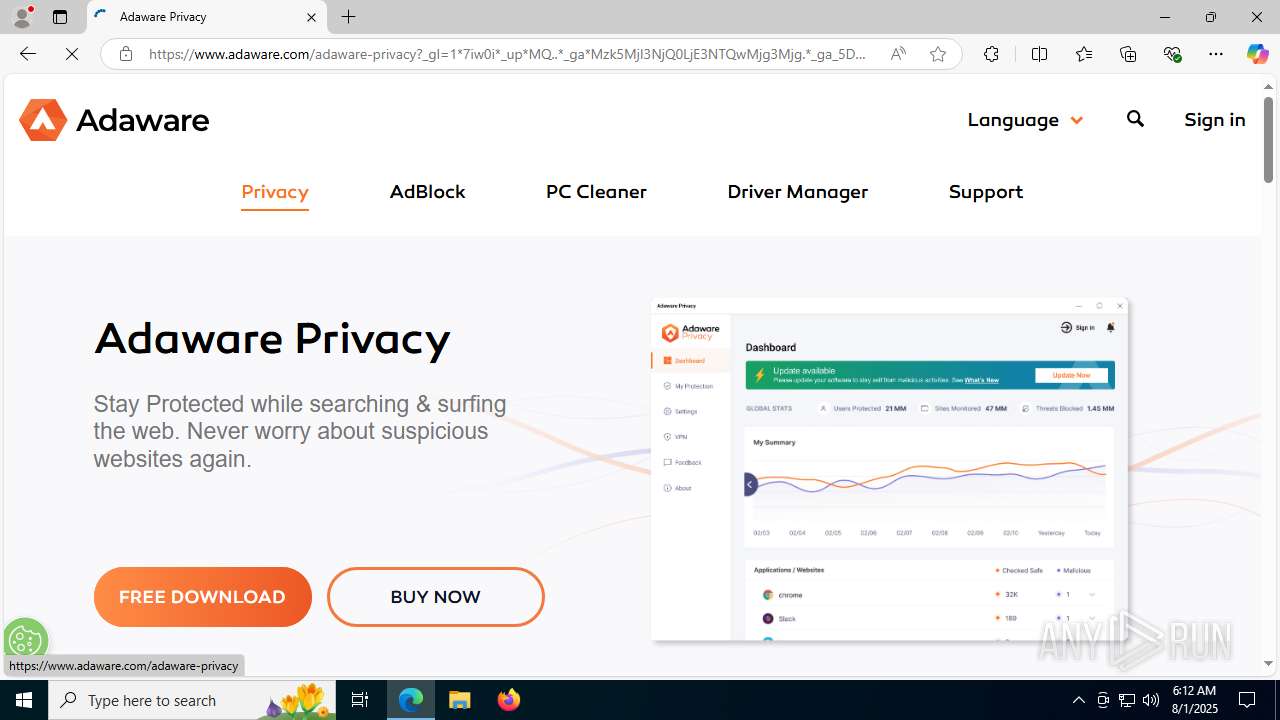
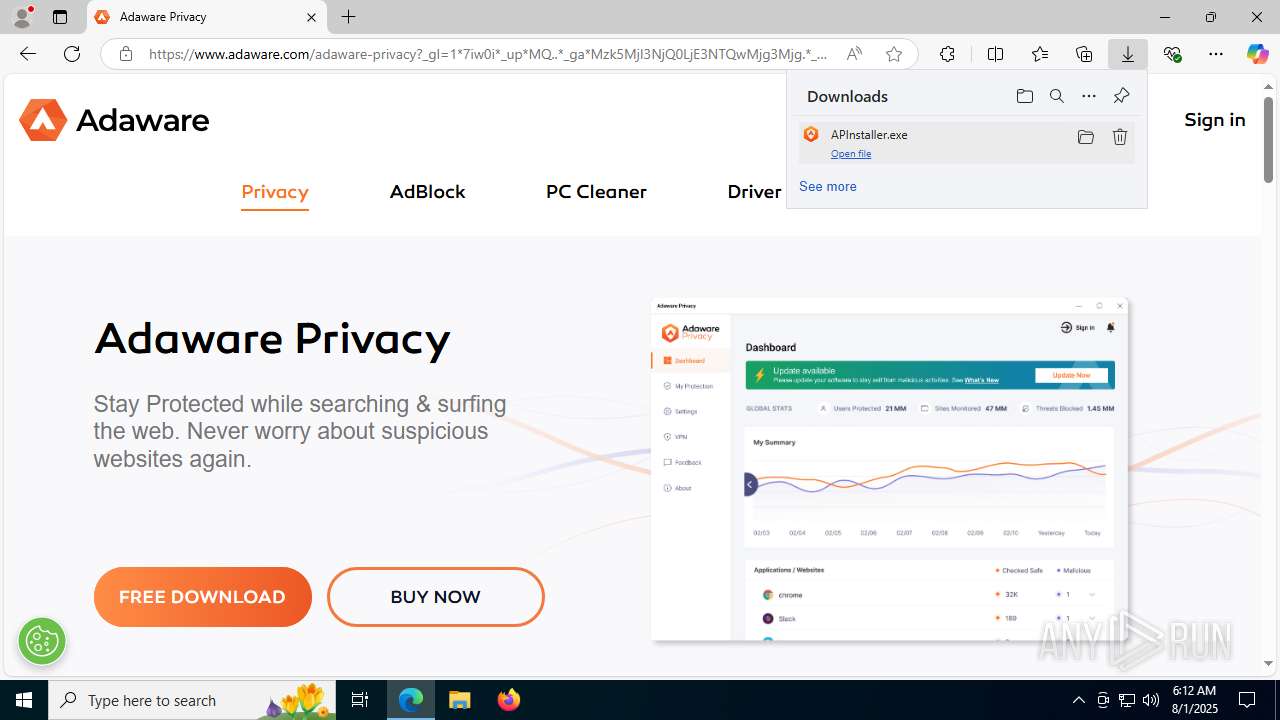
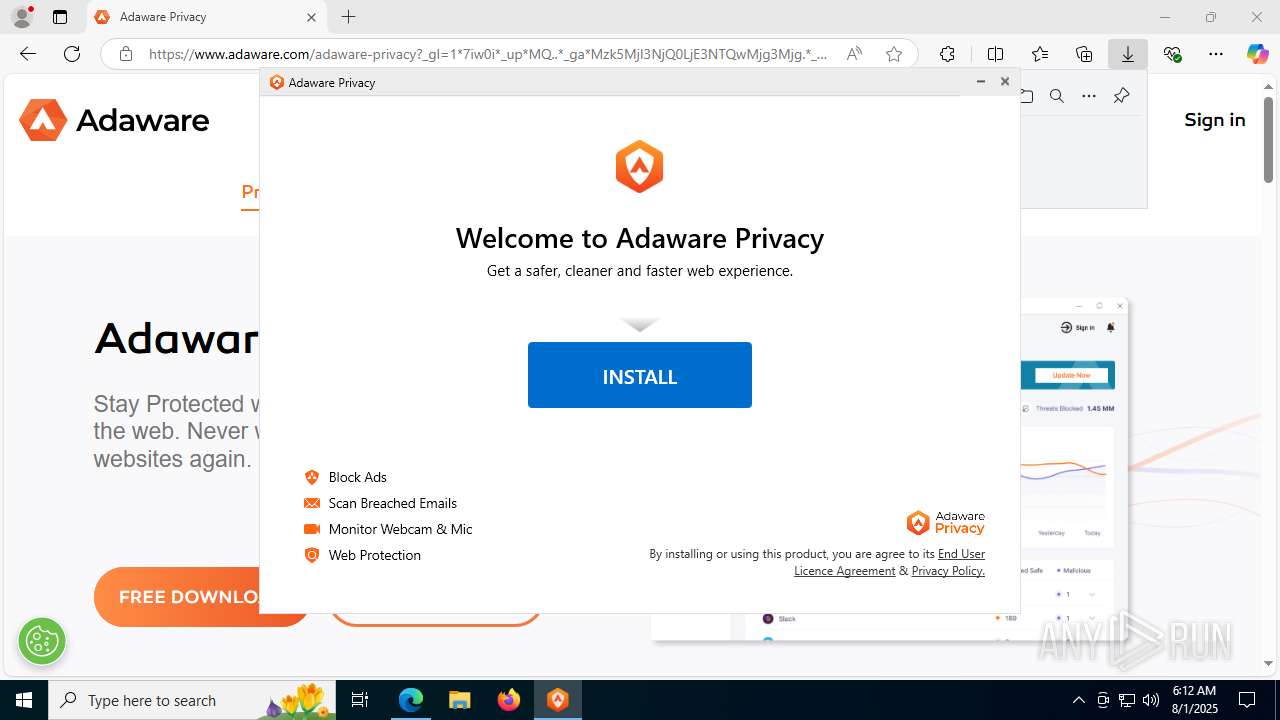
| URL: | https://www.adaware.com/adaware-privacy/thank-you?partner=AP250501&campaign=21786890600 |
| Full analysis: | https://app.any.run/tasks/699e21ad-db11-4ec1-b5a7-001174c92075 |
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2025, 06:11:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1019D0636F148F534A389469D06DD054 |
| SHA1: | D62F98A0E4CC6B0E94AF4F96B223CA71C6E2A32C |
| SHA256: | 2F1E9E1733CBF28680EF8959FE32965327A6AF60EBE220D0035A64D34674E714 |
| SSDEEP: | 3:N8DSLZSEQLd0BEXAIVcYDLOMVEXQA8hVEMIz:2OL4iyXH1EXUDmz |
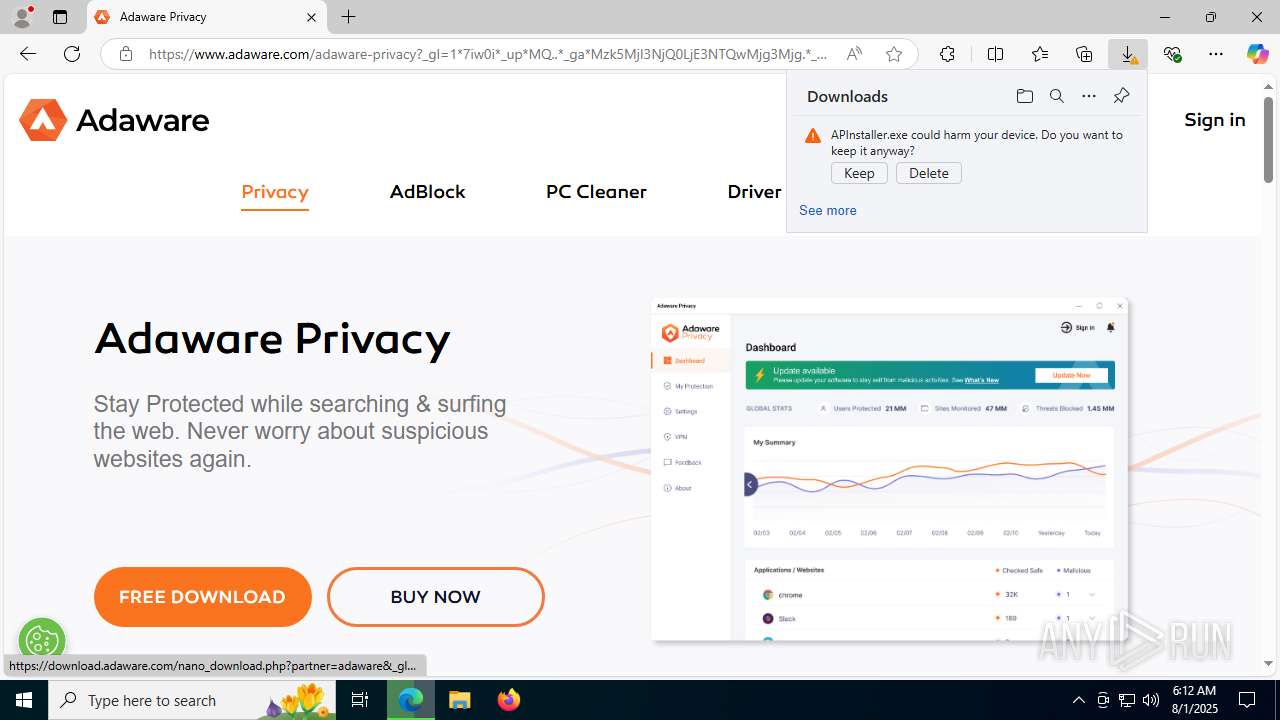
MALICIOUS
Changes the autorun value in the registry
- rundll32.exe (PID: 7312)
Starts NET.EXE for service management
- APInstaller.exe (PID: 7716)
- net.exe (PID: 7940)
SUSPICIOUS
The process drops C-runtime libraries
- APInstaller.exe (PID: 7716)
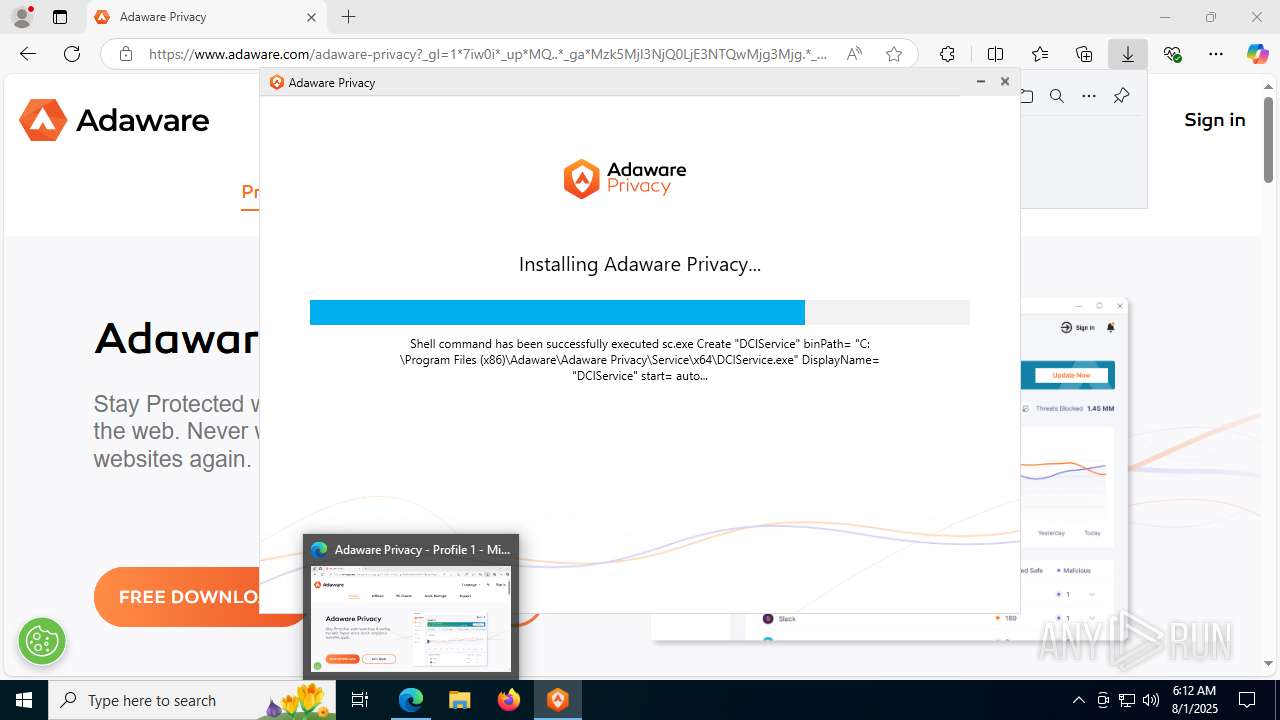
Windows service management via SC.EXE
- sc.exe (PID: 7600)
- sc.exe (PID: 8040)
- sc.exe (PID: 7008)
- sc.exe (PID: 7904)
- sc.exe (PID: 8024)
Executable content was dropped or overwritten
- APInstaller.exe (PID: 7716)
- rundll32.exe (PID: 7312)
Drops a system driver (possible attempt to evade defenses)
- APInstaller.exe (PID: 7716)
- rundll32.exe (PID: 7312)
Reads security settings of Internet Explorer
- APInstaller.exe (PID: 7716)
- AP-Assistant-Service.exe (PID: 4160)
Process drops legitimate windows executable
- APInstaller.exe (PID: 7716)
The process verifies whether the antivirus software is installed
- APInstaller.exe (PID: 7716)
- rundll32.exe (PID: 7312)
- AP-Assistant-Service.exe (PID: 4160)
Uses RUNDLL32.EXE to load library
- APInstaller.exe (PID: 7716)
Creates or modifies Windows services
- rundll32.exe (PID: 7312)
Restarts service on failure
- sc.exe (PID: 7636)
Executes as Windows Service
- AP-Assistant-Service.exe (PID: 4160)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 7672)
There is functionality for capture public ip (YARA)
- APInstaller.exe (PID: 7716)
Starts CMD.EXE for commands execution
- AP-Assistant-Service.exe (PID: 4160)
INFO
Application launched itself
- msedge.exe (PID: 2492)
Reads Environment values
- identity_helper.exe (PID: 7556)
Checks supported languages
- identity_helper.exe (PID: 7556)
- APInstaller.exe (PID: 7716)
- AP-Assistant-Service.exe (PID: 4160)
Reads the computer name
- identity_helper.exe (PID: 7556)
- APInstaller.exe (PID: 7716)
- AP-Assistant-Service.exe (PID: 4160)
Executable content was dropped or overwritten
- msedge.exe (PID: 6676)
- msedge.exe (PID: 2492)
Reads the machine GUID from the registry
- APInstaller.exe (PID: 7716)
- AP-Assistant-Service.exe (PID: 4160)
The sample compiled with english language support
- APInstaller.exe (PID: 7716)
- rundll32.exe (PID: 7312)
Create files in a temporary directory
- APInstaller.exe (PID: 7716)
Checks proxy server information
- APInstaller.exe (PID: 7716)
Creates files in the program directory
- APInstaller.exe (PID: 7716)
- AP-Assistant-Service.exe (PID: 4160)
Disables trace logs
- APInstaller.exe (PID: 7716)
Reads the software policy settings
- APInstaller.exe (PID: 7716)
Process checks computer location settings
- APInstaller.exe (PID: 7716)
Creates files in the driver directory
- rundll32.exe (PID: 7312)
Launching a file from a Registry key
- rundll32.exe (PID: 7312)
Reads security settings of Internet Explorer
- runonce.exe (PID: 6404)
Reads the time zone
- runonce.exe (PID: 6404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
188
Monitored processes
49
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1636 | "C:\Windows\System32\grpconv.exe" -o | C:\Windows\System32\grpconv.exe | — | runonce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1828 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2368,i,15622516305549661771,7509117322652818374,262144 --variations-seed-version --mojo-platform-channel-handle=2364 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2624,i,15622516305549661771,7509117322652818374,262144 --variations-seed-version --mojo-platform-channel-handle=2640 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2032 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7572,i,15622516305549661771,7509117322652818374,262144 --variations-seed-version --mojo-platform-channel-handle=7456 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2492 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://www.adaware.com/adaware-privacy/thank-you?partner=AP250501&campaign=21786890600" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3760 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7536,i,15622516305549661771,7509117322652818374,262144 --variations-seed-version --mojo-platform-channel-handle=7540 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3852 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x31c,0x320,0x324,0x314,0x32c,0x7ffc4394f208,0x7ffc4394f214,0x7ffc4394f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3888 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 615
Read events
9 547
Write events
67
Delete events
1
Modification events
| (PID) Process: | (2492) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2492) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2492) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2492) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2492) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590572 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B27646A0-AFE9-48FC-AB1C-DA36742335EC} | |||
| (PID) Process: | (2492) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 829EB7EBDD992F00 | |||
| (PID) Process: | (2492) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590572 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {ECB1B9CD-3A23-41D9-966C-CC17C1443A8D} | |||
| (PID) Process: | (2492) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590572 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {40FD27A0-FF99-45FB-B701-75B7998ED373} | |||
| (PID) Process: | (2492) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590572 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D464E9B6-EAB6-4996-B05C-068EE77259DB} | |||
| (PID) Process: | (2492) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590572 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {91F92803-AB97-4973-A4B8-1026525A39B3} | |||
Executable files
183
Suspicious files
243
Text files
101
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18ed1a.TMP | — | |
MD5:— | SHA256:— | |||
| 2492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18ed1a.TMP | — | |
MD5:— | SHA256:— | |||
| 2492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18ed1a.TMP | — | |
MD5:— | SHA256:— | |||
| 2492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18ed1a.TMP | — | |
MD5:— | SHA256:— | |||
| 2492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF18ed1a.TMP | — | |
MD5:— | SHA256:— | |||
| 2492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18ed2a.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
168
DNS requests
106
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6676 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:eq-gkcBw5NX__VDyG20IeHFdtM-AUfrc9b51u2G_-Go&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8168 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5084 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8168 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7716 | APInstaller.exe | GET | 200 | 104.16.149.130:80 | http://geo.lavasoft.com/ | unknown | — | — | whitelisted |
7716 | APInstaller.exe | GET | 200 | 104.16.149.130:80 | http://geo.lavasoft.com/ | unknown | — | — | whitelisted |
7716 | APInstaller.exe | GET | 200 | 104.16.149.130:80 | http://geo.lavasoft.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4084 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6676 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6676 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6676 | msedge.exe | 104.16.213.94:443 | www.adaware.com | CLOUDFLARENET | — | whitelisted |
6676 | msedge.exe | 2.16.241.224:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
6676 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.adaware.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6676 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6676 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6676 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6676 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6676 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6676 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
Process | Message |
|---|---|
APInstaller.exe | Message: Installer starts
|
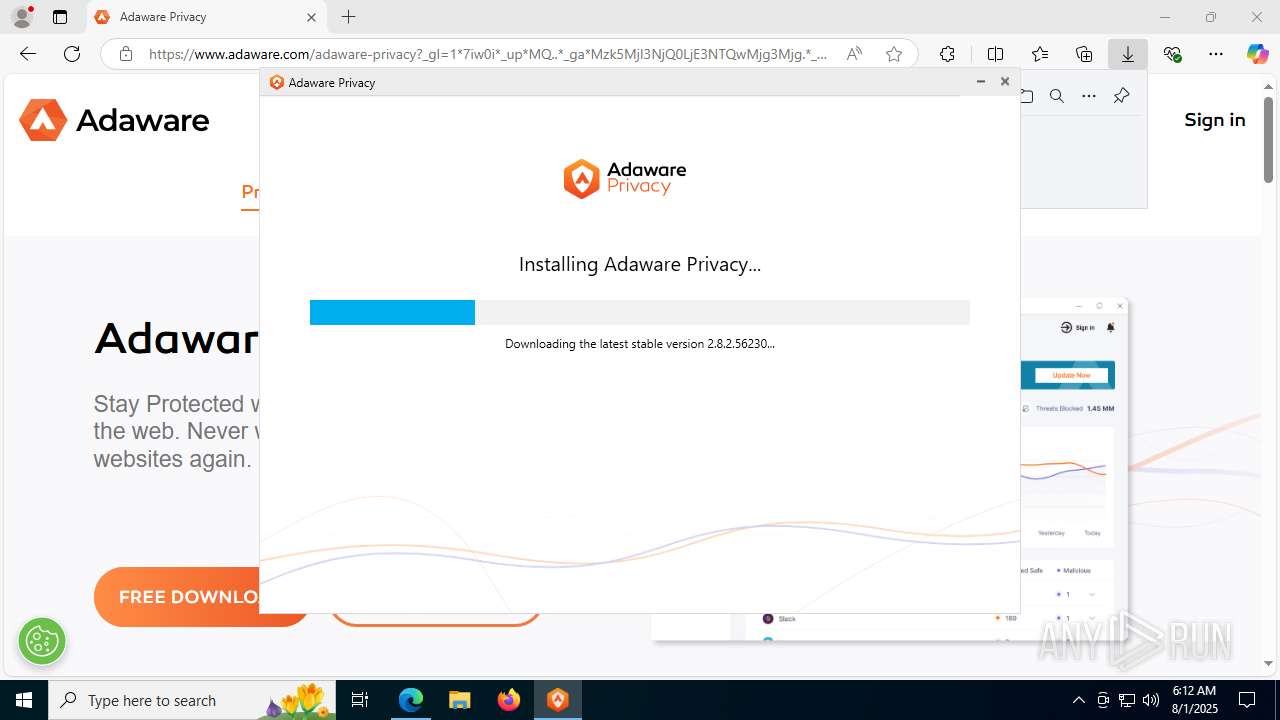
APInstaller.exe | Message: ResourceExtractor starts
|
APInstaller.exe | Message: ExtractFileFromAssemblyResources starts
|
APInstaller.exe | Message: ExtractFileFromAssemblyResources filePath=C:\Users\admin\AppData\Local\Temp\APResources\App.config
|
APInstaller.exe | Message: ExtractFileFromAssemblyResources end
|
APInstaller.exe | Message: Extracted App Config PathC:\Users\admin\AppData\Local\Temp\APResources\App.config
|
APInstaller.exe | Message: ResourceExtractor end
|
APInstaller.exe | Message: GetSelfVersion starts
|
APInstaller.exe | Message: InitializeDataCollector starts
|
APInstaller.exe | Message: filePath is C:\Users\admin\Downloads\APInstaller.exe
|