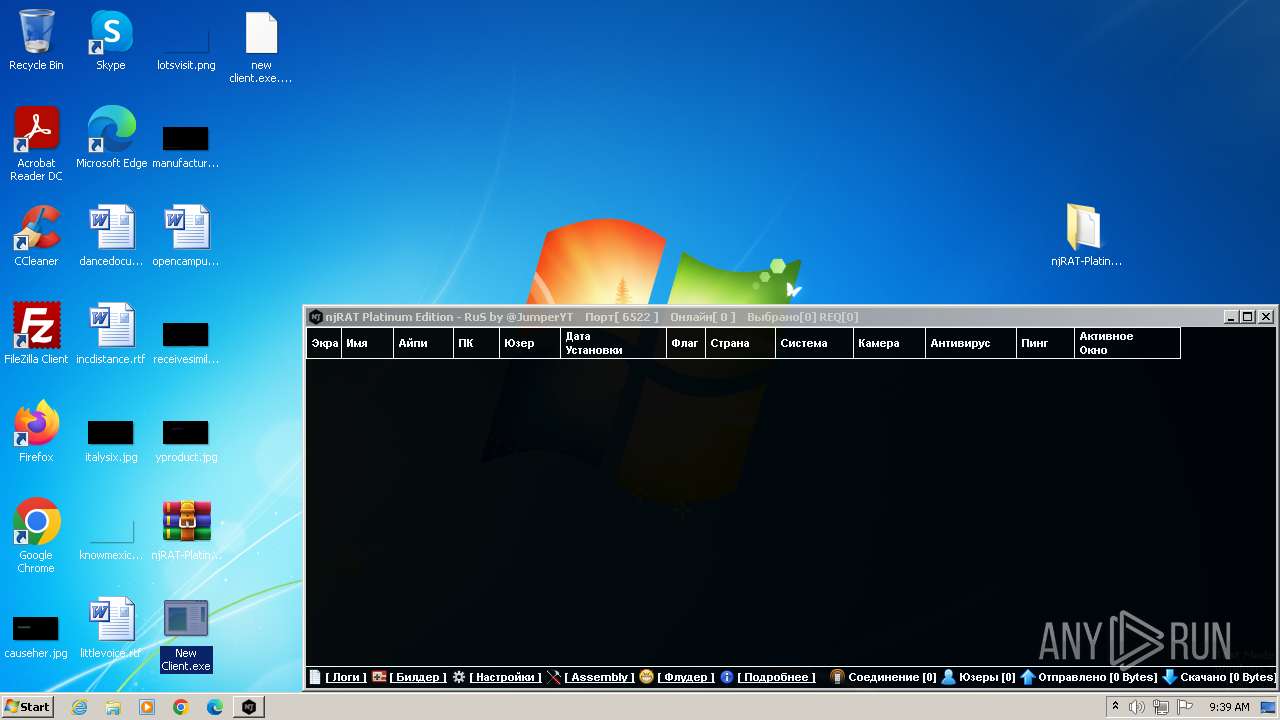
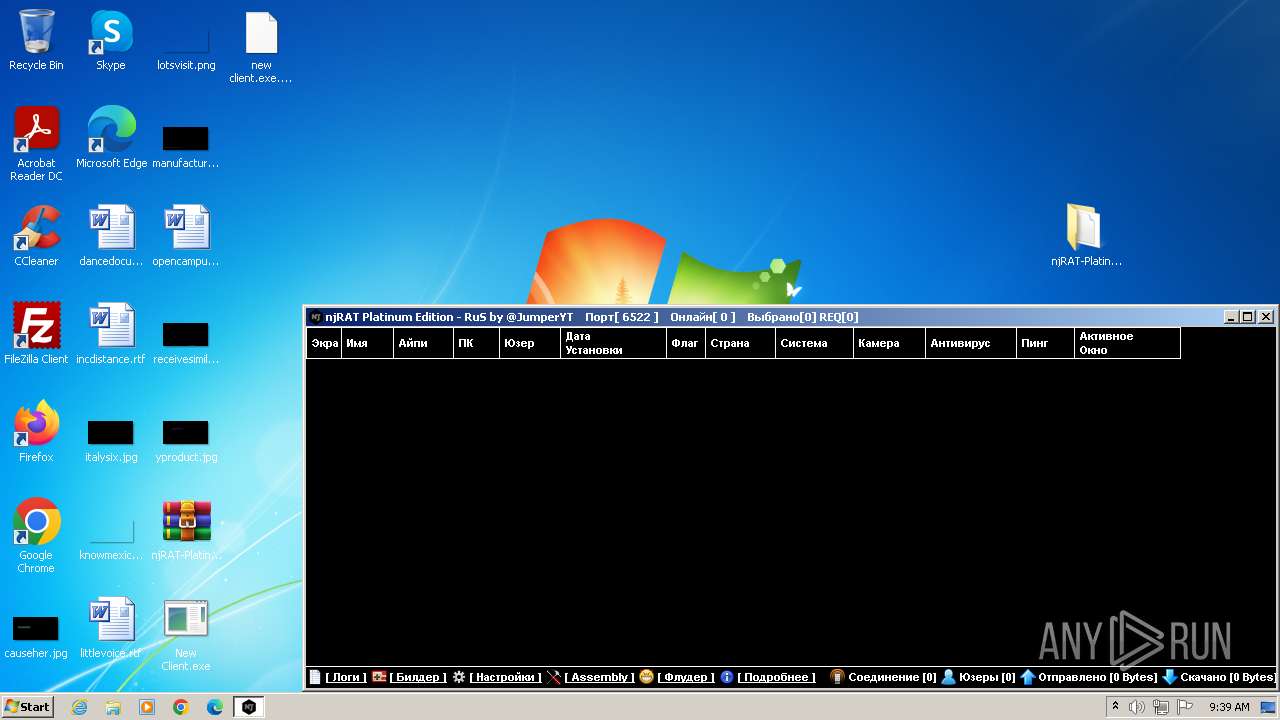
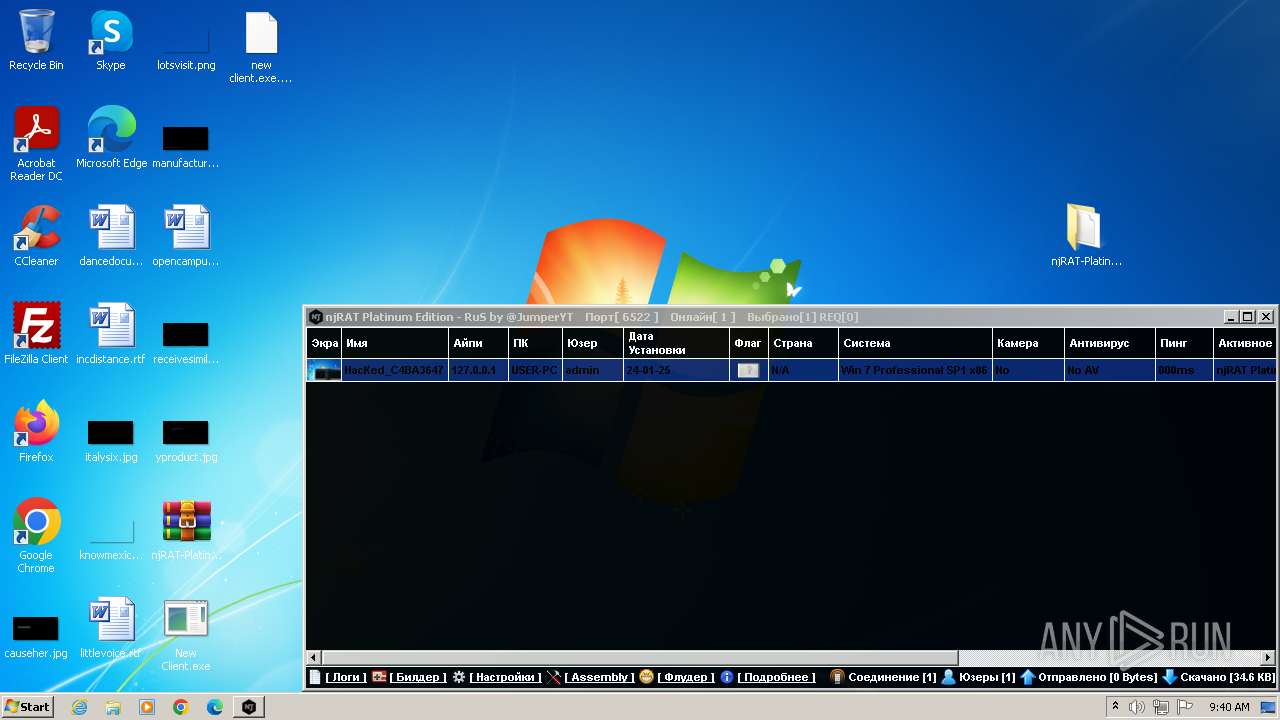
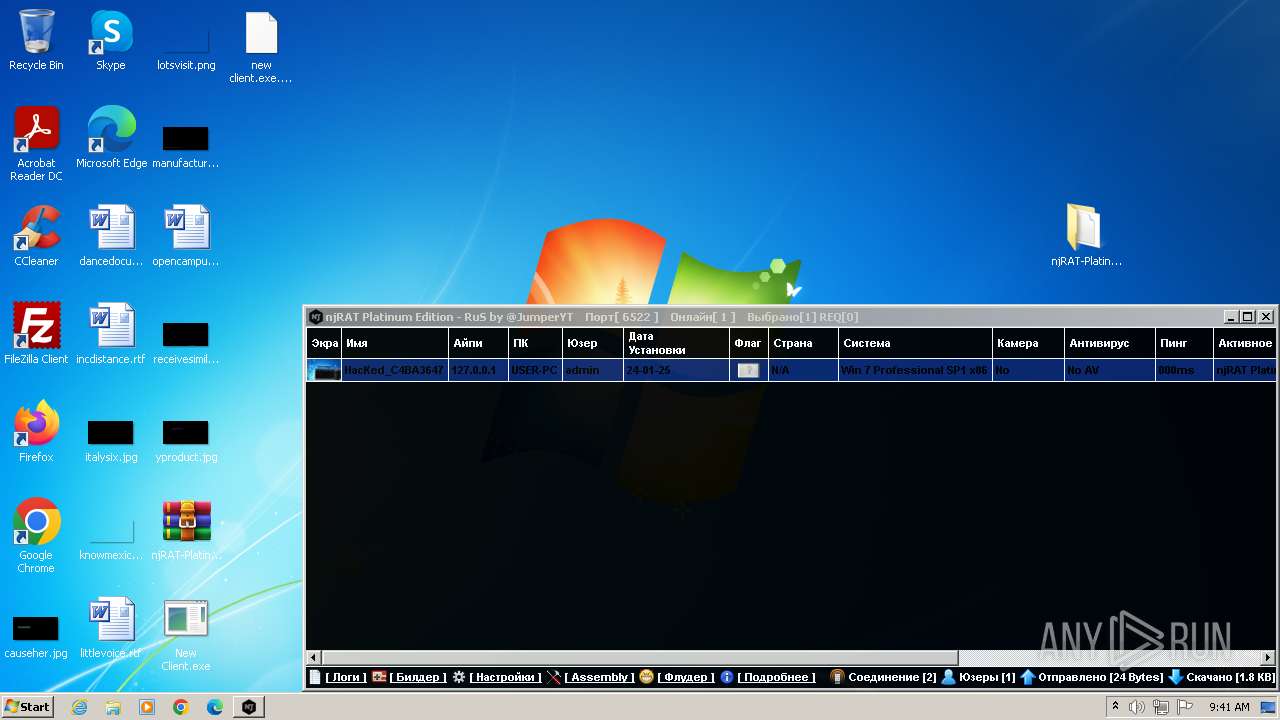
Total processes
85
Monitored processes
23
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Users\admin\Desktop\New Client.exe" | C:\Users\admin\Desktop\New Client.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 668 | "C:\Windows\System32\cmd.exe" /C choice /C Y /N /D Y /T 5 & Del "C:\Users\admin\Desktop\New Client.exe" | C:\Windows\System32\cmd.exe | — | New Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 696 | "C:\Users\admin\Desktop\njRAT-Platinum-Edition-RuS-main\njRAT-0.7d-Platinum-Edition-RuS\NjRat Platinum Edition.exe" | C:\Users\admin\Desktop\njRAT-Platinum-Edition-RuS-main\njRAT-0.7d-Platinum-Edition-RuS\NjRat Platinum Edition.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 0.7.0.6 Modules
| |||||||||||||||
| 992 | TASKKILL /F /IM cmd.exe | C:\Windows\System32\taskkill.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1380 | choice /C Y /N /D Y /T 5 | C:\Windows\System32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Offers the user a choice Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1584 | schtasks /delete /tn "MicrosoftEdgeUpdateTaskMachine" /f | C:\Windows\System32\schtasks.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1596 | TASKKILL /F /IM wscript.exe | C:\Windows\System32\taskkill.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1924 | C:\Users\admin\AppData\Local\Temp\Client.exe | C:\Users\admin\AppData\Local\Temp\Client.exe | — | taskeng.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1928 | TASKKILL /F /IM wscript.exe | C:\Windows\System32\taskkill.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2064 | TASKKILL /F /IM cmd.exe | C:\Windows\System32\taskkill.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
9 942
Read events
9 562
Write events
373
Delete events
7
Modification events
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
17
Suspicious files
7
Text files
15
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2580.40888\njRAT-Platinum-Edition-RuS-main\README.md | text | |
MD5:60CBF75EB517CBF66EDB545C066E8E11 | SHA256:37837A0FC2489133CF692DCF756379729E570E7A82602E683DAE77700D820142 | |||
| 2580 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2580.40888\njRAT-Platinum-Edition-RuS-main\njRAT-0.7d-Platinum-Edition-RuS\Mono.Cecil.dll | executable | |
MD5:851EC9D84343FBD089520D420348A902 | SHA256:CDADC26C09F869E21053EE1A0ACF3B2D11DF8EDD599FE9C377BD4D3CE1C9CDA9 | |||
| 2580 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2580.40888\njRAT-Platinum-Edition-RuS-main\njRAT-0.7d-Platinum-Edition-RuS\Plugin\ch.dll | executable | |
MD5:9000A99EE61E1C87FB811A77DF2E7B91 | SHA256:47F7C69C4CC4C0FEB6A6F1730D697CA95E24D5CEDD490C31D8E30CD1FA3B3859 | |||
| 2580 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2580.40888\njRAT-Platinum-Edition-RuS-main\njRAT-0.7d-Platinum-Edition-RuS\Plugin\cam.dll | executable | |
MD5:B0F1130C6DA19DBDB8556F910F168420 | SHA256:8AEEC9C0A673F2043BEC795D8430C280392913AC275FBAA3380524AD2148EAF8 | |||
| 2580 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2580.40888\njRAT-Platinum-Edition-RuS-main\njRAT-0.7d-Platinum-Edition-RuS\Plugin\mic.dll | executable | |
MD5:E9214452435D0E6F782B545EC0123331 | SHA256:7BAE6EC2613874287C20DDCBDF75E7CCA0AC65132485DFCFD632D0E5F97C1719 | |||
| 2580 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2580.40888\njRAT-Platinum-Edition-RuS-main\njRAT-0.7d-Platinum-Edition-RuS\NjRat Platinum Edition.exe | executable | |
MD5:9EA34BD96A5E4C536787107A532E1BF2 | SHA256:989114EAC06B024E0FD631D7D7B6E5435F86EA349CDB59C9B7C4407D1527AE38 | |||
| 2580 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2580.40888\njRAT-Platinum-Edition-RuS-main\njRAT-0.7d-Platinum-Edition-RuS\Plugin\plg.dll | executable | |
MD5:4643DB3DBF75200EFA97E80CFCF2DA1D | SHA256:BD5A390EFA75B9A47077FA1E7558713842563EC5822EB7F1DBF35AD9020012DC | |||
| 2580 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2580.40888\njRAT-Platinum-Edition-RuS-main\njRAT-0.7d-Platinum-Edition-RuS\Sound\Sound.wav | binary | |
MD5:11CA5B5FEBA113CCF66D6649B5B3CB40 | SHA256:9430FEC62EB1BFECB35F4A9CEB2DDD5CE6294751CDE85FD7169C8DEF811AF49E | |||
| 2580 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2580.40888\njRAT-Platinum-Edition-RuS-main\njRAT-0.7d-Platinum-Edition-RuS\NjRat Platinum Edition.exe.config | xml | |
MD5:DA15A1D8D770B57356DDD384342B3034 | SHA256:C45C9D1D30F940289498BE2AF978D74178A5C24CEB7755C2648F6C7A89353813 | |||
| 2580 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2580.40888\njRAT-Platinum-Edition-RuS-main\njRAT-0.7d-Platinum-Edition-RuS\Plugin\sc2.dll | executable | |
MD5:801A5D1E272399CA14FF7D6DA60315EF | SHA256:8E816523110BB2AB5E7611C0322CC4AA2D6C8D2A899B3A03731965ED1644549B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
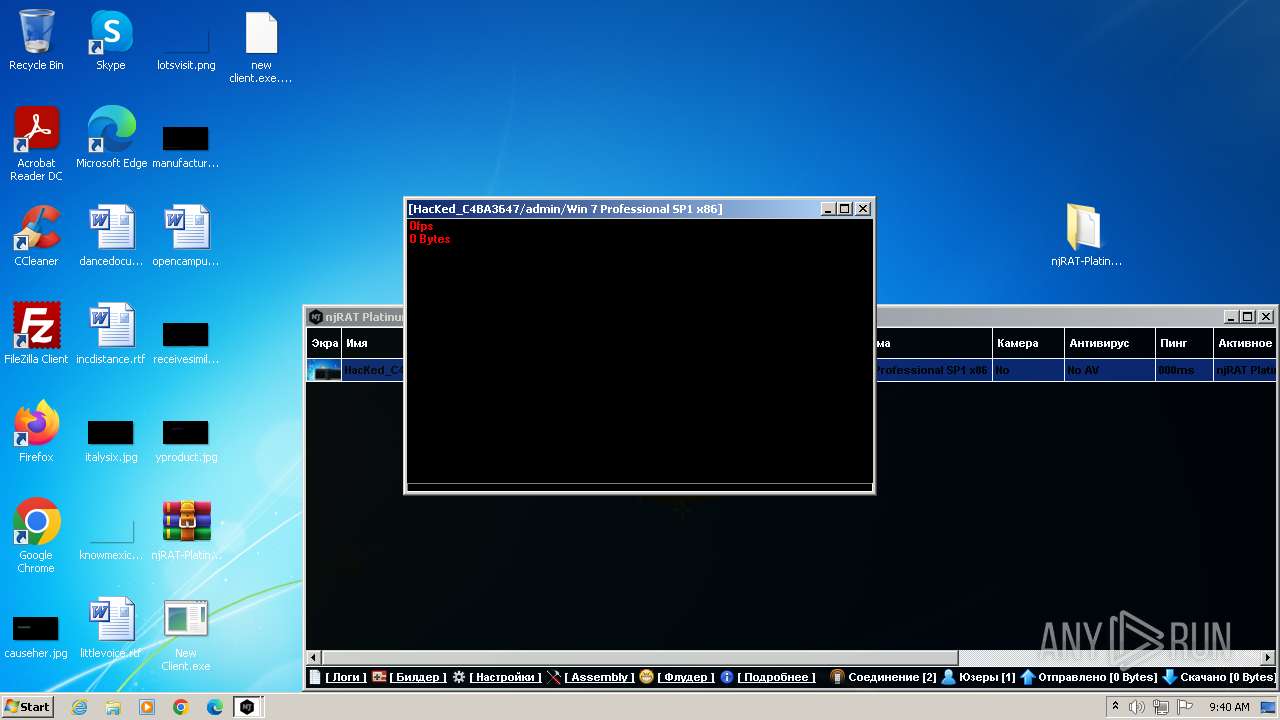
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |