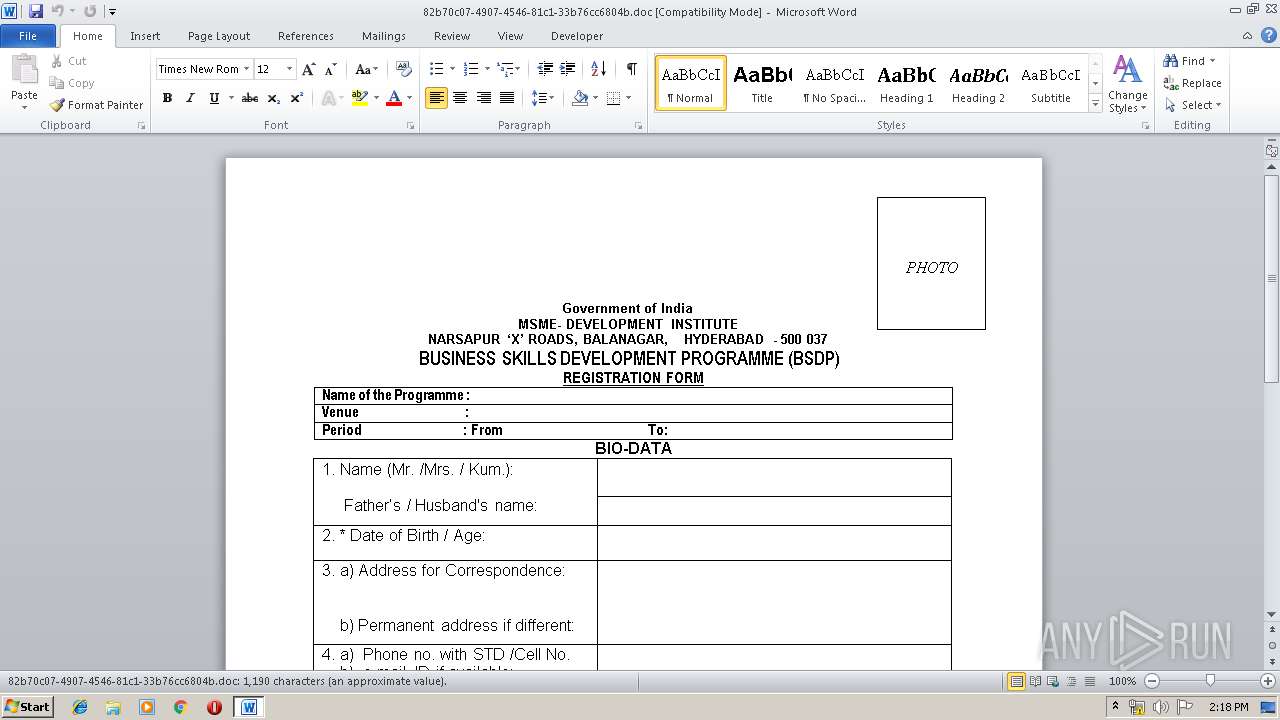
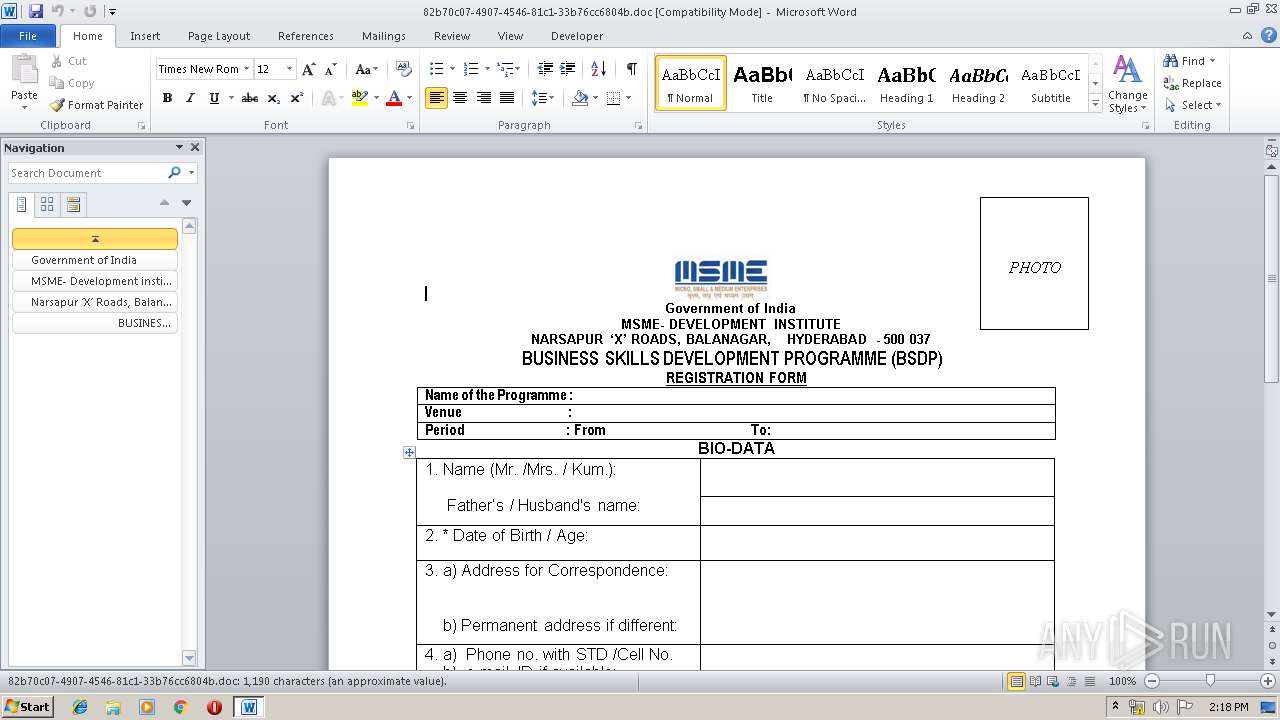
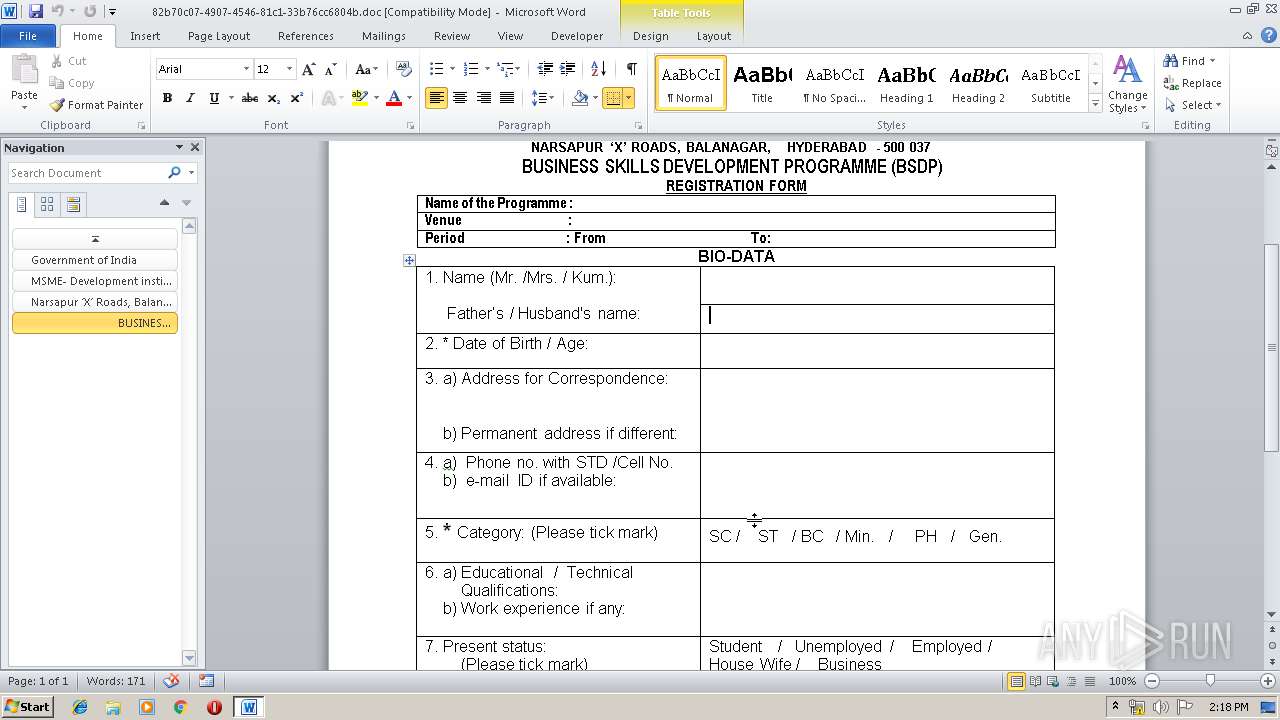
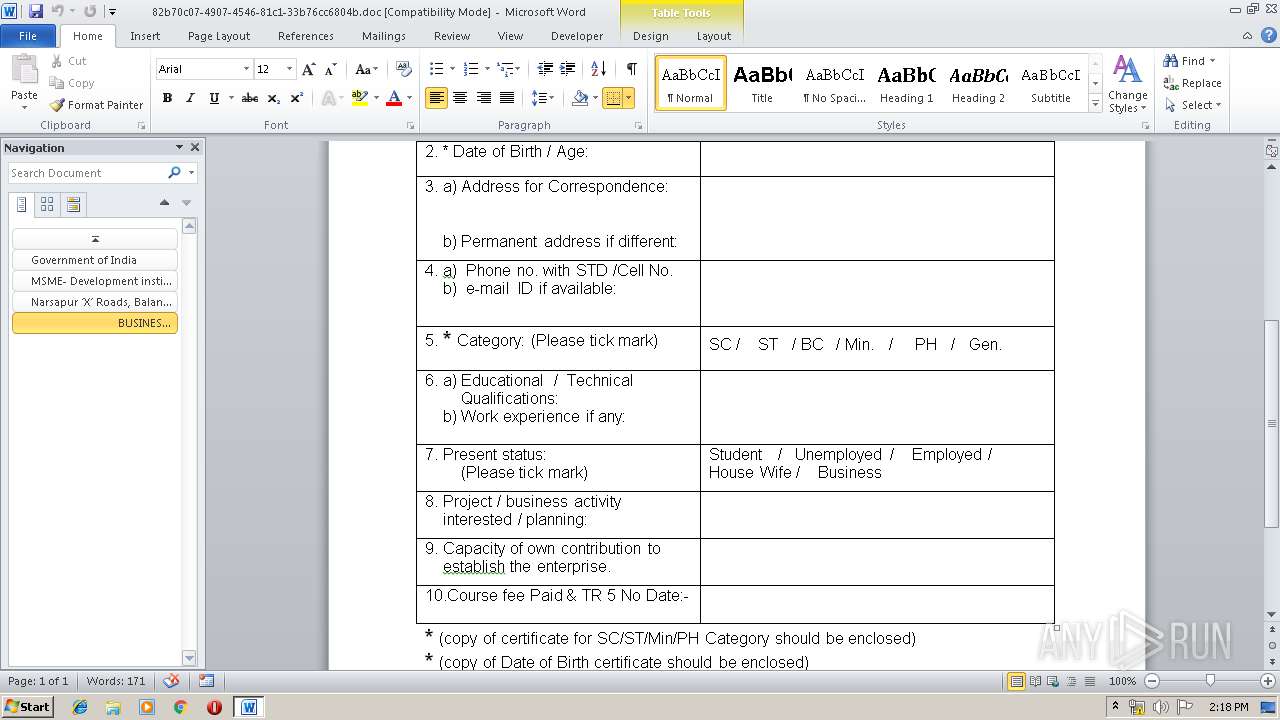
| download: | Appln%20Form%20for%20BSDP.doc |
| Full analysis: | https://app.any.run/tasks/a4091824-350d-4304-a67f-380f10d5862b |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 14:18:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 5.1, Code page: 1252, Author: Temp, Template: Normal, Last Saved By: ZENITH, Revision Number: 6, Name of Creating Application: Microsoft Office Word, Total Editing Time: 02:00, Create Time/Date: Tue Aug 3 08:16:00 2010, Last Saved Time/Date: Tue Aug 3 08:17:00 2010, Number of Pages: 1, Number of Words: 215, Number of Characters: 1228, Security: 0 |
| MD5: | 40B274B3D988521664689BE95A5D682A |
| SHA1: | B7CA1CD1F78EC896E4F971E65E97563959FA3061 |
| SHA256: | 2E9BC84CCF212E9ABEA8FCA41C2E6BB04B50B679165BB3E8C7BA0DACDFE66BA0 |
| SSDEEP: | 1536:eB71OP5xWJon+1xzEoPzlhUjefmi93pfgo399:eTn1xdp1N |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3356)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2712)
Application launched itself
- chrome.exe (PID: 3356)
Creates files in the user directory
- WINWORD.EXE (PID: 2712)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Temp |
| Keywords: | - |
| Comments: | - |
| Template: | Normal |
| LastModifiedBy: | ZENITH |
| RevisionNumber: | 6 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 2.0 minutes |
| CreateDate: | 2010:08:03 07:16:00 |
| ModifyDate: | 2010:08:03 07:17:00 |
| Pages: | 1 |
| Words: | 215 |
| Characters: | 1228 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 10 |
| Paragraphs: | 2 |
| CharCountWithSpaces: | 1441 |
| AppVersion: | 12 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 39 |
| CompObjUserType: | Microsoft Office Word 97-2003 Document |
Total processes
54
Monitored processes
24
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,6852636137447332447,3856167225378138348,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5453989604312875973 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5453989604312875973 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3788 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,6852636137447332447,3856167225378138348,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3031711415094130926 --mojo-platform-channel-handle=3356 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=948,6852636137447332447,3856167225378138348,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10680783741658865570 --mojo-platform-channel-handle=968 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,6852636137447332447,3856167225378138348,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9795887753248514905 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9795887753248514905 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3552 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,6852636137447332447,3856167225378138348,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5021454924972493952 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5021454924972493952 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2872 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,6852636137447332447,3856167225378138348,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5170757014305800580 --mojo-platform-channel-handle=1520 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=948,6852636137447332447,3856167225378138348,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6780648996753394173 --mojo-platform-channel-handle=4184 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,6852636137447332447,3856167225378138348,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3302493305255174001 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3302493305255174001 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2204 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2712 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\82b70c07-4907-4546-81c1-33b76cc6804b.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,6852636137447332447,3856167225378138348,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12056547506478896113 --mojo-platform-channel-handle=3132 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 023
Read events
895
Write events
115
Delete events
13
Modification events
| (PID) Process: | (2712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | d6: |
Value: 64363A00980A0000010000000000000000000000 | |||
| (PID) Process: | (2712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2712) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1316290590 | |||
| (PID) Process: | (2712) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1316290704 | |||
| (PID) Process: | (2712) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1316290705 | |||
| (PID) Process: | (2712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 980A0000E825B6FDF0DFD40100000000 | |||
| (PID) Process: | (2712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | n7: |
Value: 6E373A00980A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | n7: |
Value: 6E373A00980A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
172
Text files
202
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2712 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRFA64.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2712 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF954BC8F36E5F5639.TMP | — | |
MD5:— | SHA256:— | |||
| 2712 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{705A4D71-14AB-4AB2-9F9C-6E93EE9A4B4E}.tmp | — | |
MD5:— | SHA256:— | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e7be01f2-9752-4ef0-a73a-bd500e280fda.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
127
DNS requests
87
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2568 | chrome.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
2568 | chrome.exe | GET | 200 | 173.194.183.103:80 | http://r2---sn-aigl6nek.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=194.187.251.125&mm=28&mn=sn-aigl6nek&ms=nvh&mt=1553177844&mv=m&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2568 | chrome.exe | GET | 302 | 172.217.23.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 506 b | whitelisted |
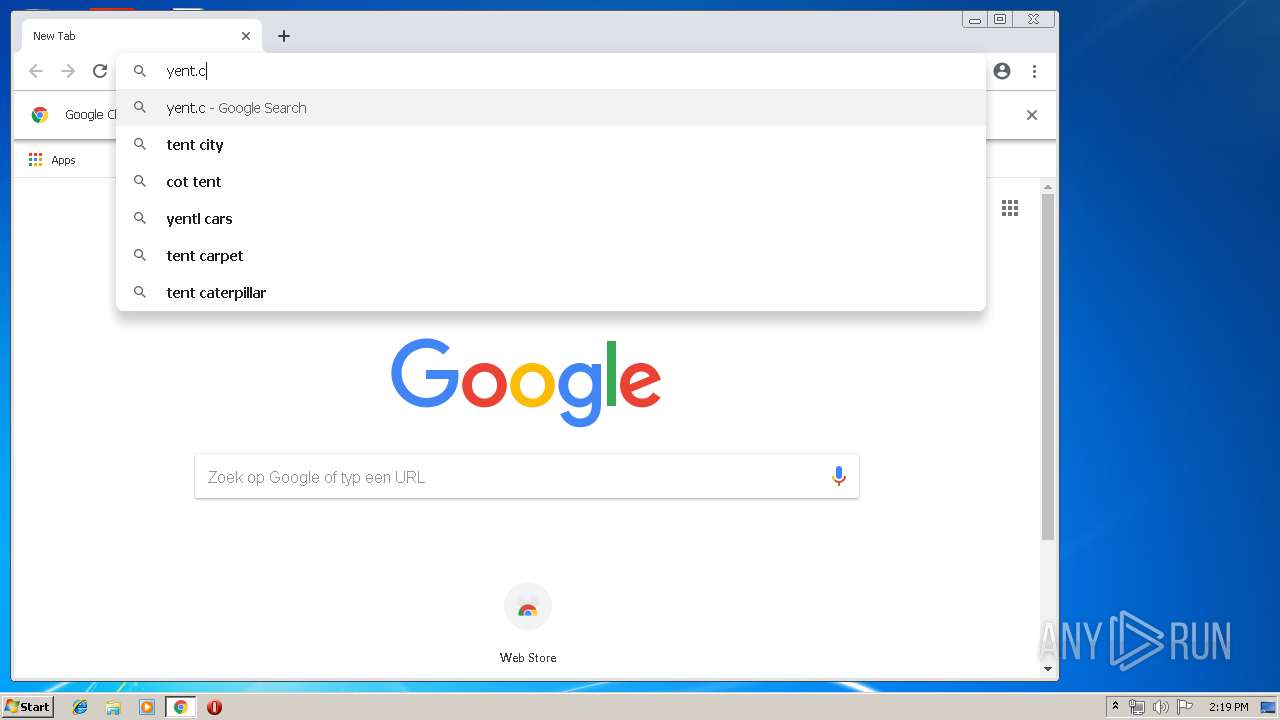
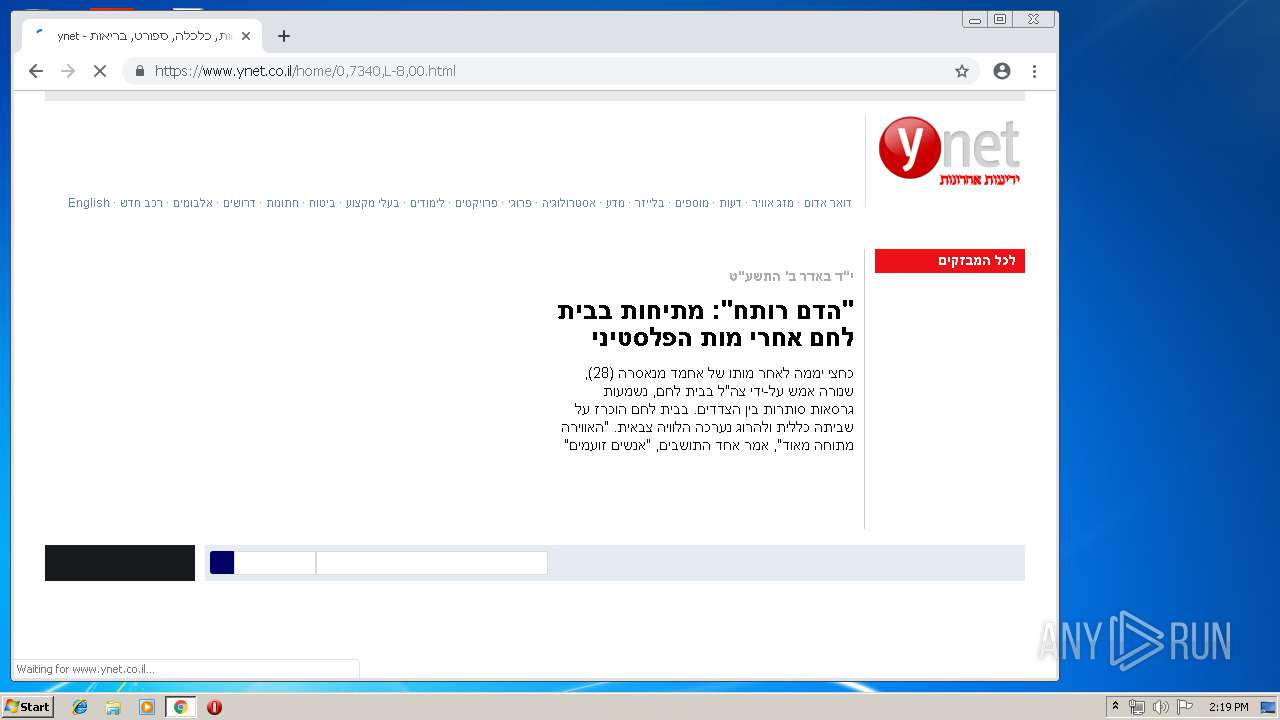
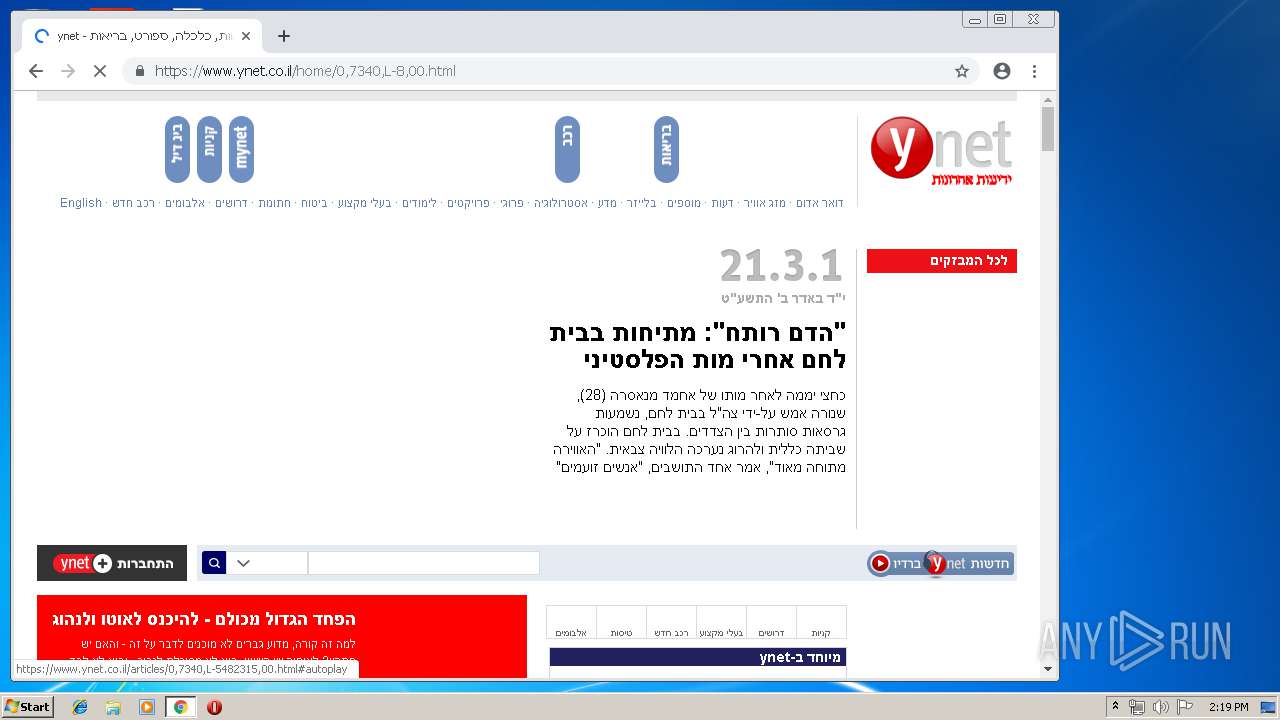
2568 | chrome.exe | GET | 301 | 2.18.235.16:80 | http://www.ynet.co.il/ | unknown | — | — | whitelisted |
2568 | chrome.exe | GET | 302 | 92.122.254.83:80 | http://ynet.co.il/ | unknown | — | — | unknown |
2568 | chrome.exe | GET | 200 | 204.13.202.71:80 | http://ssl.trustwave.com/issuers/STCA.crt | US | der | 956 b | whitelisted |
2568 | chrome.exe | GET | 200 | 13.32.222.120:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2568 | chrome.exe | 216.58.207.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
2568 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
2568 | chrome.exe | 172.217.23.174:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2568 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2568 | chrome.exe | 173.194.183.103:80 | r2---sn-aigl6nek.gvt1.com | Google Inc. | US | whitelisted |
2568 | chrome.exe | 92.122.254.83:80 | ynet.co.il | GTT Communications Inc. | — | unknown |
2568 | chrome.exe | 2.18.235.16:80 | www.ynet.co.il | Akamai International B.V. | — | whitelisted |
2568 | chrome.exe | 104.25.232.13:443 | www.promisejs.org | Cloudflare Inc | US | shared |
2568 | chrome.exe | 104.109.74.252:443 | totalmedia2.ynet.co.il | Akamai International B.V. | NL | whitelisted |
2568 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
r2---sn-aigl6nek.gvt1.com |
| whitelisted |
apis.google.com |
| whitelisted |
ynet.co.il |
| unknown |