| File name: | Hacks_help.bat |
| Full analysis: | https://app.any.run/tasks/7bc8cca7-d09d-43c6-b50d-f660b99f7420 |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2020, 14:16:29 |
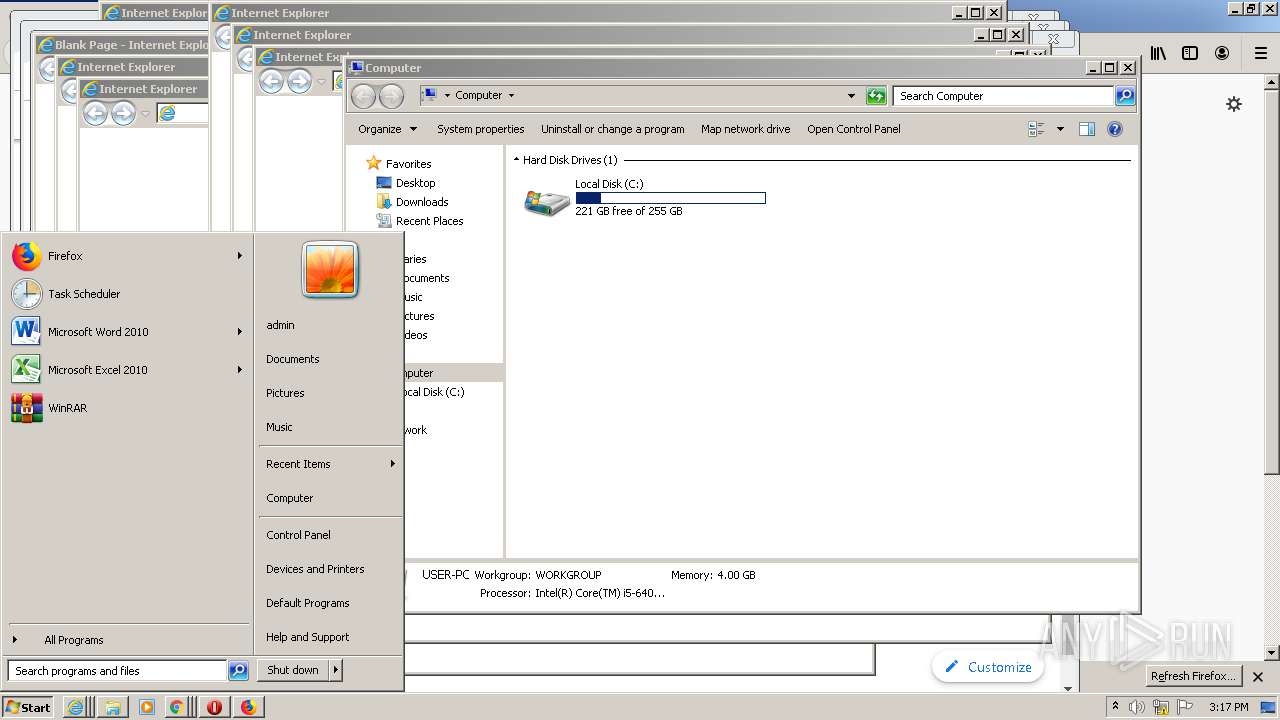
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | 9CA869E87F19C6CEC928EB92CF6A95CE |
| SHA1: | 5FFA994C06AE96EB4AB14F3B9430EBE5E9E4FB71 |
| SHA256: | 2EBED4DA38A8F3151D4583E92972717E58BF7D51F42678304630D7F2A173CAEC |
| SSDEEP: | 12:SKKo2aEKs6+MwyY7AJqbw+5nr5IweFucY7AJqbwRcRwezOrLvwRHQVwQ:5q3k+MXcAJL+5FxecccAJLeyenlBQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 2728)
Modifies files in Chrome extension folder
- chrome.exe (PID: 4020)
INFO
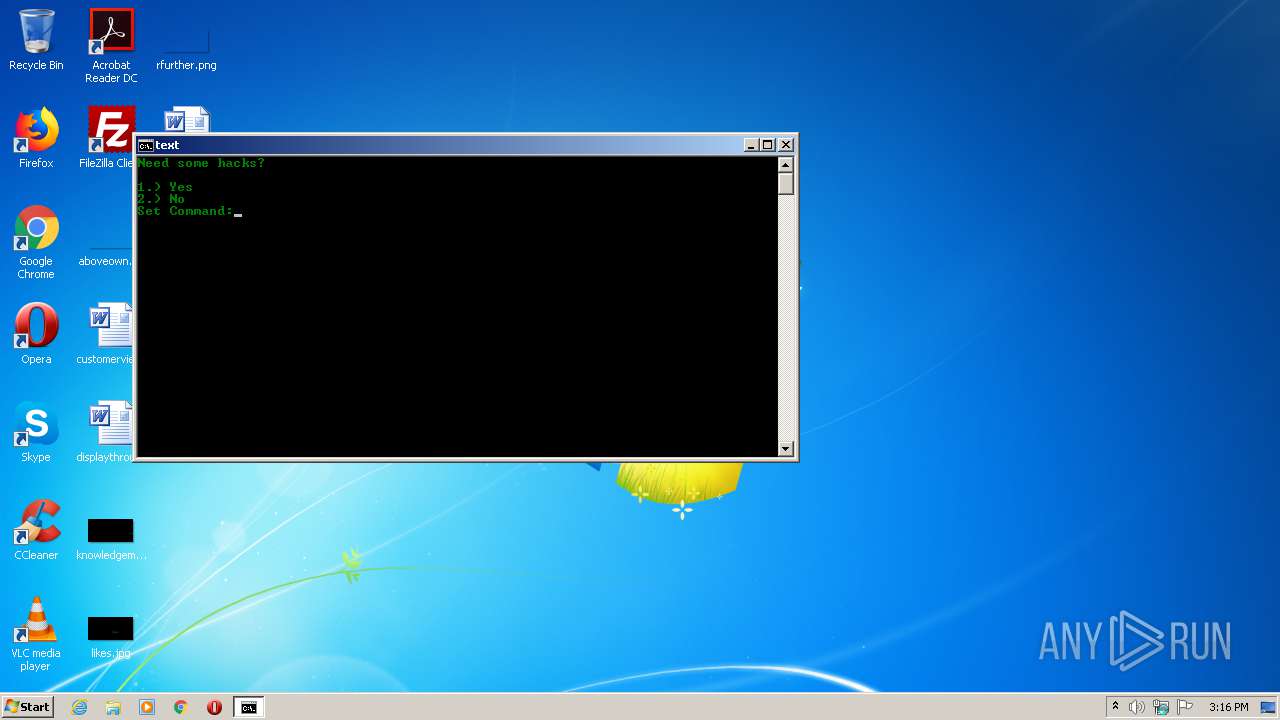
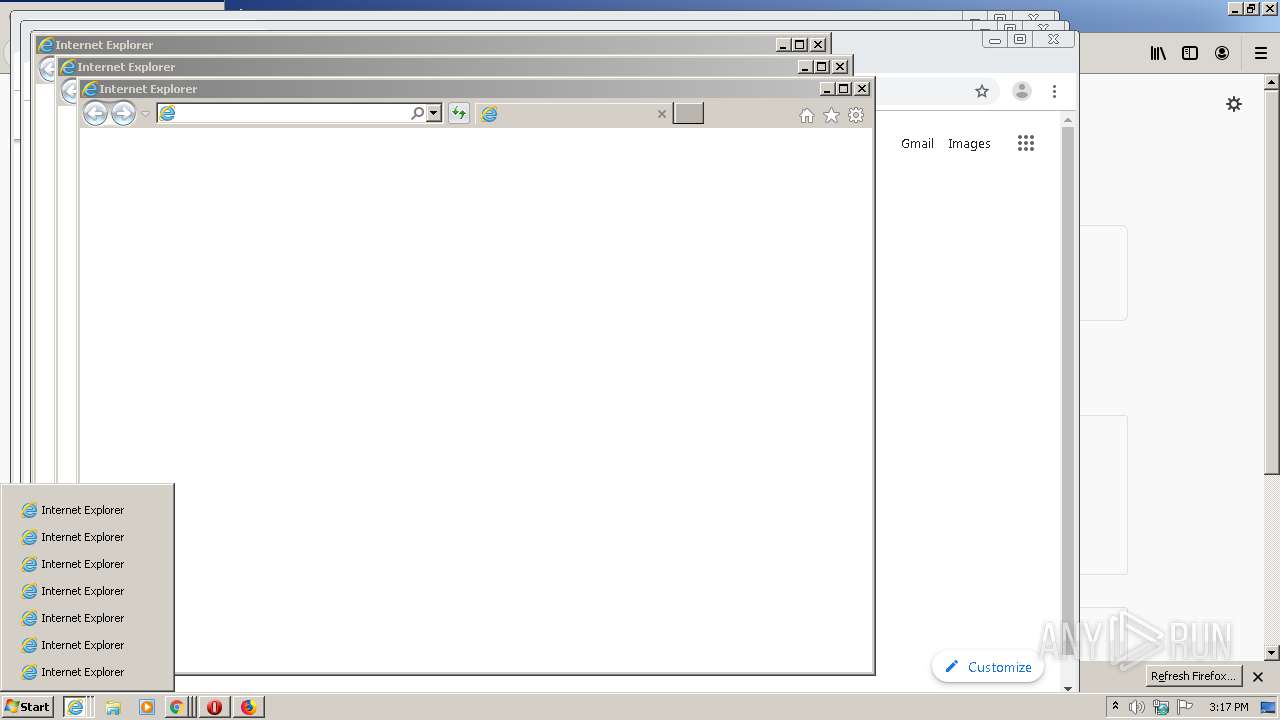
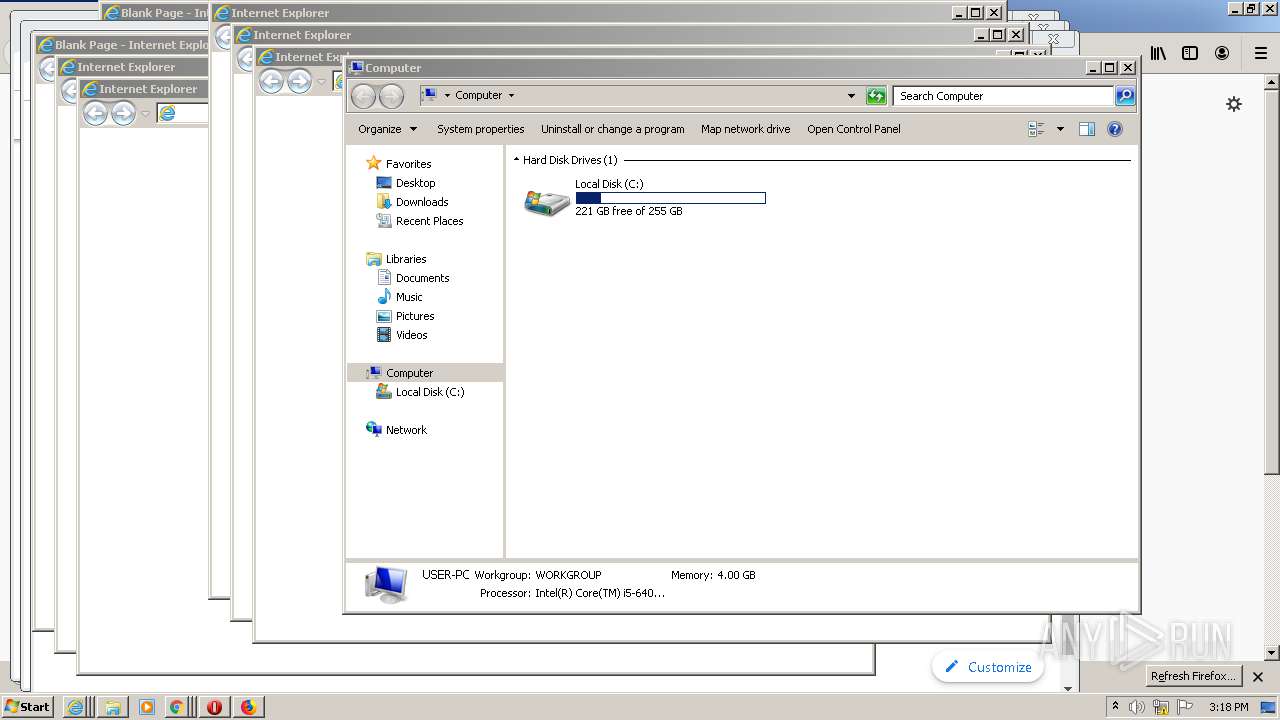
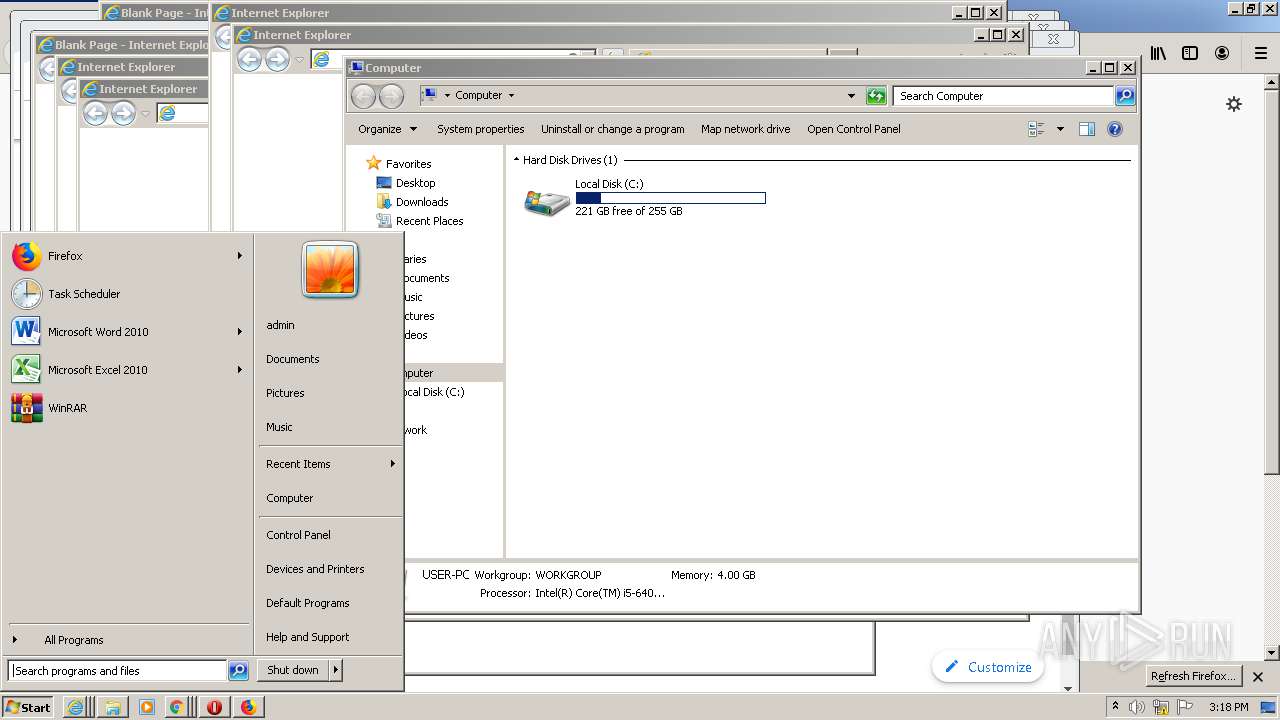
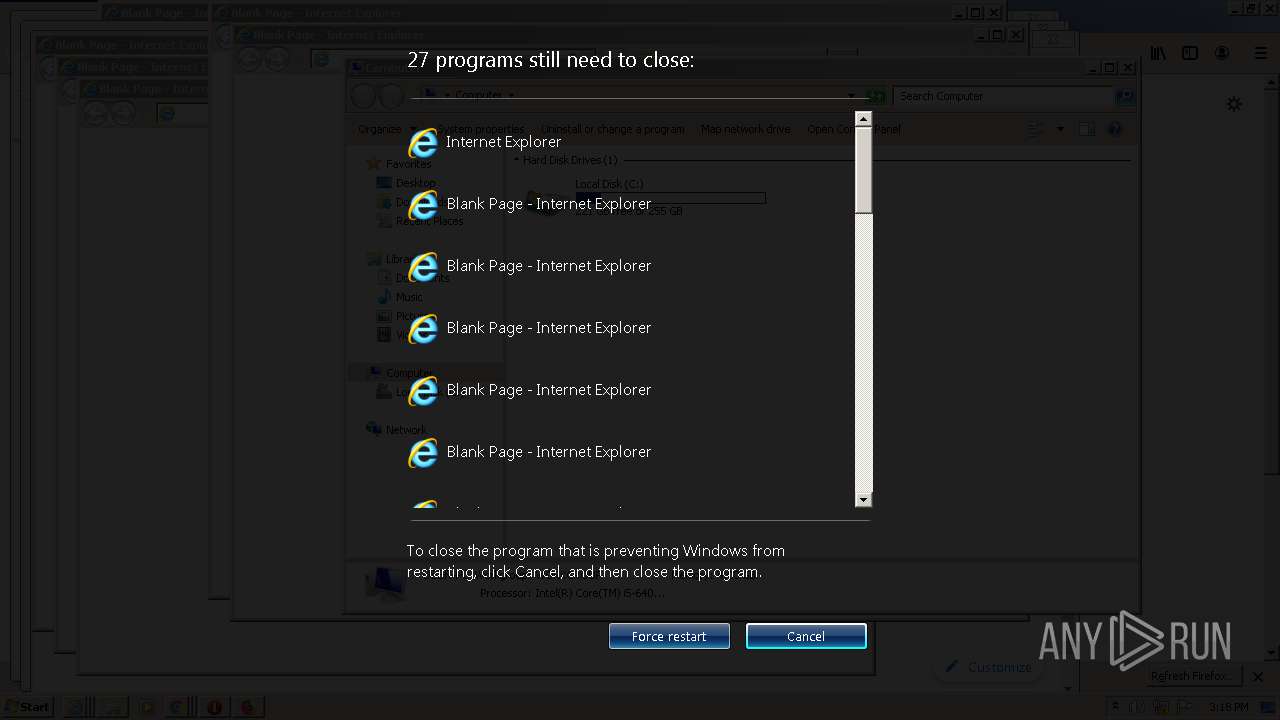
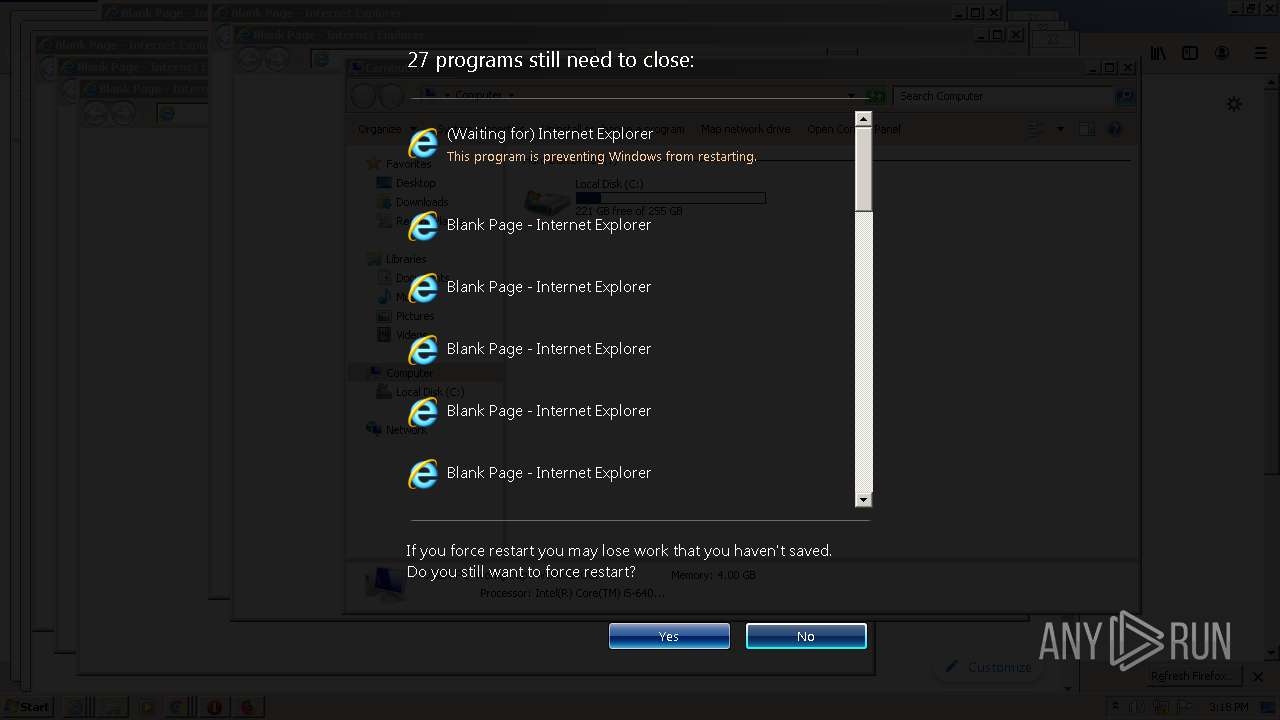
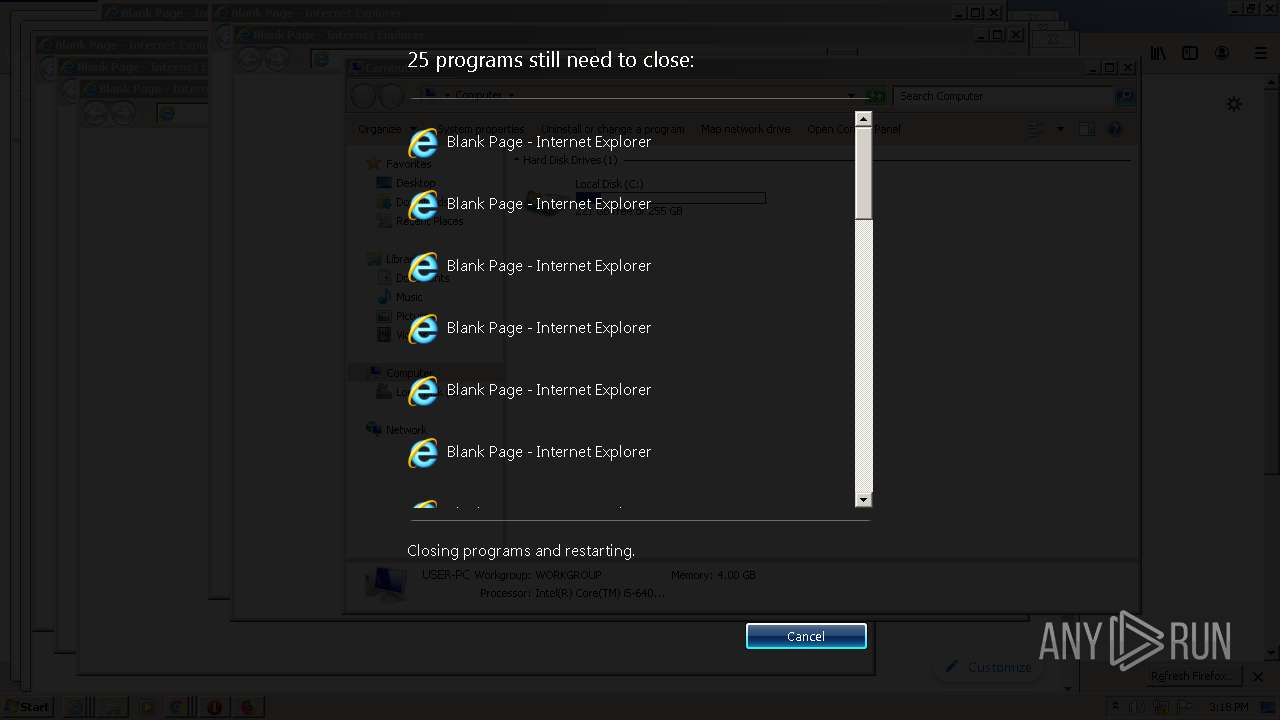
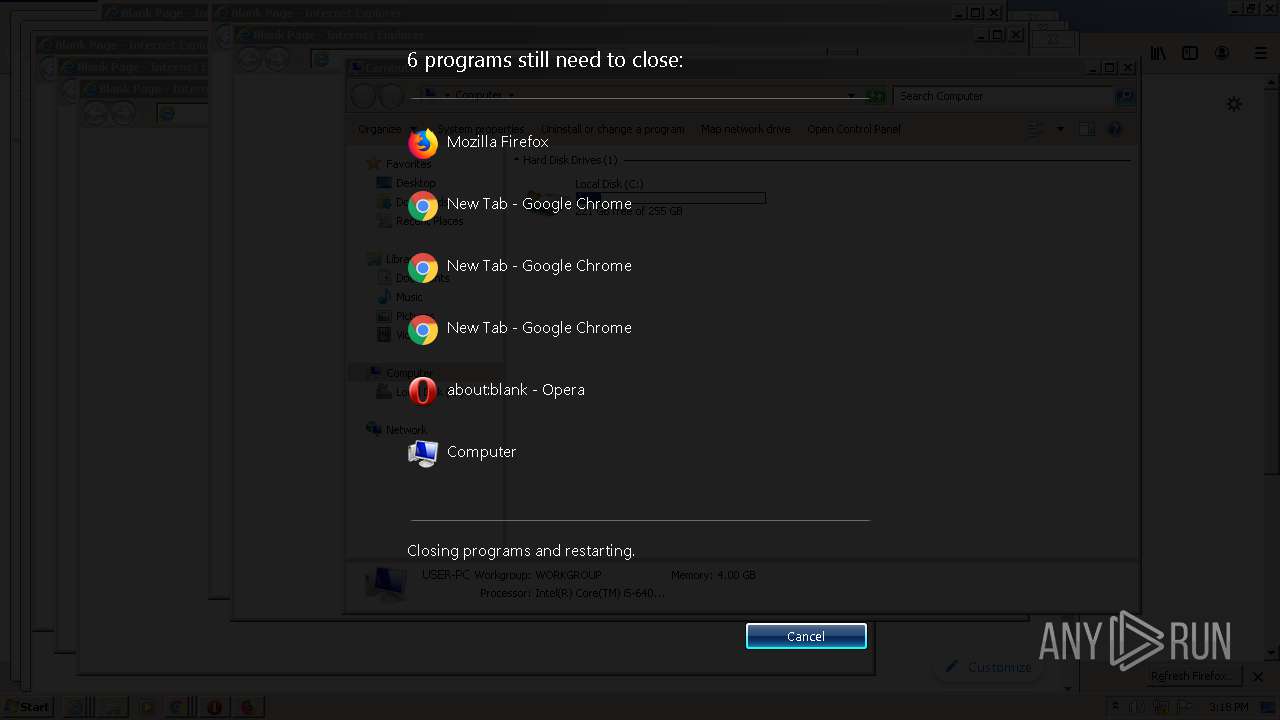
Manual execution by user
- opera.exe (PID: 2388)
- opera.exe (PID: 3716)
- opera.exe (PID: 1252)
- opera.exe (PID: 2812)
- opera.exe (PID: 2112)
- opera.exe (PID: 556)
- opera.exe (PID: 988)
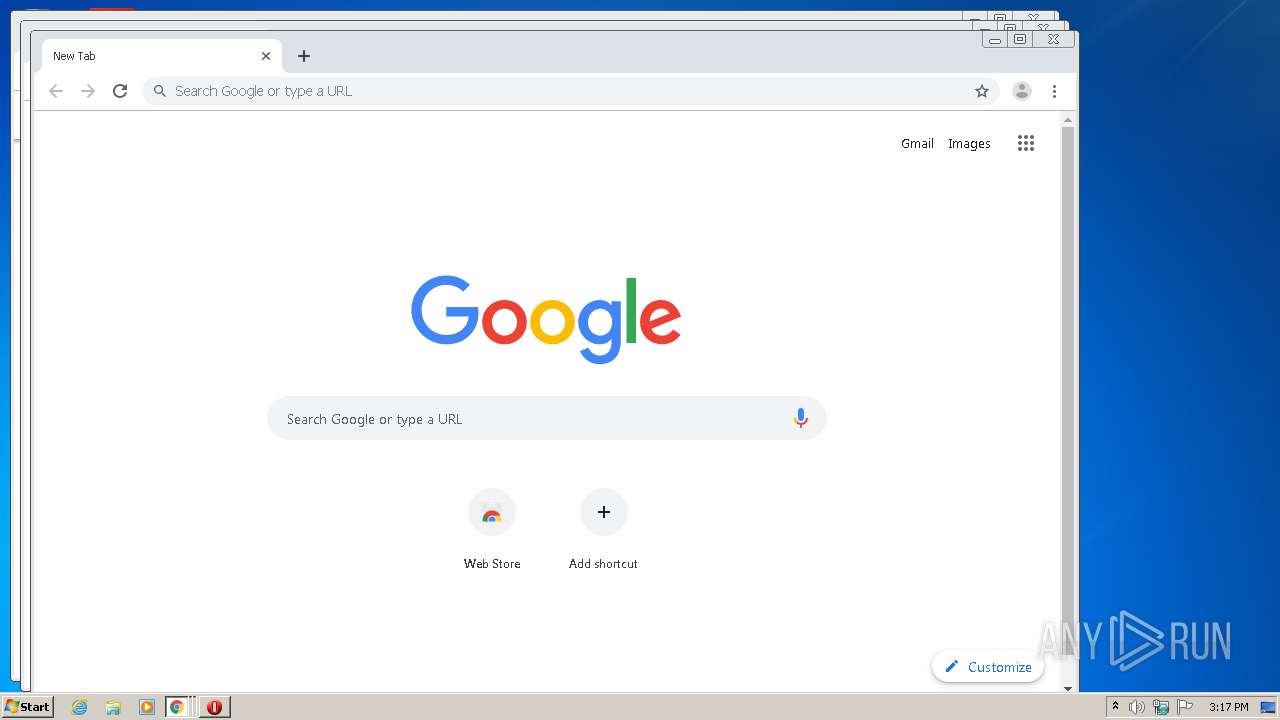
- chrome.exe (PID: 4020)
- chrome.exe (PID: 3396)
- chrome.exe (PID: 2880)
- firefox.exe (PID: 3936)
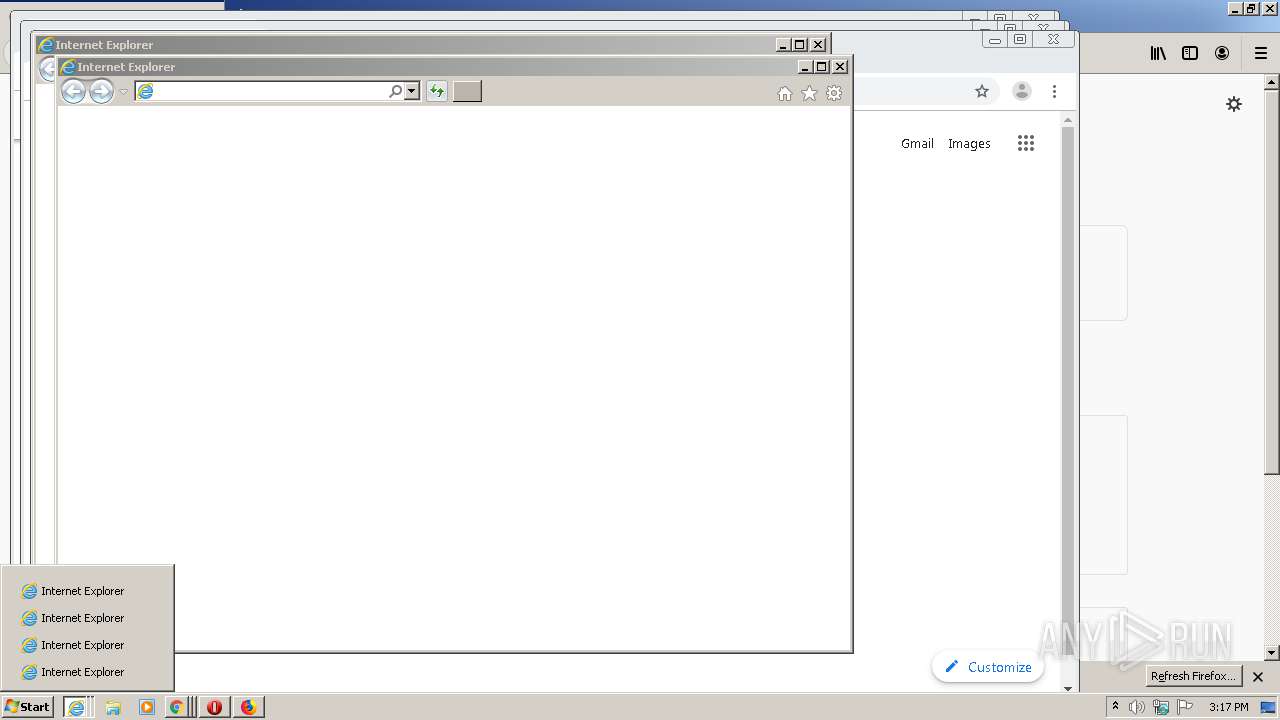
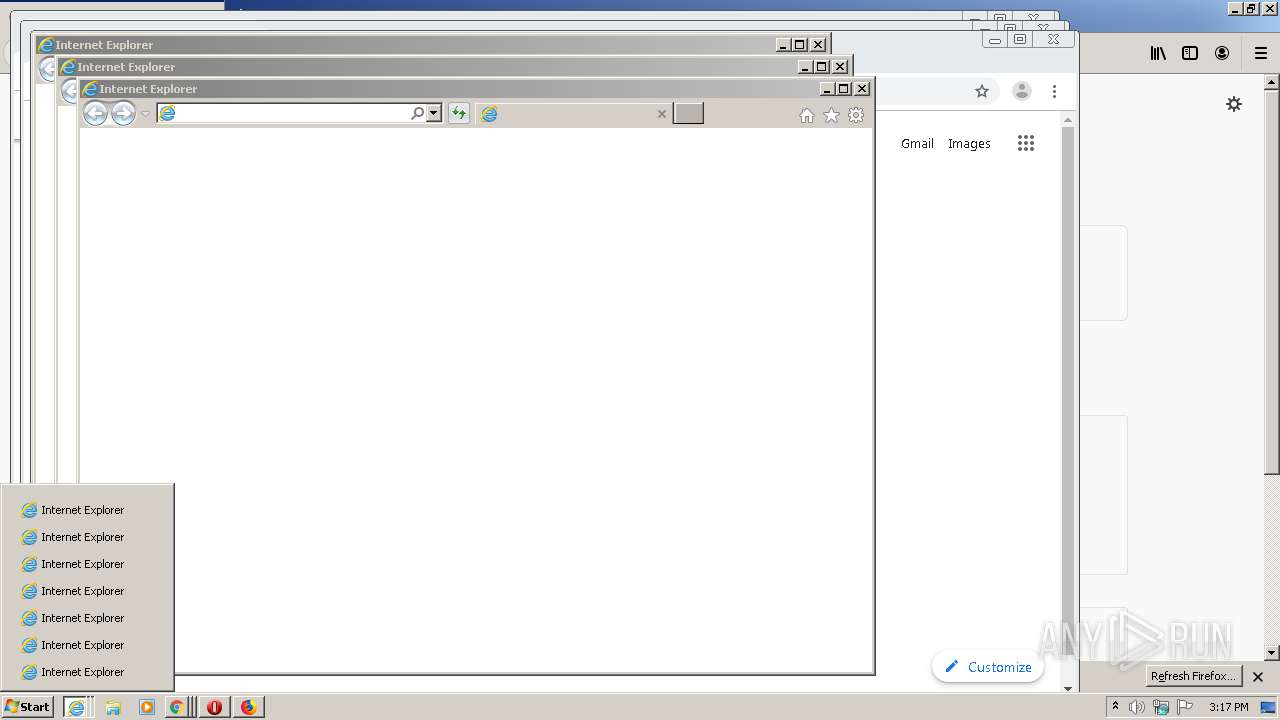
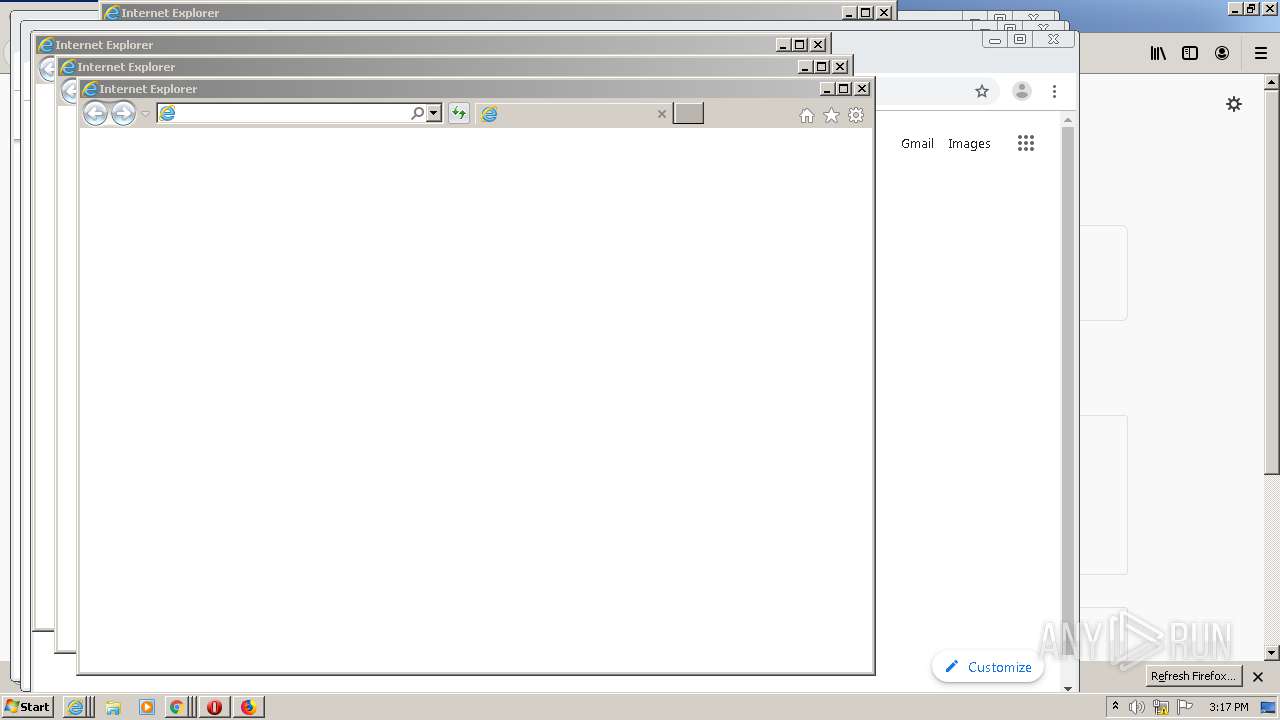
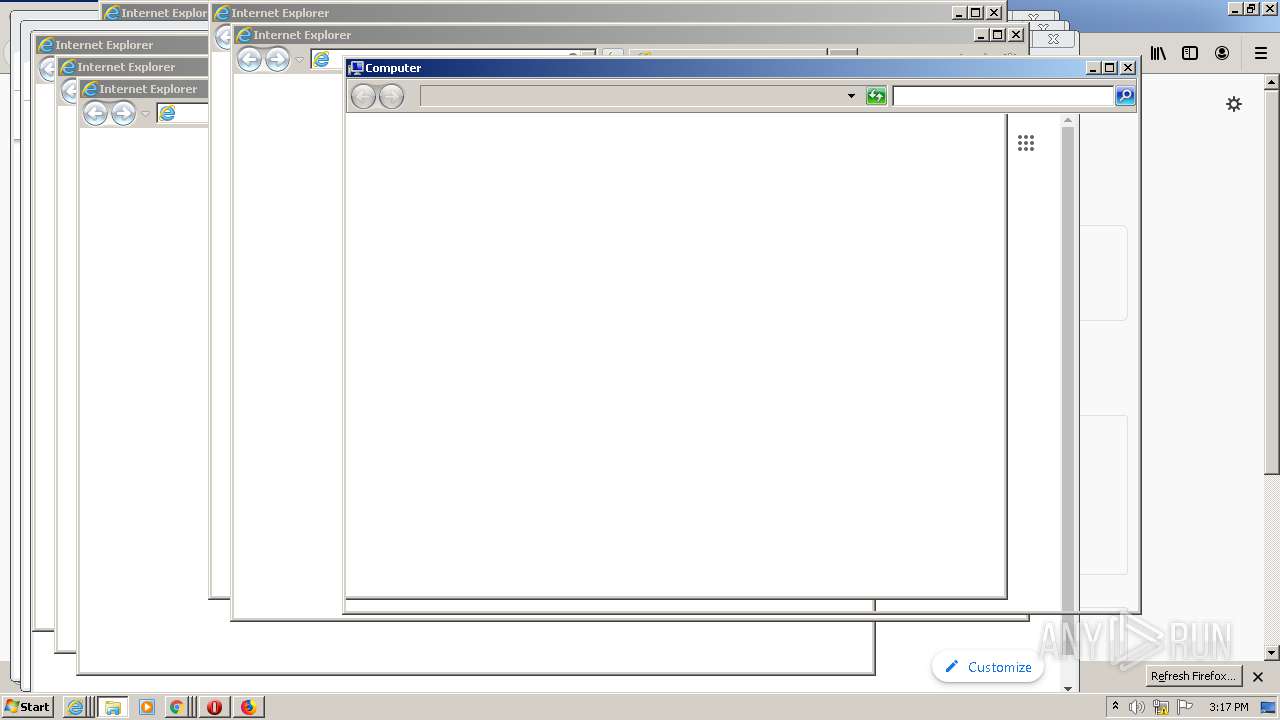
- iexplore.exe (PID: 1752)
- iexplore.exe (PID: 444)
- iexplore.exe (PID: 1624)
- iexplore.exe (PID: 2536)
- iexplore.exe (PID: 4064)
- iexplore.exe (PID: 3972)
- iexplore.exe (PID: 2636)
- iexplore.exe (PID: 1824)
- iexplore.exe (PID: 2452)
- iexplore.exe (PID: 2336)
- iexplore.exe (PID: 5488)
- iexplore.exe (PID: 5072)
- iexplore.exe (PID: 4836)
- iexplore.exe (PID: 4520)
- iexplore.exe (PID: 5736)
- iexplore.exe (PID: 6040)
- iexplore.exe (PID: 4144)
- iexplore.exe (PID: 4932)
- iexplore.exe (PID: 4444)
- iexplore.exe (PID: 5748)
- iexplore.exe (PID: 4340)
- iexplore.exe (PID: 4912)
Application launched itself
- chrome.exe (PID: 4020)
- chrome.exe (PID: 3396)
- chrome.exe (PID: 2880)
- firefox.exe (PID: 3936)
- firefox.exe (PID: 2728)
- iexplore.exe (PID: 1752)
- iexplore.exe (PID: 444)
- iexplore.exe (PID: 1624)
- iexplore.exe (PID: 2536)
- iexplore.exe (PID: 2636)
- iexplore.exe (PID: 1824)
- iexplore.exe (PID: 3972)
- iexplore.exe (PID: 4064)
- iexplore.exe (PID: 2452)
- iexplore.exe (PID: 2336)
- iexplore.exe (PID: 5488)
- iexplore.exe (PID: 5072)
- iexplore.exe (PID: 4836)
- iexplore.exe (PID: 4520)
- iexplore.exe (PID: 5736)
- iexplore.exe (PID: 4144)
- iexplore.exe (PID: 5748)
- iexplore.exe (PID: 4932)
- iexplore.exe (PID: 4444)
- iexplore.exe (PID: 4912)
- iexplore.exe (PID: 6040)
- iexplore.exe (PID: 4340)
Reads the hosts file
- chrome.exe (PID: 2532)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 3396)
Creates files in the user directory
- opera.exe (PID: 3716)
- firefox.exe (PID: 2728)
Reads settings of System Certificates
- chrome.exe (PID: 2532)
- iexplore.exe (PID: 4064)
Reads Internet Cache Settings
- firefox.exe (PID: 2728)
- iexplore.exe (PID: 444)
- iexplore.exe (PID: 1752)
- iexplore.exe (PID: 2536)
- iexplore.exe (PID: 4064)
- iexplore.exe (PID: 3972)
- iexplore.exe (PID: 2452)
- iexplore.exe (PID: 2336)
- iexplore.exe (PID: 5488)
- iexplore.exe (PID: 1624)
- iexplore.exe (PID: 2636)
- iexplore.exe (PID: 1824)
- iexplore.exe (PID: 5072)
- iexplore.exe (PID: 4836)
- iexplore.exe (PID: 4520)
- iexplore.exe (PID: 3984)
- iexplore.exe (PID: 4132)
- iexplore.exe (PID: 6132)
- iexplore.exe (PID: 4772)
- iexplore.exe (PID: 4124)
- iexplore.exe (PID: 5028)
- iexplore.exe (PID: 6040)
- iexplore.exe (PID: 5608)
- iexplore.exe (PID: 4144)
- iexplore.exe (PID: 4932)
- iexplore.exe (PID: 4444)
- iexplore.exe (PID: 5748)
- iexplore.exe (PID: 5736)
- iexplore.exe (PID: 4912)
- iexplore.exe (PID: 4340)
- iexplore.exe (PID: 4980)
- iexplore.exe (PID: 5796)
- iexplore.exe (PID: 5076)
- iexplore.exe (PID: 1616)
- iexplore.exe (PID: 5336)
- iexplore.exe (PID: 5616)
- iexplore.exe (PID: 4288)
- iexplore.exe (PID: 1488)
- iexplore.exe (PID: 4812)
- iexplore.exe (PID: 3572)
- iexplore.exe (PID: 3520)
- iexplore.exe (PID: 3576)
- iexplore.exe (PID: 5456)
- iexplore.exe (PID: 5364)
Reads CPU info
- firefox.exe (PID: 2728)
Changes internet zones settings
- iexplore.exe (PID: 1624)
- iexplore.exe (PID: 444)
- iexplore.exe (PID: 2536)
- iexplore.exe (PID: 1752)
- iexplore.exe (PID: 1824)
- iexplore.exe (PID: 2636)
- iexplore.exe (PID: 4064)
- iexplore.exe (PID: 3972)
- iexplore.exe (PID: 2452)
- iexplore.exe (PID: 2336)
- iexplore.exe (PID: 5488)
- iexplore.exe (PID: 5072)
- iexplore.exe (PID: 4836)
- iexplore.exe (PID: 6040)
- iexplore.exe (PID: 4520)
- iexplore.exe (PID: 5736)
- iexplore.exe (PID: 4144)
- iexplore.exe (PID: 4444)
- iexplore.exe (PID: 4912)
- iexplore.exe (PID: 5748)
- iexplore.exe (PID: 4932)
- iexplore.exe (PID: 4340)
Reads internet explorer settings
- iexplore.exe (PID: 4132)
- iexplore.exe (PID: 6132)
- iexplore.exe (PID: 5616)
- iexplore.exe (PID: 4980)
- iexplore.exe (PID: 4772)
- iexplore.exe (PID: 5336)
- iexplore.exe (PID: 4124)
- iexplore.exe (PID: 5608)
- iexplore.exe (PID: 3520)
- iexplore.exe (PID: 3576)
- iexplore.exe (PID: 1488)
- iexplore.exe (PID: 5076)
- iexplore.exe (PID: 4288)
- iexplore.exe (PID: 5796)
- iexplore.exe (PID: 3572)
- iexplore.exe (PID: 5456)
- iexplore.exe (PID: 1616)
- iexplore.exe (PID: 4812)
- iexplore.exe (PID: 3984)
- iexplore.exe (PID: 5028)
Adds / modifies Windows certificates
- iexplore.exe (PID: 4064)
Changes settings of System certificates
- iexplore.exe (PID: 4064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
135
Monitored processes
97
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | cmd /c ""C:\Users\admin\AppData\Local\Temp\Hacks_help.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 255 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,6061960415994512232,17955704457270822803,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3833338458916248017 --mojo-platform-channel-handle=2920 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 444 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1073807364 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f21a9d0,0x6f21a9e0,0x6f21a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 556 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | — | explorer.exe | |||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 700 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2728.20.1979724796\1004886783" -childID 3 -isForBrowser -prefsHandle 3776 -prefMapHandle 3780 -prefsLen 7355 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2728 "\\.\pipe\gecko-crash-server-pipe.2728" 3788 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,6061960415994512232,17955704457270822803,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16474483305590617122 --mojo-platform-channel-handle=4288 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 988 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | — | explorer.exe | |||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,6061960415994512232,17955704457270822803,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13339534237783059851 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | — | explorer.exe | |||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
Total events
6 956
Read events
5 053
Write events
1 614
Delete events
289
Modification events
| (PID) Process: | (3716) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (3716) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3396) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3396) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3396) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3396) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (4020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (4020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
Executable files
0
Suspicious files
169
Text files
298
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3716 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprEF15.tmp | — | |
MD5:— | SHA256:— | |||
| 3716 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprEF64.tmp | — | |
MD5:— | SHA256:— | |||
| 4020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F0B1B62-FB4.pma | — | |
MD5:— | SHA256:— | |||
| 3716 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 3716 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:— | SHA256:— | |||
| 4020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3716 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
| 4020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF10f34b.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
44
DNS requests
81
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2532 | chrome.exe | GET | 200 | 173.194.5.170:80 | http://r4---sn-aigl6n7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=185.217.117.39&mm=28&mn=sn-aigl6n7s&ms=nvh&mt=1594563315&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 823 Kb | whitelisted |
2532 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
3716 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 564 b | whitelisted |
2532 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
2728 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2728 | firefox.exe | POST | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
2728 | firefox.exe | GET | 200 | 2.16.177.51:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
444 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2728 | firefox.exe | GET | 200 | 2.16.177.51:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
2728 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3716 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
— | — | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2532 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2532 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2532 | chrome.exe | 172.217.23.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2532 | chrome.exe | 172.217.23.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2532 | chrome.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2532 | chrome.exe | 216.58.207.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2532 | chrome.exe | 172.217.16.142:443 | apis.google.com | Google Inc. | US | whitelisted |
2532 | chrome.exe | 172.217.16.206:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |