| File name: | 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1 |
| Full analysis: | https://app.any.run/tasks/ef1a09e2-ea44-407f-9421-782b6c387277 |
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2024, 06:29:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | AB04C42B9999645A9BC5B11F2D7AC559 |
| SHA1: | 1CBB96C749CB3EA02F6094574B81D6B992CE5019 |
| SHA256: | 2E98AF1B2D63E065FF0A69593A045FCD3E94E616D2F2822D82252B35E2FDCDA1 |
| SSDEEP: | 98304:YXjqWXLotZqnk0OBjHkvi7SKY30Pp1YJj0/op1gU9QNPelDwMdqpSmtLe98Moj7r:mOj4pdm4O2+P |
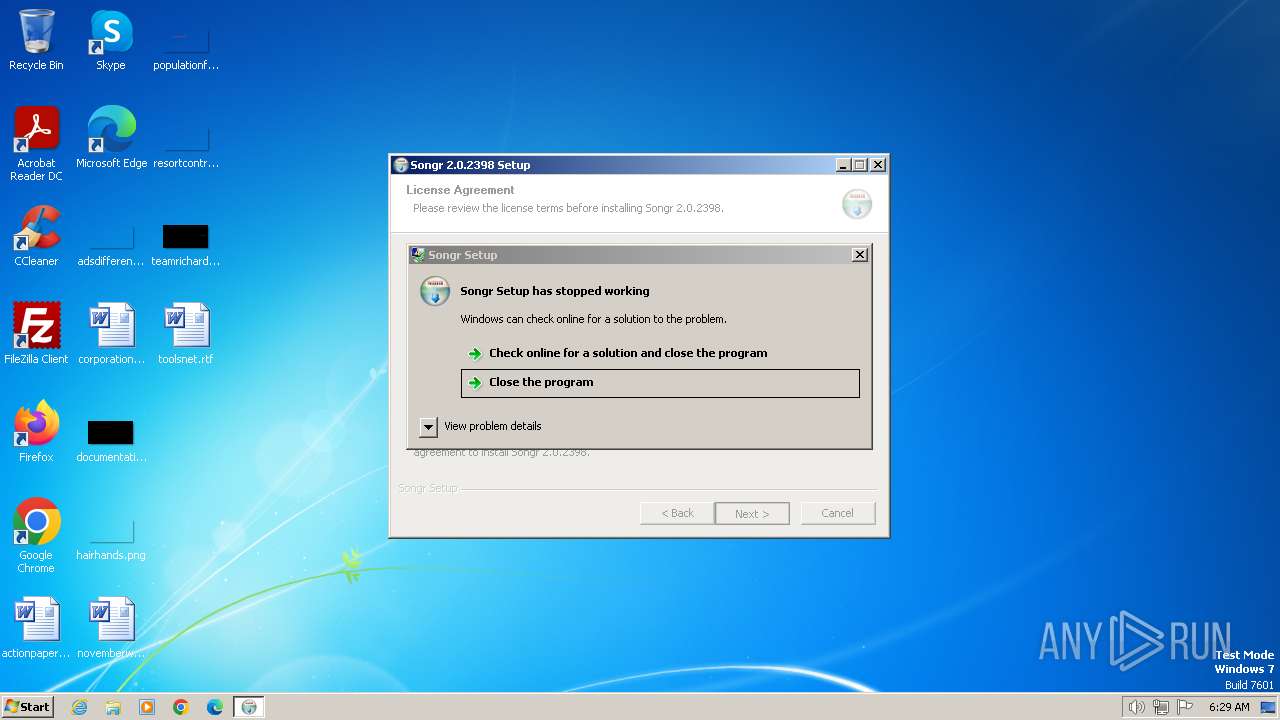
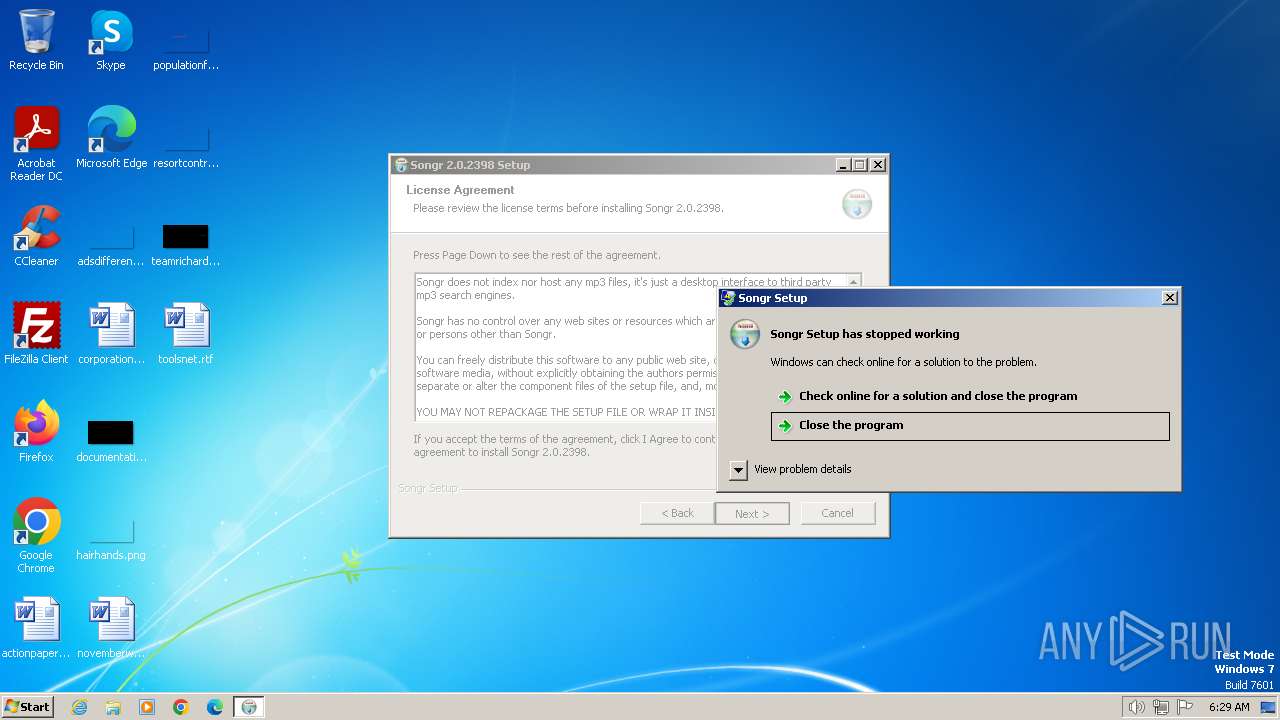
MALICIOUS
Drops the executable file immediately after the start
- 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe (PID: 3864)
- 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe (PID: 2848)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe (PID: 2848)
Application launched itself
- 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe (PID: 3864)
Executable content was dropped or overwritten
- 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe (PID: 3864)
- 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe (PID: 2848)
The process creates files with name similar to system file names
- 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe (PID: 2848)
Reads the Internet Settings
- 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe (PID: 2848)
Reads security settings of Internet Explorer
- 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe (PID: 2848)
INFO
Checks supported languages
- 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe (PID: 3864)
- 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe (PID: 2848)
Reads the computer name
- 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe (PID: 3864)
- 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe (PID: 2848)
Process checks whether UAC notifications are on
- 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe (PID: 3864)
Create files in a temporary directory
- 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe (PID: 3864)
- 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe (PID: 2848)
Reads the machine GUID from the registry
- 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe (PID: 2848)
Checks proxy server information
- 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe (PID: 2848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 22:50:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
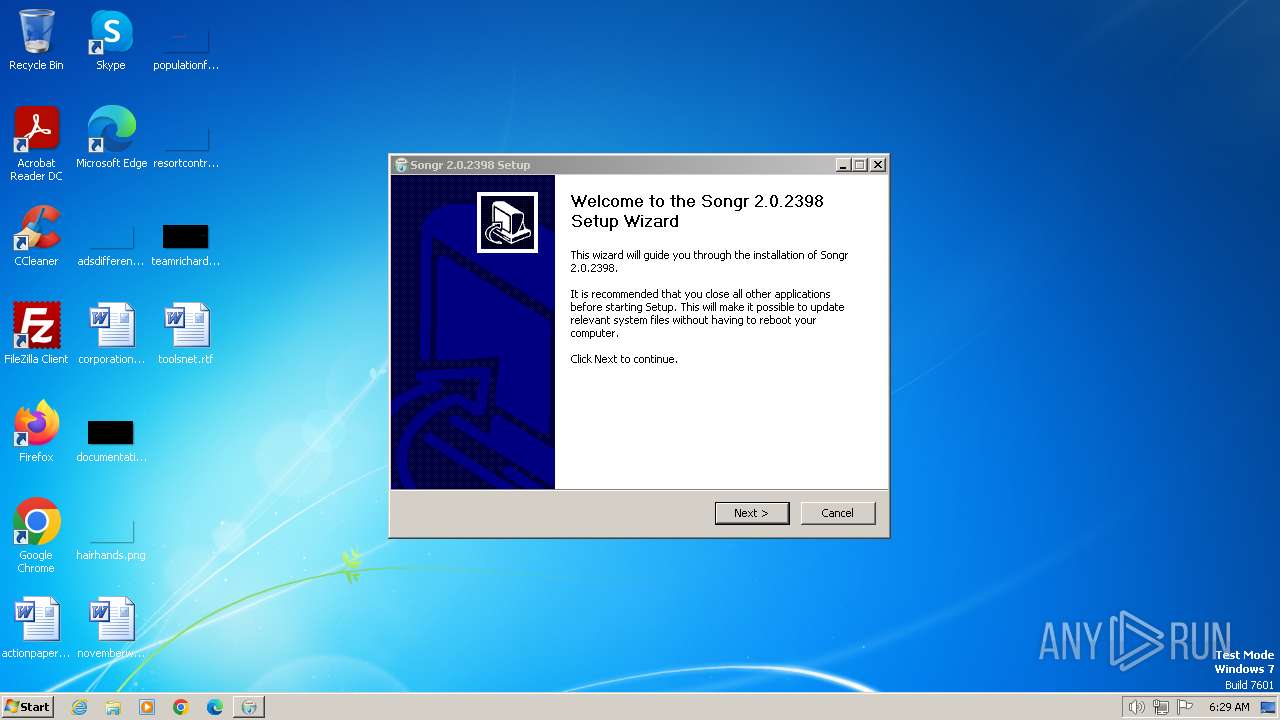
| FileVersionNumber: | 2.0.2398.0 |
| ProductVersionNumber: | 2.0.2398.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Xamasoft |
| FileDescription: | Songr Setup |
| FileVersion: | 2.0.2398.0 |
| LegalCopyright: | © 2009-2012 at-my-window.blogspot.com |
| OriginalFileName: | Songr_2_0_2398_Setup.exe |
| ProductDescription: | Songr Setup |
| ProductName: | Songr |
| ProductVersion: | 2.0.2398.0 (f3277505763a) |
Total processes
44
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2848 | "C:\Users\admin\AppData\Local\Temp\2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe" /UAC:12019C /NCRC | C:\Users\admin\AppData\Local\Temp\2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | ||||||||||||
User: admin Company: Xamasoft Integrity Level: HIGH Description: Songr Setup Exit code: 3221225477 Version: 2.0.2398.0 Modules
| |||||||||||||||
| 3864 | "C:\Users\admin\AppData\Local\Temp\2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe" | C:\Users\admin\AppData\Local\Temp\2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | explorer.exe | ||||||||||||
User: admin Company: Xamasoft Integrity Level: MEDIUM Description: Songr Setup Exit code: 3221225477 Version: 2.0.2398.0 Modules
| |||||||||||||||
Total events
5 172
Read events
5 129
Write events
34
Delete events
9
Modification events
| (PID) Process: | (2848) 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2848) 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (2848) 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (2848) 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (2848) 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
| (PID) Process: | (2848) 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005C010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2848) 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2848) 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2848) 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2848) 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
10
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2848 | 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | C:\Users\admin\AppData\Local\Temp\nshF88B.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
| 2848 | 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | C:\Users\admin\AppData\Local\Temp\nshF88B.tmp\UAC.dll | executable | |
MD5:88AD3FD90FC52AC3EE0441A38400A384 | SHA256:E58884695378CF02715373928BB8ADE270BAF03144369463F505C3B3808CBC42 | |||
| 2848 | 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | C:\Users\admin\AppData\Local\Temp\nshF88B.tmp\md5dll.dll | executable | |
MD5:0745FF646F5AF1F1CDD784C06F40FCE9 | SHA256:FBED2F1160469F42CE97C33AD558201B2B43E3020257F9B2259E3CE295317A70 | |||
| 2848 | 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | C:\Users\admin\AppData\Local\Temp\nshF88B.tmp\Banner.dll | executable | |
MD5:0116A50101C4107A138A588D1E46FCA5 | SHA256:AB80CF45070D936F0745F5E39B22E6E07BA90AA179B5EC4469EF6E2CB1B9EF6B | |||
| 2848 | 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | C:\Users\admin\AppData\Local\Temp\nshF88B.tmp\nsProcess.dll | executable | |
MD5:05450FACE243B3A7472407B999B03A72 | SHA256:95FE9D92512FF2318CC2520311EF9145B2CEE01209AB0E1B6E45C7CE1D4D0E89 | |||
| 2848 | 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | C:\Users\admin\AppData\Local\Temp\nshF88B.tmp\inetc.dll | executable | |
MD5:D7A3FA6A6C738B4A3C40D5602AF20B08 | SHA256:67EFF17C53A78C8EC9A28F392B9BB93DF3E74F96F6ECD87A333A482C36546B3E | |||
| 2848 | 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | C:\Users\admin\AppData\Local\Temp\nshF88B.tmp\xml.dll | executable | |
MD5:42DF1FBAA87567ADF2B4050805A1A545 | SHA256:E900FCB9D598643EB0EE3E4005DA925E73E70DBAA010EDC4473E99EA0638B845 | |||
| 3864 | 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | C:\Users\admin\AppData\Local\Temp\nsbF781.tmp\UAC.dll | executable | |
MD5:88AD3FD90FC52AC3EE0441A38400A384 | SHA256:E58884695378CF02715373928BB8ADE270BAF03144369463F505C3B3808CBC42 | |||
| 2848 | 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | C:\Users\admin\AppData\Local\Temp\nsrF87A.tmp | binary | |
MD5:E20A4F2E8A216290DC521E6C5B066237 | SHA256:41E3507B6DFF20108865658BEBA3C16B2B8D816F69E23C6EE428C0FB37EAF196 | |||
| 3864 | 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | C:\Users\admin\AppData\Local\Temp\nslF770.tmp | binary | |
MD5:4ABE6501A8C385A8BA82616843F6BAC2 | SHA256:5F41D61E586FA2850B2C711784A3590973649E8FA4FE753E22959CE9E12FDAB0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
7
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2848 | 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | GET | — | 3.130.253.23:80 | http://bi.bisrv.com/logpinger?event_type=401&installer_source=binsis&software_type=sponsored&muid=05e28309b8d1983aa928469025e49813&client_uid=537845DAD0164D20B62792D2EA4B22E0&affiliate_id=songr&software_id=songr&sponsored_id=&tokyo_csrf2_key=&tokyo_csrf2_timestamp=&slot_number=1&index_in_screen=1&index_in_session=1&bi_cmd_line=0&10283901 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
2848 | 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | 3.130.253.23:80 | bi.bisrv.com | AMAZON-02 | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2848 | 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | 3.130.204.160:80 | bi.bisrv.com | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bi.bisrv.com |
| malicious |
d27foqb3kkzkt9.cloudfront.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2848 | 2e98af1b2d63e065ff0a69593a045fcd3e94e616d2f2822d82252b35e2fdcda1.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |