| File name: | jokey##357504783.vbs |
| Full analysis: | https://app.any.run/tasks/d00e46fd-6cfe-4d8a-b883-c871b15de945 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 16:09:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with no line terminators |
| MD5: | 94E56D4A2188FC79D736B3DB51607B18 |
| SHA1: | EFA041CCEF361EFC51A411D64E6E70F41CB7471F |
| SHA256: | 2ECC4976FB5FE84FBF51A7BAECB0B0CE29BD4CBA7D96E63A97562A90929C49E5 |
| SSDEEP: | 6144:6JZD/fxHwq6dByF7H4V2xfj8jon7Cf6OIz5OwRhic3mW8Crp1541qBUH3bFqDr1o:C/zCgzSwKd9 |
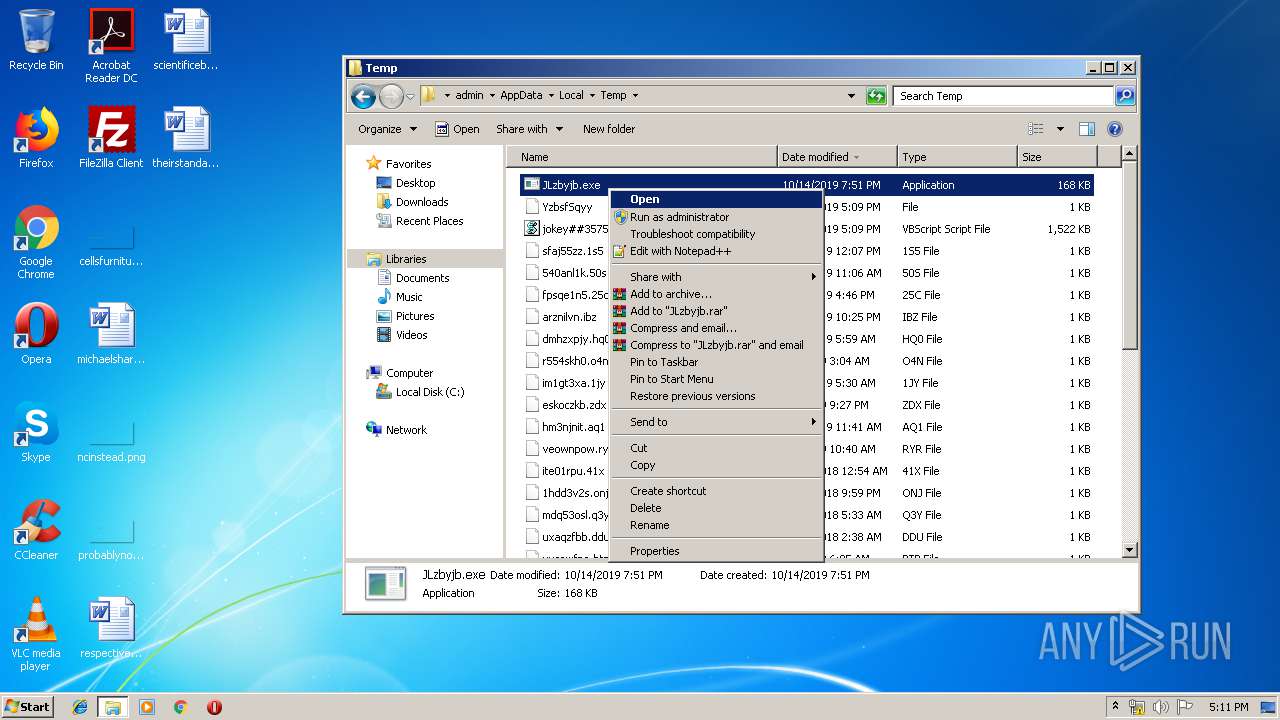
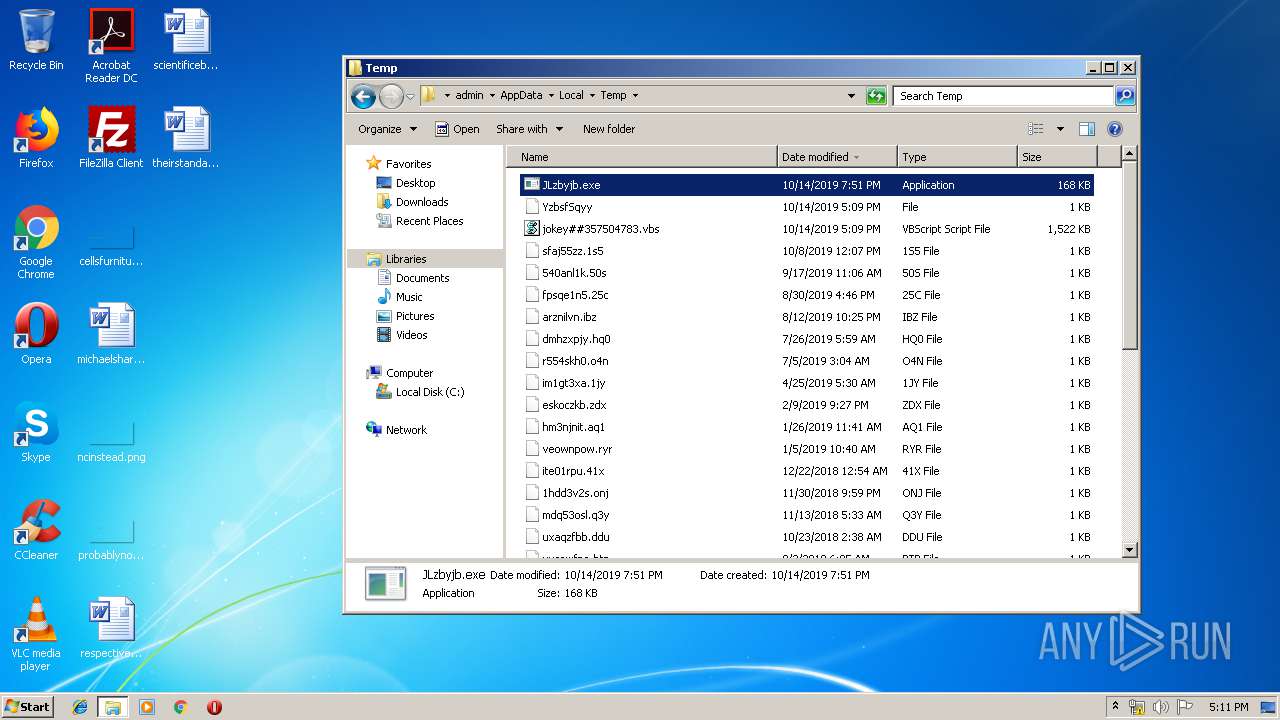
MALICIOUS
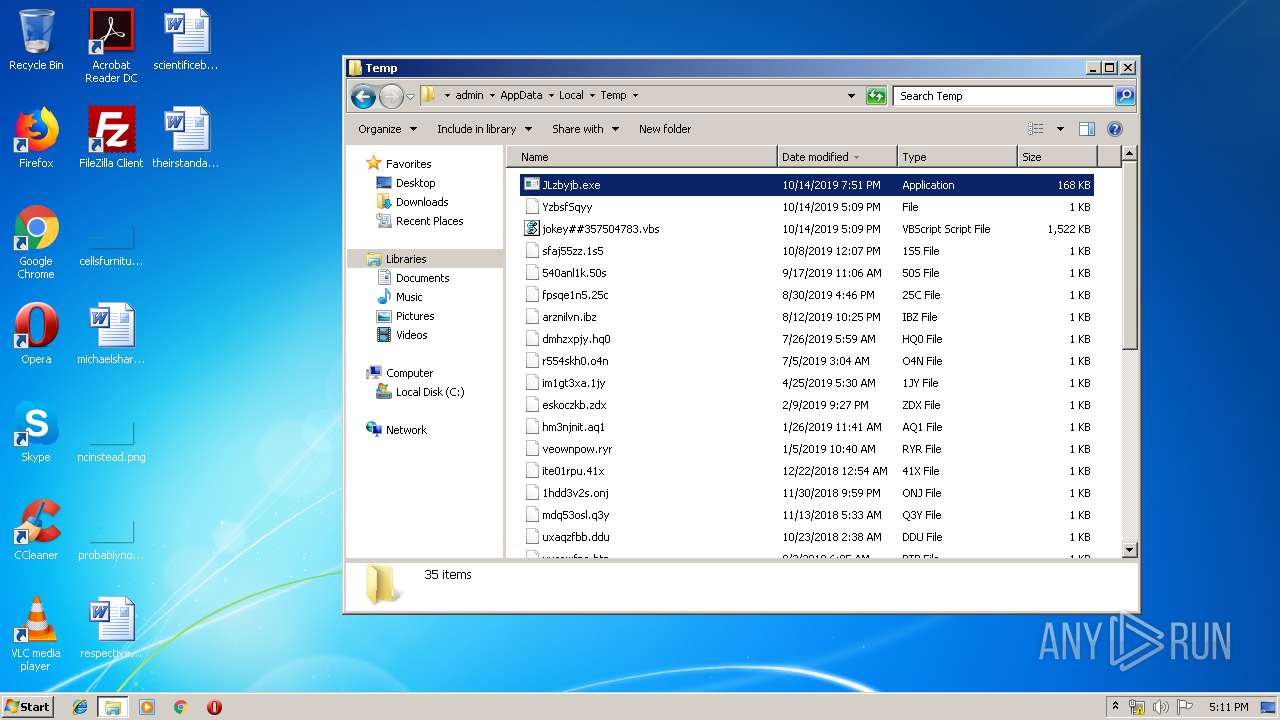
Application was dropped or rewritten from another process
- JLzbyjb.exe (PID: 2832)
- JLzbyjb.exe (PID: 3172)
SUSPICIOUS
Executed via WMI
- JLzbyjb.exe (PID: 2832)
Executable content was dropped or overwritten
- WScript.exe (PID: 2300)
INFO
Manual execution by user
- JLzbyjb.exe (PID: 3172)
- explorer.exe (PID: 184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
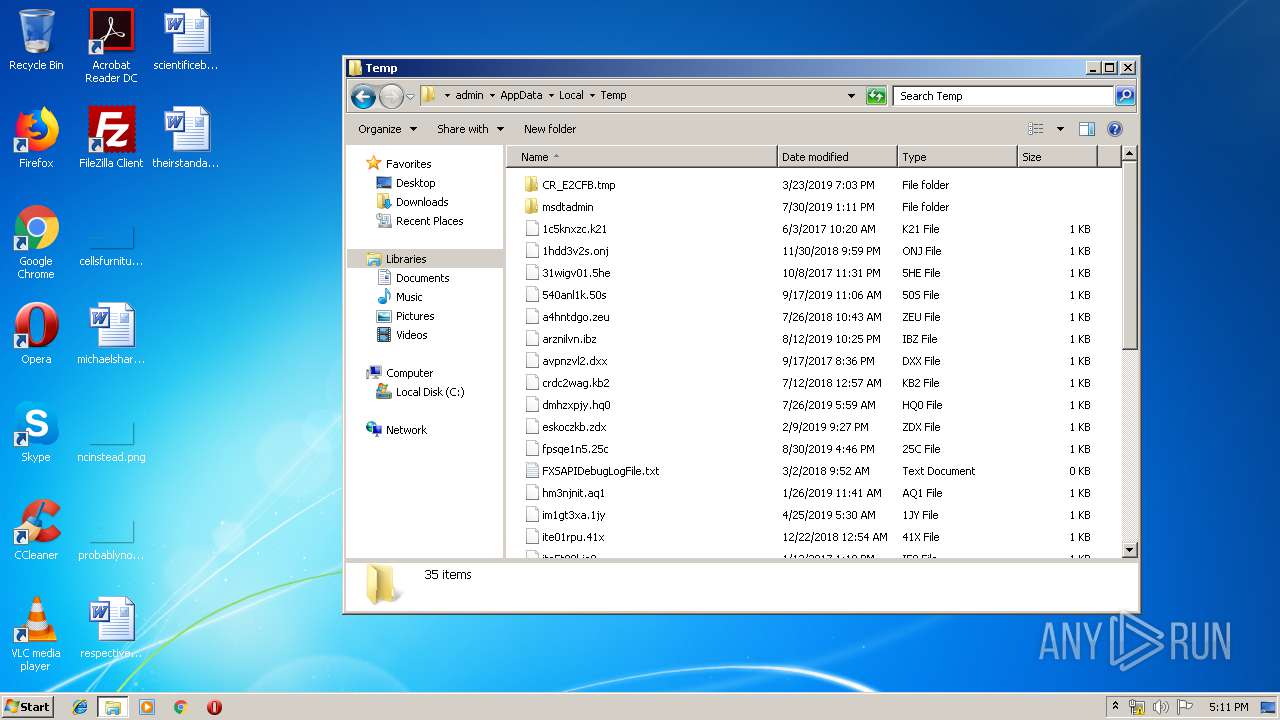
| 2300 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\jokey##357504783.vbs" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2832 | C:\Users\admin\AppData\Local\Temp\JLzbyjb.exe | C:\Users\admin\AppData\Local\Temp\JLzbyjb.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft MIB-II subagent Exit code: 0 Version: 6.1.7601.17514 ( Modules
| |||||||||||||||
| 3172 | "C:\Users\admin\AppData\Local\Temp\JLzbyjb.exe" | C:\Users\admin\AppData\Local\Temp\JLzbyjb.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft MIB-II subagent Exit code: 0 Version: 6.1.7601.17514 ( Modules
| |||||||||||||||
Total events
437
Read events
431
Write events
6
Delete events
0
Modification events
| (PID) Process: | (2300) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2300) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2300) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\Component Categories\{56FFCC30-D398-11D0-B2AE-00A0C908FA49}\Enum |
| Operation: | write | Name: | Implementing |
Value: 1C00000001000000E3070A0001000E00100009002F008D0100000000 | |||
Executable files
1
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
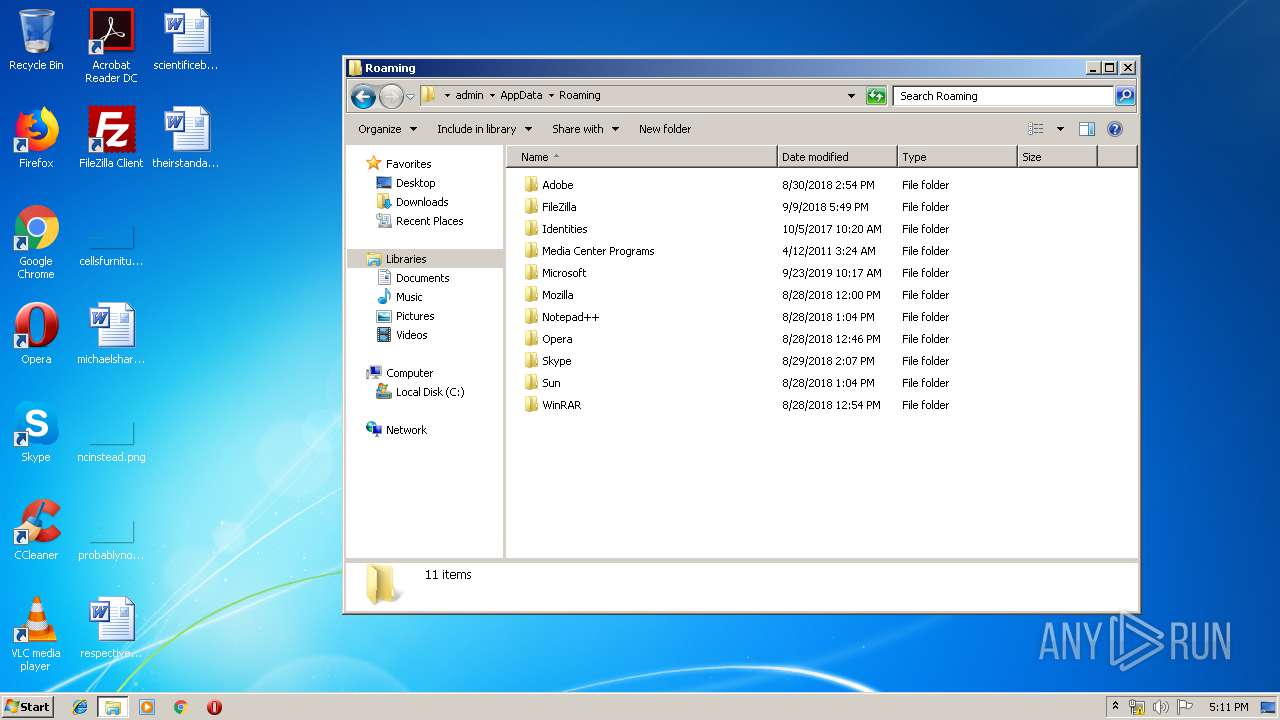
| 2300 | WScript.exe | C:\Users\admin\AppData\Local\Temp\YzbsfSqyy | text | |
MD5:— | SHA256:— | |||
| 2300 | WScript.exe | C:\Users\admin\AppData\Local\Temp\HwjPoTtXh.txt.zip | compressed | |
MD5:— | SHA256:— | |||
| 2300 | WScript.exe | C:\Users\admin\AppData\Local\Temp\HwjPoTtXh.txt | compressed | |
MD5:— | SHA256:— | |||
| 2300 | WScript.exe | C:\Users\admin\AppData\Local\Temp\JLzbyjb.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
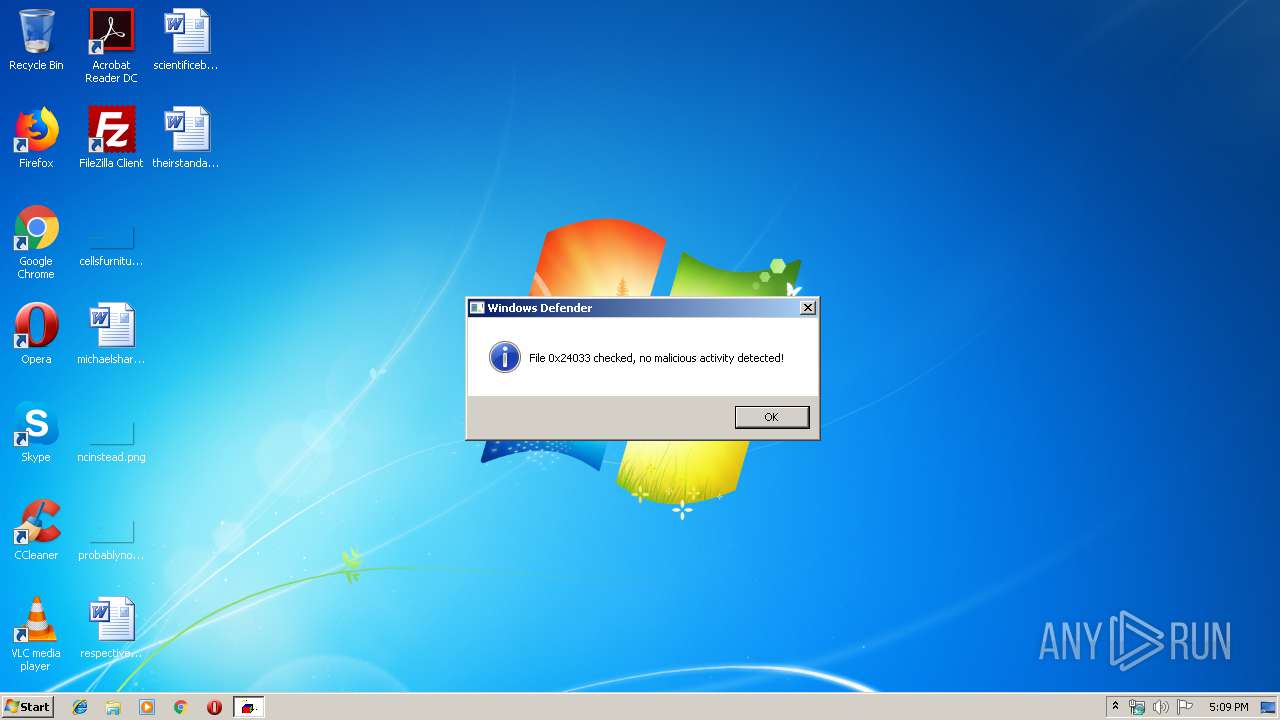
Process | Message |
|---|---|
JLzbyjb.exe | Installing...
|
JLzbyjb.exe | Installing...
|
JLzbyjb.exe | Installing...
|
JLzbyjb.exe | Installing...
|
JLzbyjb.exe | Installing...
|
JLzbyjb.exe | Installing...
|
JLzbyjb.exe | Installing...
|
JLzbyjb.exe | Installing...
|
JLzbyjb.exe | Installing...
|
JLzbyjb.exe | Installing...
|