| File name: | DLA.exe |
| Full analysis: | https://app.any.run/tasks/11d75d34-3a60-429a-ab42-c22fe8d79691 |
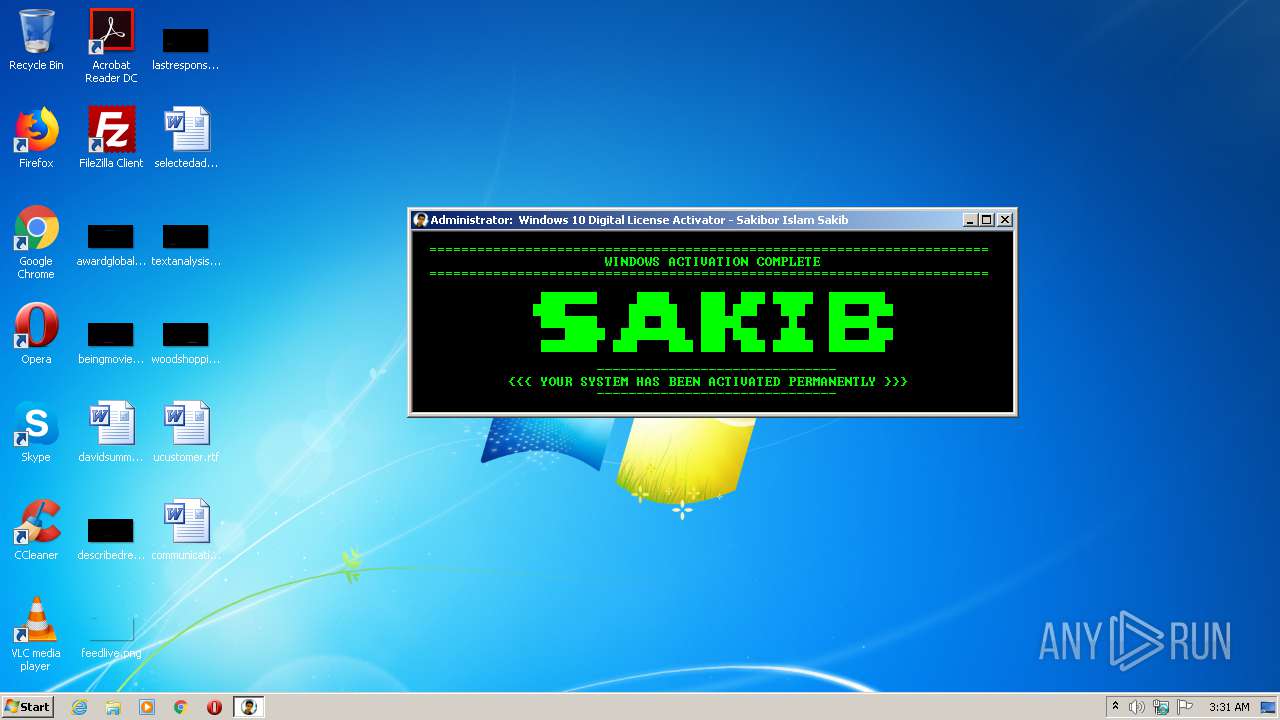
| Verdict: | Malicious activity |
| Analysis date: | July 07, 2020, 02:30:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, UPX compressed |
| MD5: | AF2D0238745ED676BA94EFB33BC73DA5 |
| SHA1: | BCB4AAA87F071AC1BC7C83F94C80365E6C276F24 |
| SHA256: | 2EEB2C65548A43F097504CD38D825F3B37A76DEAA18648DA8D0390B93467C044 |
| SSDEEP: | 49152:vNHmXpLfcDTWjw7A/Tqa1Ie0pB40de2EKTMiy1rzab8akZtFGvX7:mAWU7A/TqmdbENTirtU |
MALICIOUS
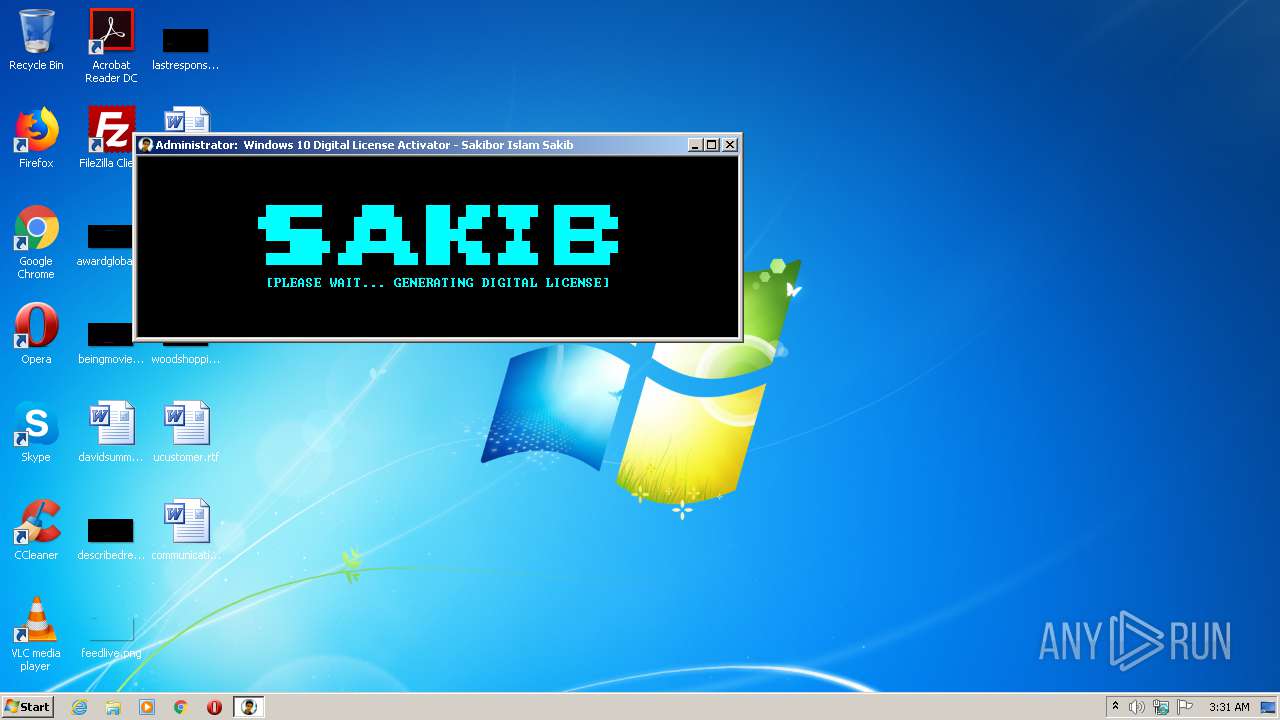
Application was dropped or rewritten from another process
- DigitalLicense.exe (PID: 840)
- GatherOsState.exe (PID: 2300)
Loads dropped or rewritten executable
- GatherOsState.exe (PID: 2300)
SUSPICIOUS
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 2888)
Starts CMD.EXE for commands execution
- DLA.exe (PID: 2556)
- cmd.exe (PID: 2272)
- DigitalLicense.exe (PID: 840)
Creates files in the user directory
- DLA.exe (PID: 2556)
Reads Environment values
- reg.exe (PID: 4076)
Executable content was dropped or overwritten
- DLA.exe (PID: 2556)
- DigitalLicense.exe (PID: 840)
Executes scripts
- cmd.exe (PID: 3748)
- cmd.exe (PID: 3092)
Creates files in the Windows directory
- DigitalLicense.exe (PID: 840)
- GatherOsState.exe (PID: 2300)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3828)
Application launched itself
- cmd.exe (PID: 2272)
Removes files from Windows directory
- DigitalLicense.exe (PID: 840)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.1) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.5) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:01 21:18:05+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 2306048 |
| InitializedDataSize: | 249856 |
| UninitializedDataSize: | 307200 |
| EntryPoint: | 0x27e210 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.1.0 |
| ProductVersionNumber: | 1.0.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileVersion: | 1.0.1.0 |
| ProductVersion: | 1.0.1.0 |
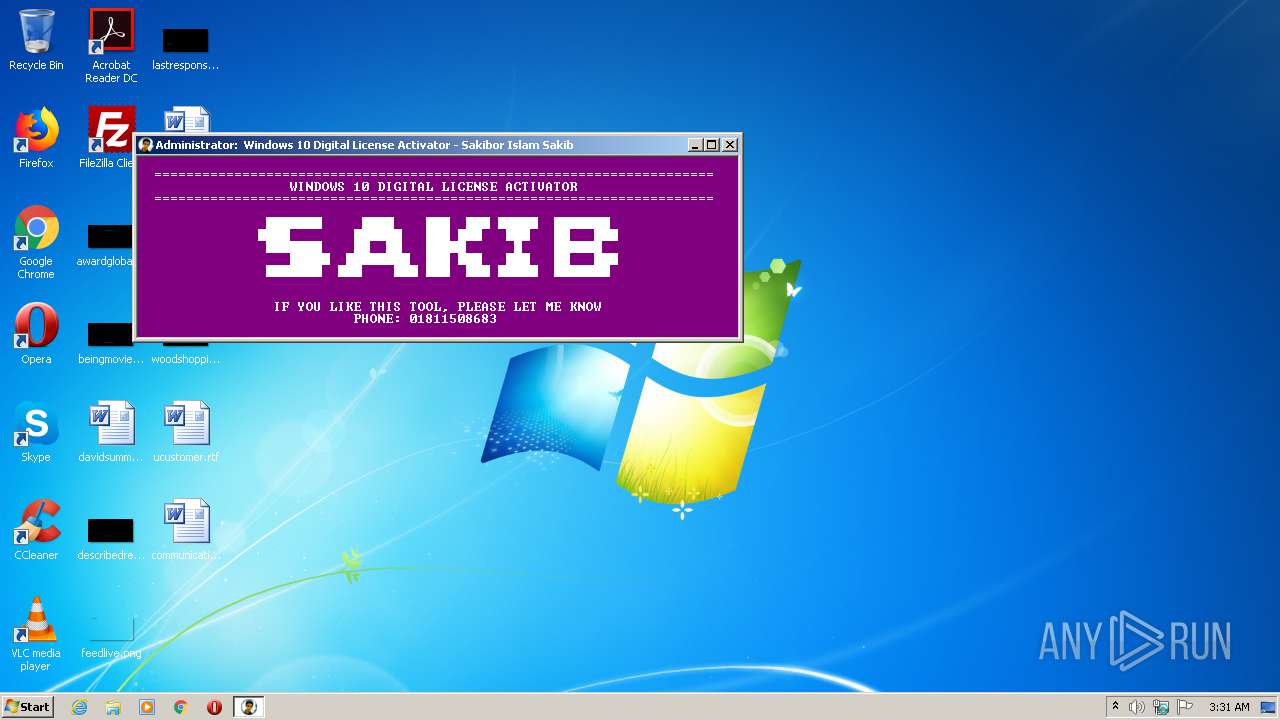
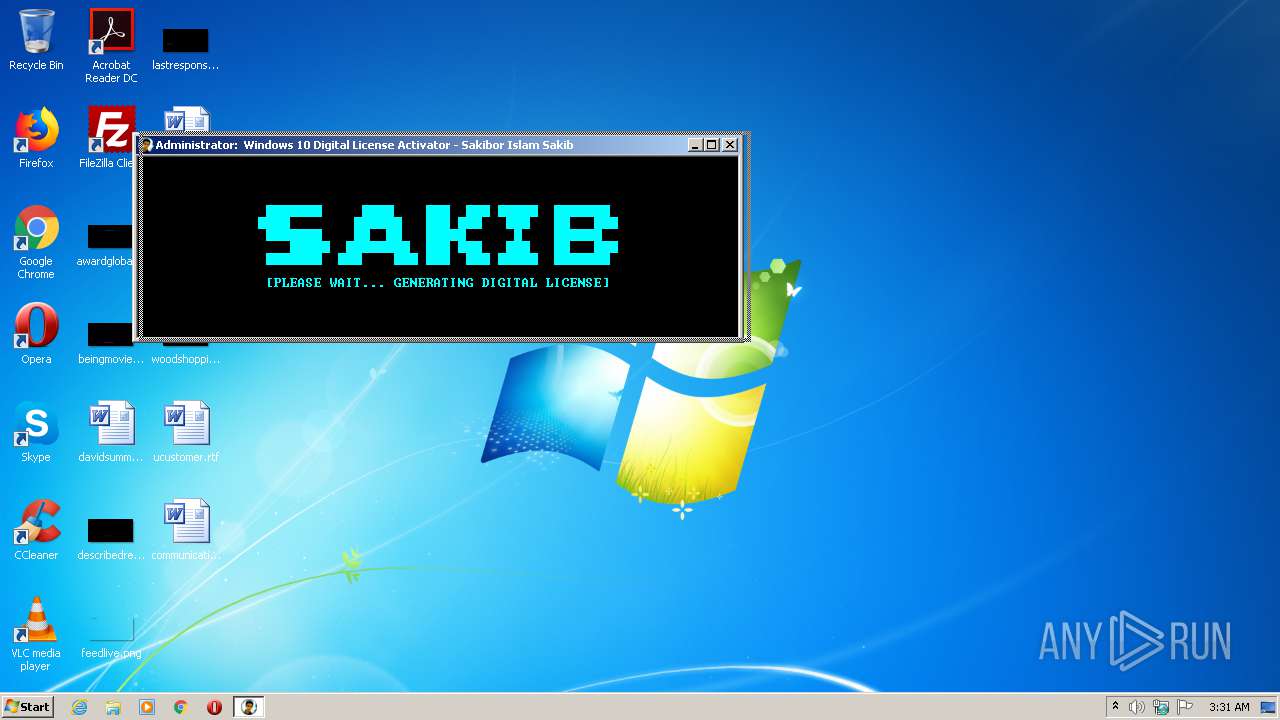
| ProductName: | Windows 10 Digital License Activator |
| FileDescription: | Windows 10 Digital License Activator |
| CompanyName: | Sakibor Islam Sakib |
| LegalTrademarks: | Sakibor Islam Sakib |
| LegalCopyright: | Sakibor Islam Sakib |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 01-Feb-2018 20:18:05 |
| Detected languages: |
|
| FileVersion: | 1.0.1.0 |
| ProductVersion: | 1.0.1.0 |
| ProductName: | Windows 10 Digital License Activator |
| FileDescription: | Windows 10 Digital License Activator |
| CompanyName: | Sakibor Islam Sakib |
| LegalTrademarks: | Sakibor Islam Sakib |
| LegalCopyright: | Sakibor Islam Sakib |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Feb-2018 20:18:05 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0004B000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0004C000 | 0x00233000 | 0x00232E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9999 |
.rsrc | 0x0027F000 | 0x0003D000 | 0x0003C400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.62173 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08821 | 672 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 4.92532 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.04578 | 38056 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.27156 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.47496 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.82556 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 6.017 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 6.35311 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
05C03F6700 | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
0DAE90A4F8E5270A1A589063B180528704D30000 | 7.99992 | 2221935 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.DLL |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
WINMM.DLL |
Total processes
63
Monitored processes
22
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | "C:\Users\admin\AppData\Local\Temp\DLA.exe" | C:\Users\admin\AppData\Local\Temp\DLA.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 840 | DigitalLicense.exe hidden | C:\Users\admin\AppData\Roaming\DigitalLicense.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Windows 10 Digital License Activator - Sakibor Islam Sakib Exit code: 0 Version: 1.0.1.0 Modules
| |||||||||||||||
| 860 | timeout /t 3 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 944 | C:\Windows\system32\cmd.exe /c "clipup -v -o -altto "C:\Windows\temp\GatherOsState1255484830"" | C:\Windows\system32\cmd.exe | — | DigitalLicense.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 944 | timeout /t 2 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 976 | mode con:cols=75 lines=15 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1268 | mode con: cols=75 lines=15 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1372 | timeout /t 3 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1740 | cscript.exe /nologo C:\Windows\system32\slmgr.vbs -ato | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2104 | mode con:cols=75 lines=15 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
189
Read events
184
Write events
3
Delete events
2
Modification events
| (PID) Process: | (840) DigitalLicense.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Tokens |
| Operation: | write | Name: | Channel |
Value: Retail | |||
| (PID) Process: | (840) DigitalLicense.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Tokens\Kernel |
| Operation: | write | Name: | Kernel-ProductInfo |
Value: 48 | |||
| (PID) Process: | (840) DigitalLicense.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Tokens\Kernel |
| Operation: | write | Name: | Security-SPP-GenuineLocalStatus |
Value: 1 | |||
| (PID) Process: | (840) DigitalLicense.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Tokens\Kernel |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (840) DigitalLicense.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Tokens |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
3
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2300 | GatherOsState.exe | C:\Windows\temp\GatherOsState1255484830\GenuineTicket.xml | xml | |
MD5:— | SHA256:— | |||
| 2556 | DLA.exe | C:\Users\admin\AppData\Local\Temp\980E.tmp\980F.tmp\9810.bat | text | |
MD5:— | SHA256:— | |||
| 840 | DigitalLicense.exe | C:\Windows\temp\GatherOsState1255484830\slc.dll | executable | |
MD5:31E221D3B930629A14ED2AF067F777E3 | SHA256:32073D9D5706476785E3FBCB208B65DFF56038C6CA9A8A2B15D2AB1590CC8E04 | |||
| 840 | DigitalLicense.exe | C:\Windows\temp\GatherOsState1255484830\GatherOsState.exe | executable | |
MD5:B13BC5B62F54607C334A6464D9B85CC8 | SHA256:51791625054B01802FD5AAA6C4A929827B369DFEF7B2891B5F55E0FA61AF0C7D | |||
| 2556 | DLA.exe | C:\Users\admin\AppData\Roaming\DigitalLicense.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2628 | wmiprvse.exe | POST | 302 | 184.25.217.162:80 | http://go.microsoft.com/fwlink/?LinkID=88341 | NL | — | — | whitelisted |
2628 | wmiprvse.exe | POST | 302 | 184.25.217.162:80 | http://go.microsoft.com/fwlink/?LinkID=88339 | NL | — | — | whitelisted |
2628 | wmiprvse.exe | POST | 302 | 184.25.217.162:80 | http://go.microsoft.com/fwlink/?LinkID=88340 | NL | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2628 | wmiprvse.exe | 40.91.122.234:443 | activation.sls.microsoft.com | Microsoft Corporation | US | unknown |
2628 | wmiprvse.exe | 184.25.217.162:80 | go.microsoft.com | Akamai International B.V. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
activation.sls.microsoft.com |
| whitelisted |