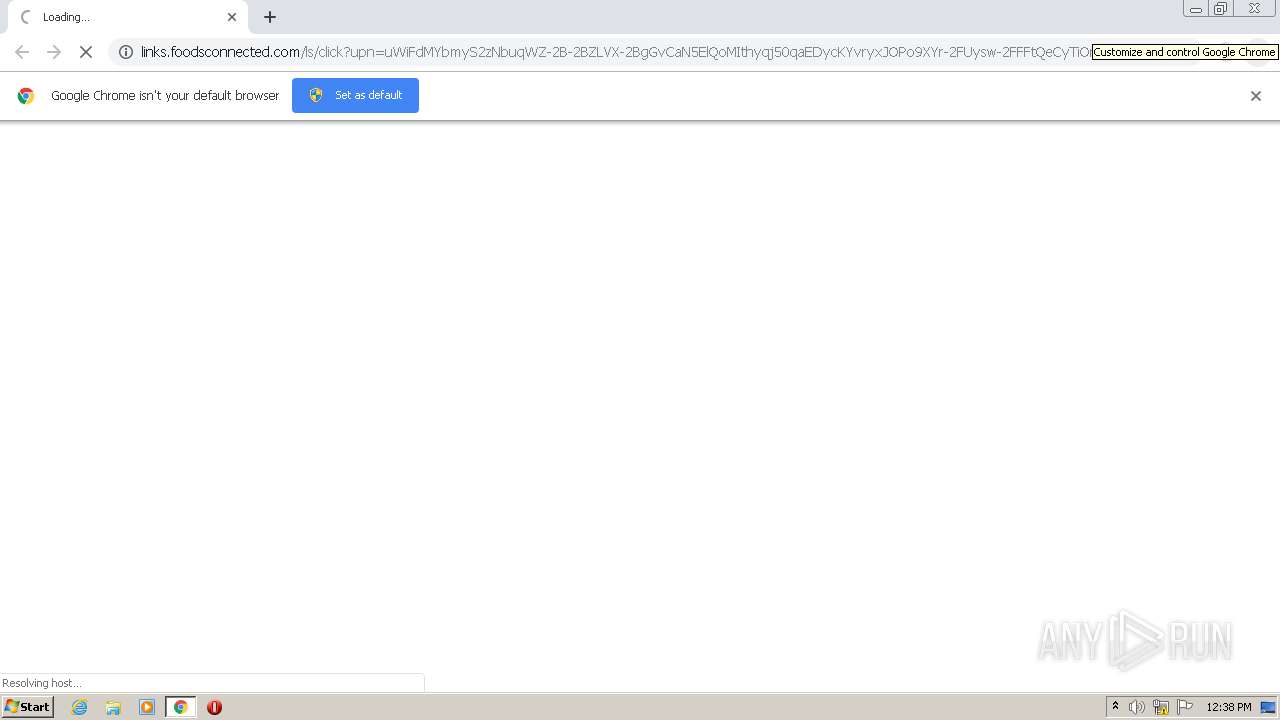
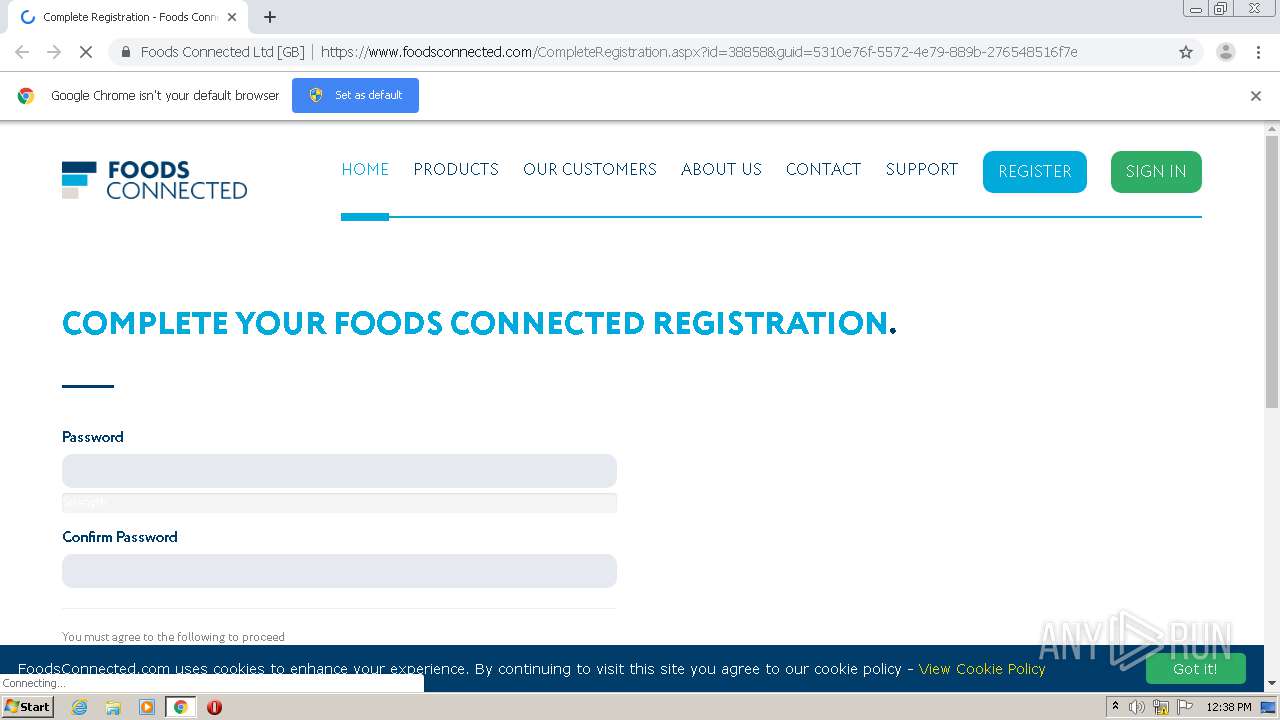
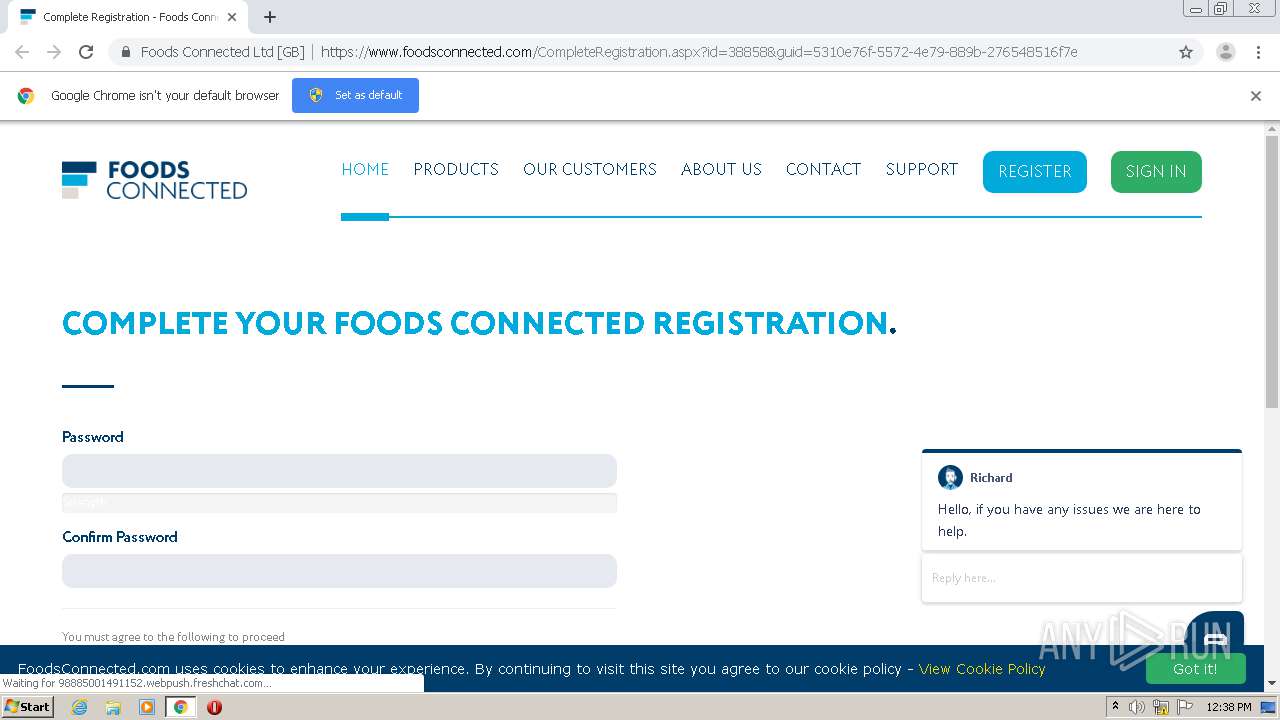
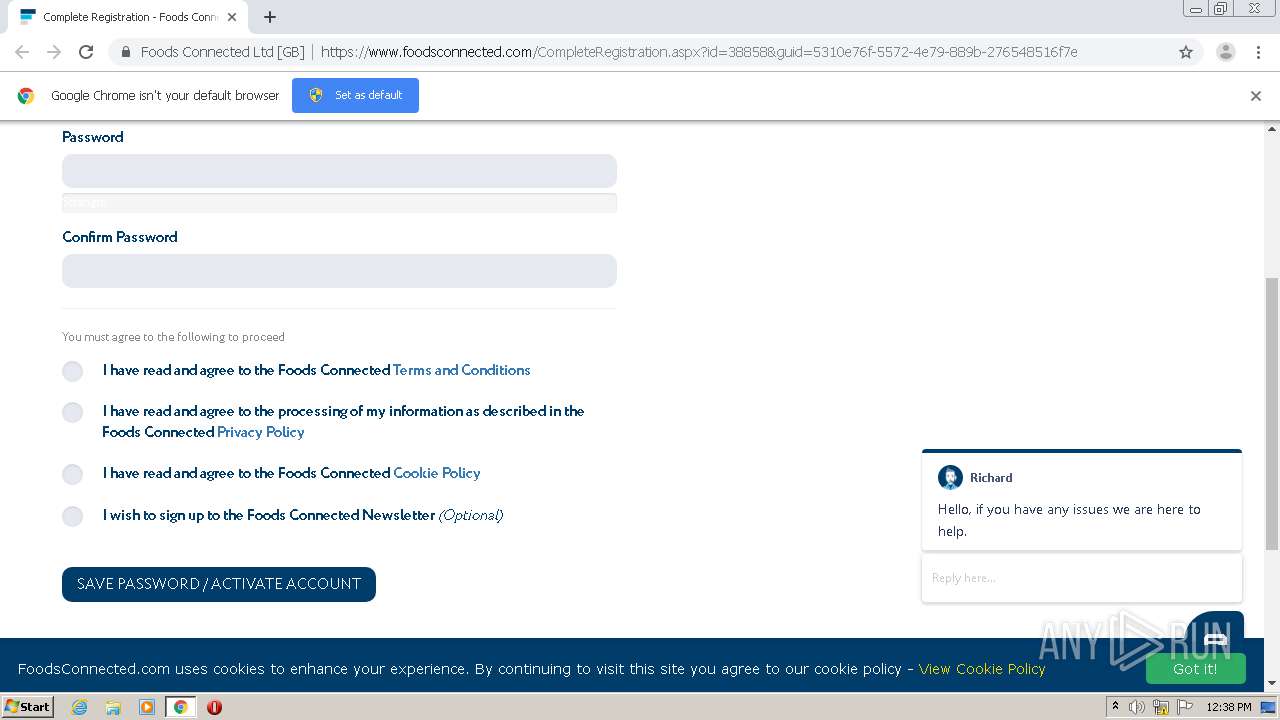
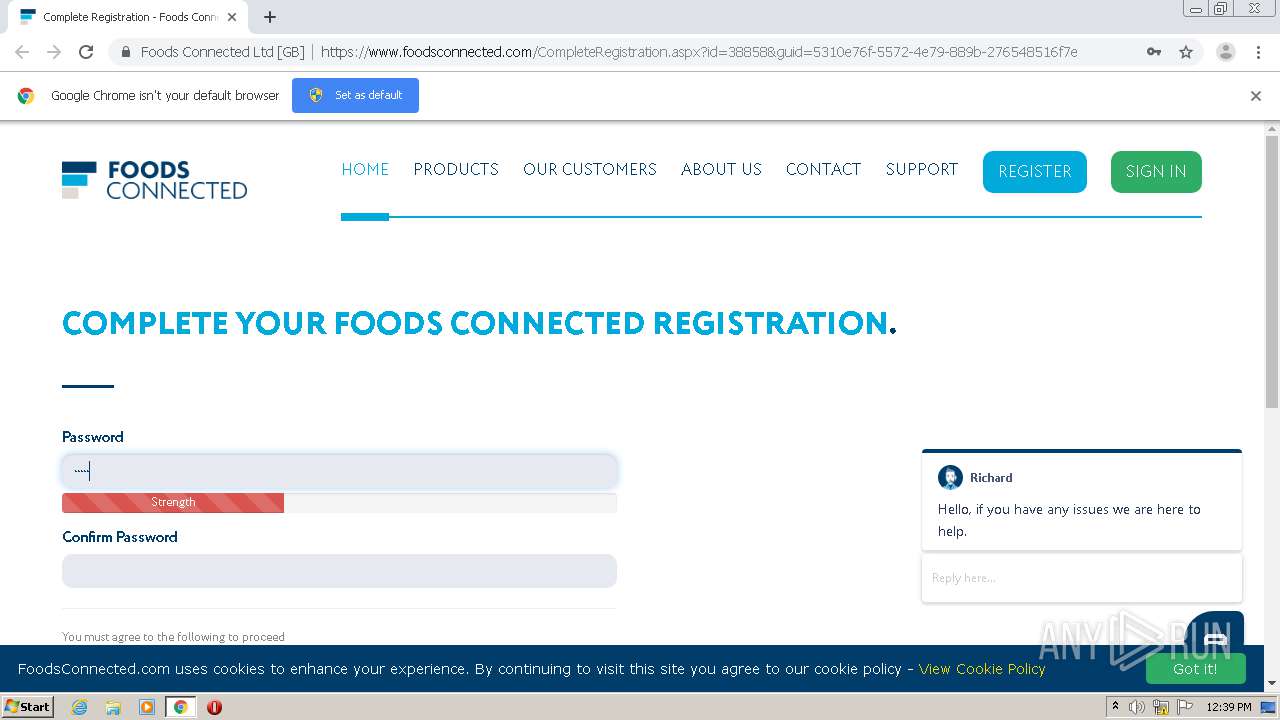
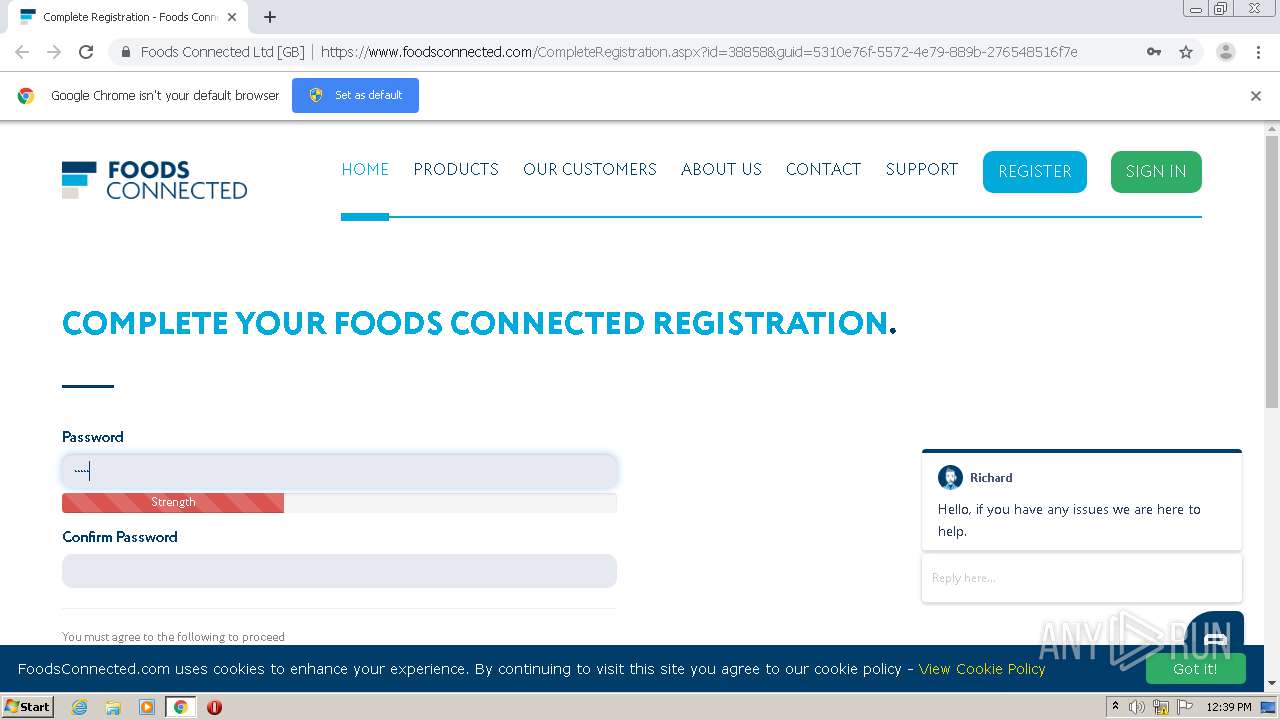
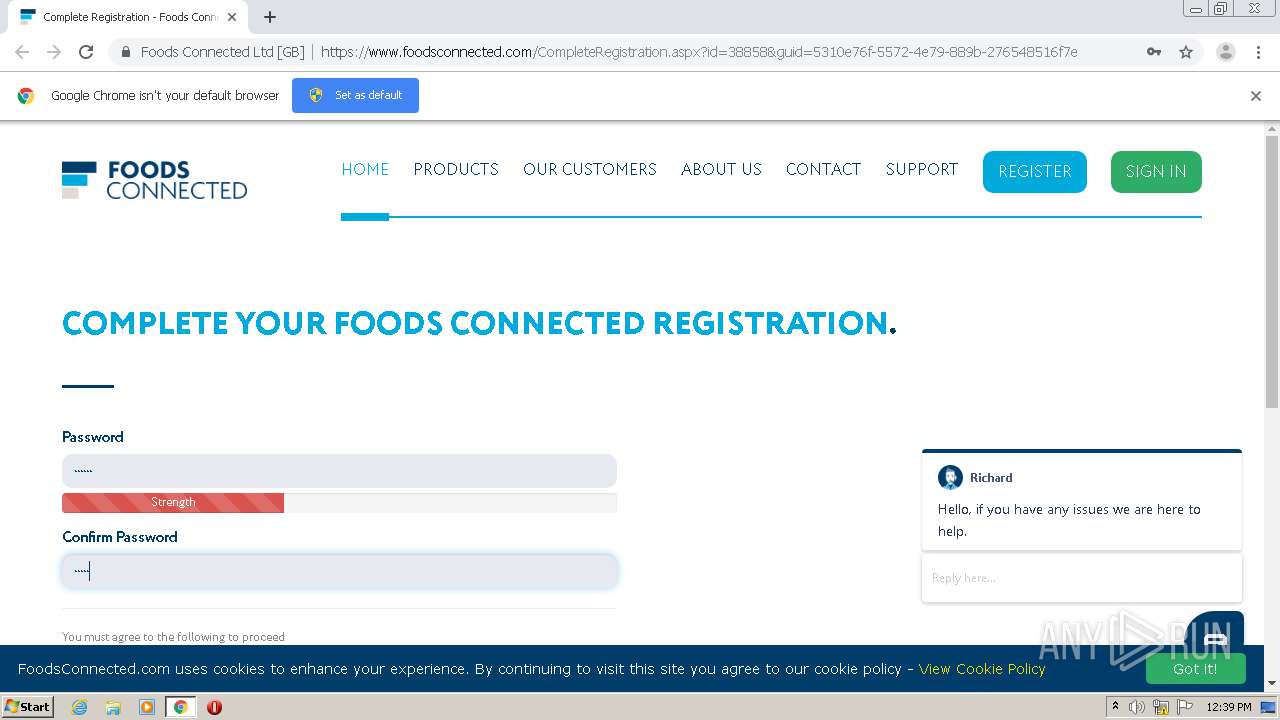
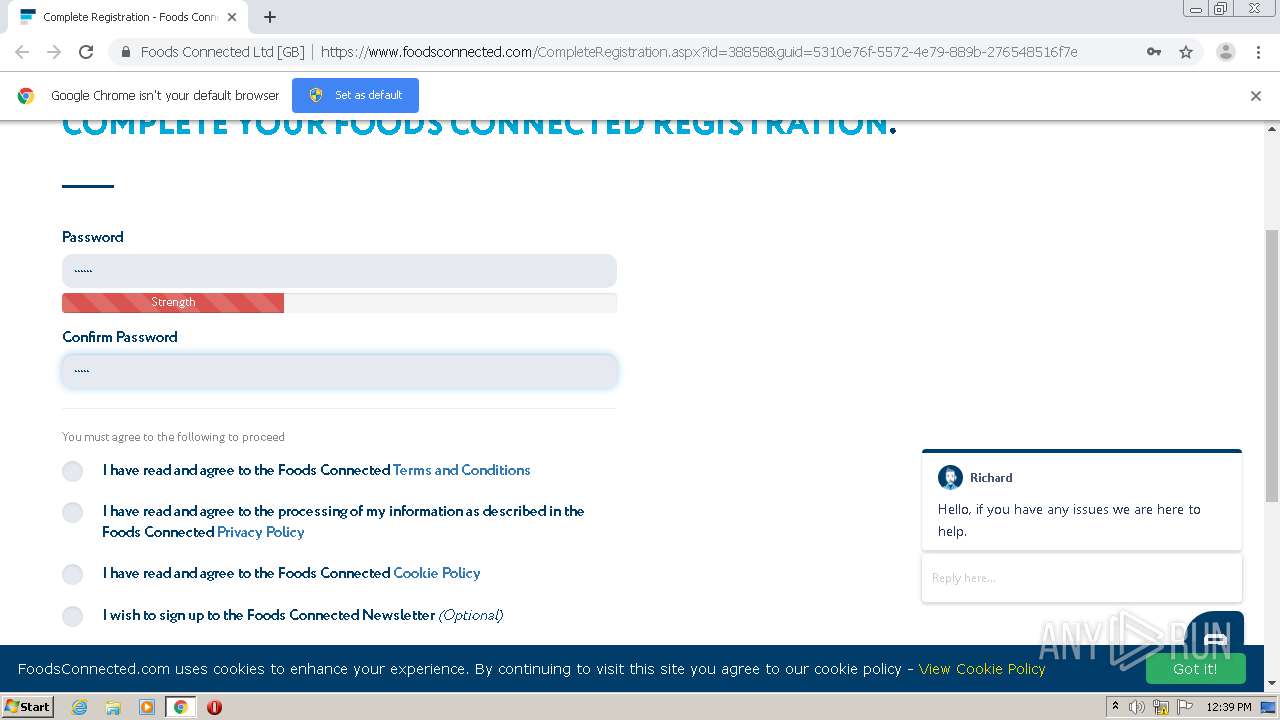
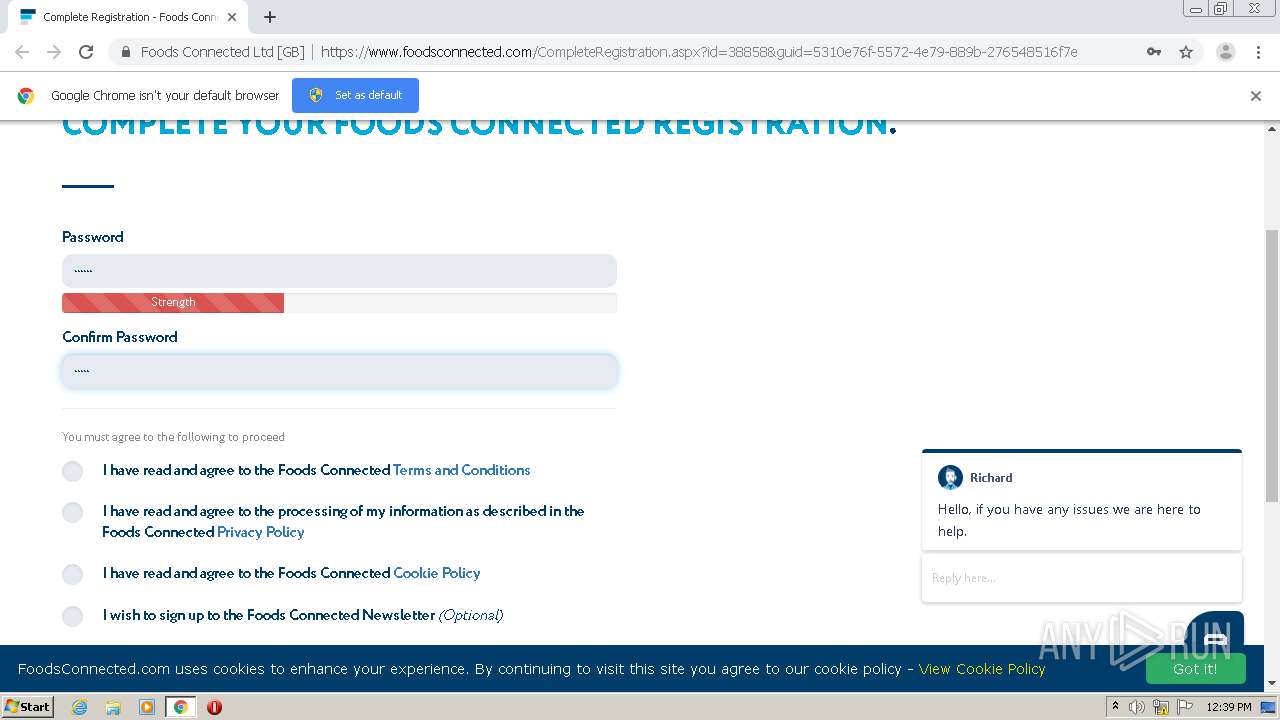
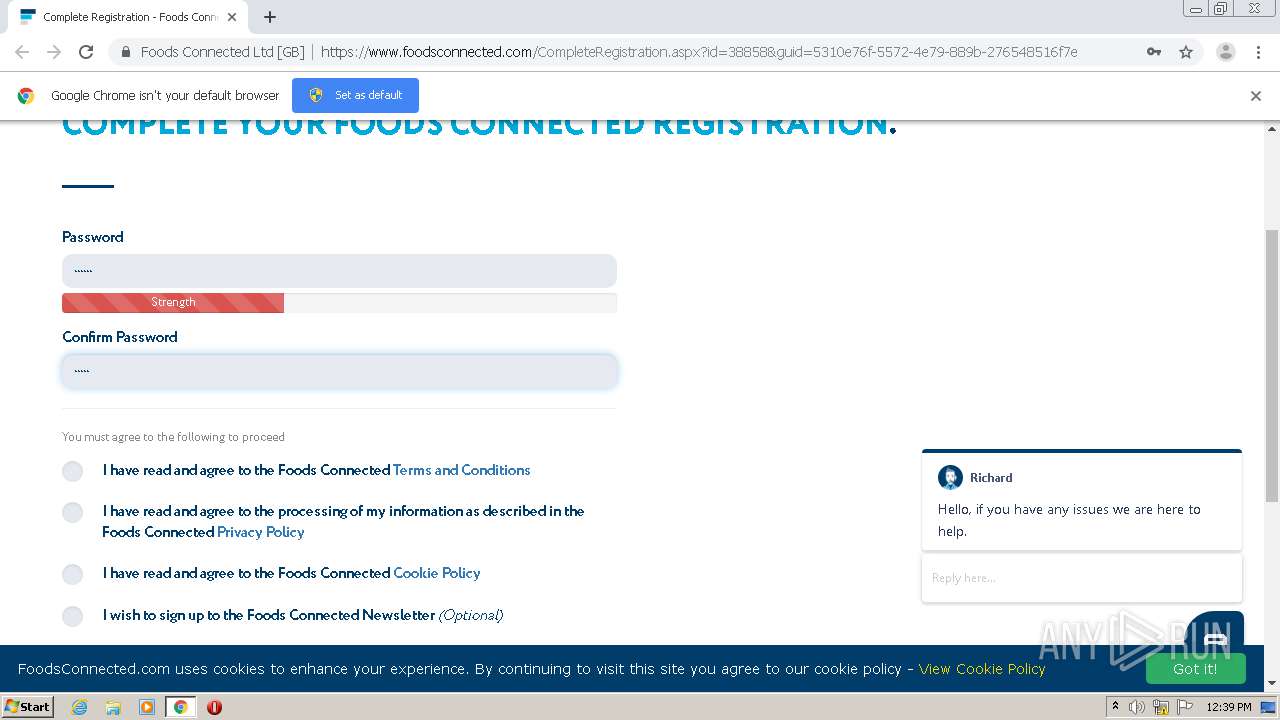
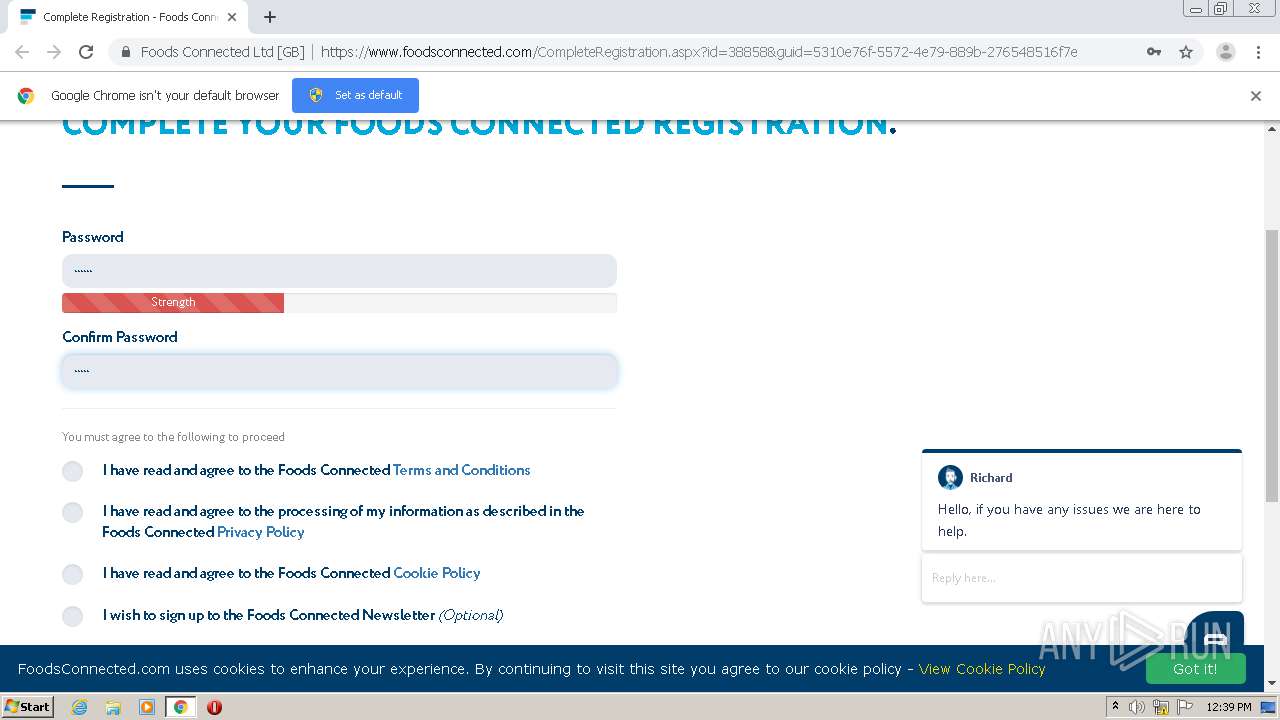
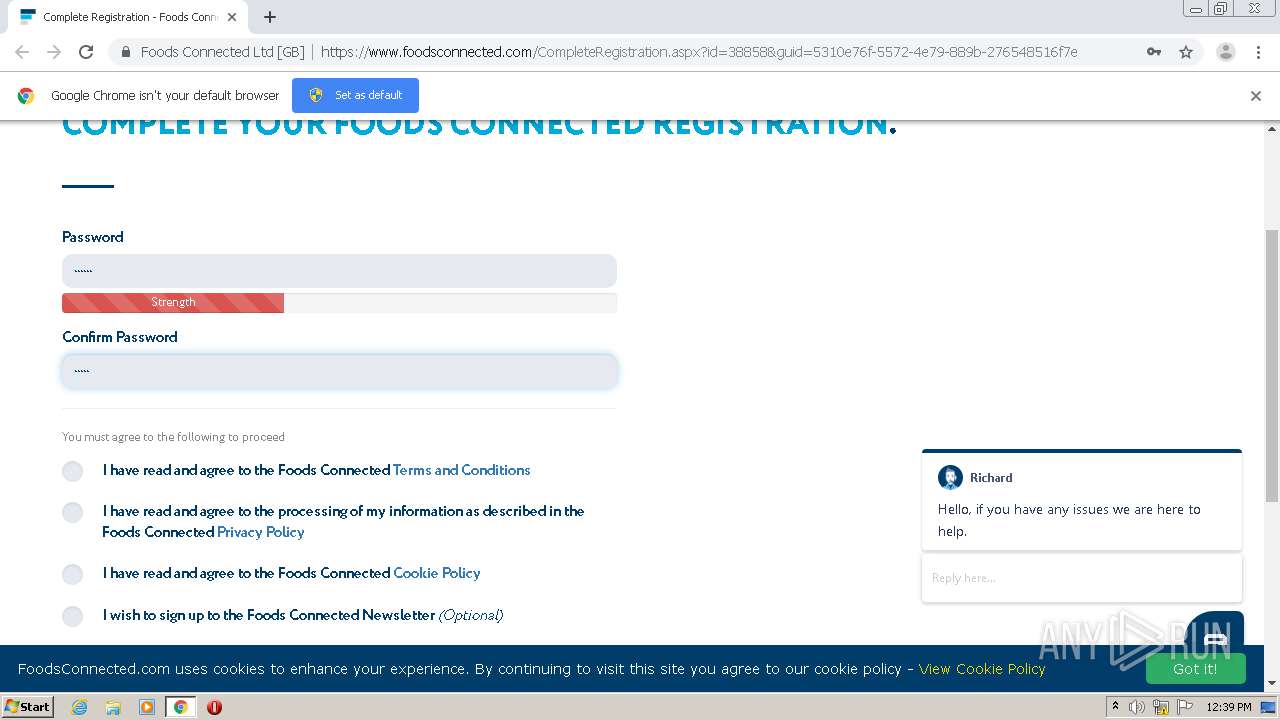
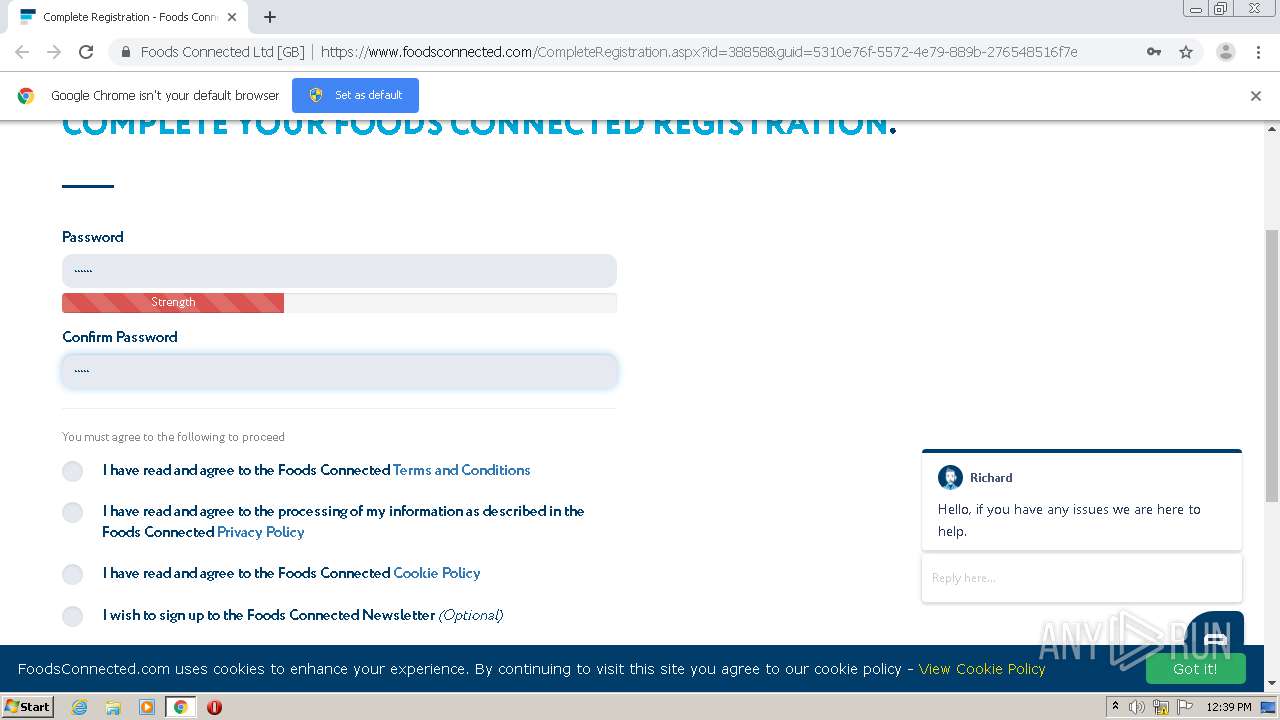
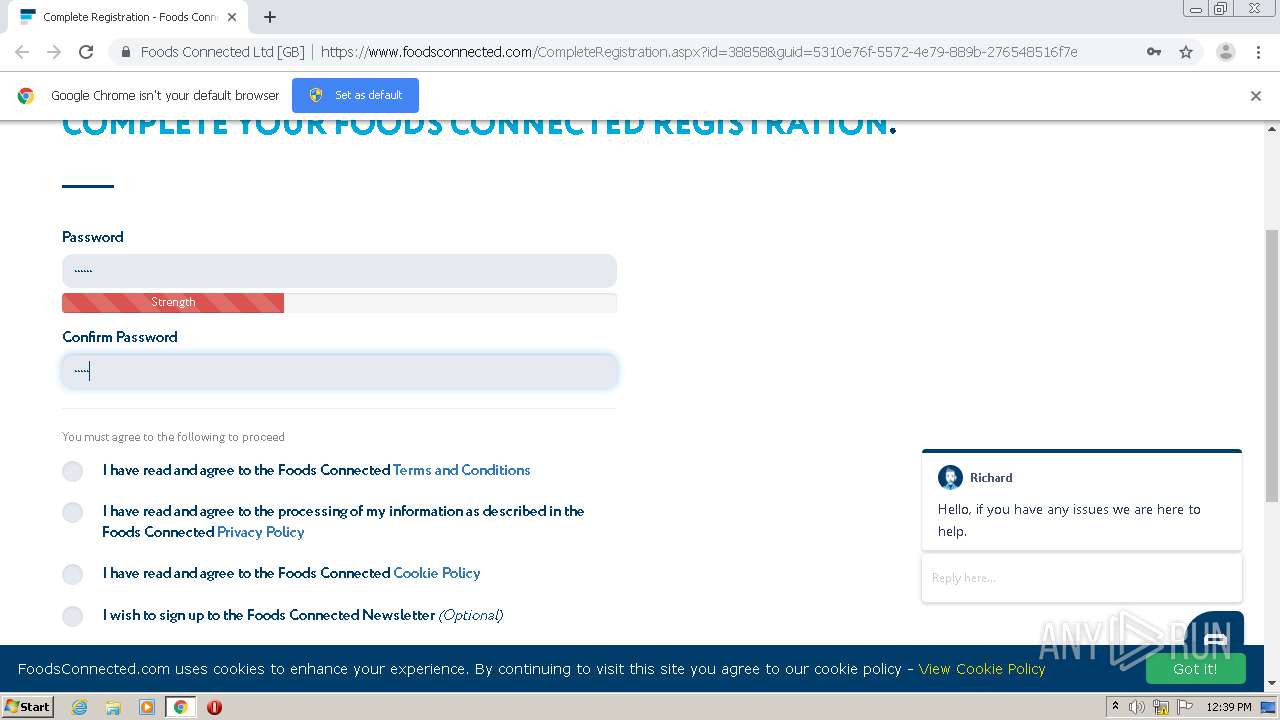
| URL: | http://links.foodsconnected.com/ls/click?upn=uWiFdMYbmyS2zNbuqWZ-2B-2BZLVX-2BgGvCaN5ElQoMIthyqj50qaEDycKYvryxJOPo9XYr-2FUysw-2FFFtQeCyTiOnr14BKVdyehO6TtR0-2F75O-2B7NY7SkPobTlih0U9msY8KhjZC7YnOi1buOsPtRwHl12gC3ILF9skC7ta2GuUNzr8DTw-3DGkqh_QuISWQjKKuMQibsDHimYNstabJjjD-2FX06IJ7IN2kni03PBwsj1Iw5zo8Y-2BBUoxJQ7K3QgibCTIrpKkkGRN-2FOJnCBIfJSBVtlD4AIdzQrS2yLX1l-2B8x0SwZ1cFDoyqnDRN-2BhMfNUT3e4jFMcGO1p43TLpPh2js34UICSwEERvEVLJPPsDVLogIdcU8q6GwyRry7I2eI6SWrXHqfB2vdeyxhbe4FYiaInjwqU3DaHQkr9K-2FBSDUMBRlW6cWslwh2Yf |
| Full analysis: | https://app.any.run/tasks/c121f976-1ffc-4cf9-97d0-67ccc81fd57b |
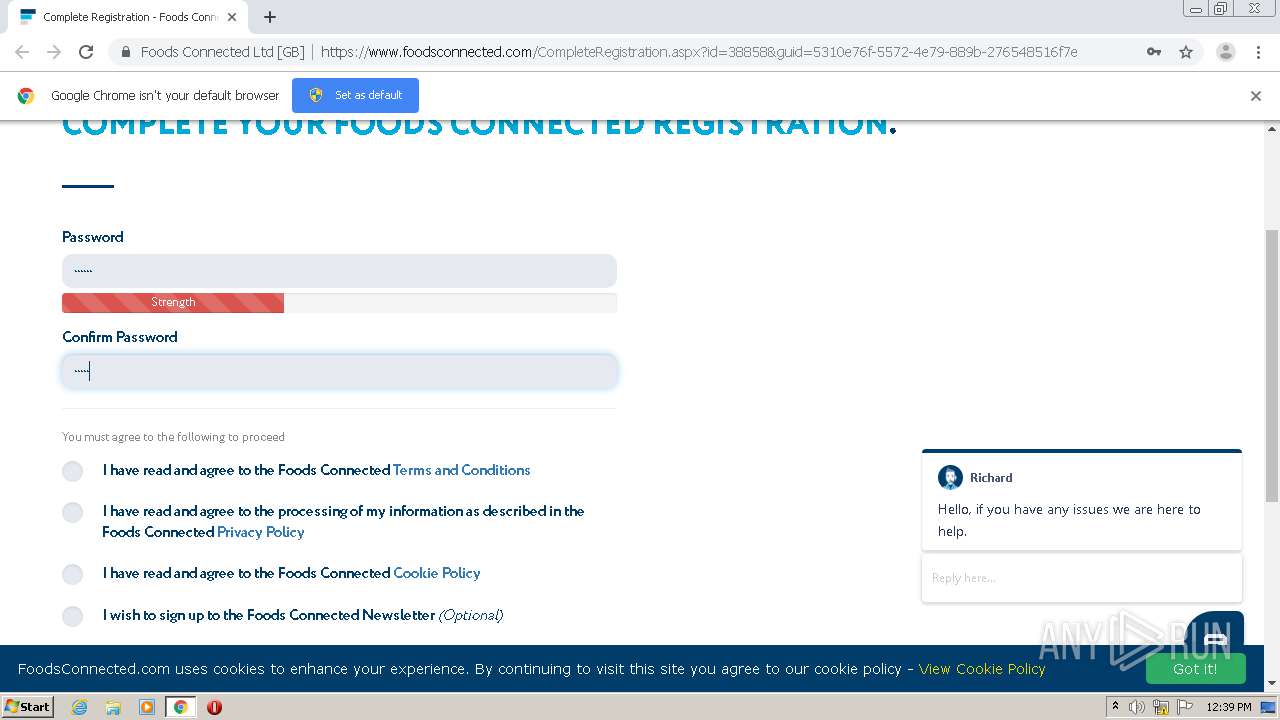
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 11:38:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B65BFB87F3C6896CB41E77161762CD69 |
| SHA1: | 13FBCFC3BCBB0E62547FEA213582DD8A3D7F1735 |
| SHA256: | 2F2B19FBF6A3530BD75F4DE56CAC48C2A13FDDB7B605C64D4F4832F067A04CCB |
| SSDEEP: | 12:rjJSxyMyLqjAIJTpdREdfHMSMi2rjRNFBUUlqZH++/r/Vn:rQAgTpLWOiMDFvWTVn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2560)
- chrome.exe (PID: 1628)
Application launched itself
- chrome.exe (PID: 2560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
15
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,2746433620658289407,14115709085235757729,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15311428349901724909 --mojo-platform-channel-handle=3408 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,2746433620658289407,14115709085235757729,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5622440505985128044 --mojo-platform-channel-handle=1624 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,2746433620658289407,14115709085235757729,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7340500052918385006 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,2746433620658289407,14115709085235757729,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12875700342888965721 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2220 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2564 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,2746433620658289407,14115709085235757729,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8031570293756843128 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3036 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,2746433620658289407,14115709085235757729,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10800467728550411905 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://links.foodsconnected.com/ls/click?upn=uWiFdMYbmyS2zNbuqWZ-2B-2BZLVX-2BgGvCaN5ElQoMIthyqj50qaEDycKYvryxJOPo9XYr-2FUysw-2FFFtQeCyTiOnr14BKVdyehO6TtR0-2F75O-2B7NY7SkPobTlih0U9msY8KhjZC7YnOi1buOsPtRwHl12gC3ILF9skC7ta2GuUNzr8DTw-3DGkqh_QuISWQjKKuMQibsDHimYNstabJjjD-2FX06IJ7IN2kni03PBwsj1Iw5zo8Y-2BBUoxJQ7K3QgibCTIrpKkkGRN-2FOJnCBIfJSBVtlD4AIdzQrS2yLX1l-2B8x0SwZ1cFDoyqnDRN-2BhMfNUT3e4jFMcGO1p43TLpPh2js34UICSwEERvEVLJPPsDVLogIdcU8q6GwyRry7I2eI6SWrXHqfB2vdeyxhbe4FYiaInjwqU3DaHQkr9K-2FBSDUMBRlW6cWslwh2Yf" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,2746433620658289407,14115709085235757729,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13866096003080088306 --mojo-platform-channel-handle=3624 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6c57a9d0,0x6c57a9e0,0x6c57a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
615
Read events
540
Write events
71
Delete events
4
Modification events
| (PID) Process: | (2084) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2560-13247667503631250 |
Value: 259 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2560-13247667503631250 |
Value: 259 | |||
Executable files
0
Suspicious files
48
Text files
72
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8ECC30-A00.pma | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\da9973c5-755a-4134-bf77-4f21e7c3c15a.tmp | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF2d3cee.TMP | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2d3cbf.TMP | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF2d3cdf.TMP | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF2d3cbf.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
44
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
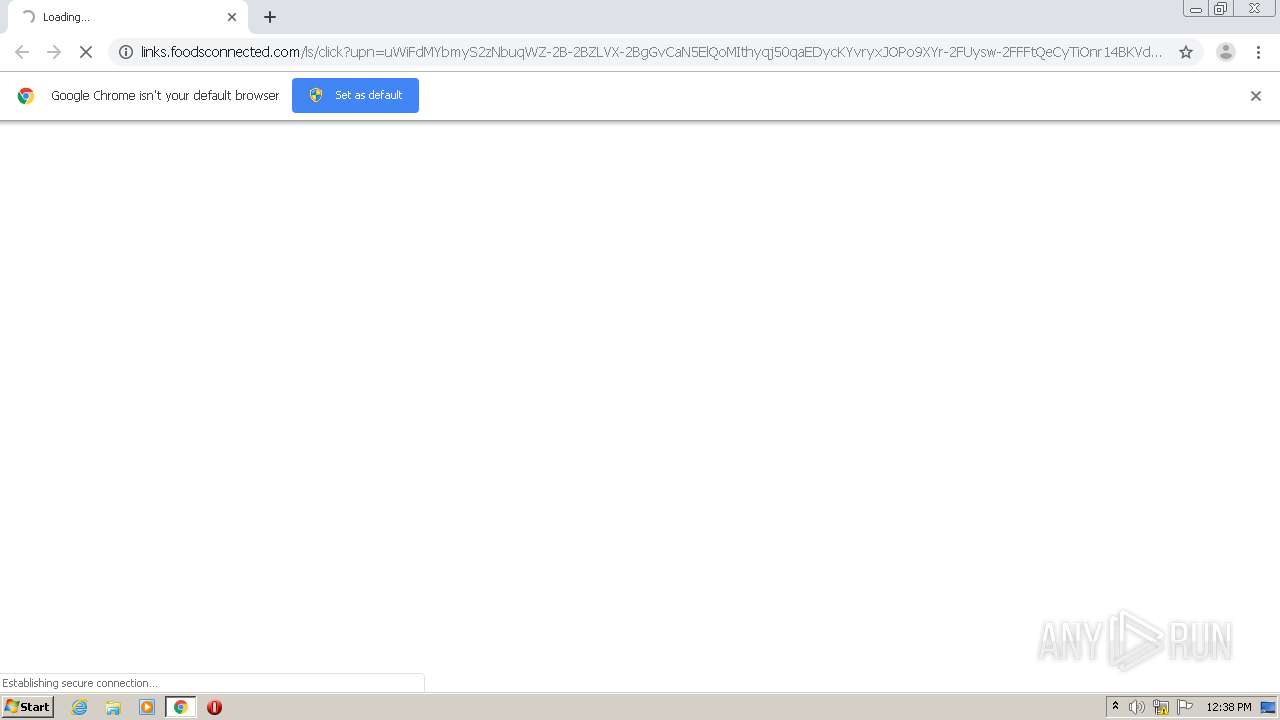
1628 | chrome.exe | GET | 302 | 167.89.115.56:80 | http://links.foodsconnected.com/ls/click?upn=uWiFdMYbmyS2zNbuqWZ-2B-2BZLVX-2BgGvCaN5ElQoMIthyqj50qaEDycKYvryxJOPo9XYr-2FUysw-2FFFtQeCyTiOnr14BKVdyehO6TtR0-2F75O-2B7NY7SkPobTlih0U9msY8KhjZC7YnOi1buOsPtRwHl12gC3ILF9skC7ta2GuUNzr8DTw-3DGkqh_QuISWQjKKuMQibsDHimYNstabJjjD-2FX06IJ7IN2kni03PBwsj1Iw5zo8Y-2BBUoxJQ7K3QgibCTIrpKkkGRN-2FOJnCBIfJSBVtlD4AIdzQrS2yLX1l-2B8x0SwZ1cFDoyqnDRN-2BhMfNUT3e4jFMcGO1p43TLpPh2js34UICSwEERvEVLJPPsDVLogIdcU8q6GwyRry7I2eI6SWrXHqfB2vdeyxhbe4FYiaInjwqU3DaHQkr9K-2FBSDUMBRlW6cWslwh2Yf | US | html | 134 b | suspicious |
1628 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAfoCOOdMHToVhrqESyUD6Q%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1628 | chrome.exe | 172.217.23.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1628 | chrome.exe | 167.89.115.56:80 | links.foodsconnected.com | SendGrid, Inc. | US | suspicious |
1628 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1628 | chrome.exe | 212.54.130.254:443 | www.foodsconnected.com | Access UK Ltd | GB | unknown |
1628 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
1628 | chrome.exe | 172.217.22.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1628 | chrome.exe | 167.89.123.54:80 | links.foodsconnected.com | SendGrid, Inc. | US | suspicious |
1628 | chrome.exe | 209.197.3.15:443 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
1628 | chrome.exe | 104.16.125.175:443 | unpkg.com | Cloudflare Inc | US | shared |
1628 | chrome.exe | 209.197.3.24:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
links.foodsconnected.com |
| suspicious |
accounts.google.com |
| shared |
www.foodsconnected.com |
| unknown |
ocsp.digicert.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
unpkg.com |
| whitelisted |