analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
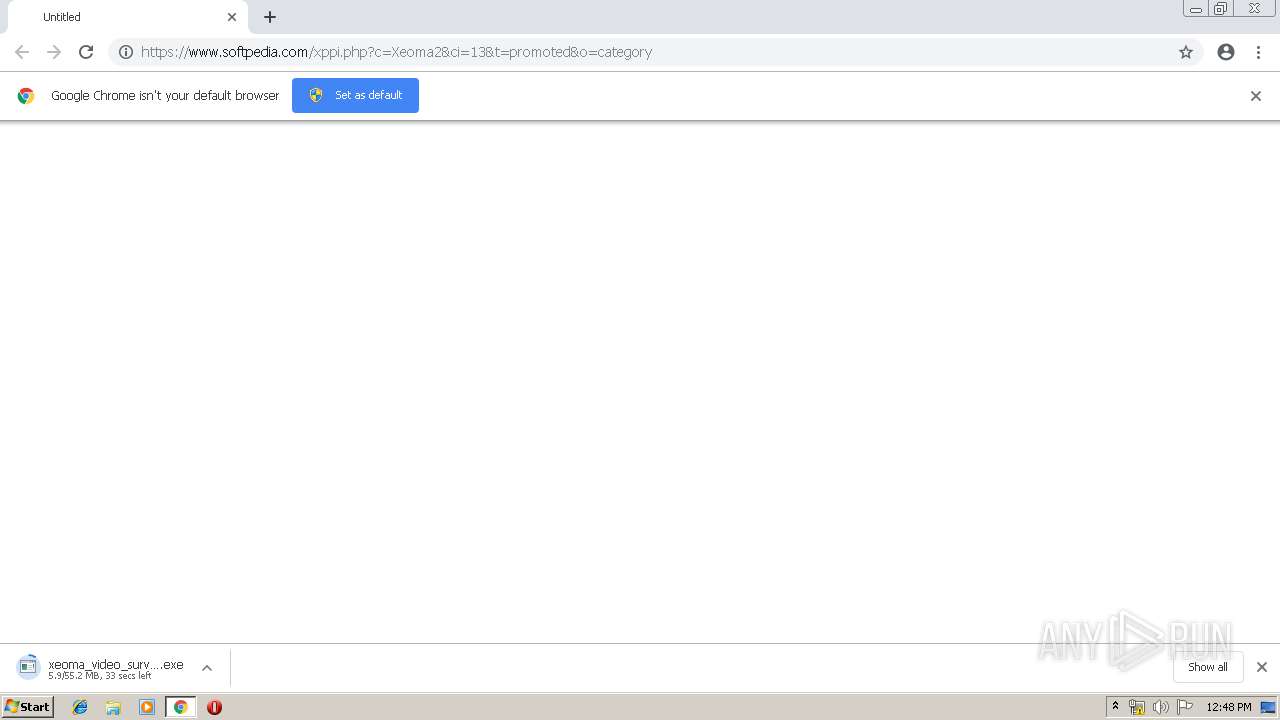
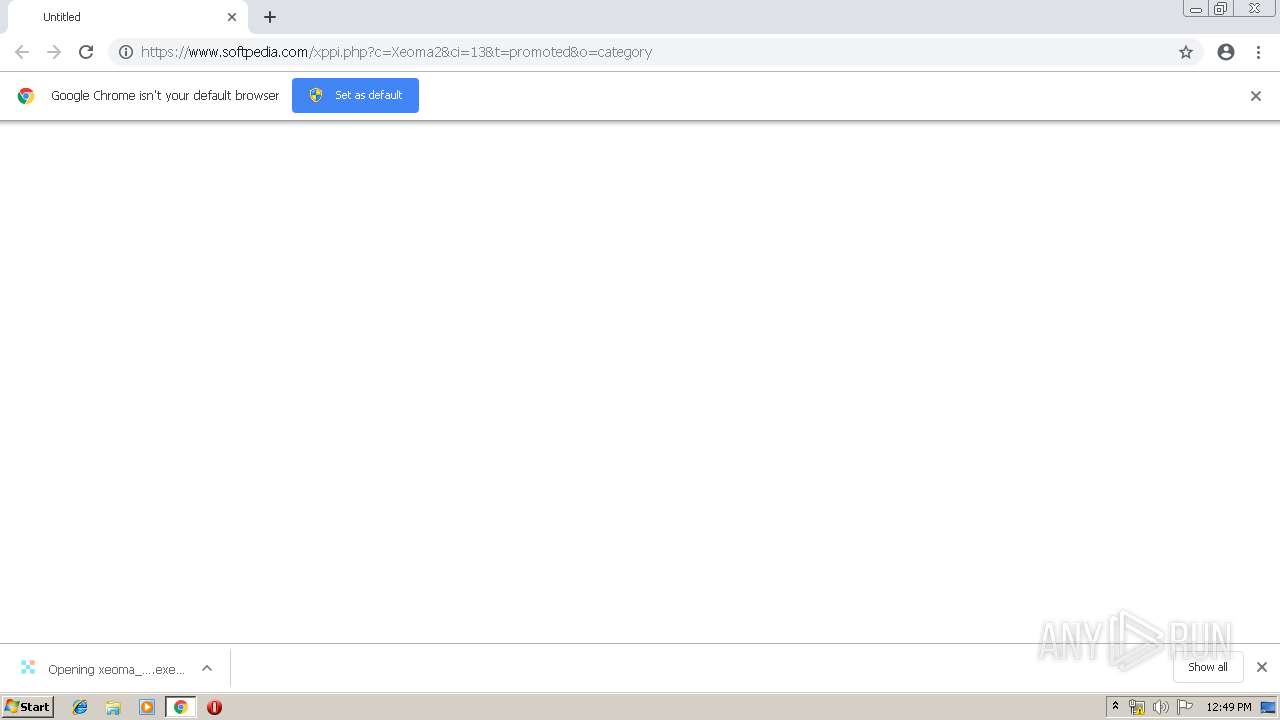
| URL: | https://www.softpedia.com/xppi.php?c=Xeoma2&ci=13&t=promoted&o=category |
| Full analysis: | https://app.any.run/tasks/004eaa5d-41c5-461b-917e-07507aebbe49 |
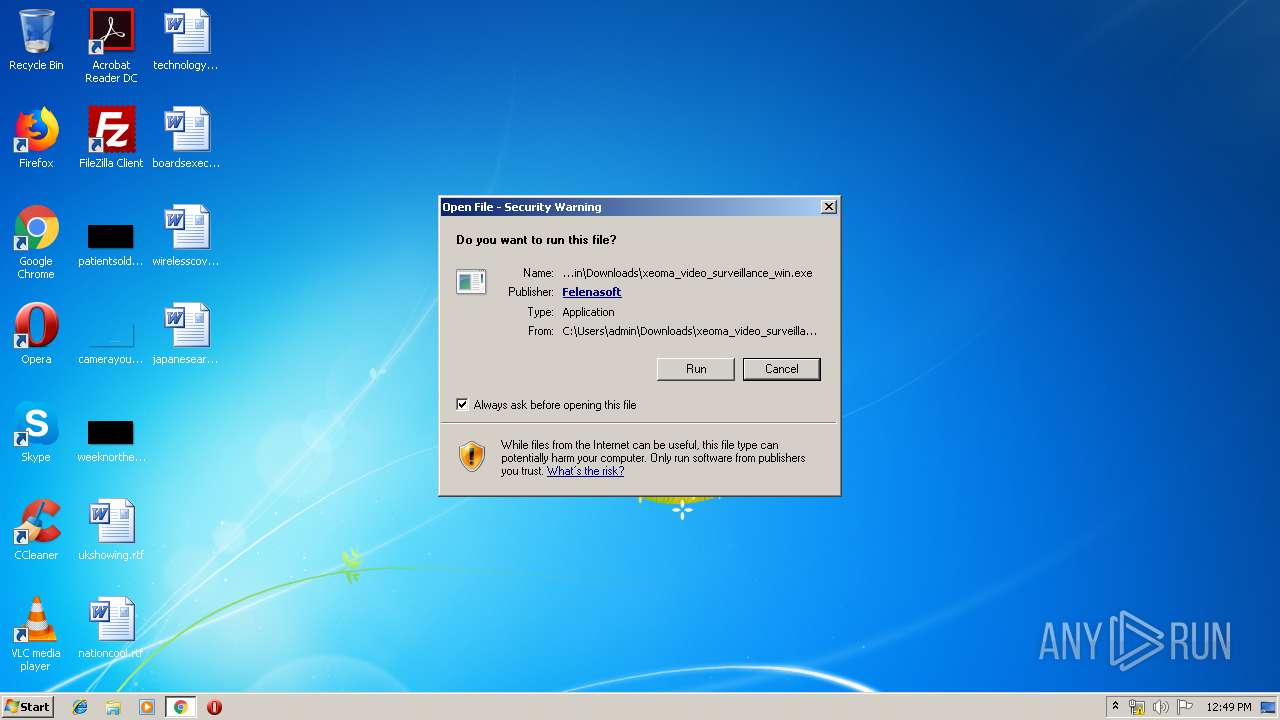
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 11:48:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AFB4E96362C7ACE989491FD9FF1B287F |
| SHA1: | 9698D201D07690DD84D933CBA39A0D67EB36F86C |
| SHA256: | 2EA249C1F92F7D8713C6050999E195E08F0220C04D1D84B27868EC5048701BC0 |
| SSDEEP: | 3:N8DSLavNV2aeEX4UWmWA:2OLU0pUWmWA |
MALICIOUS
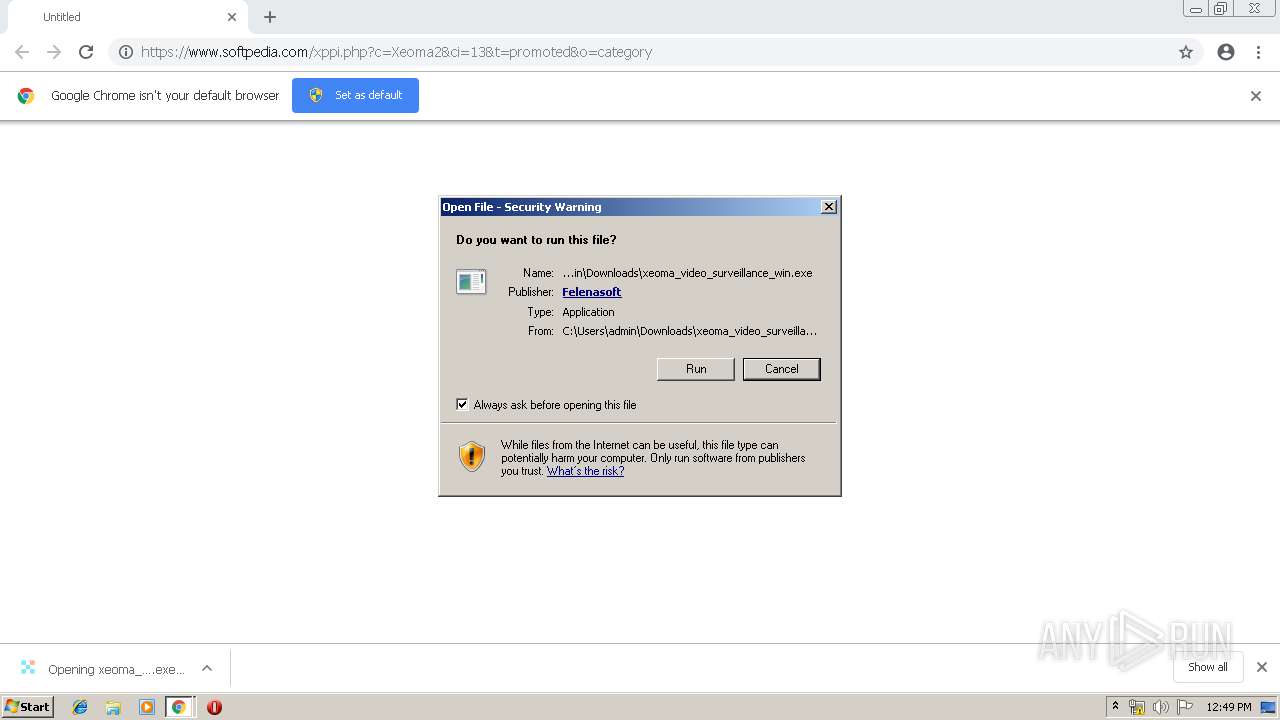
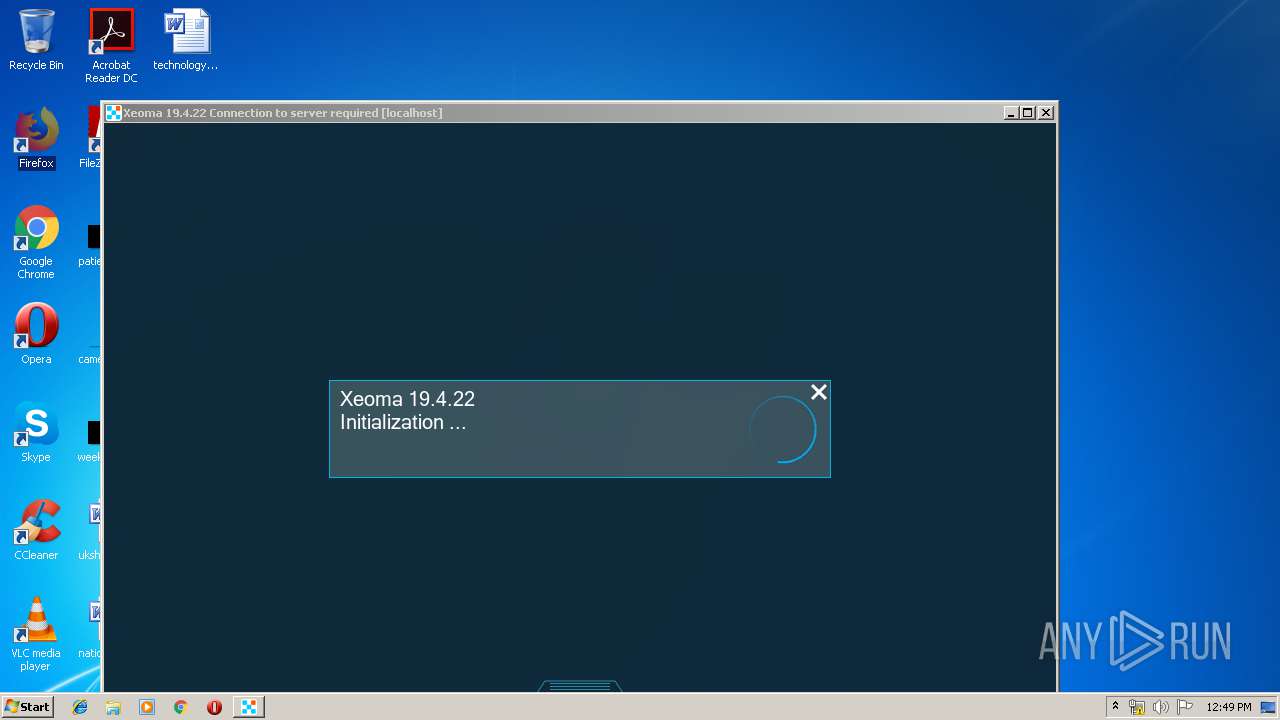
Application was dropped or rewritten from another process
- xeoma_video_surveillance_win.exe (PID: 2472)
- ffmpeg_213_180827.exe (PID: 1736)
Loads dropped or rewritten executable
- xeoma_video_surveillance_win.exe (PID: 2472)
- SearchProtocolHost.exe (PID: 2880)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 1560)
- xeoma_video_surveillance_win.exe (PID: 2472)
Creates files in the user directory
- xeoma_video_surveillance_win.exe (PID: 2472)
Cleans NTFS data-stream (Zone Identifier)
- xeoma_video_surveillance_win.exe (PID: 2472)
INFO
Application launched itself
- chrome.exe (PID: 1560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
11
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 1560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://www.softpedia.com/xppi.php?c=Xeoma2&ci=13&t=promoted&o=category | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | |
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 73.0.3683.75 | ||||
| 2468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f470f18,0x6f470f28,0x6f470f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 | ||||
| 3080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=308 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 | ||||
| 2384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=896,5107016037755300955,10787511397607013996,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3781167887436248596 --mojo-platform-channel-handle=988 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 | ||||
| 3740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=896,5107016037755300955,10787511397607013996,131072 --enable-features=PasswordImport --service-pipe-token=1353520890093854354 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1353520890093854354 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2016 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 | ||||
| 2188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=896,5107016037755300955,10787511397607013996,131072 --enable-features=PasswordImport --service-pipe-token=754424129531686178 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=754424129531686178 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2036 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 | ||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=896,5107016037755300955,10787511397607013996,131072 --enable-features=PasswordImport --service-pipe-token=11289035891086592568 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11289035891086592568 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 | ||||
| 2936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=896,5107016037755300955,10787511397607013996,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10376973764119458399 --mojo-platform-channel-handle=3544 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 | ||||
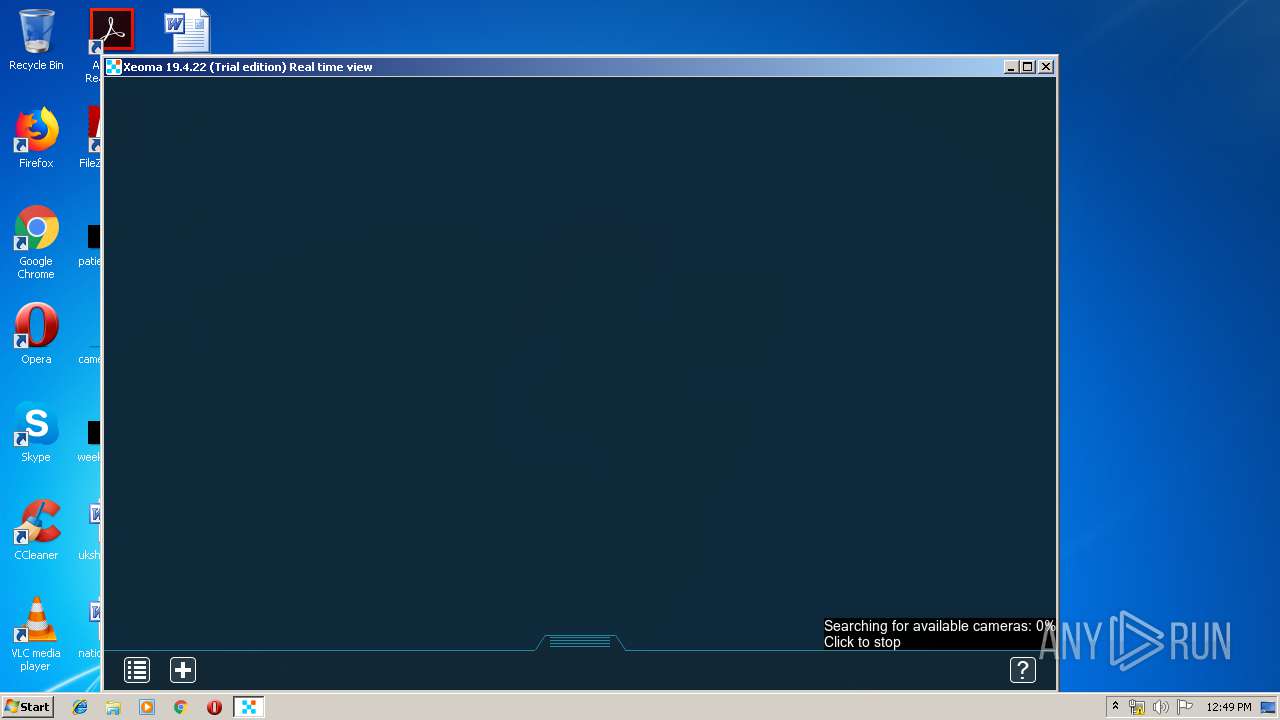
| 2472 | "C:\Users\admin\Downloads\xeoma_video_surveillance_win.exe" | C:\Users\admin\Downloads\xeoma_video_surveillance_win.exe | chrome.exe | |
User: admin Integrity Level: MEDIUM | ||||
| 1736 | "C:\Users\Public\Documents\Xeoma\Additional\ffmpeg_213_180827.exe" -crash_log_file "C:\Users\Public\Documents\Xeoma\Logs\FFmpeg\41991227_ffmpeg_trace.log" -loglevel quiet -encoders | C:\Users\Public\Documents\Xeoma\Additional\ffmpeg_213_180827.exe | — | xeoma_video_surveillance_win.exe |
User: admin Integrity Level: MEDIUM Exit code: 0 | ||||
Total events
874
Read events
819
Write events
0
Delete events
0
Modification events
Executable files
6
Suspicious files
41
Text files
66
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\28852bb1-d462-4390-b63e-a29e6faead8b.tmp | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
20
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1560 | chrome.exe | GET | 302 | 216.58.206.2:80 | http://adclick.g.doubleclick.net/pcs/click?xai=AKAOjsvh_WdPqw3_zNr4cBxekDhRLmmDO1cJQkzmO3ah_czCY4rB9IGuurP3zSf-woK_I-LUw2iGCMGgVg7-ZPdnd3gEcMUwotjQPnBbe0wwLHQyTRAczSm4U6fQMC-a-AyJHfBB4XEHhy6nd8iveVqizsZNkvGZYs_tn0g_rhJL1aMXrO36kqejFotFpvULDIyanVjHFedlEuZeRjZKyyMT_H07qTYzCv45bVUwZis3rUVpJfp_h7HbveunQjRJIWY1XC2tXIBfoJ6uZ4fjbFgHA_FkQ9Lw_xrtqL0&sig=Cg0ArKJSzMoEIHTWbX6k&adurl=https://felenasoft.com/xeoma/downloads/xeoma_video_surveillance_win.exe%3Fsrc%3Dsoftpedia | US | — | — | whitelisted |
1560 | chrome.exe | GET | 302 | 172.217.16.130:80 | http://pubads.g.doubleclick.net/gampad/clk?id=5046993530&iu=/1004334/Softpedia_PPD_ClickOnly_Unit/PPD_Xeoma2_32bit | US | — | — | whitelisted |
2472 | xeoma_video_surveillance_win.exe | GET | — | 144.76.74.35:80 | http://version.xeoma.com/?v=19.4.22&f=19.04.25&is=0&os=win32.6.1.7601&i=3f5dede654&l=en&e=trial&m=0 | DE | — | — | unknown |
1560 | chrome.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.6 Kb | whitelisted |
2472 | xeoma_video_surveillance_win.exe | GET | 200 | 144.76.74.35:80 | http://felenasoft.com/xeoma/downloads/version3.xml | DE | text | 1.42 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1560 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1560 | chrome.exe | 172.217.16.130:80 | pubads.g.doubleclick.net | Google Inc. | US | whitelisted |
1560 | chrome.exe | 184.172.133.98:443 | felenasoft.com | SoftLayer Technologies Inc. | US | unknown |
1560 | chrome.exe | 216.58.206.2:80 | adclick.g.doubleclick.net | Google Inc. | US | whitelisted |
1560 | chrome.exe | 64.225.158.192:443 | www.softpedia.com | Peer 1 Network (USA) Inc. | CA | unknown |
1560 | chrome.exe | 74.125.133.106:443 | www.google.com | Google Inc. | US | unknown |
1560 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
1560 | chrome.exe | 64.225.158.190:443 | www.softpedia.com | Peer 1 Network (USA) Inc. | CA | unknown |
1560 | chrome.exe | 74.125.133.104:443 | www.google.com | Google Inc. | US | whitelisted |
1560 | chrome.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.softpedia.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
pubads.g.doubleclick.net |
| whitelisted |
adclick.g.doubleclick.net |
| whitelisted |
felenasoft.com |
| unknown |
www.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |