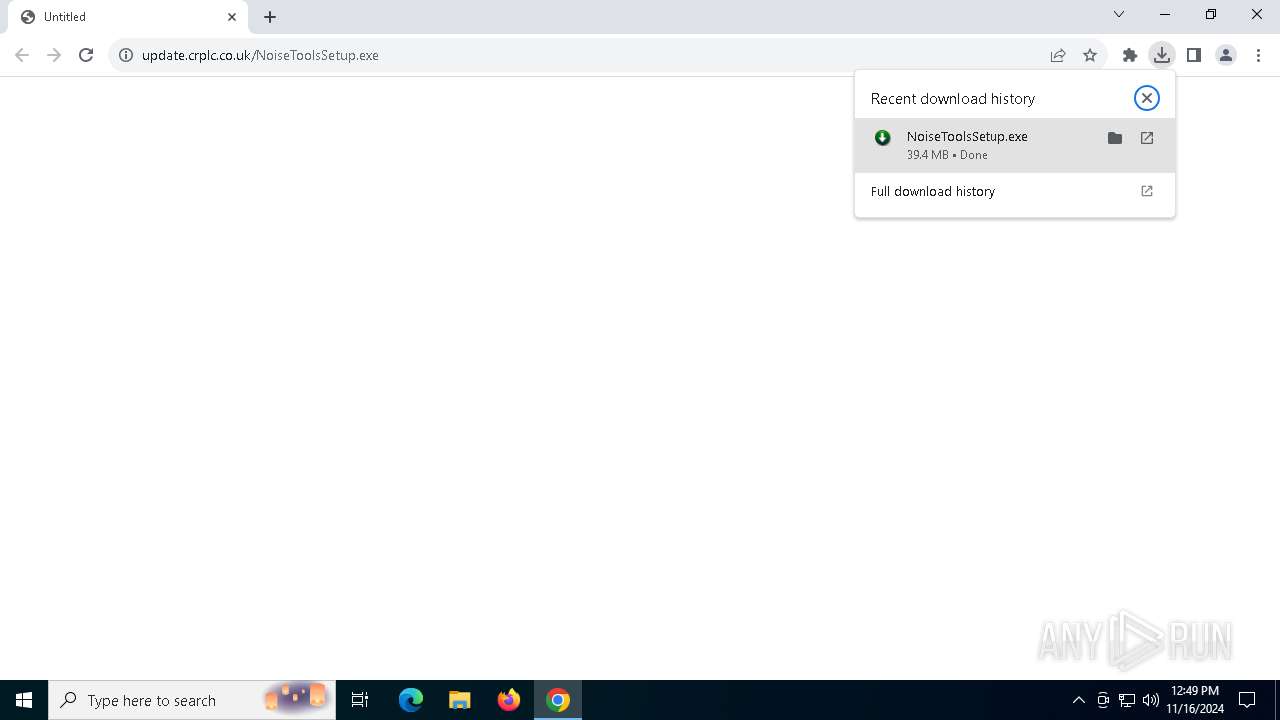
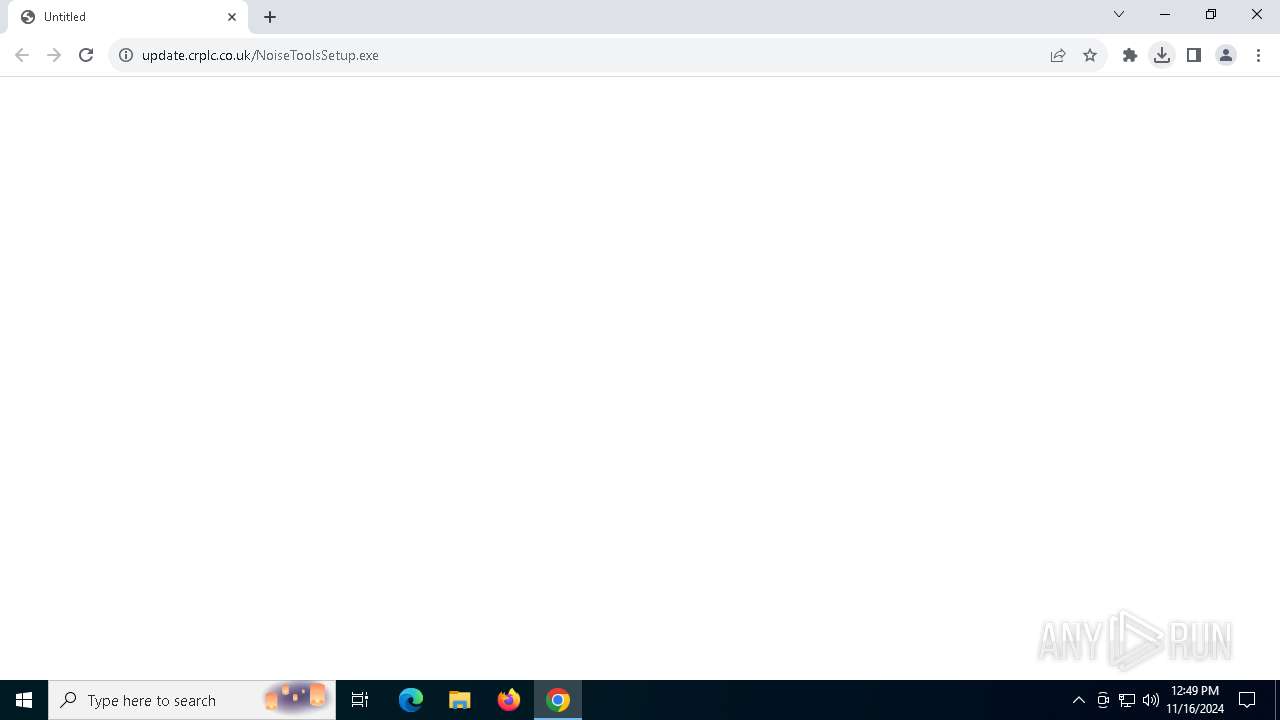
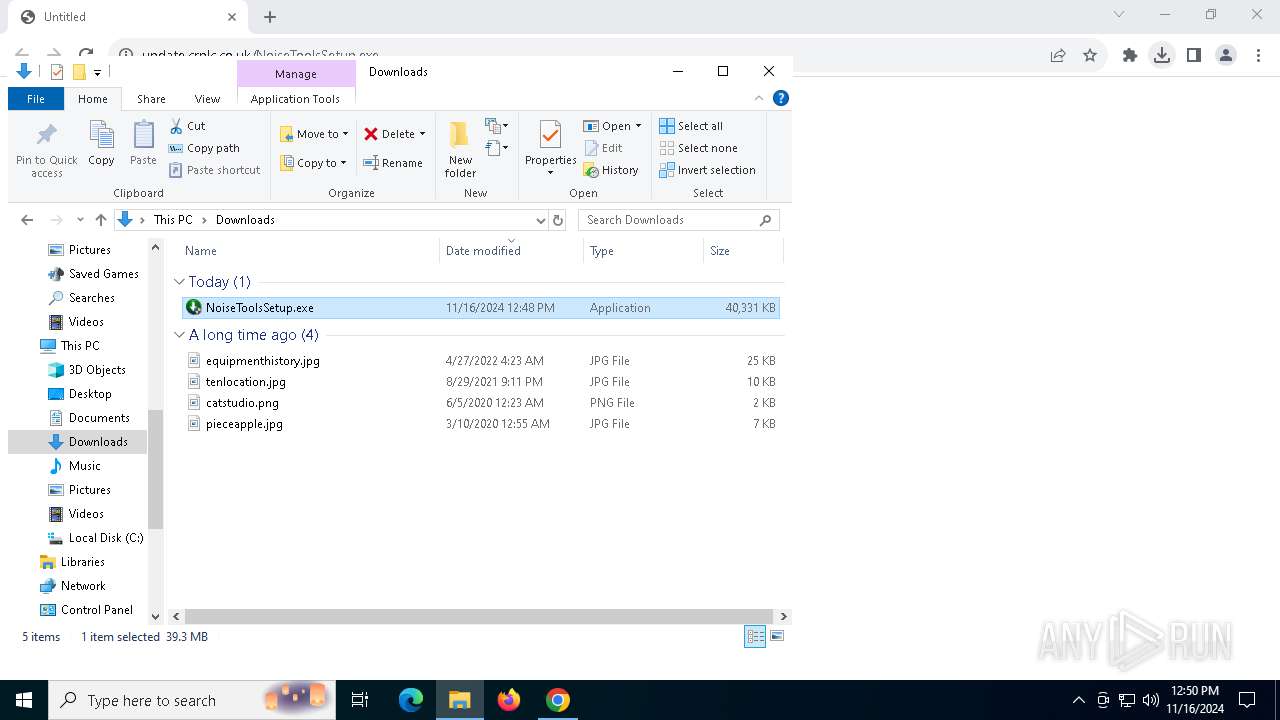
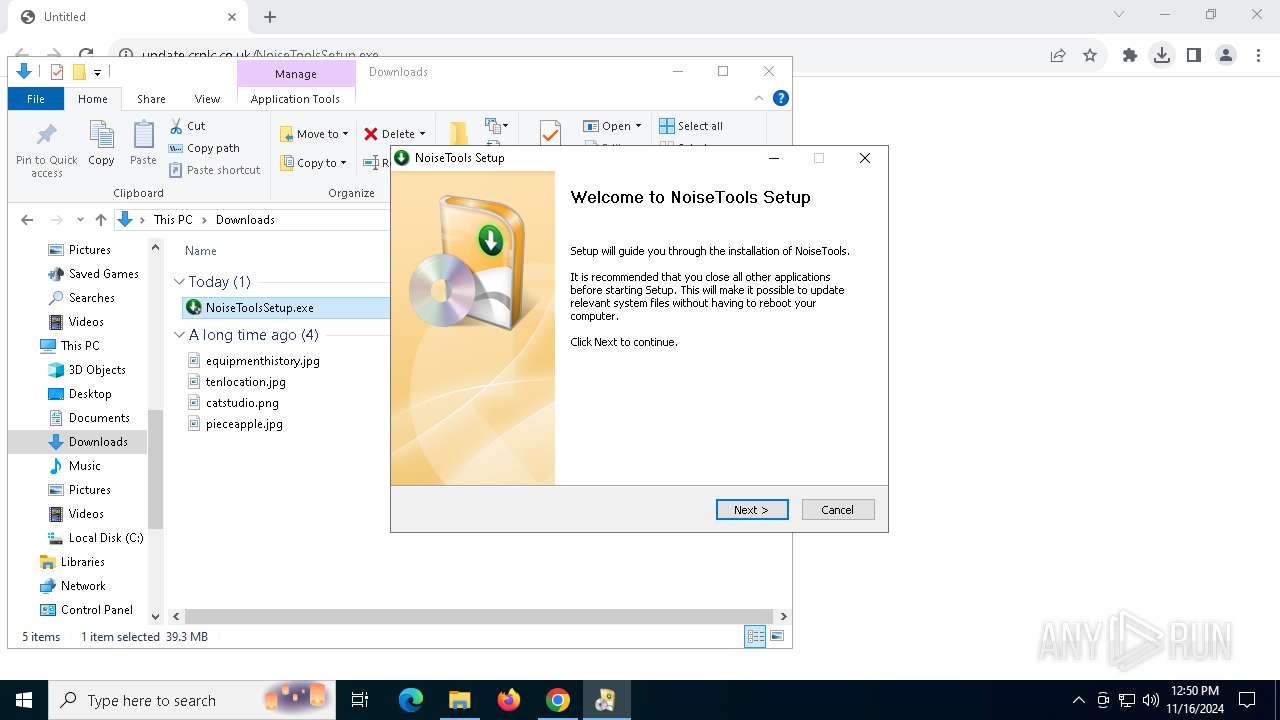
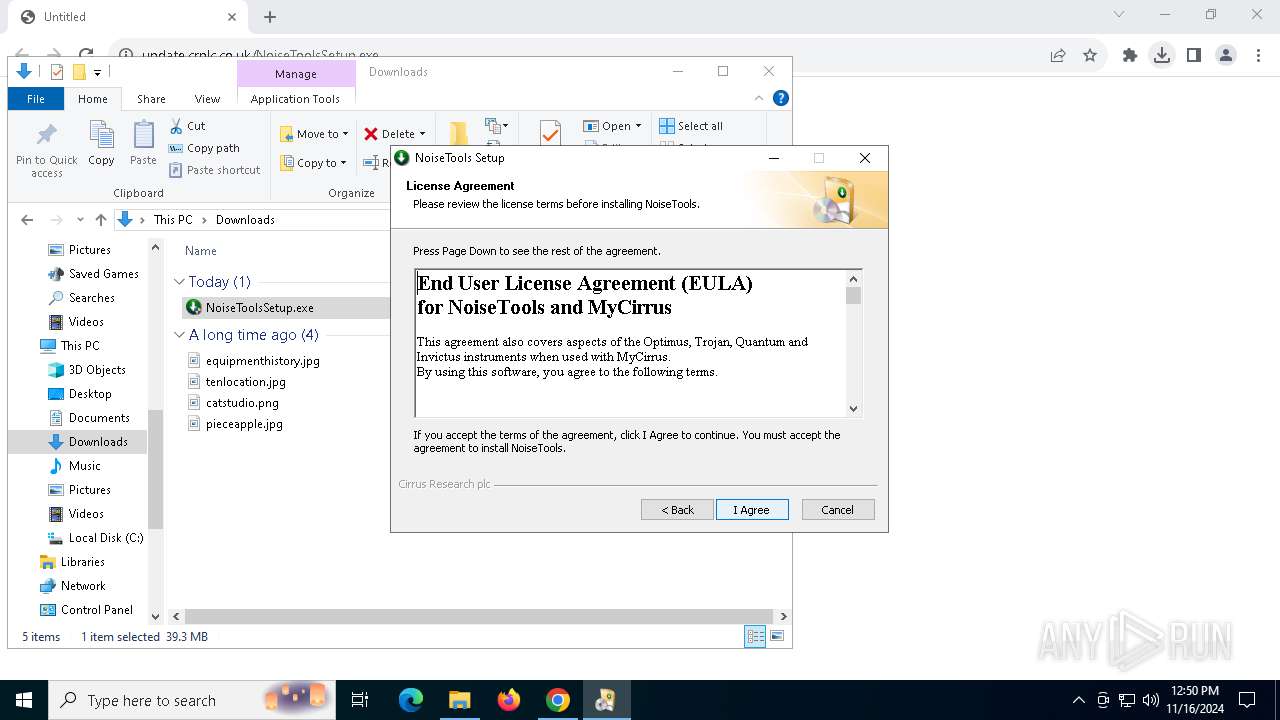
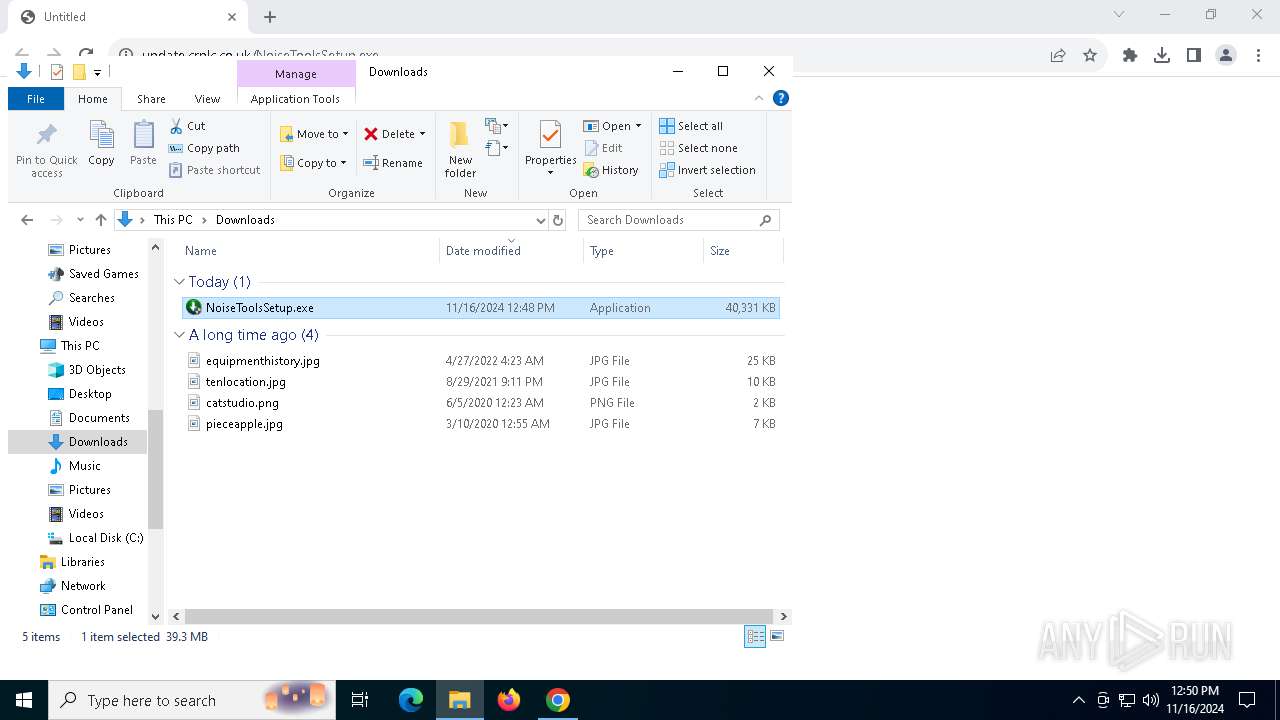
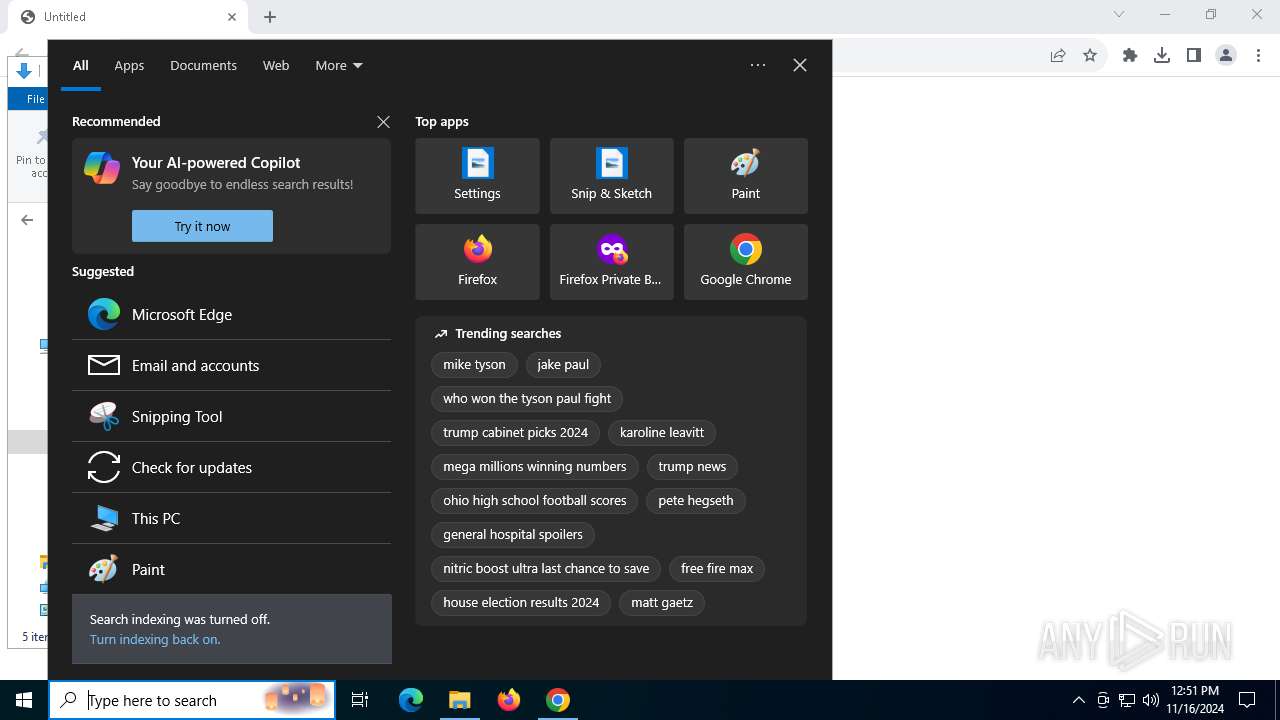
| URL: | https://update.crplc.co.uk/NoiseToolsSetup.exe |
| Full analysis: | https://app.any.run/tasks/127d560c-ad9b-419d-92f3-14803d20b474 |
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2024, 12:48:28 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 0F1C6BAB410ABB48EA113F88221DAA0B |
| SHA1: | 1F5A4A3CA53264DBF42A5065BEEBA4F90A38502C |
| SHA256: | 2F09D69667534B5B3601F4C4172BCF52B661D8EEB61692AB0515EC3EB924A1EA |
| SSDEEP: | 3:N8vRAE6LGKkO/XTS6A:2vH6yKkO/TFA |
MALICIOUS
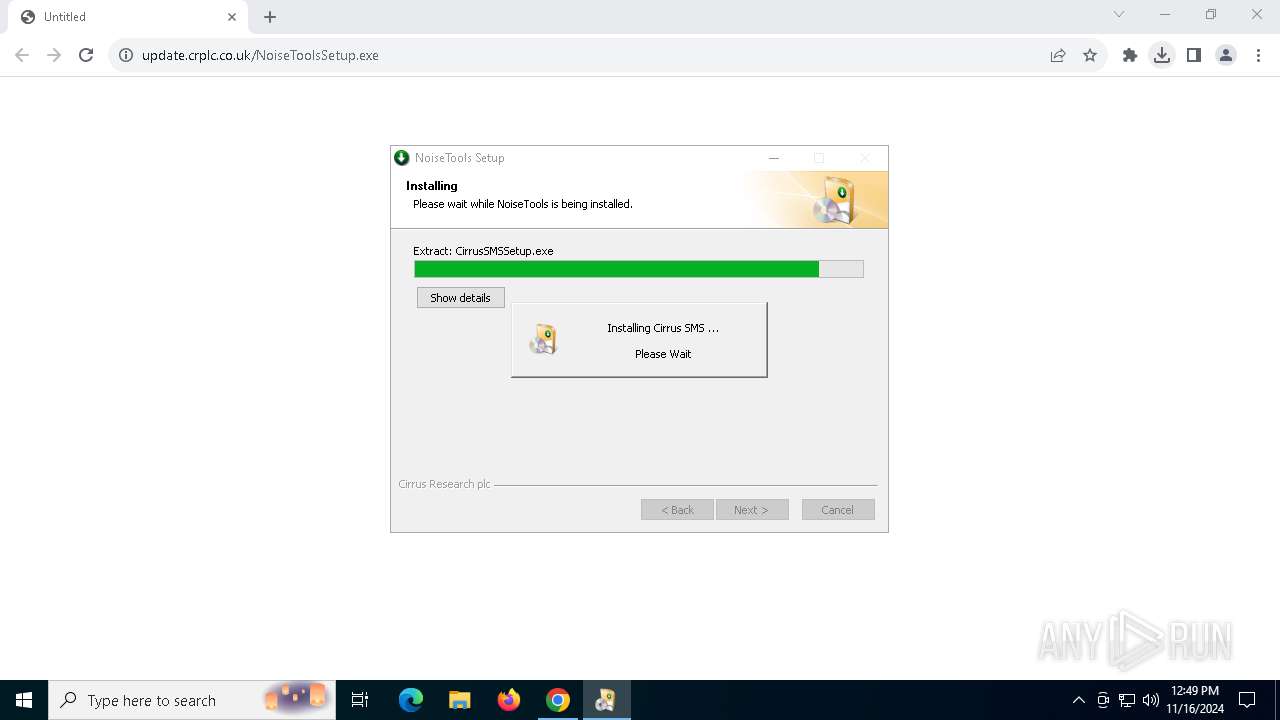
Starts NET.EXE for service management
- CirrusSMSSetup.exe (PID: 2416)
- net.exe (PID: 5956)
- net.exe (PID: 7620)
- CirrusSMSSetup.exe (PID: 6128)
- net.exe (PID: 3940)
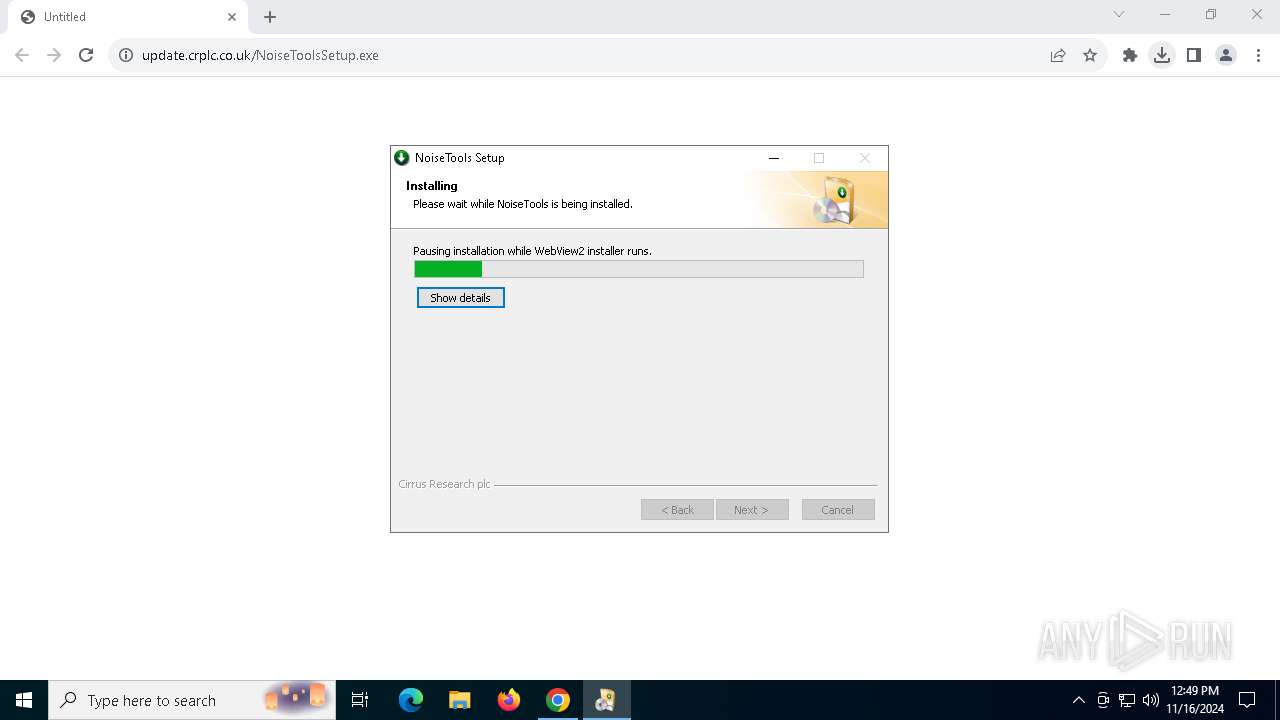
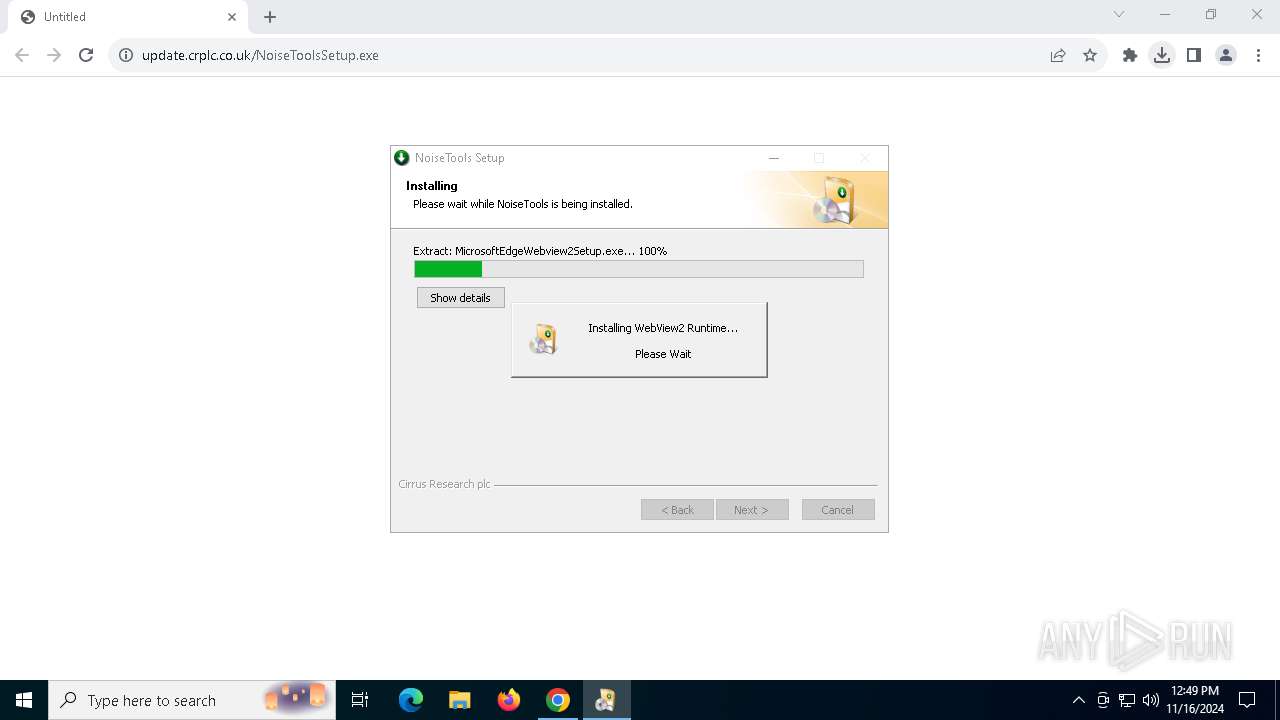
SUSPICIOUS
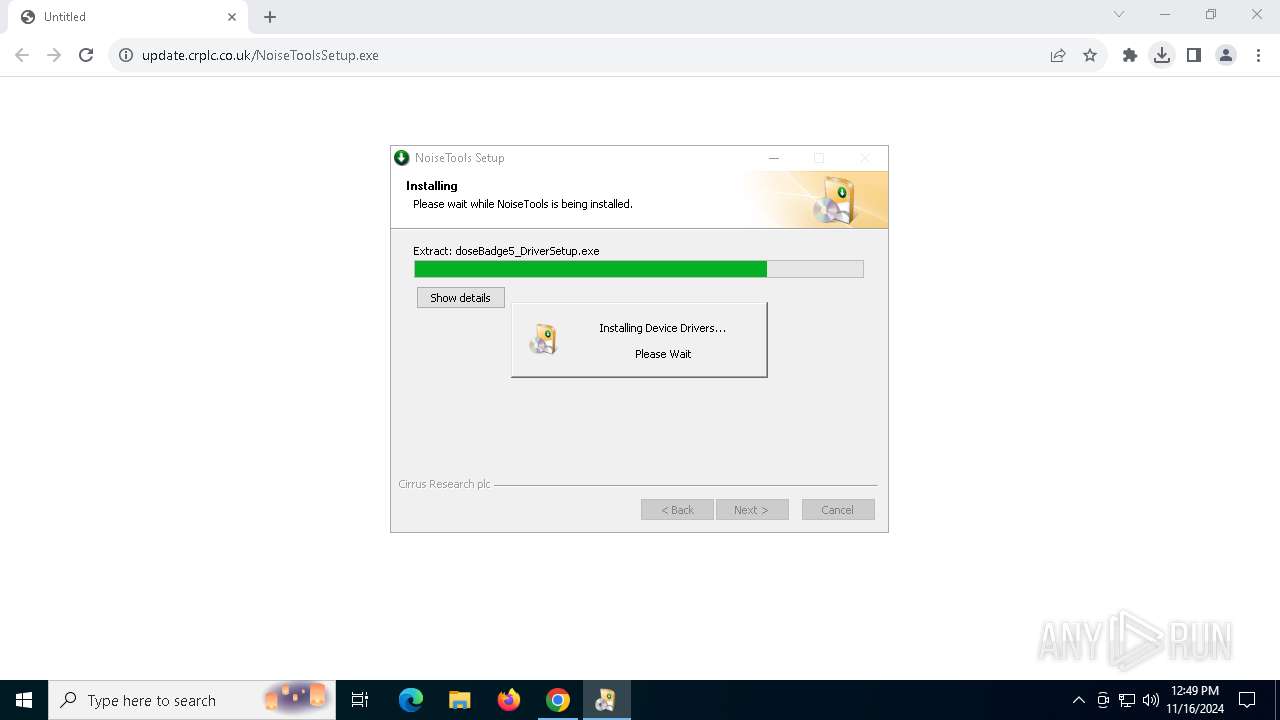
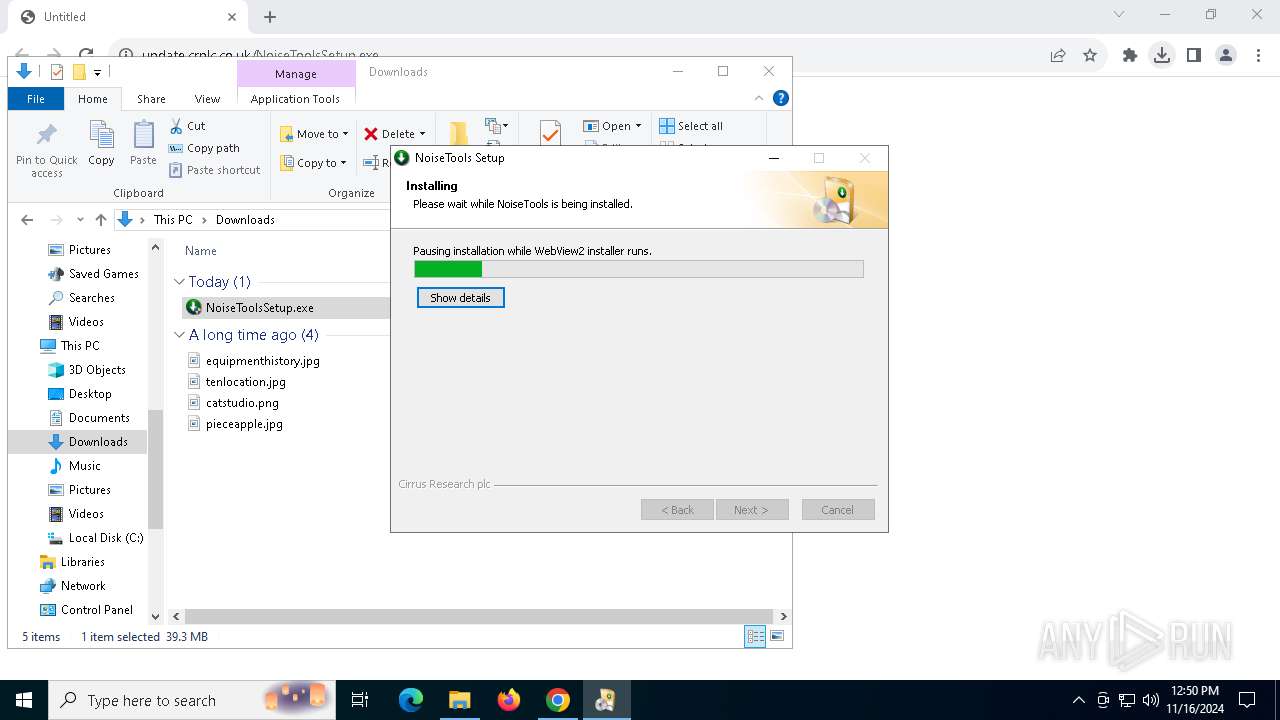
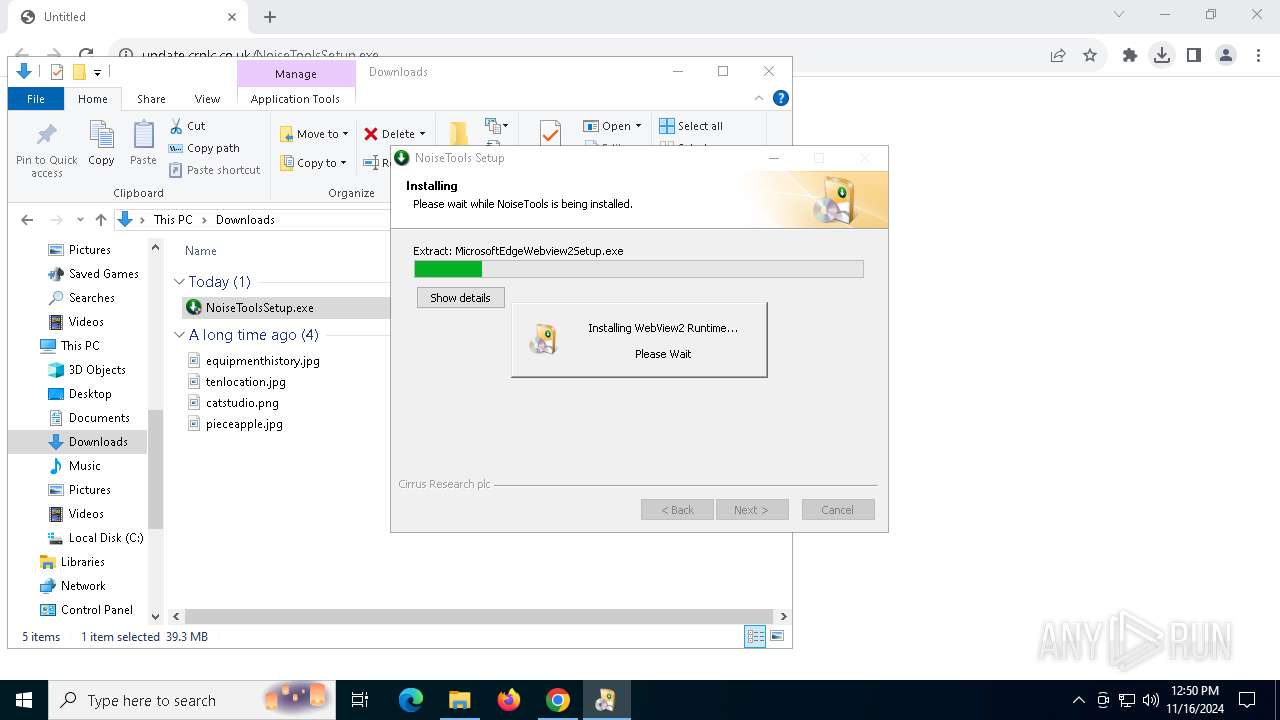
Process drops legitimate windows executable
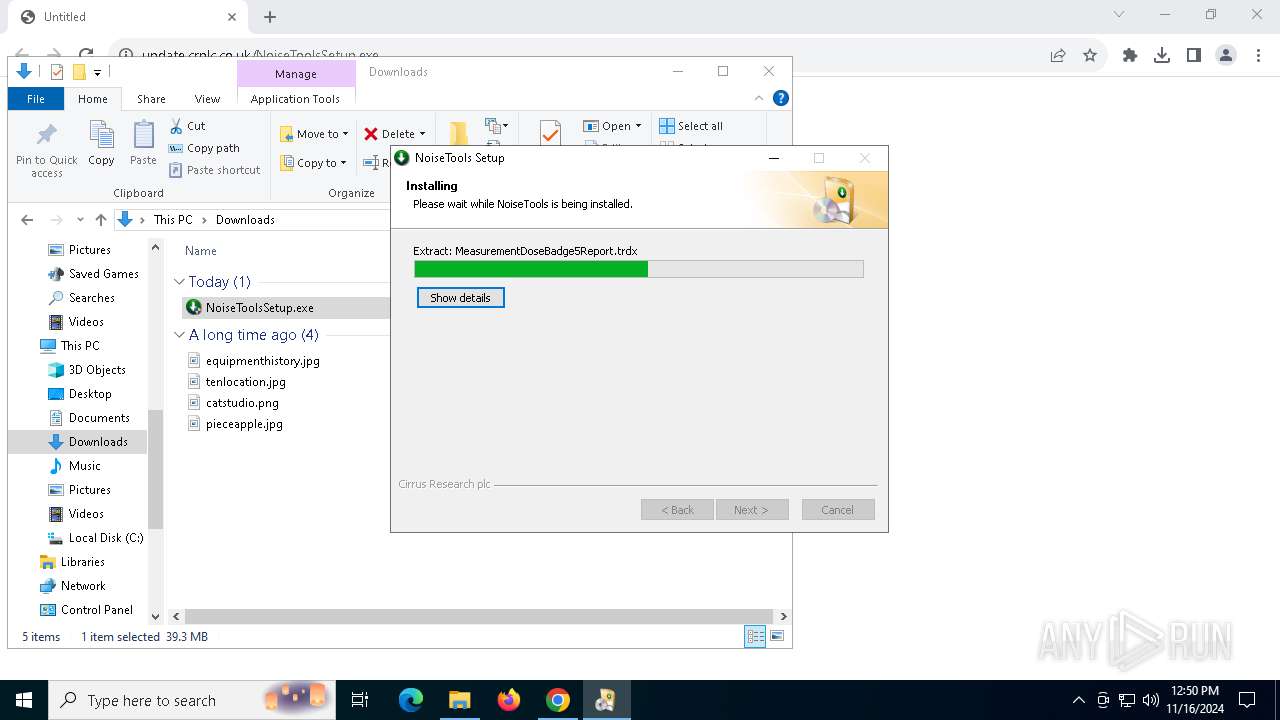
- NoiseToolsSetup.exe (PID: 8036)
- MicrosoftEdgeWebview2Setup.exe (PID: 7408)
- MicrosoftEdgeUpdate.exe (PID: 7384)
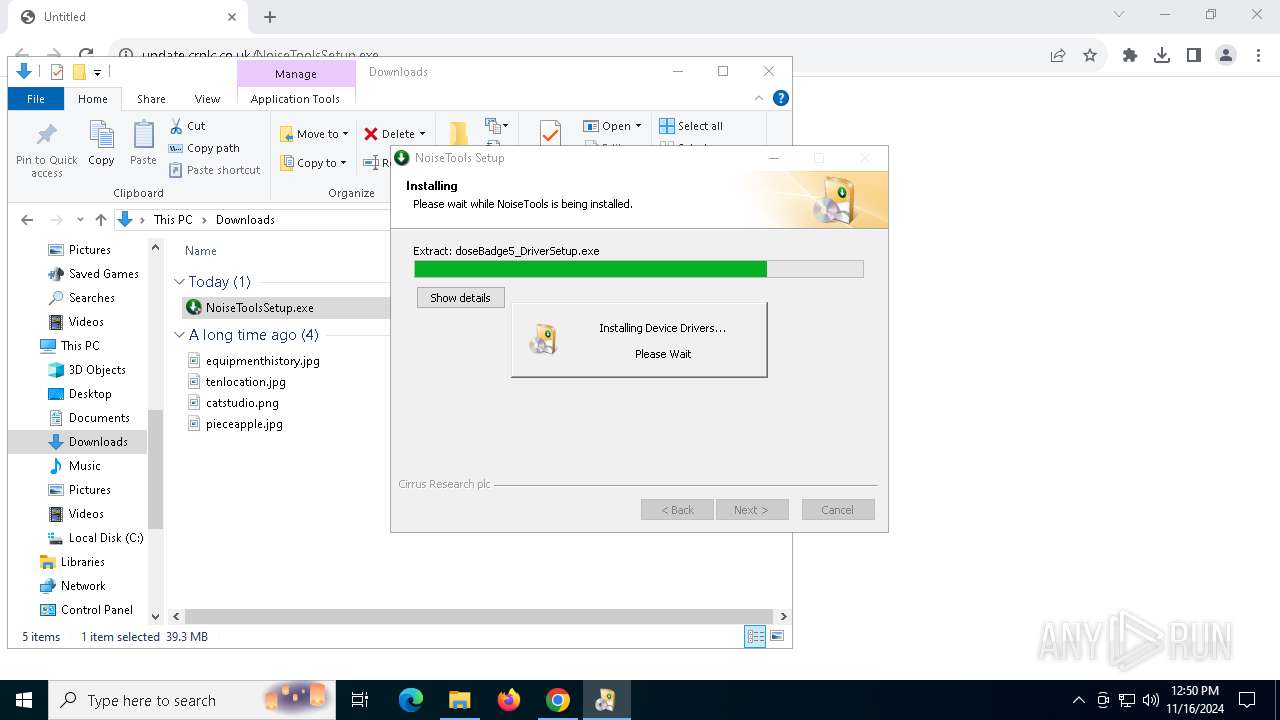
- doseBadge5_DriverSetup.exe (PID: 6992)
- MicrosoftEdgeWebview2Setup.exe (PID: 5588)
- MicrosoftEdgeUpdate.exe (PID: 7616)
- doseBadge5_DriverSetup.exe (PID: 780)
- doseBadgeReader_DriverSetup.exe (PID: 6604)
- NoiseToolsSetup.exe (PID: 7888)
- doseBadgeReader_DriverSetup.exe (PID: 8072)
Executable content was dropped or overwritten
- NoiseToolsSetup.exe (PID: 8036)
- MicrosoftEdgeWebview2Setup.exe (PID: 7408)
- doseBadgeReader_DriverSetup.exe (PID: 8072)
- drvinst.exe (PID: 8120)
- drvinst.exe (PID: 3644)
- CirrusSMSSetup.exe (PID: 2416)
- dpinst_x64.exe (PID: 632)
- MicrosoftEdgeWebview2Setup.exe (PID: 5588)
- doseBadge5_DriverSetup.exe (PID: 780)
- doseBadgeReader_DriverSetup.exe (PID: 6604)
- NoiseToolsSetup.exe (PID: 7888)
- CirrusSMSSetup.exe (PID: 6128)
- doseBadge5_DriverSetup.exe (PID: 6992)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 7408)
- MicrosoftEdgeUpdate.exe (PID: 7384)
- dpinst_x64.exe (PID: 632)
- MicrosoftEdgeUpdate.exe (PID: 7616)
- dpinst_x64.exe (PID: 7628)
- MicrosoftEdgeWebview2Setup.exe (PID: 5588)
- dpinst_x64.exe (PID: 6888)
- dpinst_x64.exe (PID: 7908)
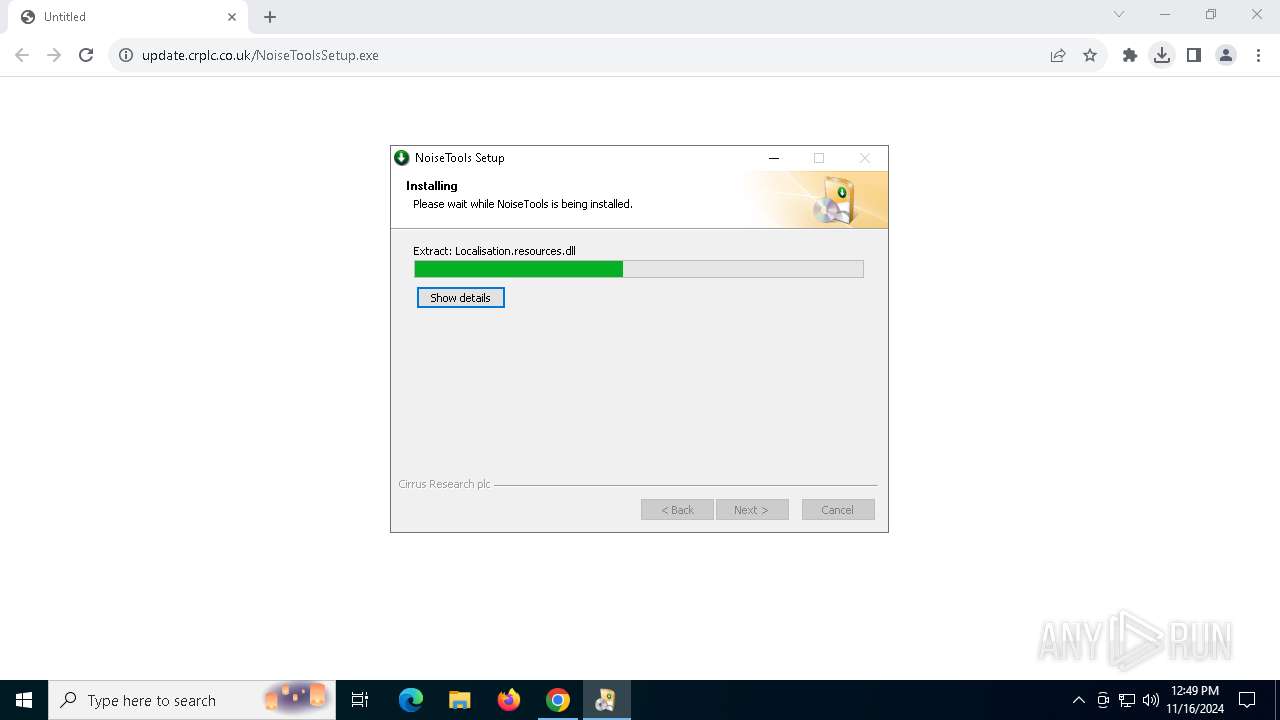
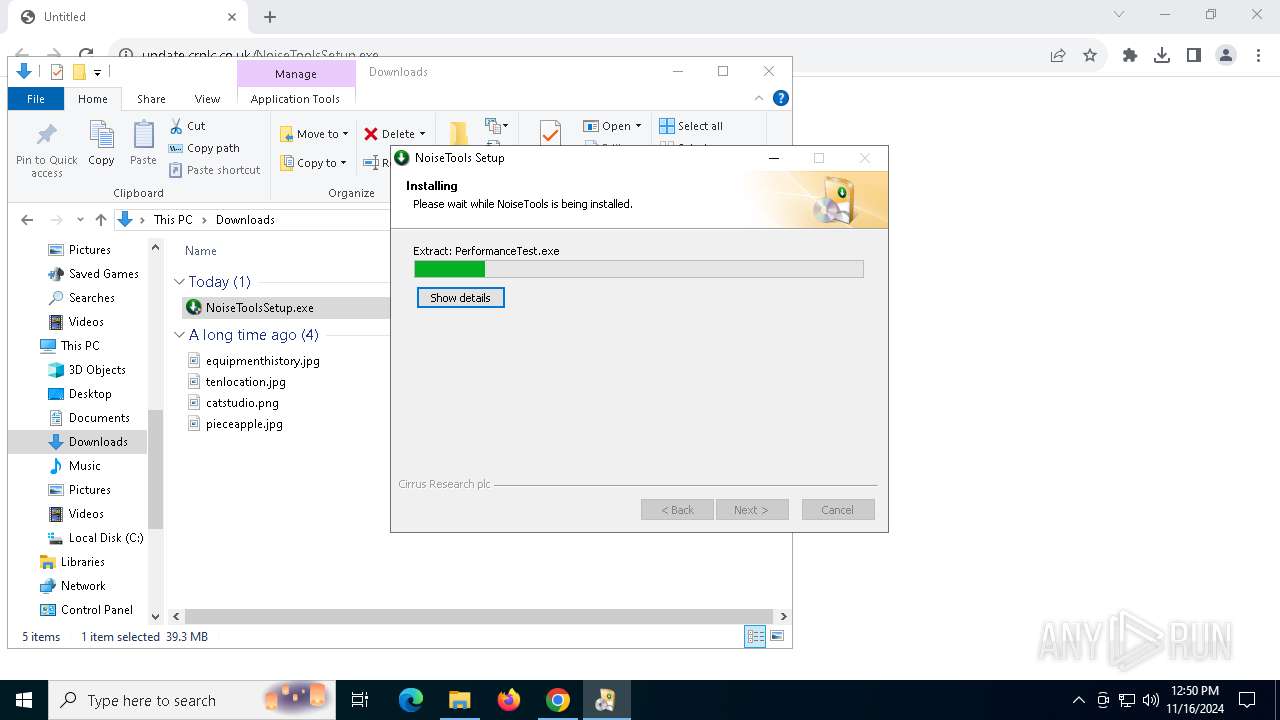
Malware-specific behavior (creating "System.dll" in Temp)
- doseBadge5_DriverSetup.exe (PID: 6992)
- NoiseToolsSetup.exe (PID: 8036)
- doseBadgeReader_DriverSetup.exe (PID: 6604)
- doseBadge5_DriverSetup.exe (PID: 780)
- NoiseToolsSetup.exe (PID: 7888)
- doseBadgeReader_DriverSetup.exe (PID: 8072)
Drops a system driver (possible attempt to evade defenses)
- doseBadgeReader_DriverSetup.exe (PID: 8072)
- drvinst.exe (PID: 8120)
- dpinst_x64.exe (PID: 632)
- drvinst.exe (PID: 3644)
- doseBadgeReader_DriverSetup.exe (PID: 6604)
Executes as Windows Service
- CirrusSMS.exe (PID: 7660)
- WmiApSrv.exe (PID: 6440)
Suspicious use of NETSH.EXE
- NoiseTools.exe (PID: 2360)
- NoiseTools.exe (PID: 6192)
INFO
Application launched itself
- chrome.exe (PID: 4316)
Executable content was dropped or overwritten
- chrome.exe (PID: 4316)
- chrome.exe (PID: 6860)
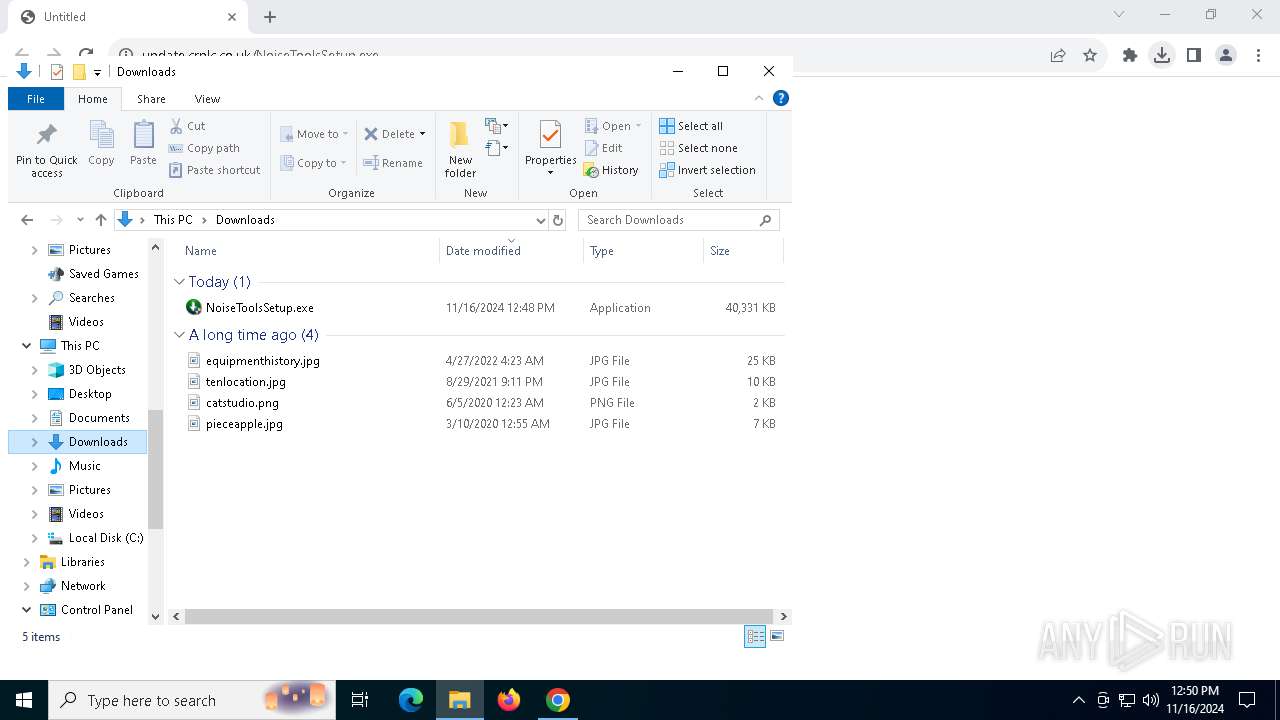
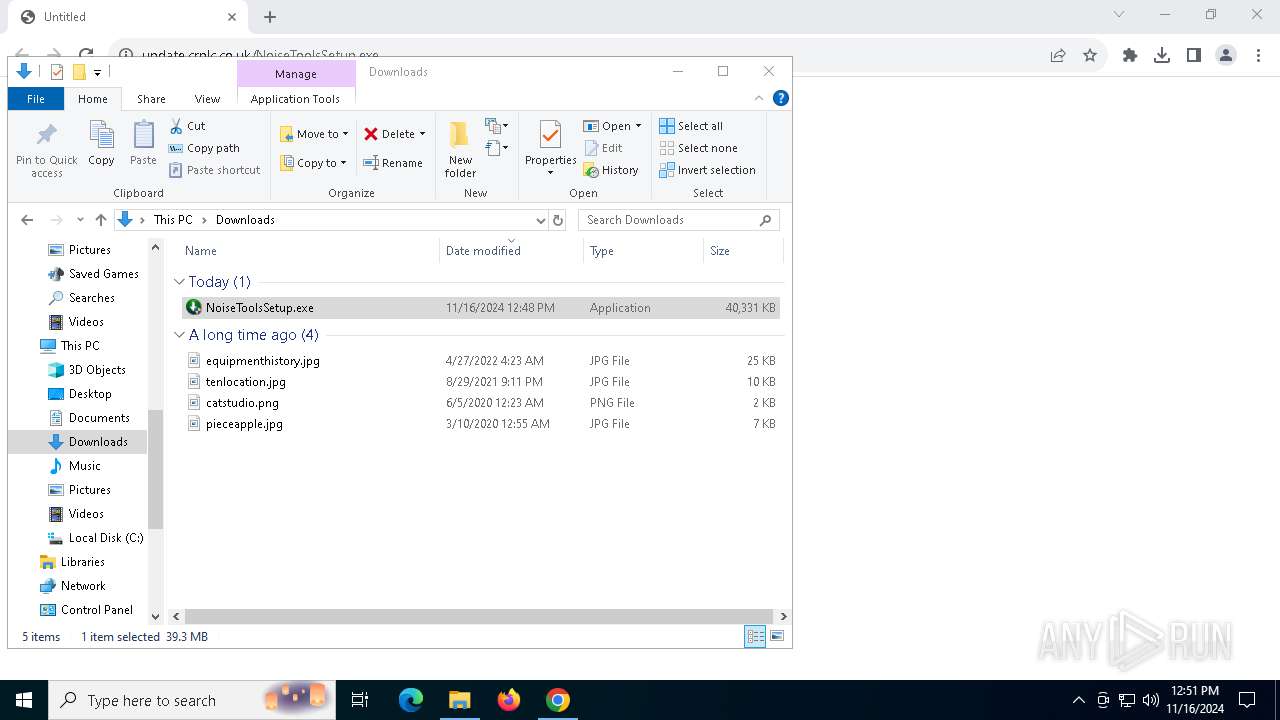
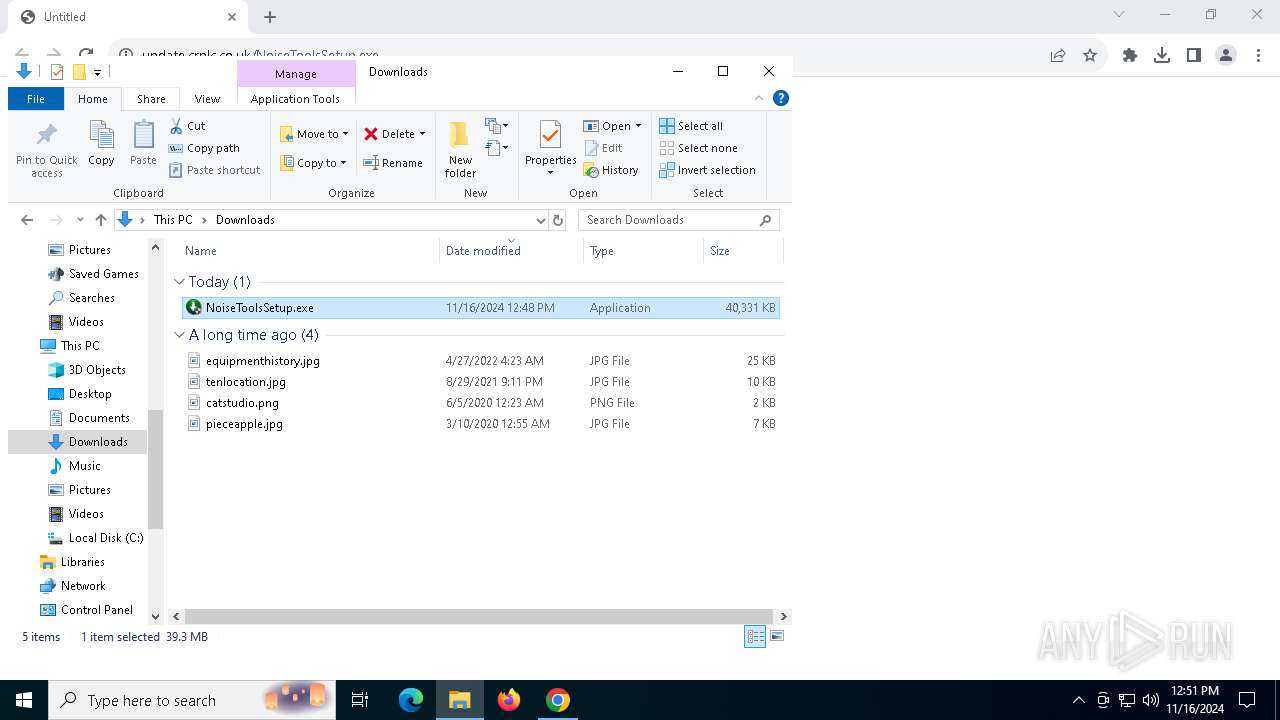
The process uses the downloaded file
- chrome.exe (PID: 4316)
- chrome.exe (PID: 7480)
Creates files in the program directory
- MicrosoftEdgeWebview2Setup.exe (PID: 7408)
- NoiseToolsSetup.exe (PID: 8036)
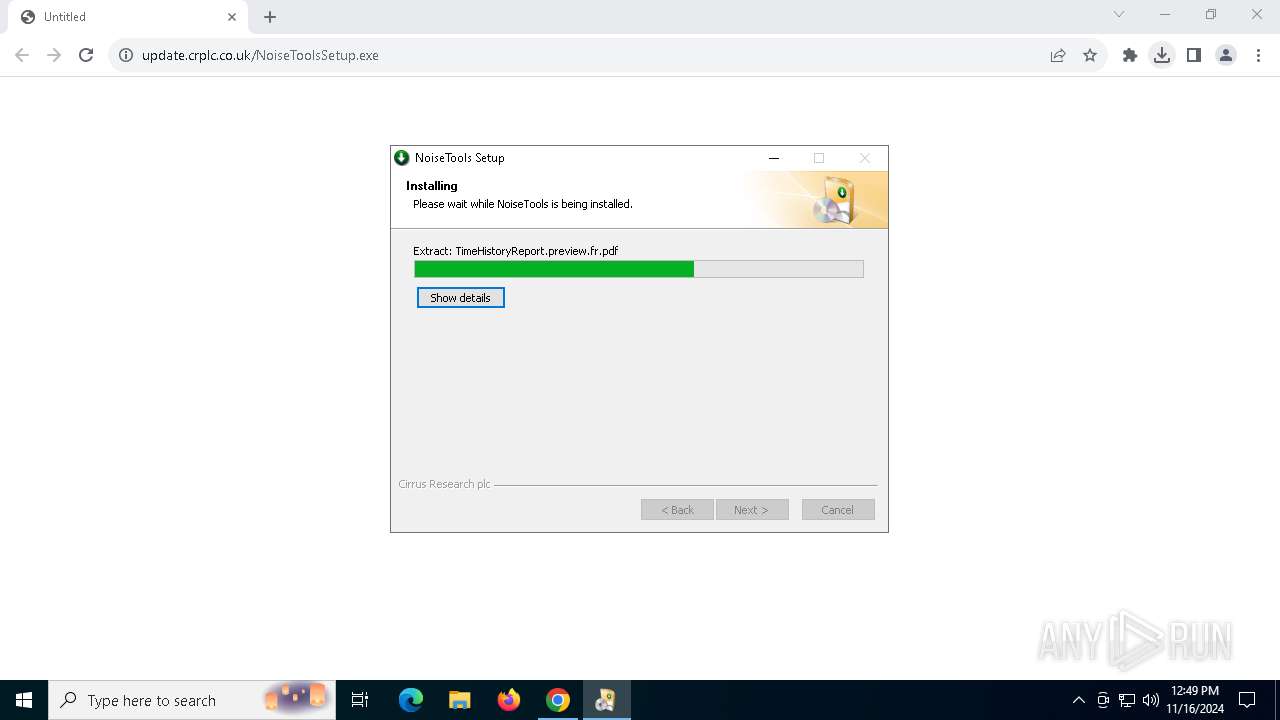
Create files in a temporary directory
- NoiseToolsSetup.exe (PID: 8036)
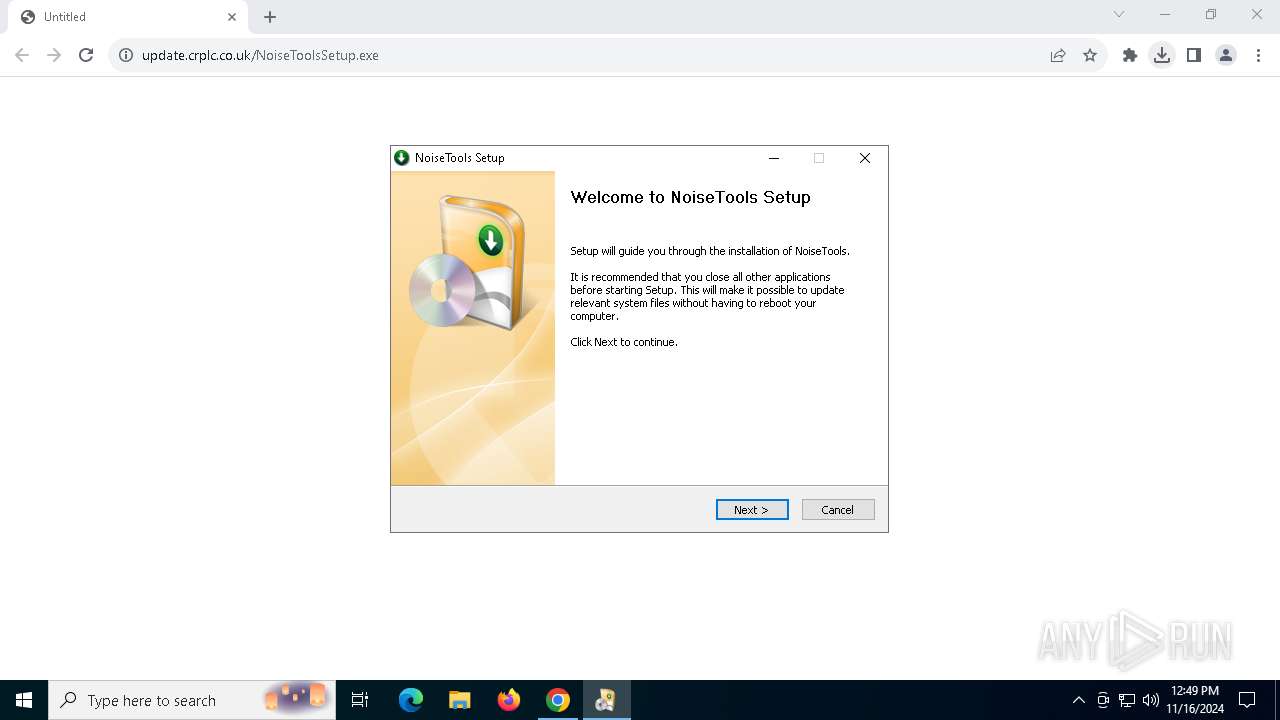
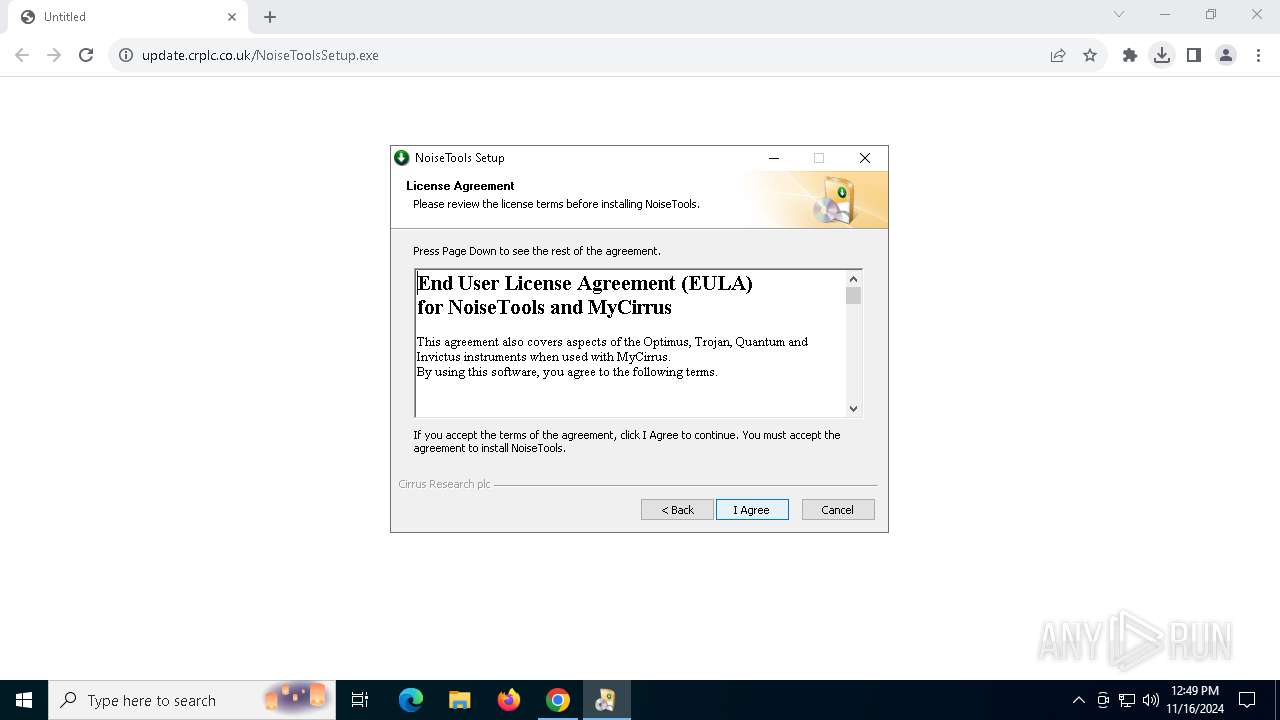
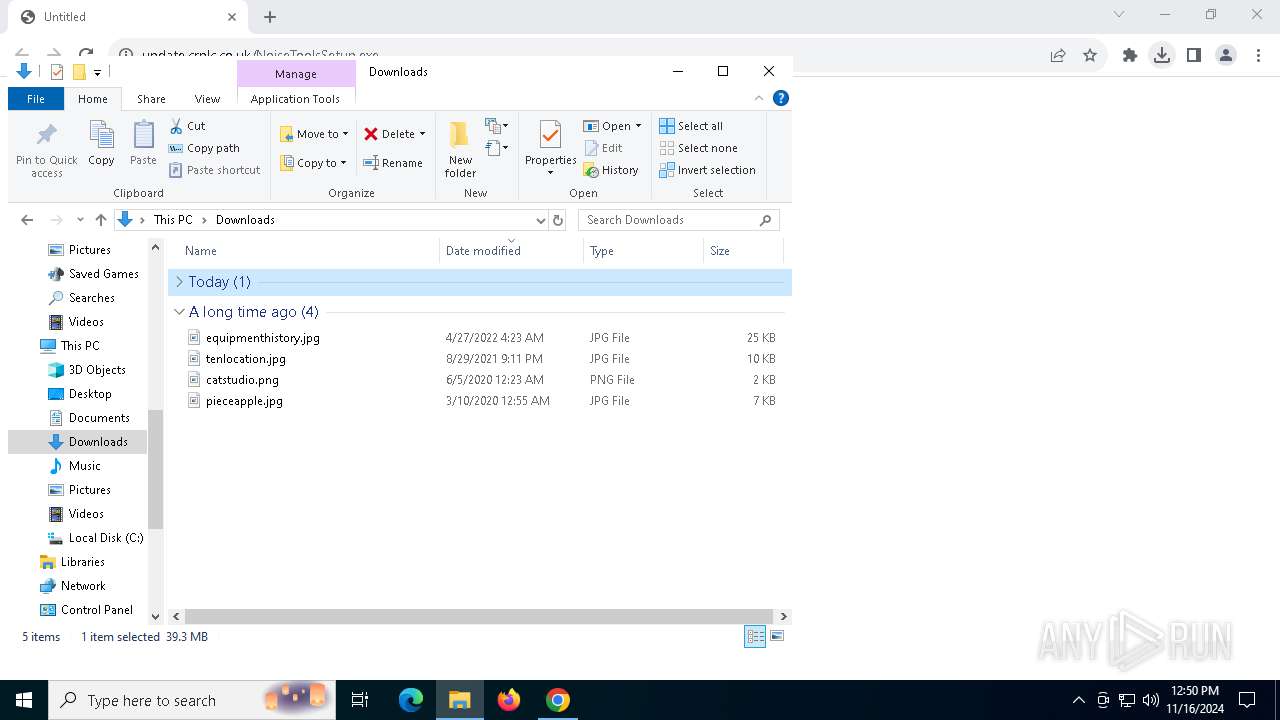
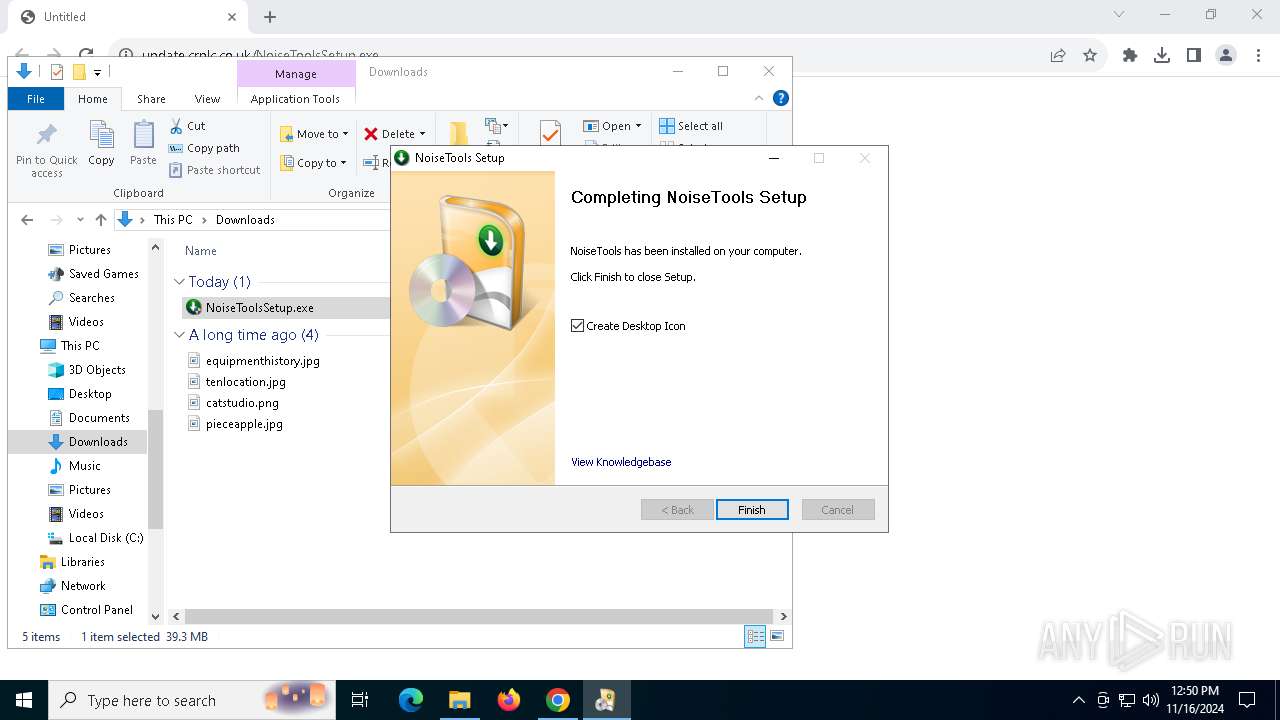
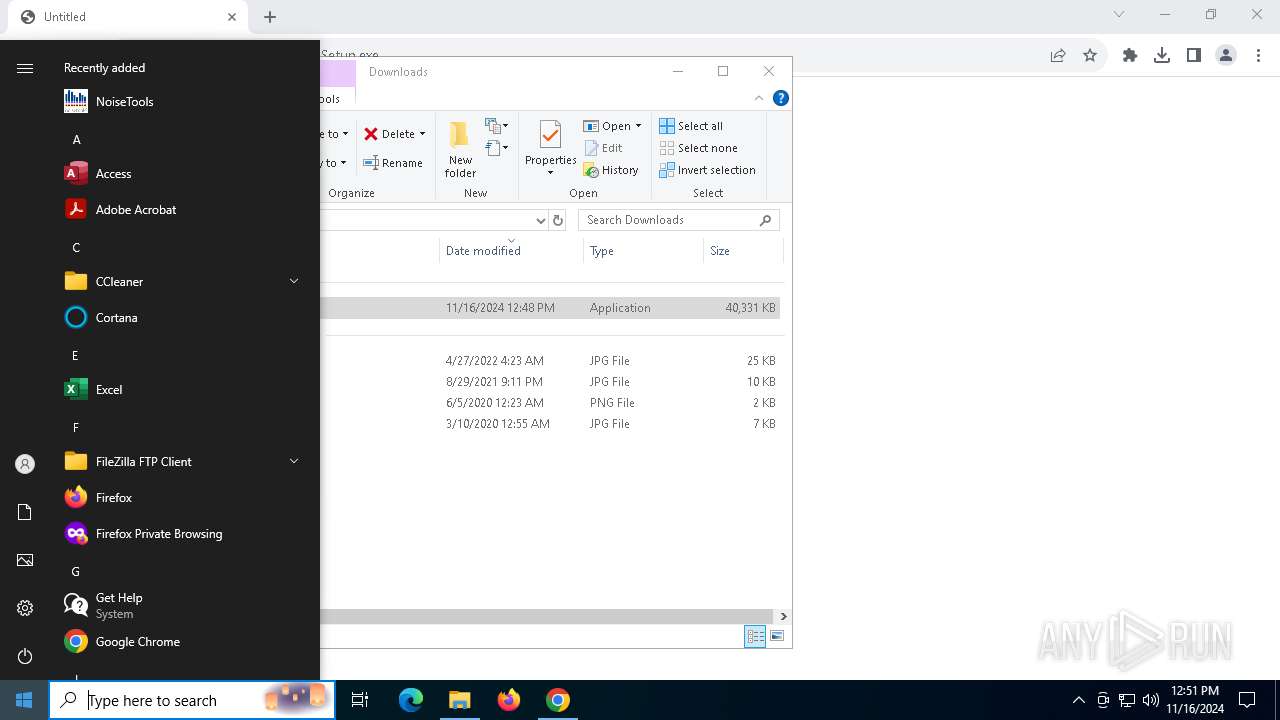
Manual execution by a user
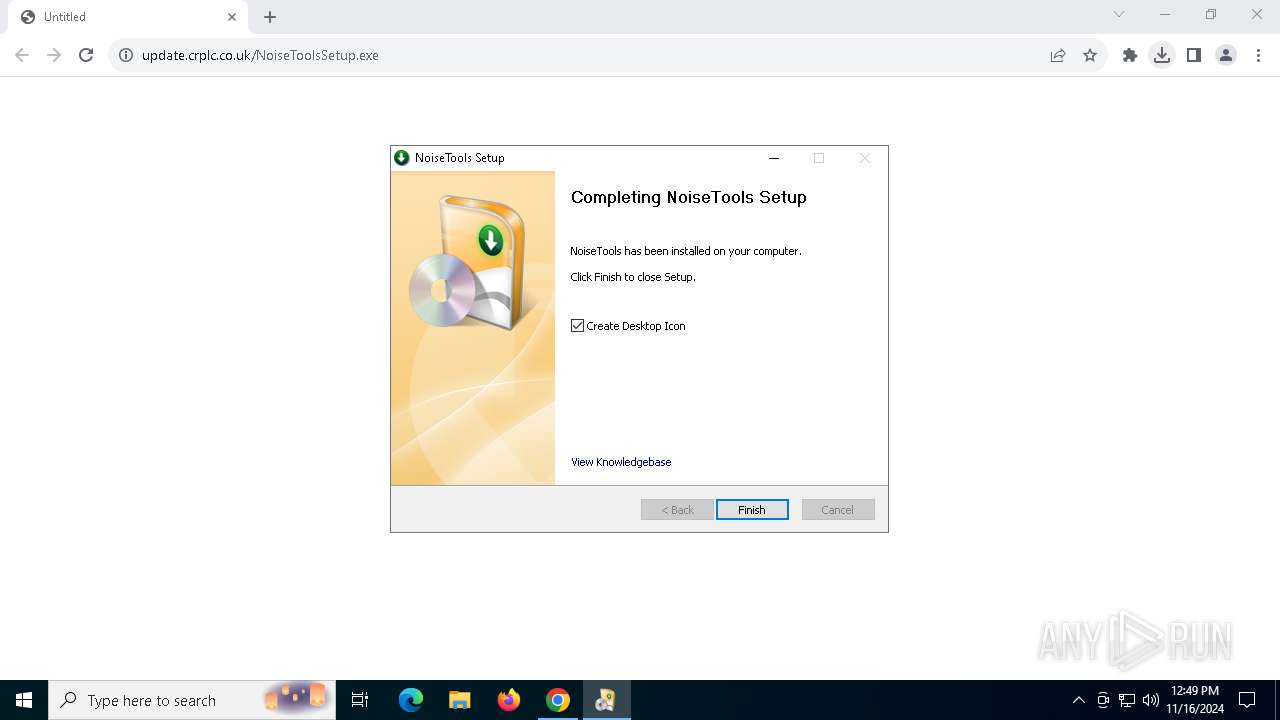
- NoiseToolsSetup.exe (PID: 7284)
- NoiseToolsSetup.exe (PID: 7888)
- NoiseTools.exe (PID: 5756)
- NoiseTools.exe (PID: 3732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
231
Monitored processes
84
Malicious processes
10
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | dpinst_x64 /c /sw /sa /f /el /path . | C:\Users\admin\AppData\Local\Temp\doseBadgeReaderDriver\dpinst_x64.exe | doseBadgeReader_DriverSetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Driver Package Installer Exit code: 512 Version: 2.1 Modules
| |||||||||||||||
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3108 --field-trial-handle=1920,i,5583548559154989771,8795790423188206692,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 780 | "C:\Users\admin\AppData\Local\Temp\doseBadge5_DriverSetup.exe" /S | C:\Users\admin\AppData\Local\Temp\doseBadge5_DriverSetup.exe | NoiseToolsSetup.exe | ||||||||||||
User: admin Company: Cirrus Research plc Integrity Level: HIGH Description: doseBadge5 Driver Installer Exit code: 0 Version: 1.0.2.7663 Modules
| |||||||||||||||
| 864 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | PerformanceTest.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | PerformanceTest.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2080 --field-trial-handle=1920,i,5583548559154989771,8795790423188206692,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
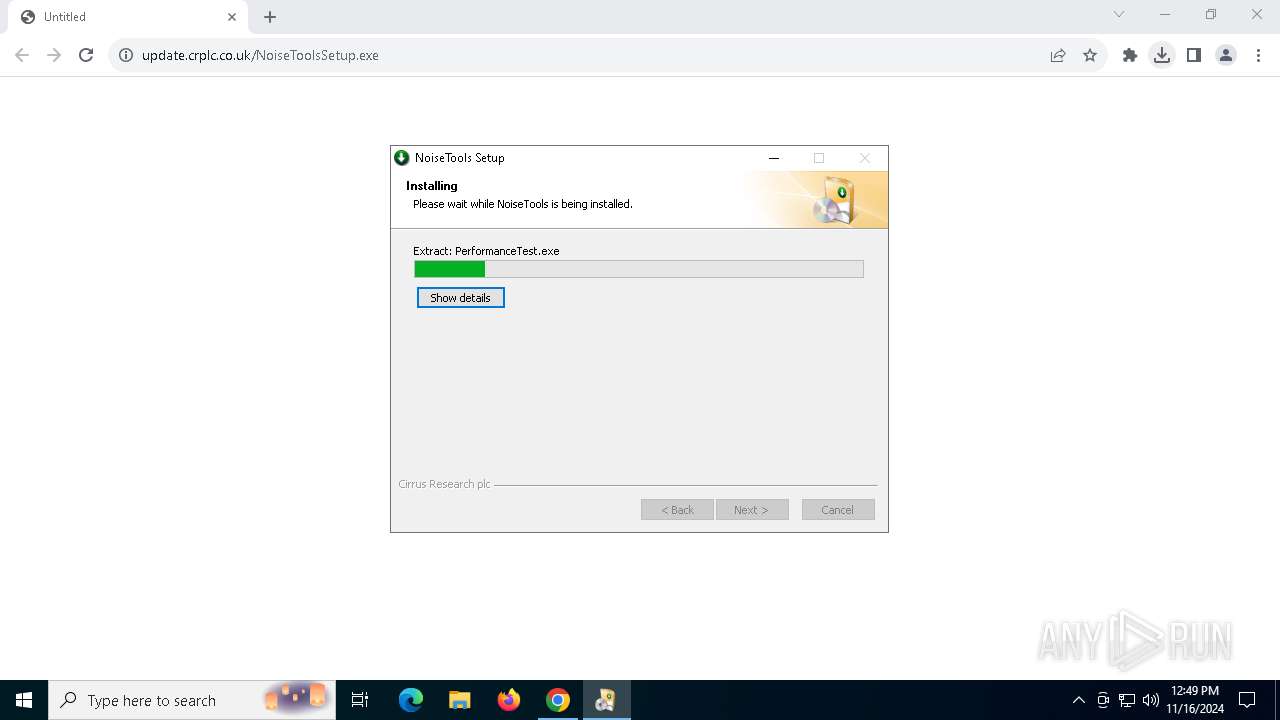
| 2088 | "C:\Users\admin\AppData\Local\Temp\PerformanceTest.exe" /cpuc | C:\Users\admin\AppData\Local\Temp\PerformanceTest.exe | — | NoiseToolsSetup.exe | |||||||||||
User: admin Company: Cirrus Research plc Integrity Level: HIGH Description: PerformanceTest Exit code: 0 Version: 1.2.0.13572 Modules
| |||||||||||||||
| 2360 | "C:\Program Files (x86)\Cirrus Research\NoiseTools\NoiseTools.exe" /firewall | C:\Program Files (x86)\Cirrus Research\NoiseTools\NoiseTools.exe | — | NoiseToolsSetup.exe | |||||||||||
User: admin Company: Cirrus Research plc Integrity Level: HIGH Description: NoiseTools Exit code: 0 Version: 1.8.9.13572 Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=6060 --field-trial-handle=1920,i,5583548559154989771,8795790423188206692,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2416 | C:\Users\admin\AppData\Local\Temp\CirrusSMSSetup.exe | C:\Users\admin\AppData\Local\Temp\CirrusSMSSetup.exe | NoiseToolsSetup.exe | ||||||||||||
User: admin Company: Cirrus Research plc Integrity Level: HIGH Description: Cirrus SMS Installer Exit code: 0 Version: 2.3.1.12229 Modules
| |||||||||||||||
Total events
49 201
Read events
49 007
Write events
181
Delete events
13
Modification events
| (PID) Process: | (4316) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4316) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4316) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4316) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4316) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7480) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000394386E02538DB01 | |||
| (PID) Process: | (7384) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MicrosoftEdgeUpdate.exe |
| Operation: | write | Name: | DisableExceptionChainValidation |
Value: 0 | |||
| (PID) Process: | (7384) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\PersistedPings\{F3DA8005-477A-4B6C-A8BB-BAAEEAD784EE} |
| Operation: | write | Name: | PersistedPingString |
Value: <?xml version="1.0" encoding="UTF-8"?><request protocol="3.0" updater="Omaha" updaterversion="1.3.169.31" shell_version="1.3.147.37" ismachine="1" sessionid="{8DDC6F6E-76A4-4DFE-B1BA-B2701677B8F8}" userid="{FD984739-A122-4DB0-BE5B-46E3E09D84E4}" installsource="otherinstallcmd" requestid="{F3DA8005-477A-4B6C-A8BB-BAAEEAD784EE}" dedup="cr" domainjoined="0"><hw logical_cpus="4" physmemory="4" disk_type="2" sse="1" sse2="1" sse3="1" ssse3="1" sse41="1" sse42="1" avx="1"/><os platform="win" version="10.0.19045.4046" sp="" arch="x64" product_type="48" is_wip="0"/><oem product_manufacturer="DELL" product_name="DELL"/><exp etag=""r452t1+k2Tgq/HXzjvFNBRhopBWR9sbjXxqeUDH9uX0=""/><app appid="{F3C4FE00-EFD5-403B-9569-398A20F1BA4A}" version="1.3.185.17" nextversion="1.3.169.31" lang="" brand="" client=""><event eventtype="2" eventresult="1" errorcode="0" extracode1="0" system_uptime_ticks="6123582681" install_time_ms="355"/></app></request> | |||
| (PID) Process: | (7384) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\PersistedPings\{F3DA8005-477A-4B6C-A8BB-BAAEEAD784EE} |
| Operation: | write | Name: | PersistedPingTime |
Value: 133762349546041489 | |||
| (PID) Process: | (7384) MicrosoftEdgeUpdate.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\proxy |
| Operation: | write | Name: | source |
Value: auto | |||
Executable files
563
Suspicious files
266
Text files
384
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF8c2cc.TMP | — | |
MD5:— | SHA256:— | |||
| 4316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF8c2cc.TMP | — | |
MD5:— | SHA256:— | |||
| 4316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF8c2db.TMP | — | |
MD5:— | SHA256:— | |||
| 4316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF8c2db.TMP | — | |
MD5:— | SHA256:— | |||
| 4316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF8c2db.TMP | — | |
MD5:— | SHA256:— | |||
| 4316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF8c2db.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
71
DNS requests
44
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4376 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7776 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3600 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7160 | wermgr.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7776 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5264 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7160 | wermgr.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 20.72.205.209:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 20.72.205.209:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
864 | RUXIMICS.exe | 20.72.205.209:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4316 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1732 | chrome.exe | 172.67.144.129:443 | update.crplc.co.uk | CLOUDFLARENET | US | unknown |
1732 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
4360 | SearchApp.exe | 2.23.209.185:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
update.crplc.co.uk |
| unknown |
accounts.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
www.google.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |