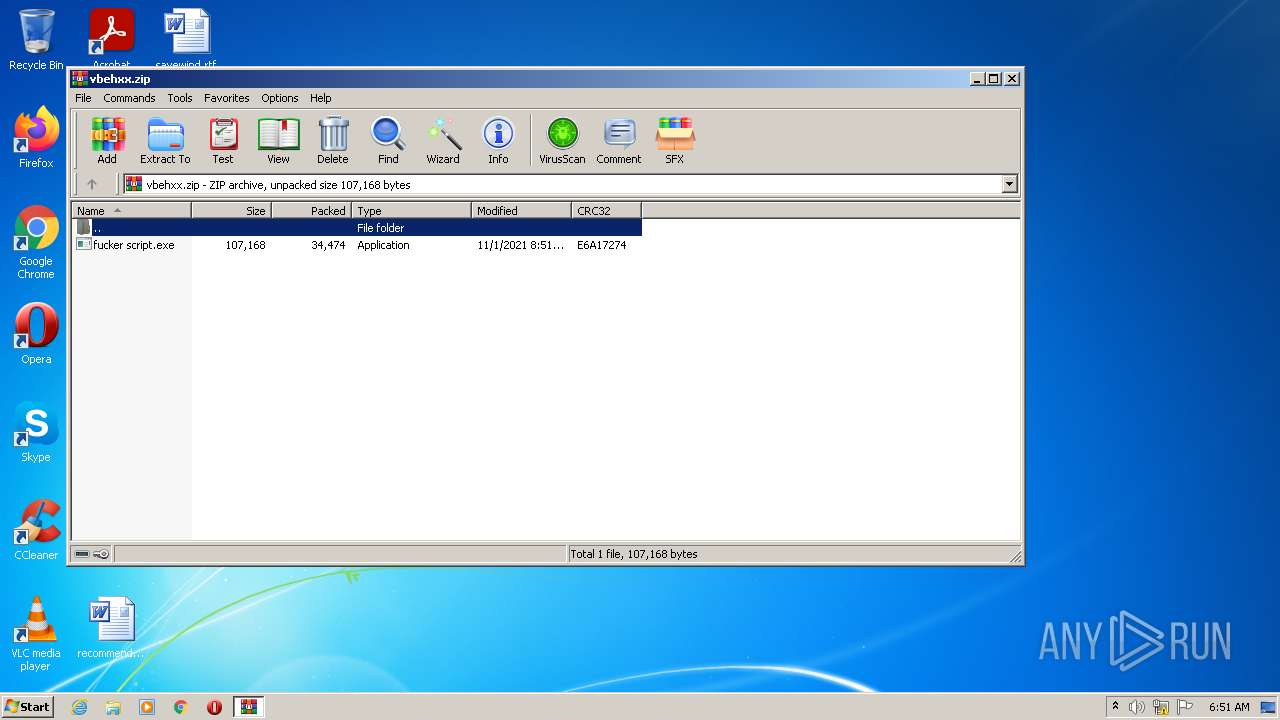
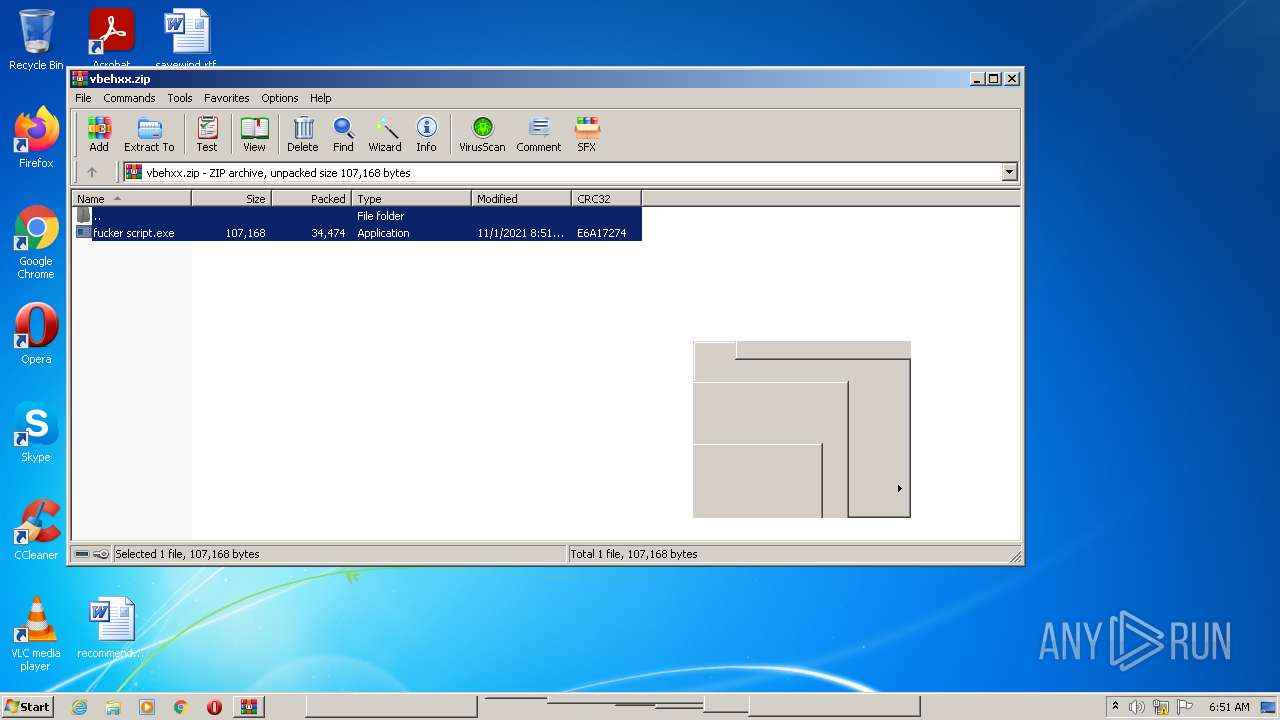
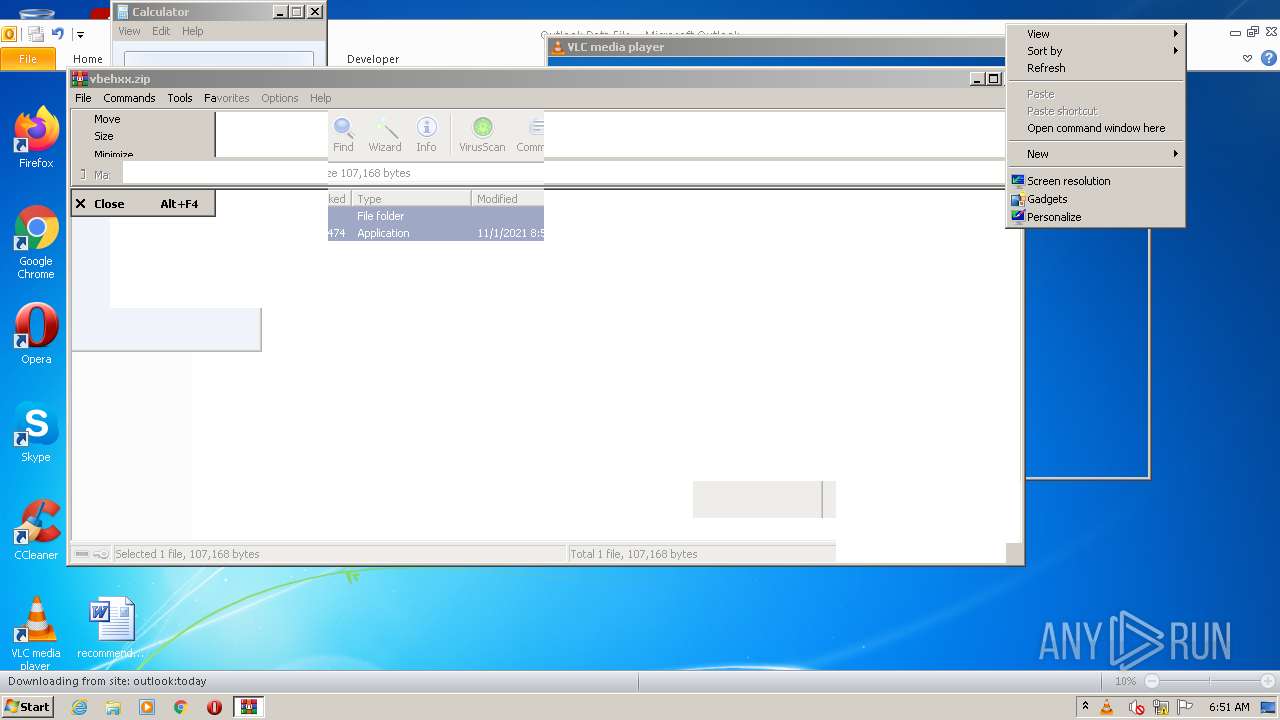
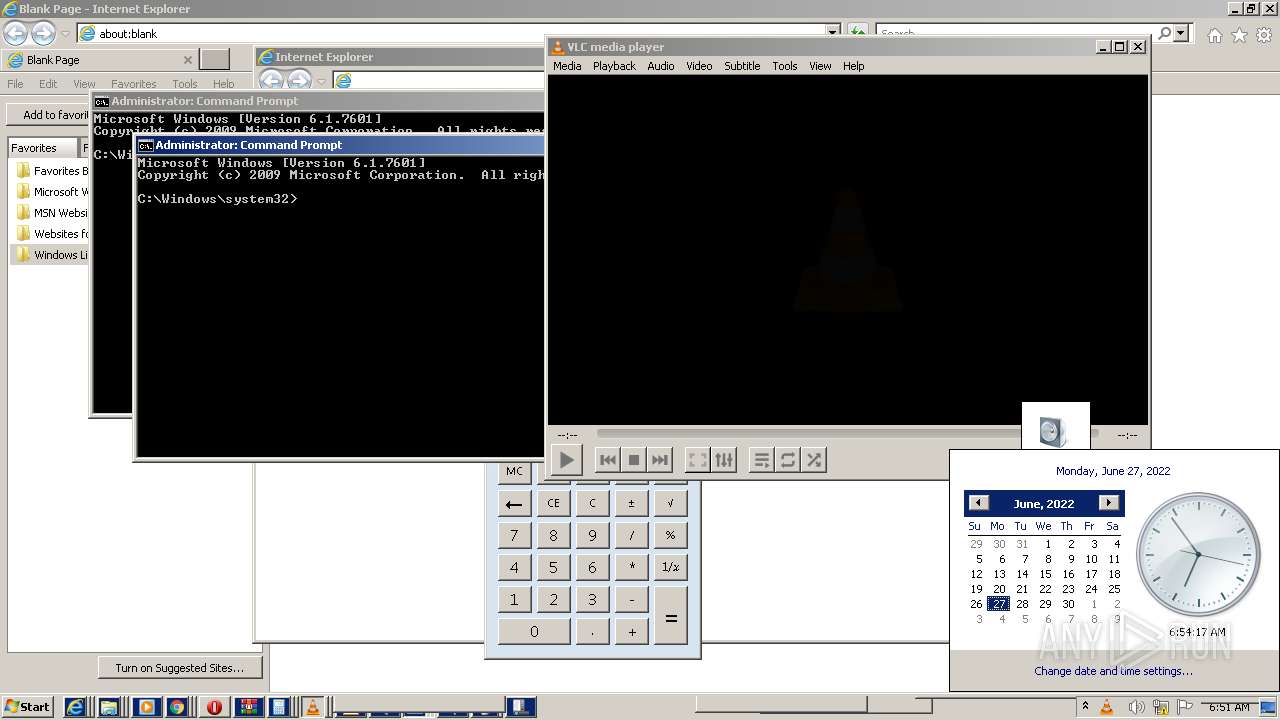
| File name: | vbehxx.zip |
| Full analysis: | https://app.any.run/tasks/c008eb05-0e0e-49e8-9d49-f827d6c4d2eb |
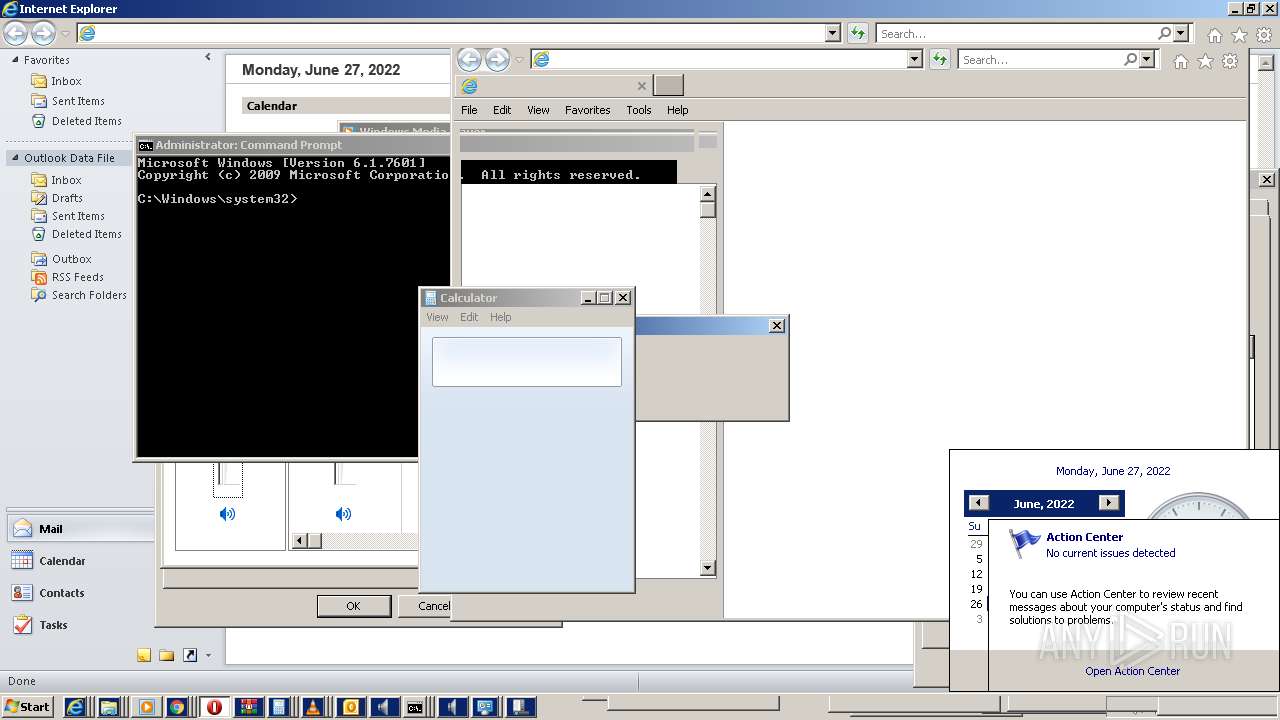
| Verdict: | Malicious activity |
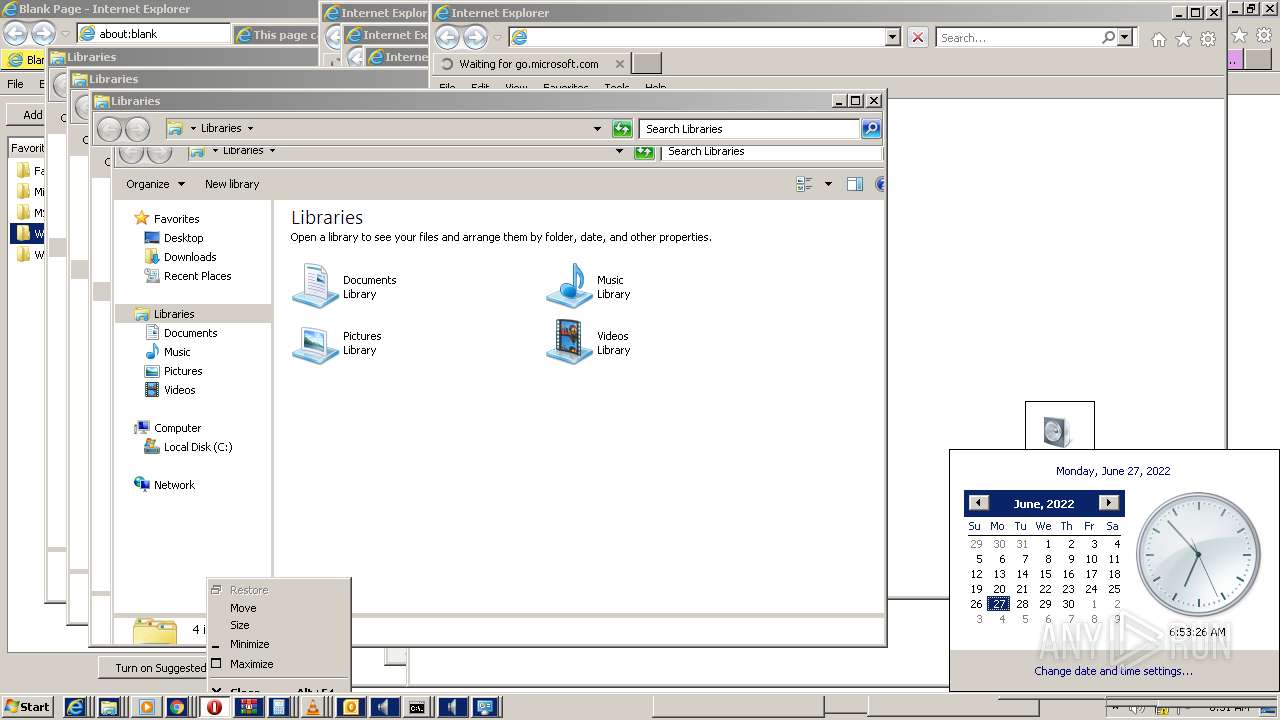
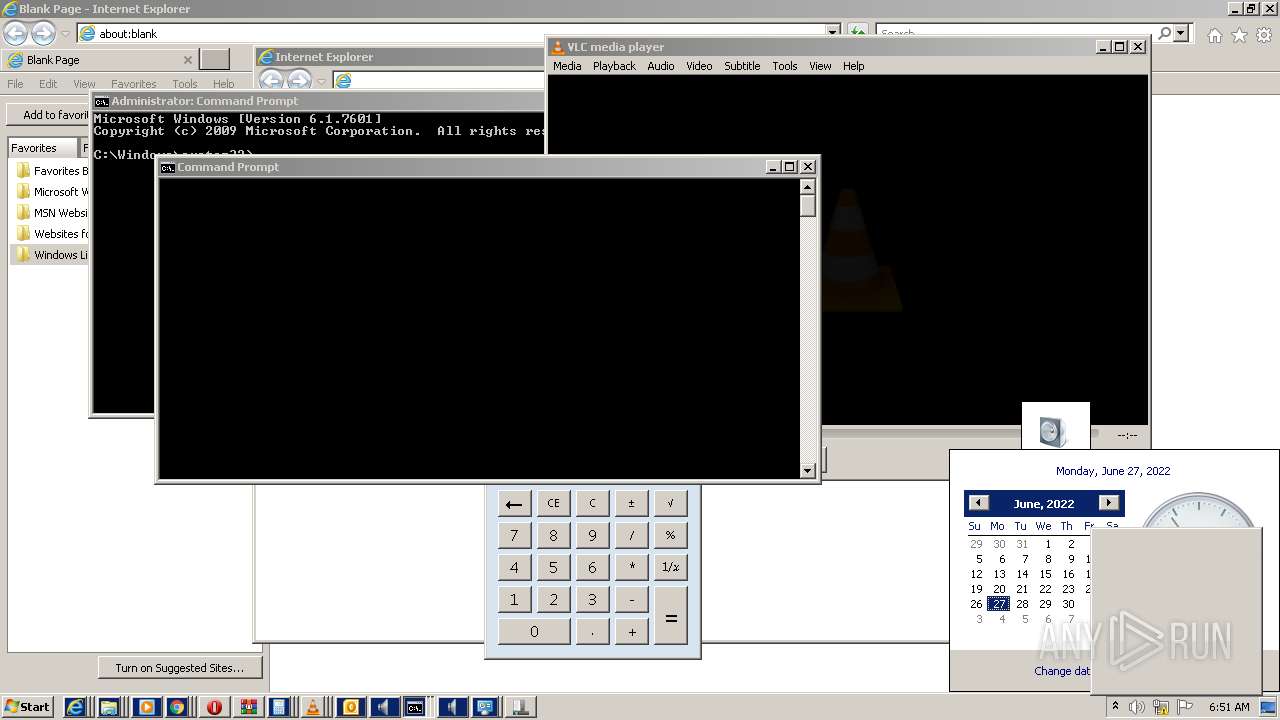
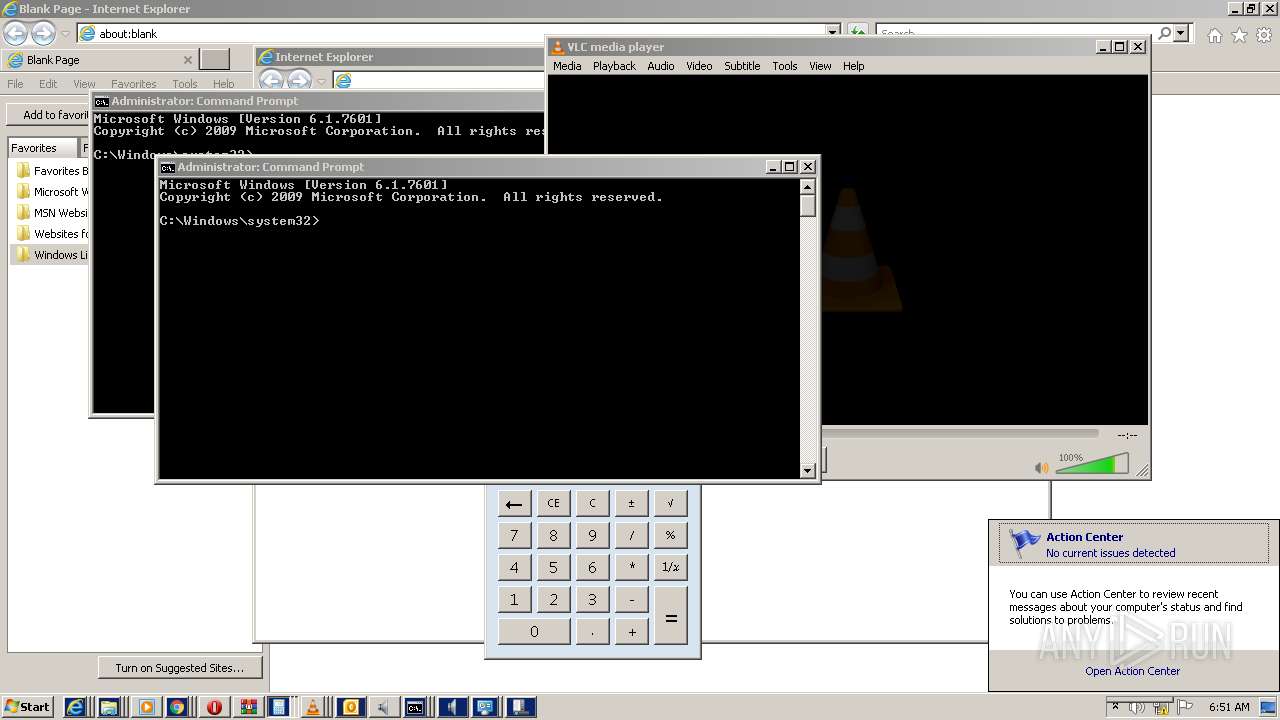
| Analysis date: | June 27, 2022, 05:51:42 |
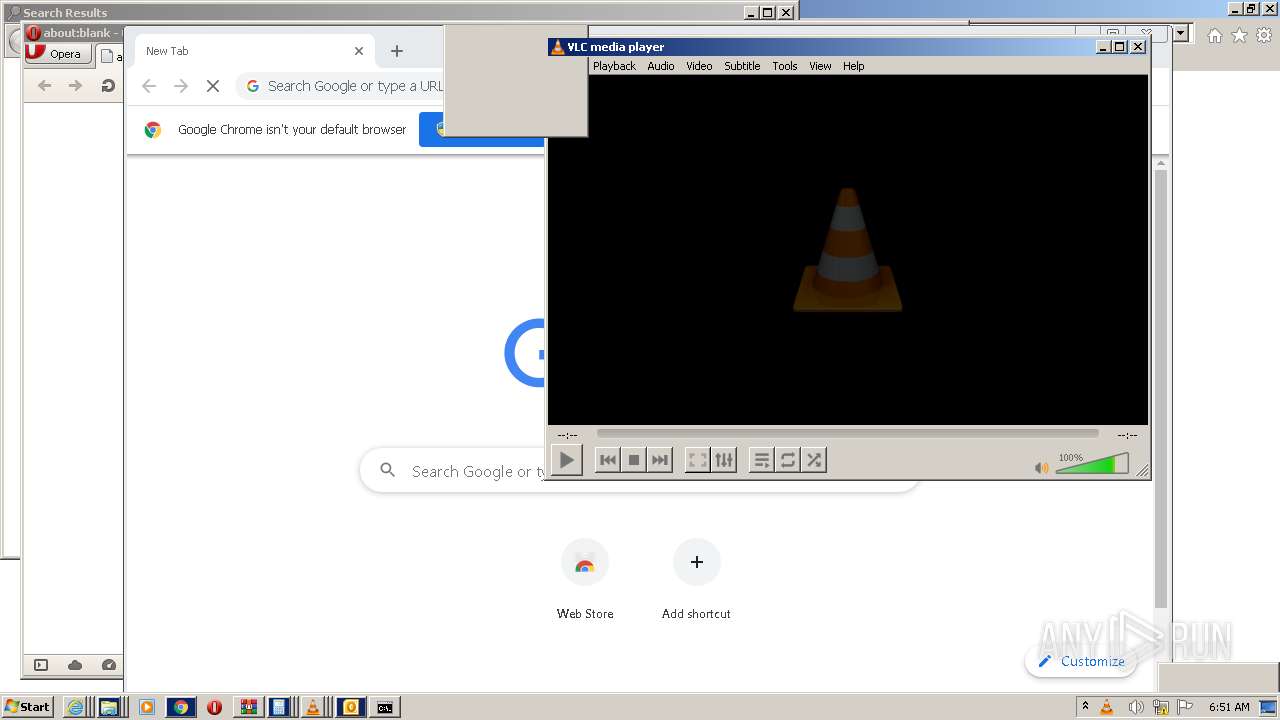
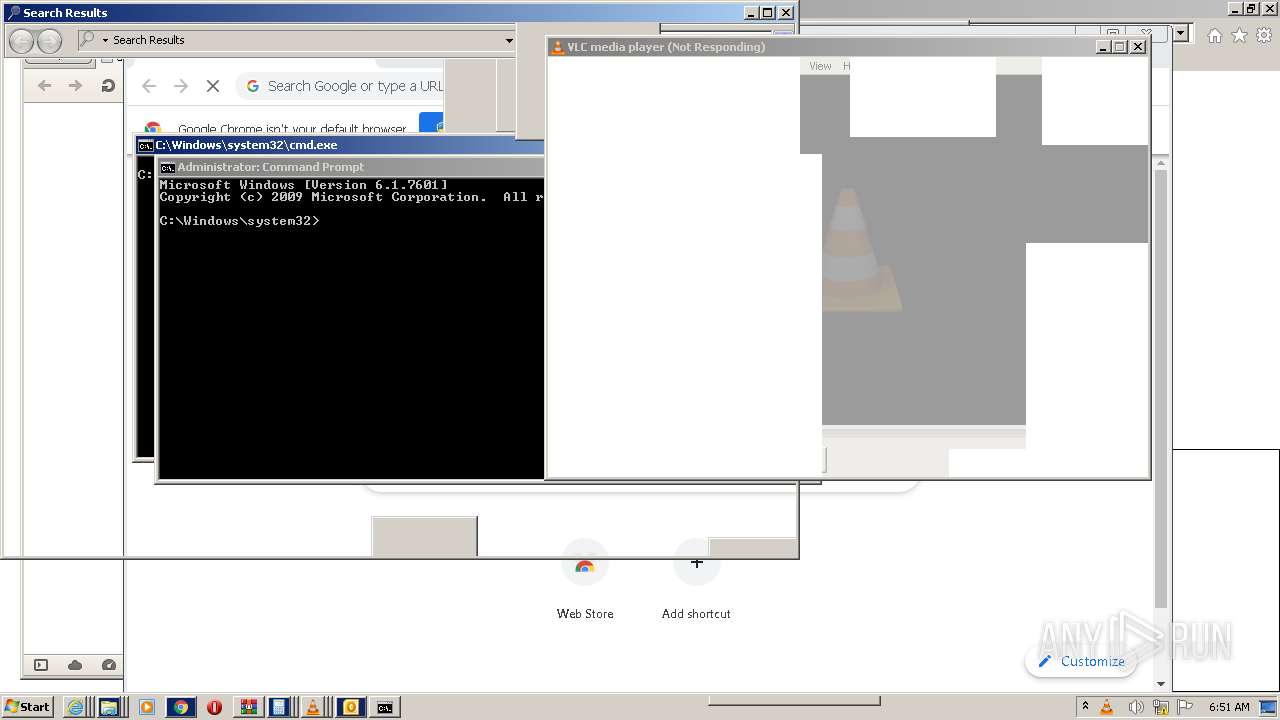
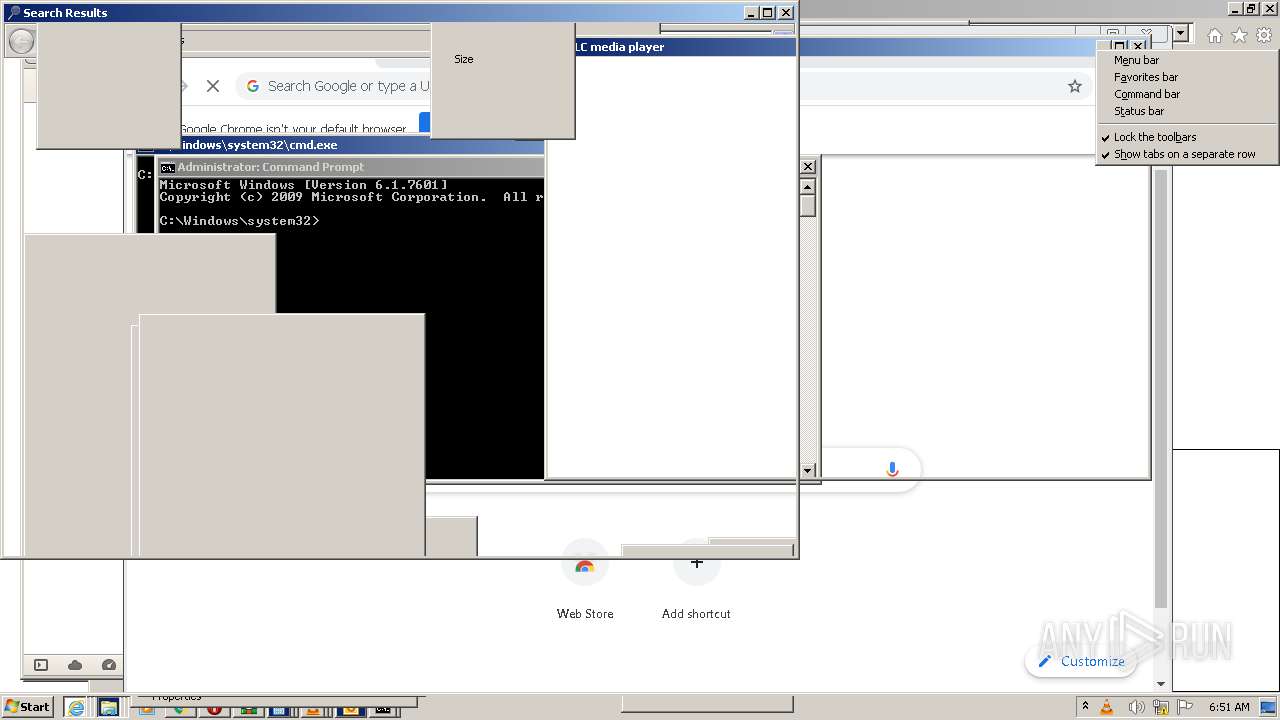
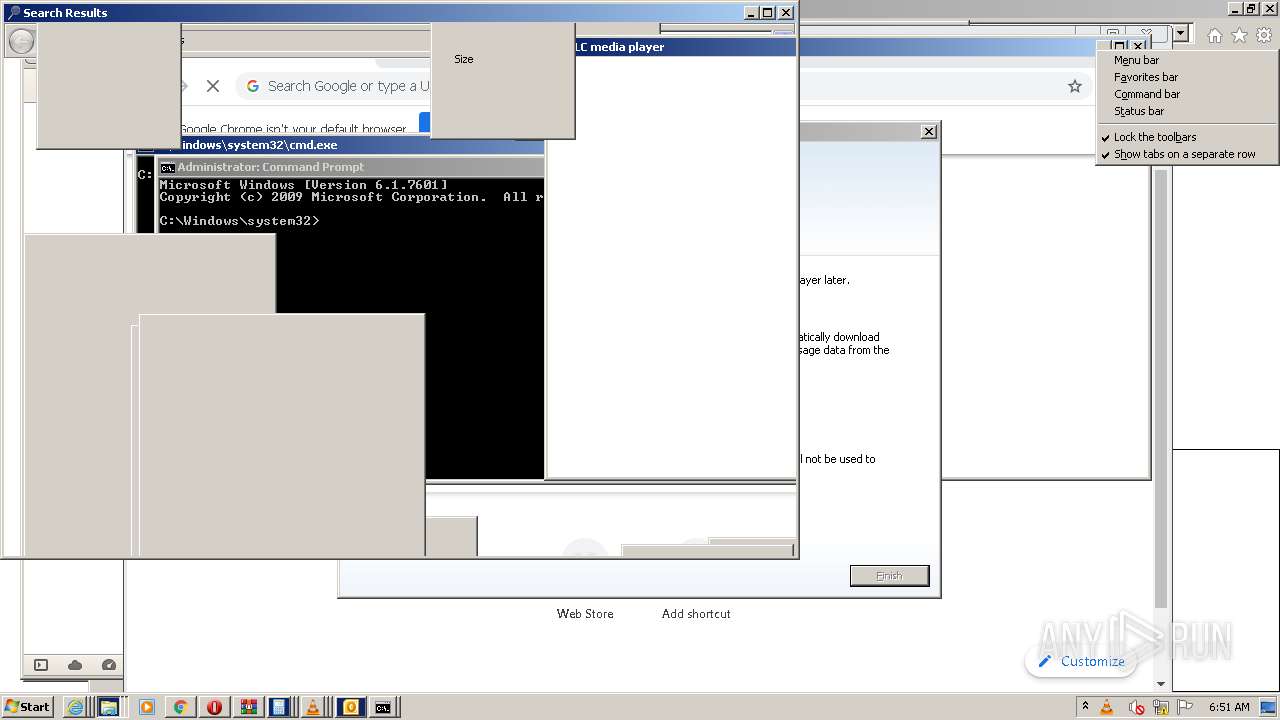
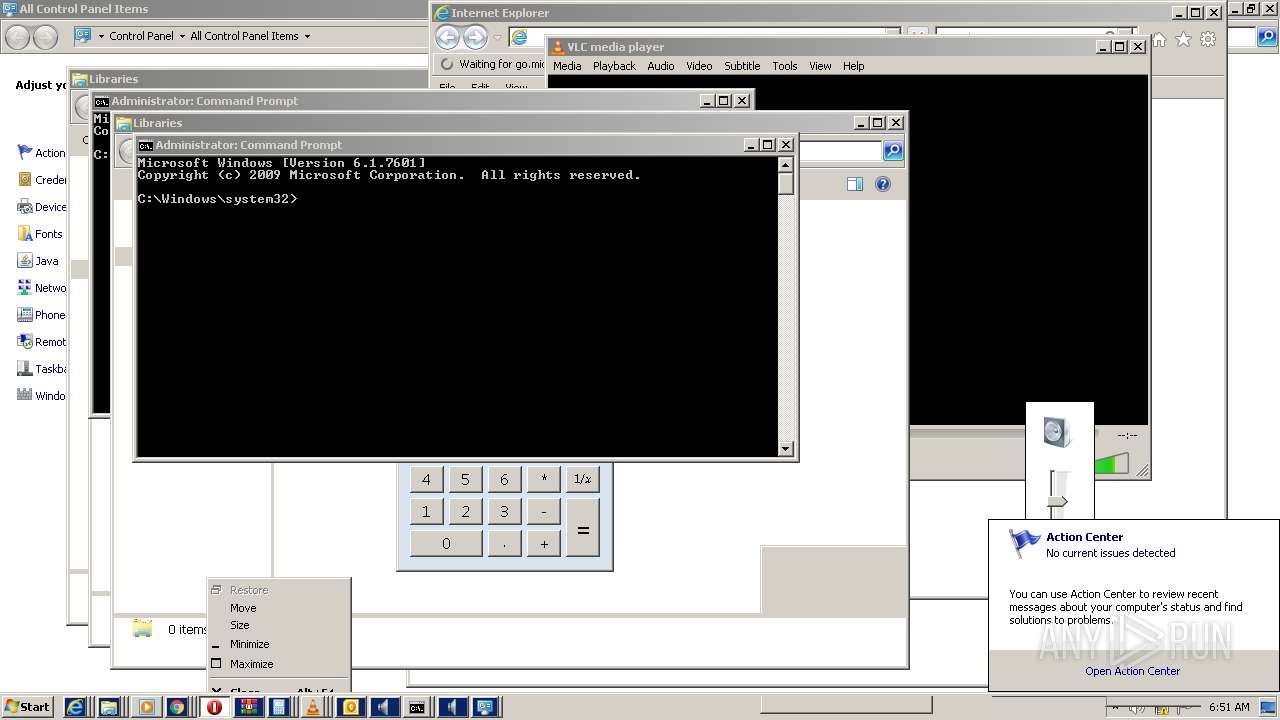
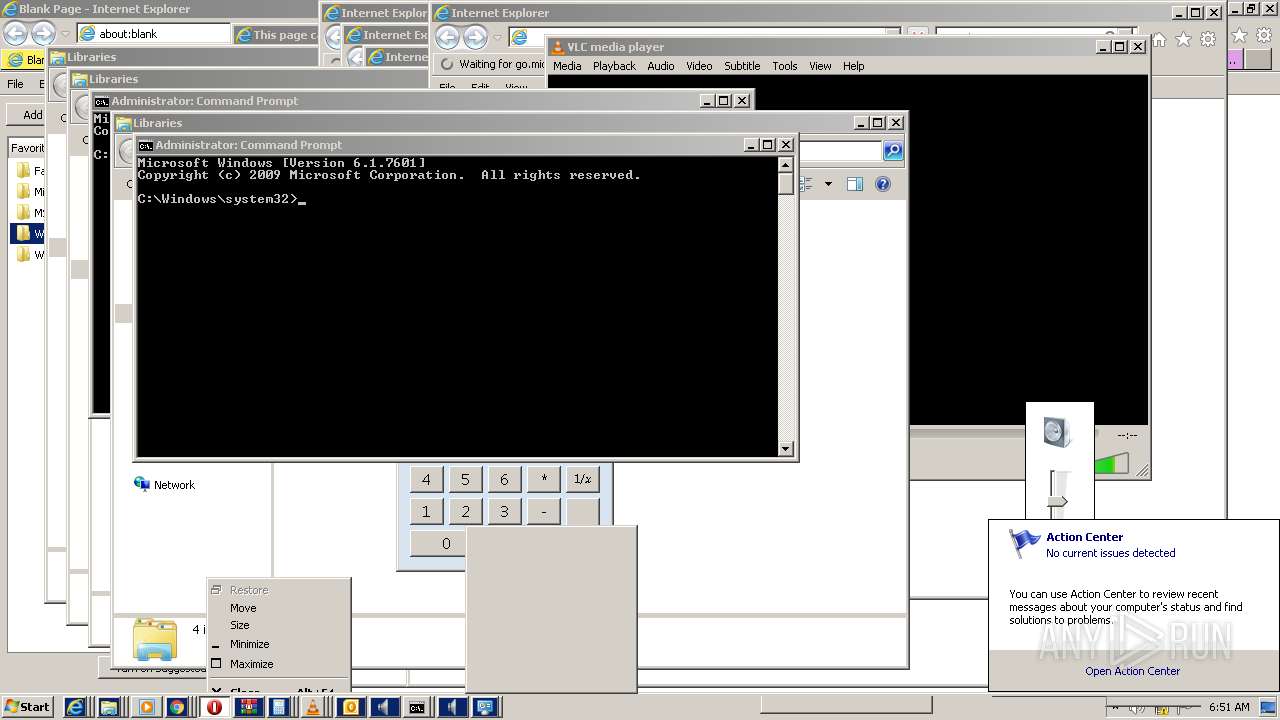
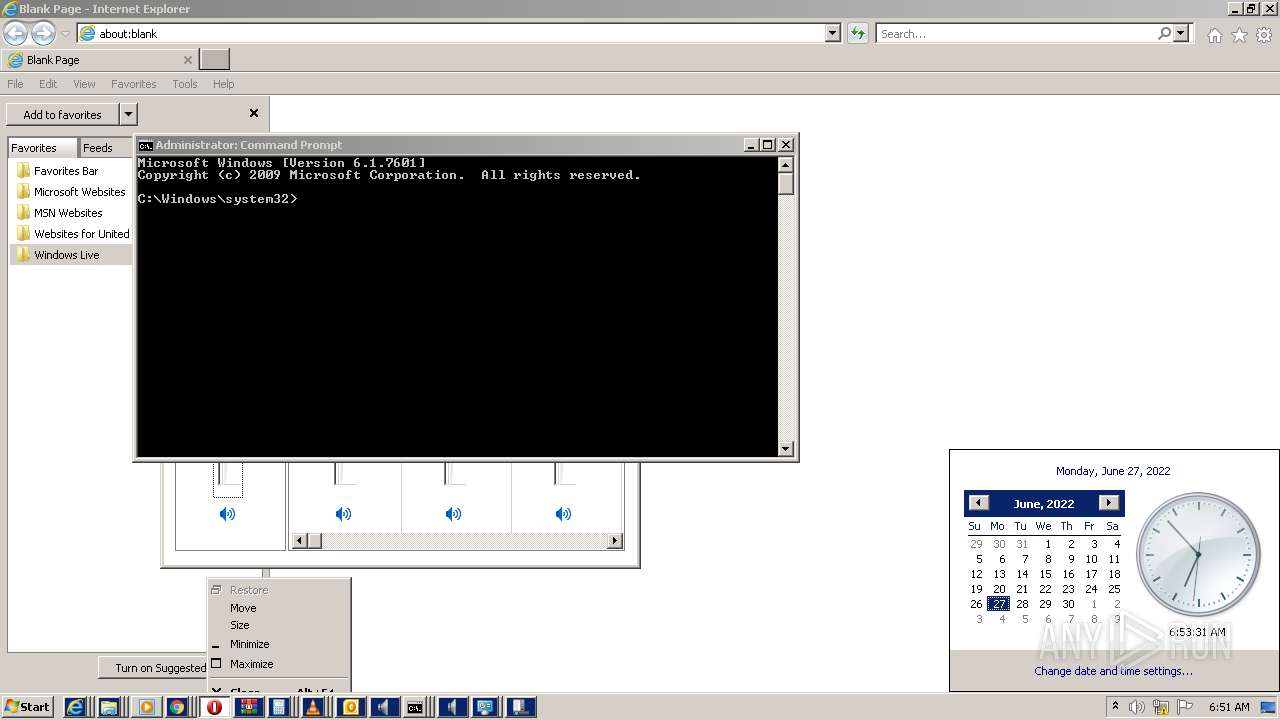
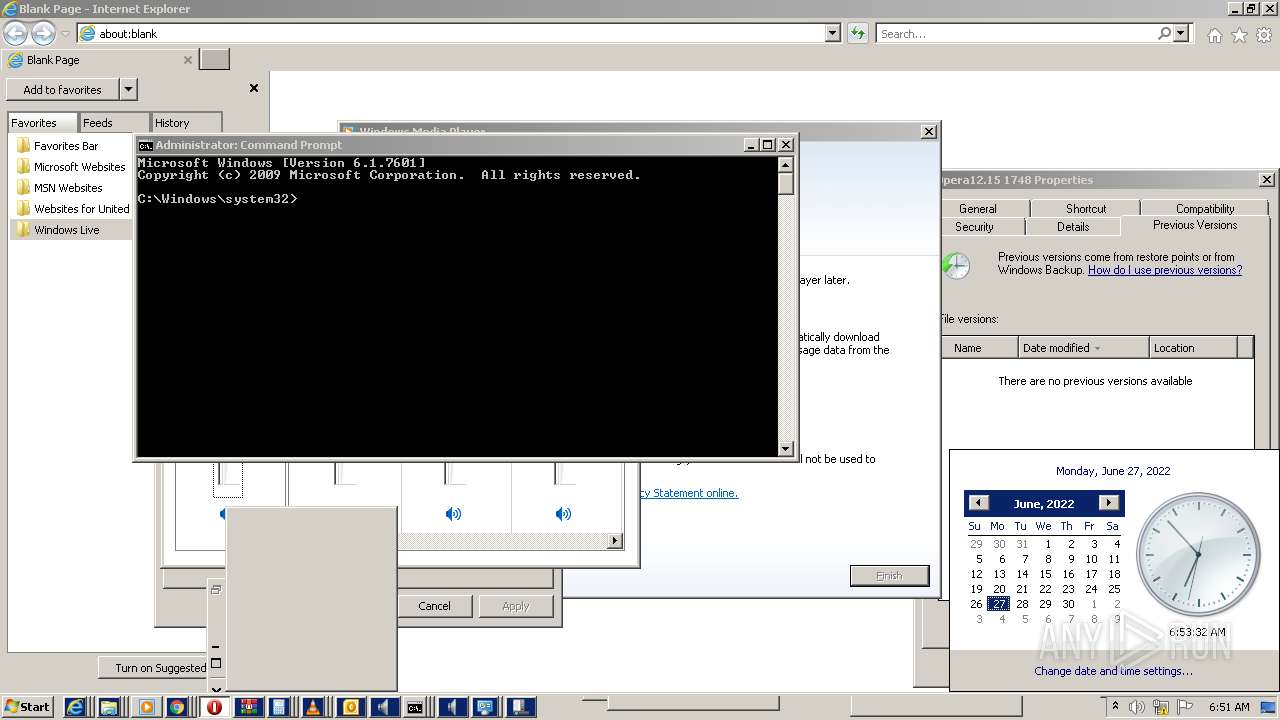
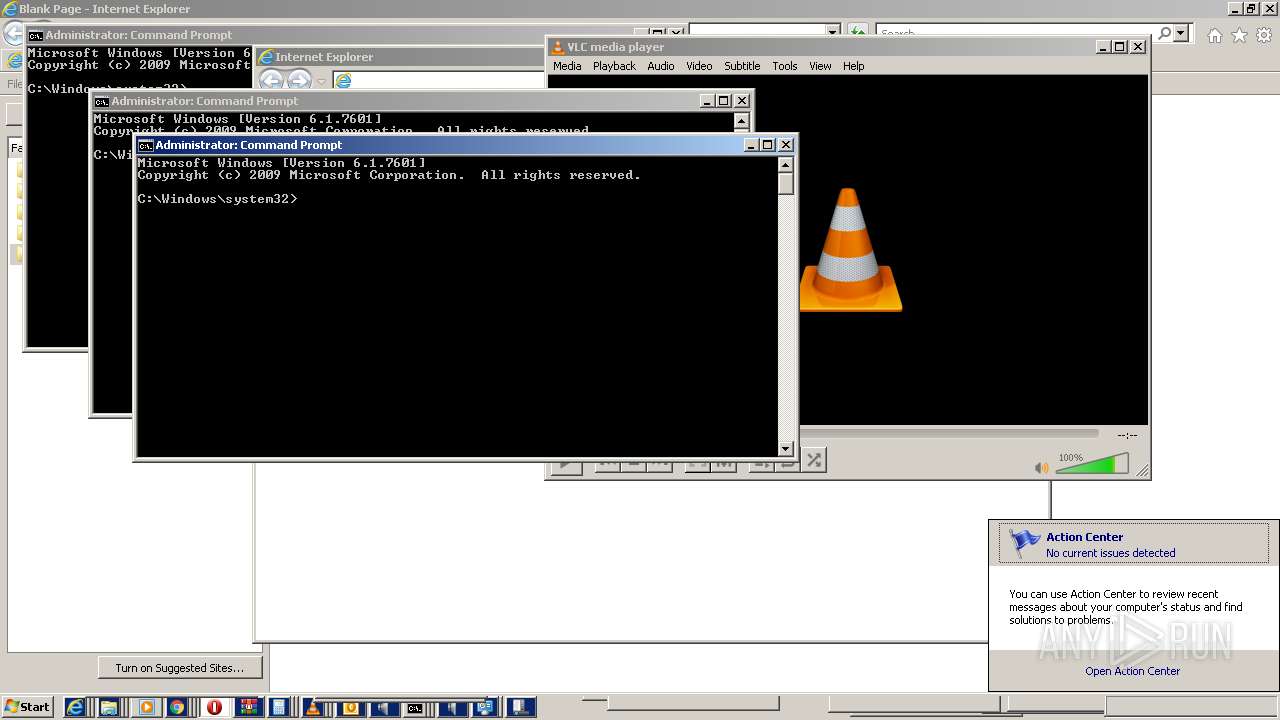
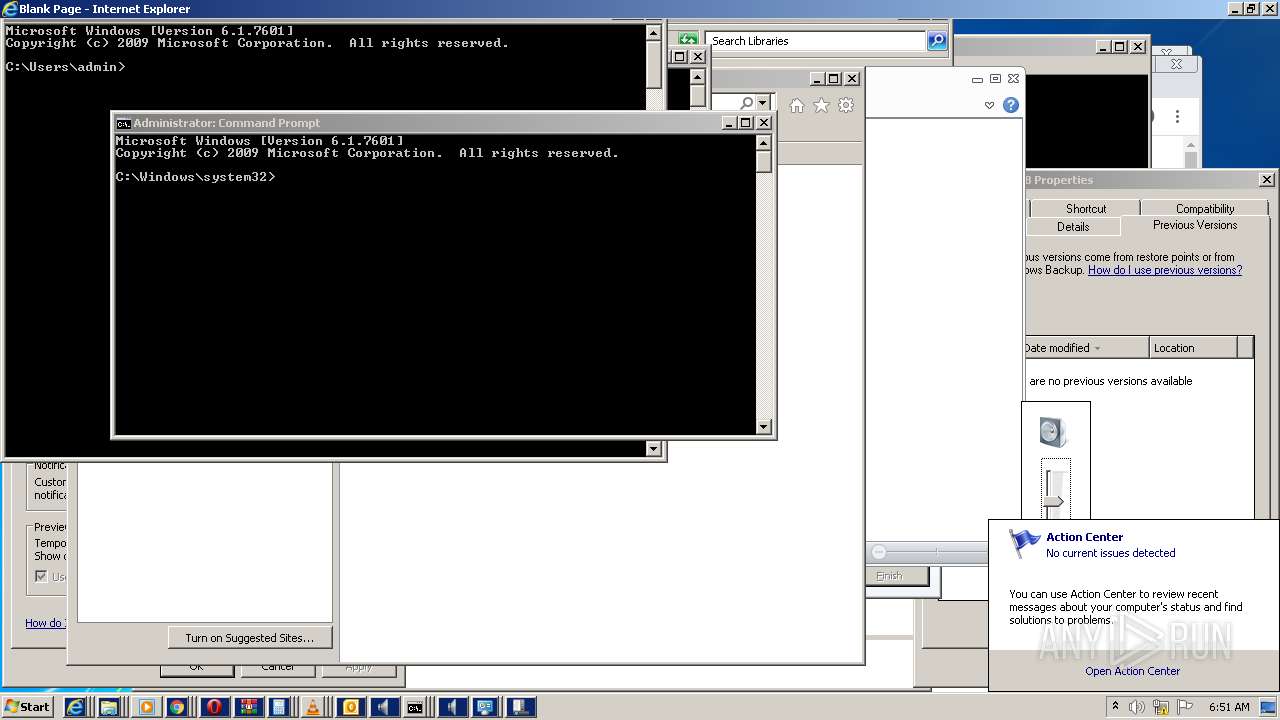
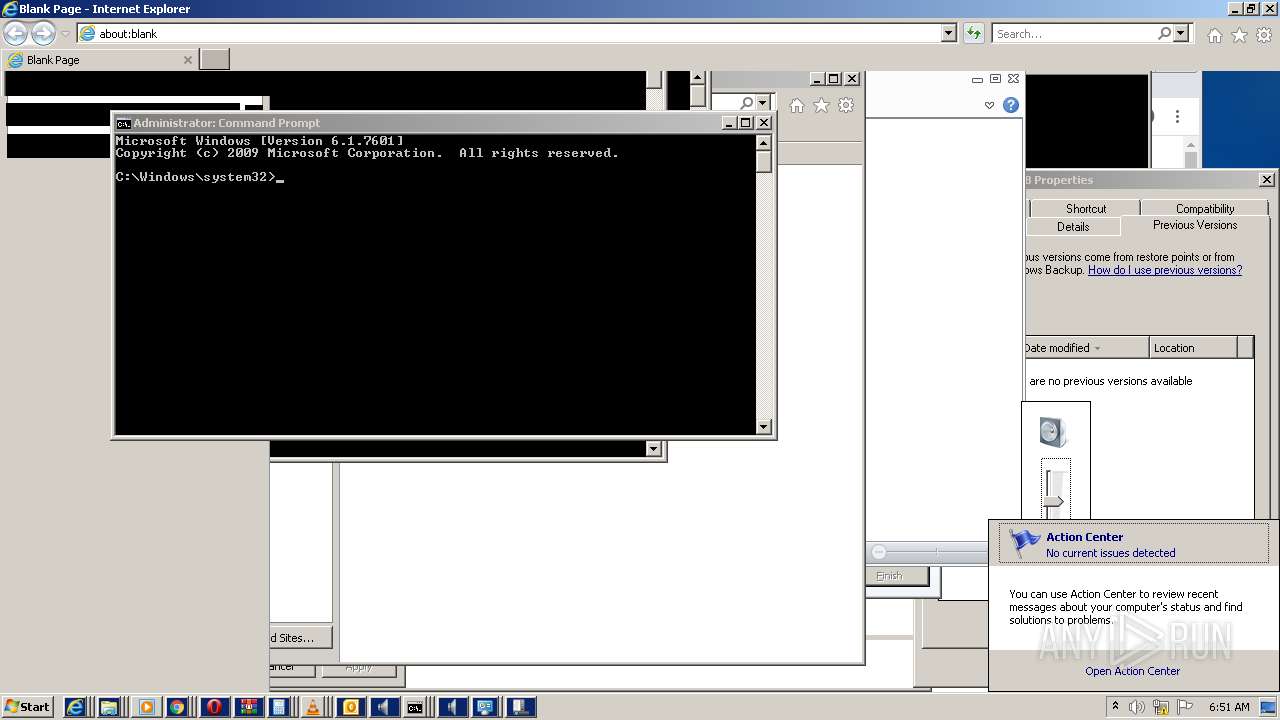
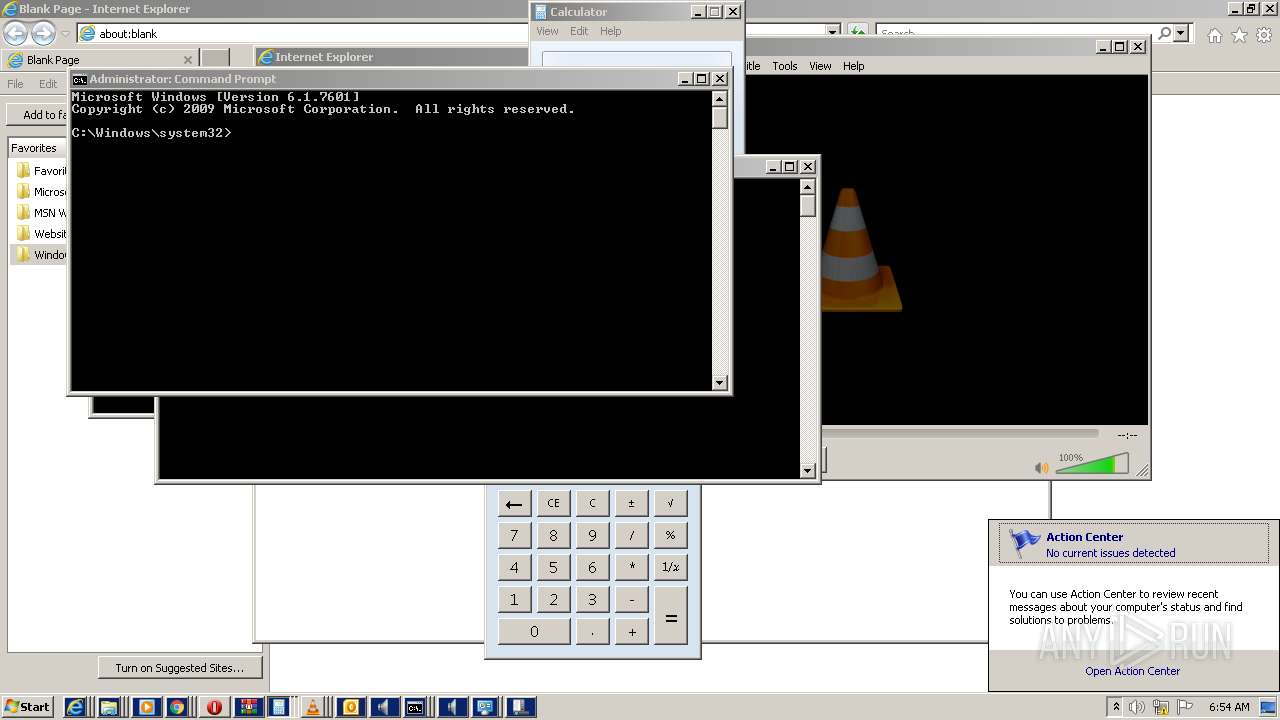
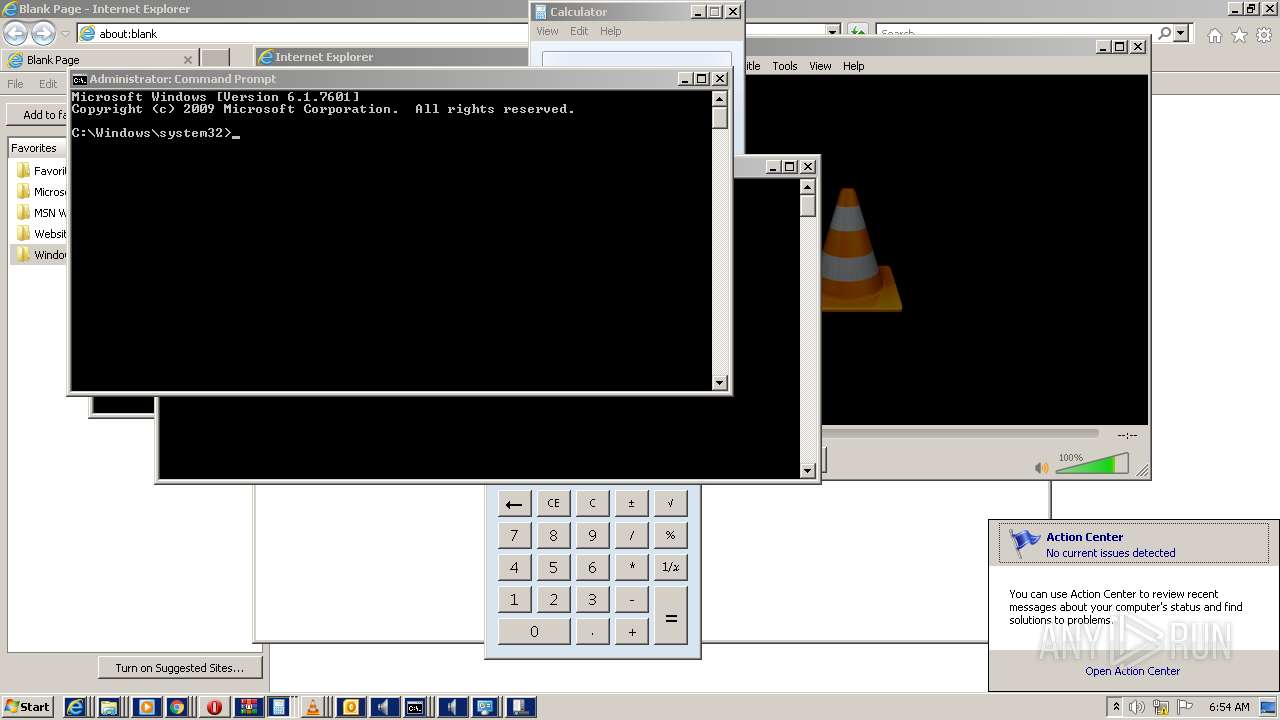
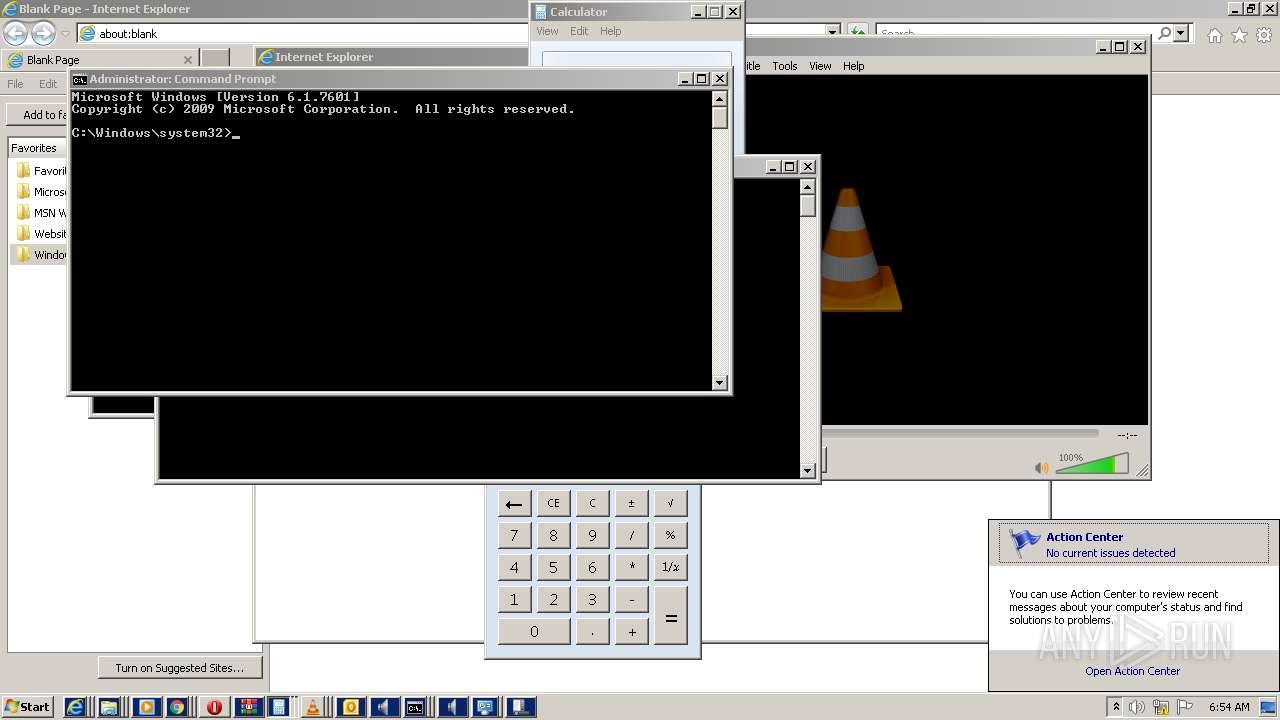
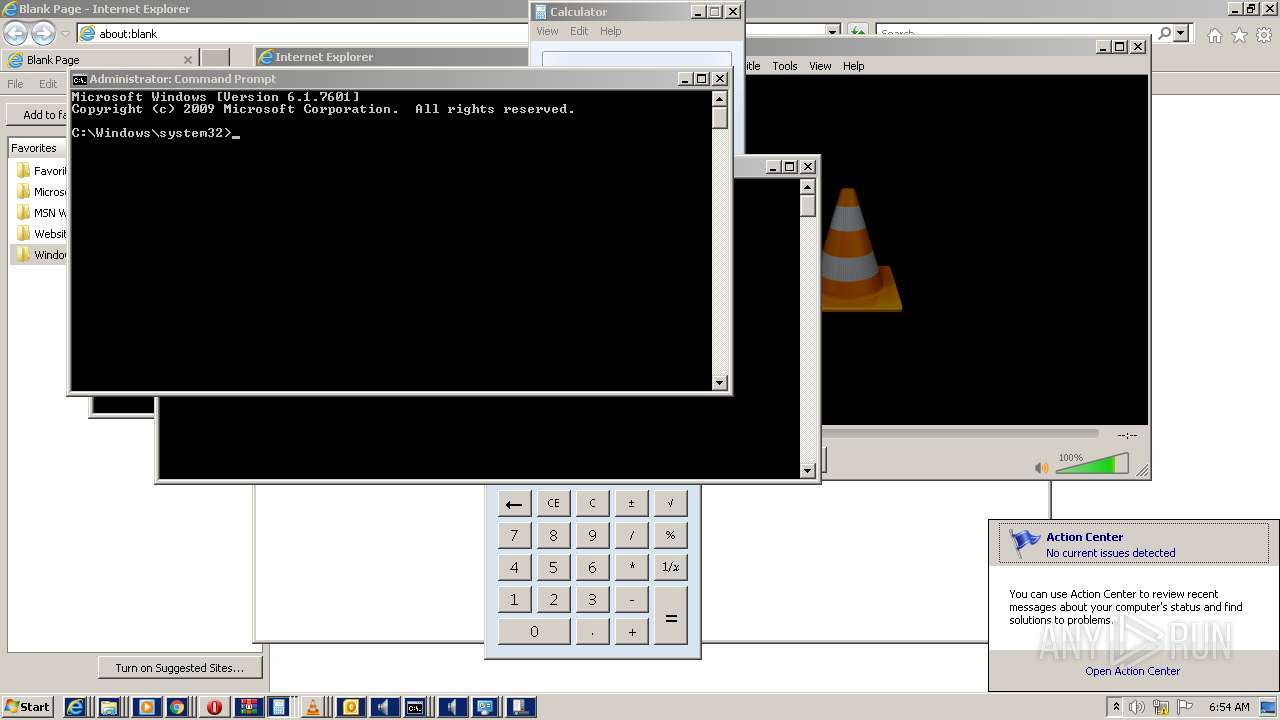
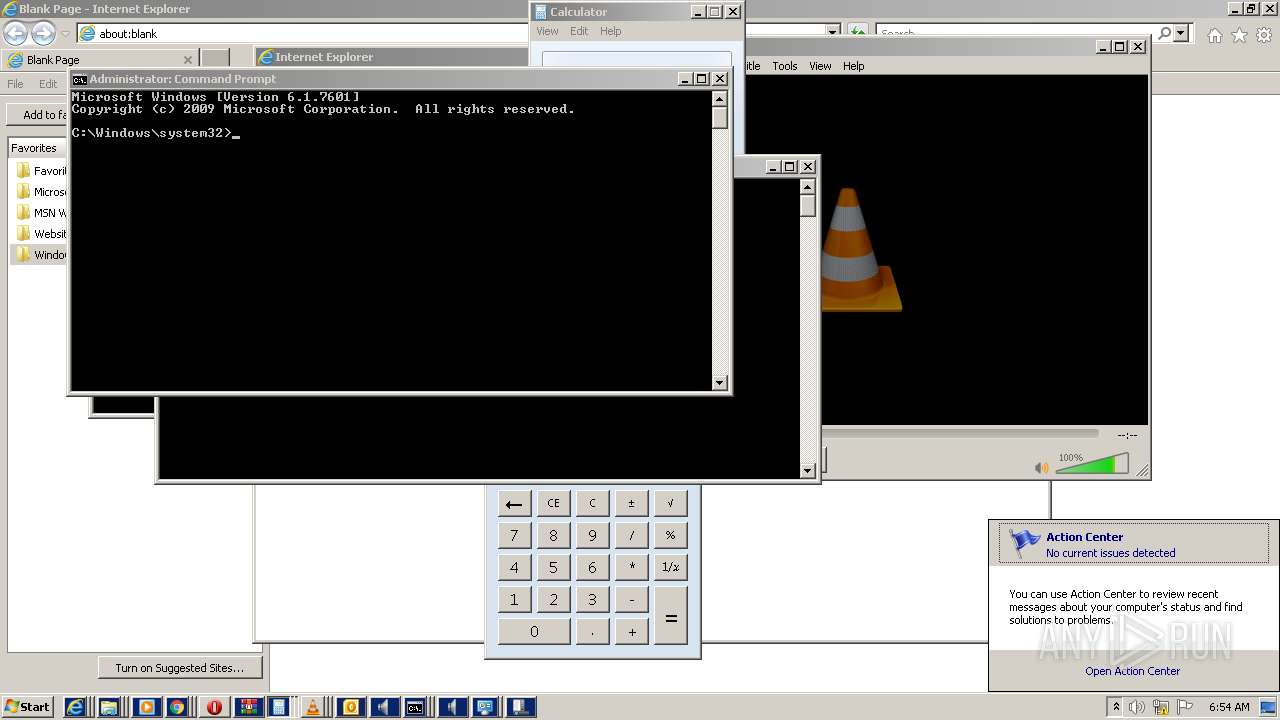
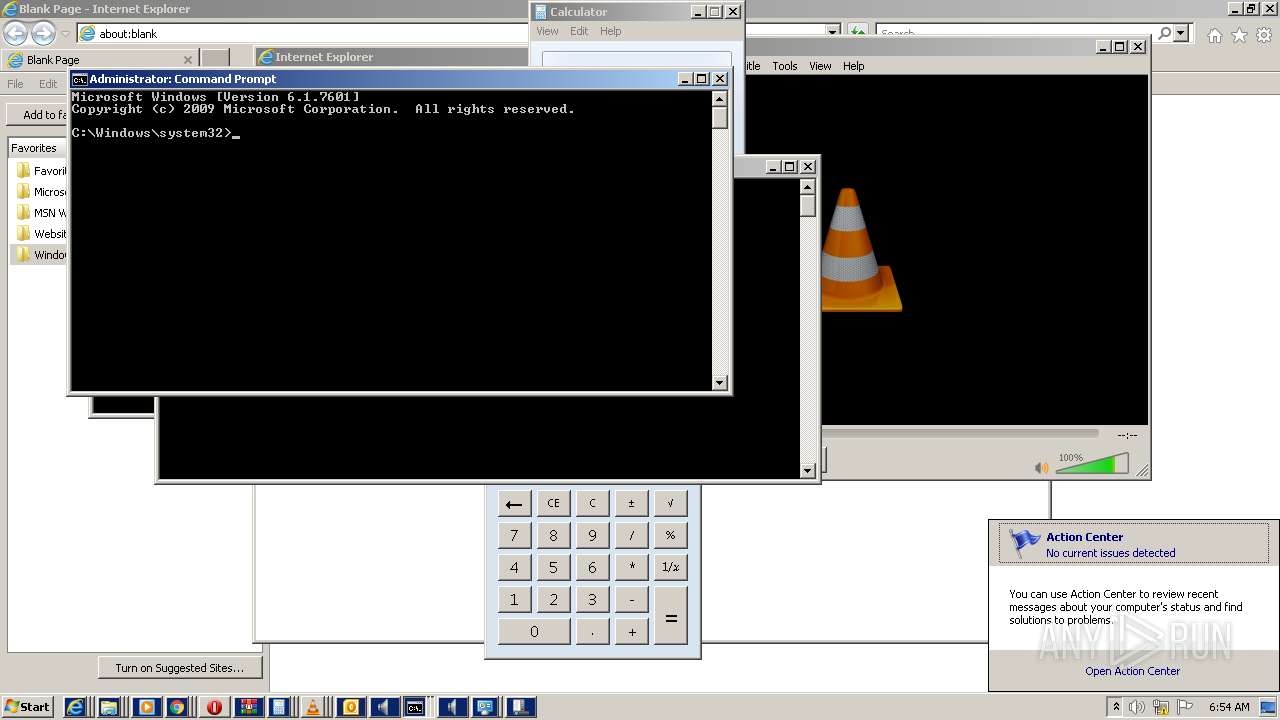
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | DFB15C3BDEFF52B5B2D88F8CCA0B76FF |
| SHA1: | 02CE8A26A825CBE44A28820415DB10CF5C75CF27 |
| SHA256: | 2E80059A92E23F07ECE25CD25F4E855CB01C8623A5CA9D8D63756C2273368563 |
| SSDEEP: | 768:YgV76KrqScCf4h4ywSC1/VzXDiAJgwkLF3YwzyrNjP:Yc6Kr27SV1/5z5Hhz |
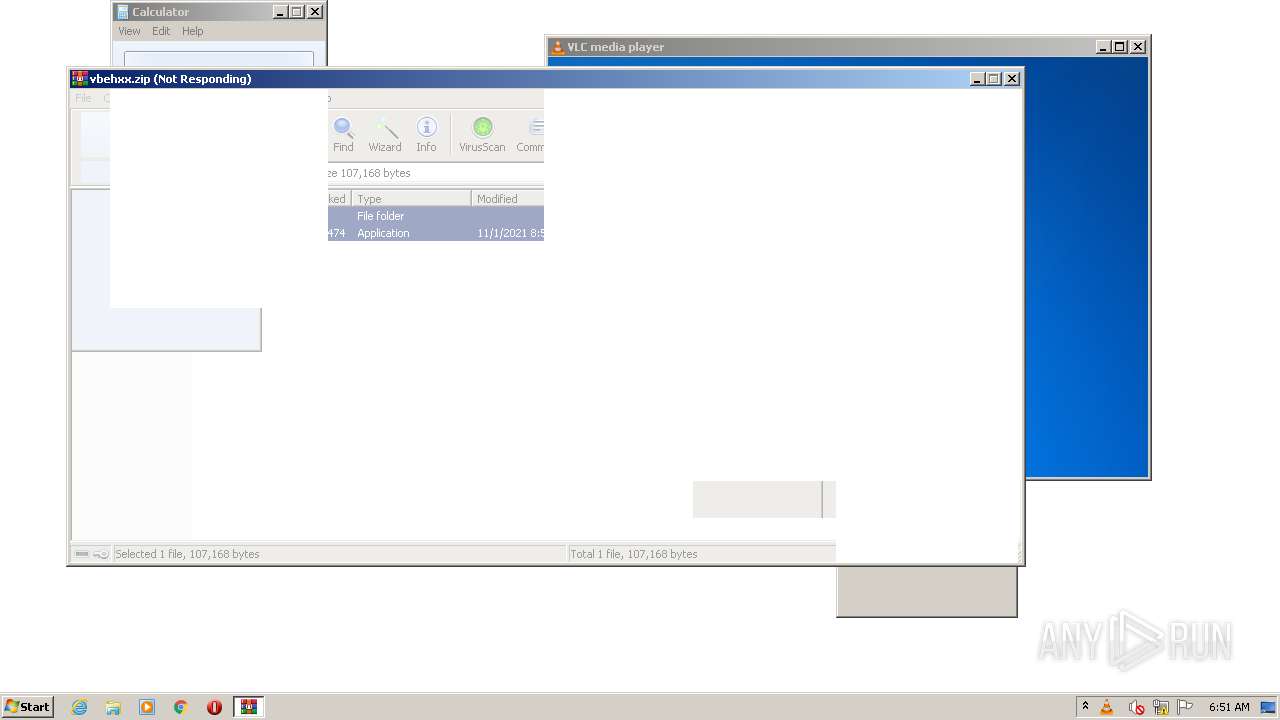
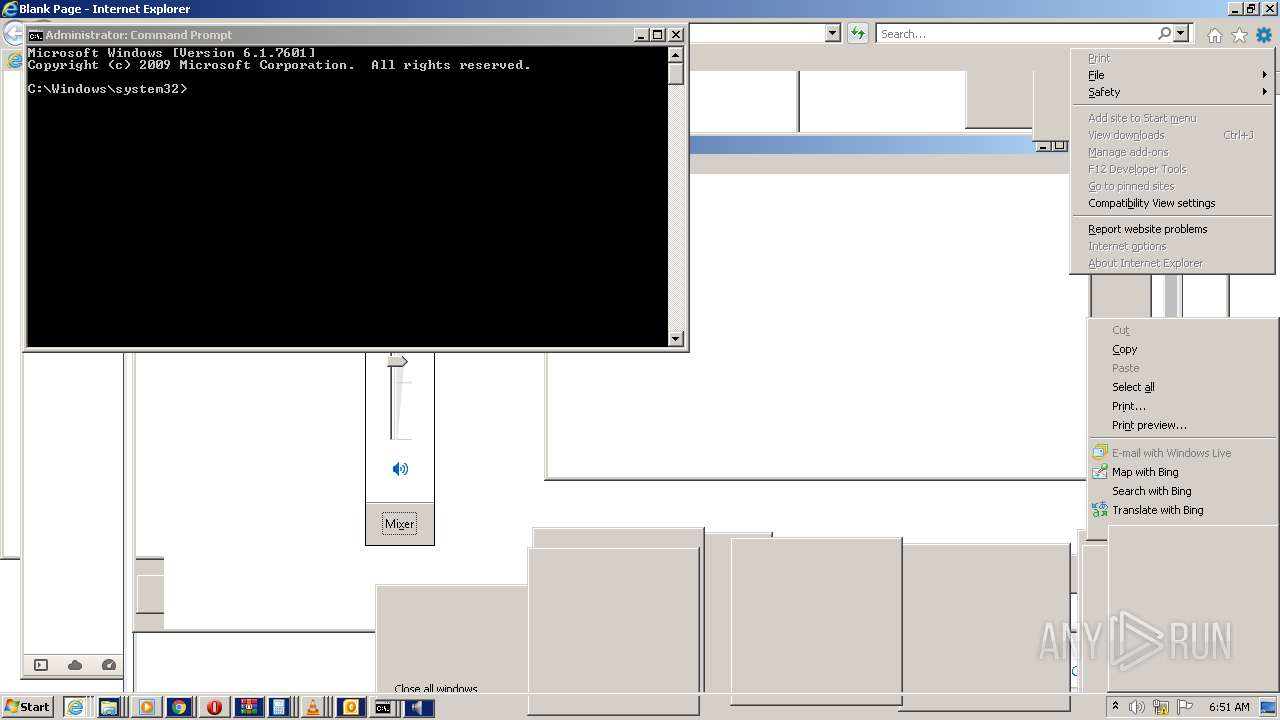
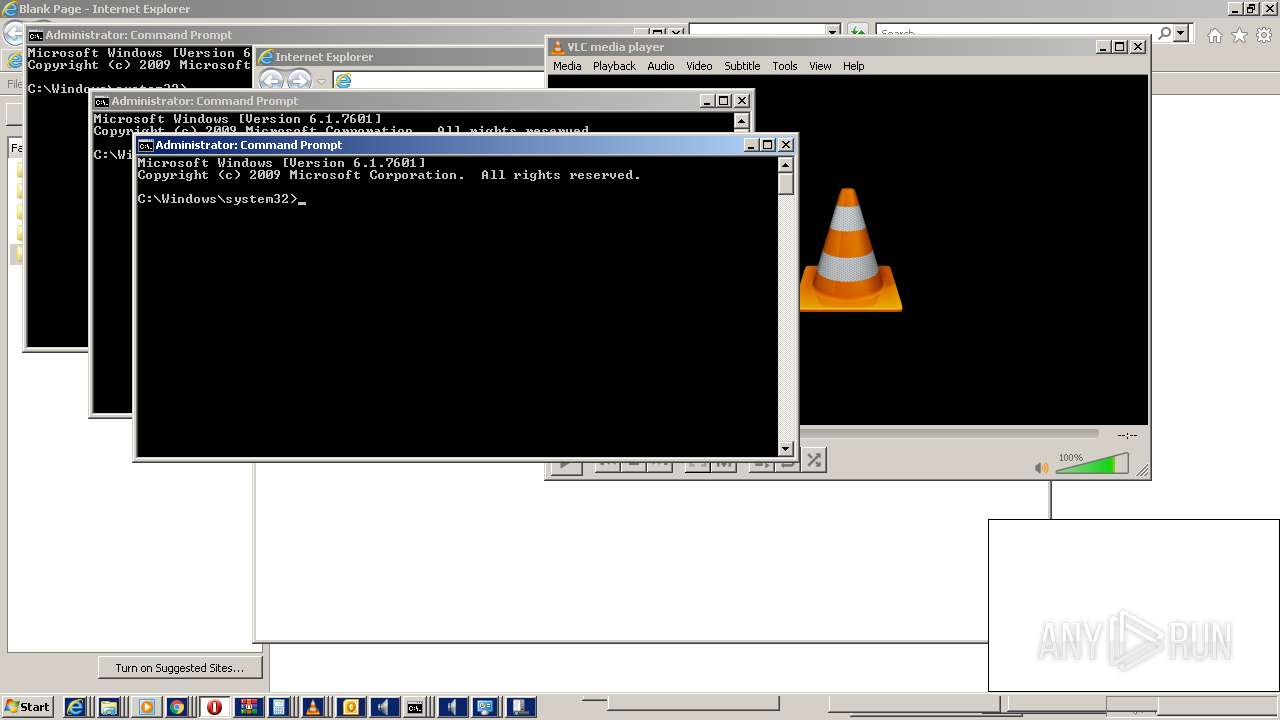
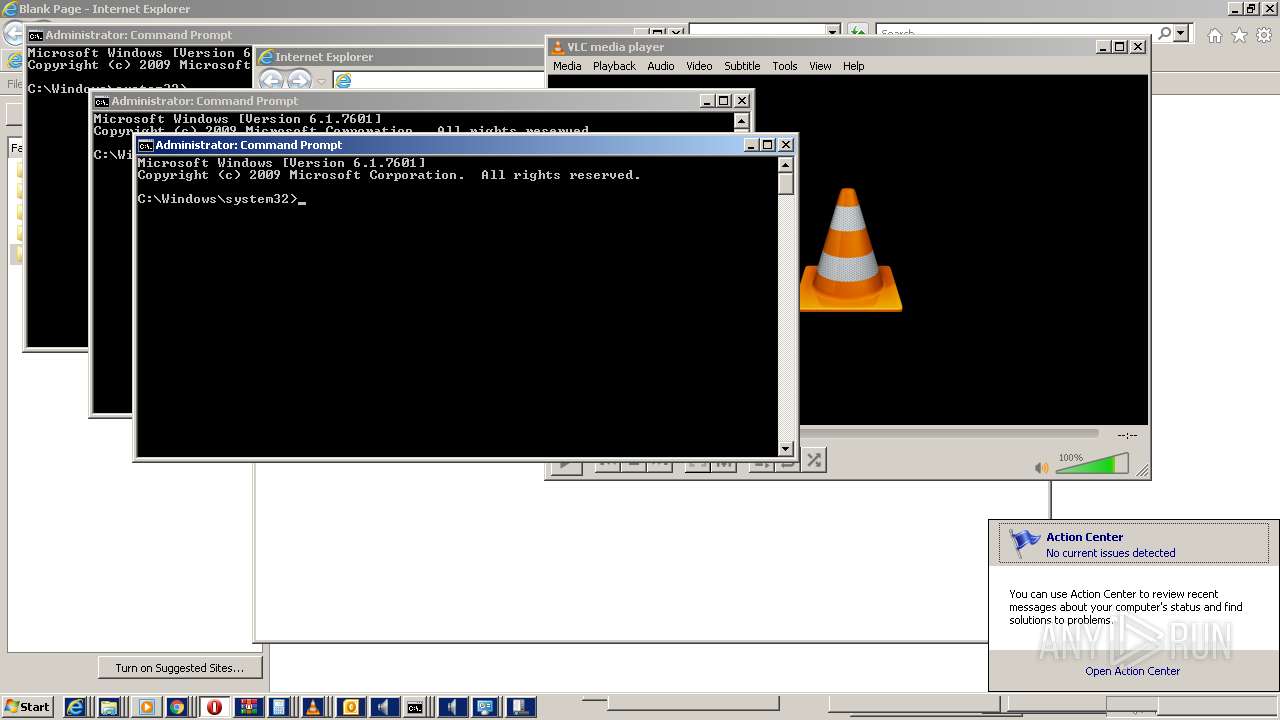
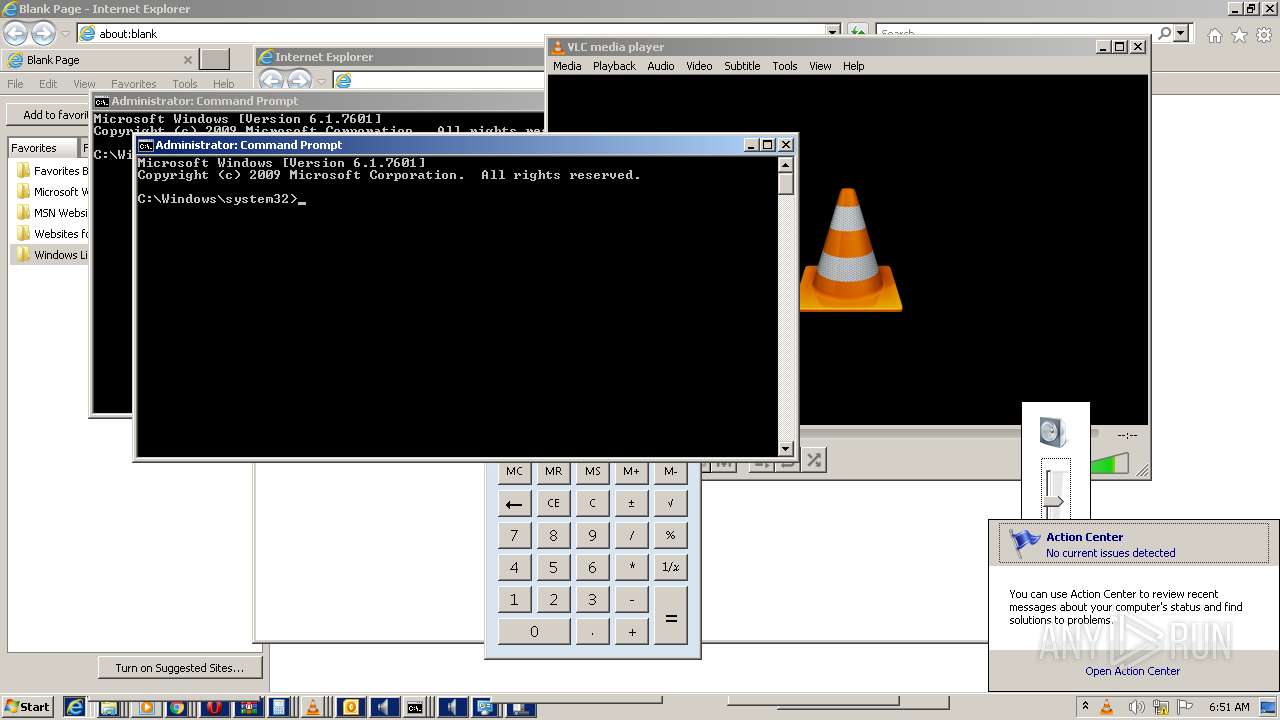
MALICIOUS
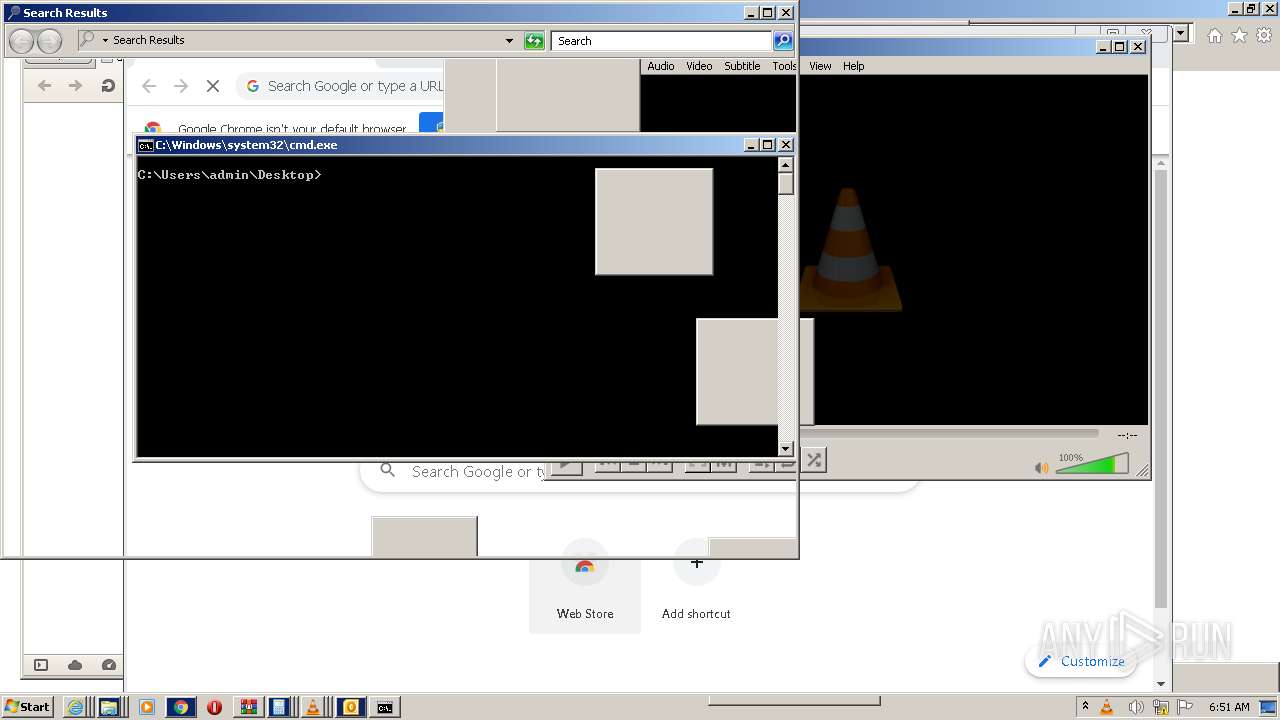
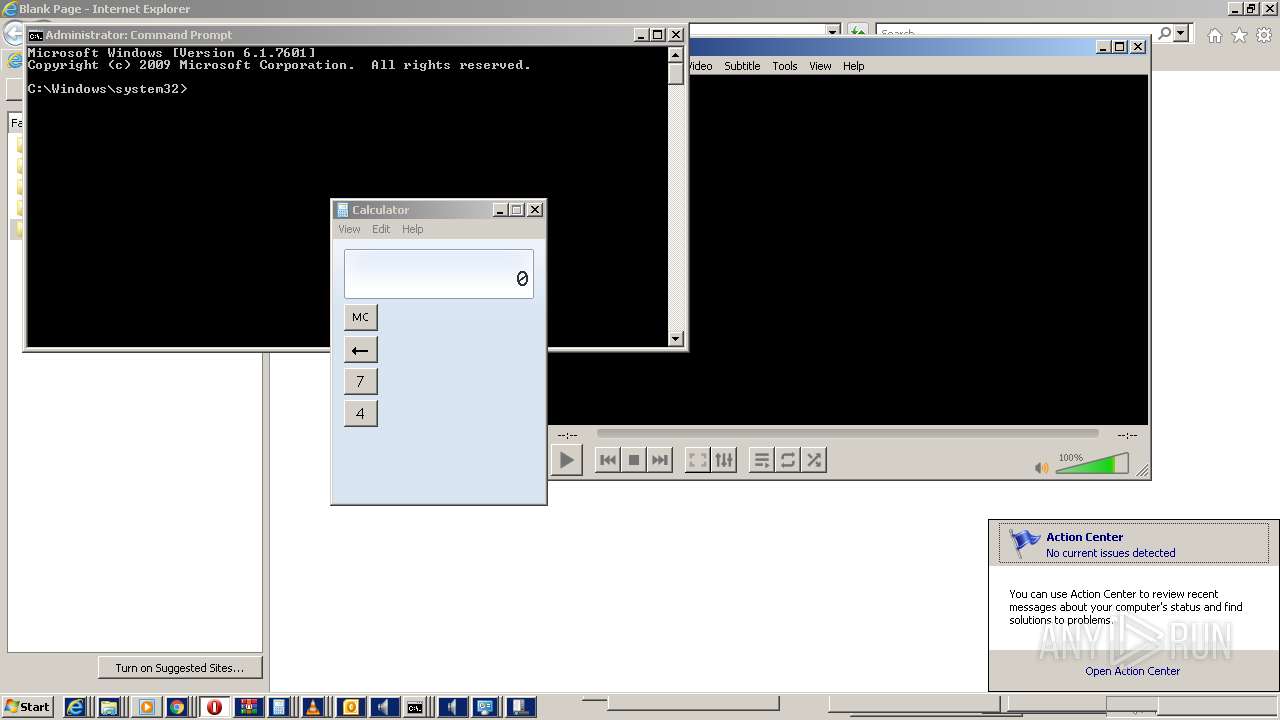
Drops executable file immediately after starts
- WinRAR.exe (PID: 1348)
Application was dropped or rewritten from another process
- fucker script.exe (PID: 2492)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 1348)
- OUTLOOK.EXE (PID: 2336)
- vlc.exe (PID: 4020)
- vlc.exe (PID: 3256)
- vlc.exe (PID: 2768)
- vlc.exe (PID: 3628)
- vlc.exe (PID: 3712)
- vlc.exe (PID: 3388)
- vlc.exe (PID: 1188)
- vlc.exe (PID: 3332)
- vlc.exe (PID: 5688)
- vlc.exe (PID: 5812)
- vlc.exe (PID: 5940)
- vlc.exe (PID: 5292)
- vlc.exe (PID: 928)
- wmplayer.exe (PID: 5520)
- vlc.exe (PID: 4236)
- setup_wm.exe (PID: 5820)
- vlc.exe (PID: 4300)
- vlc.exe (PID: 2200)
- vlc.exe (PID: 4272)
- vlc.exe (PID: 5192)
- vlc.exe (PID: 6424)
- vlc.exe (PID: 6280)
- vlc.exe (PID: 6908)
- vlc.exe (PID: 8040)
- wmplayer.exe (PID: 6256)
- vlc.exe (PID: 6360)
- setup_wm.exe (PID: 952)
- wmplayer.exe (PID: 1844)
- setup_wm.exe (PID: 6444)
- setup_wm.exe (PID: 8512)
- wmplayer.exe (PID: 6528)
- wmplayer.exe (PID: 8664)
- setup_wm.exe (PID: 9196)
- wmplayer.exe (PID: 8816)
- setup_wm.exe (PID: 8144)
- vlc.exe (PID: 9248)
- vlc.exe (PID: 8108)
- setup_wm.exe (PID: 9872)
- vlc.exe (PID: 8856)
- wmplayer.exe (PID: 9524)
- wmplayer.exe (PID: 9168)
- setup_wm.exe (PID: 4100)
- vlc.exe (PID: 6940)
- vlc.exe (PID: 6836)
- wmplayer.exe (PID: 5588)
- setup_wm.exe (PID: 6804)
- vlc.exe (PID: 6060)
- vlc.exe (PID: 7376)
- wmplayer.exe (PID: 3432)
- setup_wm.exe (PID: 5552)
- OUTLOOK.EXE (PID: 9356)
- WinRAR.exe (PID: 8524)
- WinRAR.exe (PID: 5964)
- vlc.exe (PID: 2660)
- vlc.exe (PID: 956)
- vlc.exe (PID: 7436)
- vlc.exe (PID: 7988)
- vlc.exe (PID: 7908)
- vlc.exe (PID: 10476)
- vlc.exe (PID: 9736)
- vlc.exe (PID: 11160)
- vlc.exe (PID: 11612)
- vlc.exe (PID: 11808)
- vlc.exe (PID: 10436)
- vlc.exe (PID: 9224)
- vlc.exe (PID: 11348)
- vlc.exe (PID: 7600)
Checks supported languages
- WinRAR.exe (PID: 1348)
- fucker script.exe (PID: 2492)
- vlc.exe (PID: 2768)
- vlc.exe (PID: 3712)
- vlc.exe (PID: 3256)
- vlc.exe (PID: 3628)
- vlc.exe (PID: 4020)
- OUTLOOK.EXE (PID: 2336)
- OUTLOOK.EXE (PID: 3596)
- OUTLOOK.EXE (PID: 3020)
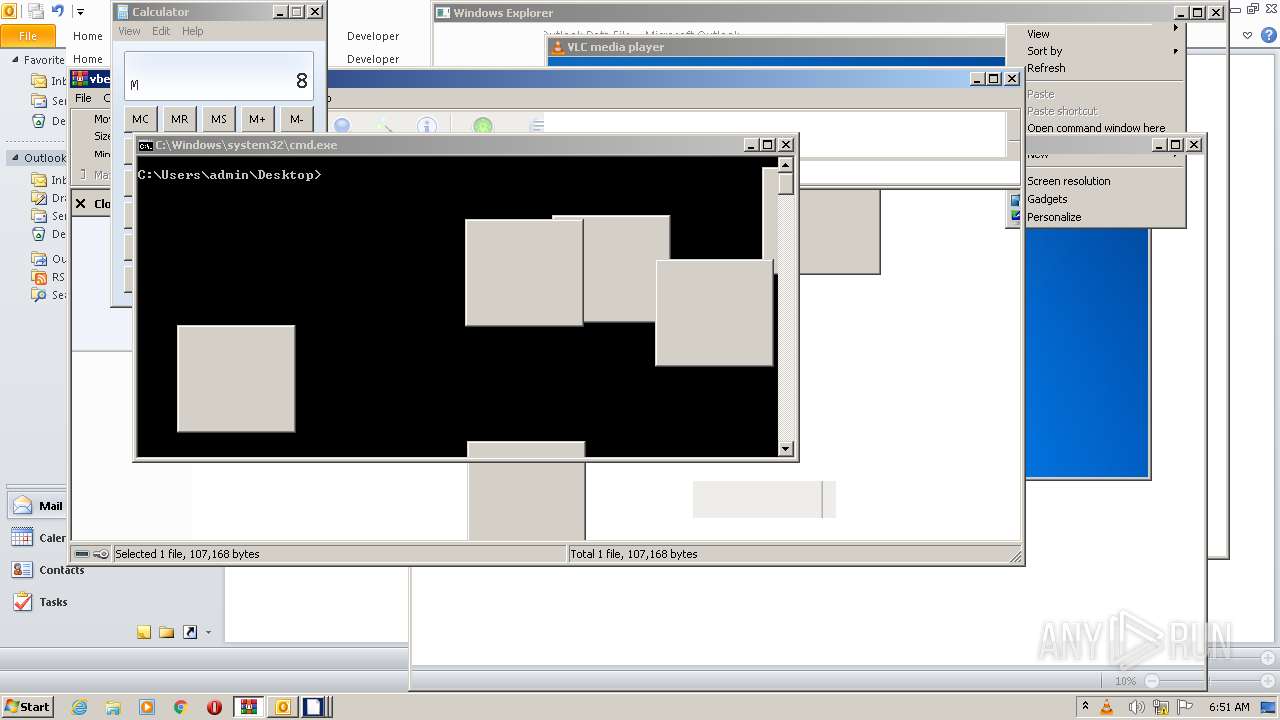
- cmd.exe (PID: 3864)
- vlc.exe (PID: 3388)
- vlc.exe (PID: 1188)
- vlc.exe (PID: 3332)
- OUTLOOK.EXE (PID: 3384)
- OUTLOOK.EXE (PID: 1204)
- OUTLOOK.EXE (PID: 4352)
- vlc.exe (PID: 5812)
- vlc.exe (PID: 5688)
- vlc.exe (PID: 5940)
- OUTLOOK.EXE (PID: 5220)
- OUTLOOK.EXE (PID: 5132)
- vlc.exe (PID: 5292)
- OUTLOOK.EXE (PID: 4224)
- OUTLOOK.EXE (PID: 4744)
- vlc.exe (PID: 928)
- OUTLOOK.EXE (PID: 5356)
- OUTLOOK.EXE (PID: 4176)
- OUTLOOK.EXE (PID: 5432)
- cmd.exe (PID: 5916)
- vlc.exe (PID: 4236)
- wmplayer.exe (PID: 5520)
- setup_wm.exe (PID: 5820)
- vlc.exe (PID: 4300)
- OUTLOOK.EXE (PID: 1568)
- vlc.exe (PID: 2200)
- vlc.exe (PID: 4272)
- OUTLOOK.EXE (PID: 3744)
- vlc.exe (PID: 6424)
- vlc.exe (PID: 5192)
- vlc.exe (PID: 6280)
- OUTLOOK.EXE (PID: 7288)
- vlc.exe (PID: 6908)
- cmd.exe (PID: 6564)
- OUTLOOK.EXE (PID: 7672)
- wmplayer.exe (PID: 6256)
- vlc.exe (PID: 8040)
- vlc.exe (PID: 6360)
- setup_wm.exe (PID: 952)
- cmd.exe (PID: 1824)
- wmplayer.exe (PID: 1844)
- setup_wm.exe (PID: 6444)
- wmplayer.exe (PID: 6528)
- setup_wm.exe (PID: 8512)
- cmd.exe (PID: 7884)
- setup_wm.exe (PID: 9196)
- wmplayer.exe (PID: 8664)
- cmd.exe (PID: 9364)
- wmplayer.exe (PID: 8816)
- setup_wm.exe (PID: 8144)
- vlc.exe (PID: 9248)
- vlc.exe (PID: 8108)
- wmplayer.exe (PID: 9524)
- setup_wm.exe (PID: 9872)
- setup_wm.exe (PID: 4100)
- wmplayer.exe (PID: 9168)
- cmd.exe (PID: 10208)
- cmd.exe (PID: 8364)
- cmd.exe (PID: 2680)
- vlc.exe (PID: 8856)
- vlc.exe (PID: 6940)
- vlc.exe (PID: 6836)
- cmd.exe (PID: 9236)
- wmplayer.exe (PID: 5588)
- setup_wm.exe (PID: 6804)
- cmd.exe (PID: 8492)
- vlc.exe (PID: 7376)
- vlc.exe (PID: 6060)
- wmplayer.exe (PID: 3432)
- setup_wm.exe (PID: 5552)
- OUTLOOK.EXE (PID: 9356)
- WinRAR.exe (PID: 8524)
- WinRAR.exe (PID: 5964)
- vlc.exe (PID: 2660)
- vlc.exe (PID: 956)
- vlc.exe (PID: 7908)
- vlc.exe (PID: 7436)
- vlc.exe (PID: 7988)
- OUTLOOK.EXE (PID: 2784)
- vlc.exe (PID: 9736)
- OUTLOOK.EXE (PID: 3808)
- vlc.exe (PID: 10476)
- OUTLOOK.EXE (PID: 2112)
- vlc.exe (PID: 11160)
- vlc.exe (PID: 11612)
- OUTLOOK.EXE (PID: 10612)
- OUTLOOK.EXE (PID: 11128)
- vlc.exe (PID: 10436)
- OUTLOOK.EXE (PID: 11236)
- vlc.exe (PID: 11808)
- OUTLOOK.EXE (PID: 11252)
- OUTLOOK.EXE (PID: 11248)
- vlc.exe (PID: 9224)
- OUTLOOK.EXE (PID: 11892)
- vlc.exe (PID: 7600)
- vlc.exe (PID: 11348)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1348)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 1348)
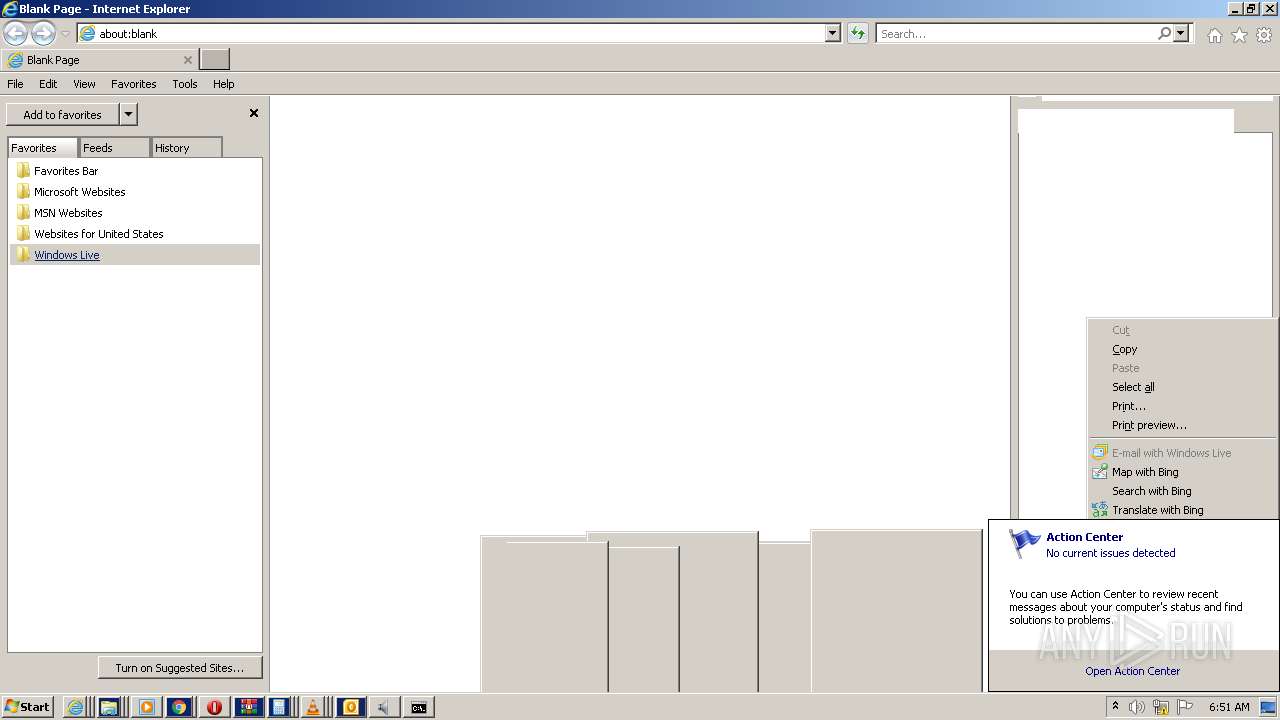
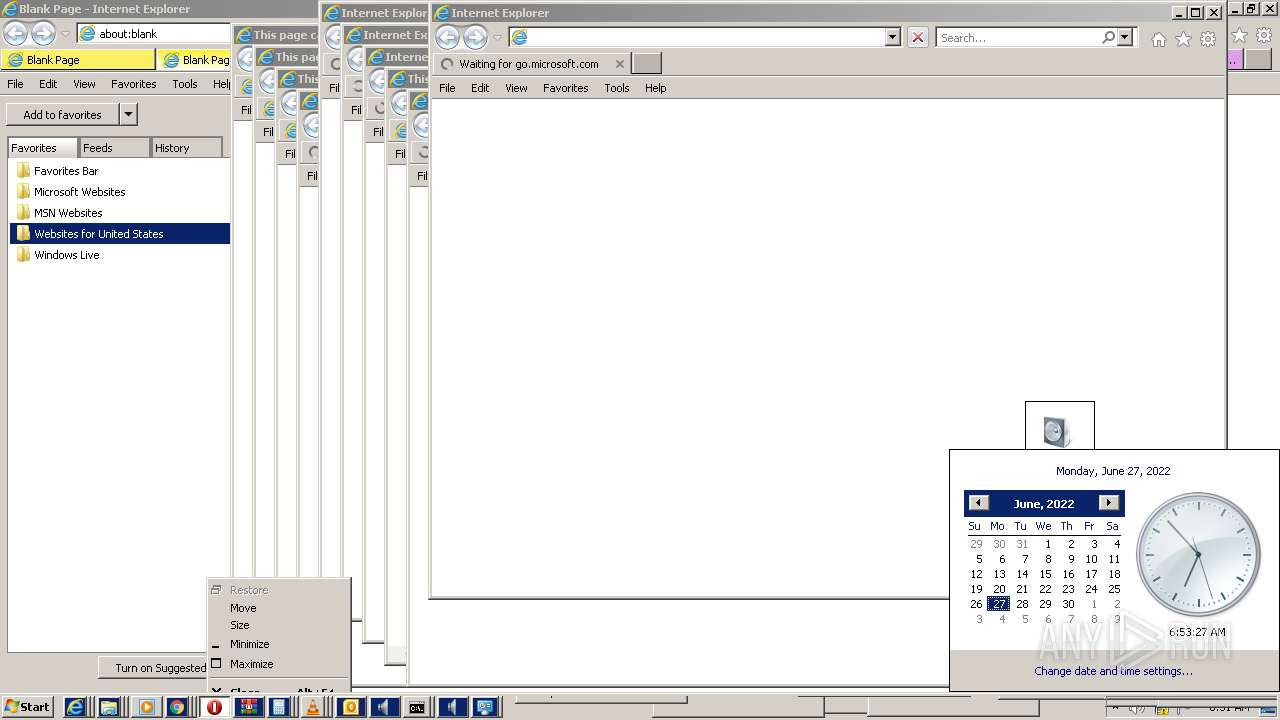
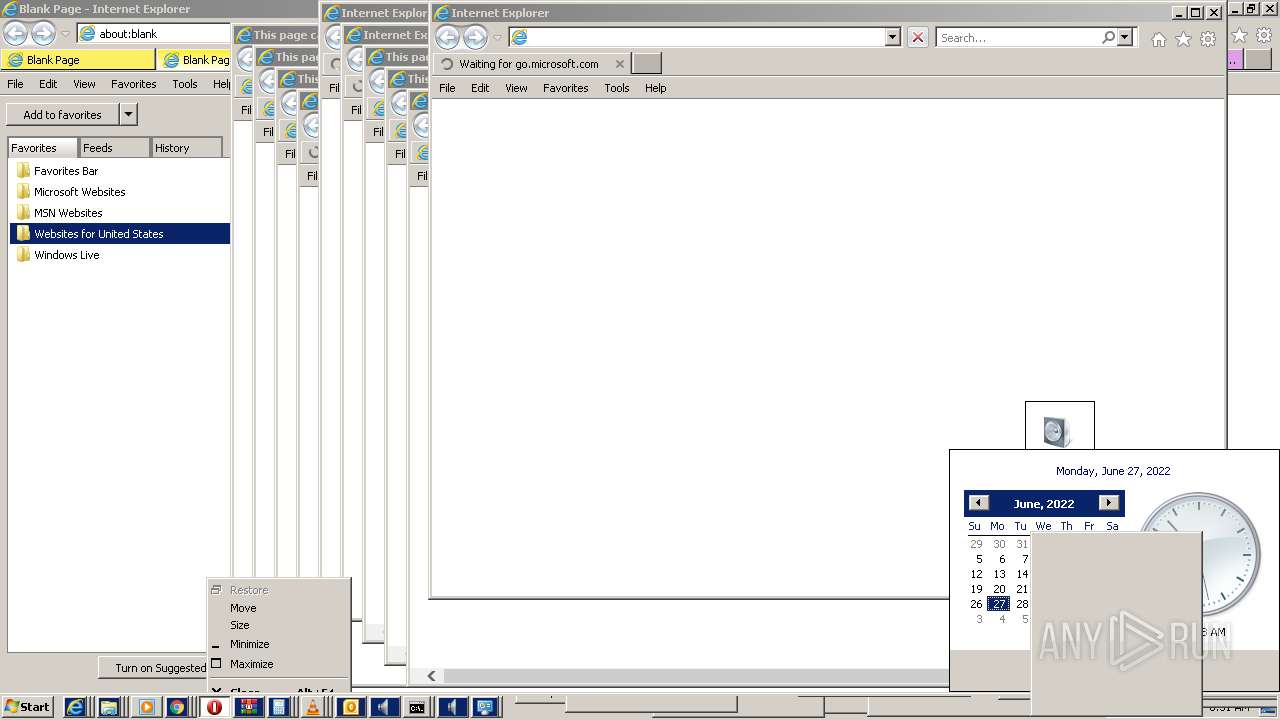
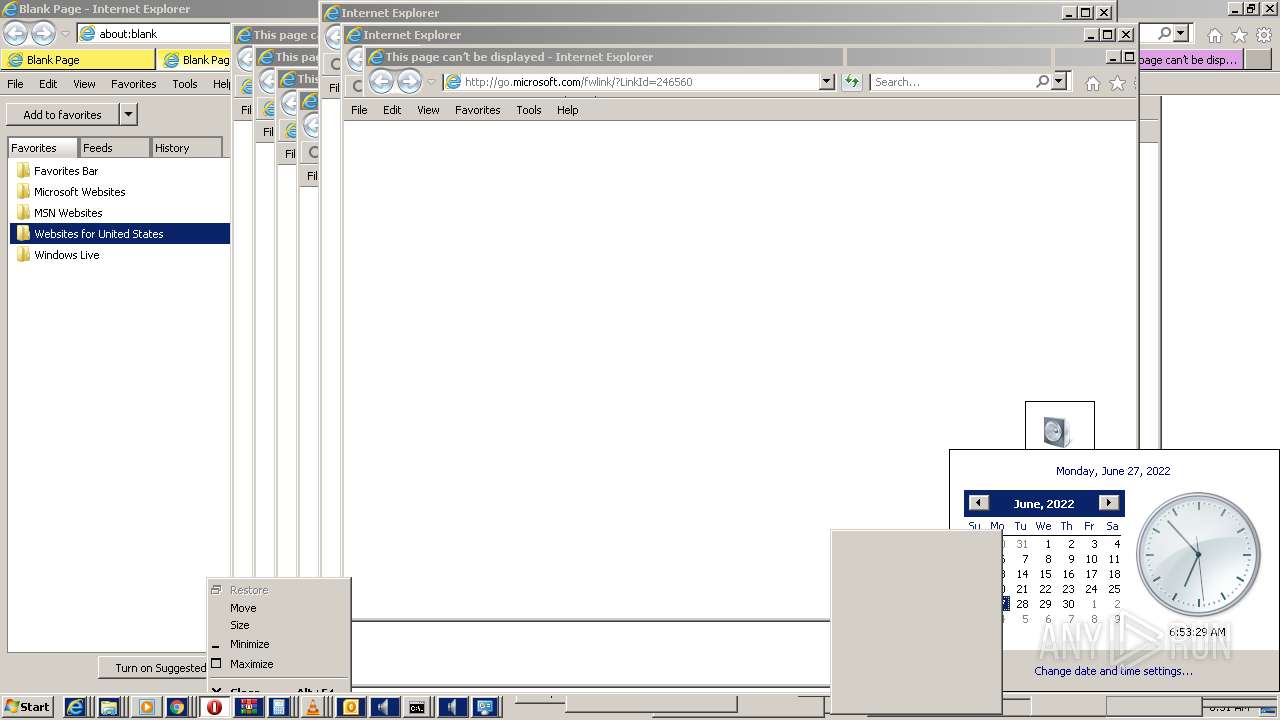
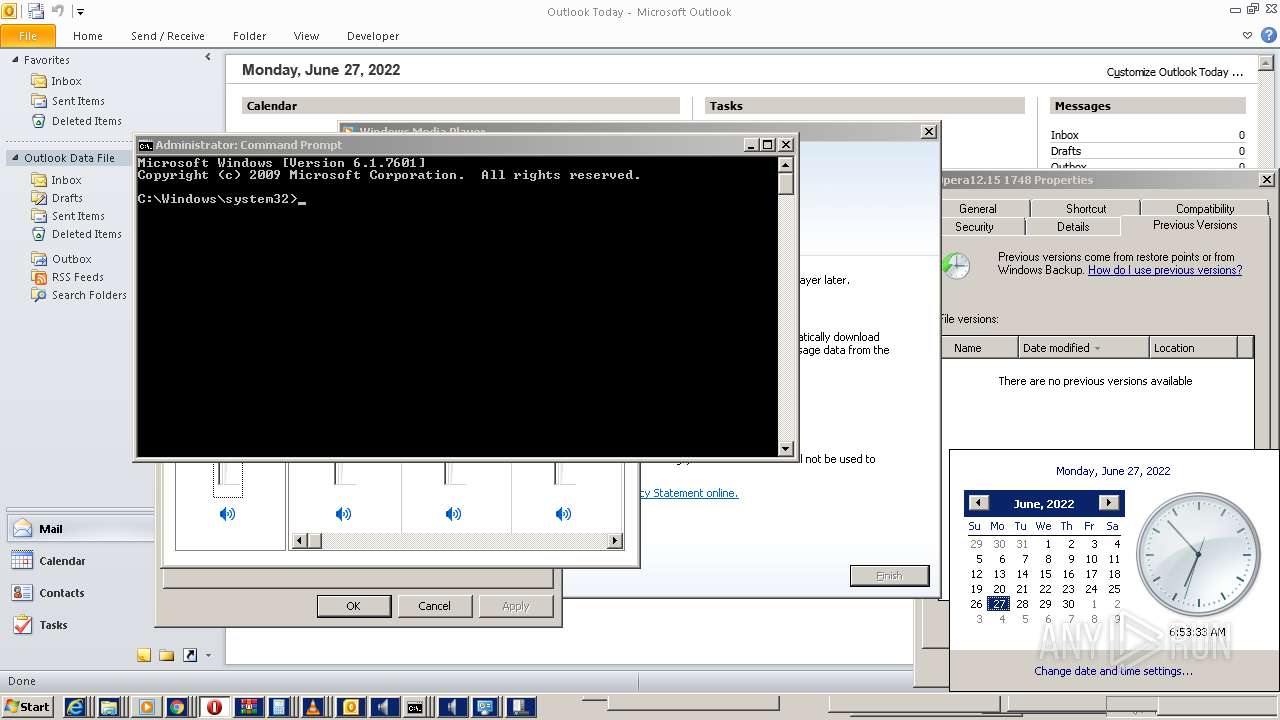
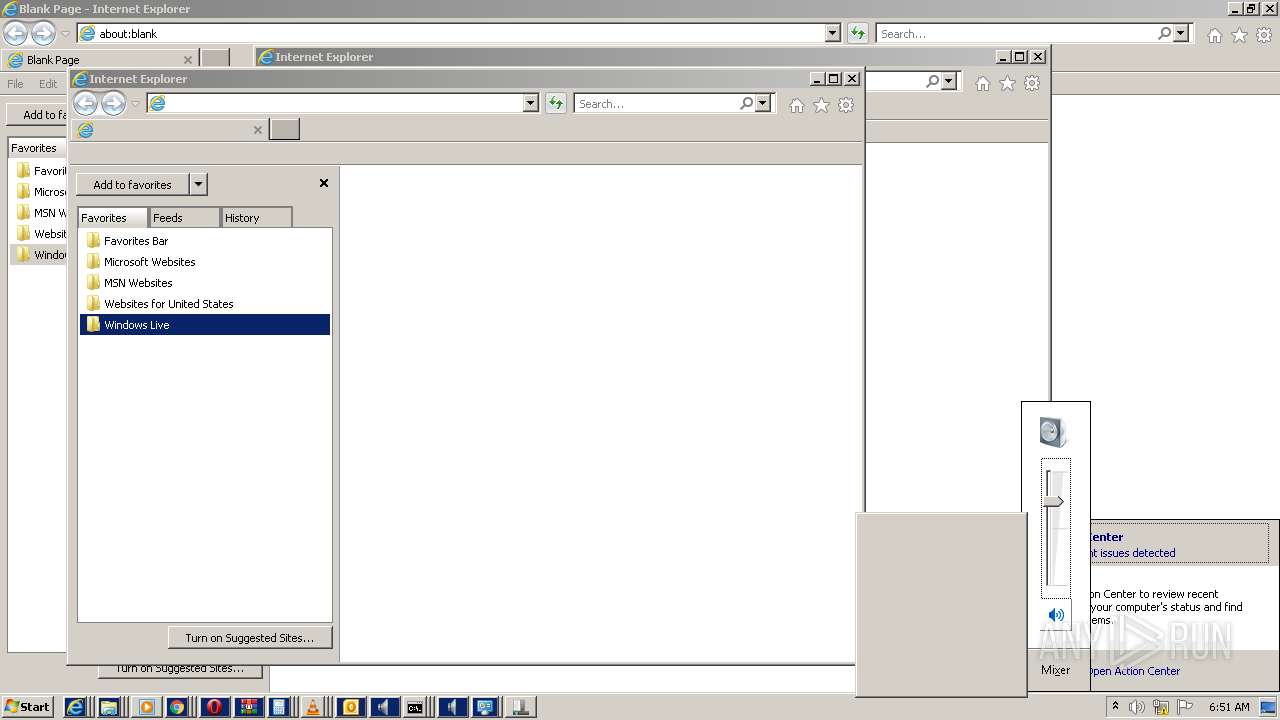
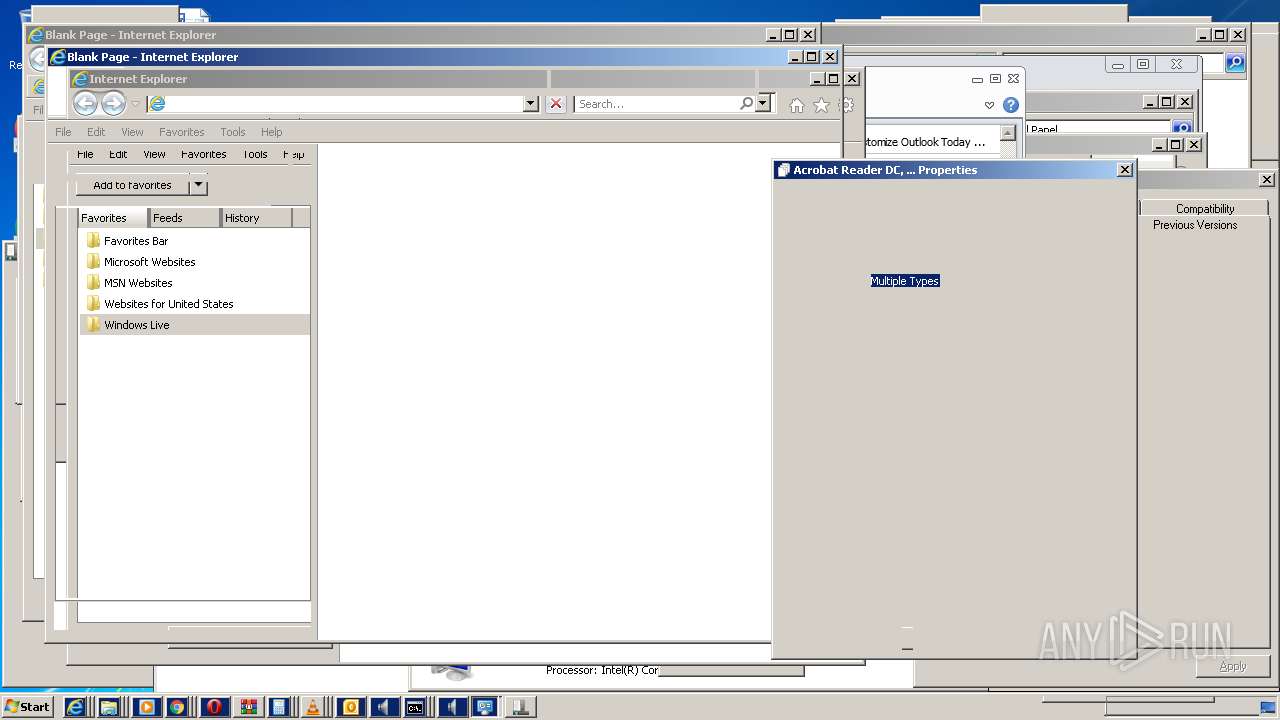
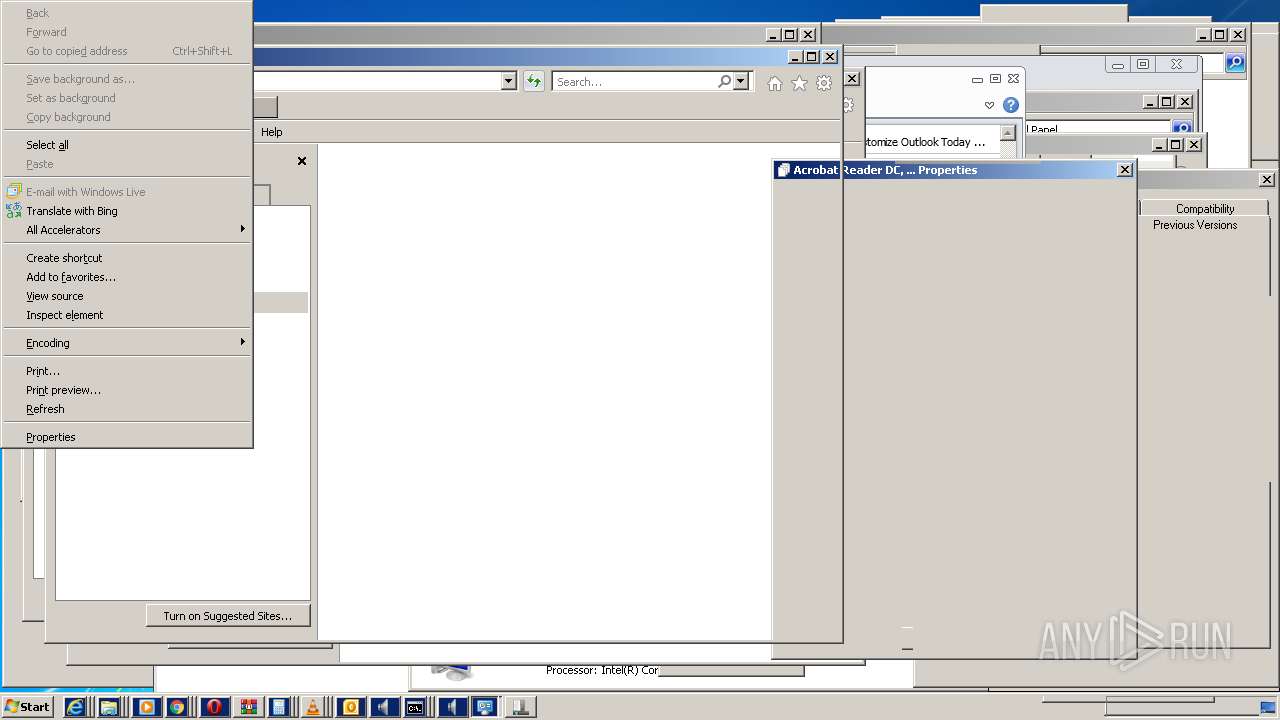
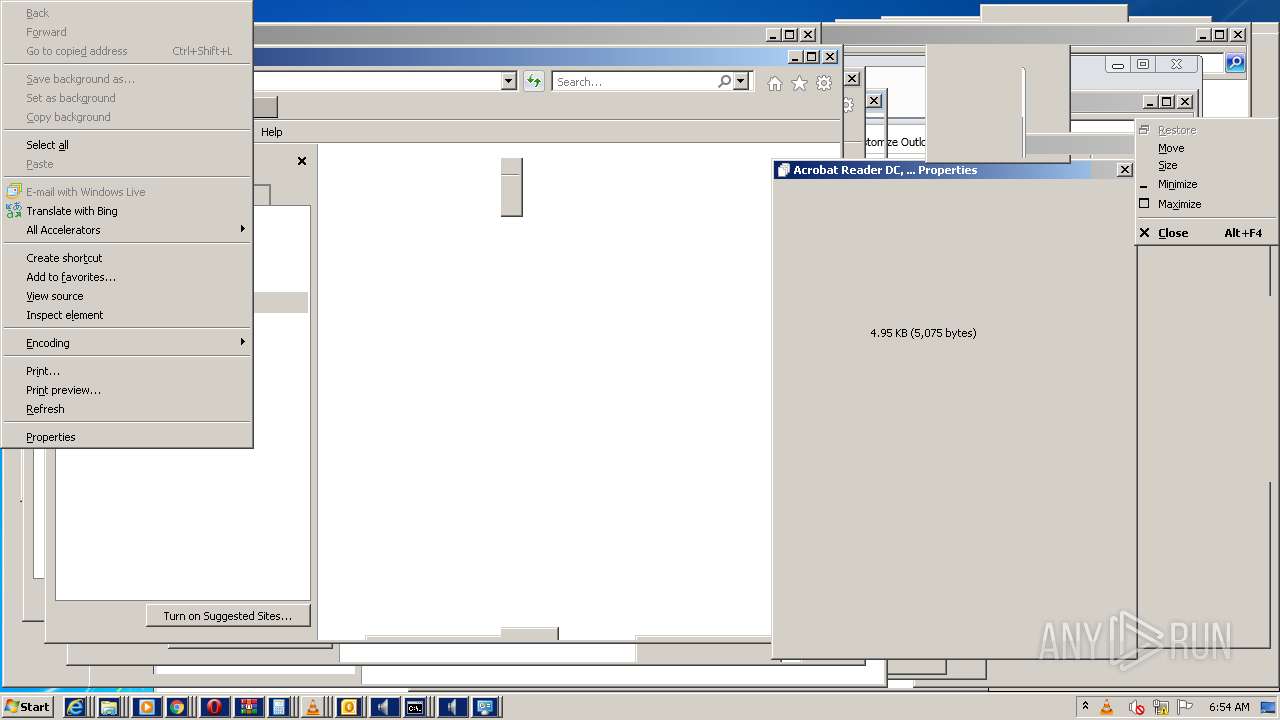
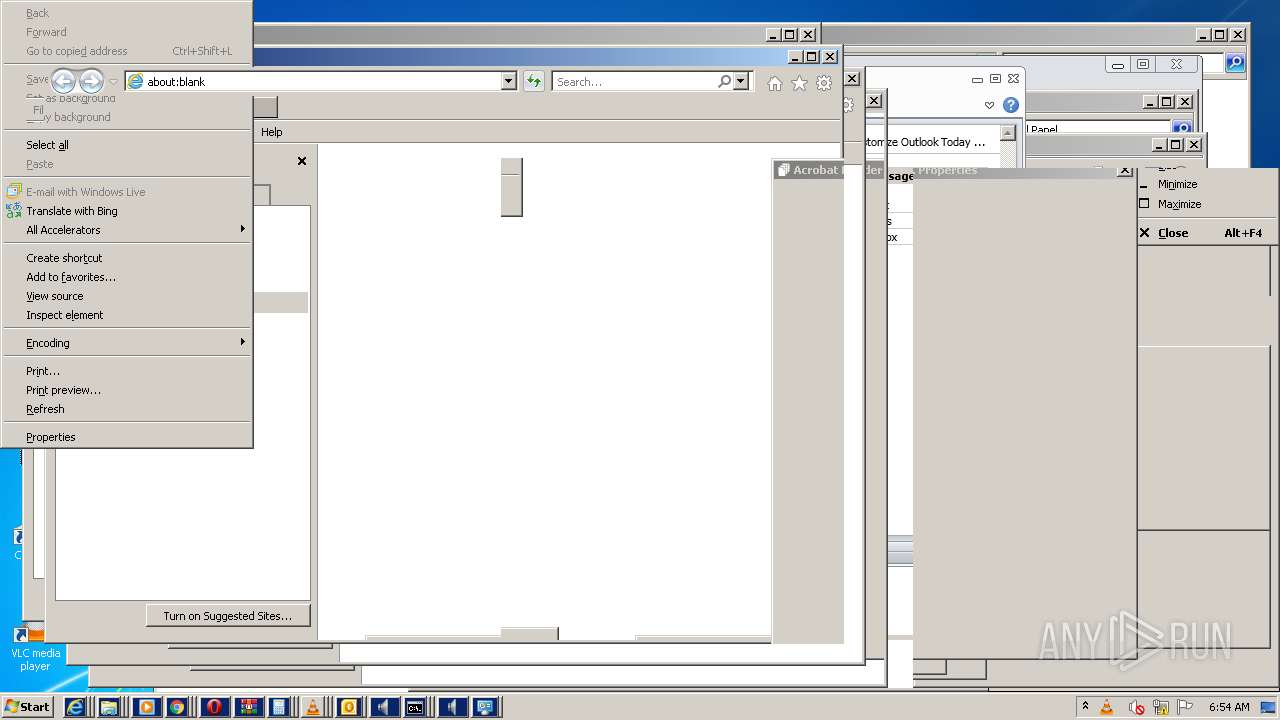
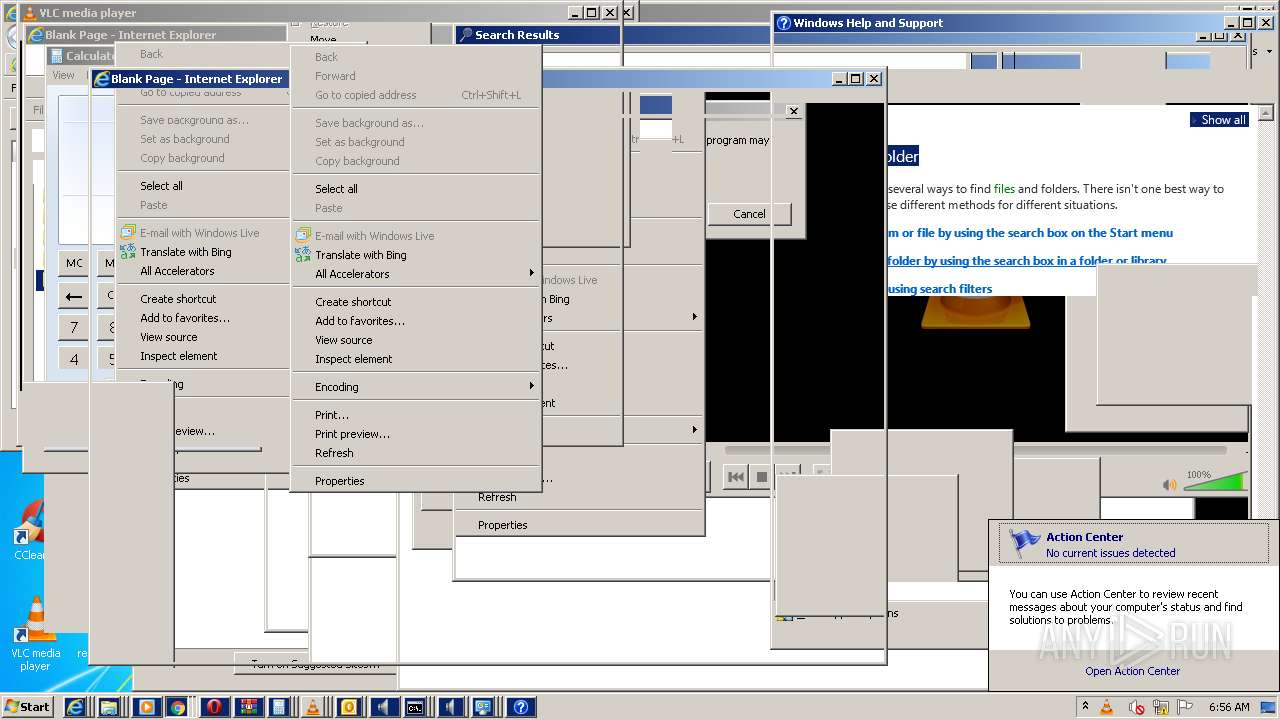
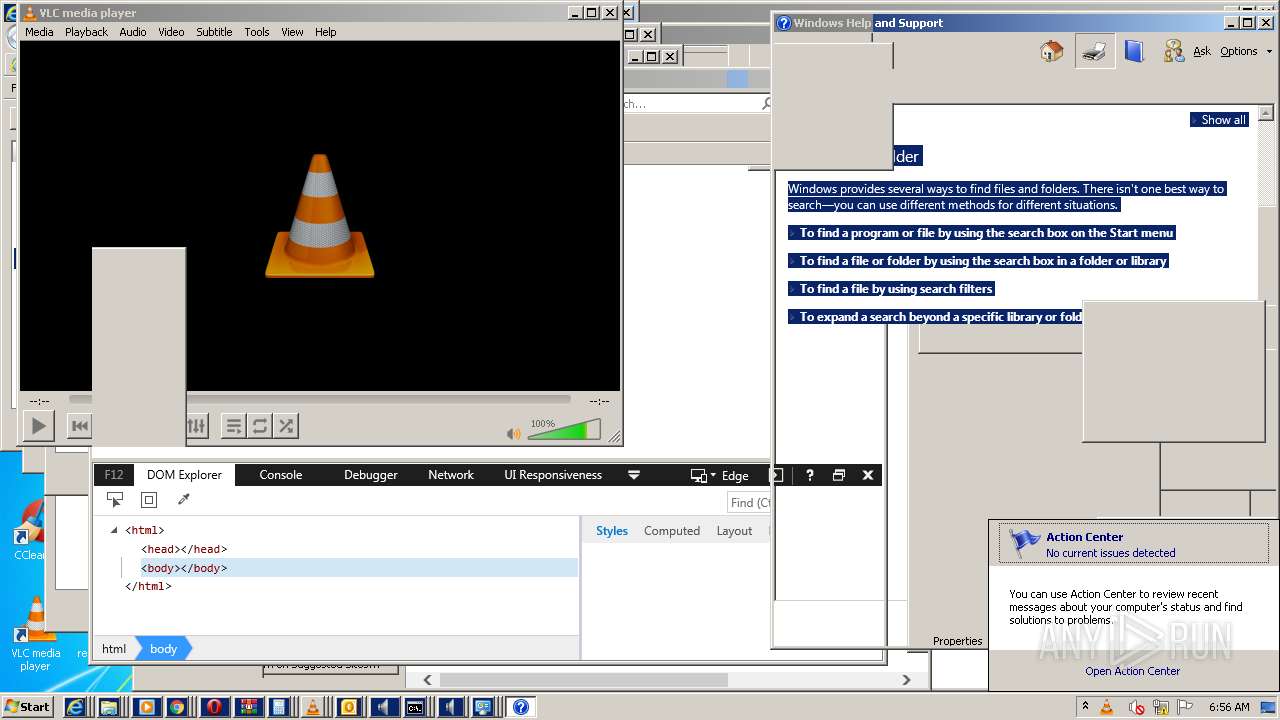
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 772)
- OUTLOOK.EXE (PID: 2336)
- iexplore.exe (PID: 3044)
- iexplore.exe (PID: 3584)
- iexplore.exe (PID: 4736)
- iexplore.exe (PID: 5752)
- iexplore.exe (PID: 4284)
- iexplore.exe (PID: 4676)
- iexplore.exe (PID: 6760)
- iexplore.exe (PID: 5284)
- iexplore.exe (PID: 8148)
- iexplore.exe (PID: 7616)
- iexplore.exe (PID: 6936)
- iexplore.exe (PID: 6244)
- iexplore.exe (PID: 7664)
- iexplore.exe (PID: 7944)
- iexplore.exe (PID: 9916)
- iexplore.exe (PID: 10000)
- iexplore.exe (PID: 8400)
- iexplore.exe (PID: 10116)
- helppane.exe (PID: 8376)
- iexplore.exe (PID: 10988)
Reads internet explorer settings
- OUTLOOK.EXE (PID: 2336)
- helppane.exe (PID: 8376)
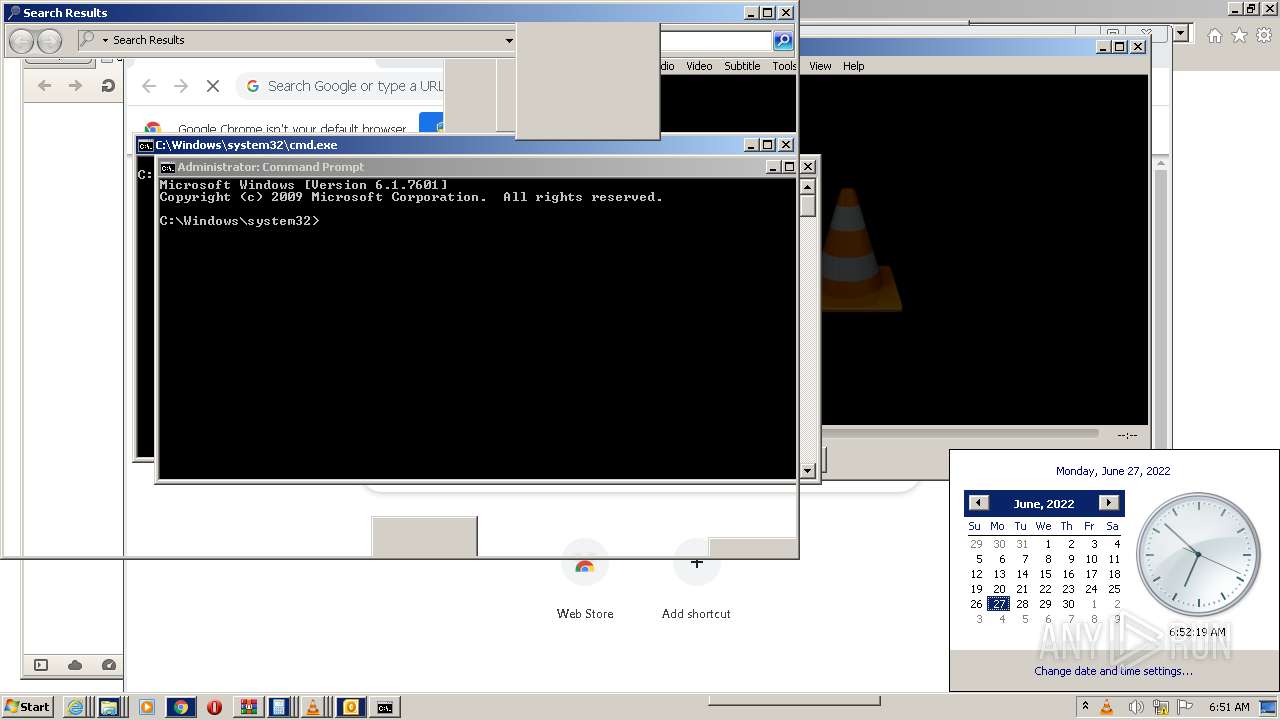
Reads the date of Windows installation
- OUTLOOK.EXE (PID: 2336)
Reads Environment values
- setup_wm.exe (PID: 5820)
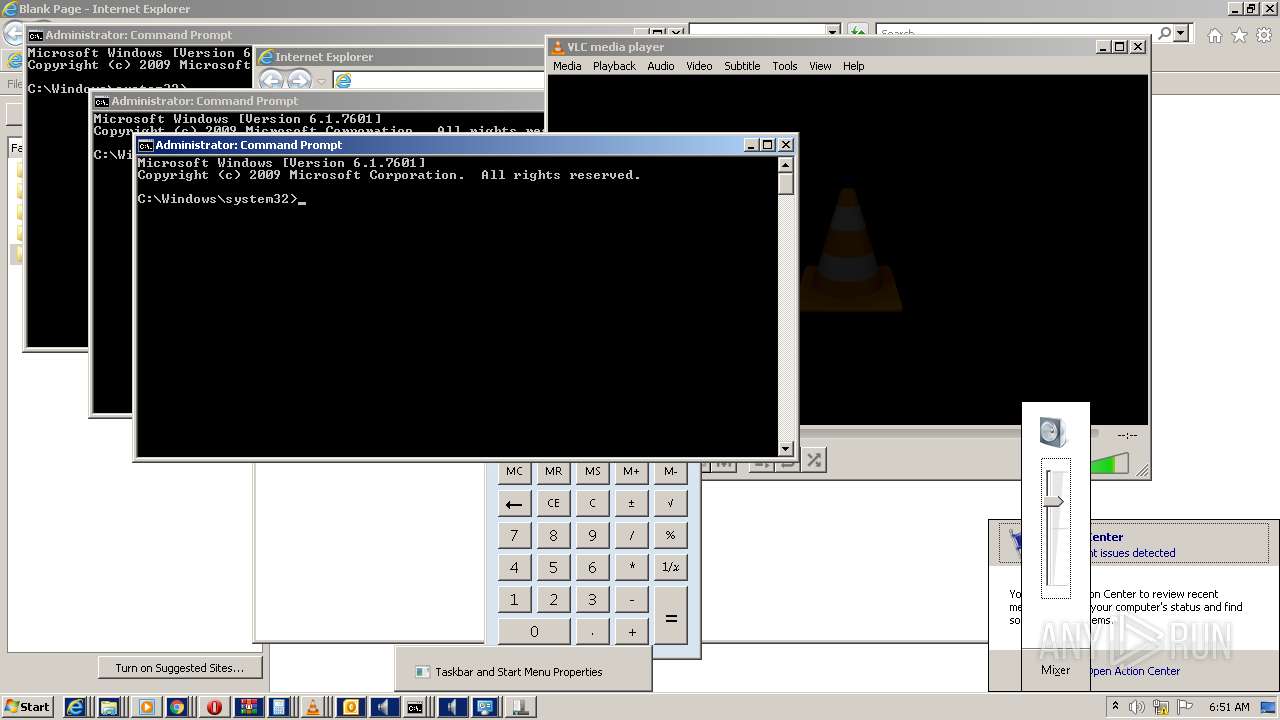
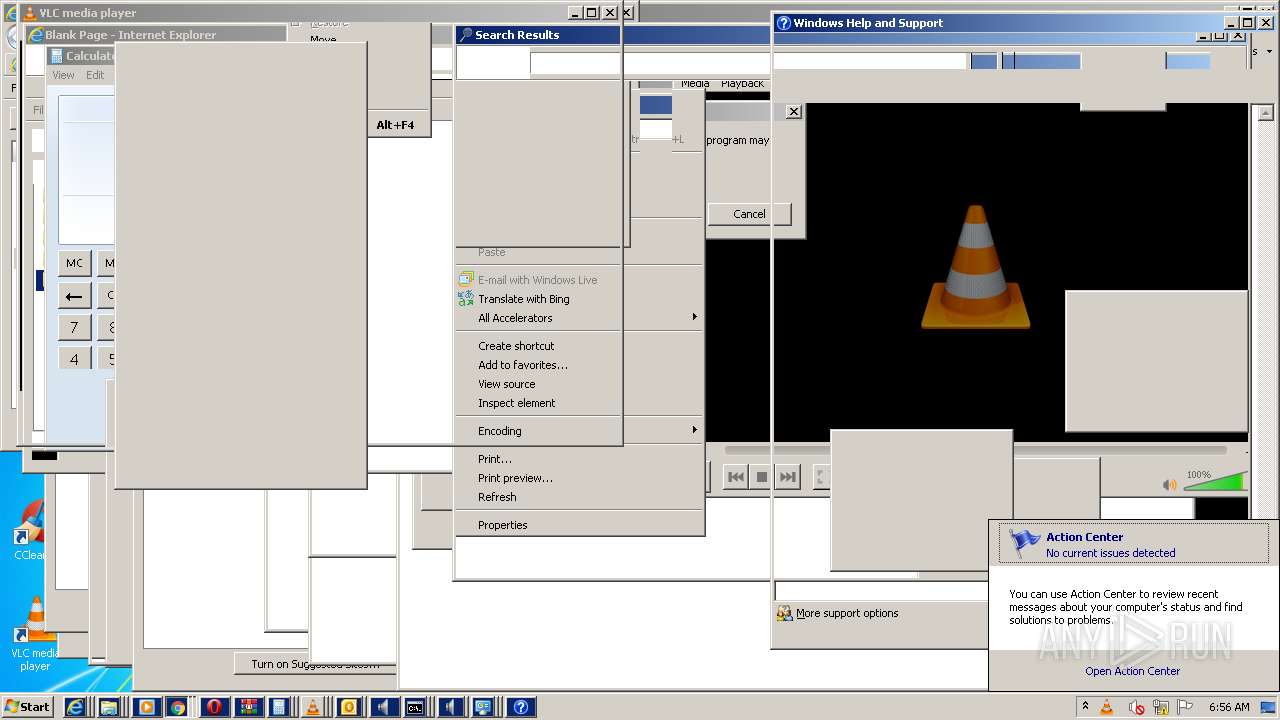
Uses RUNDLL32.EXE to load library
- control.exe (PID: 2024)
- control.exe (PID: 7180)
- control.exe (PID: 7808)
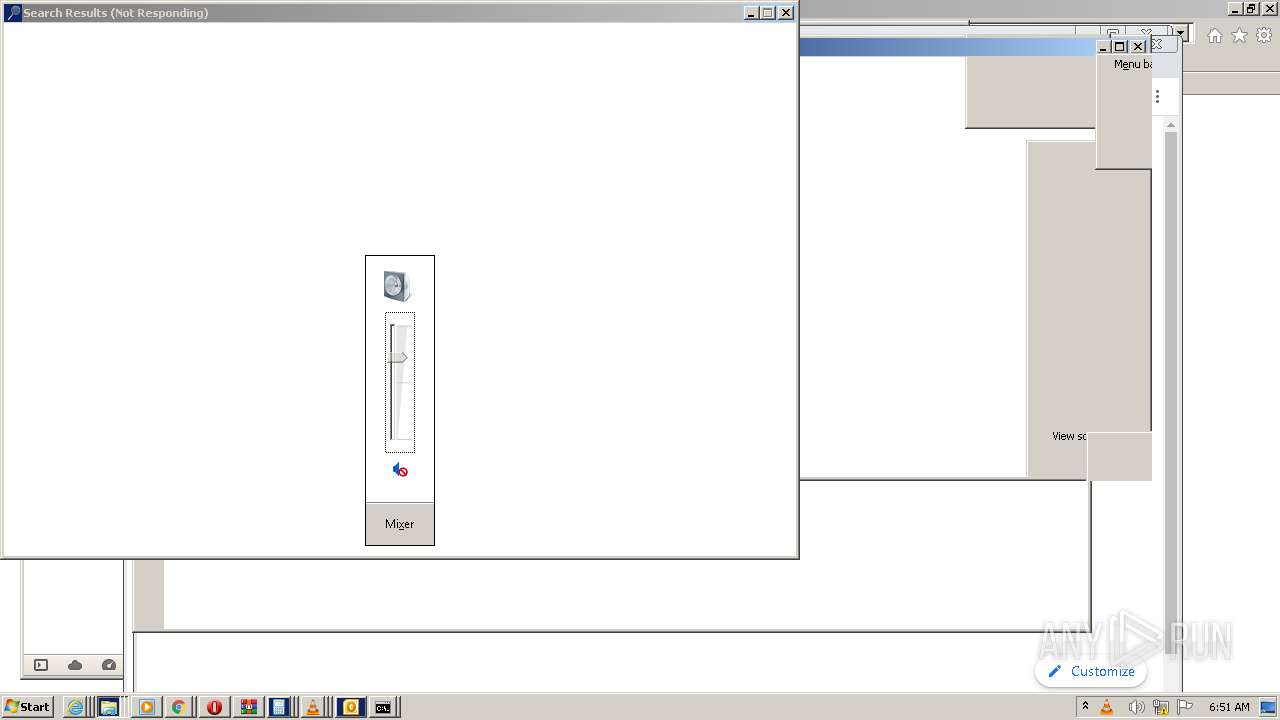
Application launched itself
- SndVol.exe (PID: 4460)
- SndVol.exe (PID: 6436)
- WinRAR.exe (PID: 8524)
Executed via COM
- DllHost.exe (PID: 8576)
- DllHost.exe (PID: 5552)
- helppane.exe (PID: 8376)
Creates files in the user directory
- vlc.exe (PID: 11612)
- vlc.exe (PID: 10436)
Executed as Windows Service
- IEEtwCollector.exe (PID: 7160)
Creates files in the Windows directory
- IEEtwCollector.exe (PID: 7160)
Reads the time zone
- IEEtwCollector.exe (PID: 7160)
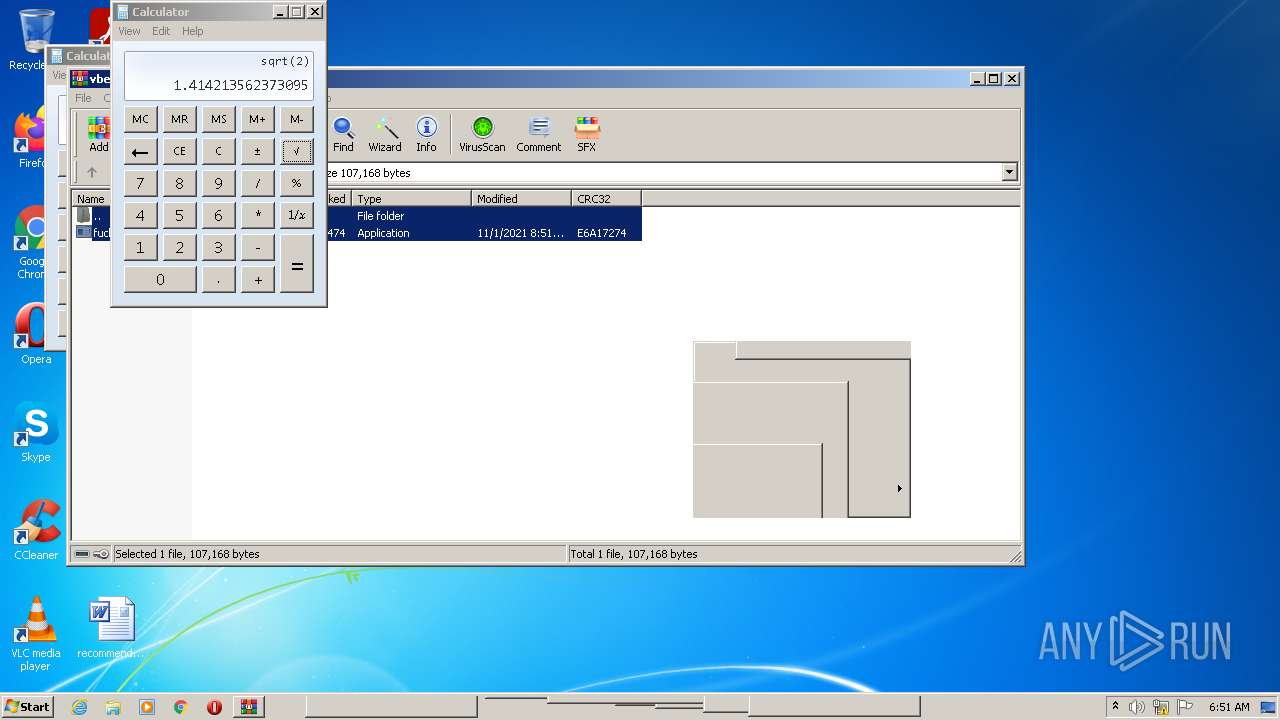
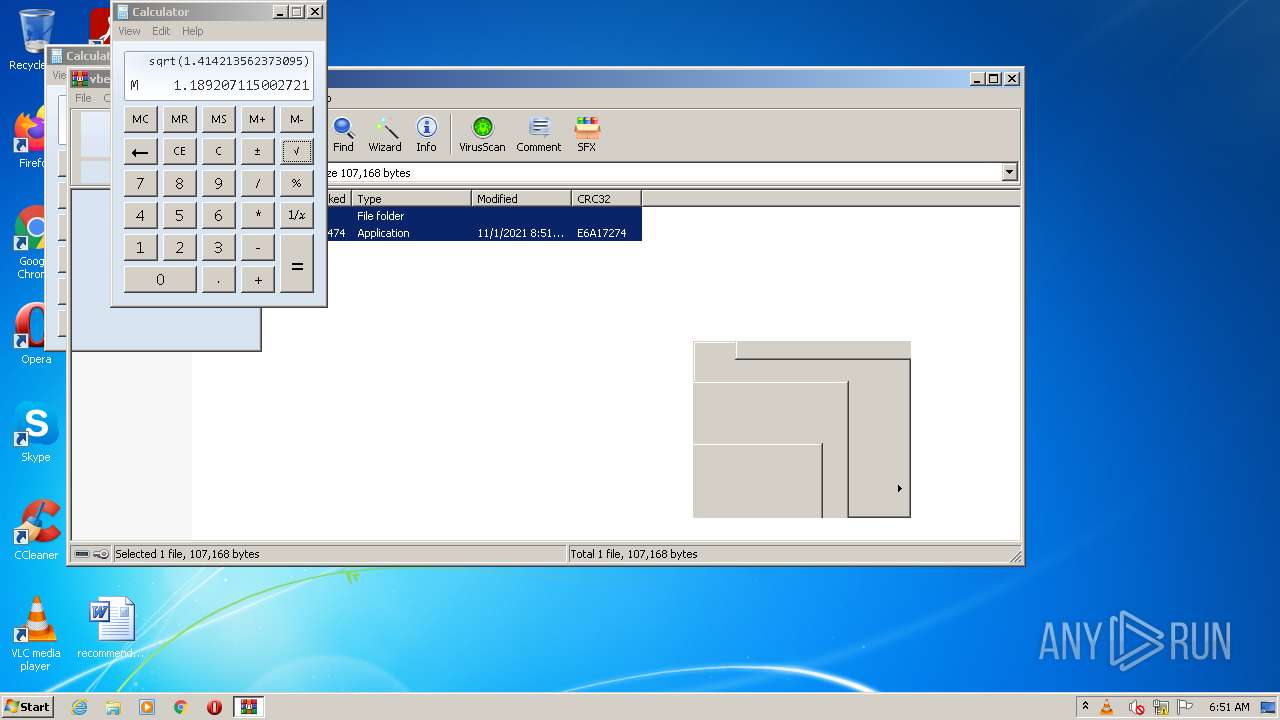
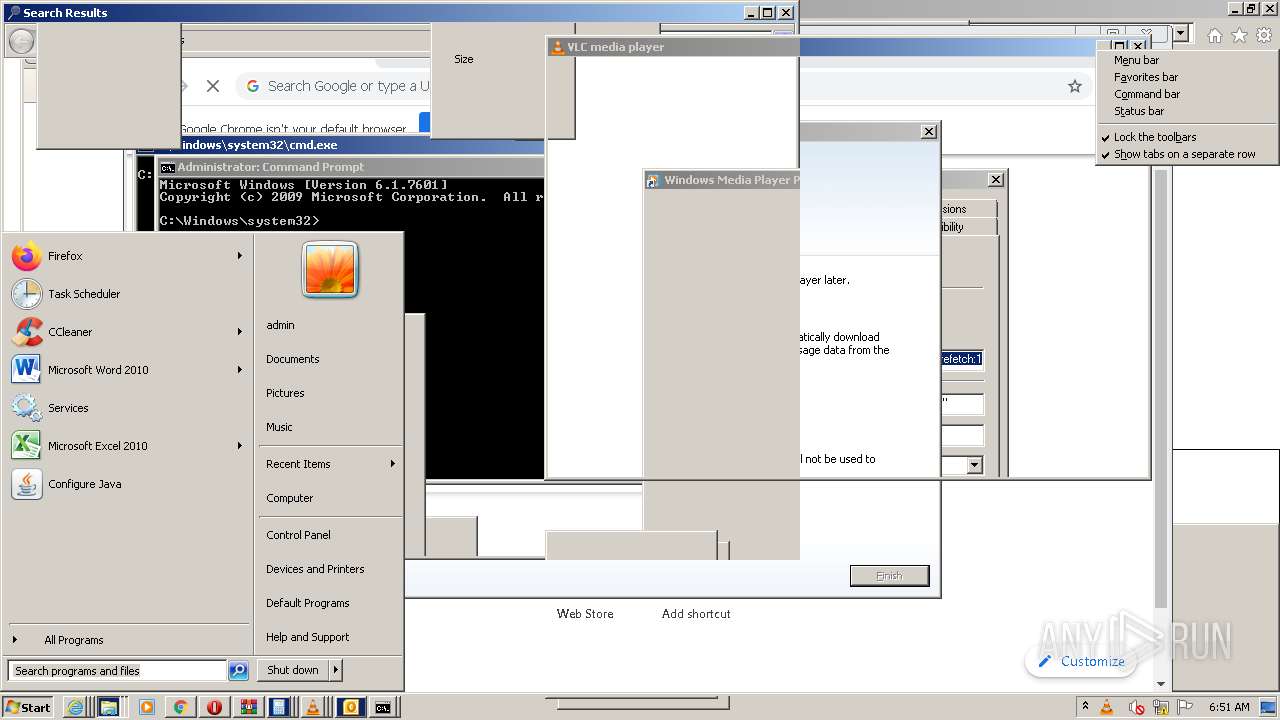
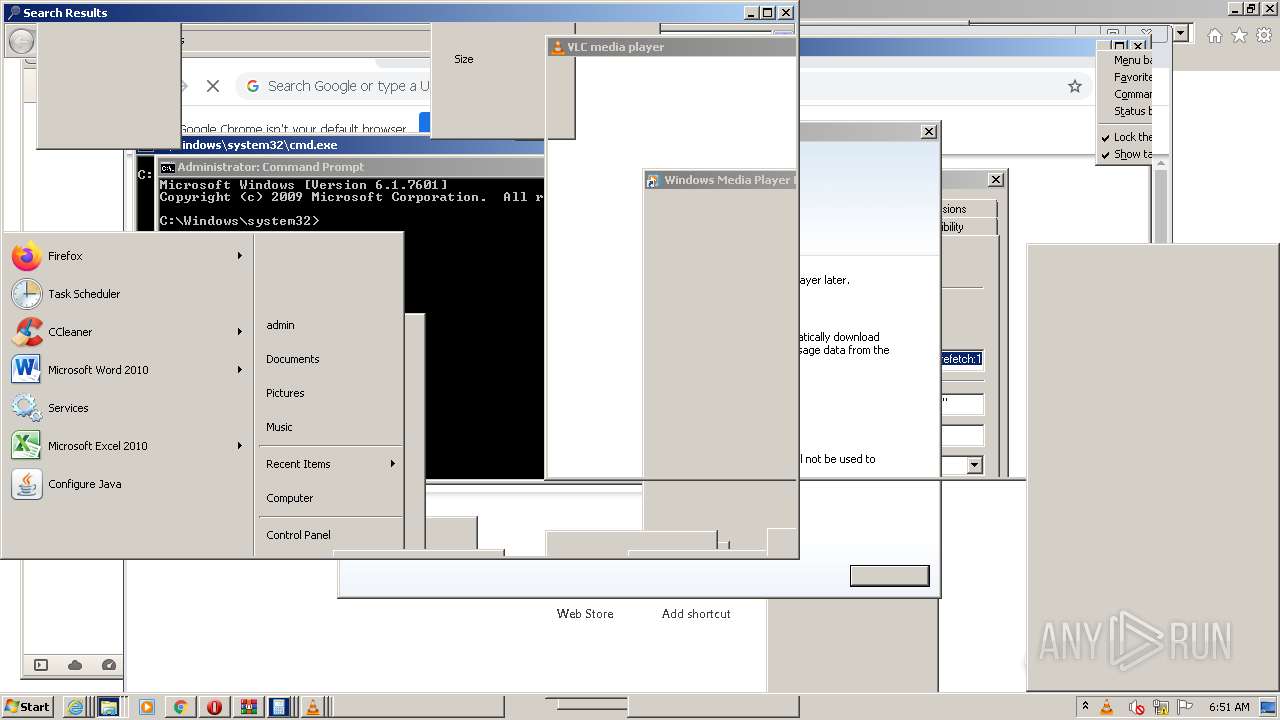
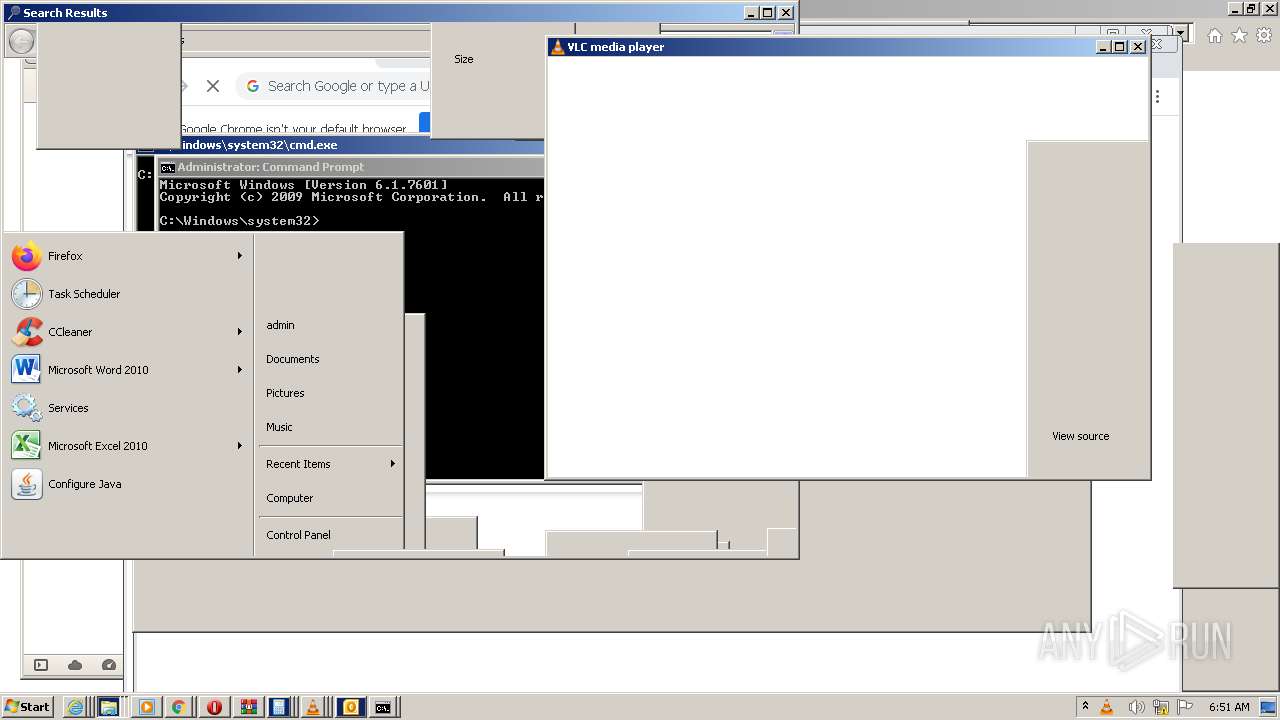
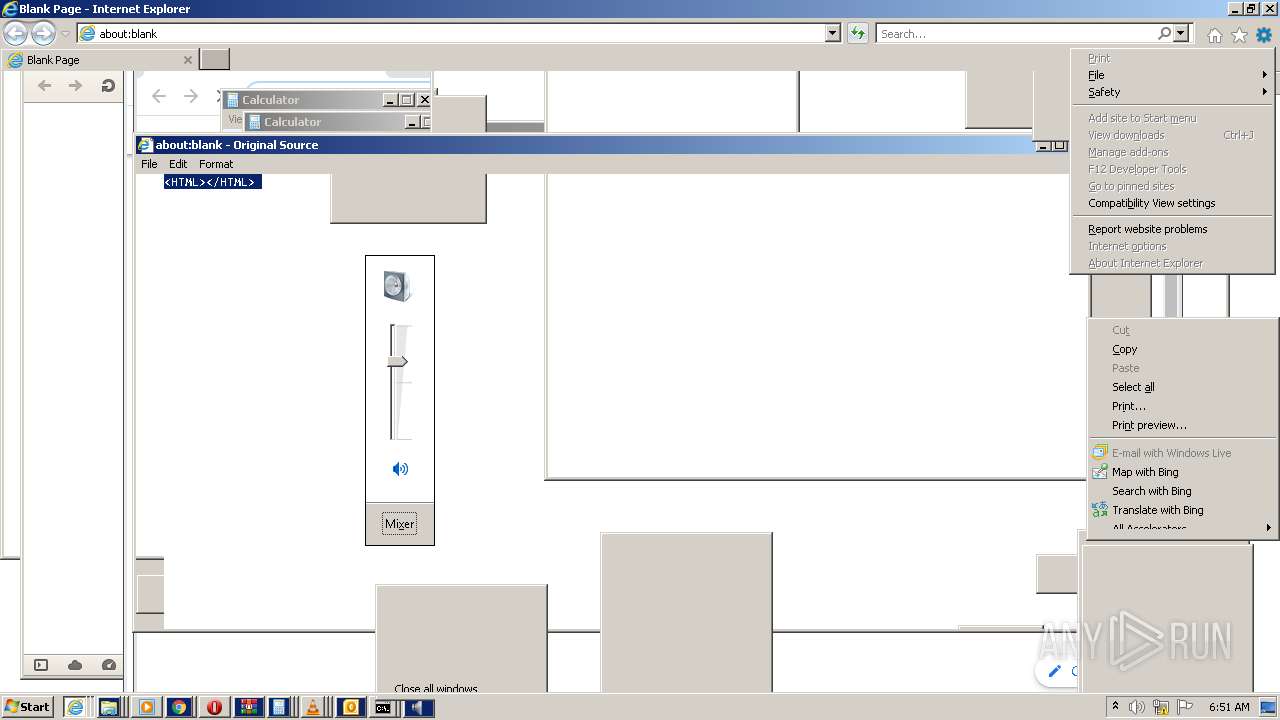
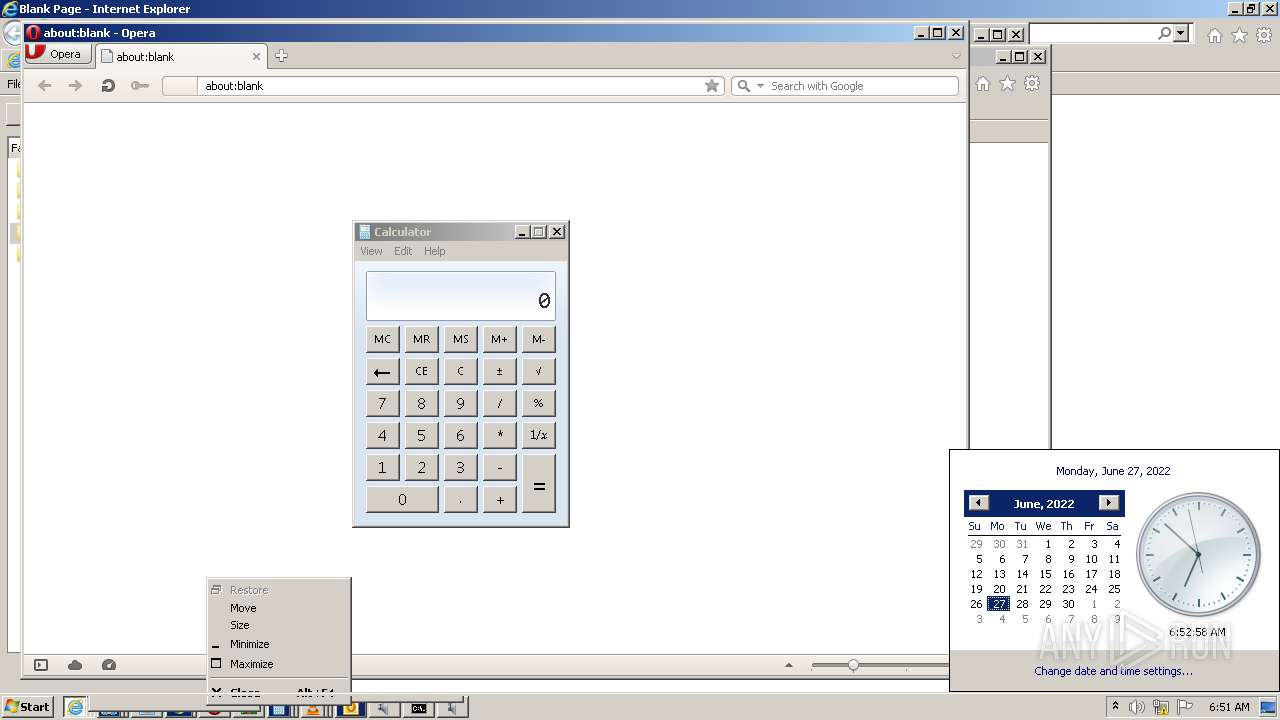
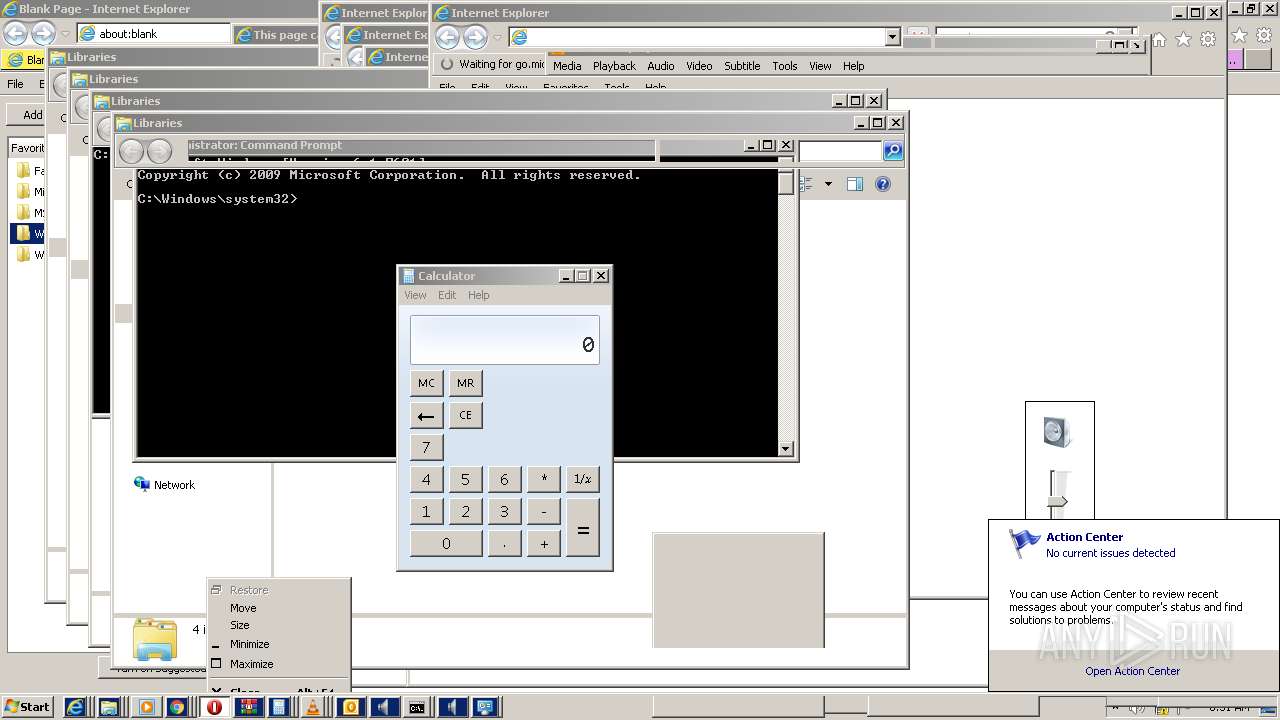
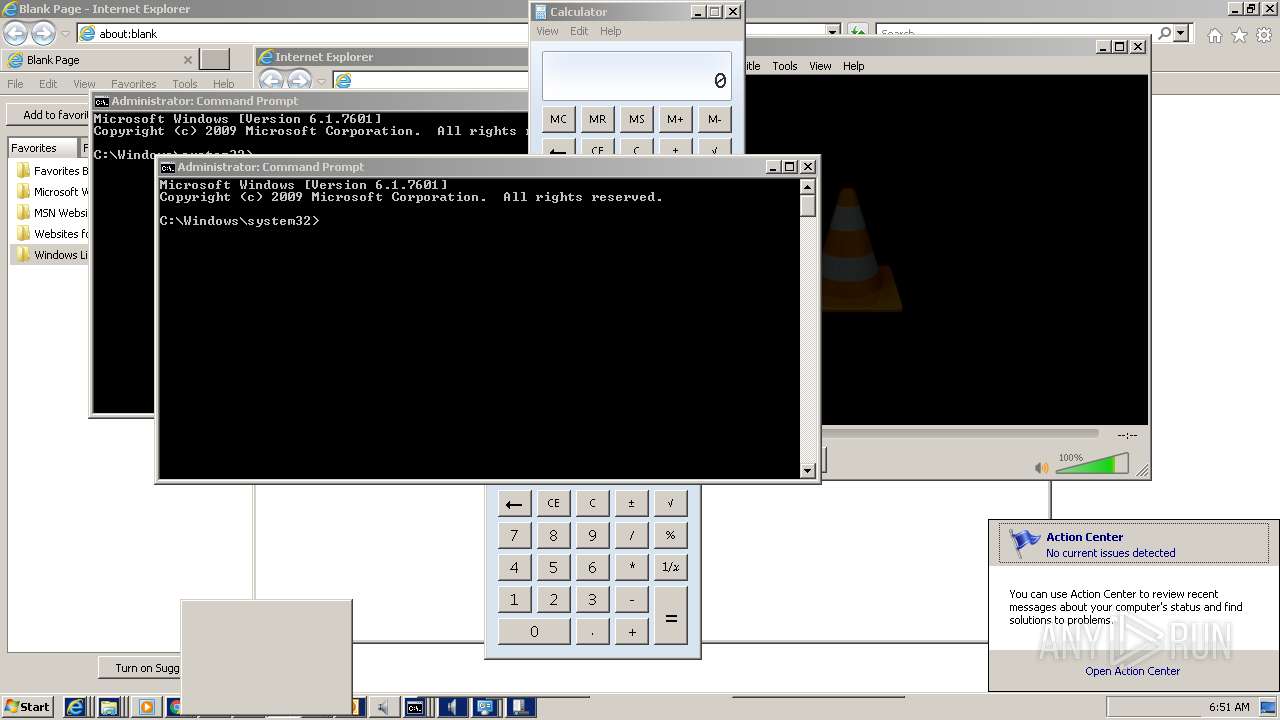
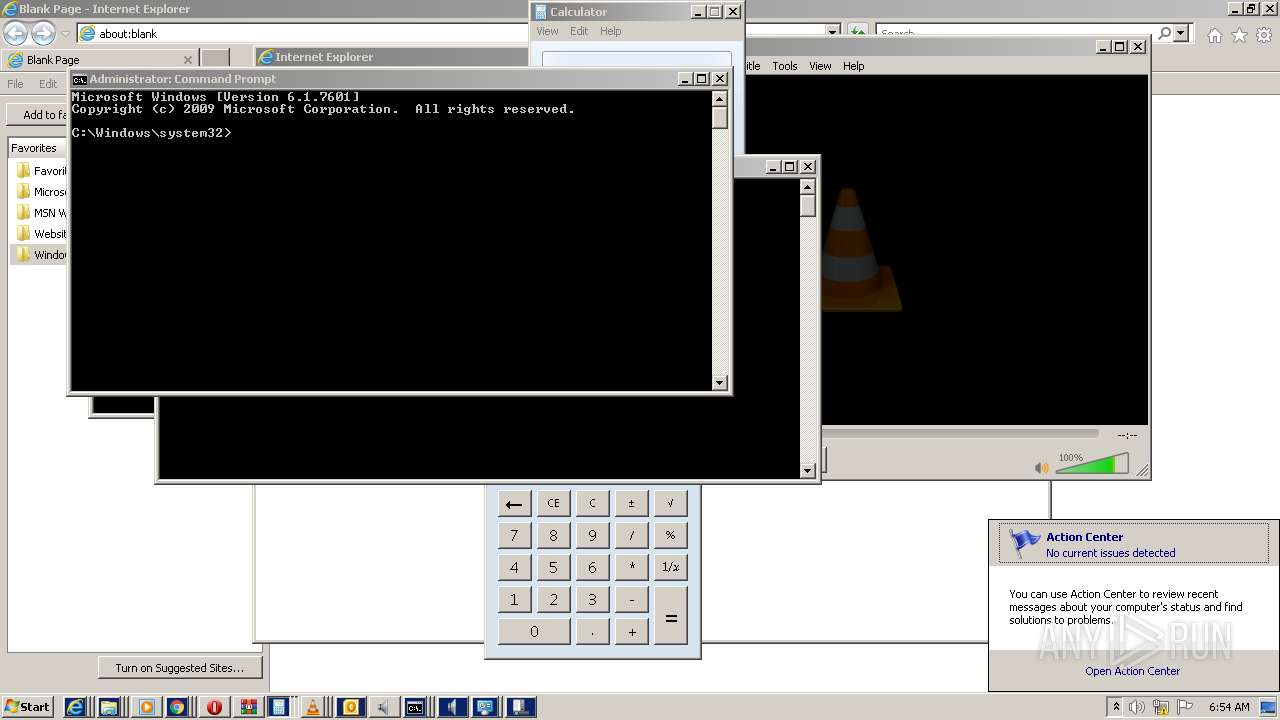
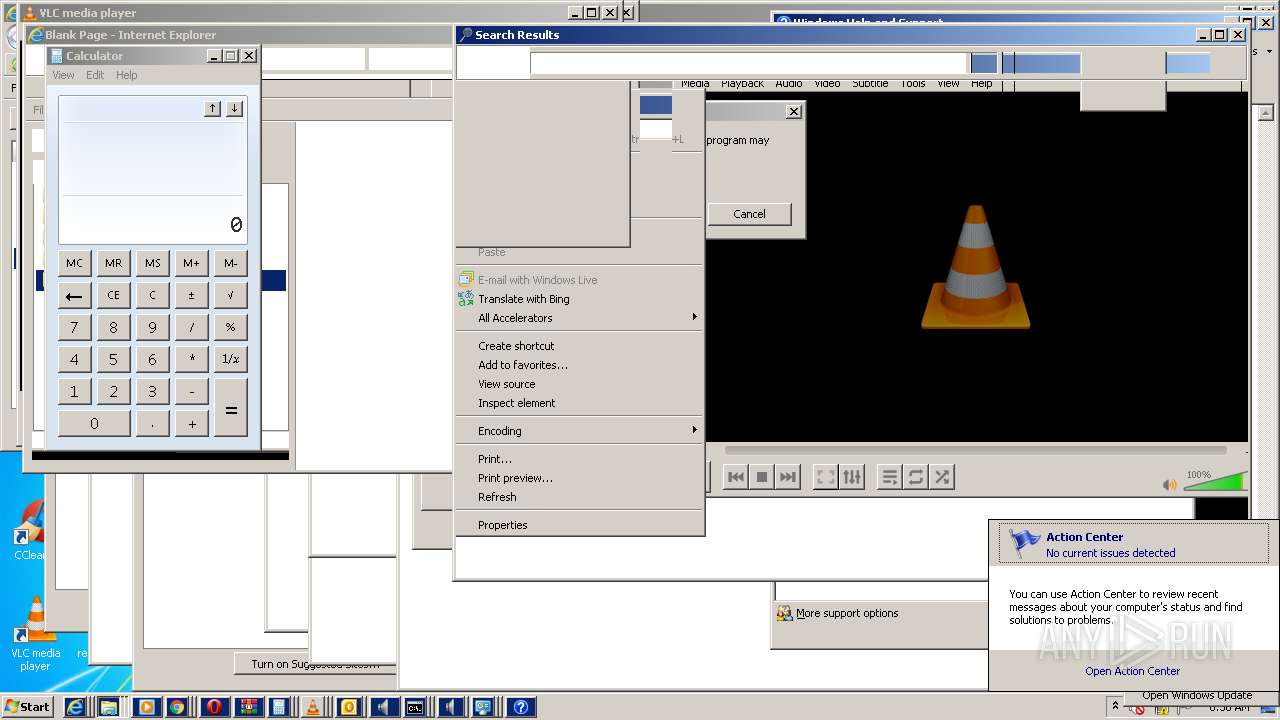
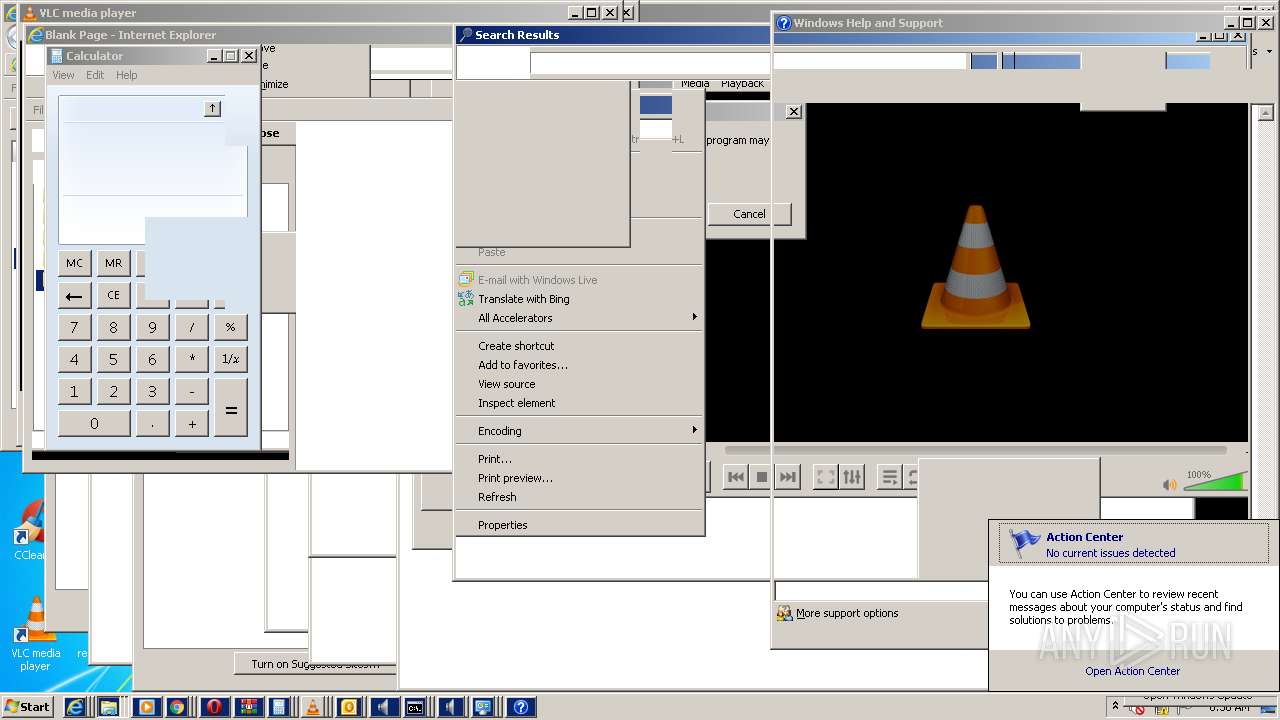
INFO
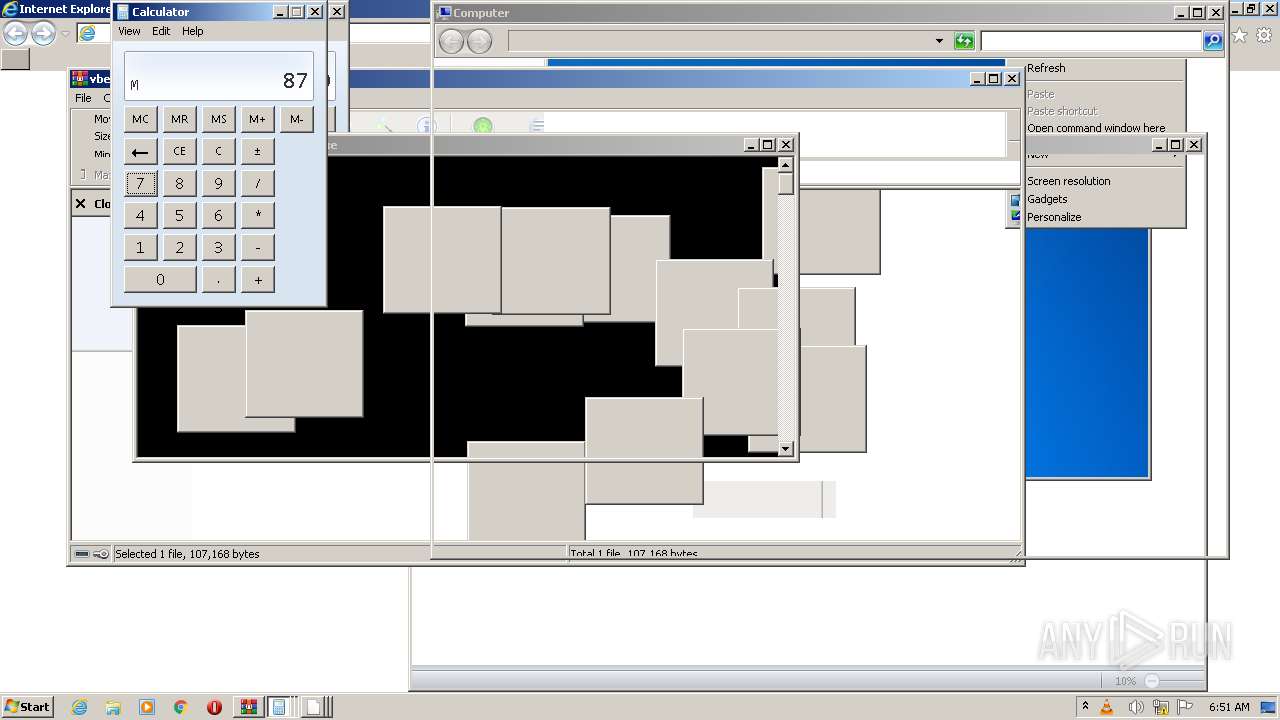
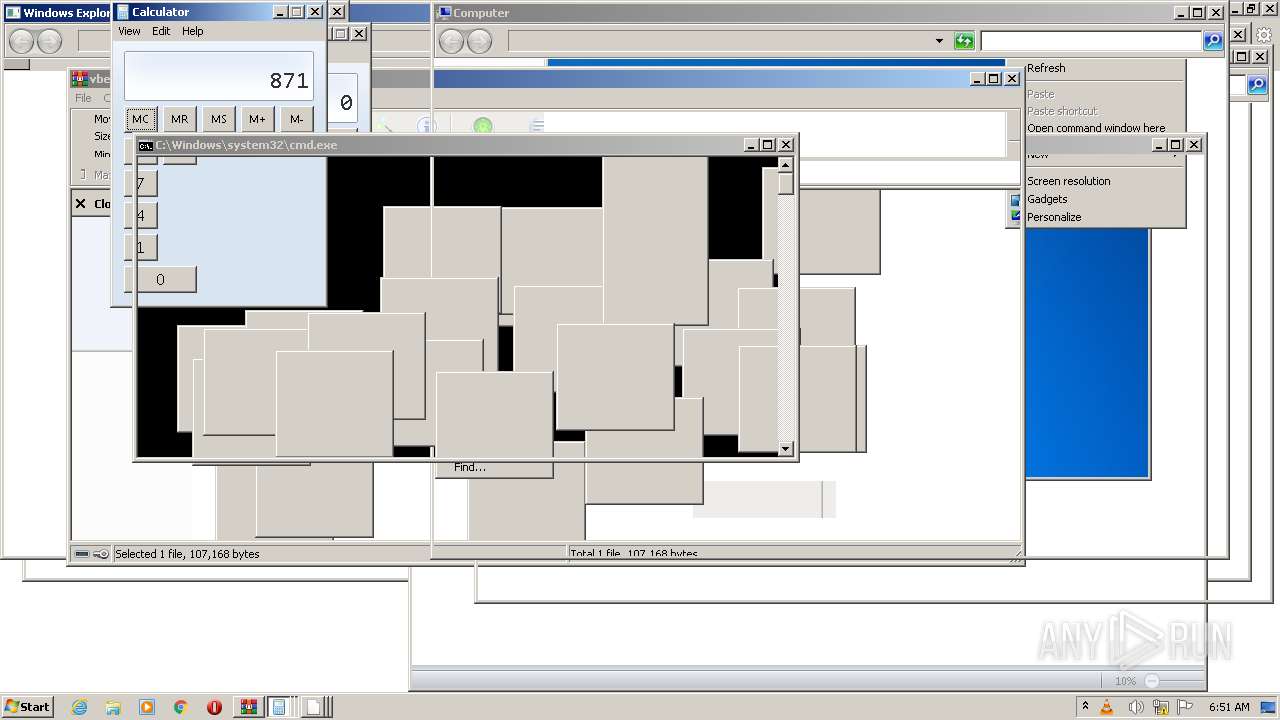
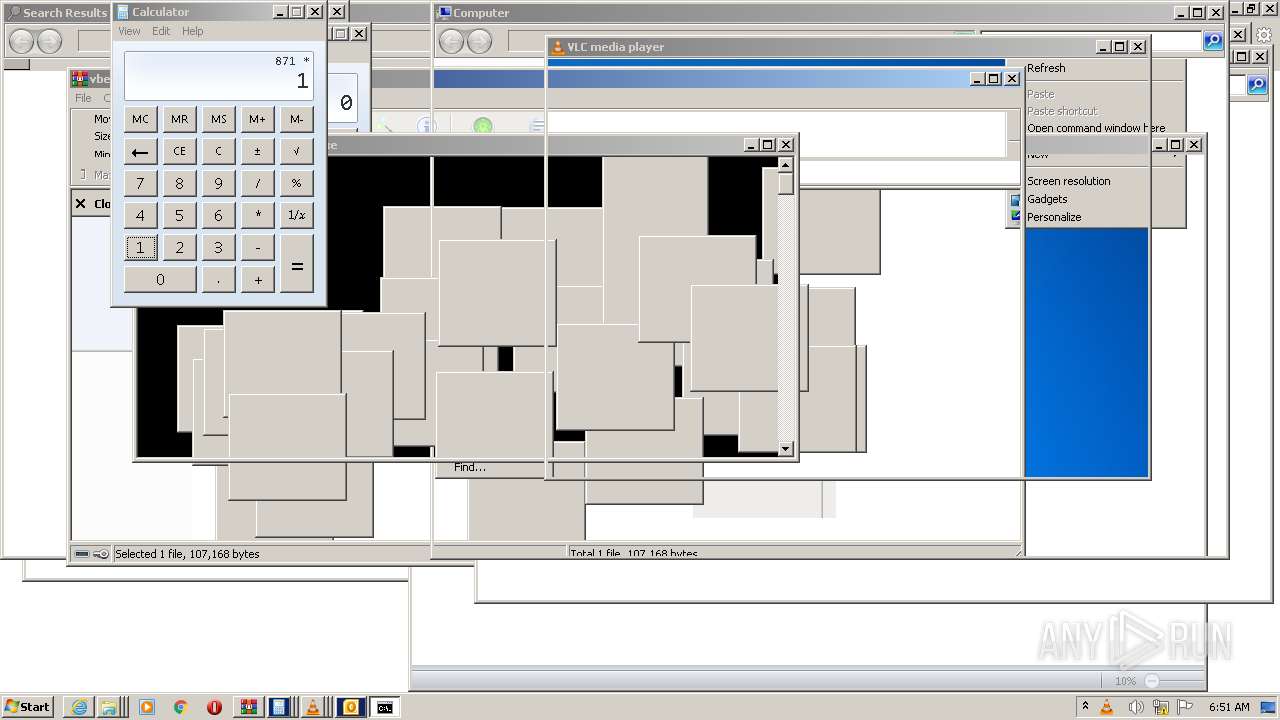
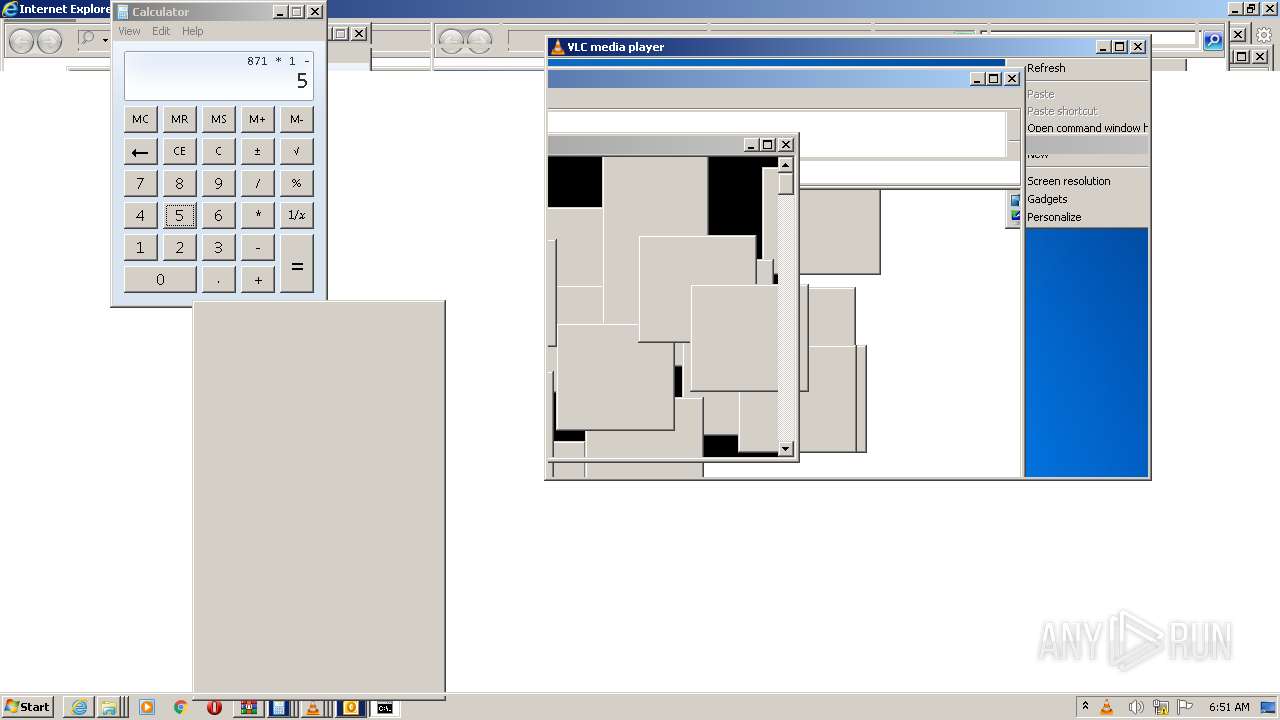
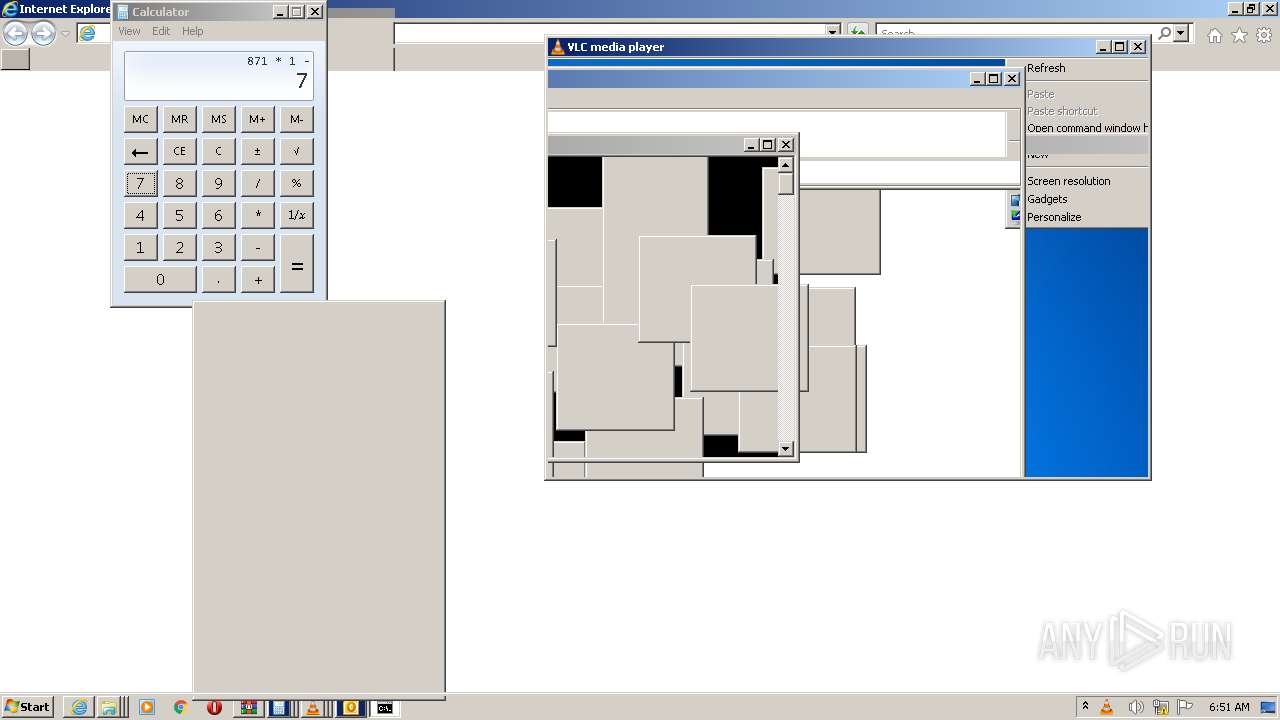
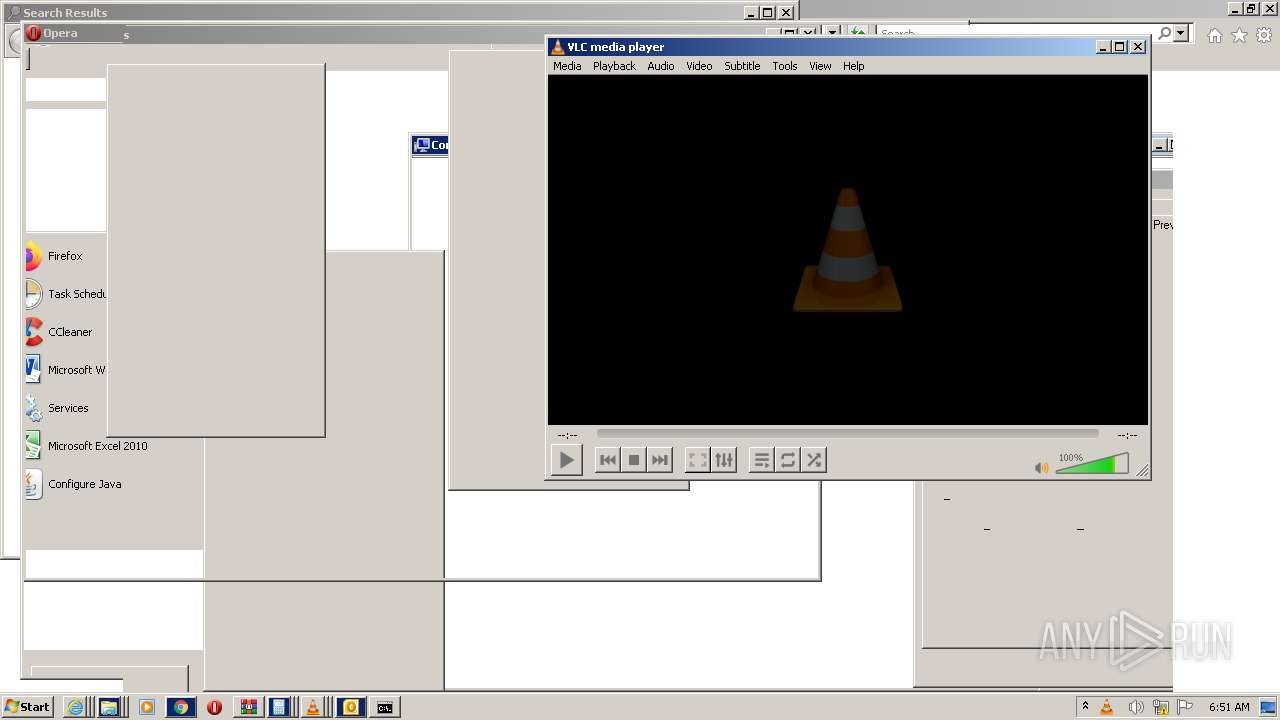
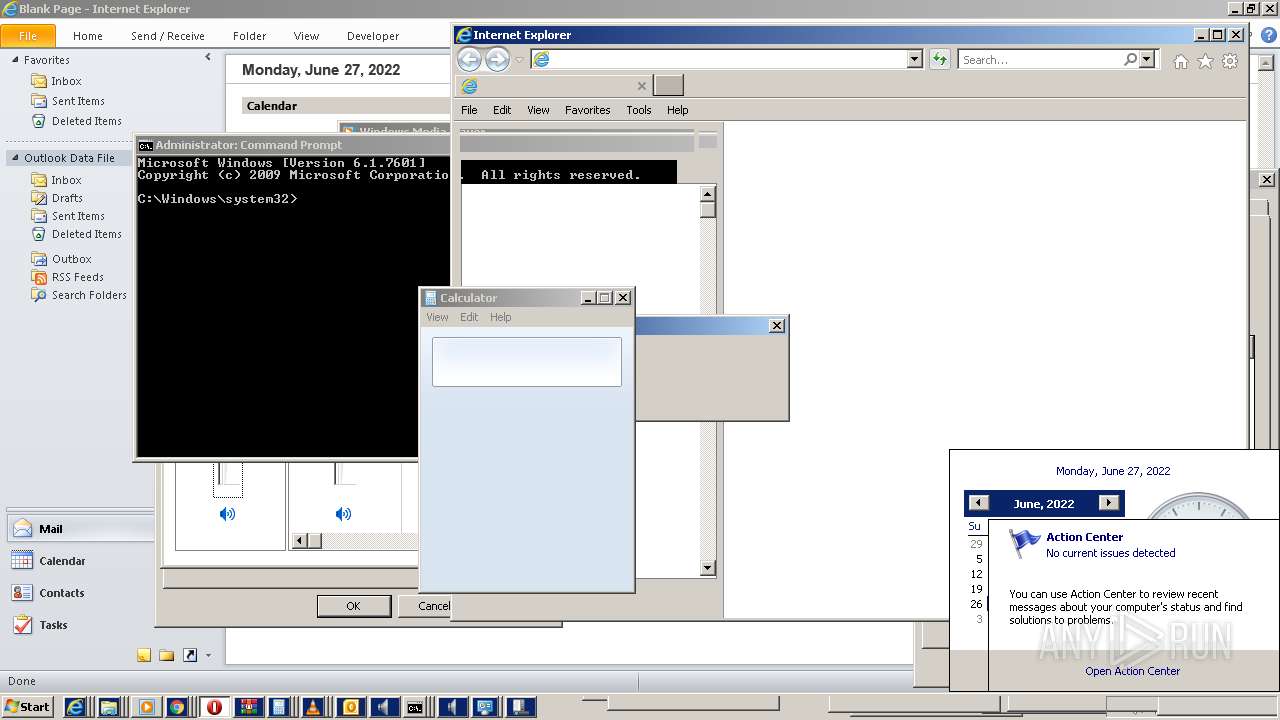
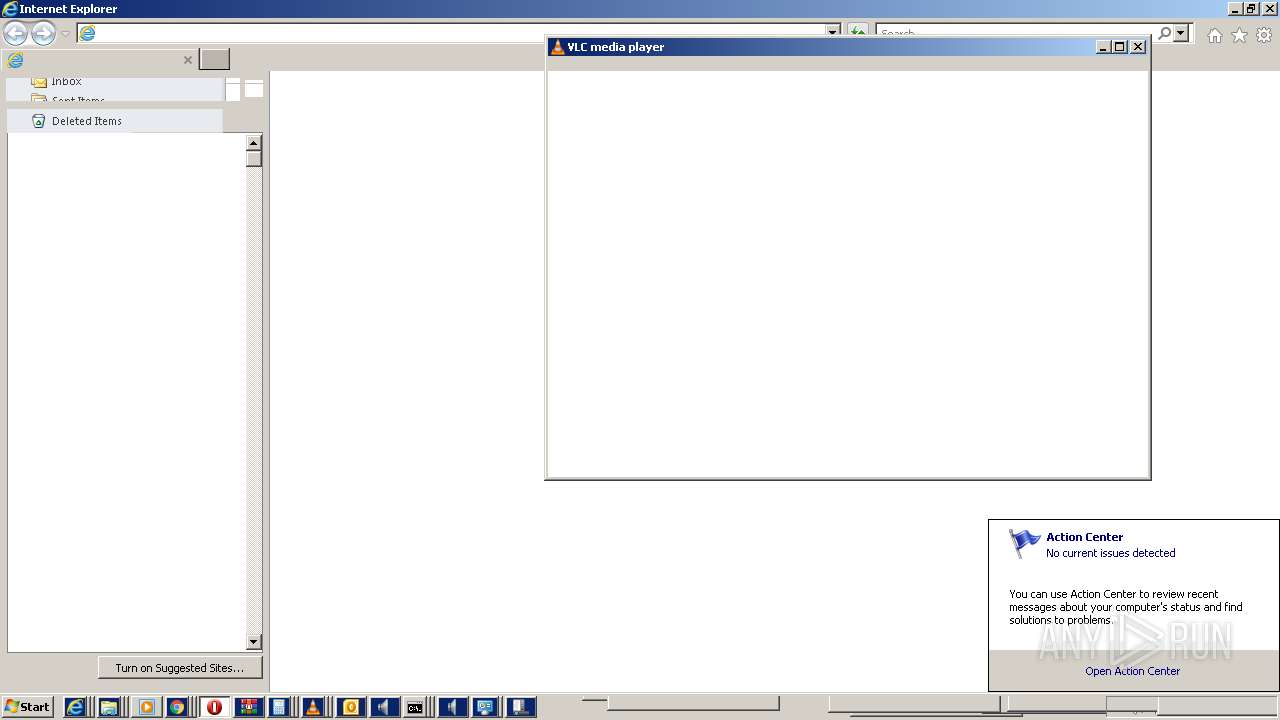
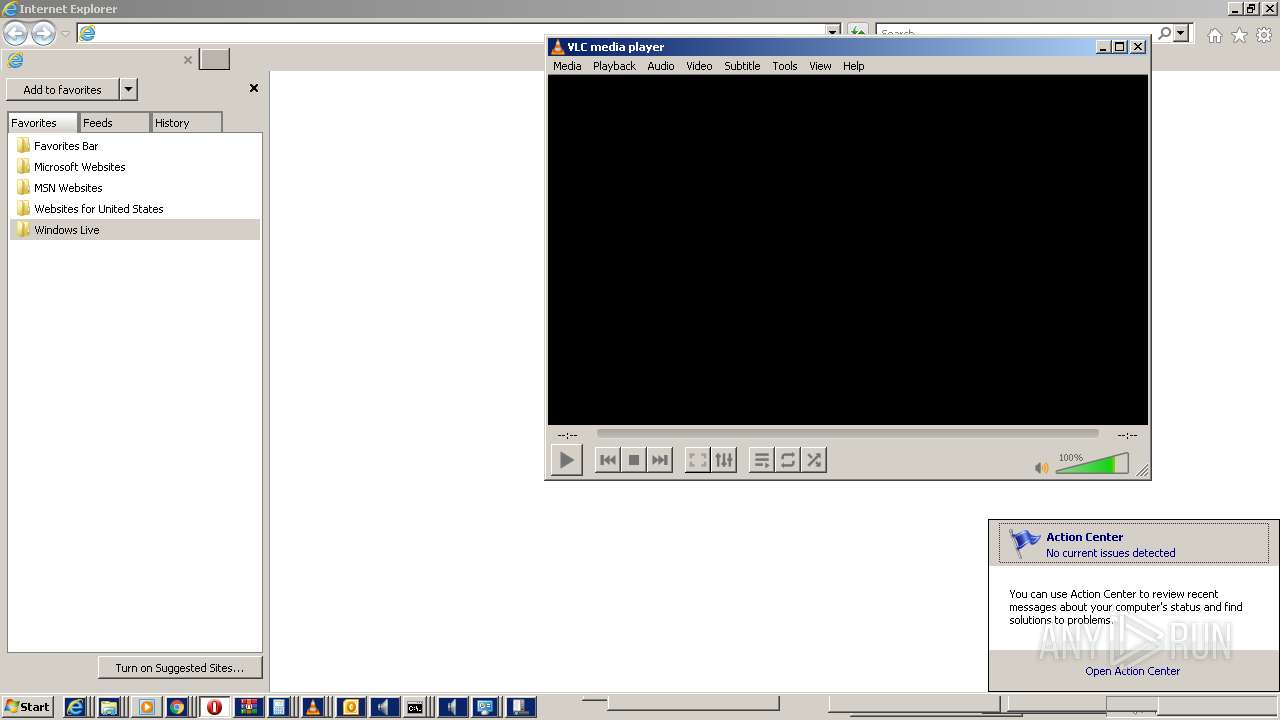
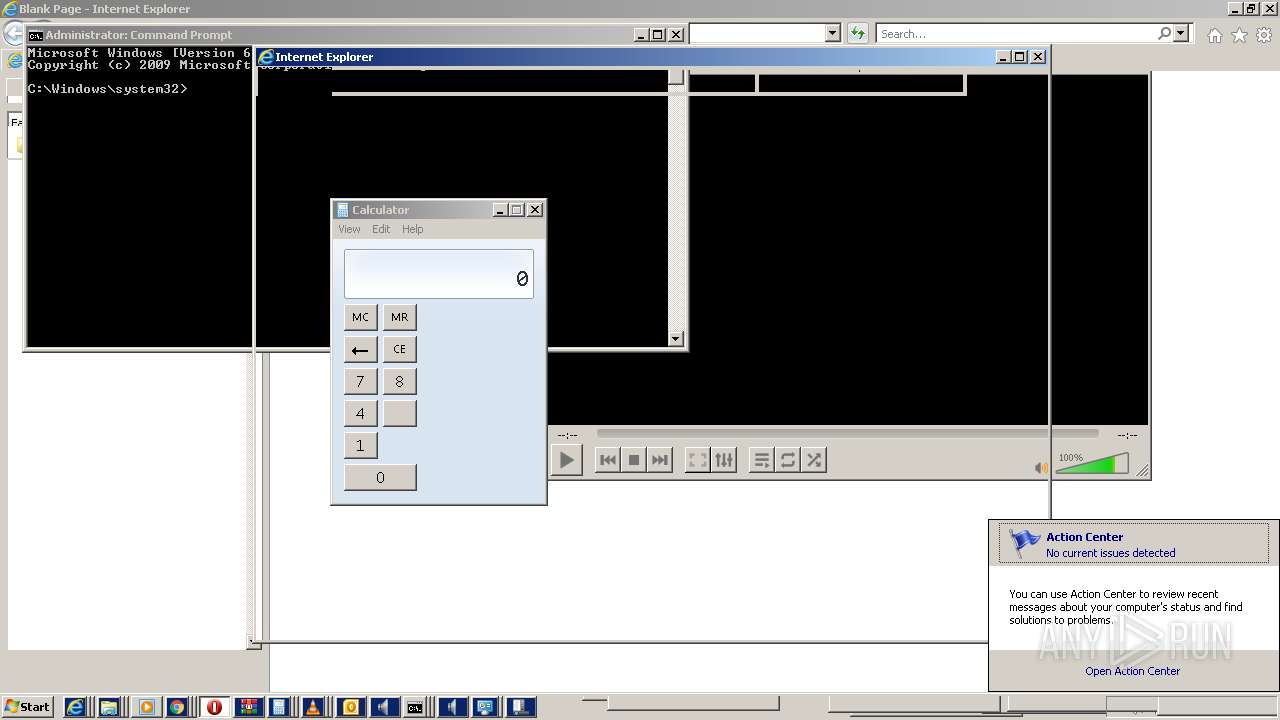
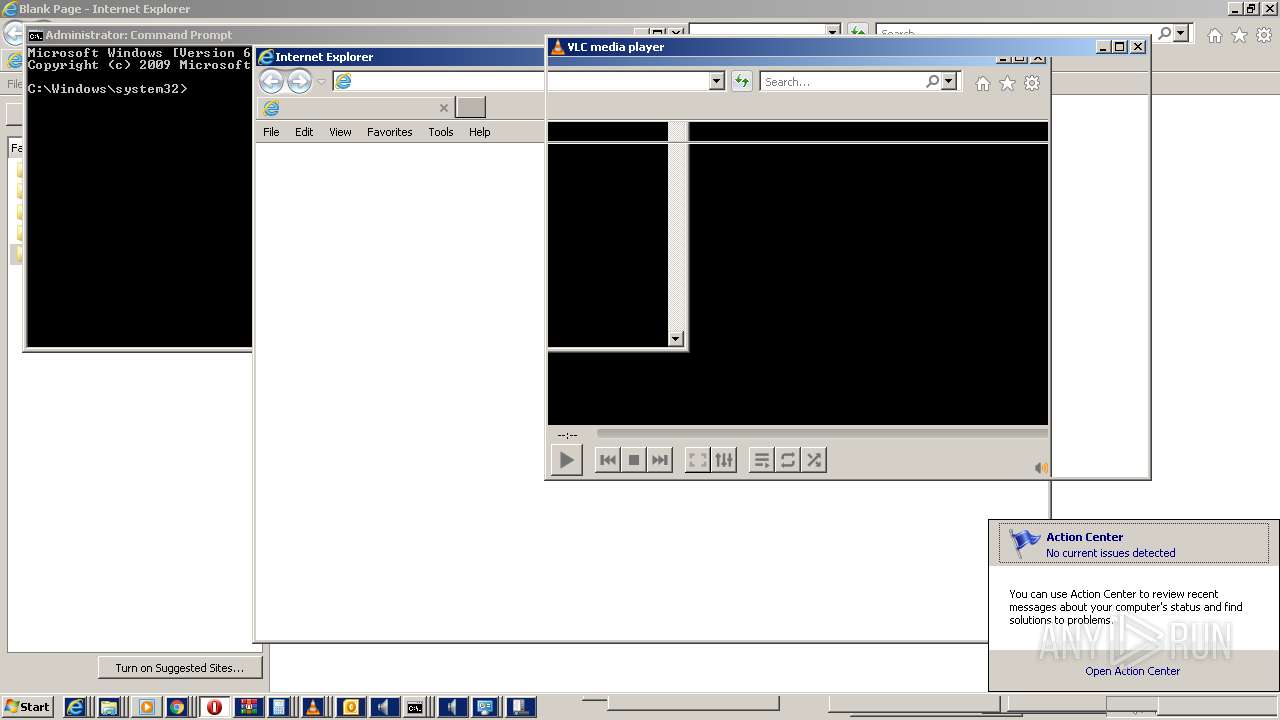
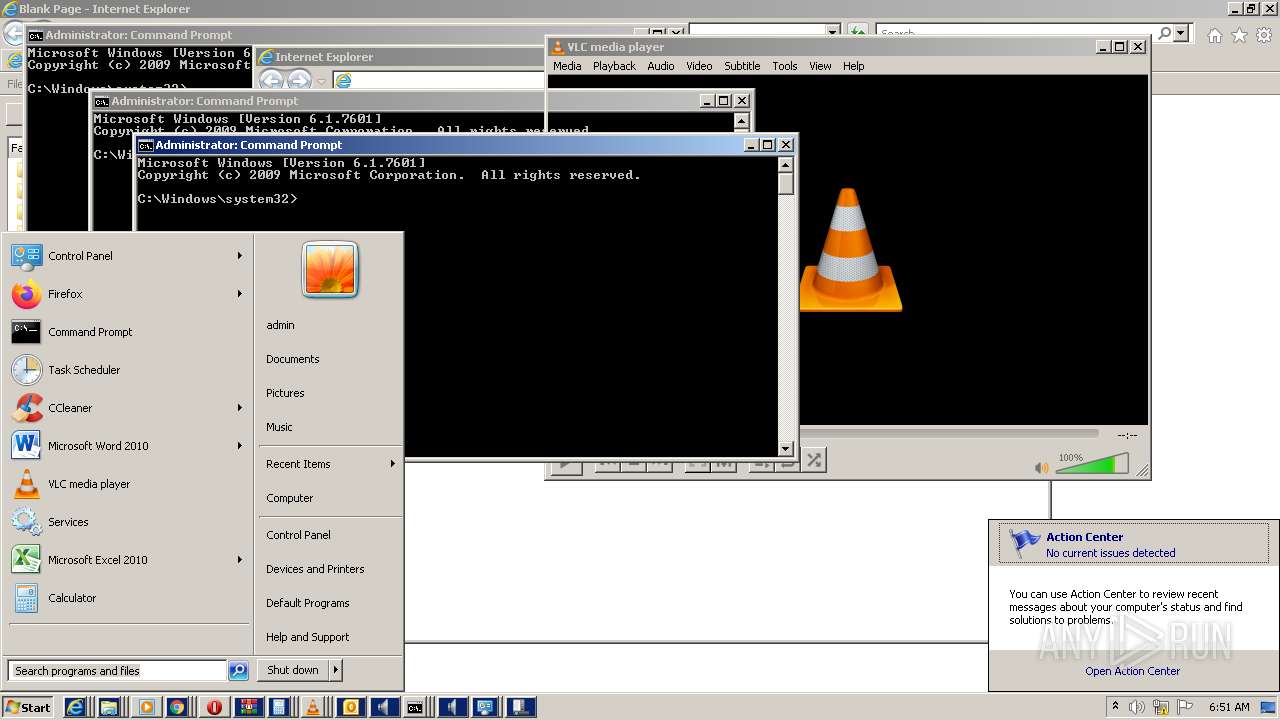
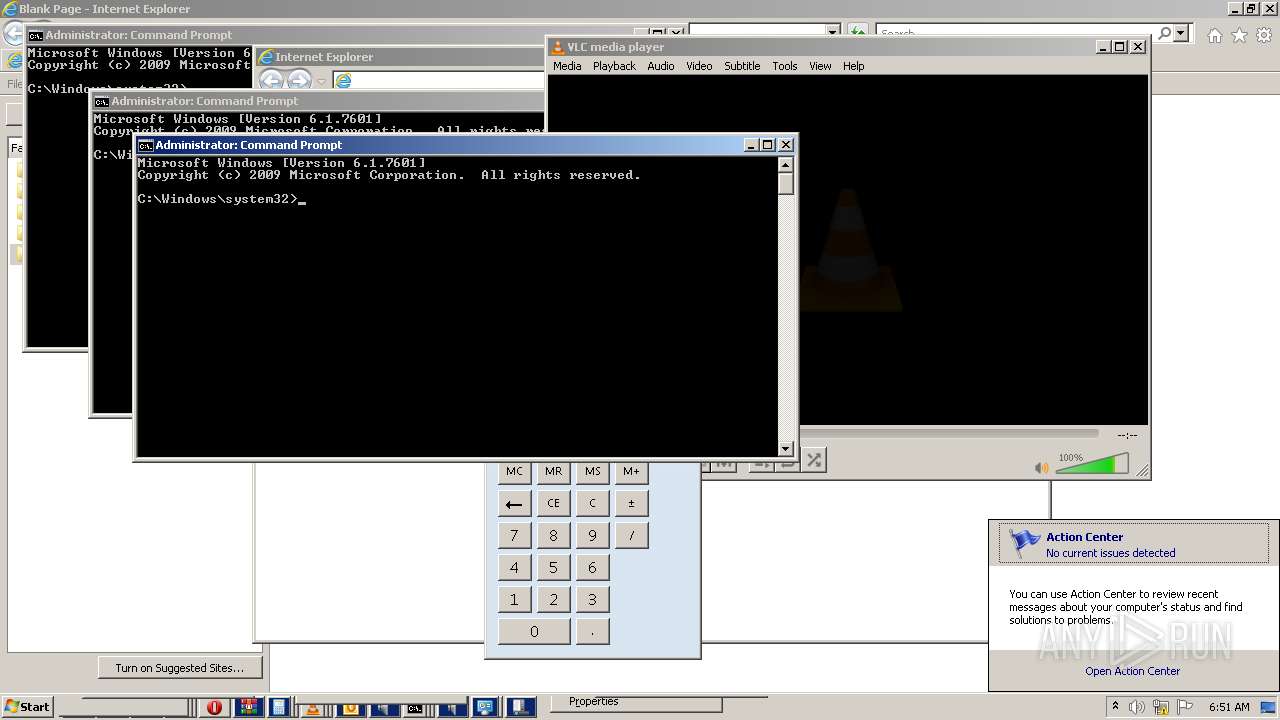
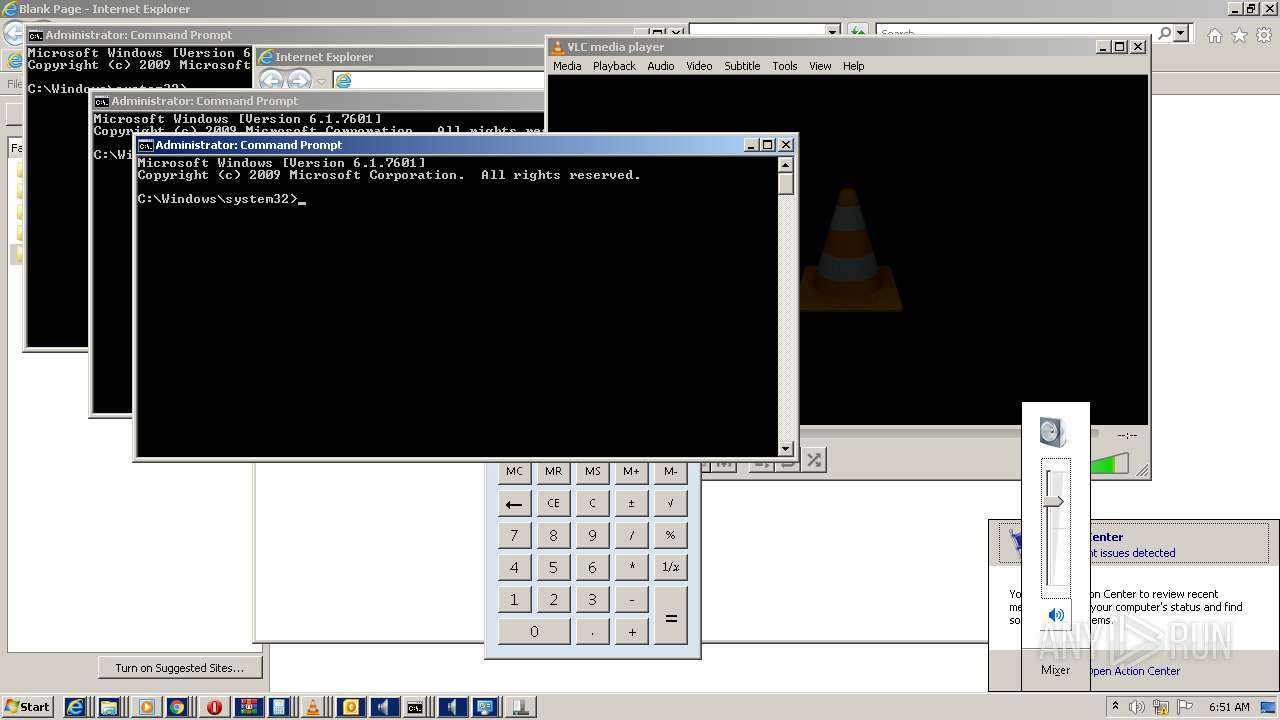
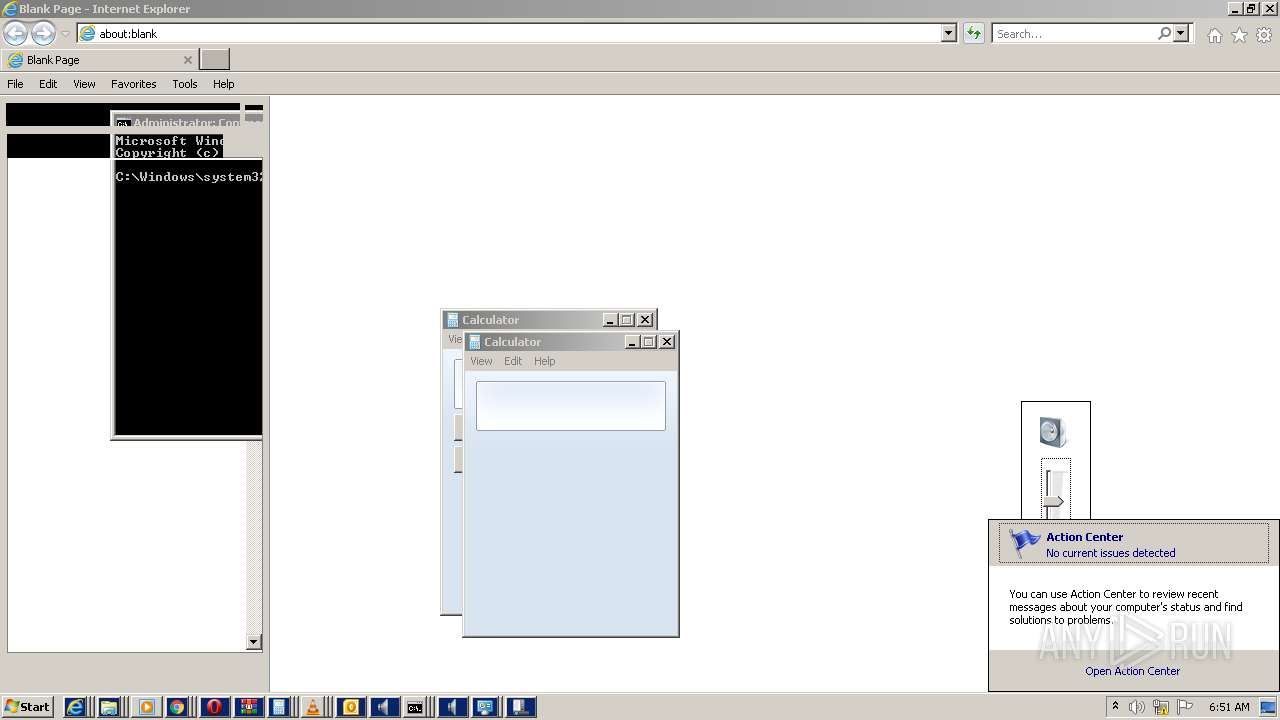
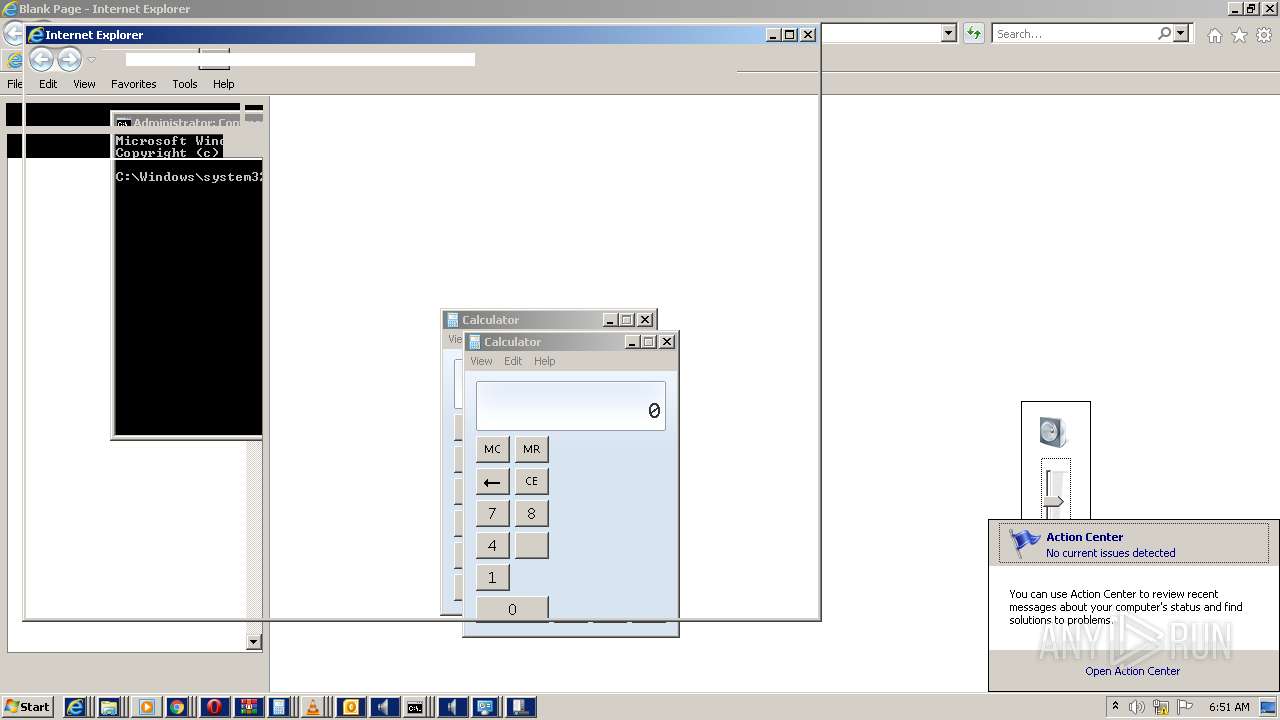
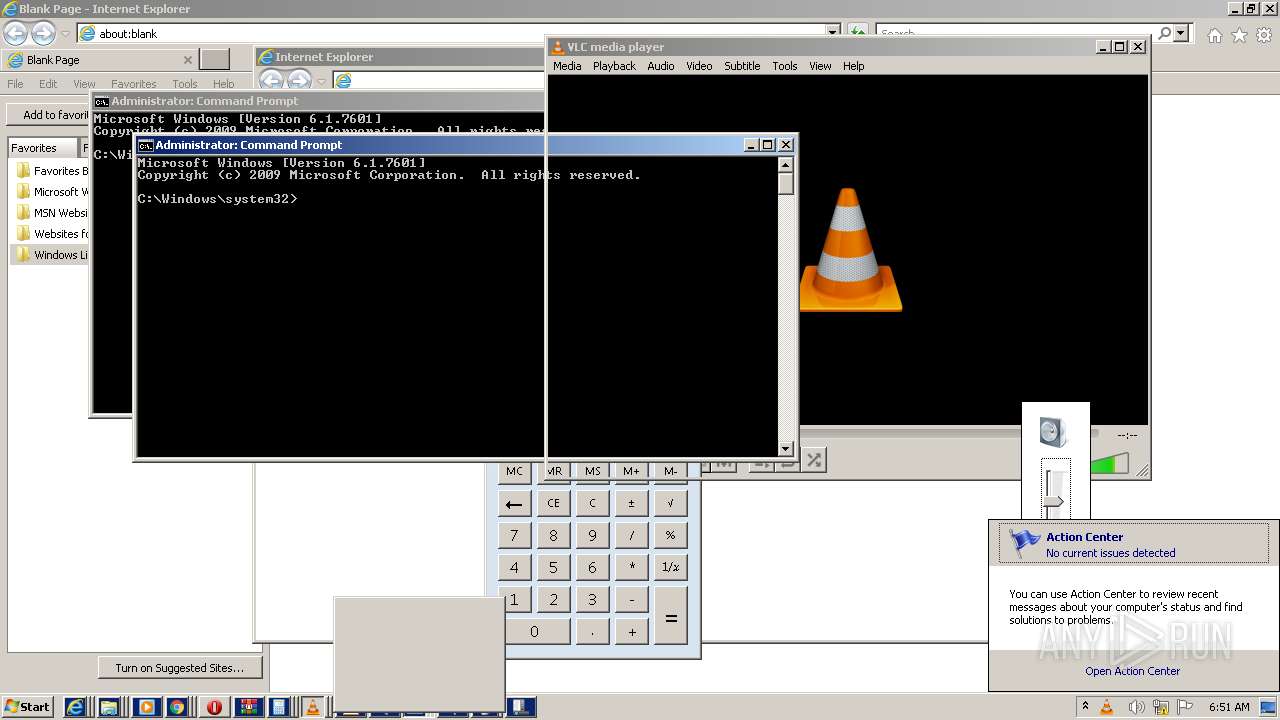
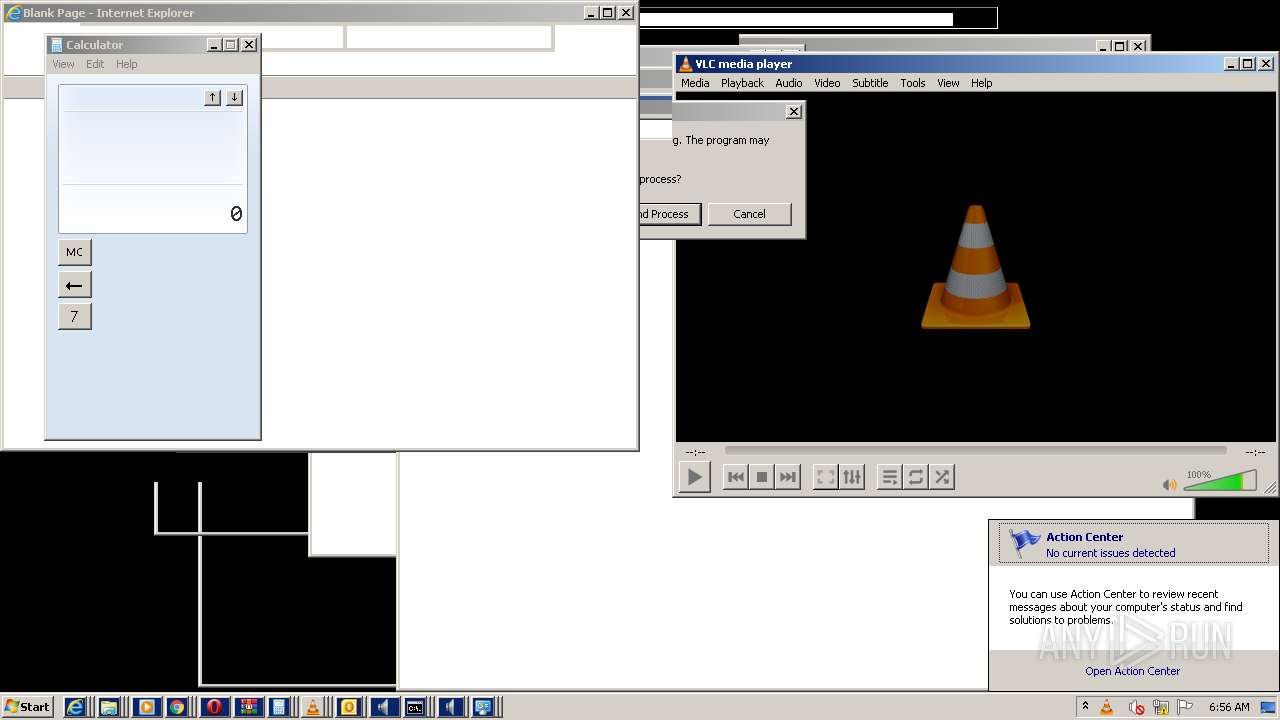
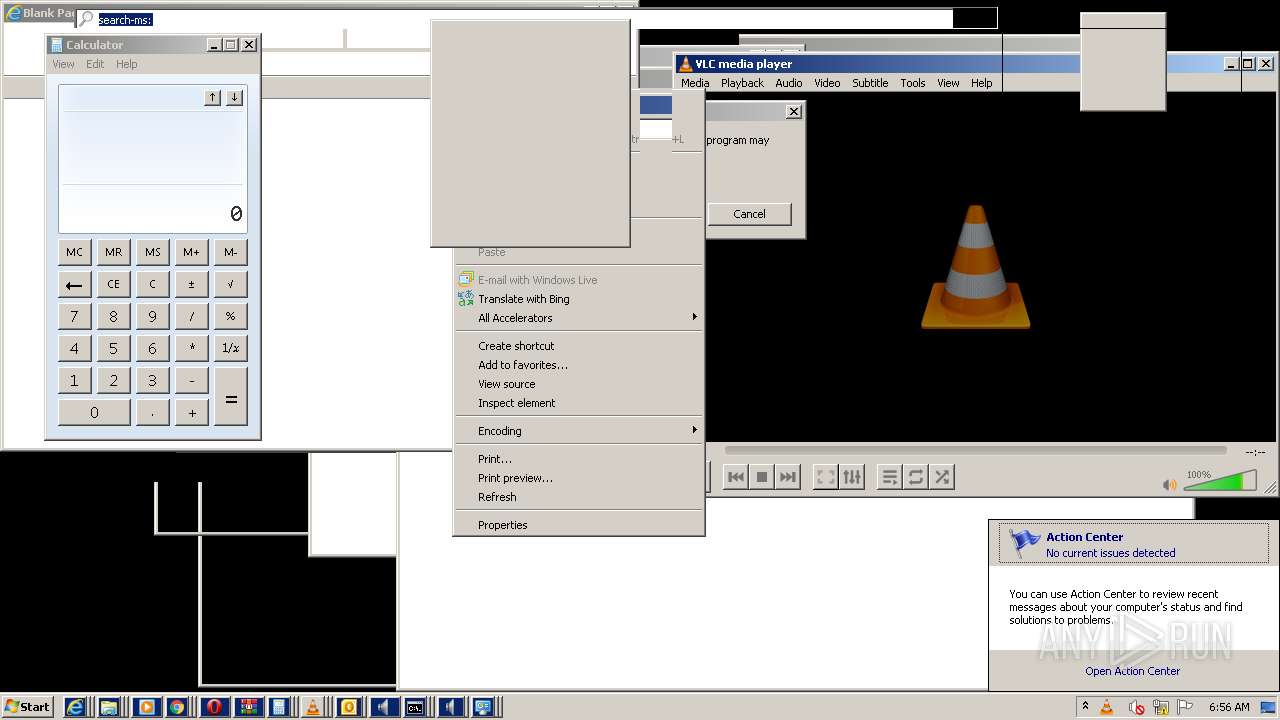
Manual execution by user
- vlc.exe (PID: 2768)
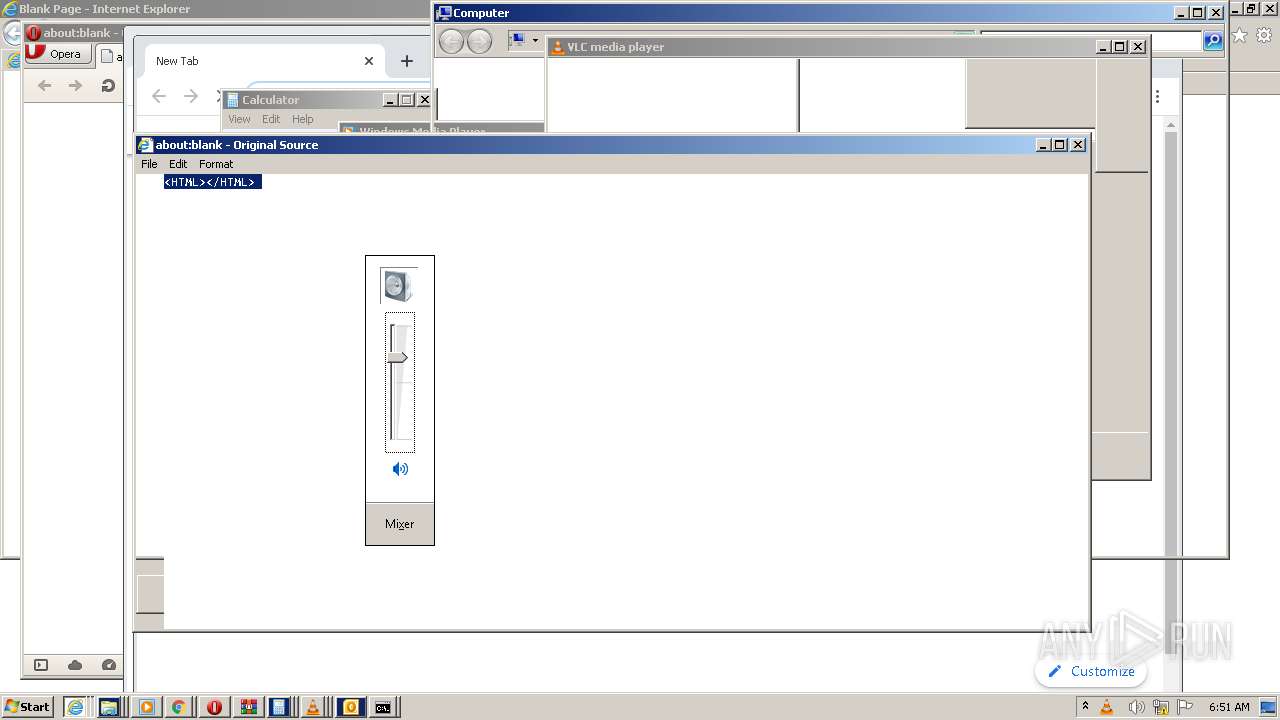
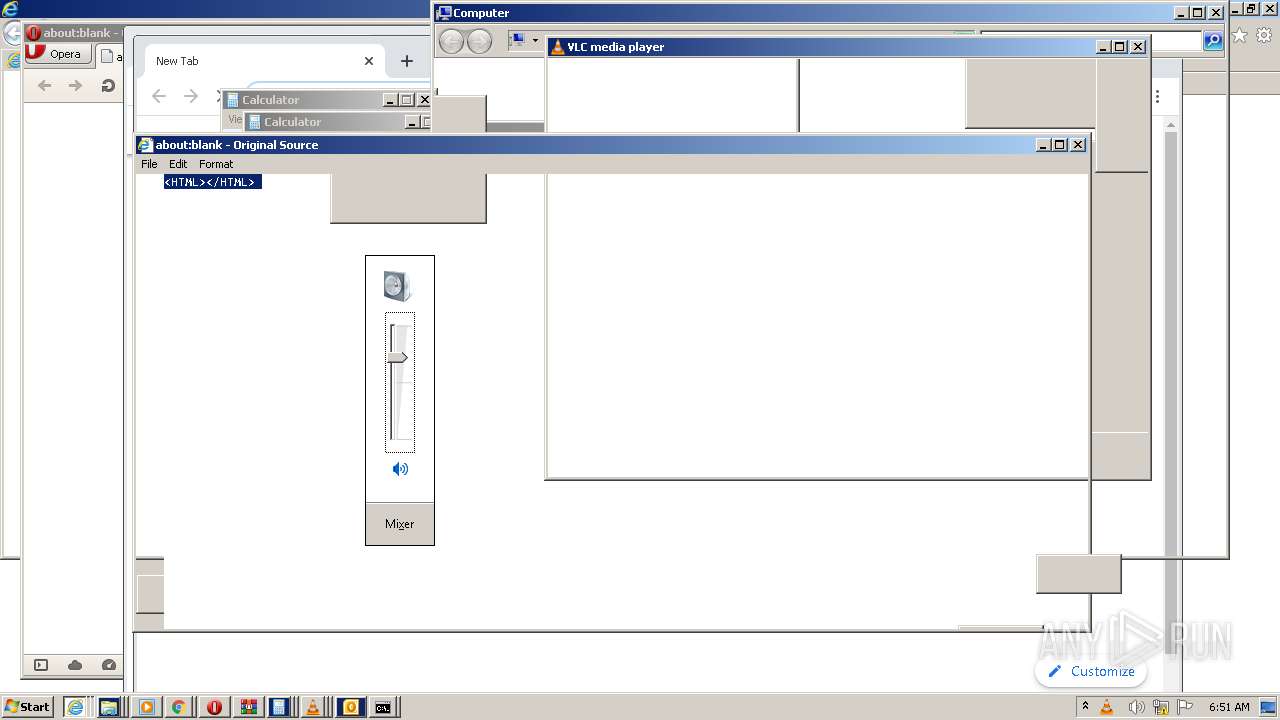
- calc.exe (PID: 1676)
- vlc.exe (PID: 3712)
- calc.exe (PID: 1276)
- vlc.exe (PID: 3256)
- vlc.exe (PID: 3628)
- OUTLOOK.EXE (PID: 2336)
- vlc.exe (PID: 4020)
- calc.exe (PID: 1800)
- iexplore.exe (PID: 772)
- calc.exe (PID: 1624)
- calc.exe (PID: 3216)
- OUTLOOK.EXE (PID: 3596)
- OUTLOOK.EXE (PID: 3020)
- cmd.exe (PID: 3864)
- calc.exe (PID: 2864)
- calc.exe (PID: 4004)
- calc.exe (PID: 1872)
- vlc.exe (PID: 3388)
- vlc.exe (PID: 1188)
- vlc.exe (PID: 3332)
- OUTLOOK.EXE (PID: 3384)
- OUTLOOK.EXE (PID: 1204)
- chrome.exe (PID: 3592)
- iexplore.exe (PID: 116)
- OUTLOOK.EXE (PID: 4352)
- iexplore.exe (PID: 4480)
- iexplore.exe (PID: 5452)
- vlc.exe (PID: 5688)
- OUTLOOK.EXE (PID: 5220)
- vlc.exe (PID: 5812)
- vlc.exe (PID: 5940)
- OUTLOOK.EXE (PID: 5132)
- vlc.exe (PID: 5292)
- calc.exe (PID: 5700)
- OUTLOOK.EXE (PID: 4224)
- explorer.exe (PID: 5284)
- iexplore.exe (PID: 5856)
- iexplore.exe (PID: 4168)
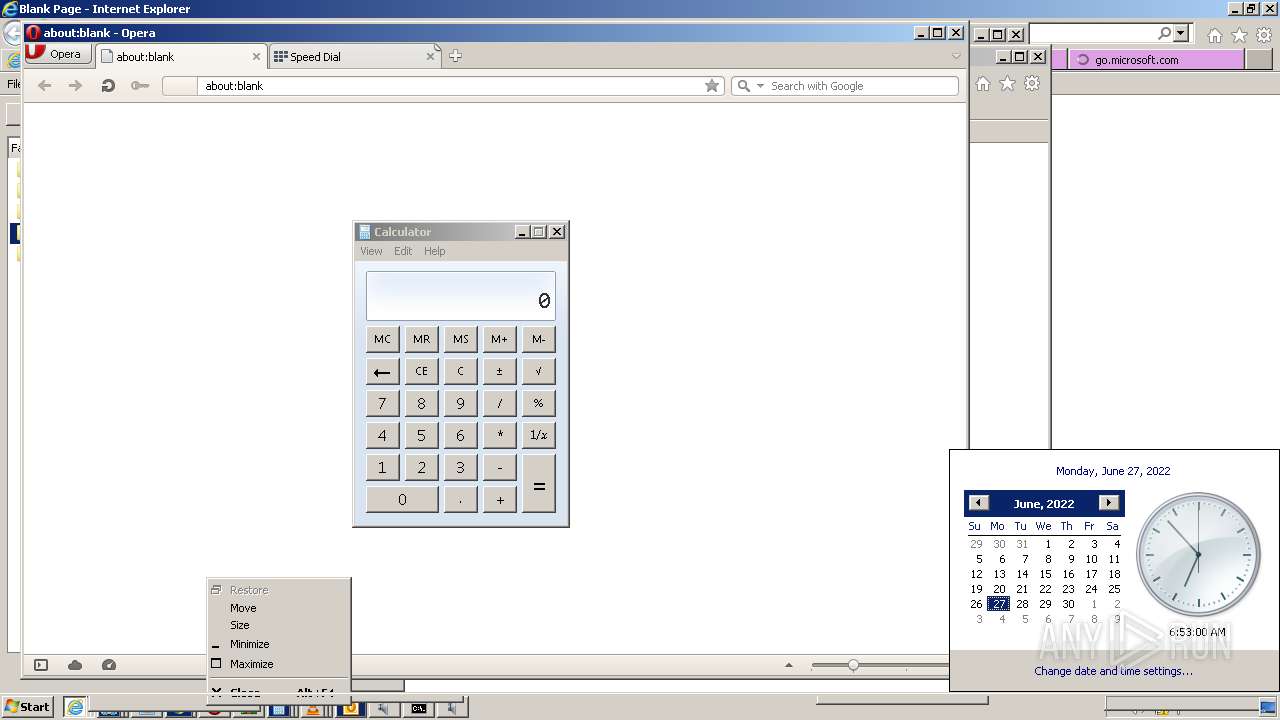
- opera.exe (PID: 6068)
- OUTLOOK.EXE (PID: 4744)
- vlc.exe (PID: 928)
- OUTLOOK.EXE (PID: 5356)
- calc.exe (PID: 5756)
- OUTLOOK.EXE (PID: 4176)
- calc.exe (PID: 5300)
- cmd.exe (PID: 5916)
- vlc.exe (PID: 4236)
- OUTLOOK.EXE (PID: 5432)
- wmplayer.exe (PID: 5520)
- iexplore.exe (PID: 5368)
- vlc.exe (PID: 4300)
- chrome.exe (PID: 5512)
- SndVol.exe (PID: 4460)
- calc.exe (PID: 4440)
- OUTLOOK.EXE (PID: 1568)
- calc.exe (PID: 4892)
- vlc.exe (PID: 2200)
- vlc.exe (PID: 4272)
- iexplore.exe (PID: 5284)
- OUTLOOK.EXE (PID: 3744)
- iexplore.exe (PID: 2220)
- calc.exe (PID: 5496)
- calc.exe (PID: 6220)
- vlc.exe (PID: 6424)
- vlc.exe (PID: 5192)
- iexplore.exe (PID: 7656)
- iexplore.exe (PID: 7880)
- calc.exe (PID: 6624)
- calc.exe (PID: 6536)
- vlc.exe (PID: 6908)
- OUTLOOK.EXE (PID: 7288)
- OUTLOOK.EXE (PID: 7672)
- vlc.exe (PID: 6280)
- explorer.exe (PID: 7324)
- cmd.exe (PID: 6564)
- calc.exe (PID: 8072)
- calc.exe (PID: 7824)
- calc.exe (PID: 6356)
- iexplore.exe (PID: 4452)
- opera.exe (PID: 6940)
- OUTLOOK.EXE (PID: 6984)
- SndVol.exe (PID: 6544)
- calc.exe (PID: 6976)
- explorer.exe (PID: 2732)
- control.exe (PID: 7636)
- explorer.exe (PID: 6352)
- wmplayer.exe (PID: 6256)
- chrome.exe (PID: 4312)
- vlc.exe (PID: 8040)
- vlc.exe (PID: 6360)
- calc.exe (PID: 7204)
- cmd.exe (PID: 1824)
- explorer.exe (PID: 4292)
- explorer.exe (PID: 6568)
- calc.exe (PID: 6972)
- calc.exe (PID: 7680)
- OUTLOOK.EXE (PID: 6164)
- wmplayer.exe (PID: 1844)
- wmplayer.exe (PID: 6528)
- iexplore.exe (PID: 4592)
- cmd.exe (PID: 7884)
- calc.exe (PID: 10136)
- calc.exe (PID: 8788)
- iexplore.exe (PID: 9444)
- calc.exe (PID: 9080)
- control.exe (PID: 9264)
- cmd.exe (PID: 9364)
- OUTLOOK.EXE (PID: 9944)
- wmplayer.exe (PID: 8664)
- control.exe (PID: 8468)
- chrome.exe (PID: 3864)
- iexplore.exe (PID: 9392)
- opera.exe (PID: 8900)
- wmplayer.exe (PID: 8816)
- vlc.exe (PID: 9248)
- opera.exe (PID: 9288)
- SndVol.exe (PID: 9628)
- vlc.exe (PID: 8108)
- calc.exe (PID: 8804)
- iexplore.exe (PID: 9972)
- vlc.exe (PID: 8856)
- chrome.exe (PID: 8308)
- wmplayer.exe (PID: 9524)
- chrome.exe (PID: 3972)
- explorer.exe (PID: 8420)
- opera.exe (PID: 9760)
- wmplayer.exe (PID: 9168)
- rundll32.exe (PID: 4380)
- cmd.exe (PID: 10208)
- cmd.exe (PID: 8364)
- explorer.exe (PID: 9584)
- iexplore.exe (PID: 3668)
- cmd.exe (PID: 2680)
- calc.exe (PID: 8748)
- vlc.exe (PID: 6940)
- rundll32.exe (PID: 8308)
- wmplayer.exe (PID: 5588)
- cmd.exe (PID: 9236)
- control.exe (PID: 8532)
- vlc.exe (PID: 6836)
- rundll32.exe (PID: 10164)
- chrome.exe (PID: 8716)
- vlc.exe (PID: 6060)
- calc.exe (PID: 8300)
- control.exe (PID: 4520)
- cmd.exe (PID: 8492)
- OUTLOOK.EXE (PID: 9788)
- vlc.exe (PID: 7376)
- calc.exe (PID: 3468)
- rundll32.exe (PID: 8236)
- wmplayer.exe (PID: 3432)
- opera.exe (PID: 3276)
- calc.exe (PID: 9140)
- useraccountcontrolsettings.exe (PID: 836)
- SndVol.exe (PID: 6436)
- chrome.exe (PID: 8212)
- OUTLOOK.EXE (PID: 9356)
- iexplore.exe (PID: 2972)
- calc.exe (PID: 10072)
- vlc.exe (PID: 2660)
- calc.exe (PID: 8728)
- iexplore.exe (PID: 7920)
- WinRAR.exe (PID: 8524)
- iexplore.exe (PID: 9060)
- vlc.exe (PID: 7908)
- calc.exe (PID: 8908)
- OUTLOOK.EXE (PID: 2784)
- calc.exe (PID: 7052)
- calc.exe (PID: 9060)
- vlc.exe (PID: 956)
- iexplore.exe (PID: 7788)
- iexplore.exe (PID: 7744)
- calc.exe (PID: 8396)
- vlc.exe (PID: 7436)
- vlc.exe (PID: 7988)
- iexplore.exe (PID: 8344)
- OUTLOOK.EXE (PID: 2112)
- OUTLOOK.EXE (PID: 3808)
- calc.exe (PID: 10172)
- iexplore.exe (PID: 8304)
- vlc.exe (PID: 9736)
- iexplore.exe (PID: 12084)
- vlc.exe (PID: 10476)
- vlc.exe (PID: 11160)
- calc.exe (PID: 11976)
- calc.exe (PID: 11408)
- vlc.exe (PID: 11612)
- opera.exe (PID: 12048)
- OUTLOOK.EXE (PID: 10612)
- calc.exe (PID: 10916)
- calc.exe (PID: 11088)
- OUTLOOK.EXE (PID: 11128)
- calc.exe (PID: 11484)
- calc.exe (PID: 11564)
- vlc.exe (PID: 11808)
- iexplore.exe (PID: 11460)
- calc.exe (PID: 9288)
- vlc.exe (PID: 10436)
- OUTLOOK.EXE (PID: 11236)
- iexplore.exe (PID: 11504)
- OUTLOOK.EXE (PID: 11252)
- vlc.exe (PID: 9224)
- OUTLOOK.EXE (PID: 11892)
- calc.exe (PID: 10316)
- OUTLOOK.EXE (PID: 11248)
- vlc.exe (PID: 7600)
- vlc.exe (PID: 11348)
- calc.exe (PID: 11816)
- pcwrun.exe (PID: 11528)
Checks supported languages
- calc.exe (PID: 1276)
- calc.exe (PID: 1676)
- iexplore.exe (PID: 772)
- calc.exe (PID: 1624)
- calc.exe (PID: 1800)
- calc.exe (PID: 3216)
- iexplore.exe (PID: 3044)
- calc.exe (PID: 2864)
- calc.exe (PID: 1872)
- calc.exe (PID: 4004)
- iexplore.exe (PID: 116)
- chrome.exe (PID: 3592)
- chrome.exe (PID: 1964)
- iexplore.exe (PID: 3584)
- chrome.exe (PID: 3268)
- chrome.exe (PID: 4044)
- chrome.exe (PID: 948)
- chrome.exe (PID: 1916)
- chrome.exe (PID: 3240)
- iexplore.exe (PID: 4480)
- chrome.exe (PID: 4848)
- iexplore.exe (PID: 5452)
- iexplore.exe (PID: 4736)
- iexplore.exe (PID: 5752)
- calc.exe (PID: 5700)
- iexplore.exe (PID: 5856)
- iexplore.exe (PID: 4284)
- explorer.exe (PID: 5284)
- iexplore.exe (PID: 4168)
- iexplore.exe (PID: 4676)
- opera.exe (PID: 6068)
- calc.exe (PID: 5756)
- iexplore.exe (PID: 5368)
- calc.exe (PID: 5300)
- chrome.exe (PID: 5512)
- chrome.exe (PID: 5528)
- SndVol.exe (PID: 4460)
- iexplore.exe (PID: 5284)
- calc.exe (PID: 4440)
- calc.exe (PID: 4892)
- chrome.exe (PID: 3776)
- rundll32.exe (PID: 5260)
- iexplore.exe (PID: 2220)
- calc.exe (PID: 5496)
- calc.exe (PID: 6220)
- control.exe (PID: 2024)
- iexplore.exe (PID: 6760)
- iexplore.exe (PID: 7656)
- iexplore.exe (PID: 7880)
- rundll32.exe (PID: 7380)
- control.exe (PID: 7808)
- control.exe (PID: 7180)
- calc.exe (PID: 6624)
- iexplore.exe (PID: 8148)
- rundll32.exe (PID: 8056)
- calc.exe (PID: 6536)
- calc.exe (PID: 8072)
- chrome.exe (PID: 6464)
- SndVol.exe (PID: 2912)
- explorer.exe (PID: 7324)
- chrome.exe (PID: 7928)
- calc.exe (PID: 6356)
- calc.exe (PID: 7824)
- iexplore.exe (PID: 4452)
- iexplore.exe (PID: 7616)
- iexplore.exe (PID: 6936)
- calc.exe (PID: 6976)
- OUTLOOK.EXE (PID: 6984)
- explorer.exe (PID: 2732)
- iexplore.exe (PID: 6244)
- SndVol.exe (PID: 6544)
- opera.exe (PID: 6940)
- chrome.exe (PID: 6940)
- explorer.exe (PID: 6352)
- control.exe (PID: 7636)
- chrome.exe (PID: 4312)
- iexplore.exe (PID: 7664)
- calc.exe (PID: 7204)
- explorer.exe (PID: 4292)
- explorer.exe (PID: 6568)
- calc.exe (PID: 7680)
- OUTLOOK.EXE (PID: 6164)
- calc.exe (PID: 6972)
- iexplore.exe (PID: 7944)
- iexplore.exe (PID: 4592)
- calc.exe (PID: 10136)
- iexplore.exe (PID: 9444)
- calc.exe (PID: 9080)
- control.exe (PID: 9264)
- calc.exe (PID: 8788)
- OUTLOOK.EXE (PID: 9944)
- opera.exe (PID: 8900)
- iexplore.exe (PID: 9916)
- chrome.exe (PID: 9172)
- control.exe (PID: 8468)
- chrome.exe (PID: 3864)
- opera.exe (PID: 9288)
- iexplore.exe (PID: 9392)
- iexplore.exe (PID: 10000)
- SndVol.exe (PID: 9628)
- iexplore.exe (PID: 9972)
- calc.exe (PID: 8804)
- iexplore.exe (PID: 8400)
- chrome.exe (PID: 8308)
- opera.exe (PID: 9760)
- chrome.exe (PID: 9044)
- chrome.exe (PID: 8756)
- explorer.exe (PID: 8420)
- chrome.exe (PID: 3972)
- rundll32.exe (PID: 4380)
- explorer.exe (PID: 9584)
- calc.exe (PID: 8748)
- iexplore.exe (PID: 3668)
- iexplore.exe (PID: 10116)
- rundll32.exe (PID: 10164)
- control.exe (PID: 8532)
- rundll32.exe (PID: 8308)
- chrome.exe (PID: 8716)
- chrome.exe (PID: 7024)
- calc.exe (PID: 8300)
- control.exe (PID: 4520)
- OUTLOOK.EXE (PID: 9788)
- calc.exe (PID: 3468)
- rundll32.exe (PID: 8236)
- opera.exe (PID: 3276)
- SndVol.exe (PID: 6436)
- useraccountcontrolsettings.exe (PID: 836)
- chrome.exe (PID: 8212)
- calc.exe (PID: 9140)
- DllHost.exe (PID: 5552)
- SndVol.exe (PID: 9384)
- chrome.exe (PID: 8852)
- DllHost.exe (PID: 8576)
- iexplore.exe (PID: 2972)
- calc.exe (PID: 10072)
- iexplore.exe (PID: 9060)
- calc.exe (PID: 8728)
- iexplore.exe (PID: 7920)
- calc.exe (PID: 9060)
- calc.exe (PID: 8908)
- calc.exe (PID: 7052)
- iexplore.exe (PID: 7744)
- calc.exe (PID: 8396)
- iexplore.exe (PID: 7788)
- iexplore.exe (PID: 8304)
- iexplore.exe (PID: 8344)
- calc.exe (PID: 10172)
- iexplore.exe (PID: 12084)
- calc.exe (PID: 11976)
- calc.exe (PID: 10916)
- opera.exe (PID: 12048)
- calc.exe (PID: 11088)
- calc.exe (PID: 11408)
- calc.exe (PID: 11484)
- iexplore.exe (PID: 11460)
- calc.exe (PID: 9288)
- calc.exe (PID: 11564)
- helppane.exe (PID: 8376)
- iexplore.exe (PID: 11504)
- iexplore.exe (PID: 10988)
- calc.exe (PID: 10316)
- IEEtwCollector.exe (PID: 7160)
Reads the computer name
- iexplore.exe (PID: 772)
- iexplore.exe (PID: 3044)
- iexplore.exe (PID: 116)
- iexplore.exe (PID: 3584)
- chrome.exe (PID: 3592)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 3268)
- iexplore.exe (PID: 4480)
- iexplore.exe (PID: 4736)
- chrome.exe (PID: 4848)
- iexplore.exe (PID: 5452)
- iexplore.exe (PID: 5752)
- iexplore.exe (PID: 4676)
- iexplore.exe (PID: 5856)
- iexplore.exe (PID: 4284)
- iexplore.exe (PID: 4168)
- explorer.exe (PID: 5284)
- opera.exe (PID: 6068)
- iexplore.exe (PID: 5368)
- chrome.exe (PID: 5512)
- SndVol.exe (PID: 4460)
- iexplore.exe (PID: 5284)
- chrome.exe (PID: 3776)
- rundll32.exe (PID: 5260)
- iexplore.exe (PID: 2220)
- control.exe (PID: 2024)
- iexplore.exe (PID: 6760)
- iexplore.exe (PID: 7656)
- iexplore.exe (PID: 7880)
- control.exe (PID: 7180)
- control.exe (PID: 7808)
- iexplore.exe (PID: 8148)
- chrome.exe (PID: 6464)
- SndVol.exe (PID: 2912)
- explorer.exe (PID: 7324)
- iexplore.exe (PID: 4452)
- iexplore.exe (PID: 7616)
- chrome.exe (PID: 7928)
- iexplore.exe (PID: 6936)
- opera.exe (PID: 6940)
- explorer.exe (PID: 2732)
- SndVol.exe (PID: 6544)
- iexplore.exe (PID: 6244)
- chrome.exe (PID: 4312)
- control.exe (PID: 7636)
- explorer.exe (PID: 6352)
- iexplore.exe (PID: 7664)
- explorer.exe (PID: 4292)
- explorer.exe (PID: 6568)
- iexplore.exe (PID: 7944)
- iexplore.exe (PID: 4592)
- iexplore.exe (PID: 9444)
- control.exe (PID: 9264)
- opera.exe (PID: 8900)
- iexplore.exe (PID: 9916)
- chrome.exe (PID: 3864)
- control.exe (PID: 8468)
- opera.exe (PID: 9288)
- iexplore.exe (PID: 9392)
- iexplore.exe (PID: 10000)
- SndVol.exe (PID: 9628)
- iexplore.exe (PID: 9972)
- iexplore.exe (PID: 8400)
- explorer.exe (PID: 8420)
- opera.exe (PID: 9760)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 8308)
- explorer.exe (PID: 9584)
- iexplore.exe (PID: 3668)
- iexplore.exe (PID: 10116)
- control.exe (PID: 8532)
- control.exe (PID: 4520)
- chrome.exe (PID: 8716)
- opera.exe (PID: 3276)
- SndVol.exe (PID: 6436)
- useraccountcontrolsettings.exe (PID: 836)
- chrome.exe (PID: 8212)
- DllHost.exe (PID: 5552)
- SndVol.exe (PID: 9384)
- DllHost.exe (PID: 8576)
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 9060)
- iexplore.exe (PID: 7920)
- iexplore.exe (PID: 7788)
- iexplore.exe (PID: 7744)
- iexplore.exe (PID: 8344)
- iexplore.exe (PID: 8304)
- iexplore.exe (PID: 12084)
- opera.exe (PID: 12048)
- iexplore.exe (PID: 11460)
- helppane.exe (PID: 8376)
- iexplore.exe (PID: 10988)
- iexplore.exe (PID: 11504)
- IEEtwCollector.exe (PID: 7160)
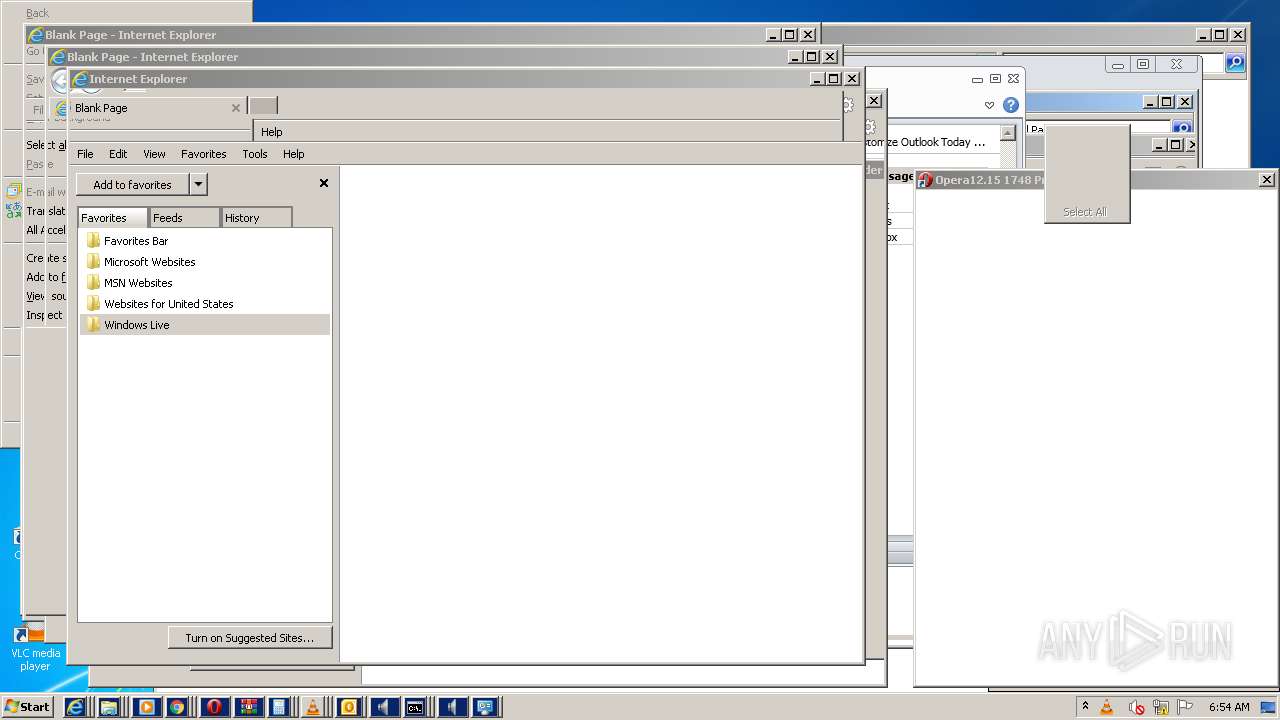
Changes internet zones settings
- iexplore.exe (PID: 772)
- iexplore.exe (PID: 5856)
- iexplore.exe (PID: 4168)
- iexplore.exe (PID: 5284)
- iexplore.exe (PID: 4452)
- iexplore.exe (PID: 4592)
- iexplore.exe (PID: 9444)
- iexplore.exe (PID: 9392)
- iexplore.exe (PID: 9972)
- iexplore.exe (PID: 3668)
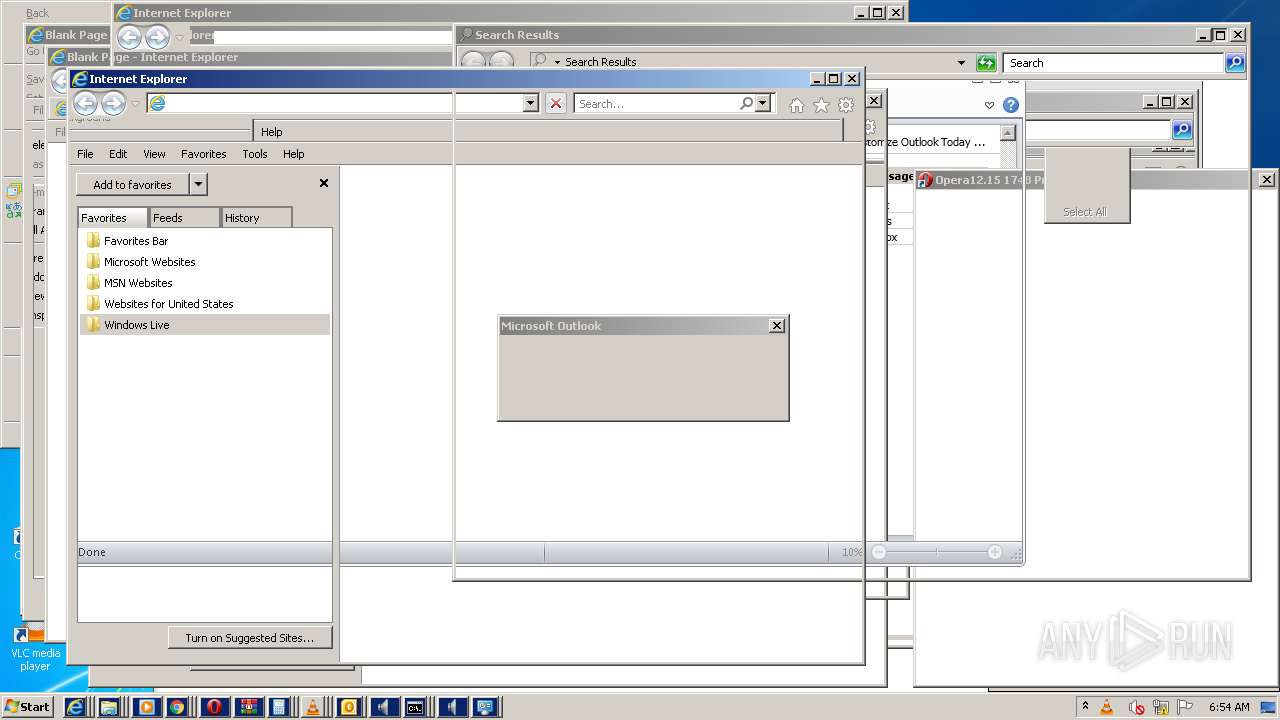
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3596)
- OUTLOOK.EXE (PID: 3020)
- OUTLOOK.EXE (PID: 2336)
- OUTLOOK.EXE (PID: 3384)
- OUTLOOK.EXE (PID: 1204)
- OUTLOOK.EXE (PID: 4352)
- OUTLOOK.EXE (PID: 5220)
- OUTLOOK.EXE (PID: 4224)
- OUTLOOK.EXE (PID: 5132)
- OUTLOOK.EXE (PID: 5356)
- OUTLOOK.EXE (PID: 4744)
- OUTLOOK.EXE (PID: 4176)
- OUTLOOK.EXE (PID: 5432)
- OUTLOOK.EXE (PID: 1568)
- OUTLOOK.EXE (PID: 3744)
- OUTLOOK.EXE (PID: 7288)
- OUTLOOK.EXE (PID: 7672)
- OUTLOOK.EXE (PID: 6984)
- OUTLOOK.EXE (PID: 6164)
- OUTLOOK.EXE (PID: 9944)
- OUTLOOK.EXE (PID: 9788)
- OUTLOOK.EXE (PID: 9356)
- OUTLOOK.EXE (PID: 2784)
- OUTLOOK.EXE (PID: 3808)
- OUTLOOK.EXE (PID: 2112)
- OUTLOOK.EXE (PID: 10612)
- OUTLOOK.EXE (PID: 11128)
- OUTLOOK.EXE (PID: 11236)
- OUTLOOK.EXE (PID: 11252)
- OUTLOOK.EXE (PID: 11892)
- OUTLOOK.EXE (PID: 11248)
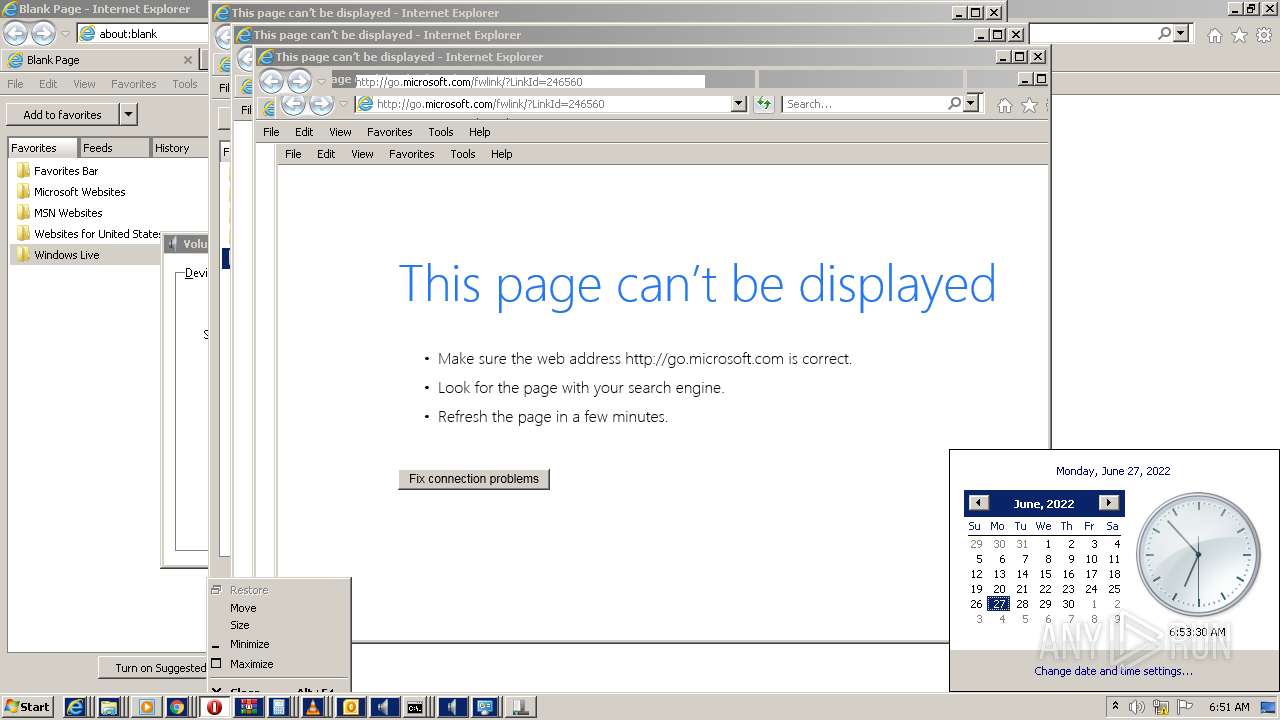
Application launched itself
- iexplore.exe (PID: 772)
- chrome.exe (PID: 3592)
- iexplore.exe (PID: 5856)
- iexplore.exe (PID: 4168)
- chrome.exe (PID: 5512)
- iexplore.exe (PID: 5284)
- iexplore.exe (PID: 4452)
- chrome.exe (PID: 4312)
- iexplore.exe (PID: 4592)
- iexplore.exe (PID: 9444)
- chrome.exe (PID: 3864)
- iexplore.exe (PID: 9392)
- iexplore.exe (PID: 9972)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 8308)
- iexplore.exe (PID: 3668)
- chrome.exe (PID: 8716)
- chrome.exe (PID: 8212)
Reads the hosts file
- chrome.exe (PID: 3592)
- chrome.exe (PID: 3268)
Reads internet explorer settings
- iexplore.exe (PID: 3584)
- iexplore.exe (PID: 3044)
- iexplore.exe (PID: 4736)
- iexplore.exe (PID: 5752)
- iexplore.exe (PID: 6760)
- iexplore.exe (PID: 8148)
- iexplore.exe (PID: 6936)
- iexplore.exe (PID: 6244)
- iexplore.exe (PID: 7664)
- iexplore.exe (PID: 10988)
Check for Java to be installed
- opera.exe (PID: 6068)
Reads the date of Windows installation
- opera.exe (PID: 6068)
- chrome.exe (PID: 7928)
- iexplore.exe (PID: 772)
Creates files in the user directory
- opera.exe (PID: 6068)
- iexplore.exe (PID: 772)
Reads CPU info
- IEEtwCollector.exe (PID: 7160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | fucker script.exe |
|---|---|
| ZipUncompressedSize: | 107168 |
| ZipCompressedSize: | 34474 |
| ZipCRC: | 0xe6a17274 |
| ZipModifyDate: | 2021:11:01 16:51:27 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
436
Monitored processes
271
Malicious processes
2
Suspicious processes
3
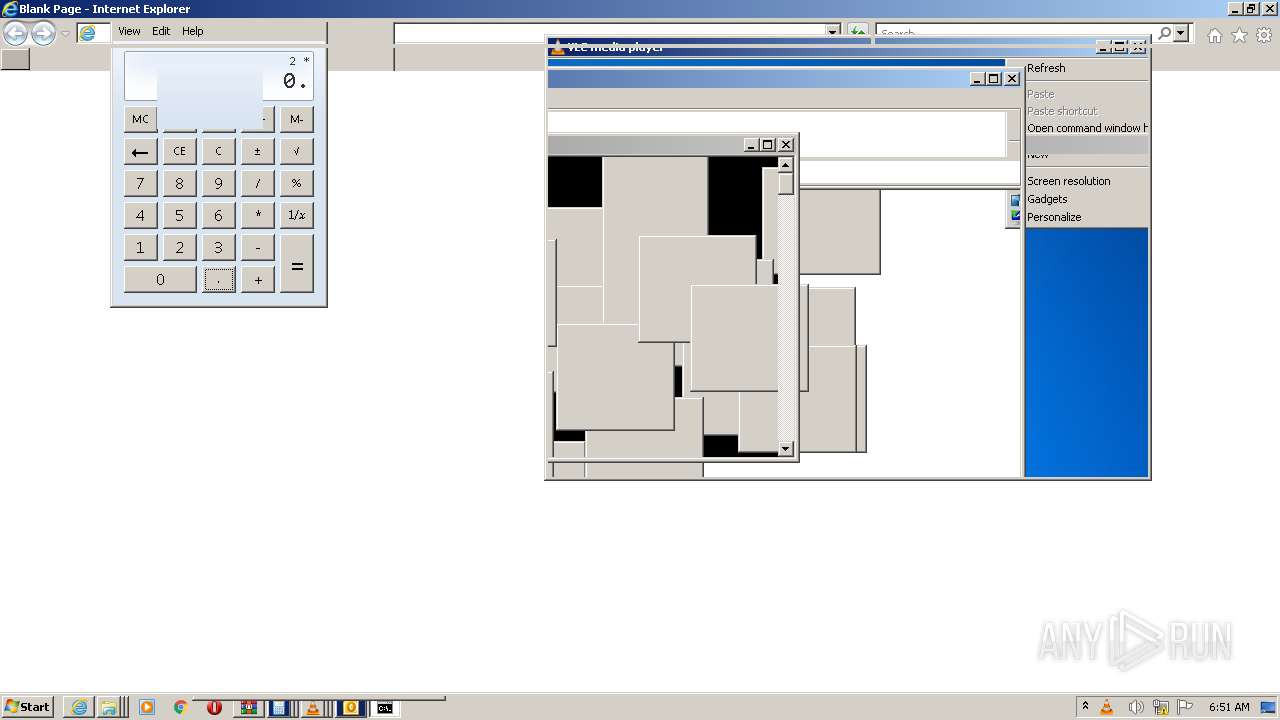
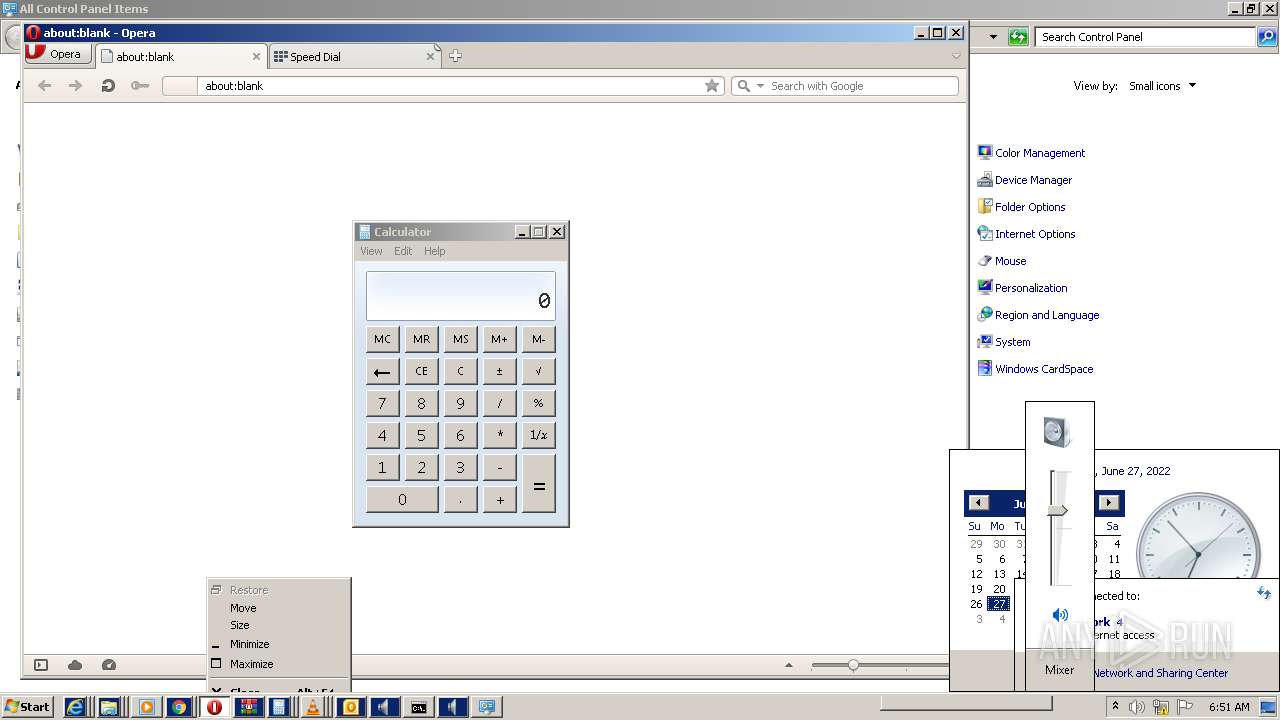
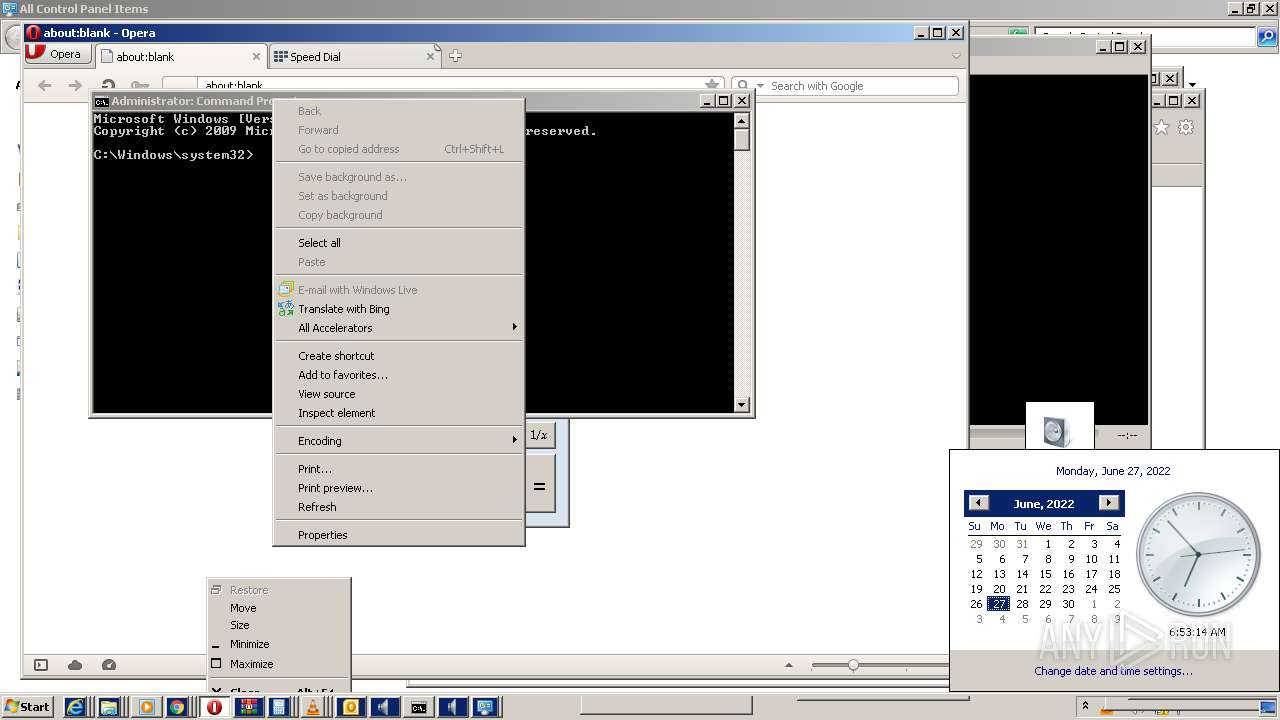
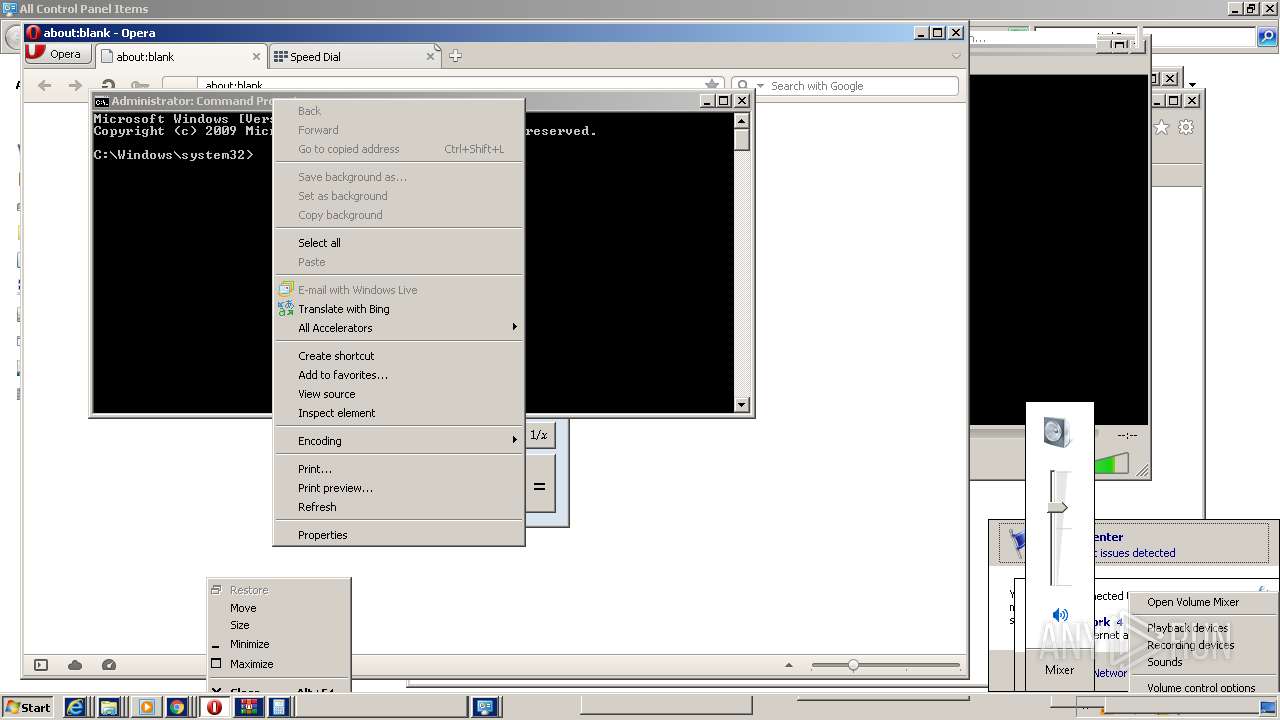
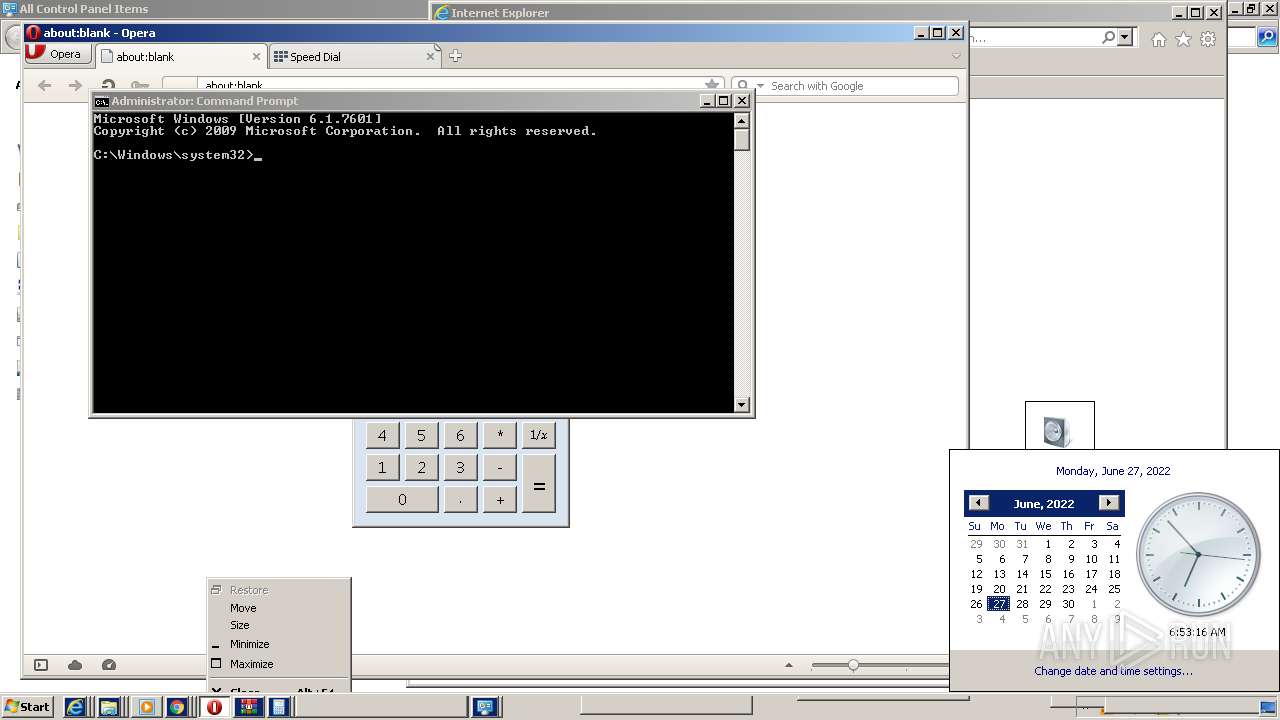
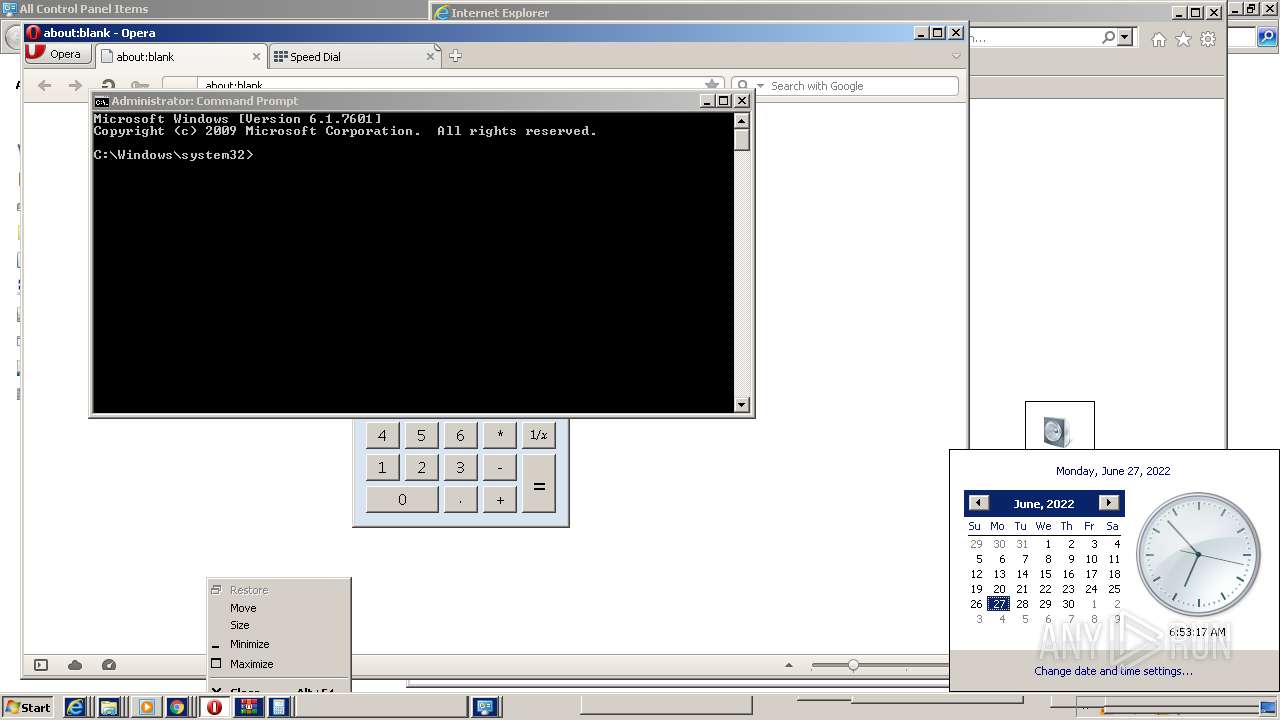
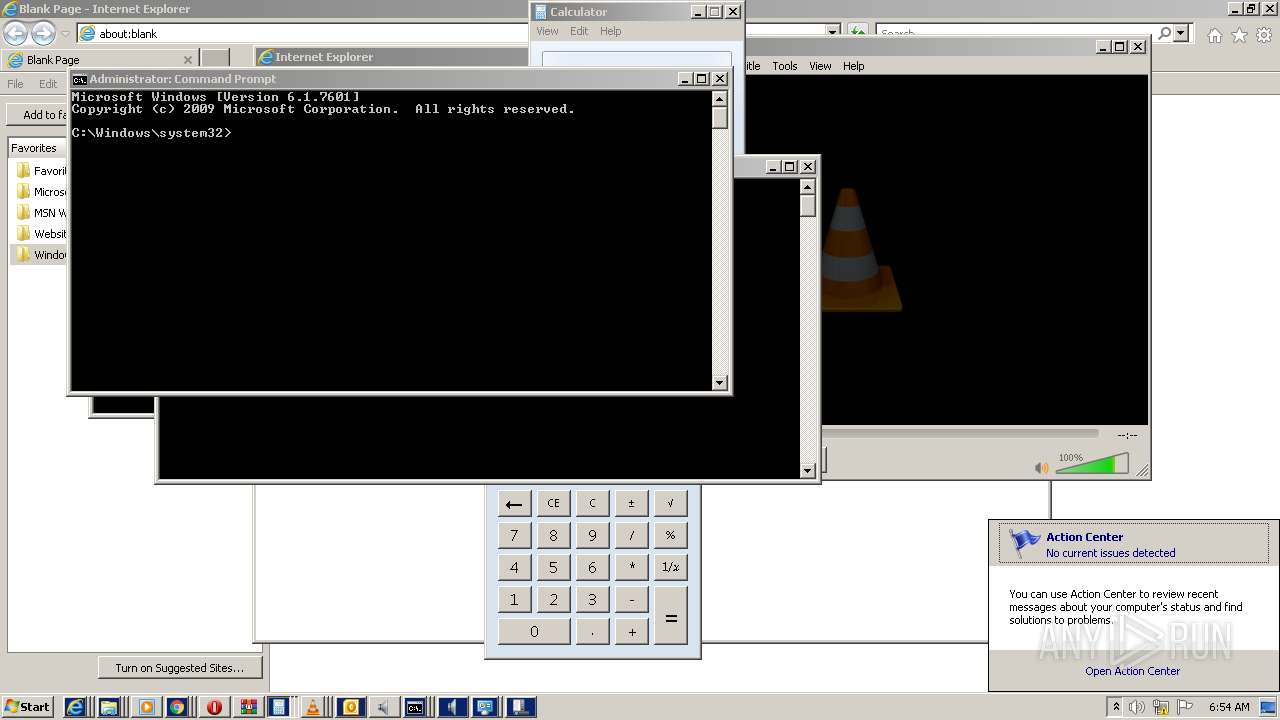
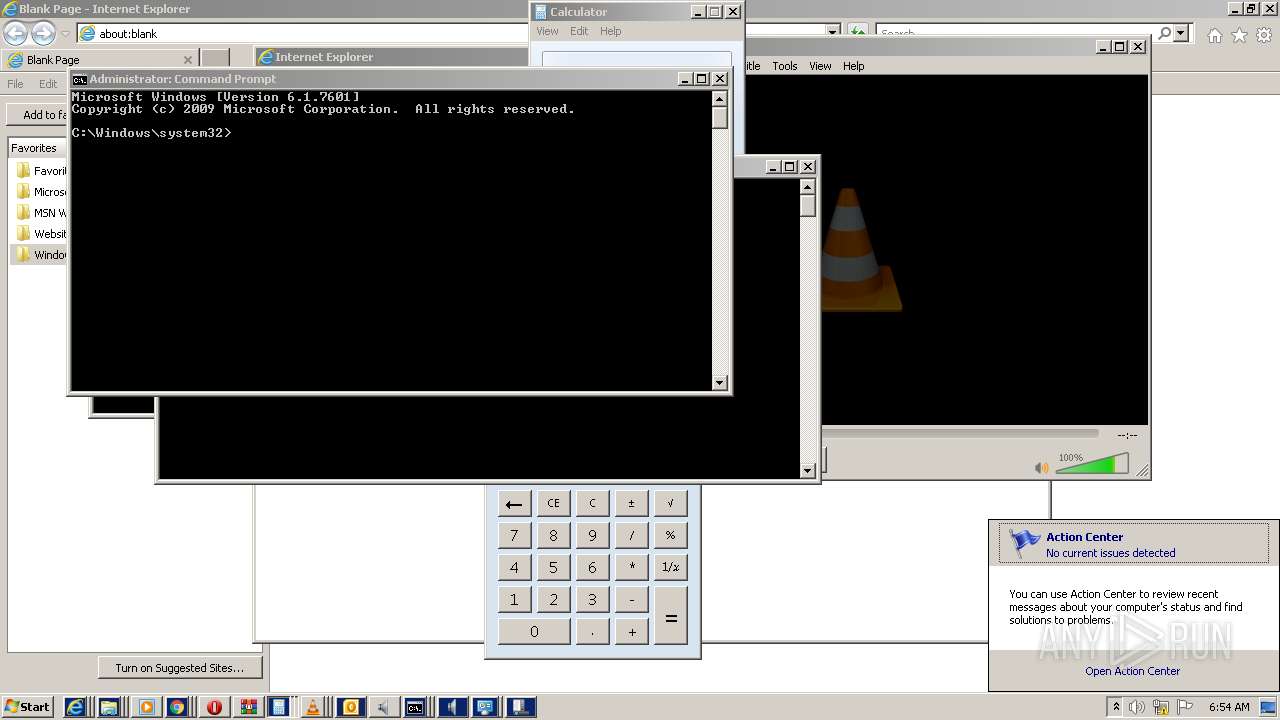
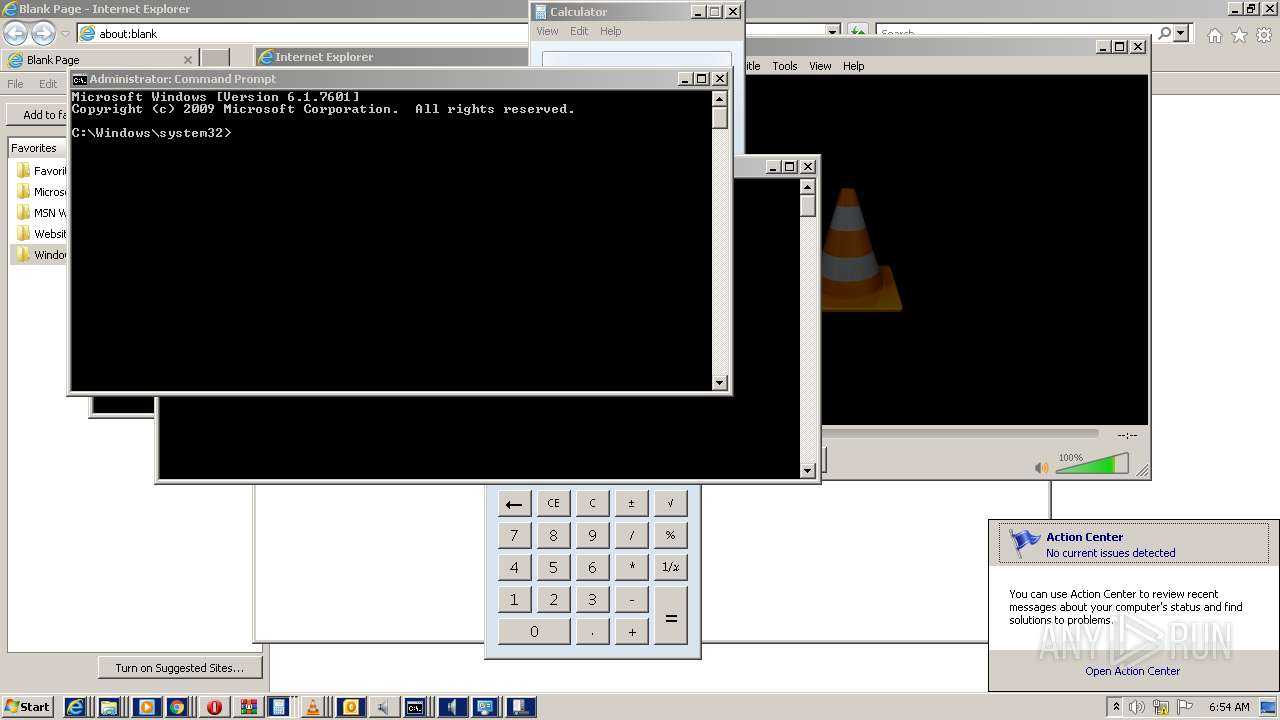
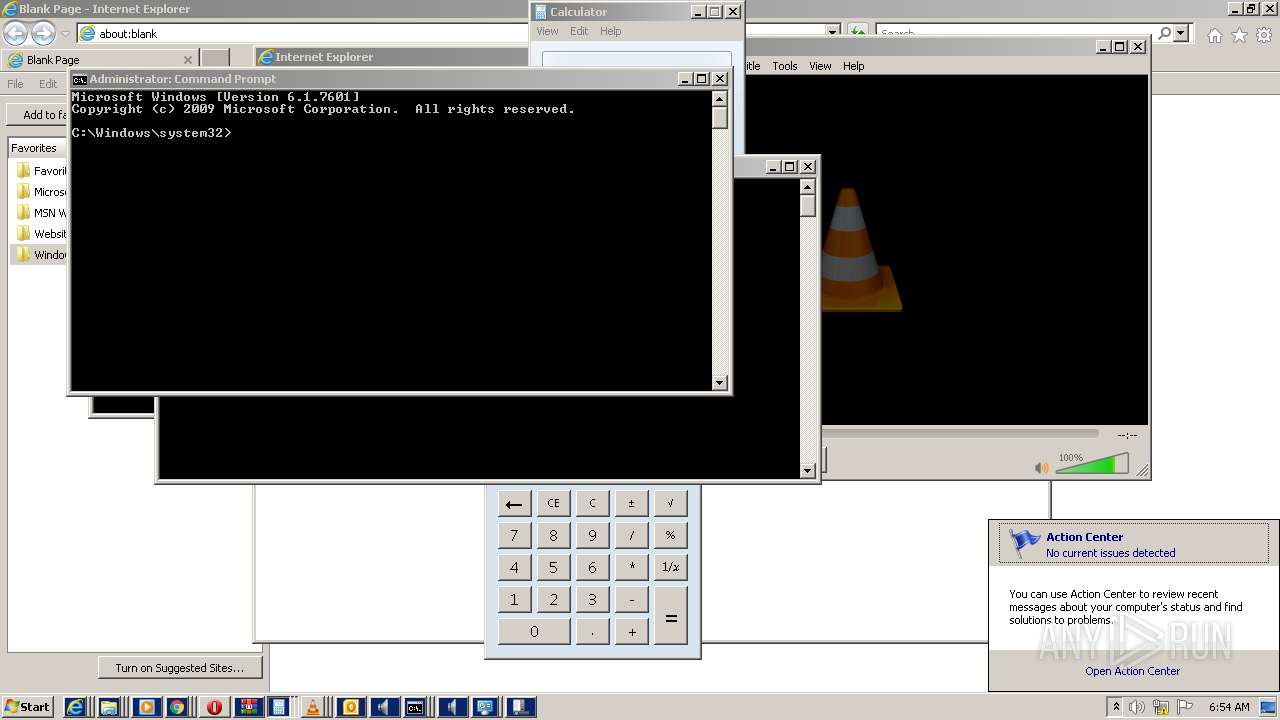
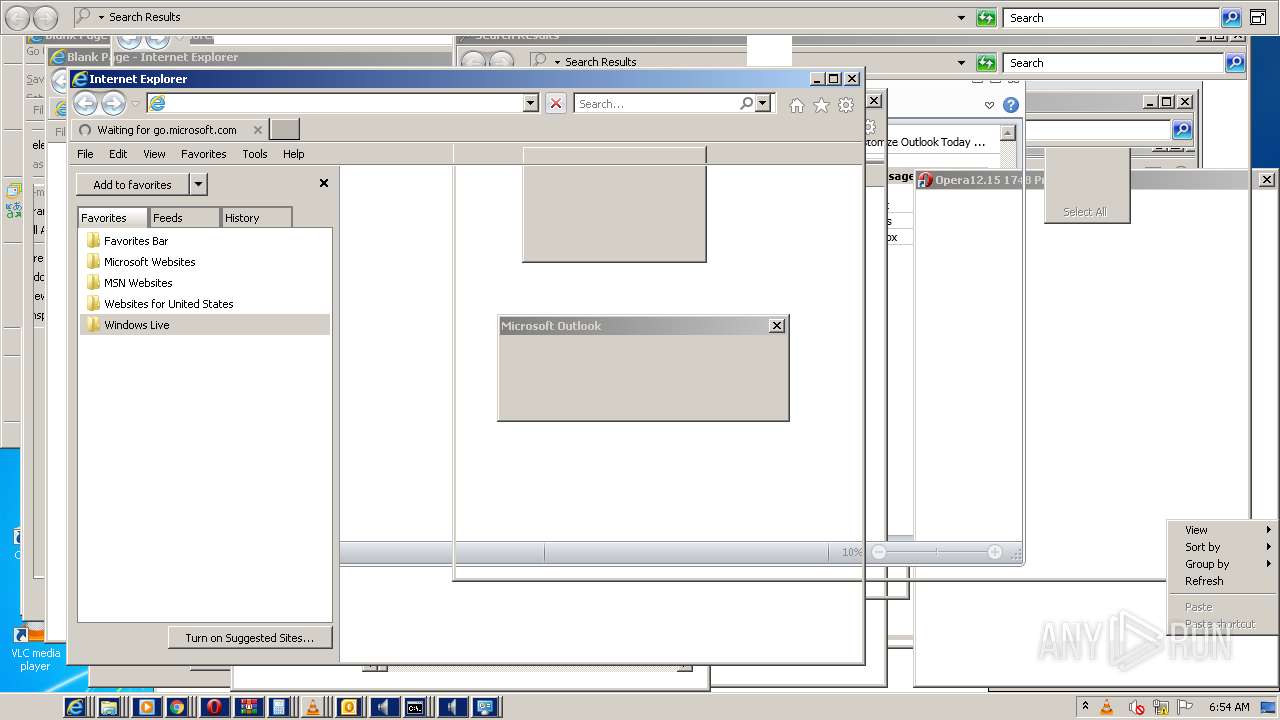
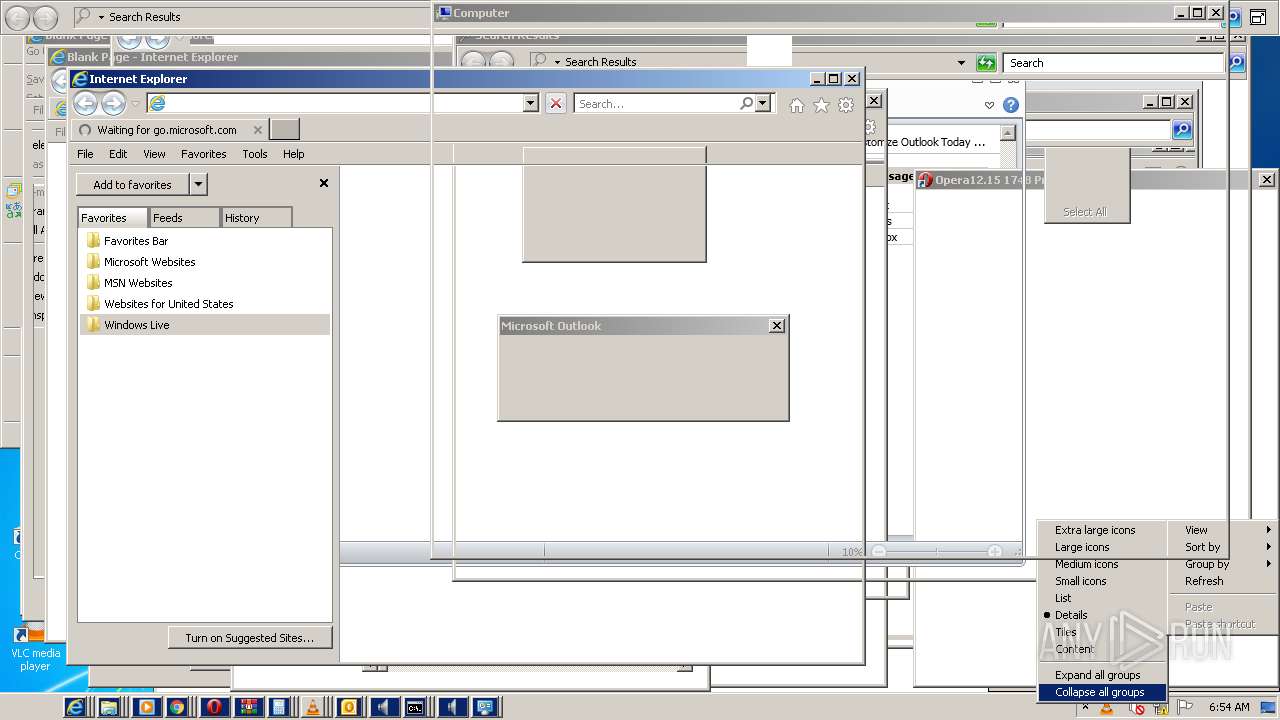
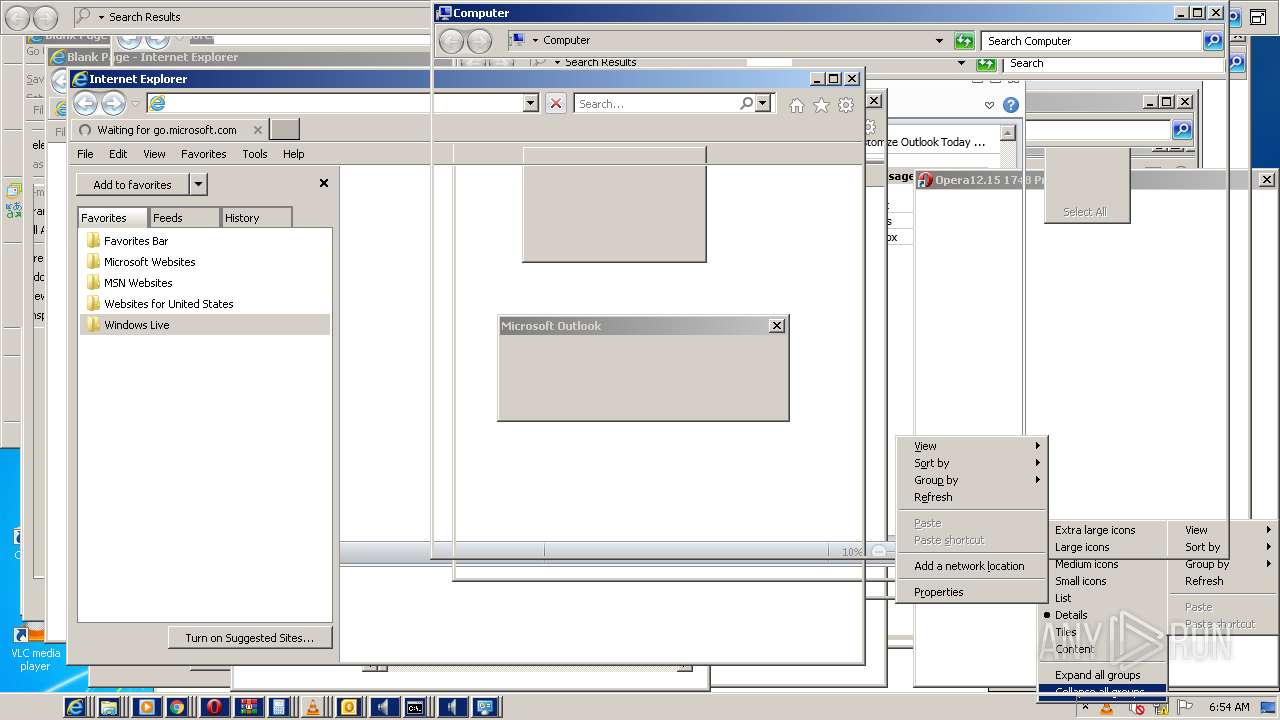
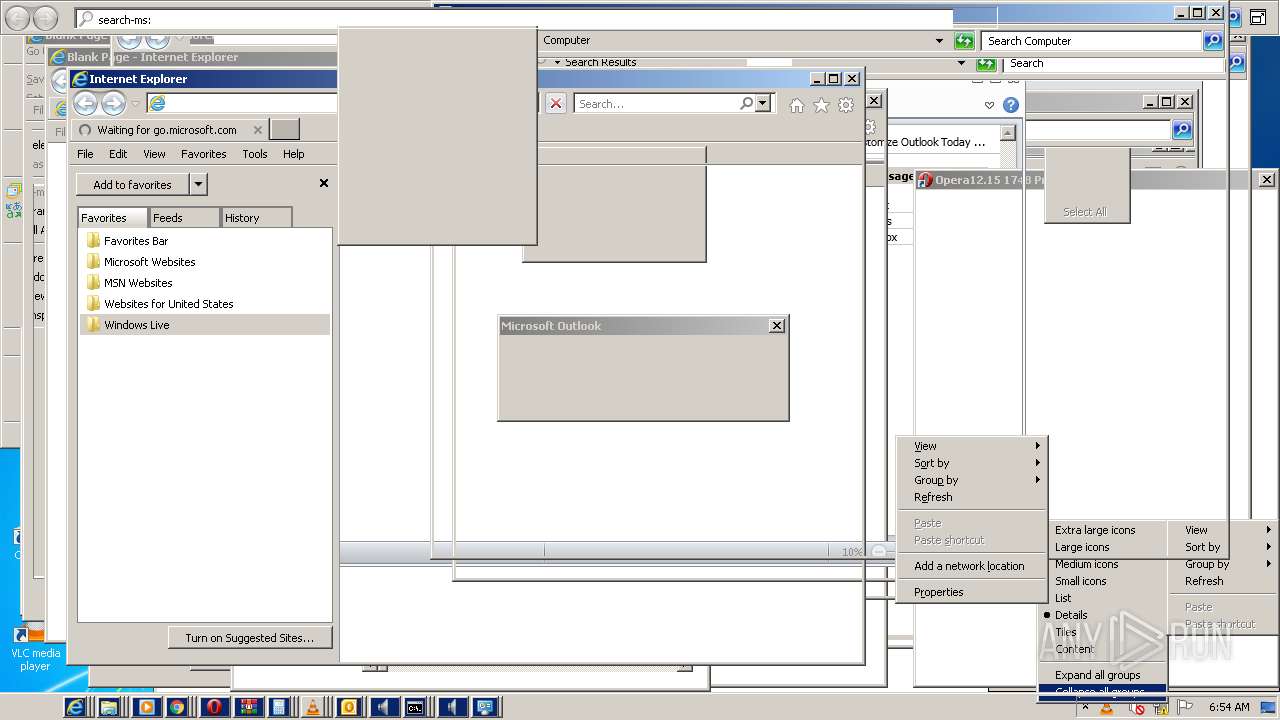
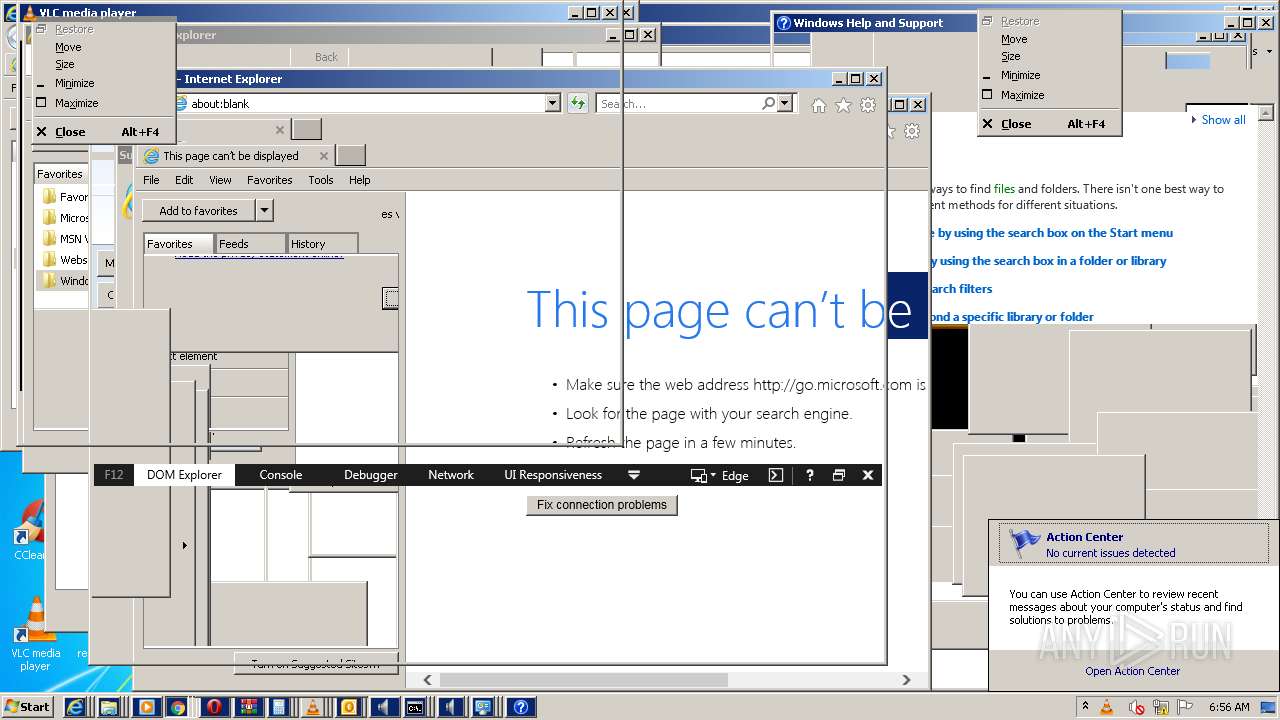
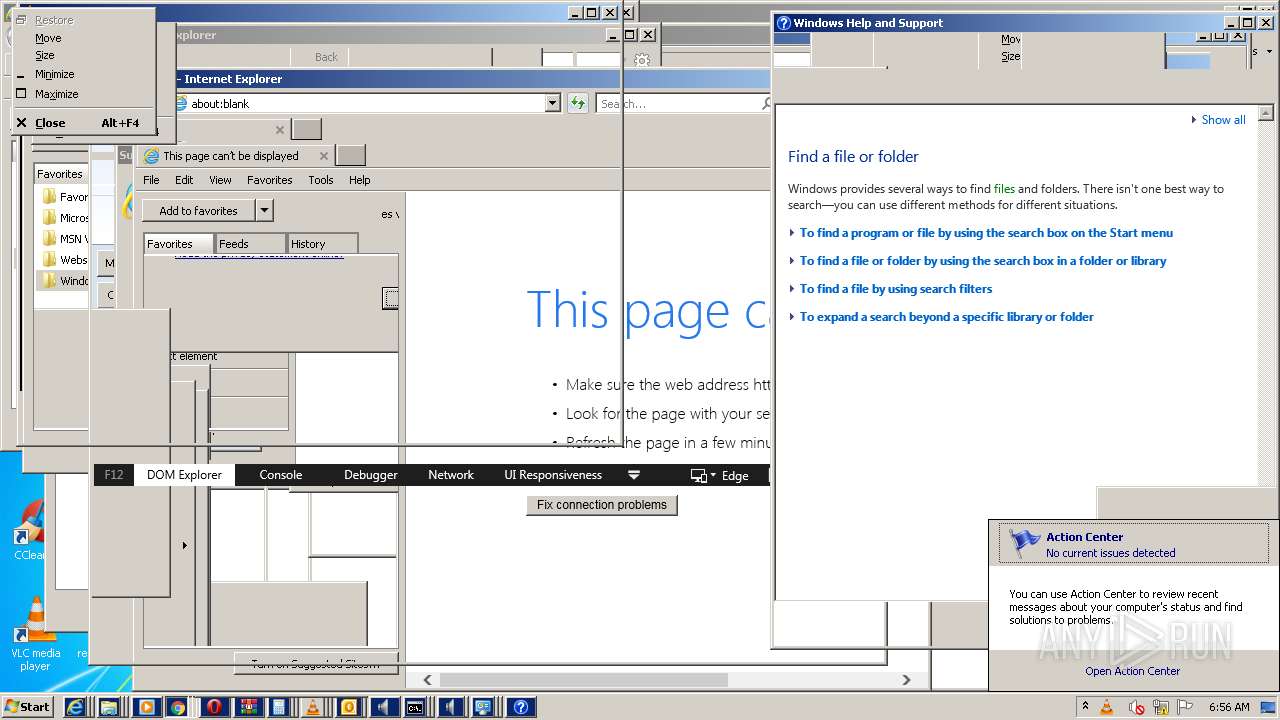
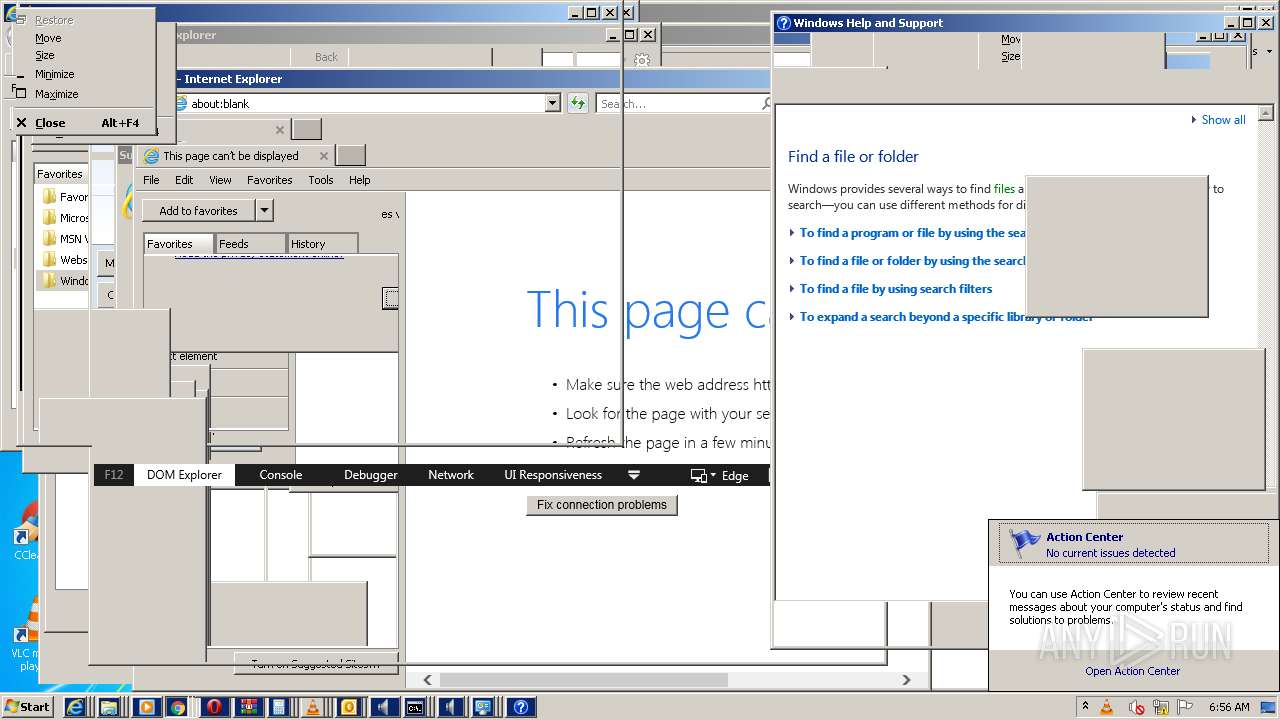
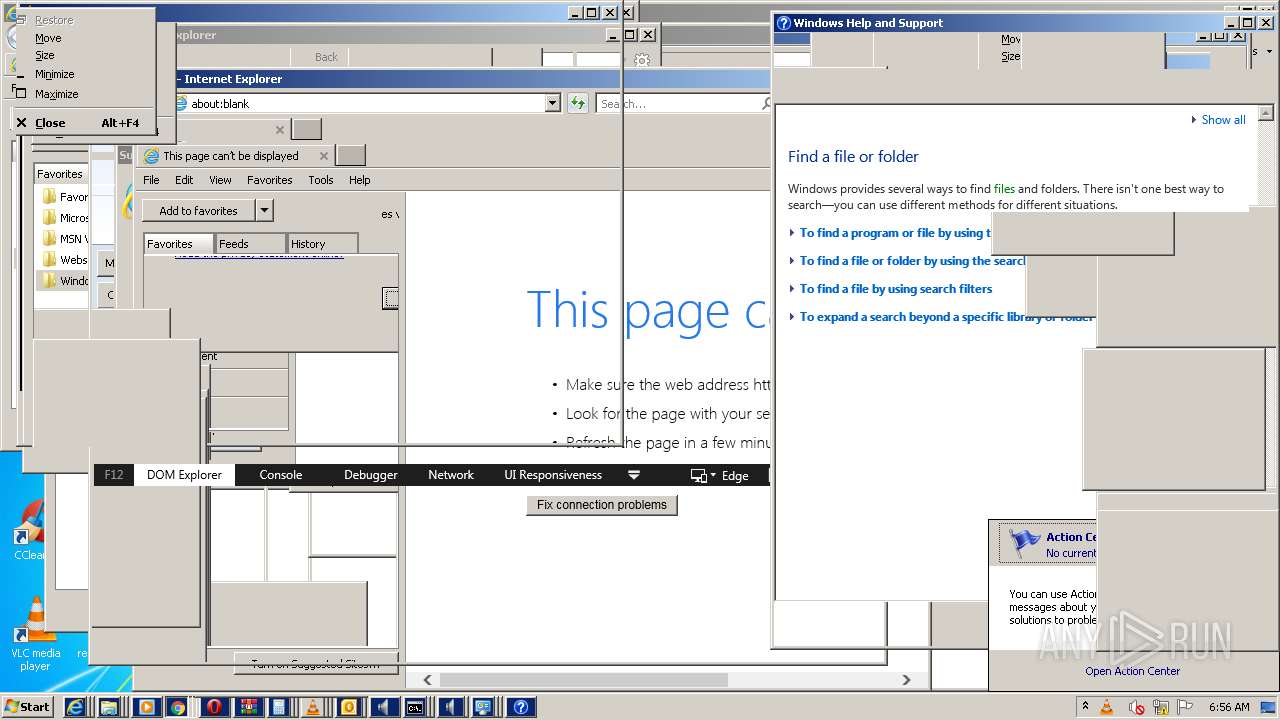
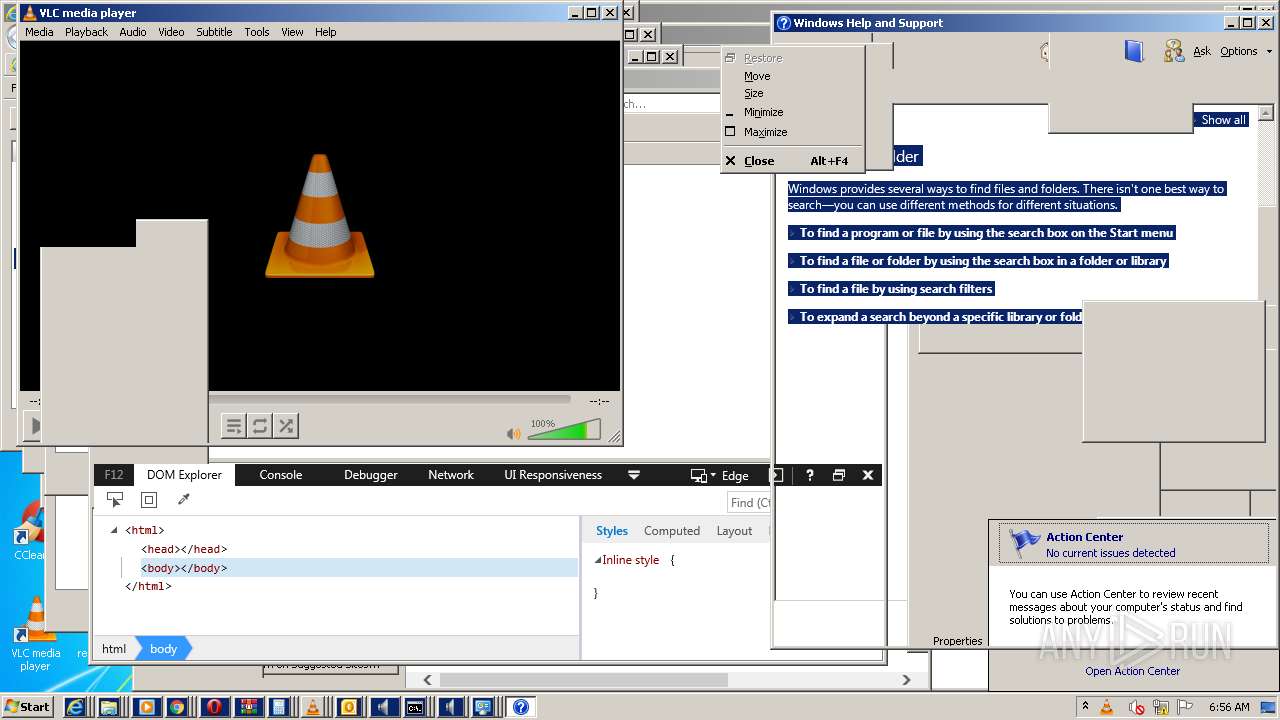
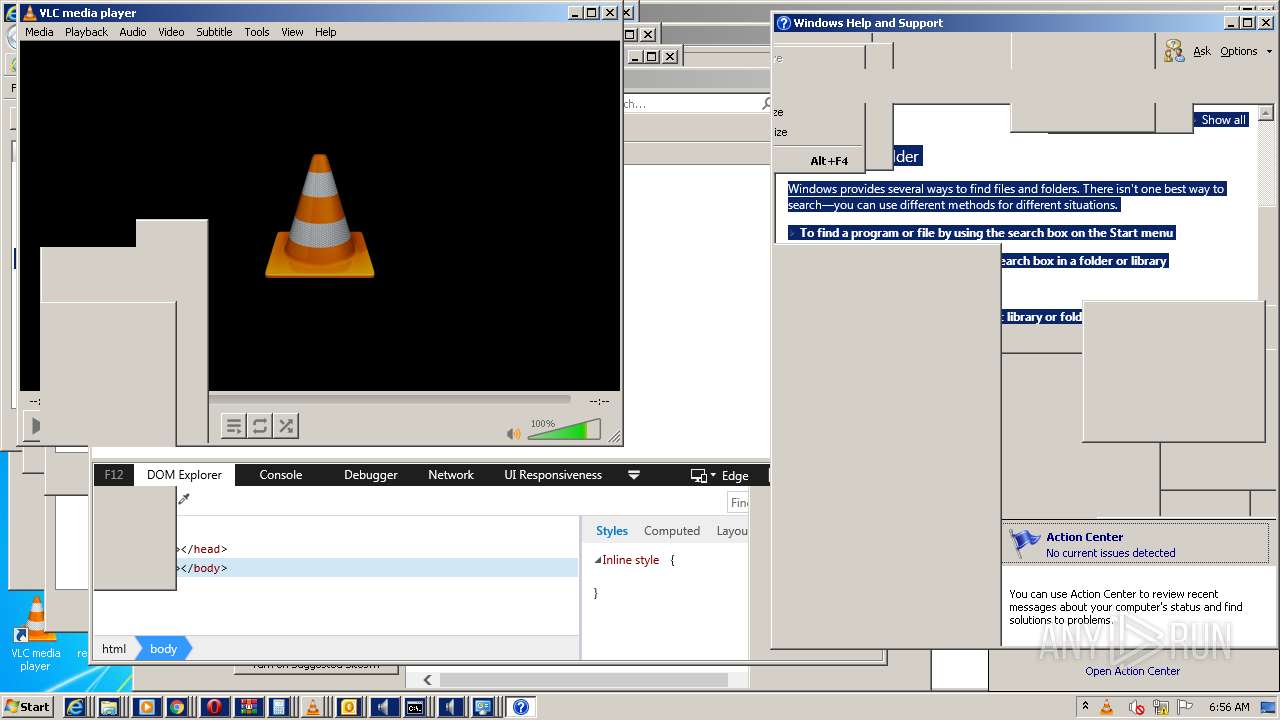
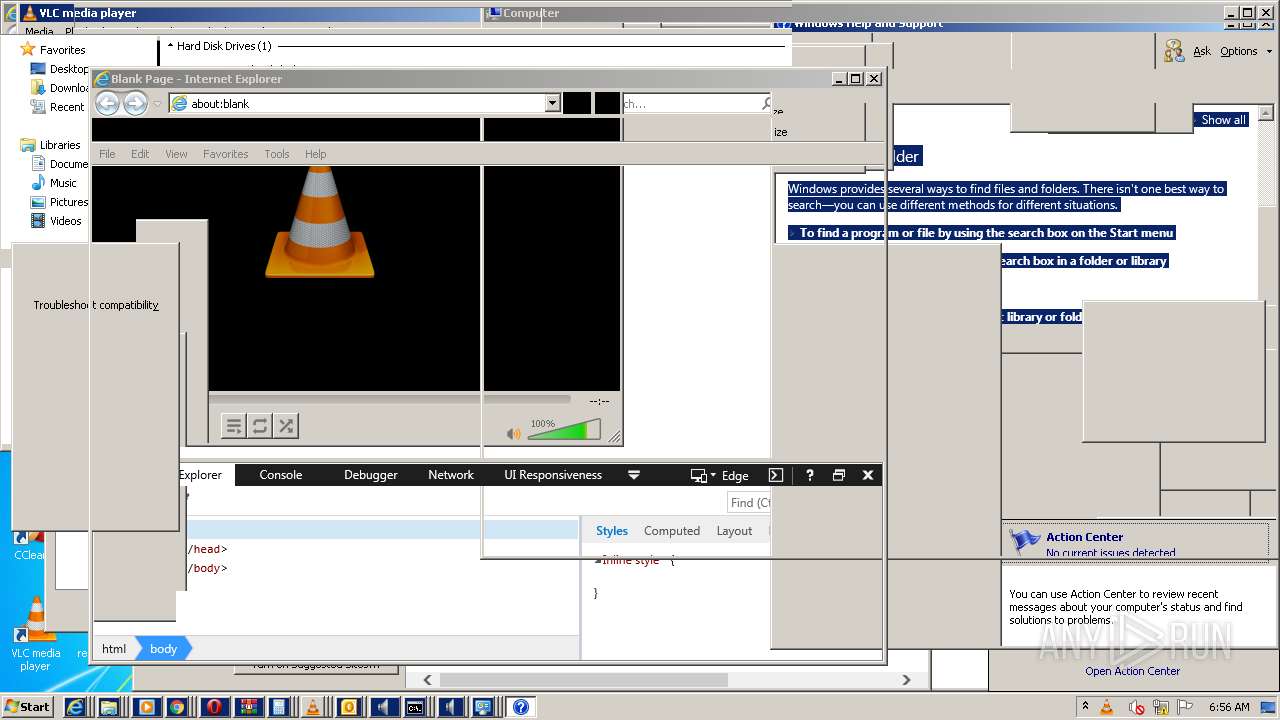
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 772 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 836 | "C:\Windows\system32\useraccountcontrolsettings.exe" | C:\Windows\system32\useraccountcontrolsettings.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: UserAccountControlSettings Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
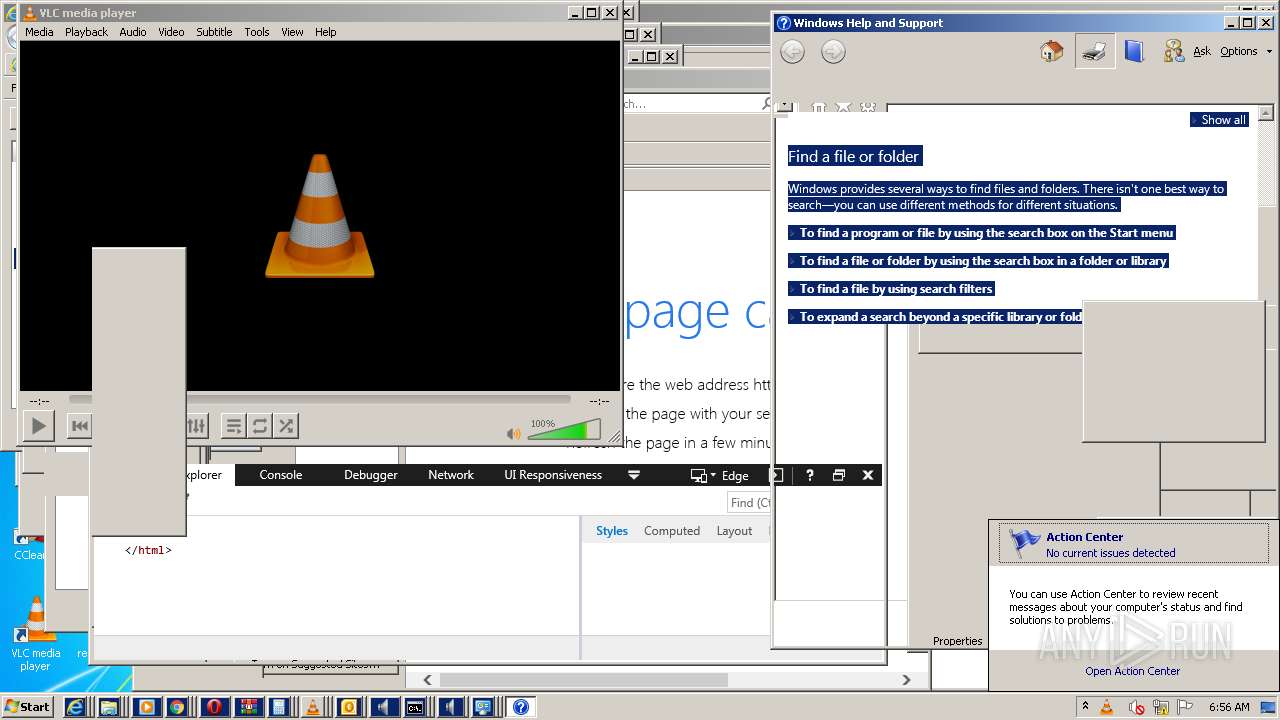
| 928 | "C:\Program Files\VideoLAN\VLC\vlc.exe" | C:\Program Files\VideoLAN\VLC\vlc.exe | Explorer.EXE | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 3.0.11 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,5262874613636659459,12207390634306132522,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1940 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Windows Media Player\setup_wm.exe" /RunOnce:"C:\Program Files\Windows Media Player\wmplayer.exe" /prefetch:1 | C:\Program Files\Windows Media Player\setup_wm.exe | — | wmplayer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Windows Media Configuration Utility Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 956 | "C:\Program Files\VideoLAN\VLC\vlc.exe" | C:\Program Files\VideoLAN\VLC\vlc.exe | Explorer.EXE | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 3.0.11 Modules
| |||||||||||||||
| 1188 | "C:\Program Files\VideoLAN\VLC\vlc.exe" | C:\Program Files\VideoLAN\VLC\vlc.exe | Explorer.EXE | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 3.0.11 Modules
| |||||||||||||||
| 1204 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 1276 | "C:\Windows\system32\calc.exe" | C:\Windows\system32\calc.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Calculator Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
347 440
Read events
340 348
Write events
6 882
Delete events
210
Modification events
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\vbehxx.zip | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
1
Suspicious files
43
Text files
137
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2336 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRAF51.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2336 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 3596 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRC24D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3020 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRC24D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRD122.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1204 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRD5A6.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62B94584-E08.pma | — | |
MD5:— | SHA256:— | |||
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 2336 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2336 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\Microsoft Outlook.lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=i686-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=i686-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x86/contrib/i686-w64-mingw32/lib/pkgconfig'
|
vlc.exe | main libvlc debug: using multimedia timers as clock source
|
vlc.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc.exe | main libvlc debug: searching plug-in modules
|
vlc.exe | main libvlc debug: loading plugins cache file C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|
vlc.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
vlc.exe | main libvlc error: stale plugins cache: modified C:\Program Files\VideoLAN\VLC\plugins\access\libaccess_concat_plugin.dll
|