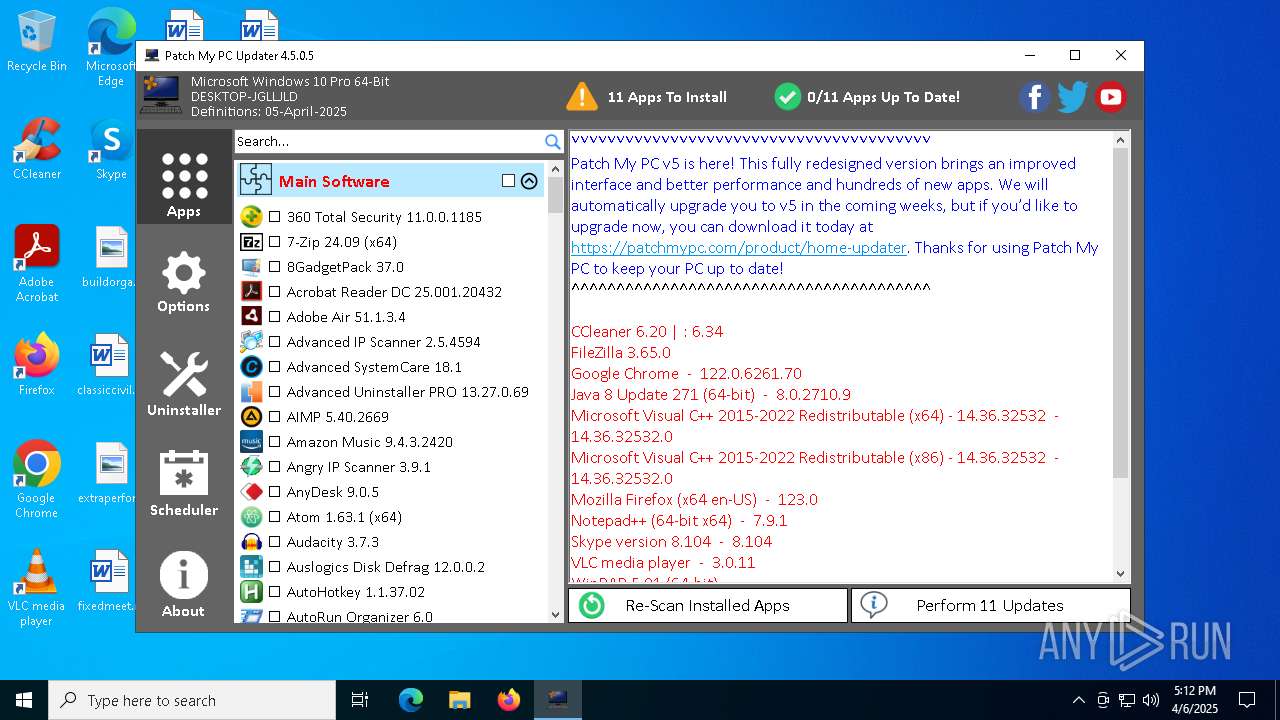
| File name: | PatchMyPC.exe |
| Full analysis: | https://app.any.run/tasks/0c288232-bfc7-42d3-97f2-5a1b1b4a2122 |
| Verdict: | Malicious activity |
| Analysis date: | April 06, 2025, 17:12:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | D82CB08C93ED60168A99727421EE2261 |
| SHA1: | 08EC5D854C07729E4890D81F29BC584451A996DF |
| SHA256: | 2E8B16DA78D2207FD80C77715B6F2F236218D7BE15862194DFEB1DB0F540825E |
| SSDEEP: | 49152:ooirjM+8I5iRo2rU+1+FmPqKmxKLJN+MTEUKKsH0KNC7QjxiiR/:o73iRo24lmSKWKLP+TUeH67Qj8iR/ |
MALICIOUS
GENERIC has been found (auto)
- runas.exe (PID: 1276)
Executing a file with an untrusted certificate
- gacutil.exe (PID: 6028)
Changes the autorun value in the registry
- VC_redist.x64.exe (PID: 2984)
- VC_redist.x86.exe (PID: 4428)
SUSPICIOUS
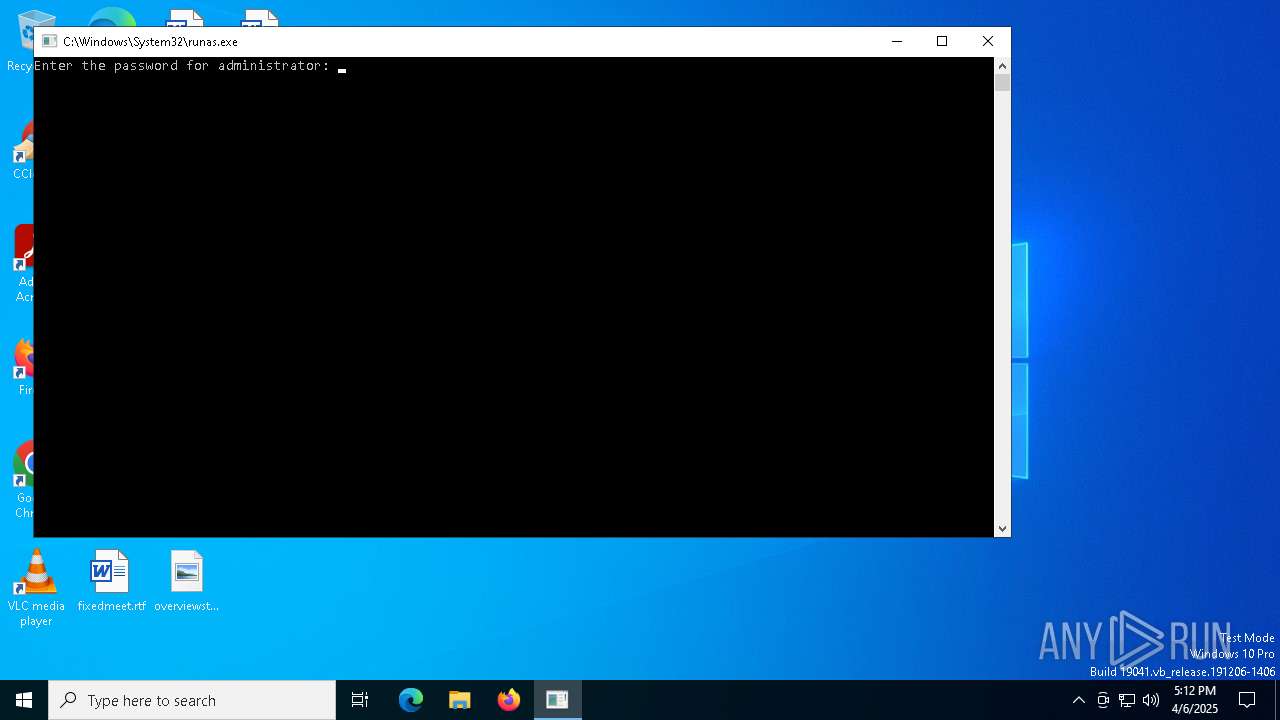
Starts another process probably with elevated privileges via RUNAS.EXE
- runas.exe (PID: 1276)
Reads security settings of Internet Explorer
- PatchMyPC.exe (PID: 744)
- C++ 2022 Redist. 14.42.34438.0 (x64).exe (PID: 2908)
- VC_redist.x64.exe (PID: 8012)
- C++ 2022 Redist. 14.42.34438.0 (x86).exe (PID: 7256)
Process drops legitimate windows executable
- PatchMyPC.exe (PID: 744)
- msiexec.exe (PID: 7820)
- C++ 2022 Redist. 14.42.34438.0 (x86).exe (PID: 8172)
- C++ 2022 Redist. 14.42.34438.0 (x86).exe (PID: 7256)
- VC_redist.x64.exe (PID: 8060)
- VC_redist.x86.exe (PID: 4428)
Reads the date of Windows installation
- PatchMyPC.exe (PID: 744)
Executable content was dropped or overwritten
- PatchMyPC.exe (PID: 744)
- gacutil.exe (PID: 6028)
- C++ 2022 Redist. 14.42.34438.0 (x64).exe (PID: 5964)
- VC_redist.x64.exe (PID: 2984)
- VC_redist.x64.exe (PID: 8012)
- VC_redist.x64.exe (PID: 8060)
- C++ 2022 Redist. 14.42.34438.0 (x86).exe (PID: 8172)
- C++ 2022 Redist. 14.42.34438.0 (x86).exe (PID: 7256)
- VC_redist.x86.exe (PID: 4428)
- C++ 2022 Redist. 14.42.34438.0 (x64).exe (PID: 2908)
Reads Microsoft Outlook installation path
- PatchMyPC.exe (PID: 744)
Starts a Microsoft application from unusual location
- C++ 2022 Redist. 14.42.34438.0 (x64).exe (PID: 2908)
- VC_redist.x64.exe (PID: 2984)
- C++ 2022 Redist. 14.42.34438.0 (x86).exe (PID: 7256)
- VC_redist.x86.exe (PID: 4428)
Starts itself from another location
- C++ 2022 Redist. 14.42.34438.0 (x64).exe (PID: 2908)
- C++ 2022 Redist. 14.42.34438.0 (x86).exe (PID: 7256)
Executes as Windows Service
- VSSVC.exe (PID: 5176)
Reads Internet Explorer settings
- PatchMyPC.exe (PID: 744)
The process checks if it is being run in the virtual environment
- msiexec.exe (PID: 7820)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7820)
The process drops C-runtime libraries
- msiexec.exe (PID: 7820)
Searches for installed software
- dllhost.exe (PID: 4756)
- VC_redist.x64.exe (PID: 8012)
- VC_redist.x64.exe (PID: 8060)
- C++ 2022 Redist. 14.42.34438.0 (x86).exe (PID: 7256)
- VC_redist.x86.exe (PID: 4428)
- PatchMyPC.exe (PID: 744)
Creates a software uninstall entry
- VC_redist.x64.exe (PID: 2984)
- VC_redist.x86.exe (PID: 4428)
Application launched itself
- VC_redist.x64.exe (PID: 8012)
- VC_redist.x64.exe (PID: 7988)
INFO
Reads the computer name
- PatchMyPC.exe (PID: 744)
- C++ 2022 Redist. 14.42.34438.0 (x64).exe (PID: 5964)
- C++ 2022 Redist. 14.42.34438.0 (x64).exe (PID: 2908)
- VC_redist.x64.exe (PID: 2984)
- msiexec.exe (PID: 7820)
- VC_redist.x64.exe (PID: 8012)
- VC_redist.x64.exe (PID: 8060)
- C++ 2022 Redist. 14.42.34438.0 (x86).exe (PID: 8172)
- C++ 2022 Redist. 14.42.34438.0 (x86).exe (PID: 7256)
- VC_redist.x86.exe (PID: 4428)
Reads Environment values
- PatchMyPC.exe (PID: 744)
Disables trace logs
- PatchMyPC.exe (PID: 744)
Checks supported languages
- PatchMyPC.exe (PID: 744)
- gacutil.exe (PID: 6028)
- C++ 2022 Redist. 14.42.34438.0 (x64).exe (PID: 2908)
- C++ 2022 Redist. 14.42.34438.0 (x64).exe (PID: 5964)
- VC_redist.x64.exe (PID: 2984)
- msiexec.exe (PID: 7820)
- VC_redist.x64.exe (PID: 7988)
- VC_redist.x64.exe (PID: 8012)
- VC_redist.x64.exe (PID: 8060)
- C++ 2022 Redist. 14.42.34438.0 (x86).exe (PID: 7256)
- C++ 2022 Redist. 14.42.34438.0 (x86).exe (PID: 8172)
- VC_redist.x86.exe (PID: 4428)
Reads the machine GUID from the registry
- PatchMyPC.exe (PID: 744)
- gacutil.exe (PID: 6028)
- VC_redist.x64.exe (PID: 2984)
- msiexec.exe (PID: 7820)
- VC_redist.x86.exe (PID: 4428)
Reads the software policy settings
- PatchMyPC.exe (PID: 744)
- msiexec.exe (PID: 7820)
The sample compiled with english language support
- PatchMyPC.exe (PID: 744)
- C++ 2022 Redist. 14.42.34438.0 (x64).exe (PID: 2908)
- msiexec.exe (PID: 7820)
- VC_redist.x64.exe (PID: 8012)
- VC_redist.x64.exe (PID: 8060)
- C++ 2022 Redist. 14.42.34438.0 (x86).exe (PID: 8172)
- C++ 2022 Redist. 14.42.34438.0 (x86).exe (PID: 7256)
- VC_redist.x86.exe (PID: 4428)
Checks proxy server information
- PatchMyPC.exe (PID: 744)
Creates files in the program directory
- VC_redist.x64.exe (PID: 2984)
- VC_redist.x86.exe (PID: 4428)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7820)
Manages system restore points
- SrTasks.exe (PID: 7728)
Creates a software uninstall entry
- msiexec.exe (PID: 7820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (49.4) |
|---|---|---|
| .scr | | | Windows screen saver (23.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (11.7) |
| .exe | | | Win32 Executable (generic) (8) |
| .exe | | | Generic Win/DOS Executable (3.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:03:13 07:58:05+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 2596864 |
| InitializedDataSize: | 57856 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x27bff6 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.5.0.5 |
| ProductVersionNumber: | 0.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Third-Party App Updater |
| CompanyName: | Patch My PC, LLC |
| FileDescription: | Patch My PC |
| FileVersion: | 4.5.0.5 |
| InternalName: | PatchMyPC.exe |
| LegalCopyright: | Copyright © Patch My PC, LLC |
| LegalTrademarks: | - |
| OriginalFileName: | PatchMyPC.exe |
| ProductName: | Patch My PC |
| ProductVersion: | 0.0.0.1 |
| AssemblyVersion: | 4.5.0.5 |
Total processes
153
Monitored processes
22
Malicious processes
12
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 744 | C:\Users\admin\Desktop\PatchMyPC.exe | C:\Users\admin\Desktop\PatchMyPC.exe | runas.exe | ||||||||||||
User: Administrator Company: Patch My PC, LLC Integrity Level: HIGH Description: Patch My PC Version: 4.5.0.5 Modules
| |||||||||||||||
| 904 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | C:\WINDOWS\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1276 | "C:\Windows\System32\runas.exe" /user:administrator C:\Users\admin\Desktop\PatchMyPC.exe | C:\Windows\System32\runas.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Run As Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2908 | "C:\WINDOWS\Temp\{1F1B4E48-FB01-473F-8FCC-B1B75236266E}\.cr\C++ 2022 Redist. 14.42.34438.0 (x64).exe" -burn.clean.room="C:\PatchMyPCUpdates\C++ 2022 Redist. 14.42.34438.0 (x64).exe" -burn.filehandle.attached=580 -burn.filehandle.self=576 /install /quiet /norestart | C:\Windows\Temp\{1F1B4E48-FB01-473F-8FCC-B1B75236266E}\.cr\C++ 2022 Redist. 14.42.34438.0 (x64).exe | C++ 2022 Redist. 14.42.34438.0 (x64).exe | ||||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.42.34438 Exit code: 3010 Version: 14.42.34438.0 Modules
| |||||||||||||||
| 2984 | "C:\WINDOWS\Temp\{EC146DFD-1A59-4EEC-A936-CF806C940A98}\.be\VC_redist.x64.exe" -q -burn.elevated BurnPipe.{8557C688-218C-40DF-AF81-50D5ABB11EE4} {FFBCE3D1-F535-4852-BE07-82EE355206B7} 2908 | C:\Windows\Temp\{EC146DFD-1A59-4EEC-A936-CF806C940A98}\.be\VC_redist.x64.exe | C++ 2022 Redist. 14.42.34438.0 (x64).exe | ||||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.42.34438 Exit code: 3010 Version: 14.42.34438.0 Modules
| |||||||||||||||
| 4428 | "C:\WINDOWS\Temp\{66D20B06-5D30-4CBD-8590-EA31DD6115F7}\.be\VC_redist.x86.exe" -q -burn.elevated BurnPipe.{9B660AC4-C17F-45BF-8C7D-BE85D65D4FC5} {C8DBC100-A654-4777-BF38-215D7CF51F84} 7256 | C:\Windows\Temp\{66D20B06-5D30-4CBD-8590-EA31DD6115F7}\.be\VC_redist.x86.exe | C++ 2022 Redist. 14.42.34438.0 (x86).exe | ||||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.42.34438 Version: 14.42.34438.0 Modules
| |||||||||||||||
| 4756 | C:\WINDOWS\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5176 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | runas.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5176 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
22 325
Read events
20 931
Write events
906
Delete events
488
Modification events
| (PID) Process: | (744) PatchMyPC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Patch My PC |
| Operation: | write | Name: | PATH |
Value: C:\Users\admin\Desktop\PatchMyPC.exe | |||
| (PID) Process: | (744) PatchMyPC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PatchMyPC_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (744) PatchMyPC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PatchMyPC_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (744) PatchMyPC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PatchMyPC_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (744) PatchMyPC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PatchMyPC_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (744) PatchMyPC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PatchMyPC_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (744) PatchMyPC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PatchMyPC_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (744) PatchMyPC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PatchMyPC_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (744) PatchMyPC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PatchMyPC_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (744) PatchMyPC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PatchMyPC_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
107
Suspicious files
98
Text files
106
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 744 | PatchMyPC.exe | C:\Users\Administrator\AppData\Roaming\PatchMyPC\Microsoft.Win32.TaskScheduler.dll | executable | |
MD5:E4A7B55E9F8C52B356E264C347035CD5 | SHA256:F3C2D5A2DB68B9E6CA161AC126BB8FA47B5889D5786B5DDB28F9193DD500C87D | |||
| 744 | PatchMyPC.exe | C:\Users\Administrator\AppData\Roaming\PatchMyPC\1033\gacutlrc.dll | executable | |
MD5:98724A7D91993527C8F821F0F722995D | SHA256:35B093F47A7220B789F431B866537E72BB78609FE03F45C7E12926DB94C6634C | |||
| 744 | PatchMyPC.exe | C:\Users\Administrator\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:261354E2FAB7329810F3EAE9685DEE14 | SHA256:30282BE3FA4B12951F9557C2F716560A8377EF6501B55D19CA4DD6F99E2FC766 | |||
| 744 | PatchMyPC.exe | C:\Users\Administrator\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:F1E04442796C6FA8597364BCE2C2AE23 | SHA256:C4B5E5AE865BA261A5ED5D6D4812B6F426363B8671B04963FCDE40F7EE30D7F8 | |||
| 744 | PatchMyPC.exe | C:\Users\Administrator\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:36793A407347E8594BB44A7A0CEF946F | SHA256:D95CAD417B24F3BE3BA2F6981483EDE0E74E08262E3B3B1D6246EAE2A6EFEEBF | |||
| 744 | PatchMyPC.exe | C:\Users\Administrator\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:ACD03AAFA192E7232D87A39FCD4D7D89 | SHA256:F35762AB6BC38DF73202082FAFDB920DE737C517570A5BD8B572D2E331233C08 | |||
| 744 | PatchMyPC.exe | C:\Users\Administrator\AppData\Local\Temp\Home Updater\definitions.xml | text | |
MD5:6D1D67EF2294B6546B92D835F5603B5F | SHA256:F1418C10C532BFA3F25141DA246EDD498B55972F8FFAD50DDFC8F2B2CDCF0F92 | |||
| 744 | PatchMyPC.exe | C:\Users\Administrator\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8EC9B1D0ABBD7F98B401D425828828CE_6C6ABF5B95E12F43EA8BA7E809010C70 | binary | |
MD5:D0C7E044EB576C94A9440FD6E7CC5E35 | SHA256:9563182140A0EBA31C75AB4A007EB549270564F6CF4F18C220D2D46901C7A3C2 | |||
| 744 | PatchMyPC.exe | C:\Users\Administrator\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8EC9B1D0ABBD7F98B401D425828828CE_6C6ABF5B95E12F43EA8BA7E809010C70 | binary | |
MD5:006B0E35178492BD6ED2AA9BD72ADBFB | SHA256:5A40AF0BE2AFA5E5125A074DF9AC11F94BA755957805CDF78549DA4D0AECA956 | |||
| 744 | PatchMyPC.exe | C:\Users\Administrator\AppData\Roaming\PatchMyPC\gacutil.exe.config | xml | |
MD5:7033A6FA2F8A457716F6D642137CC7DB | SHA256:D1E116F59C6CF832090DA36F95725827A7F5EDB3173CBCE13FFEDC4FB6B61D2E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
38
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.38:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
744 | PatchMyPC.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
744 | PatchMyPC.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAzDcPO1O1GePB79c2utY6I%3D | unknown | — | — | whitelisted |
744 | PatchMyPC.exe | GET | 301 | 172.67.7.92:80 | http://patchmypc.com/freeupdater/definitions/definitions.xml | unknown | — | — | malicious |
744 | PatchMyPC.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAFnjx%2FviCJV2LCnDmt7siA%3D | unknown | — | — | whitelisted |
744 | PatchMyPC.exe | GET | 301 | 172.67.7.92:80 | http://patchmypc.com/freeupdater/definitions/definitions.xml | unknown | — | — | malicious |
744 | PatchMyPC.exe | GET | 301 | 172.67.7.92:80 | http://patchmypc.com/redirect.htm?V=4.5.0.5&OS=Win10&SILENT=0 | unknown | — | — | unknown |
744 | PatchMyPC.exe | GET | 301 | 104.21.48.1:80 | http://patchmypc.net/redirected.htm?source=app | unknown | — | — | whitelisted |
7412 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.38:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.172.255.218:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6544 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
744 | PatchMyPC.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
744 | PatchMyPC.exe | 172.67.7.92:443 | patchmypc.com | CLOUDFLARENET | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
patchmypc.com |
| unknown |
patchmypc.net |
| whitelisted |
aka.ms |
| whitelisted |
download.visualstudio.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
msiexec.exe | Failed to release Service
|