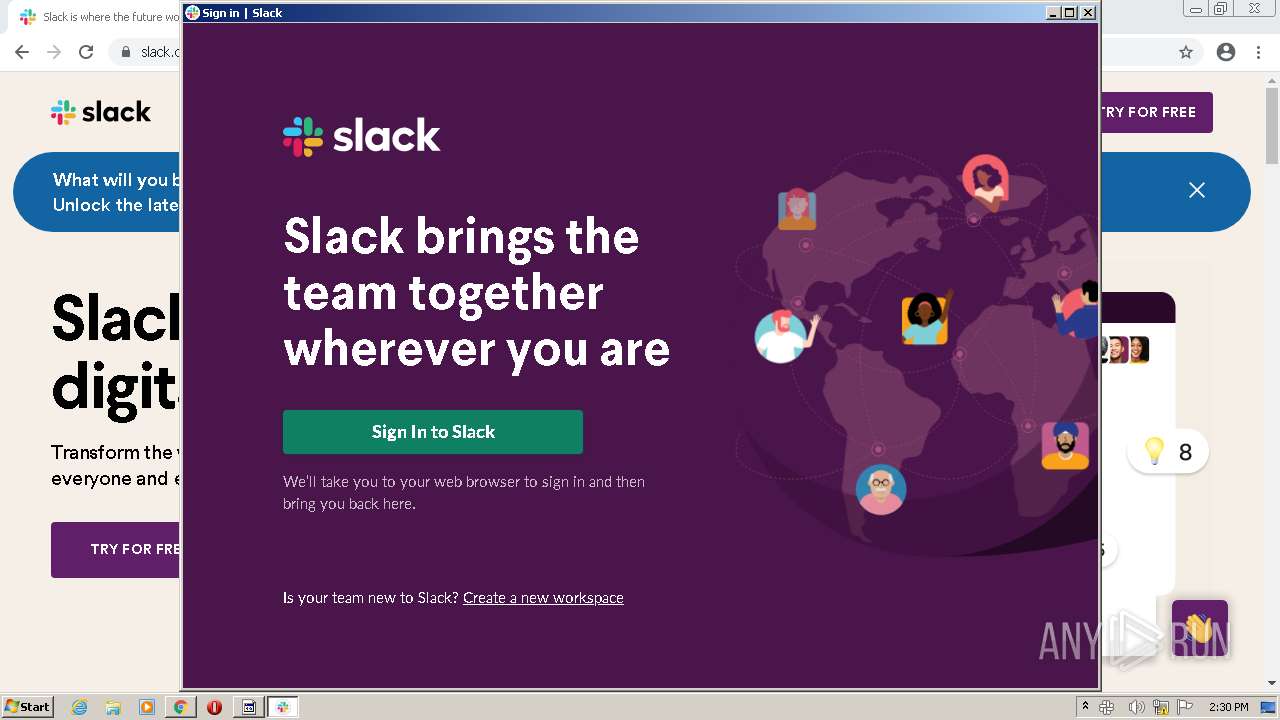
| URL: | https://files.slack.com |
| Full analysis: | https://app.any.run/tasks/d478f660-4952-4017-b2b0-457d621b0706 |
| Verdict: | Malicious activity |
| Analysis date: | February 24, 2022, 14:26:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D0459EC93384C89EA2EB9807147C50A4 |
| SHA1: | 7774EC2E9B1B10ECE98B73377A19E081A16A7AF9 |
| SHA256: | 2EE87A0DD437A20853F79F5EA722D89AE4800476C38A674A575D9DC8CD8D22AA |
| SSDEEP: | 3:N8MSyIn:2MYn |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 2420)
- Update.exe (PID: 2604)
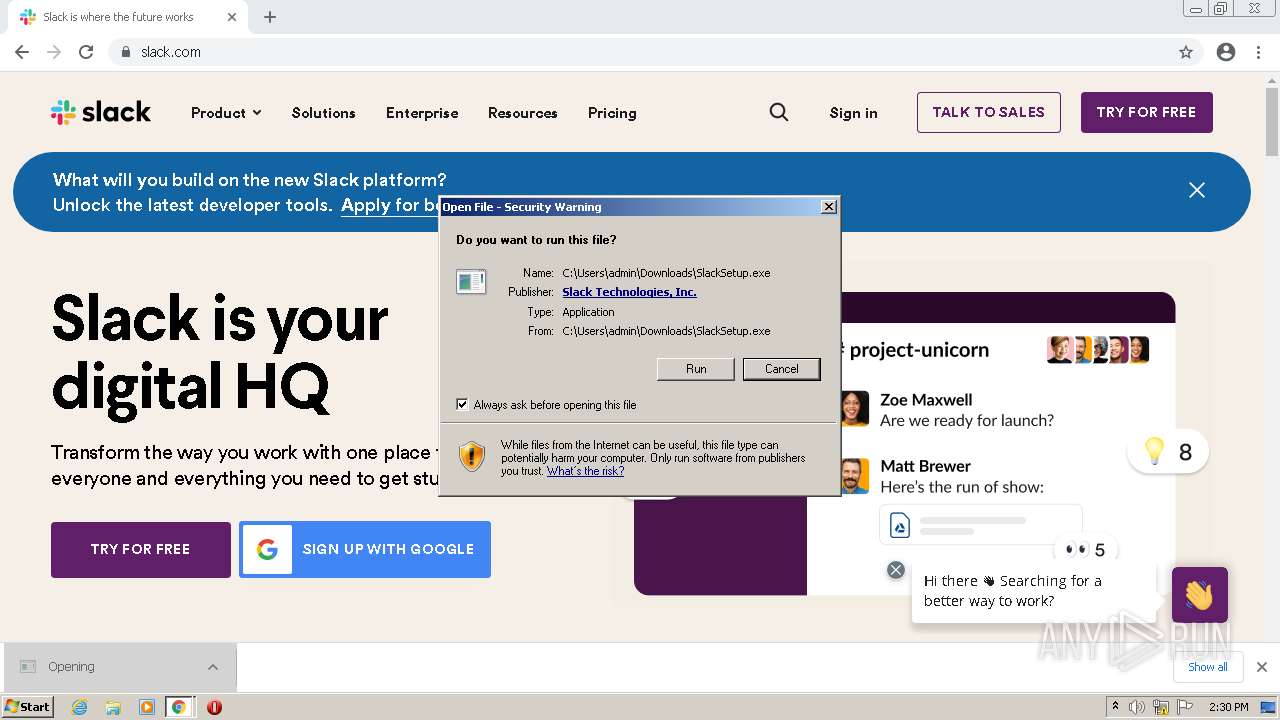
Application was dropped or rewritten from another process
- SlackSetup.exe (PID: 2276)
- Update.exe (PID: 2604)
- update.exe (PID: 2556)
- Squirrel.exe (PID: 3024)
Loads dropped or rewritten executable
- slack.exe (PID: 416)
- slack.exe (PID: 1780)
- slack.exe (PID: 128)
- slack.exe (PID: 1168)
- slack.exe (PID: 3272)
- slack.exe (PID: 2924)
- slack.exe (PID: 2552)
- slack.exe (PID: 2016)
- slack.exe (PID: 1340)
- slack.exe (PID: 2140)
Changes the autorun value in the registry
- slack.exe (PID: 416)
- slack.exe (PID: 128)
SUSPICIOUS
Drops a file that was compiled in debug mode
- chrome.exe (PID: 2420)
- Update.exe (PID: 2604)
Executable content was dropped or overwritten
- chrome.exe (PID: 2420)
- chrome.exe (PID: 2948)
- SlackSetup.exe (PID: 2276)
- Update.exe (PID: 2604)
Reads Microsoft Outlook installation path
- chrome.exe (PID: 3444)
- iexplore.exe (PID: 3488)
Checks supported languages
- SlackSetup.exe (PID: 2276)
- Update.exe (PID: 2604)
- Squirrel.exe (PID: 3024)
- slack.exe (PID: 416)
- update.exe (PID: 2556)
- slack.exe (PID: 128)
- slack.exe (PID: 3272)
- slack.exe (PID: 1168)
- slack.exe (PID: 2924)
- slack.exe (PID: 1780)
- slack.exe (PID: 2016)
- slack.exe (PID: 2552)
- slack.exe (PID: 2140)
- slack.exe (PID: 1340)
Reads the computer name
- Update.exe (PID: 2604)
- slack.exe (PID: 416)
- update.exe (PID: 2556)
- Squirrel.exe (PID: 3024)
- slack.exe (PID: 128)
- slack.exe (PID: 1780)
- slack.exe (PID: 3272)
- slack.exe (PID: 2924)
- slack.exe (PID: 2016)
Drops a file with too old compile date
- Update.exe (PID: 2604)
Reads Environment values
- slack.exe (PID: 416)
- Update.exe (PID: 2604)
- slack.exe (PID: 128)
Creates files in the user directory
- slack.exe (PID: 416)
- slack.exe (PID: 1168)
- update.exe (PID: 2556)
- slack.exe (PID: 128)
- slack.exe (PID: 2924)
Application launched itself
- slack.exe (PID: 416)
- slack.exe (PID: 128)
Changes default file association
- slack.exe (PID: 128)
Reads CPU info
- slack.exe (PID: 128)
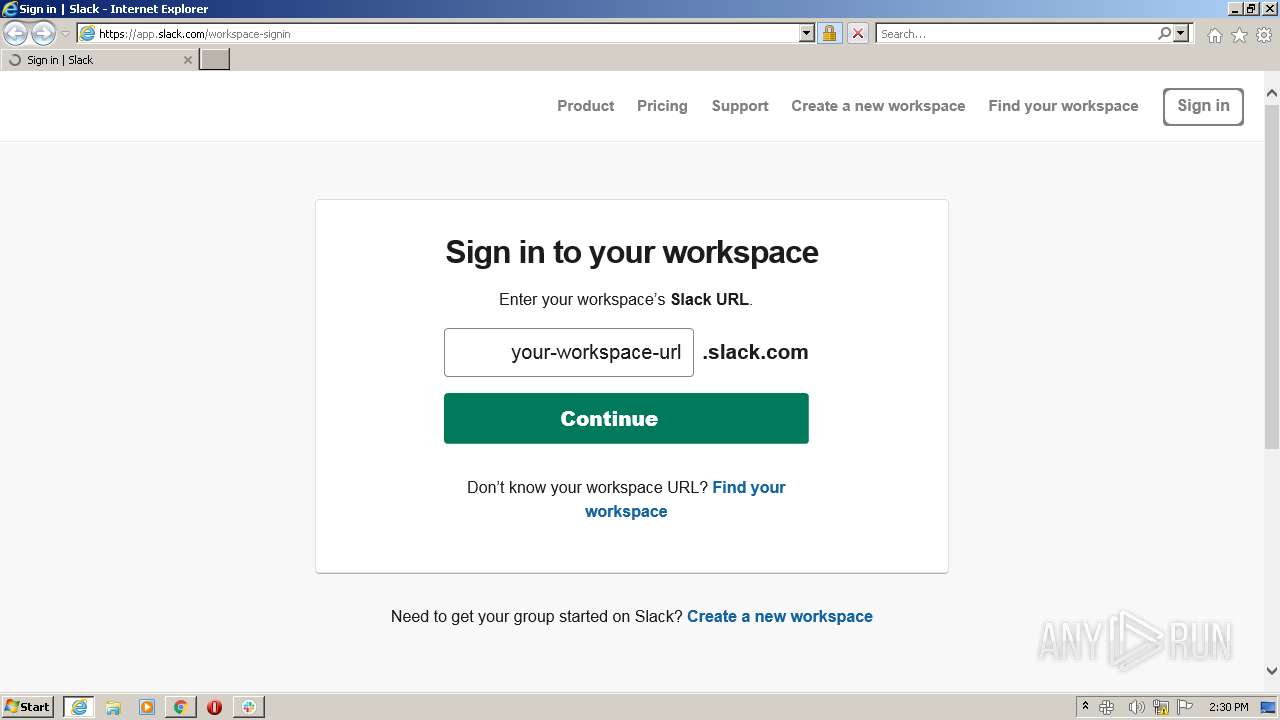
Starts Internet Explorer
- slack.exe (PID: 128)
Creates a software uninstall entry
- Update.exe (PID: 2604)
INFO
Checks supported languages
- chrome.exe (PID: 3160)
- chrome.exe (PID: 2572)
- chrome.exe (PID: 3148)
- chrome.exe (PID: 2948)
- chrome.exe (PID: 2300)
- chrome.exe (PID: 2412)
- chrome.exe (PID: 2304)
- chrome.exe (PID: 3684)
- chrome.exe (PID: 1396)
- chrome.exe (PID: 2284)
- chrome.exe (PID: 3448)
- chrome.exe (PID: 2172)
- chrome.exe (PID: 3072)
- chrome.exe (PID: 3236)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 2584)
- chrome.exe (PID: 2532)
- chrome.exe (PID: 116)
- chrome.exe (PID: 3804)
- chrome.exe (PID: 1344)
- chrome.exe (PID: 516)
- chrome.exe (PID: 3264)
- chrome.exe (PID: 4032)
- chrome.exe (PID: 2356)
- chrome.exe (PID: 3560)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 3400)
- chrome.exe (PID: 328)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 3880)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 2412)
- chrome.exe (PID: 3736)
- chrome.exe (PID: 2212)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 2200)
- chrome.exe (PID: 3828)
- chrome.exe (PID: 3304)
- chrome.exe (PID: 3292)
- chrome.exe (PID: 2124)
- chrome.exe (PID: 2884)
- chrome.exe (PID: 3444)
- chrome.exe (PID: 2792)
- chrome.exe (PID: 3024)
- chrome.exe (PID: 3532)
- chrome.exe (PID: 2928)
- chrome.exe (PID: 3080)
- WISPTIS.EXE (PID: 2028)
- iexplore.exe (PID: 3284)
- iexplore.exe (PID: 3488)
- chrome.exe (PID: 4072)
- chrome.exe (PID: 3456)
Application launched itself
- chrome.exe (PID: 2948)
- iexplore.exe (PID: 3284)
Reads the hosts file
- chrome.exe (PID: 2948)
- chrome.exe (PID: 2572)
- slack.exe (PID: 416)
- slack.exe (PID: 128)
- slack.exe (PID: 2924)
Reads the computer name
- chrome.exe (PID: 2948)
- chrome.exe (PID: 3160)
- chrome.exe (PID: 2572)
- chrome.exe (PID: 1396)
- chrome.exe (PID: 3236)
- chrome.exe (PID: 1344)
- chrome.exe (PID: 516)
- chrome.exe (PID: 2412)
- chrome.exe (PID: 3072)
- chrome.exe (PID: 3444)
- chrome.exe (PID: 2884)
- chrome.exe (PID: 2928)
- WISPTIS.EXE (PID: 2028)
- iexplore.exe (PID: 3284)
- iexplore.exe (PID: 3488)
Reads settings of System Certificates
- chrome.exe (PID: 2572)
- chrome.exe (PID: 2948)
- slack.exe (PID: 128)
- Update.exe (PID: 2604)
- iexplore.exe (PID: 3488)
- iexplore.exe (PID: 3284)
Reads the date of Windows installation
- chrome.exe (PID: 516)
Checks Windows Trust Settings
- chrome.exe (PID: 2948)
- iexplore.exe (PID: 3488)
- iexplore.exe (PID: 3284)
Dropped object may contain Bitcoin addresses
- Update.exe (PID: 2604)
Changes internet zones settings
- iexplore.exe (PID: 3284)
Creates files in the user directory
- iexplore.exe (PID: 3488)
Reads internet explorer settings
- iexplore.exe (PID: 3488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
107
Monitored processes
67
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,8420905723023492817,1863921715114014642,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4300 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 128 | "C:\Users\admin\AppData\Local\slack\app-4.23.0\slack.exe" --squirrel-firstrun | C:\Users\admin\AppData\Local\slack\app-4.23.0\slack.exe | Update.exe | ||||||||||||
User: admin Company: Slack Technologies Inc. Integrity Level: MEDIUM Description: Slack Exit code: 0 Version: 4.23.0 Modules
| |||||||||||||||
| 328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,8420905723023492817,1863921715114014642,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4000 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 416 | "C:\Users\admin\AppData\Local\slack\app-4.23.0\slack.exe" --squirrel-install 4.23.0 | C:\Users\admin\AppData\Local\slack\app-4.23.0\slack.exe | Update.exe | ||||||||||||
User: admin Company: Slack Technologies Inc. Integrity Level: MEDIUM Description: Slack Exit code: 0 Version: 4.23.0 Modules
| |||||||||||||||
| 516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,8420905723023492817,1863921715114014642,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1612 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1168 | C:\Users\admin\AppData\Local\slack\app-4.23.0\slack.exe --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Roaming\Slack /prefetch:7 --no-rate-limit --no-upload-gzip --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Roaming\Slack\Crashpad --url=https://slack.com/apps/sentryproxy/api/5277886/minidump/?sentry_key=fd30fe469dbf4aec9db40548e5acf91e --annotation=_productName=Slack --annotation=_version=4.23.0 --annotation=prod=Electron "--annotation=sentry___initialScope={\"release\":\"Slack@4.23.0\",\"environment\":\"production\",\"user\":{\"id\":\"f0bd91c9-3b7b-4709-af43-621c99931cfd\"},\"tags\":{\"uuid\":\"f0bd91c9-3b7b-4709-af43-621c99931cfd\"}}" --annotation=ver=16.0.4 --initial-client-data=0x2f4,0x2f8,0x2fc,0x2f0,0x300,0x75d79c0,0x75d79d0,0x75d79dc | C:\Users\admin\AppData\Local\slack\app-4.23.0\slack.exe | — | slack.exe | |||||||||||
User: admin Company: Slack Technologies Inc. Integrity Level: MEDIUM Description: Slack Exit code: 0 Version: 4.23.0 Modules
| |||||||||||||||
| 1340 | "C:\Users\admin\AppData\Local\slack\app-4.23.0\slack.exe" --type=gpu-process --field-trial-handle=1052,4080070804811838504,6684978680448821395,131072 --disable-features=AllowAggressiveThrottlingWithWebSocket,CalculateNativeWinOcclusion,HardwareMediaKeyHandling,IntensiveWakeUpThrottling,PlzServiceWorker,RequestInitiatorSiteLockEnfocement,SpareRendererForSitePerProcess,WebRtcHideLocalIpsWithMdns,WinRetrieveSuggestionsOnlyOnDemand --user-data-dir="C:\Users\admin\AppData\Roaming\Slack" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAANAAAAEAAAAAAAAAABAAAADQAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=disabled --mojo-platform-channel-handle=1680 /prefetch:2 | C:\Users\admin\AppData\Local\slack\app-4.23.0\slack.exe | — | slack.exe | |||||||||||
User: admin Company: Slack Technologies Inc. Integrity Level: LOW Description: Slack Exit code: 0 Version: 4.23.0 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,8420905723023492817,1863921715114014642,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4124 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1056,8420905723023492817,1863921715114014642,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1064 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1780 | "C:\Users\admin\AppData\Local\slack\app-4.23.0\slack.exe" --type=gpu-process --field-trial-handle=1088,14514596506543850274,13922954499449010311,131072 --disable-features=AllowAggressiveThrottlingWithWebSocket,CalculateNativeWinOcclusion,HardwareMediaKeyHandling,IntensiveWakeUpThrottling,PlzServiceWorker,RequestInitiatorSiteLockEnfocement,SpareRendererForSitePerProcess,WebRtcHideLocalIpsWithMdns,WinRetrieveSuggestionsOnlyOnDemand --user-data-dir="C:\Users\admin\AppData\Roaming\Slack" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAANAAAAEAAAAAAAAAABAAAADQAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1120 /prefetch:2 | C:\Users\admin\AppData\Local\slack\app-4.23.0\slack.exe | — | slack.exe | |||||||||||
User: admin Company: Slack Technologies Inc. Integrity Level: LOW Description: Slack Exit code: 0 Version: 4.23.0 Modules
| |||||||||||||||
Total events
51 939
Read events
51 507
Write events
425
Delete events
7
Modification events
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
97
Suspicious files
91
Text files
302
Unknown types
110
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62179592-B84.pma | — | |
MD5:— | SHA256:— | |||
| 2948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\71f0aa22-fd60-43d0-9783-3ebd9eeb7dc4.tmp | text | |
MD5:— | SHA256:— | |||
| 2948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFede65.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 2948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\99b98a50-861d-4169-8af7-bbd47f6dae23.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 2948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFedf7e.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 2948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old~RFee27c.TMP | text | |
MD5:D0BA19096D6C8F8DE58312E8D938E893 | SHA256:AADE90A7B0984F3C719D528E4E6FAE3854E28B30363BDD4DF65037E69784A078 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
223
DNS requests
132
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | html | 593 b | whitelisted |
884 | svchost.exe | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | html | 559 b | whitelisted |
2572 | chrome.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
884 | svchost.exe | GET | 206 | 74.125.8.72:80 | http://r3---sn-5hneknee.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx?cms_redirect=yes&mh=X7&mip=212.30.37.63&mm=28&mn=sn-5hneknee&ms=nvh&mt=1645712420&mv=m&mvi=3&pl=24&shardbypass=yes&smhost=r3---sn-5hnekn7s.gvt1.com | US | binary | 7.39 Kb | whitelisted |
884 | svchost.exe | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | html | 559 b | whitelisted |
884 | svchost.exe | HEAD | 200 | 209.85.226.71:80 | http://r2---sn-5hnekn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOGMyQUFYUjhaZkNqaEUyZDFCRWM2S3dUZw/1.0.0.11_llkgjffcdpffmhiakmfcdcblohccpfmo.crx?cms_redirect=yes&mh=mM&mip=212.30.37.63&mm=28&mn=sn-5hnekn7k&ms=nvh&mt=1645712420&mv=m&mvi=2&pl=24&rmhost=r1---sn-5hnekn7k.gvt1.com&shardbypass=yes&smhost=r1---sn-5hnekn7l.gvt1.com | US | — | — | whitelisted |
884 | svchost.exe | HEAD | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOGMyQUFYUjhaZkNqaEUyZDFCRWM2S3dUZw/1.0.0.11_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
884 | svchost.exe | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | html | 559 b | whitelisted |
884 | svchost.exe | GET | 206 | 74.125.8.72:80 | http://r3---sn-5hneknee.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx?cms_redirect=yes&mh=X7&mip=212.30.37.63&mm=28&mn=sn-5hneknee&ms=nvh&mt=1645712420&mv=m&mvi=3&pl=24&shardbypass=yes&smhost=r3---sn-5hnekn7s.gvt1.com | US | binary | 18.2 Kb | whitelisted |
884 | svchost.exe | GET | 206 | 74.125.8.72:80 | http://r3---sn-5hneknee.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx?cms_redirect=yes&mh=X7&mip=212.30.37.63&mm=28&mn=sn-5hneknee&ms=nvh&mt=1645712420&mv=m&mvi=3&pl=24&shardbypass=yes&smhost=r3---sn-5hnekn7s.gvt1.com | US | binary | 14.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2572 | chrome.exe | 18.66.248.90:443 | files.slack.com | Massachusetts Institute of Technology | US | unknown |
2572 | chrome.exe | 172.217.18.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
2572 | chrome.exe | 108.157.4.123:443 | a.slack-edge.com | — | US | malicious |
2572 | chrome.exe | 142.250.185.173:443 | accounts.google.com | Google Inc. | US | suspicious |
2572 | chrome.exe | 18.159.197.225:443 | slack.com | Massachusetts Institute of Technology | US | unknown |
2572 | chrome.exe | 104.75.88.161:443 | cdn.optimizely.com | Akamai Technologies, Inc. | NL | unknown |
2572 | chrome.exe | 104.16.148.64:443 | cdn.cookielaw.org | Cloudflare Inc | US | unknown |
2572 | chrome.exe | 104.20.185.68:443 | geolocation.onetrust.com | Cloudflare Inc | US | shared |
2572 | chrome.exe | 104.89.17.148:443 | a11179690159.cdn.optimizely.com | Akamai Technologies, Inc. | NL | suspicious |
2572 | chrome.exe | 104.90.152.53:443 | cdn3.optimizely.com | Akamai Technologies, Inc. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
files.slack.com |
| shared |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
slack.com |
| whitelisted |
a.slack-edge.com |
| whitelisted |
cdn.cookielaw.org |
| whitelisted |
cdn.optimizely.com |
| whitelisted |
geolocation.onetrust.com |
| whitelisted |
cdn3.optimizely.com |
| whitelisted |
www.youtube.com |
| whitelisted |