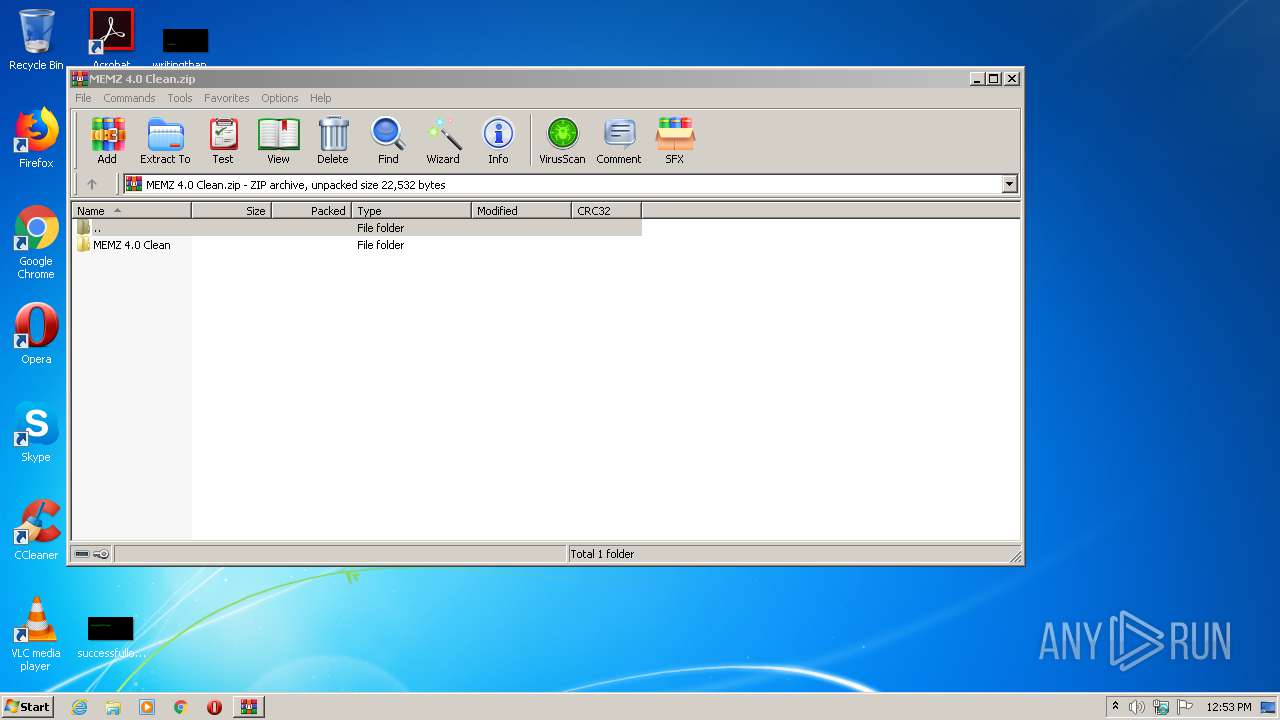
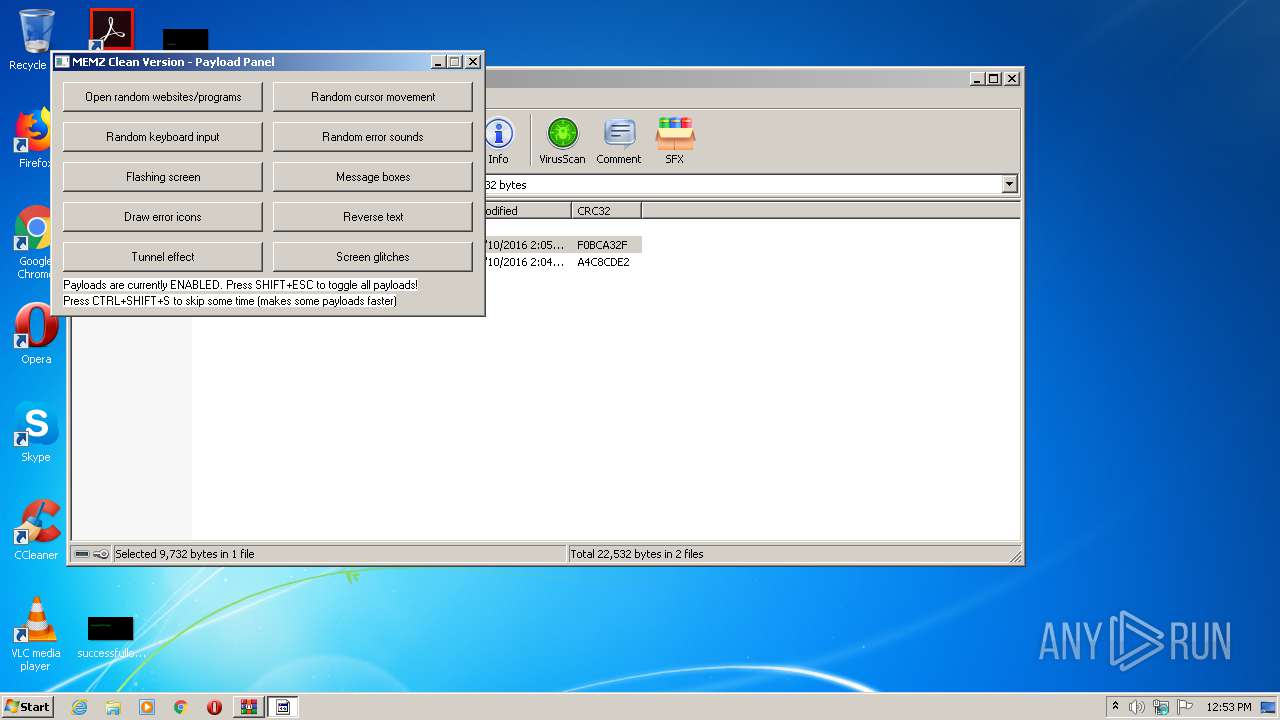
| File name: | MEMZ 4.0 Clean.zip |
| Full analysis: | https://app.any.run/tasks/9a9ec3d0-142a-411b-ac5c-cbc2ac599454 |
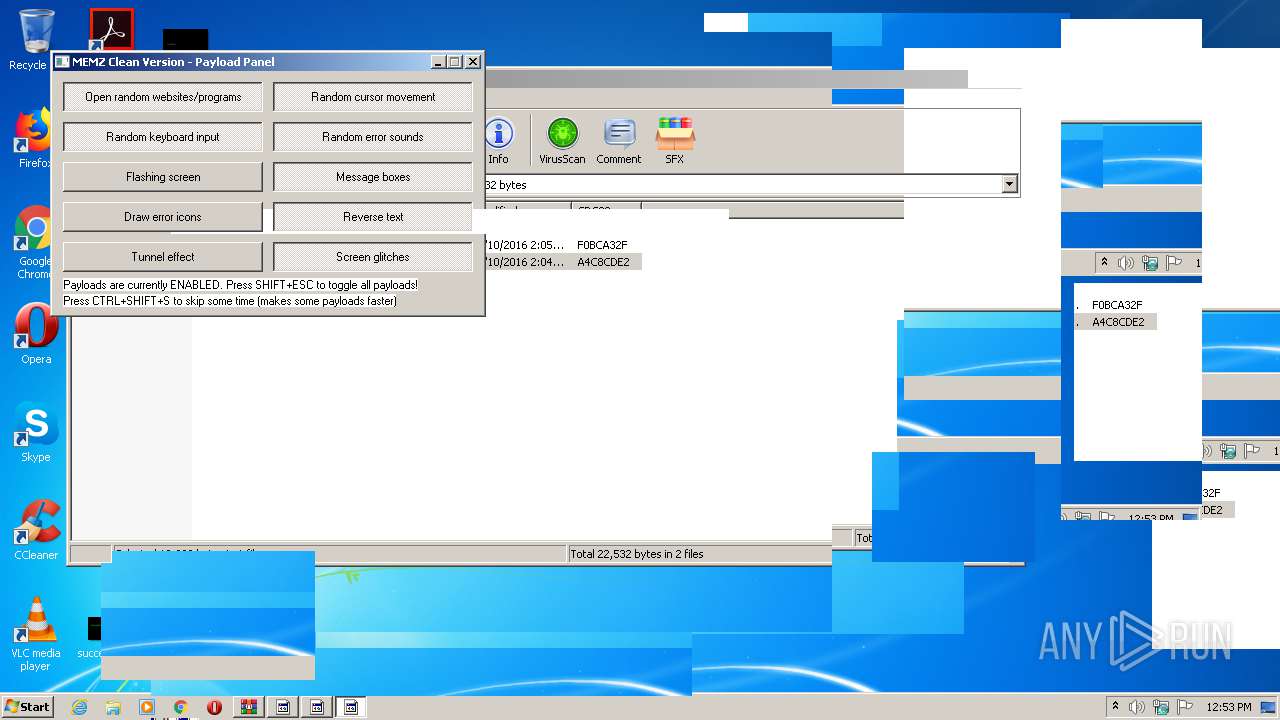
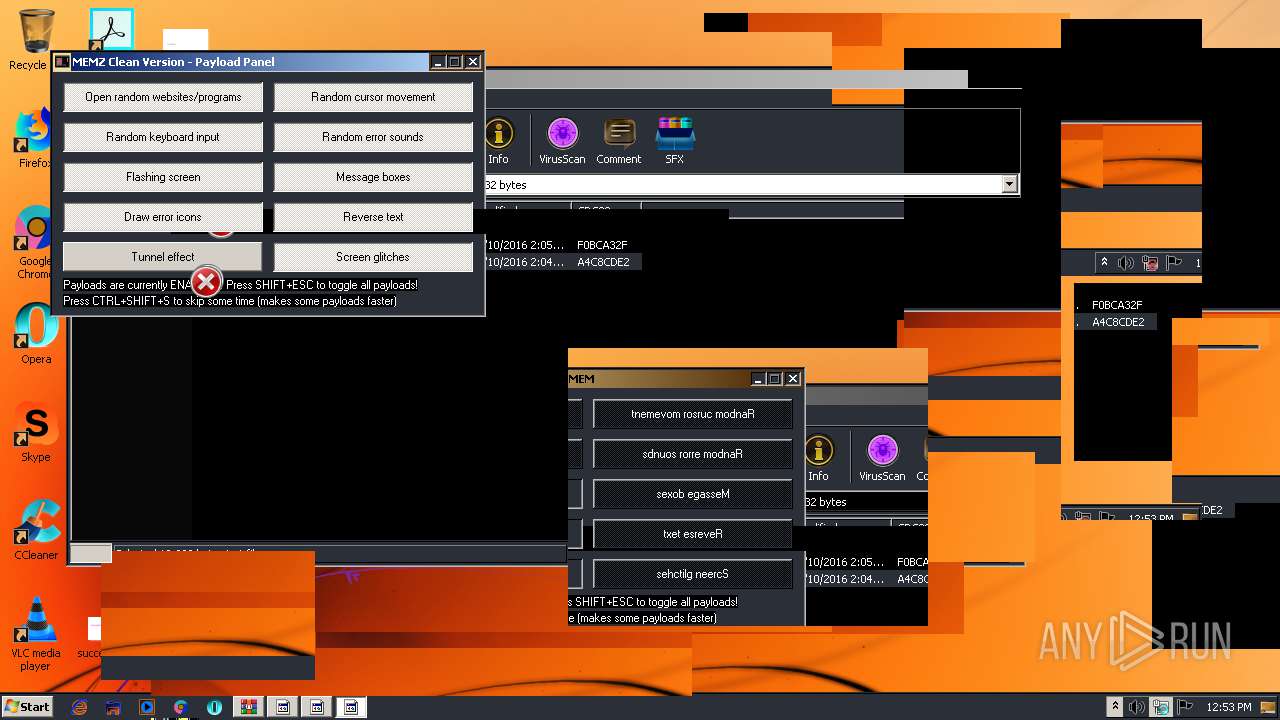
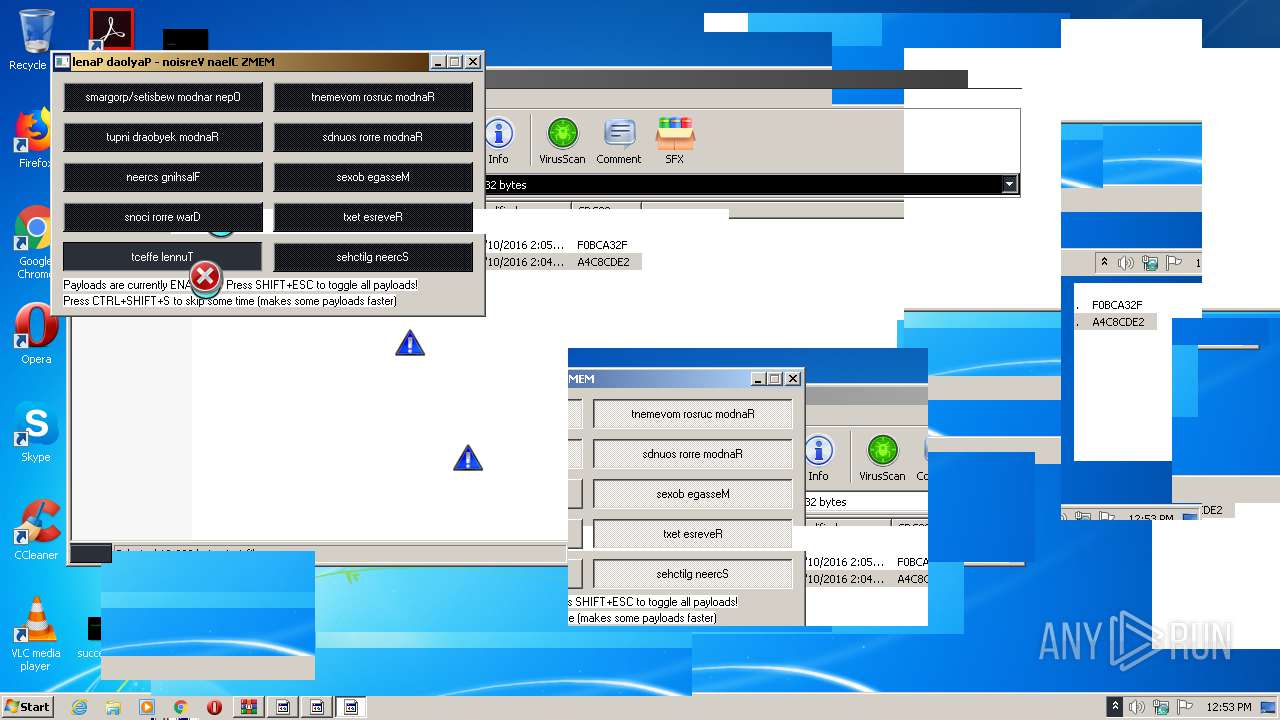
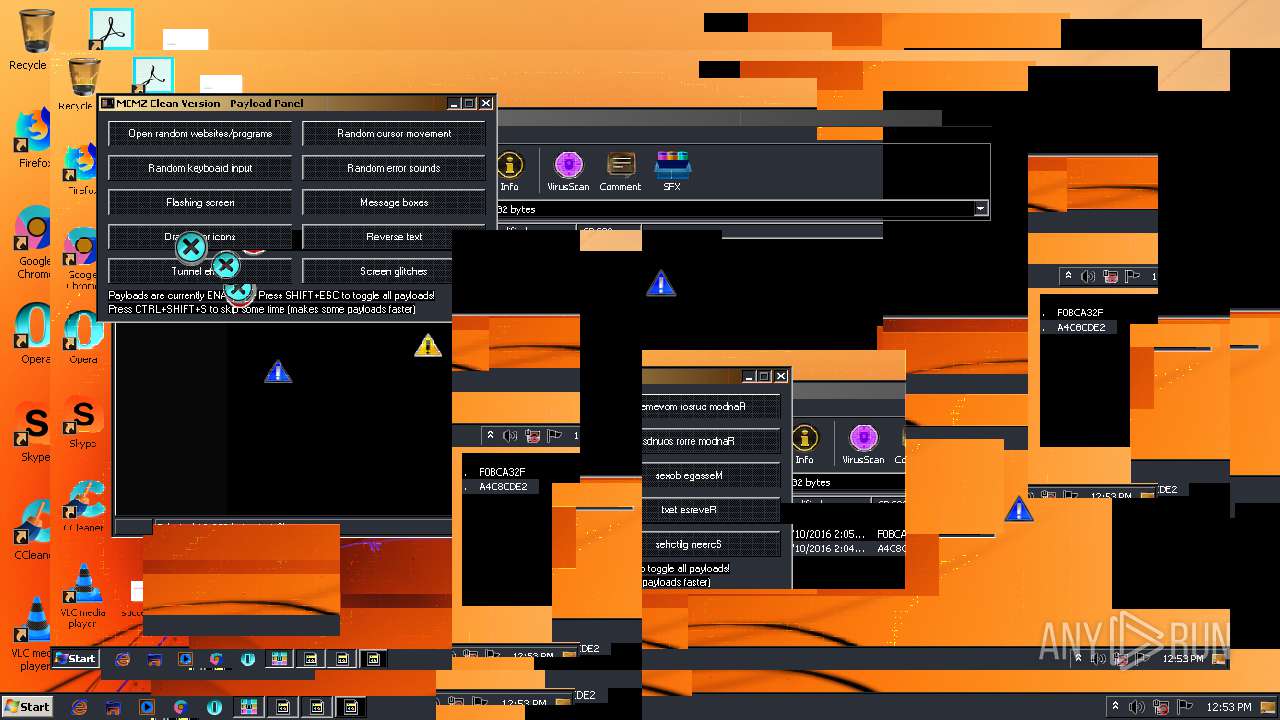
| Verdict: | Suspicious activity |
| Analysis date: | June 09, 2020, 11:52:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 8F40AB355CE87D20B87DE8B224242BFC |
| SHA1: | 15FE66ECED37A3A90821464702725E408644AF77 |
| SHA256: | 2F1C3F37C6468EBB385731AE5867A7A142EBD58CBB6791F3208A19504CC7E822 |
| SSDEEP: | 384:xxSNTiX51gXaRlSVVaFSM5Ut8fw+WO9CNf:xxSwXLgG8VVaFSMet8KOef |
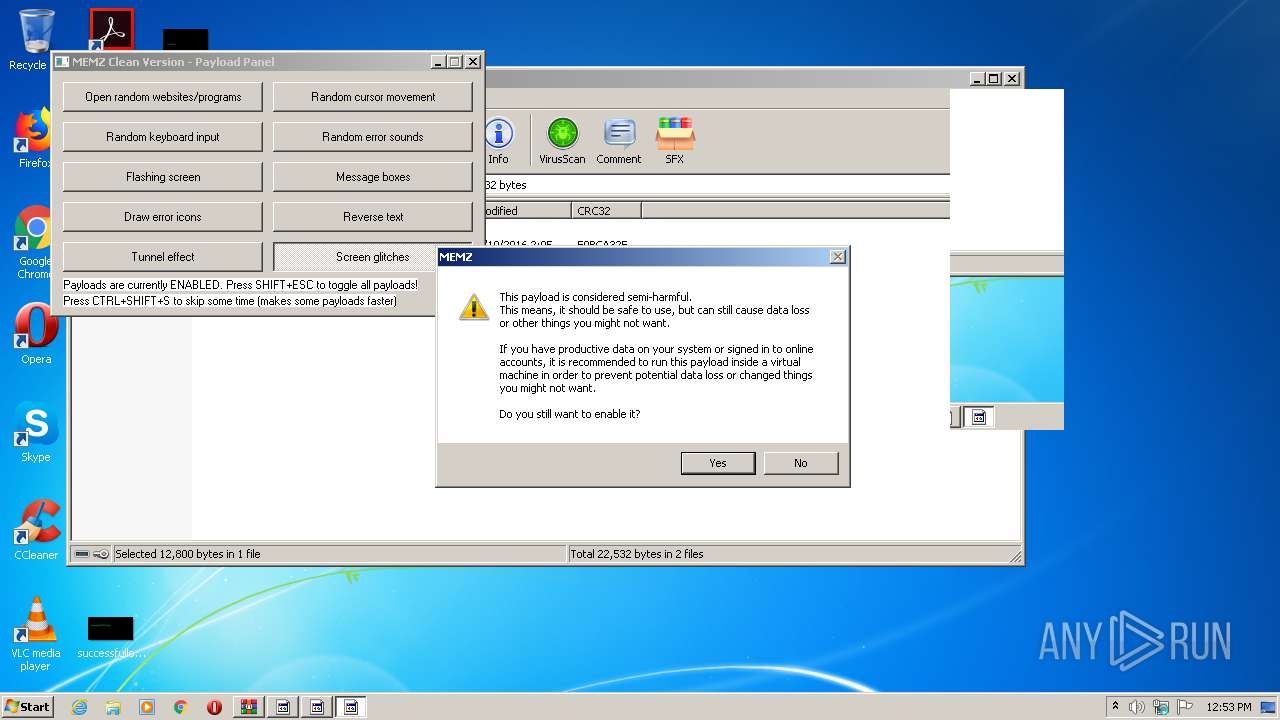
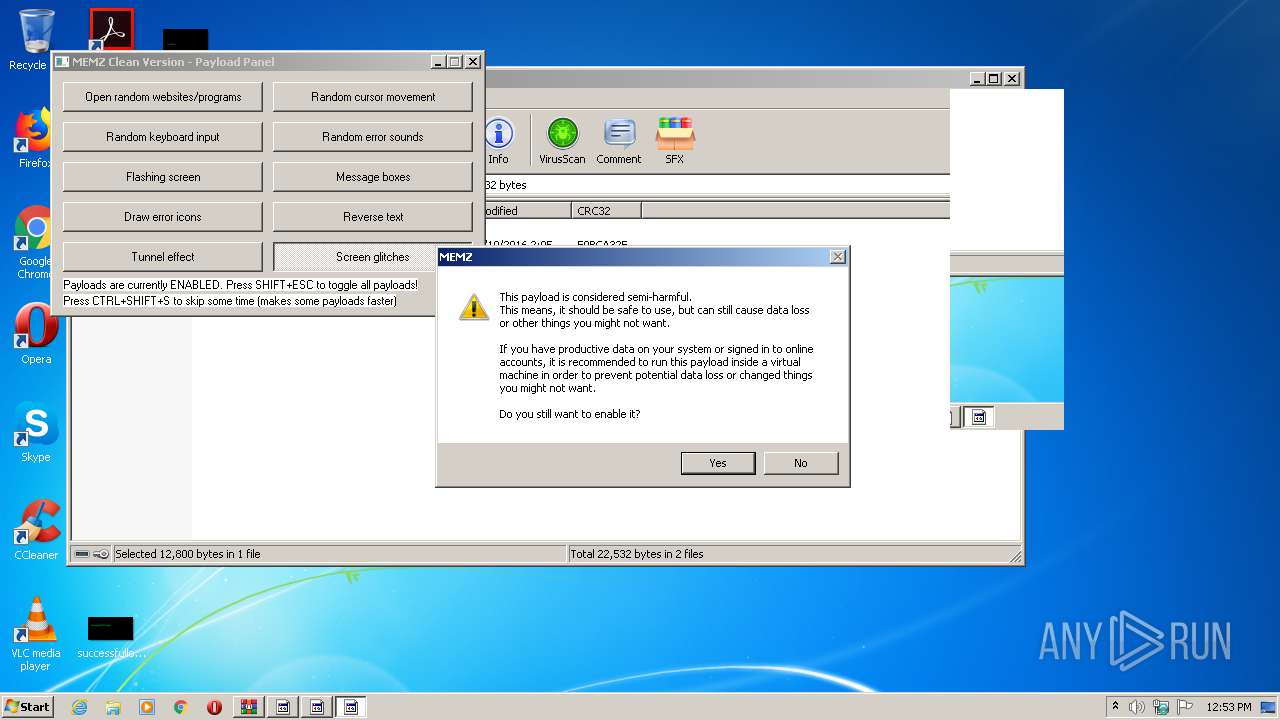
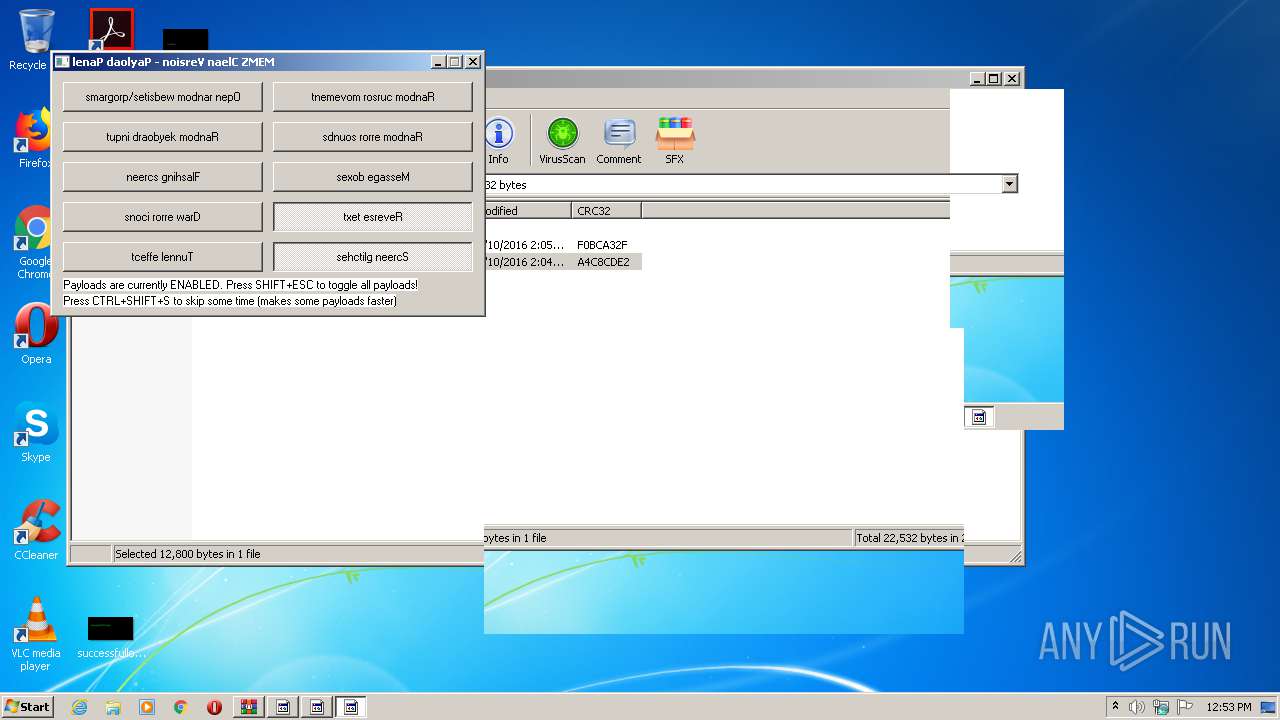
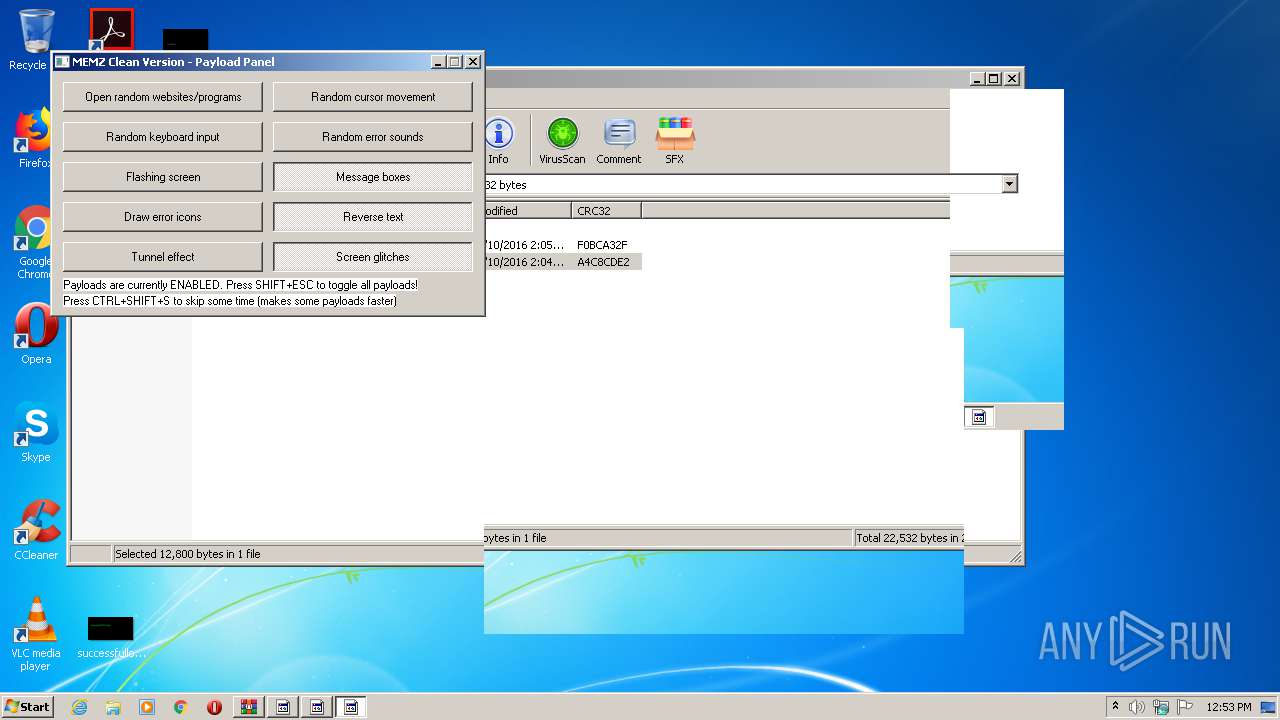
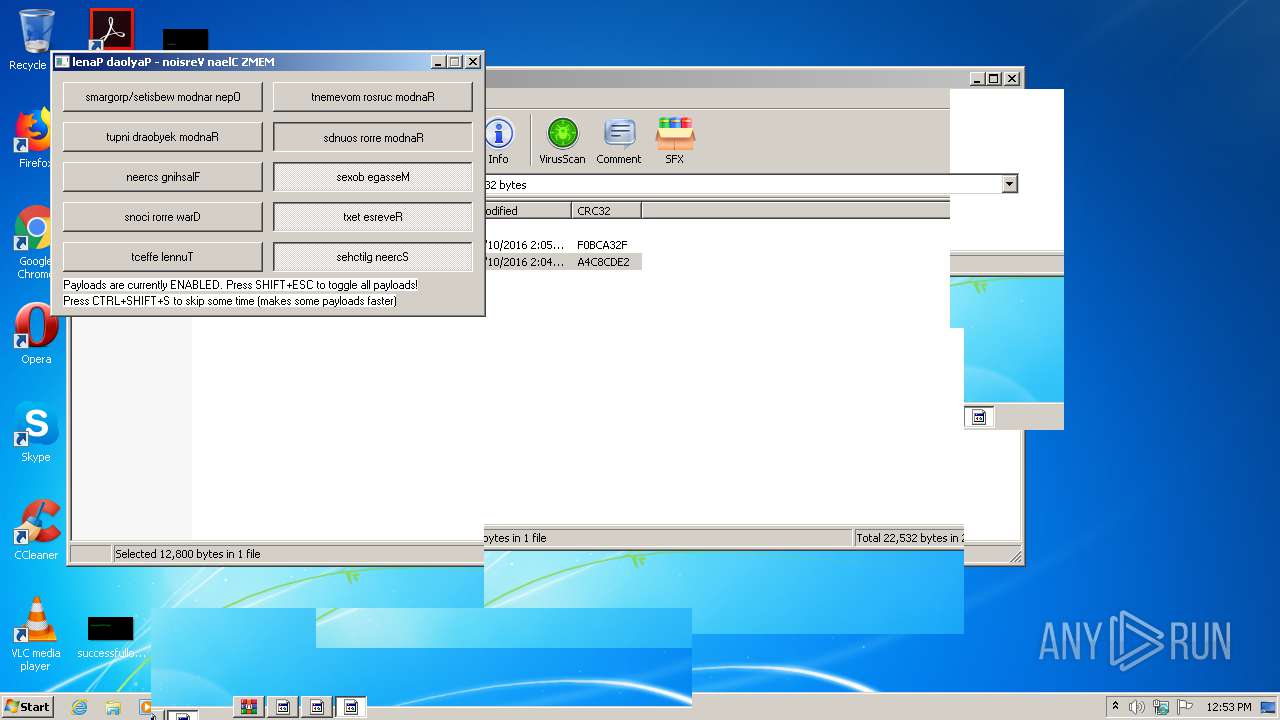
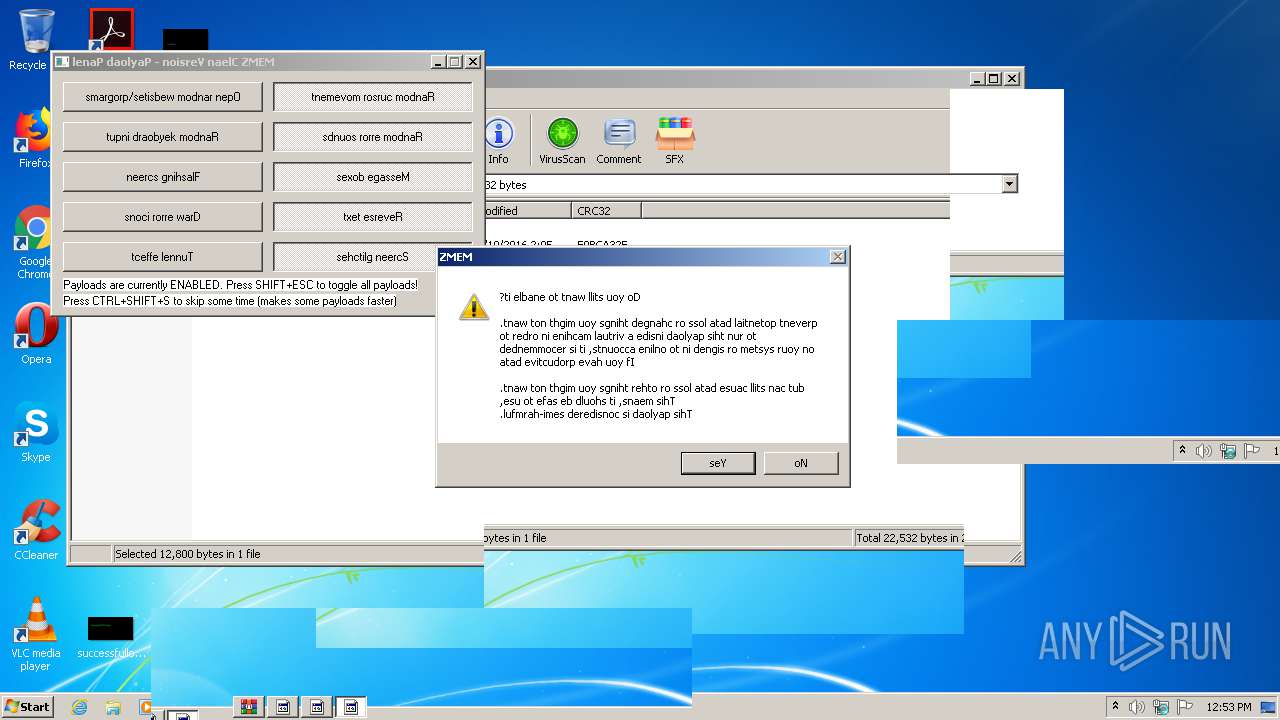
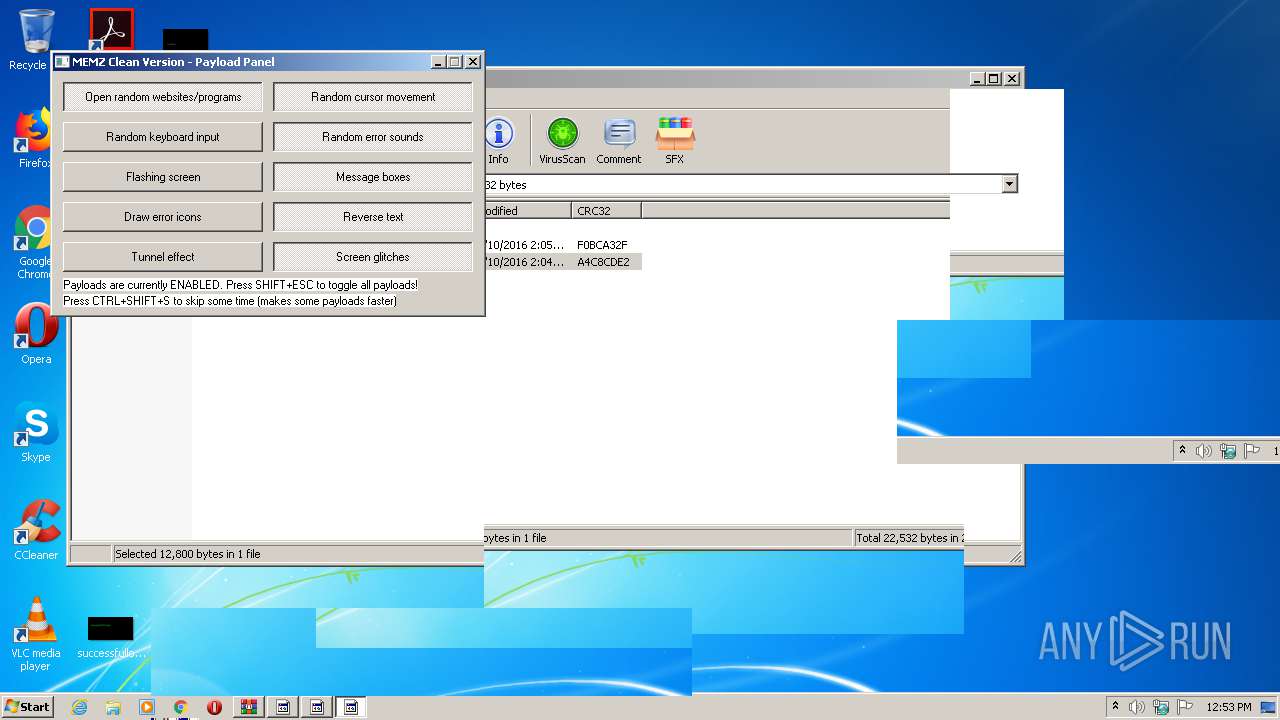
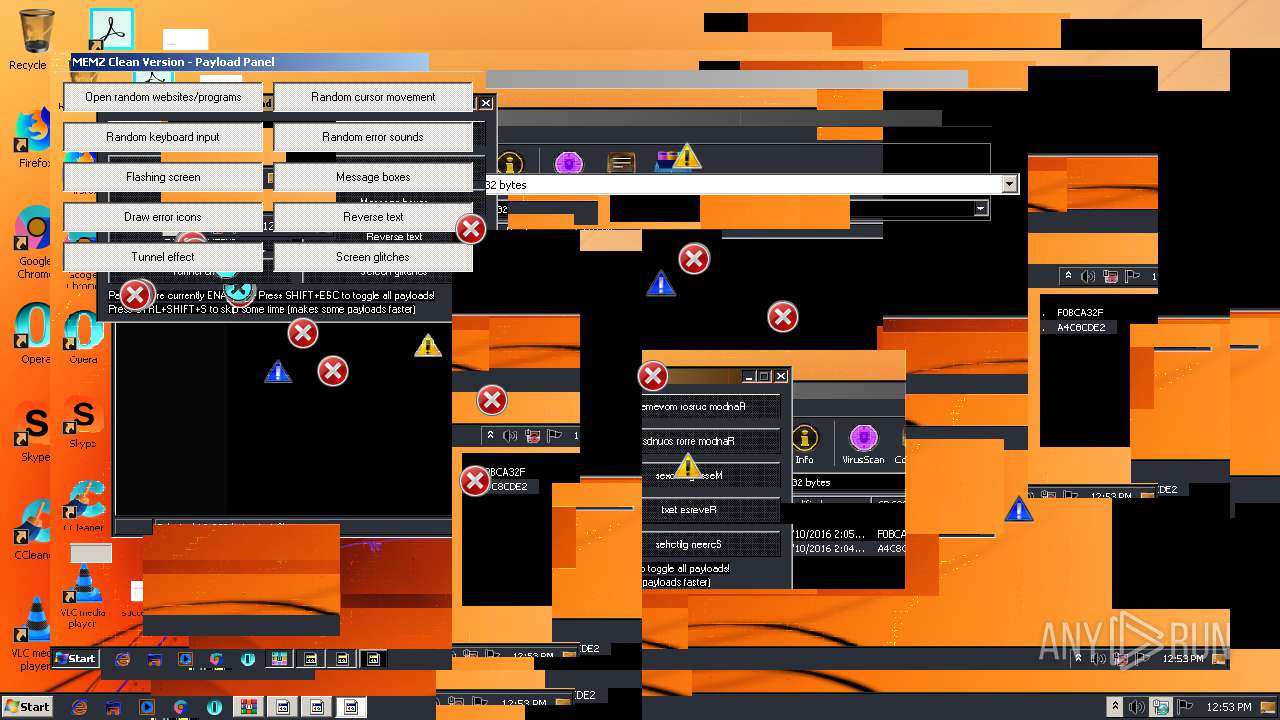
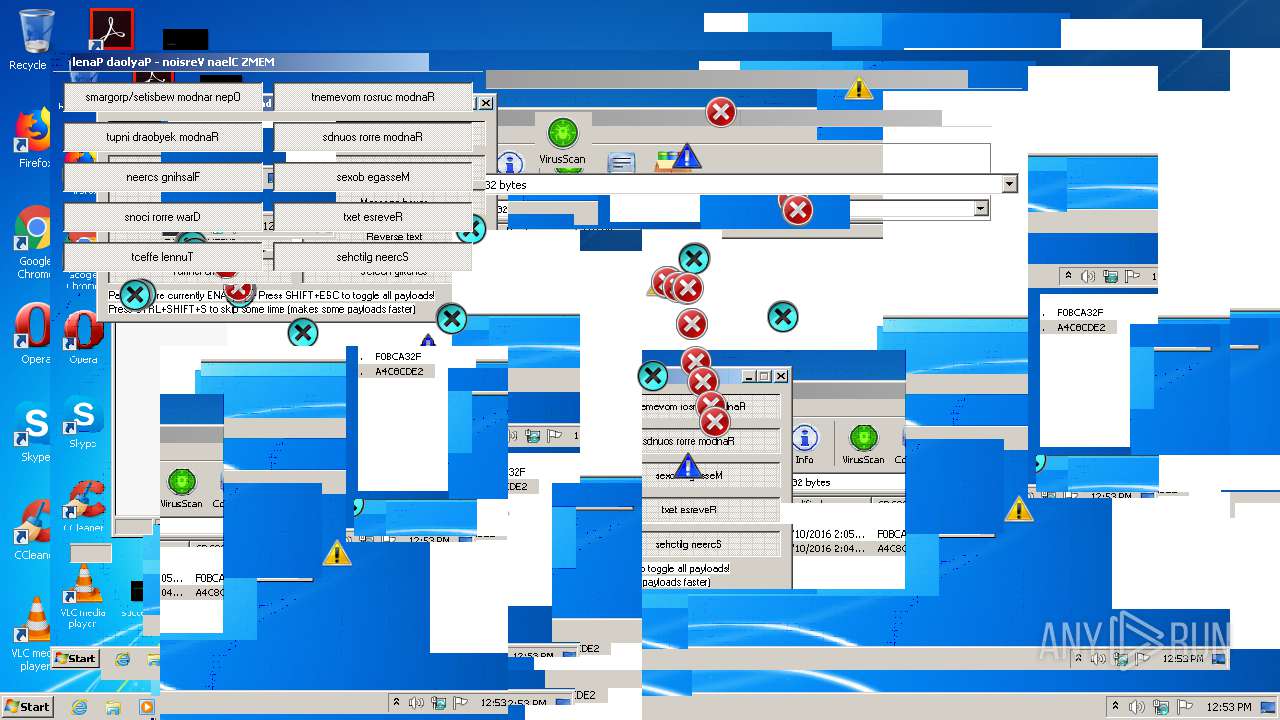
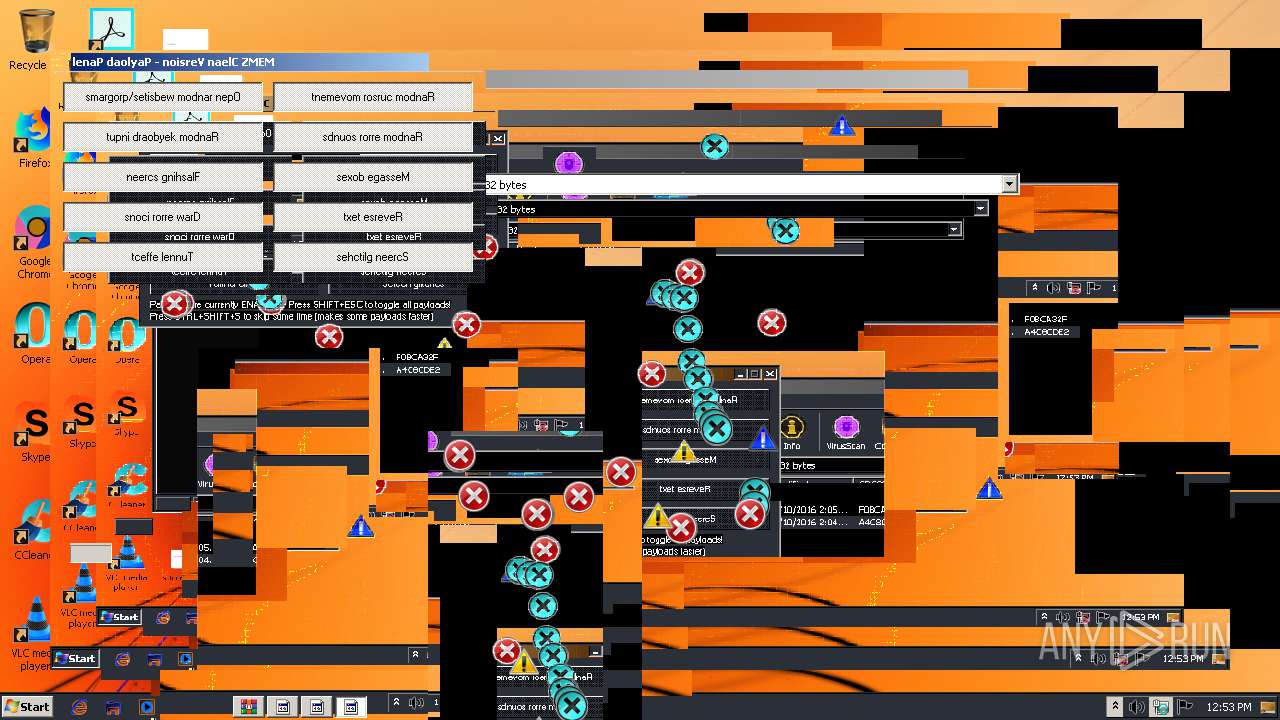
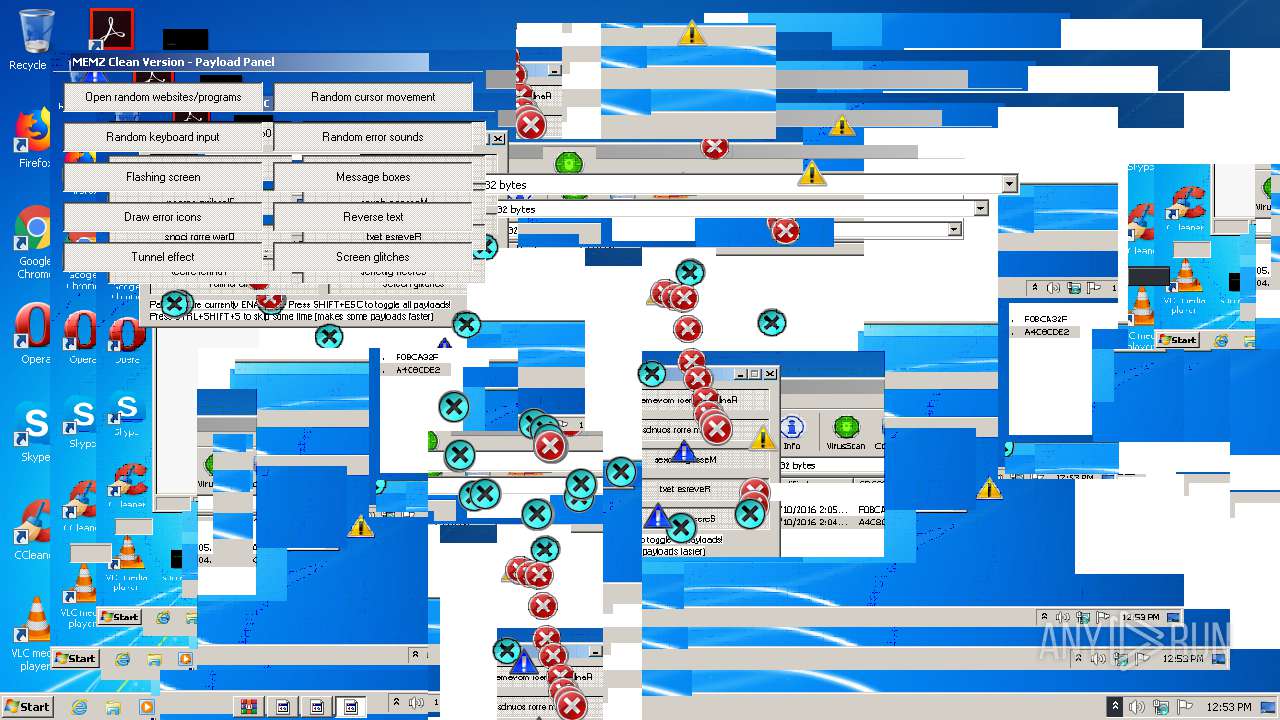
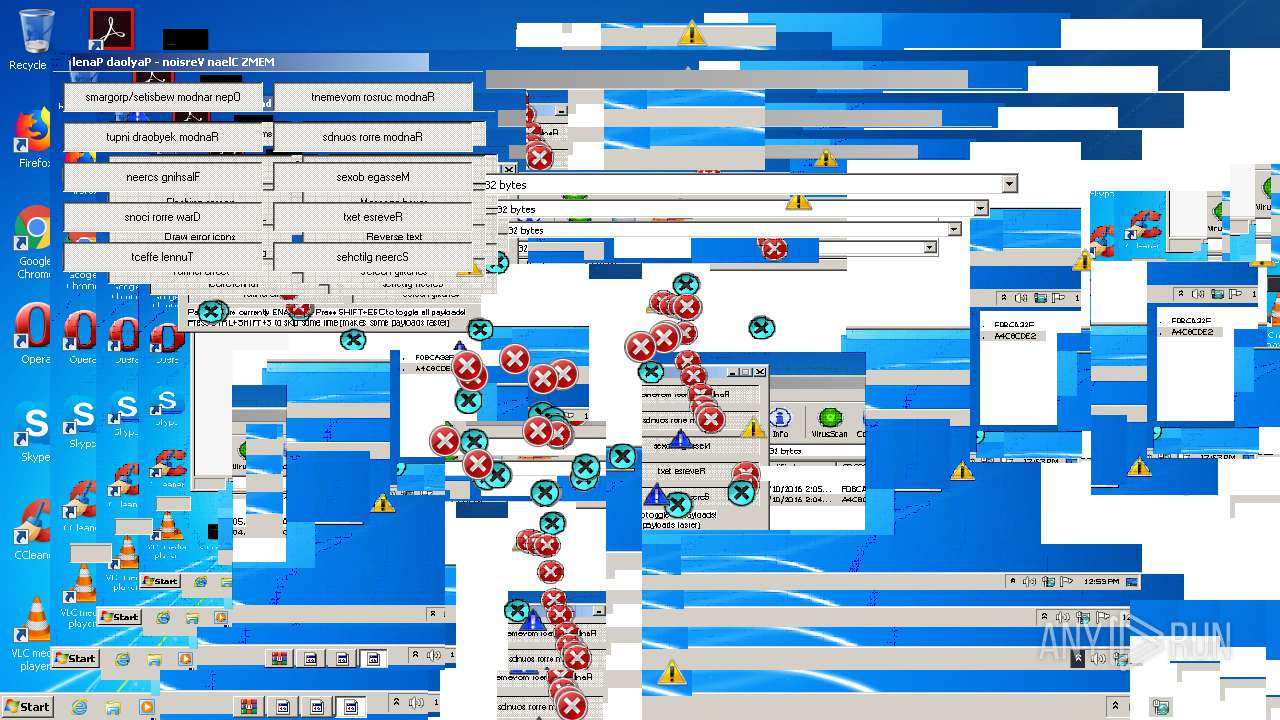
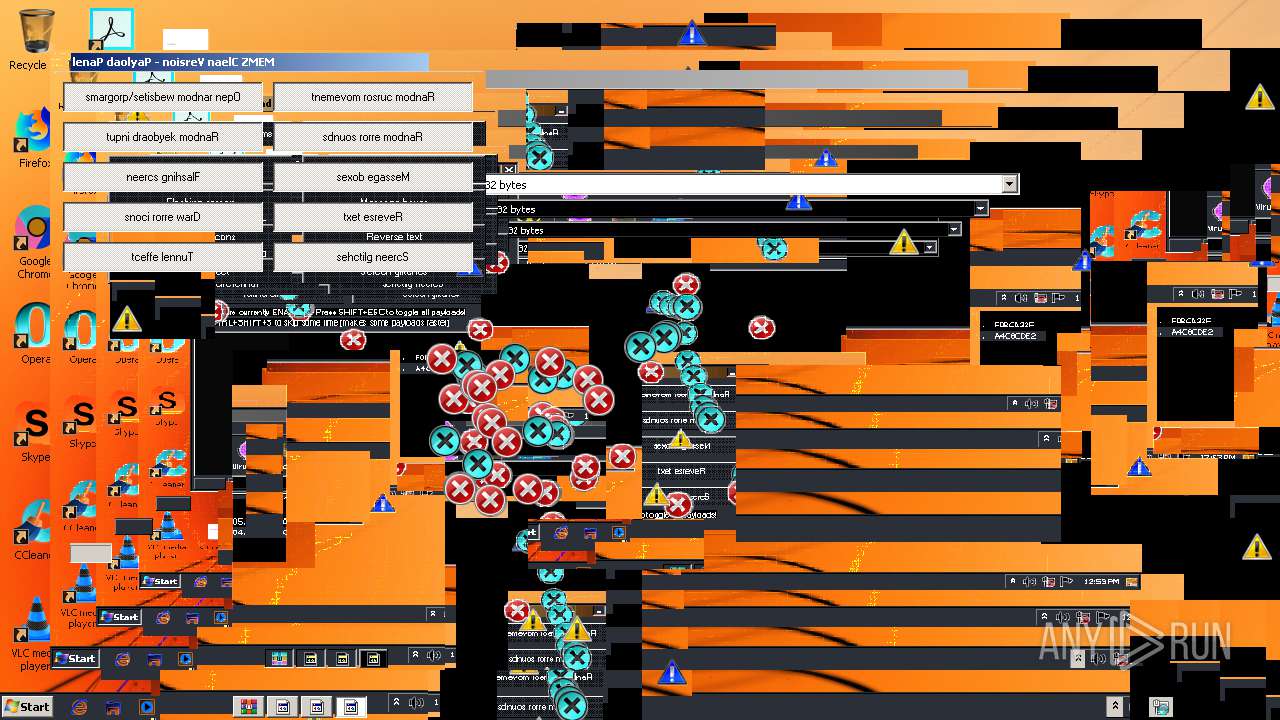
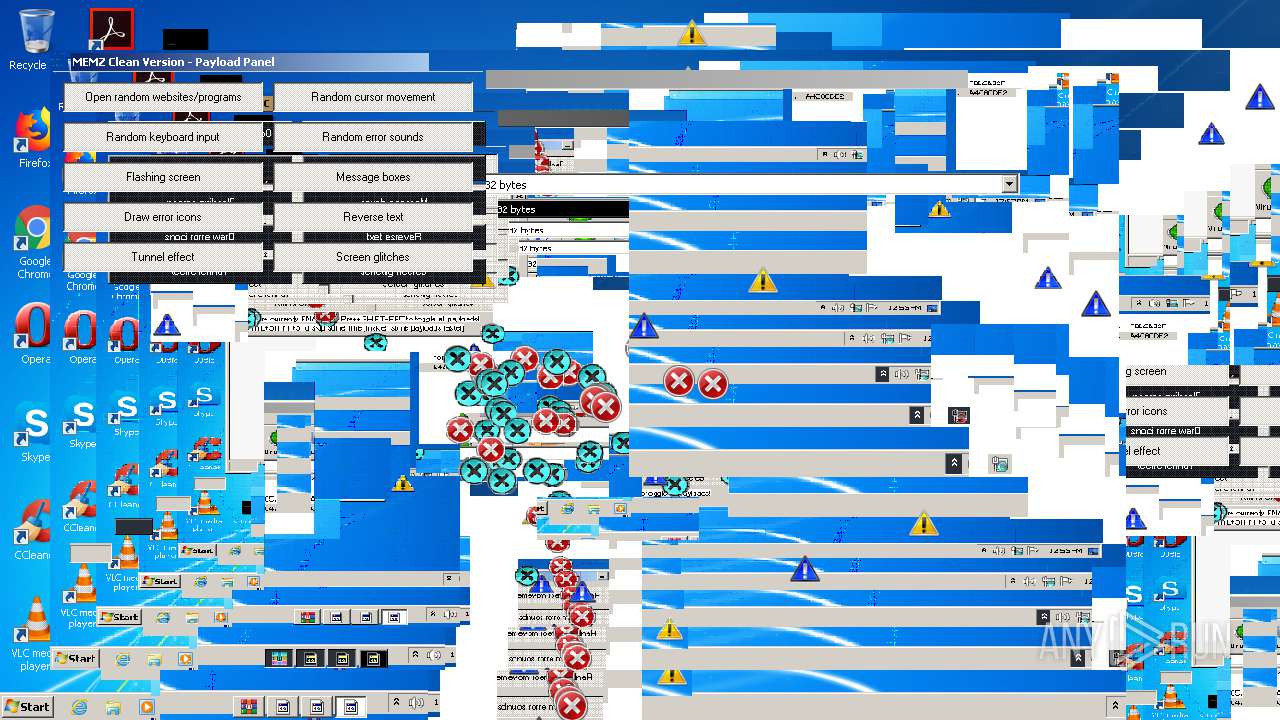
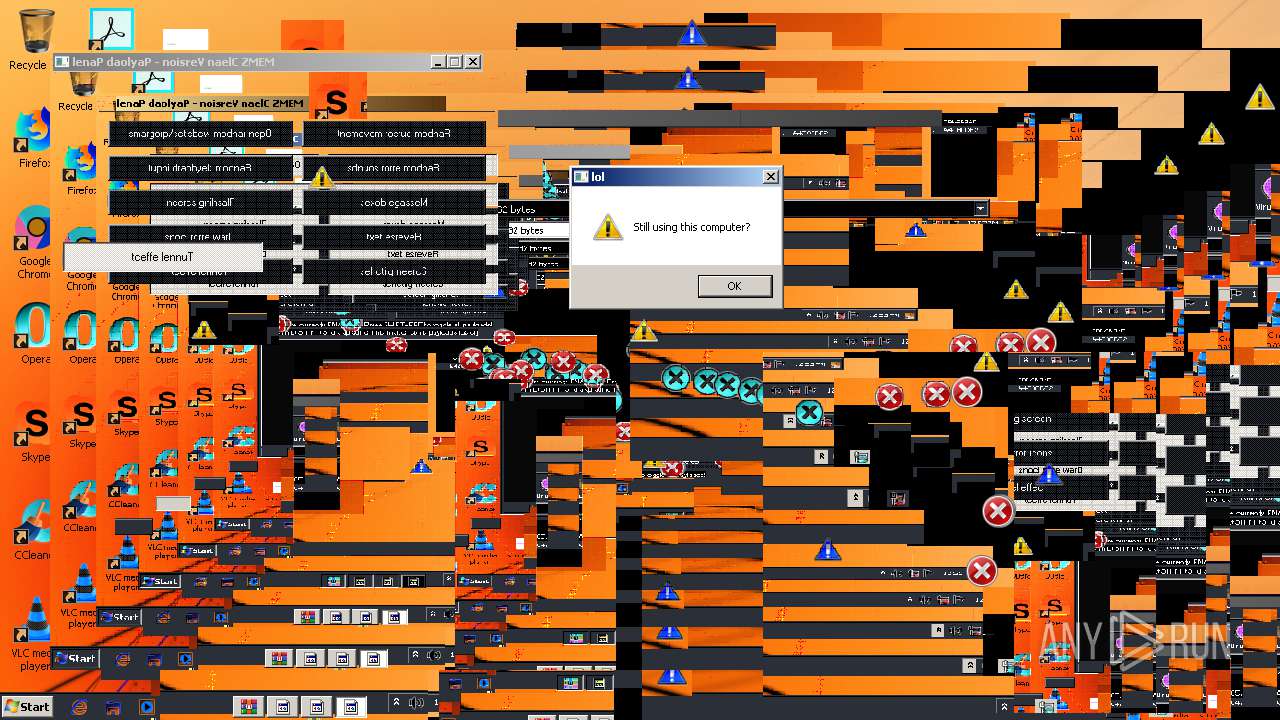
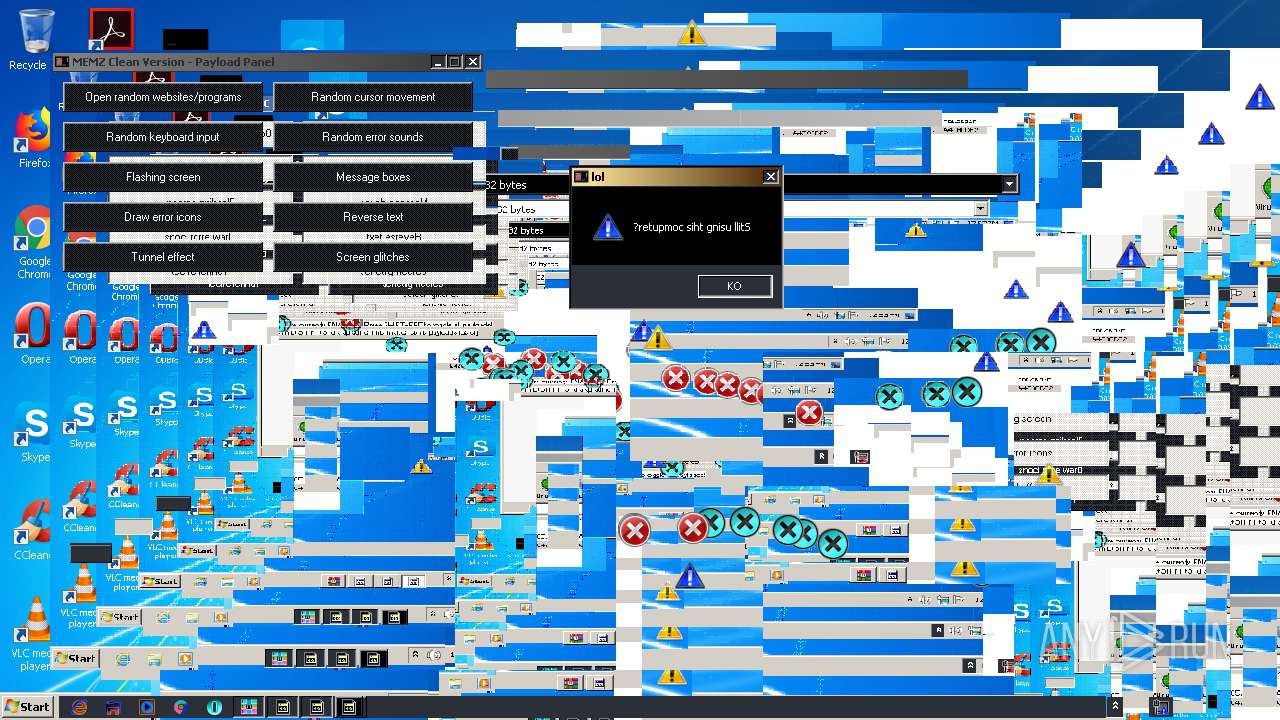
MALICIOUS
Application was dropped or rewritten from another process
- MEMZ-Clean.exe (PID: 3492)
- MEMZ-Clean.exe (PID: 2348)
- MEMZ.exe (PID: 2140)
SUSPICIOUS
Executable content was dropped or overwritten
- cscript.exe (PID: 3544)
- WinRAR.exe (PID: 2904)
Executes scripts
- cmd.exe (PID: 2772)
Creates files in the user directory
- cscript.exe (PID: 3544)
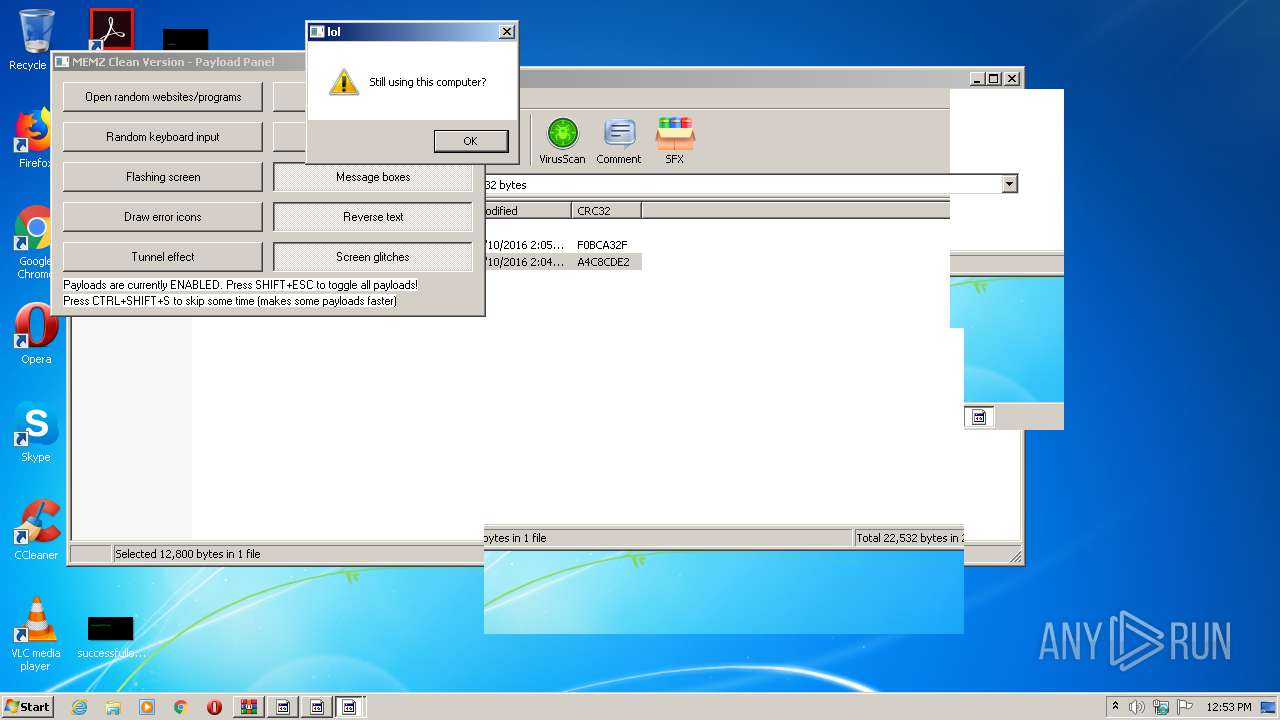
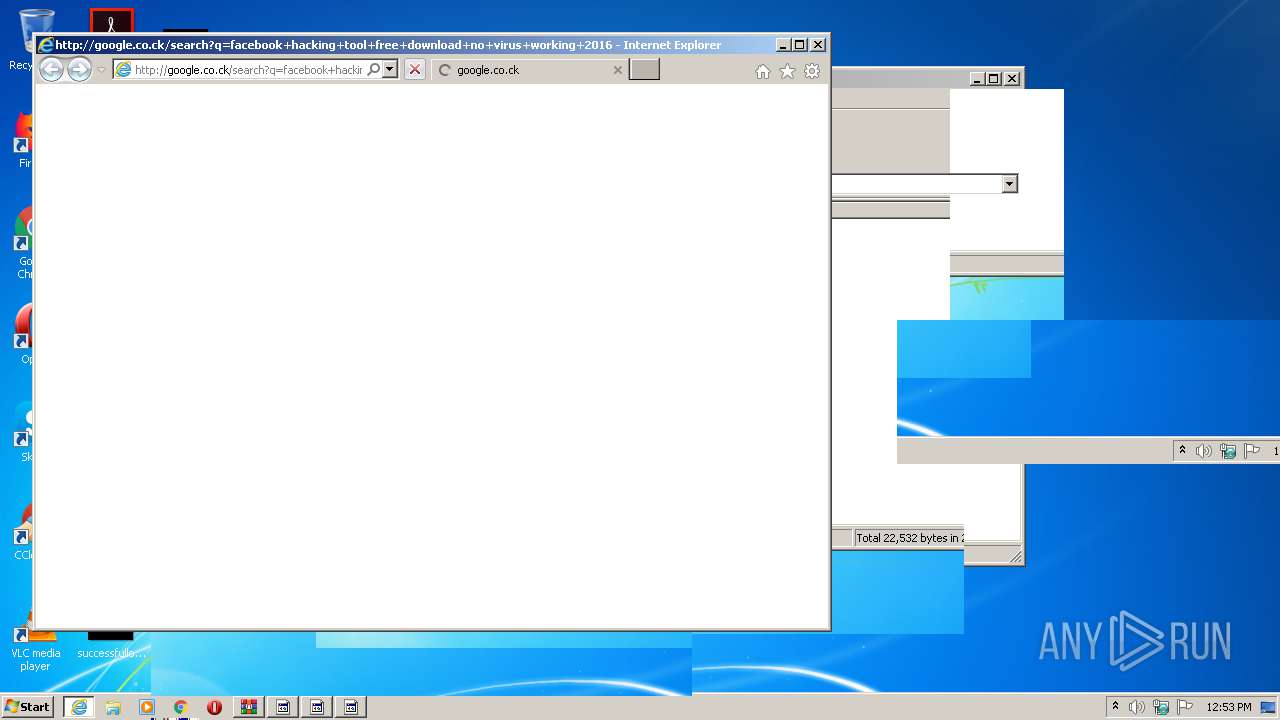
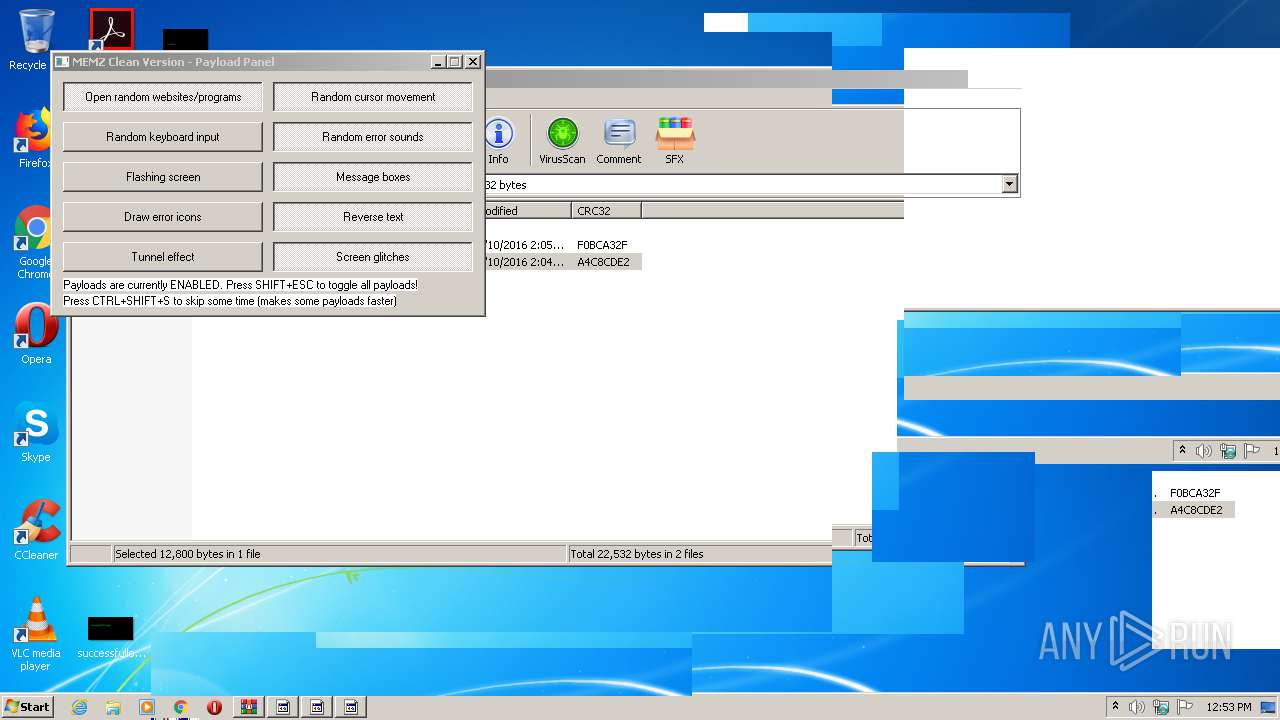
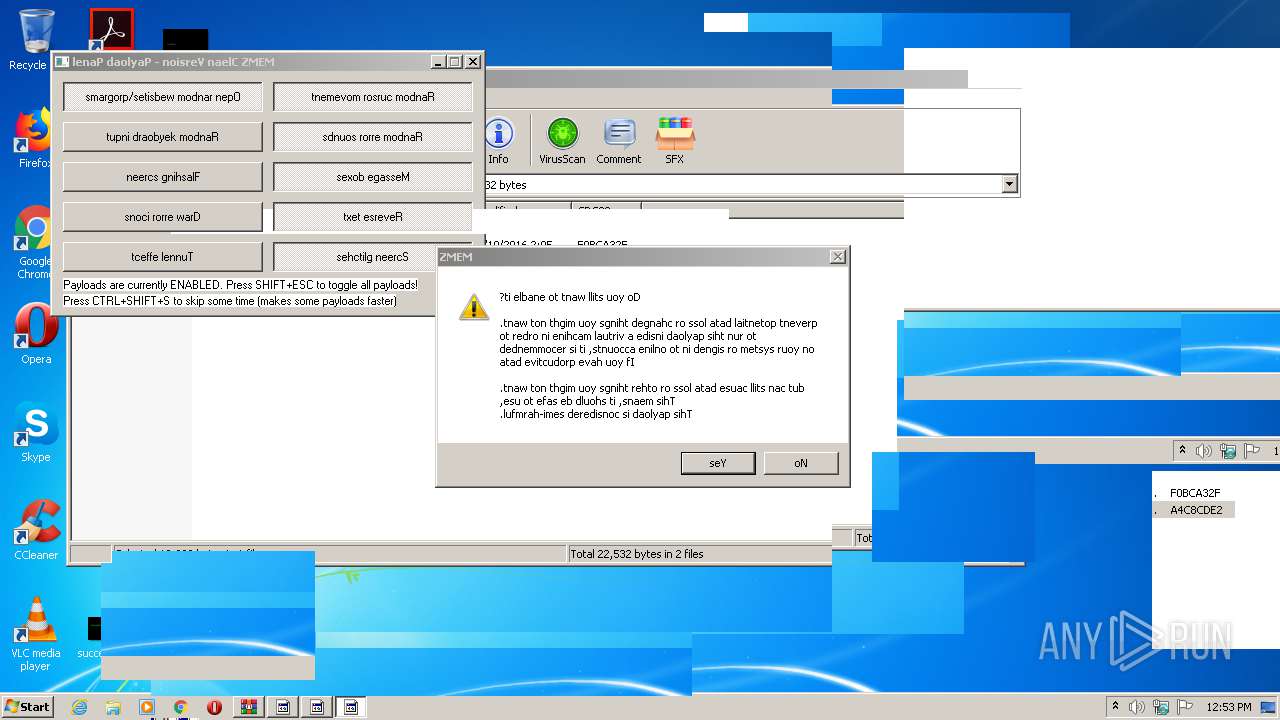
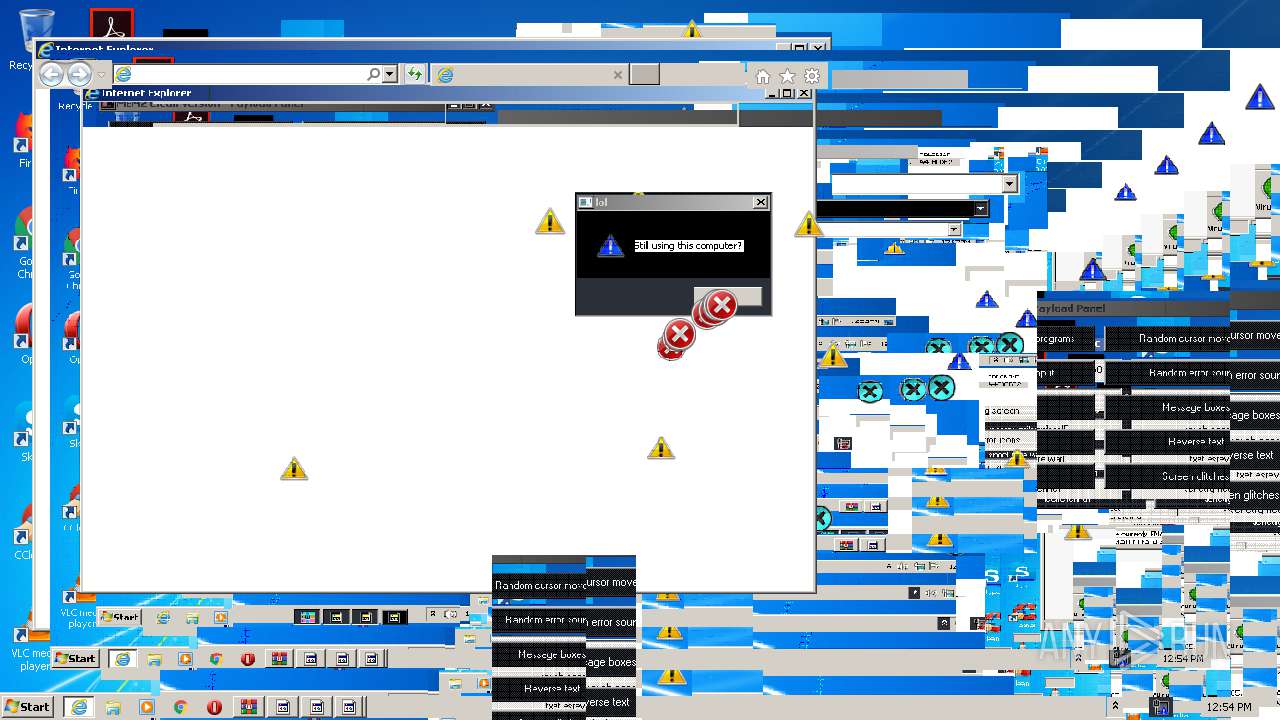
Starts Internet Explorer
- MEMZ-Clean.exe (PID: 2348)
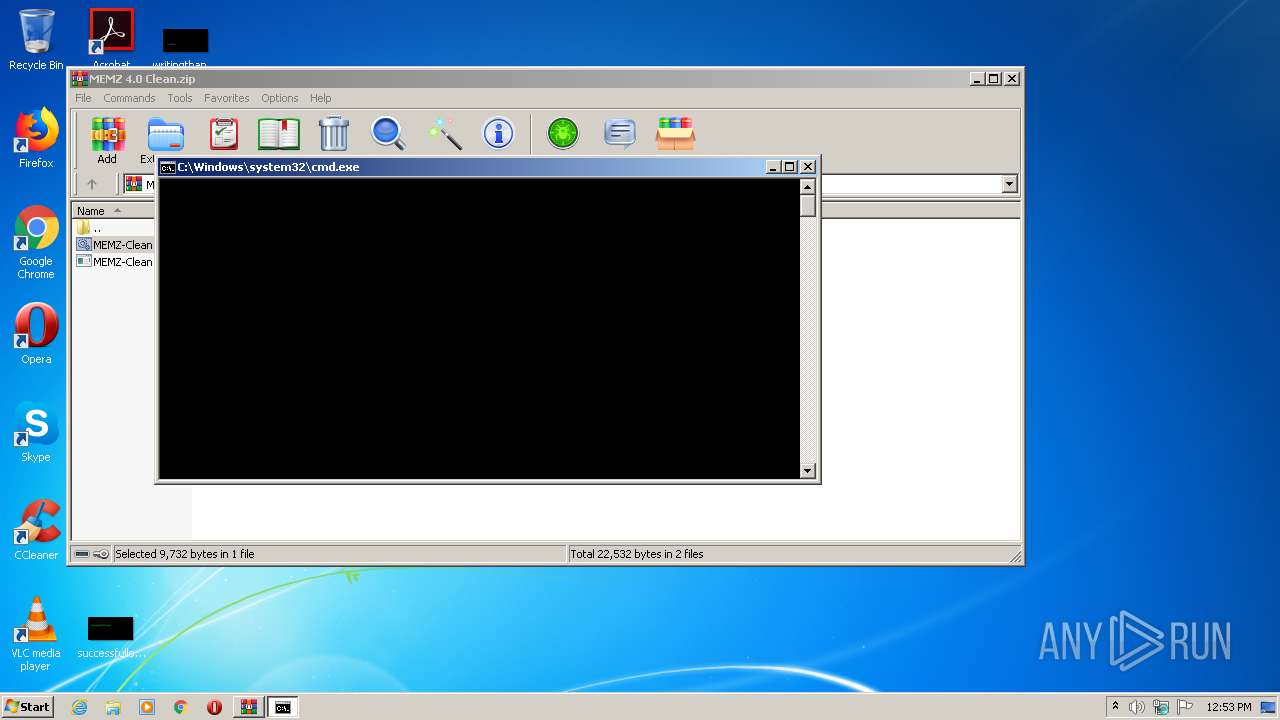
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 2904)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2460)
- iexplore.exe (PID: 2452)
- iexplore.exe (PID: 3792)
- iexplore.exe (PID: 3484)
Changes internet zones settings
- iexplore.exe (PID: 2452)
- iexplore.exe (PID: 3792)
Application launched itself
- iexplore.exe (PID: 3792)
- iexplore.exe (PID: 2452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2016:07:10 14:05:09 |
| ZipCRC: | 0xf0bca32f |
| ZipCompressedSize: | 6708 |
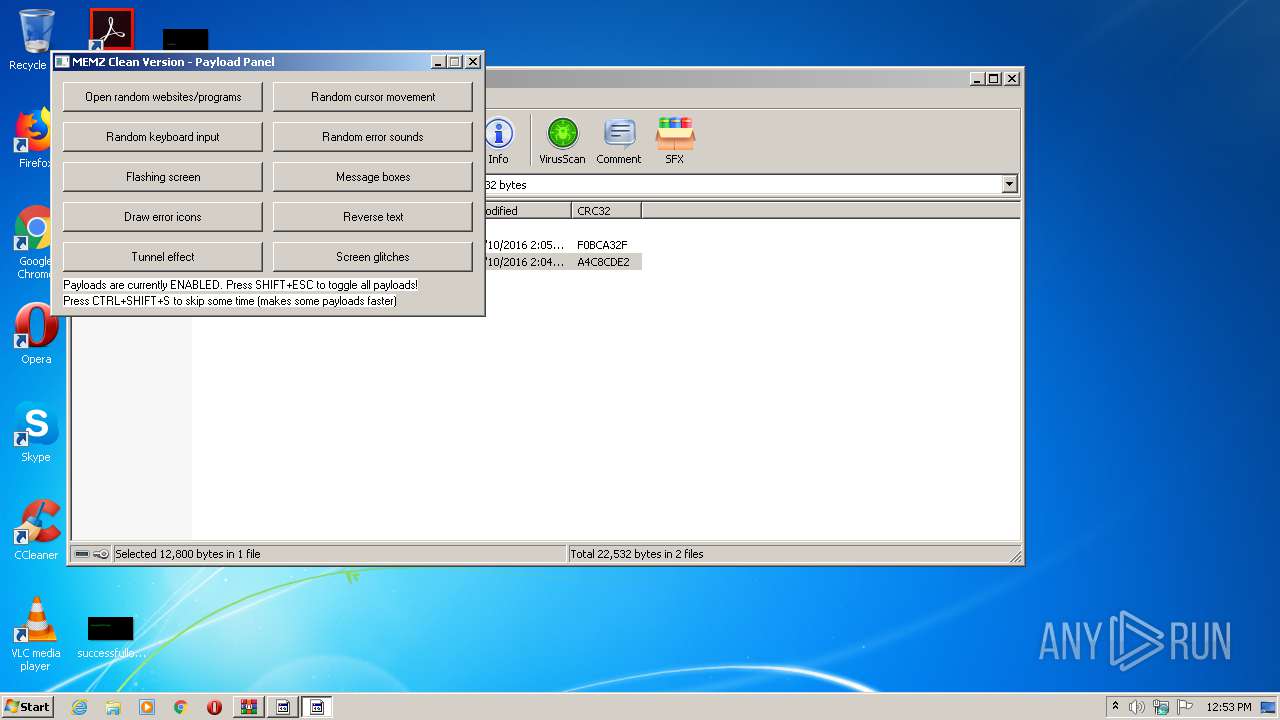
| ZipUncompressedSize: | 9732 |
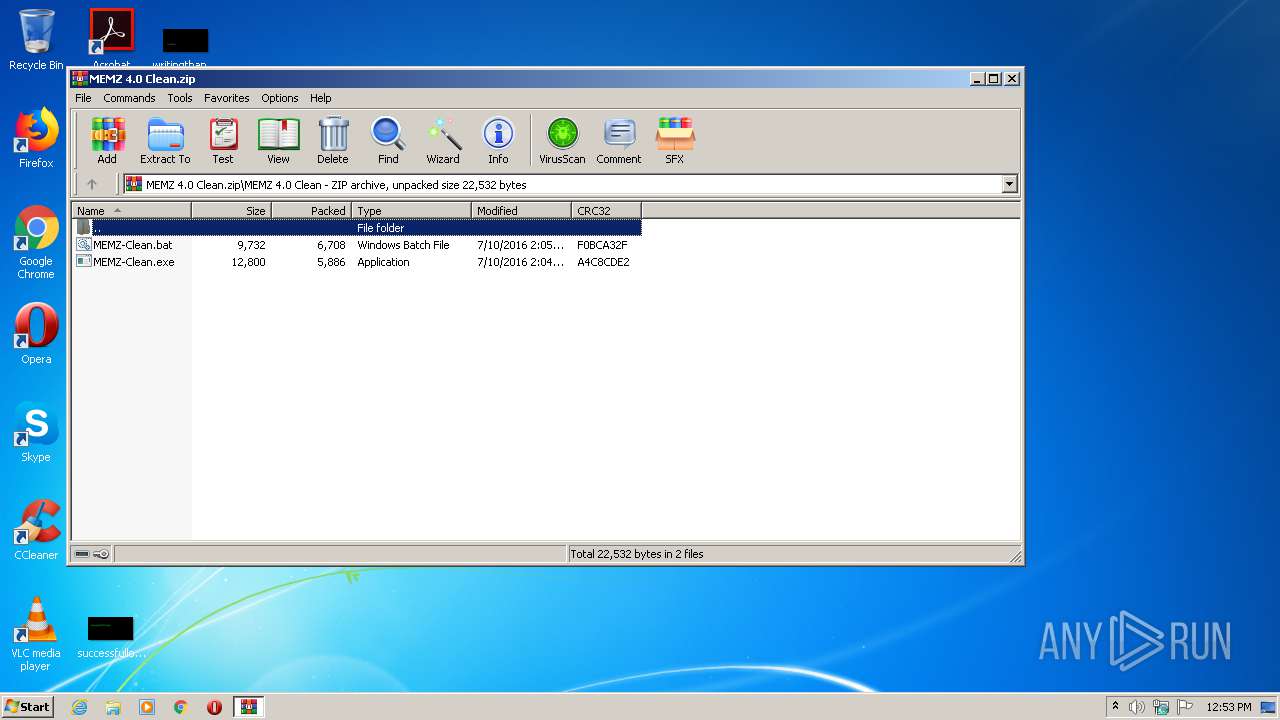
| ZipFileName: | MEMZ 4.0 Clean/MEMZ-Clean.bat |
Total processes
44
Monitored processes
10
Malicious processes
0
Suspicious processes
2
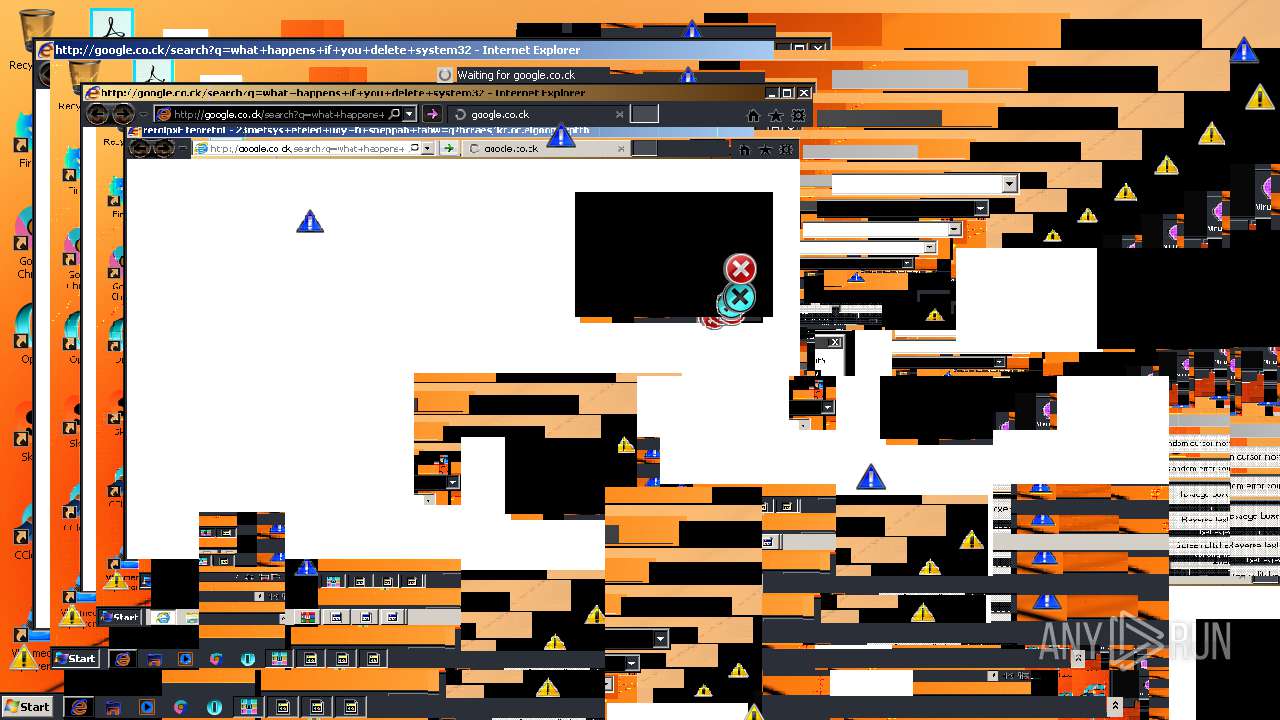
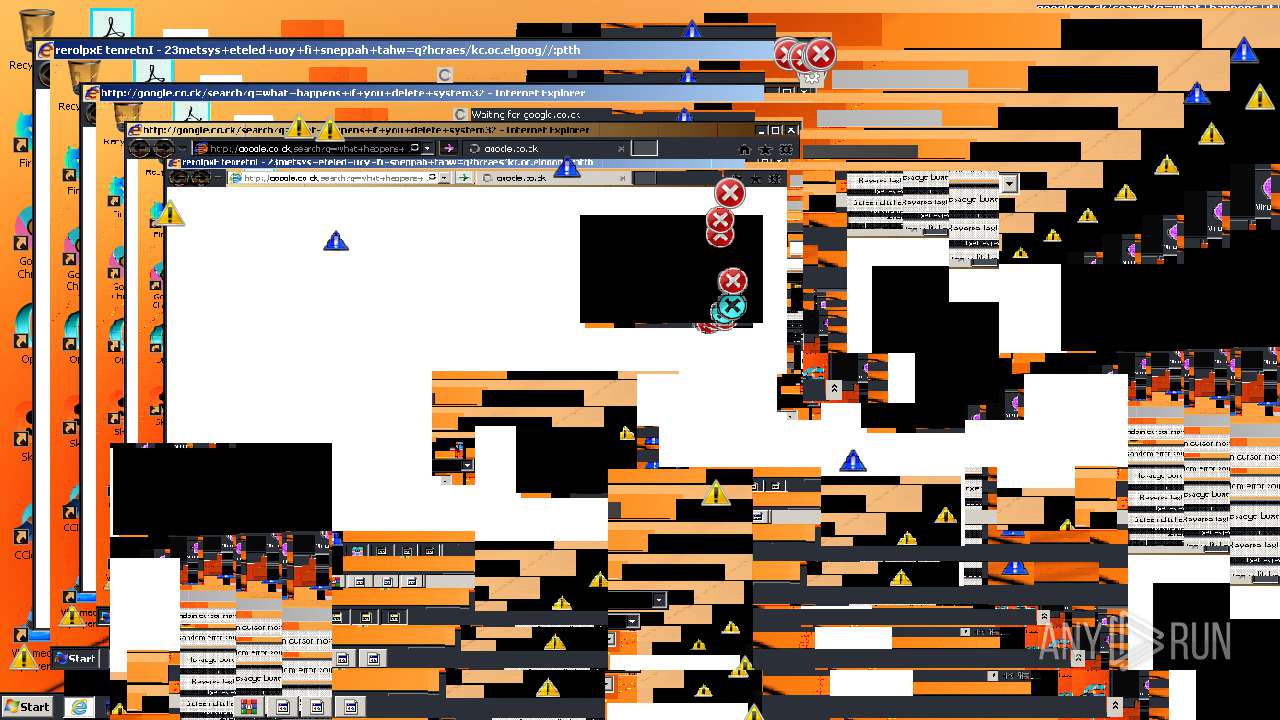
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2140 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" | C:\Users\admin\AppData\Roaming\MEMZ.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2348 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2904.43516\MEMZ 4.0 Clean\MEMZ-Clean.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2904.43516\MEMZ 4.0 Clean\MEMZ-Clean.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
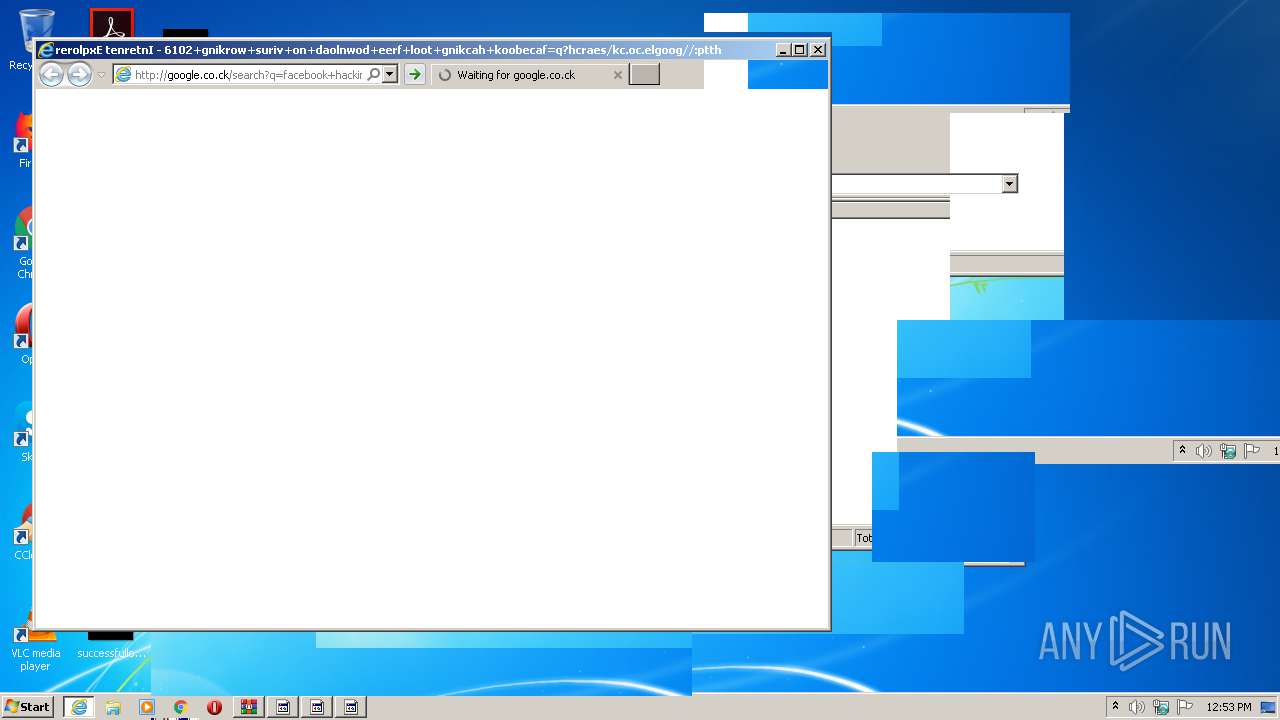
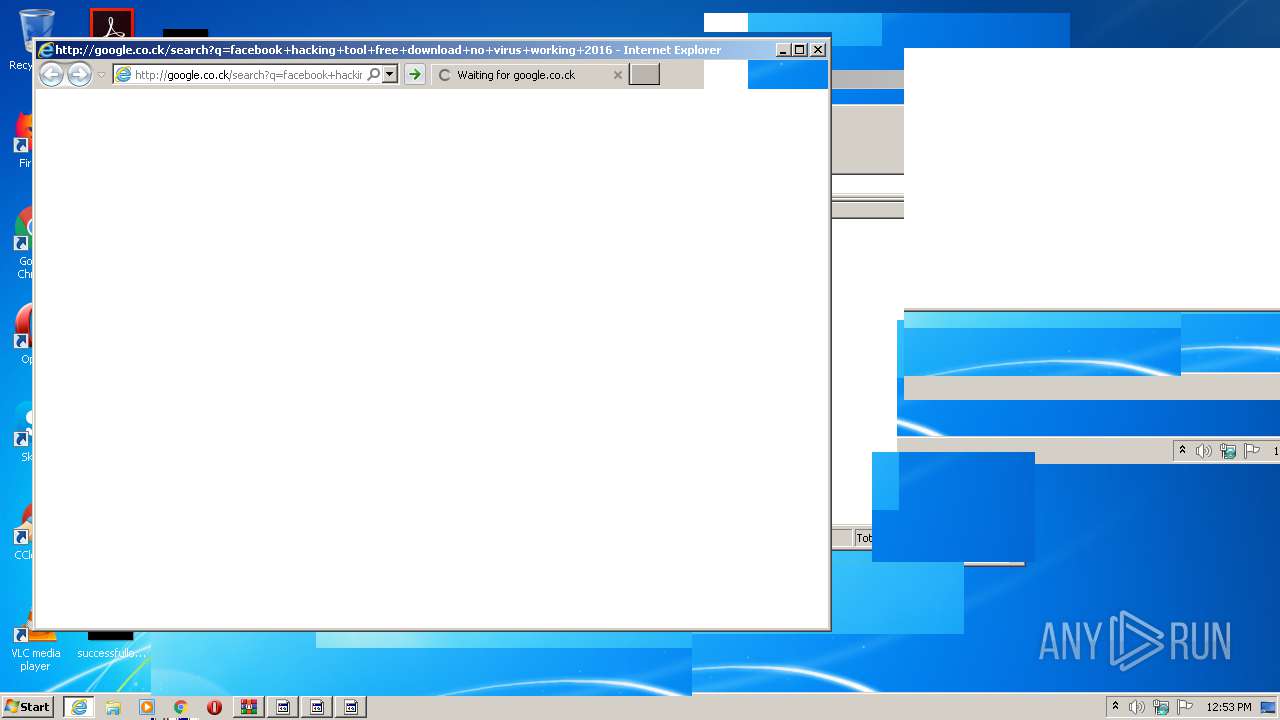
| 2452 | "C:\Program Files\Internet Explorer\iexplore.exe" http://google.co.ck/search?q=facebook+hacking+tool+free+download+no+virus+working+2016 | C:\Program Files\Internet Explorer\iexplore.exe | — | MEMZ-Clean.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2452 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2772 | cmd /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa2904.42647\MEMZ-Clean.bat" " | C:\Windows\system32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2904 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\MEMZ 4.0 Clean.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3484 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3792 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3492 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2904.43260\MEMZ 4.0 Clean\MEMZ-Clean.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2904.43260\MEMZ 4.0 Clean\MEMZ-Clean.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3544 | cscript x.js | C:\Windows\system32\cscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
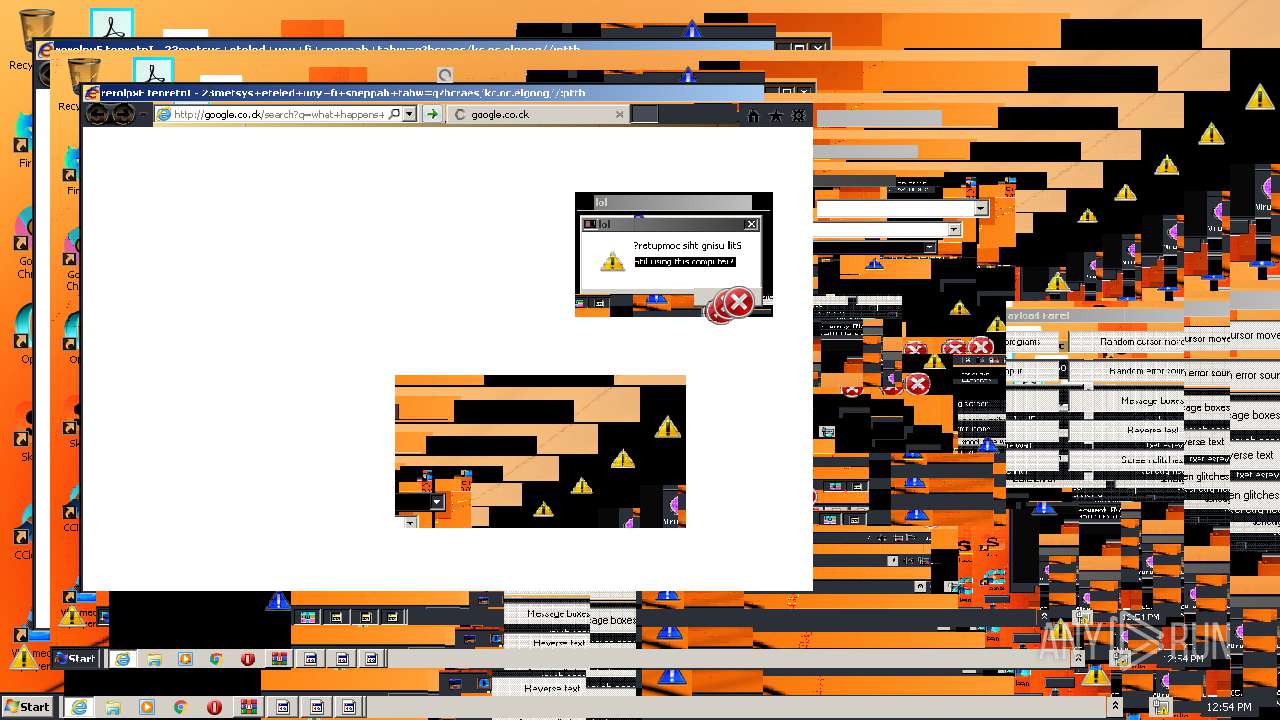
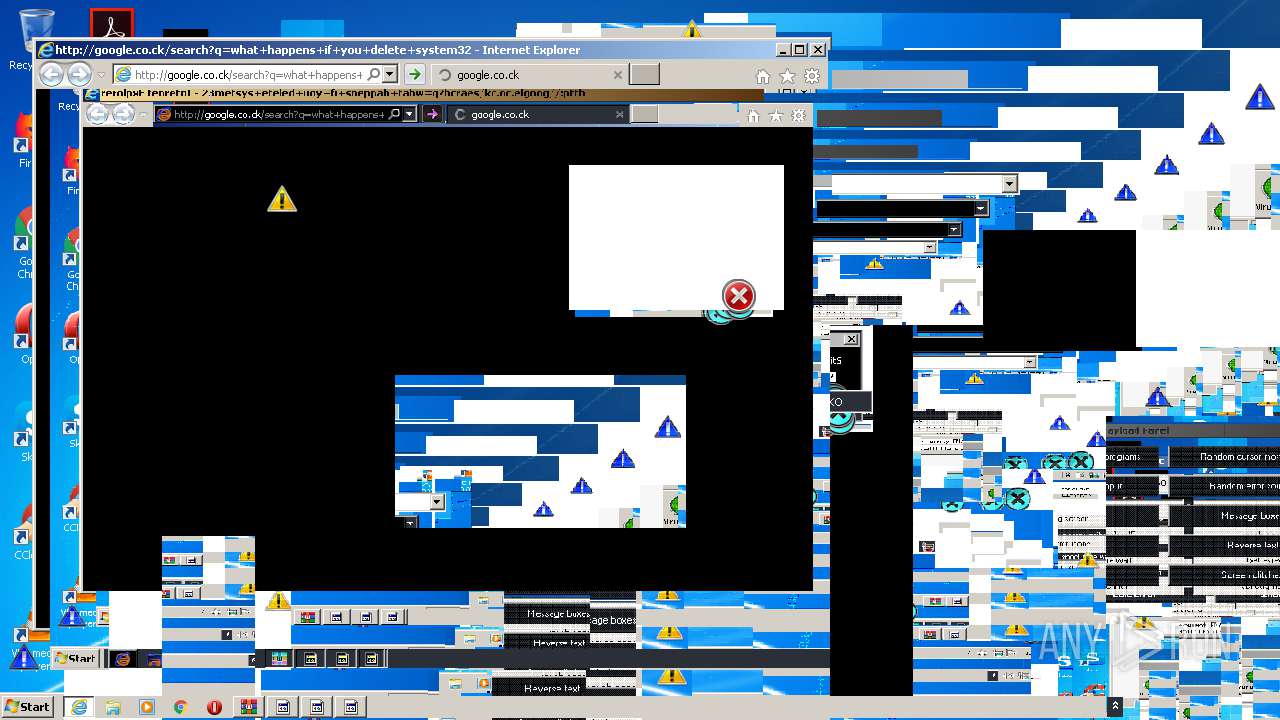
| 3792 | "C:\Program Files\Internet Explorer\iexplore.exe" http://google.co.ck/search?q=what+happens+if+you+delete+system32 | C:\Program Files\Internet Explorer\iexplore.exe | — | MEMZ-Clean.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 229
Read events
1 128
Write events
97
Delete events
4
Modification events
| (PID) Process: | (2904) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2904) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2904) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2904) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2904) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\MEMZ 4.0 Clean.zip | |||
| (PID) Process: | (2904) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2904) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2904) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2904) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2904) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\acppage.dll,-6002 |
Value: Windows Batch File | |||
Executable files
3
Suspicious files
3
Text files
107
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2452 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA28A7BFAC8C45DDC.TMP | — | |
MD5:— | SHA256:— | |||
| 2452 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB2D662BADE421430.TMP | — | |
MD5:— | SHA256:— | |||
| 2452 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB9A51FD847777BE6.TMP | — | |
MD5:— | SHA256:— | |||
| 2452 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{DB293CCE-AA47-11EA-AA5F-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2452 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF4A868570AF01F07C.TMP | — | |
MD5:— | SHA256:— | |||
| 2452 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{DB293CCC-AA47-11EA-AA5F-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2452 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{DB293CCF-AA47-11EA-AA5F-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 2772 | cmd.exe | C:\Users\admin\AppData\Local\Temp\x | text | |
MD5:— | SHA256:— | |||
| 3544 | cscript.exe | C:\Users\admin\AppData\Local\Temp\z.zip | compressed | |
MD5:D2EA024B943CAA1361833885B832D20B | SHA256:39DF3364A3AF6F7D360AA7E1345E27BEFC4BE960E0E7E7E060B20F3389B80E76 | |||
| 2452 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{42A7EDC2-DE02-11E9-92C0-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
6
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3484 | iexplore.exe | GET | 301 | 172.217.18.100:80 | http://google.co.ck/search?q=what+happens+if+you+delete+system32 | US | html | 265 b | whitelisted |
3484 | iexplore.exe | GET | 302 | 172.217.18.163:80 | http://www.google.co.ck/search?q=what+happens+if+you+delete+system32 | US | html | 281 b | whitelisted |
2460 | iexplore.exe | GET | — | 172.217.18.100:80 | http://google.co.ck/search?q=facebook+hacking+tool+free+download+no+virus+working+2016 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2460 | iexplore.exe | 172.217.18.100:80 | google.co.ck | Google Inc. | US | whitelisted |
3484 | iexplore.exe | 172.217.18.100:80 | google.co.ck | Google Inc. | US | whitelisted |
3484 | iexplore.exe | 172.217.18.163:80 | www.google.co.ck | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.co.ck |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.google.co.ck |
| whitelisted |