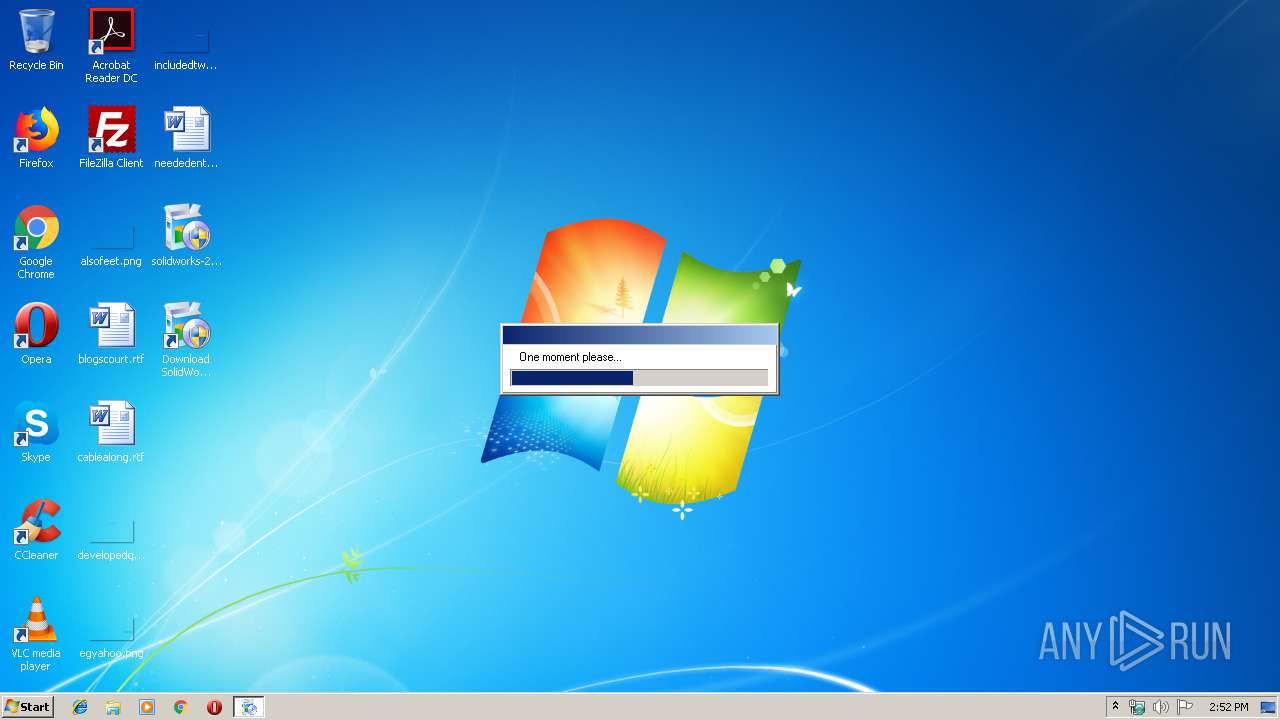
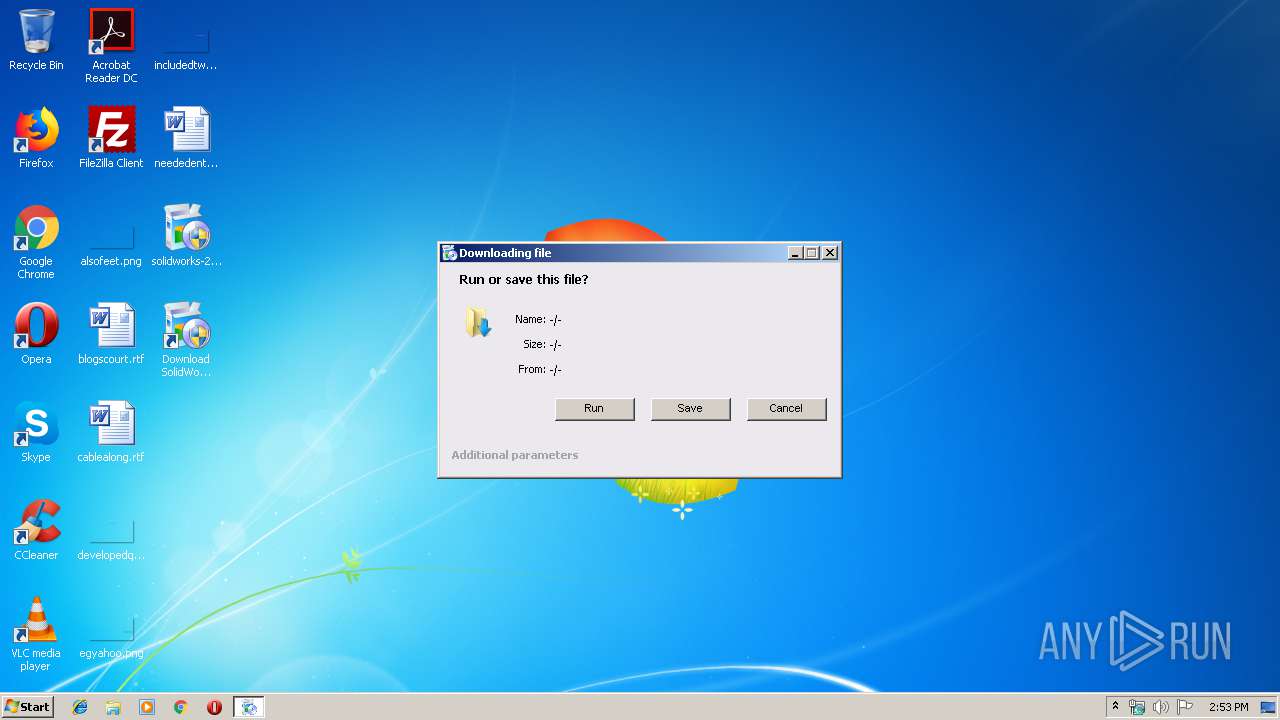
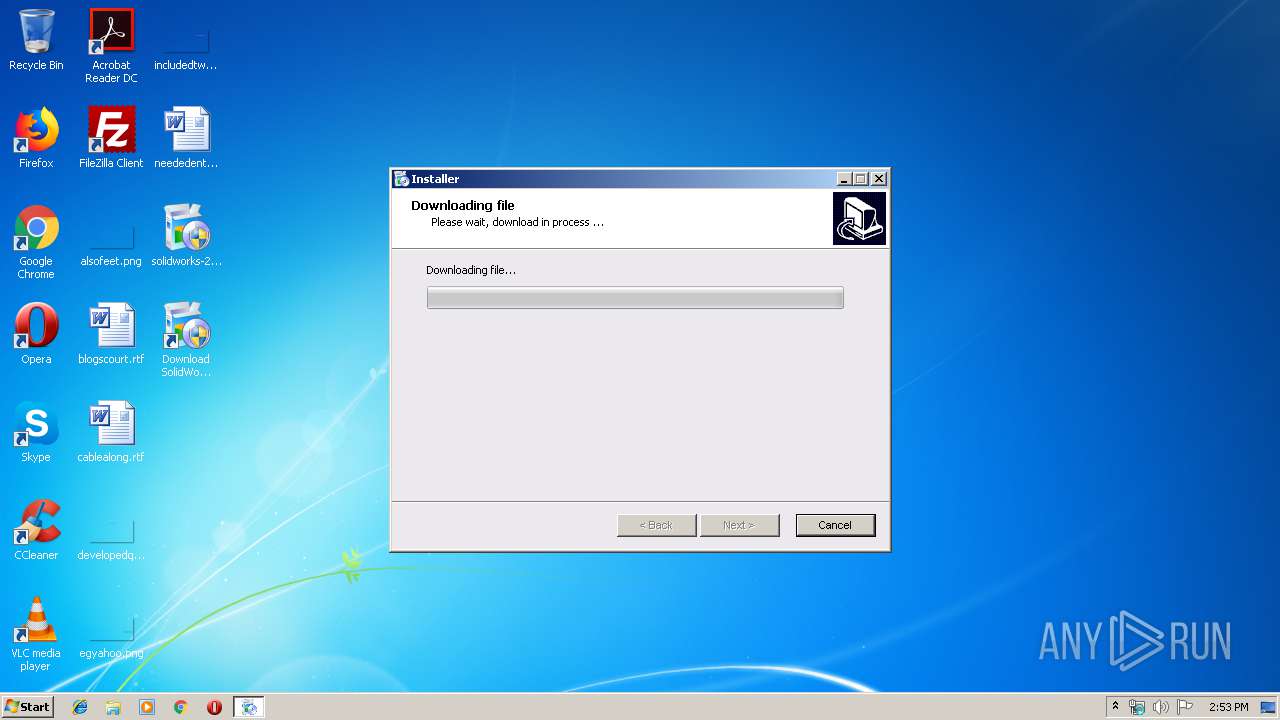
| File name: | solidworks-2017-crack.exe |
| Full analysis: | https://app.any.run/tasks/deaf6b41-29c2-4605-ad85-eb2c1d66869d |
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2019, 14:52:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3621B79EA5BD2AAC45E9233AE48D73B5 |
| SHA1: | CA04848FC86E5C31DF54C5943889C652536A2429 |
| SHA256: | 2EC1A6306115036669608FF5A3E1DE0899DDCFE6C1A8812D2EEB640FB306B3D9 |
| SSDEEP: | 98304:IE1XYwEI+30qExQtdJg16/2rmNmbU7pQF47pQF47pQFF:vcI+3nrQrmNmbSpQF+pQF+pQFF |
MALICIOUS
Connects to CnC server
- solidworks-2017-crack.exe (PID: 3336)
SUSPICIOUS
Low-level read access rights to disk partition
- solidworks-2017-crack.exe (PID: 3336)
Reads Internet Cache Settings
- solidworks-2017-crack.exe (PID: 3336)
Reads internet explorer settings
- solidworks-2017-crack.exe (PID: 3336)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 1484800 |
| InitializedDataSize: | 3397120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16b28c |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductVersion: | 1.0.0.0 |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | Software Installer |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| ProductVersion: | 1.0.0.0 |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | Software Installer |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0016A714 | 0x0016A800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57849 |
DATA | 0x0016C000 | 0x000C8118 | 0x000C8200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.69154 |
BSS | 0x00235000 | 0x00008C65 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0023E000 | 0x00003566 | 0x00003600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.11009 |
.tls | 0x00242000 | 0x00000030 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00243000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.20692 |
.reloc | 0x00244000 | 0x0001DD48 | 0x0001DE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.75795 |
.rsrc | 0x00262000 | 0x00253C29 | 0x00253E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 7.83263 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.39138 | 1145 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.98266 | 704461 | UNKNOWN | UNKNOWN | RT_RCDATA |
3 | 7.98266 | 704461 | UNKNOWN | UNKNOWN | RT_RCDATA |
4 | 2.56318 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
4052 | 2.53098 | 128 | UNKNOWN | UNKNOWN | RT_STRING |
4053 | 3.1697 | 936 | UNKNOWN | UNKNOWN | RT_STRING |
4054 | 3.31387 | 480 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
Netapi32.dll |
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
mpr.dll |
ole32.dll |
oleaut32.dll |
user32.dll |
Total processes
40
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1948 | "C:\Users\admin\Desktop\solidworks-2017-crack.exe" | C:\Users\admin\Desktop\solidworks-2017-crack.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3336 | "C:\Users\admin\Desktop\solidworks-2017-crack.exe" | C:\Users\admin\Desktop\solidworks-2017-crack.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
248
Read events
244
Write events
4
Delete events
0
Modification events
| (PID) Process: | (3336) solidworks-2017-crack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3336) solidworks-2017-crack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3336 | solidworks-2017-crack.exe | C:\Users\Public\Desktop\Download SolidWorks 201...lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
10
DNS requests
6
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3336 | solidworks-2017-crack.exe | POST | 404 | 34.253.187.85:80 | http://ec2-34-253-187-85.eu-west-1.compute.amazonaws.com/api | IE | html | 317 b | shared |
3336 | solidworks-2017-crack.exe | POST | 404 | 34.253.187.85:80 | http://ec2-34-253-187-85.eu-west-1.compute.amazonaws.com/api | IE | html | 317 b | shared |
3336 | solidworks-2017-crack.exe | POST | 404 | 34.253.187.85:80 | http://ec2-34-253-187-85.eu-west-1.compute.amazonaws.com/api | IE | html | 317 b | shared |
3336 | solidworks-2017-crack.exe | GET | — | 104.20.219.106:80 | http://www.FriendlyDuck.com/AF_TA/rel/index.cfm?RST=UNF&TAD=436770&fn=$%7BPRODUCT_NAME%7D&SubID=$%7BENCODED_PIXEL%7D | US | — | — | malicious |
3336 | solidworks-2017-crack.exe | POST | 404 | 34.253.187.85:80 | http://ec2-34-253-187-85.eu-west-1.compute.amazonaws.com/api | IE | html | 317 b | shared |
3336 | solidworks-2017-crack.exe | POST | 404 | 34.253.187.85:80 | http://ec2-34-253-187-85.eu-west-1.compute.amazonaws.com/api | IE | html | 317 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3336 | solidworks-2017-crack.exe | 34.253.187.85:80 | ec2-34-253-187-85.eu-west-1.compute.amazonaws.com | Amazon.com, Inc. | IE | shared |
3336 | solidworks-2017-crack.exe | 104.20.220.106:80 | www.FriendlyDuck.com | Cloudflare Inc | US | shared |
3336 | solidworks-2017-crack.exe | 104.20.219.106:80 | www.FriendlyDuck.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
combinatorial.respection.ru |
| unknown |
ec2-34-253-187-85.eu-west-1.compute.amazonaws.com |
| shared |
dns.msftncsi.com |
| shared |
www.FriendlyDuck.com |
| malicious |
Threats
7 ETPRO signatures available at the full report