| File name: | vulkan-1.dll |
| Full analysis: | https://app.any.run/tasks/bce10485-d492-48b2-87e0-a15b2ede8303 |
| Verdict: | Suspicious activity |
| Analysis date: | November 26, 2020, 17:01:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (DLL) (console) x86-64, for MS Windows |
| MD5: | 2BB8BB231934119F706A6504A0A3CBCA |
| SHA1: | 7917F97953703068C3ED5C75E4BCD5362A7B72BA |
| SHA256: | 2E9F4BA88DA92D3B424281FC8DB8F5284BE00779E4357E3FA5FF8D1979E0A7B3 |
| SSDEEP: | 6144:1BfJZP+T/fyZvVNKmizRn53JGJKkDXXCQ972K6sZZAwS6R1Rog2Zvs3j0ZgiDW3N:bffmTnSdTizRnfGJVTV2n695oXC |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 2008)
INFO
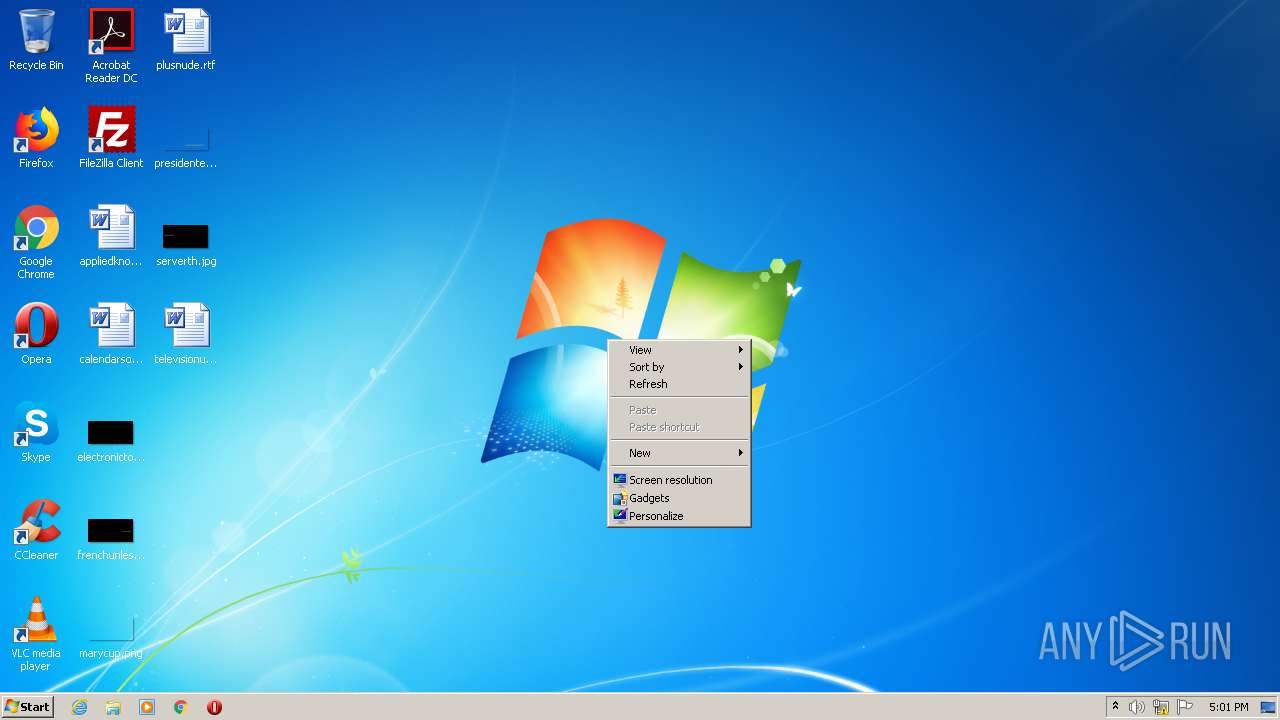
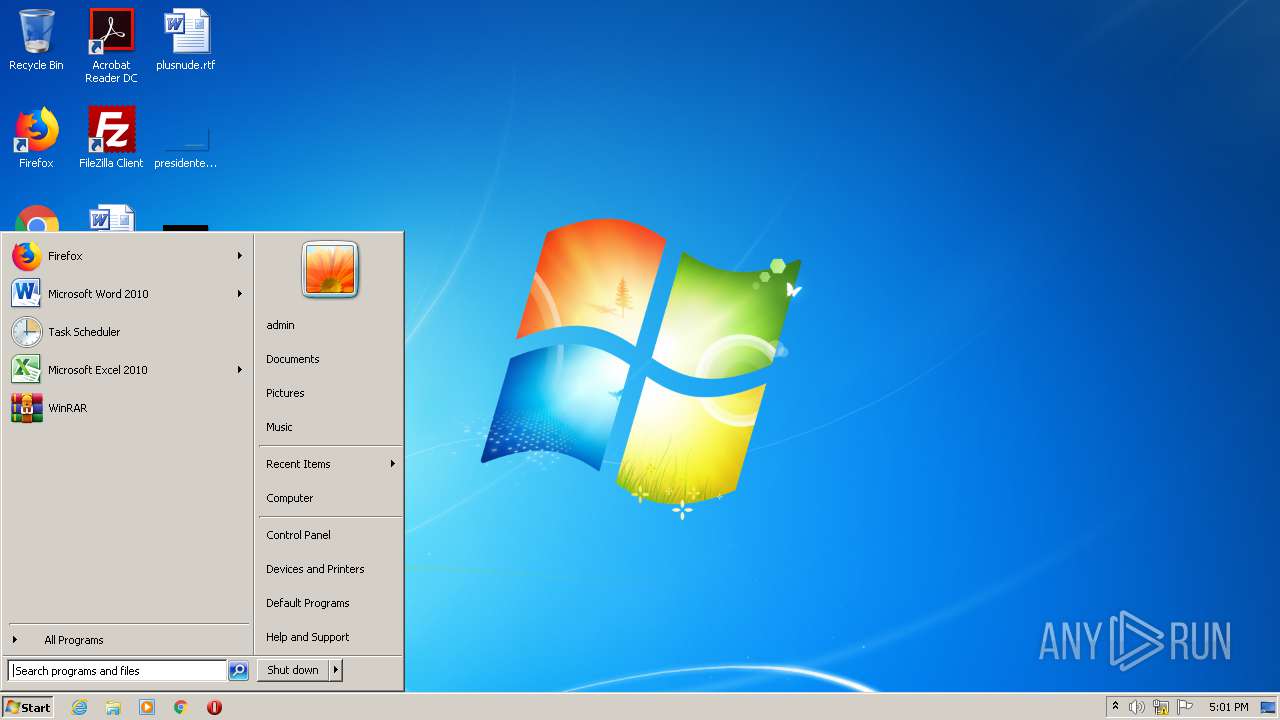
Manual execution by user
- opera.exe (PID: 376)
Creates files in the user directory
- opera.exe (PID: 376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2020:09:29 08:17:37+02:00 |
| PEType: | PE32+ |
| LinkerVersion: | 14 |
| CodeSize: | 434688 |
| InitializedDataSize: | 186880 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x42c20 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_AMD64 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 29-Sep-2020 06:17:37 |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0078 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0x0000 |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x0000 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000078 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_AMD64 |
| Number of sections: | 7 |
| Time date stamp: | 29-Sep-2020 06:17:37 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00F0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0006A046 | 0x0006A200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.38957 |
.rdata | 0x0006C000 | 0x00025A94 | 0x00025C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.66389 |
.data | 0x00092000 | 0x00004B7C | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.76221 |
.pdata | 0x00097000 | 0x00004D70 | 0x00004E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.80329 |
.00cfg | 0x0009C000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.195869 |
.tls | 0x0009D000 | 0x00000015 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.reloc | 0x0009E000 | 0x00000D18 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.31613 |
Imports
ADVAPI32.dll |
CFGMGR32.dll |
KERNEL32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
0 | 0x00000000 | |
vkAcquireNextImage2KHR | 1 | 0x0002726E |
vkAcquireNextImageKHR | 2 | 0x0002674D |
vkAllocateCommandBuffers | 3 | 0x0001EE9B |
vkAllocateDescriptorSets | 4 | 0x0001EE0C |
vkAllocateMemory | 5 | 0x0001EB4E |
vkBeginCommandBuffer | 6 | 0x0001EEF1 |
vkBindBufferMemory | 7 | 0x0001EB94 |
vkBindBufferMemory2 | 8 | 0x0001F899 |
vkBindImageMemory | 9 | 0x0001EB9E |
Total processes
39
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
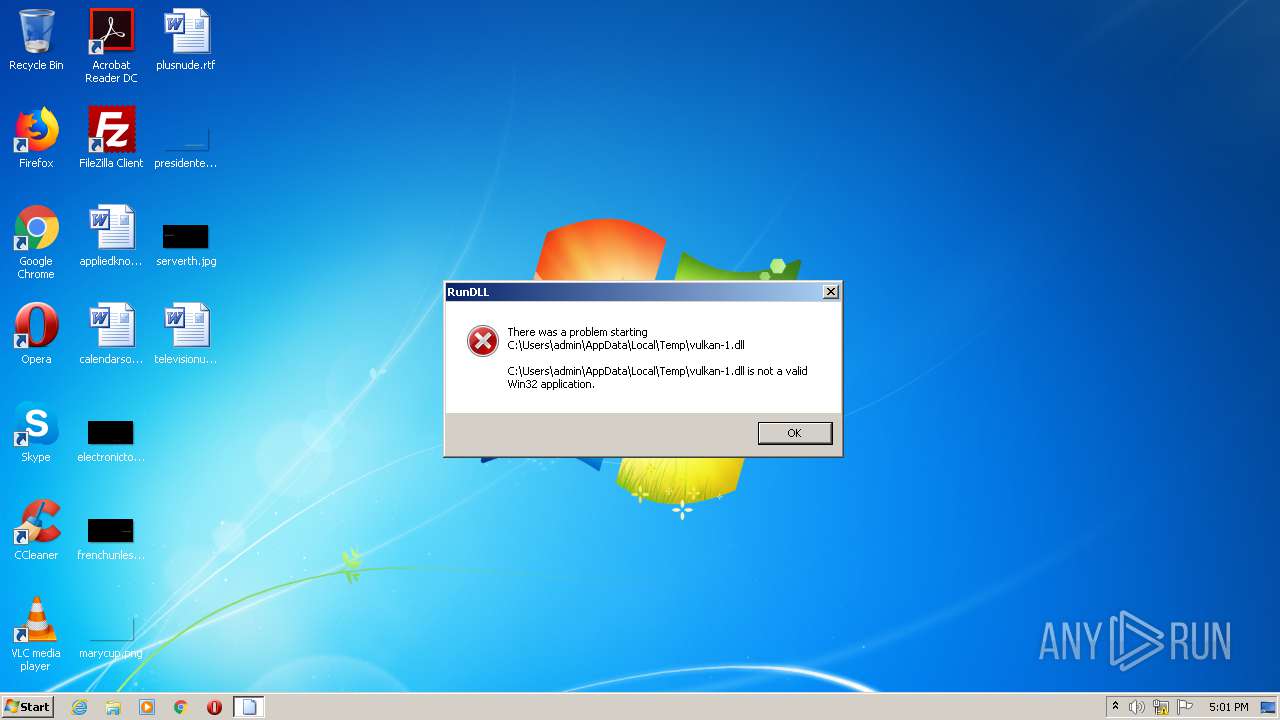
| 896 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\vulkan-1.dll", vkAcquireNextImage2KHR | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2008 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
303
Read events
189
Write events
114
Delete events
0
Modification events
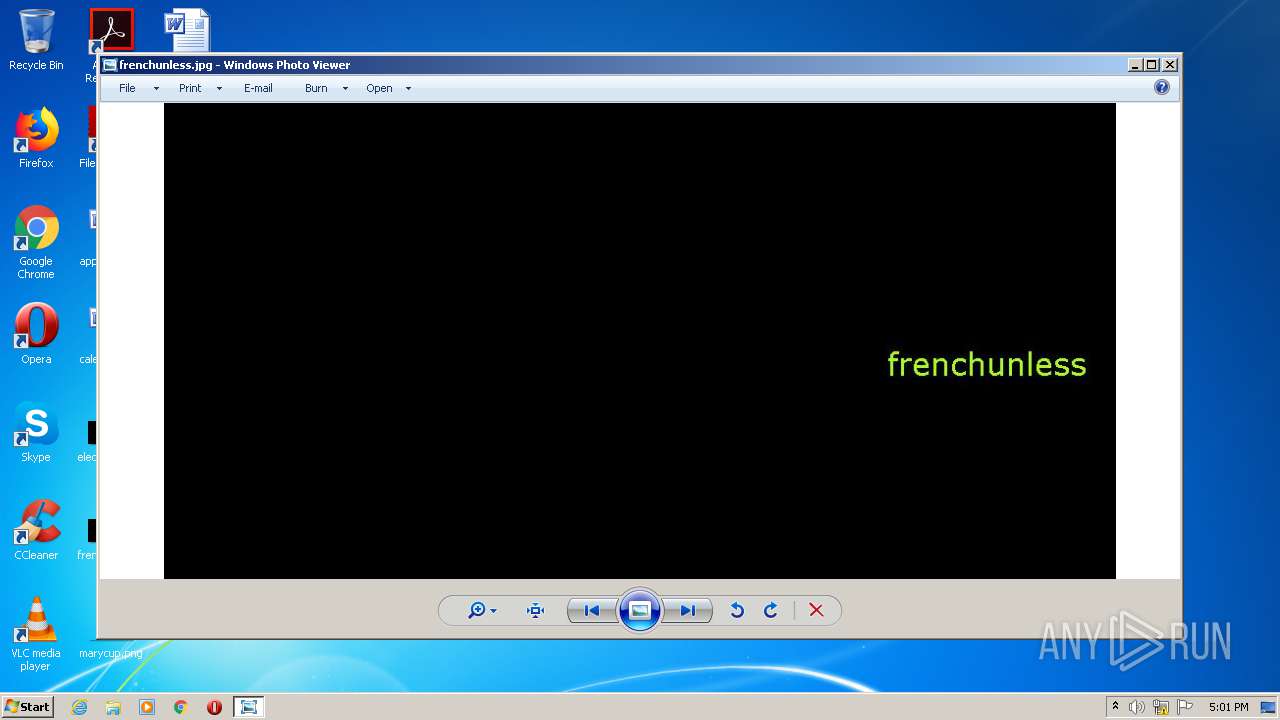
| (PID) Process: | (2008) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (2008) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 6000000034000000A00400008002000000000000 | |||
| (PID) Process: | (376) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (376) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
34
Text files
9
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 376 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprED76.tmp | — | |
MD5:— | SHA256:— | |||
| 376 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprED97.tmp | — | |
MD5:— | SHA256:— | |||
| 376 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | — | |
MD5:— | SHA256:— | |||
| 376 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\LRLPK00D4N9VOLHWLZS5.temp | — | |
MD5:— | SHA256:— | |||
| 376 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\VFS68J6M8W2QWY58BOC6.temp | — | |
MD5:— | SHA256:— | |||
| 376 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr1033.tmp | — | |
MD5:— | SHA256:— | |||
| 376 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr1044.tmp | — | |
MD5:— | SHA256:— | |||
| 376 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr1045.tmp | — | |
MD5:— | SHA256:— | |||
| 376 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 376 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
376 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
376 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
376 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |