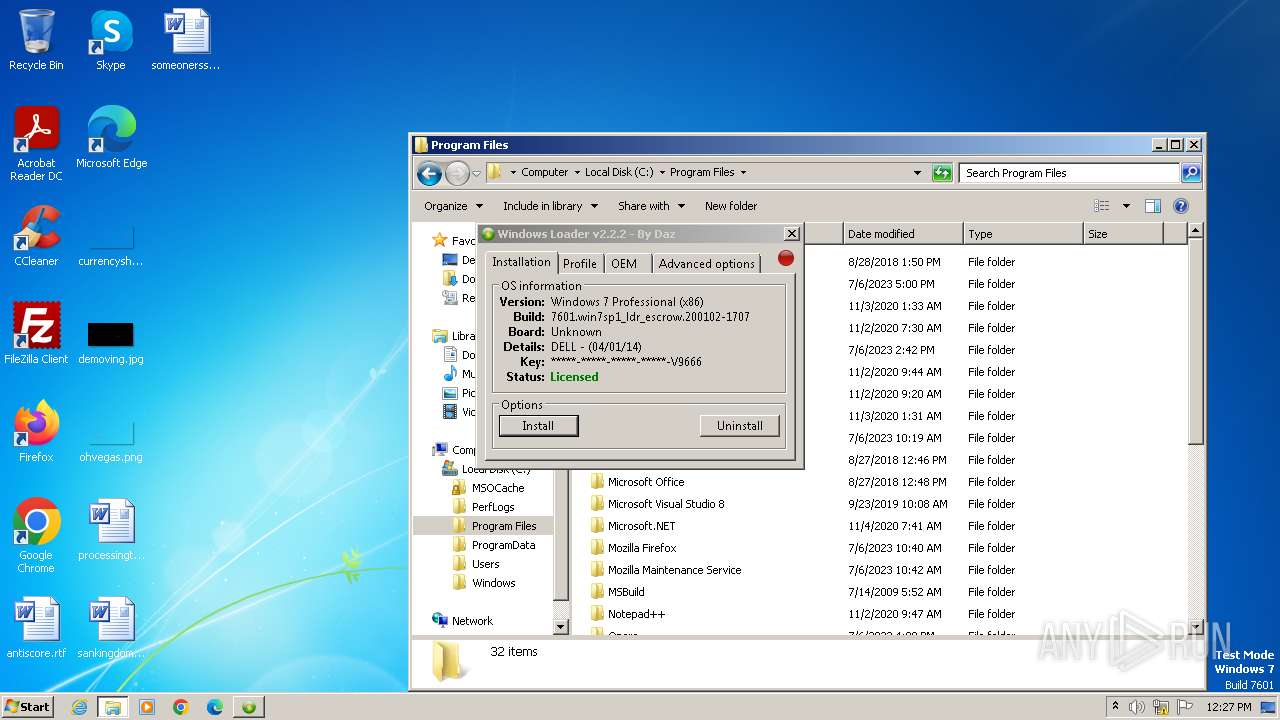
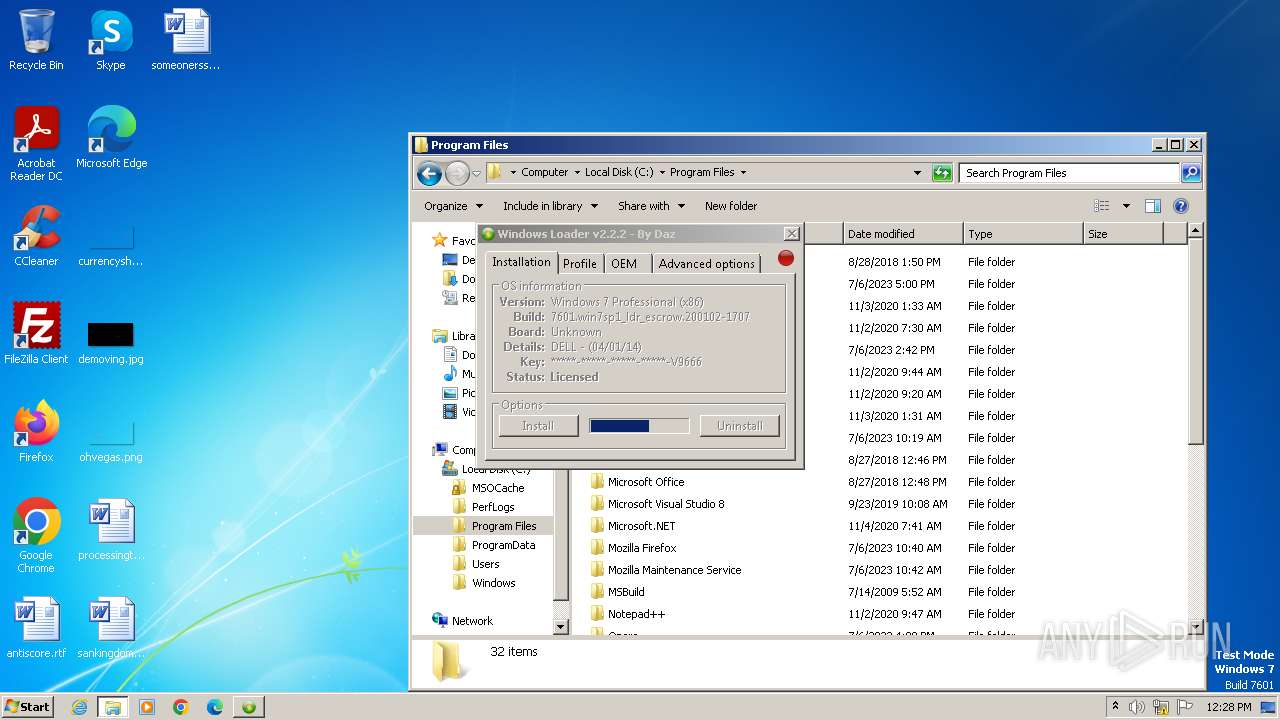
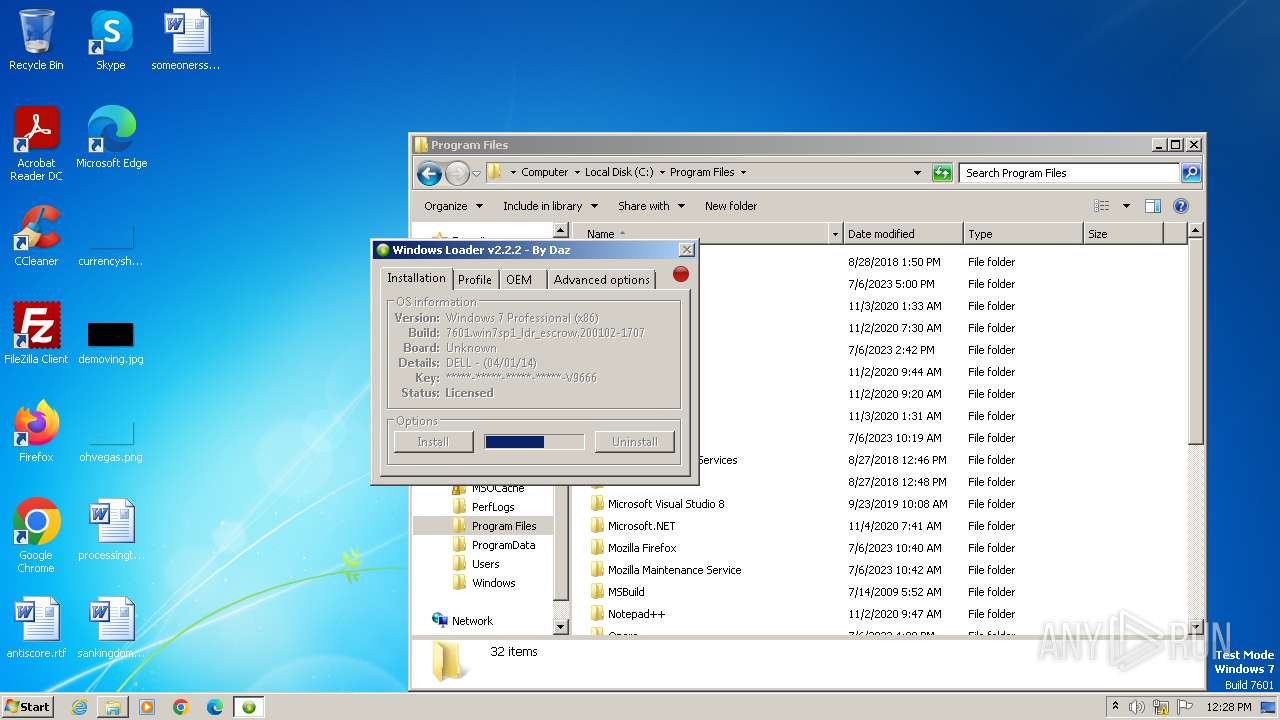
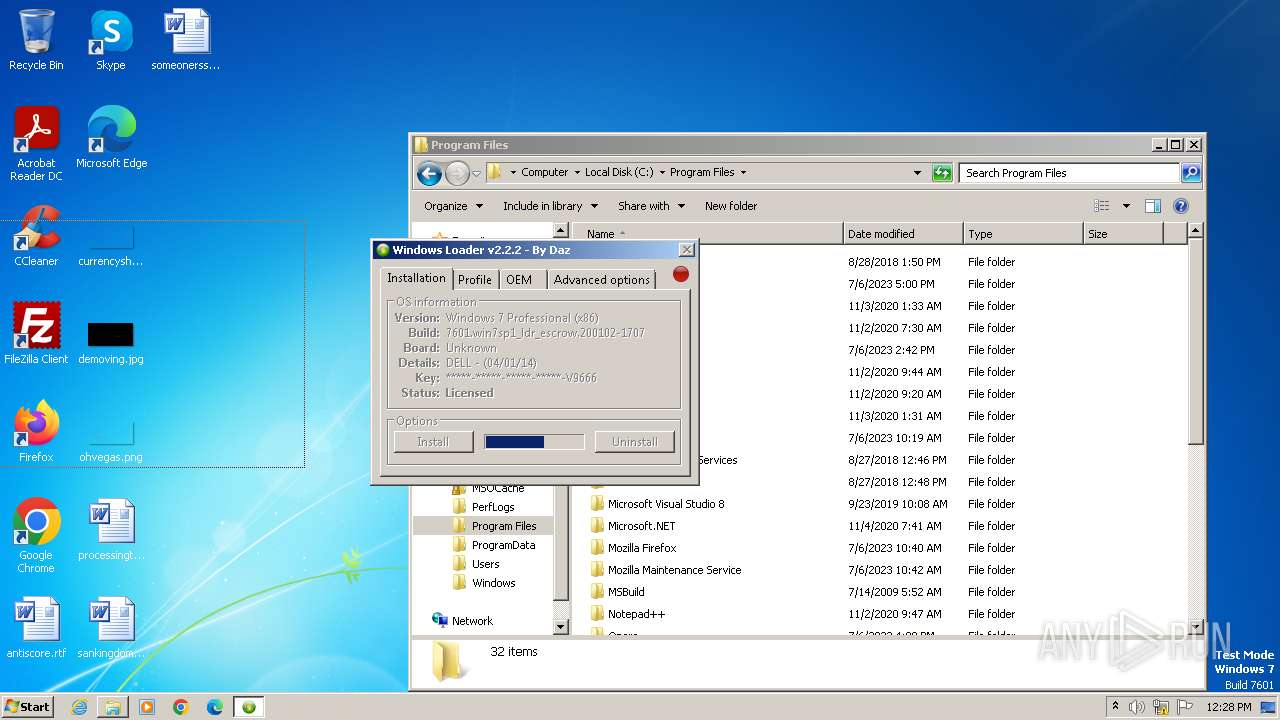
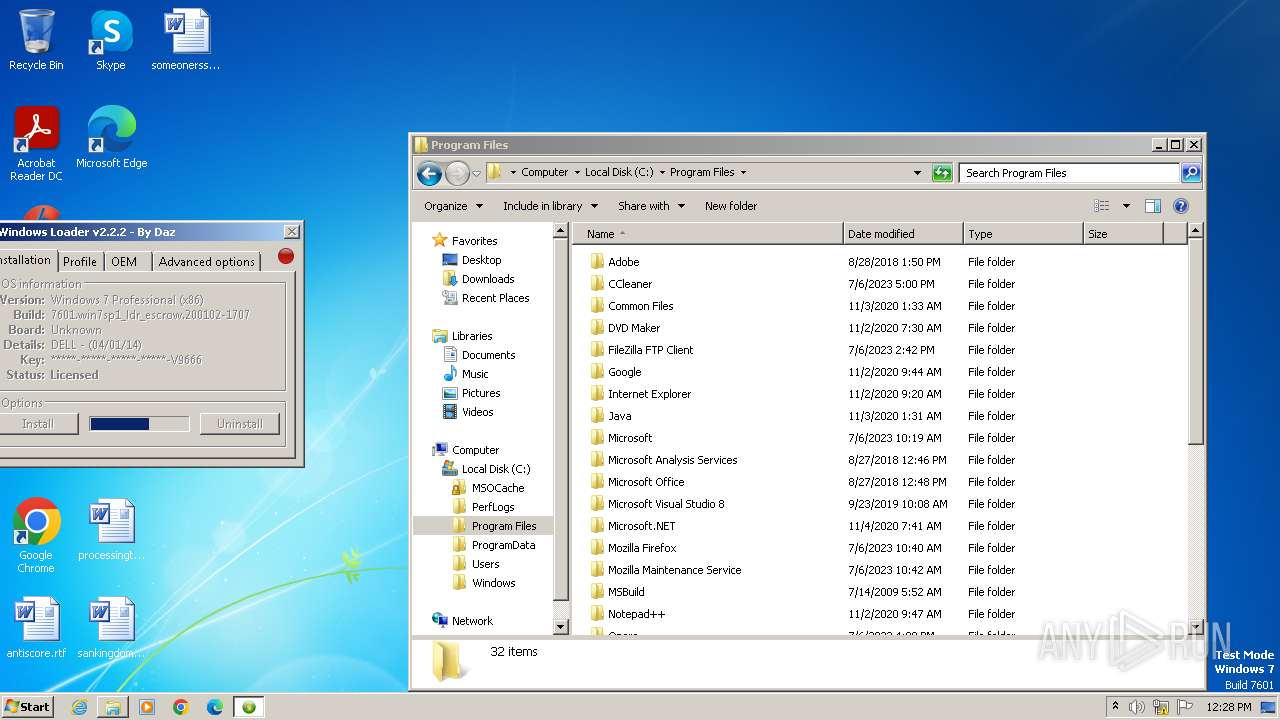
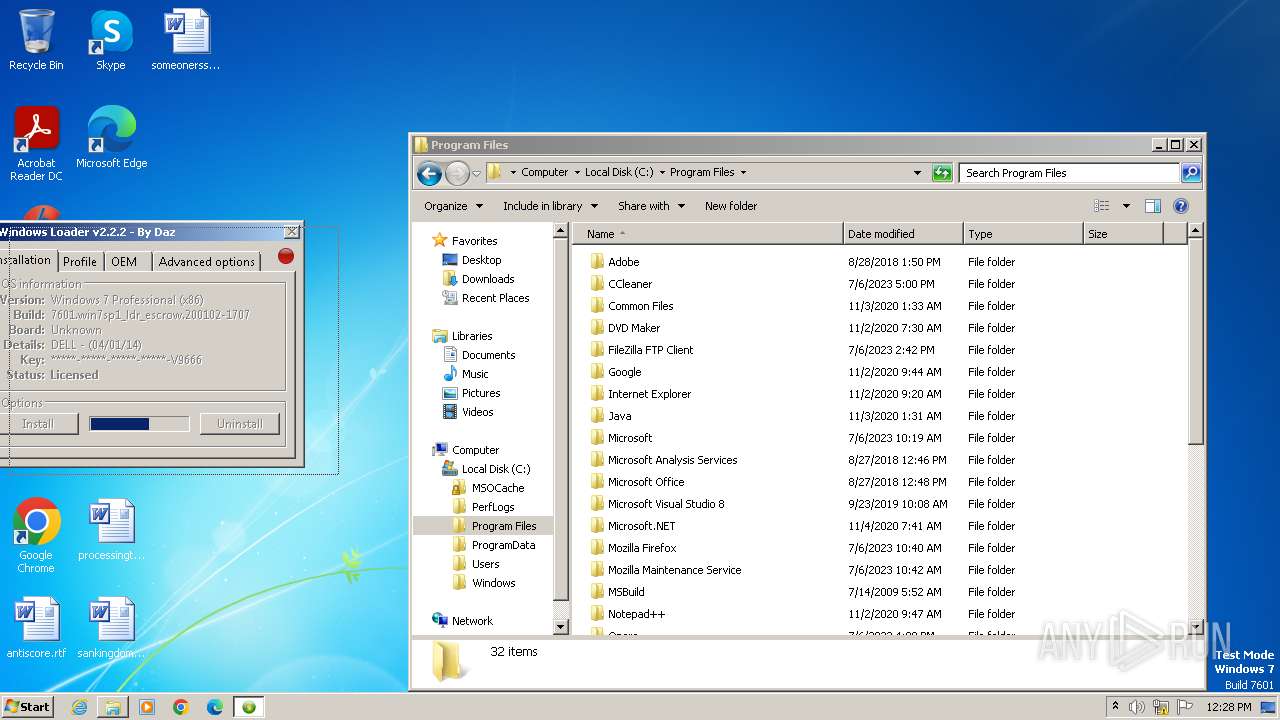
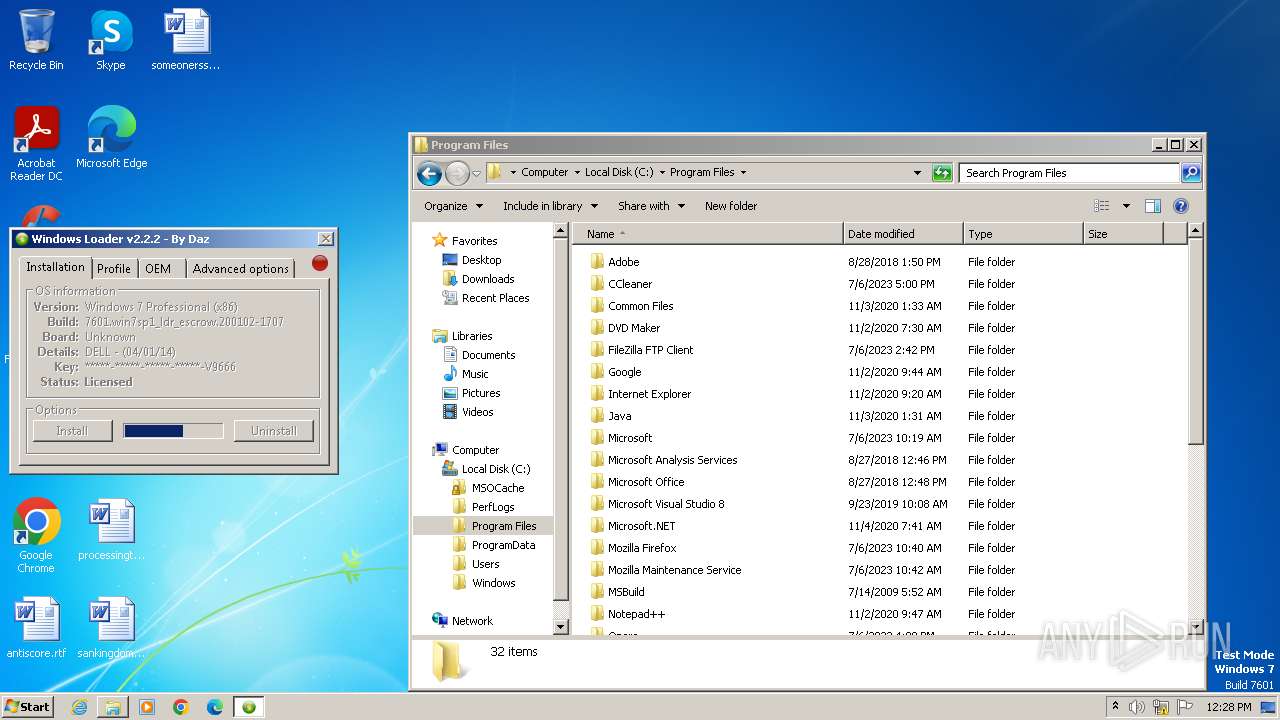
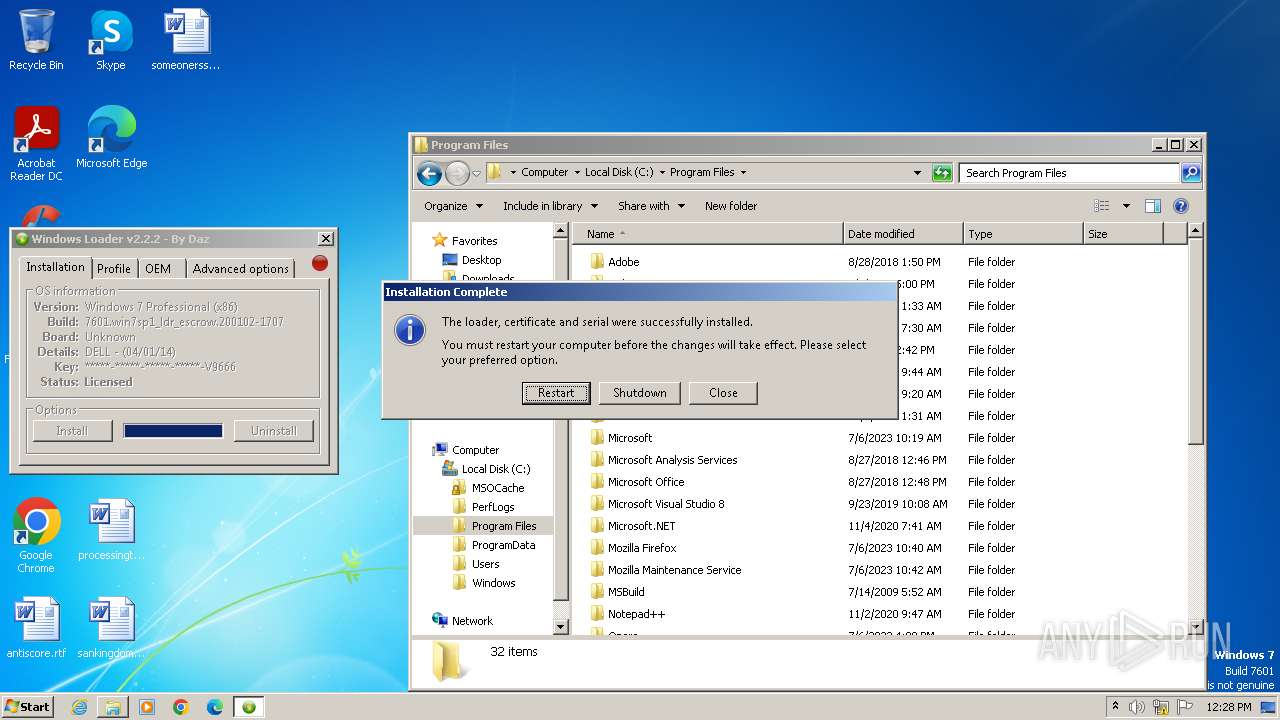
| File name: | Windows Loader.exe |
| Full analysis: | https://app.any.run/tasks/eea2550a-7b15-4e35-a5ef-c347c81ad7cf |
| Verdict: | Malicious activity |
| Analysis date: | November 25, 2023, 12:27:18 |
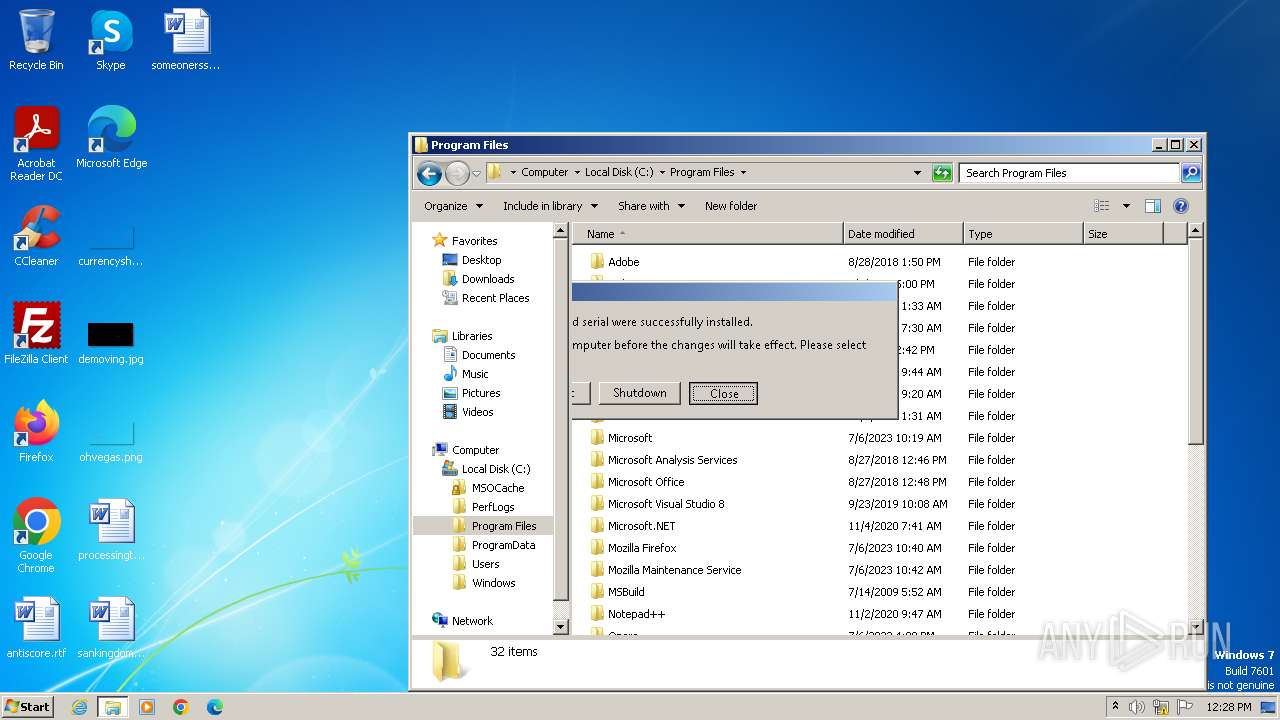
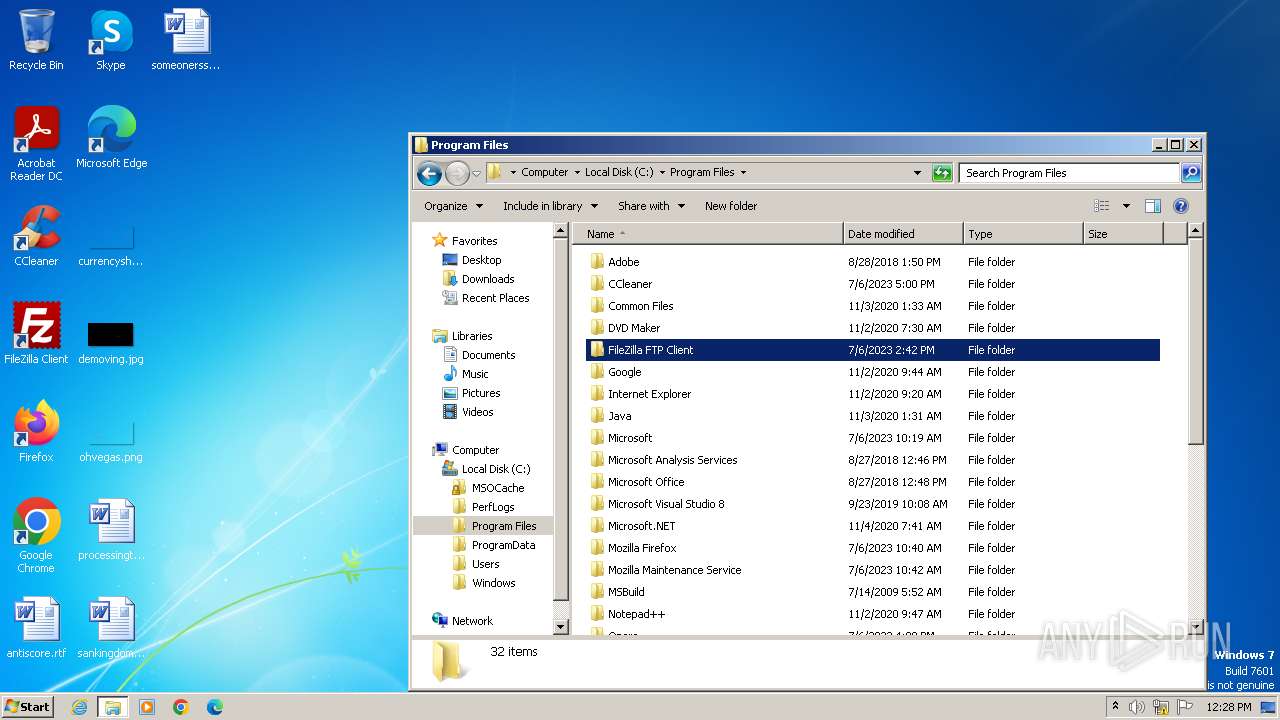
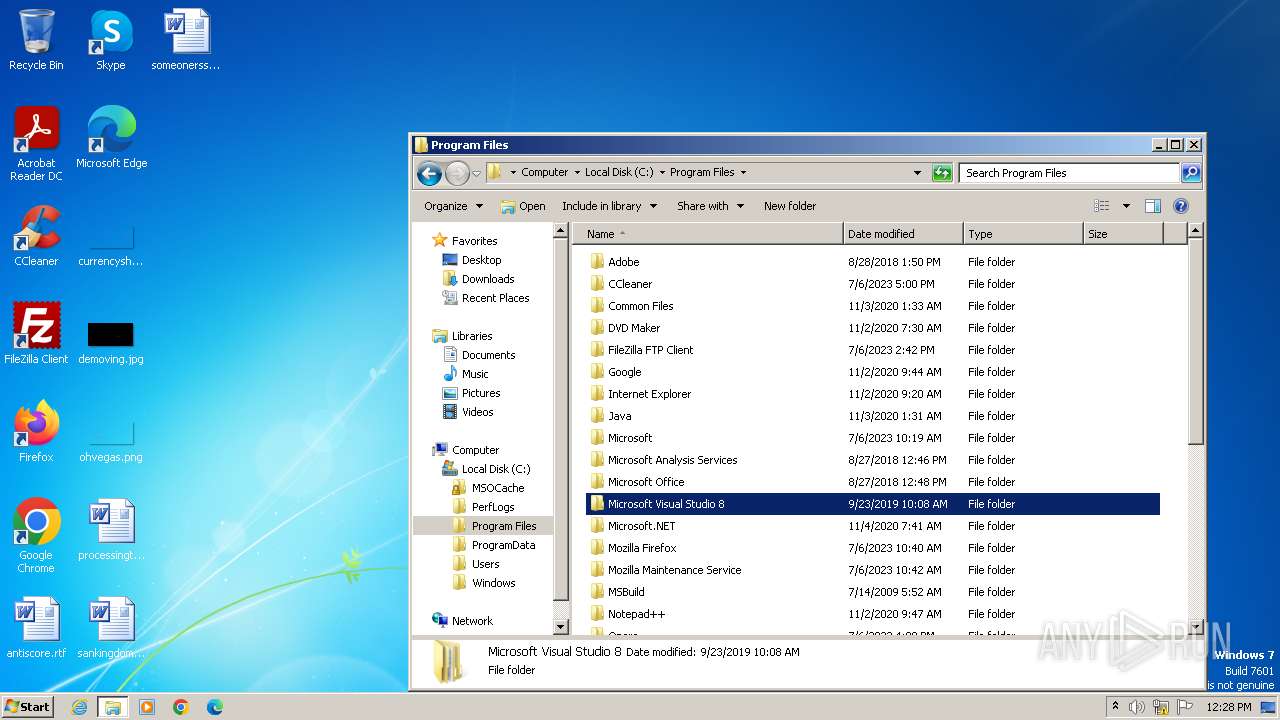
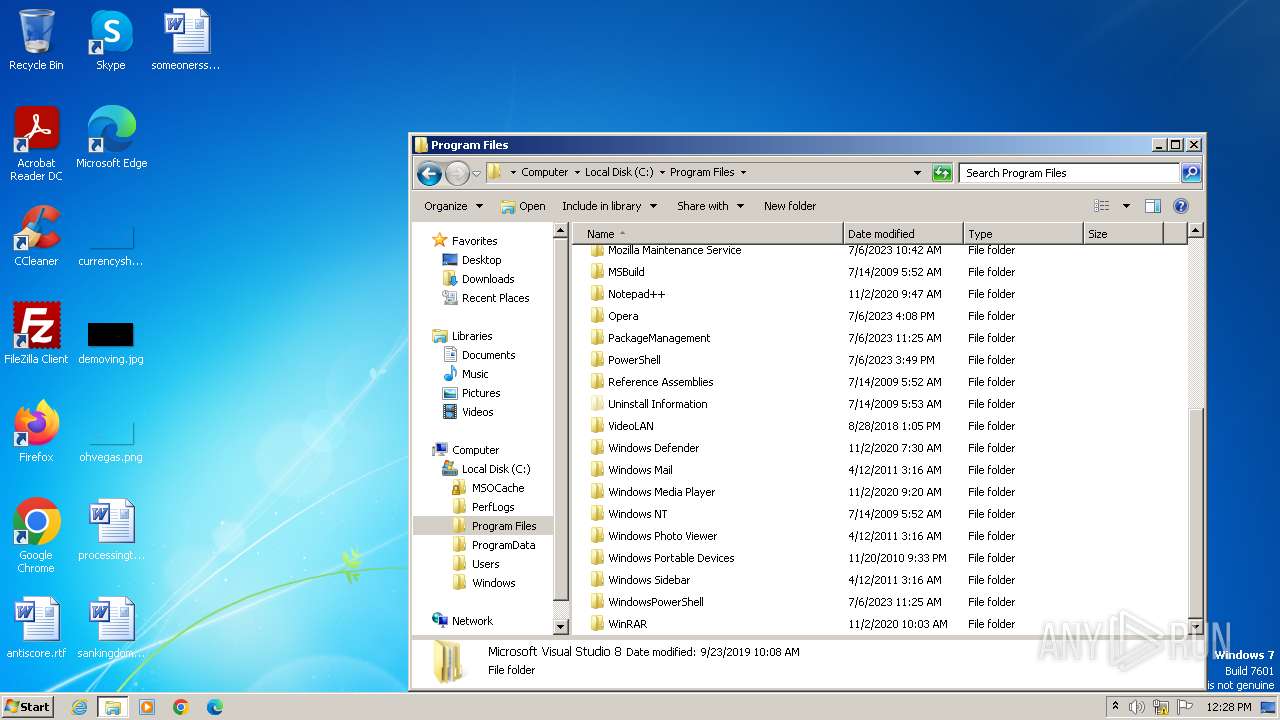
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 323C0FD51071400B51EEDB1BE90A8188 |
| SHA1: | 0EFC35935957C25193BBE9A83AB6CAA25A487ADA |
| SHA256: | 2F2ABA1E074F5F4BAA08B524875461889F8F04D4FFC43972AC212E286022AB94 |
| SSDEEP: | 49152:cEYCFEvlmOmTgtFM3uK5m3imrHuiff+puWV355FXw/+zuWV355FXw/+DuWV355Fx:cEYzEFTgtFM3ukm3imPnts |
MALICIOUS
Opens a text file (SCRIPT)
- cscript.exe (PID: 3632)
- cscript.exe (PID: 3156)
Drops the executable file immediately after the start
- Windows Loader.exe (PID: 1668)
SUSPICIOUS
Reads the BIOS version
- Windows Loader.exe (PID: 1668)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2896)
- Windows Loader.exe (PID: 1668)
- cmd.exe (PID: 2996)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 2716)
- cmd.exe (PID: 2728)
Application launched itself
- cmd.exe (PID: 2996)
- cmd.exe (PID: 2896)
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 3436)
- cmd.exe (PID: 3140)
The process executes VB scripts
- cmd.exe (PID: 3932)
- cmd.exe (PID: 2488)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 3632)
- cscript.exe (PID: 3156)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 3632)
- cscript.exe (PID: 3156)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 3632)
- cscript.exe (PID: 3156)
Reads data from a binary Stream object (SCRIPT)
- cscript.exe (PID: 3632)
- cscript.exe (PID: 3156)
Checks whether a specific file exists (SCRIPT)
- cscript.exe (PID: 3632)
- cscript.exe (PID: 3156)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- cscript.exe (PID: 3632)
Executes WMI query (SCRIPT)
- cscript.exe (PID: 3632)
- cscript.exe (PID: 3156)
Changes charset (SCRIPT)
- cscript.exe (PID: 3632)
Reads data from a file (SCRIPT)
- cscript.exe (PID: 3632)
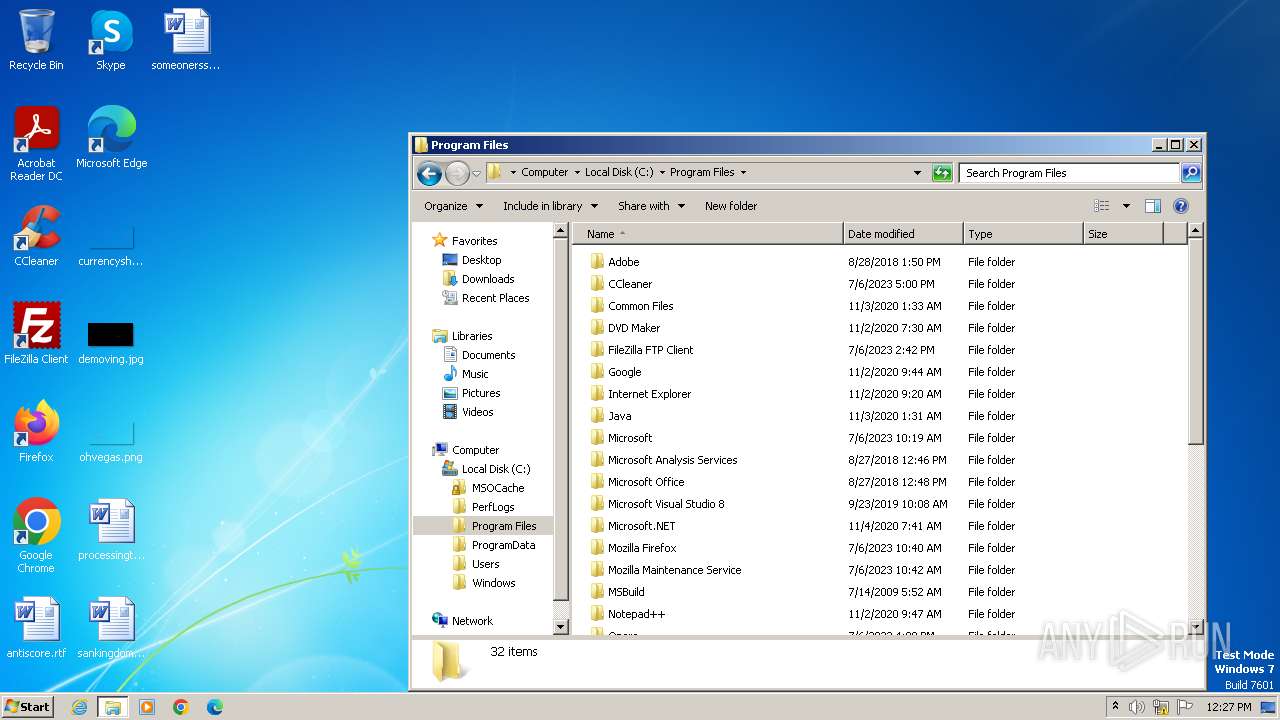
Process drops legitimate windows executable
- Windows Loader.exe (PID: 1668)
INFO
Checks supported languages
- Windows Loader.exe (PID: 1668)
- bootsect.exe (PID: 4068)
Reads the machine GUID from the registry
- Windows Loader.exe (PID: 1668)
Reads the computer name
- Windows Loader.exe (PID: 1668)
Reads product name
- Windows Loader.exe (PID: 1668)
Manual execution by a user
- explorer.exe (PID: 3280)
Reads Environment values
- Windows Loader.exe (PID: 1668)
Reads security settings of Internet Explorer
- cscript.exe (PID: 3632)
- cscript.exe (PID: 3156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (30.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (20) |
| .exe | | | UPX compressed Win32 Executable (19.6) |
| .exe | | | Win32 EXE Yoda's Crypter (19.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:10:31 17:53:19+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 593920 |
| InitializedDataSize: | 28672 |
| UninitializedDataSize: | 1613824 |
| EntryPoint: | 0x21a9a0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.2.0 |
| ProductVersionNumber: | 2.2.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Pre-release, Private build |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | - |
| FileVersion: | 2.2.2.0 |
| Country: | - |
| Release: | Final |
| FileDescription: | - |
| LegalCopyright: | - |
| ProductVersion: | - |
| ProductName: | - |
| OriginalFileName: | Windows Loader.exe |
| InternalName: | - |
Total processes
72
Monitored processes
21
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 948 | "C:\Users\admin\AppData\Local\Temp\Windows Loader.exe" | C:\Users\admin\AppData\Local\Temp\Windows Loader.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1380 | icacls C:\ldrscan\bootwin /grant *S-1-1-0:(F) | C:\Windows\System32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1668 | "C:\Users\admin\AppData\Local\Temp\Windows Loader.exe" | C:\Users\admin\AppData\Local\Temp\Windows Loader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2488 | cmd.exe /A /C "C:\Windows\System32\cscript.exe //nologo C:\Windows\System32\slmgr.vbs -ipk 32KD2-K9CTF-M3DJT-4J3WC-733WD" | C:\Windows\System32\cmd.exe | — | Windows Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2716 | cmd.exe /A /C "icacls C:\ldrscan\bootwin /grant *S-1-1-0:(F)" | C:\Windows\System32\cmd.exe | — | Windows Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2728 | cmd.exe /A /C "icacls C:\ldrscan\bootwin /grant *S-1-1-0:(F)" | C:\Windows\System32\cmd.exe | — | Windows Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2896 | cmd.exe /A /C "cmd.exe /c takeown /f C:\ldrscan\bootwin" | C:\Windows\System32\cmd.exe | — | Windows Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2996 | cmd.exe /A /C "cmd.exe /c takeown /f C:\ldrscan\bootwin" | C:\Windows\System32\cmd.exe | — | Windows Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3140 | cmd.exe /c takeown /f C:\ldrscan\bootwin | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3156 | C:\Windows\System32\cscript.exe //nologo C:\Windows\System32\slmgr.vbs -ipk 32KD2-K9CTF-M3DJT-4J3WC-733WD | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
679
Read events
679
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4068 | bootsect.exe | \Device\HarddiskVolume1 | — | |
MD5:— | SHA256:— | |||
| 1668 | Windows Loader.exe | C:\Dell.XRM-MS | xml | |
MD5:18B1E45BF56F40C3C4BBE65831178216 | SHA256:D072A059D3ED3E75C98B85B41E4319E8D5CFAE0E0C239B62436A3AD34003AB4A | |||
| 1668 | Windows Loader.exe | C:\bootsect.dat | executable | |
MD5:F87238C0CF01E2AE9D45FFA2E7D8EE72 | SHA256:20C8E265FDF0DF87F44063840C089F139D29C7128D576FC13F7A65E115533C05 | |||
| 1668 | Windows Loader.exe | C:\bootsect.exe | executable | |
MD5:F87238C0CF01E2AE9D45FFA2E7D8EE72 | SHA256:20C8E265FDF0DF87F44063840C089F139D29C7128D576FC13F7A65E115533C05 | |||
| 1668 | Windows Loader.exe | \\?\Volume{e1a82db3-a9f0-11e7-b142-806e6f6e6963}\YMSXE | binary | |
MD5:3A4953B07686DF470B3650FC12415F5E | SHA256:895214BD7FB30C7FF0F9352AA191BCEE20A2650D98F0EC95CBB0580BB63D9671 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |