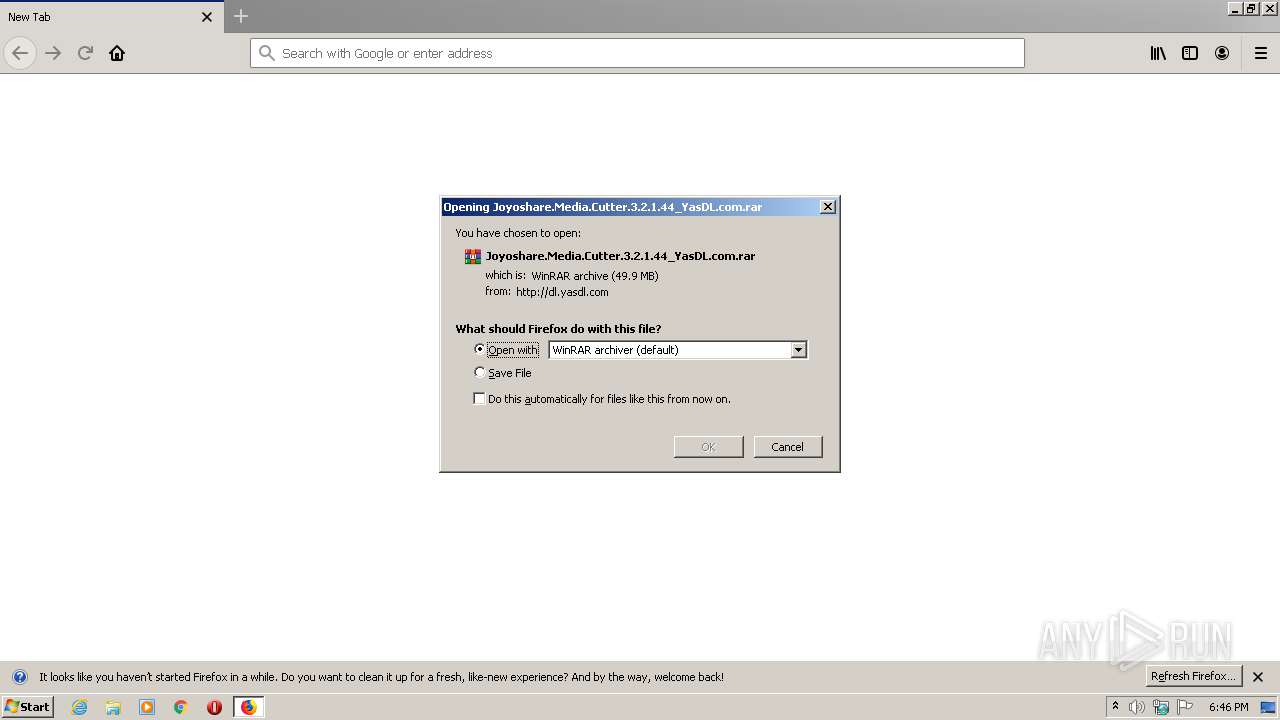
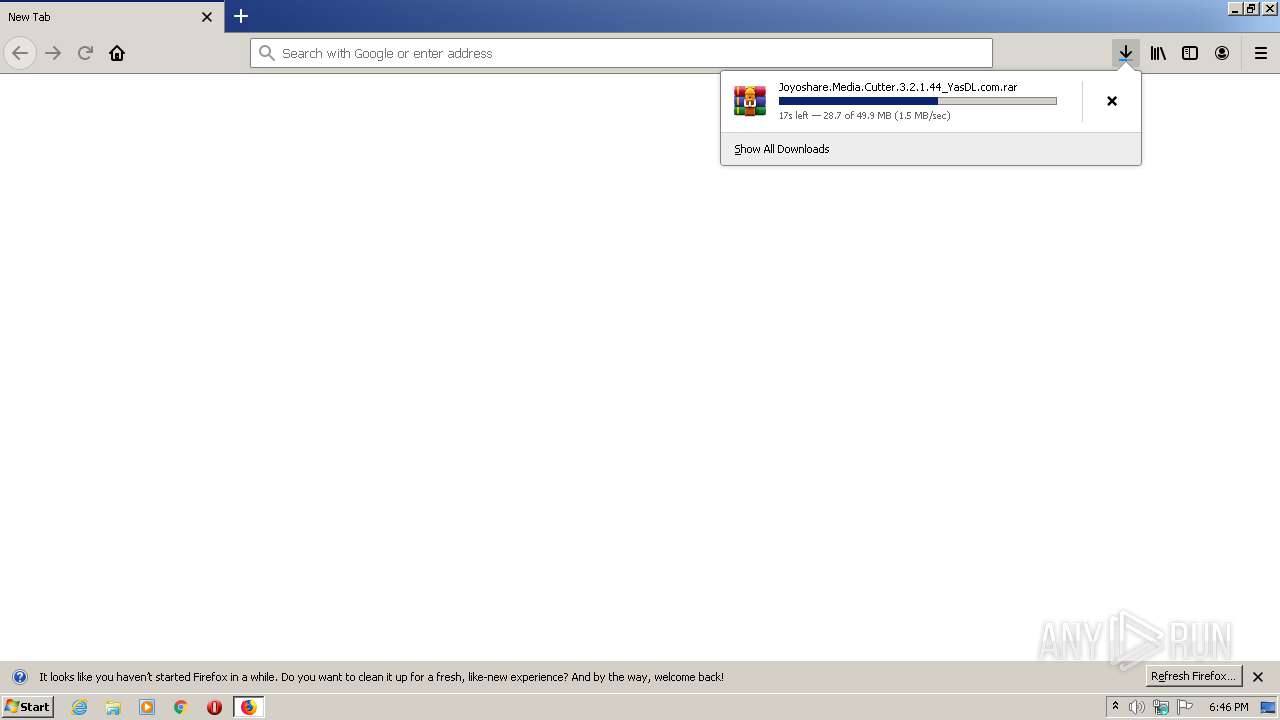
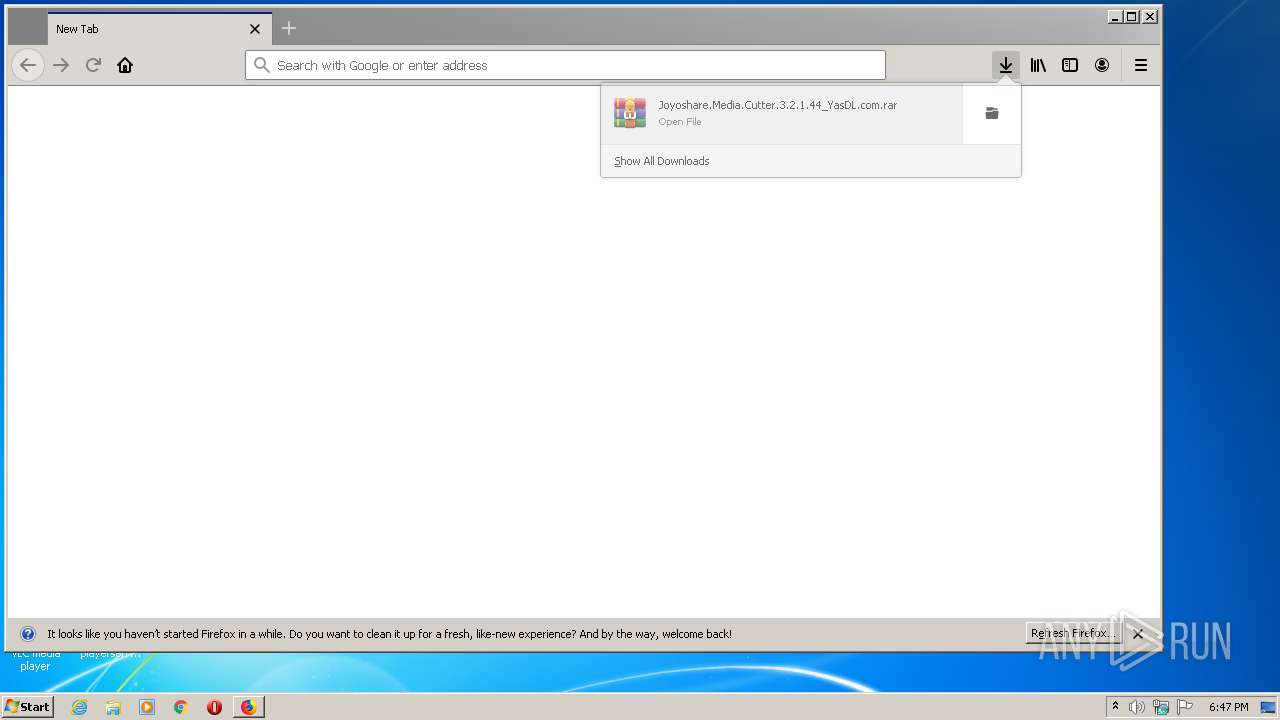
| URL: | http://dl.yasdl.com/2020/Software/Joyoshare.Media.Cutter.3.2.1.44_YasDL.com.rar?fgy |
| Full analysis: | https://app.any.run/tasks/0333f64d-edfb-4765-ba56-f64d8d91f201 |
| Verdict: | Malicious activity |
| Analysis date: | July 09, 2020, 17:46:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C659A746A9D0DB37BBC2226547CBAD77 |
| SHA1: | F1828F67E870F24CFF4E9FC149E27F6BD84D5F74 |
| SHA256: | 2E72E75D4C4D634E5437CB4C7619A63298E0442443124B0DEBB9A92560923F3F |
| SSDEEP: | 3:N1KaJcb3n4AIf/ckt3ULZMlec:CaJs3ntIckFULG8c |
MALICIOUS
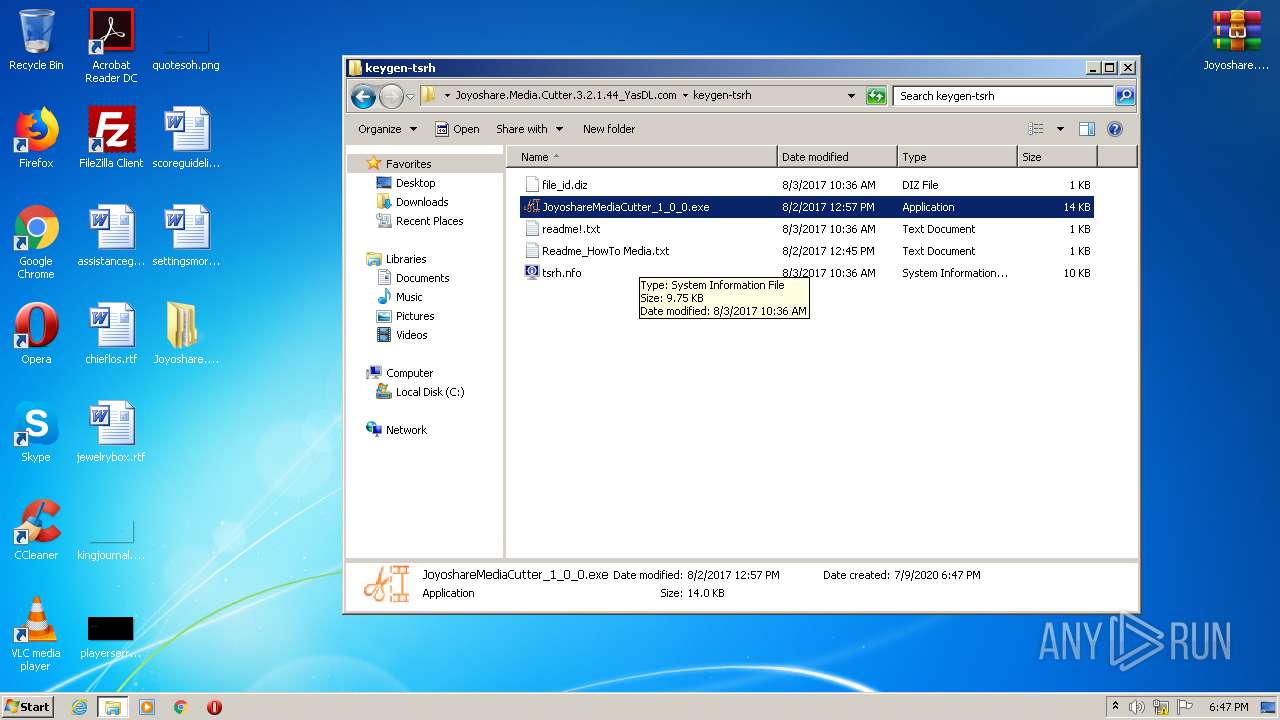
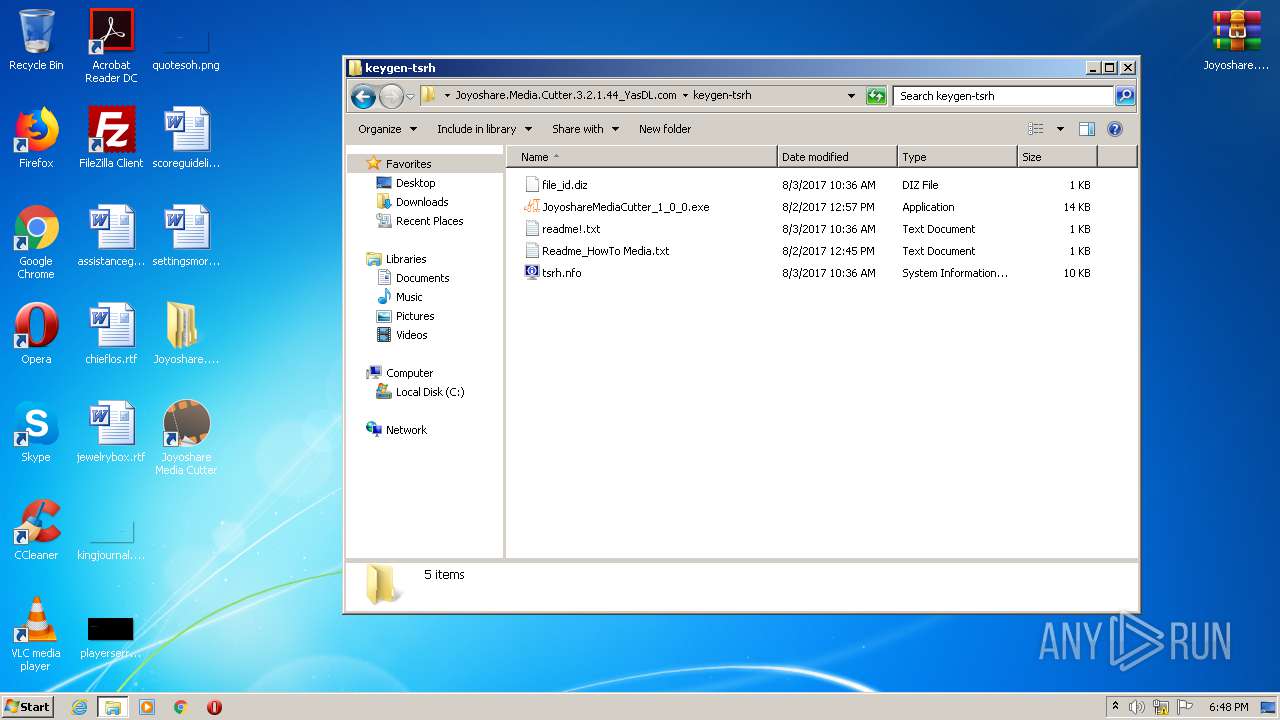
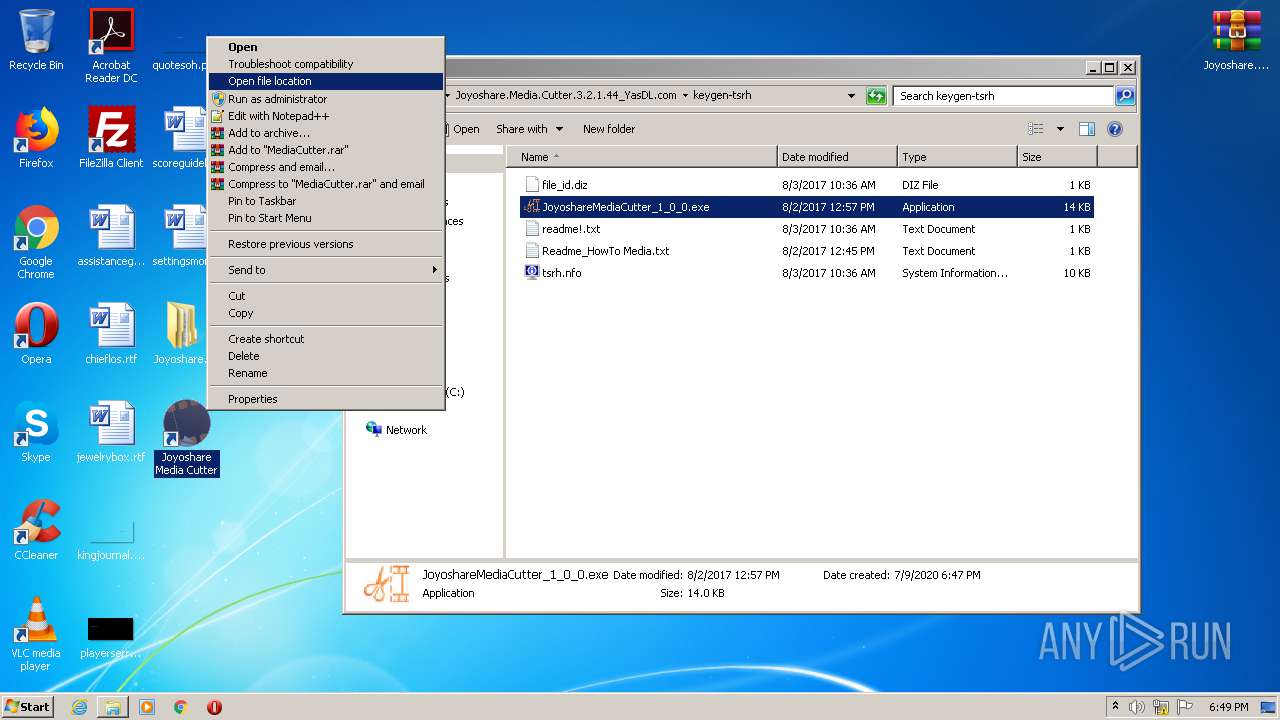
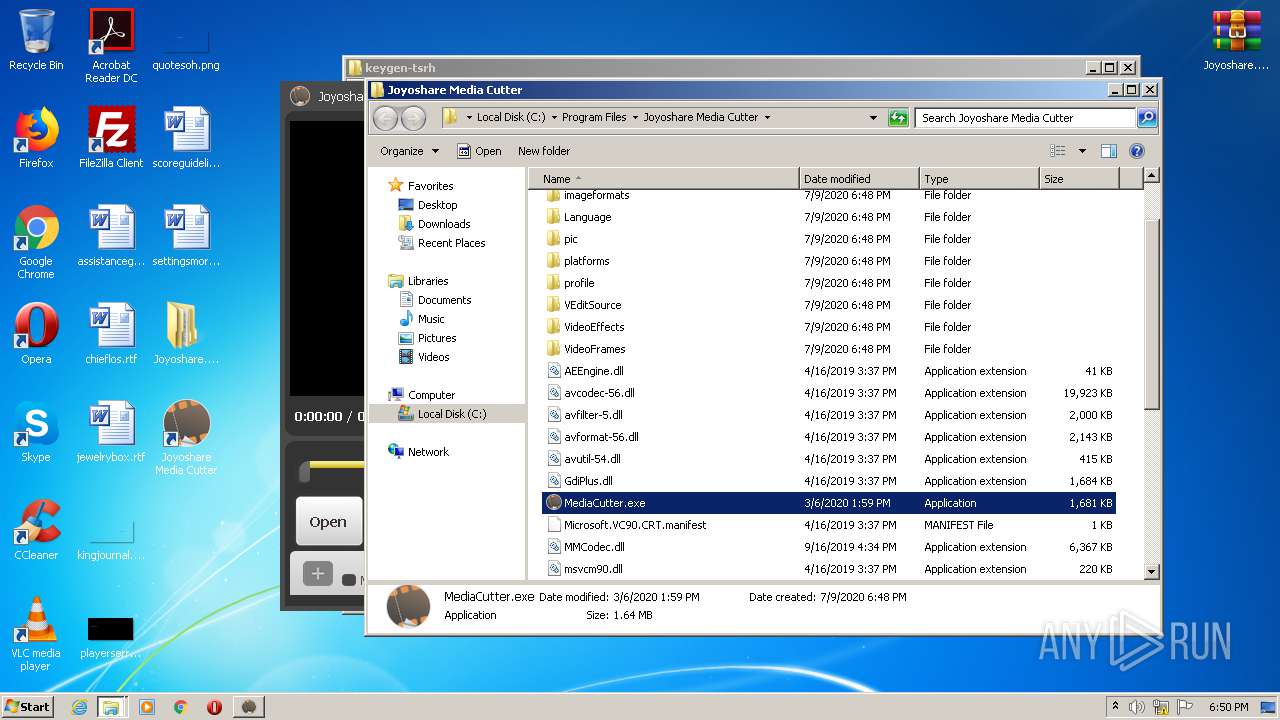
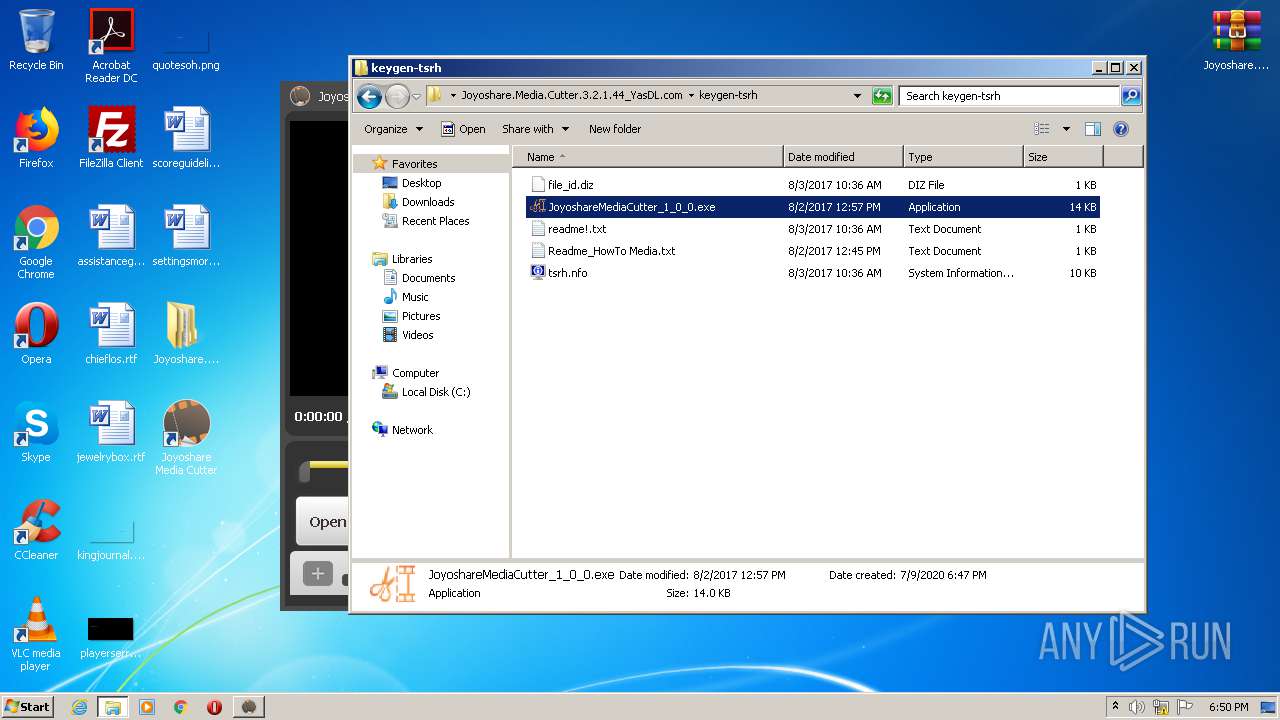
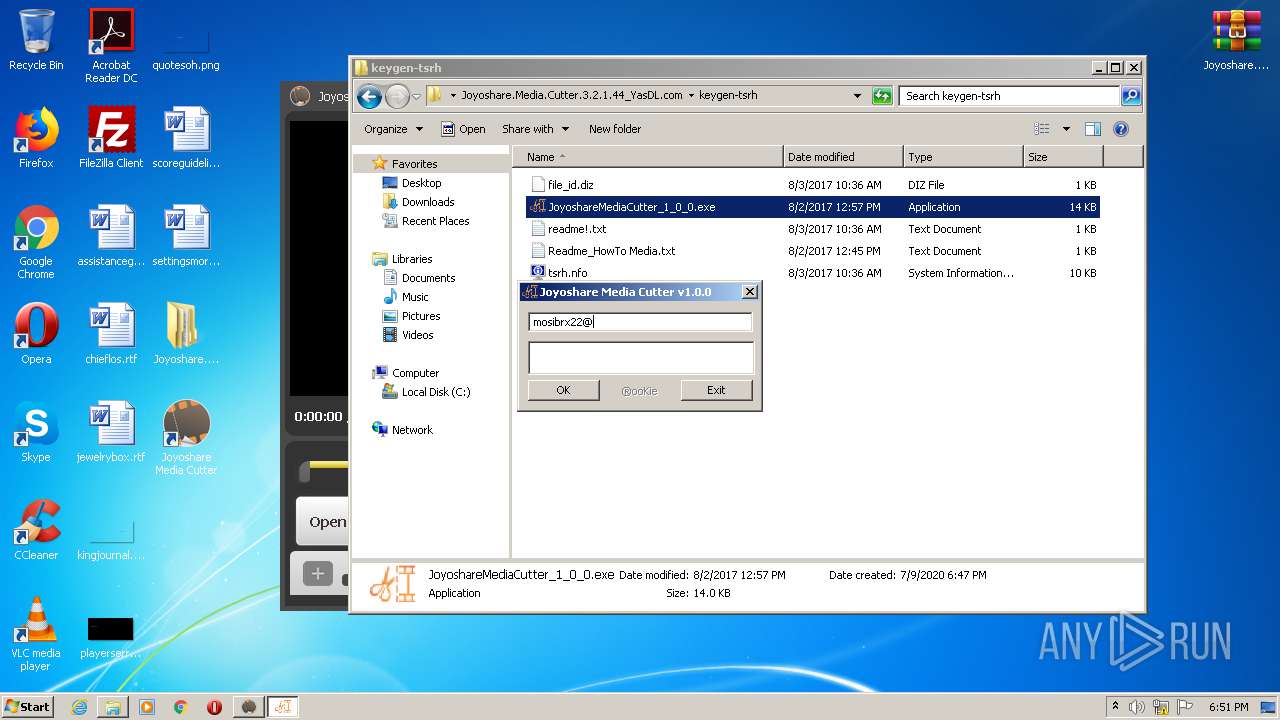
Application was dropped or rewritten from another process
- JoyoshareMediaCutter_1_0_0.exe (PID: 2412)
- JoyoshareMediaCutter_1_0_0.exe (PID: 4092)
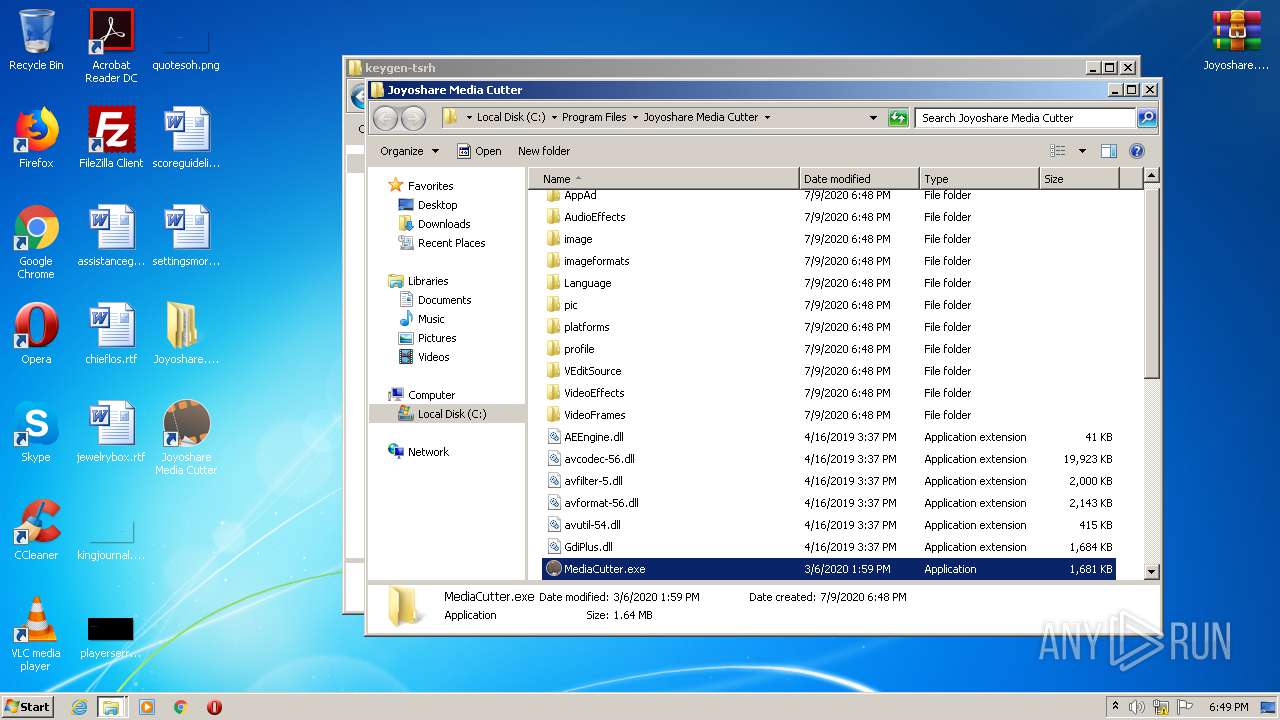
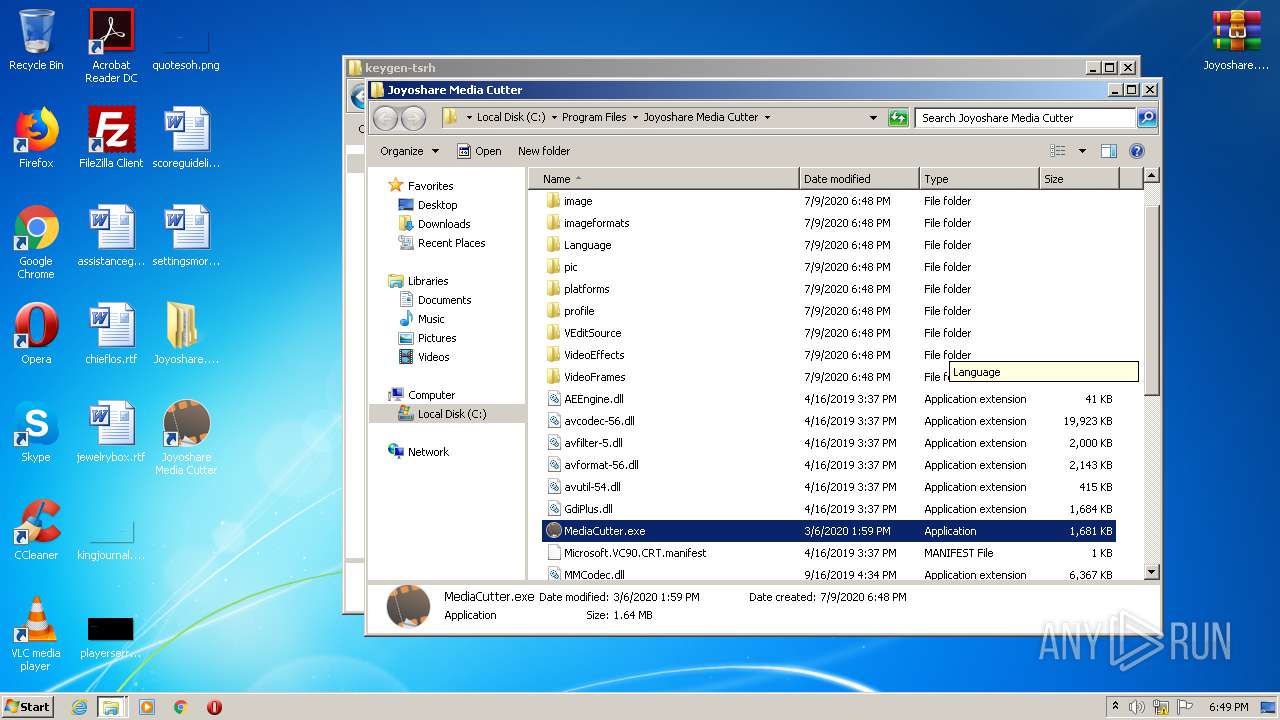
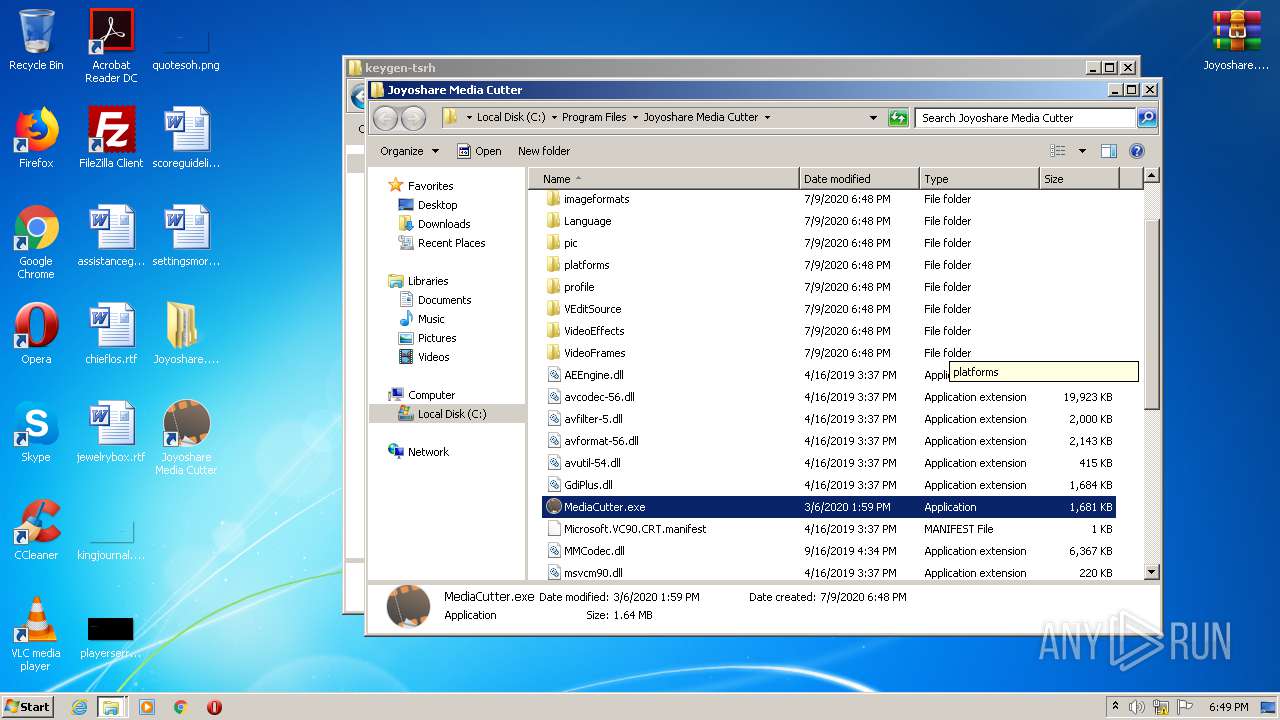
- MediaCutter.exe (PID: 2244)
- JoyoshareMediaCutter_1_0_0.exe (PID: 2976)
Loads dropped or rewritten executable
- explorer.exe (PID: 348)
- MediaCutter.exe (PID: 2244)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 2684)
Creates files in the user directory
- explorer.exe (PID: 348)
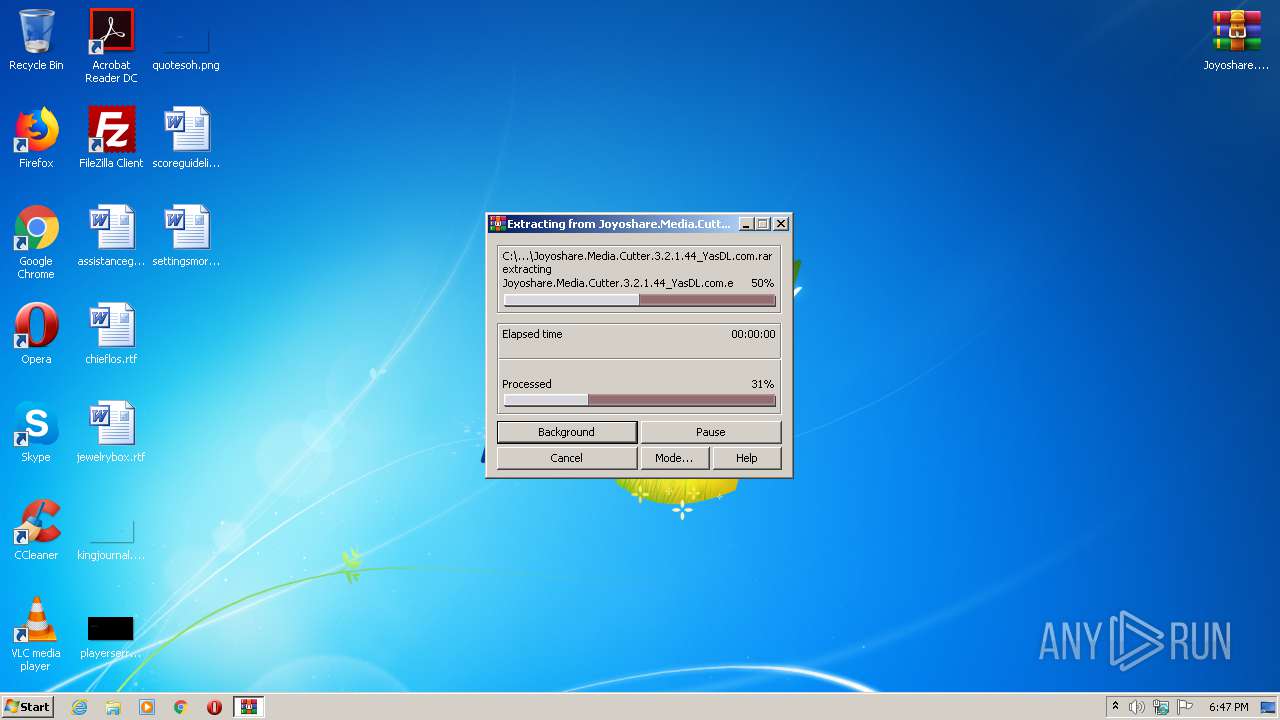
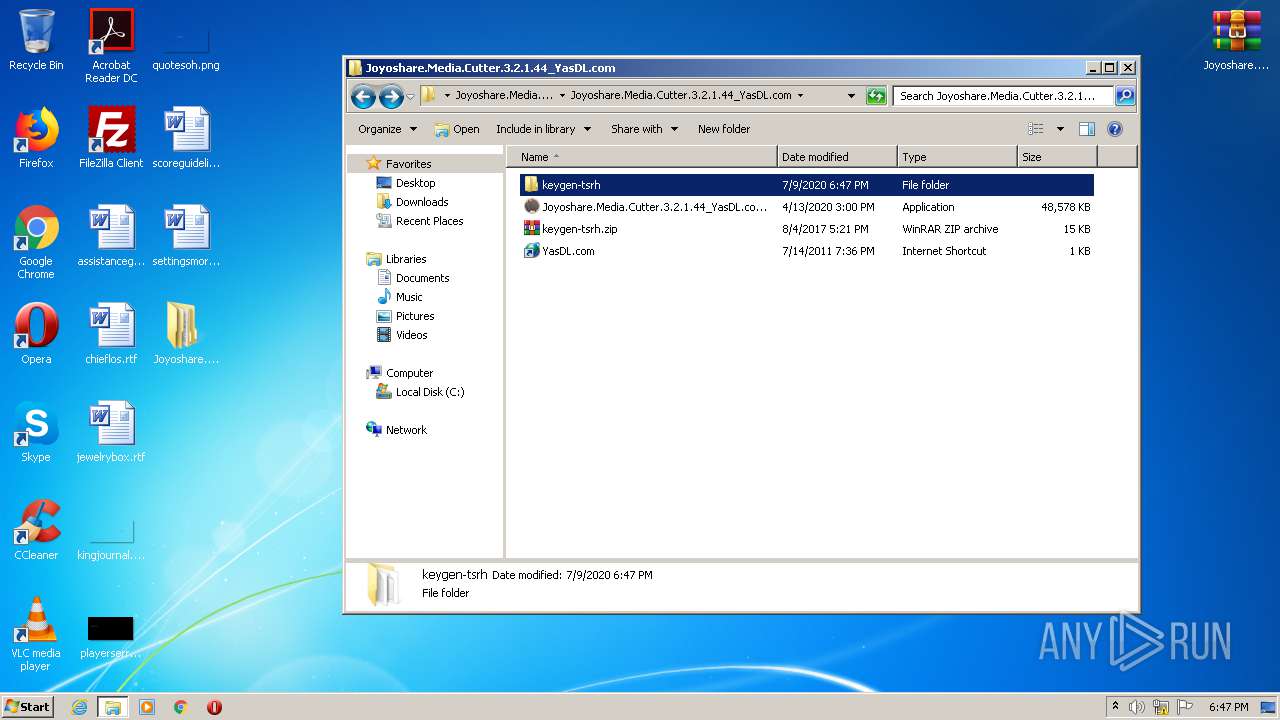
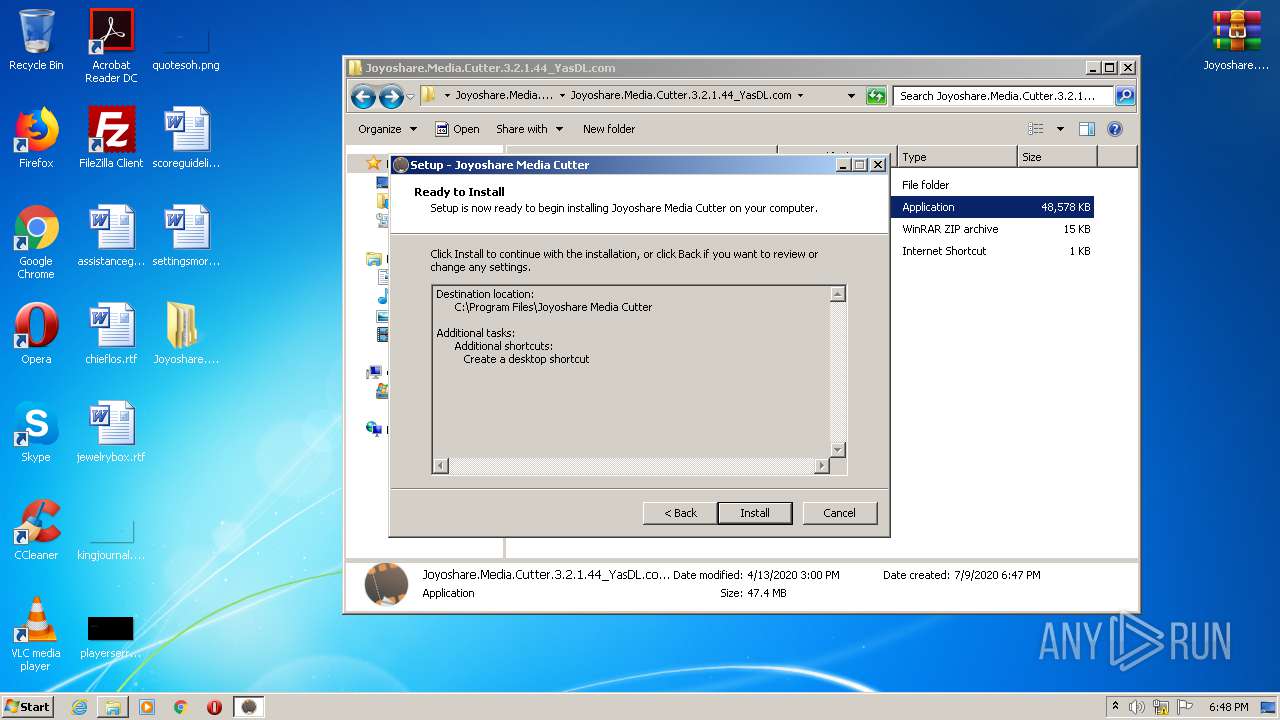
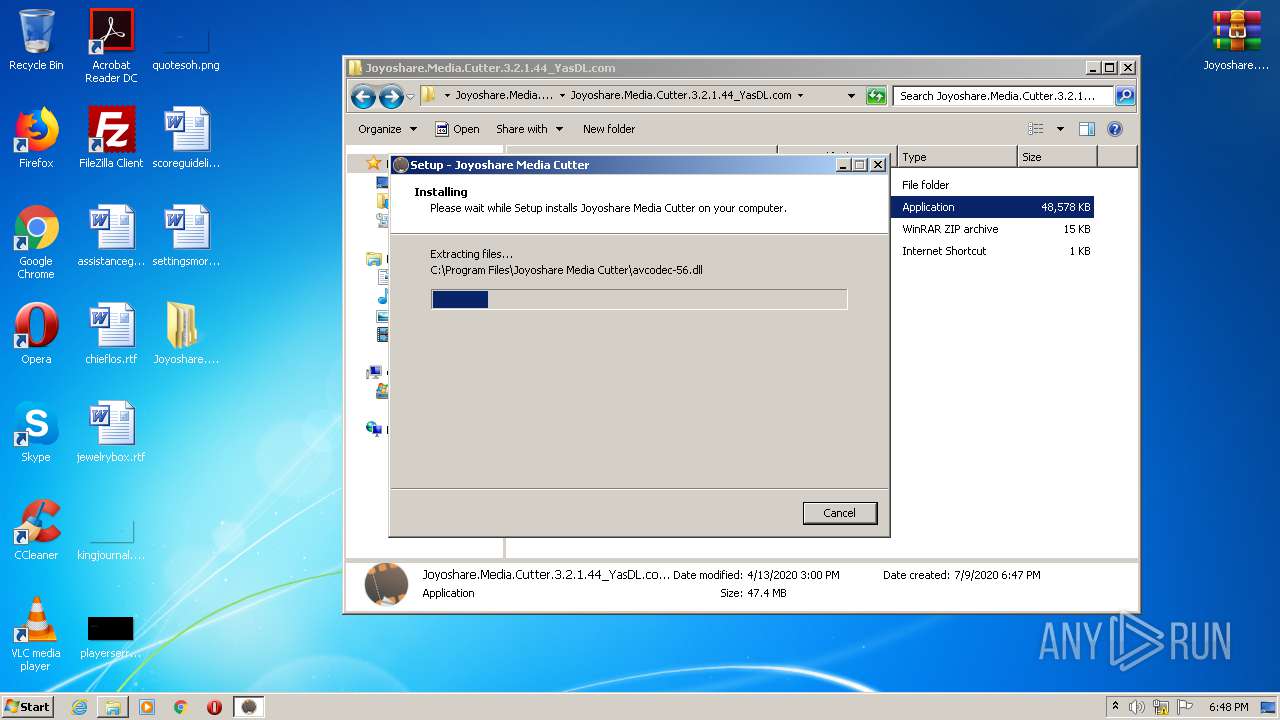
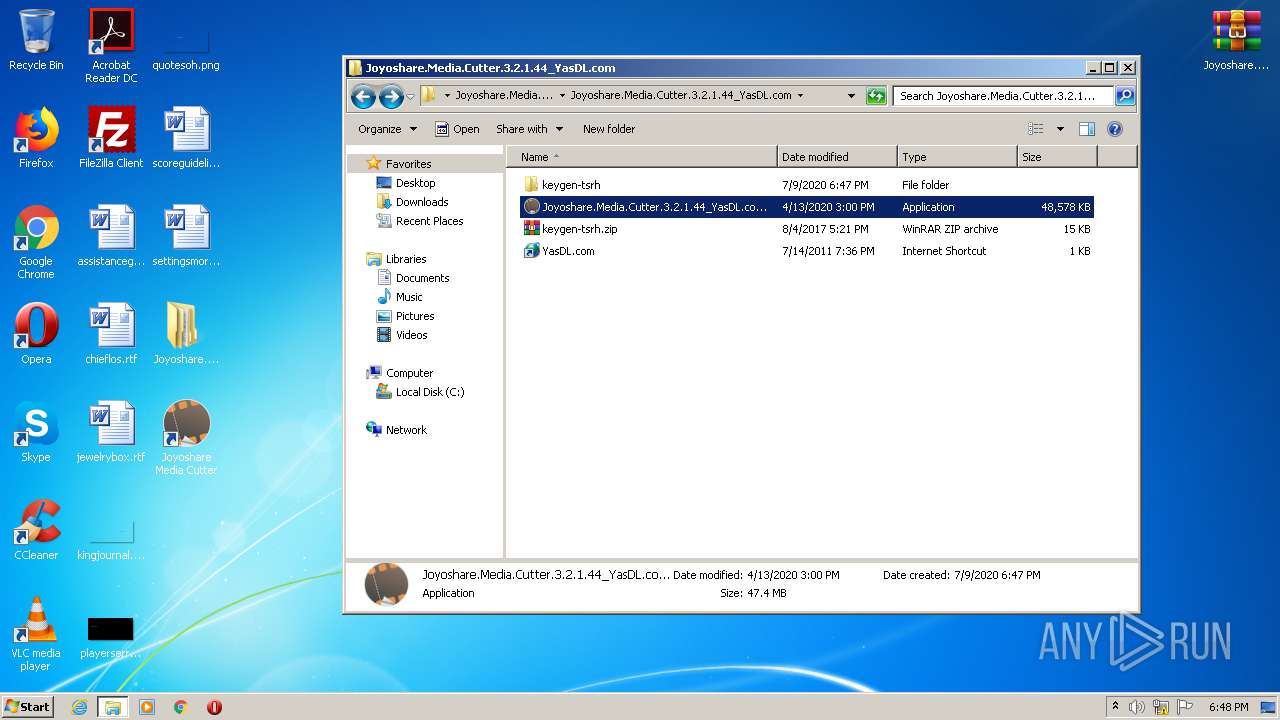
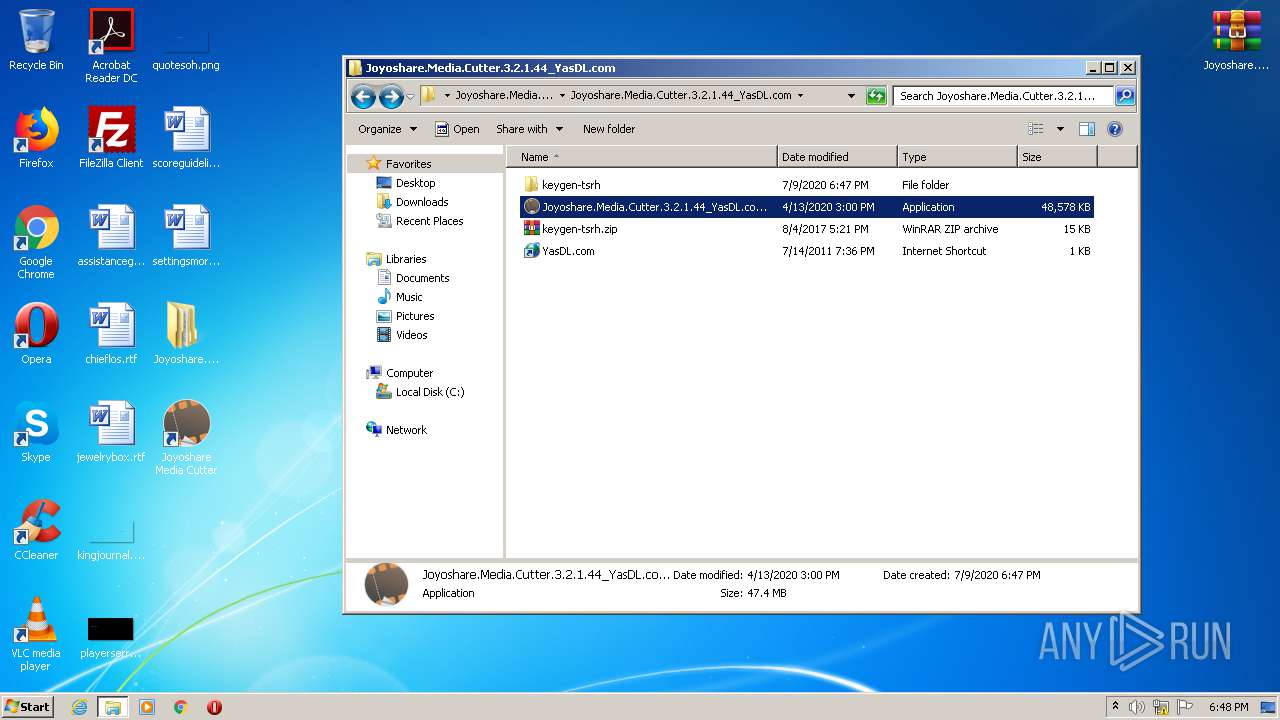
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3100)
- Joyoshare.Media.Cutter.3.2.1.44_YasDL.com.exe (PID: 3852)
- Joyoshare.Media.Cutter.3.2.1.44_YasDL.com.exe (PID: 2964)
- Joyoshare.Media.Cutter.3.2.1.44_YasDL.com.tmp (PID: 2072)
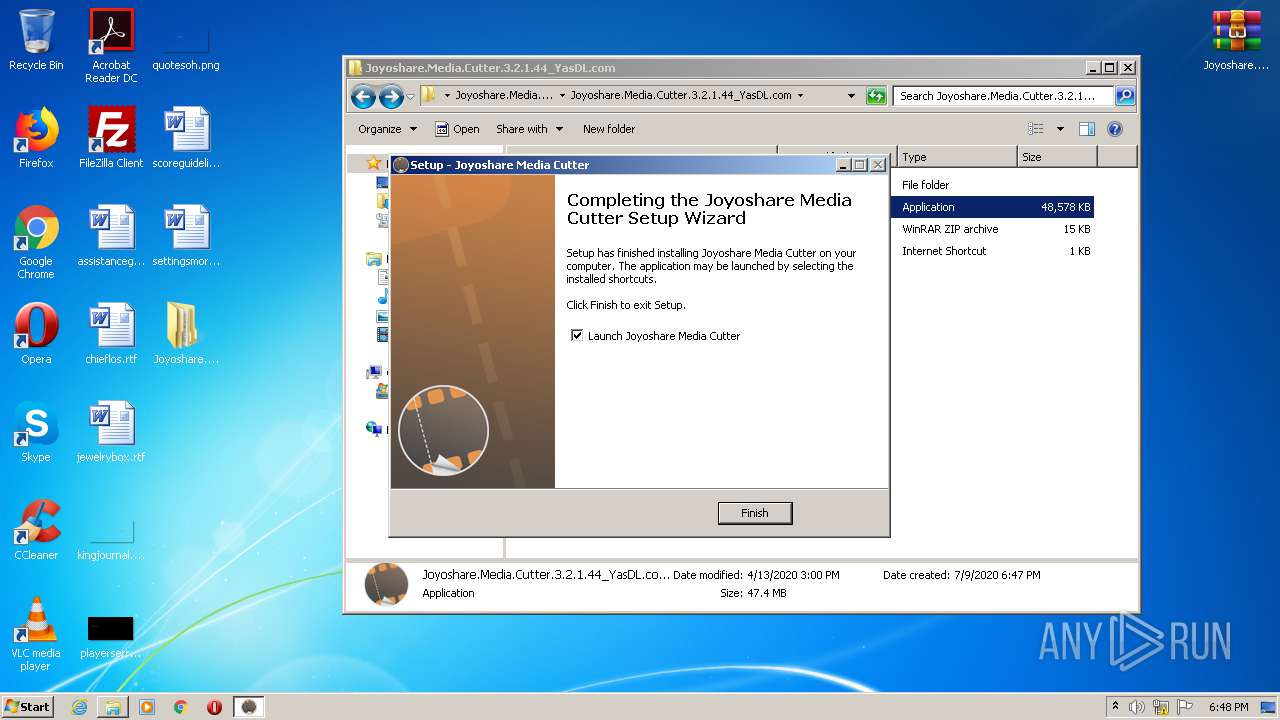
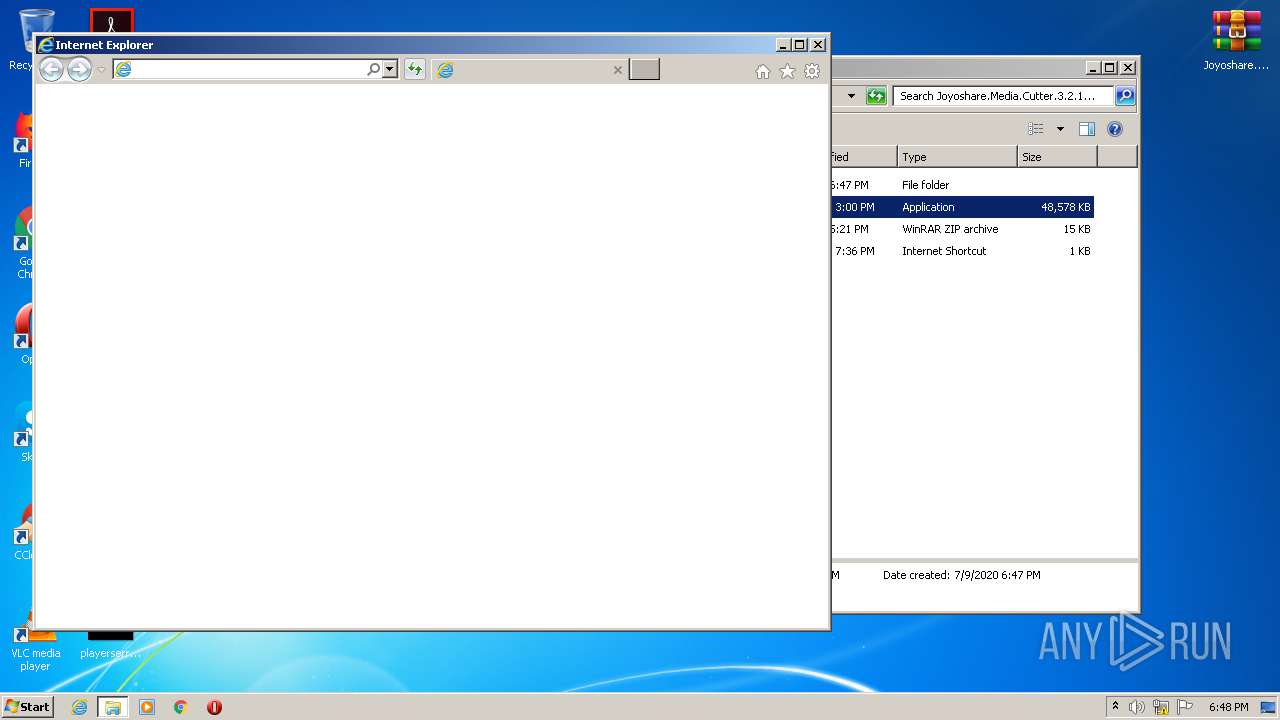
Starts Internet Explorer
- Joyoshare.Media.Cutter.3.2.1.44_YasDL.com.tmp (PID: 2072)
Reads Internet Cache Settings
- MediaCutter.exe (PID: 2244)
INFO
Application launched itself
- firefox.exe (PID: 2684)
- firefox.exe (PID: 1828)
- iexplore.exe (PID: 2488)
Reads CPU info
- firefox.exe (PID: 2684)
Reads Internet Cache Settings
- firefox.exe (PID: 2684)
- pingsender.exe (PID: 912)
- iexplore.exe (PID: 3812)
- iexplore.exe (PID: 2488)
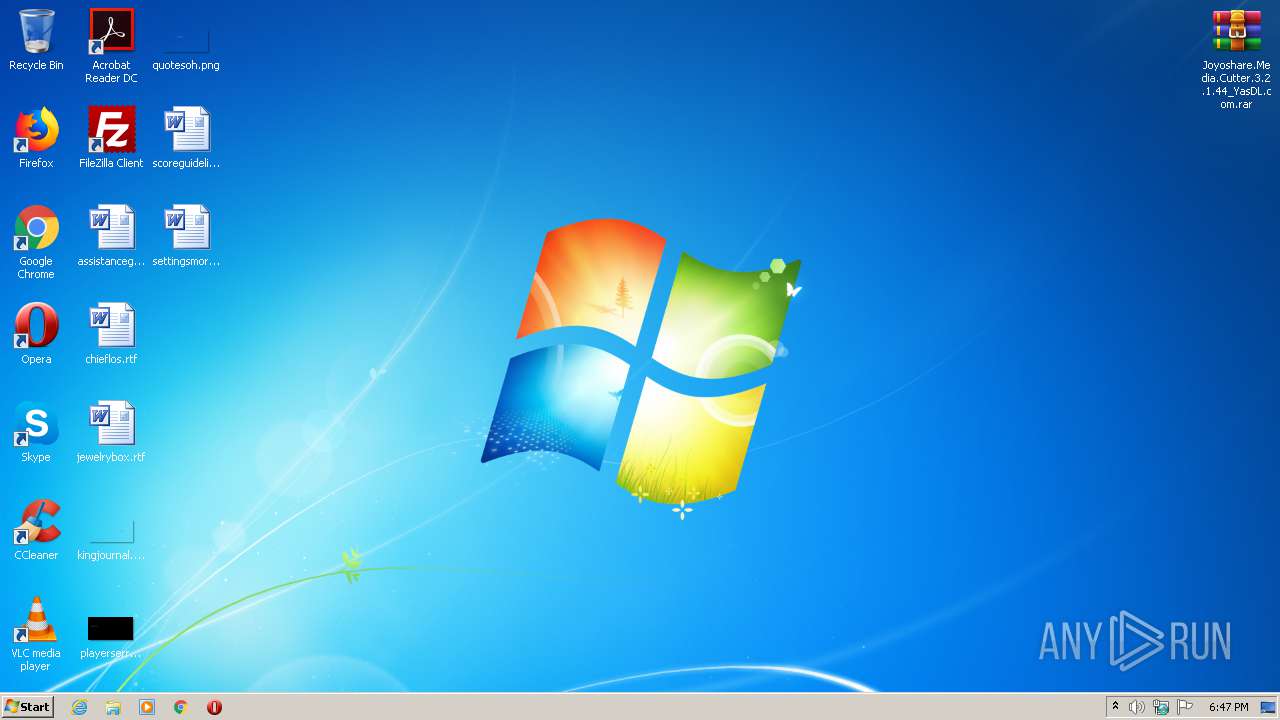
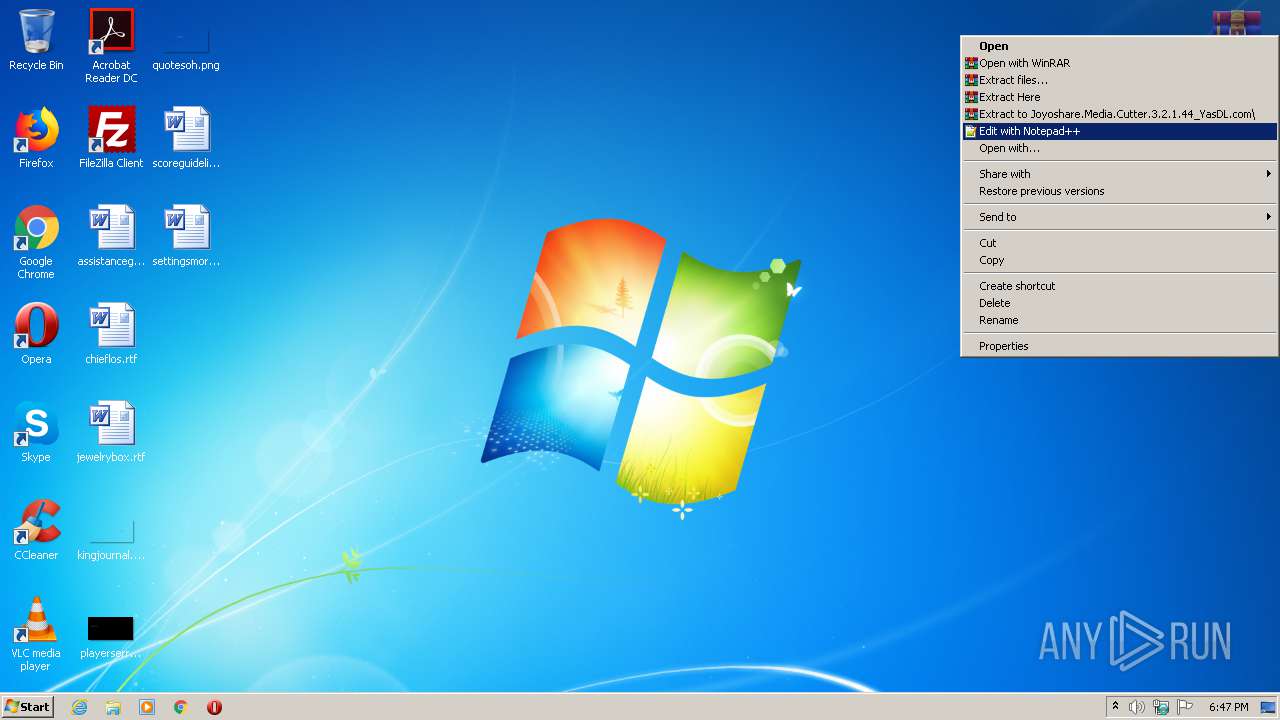
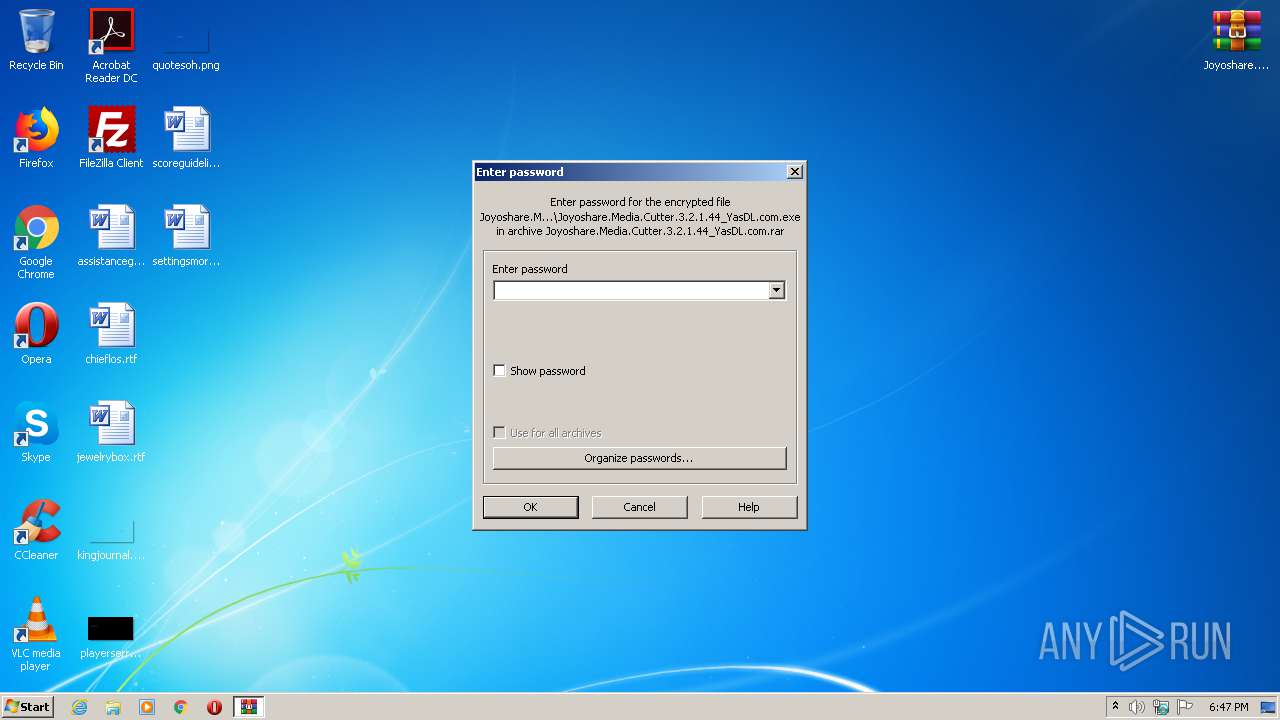
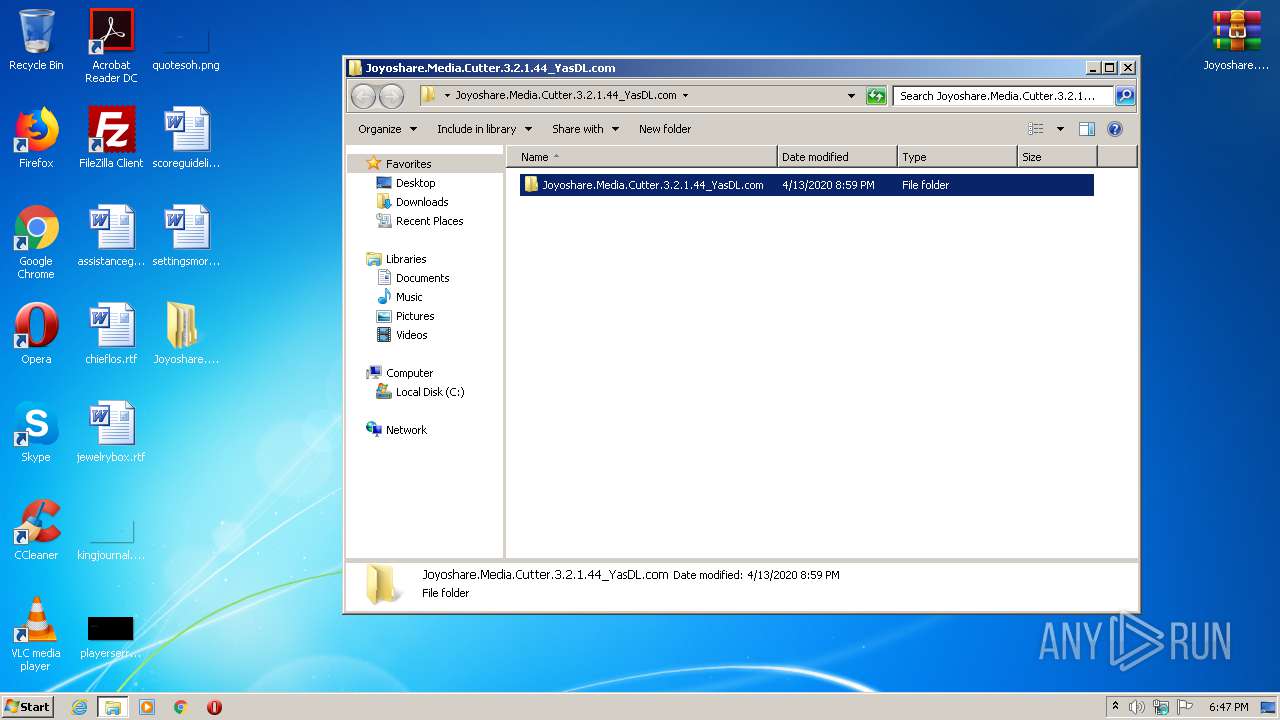
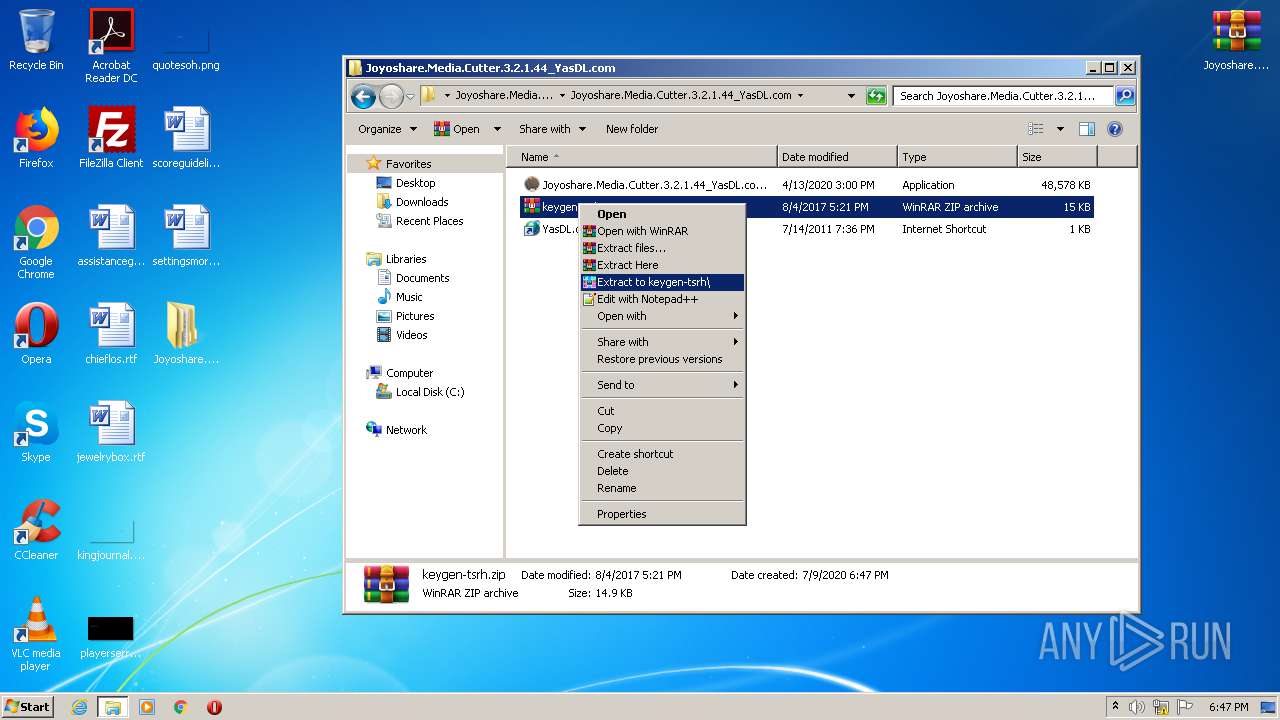
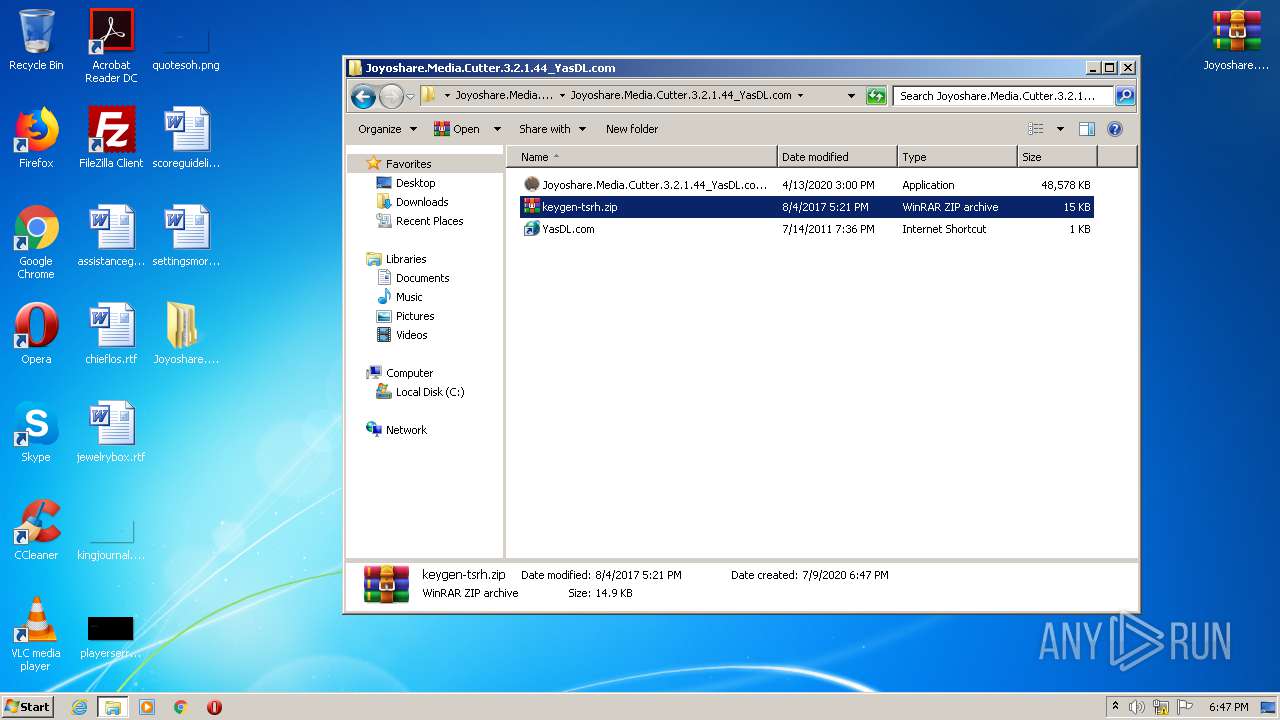
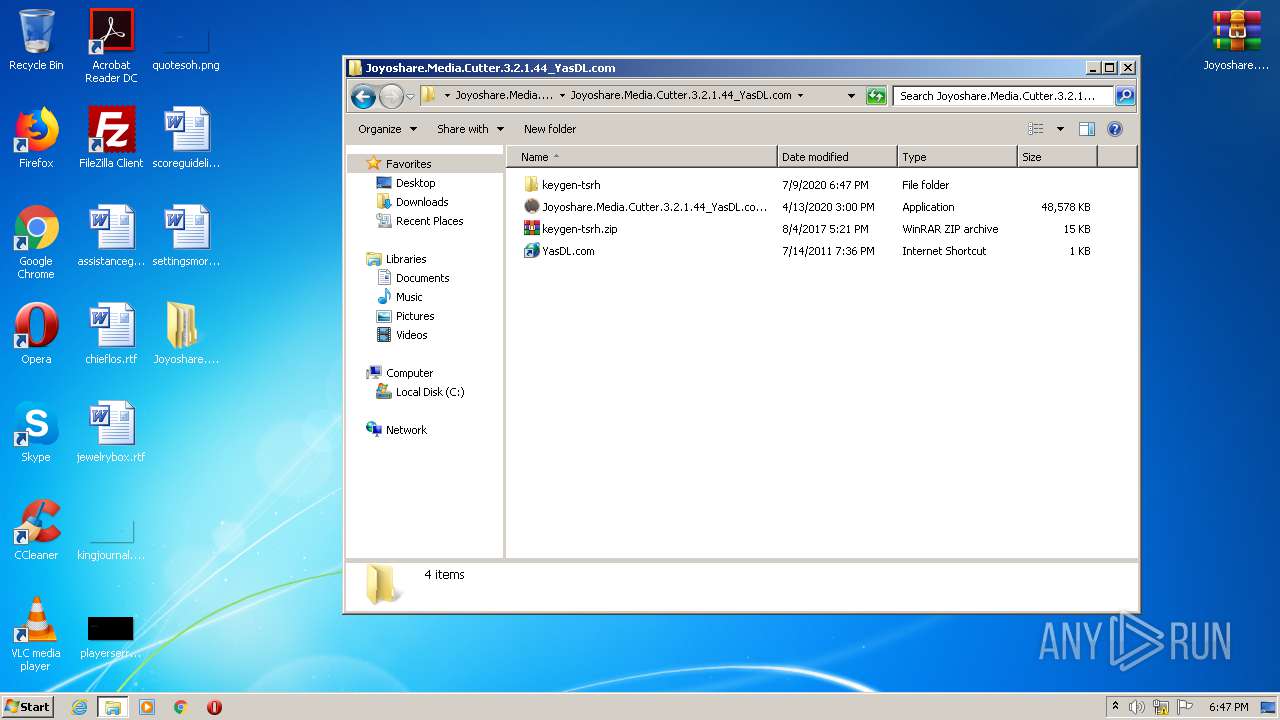
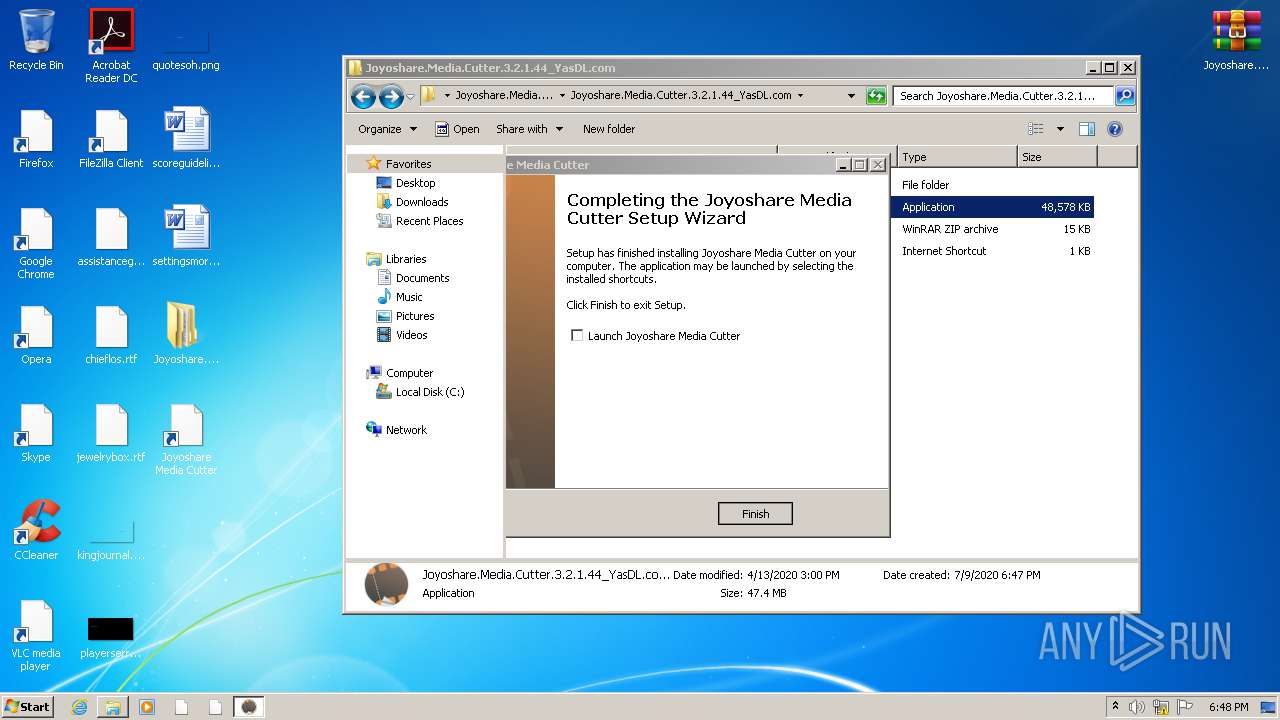
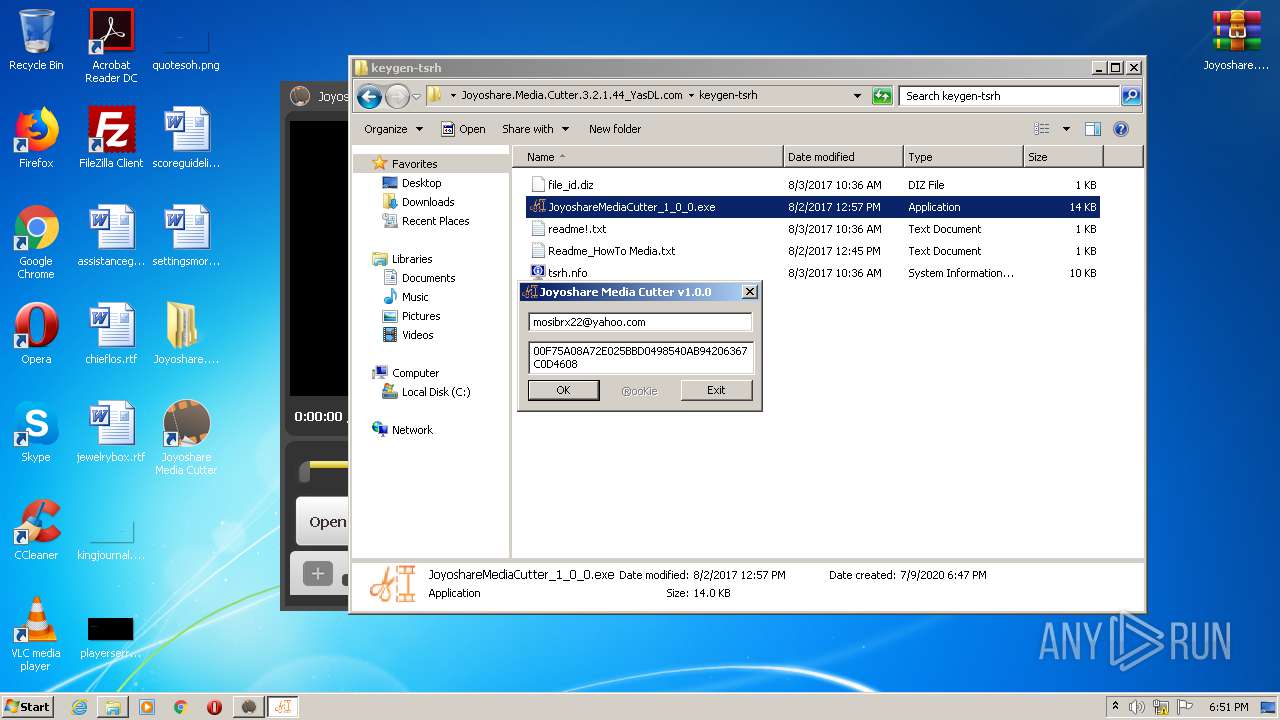
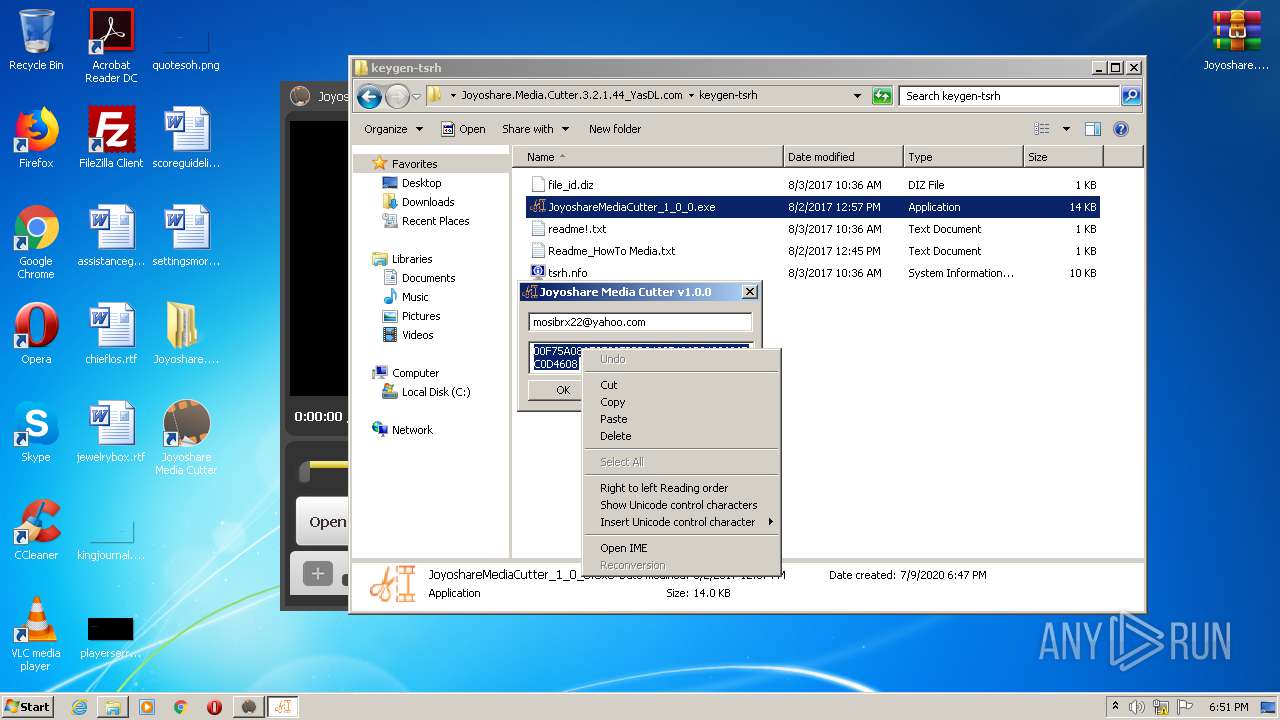
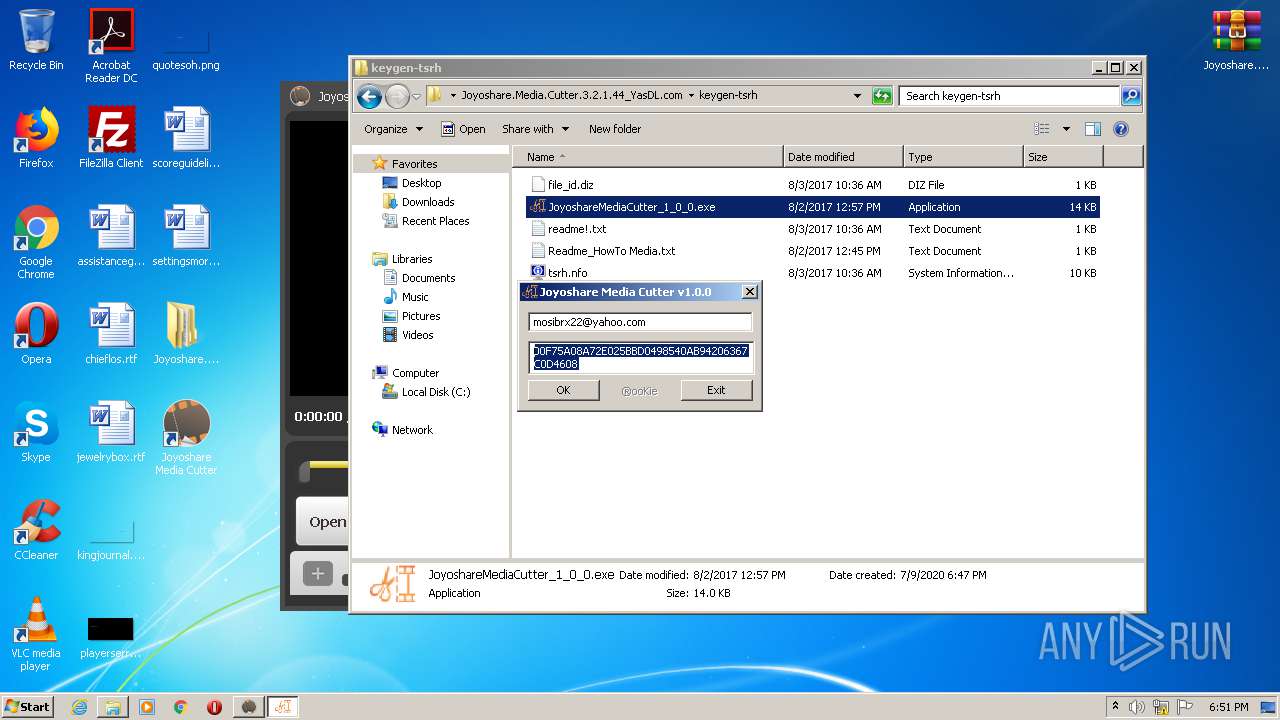
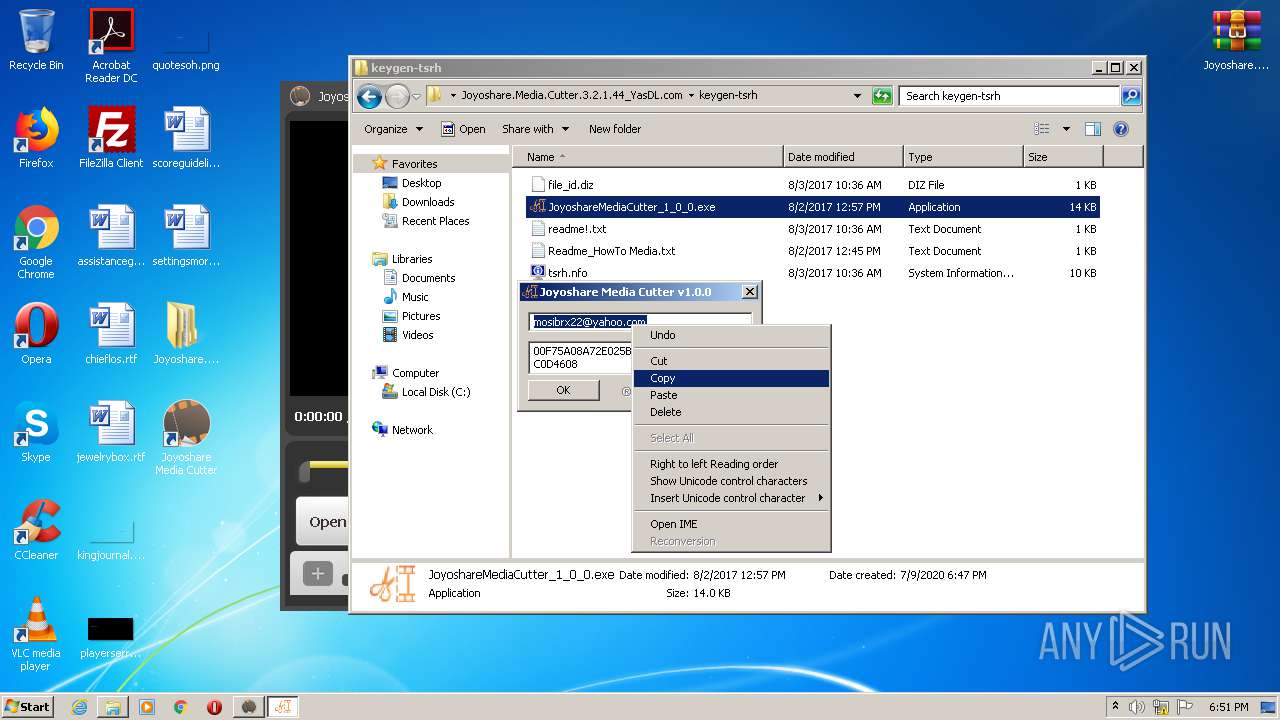
Manual execution by user
- Joyoshare.Media.Cutter.3.2.1.44_YasDL.com.exe (PID: 3852)
- WinRAR.exe (PID: 1952)
- WinRAR.exe (PID: 3100)
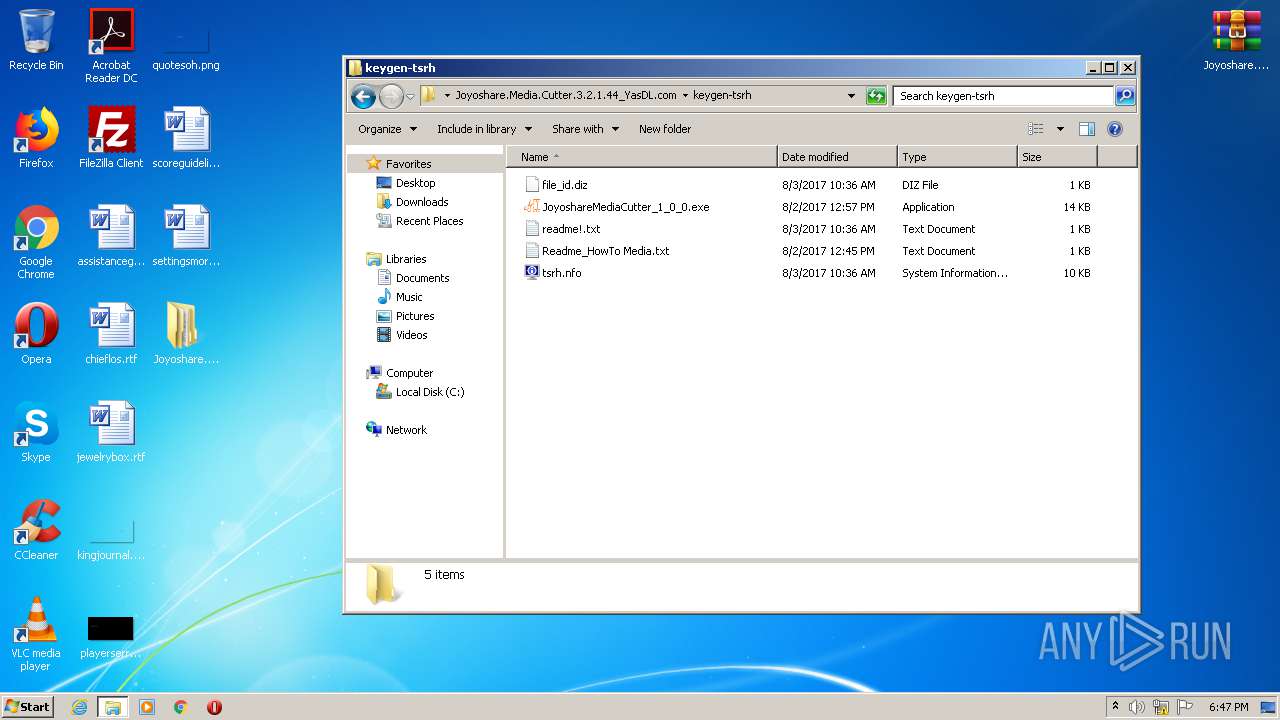
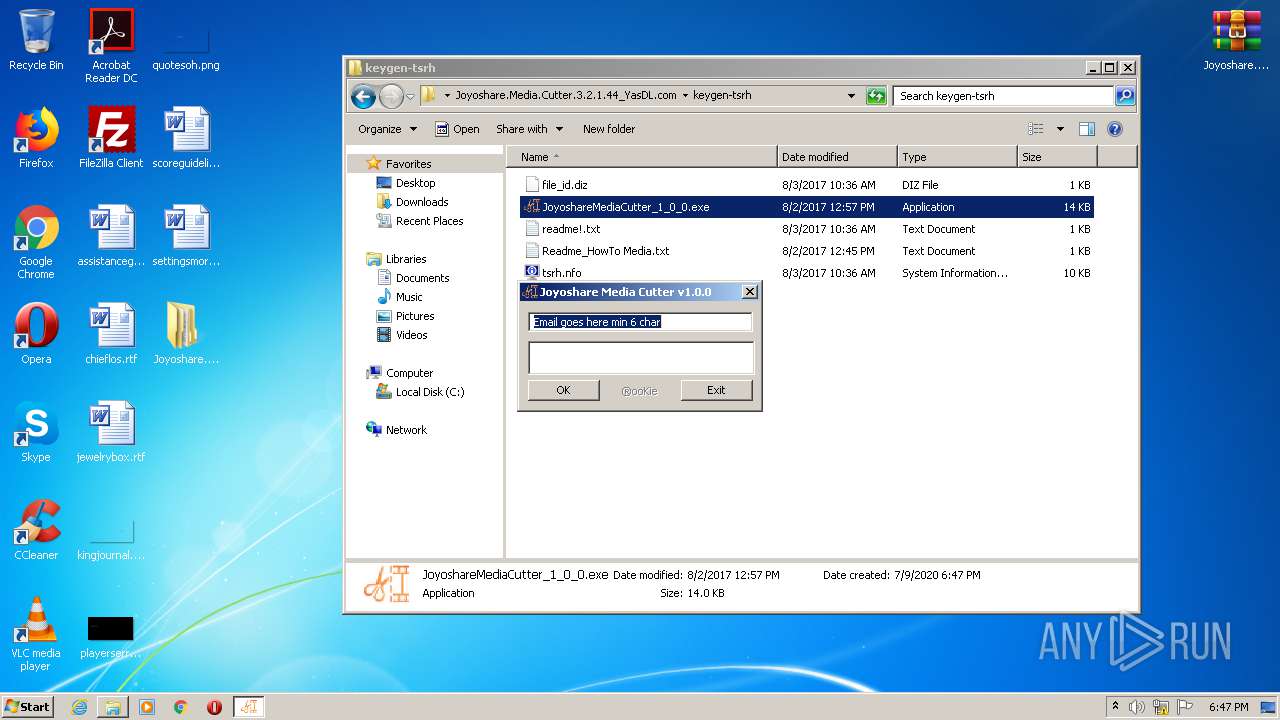
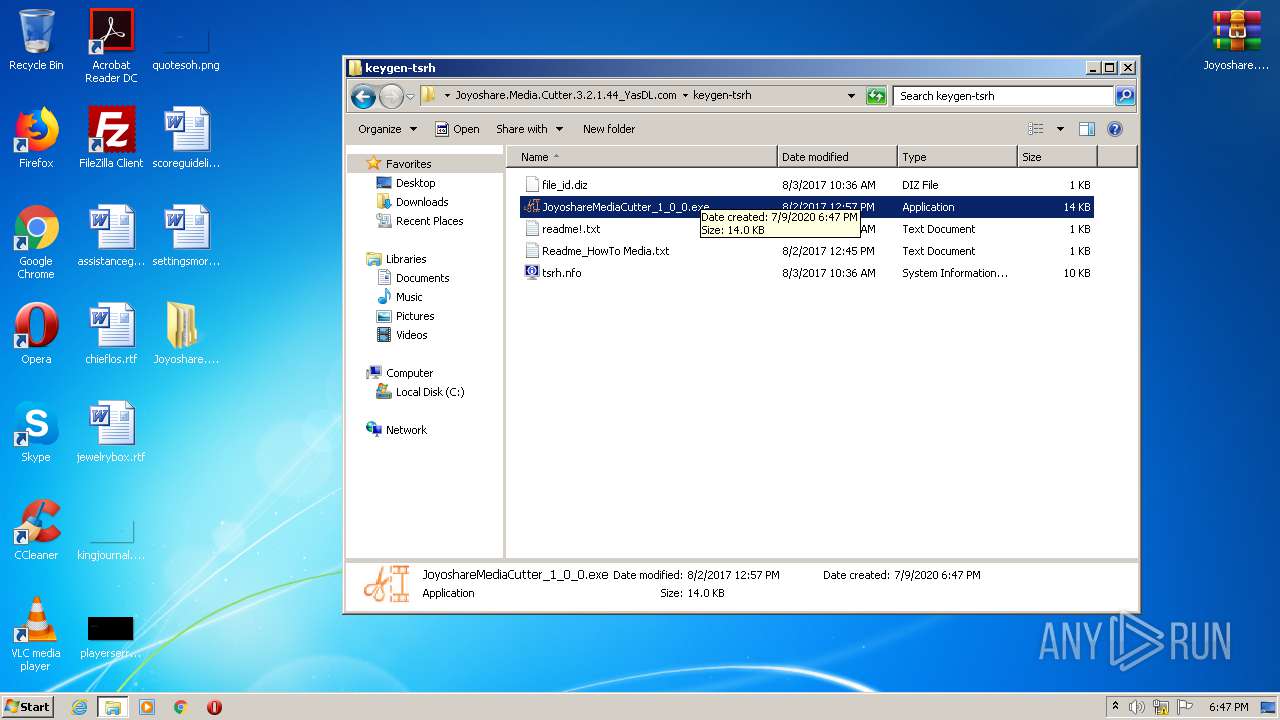
- JoyoshareMediaCutter_1_0_0.exe (PID: 2412)
- JoyoshareMediaCutter_1_0_0.exe (PID: 4092)
Application was dropped or rewritten from another process
- Joyoshare.Media.Cutter.3.2.1.44_YasDL.com.tmp (PID: 2072)
- Joyoshare.Media.Cutter.3.2.1.44_YasDL.com.tmp (PID: 3696)
Creates files in the user directory
- firefox.exe (PID: 2684)
Changes internet zones settings
- iexplore.exe (PID: 2488)
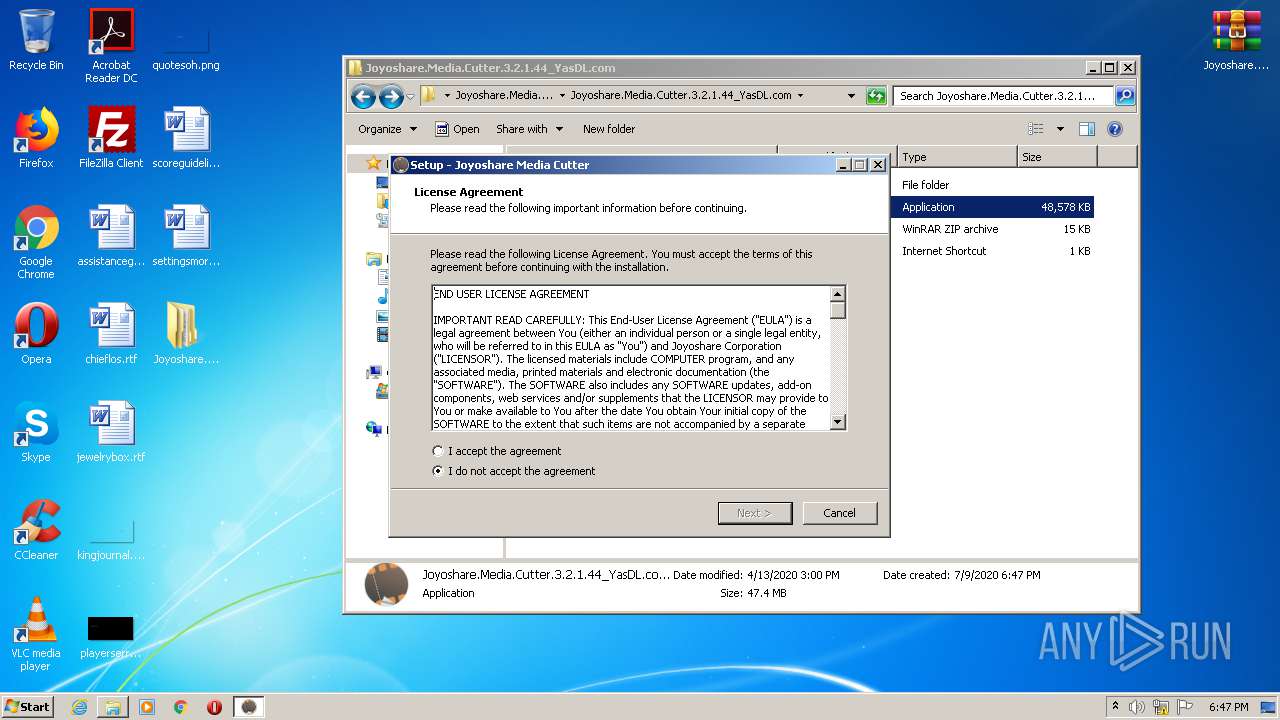
Creates a software uninstall entry
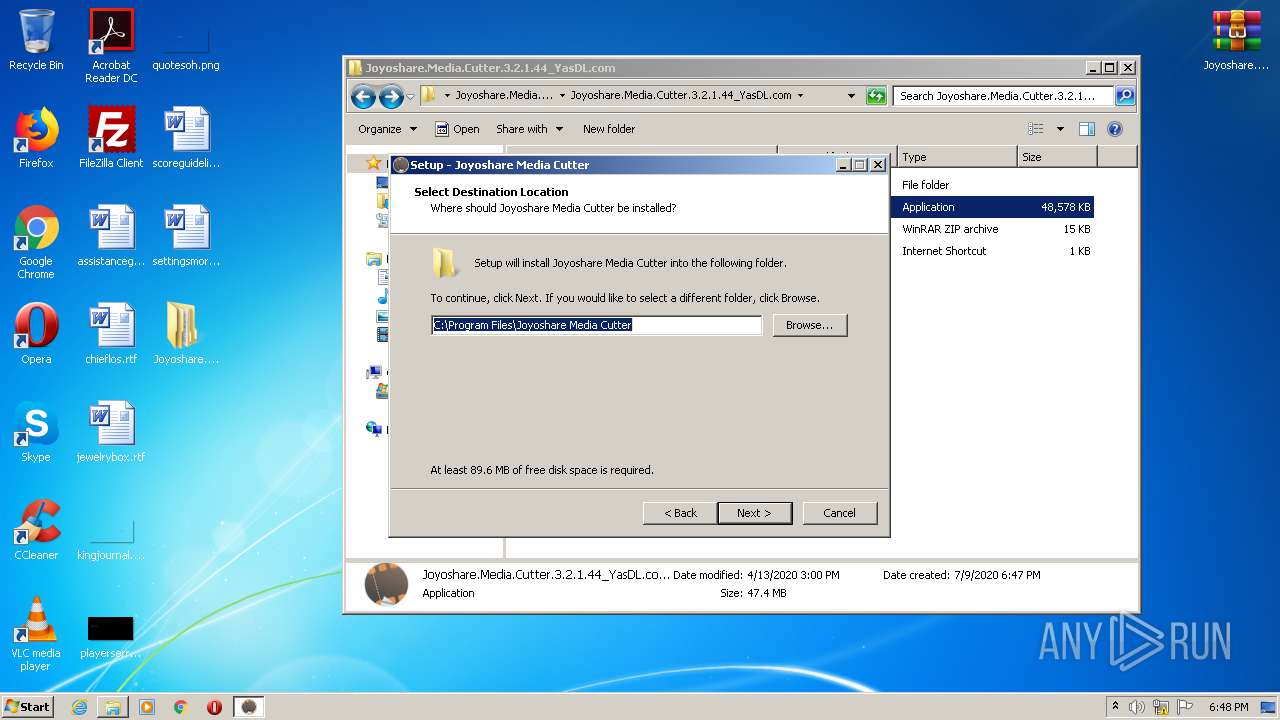
- Joyoshare.Media.Cutter.3.2.1.44_YasDL.com.tmp (PID: 2072)
Dropped object may contain Bitcoin addresses
- Joyoshare.Media.Cutter.3.2.1.44_YasDL.com.tmp (PID: 2072)
Creates files in the program directory
- Joyoshare.Media.Cutter.3.2.1.44_YasDL.com.tmp (PID: 2072)
Reads settings of System Certificates
- iexplore.exe (PID: 3812)
Changes settings of System certificates
- iexplore.exe (PID: 3812)
- pingsender.exe (PID: 912)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3812)
- pingsender.exe (PID: 912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
20
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 912 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/d3563cd6-d24c-47c8-8080-e006036b854c/main/Firefox/68.0.1/release/20190717172542?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\saved-telemetry-pings\d3563cd6-d24c-47c8-8080-e006036b854c | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1396 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2684.0.737256953\1106572022" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2684 "\\.\pipe\gecko-crash-server-pipe.2684" 1204 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 68.0.1 Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Mozilla Firefox\firefox.exe" "http://dl.yasdl.com/2020/Software/Joyoshare.Media.Cutter.3.2.1.44_YasDL.com.rar?fgy" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1952 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\Joyoshare.Media.Cutter.3.2.1.44_YasDL.com.rar" C:\Users\admin\Desktop\Joyoshare.Media.Cutter.3.2.1.44_YasDL.com\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2072 | "C:\Users\admin\AppData\Local\Temp\is-BDGDF.tmp\Joyoshare.Media.Cutter.3.2.1.44_YasDL.com.tmp" /SL5="$401BA,49376138,138752,C:\Users\admin\Desktop\Joyoshare.Media.Cutter.3.2.1.44_YasDL.com\Joyoshare.Media.Cutter.3.2.1.44_YasDL.com\Joyoshare.Media.Cutter.3.2.1.44_YasDL.com.exe" /SPAWNWND=$5017A /NOTIFYWND=$301EE | C:\Users\admin\AppData\Local\Temp\is-BDGDF.tmp\Joyoshare.Media.Cutter.3.2.1.44_YasDL.com.tmp | Joyoshare.Media.Cutter.3.2.1.44_YasDL.com.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
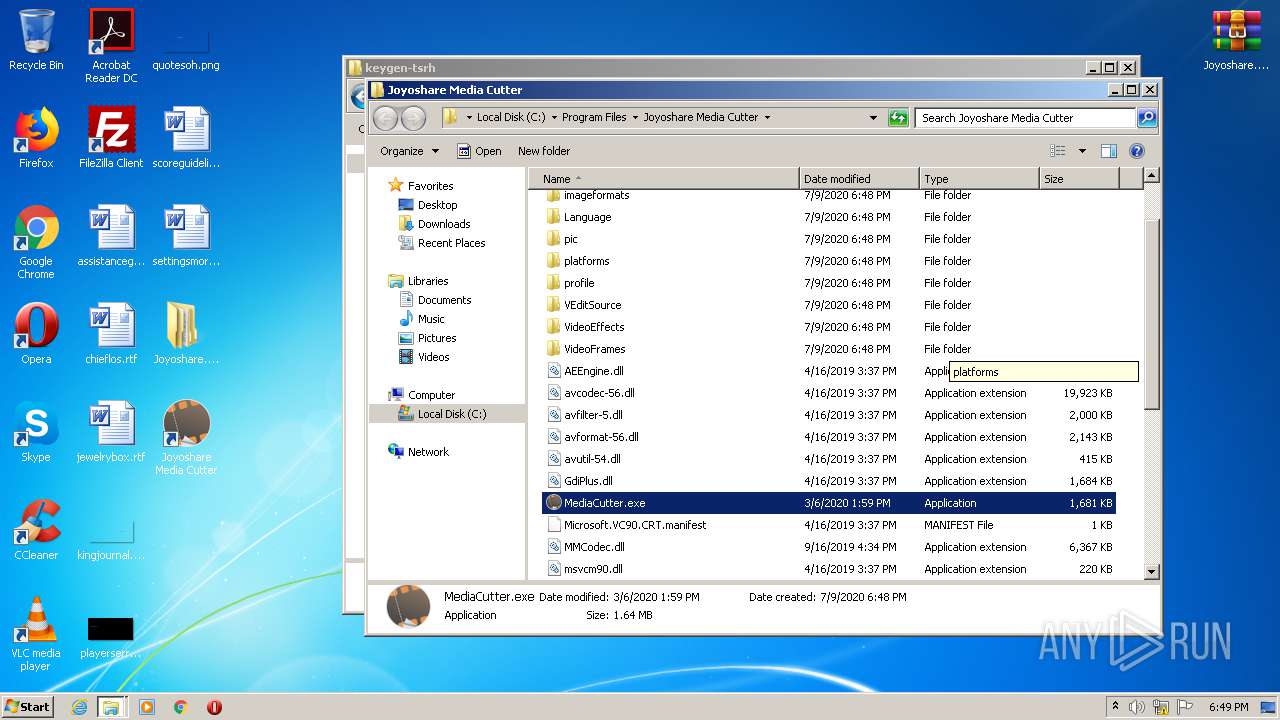
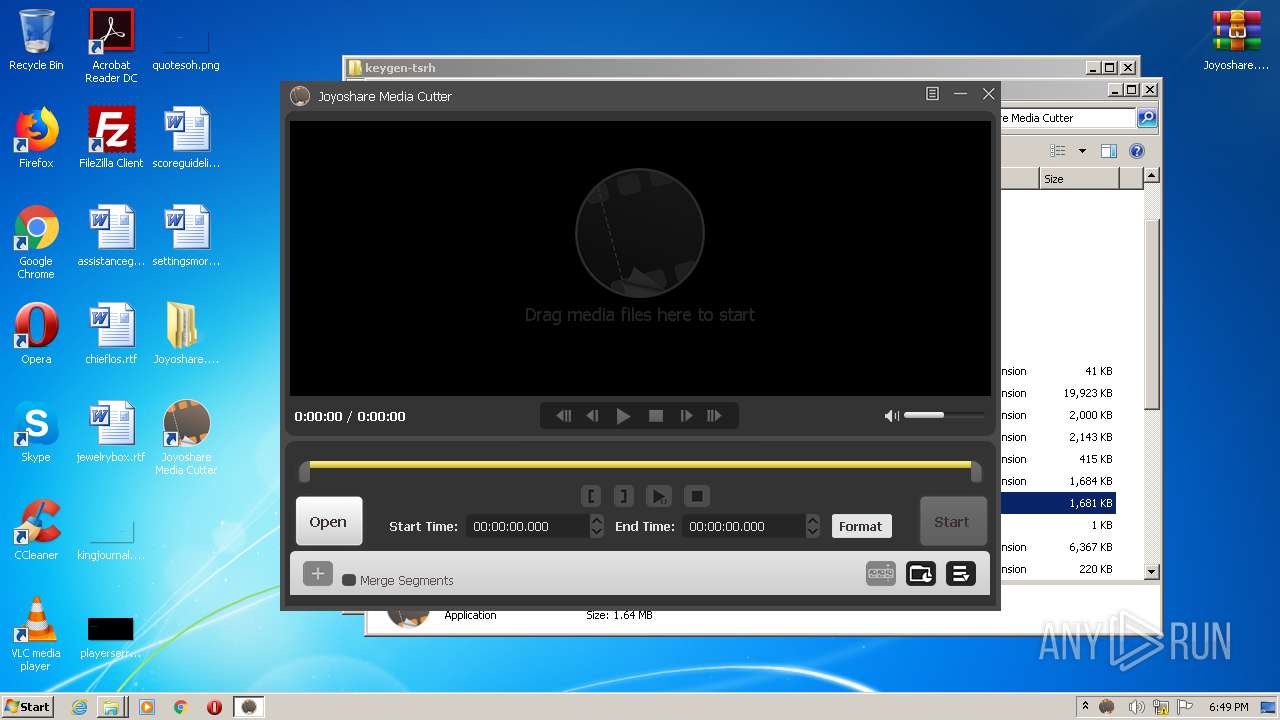
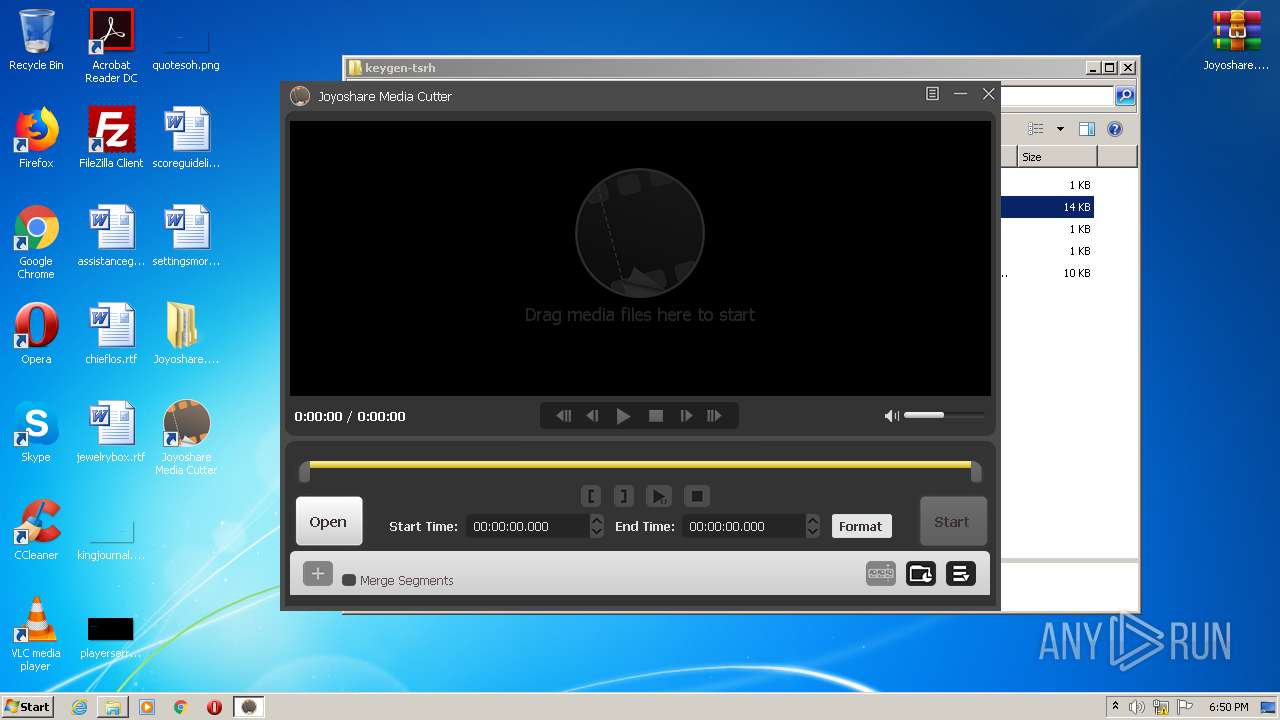
| 2244 | "C:\Program Files\Joyoshare Media Cutter\MediaCutter.exe" | C:\Program Files\Joyoshare Media Cutter\MediaCutter.exe | explorer.exe | ||||||||||||
User: admin Company: Joyoshare Integrity Level: MEDIUM Description: Joyoshare Media Cutter Exit code: 0 Version: 3.2.1.44 Modules
| |||||||||||||||
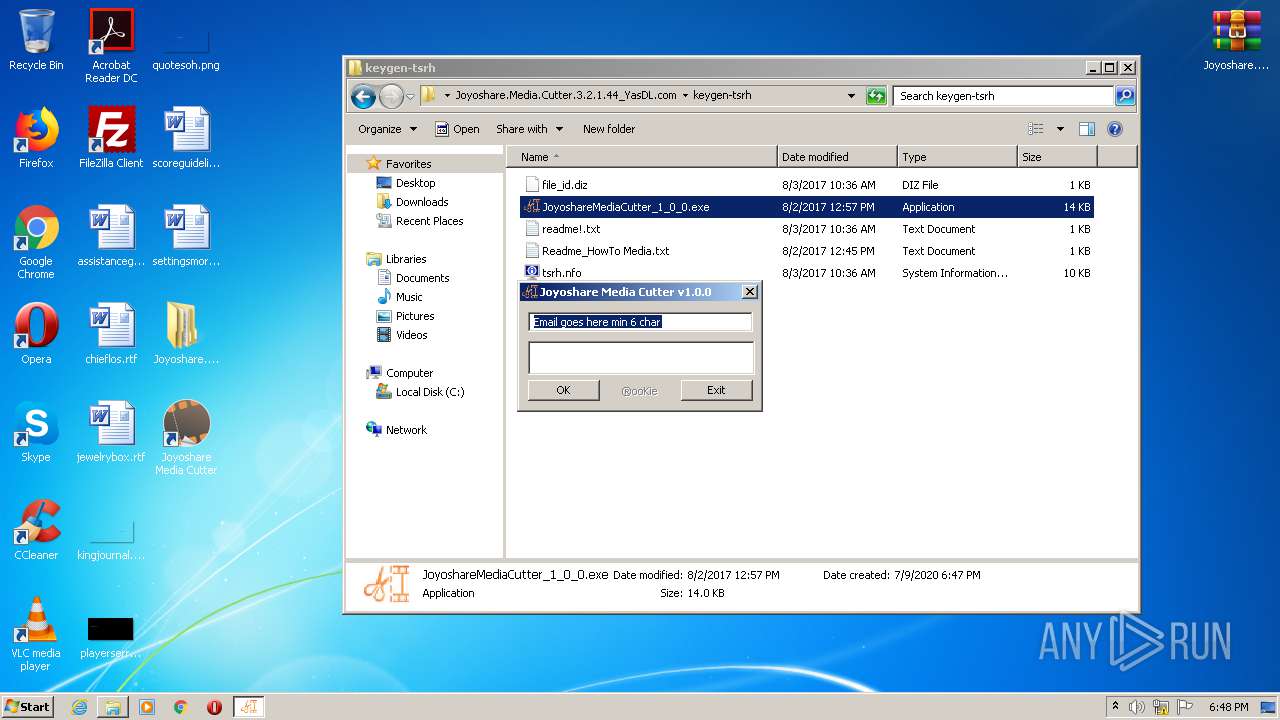
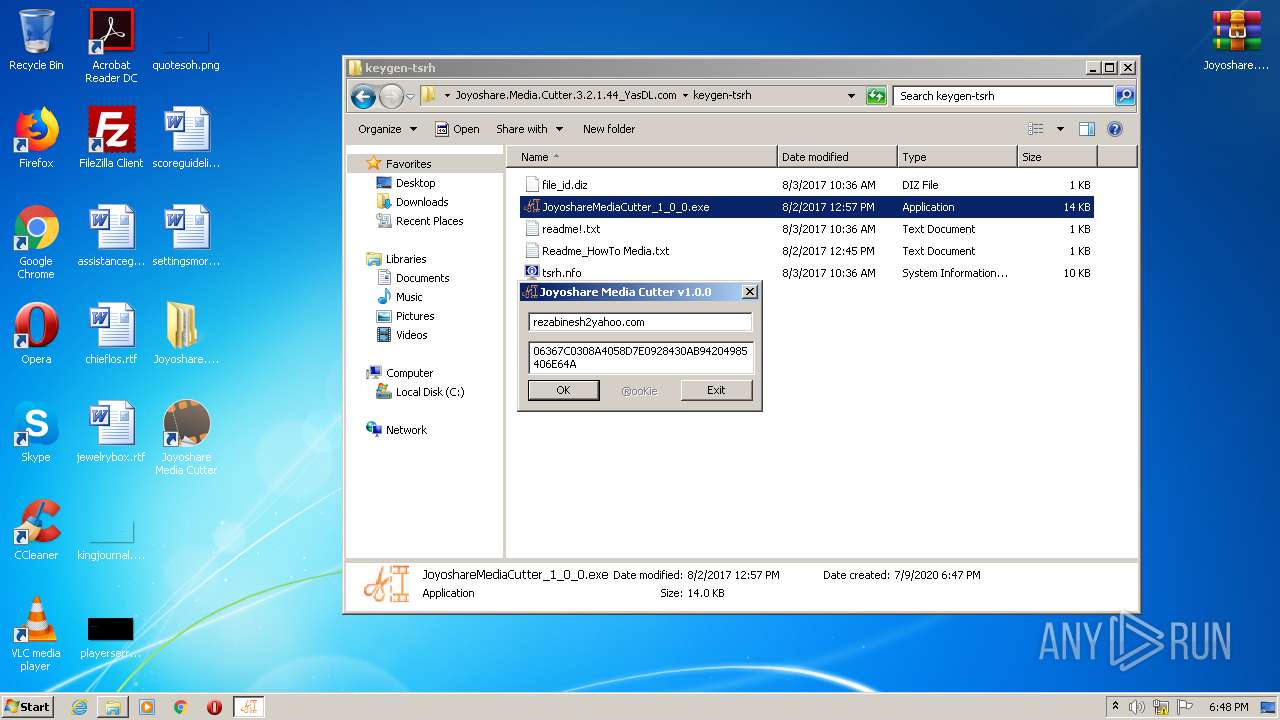
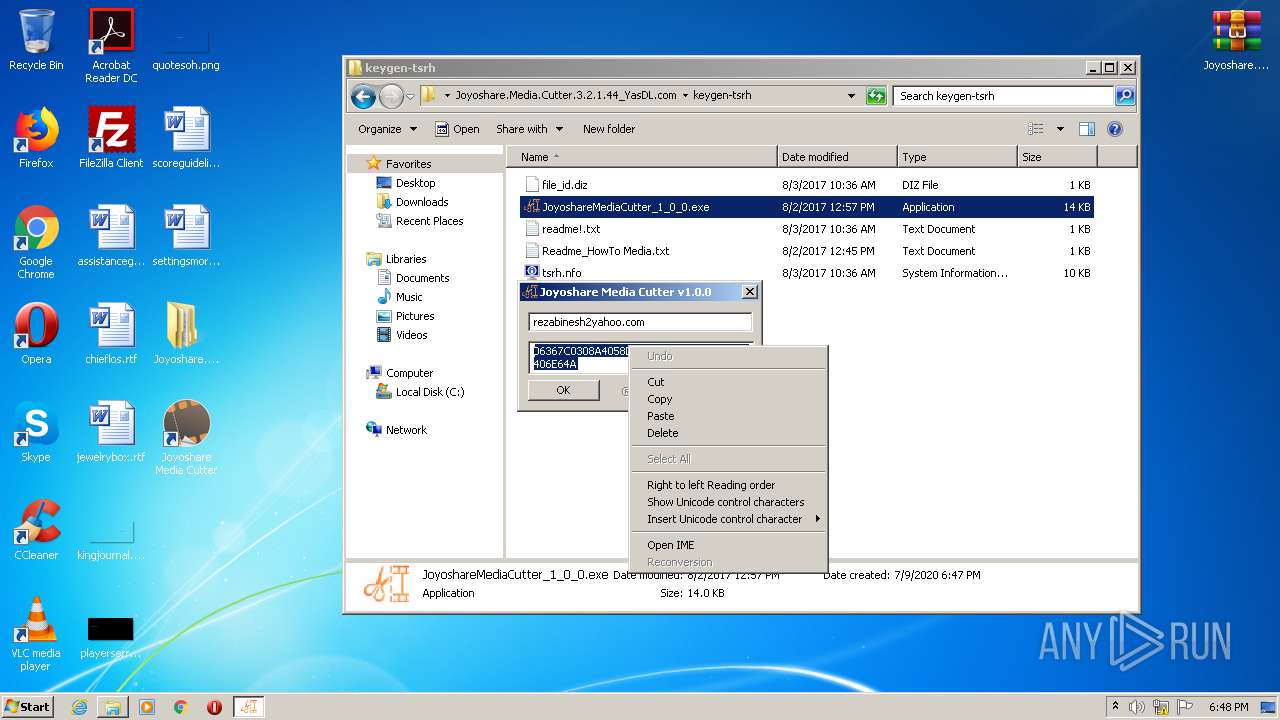
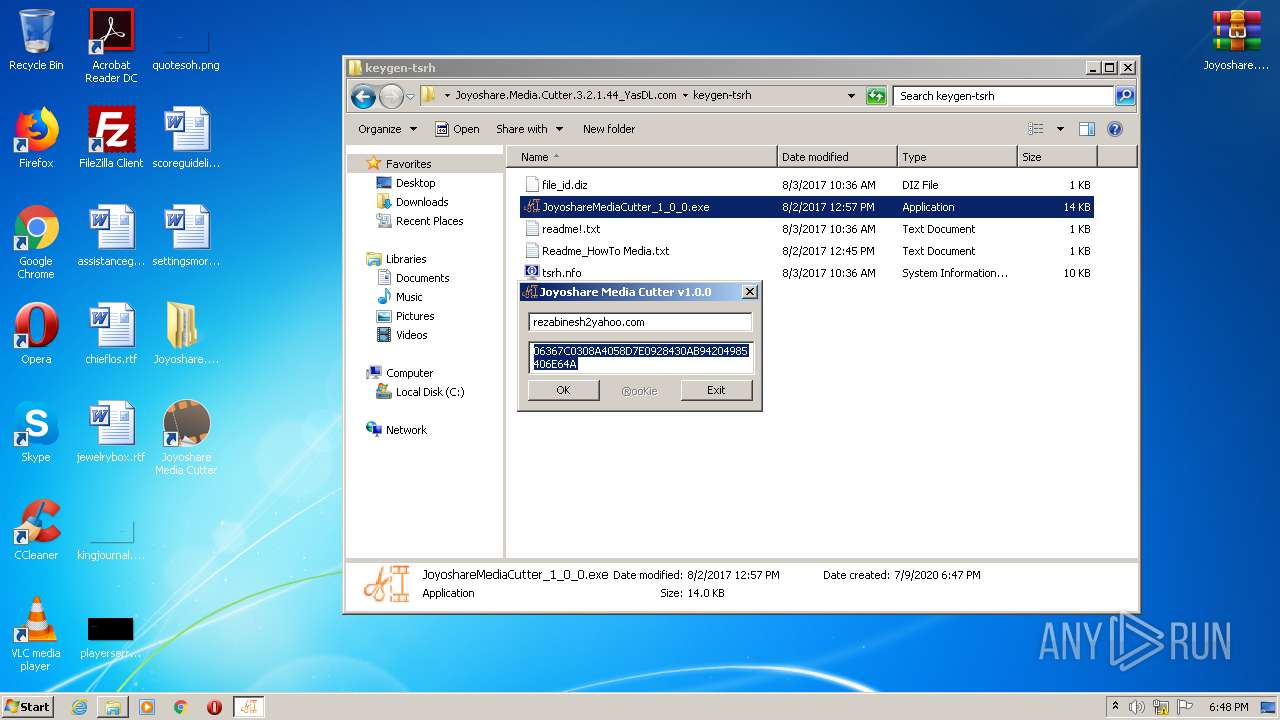
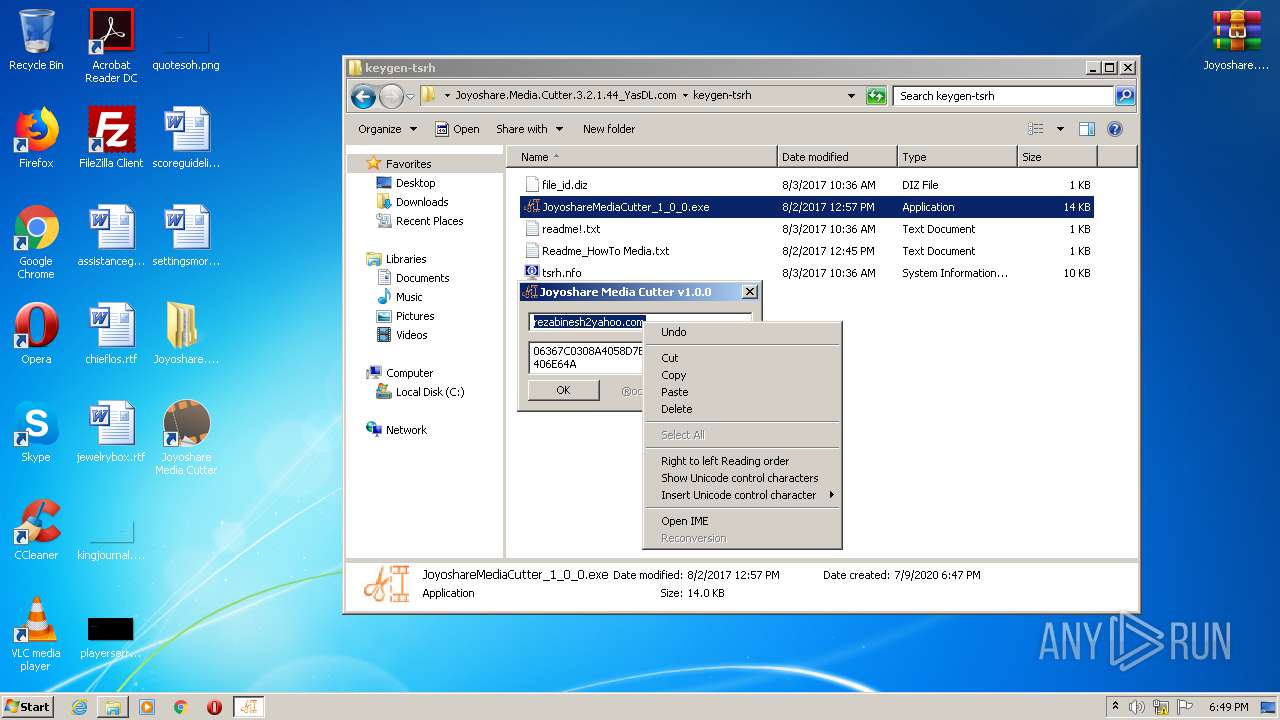
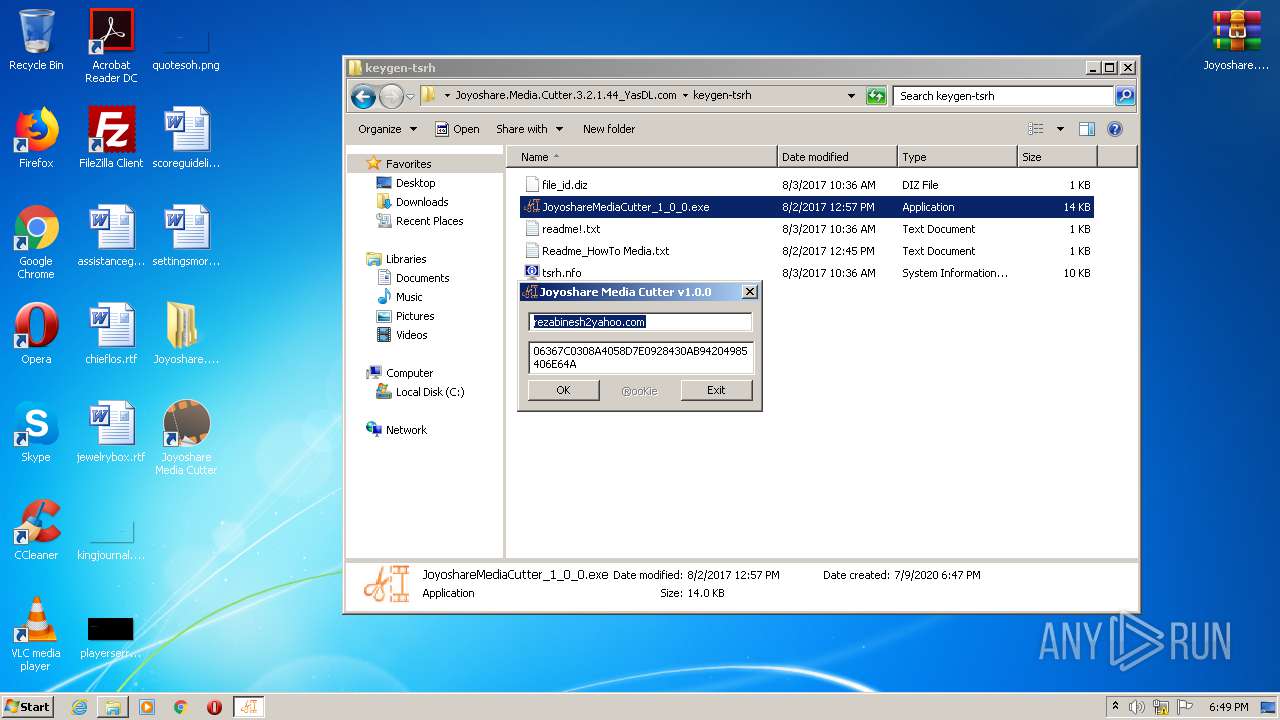
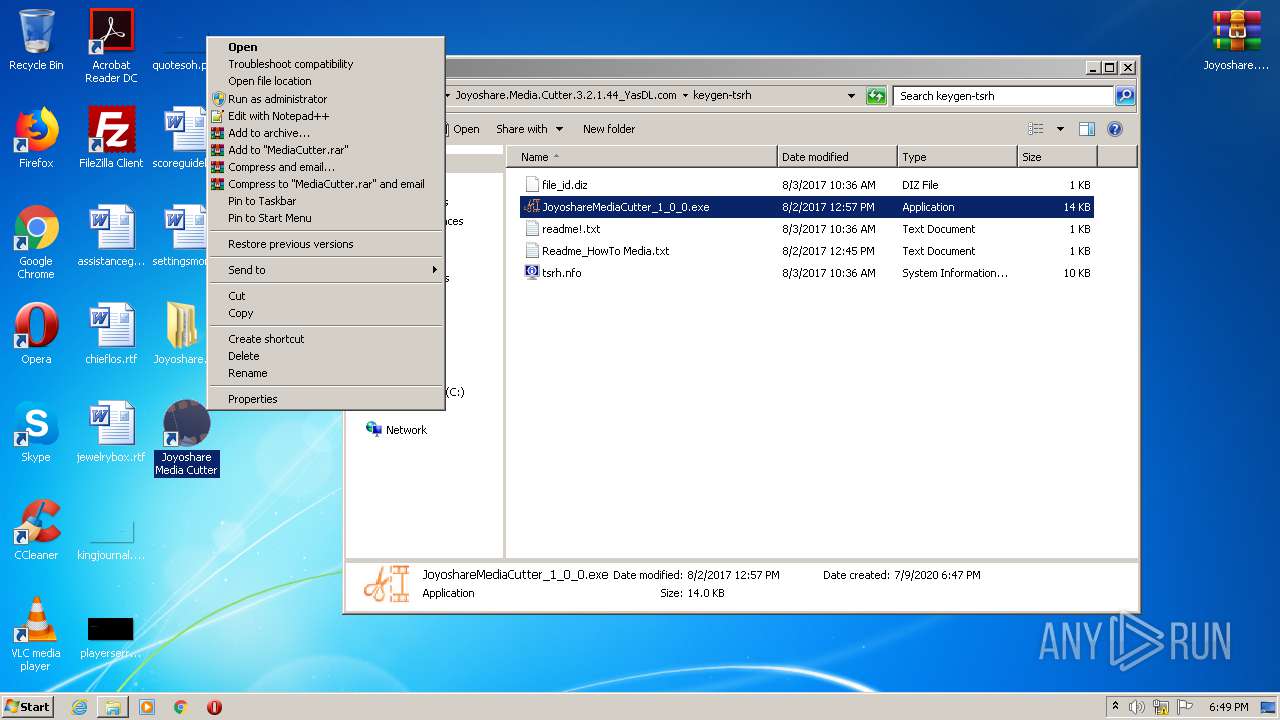
| 2412 | "C:\Users\admin\Desktop\Joyoshare.Media.Cutter.3.2.1.44_YasDL.com\Joyoshare.Media.Cutter.3.2.1.44_YasDL.com\keygen-tsrh\JoyoshareMediaCutter_1_0_0.exe" | C:\Users\admin\Desktop\Joyoshare.Media.Cutter.3.2.1.44_YasDL.com\Joyoshare.Media.Cutter.3.2.1.44_YasDL.com\keygen-tsrh\JoyoshareMediaCutter_1_0_0.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.joyoshare.com/api/product/redirect?pid=10100&page_type=install | C:\Program Files\Internet Explorer\iexplore.exe | — | Joyoshare.Media.Cutter.3.2.1.44_YasDL.com.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2684 | "C:\Program Files\Mozilla Firefox\firefox.exe" http://dl.yasdl.com/2020/Software/Joyoshare.Media.Cutter.3.2.1.44_YasDL.com.rar?fgy | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
Total events
11 338
Read events
6 746
Write events
3 388
Delete events
1 204
Modification events
| (PID) Process: | (2684) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 64E2D30400000000 | |||
| (PID) Process: | (1828) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 63E2D30400000000 | |||
| (PID) Process: | (2684) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (2684) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2684) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (348) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | 308046O0NS4N39PO |
Value: 00000000090000000D000000CC190500000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF605D425CD146D50100000000 | |||
| (PID) Process: | (348) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000004200000053000000C8ED25000B0000001A00000057BE0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000010000024E9ED017990C577B8006900000069000010000050E9ED01C4F6C4770000690000000000580269000002690064E9ED016C19C5770D00000000026900580269002CEBED0128EBED01000008009786217614E8ED0114EAED01D8E9ED0115E1C077C7670800FEFFFFFF8B8DC477108BC47701000000010000000000000004EAED01CCE9ED01E8E9ED012C8AC375010000000000000004EAED013F8AC375ED1805AB000000006CEFED0102000000FFFFFFFF0000000000000000000000000000E96FACE9ED01485F9B0050EEED01B514C5754D7B2BDFFEFFFFFF3F8AC375A36CC375A589C375651F05AB6CEFED0111000000483D3200403D32006CEFED017CEA0000C05704AB2CEAED018291D2767CEAED01EC430000FC5704AB40EAED01B69CD276F04311024C06000058EAED01603F110264EAED01789CD2763691D27611000000483D3200403D320000EBED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010B0000001A00000057BE0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000010000024E9ED017990C577B8006900000069000010000050E9ED01C4F6C4770000690000000000580269000002690064E9ED016C19C5770D00000000026900580269002CEBED0128EBED01000008009786217614E8ED0114EAED01D8E9ED0115E1C077C7670800FEFFFFFF8B8DC477108BC47701000000010000000000000004EAED01CCE9ED01E8E9ED012C8AC375010000000000000004EAED013F8AC375ED1805AB000000006CEFED0102000000FFFFFFFF0000000000000000000000000000E96FACE9ED01485F9B0050EEED01B514C5754D7B2BDFFEFFFFFF3F8AC375A36CC375A589C375651F05AB6CEFED0111000000483D3200403D32006CEFED017CEA0000C05704AB2CEAED018291D2767CEAED01EC430000FC5704AB40EAED01B69CD276F04311024C06000058EAED01603F110264EAED01789CD2763691D27611000000483D3200403D320000EBED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010B0000001A00000057BE0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000010000024E9ED017990C577B8006900000069000010000050E9ED01C4F6C4770000690000000000580269000002690064E9ED016C19C5770D00000000026900580269002CEBED0128EBED01000008009786217614E8ED0114EAED01D8E9ED0115E1C077C7670800FEFFFFFF8B8DC477108BC47701000000010000000000000004EAED01CCE9ED01E8E9ED012C8AC375010000000000000004EAED013F8AC375ED1805AB000000006CEFED0102000000FFFFFFFF0000000000000000000000000000E96FACE9ED01485F9B0050EEED01B514C5754D7B2BDFFEFFFFFF3F8AC375A36CC375A589C375651F05AB6CEFED0111000000483D3200403D32006CEFED017CEA0000C05704AB2CEAED018291D2767CEAED01EC430000FC5704AB40EAED01B69CD276F04311024C06000058EAED01603F110264EAED01789CD2763691D27611000000483D3200403D320000EBED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED01 | |||
| (PID) Process: | (2684) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2684) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (348) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithList |
| Operation: | write | Name: | a |
Value: firefox.exe | |||
Executable files
38
Suspicious files
80
Text files
370
Unknown types
65
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2684 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2684 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2684 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2684 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2684 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 2684 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 2684 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\except-flashallow-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 2684 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\except-flashallow-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 2684 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\except-flashsubdoc-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 2684 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\except-flashsubdoc-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
29
DNS requests
64
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2684 | firefox.exe | GET | 200 | 212.33.193.42:80 | http://dl.yasdl.com/2020/Software/Joyoshare.Media.Cutter.3.2.1.44_YasDL.com.rar?fgy | IR | compressed | 49.8 Mb | unknown |
912 | pingsender.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2244 | MediaCutter.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
912 | pingsender.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAd1LOvlIi%2FPXH0gOJhMUZg%3D | US | der | 471 b | whitelisted |
2684 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2684 | firefox.exe | GET | 200 | 2.16.177.51:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
2684 | firefox.exe | POST | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
2684 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2684 | firefox.exe | 212.33.193.42:80 | dl.yasdl.com | Honar Rayaneh Pooya Andisheh PJSC | IR | unknown |
2684 | firefox.exe | 34.211.106.52:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2684 | firefox.exe | 2.16.177.51:80 | detectportal.firefox.com | Akamai International B.V. | — | suspicious |
2684 | firefox.exe | 34.214.1.68:443 | push.services.mozilla.com | Amazon.com, Inc. | US | malicious |
2684 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2684 | firefox.exe | 172.217.23.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2684 | firefox.exe | 216.58.206.3:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2684 | firefox.exe | 2.16.177.49:443 | shavar.services.mozilla.com | Akamai International B.V. | — | unknown |
2684 | firefox.exe | 13.225.253.122:443 | firefox.settings.services.mozilla.com | — | US | unknown |
2684 | firefox.exe | 13.225.253.20:443 | content-signature-2.cdn.mozilla.net | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl.yasdl.com |
| unknown |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
Process | Message |
|---|---|
MediaCutter.exe | libpng warning: iCCP: known incorrect sRGB profile
|
MediaCutter.exe | libpng warning: iCCP: known incorrect sRGB profile
|
MediaCutter.exe | libpng warning: iCCP: known incorrect sRGB profile
|
MediaCutter.exe | libpng warning: iCCP: known incorrect sRGB profile
|
MediaCutter.exe | libpng warning: iCCP: known incorrect sRGB profile
|
MediaCutter.exe | libpng warning: iCCP: known incorrect sRGB profile
|
MediaCutter.exe | libpng warning: iCCP: known incorrect sRGB profile
|
MediaCutter.exe | libpng warning: iCCP: known incorrect sRGB profile
|
MediaCutter.exe | libpng warning: iCCP: known incorrect sRGB profile
|
MediaCutter.exe | libpng warning: iCCP: known incorrect sRGB profile
|