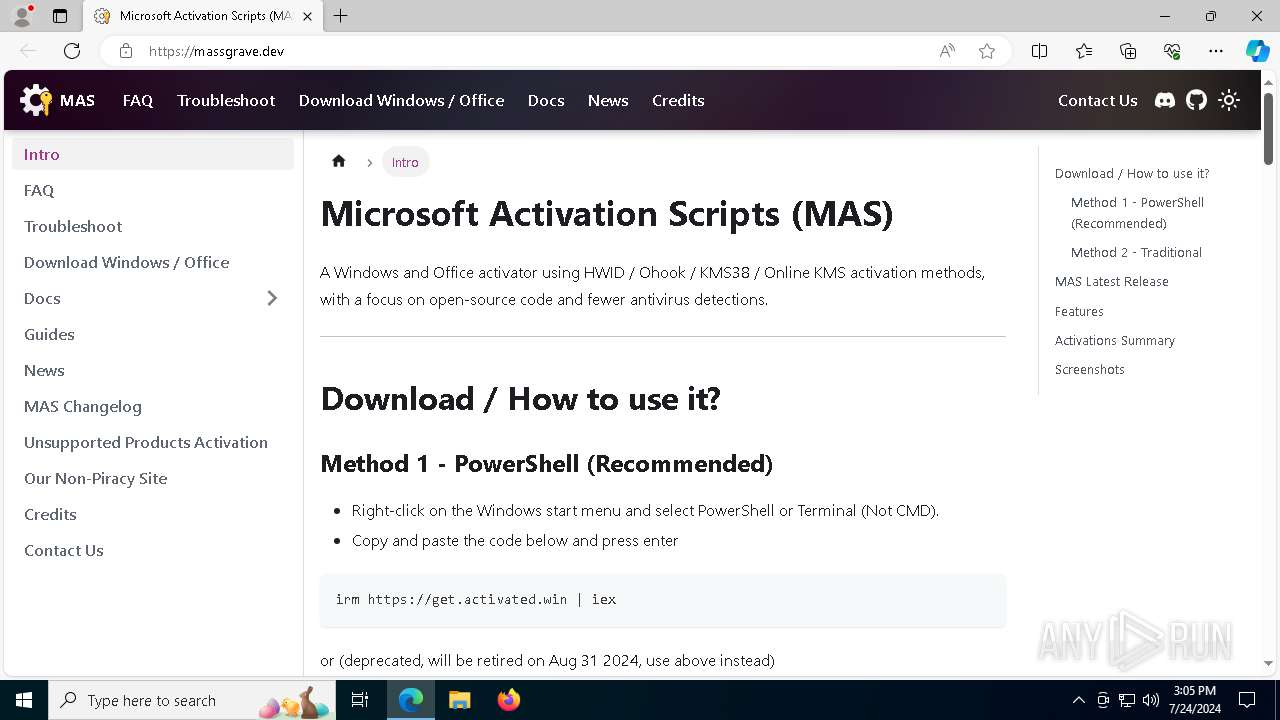
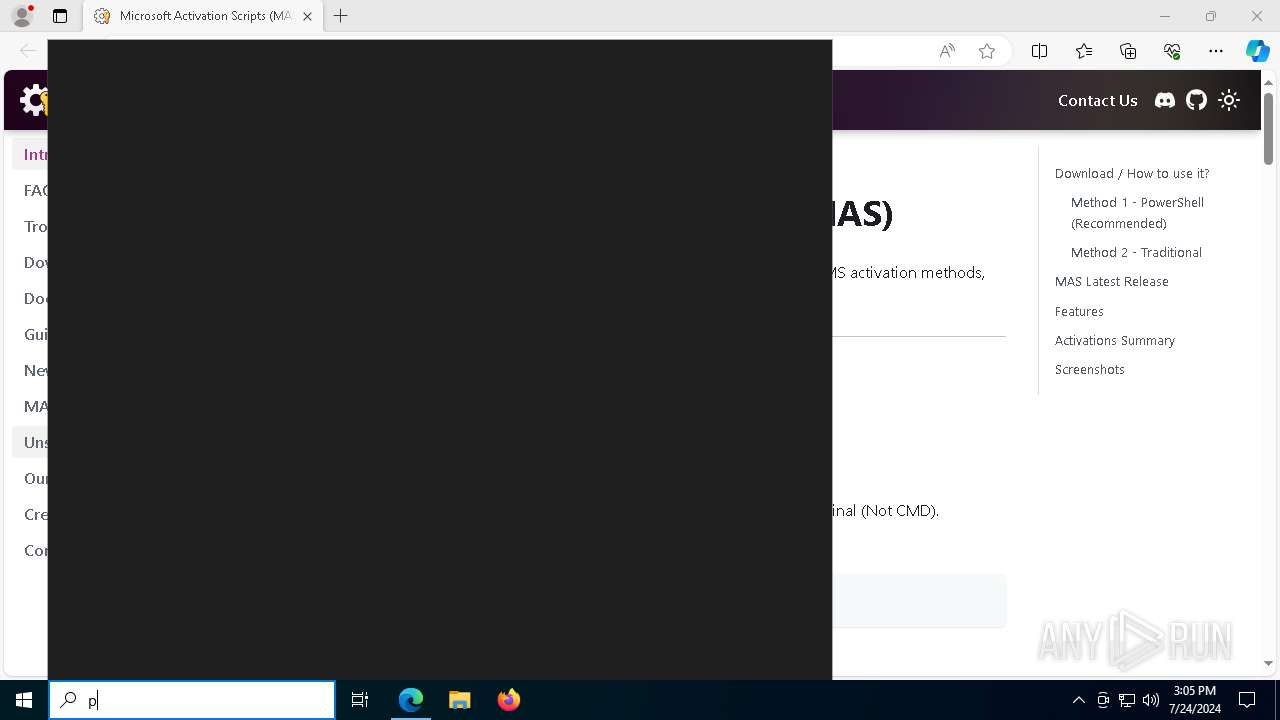
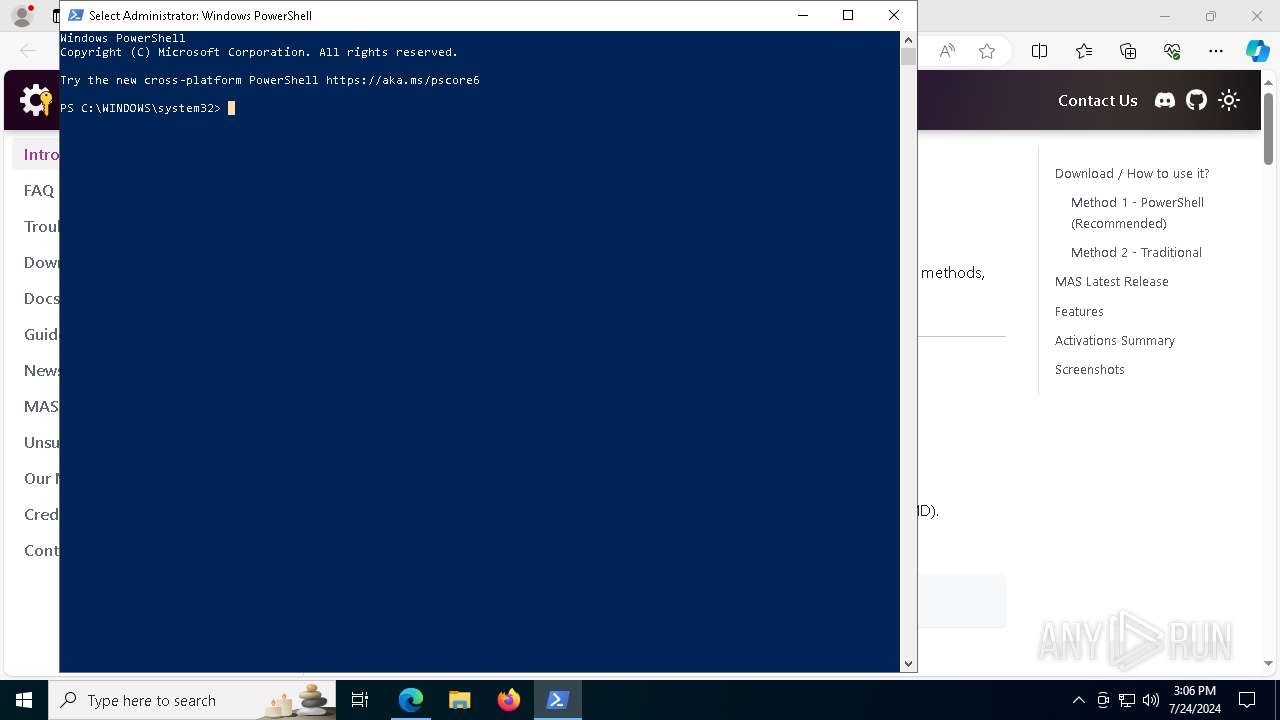
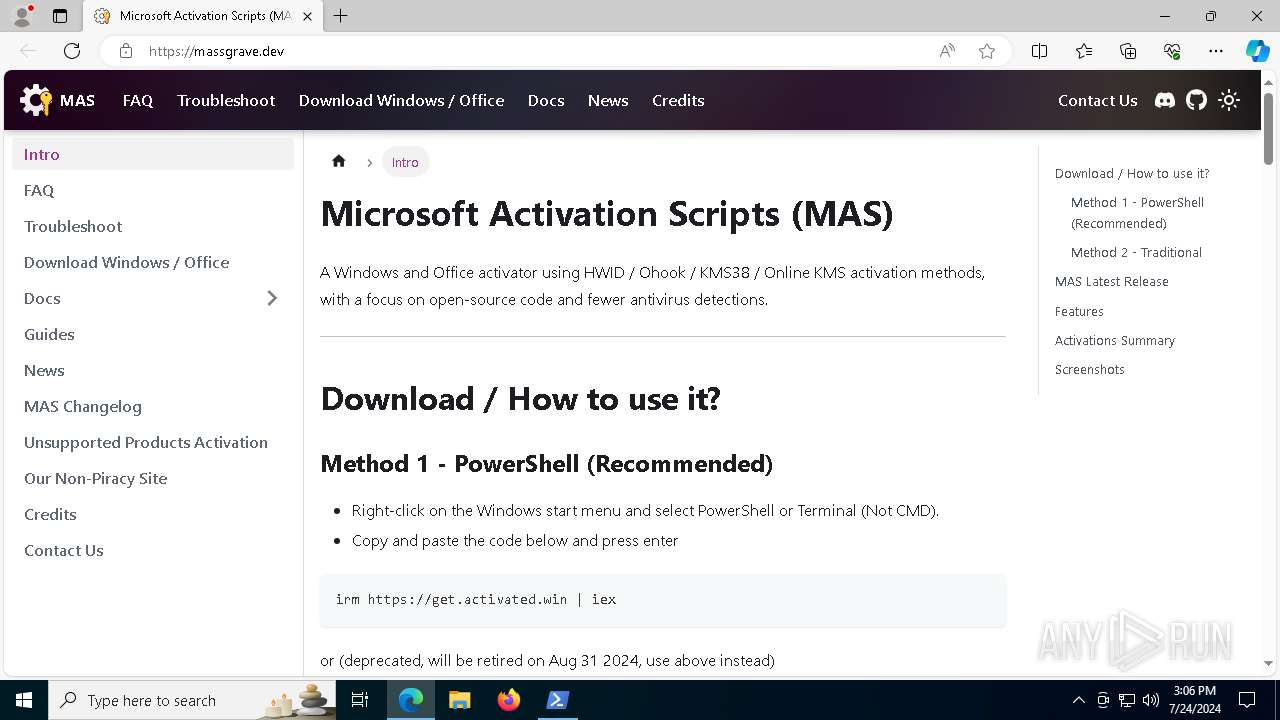
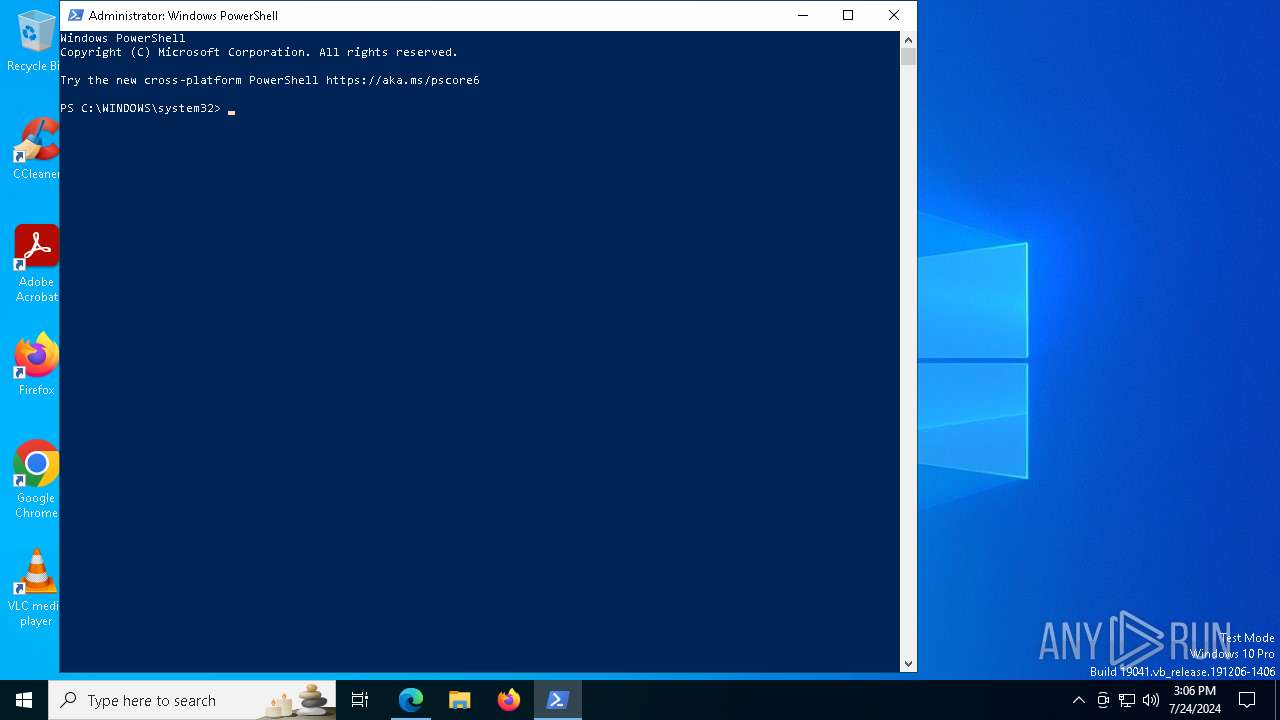
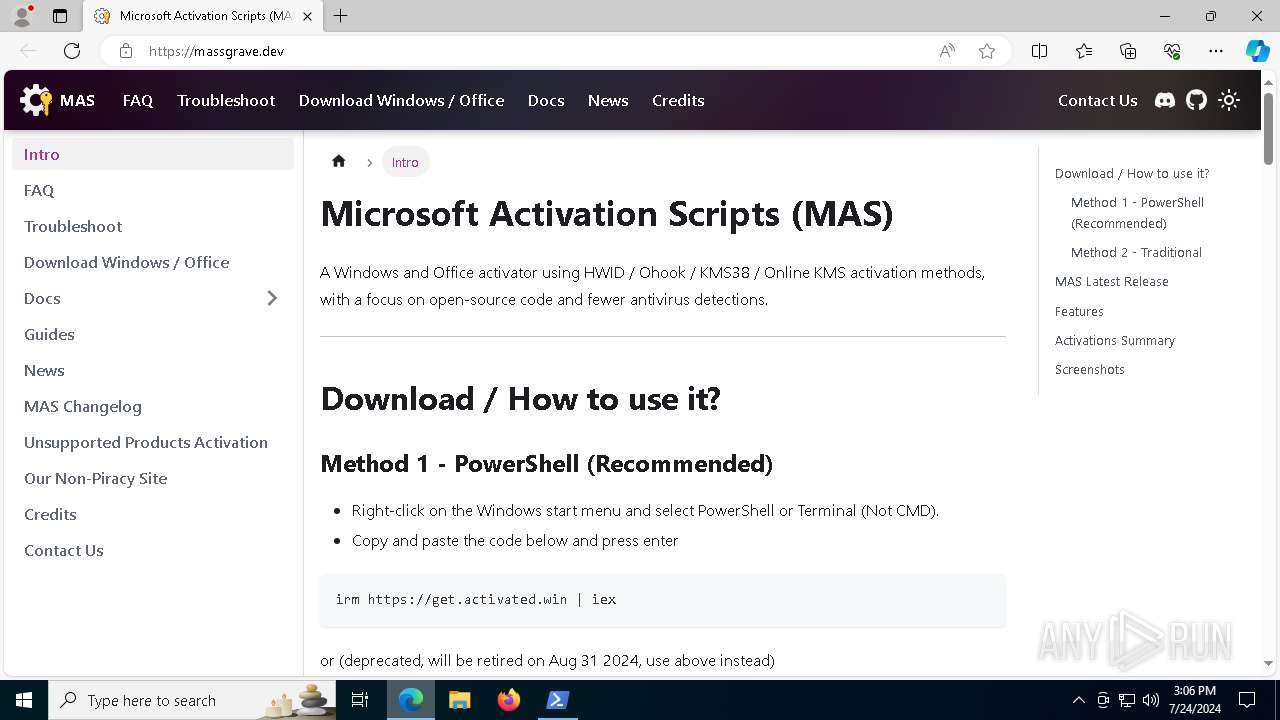
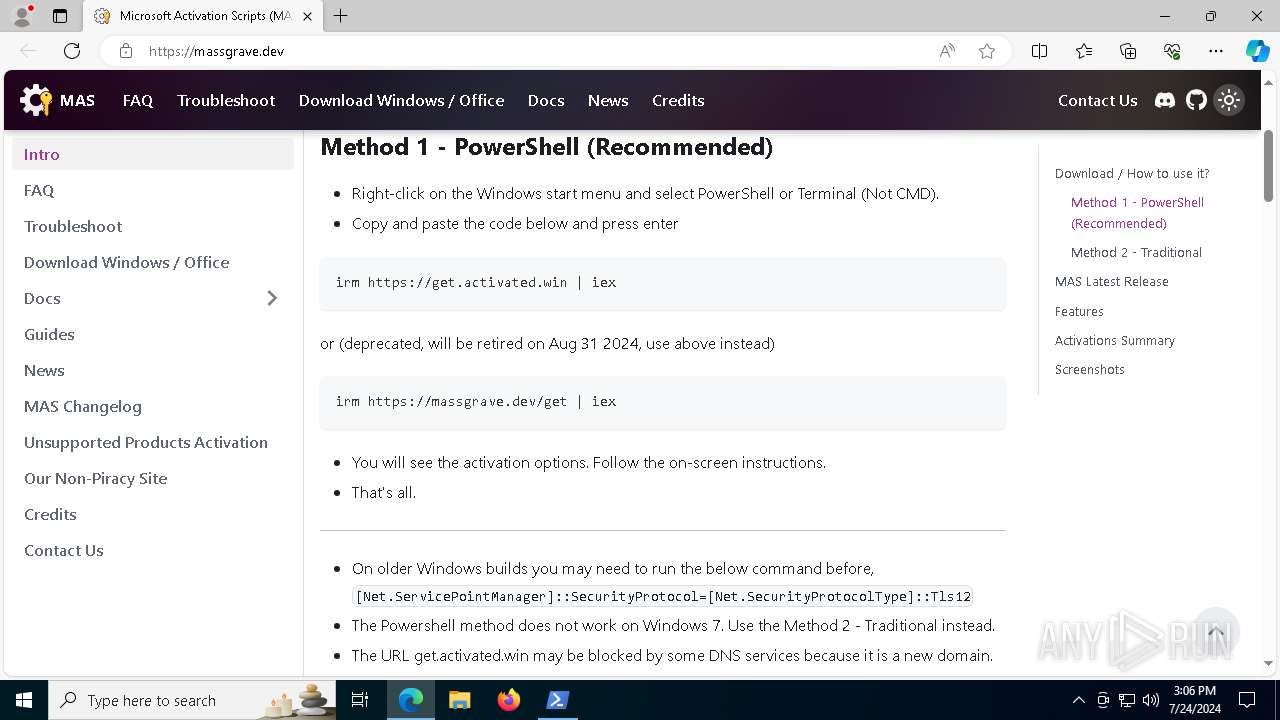
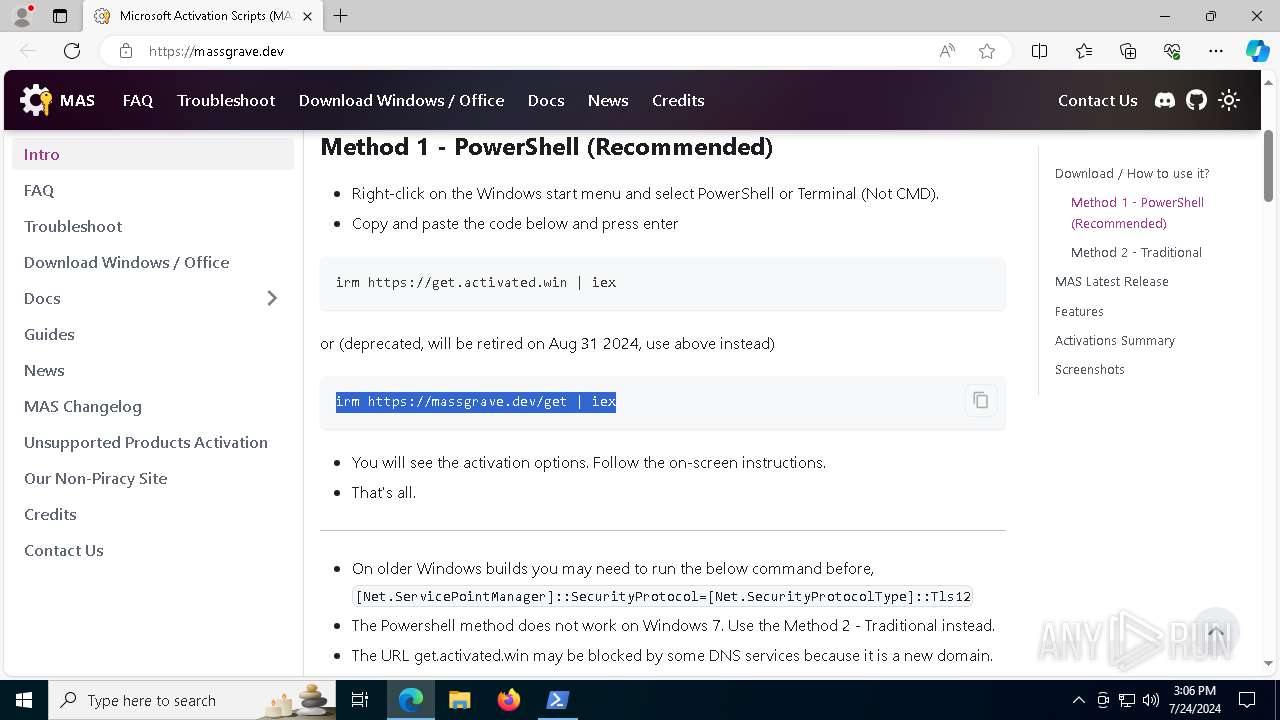
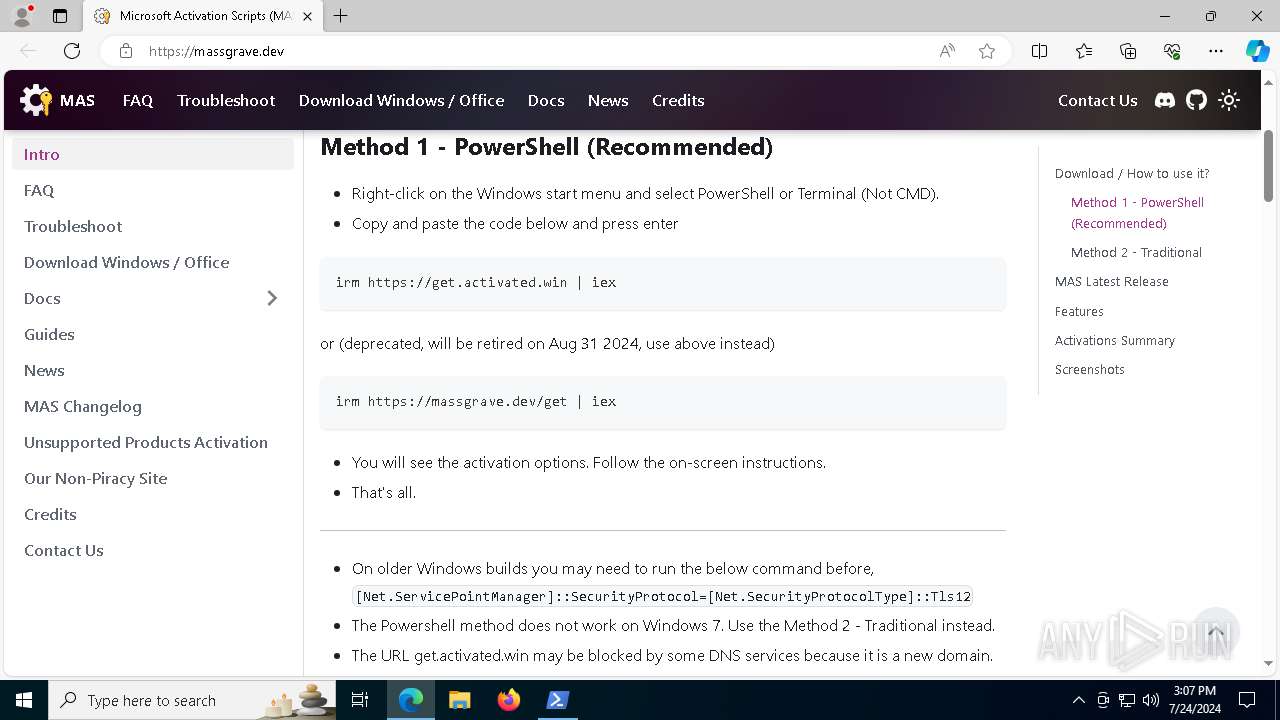
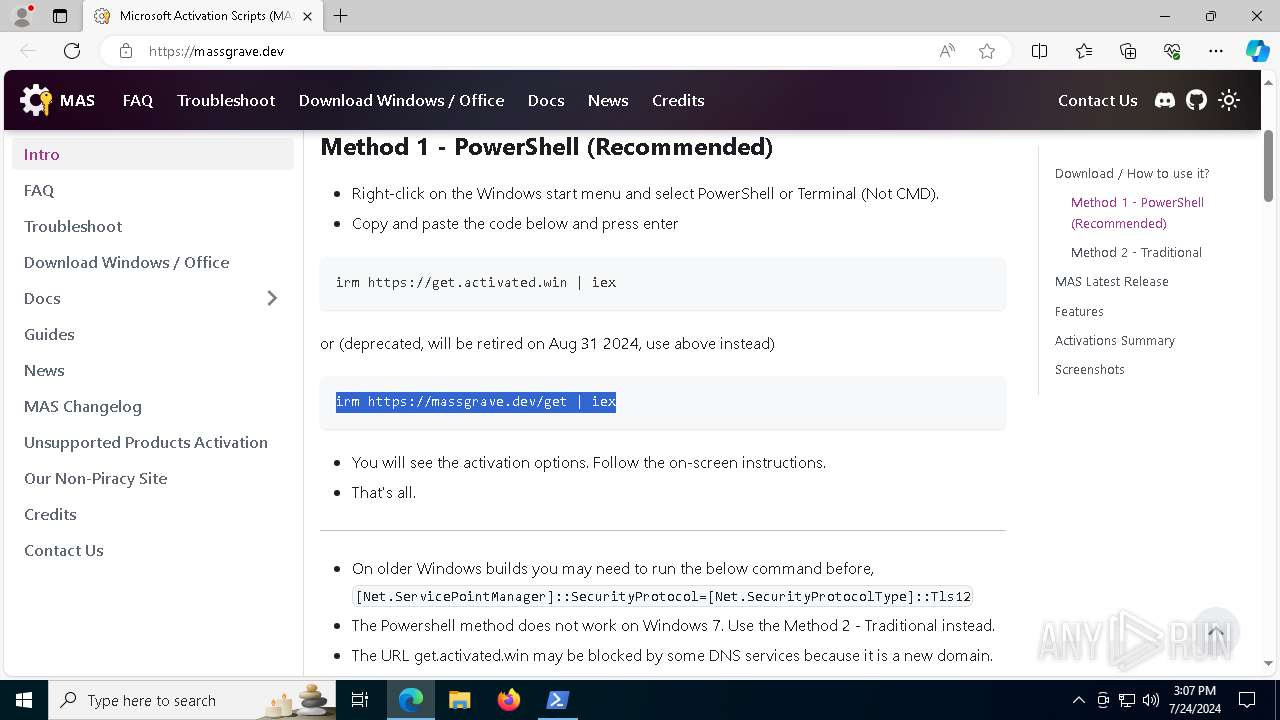
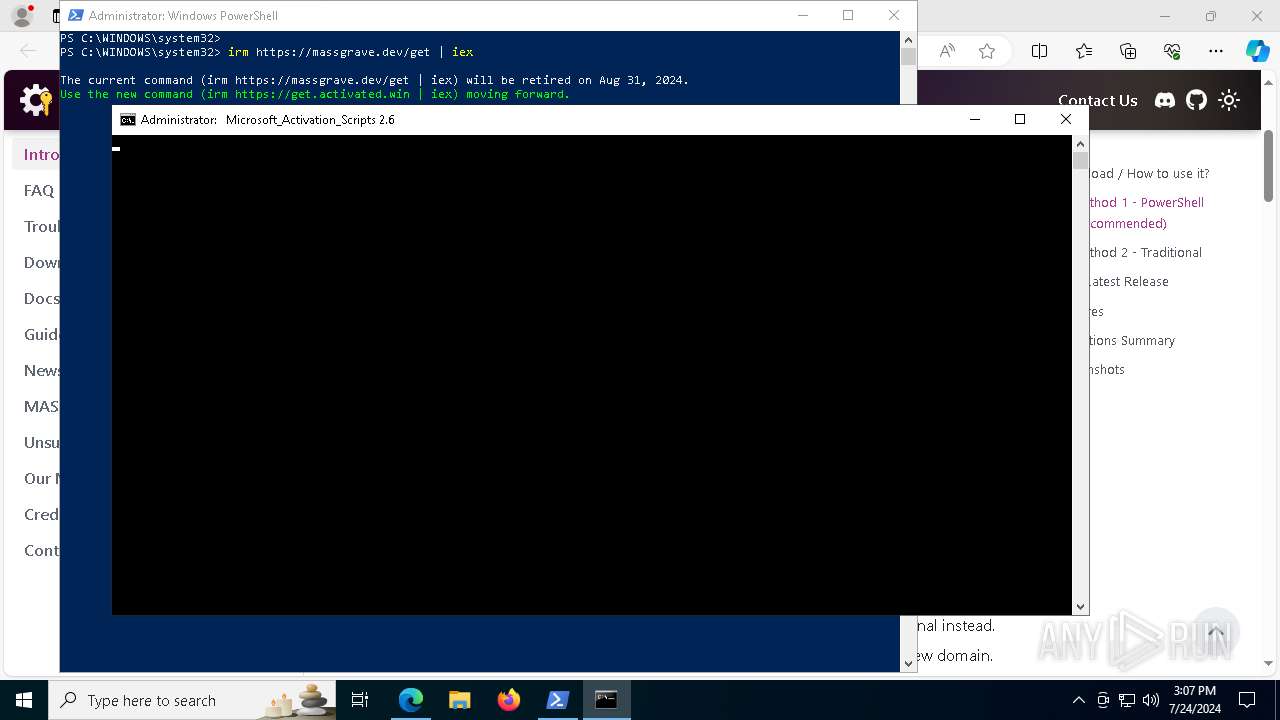
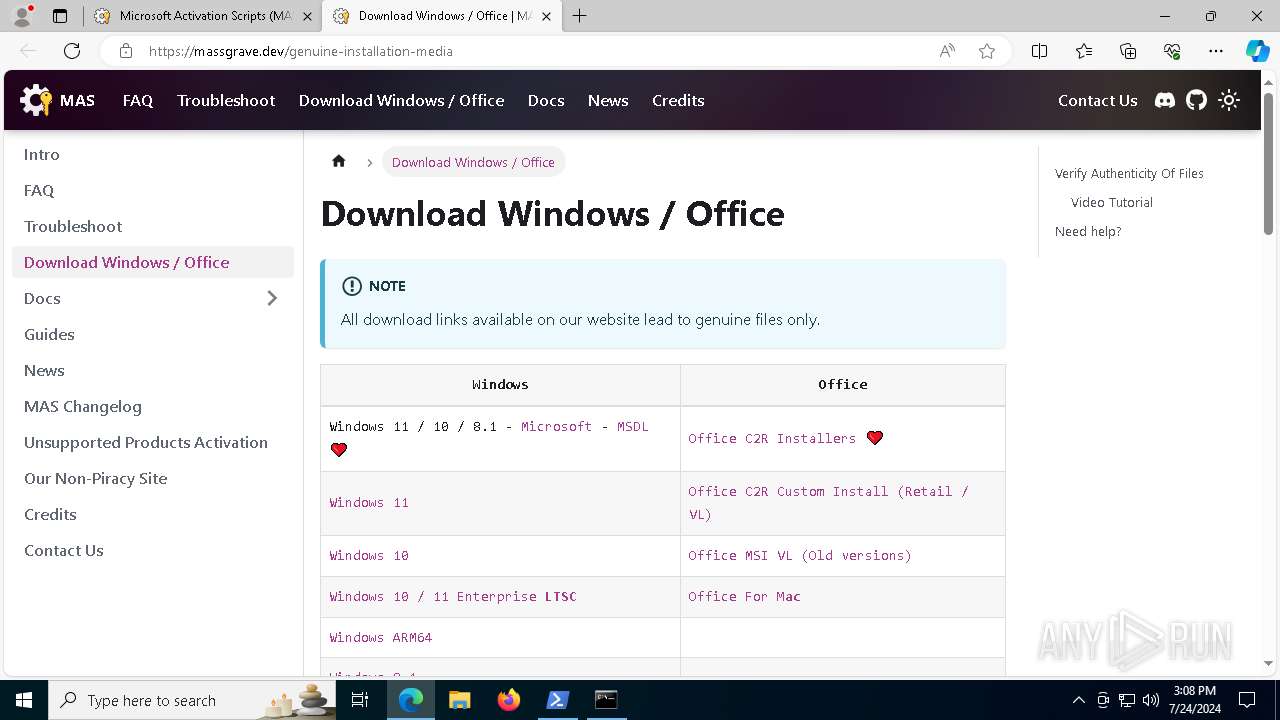
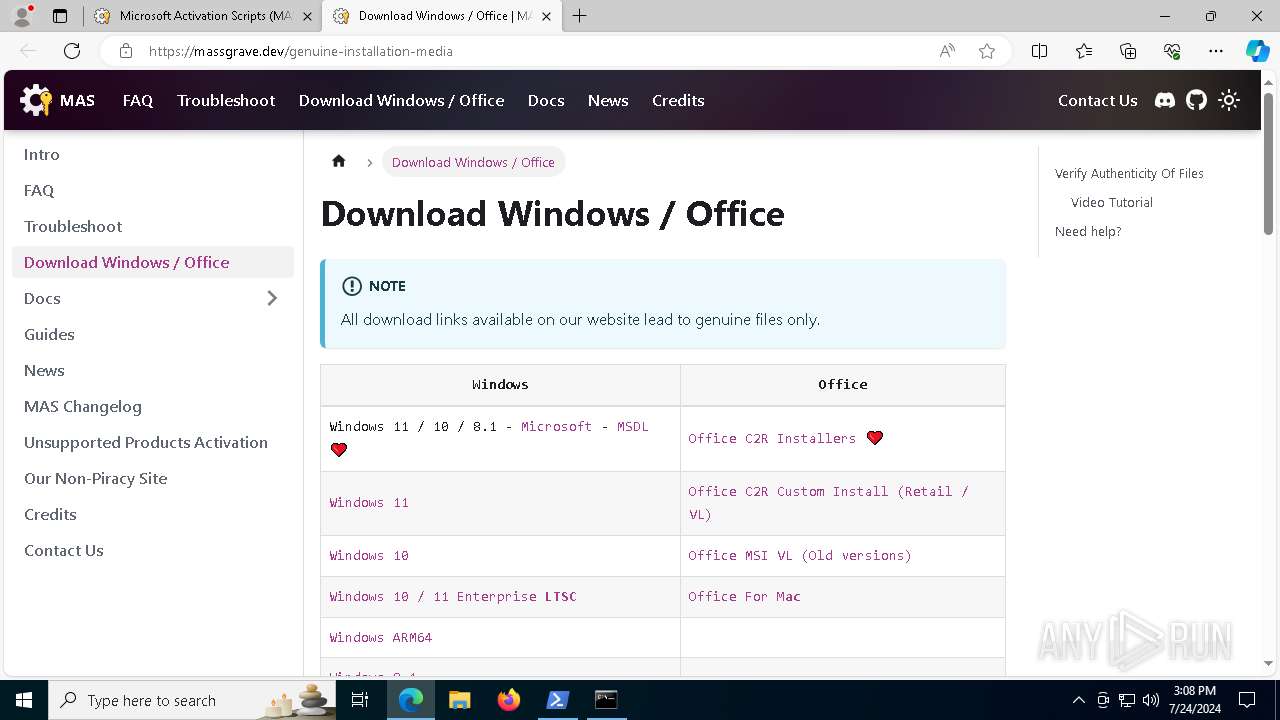
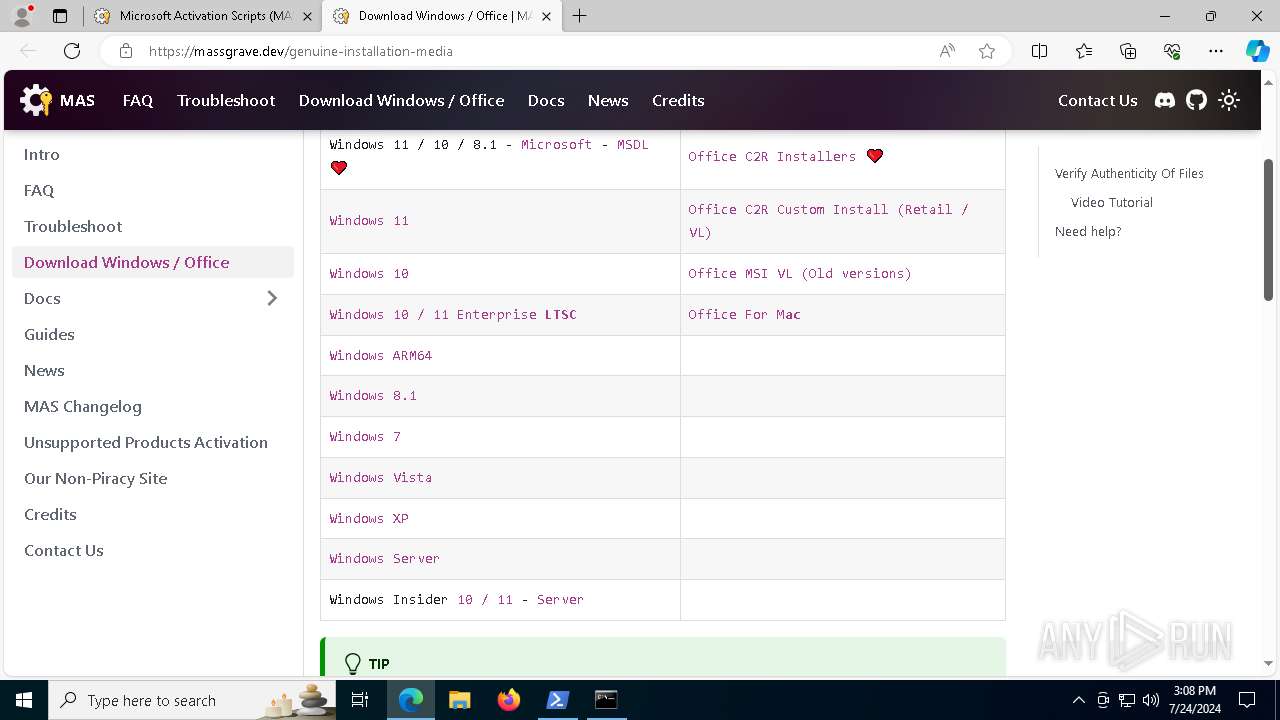
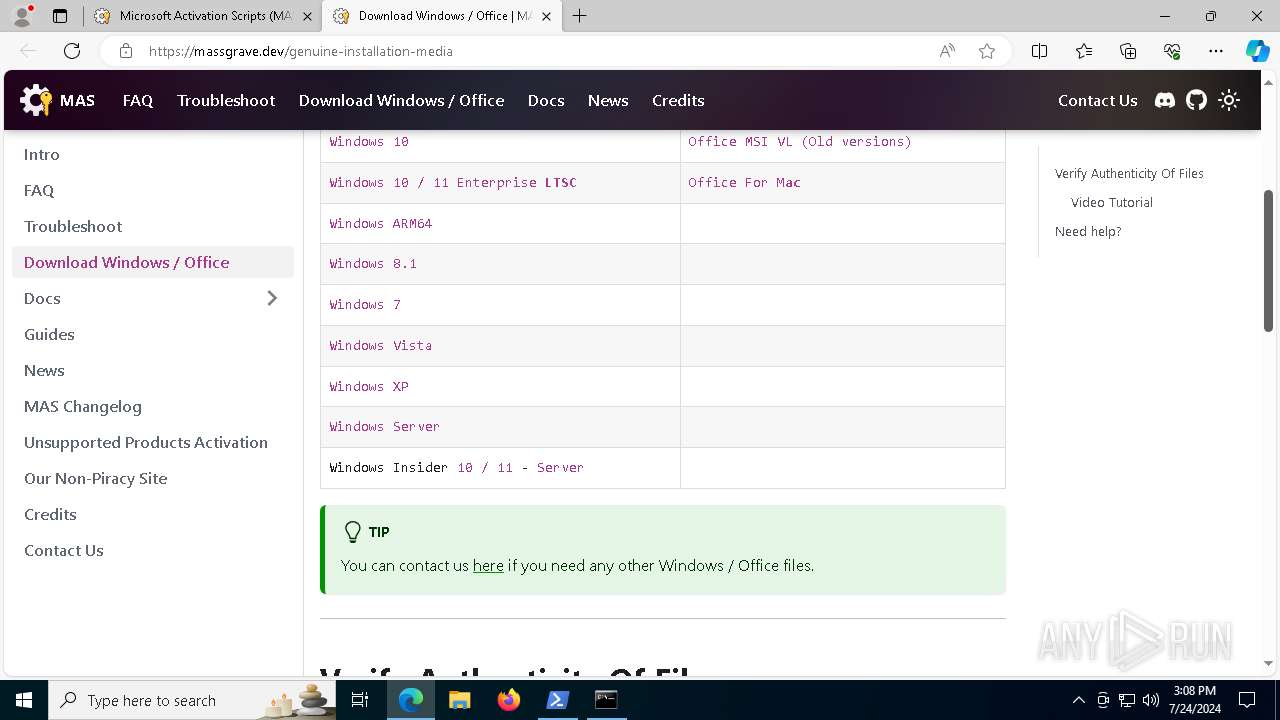
| URL: | https://massgrave.dev |
| Full analysis: | https://app.any.run/tasks/cf35e01d-b0c5-41aa-b14e-d58d2025f102 |
| Verdict: | Malicious activity |
| Analysis date: | July 24, 2024, 15:05:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3A41E379F806C0BDEF594DEFBB784E73 |
| SHA1: | 7E91F91E5017B09E6799E1AC361D7D472E5AF6B8 |
| SHA256: | 2EAD9D1E69FBB35F9AF7ED378B76B9A220F642DA57876A8164B31D3F35EC7355 |
| SSDEEP: | 3:N8a0n:2a0n |
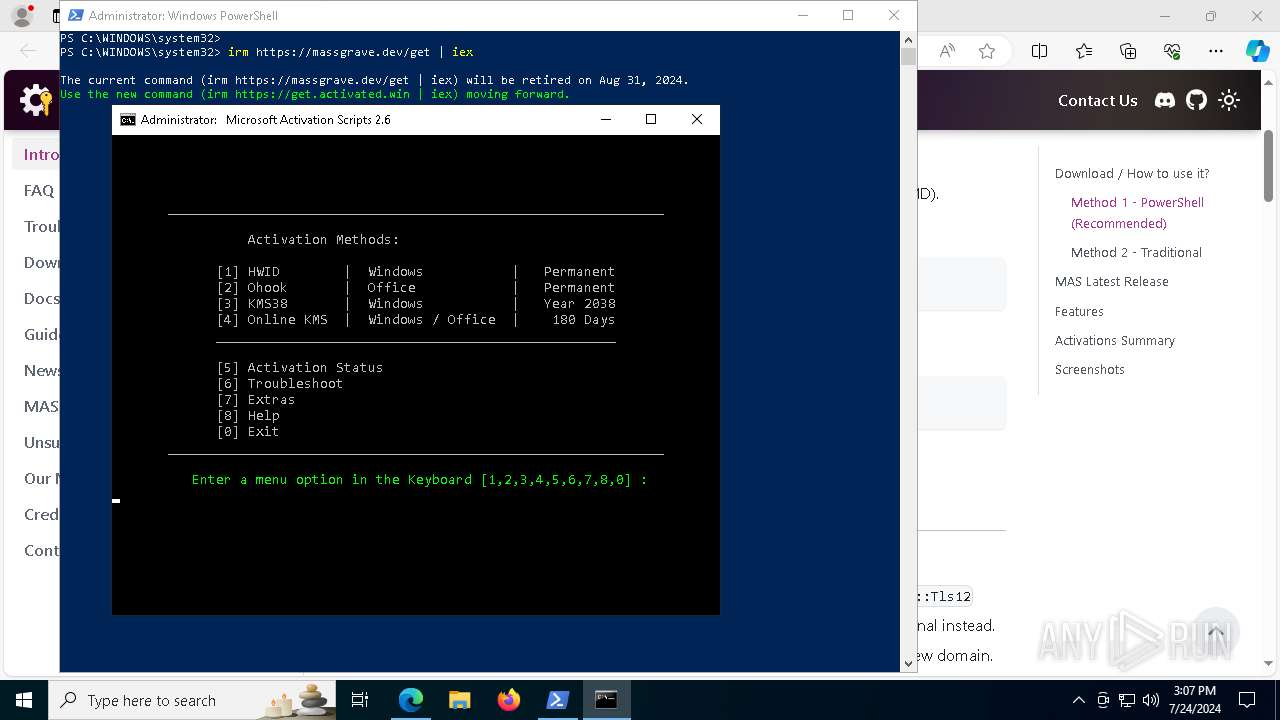
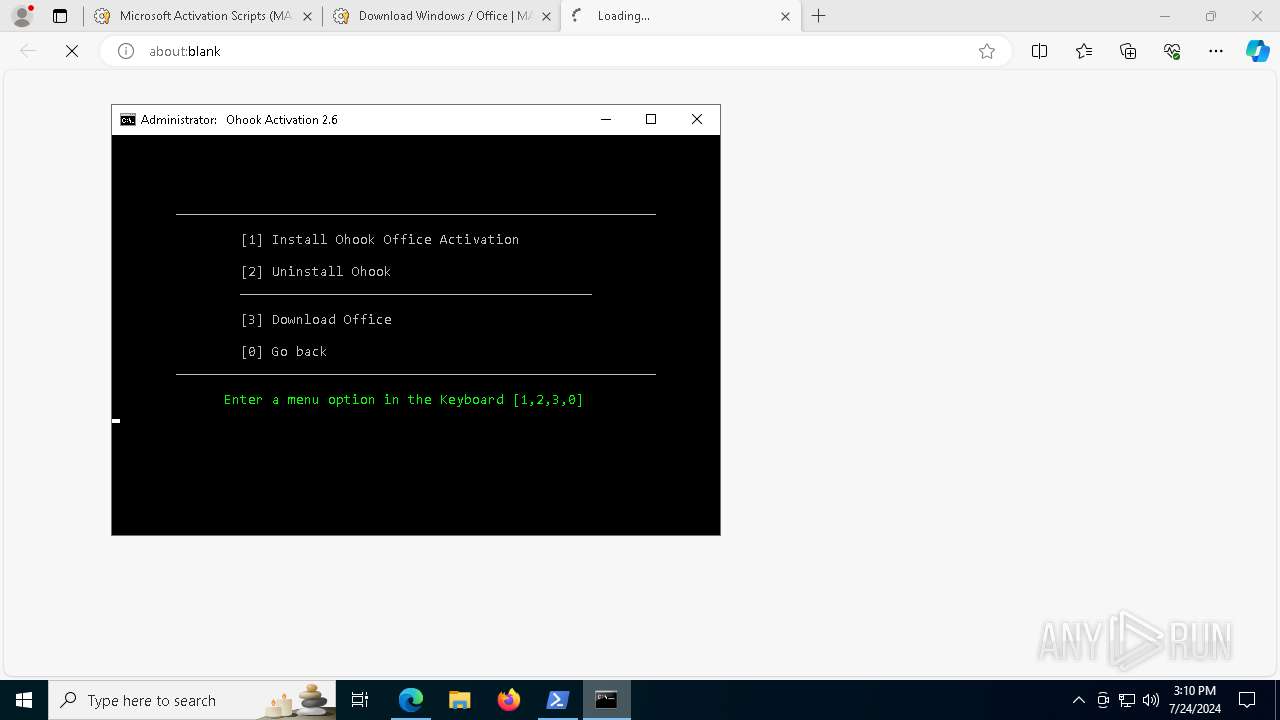
MALICIOUS
No malicious indicators.SUSPICIOUS
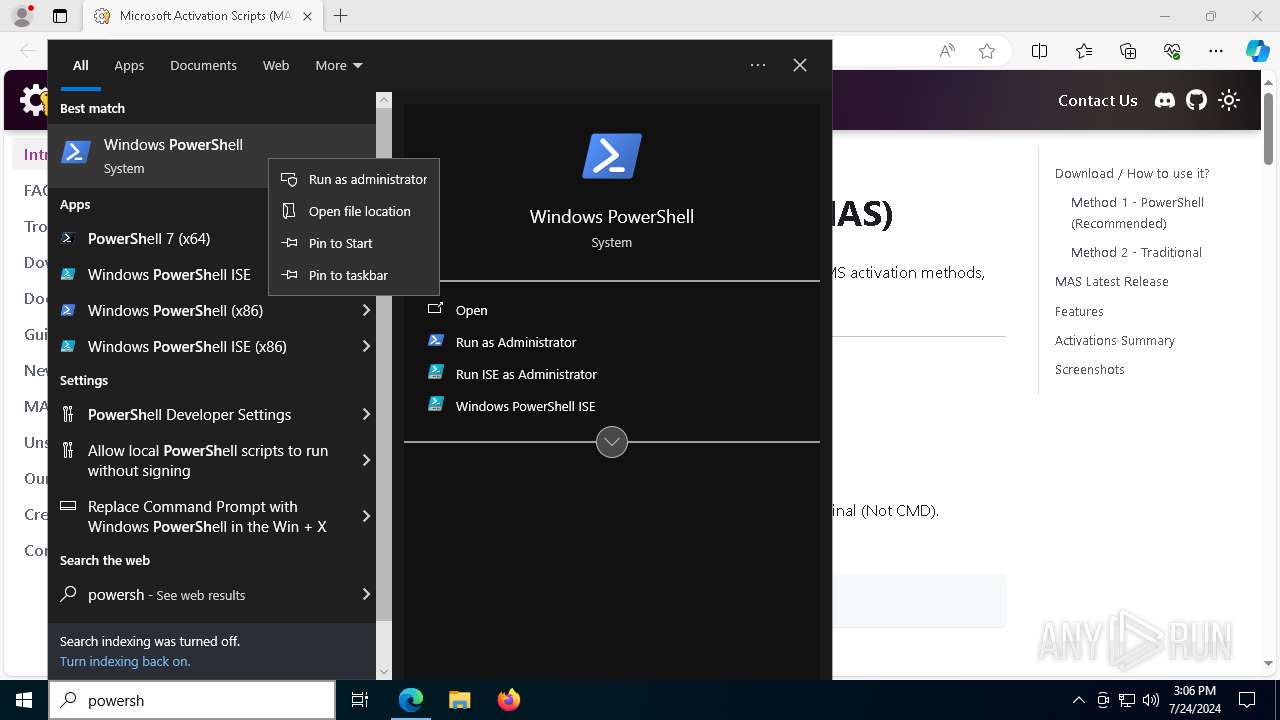
Executing commands from ".cmd" file
- powershell.exe (PID: 4672)
- cmd.exe (PID: 7424)
- cmd.exe (PID: 3276)
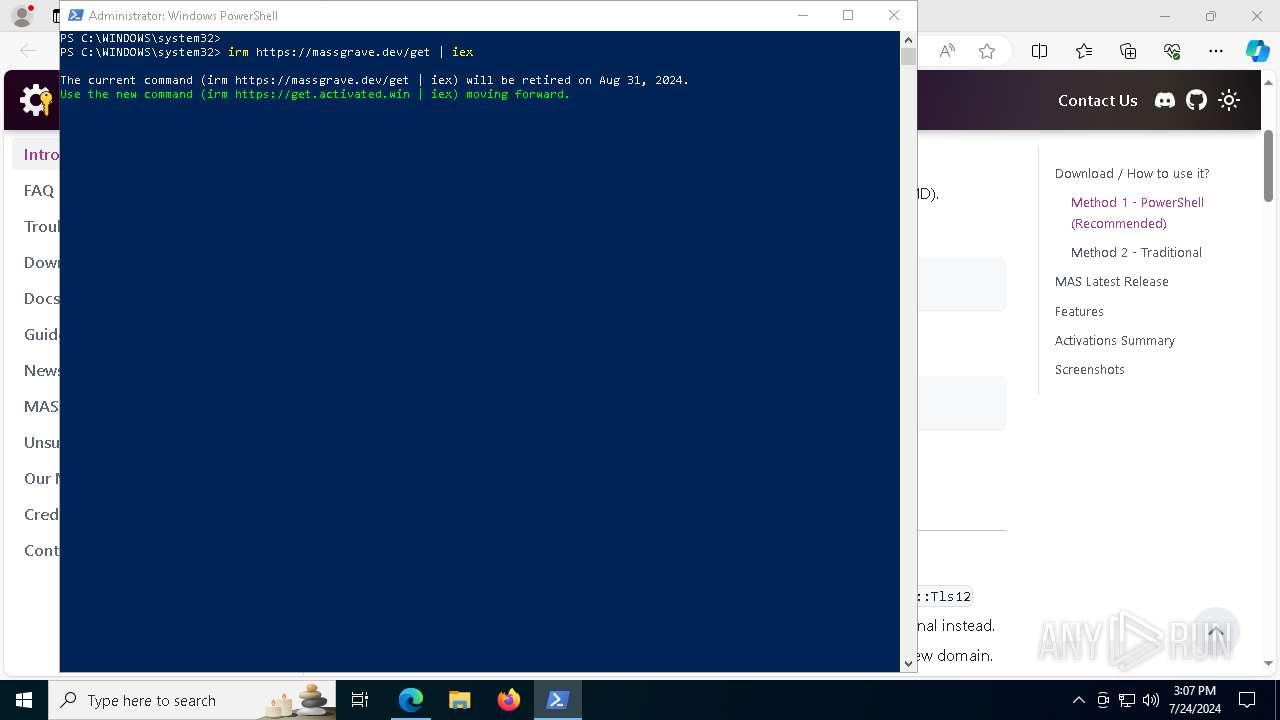
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 4672)
Starts SC.EXE for service management
- cmd.exe (PID: 7424)
- cmd.exe (PID: 3276)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 4672)
- cmd.exe (PID: 7424)
- cmd.exe (PID: 3276)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 1800)
- cmd.exe (PID: 7956)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7424)
- cmd.exe (PID: 3276)
Application launched itself
- cmd.exe (PID: 7424)
- cmd.exe (PID: 7956)
- cmd.exe (PID: 3276)
- cmd.exe (PID: 1800)
- cmd.exe (PID: 7732)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7424)
- cmd.exe (PID: 3276)
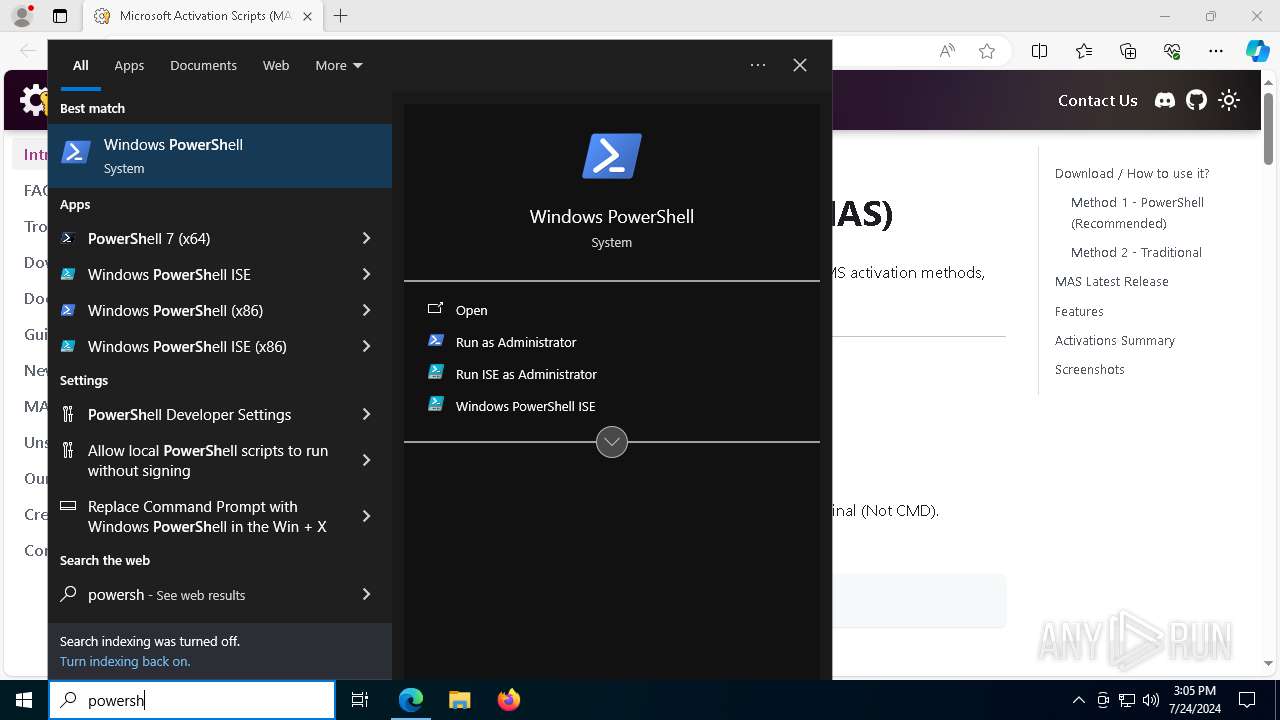
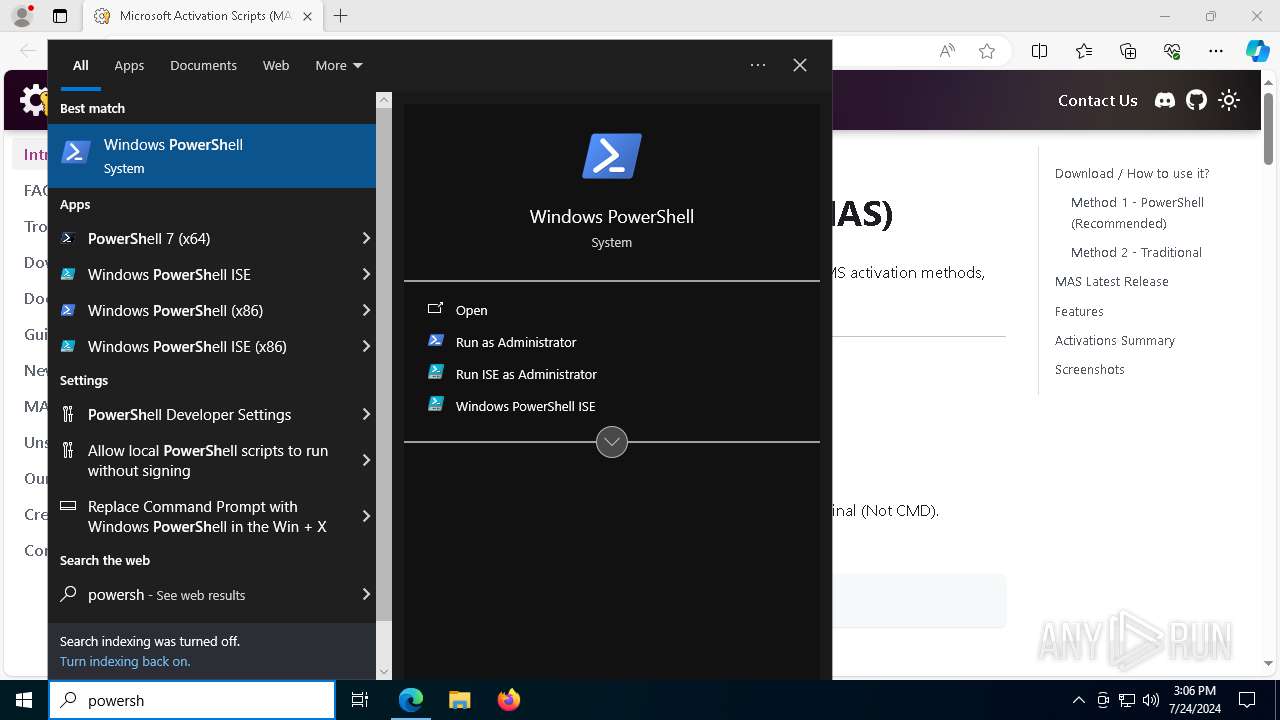
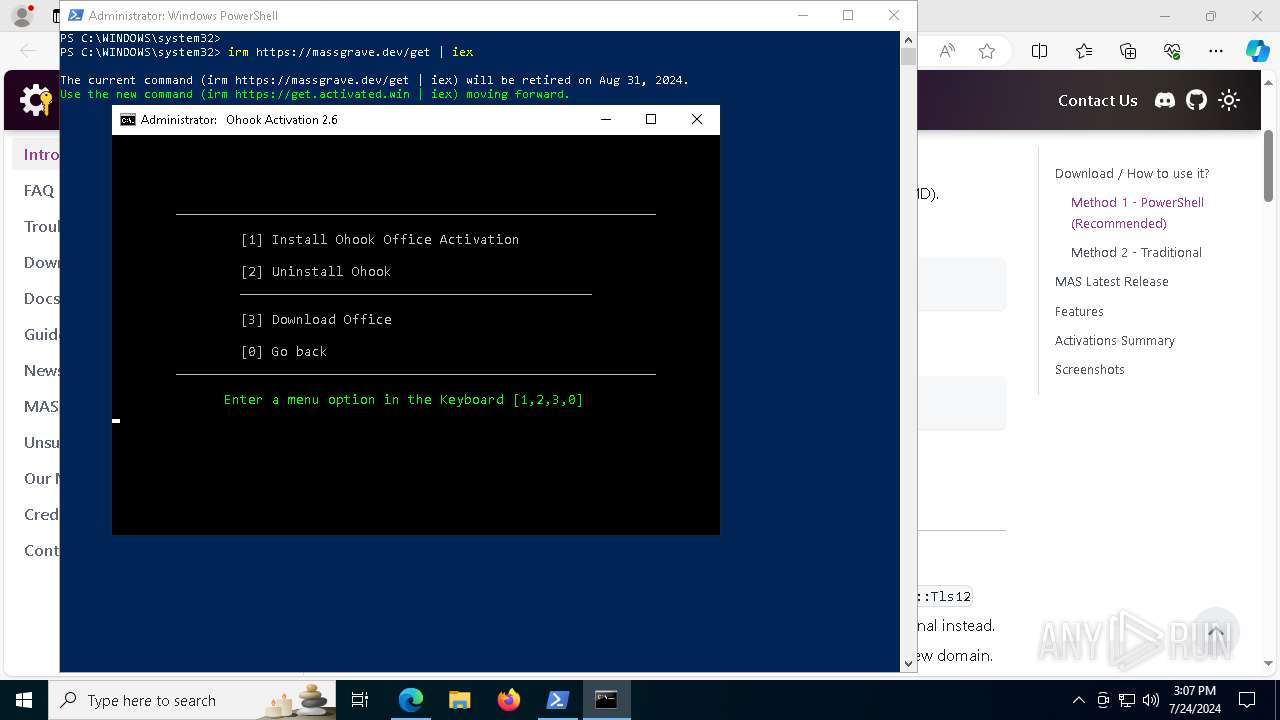
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3276)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 4660)
Hides command output
- cmd.exe (PID: 7060)
- cmd.exe (PID: 5496)
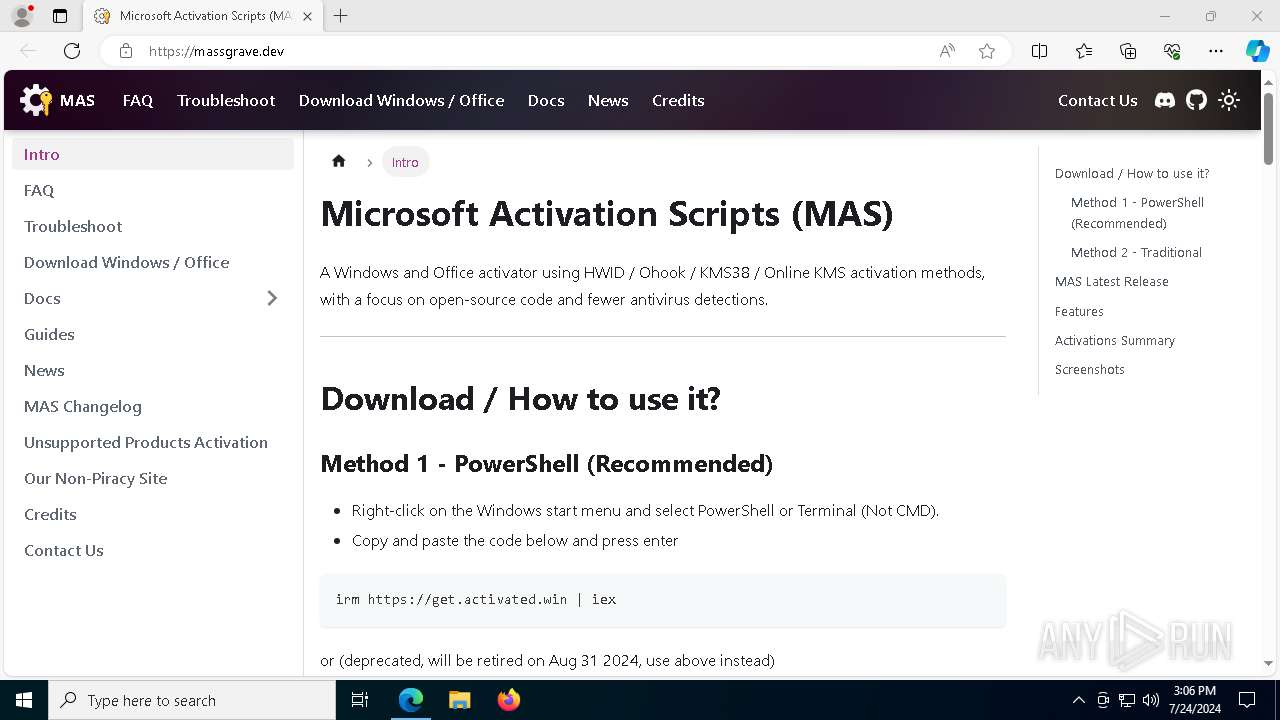
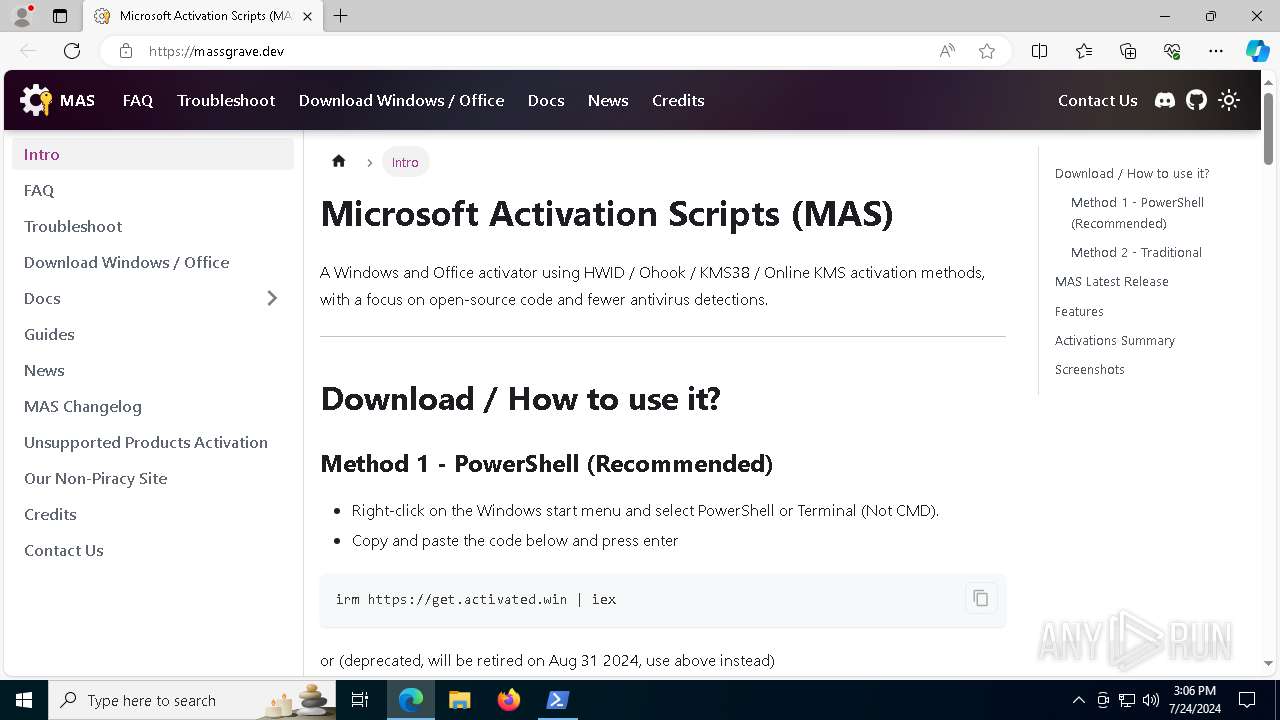
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 7060)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 7060)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1824)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 1824)
Executable content was dropped or overwritten
- Dism.exe (PID: 6836)
The process creates files with name similar to system file names
- Dism.exe (PID: 6836)
Process drops legitimate windows executable
- Dism.exe (PID: 6836)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 3276)
The process executes VB scripts
- cmd.exe (PID: 3276)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 3720)
INFO
Checks supported languages
- identity_helper.exe (PID: 7192)
- TextInputHost.exe (PID: 8056)
- mode.com (PID: 4012)
- mode.com (PID: 4040)
- mode.com (PID: 7372)
- mode.com (PID: 6760)
- DismHost.exe (PID: 3720)
Reads Environment values
- identity_helper.exe (PID: 7192)
- DismHost.exe (PID: 3720)
Reads the computer name
- identity_helper.exe (PID: 7192)
- TextInputHost.exe (PID: 8056)
- DismHost.exe (PID: 3720)
Reads Microsoft Office registry keys
- msedge.exe (PID: 3140)
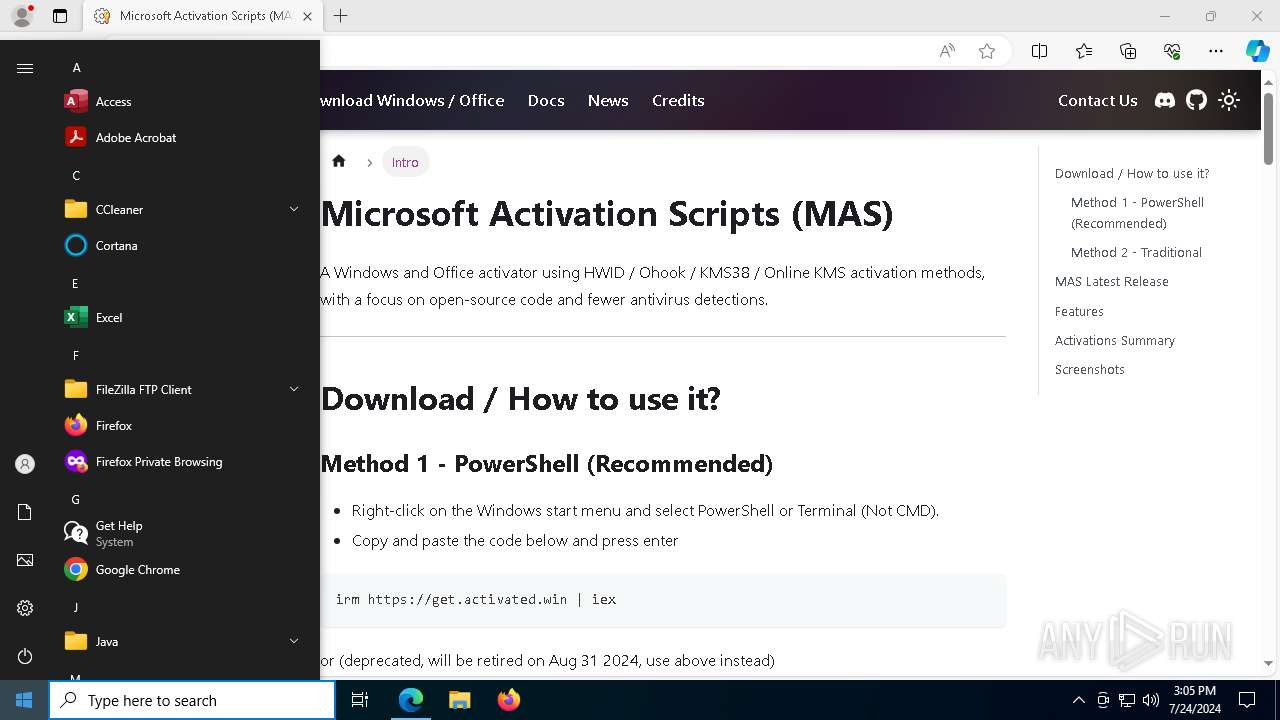
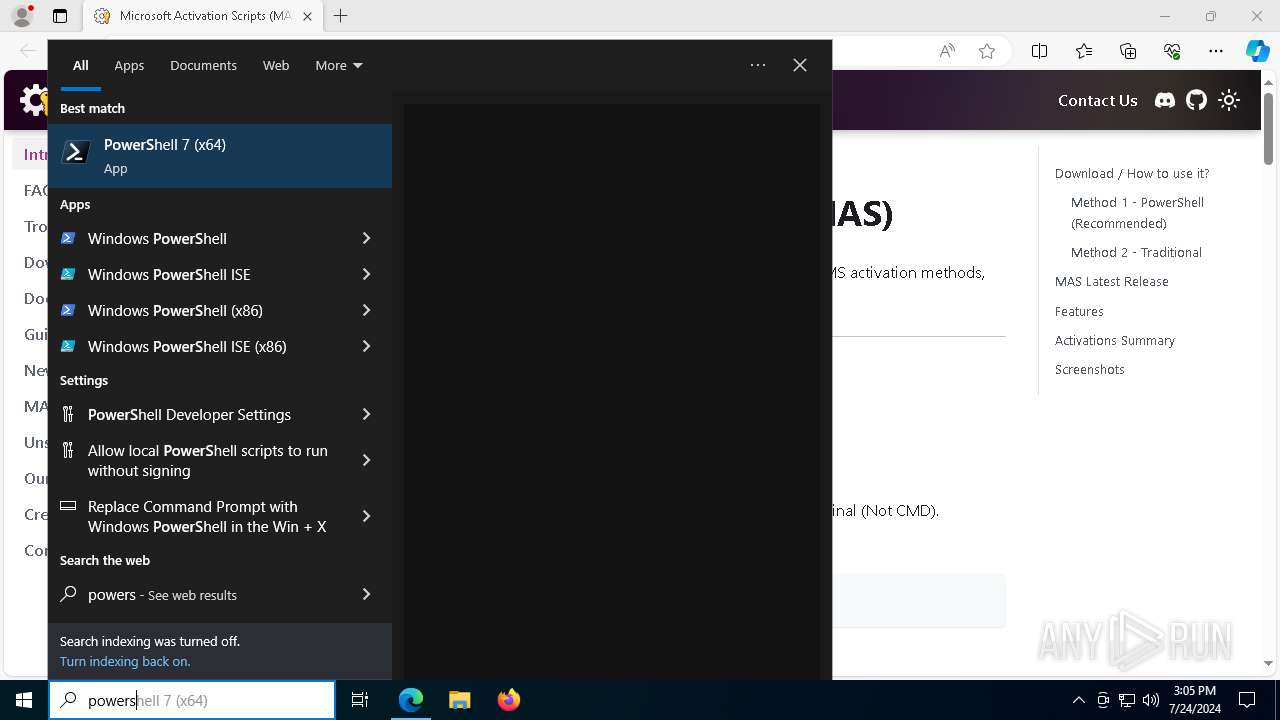
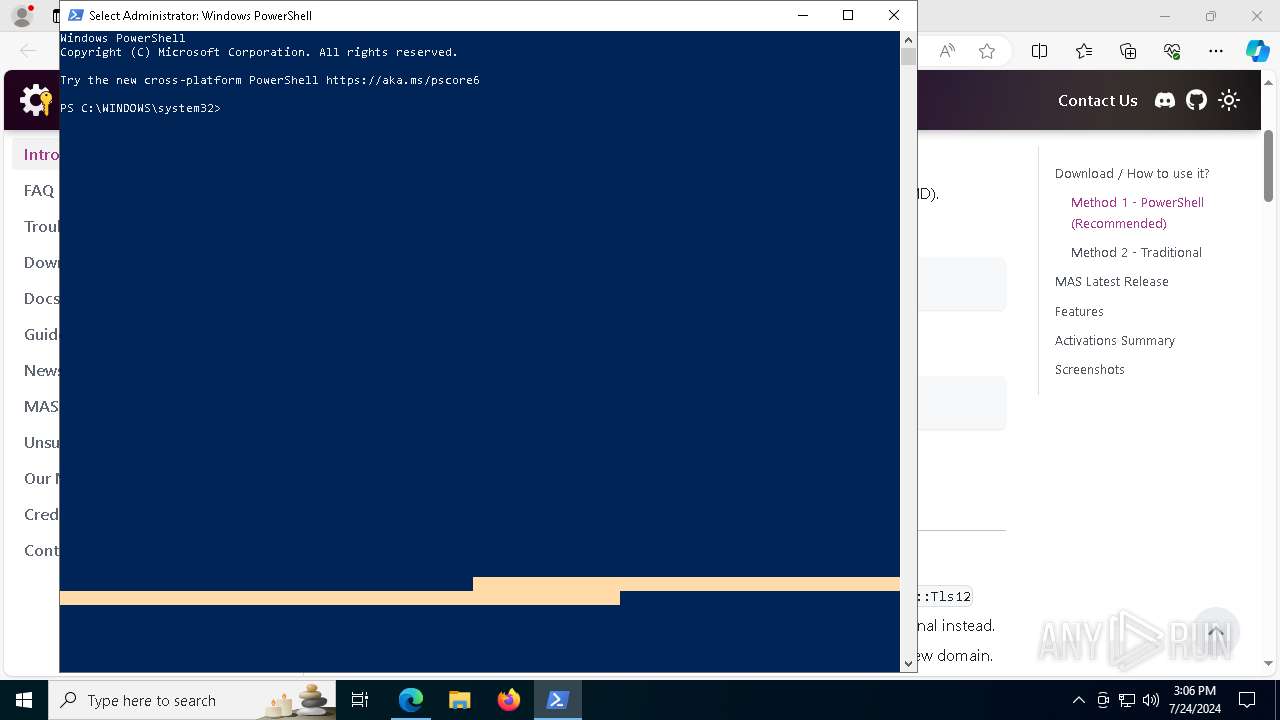
Manual execution by a user
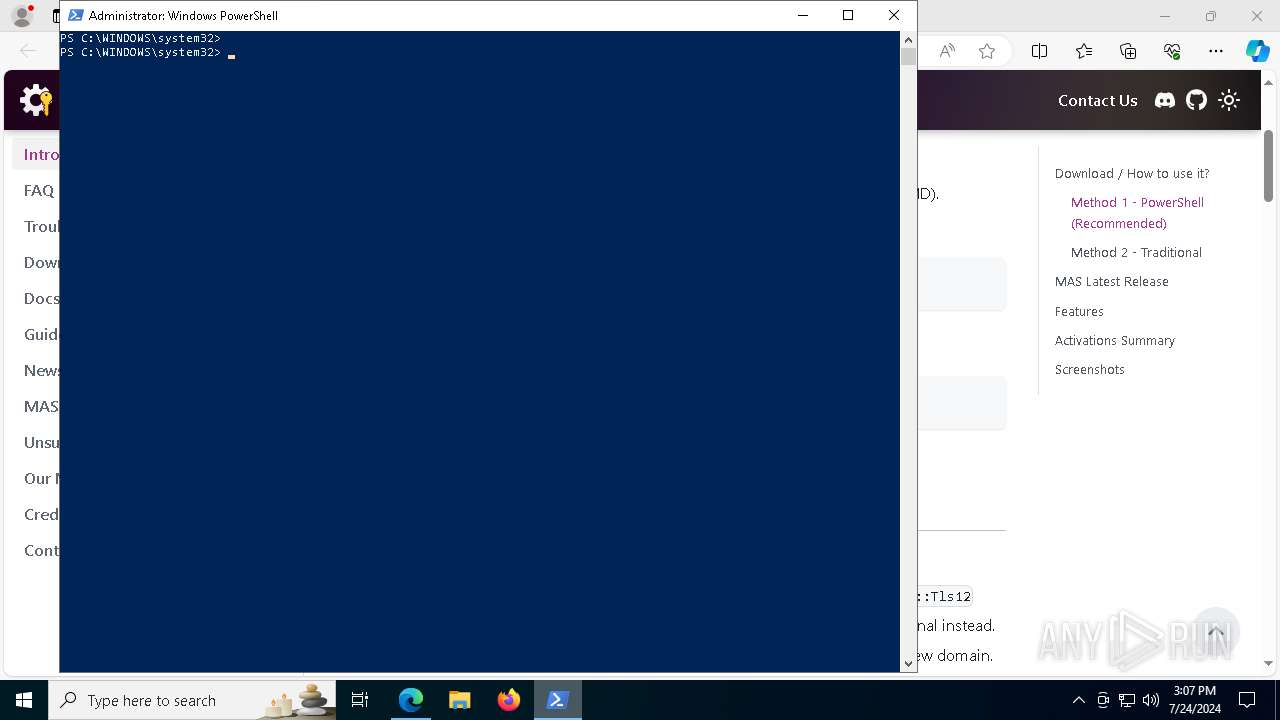
- powershell.exe (PID: 4672)
Checks current location (POWERSHELL)
- powershell.exe (PID: 4672)
Checks proxy server information
- slui.exe (PID: 3060)
- powershell.exe (PID: 4672)
Disables trace logs
- powershell.exe (PID: 4672)
Checks operating system version
- cmd.exe (PID: 7424)
- cmd.exe (PID: 3276)
Application launched itself
- msedge.exe (PID: 3140)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 3936)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 1824)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 1824)
Create files in a temporary directory
- Dism.exe (PID: 6836)
Drops the executable file immediately after the start
- Dism.exe (PID: 6836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
315
Monitored processes
168
Malicious processes
4
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | find /i "/S" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 304 | sc query sppsvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 372 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x250,0x304,0x308,0x258,0x310,0x7ffeffd55fd8,0x7ffeffd55fe4,0x7ffeffd55ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 484 | C:\WINDOWS\system32\cmd.exe /c reg query "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Setup\State" /v ImageState | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 708 | reg query HKLM\SYSTEM\CurrentControlSet\Services\Winmgmt /v ObjectName | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 884 | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 884 | find /i "Full" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4156 --field-trial-handle=2256,i,9010099085023673963,12938474261570251168,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 996 | reg query HKLM\SYSTEM\CurrentControlSet\Services\Winmgmt /v Description | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1044 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1548 --field-trial-handle=2256,i,9010099085023673963,12938474261570251168,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
28 973
Read events
28 893
Write events
79
Delete events
1
Modification events
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
51
Suspicious files
285
Text files
121
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe0f7c.TMP | — | |
MD5:— | SHA256:— | |||
| 3140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe0f7c.TMP | — | |
MD5:— | SHA256:— | |||
| 3140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe0f7c.TMP | — | |
MD5:— | SHA256:— | |||
| 3140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe0f7c.TMP | — | |
MD5:— | SHA256:— | |||
| 3140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe0f7c.TMP | — | |
MD5:— | SHA256:— | |||
| 3140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
108
DNS requests
95
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7728 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/81c945d1-1834-4d97-ab56-9ed86990a128?P1=1722301009&P2=404&P3=2&P4=HBPCGfrvqwIdyoPE%2b22blE8MVMW1kasB4CGMScdvpJBX92btGua087GQRWrTdiF%2fy8cUhZop0kc6vbCZ135Amw%3d%3d | unknown | — | — | whitelisted |
7728 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8bc315ba-54e5-49f4-9b75-997d7071eb06?P1=1722399958&P2=404&P3=2&P4=W8TYpdrYT9JNVx5A7f0WI5YnELqT5WoPS99e938xs3ZfIlIBbQg8cODCEomxJmBzV11CEU%2fNYBK3Mkko9o4ifw%3d%3d | unknown | — | — | whitelisted |
7728 | svchost.exe | GET | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/81c945d1-1834-4d97-ab56-9ed86990a128?P1=1722301009&P2=404&P3=2&P4=HBPCGfrvqwIdyoPE%2b22blE8MVMW1kasB4CGMScdvpJBX92btGua087GQRWrTdiF%2fy8cUhZop0kc6vbCZ135Amw%3d%3d | unknown | — | — | whitelisted |
7728 | svchost.exe | GET | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8bc315ba-54e5-49f4-9b75-997d7071eb06?P1=1722399958&P2=404&P3=2&P4=W8TYpdrYT9JNVx5A7f0WI5YnELqT5WoPS99e938xs3ZfIlIBbQg8cODCEomxJmBzV11CEU%2fNYBK3Mkko9o4ifw%3d%3d | unknown | — | — | whitelisted |
7728 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3431e97b-0c2a-4d25-8965-bf938067ad33?P1=1722333045&P2=404&P3=2&P4=nJs5Uf6zXSWfAaDI6NOe2jTiGz%2fauAO3yU9VqgoJVJCQ8gmnWM%2bhC%2bjHdoiU%2f7UUXeXQ8jzMD%2fgOKO8ND6aYbg%3d%3d | unknown | — | — | whitelisted |
6760 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
7108 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7728 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68eda192-d0f3-46cf-b3be-1a828f951b21?P1=1722411858&P2=404&P3=2&P4=IAI6pmvzeSU0%2bKDappt9grzDeOYVzXtoHrebkm1hUnYIUEV%2fZCvaYMBI%2fv8R3%2bquQuLInAqozCqY%2bs6wBmQxtA%3d%3d | unknown | — | — | whitelisted |
7728 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68eda192-d0f3-46cf-b3be-1a828f951b21?P1=1722411858&P2=404&P3=2&P4=IAI6pmvzeSU0%2bKDappt9grzDeOYVzXtoHrebkm1hUnYIUEV%2fZCvaYMBI%2fv8R3%2bquQuLInAqozCqY%2bs6wBmQxtA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6012 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4220 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3380 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4204 | svchost.exe | 4.209.32.67:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
5368 | SearchApp.exe | 2.23.209.140:443 | www.bing.com | Akamai International B.V. | GB | unknown |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4036 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3140 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4036 | msedge.exe | 104.21.22.3:443 | massgrave.dev | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
massgrave.dev |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2284 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
4036 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
Process | Message |
|---|---|
Dism.exe | PID=6836 TID=848 Instantiating the Provider Store. - CDISMImageSession::get_ProviderStore |
Dism.exe | PID=6836 TID=848 Initializing a provider store for the LOCAL session type. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=6836 TID=848 Attempting to initialize the logger from the Image Session. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=6836 TID=848 Provider has not previously been encountered. Attempting to initialize the provider. - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=6836 TID=848 Loading Provider from location C:\Windows\System32\Dism\LogProvider.dll - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=6836 TID=848 Connecting to the provider located at C:\Windows\System32\Dism\LogProvider.dll. - CDISMProviderStore::Internal_LoadProvider |
DismHost.exe | PID=3720 TID=736 Disconnecting the provider store - CDISMImageSession::Final_OnDisconnect |
DismHost.exe | PID=3720 TID=736 Encountered a loaded provider DISMLogger. - CDISMProviderStore::Internal_DisconnectProvider |
DismHost.exe | PID=3720 TID=736 Disconnecting Provider: DISMLogger - CDISMProviderStore::Internal_DisconnectProvider |
Dism.exe | PID=6836 TID=848 Disconnecting the provider store - CDISMImageSession::Final_OnDisconnect |