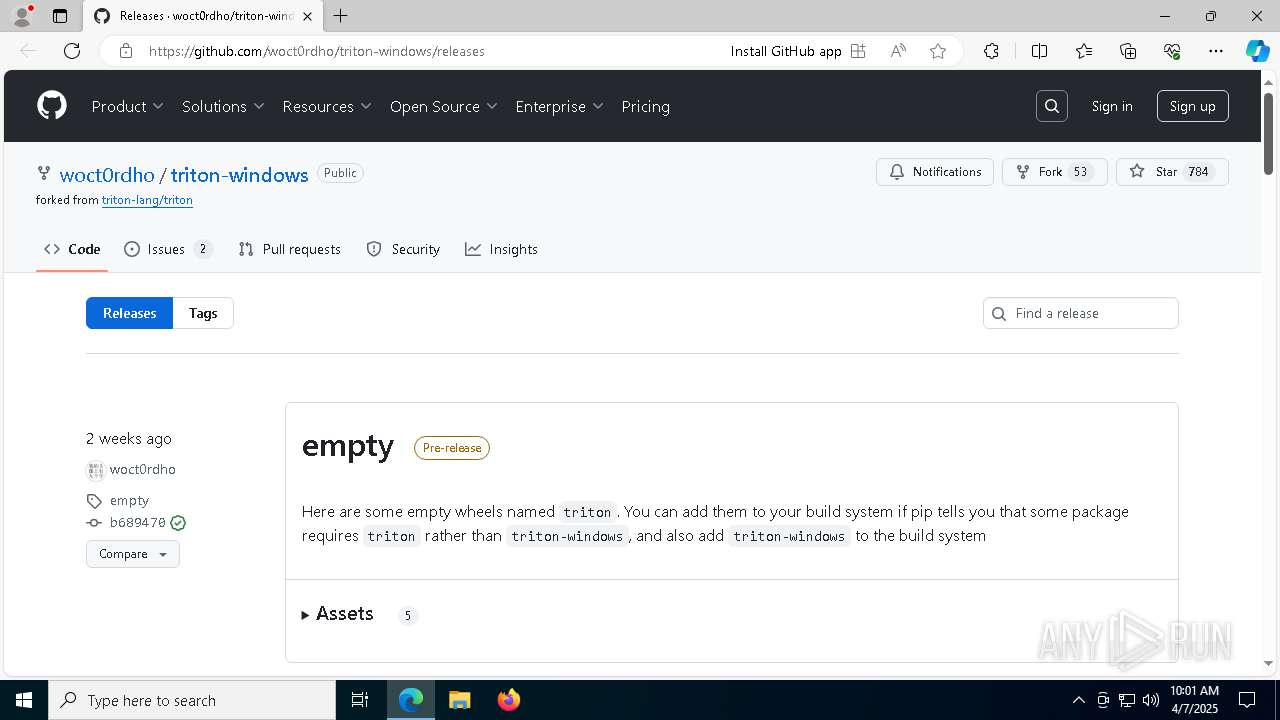
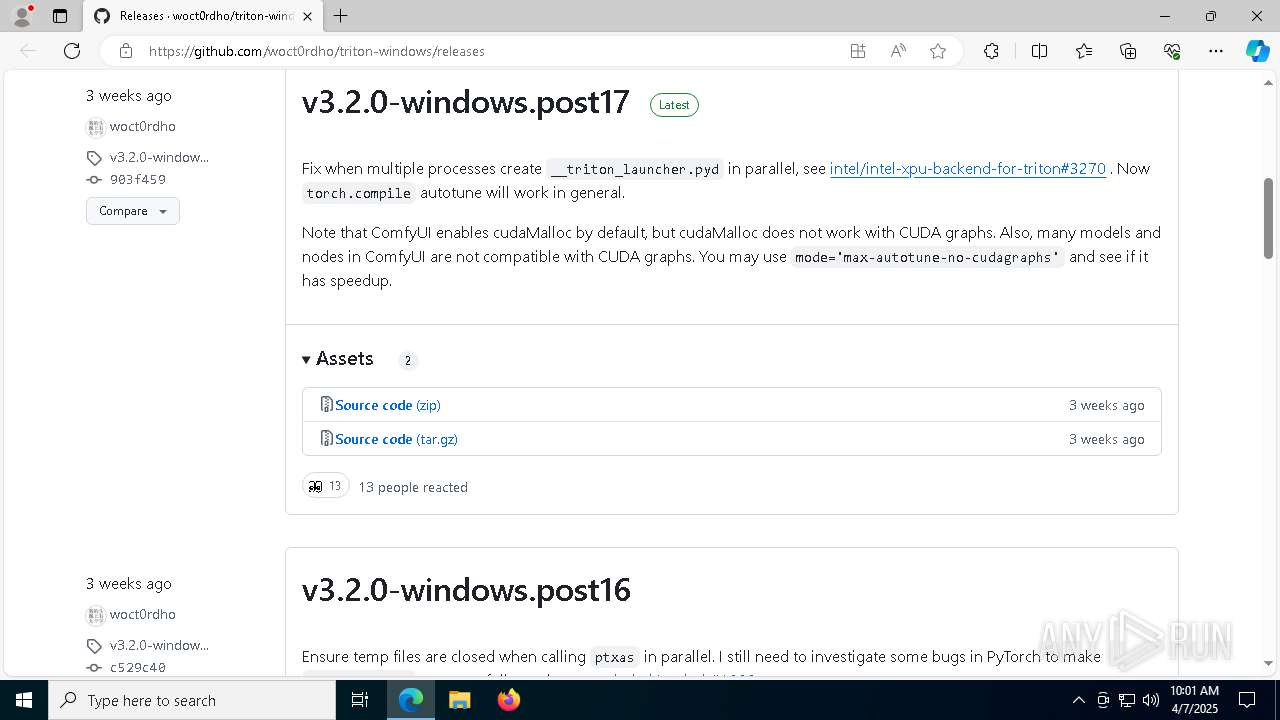
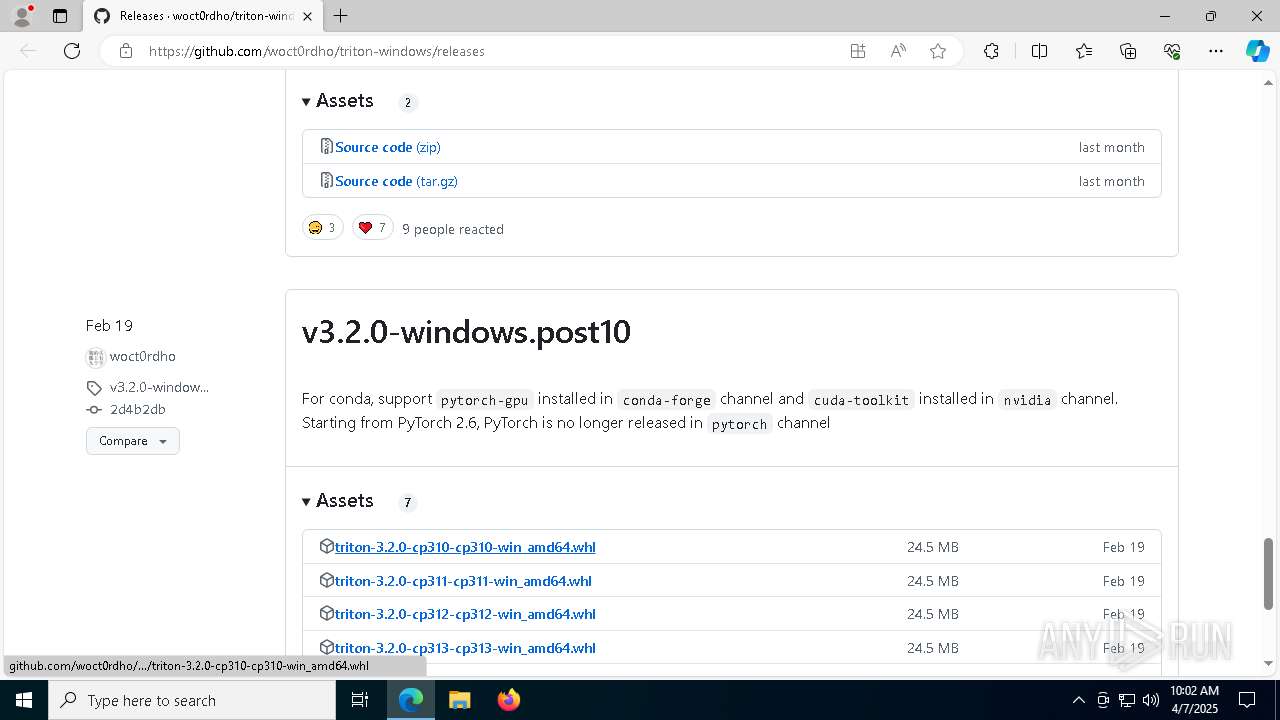
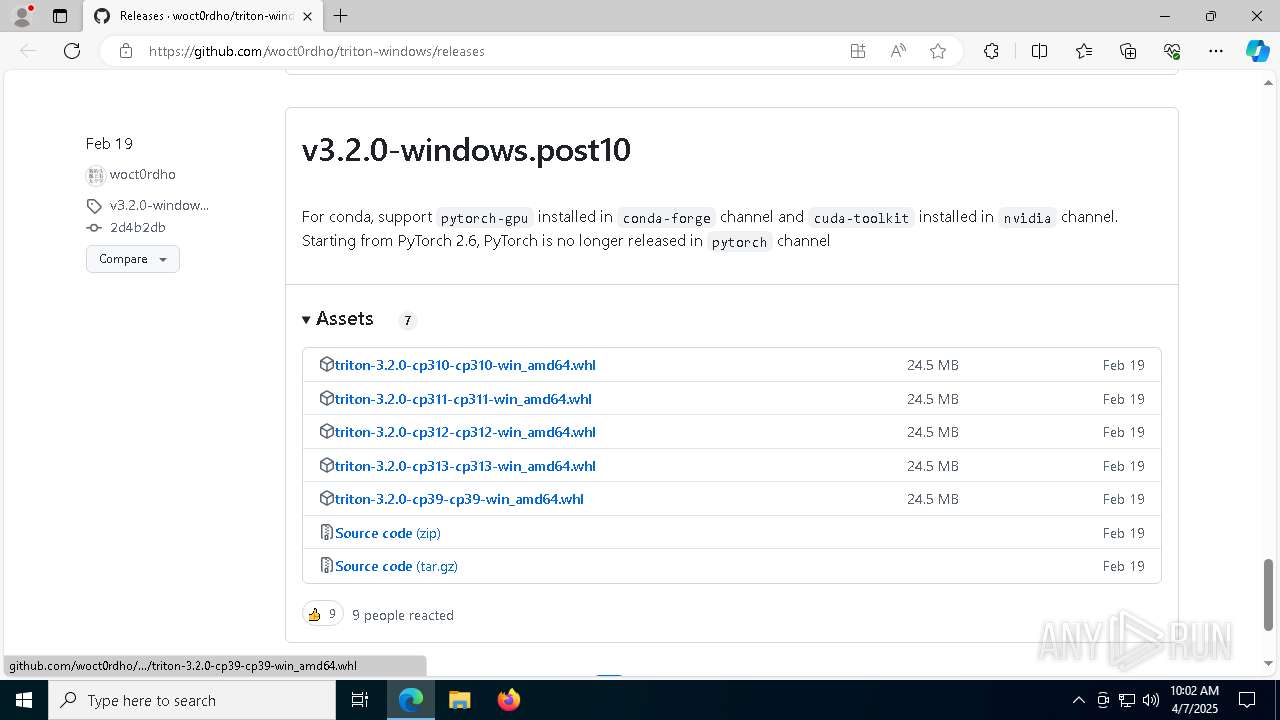
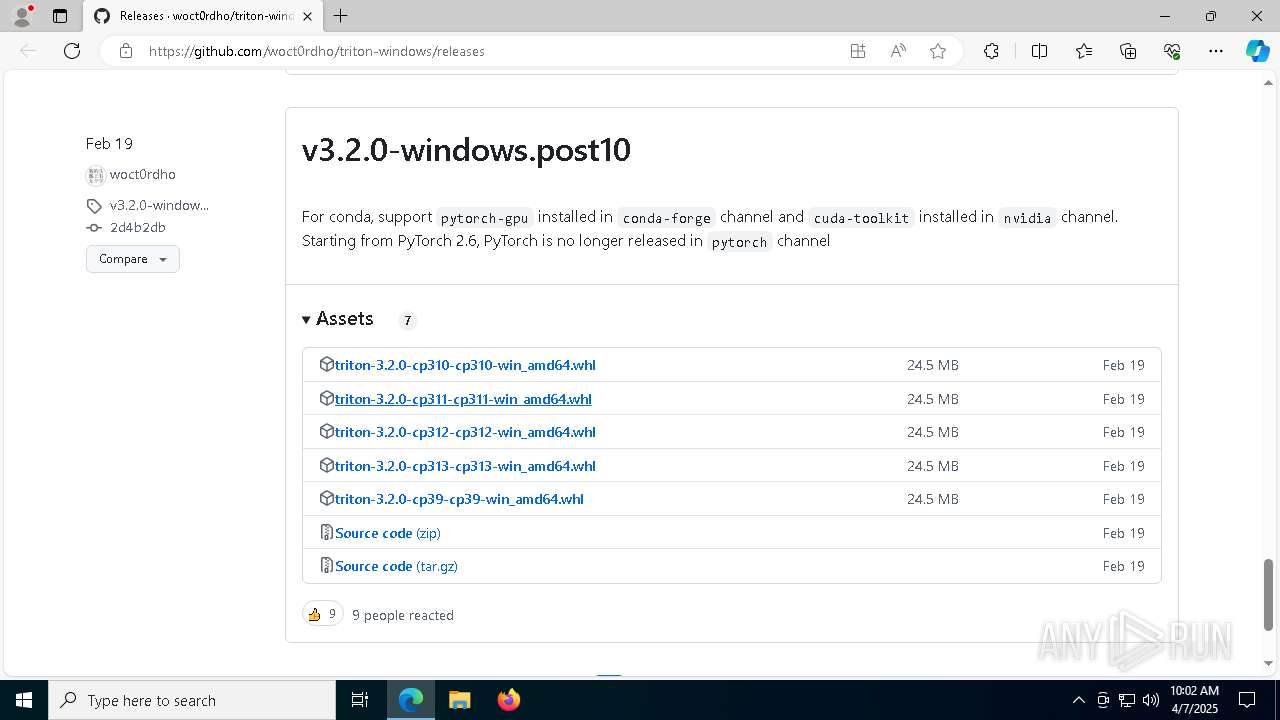
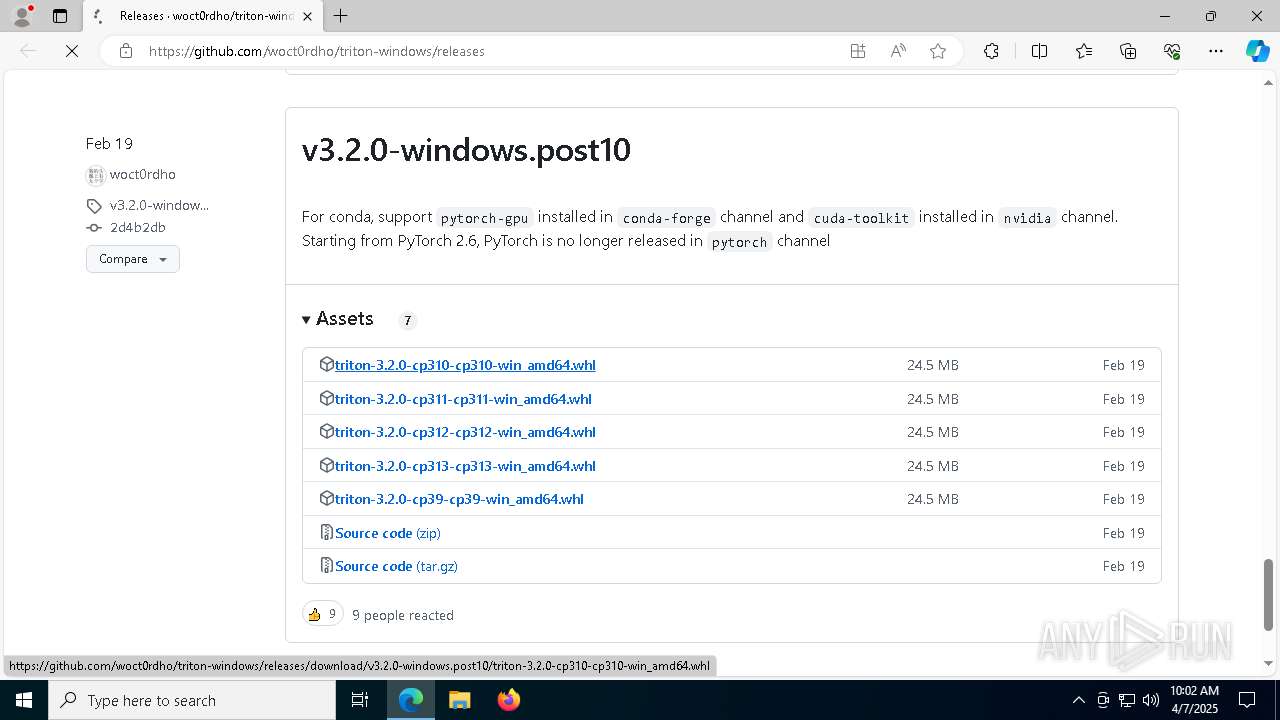
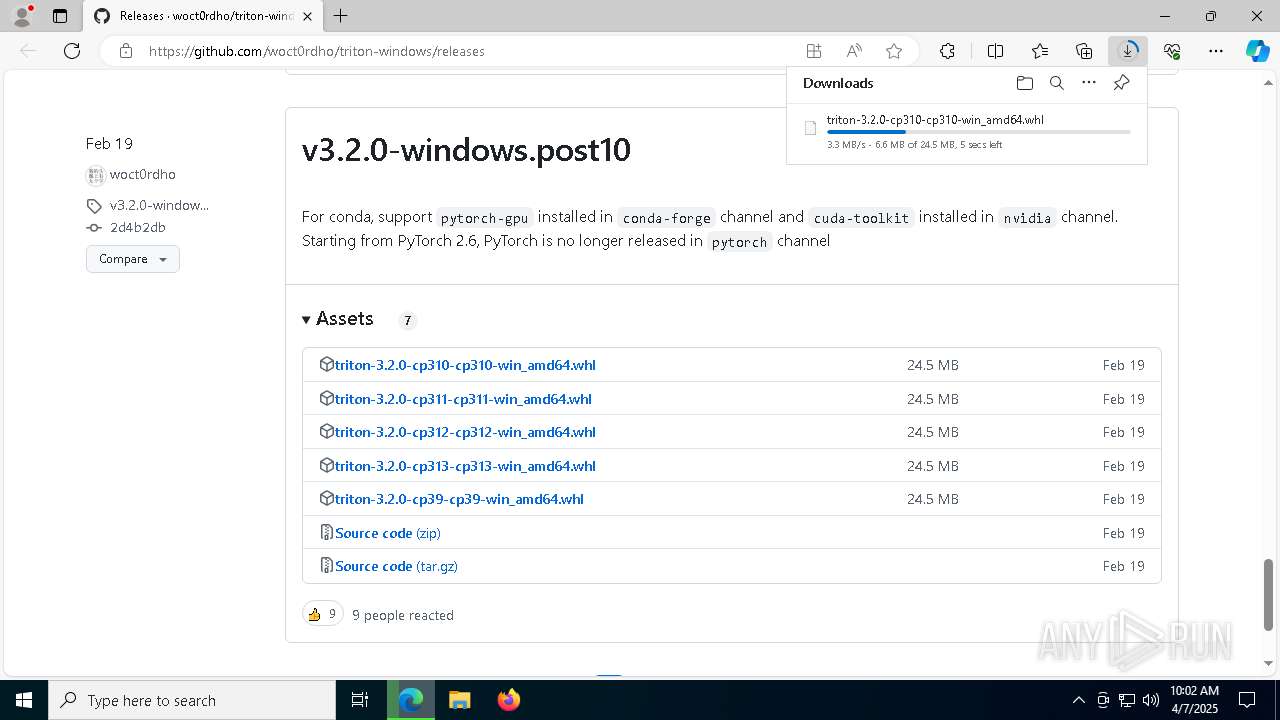
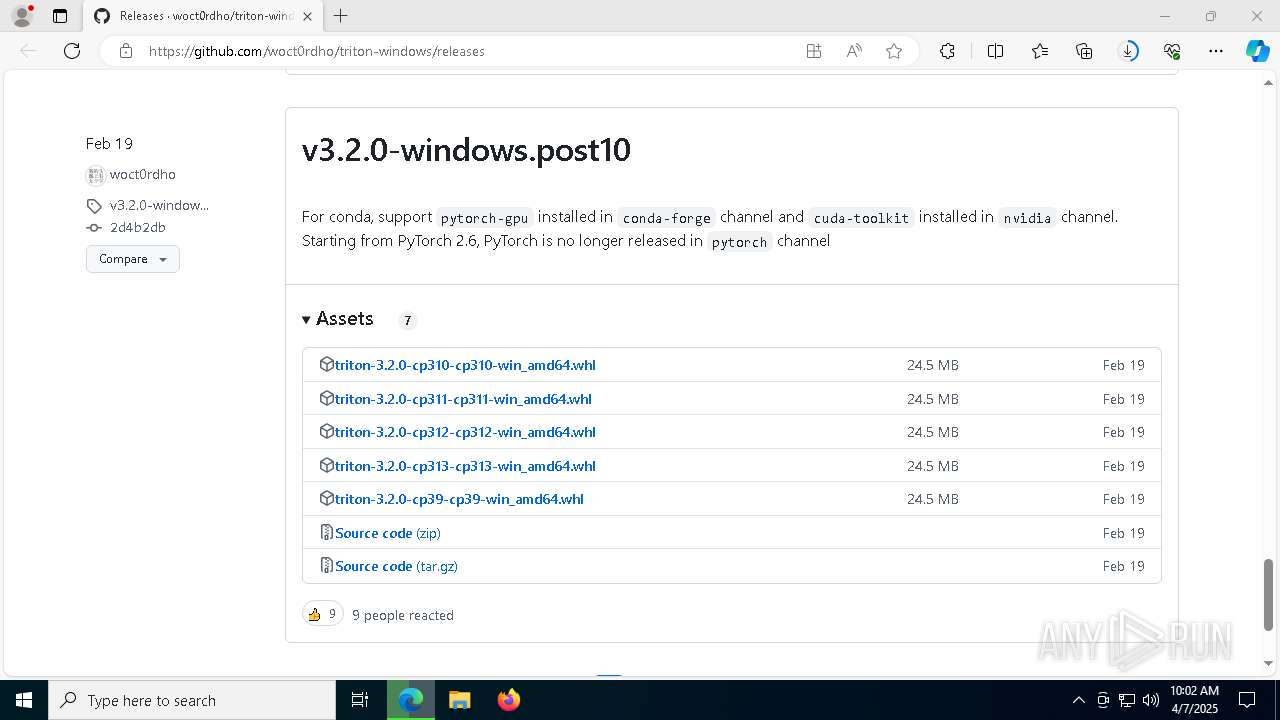
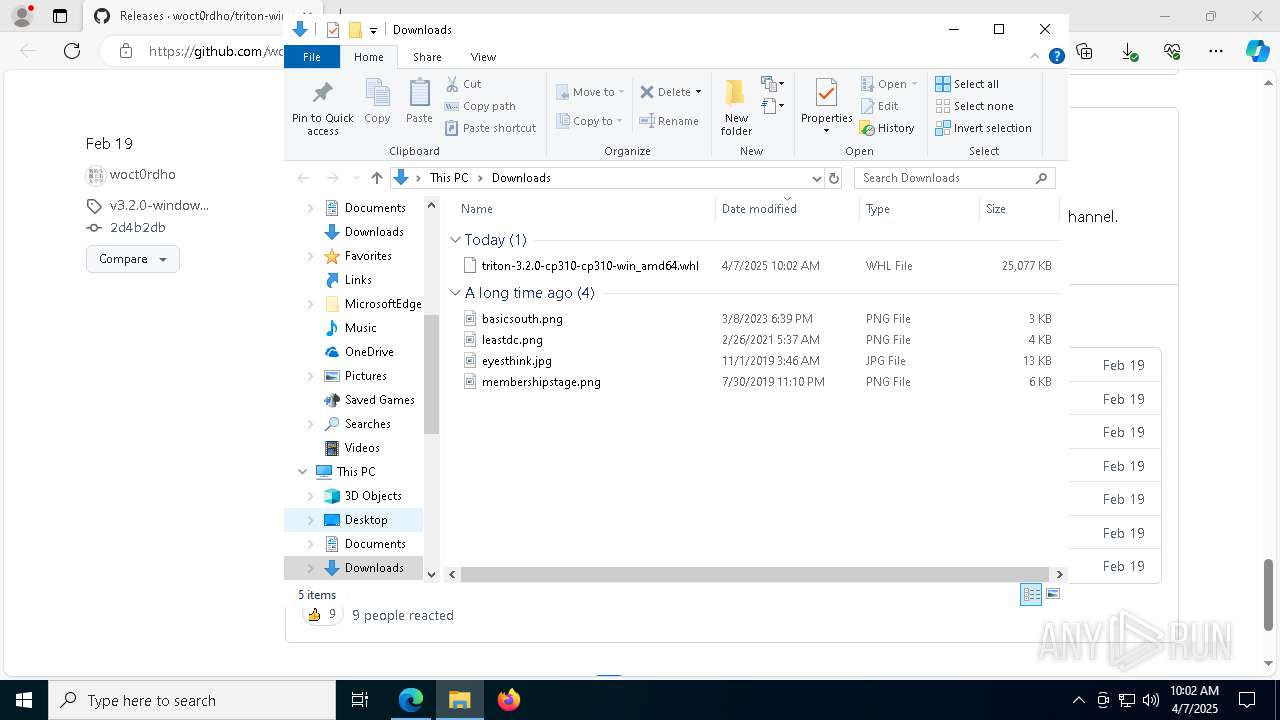
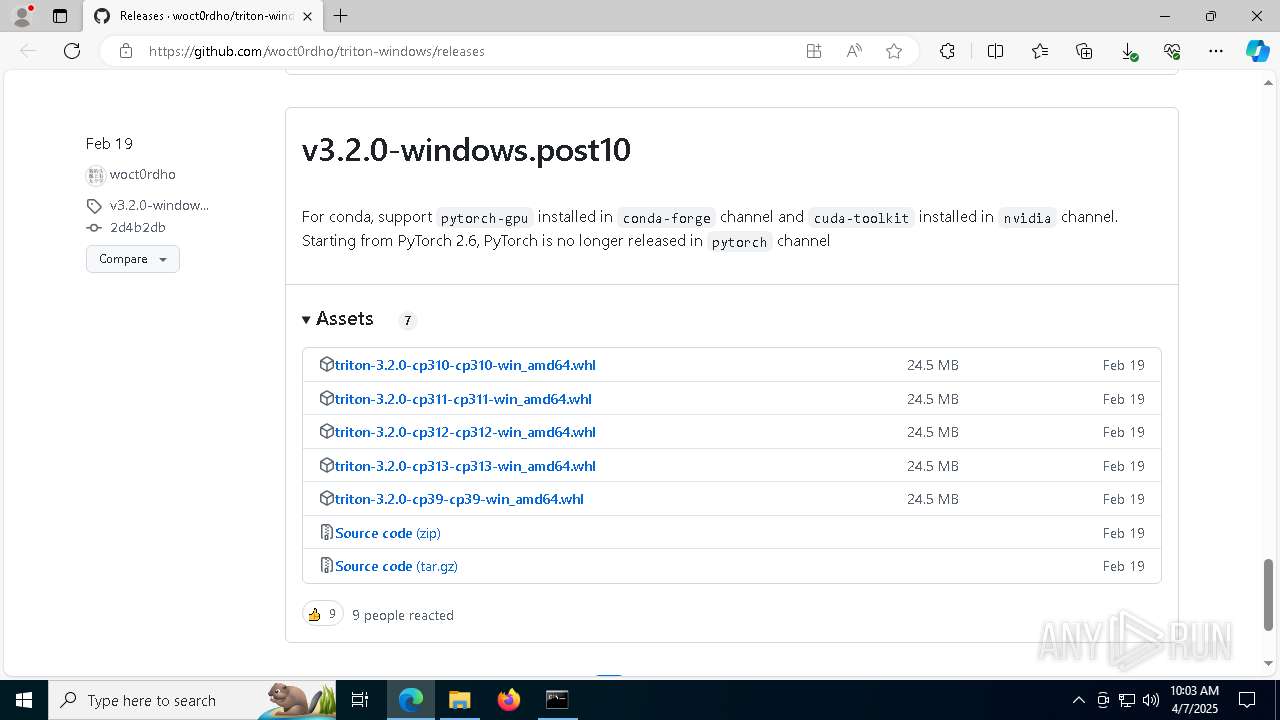
| URL: | https://github.com/woct0rdho/triton-windows/releases |
| Full analysis: | https://app.any.run/tasks/9d3eeaa3-f6a5-4a57-8865-ae2407b76e32 |
| Verdict: | Malicious activity |
| Analysis date: | April 07, 2025, 10:01:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B6ABABE95909A3E62DDD9583E610FA8D |
| SHA1: | 96B44BF478C08DFE2FE1012C87F4DE1B60EA990D |
| SHA256: | 2ED09DC7CE976E13109288AE99AB11F7CF94143FD2865F276AF05E73384B5147 |
| SSDEEP: | 3:N8tEdiKyxfLISKDFdn:2u050DDfn |
MALICIOUS
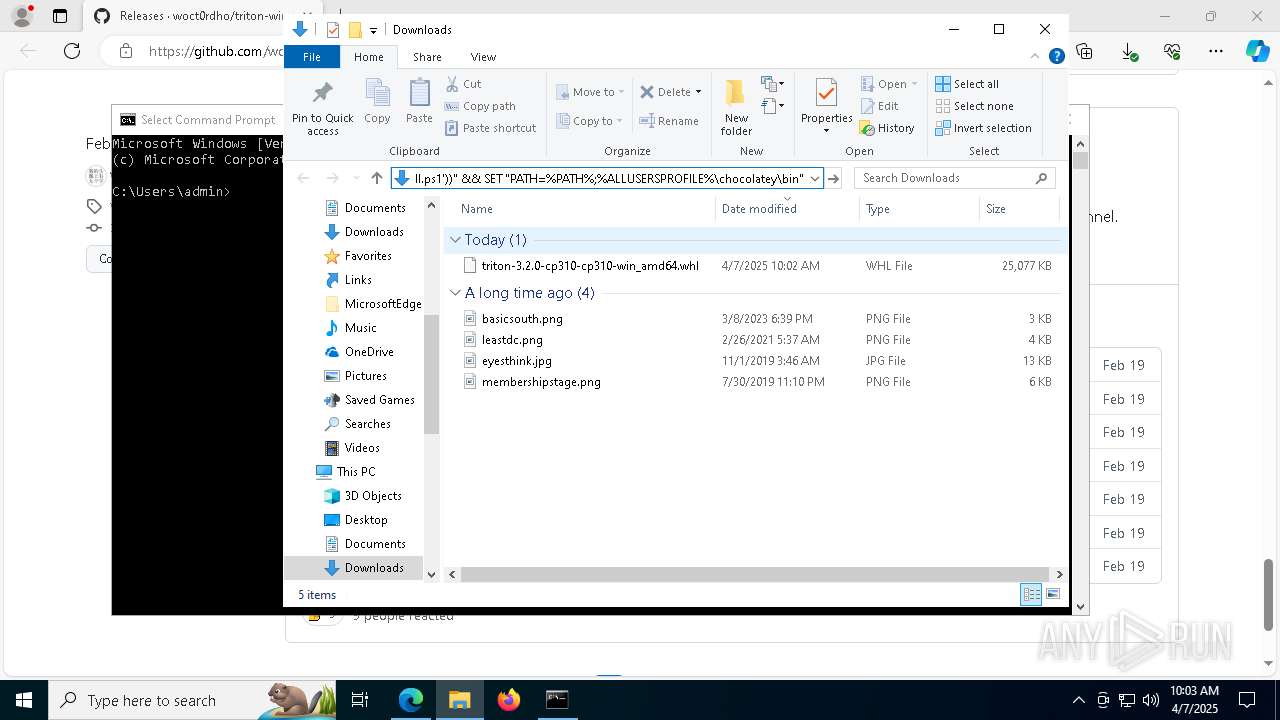
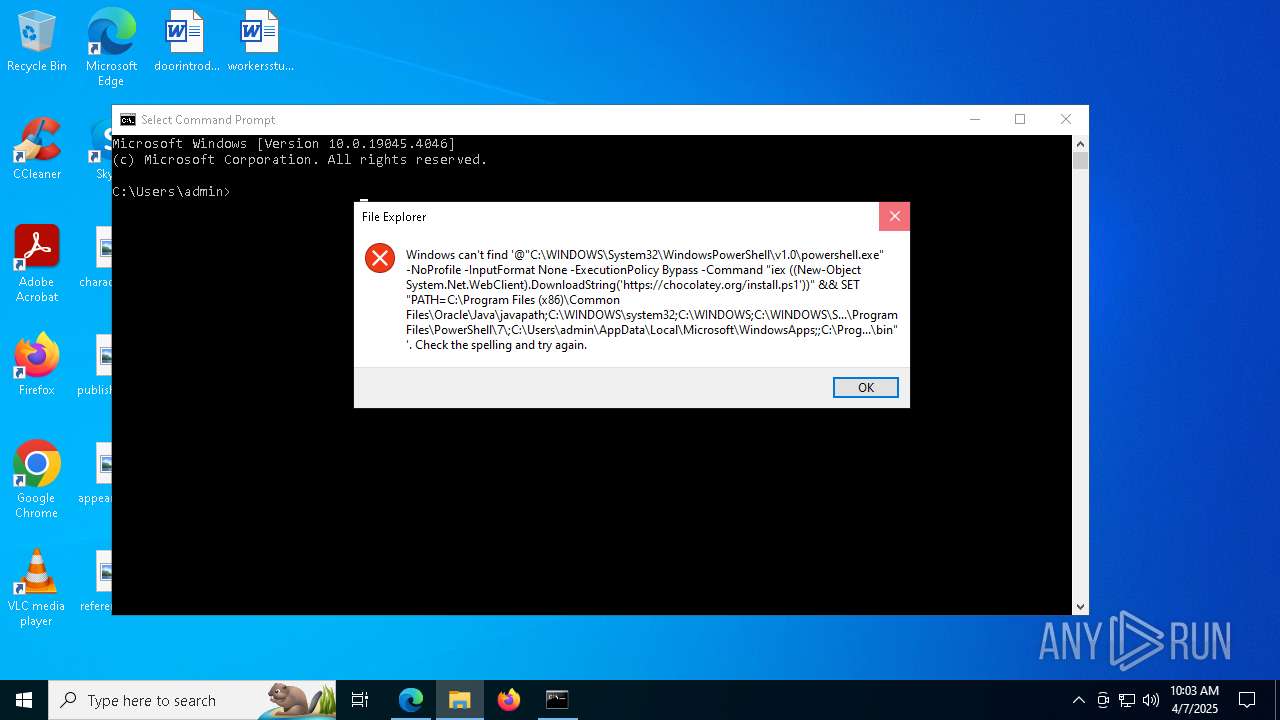
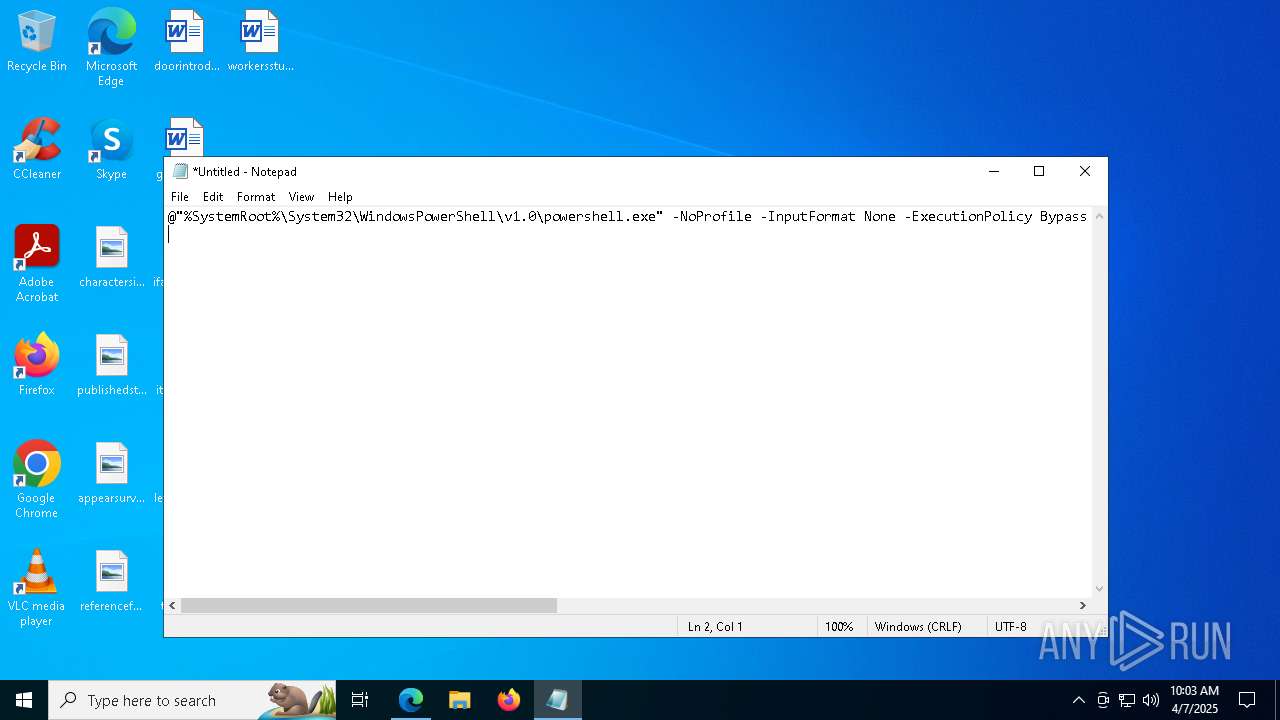
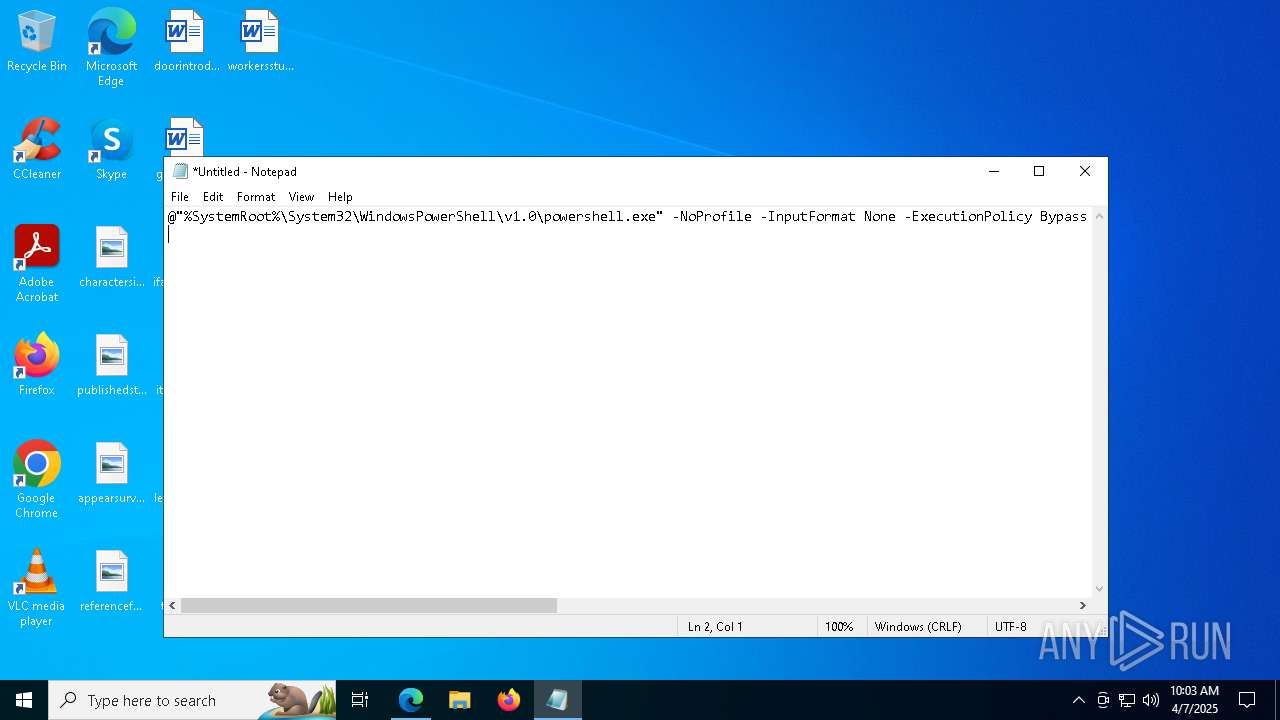
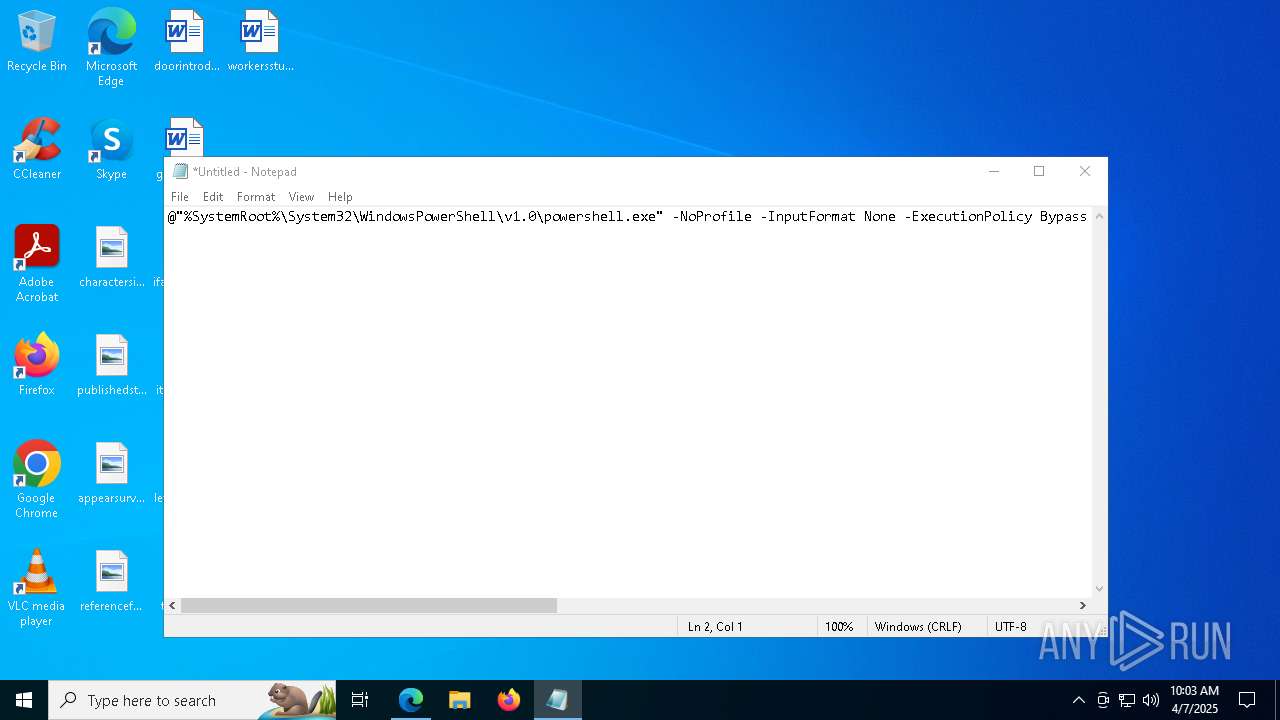
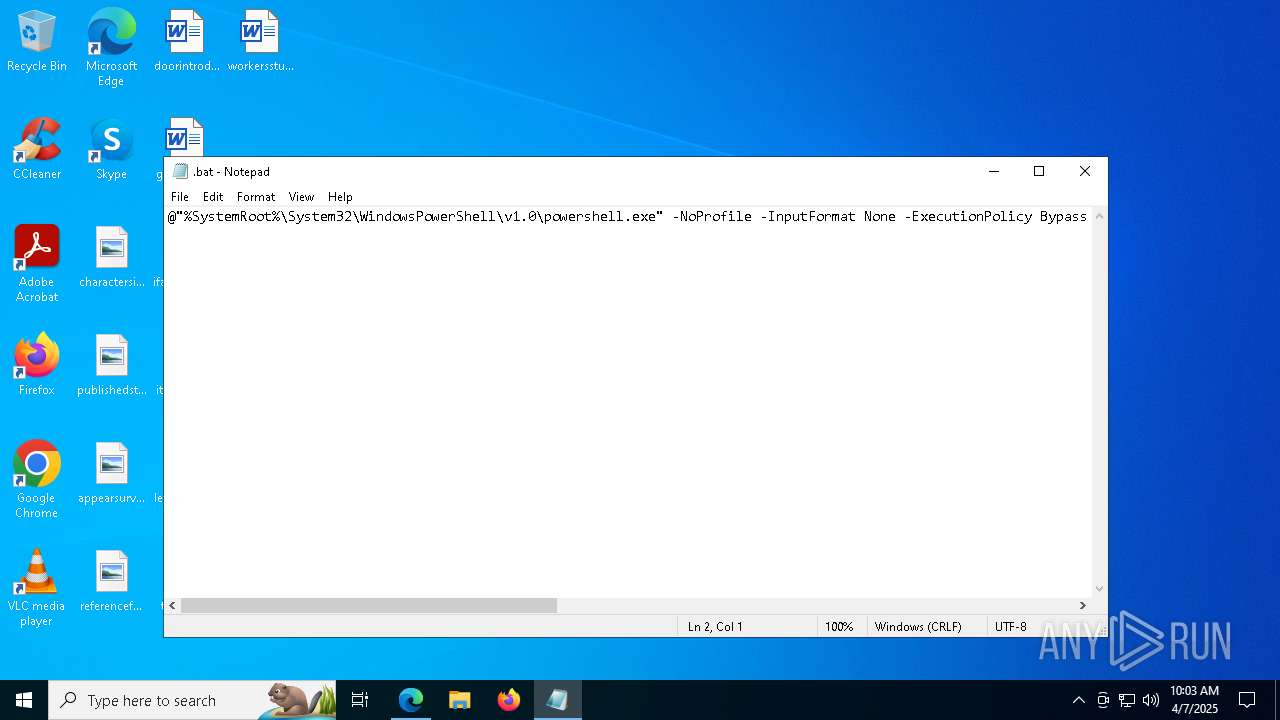
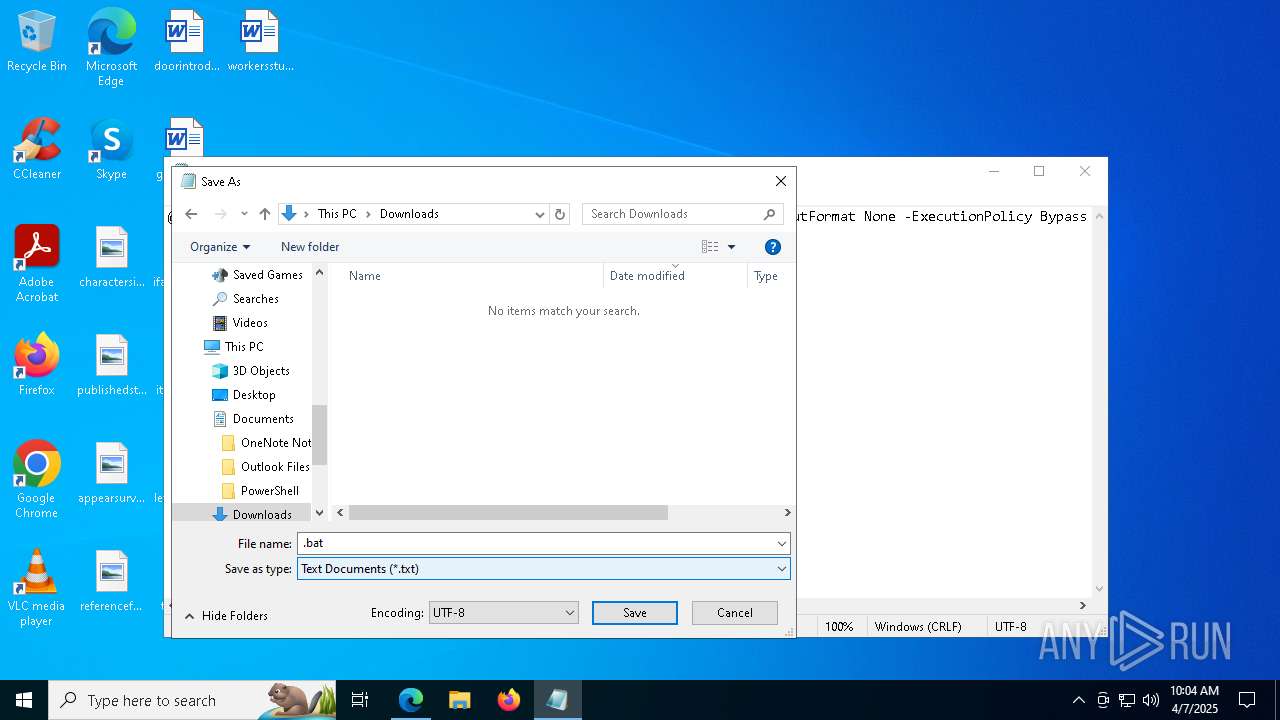
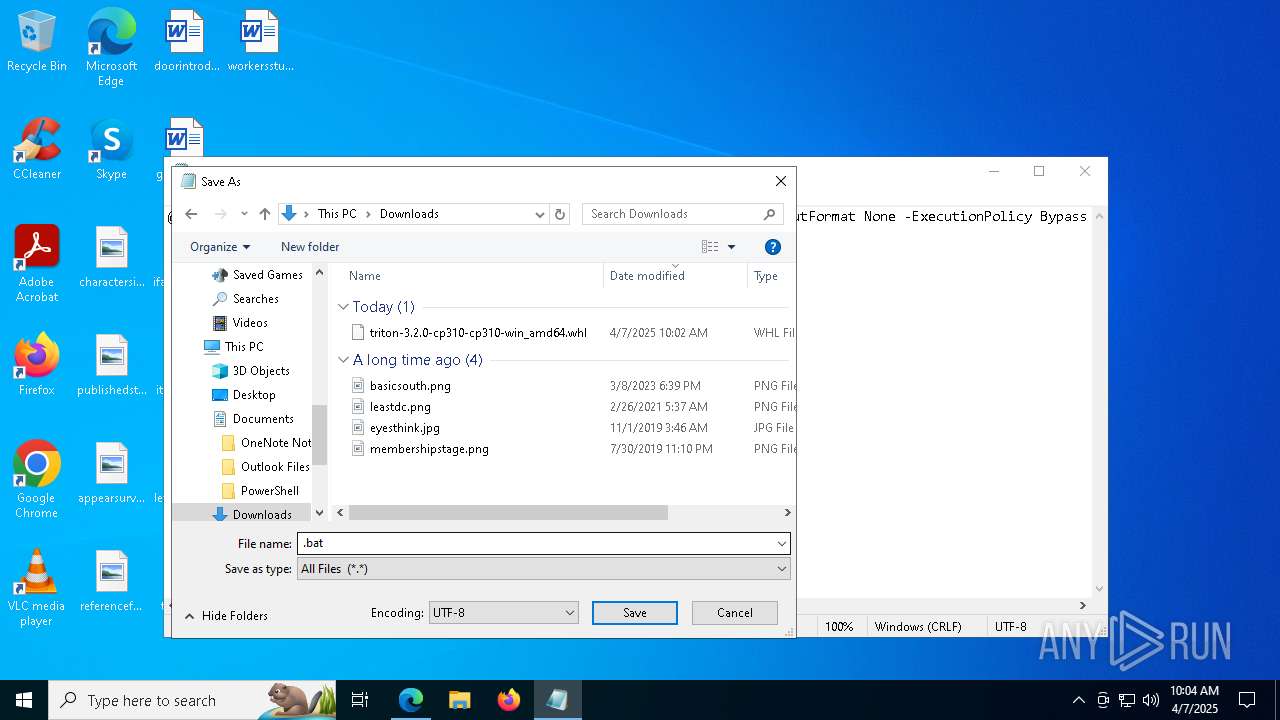
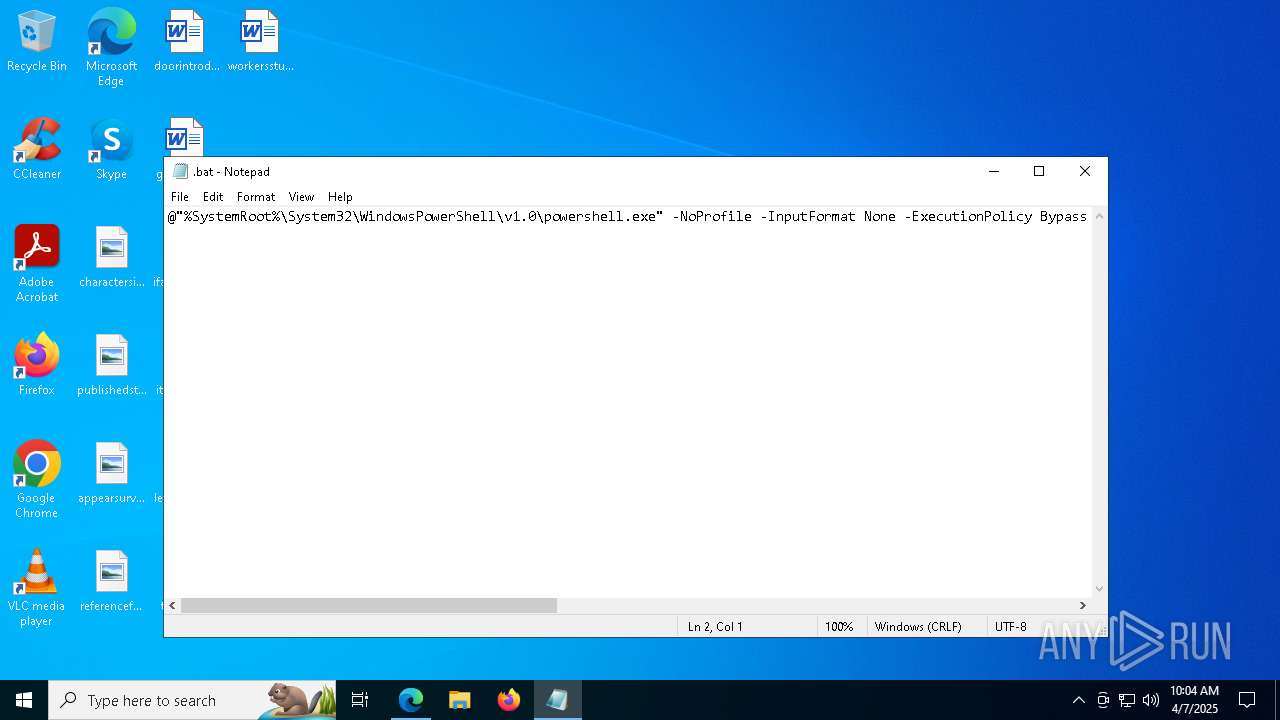
Bypass execution policy to execute commands
- powershell.exe (PID: 7892)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 5936)
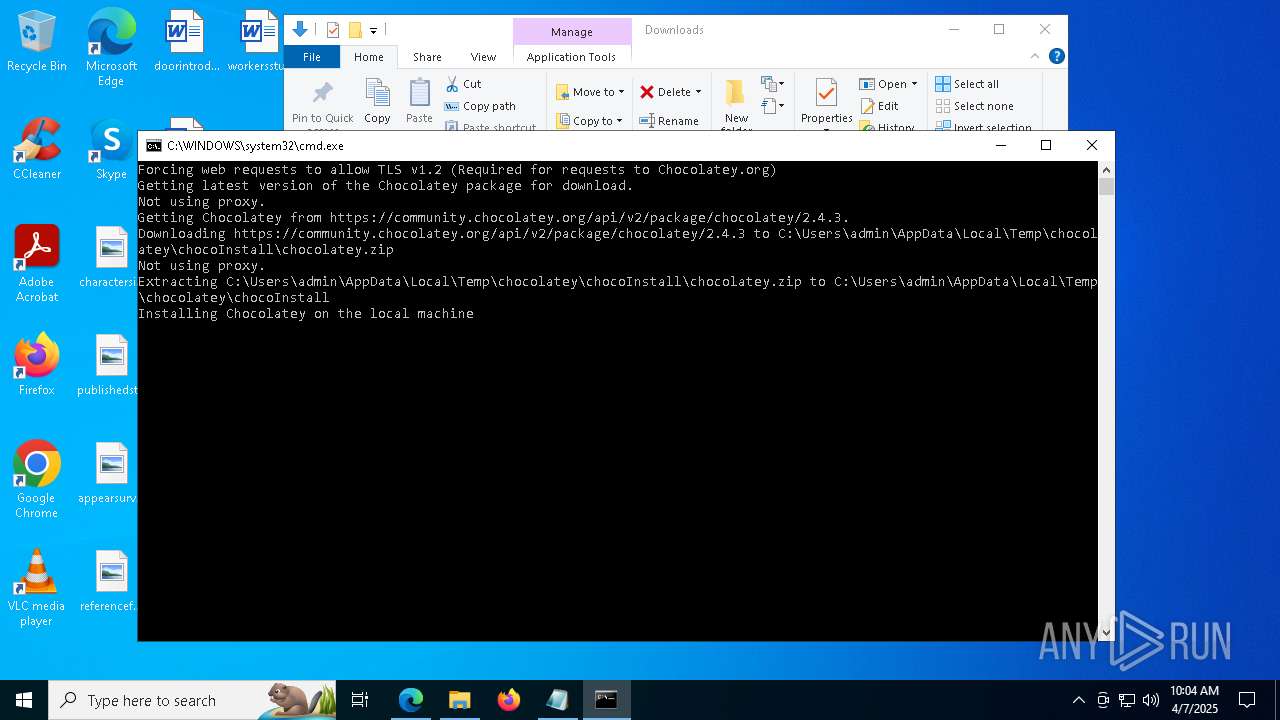
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 7892)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7892)
SUSPICIOUS
Probably download files using WebClient
- cmd.exe (PID: 5936)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 5936)
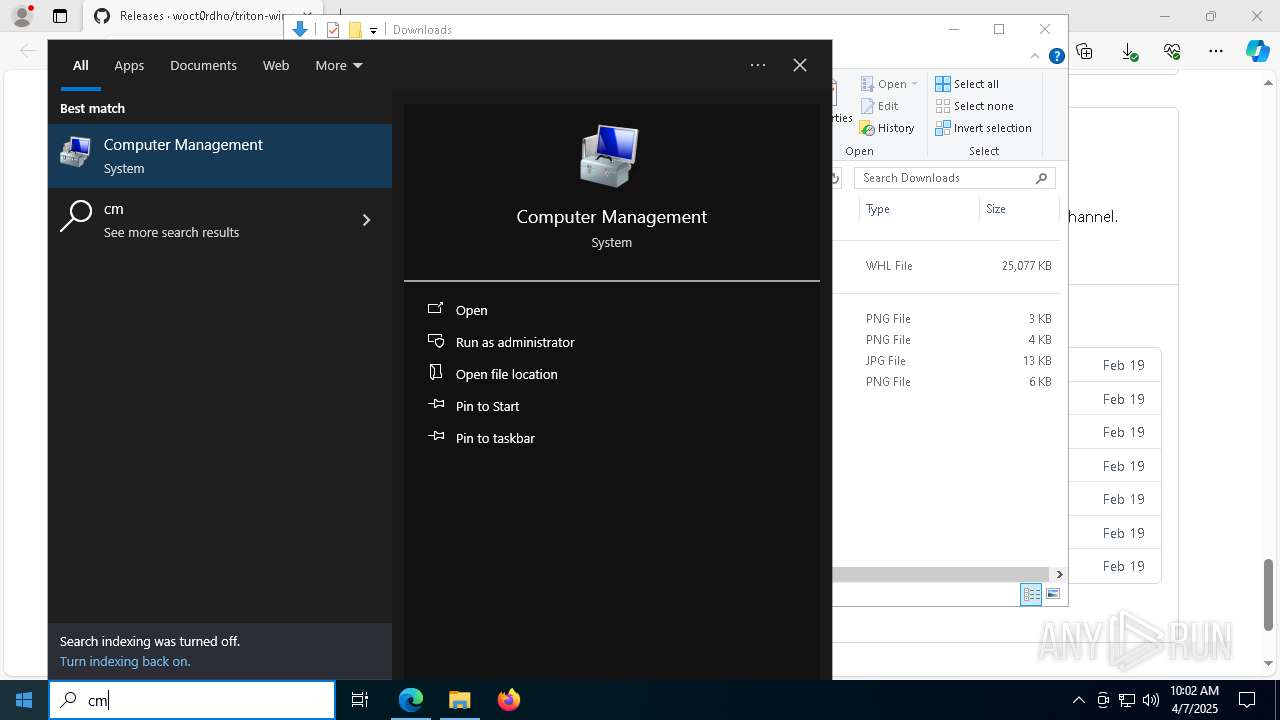
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5936)
The process executes Powershell scripts
- cmd.exe (PID: 5936)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 5936)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 7892)
The process creates files with name similar to system file names
- powershell.exe (PID: 7892)
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 7892)
Executable content was dropped or overwritten
- powershell.exe (PID: 7892)
Drops 7-zip archiver for unpacking
- powershell.exe (PID: 7892)
Creates a directory (POWERSHELL)
- powershell.exe (PID: 7892)
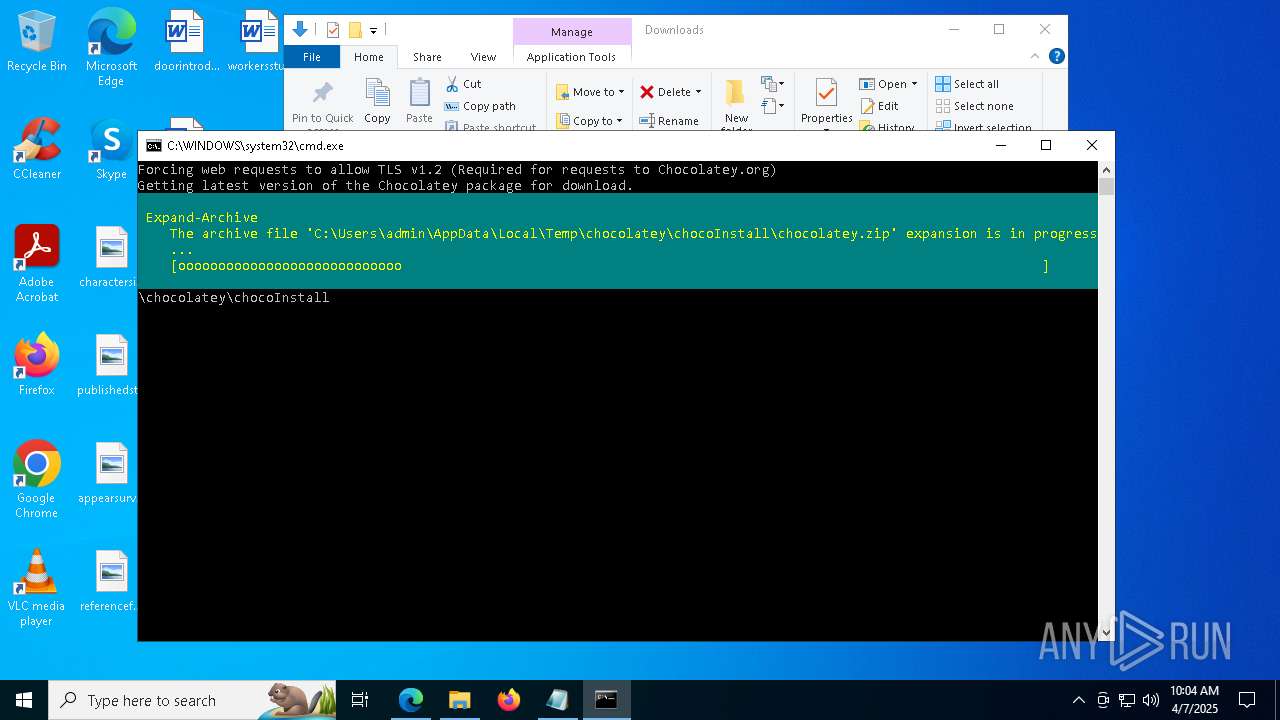
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 7892)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7892)
INFO
Application launched itself
- msedge.exe (PID: 7148)
Reads the computer name
- identity_helper.exe (PID: 6744)
Checks supported languages
- identity_helper.exe (PID: 6744)
Reads Environment values
- identity_helper.exe (PID: 6744)
Reads the software policy settings
- slui.exe (PID: 536)
- slui.exe (PID: 2392)
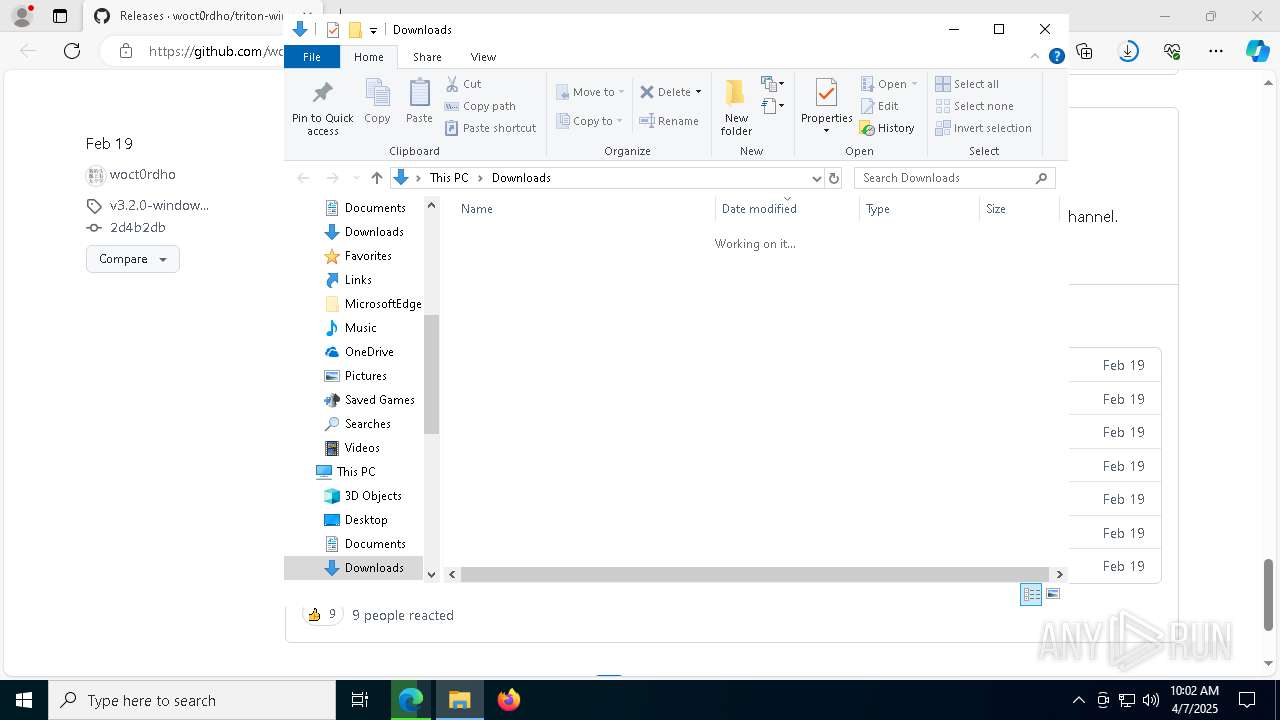
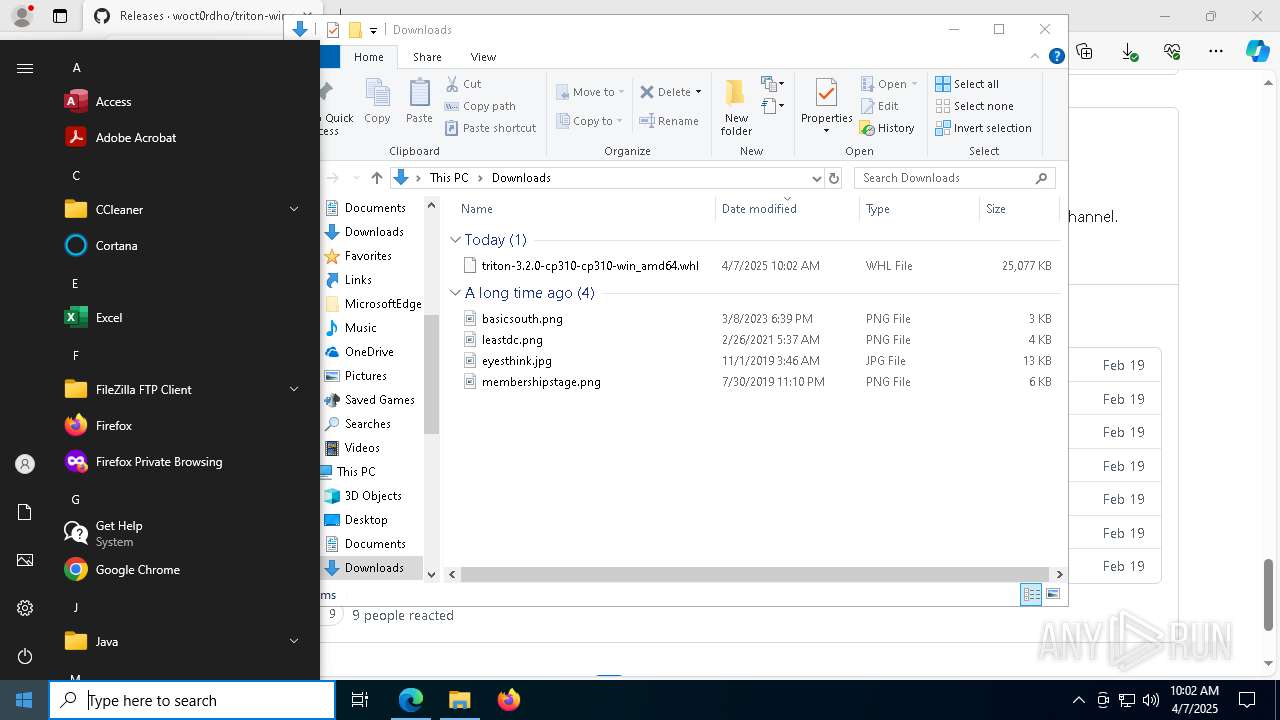
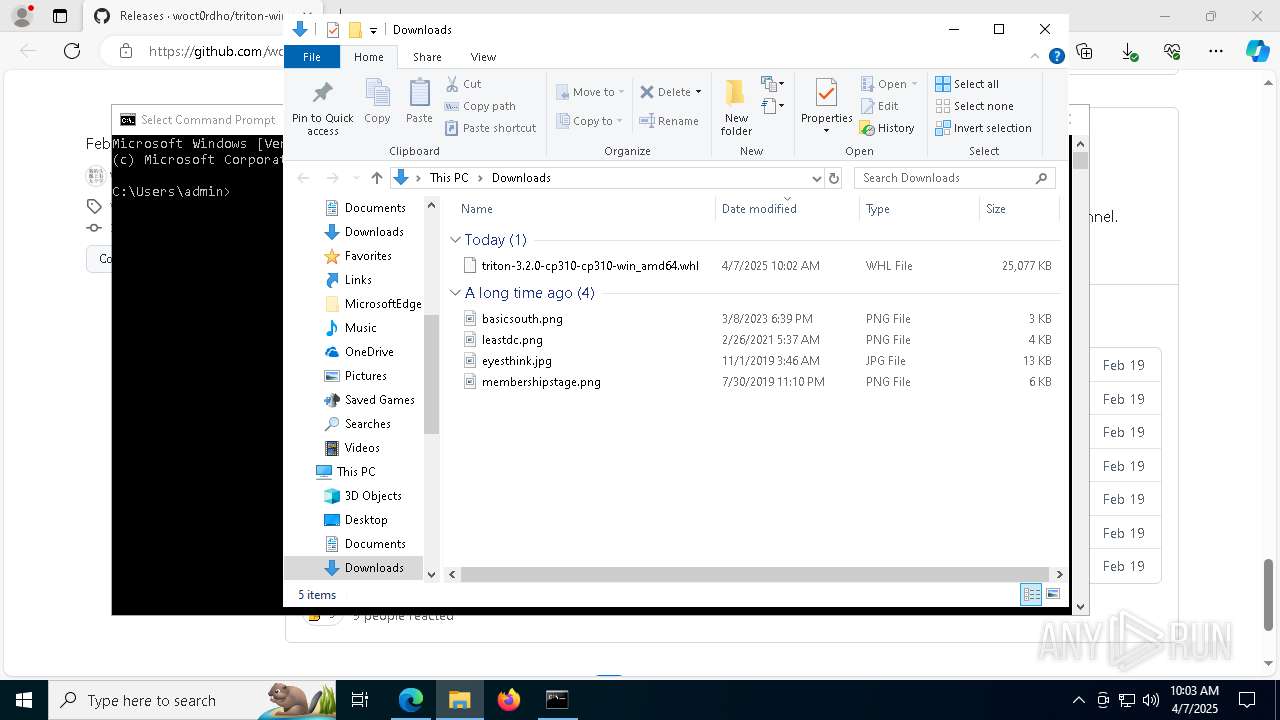
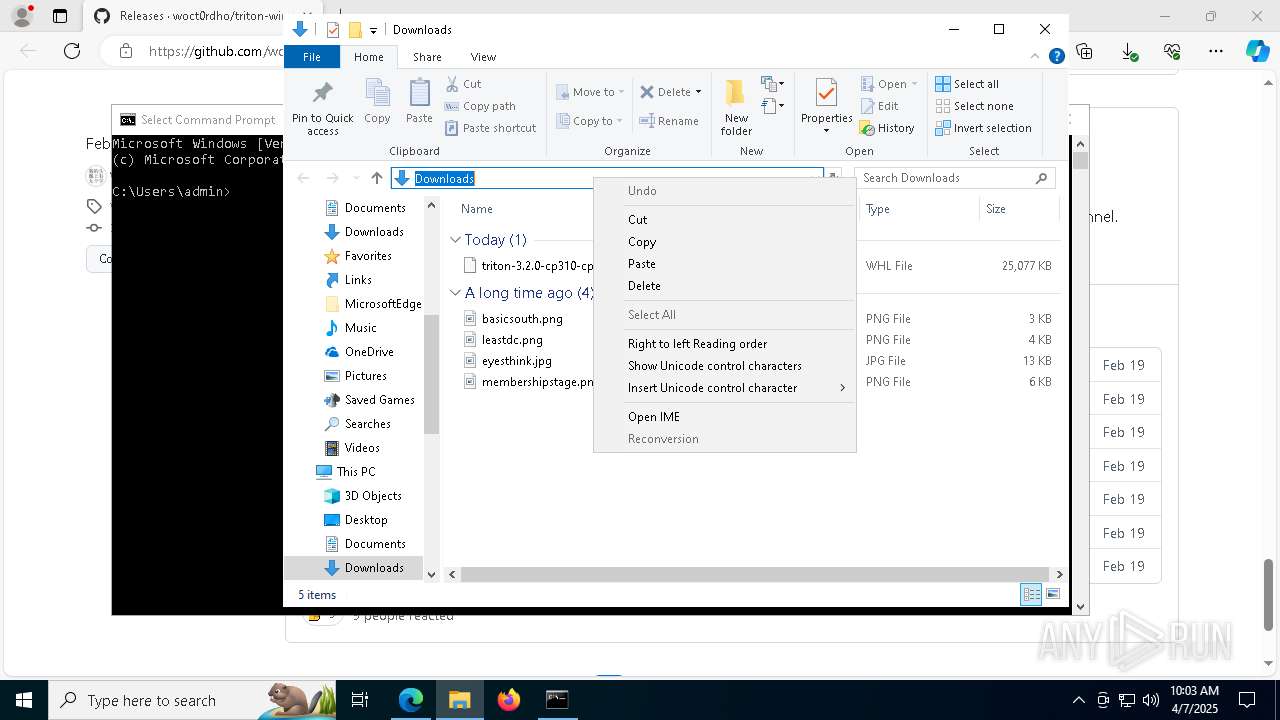
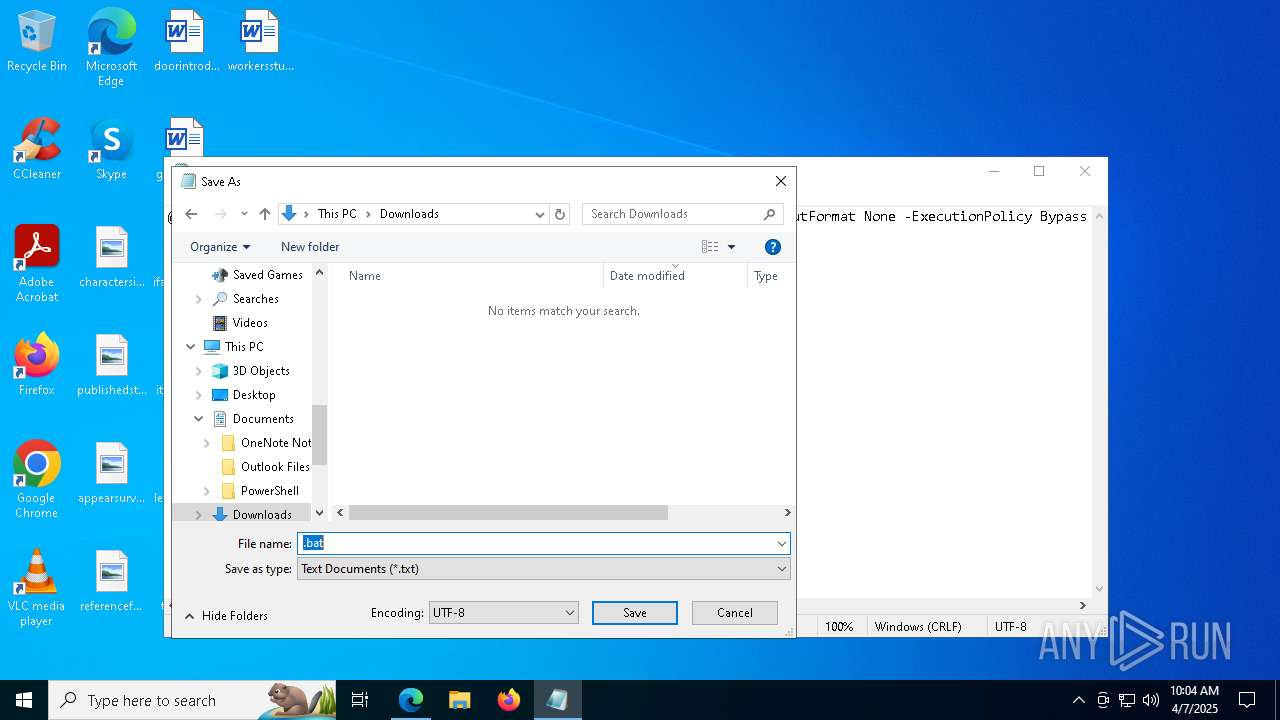
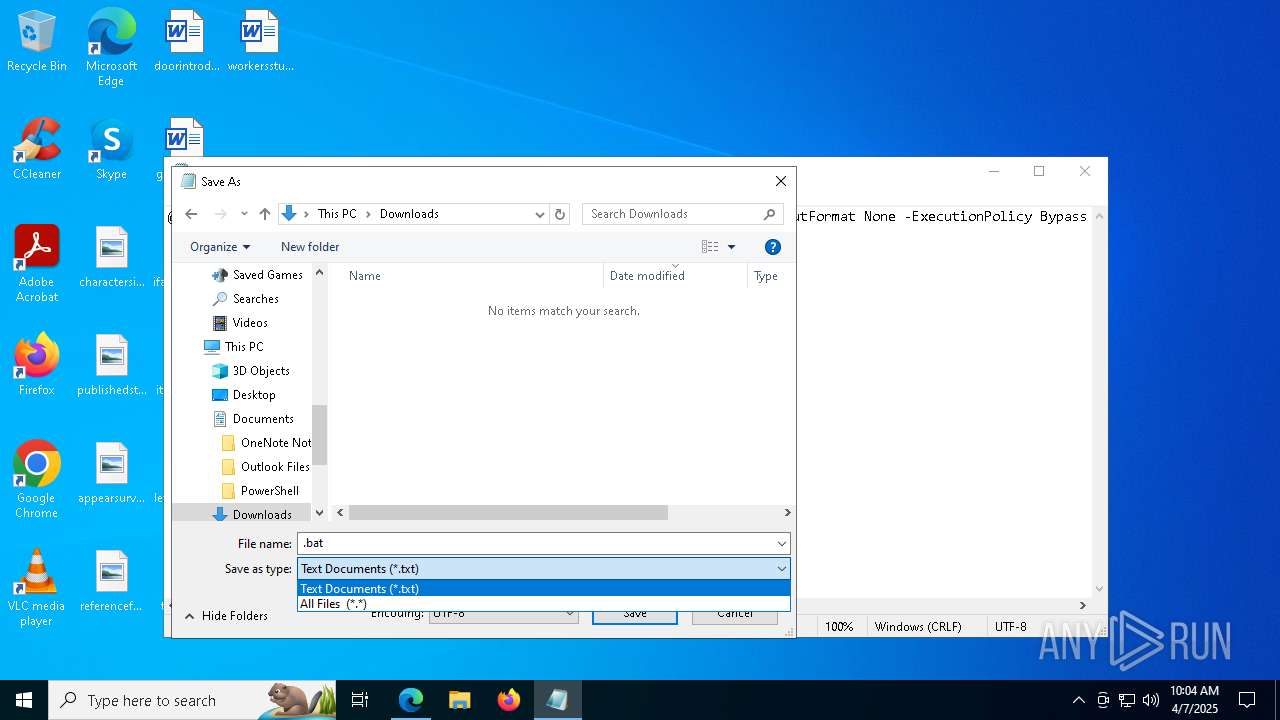
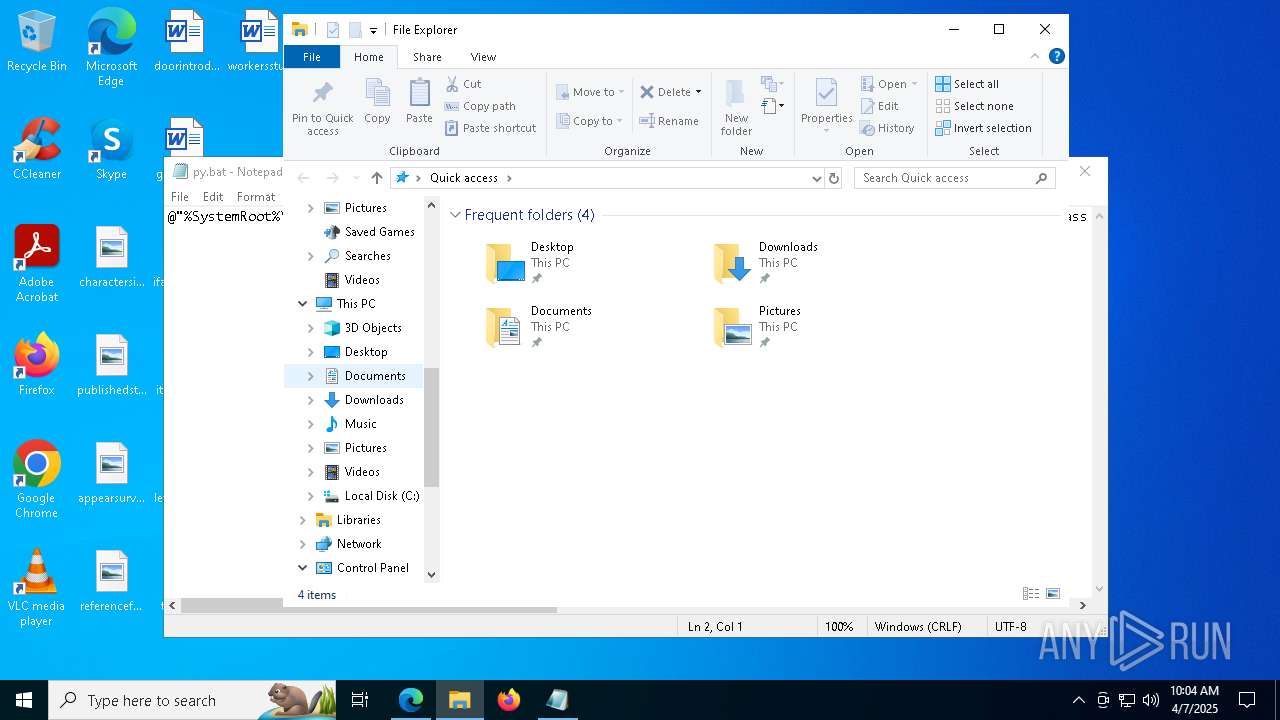
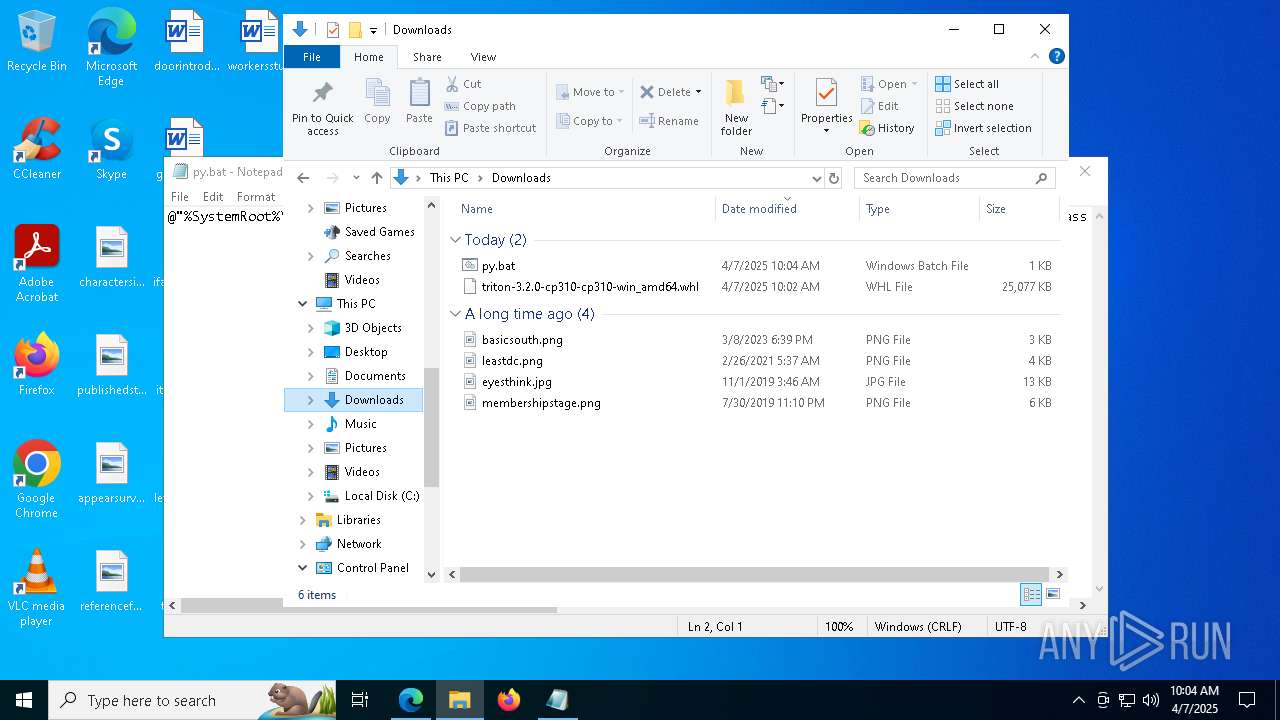
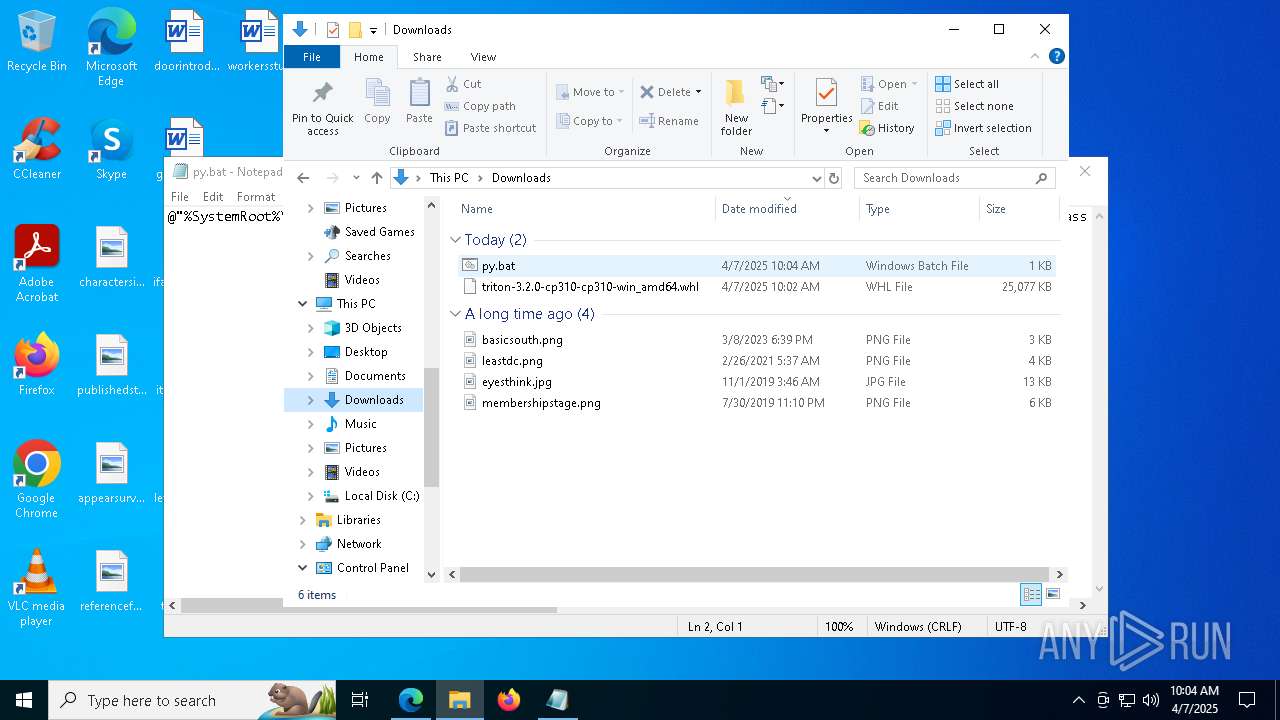
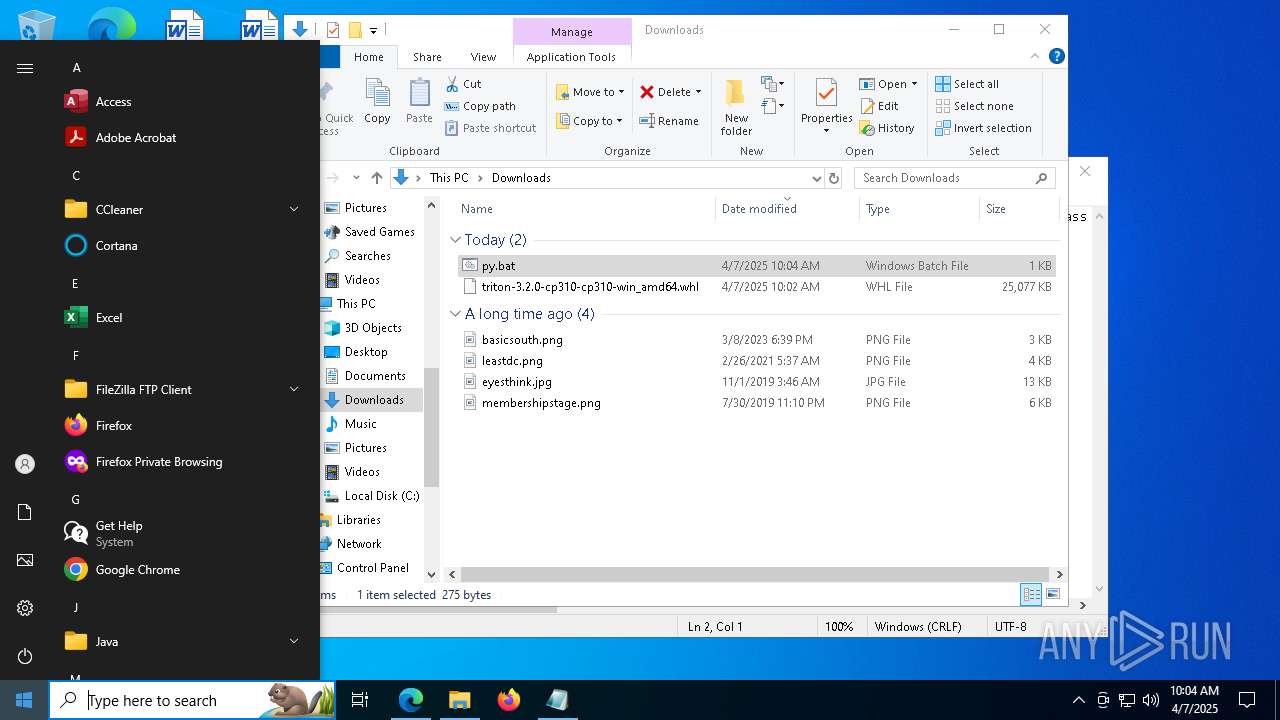
Autorun file from Downloads
- msedge.exe (PID: 7188)
- msedge.exe (PID: 7148)
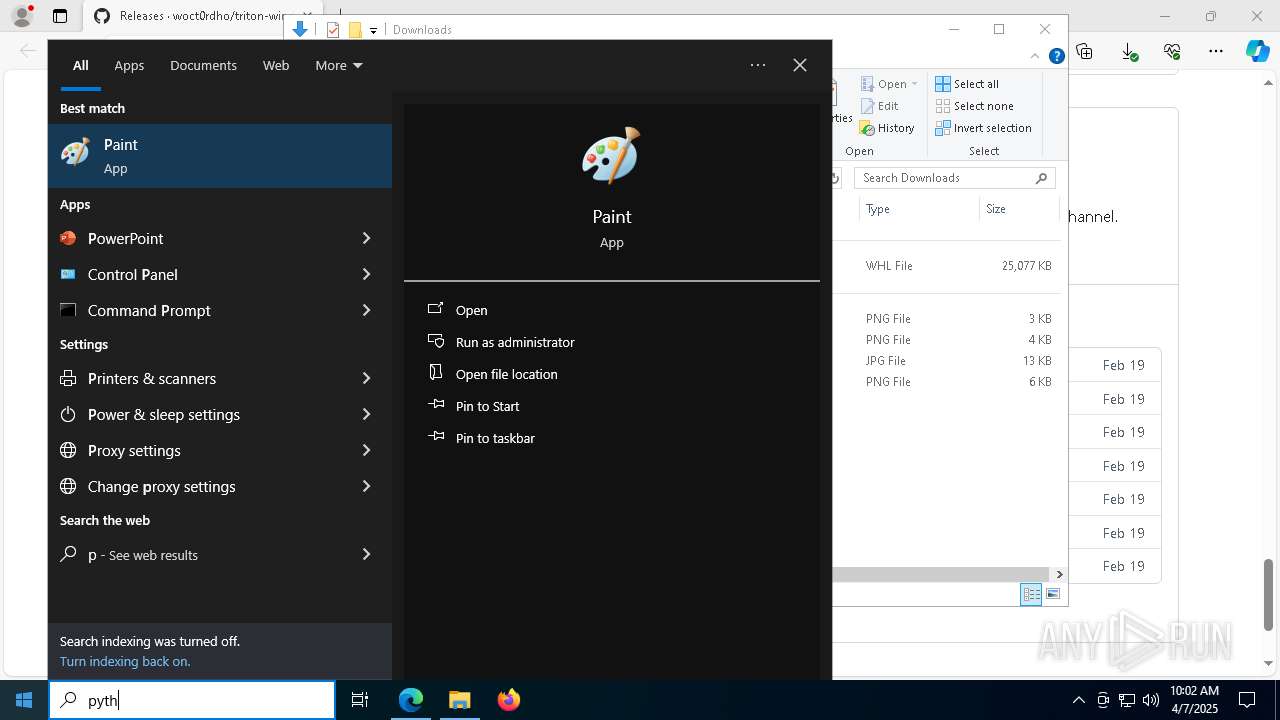
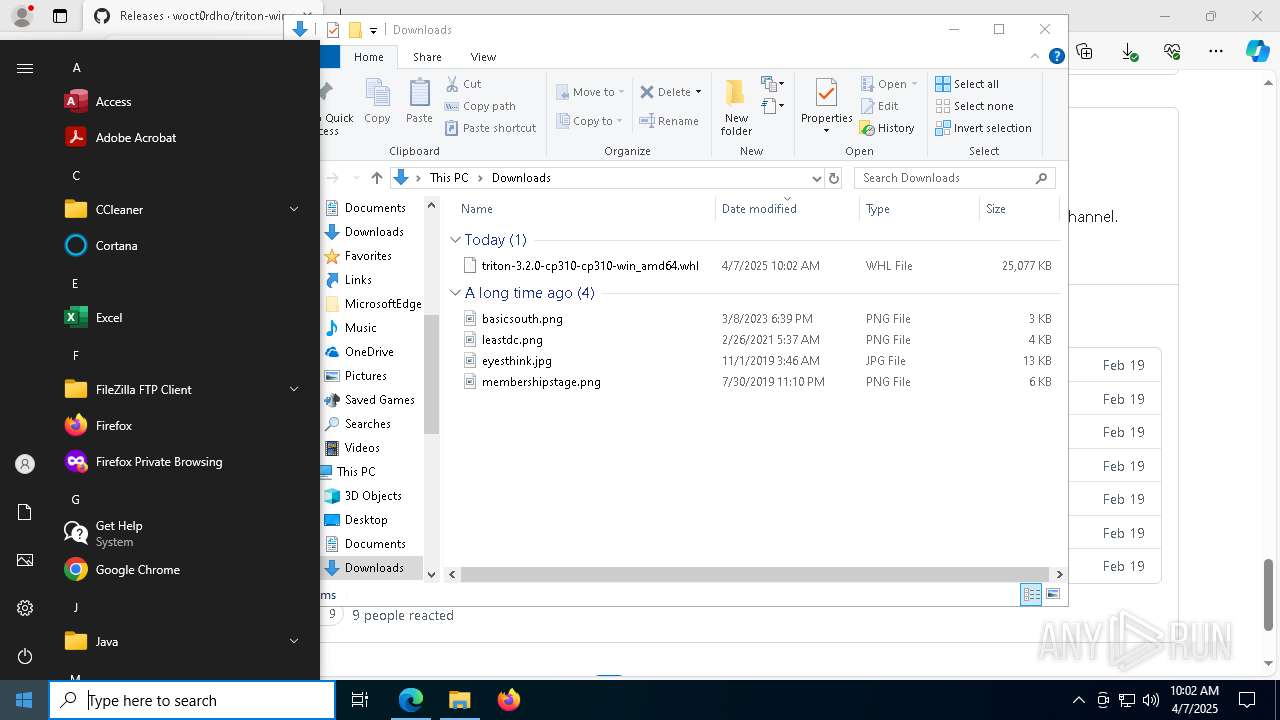
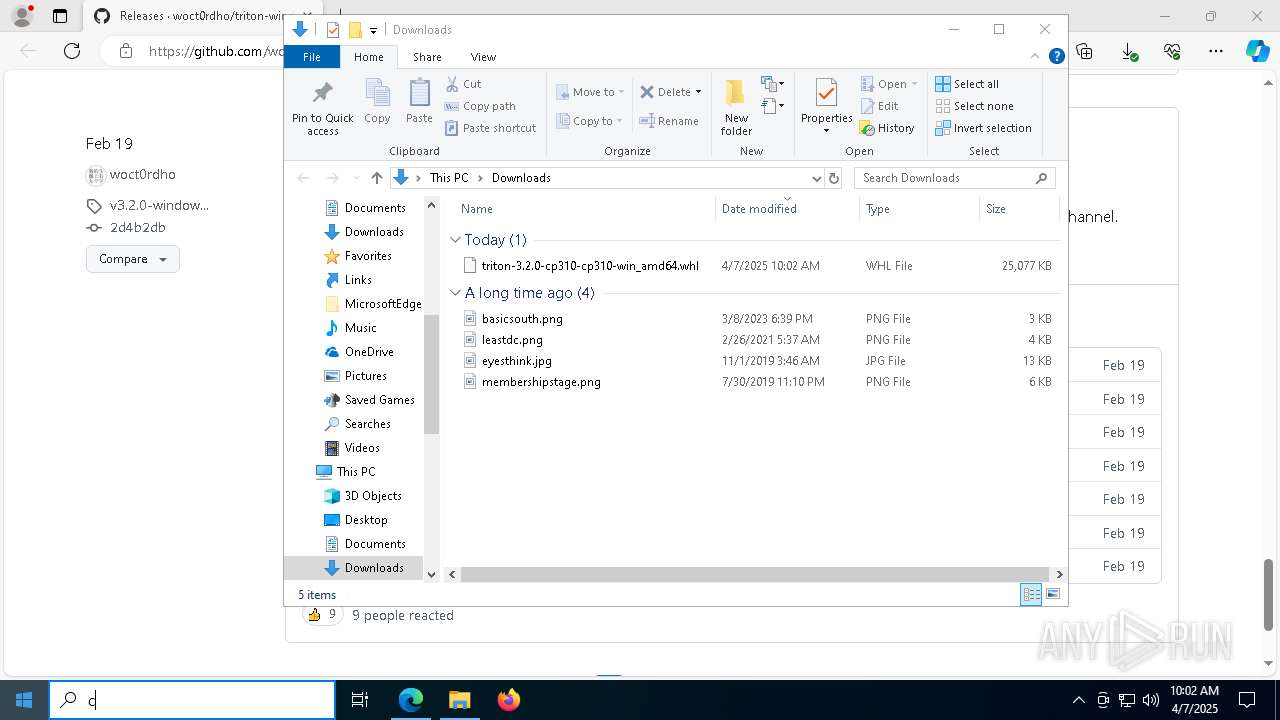
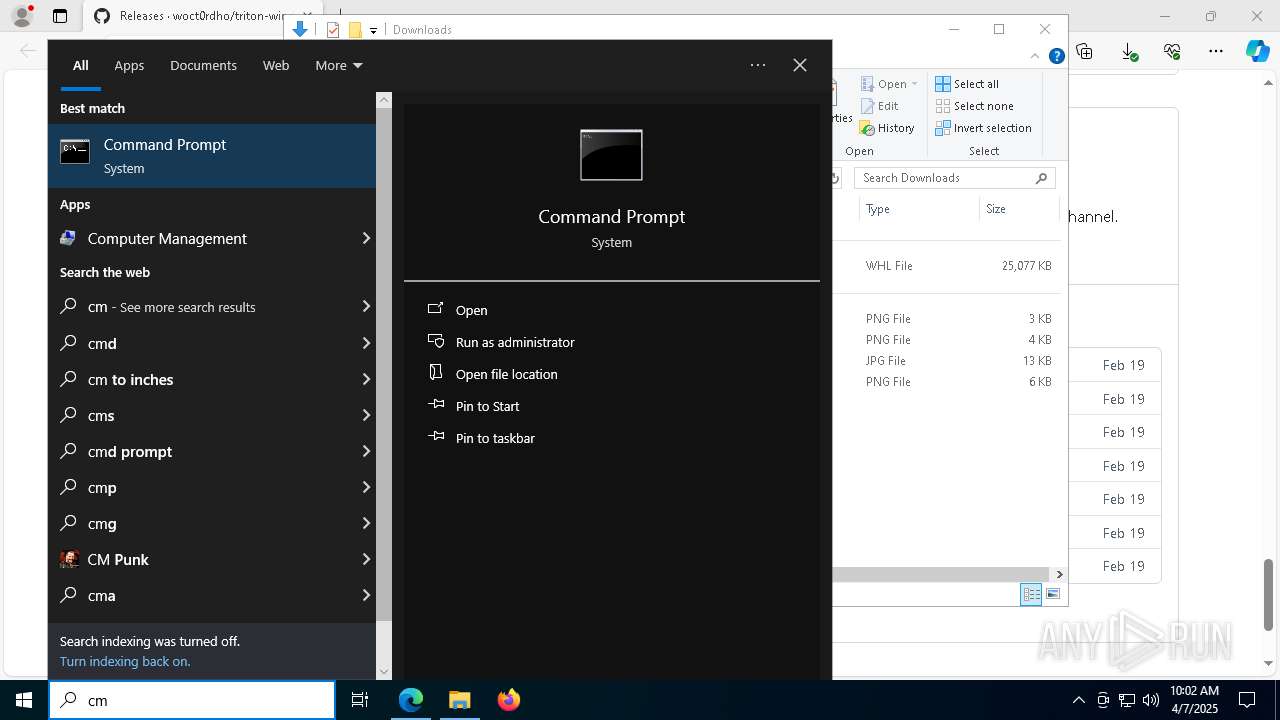
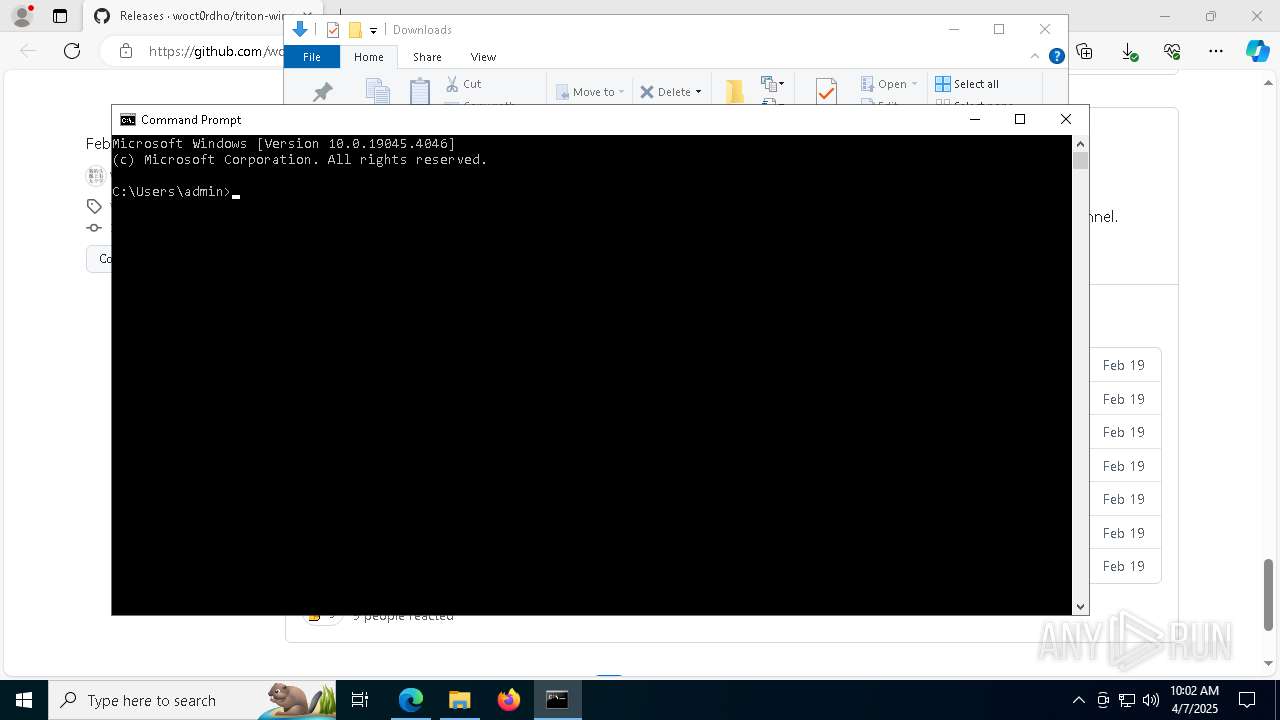
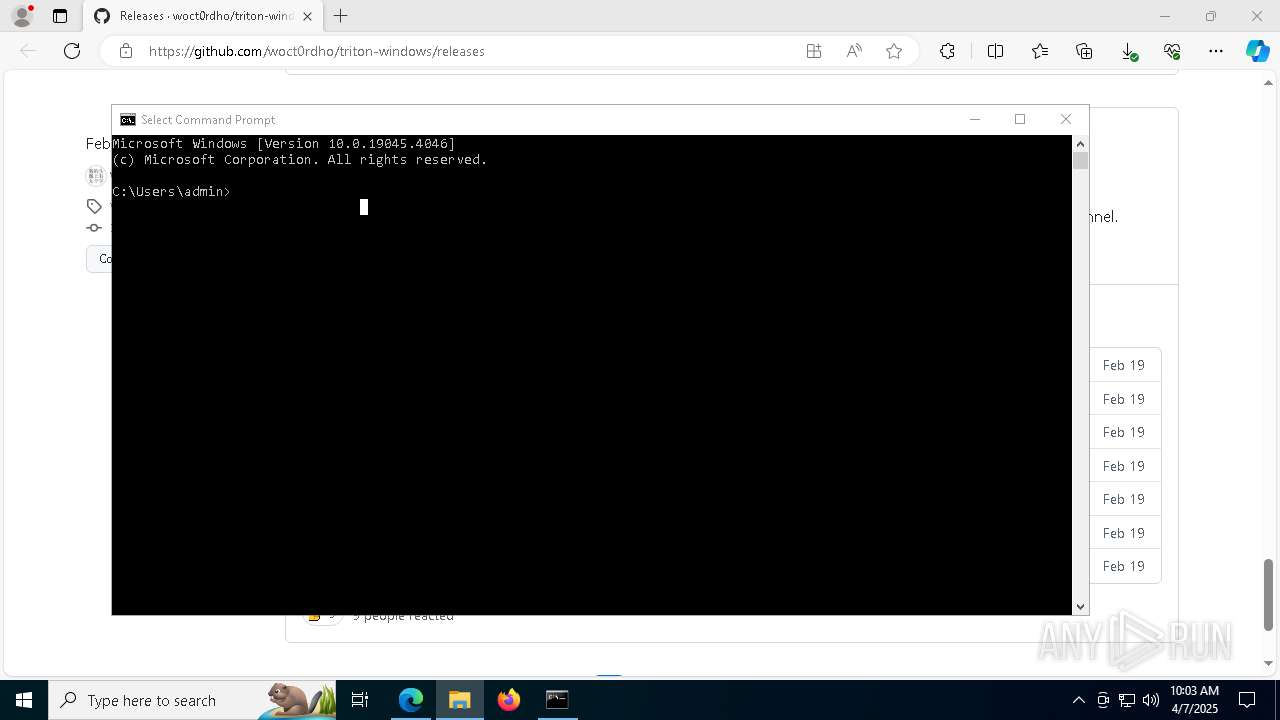
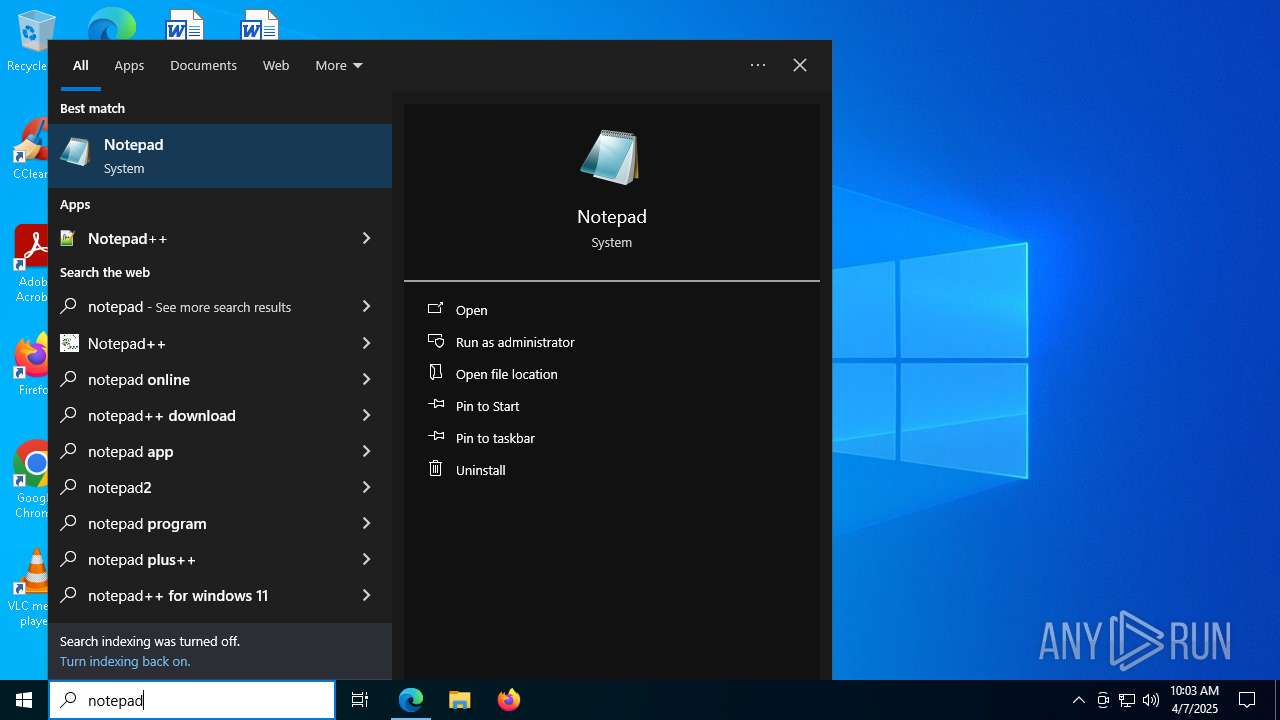
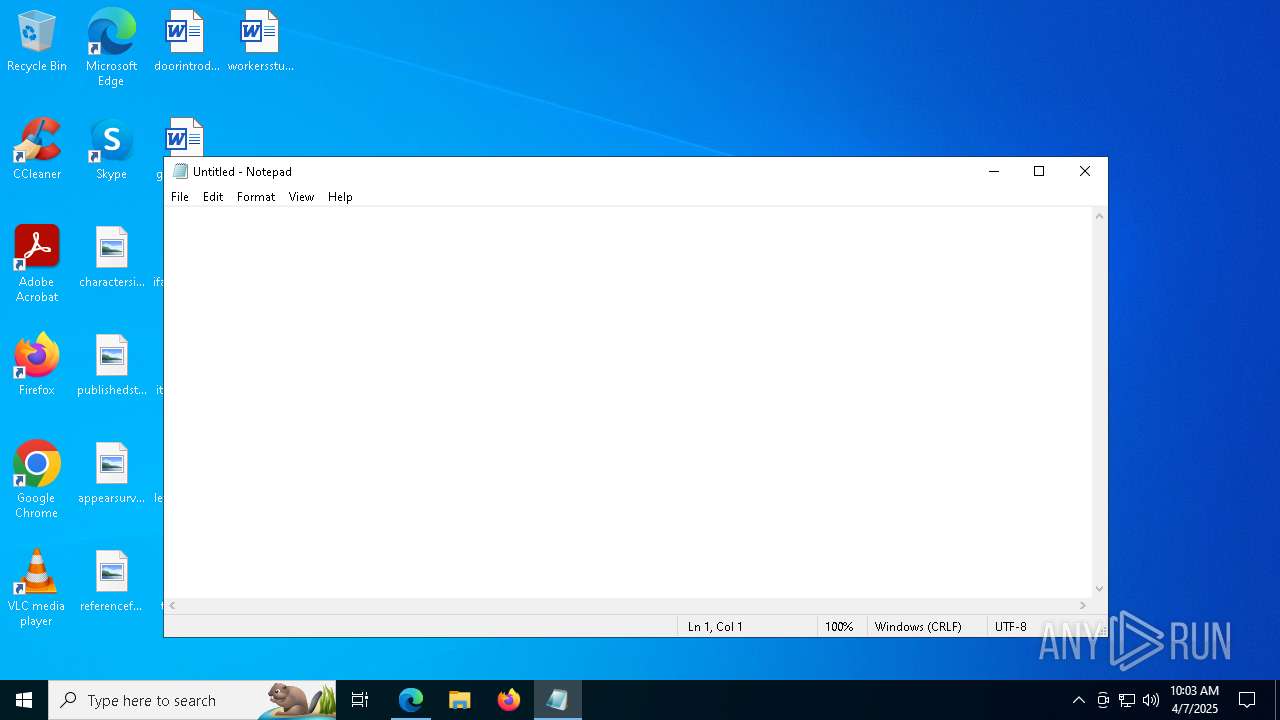
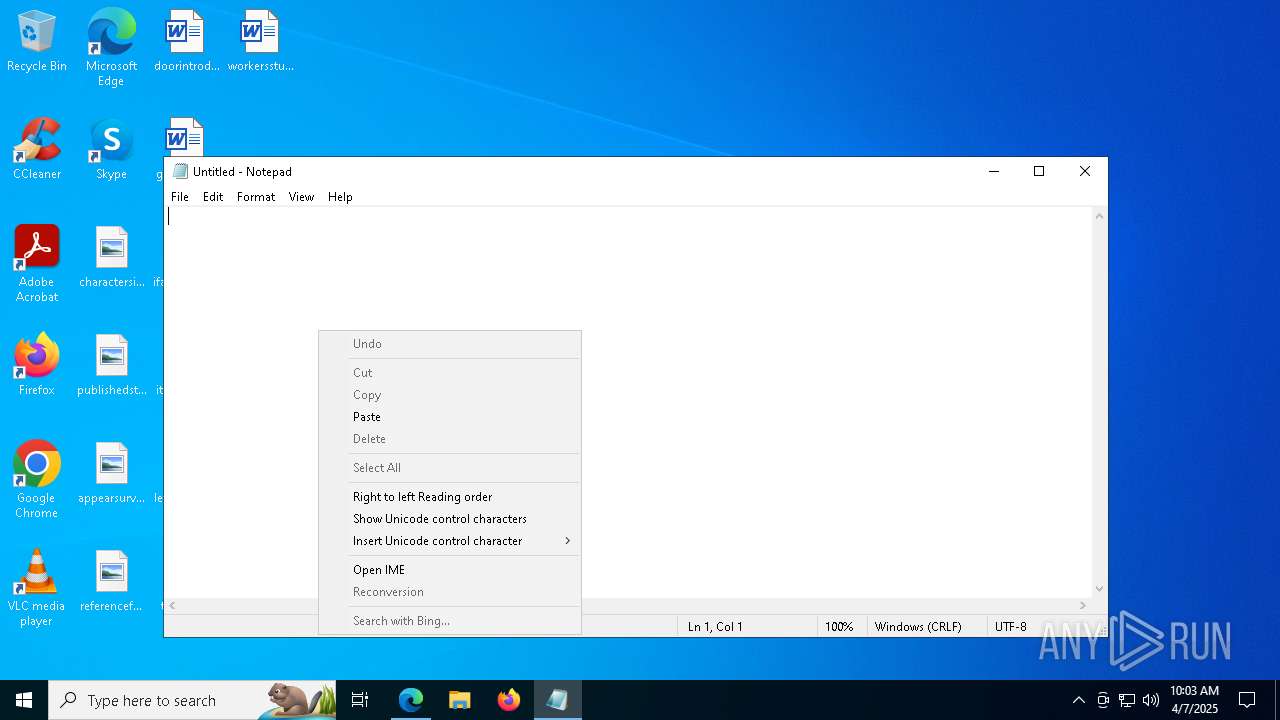
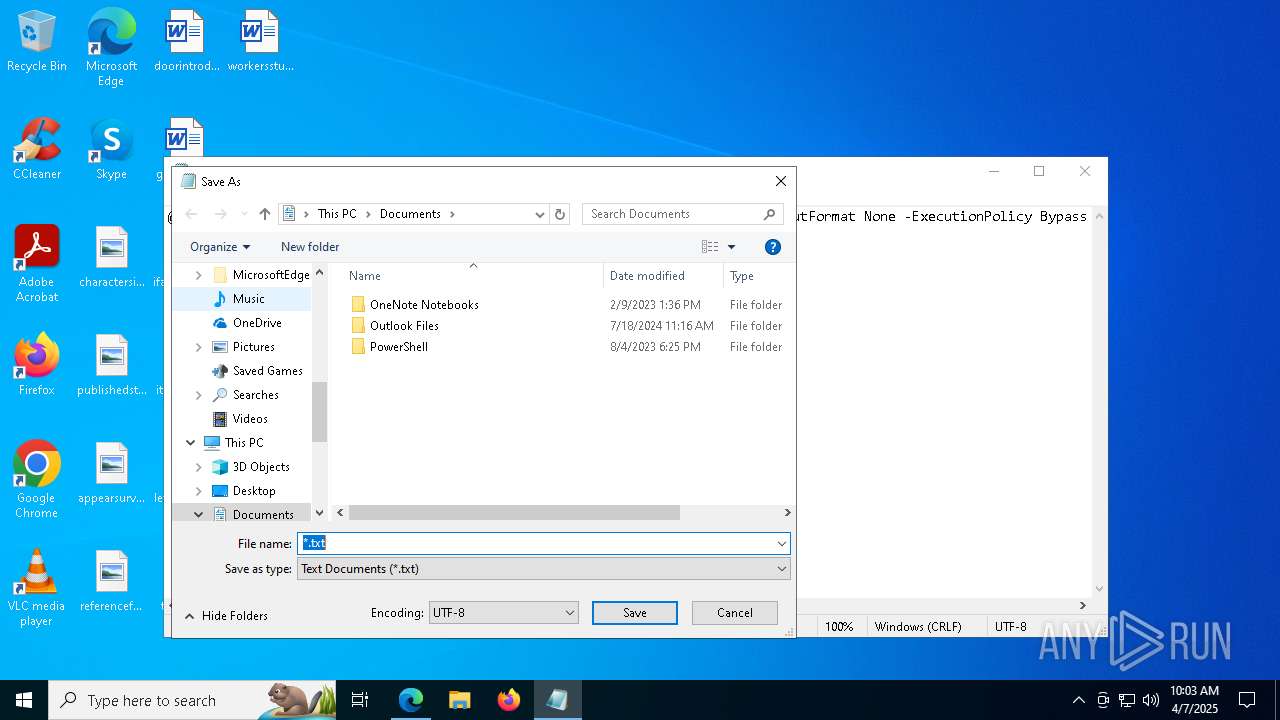
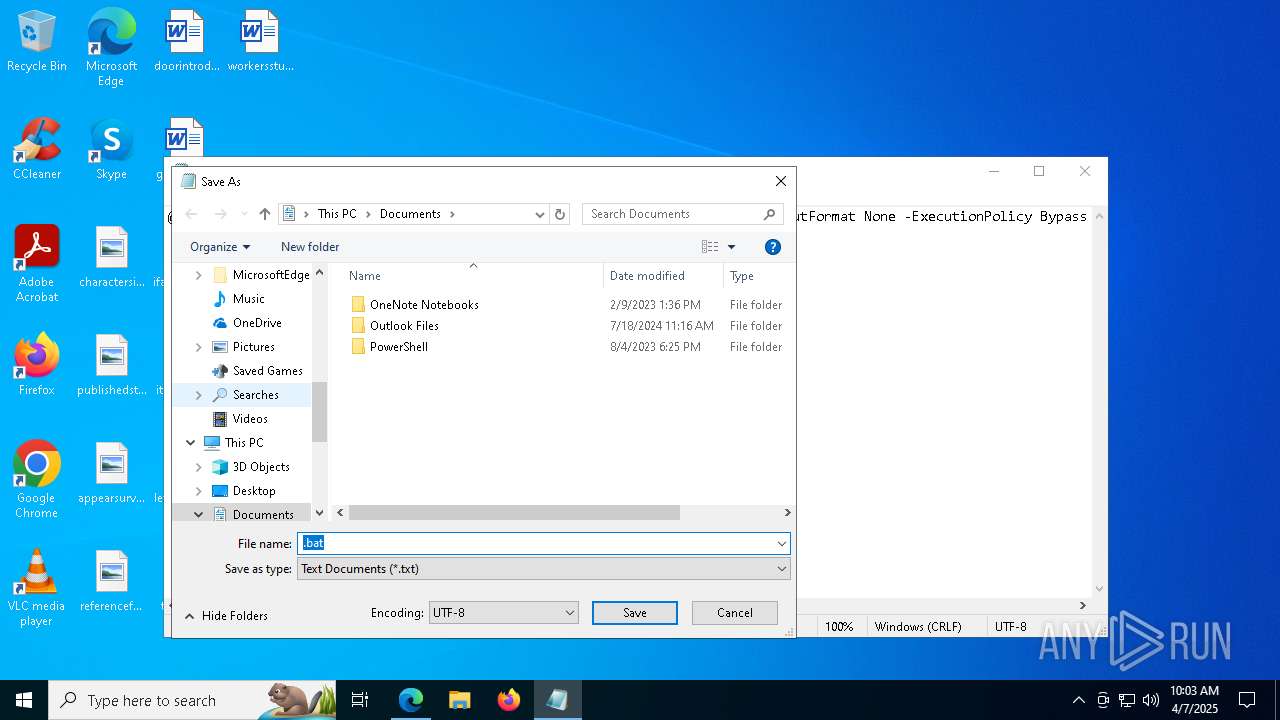
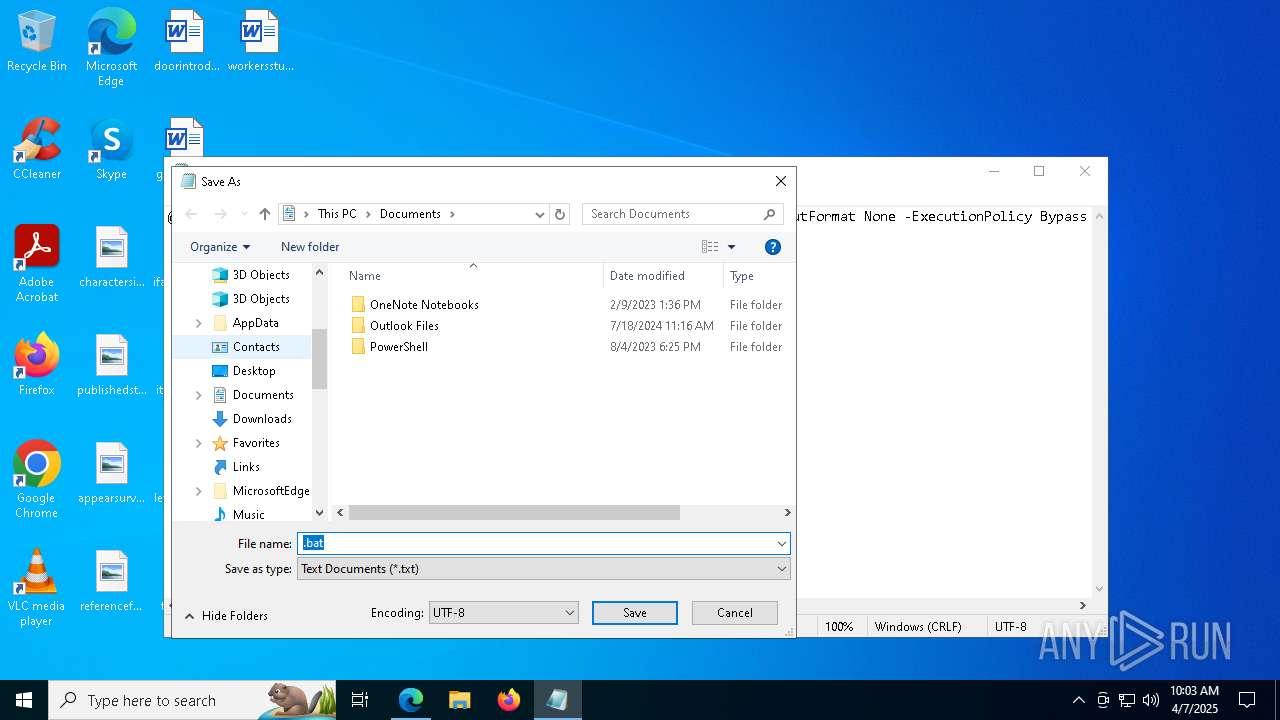
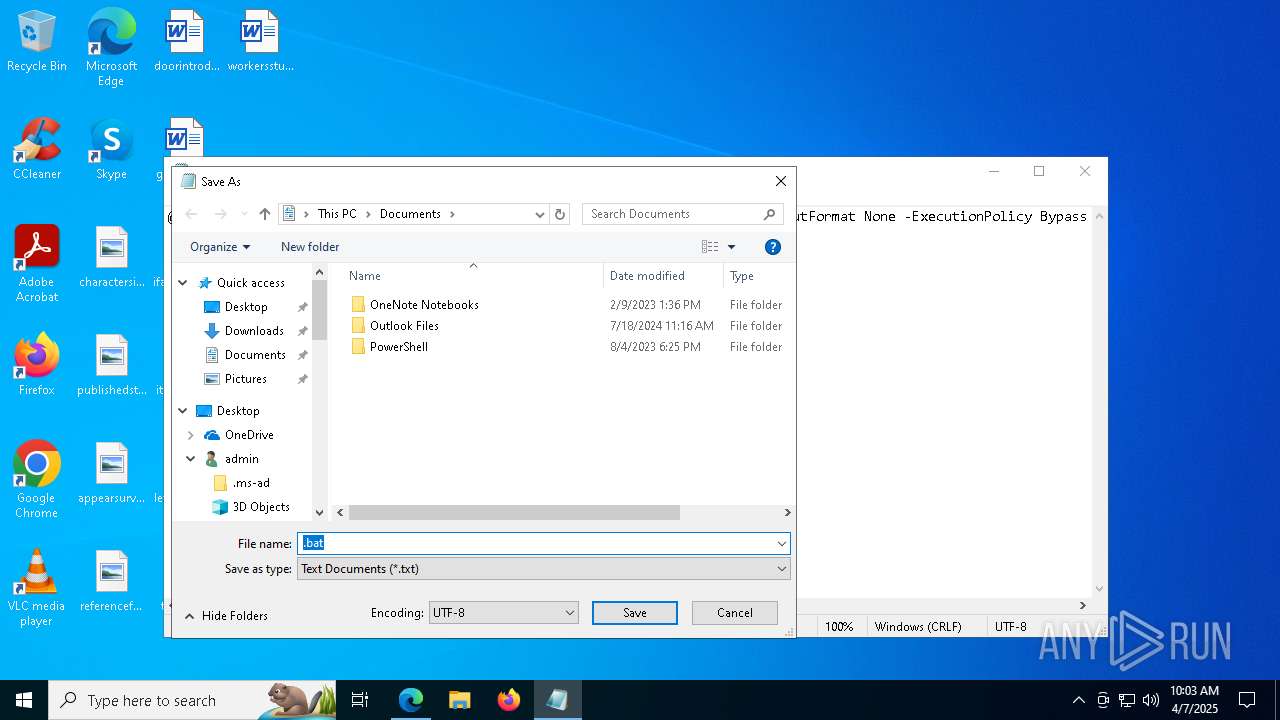
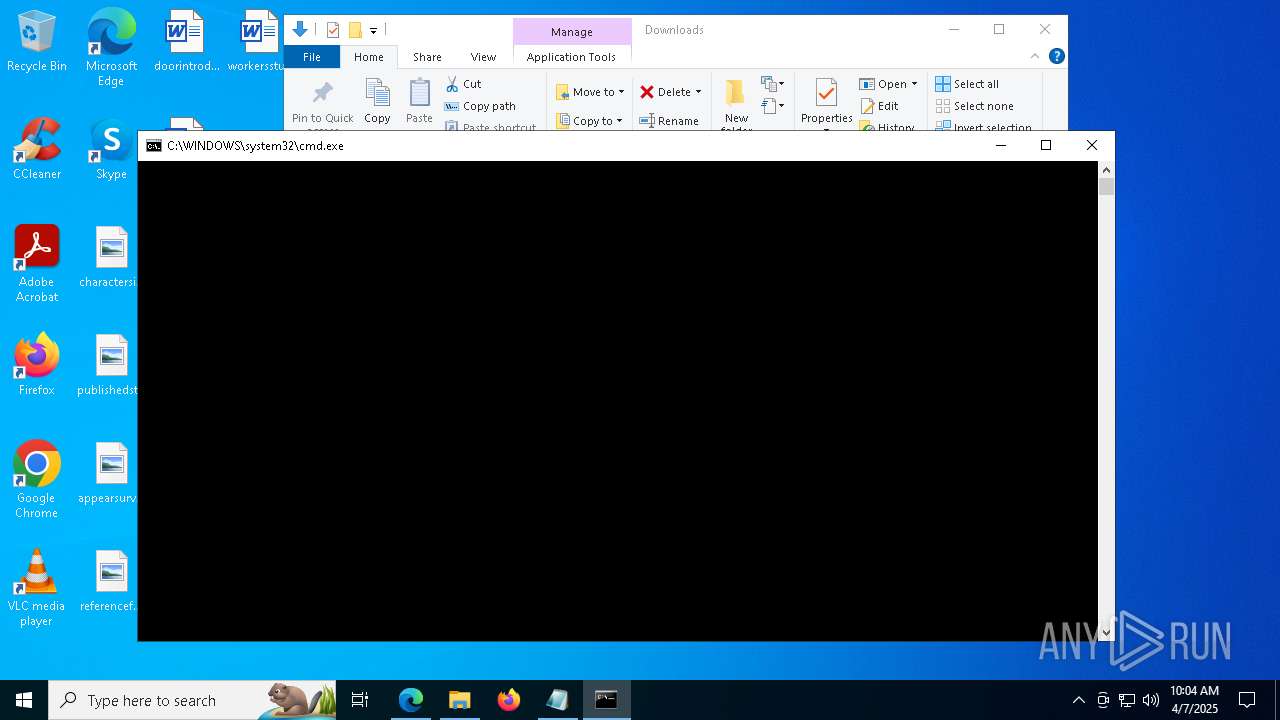
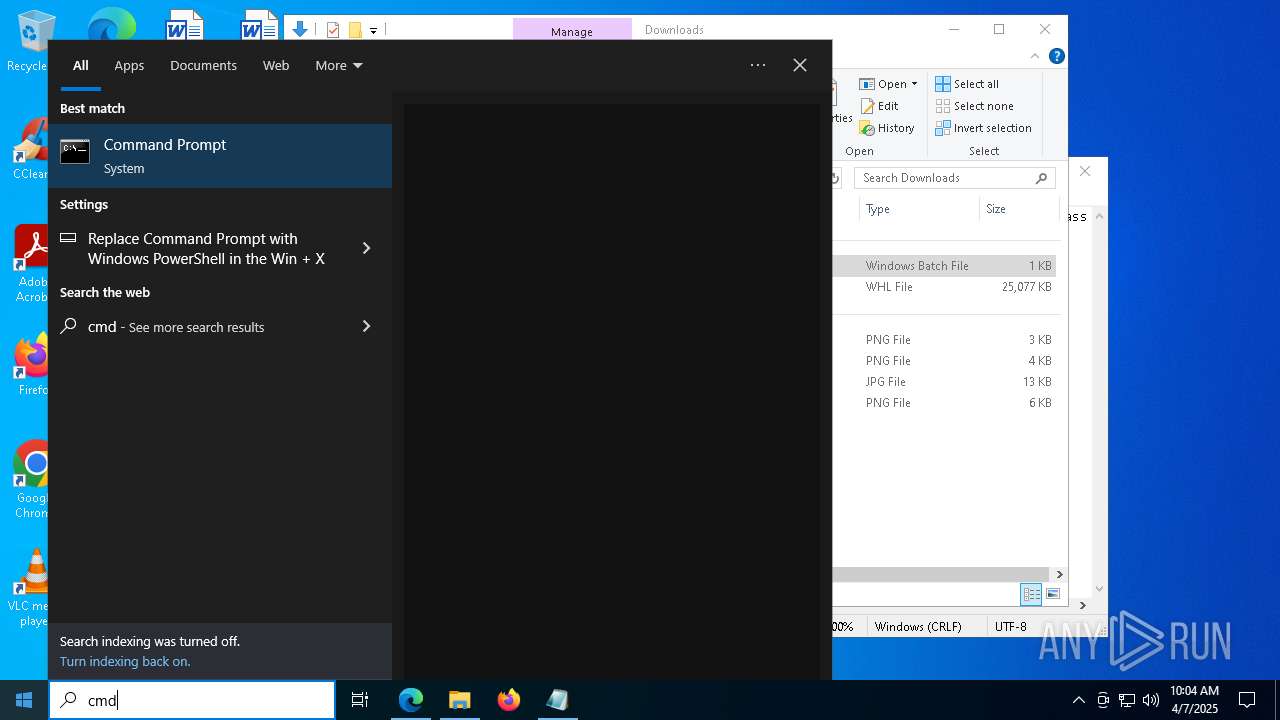
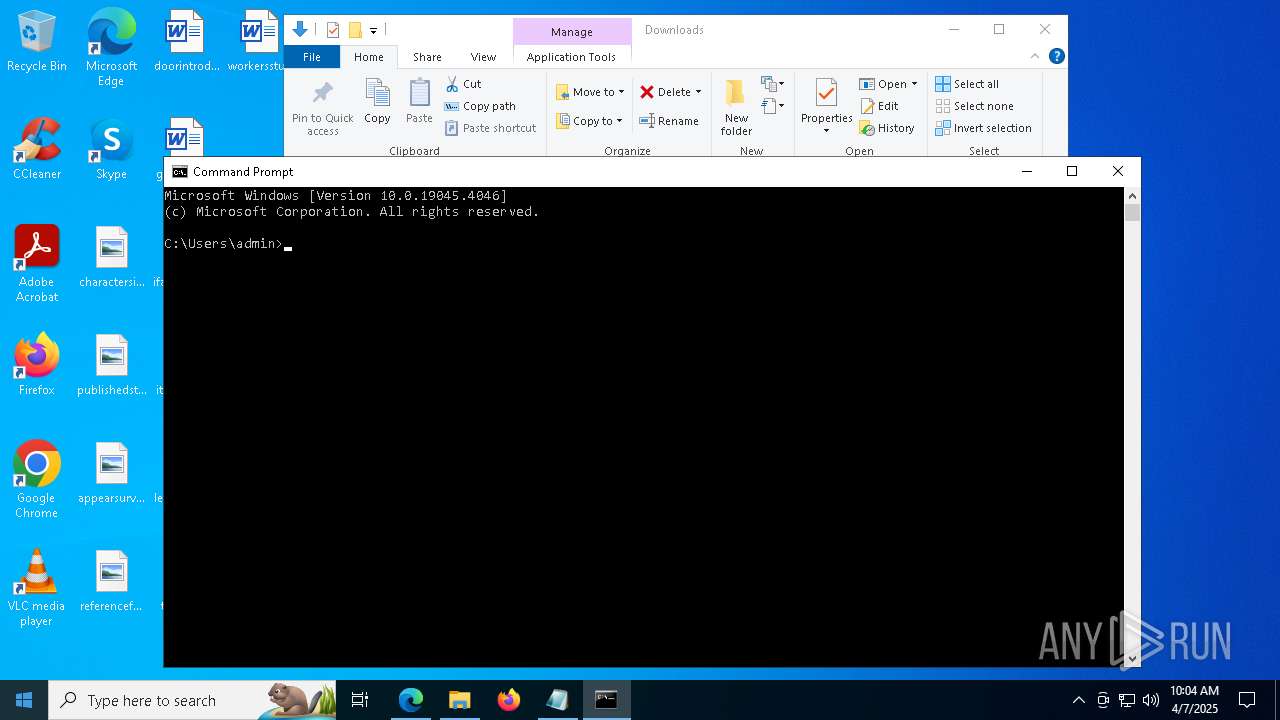
Manual execution by a user
- cmd.exe (PID: 6416)
- notepad.exe (PID: 3012)
- cmd.exe (PID: 5936)
- cmd.exe (PID: 536)
Checks proxy server information
- slui.exe (PID: 2392)
- powershell.exe (PID: 7892)
Reads security settings of Internet Explorer
- notepad.exe (PID: 3012)
Disables trace logs
- powershell.exe (PID: 7892)
The sample compiled with english language support
- powershell.exe (PID: 7892)
- msedge.exe (PID: 6088)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7892)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7892)
Creates files in the program directory
- powershell.exe (PID: 7892)
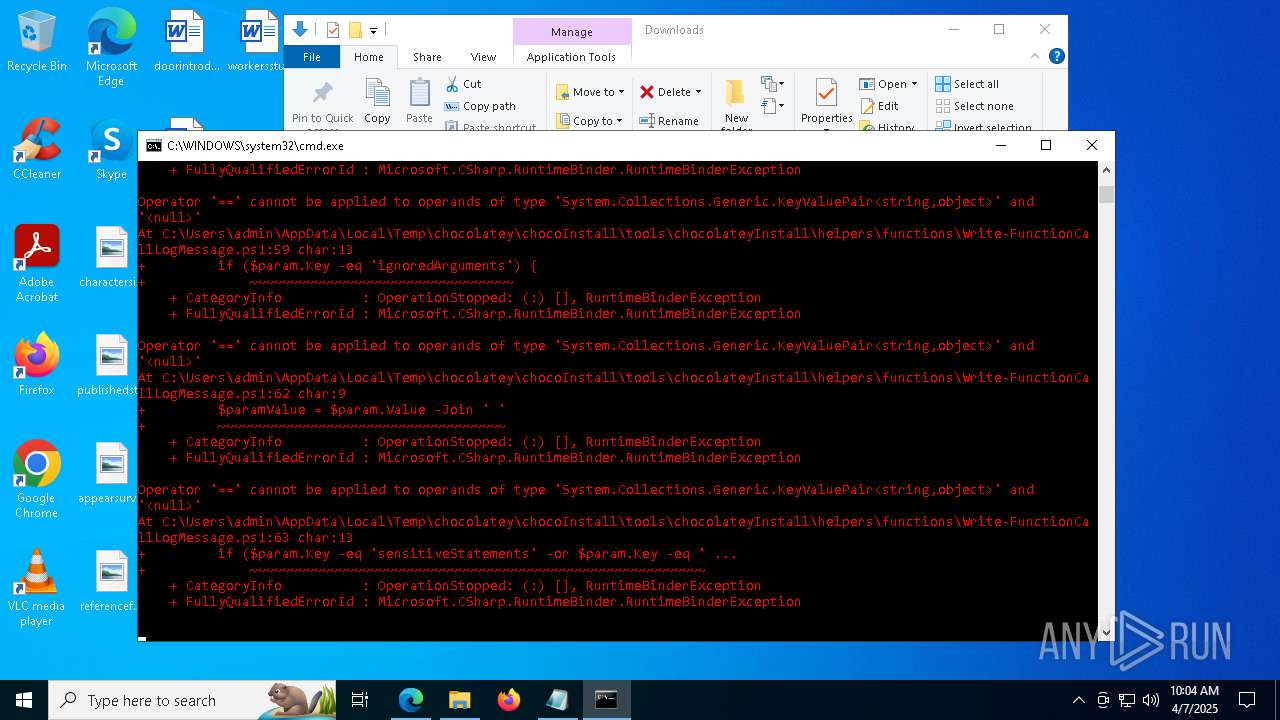
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7892)
Executable content was dropped or overwritten
- msedge.exe (PID: 6088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
200
Monitored processes
65
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=1688 --field-trial-handle=2436,i,5740415199760835914,4186268420583493518,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 668 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6804 --field-trial-handle=2436,i,5740415199760835914,4186268420583493518,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1336 --field-trial-handle=2436,i,5740415199760835914,4186268420583493518,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4168 --field-trial-handle=2436,i,5740415199760835914,4186268420583493518,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2084 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2268 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --mojo-platform-channel-handle=4640 --field-trial-handle=2436,i,5740415199760835914,4186268420583493518,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2392 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
20 745
Read events
20 614
Write events
126
Delete events
5
Modification events
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B4F16C99C3902F00 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 473C7699C3902F00 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262988 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D530C868-5D7E-4D4F-BD60-BC6AFB9AAC68} | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262988 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C52376C0-C57C-48C5-9B38-214919A4D5B8} | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262988 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {88ED4FBB-34B2-4F3D-9F5F-D82D5526ED9B} | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262988 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B1E06E6E-6498-49AE-9C82-D08A0ED6B3E7} | |||
Executable files
19
Suspicious files
442
Text files
124
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b76b.TMP | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b78a.TMP | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b78a.TMP | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b76b.TMP | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b7a9.TMP | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
48
TCP/UDP connections
98
DNS requests
104
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5124 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744054968&P2=404&P3=2&P4=L8Wz5RiXikEdz8hp%2f9aFDL2SEDerlbwrj9av4O2RtFhsi8lGEoOc1ZyqWpIah420GLYz0IyT3s64OXekrj4czQ%3d%3d | unknown | — | — | whitelisted |
5124 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744054968&P2=404&P3=2&P4=L8Wz5RiXikEdz8hp%2f9aFDL2SEDerlbwrj9av4O2RtFhsi8lGEoOc1ZyqWpIah420GLYz0IyT3s64OXekrj4czQ%3d%3d | unknown | — | — | whitelisted |
5124 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744054968&P2=404&P3=2&P4=L8Wz5RiXikEdz8hp%2f9aFDL2SEDerlbwrj9av4O2RtFhsi8lGEoOc1ZyqWpIah420GLYz0IyT3s64OXekrj4czQ%3d%3d | unknown | — | — | whitelisted |
5124 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744054968&P2=404&P3=2&P4=L8Wz5RiXikEdz8hp%2f9aFDL2SEDerlbwrj9av4O2RtFhsi8lGEoOc1ZyqWpIah420GLYz0IyT3s64OXekrj4czQ%3d%3d | unknown | — | — | whitelisted |
5124 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744054968&P2=404&P3=2&P4=L8Wz5RiXikEdz8hp%2f9aFDL2SEDerlbwrj9av4O2RtFhsi8lGEoOc1ZyqWpIah420GLYz0IyT3s64OXekrj4czQ%3d%3d | unknown | — | — | whitelisted |
5124 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744054968&P2=404&P3=2&P4=L8Wz5RiXikEdz8hp%2f9aFDL2SEDerlbwrj9av4O2RtFhsi8lGEoOc1ZyqWpIah420GLYz0IyT3s64OXekrj4czQ%3d%3d | unknown | — | — | whitelisted |
5124 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744054968&P2=404&P3=2&P4=L8Wz5RiXikEdz8hp%2f9aFDL2SEDerlbwrj9av4O2RtFhsi8lGEoOc1ZyqWpIah420GLYz0IyT3s64OXekrj4czQ%3d%3d | unknown | — | — | whitelisted |
5124 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744054968&P2=404&P3=2&P4=L8Wz5RiXikEdz8hp%2f9aFDL2SEDerlbwrj9av4O2RtFhsi8lGEoOc1ZyqWpIah420GLYz0IyT3s64OXekrj4czQ%3d%3d | unknown | — | — | whitelisted |
5124 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744054968&P2=404&P3=2&P4=L8Wz5RiXikEdz8hp%2f9aFDL2SEDerlbwrj9av4O2RtFhsi8lGEoOc1ZyqWpIah420GLYz0IyT3s64OXekrj4czQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
7148 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7384 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7384 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
7384 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7384 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7384 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7892 | powershell.exe | Potentially Bad Traffic | ET INFO Observed Chocolatey Windows Package Management Domain (chocolatey .org in TLS SNI) |