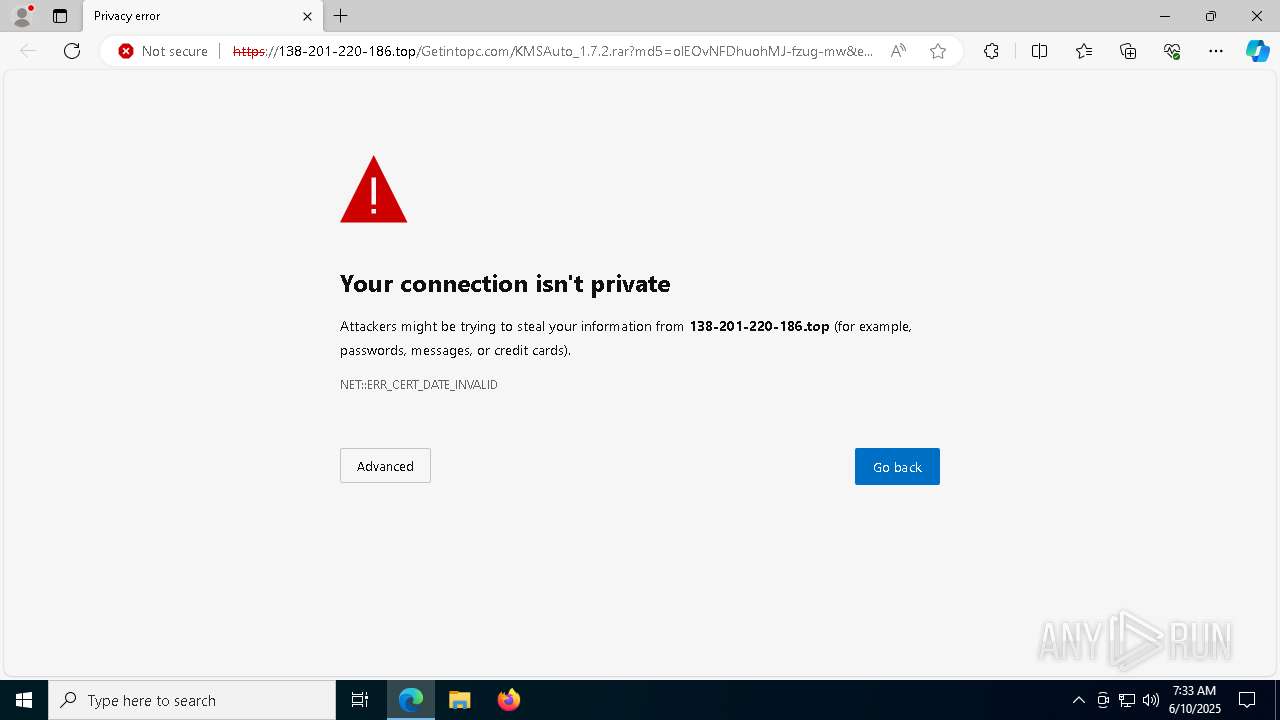
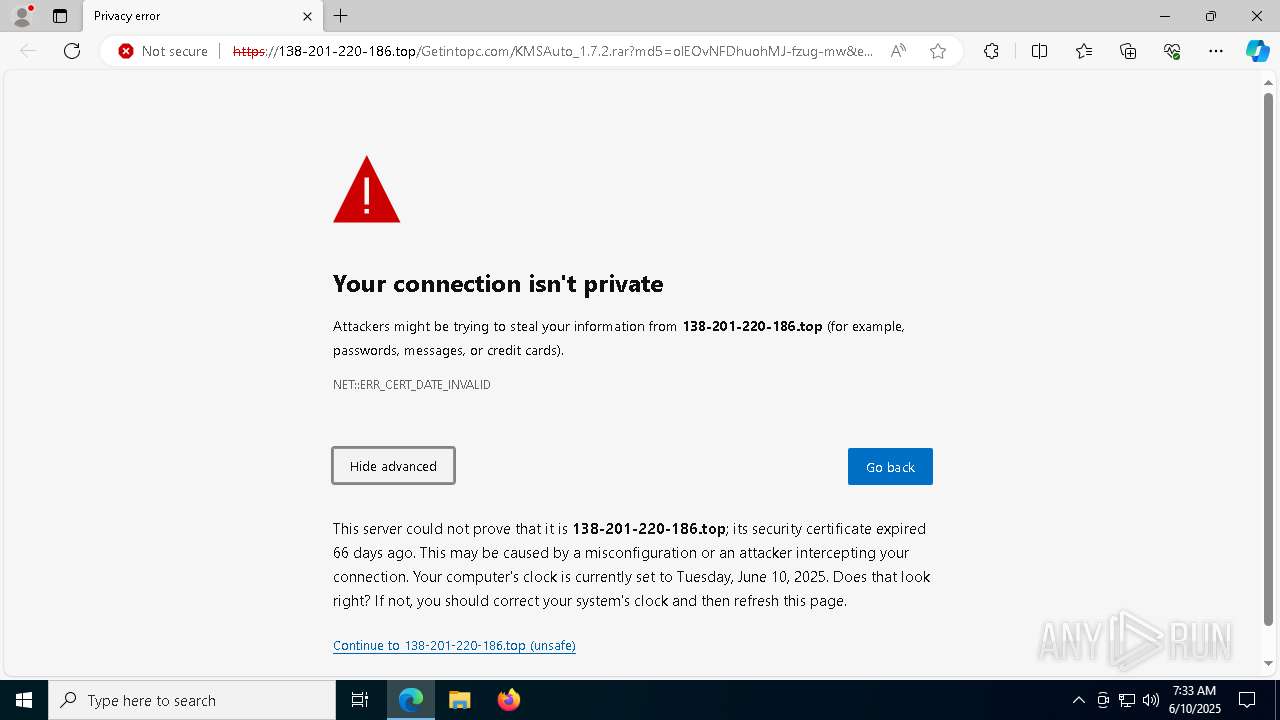
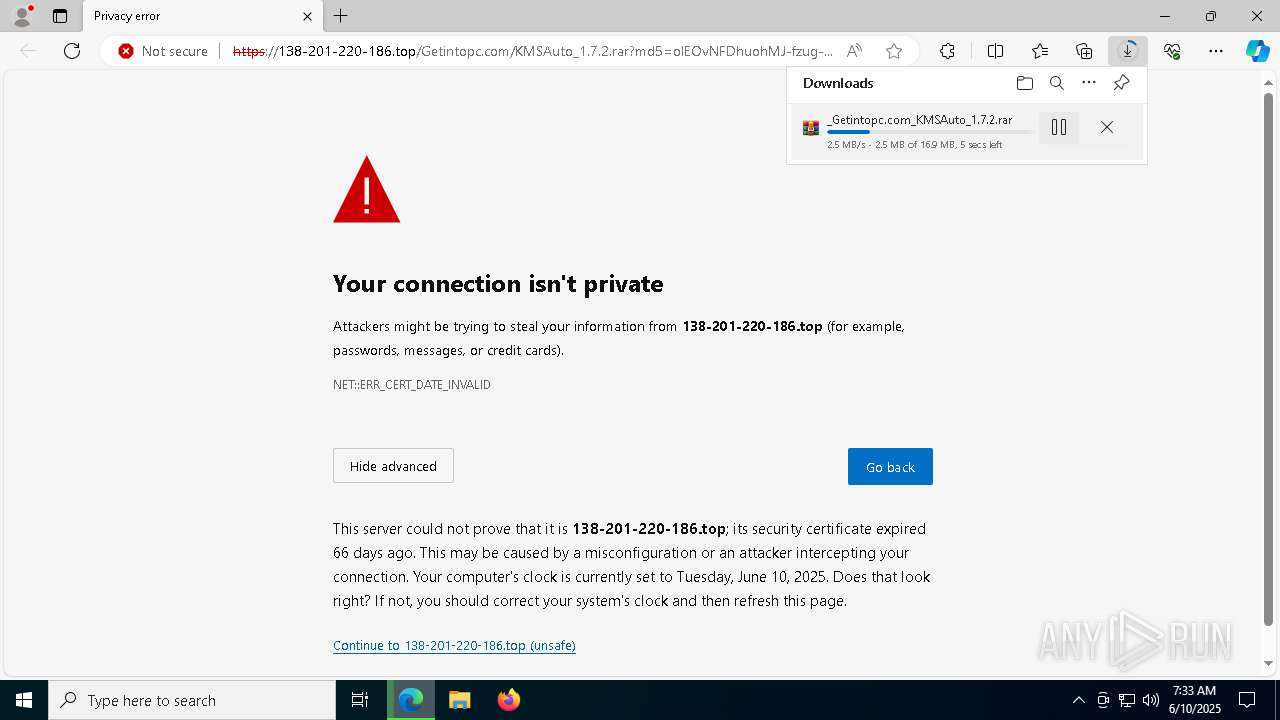
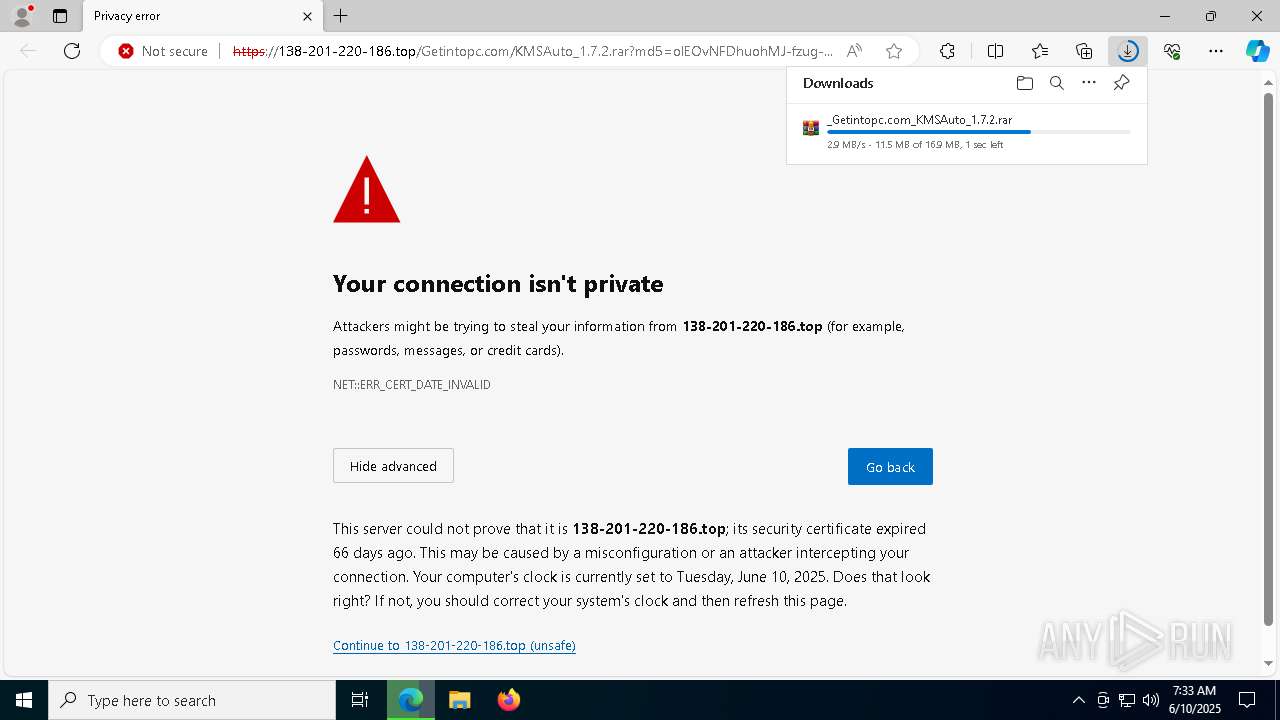
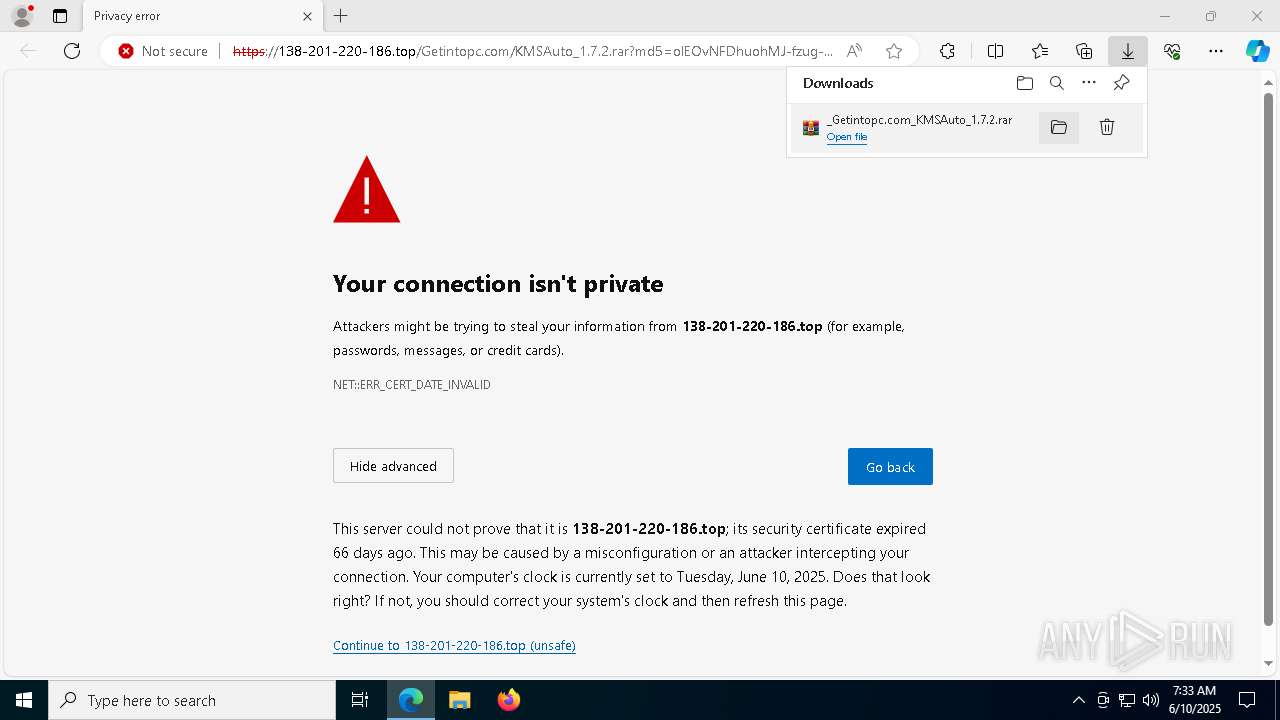
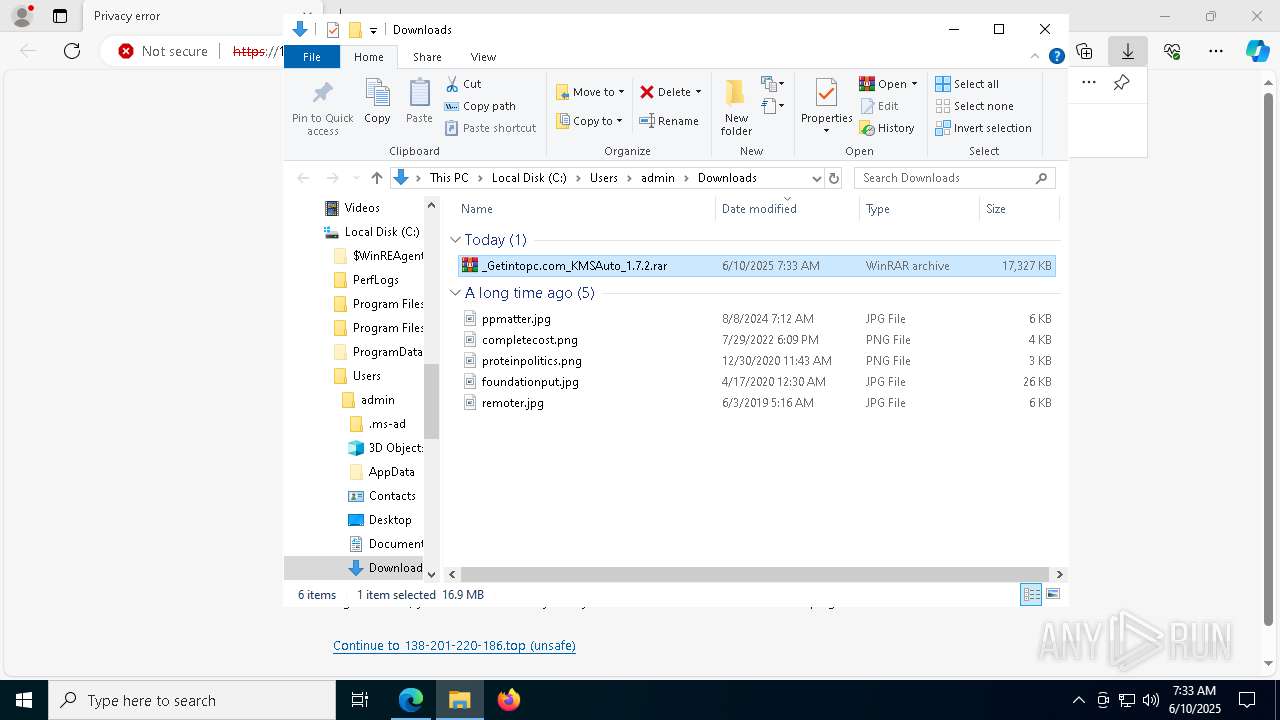
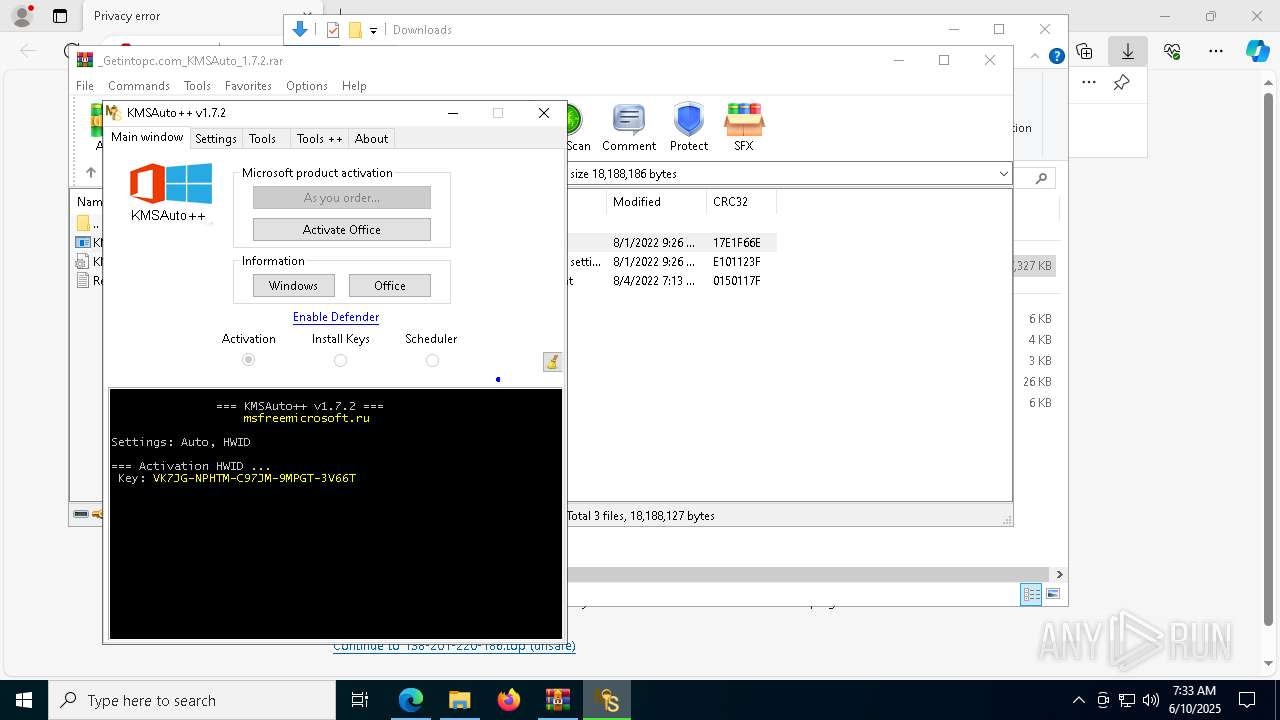
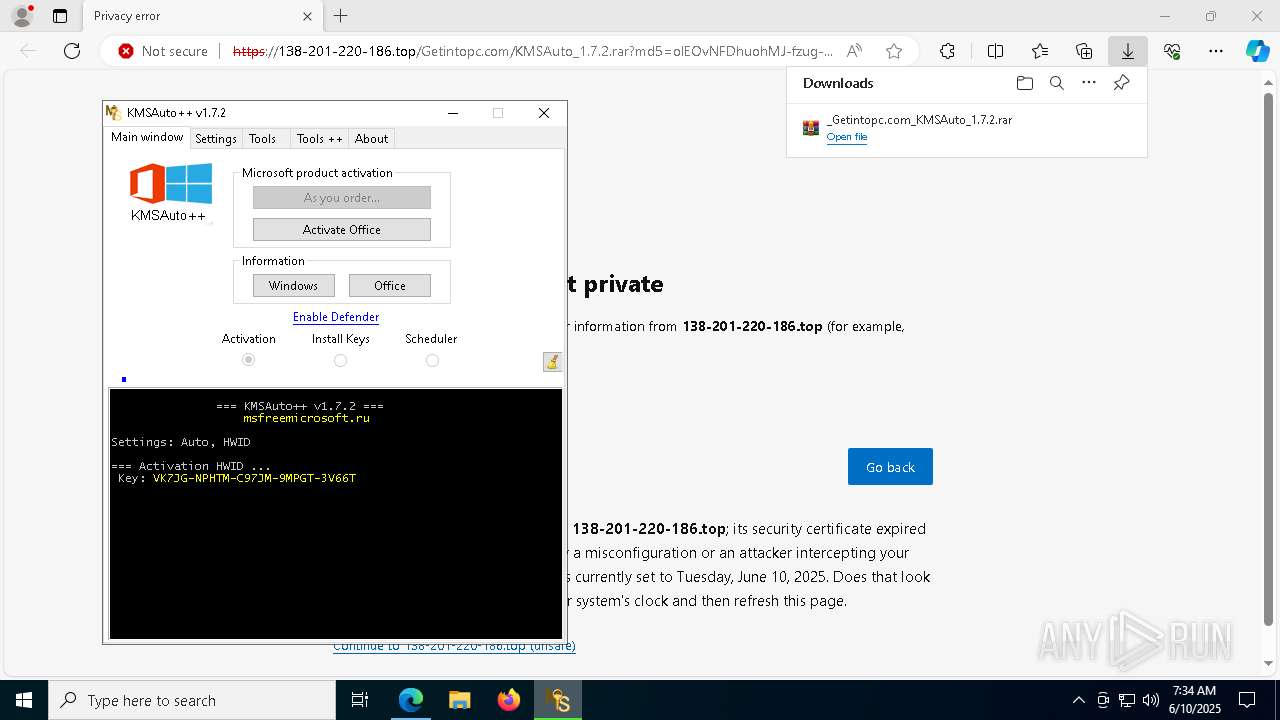
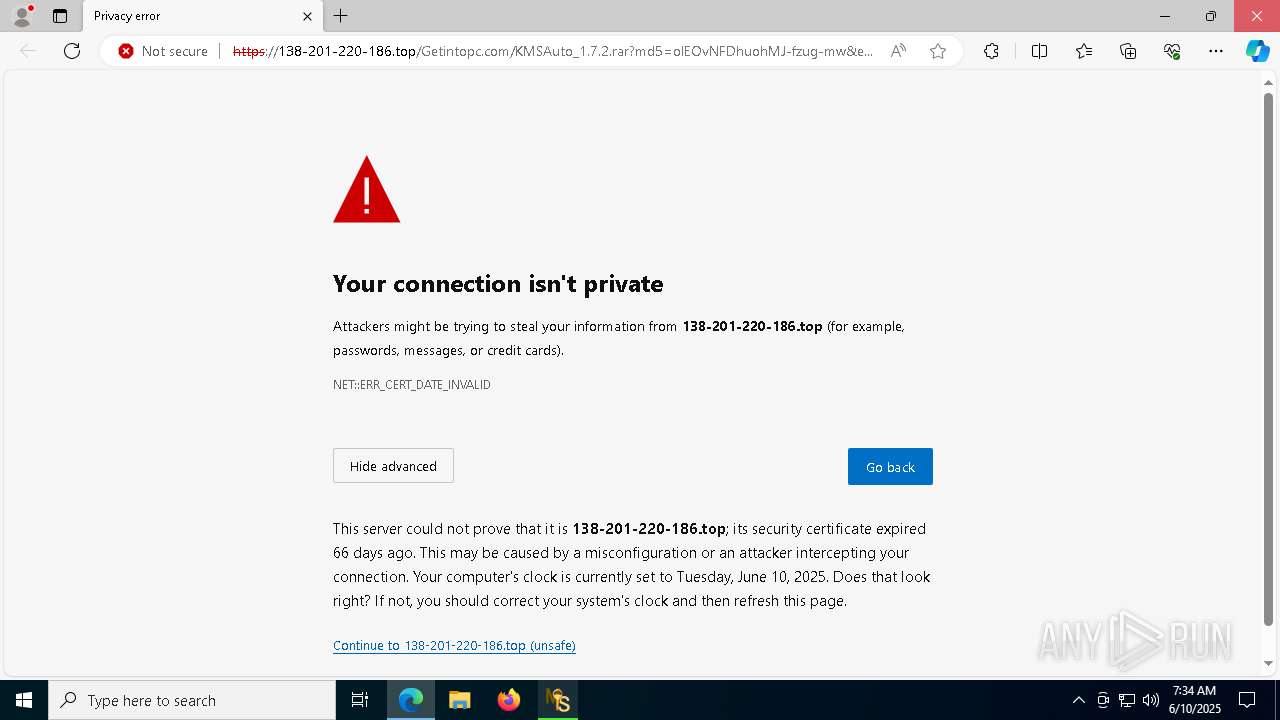
| URL: | https://138-201-220-186.top/Getintopc.com/KMSAuto_1.7.2.rar?md5=olEOvNFDhuohMJ-fzug-mw&expires=1752129632 |
| Full analysis: | https://app.any.run/tasks/4b6015c4-502f-4d43-bdf9-79a603324533 |
| Verdict: | Malicious activity |
| Analysis date: | June 10, 2025, 07:33:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 481A1670EAC50F5546B9B4B94649AF83 |
| SHA1: | AD5493BC8D12C6B11CFB3A026146B768B600F5DA |
| SHA256: | 2E81C264C5EB74D5F7085BD2ADED6C407246FA687EDBC082B8BB88CA4C10CC41 |
| SSDEEP: | 3:N89M+qHRl4KsLdIi2kj6hjuSuqjbQKNyVCPXMQW5jXzTQ:2y+SRl4KSeuS5bQW4oXMDx/Q |
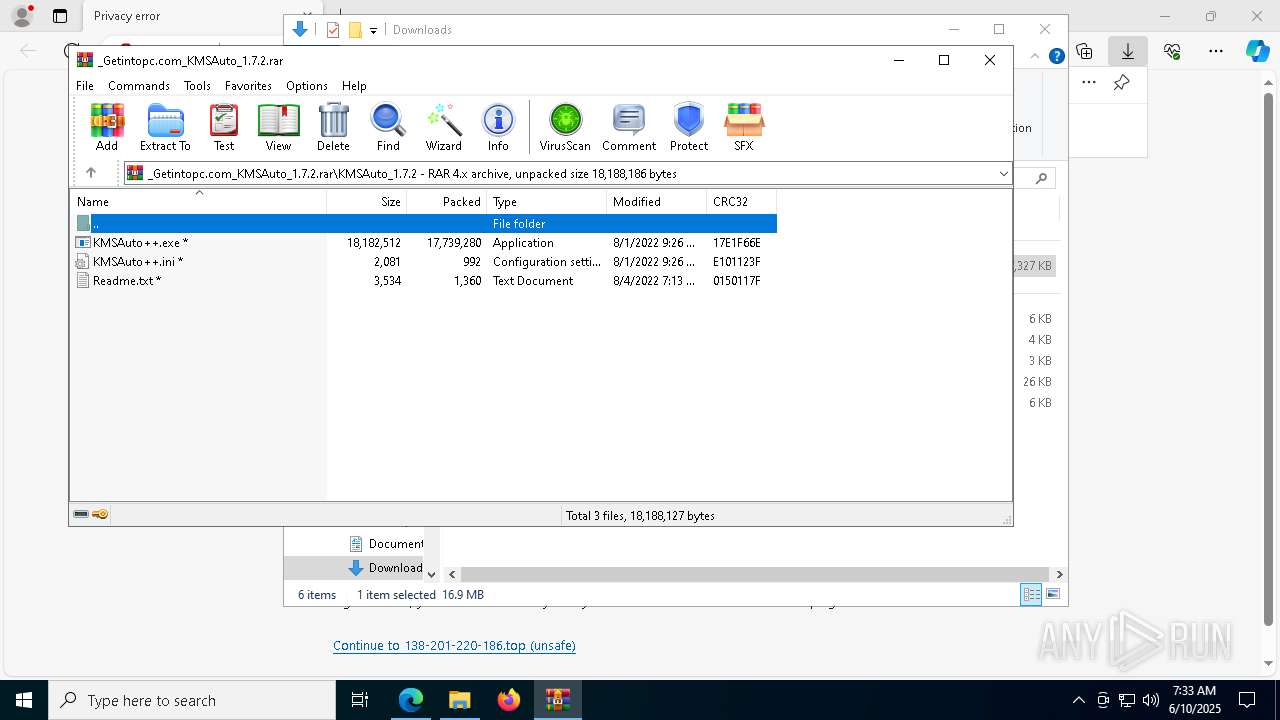
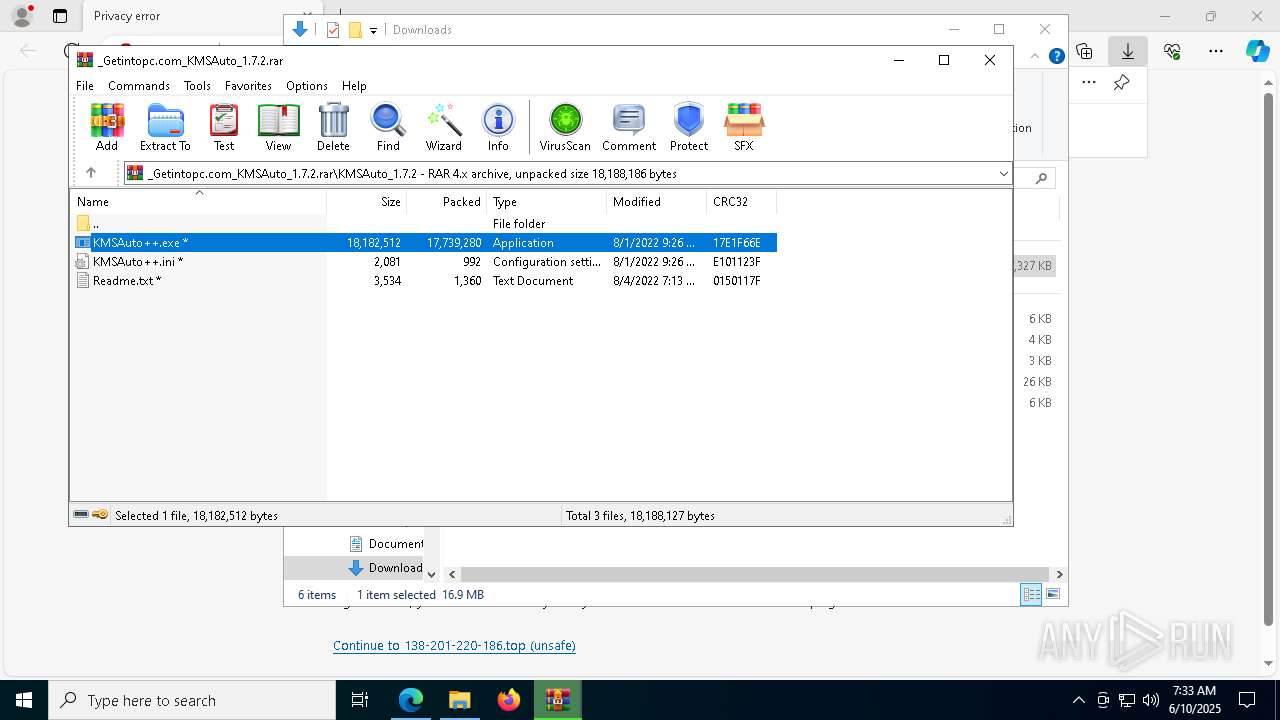
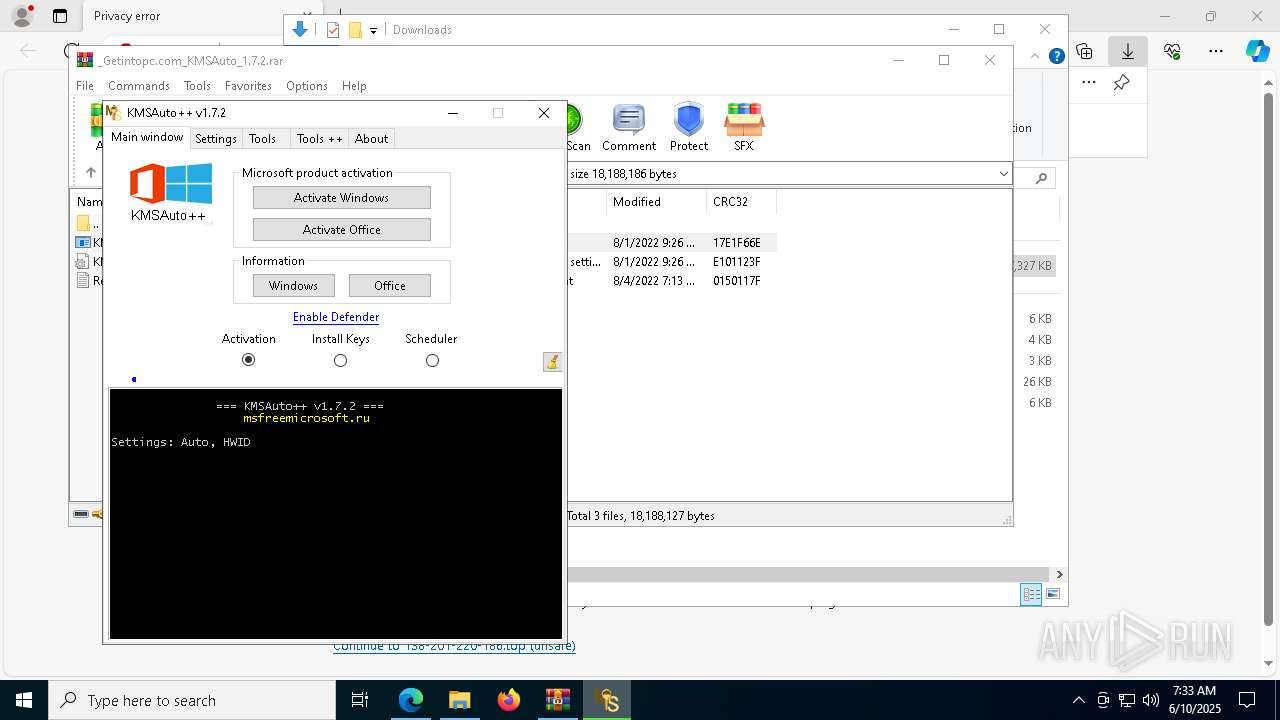
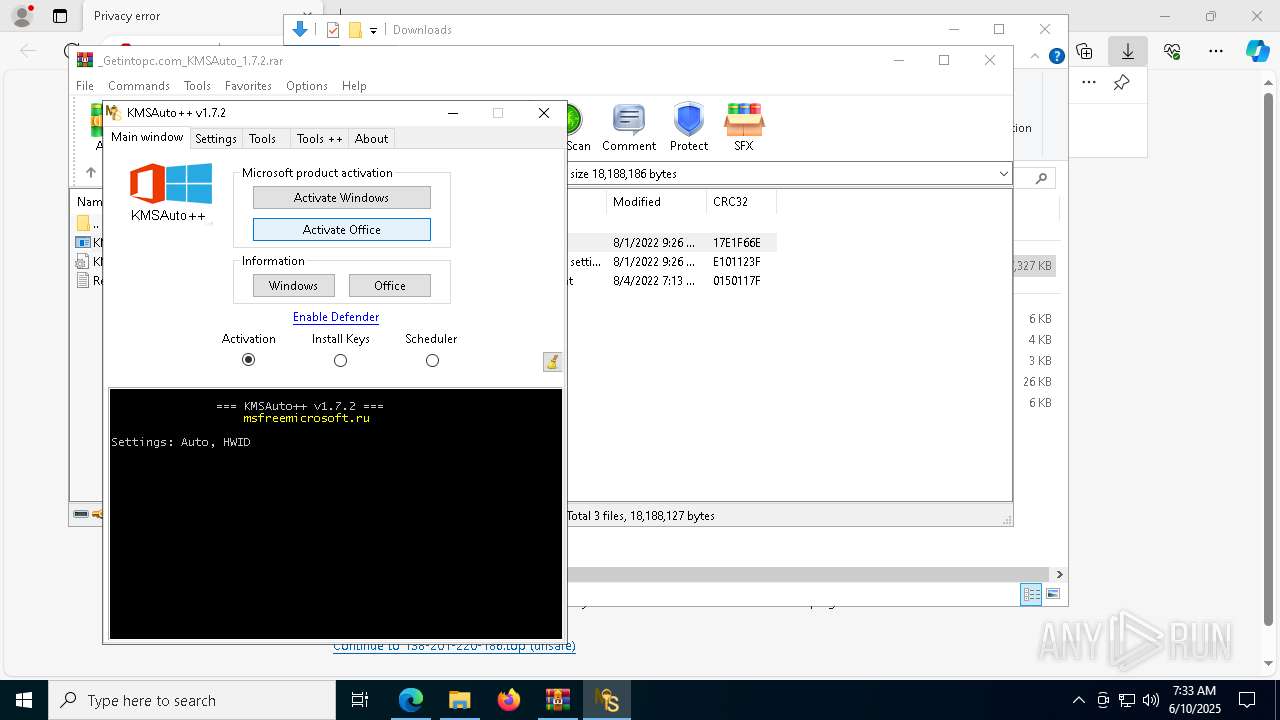
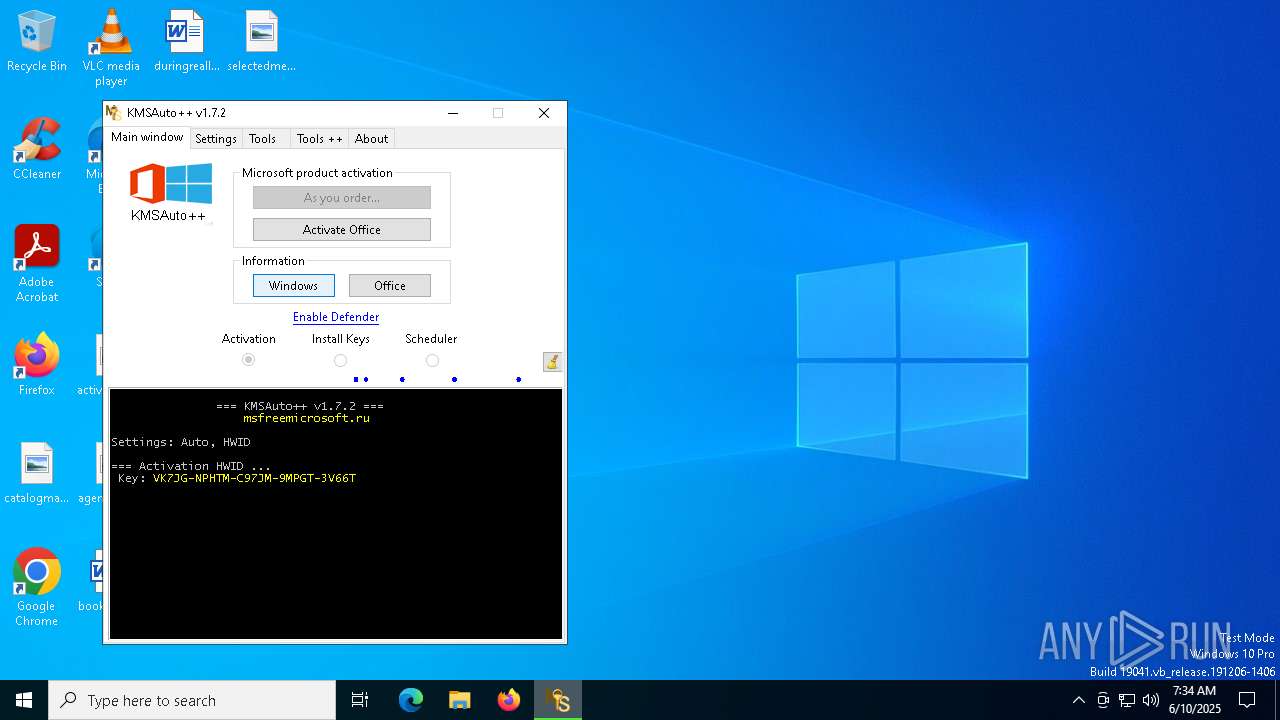
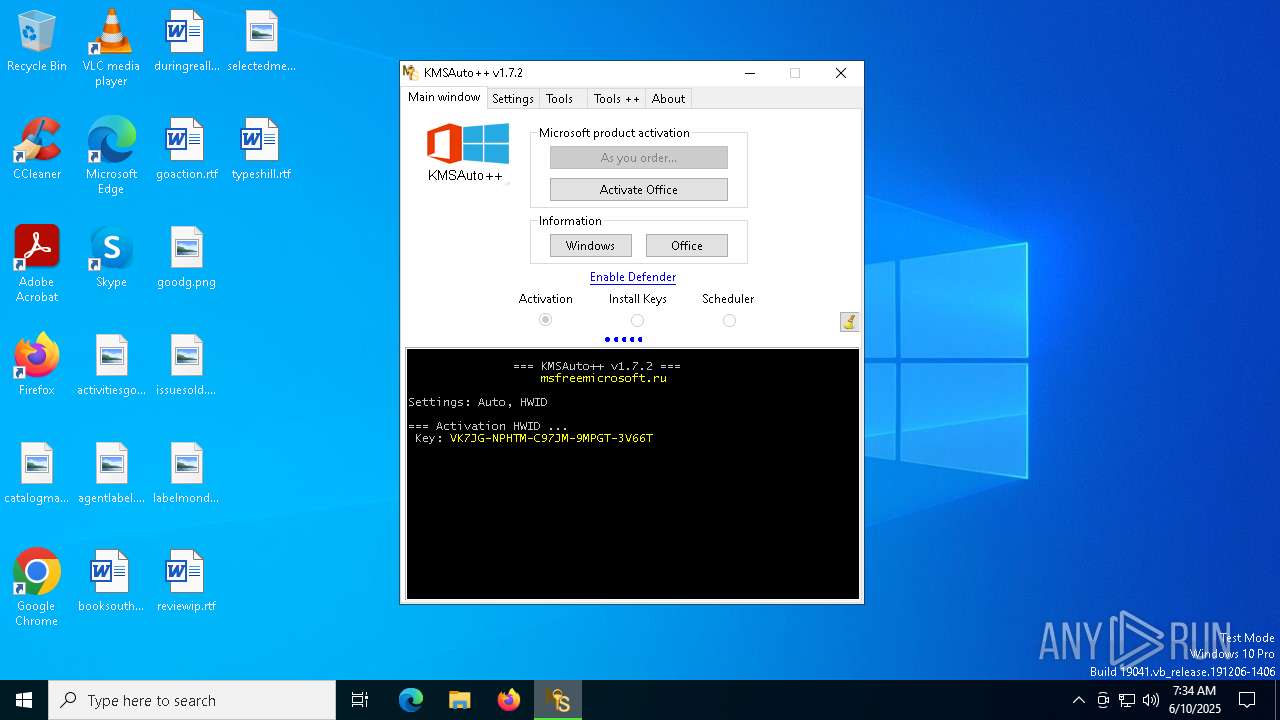
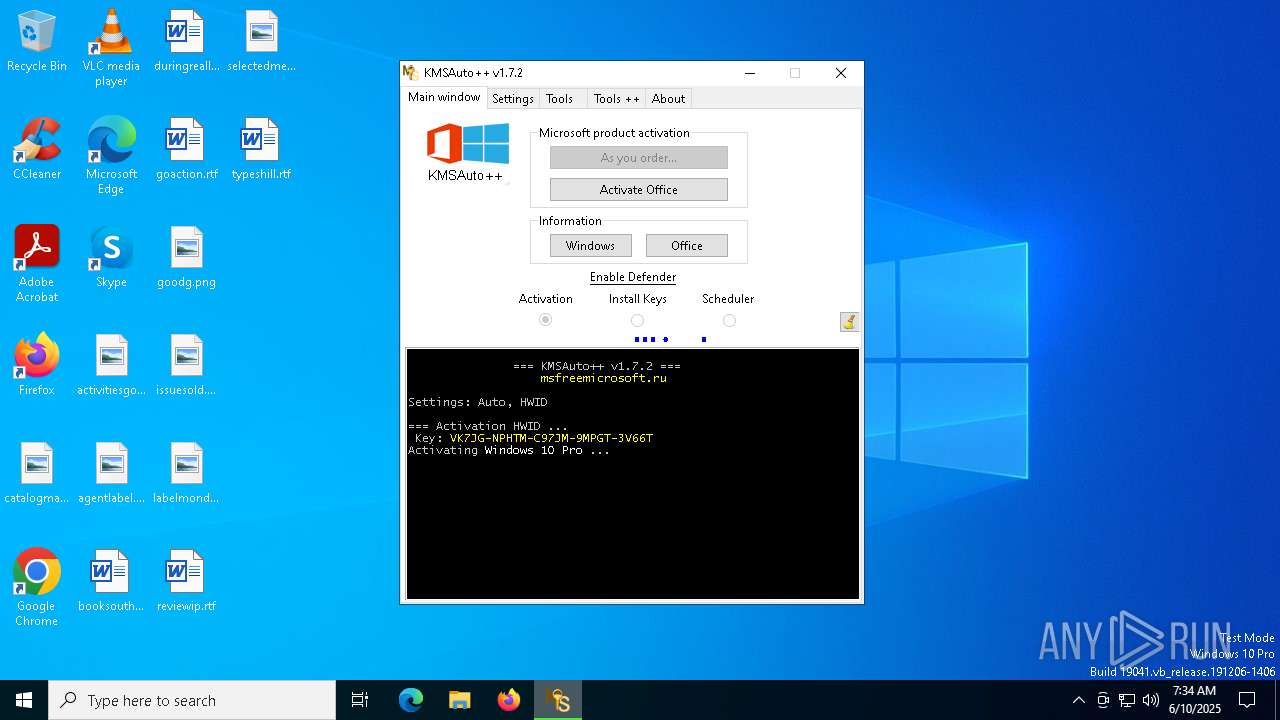
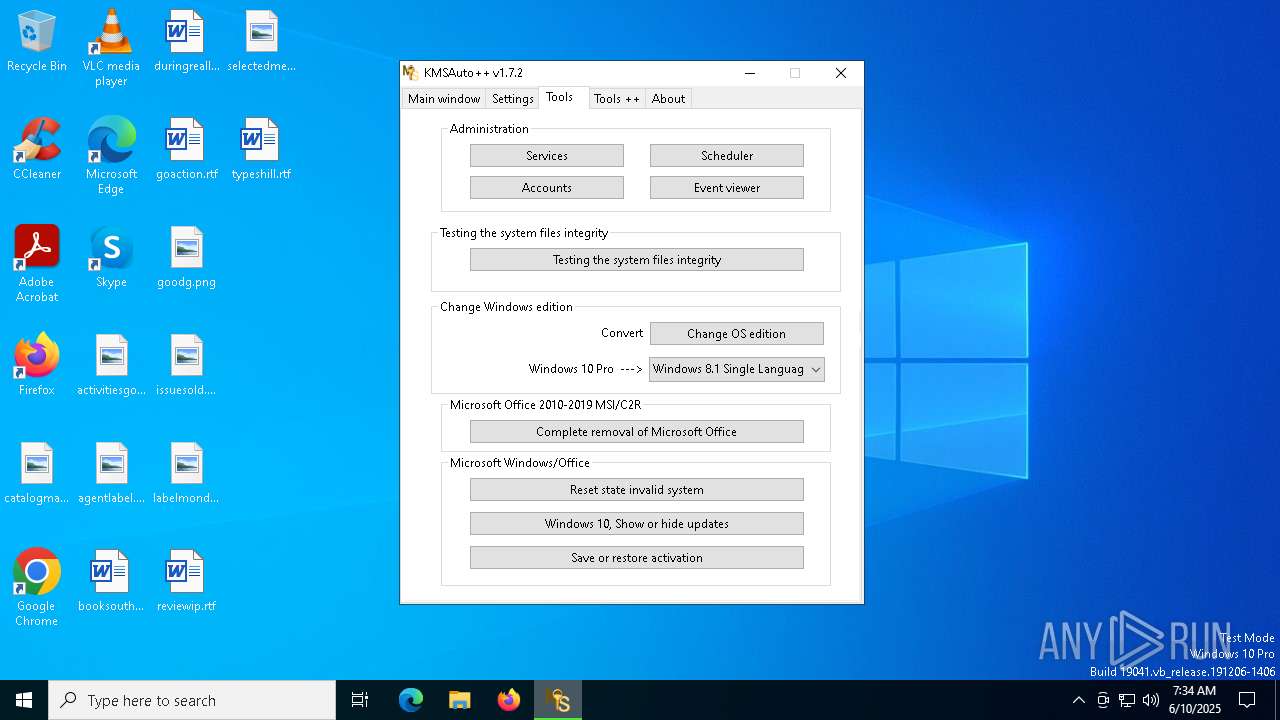
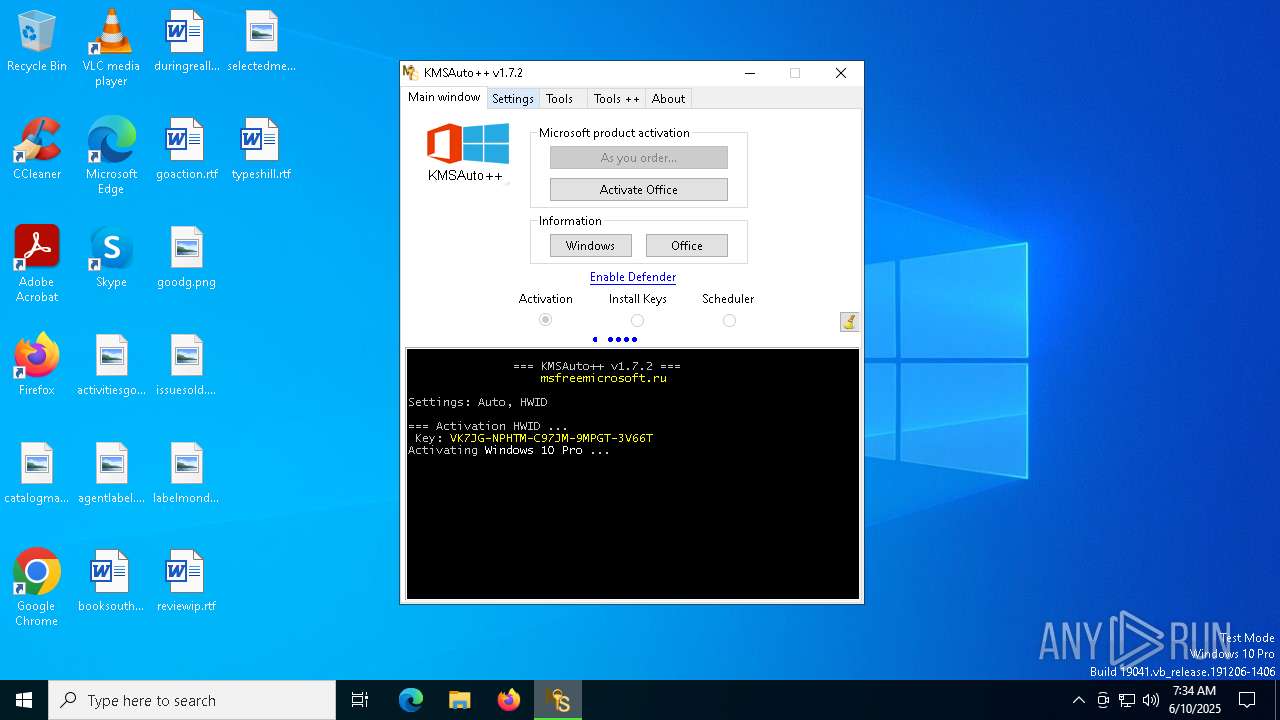
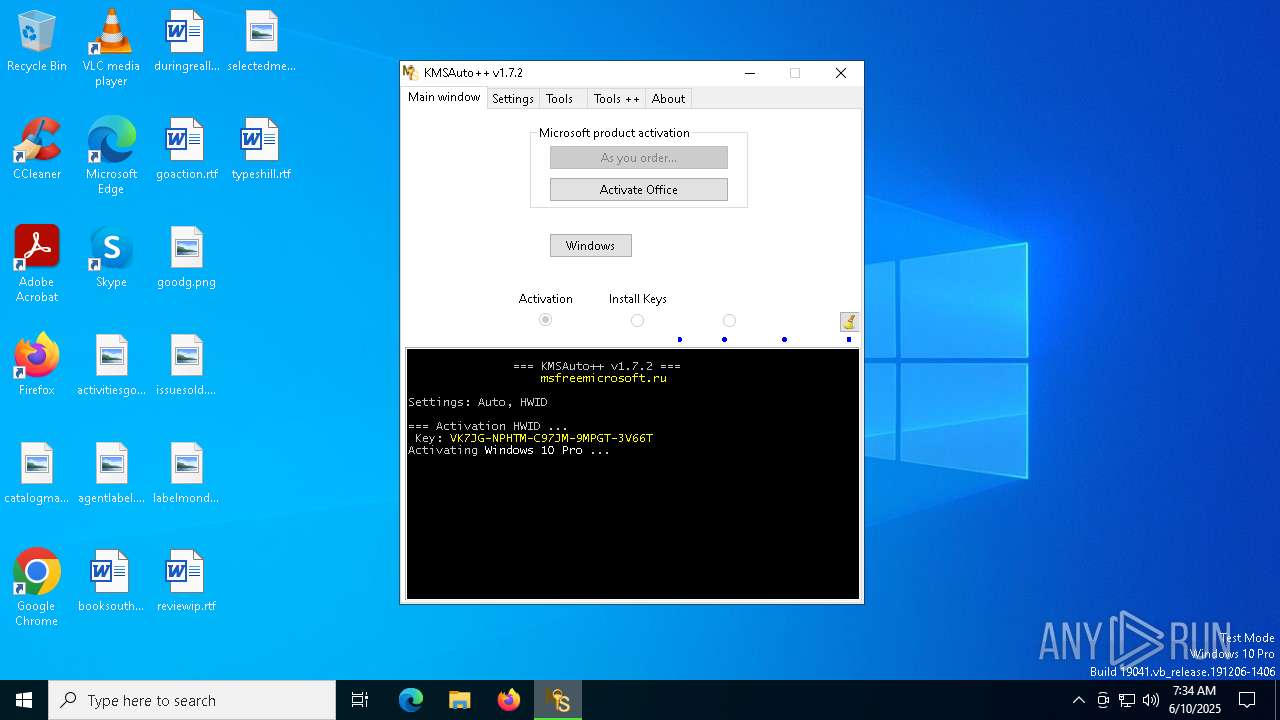
MALICIOUS
Executing a file with an untrusted certificate
- KMSAuto++.exe (PID: 7872)
- KMSAuto++.exe (PID: 8156)
- signtool.exe (PID: 5376)
- gatherosstate.exe (PID: 4628)
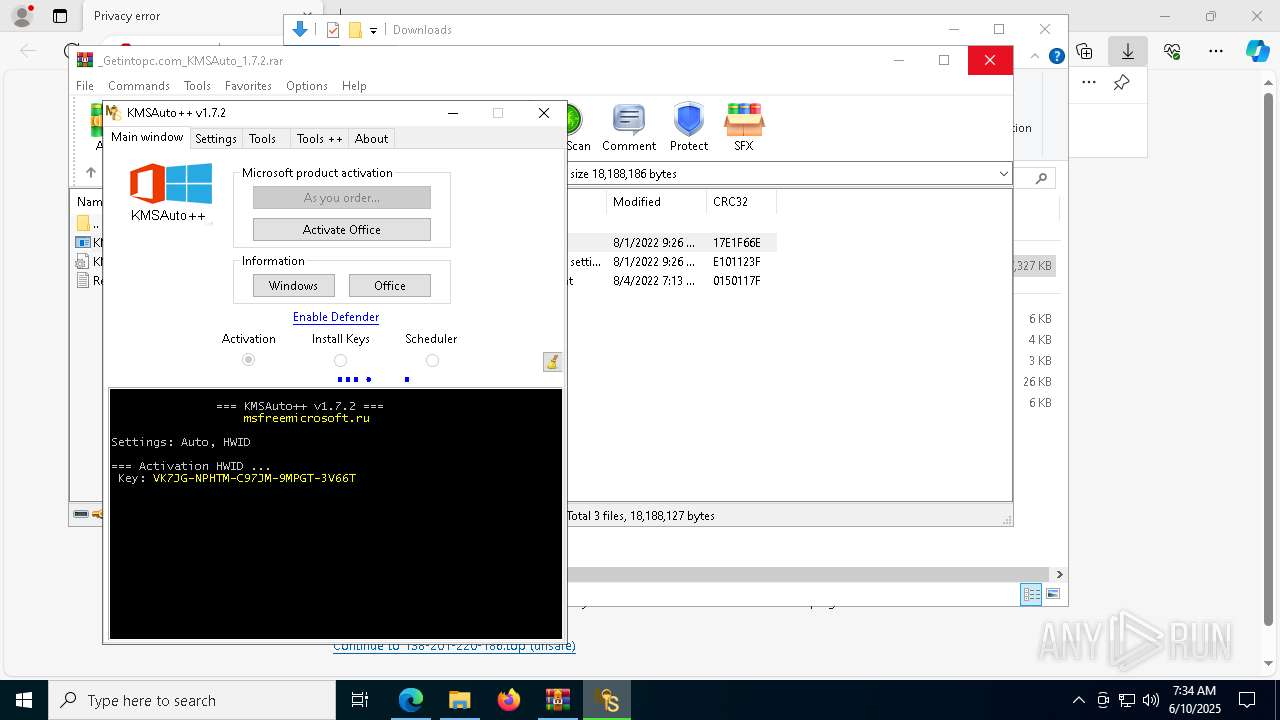
Uses WMIC.EXE to add exclusions to the Windows Defender
- cmd.exe (PID: 2136)
- cmd.exe (PID: 7280)
- cmd.exe (PID: 7960)
- cmd.exe (PID: 8084)
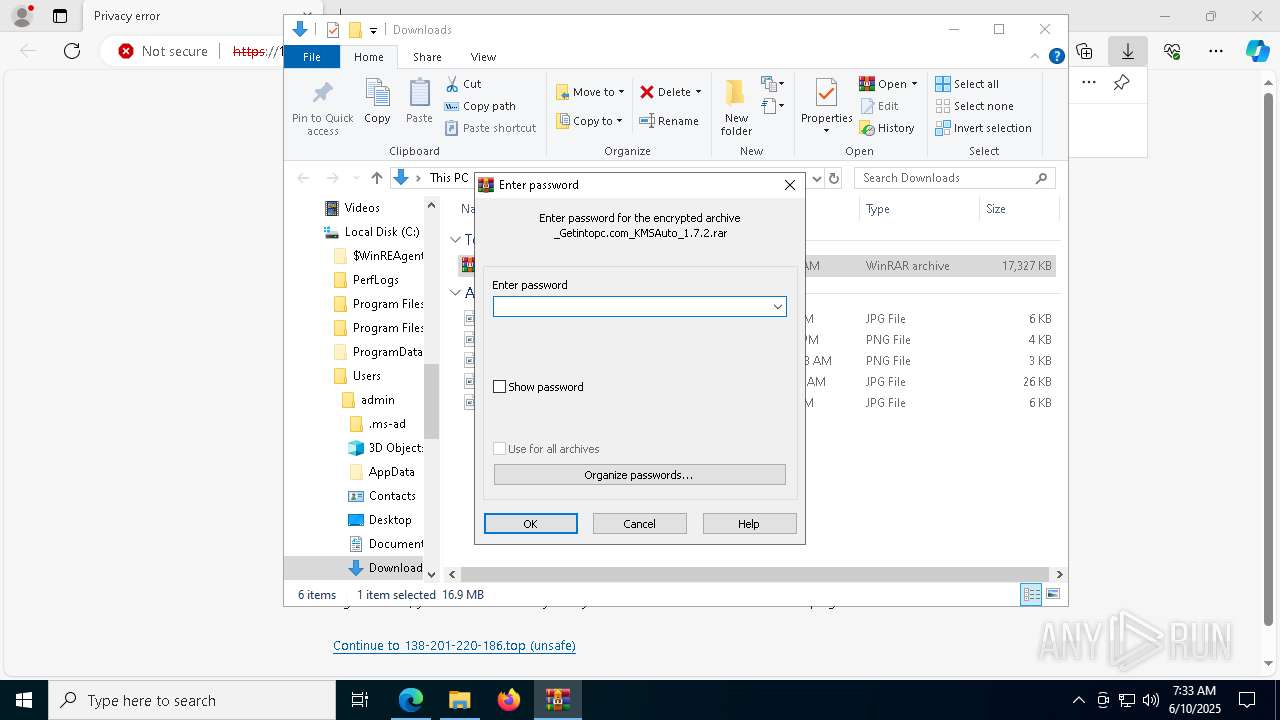
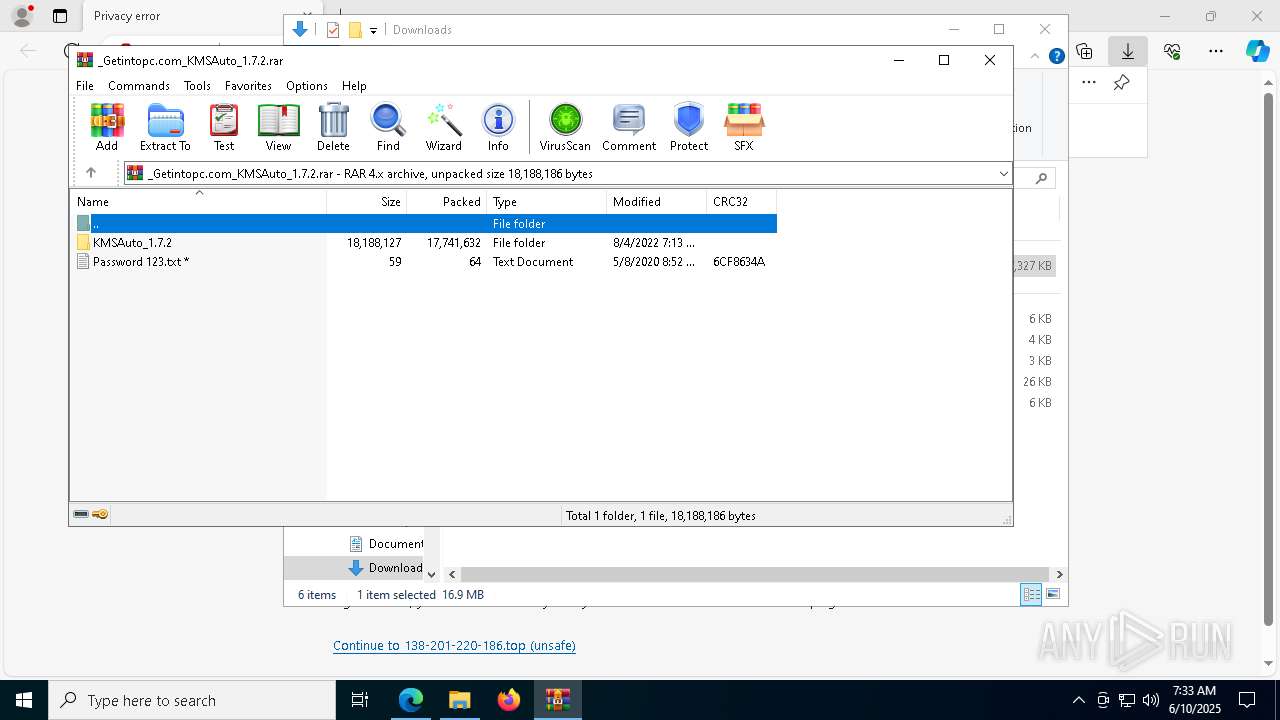
GENERIC has been found (auto)
- WinRAR.exe (PID: 3364)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3364)
- signtool.exe (PID: 5376)
Starts CMD.EXE for commands execution
- KMSAuto++.exe (PID: 7872)
Process drops legitimate windows executable
- KMSAuto++.exe (PID: 7872)
Found strings related to reading or modifying Windows Defender settings
- KMSAuto++.exe (PID: 7872)
Executable content was dropped or overwritten
- KMSAuto++.exe (PID: 7872)
Starts a Microsoft application from unusual location
- signtool.exe (PID: 5376)
- gatherosstate.exe (PID: 4628)
Starts SC.EXE for service management
- KMSAuto++.exe (PID: 7872)
- cmd.exe (PID: 4628)
- cmd.exe (PID: 6560)
- cmd.exe (PID: 7360)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 6892)
- cmd.exe (PID: 5556)
Windows service management via SC.EXE
- sc.exe (PID: 4228)
- sc.exe (PID: 4976)
- sc.exe (PID: 7292)
- sc.exe (PID: 7748)
- sc.exe (PID: 8120)
- sc.exe (PID: 7296)
- sc.exe (PID: 7916)
- sc.exe (PID: 536)
- sc.exe (PID: 5512)
- sc.exe (PID: 132)
- sc.exe (PID: 2332)
- sc.exe (PID: 7684)
- sc.exe (PID: 2040)
- sc.exe (PID: 540)
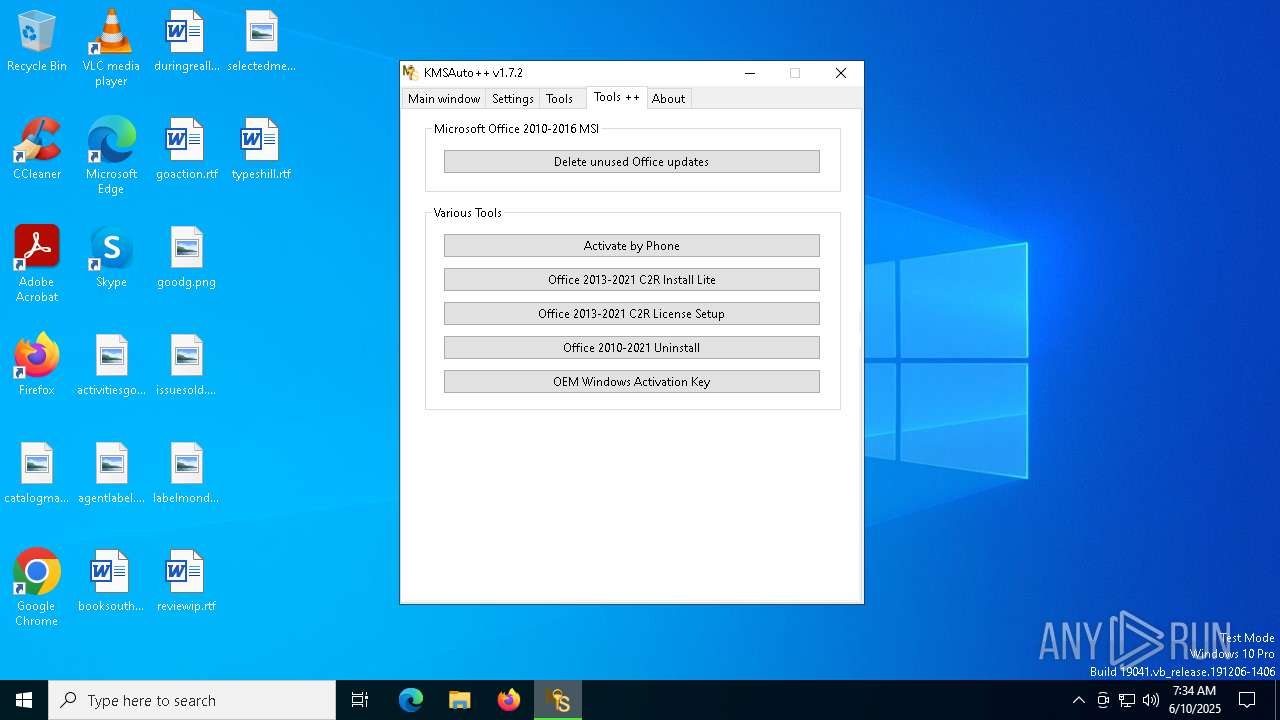
Adds/modifies Windows certificates
- signtool.exe (PID: 5376)
The process executes VB scripts
- cmd.exe (PID: 3896)
- cmd.exe (PID: 1324)
- cmd.exe (PID: 5228)
Uses WMIC.EXE
- KMSAuto++.exe (PID: 7872)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 616)
- cscript.exe (PID: 4776)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 616)
- cscript.exe (PID: 4776)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5232)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 8132)
Application launched itself
- ClipUp.exe (PID: 7888)
INFO
Reads the computer name
- identity_helper.exe (PID: 7424)
- KMSAuto++.exe (PID: 7872)
- gatherosstate.exe (PID: 4628)
Application launched itself
- msedge.exe (PID: 6072)
- msedge.exe (PID: 7732)
Checks supported languages
- identity_helper.exe (PID: 7424)
- KMSAuto++.exe (PID: 7872)
- signtool.exe (PID: 5376)
- gatherosstate.exe (PID: 4628)
Reads Environment values
- identity_helper.exe (PID: 7424)
- KMSAuto++.exe (PID: 7872)
Reads product name
- KMSAuto++.exe (PID: 7872)
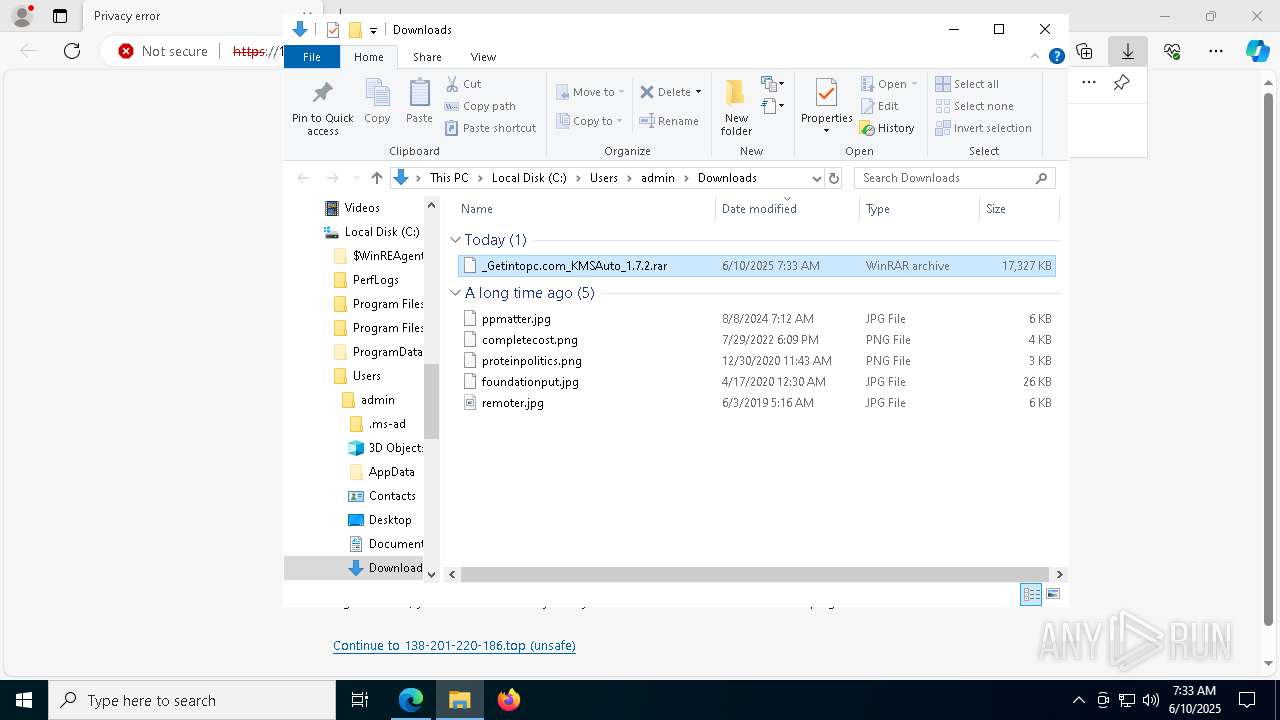
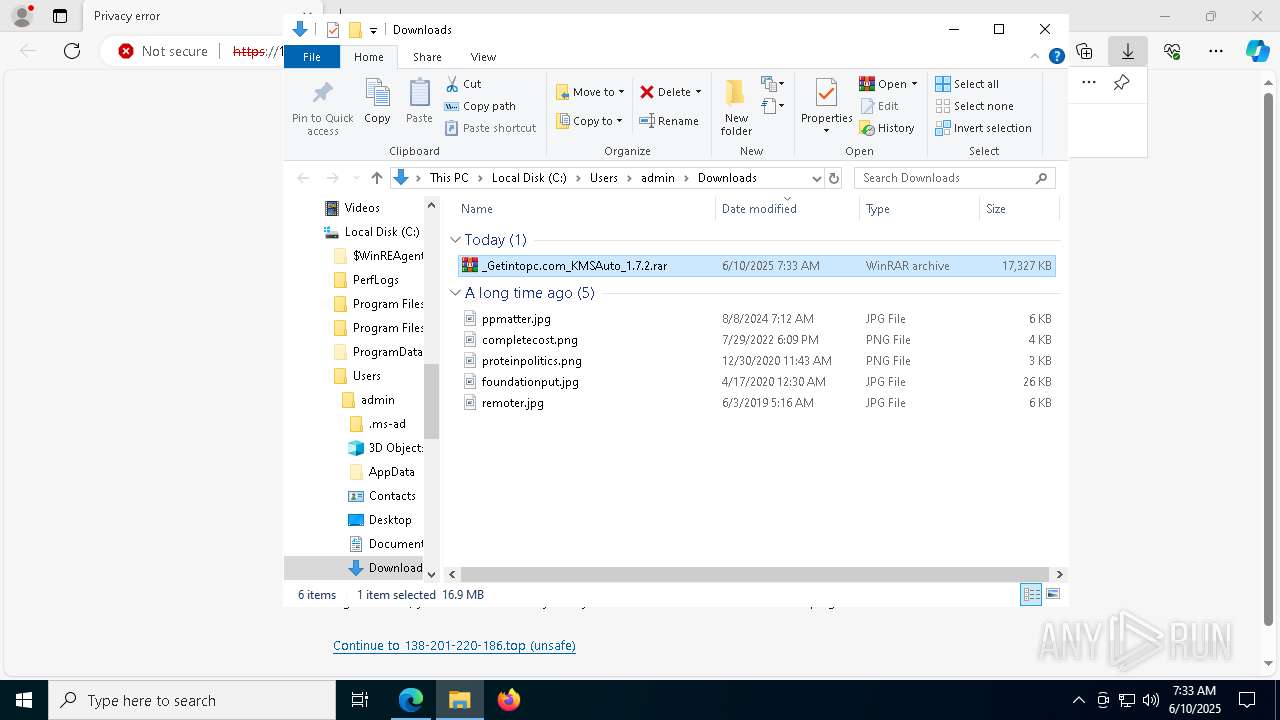
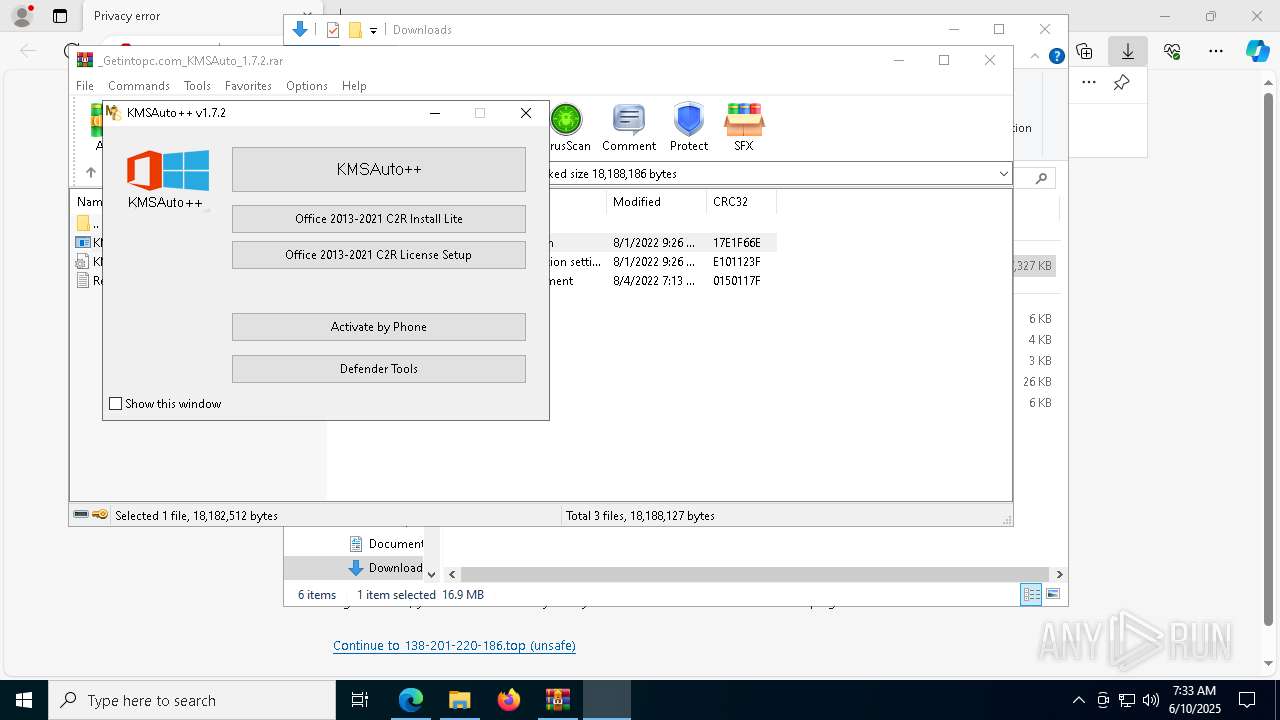
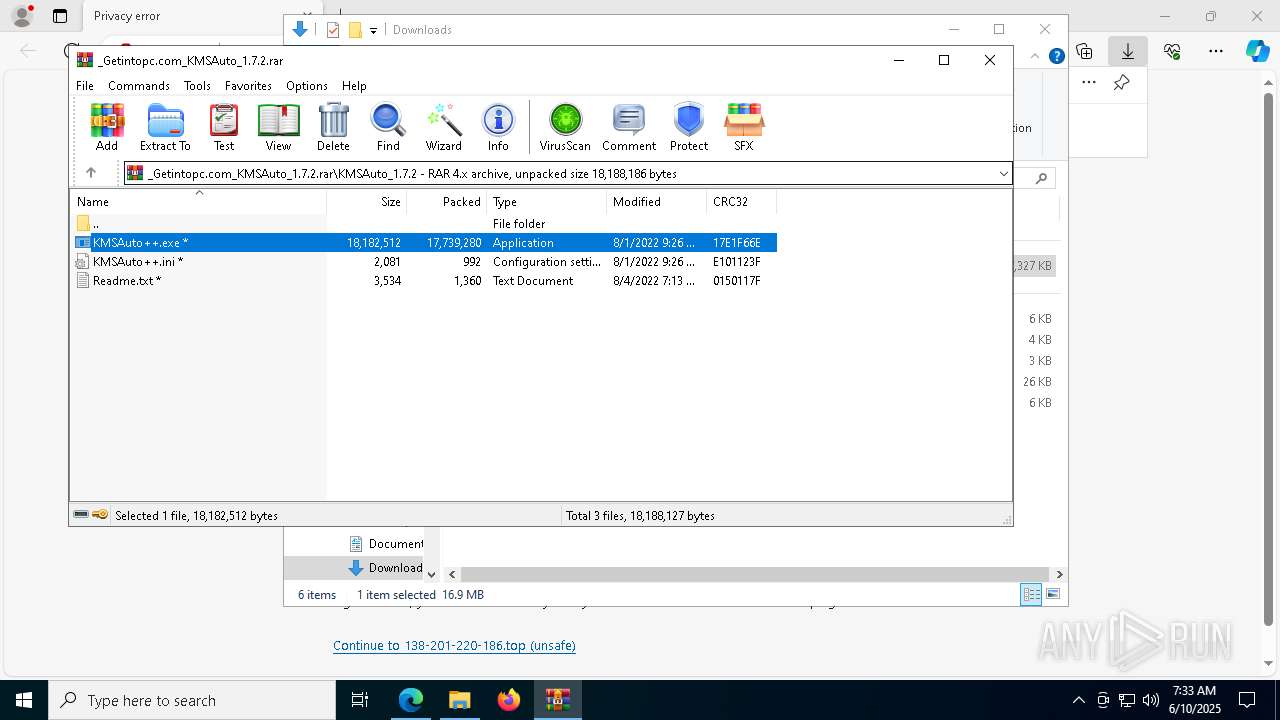
Manual execution by a user
- WinRAR.exe (PID: 3364)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3364)
Create files in a temporary directory
- KMSAuto++.exe (PID: 7872)
The sample compiled with english language support
- KMSAuto++.exe (PID: 7872)
Reads the machine GUID from the registry
- signtool.exe (PID: 5376)
- gatherosstate.exe (PID: 4628)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 2908)
- WMIC.exe (PID: 7596)
- WMIC.exe (PID: 7936)
- WMIC.exe (PID: 7740)
- WMIC.exe (PID: 2596)
- cscript.exe (PID: 616)
- cscript.exe (PID: 4776)
Reads the software policy settings
- signtool.exe (PID: 5376)
UPX packer has been detected
- KMSAuto++.exe (PID: 7872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
276
Monitored processes
146
Malicious processes
3
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | C:\WINDOWS\System32\sc.exe qc wlidsvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | C:\WINDOWS\System32\sc.exe qc licensemanager | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | C:\WINDOWS\System32\sc.exe start wlidsvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1056 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | cscript //nologo "C:\Users\admin\AppData\Local\Temp\slmgr.vbs" /ipk VK7JG-NPHTM-C97JM-9MPGT-3V66T | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 680 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 896 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6008 --field-trial-handle=2332,i,9678040254931794599,14027952295641534189,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3116 --field-trial-handle=2360,i,6160910446182306628,15338207339499163682,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1324 | "C:\WINDOWS\Sysnative\cmd.exe" /c cscript //nologo "C:\Users\admin\AppData\Local\Temp\slmgr.vbs" /xpr | C:\Windows\System32\cmd.exe | — | KMSAuto++.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 119
Read events
16 062
Write events
55
Delete events
2
Modification events
| (PID) Process: | (4400) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4400) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4400) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4400) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4400) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (4400) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (6072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
4
Suspicious files
210
Text files
53
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF11f5c7.TMP | — | |
MD5:— | SHA256:— | |||
| 6072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF11f5e6.TMP | — | |
MD5:— | SHA256:— | |||
| 6072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old~RF11f5f6.TMP | — | |
MD5:— | SHA256:— | |||
| 6072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old~RF11f5f6.TMP | — | |
MD5:— | SHA256:— | |||
| 6072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF11f605.TMP | — | |
MD5:— | SHA256:— | |||
| 6072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF11f605.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
44
DNS requests
47
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5236 | msedge.exe | GET | 200 | 69.192.161.44:80 | http://x1.i.lencr.org/ | unknown | — | — | whitelisted |
5236 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:2ejI4aYr-vopQJwtOrS7sEZhwwtdGcIJDmq6MnQ4N9s&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
5236 | msedge.exe | GET | 200 | 92.123.104.37:80 | http://r11.i.lencr.org/ | unknown | — | — | whitelisted |
5236 | msedge.exe | GET | 204 | 150.171.73.11:80 | http://edge-http.microsoft.com/captiveportal/generate_204 | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7732 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7732 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
616 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6072 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5236 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5236 | msedge.exe | 138.201.220.186:443 | 138-201-220-186.top | Hetzner Online GmbH | DE | unknown |
5236 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
138-201-220-186.top |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
x1.i.lencr.org |
| whitelisted |
r11.i.lencr.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |