| File name: | Aphrodite Zero Delay.exe |
| Full analysis: | https://app.any.run/tasks/206f4575-88da-49dd-8fcd-0a818396b08e |
| Verdict: | Malicious activity |
| Analysis date: | October 28, 2024, 13:52:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 0E7A8F915DD3B94573C512E3EE486591 |
| SHA1: | B5A1DD70882A3D2B30972D3067E461A4181CD02A |
| SHA256: | 2EAF3572B01CDB6D33DB468DBDE56B64167FDBC3A0D5ACF4BAFBAE1025C1ED84 |
| SSDEEP: | 24576:5cPN2S4kj2Y6xaOiuHxWjXIPKPfBLhjW2qr7ZSu6:5coSj2Y6xaOiuHxWjXIPKP5tjW207ZSB |
MALICIOUS
JEEFO has been detected
- Aphrodite Zero Delay.exe (PID: 5068)
SUSPICIOUS
Starts itself from another location
- icsys.icn.exe (PID: 6244)
- explorer.exe (PID: 700)
- svchost.exe (PID: 6348)
- spoolsv.exe (PID: 4380)
- Aphrodite Zero Delay.exe (PID: 7744)
- icsys.icn.exe (PID: 7908)
- Aphrodite Zero Delay.exe (PID: 5068)
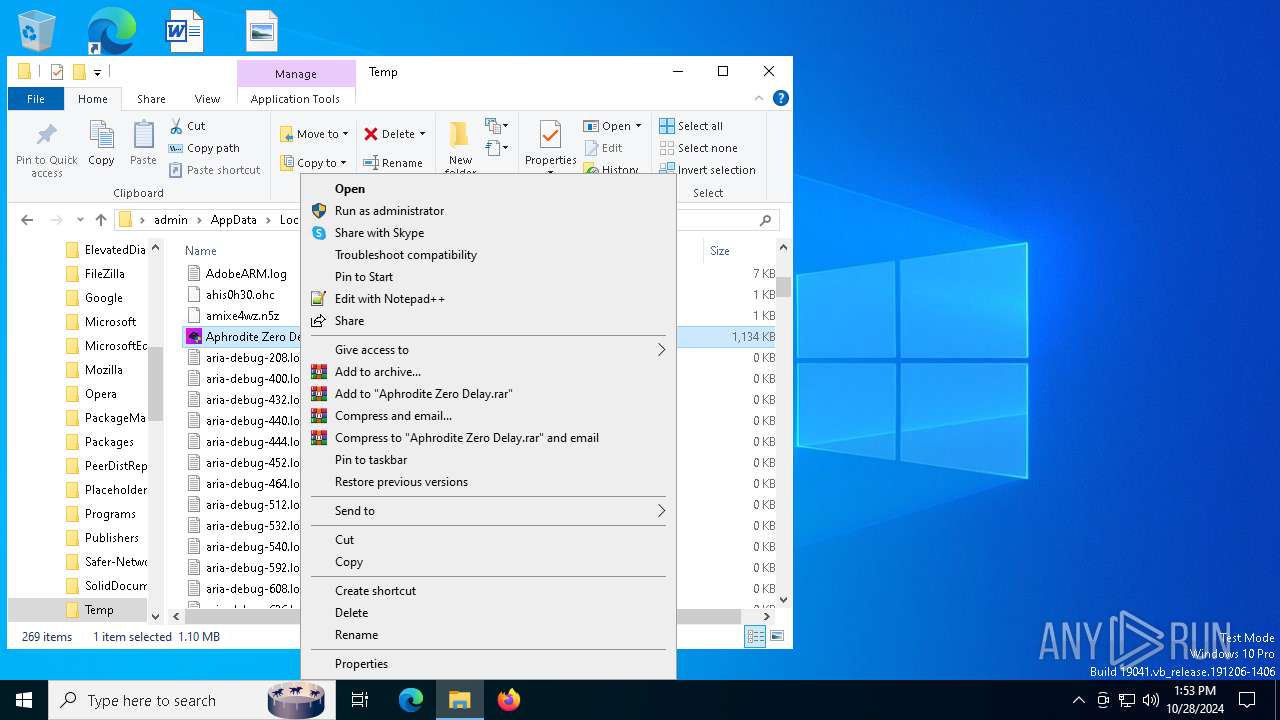
Starts application with an unusual extension
- Aphrodite Zero Delay.exe (PID: 5068)
- Aphrodite Zero Delay.exe (PID: 7744)
Executable content was dropped or overwritten
- spoolsv.exe (PID: 4380)
- explorer.exe (PID: 700)
- Aphrodite Zero Delay.exe (PID: 7744)
- icsys.icn.exe (PID: 6244)
- Aphrodite Zero Delay.exe (PID: 5068)
Executes application which crashes
- aphrodite zero delay.exe (PID: 7768)
INFO
Checks supported languages
- Aphrodite Zero Delay.exe (PID: 5068)
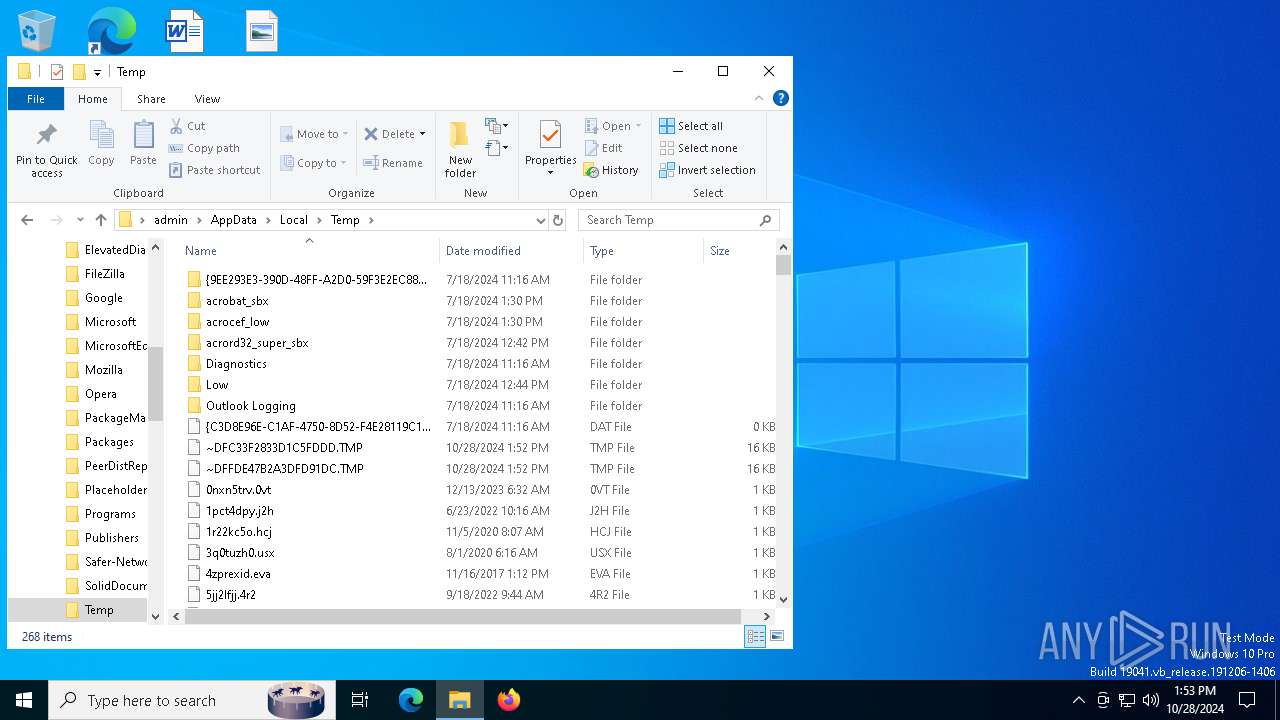
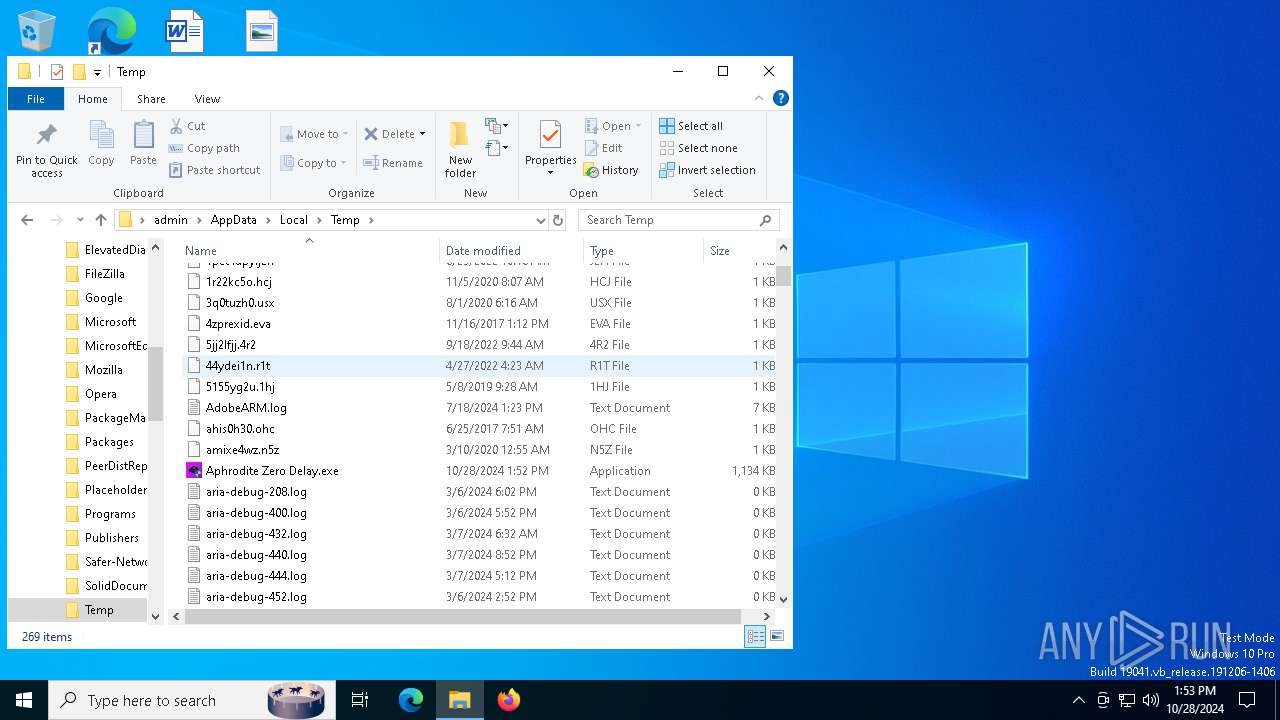
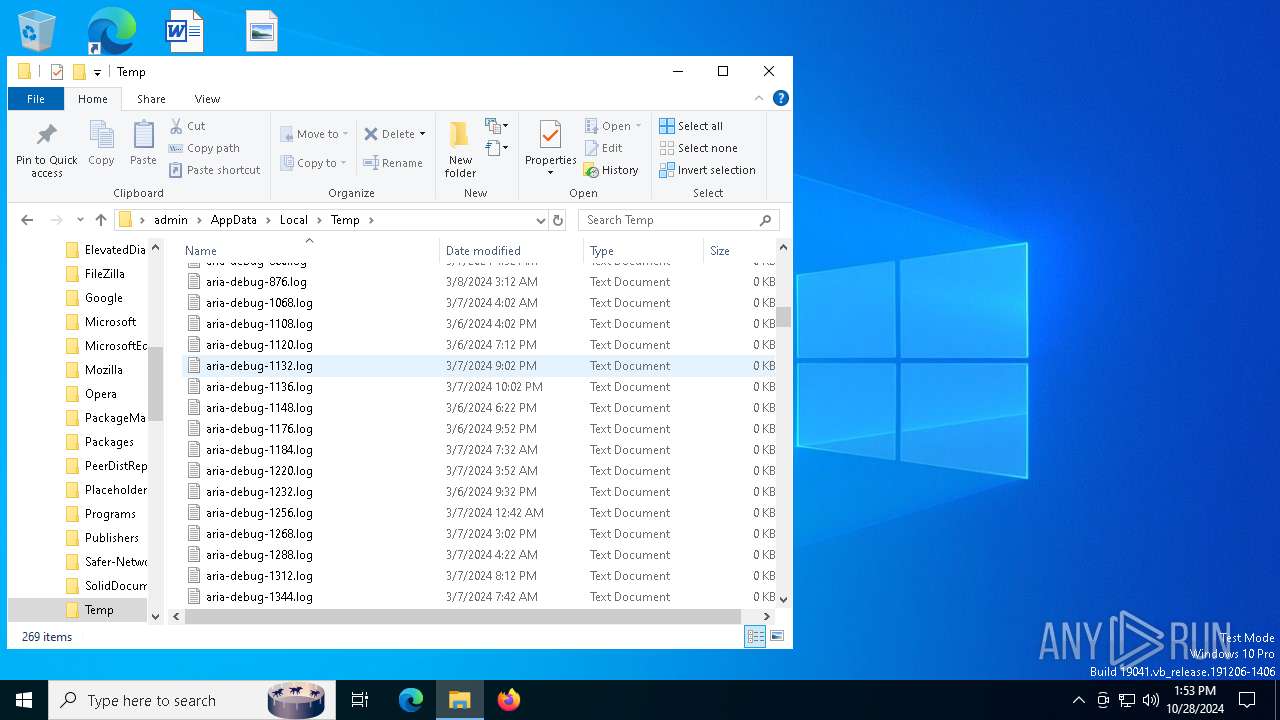
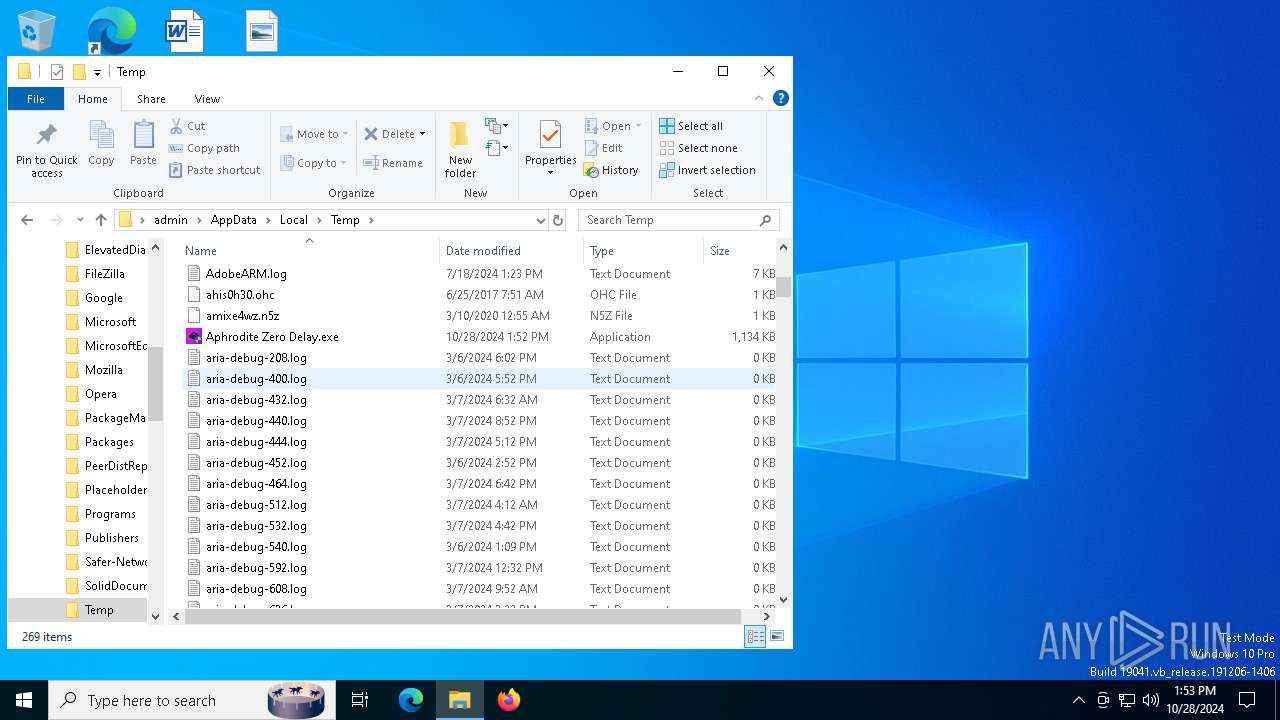
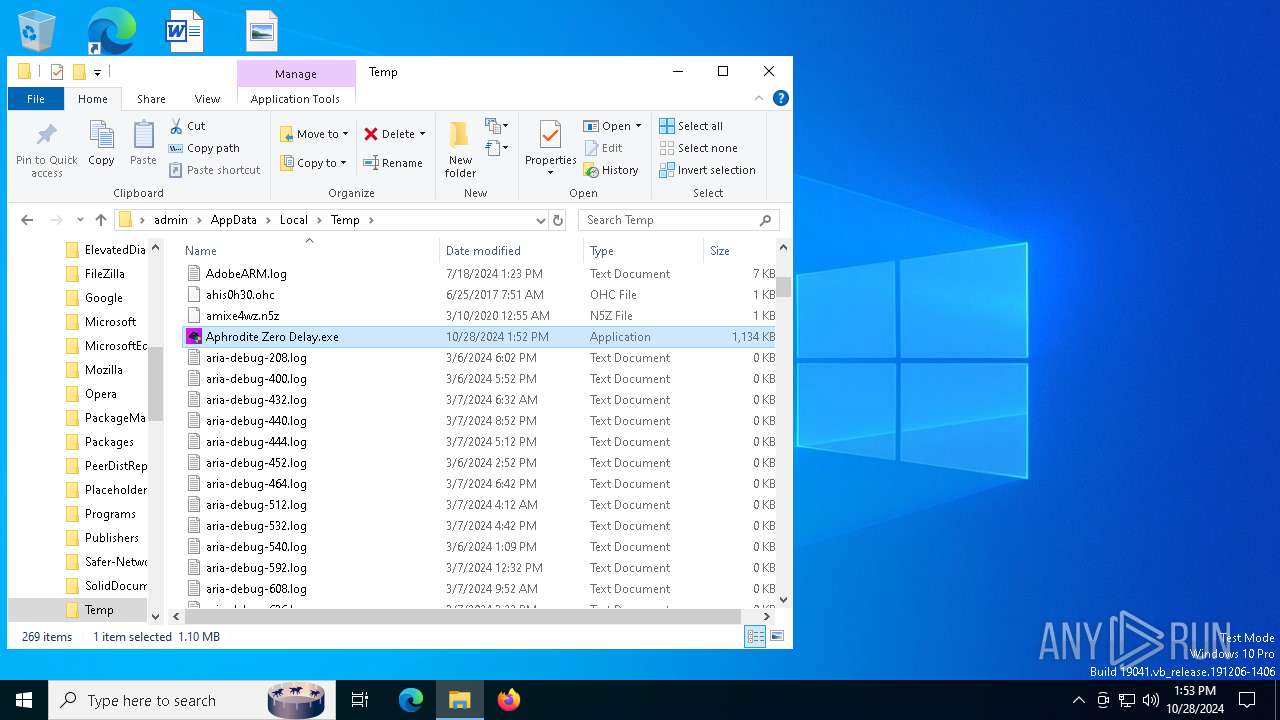
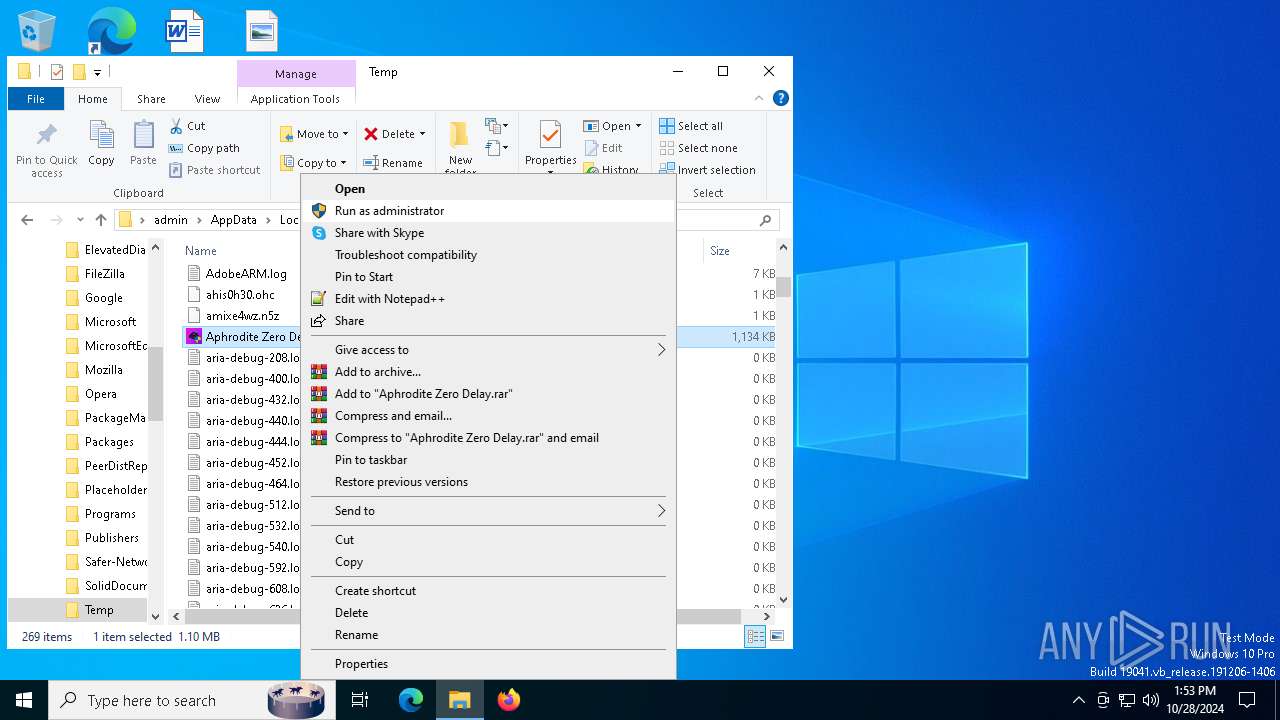
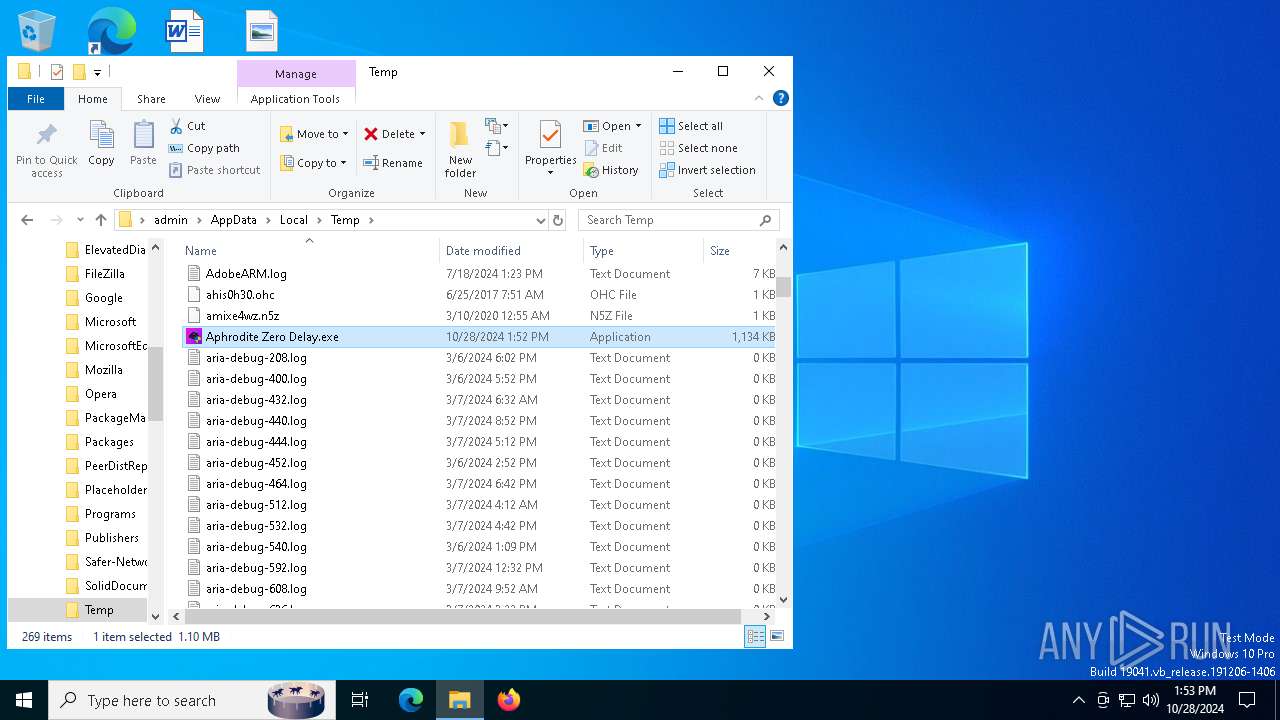
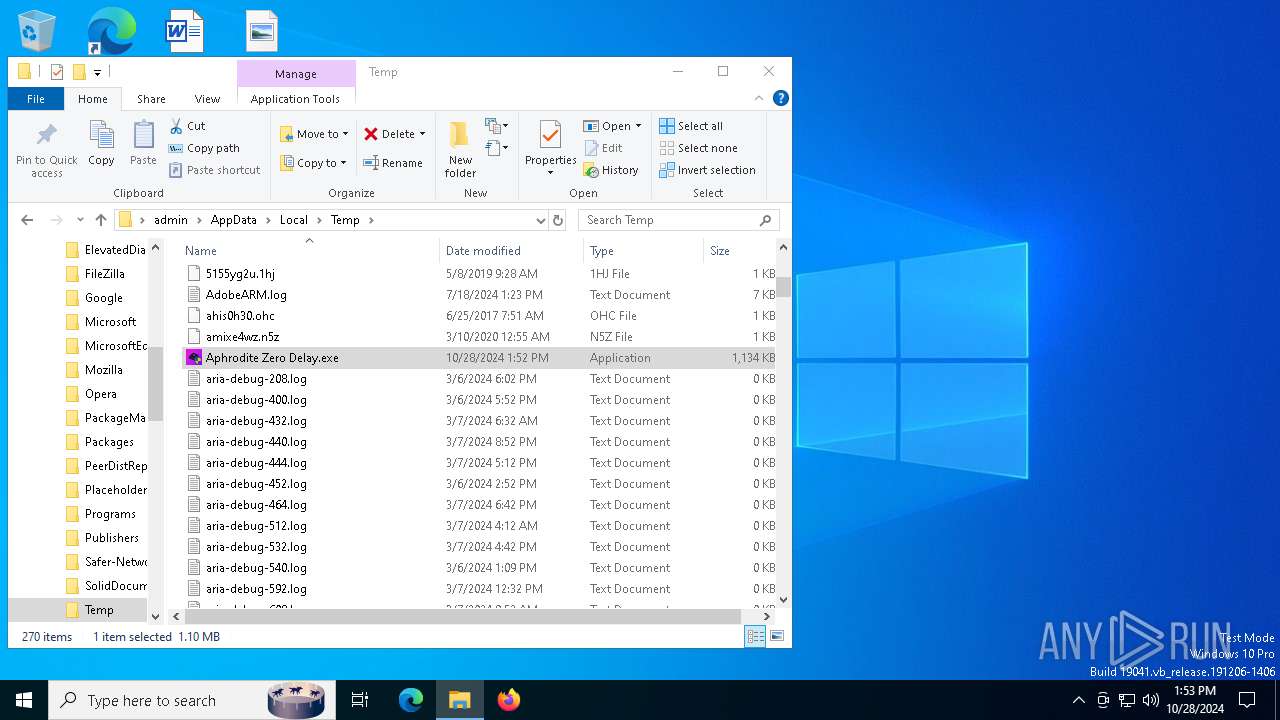
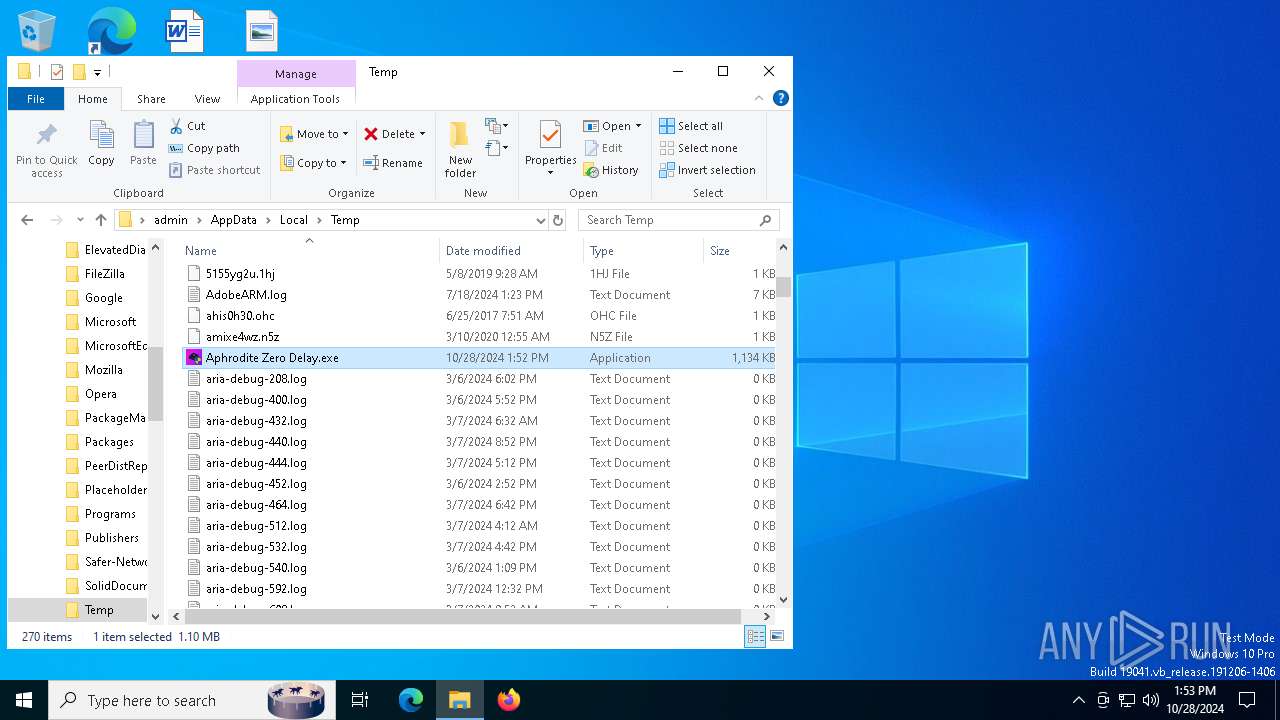
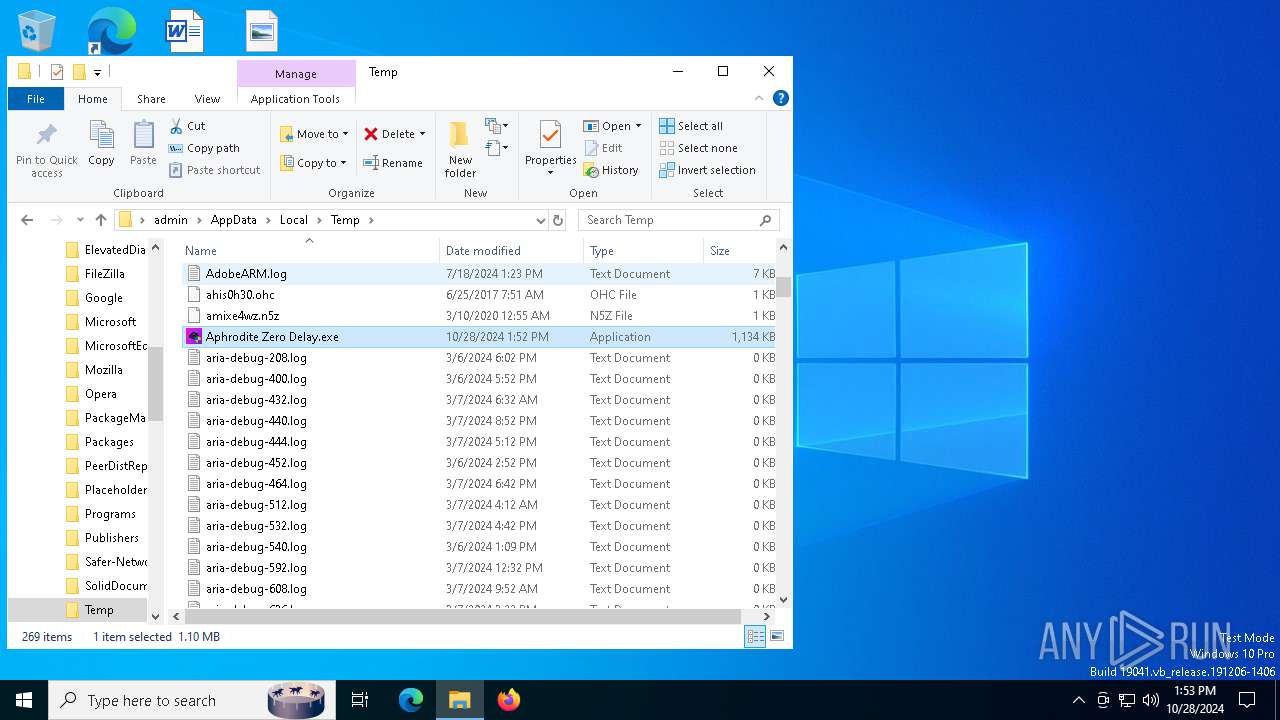
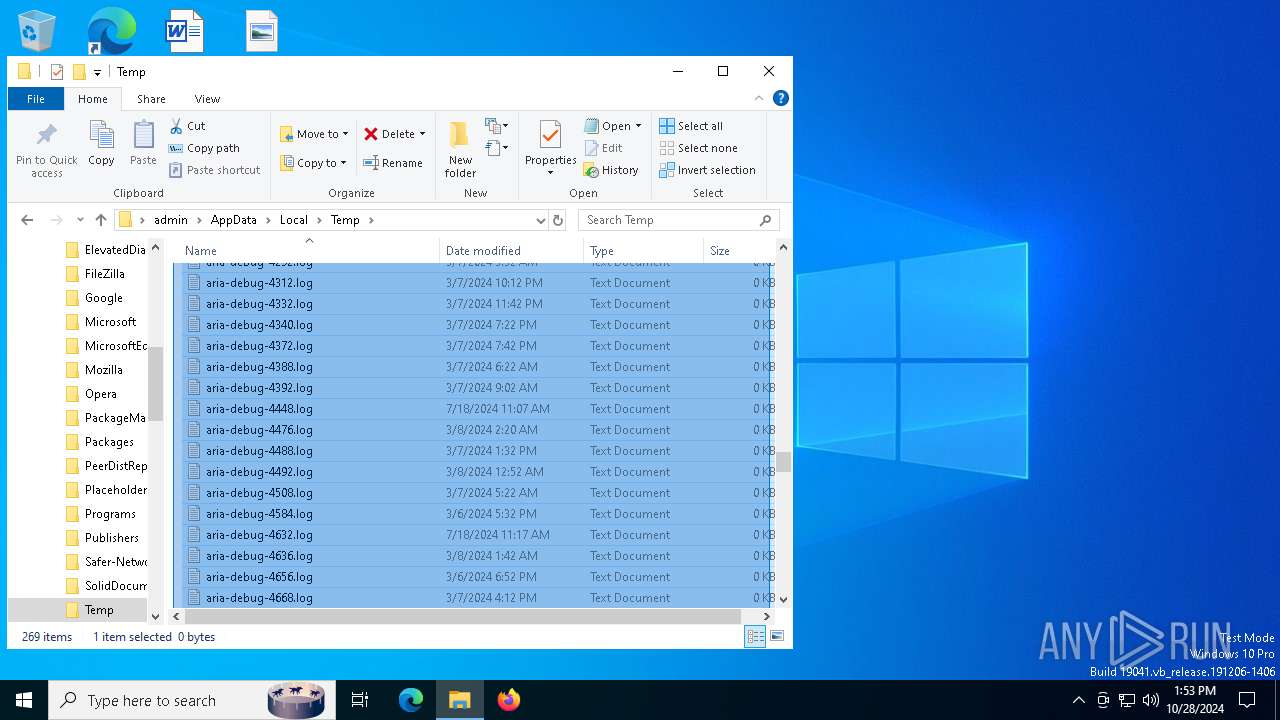
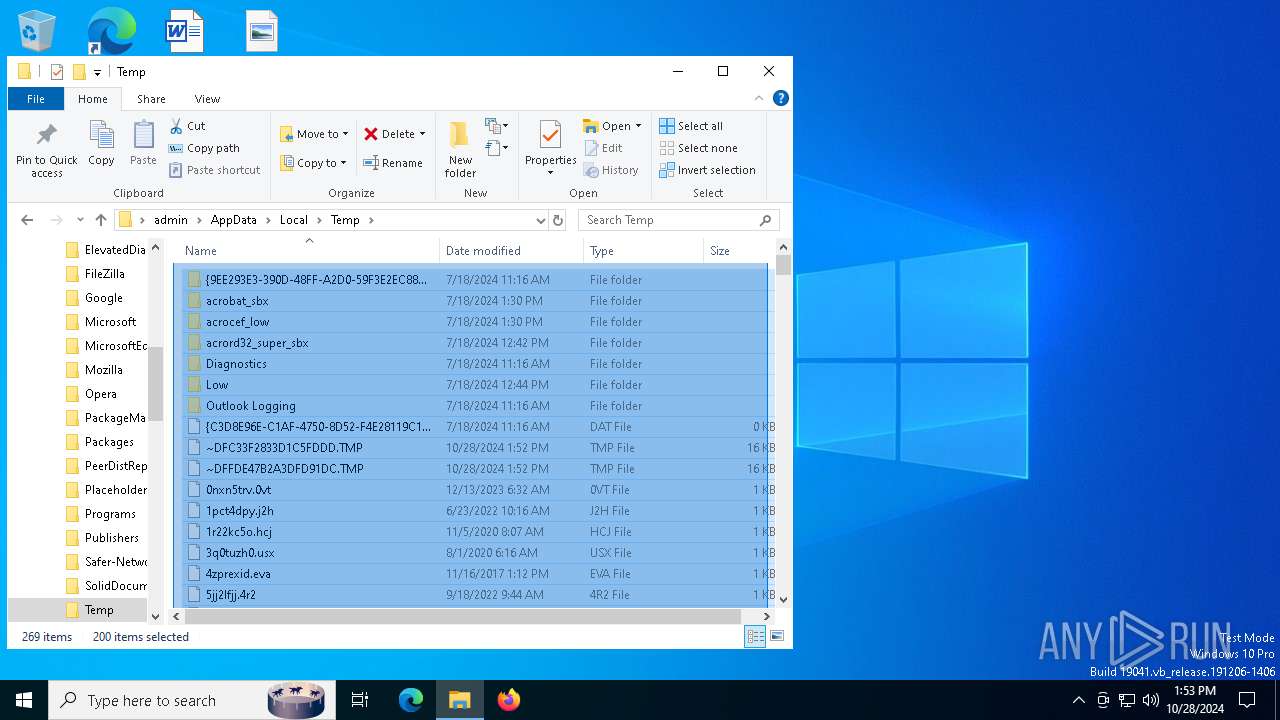
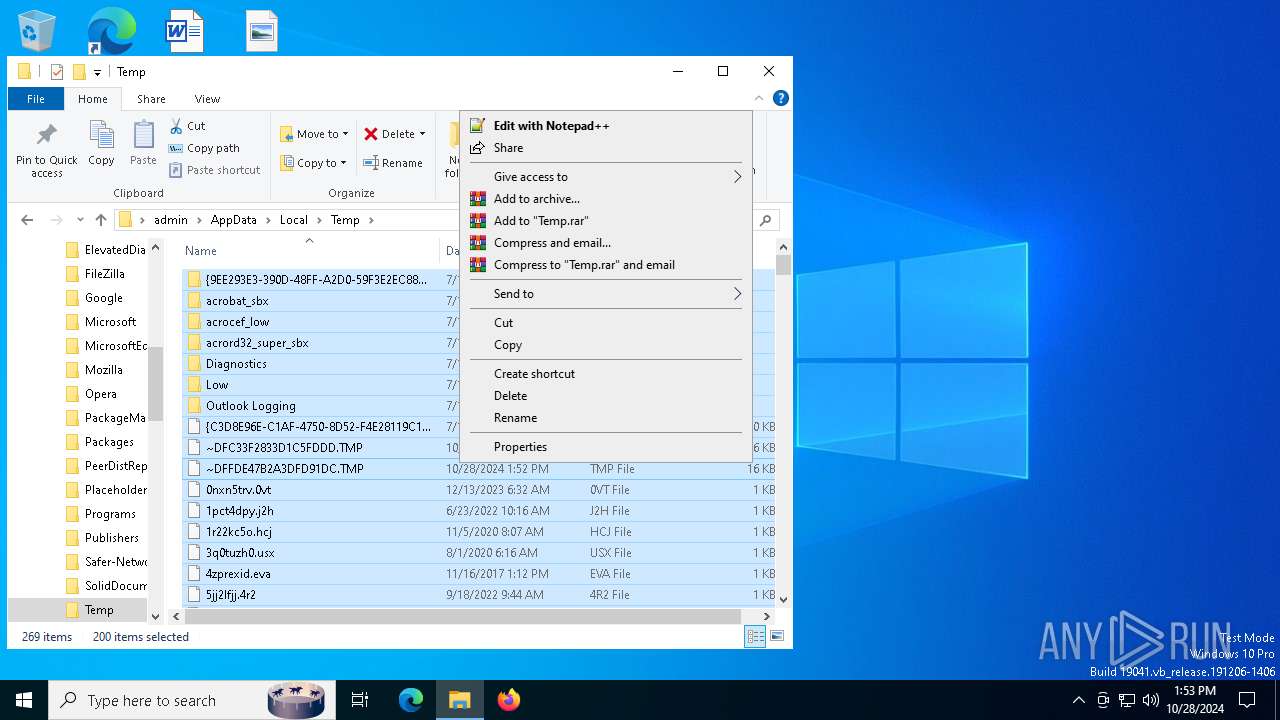
Create files in a temporary directory
- Aphrodite Zero Delay.exe (PID: 5068)
Manual execution by a user
- Aphrodite Zero Delay.exe (PID: 7744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:04:01 07:08:22+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 106496 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x290c |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | Project1 |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | TJprojMain |
| OriginalFileName: | TJprojMain.exe |
Total processes
146
Monitored processes
14
Malicious processes
1
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 700 | c:\windows\resources\themes\explorer.exe | C:\Windows\Resources\Themes\explorer.exe | icsys.icn.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 1.00 Modules
| |||||||||||||||
| 920 | "c:\users\admin\appdata\local\temp\aphrodite zero delay.exe " | C:\Users\admin\AppData\Local\Temp\aphrodite zero delay.exe | — | Aphrodite Zero Delay.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Aphrodite Zero Delay Exit code: 3762504530 Version: 1.0.0.0 | |||||||||||||||
| 4380 | c:\windows\resources\spoolsv.exe SE | C:\Windows\Resources\spoolsv.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 5068 | "C:\Users\admin\AppData\Local\Temp\Aphrodite Zero Delay.exe" | C:\Users\admin\AppData\Local\Temp\Aphrodite Zero Delay.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 5564 | c:\windows\resources\spoolsv.exe PR | C:\Windows\Resources\spoolsv.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 5584 | "C:\Users\admin\AppData\Local\Temp\Aphrodite Zero Delay.exe" | C:\Users\admin\AppData\Local\Temp\Aphrodite Zero Delay.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.00 Modules
| |||||||||||||||
| 6244 | C:\Windows\Resources\Themes\icsys.icn.exe | C:\Windows\Resources\Themes\icsys.icn.exe | Aphrodite Zero Delay.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 6348 | c:\windows\resources\svchost.exe | C:\Windows\Resources\svchost.exe | — | spoolsv.exe | |||||||||||
User: admin Integrity Level: HIGH Version: 1.00 Modules
| |||||||||||||||
| 7604 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7744 | "C:\Users\admin\AppData\Local\Temp\Aphrodite Zero Delay.exe" | C:\Users\admin\AppData\Local\Temp\Aphrodite Zero Delay.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
3 585
Read events
3 569
Write events
11
Delete events
5
Modification events
| (PID) Process: | (5068) Aphrodite Zero Delay.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (6244) icsys.icn.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (700) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\resources\themes\explorer.exe RO | |||
| (PID) Process: | (700) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\resources\svchost.exe RO | |||
| (PID) Process: | (700) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
| (PID) Process: | (700) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Svchost |
Value: | |||
| (PID) Process: | (6348) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\resources\themes\explorer.exe RO | |||
| (PID) Process: | (6348) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\resources\svchost.exe RO | |||
| (PID) Process: | (6348) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
| (PID) Process: | (6348) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Svchost |
Value: | |||
Executable files
7
Suspicious files
8
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7824 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_aphrodite zero d_11df40e126968c4448dbe1559cda837333a8c9a_7c40bb63_ad0bcab0-329b-4b25-ad31-44121b34177f\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7824 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\aphrodite zero delay.exe .7768.dmp | — | |
MD5:— | SHA256:— | |||
| 5068 | Aphrodite Zero Delay.exe | C:\Users\admin\AppData\Local\Temp\aphrodite zero delay.exe | executable | |
MD5:A566B2A0C1003DB37EE472E10640B0AC | SHA256:58D9368D16F115DD9CE8DB052AE34CB09E2AAD0FA09430BF3A865BFCB302F66C | |||
| 5068 | Aphrodite Zero Delay.exe | C:\Windows\Resources\Themes\icsys.icn.exe | executable | |
MD5:FECAE4D4C2E0693866BAA0909D3C8CC3 | SHA256:03B39F54F8AB10553FE52D562D8CDDB2240477FA9C278342C22546A1E5259978 | |||
| 7744 | Aphrodite Zero Delay.exe | C:\Windows\Resources\Themes\icsys.icn.exe | executable | |
MD5:FECAE4D4C2E0693866BAA0909D3C8CC3 | SHA256:03B39F54F8AB10553FE52D562D8CDDB2240477FA9C278342C22546A1E5259978 | |||
| 700 | explorer.exe | C:\Windows\Resources\spoolsv.exe | executable | |
MD5:3A706BC5B61A3DDE5C9DE1B656B23F28 | SHA256:6B6685FB49F1FEBD9A41E8EAF9B61E462691BD69A2AC5B5C377F8AF62BC77813 | |||
| 4380 | spoolsv.exe | C:\Windows\Resources\svchost.exe | executable | |
MD5:639AEC28154FC09D090672284FC7BC61 | SHA256:81FB2C75A1DF1EEDBB75952331C0C85E7ABC84DE62120D402D2F531E7D382980 | |||
| 6244 | icsys.icn.exe | C:\Users\admin\AppData\Local\Temp\~DFBD8C839D1E7B9D3D.TMP | binary | |
MD5:88A02AE249136754EFF96B6A579B9A28 | SHA256:05813CA59EA58D0240975548B8E2957C3F42DB9E698AD52549296F93CD0077EE | |||
| 5564 | spoolsv.exe | C:\Users\admin\AppData\Local\Temp\~DF2A096C54DDA0519A.TMP | binary | |
MD5:4EFB9F80DF53B58F527FC70D54F6ABCC | SHA256:10DFA7DE58055B526E57A77DCDC52A2DA308B9ED08056E9AB7A69DA9F66A7C0F | |||
| 6244 | icsys.icn.exe | C:\Windows\Resources\Themes\explorer.exe | executable | |
MD5:E957129DE17CDDDB991961E453B4F012 | SHA256:1E3548BF12BEDCB8AD88E60DCA3C0008BF3443D3E90FE76E82A54CA620FBAD37 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
39
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
632 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5276 | WerFault.exe | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7348 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6000 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5276 | WerFault.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7348 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2464 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4360 | SearchApp.exe | 2.23.209.160:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |