| File name: | mtppk12 (1).exe |
| Full analysis: | https://app.any.run/tasks/1a0e08e9-b72e-4a33-bc7e-3ef3b9cc86b1 |
| Verdict: | Suspicious activity |
| Analysis date: | July 04, 2018, 00:50:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 67A9DA7A0FE4B3507934D1988CCCAE5B |
| SHA1: | 1588D320E0F667436FACF99F6A0ADD31410B157B |
| SHA256: | 2F07466F0653B10EF398867152B9EFA760556D4EA5F28DCCD3F17D7E4EF831D7 |
| SSDEEP: | 98304:KwwWSe64PkYGilLX6gAP2qA5hC5b/tbYuVcqlbEXAca1ulmiyJmKtsuas73VM1:KwJPkJIz6gA85ibYuVrH1FNXuuO |
MALICIOUS
Changes the autorun value in the registry
- mtppk12 (1).exe (PID: 2592)
SUSPICIOUS
Executable content was dropped or overwritten
- msiexec.exe (PID: 3212)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 684)
Creates or modifies windows services
- msiexec.exe (PID: 3212)
- vssvc.exe (PID: 684)
Dropped object may contain URL's
- msiexec.exe (PID: 3212)
Creates a software uninstall entry
- msiexec.exe (PID: 3212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | MS generic-sfx Cabinet File Unpacker (32/64bit MSCFU) (48.1) |
|---|---|---|
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (41.6) |
| .exe | | | Win32 Executable MS Visual C++ (generic) (4.2) |
| .exe | | | Win64 Executable (generic) (3.7) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2004:08:04 08:01:37+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 39424 |
| InitializedDataSize: | 6706688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x645c |
| OSVersion: | 5.1 |
| ImageVersion: | 5.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.2900.2180 |
| ProductVersionNumber: | 6.0.2900.2180 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 6.00.2900.2180 (xpsp_sp2_rtm.040803-2158) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.00.2900.2180 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Aug-2004 06:01:37 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 6.00.2900.2180 (xpsp_sp2_rtm.040803-2158) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | WEXTRACT.EXE |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.00.2900.2180 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 04-Aug-2004 06:01:37 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000992C | 0x00009A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56502 |
.data | 0x0000B000 | 0x00001BE4 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.248 |
.rsrc | 0x0000D000 | 0x00666000 | 0x00665200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99892 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.45237 | 1076 | Latin 1 / Western European | English - United States | RT_VERSION |
2 | 3.53793 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
63 | 2.48958 | 140 | Latin 1 / Western European | English - United States | RT_STRING |
76 | 3.2674 | 1312 | Latin 1 / Western European | English - United States | RT_STRING |
77 | 3.29977 | 1484 | Latin 1 / Western European | English - United States | RT_STRING |
80 | 3.27174 | 1200 | Latin 1 / Western European | English - United States | RT_STRING |
83 | 3.2912 | 1098 | Latin 1 / Western European | English - United States | RT_STRING |
85 | 3.13591 | 974 | Latin 1 / Western European | English - United States | RT_STRING |
2001 | 3.35785 | 716 | Latin 1 / Western European | English - United States | RT_DIALOG |
2002 | 3.34986 | 394 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
VERSION.dll |
Total processes
38
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
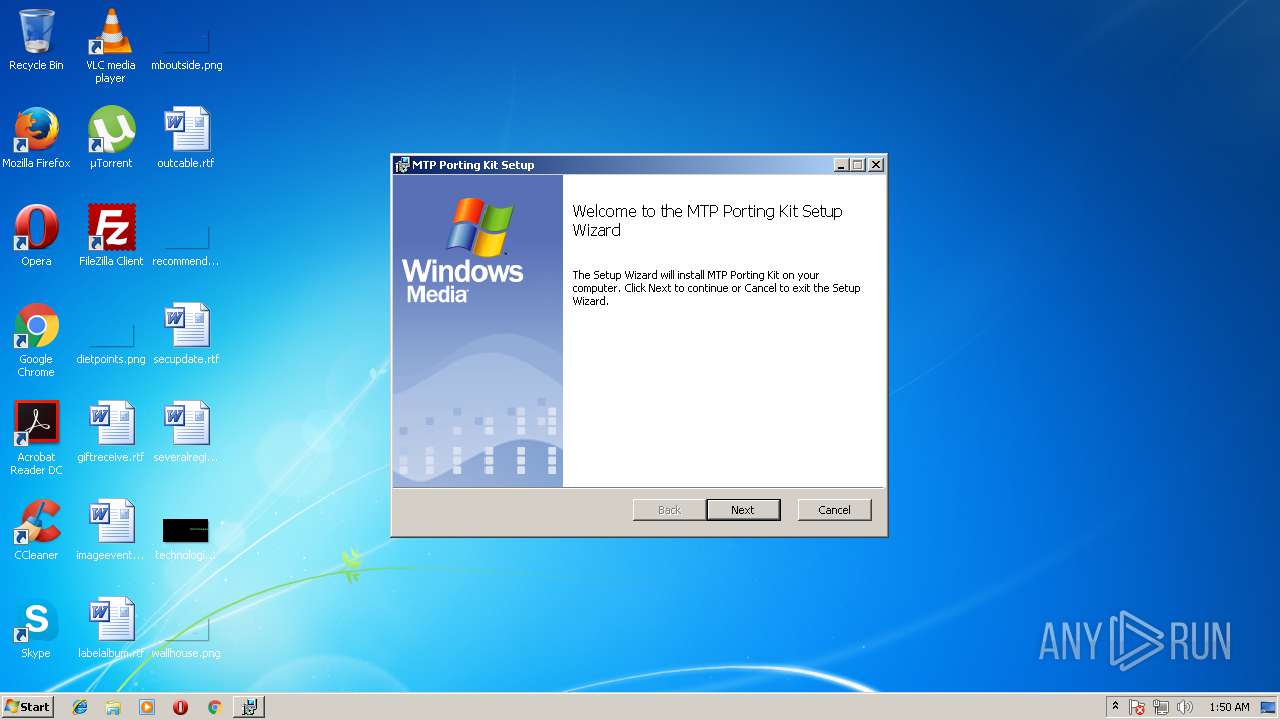
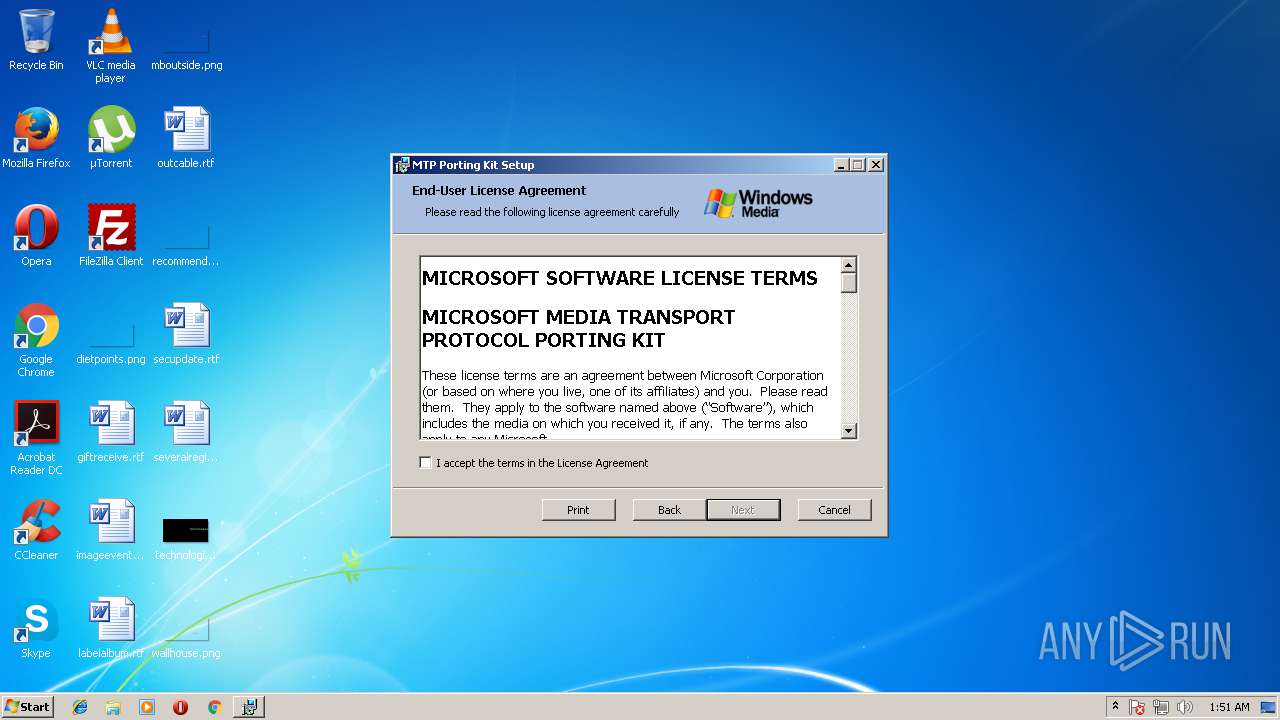
| 2592 | "C:\Users\admin\AppData\Local\Temp\mtppk12 (1).exe" | C:\Users\admin\AppData\Local\Temp\mtppk12 (1).exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 6.00.2900.2180 (xpsp_sp2_rtm.040803-2158) Modules
| |||||||||||||||
| 3212 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3856 | msiexec /i mtppk.msi | C:\Windows\system32\msiexec.exe | — | mtppk12 (1).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
669
Read events
333
Write events
324
Delete events
12
Modification events
| (PID) Process: | (2592) mtppk12 (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup0 |
Value: rundll32.exe C:\Windows\system32\advpack.dll,DelNodeRunDLL32 "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\" | |||
| (PID) Process: | (3212) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000BC00F2223113D4018C0C0000300F0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3212) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000BC00F2223113D4018C0C0000300F0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3212) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 50 | |||
| (PID) Process: | (3212) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 400000000000000034E85A233113D4018C0C0000300F0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3212) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000008E4A5D233113D4018C0C0000300D0000E8030000010000000000000000000000760E6CEB82CBD440A20A503D5D0907330000000000000000 | |||
| (PID) Process: | (684) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000004FB6D233113D401AC020000D4030000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (684) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000004FB6D233113D401AC020000840C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (684) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000004FB6D233113D401AC020000FC050000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (684) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000004FB6D233113D401AC020000080D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
14
Suspicious files
22
Text files
406
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2592 | mtppk12 (1).exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\MTPPK.msi | — | |
MD5:— | SHA256:— | |||
| 3212 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3212 | msiexec.exe | C:\Windows\Installer\1b3862.msi | — | |
MD5:— | SHA256:— | |||
| 3212 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF73075F803FE0E500.TMP | — | |
MD5:— | SHA256:— | |||
| 684 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 3212 | msiexec.exe | C:\Windows\Installer\MSI3BEC.tmp | binary | |
MD5:— | SHA256:— | |||
| 3212 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
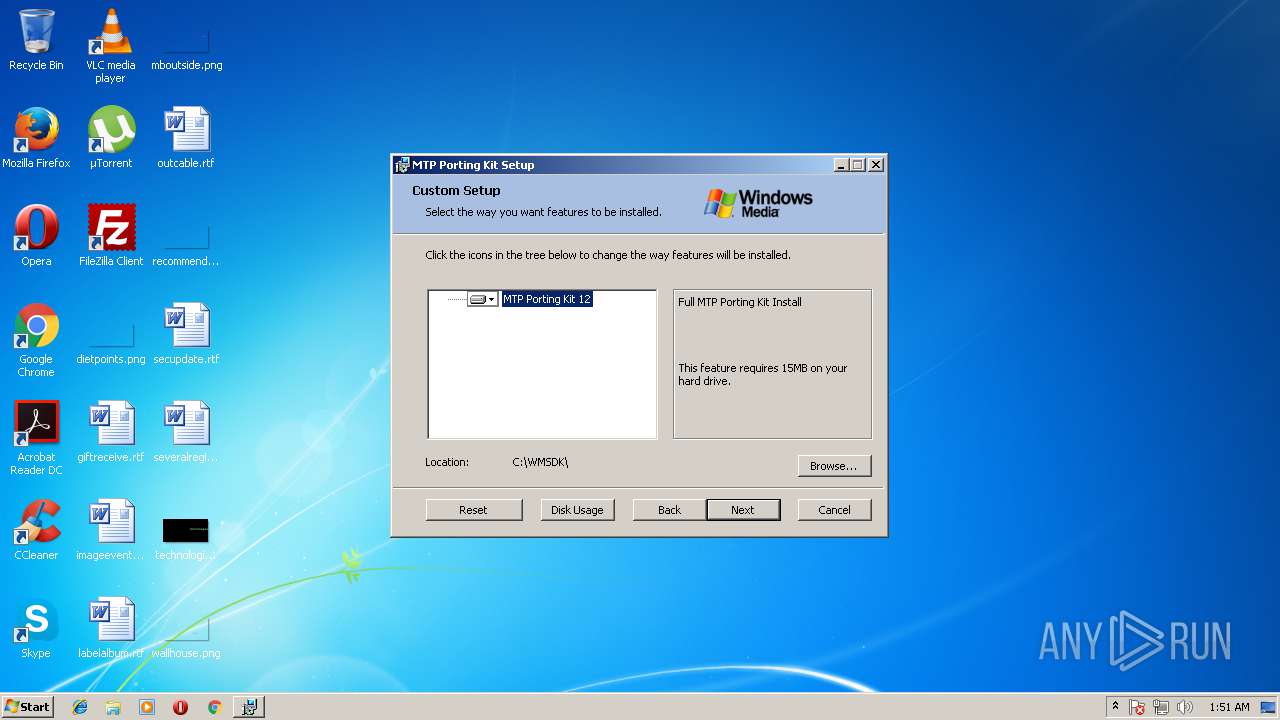
| 3212 | msiexec.exe | C:\WMSDK\MTPPK12\Responder\Windows\inc\BSDSockets.h | text | |
MD5:AED973B4F906680D9A7E86448C3EBC6C | SHA256:4733EFE27BD5BCE9177764CAD252993591CA43A1D3DDABC07ED7D060CBE82390 | |||
| 3212 | msiexec.exe | C:\WMSDK\MTPPK12\Responder\Windows\inc\External.txt | text | |
MD5:EA4CB9A140ABAFAF0C6CE7EE89E03756 | SHA256:620BBE4674C2D8F10A4D5A7B0DC401ABFFF124FC74D8BA17CDE13DF8F9B5754B | |||
| 3212 | msiexec.exe | C:\WMSDK\MTPPK12\MTPPK_Readme.htm | html | |
MD5:D0F18B37BA995A107A5B1DD4DFB391E4 | SHA256:0C7E2916E72332E394FA0CC3DF43403AE36F3D4CC0815C740D843798F1AC6873 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report