| File name: | 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5 |
| Full analysis: | https://app.any.run/tasks/133146b6-14f6-4cd9-8e1c-ea04cb8e6e26 |
| Verdict: | Malicious activity |
| Analysis date: | December 12, 2024, 18:40:33 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | E9BF284BA44F49D5629C3109BFC8F50F |
| SHA1: | 137ECC9DC28D1FFD3C86634FABC6EA6FB631C548 |
| SHA256: | 2EC3847D7B70047309DDF6030DAD2480DD738BDC2597271720CCB28699F86EF5 |
| SSDEEP: | 98304:B87HqpR6GKrfM+7DqOznb45Ift54iT01x3yGERIToiCOiZos9vC+J15SgEV6FWtq:LCCq |
MALICIOUS
Executing a file with an untrusted certificate
- KMSELDI.exe (PID: 5720)
- AutoPico.exe (PID: 308)
Changes image file execution options
- KMSELDI.exe (PID: 5720)
- AutoPico.exe (PID: 308)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 5400)
SUSPICIOUS
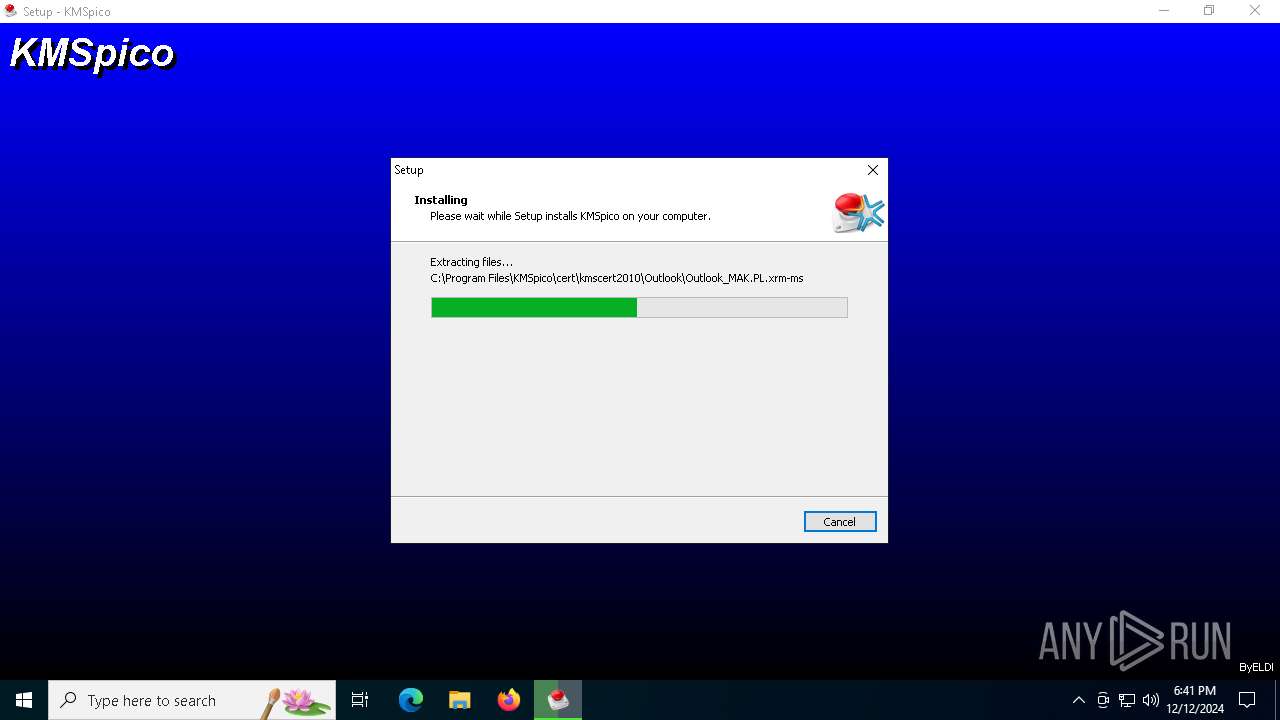
Executable content was dropped or overwritten
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.exe (PID: 5244)
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.exe (PID: 4592)
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp (PID: 3696)
- KMSELDI.exe (PID: 5720)
Reads security settings of Internet Explorer
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp (PID: 3220)
Reads the Windows owner or organization settings
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp (PID: 3696)
Process drops legitimate windows executable
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp (PID: 3696)
Modifies the phishing filter of IE
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp (PID: 3696)
Executing commands from ".cmd" file
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp (PID: 3696)
Starts SC.EXE for service management
- cmd.exe (PID: 5236)
Starts CMD.EXE for commands execution
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp (PID: 3696)
INFO
Reads the computer name
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp (PID: 3220)
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp (PID: 3696)
- KMSELDI.exe (PID: 5720)
- AutoPico.exe (PID: 308)
Checks supported languages
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.exe (PID: 5244)
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp (PID: 3220)
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp (PID: 3696)
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.exe (PID: 4592)
- KMSELDI.exe (PID: 5720)
- UninsHs.exe (PID: 2600)
- AutoPico.exe (PID: 308)
Process checks computer location settings
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp (PID: 3220)
Create files in a temporary directory
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.exe (PID: 5244)
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.exe (PID: 4592)
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp (PID: 3696)
The sample compiled with english language support
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp (PID: 3696)
Creates files in the program directory
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp (PID: 3696)
- AutoPico.exe (PID: 308)
Creates a software uninstall entry
- 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp (PID: 3696)
Reads Environment values
- KMSELDI.exe (PID: 5720)
- AutoPico.exe (PID: 308)
Reads the machine GUID from the registry
- KMSELDI.exe (PID: 5720)
- AutoPico.exe (PID: 308)
Reads product name
- KMSELDI.exe (PID: 5720)
- AutoPico.exe (PID: 308)
Reads Microsoft Office registry keys
- KMSELDI.exe (PID: 5720)
- AutoPico.exe (PID: 308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (71.1) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (9.1) |
| .scr | | | Windows screen saver (8.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.2) |
| .exe | | | Win32 Executable (generic) (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 40448 |
| InitializedDataSize: | 27648 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa5f8 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
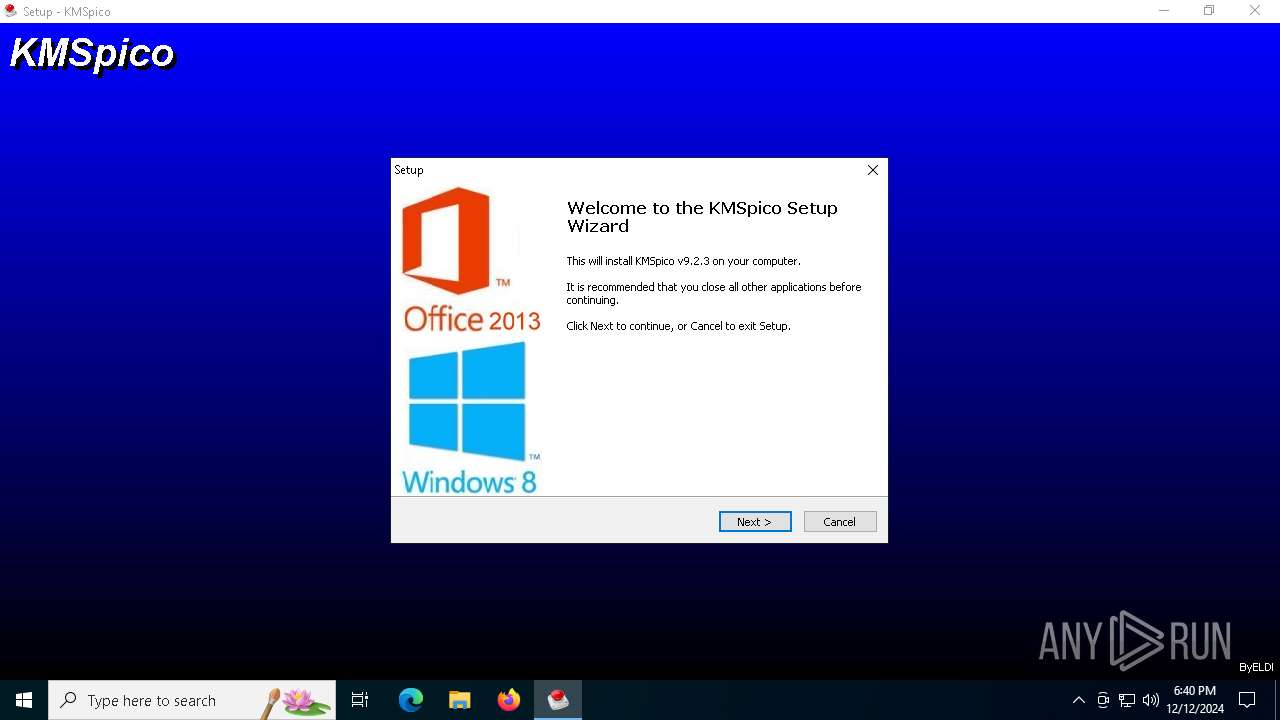
| FileVersionNumber: | 9.2.3.0 |
| ProductVersionNumber: | 9.2.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
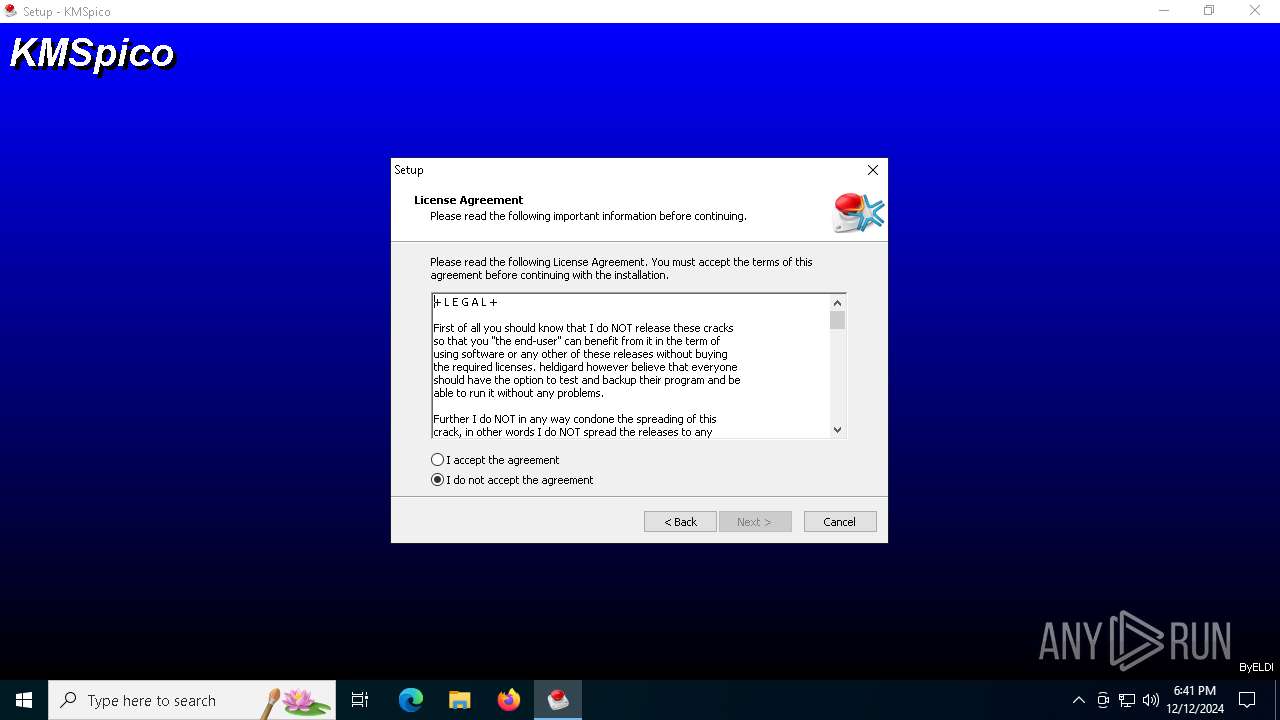
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | KMSpico Setup |
| FileVersion: | 9.2.3 |
| LegalCopyright: | ByELDI |
| ProductName: | KMSpico |
| ProductVersion: | 9.2.3 |
Total processes
139
Monitored processes
14
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Program Files\KMSpico\AutoPico.exe" /silent | C:\Program Files\KMSpico\AutoPico.exe | 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: AutoPico Exit code: 0 Version: 12.1.0.0 Modules
| |||||||||||||||
| 556 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1344 | SCHTASKS /Create /TN "AutoPico Daily Restart" /TR "'C:\Program Files\KMSpico\AutoPico.exe' /silent" /SC DAILY /ST 11:59:59 /RI 330 /DU 12:00 /RU SYSTEM /RL Highest /F | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2600 | "C:\Program Files\KMSpico\UninsHs.exe" /r0=KMSpico,default,C:\Users\admin\Desktop\2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.exe | C:\Program Files\KMSpico\UninsHs.exe | — | 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | |||||||||||
User: admin Company: Han-soft Integrity Level: HIGH Description: Uninstall for InnoSetup by Han-soft Exit code: 0 Version: 2.1.0.283 Modules
| |||||||||||||||
| 2800 | SCHTASKS /Create /TN "Service KMSELDI" /TR "sc.exe start "Service KMSELDI"" /SC DAILY /ST 04:59:59 /RI 330 /DU 12:00 /RU SYSTEM /RL Highest /F | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 2147500037 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3220 | "C:\Users\admin\AppData\Local\Temp\is-2VRG5.tmp\2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp" /SL5="$C01FE,2608489,69120,C:\Users\admin\Desktop\2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.exe" | C:\Users\admin\AppData\Local\Temp\is-2VRG5.tmp\2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | — | 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 3508 | sc create "Service KMSELDI" binPath= "C:\Program Files\KMSpico\Service_KMS.exe" type= own error= normal start= auto DisplayName= "Service KMSELDI" | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3696 | "C:\Users\admin\AppData\Local\Temp\is-R266R.tmp\2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp" /SL5="$502BA,2608489,69120,C:\Users\admin\Desktop\2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.exe" /SPAWNWND=$602C8 /NOTIFYWND=$C01FE | C:\Users\admin\AppData\Local\Temp\is-R266R.tmp\2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 4592 | "C:\Users\admin\Desktop\2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.exe" /SPAWNWND=$602C8 /NOTIFYWND=$C01FE | C:\Users\admin\Desktop\2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.exe | 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: KMSpico Setup Exit code: 0 Version: 9.2.3 Modules
| |||||||||||||||
| 4804 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 820
Read events
3 791
Write events
24
Delete events
5
Modification events
| (PID) Process: | (3696) 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\System |
| Operation: | delete value | Name: | EnableSmartScreen |
Value: | |||
| (PID) Process: | (3696) 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\System |
| Operation: | write | Name: | EnableSmartScreen |
Value: 0 | |||
| (PID) Process: | (3696) 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | delete value | Name: | SmartScreenEnabled |
Value: Off | |||
| (PID) Process: | (3696) 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SmartScreenEnabled |
Value: Off | |||
| (PID) Process: | (3696) 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\PhishingFilter |
| Operation: | delete value | Name: | EnabledV9 |
Value: | |||
| (PID) Process: | (3696) 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\PhishingFilter |
| Operation: | write | Name: | EnabledV9 |
Value: 0 | |||
| (PID) Process: | (3696) 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KMSpico_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.3 (a) | |||
| (PID) Process: | (3696) 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KMSpico_is1 |
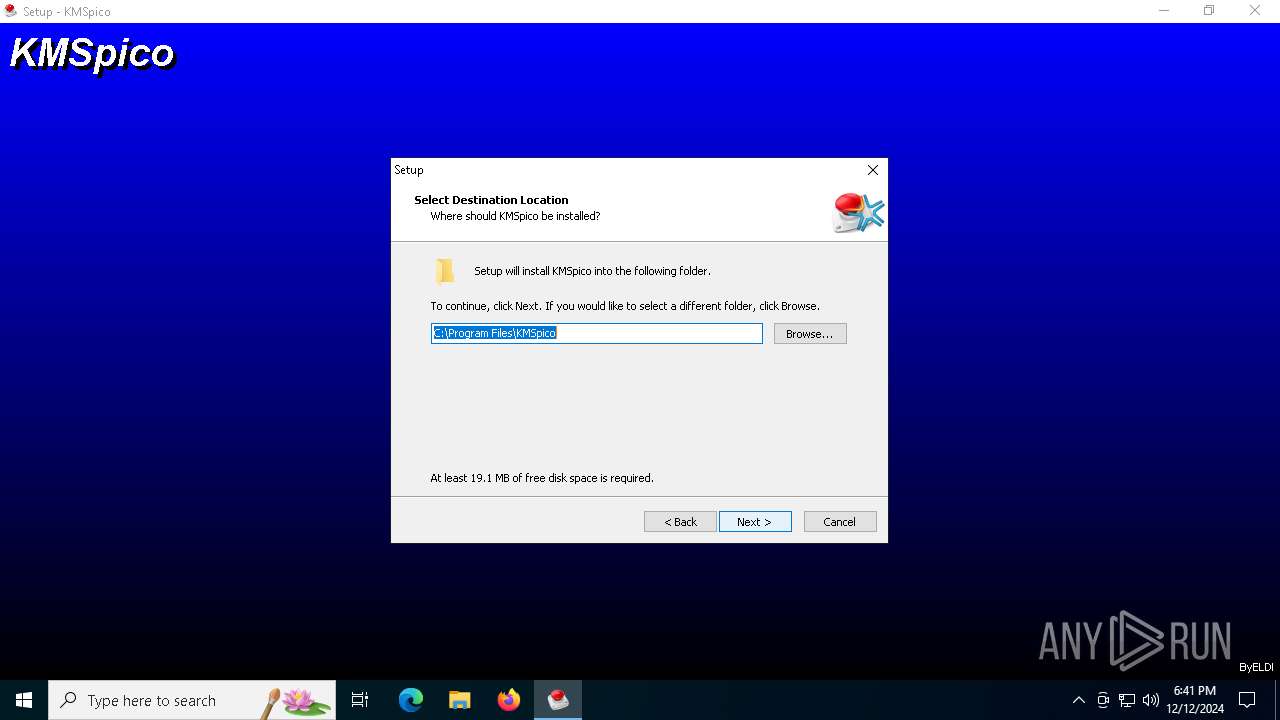
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\KMSpico | |||
| (PID) Process: | (3696) 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KMSpico_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\KMSpico\ | |||
| (PID) Process: | (3696) 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KMSpico_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: KMSpico | |||
Executable files
18
Suspicious files
29
Text files
873
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3696 | 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | C:\Users\admin\AppData\Local\Temp\is-OIQE8.tmp\_isetup\_setup64.tmp | executable | |
MD5:C8871EFD8AF2CF4D9D42D1FF8FADBF89 | SHA256:E4FC574A01B272C2D0AED0EC813F6D75212E2A15A5F5C417129DD65D69768F40 | |||
| 3696 | 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | C:\Program Files\KMSpico\driver\UnInstallDriver.cmd | text | |
MD5:4D389CB3A3A016D04E90AD9F4314238C | SHA256:72532E7DA1741269551C054D3A3461E11E182F27FBF225A06B31ADE7772AE613 | |||
| 3696 | 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | C:\Program Files\KMSpico\driver\is-625IU.tmp | text | |
MD5:4D389CB3A3A016D04E90AD9F4314238C | SHA256:72532E7DA1741269551C054D3A3461E11E182F27FBF225A06B31ADE7772AE613 | |||
| 4592 | 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.exe | C:\Users\admin\AppData\Local\Temp\is-R266R.tmp\2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | executable | |
MD5:7060027EB4044B1D80C19F47CC87CDC7 | SHA256:383D09D76BDFE36C4CD700A70D985D568BE66C54C3B15E53670CD646074F2383 | |||
| 5244 | 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.exe | C:\Users\admin\AppData\Local\Temp\is-2VRG5.tmp\2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | executable | |
MD5:7060027EB4044B1D80C19F47CC87CDC7 | SHA256:383D09D76BDFE36C4CD700A70D985D568BE66C54C3B15E53670CD646074F2383 | |||
| 3696 | 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | C:\Program Files\KMSpico\Service_KMS.exe | executable | |
MD5:77A7651C4077DC0E5EBAA6574D586749 | SHA256:EE9BC6533F490B41DDDD5140AC809891F4F9684F35B467ABB3D9306B9C07D363 | |||
| 3696 | 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | C:\Program Files\KMSpico\driver\tap-windows-9.9.2_3.exe | executable | |
MD5:AC9B2624EF366742C9AD32B86225A251 | SHA256:02E1013EE8D548EDC3FBAFAB672977EA8C677CF1F0B57018652FCF2A2411CBFB | |||
| 3696 | 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | C:\Program Files\KMSpico\AutoPico.exe | executable | |
MD5:10B201CC8EBFC96C0F20BC2BF3BF2144 | SHA256:1B7A6E65FFF28C83779212F3FF63CAB37FE2C0F7F280B1FF67F4917082D97295 | |||
| 3696 | 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | C:\Program Files\KMSpico\KMSELDI.exe | executable | |
MD5:6BBEDD3E5505AFA3C9CE2B81A0C1362D | SHA256:288B8B0B5E8D73C8005EF46AACDBEB515E5BAA32F8A478AB2CE1A0B4BEDE6237 | |||
| 3696 | 2ec3847d7b70047309ddf6030dad2480dd738bdc2597271720ccb28699f86ef5.tmp | C:\Program Files\KMSpico\logs\is-J7R0B.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
18
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5856 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3464 | RUXIMICS.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5856 | svchost.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3464 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5856 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.204.155:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5856 | svchost.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5856 | svchost.exe | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3464 | RUXIMICS.exe | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5720 | KMSELDI.exe | 94.16.122.152:123 | 3.pool.ntp.org | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
3.pool.ntp.org |
| whitelisted |
2.pool.ntp.org |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |