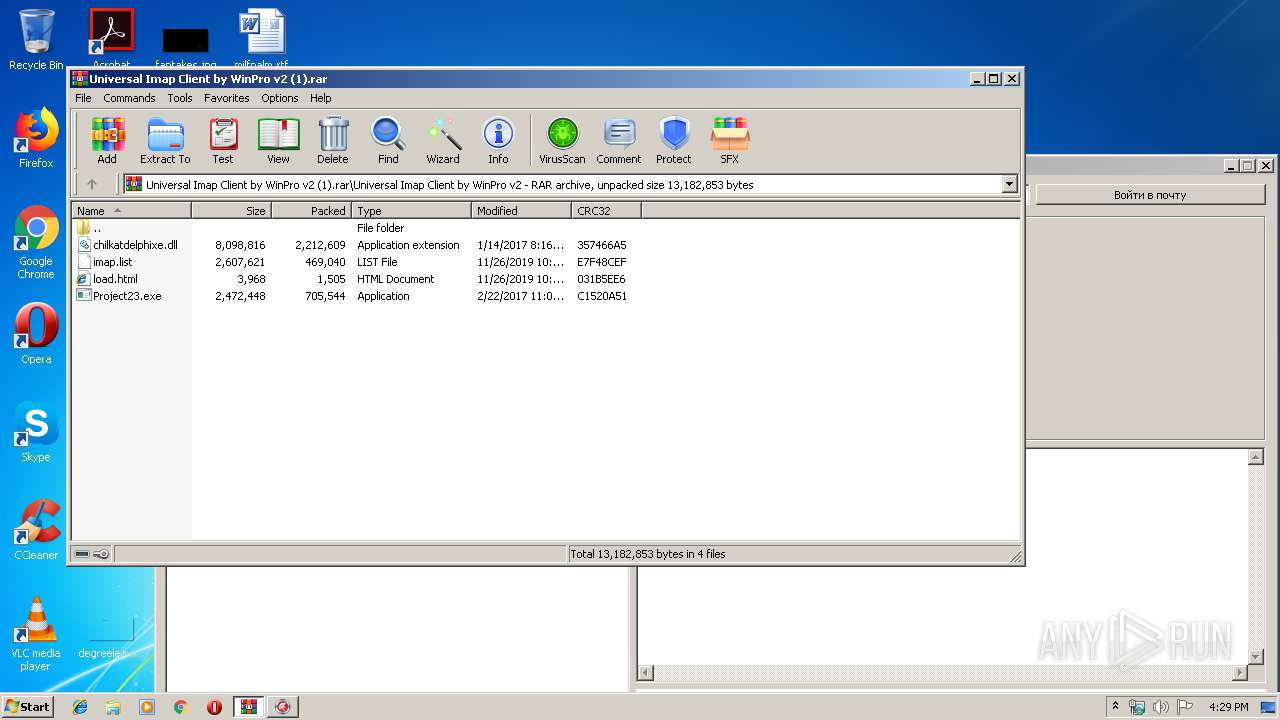
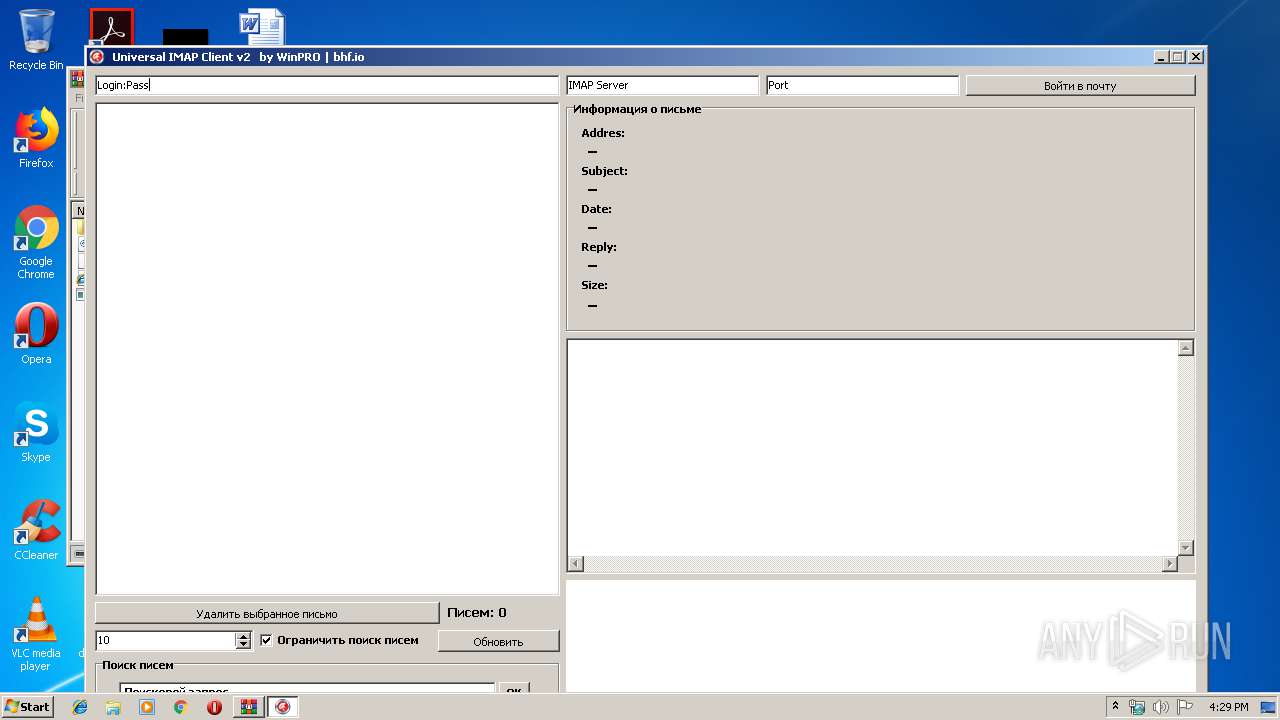
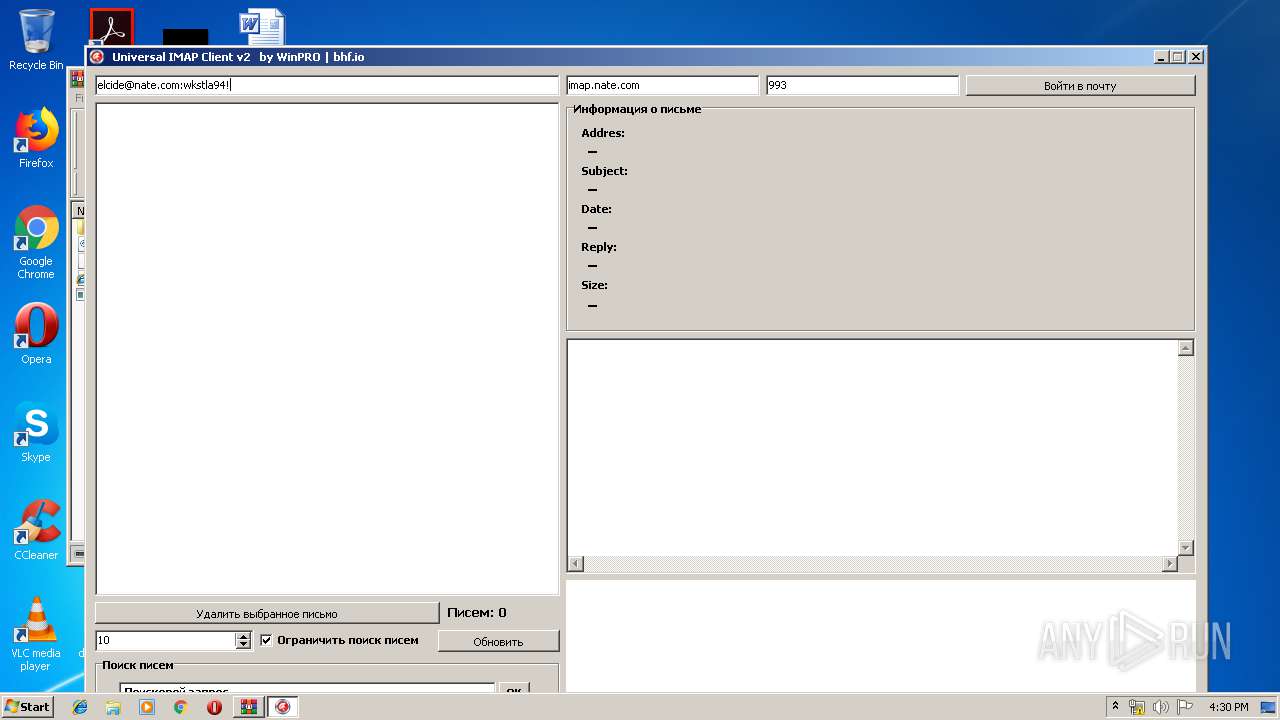
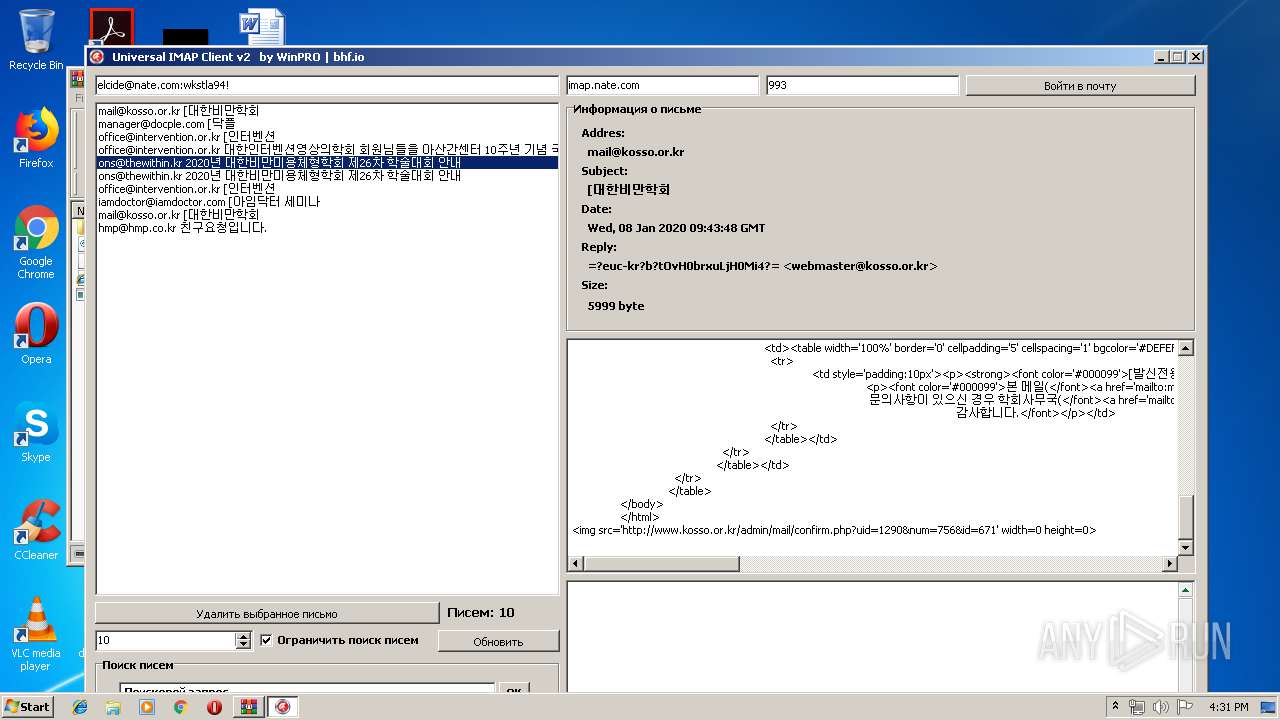
| File name: | Universal Imap Client by WinPro v2 (1).rar |
| Full analysis: | https://app.any.run/tasks/ac14897f-6d87-4df0-9ae5-f4bae45e999c |
| Verdict: | No threats detected |
| Analysis date: | January 11, 2020, 16:28:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
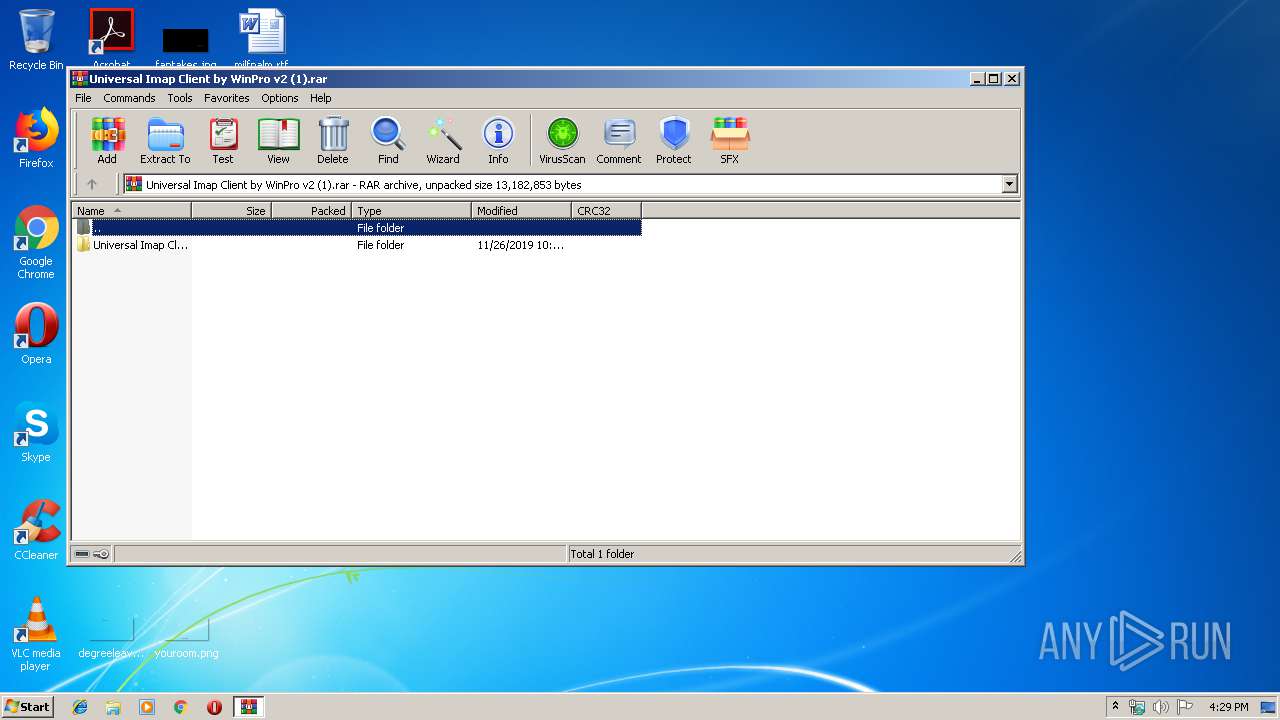
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 69FFA85607FC79726B204BC673D2FF96 |
| SHA1: | 5132F272E3CDCFC7CD1336D91F1633F5FC3D76E3 |
| SHA256: | 2EF5687E52C7B14F9E10AB1AFE0F018455E8AD07B517E5F535B436BA6E39A403 |
| SSDEEP: | 98304:NFpTfOmGHcl9y1DNKVR2RYvNcmav2paZtZDq8ed5:PFOt1DEVRfPKocLDhe/ |
MALICIOUS
Loads dropped or rewritten executable
- Project23.exe (PID: 2500)
Application was dropped or rewritten from another process
- Project23.exe (PID: 2500)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2720)
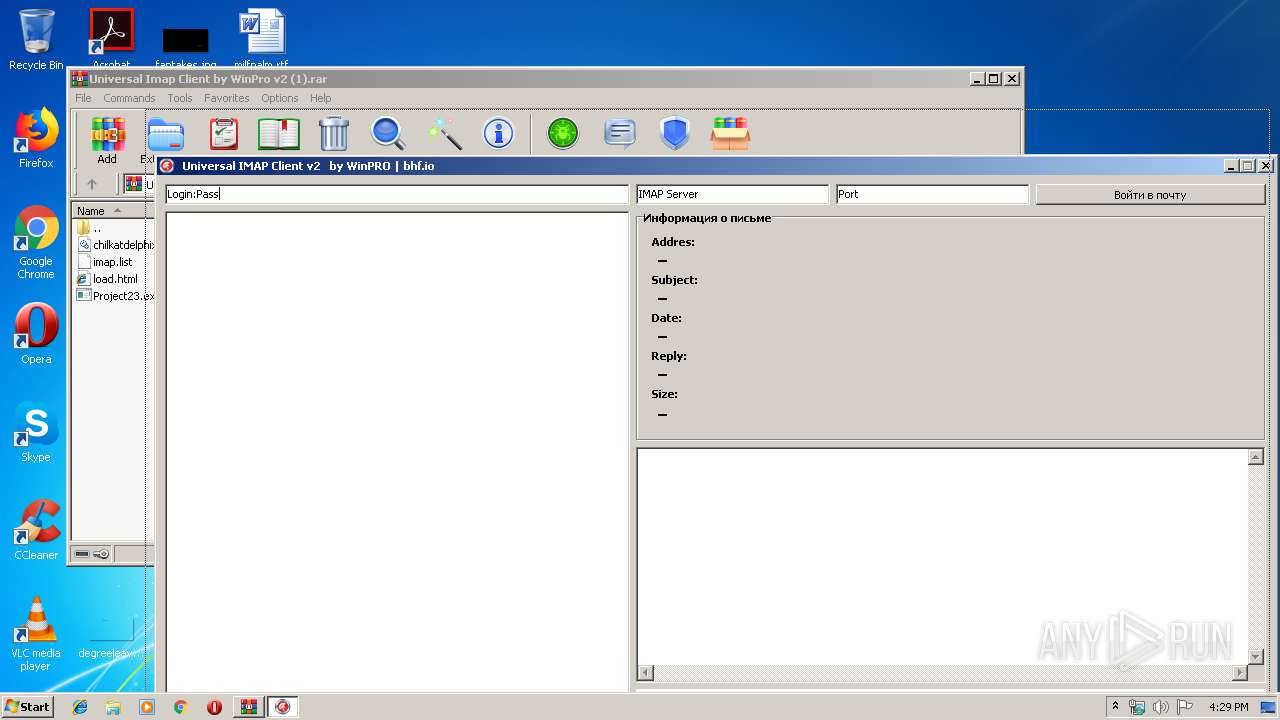
Reads internet explorer settings
- Project23.exe (PID: 2500)
Reads Internet Cache Settings
- Project23.exe (PID: 2500)
Connects to unusual port
- Project23.exe (PID: 2500)
Creates files in the user directory
- Project23.exe (PID: 2500)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
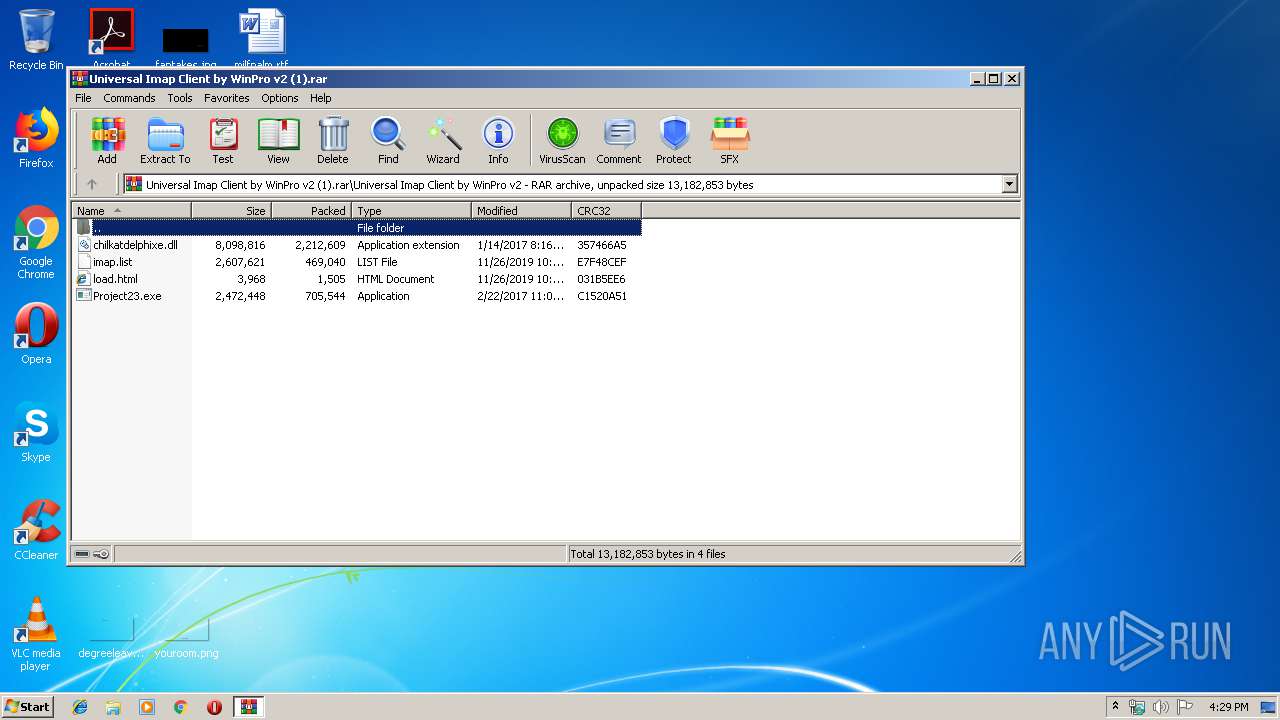
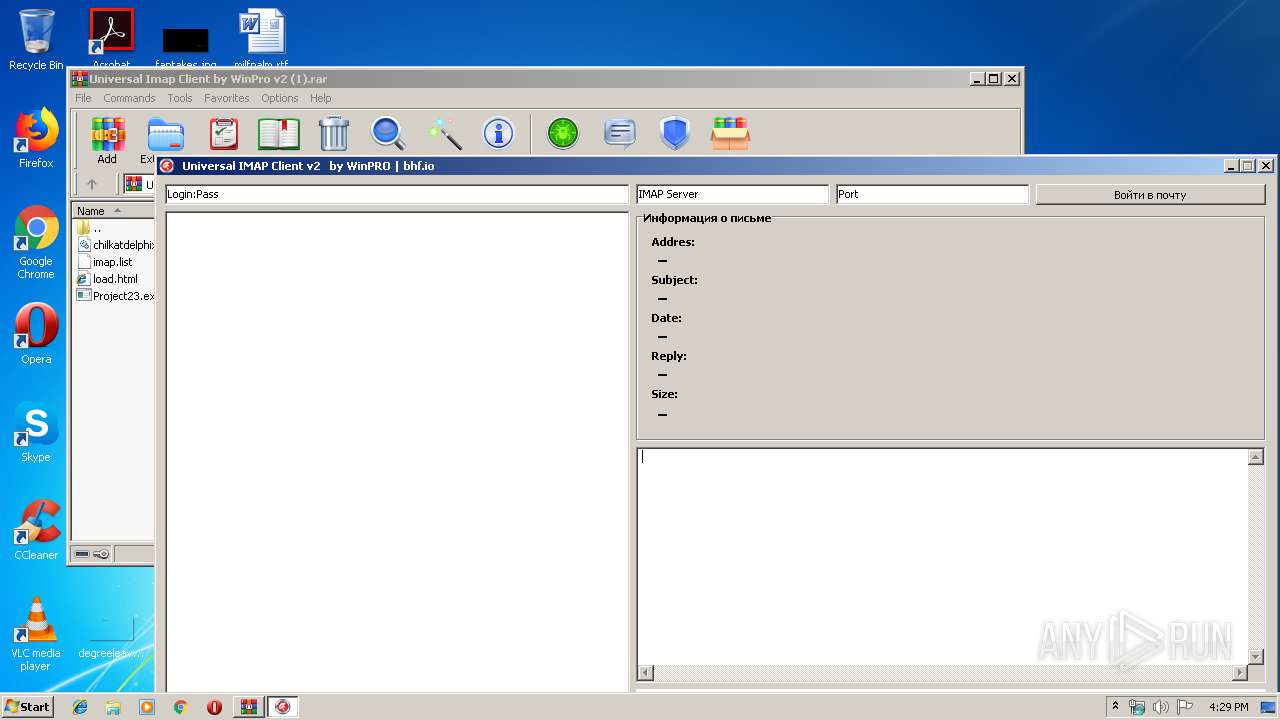
| 2500 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2720.15301\Universal Imap Client by WinPro v2\Project23.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2720.15301\Universal Imap Client by WinPro v2\Project23.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2720 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Universal Imap Client by WinPro v2 (1).rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
560
Read events
517
Write events
42
Delete events
1
Modification events
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Universal Imap Client by WinPro v2 (1).rar | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\ieframe.dll,-912 |
Value: HTML Document | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
10
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
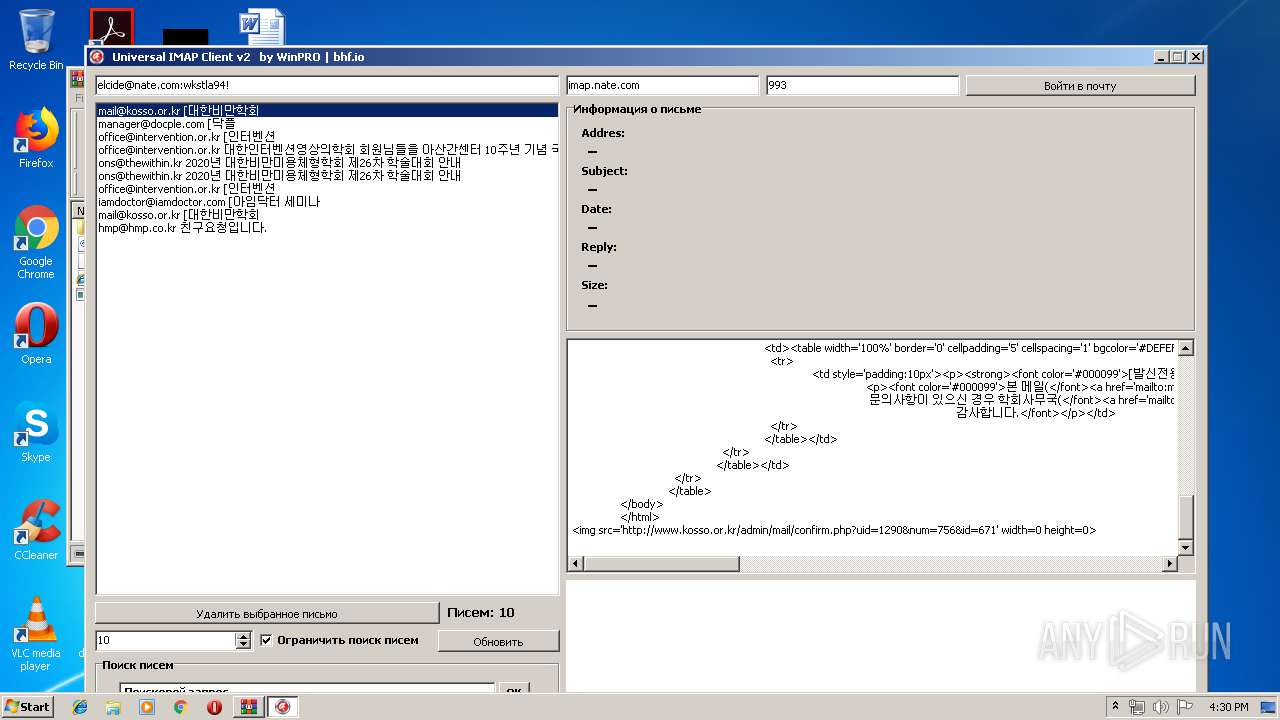
| 2500 | Project23.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\mail_top_2016[1].jpg | image | |
MD5:— | SHA256:— | |||
| 2500 | Project23.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\css2[1].css | text | |
MD5:— | SHA256:— | |||
| 2500 | Project23.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\mail_200108_0103[1].jpg | image | |
MD5:— | SHA256:— | |||
| 2500 | Project23.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\mail_200108_0101[1].jpg | image | |
MD5:— | SHA256:— | |||
| 2500 | Project23.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\mail_bottom_line_151229[1].gif | image | |
MD5:— | SHA256:— | |||
| 2500 | Project23.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012020011120200112\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2500 | Project23.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2720.15301\Universal Imap Client by WinPro v2\load.html | html | |
MD5:— | SHA256:— | |||
| 2500 | Project23.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\script[1].js | text | |
MD5:— | SHA256:— | |||
| 2500 | Project23.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\mail_200108_0102[1].jpg | image | |
MD5:— | SHA256:— | |||
| 2720 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2720.15301\Universal Imap Client by WinPro v2\load.html | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
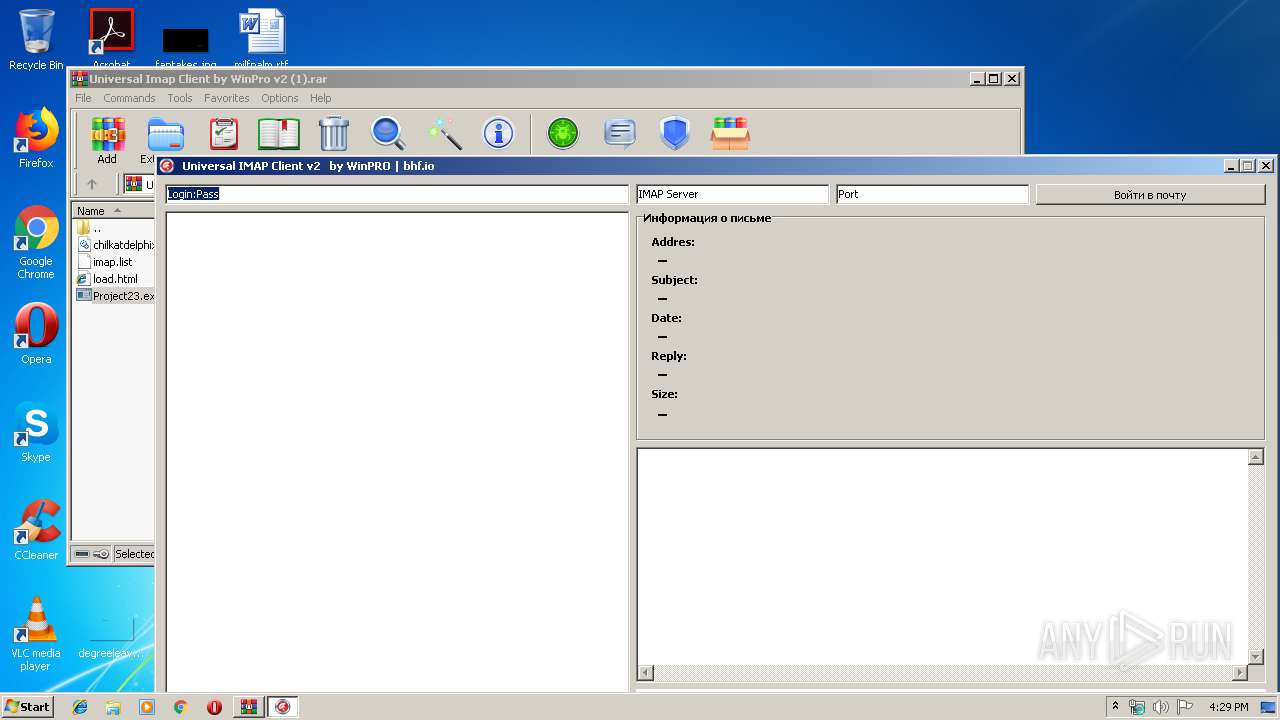
HTTP(S) requests
8
TCP/UDP connections
11
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
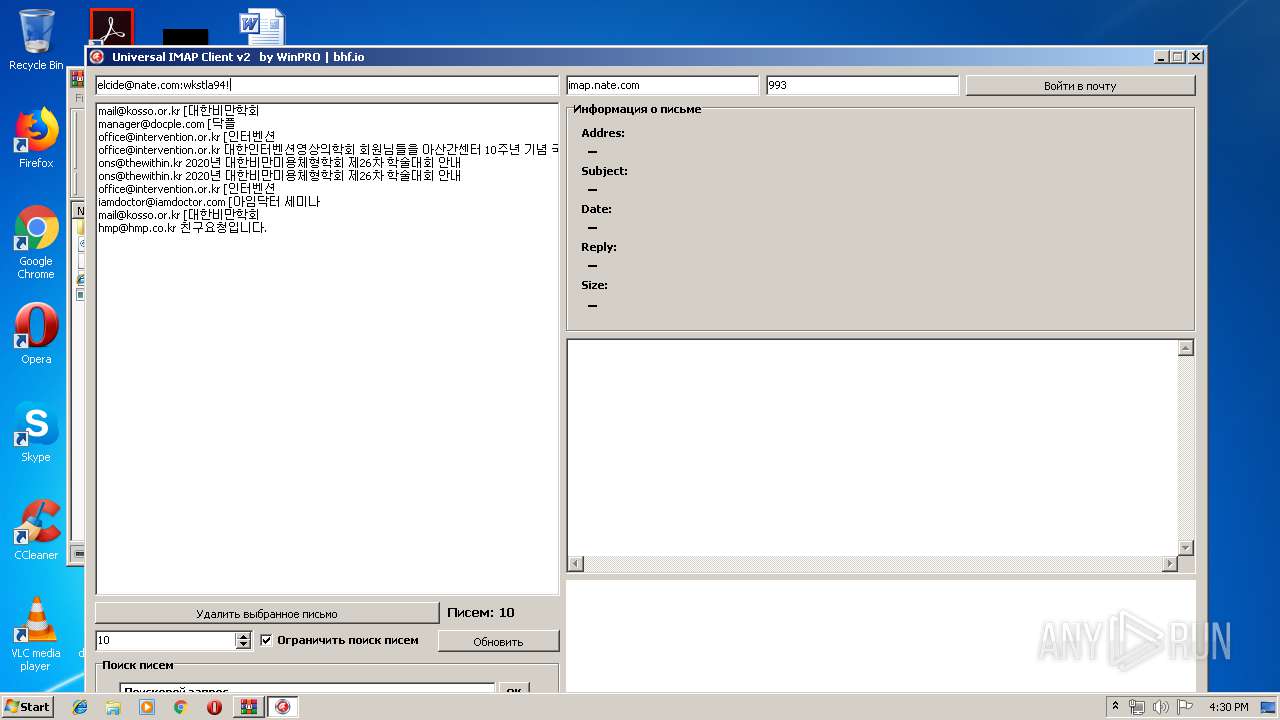
2500 | Project23.exe | GET | — | 114.108.163.166:80 | http://www.kosso.or.kr/js/css2.css | KR | — | — | unknown |
2500 | Project23.exe | GET | 200 | 114.108.163.166:80 | http://www.kosso.or.kr/js/script.js | KR | text | 23.7 Kb | unknown |
2500 | Project23.exe | GET | 200 | 114.108.163.166:80 | http://www.kosso.or.kr/mail/img/mail_200108_0102.jpg?ver=v3 | KR | image | 257 Kb | unknown |
2500 | Project23.exe | GET | 200 | 114.108.163.166:80 | http://www.kosso.or.kr/mail/img/mail_top_2016.jpg | KR | image | 42.4 Kb | unknown |
2500 | Project23.exe | GET | 200 | 114.108.163.166:80 | http://www.kosso.or.kr/mail/img/mail_200108_0101.jpg?ver=v3 | KR | image | 308 Kb | unknown |
2500 | Project23.exe | GET | 200 | 114.108.163.166:80 | http://www.kosso.or.kr/mail/img/mail_200108_0103.jpg | KR | image | 125 Kb | unknown |
2500 | Project23.exe | GET | 200 | 114.108.163.166:80 | http://www.kosso.or.kr/mail/img/mail_bottom_line_151229.gif | KR | image | 2.41 Kb | unknown |
2500 | Project23.exe | GET | 200 | 114.108.163.166:80 | http://www.kosso.or.kr/admin/mail/confirm.php?uid=1290&num=756&id=671 | KR | text | 117 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
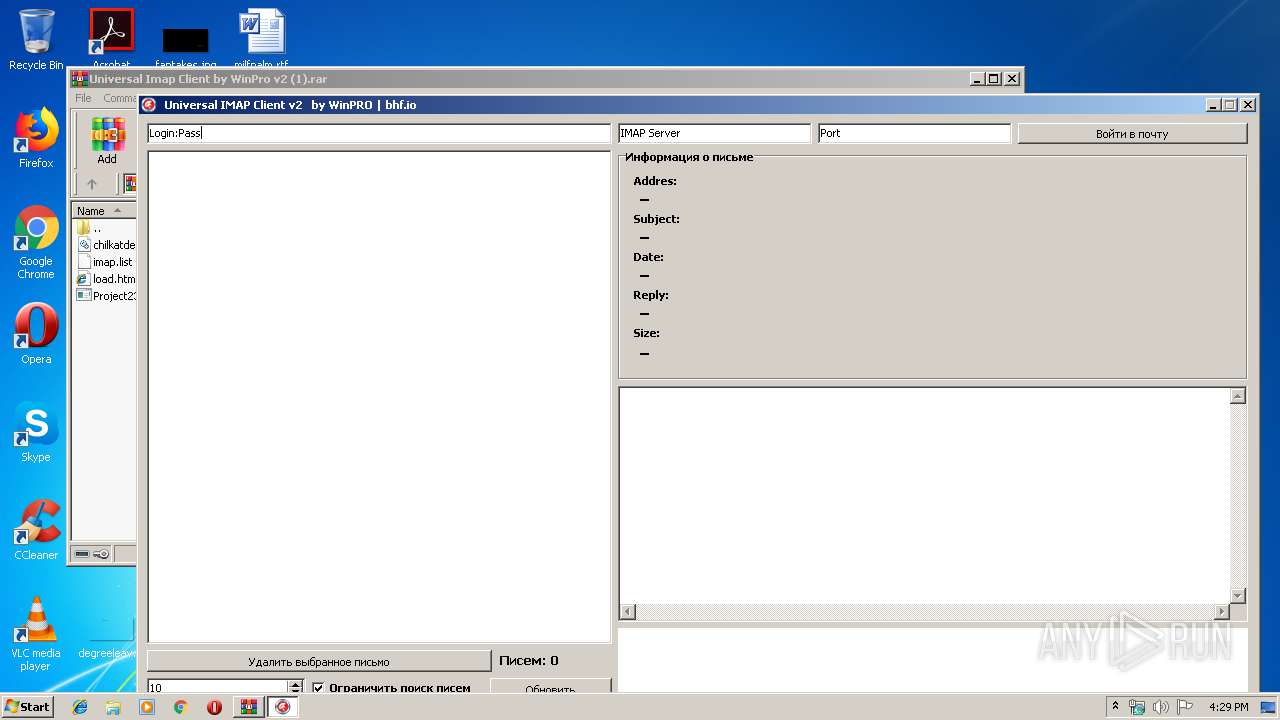
2500 | Project23.exe | 114.108.163.166:80 | www.kosso.or.kr | LG DACOM Corporation | KR | unknown |
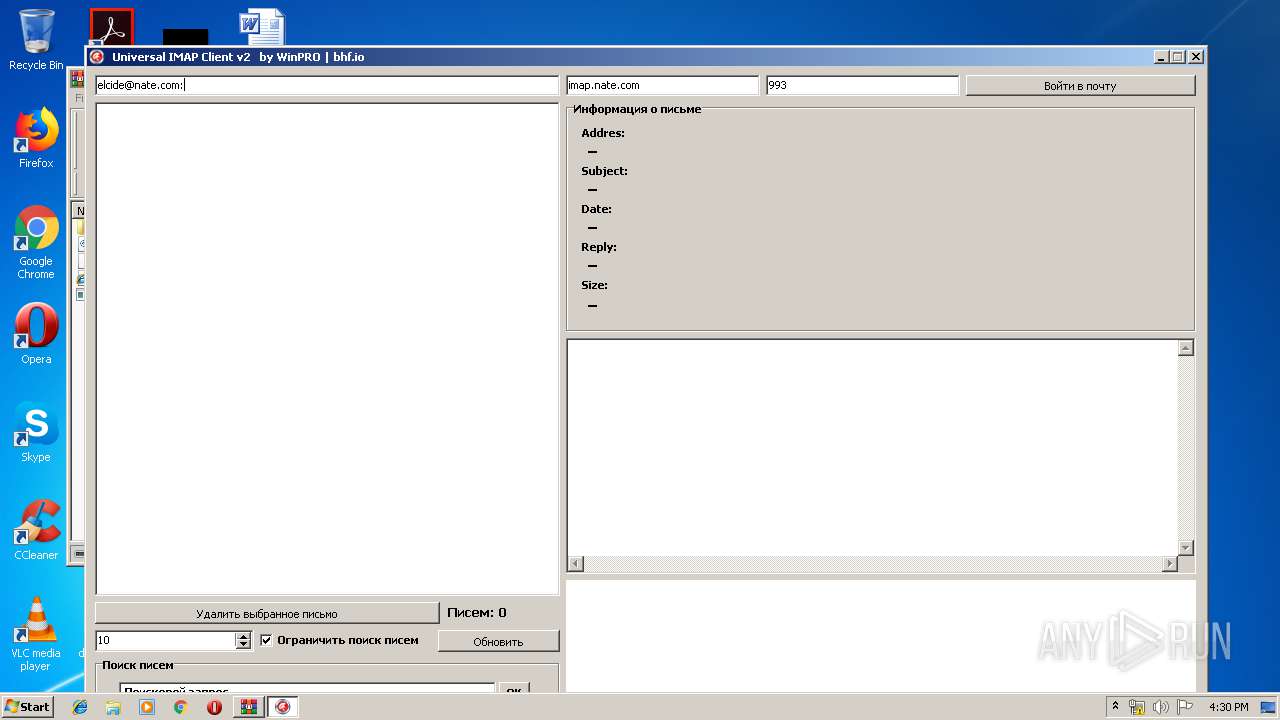
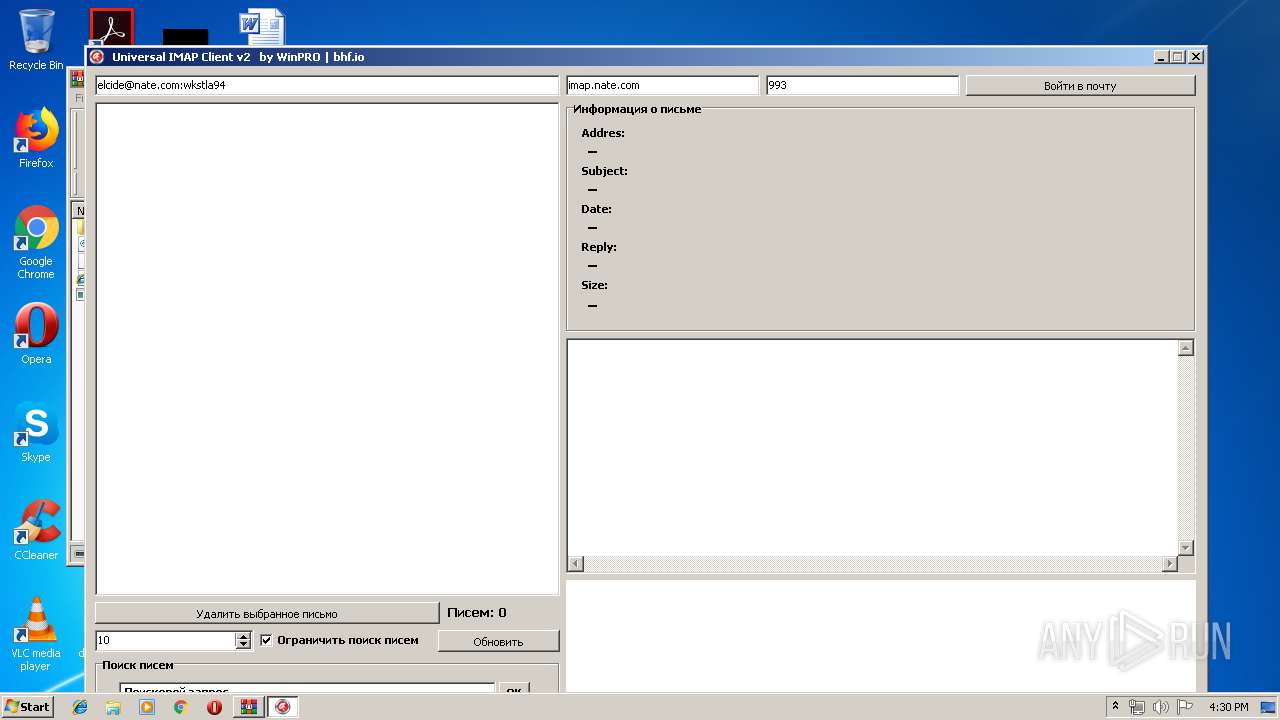
2500 | Project23.exe | 117.53.114.21:993 | imap.nate.com | SK communications | KR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
imap.nate.com |
| unknown |
www.kosso.or.kr |
| unknown |